| File name: | 4bc9d43538c8550cf1015bd0cf789a1f9695275332976140ae5e9f341bda4147 |
| Full analysis: | https://app.any.run/tasks/1f2f6400-51fa-4b82-a9f6-61c3f75e9374 |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2025, 20:24:45 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | E646F195895274EF4A32860F7E7860A3 |
| SHA1: | D420F6E890A315C400DBA85C6AE486DB4FB807C7 |
| SHA256: | 4BC9D43538C8550CF1015BD0CF789A1F9695275332976140AE5E9F341BDA4147 |
| SSDEEP: | 98304:b1mDmVm3kOj3R7Mod/IRBuH2lmH4jy1CglcZuANk4GrfVst7Tcj1iUfqT/LQD/Il:KQtXCz92WUCnmIYwYhSZHlQ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- 4bc9d43538c8550cf1015bd0cf789a1f9695275332976140ae5e9f341bda4147.exe (PID: 3540)
Contacting a server suspected of hosting an CnC
- 4bc9d43538c8550cf1015bd0cf789a1f9695275332976140ae5e9f341bda4147.exe (PID: 3540)
Executes application which crashes
- 怀旧.exe (PID: 3836)
Connects to unusual port
- 4bc9d43538c8550cf1015bd0cf789a1f9695275332976140ae5e9f341bda4147.exe (PID: 3540)
INFO
Create files in a temporary directory
- 4bc9d43538c8550cf1015bd0cf789a1f9695275332976140ae5e9f341bda4147.exe (PID: 3540)
Reads the computer name
- 4bc9d43538c8550cf1015bd0cf789a1f9695275332976140ae5e9f341bda4147.exe (PID: 3540)
Checks supported languages
- 4bc9d43538c8550cf1015bd0cf789a1f9695275332976140ae5e9f341bda4147.exe (PID: 3540)
- 怀旧.exe (PID: 3836)
The sample compiled with chinese language support
- 4bc9d43538c8550cf1015bd0cf789a1f9695275332976140ae5e9f341bda4147.exe (PID: 3540)
Sends debugging messages
- 4bc9d43538c8550cf1015bd0cf789a1f9695275332976140ae5e9f341bda4147.exe (PID: 3540)
Checks proxy server information
- WerFault.exe (PID: 5732)
Creates files or folders in the user directory
- WerFault.exe (PID: 5732)
Reads the software policy settings
- WerFault.exe (PID: 5732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:06:13 05:28:34+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 3942912 |
| InitializedDataSize: | 1898496 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1b7b6b |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.3 |
| ProductVersionNumber: | 1.0.0.3 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 1.0.0.3 |
| InternalName: | Cloud Application |
| LegalCopyright: | Copyright (C) 2021 |
| ProductName: | Cloud Application |
| ProductVersion: | 1.0.0.3 |
Total processes
124
Monitored processes
4
Malicious processes
1
Suspicious processes
0
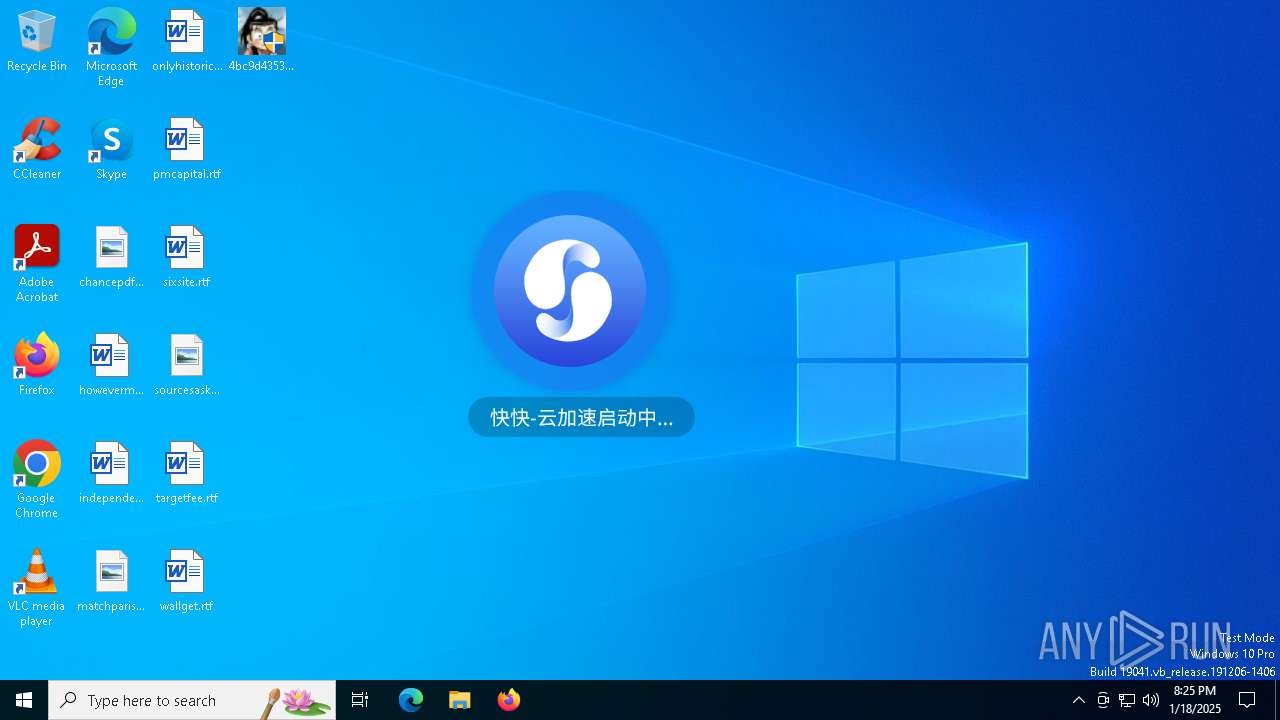
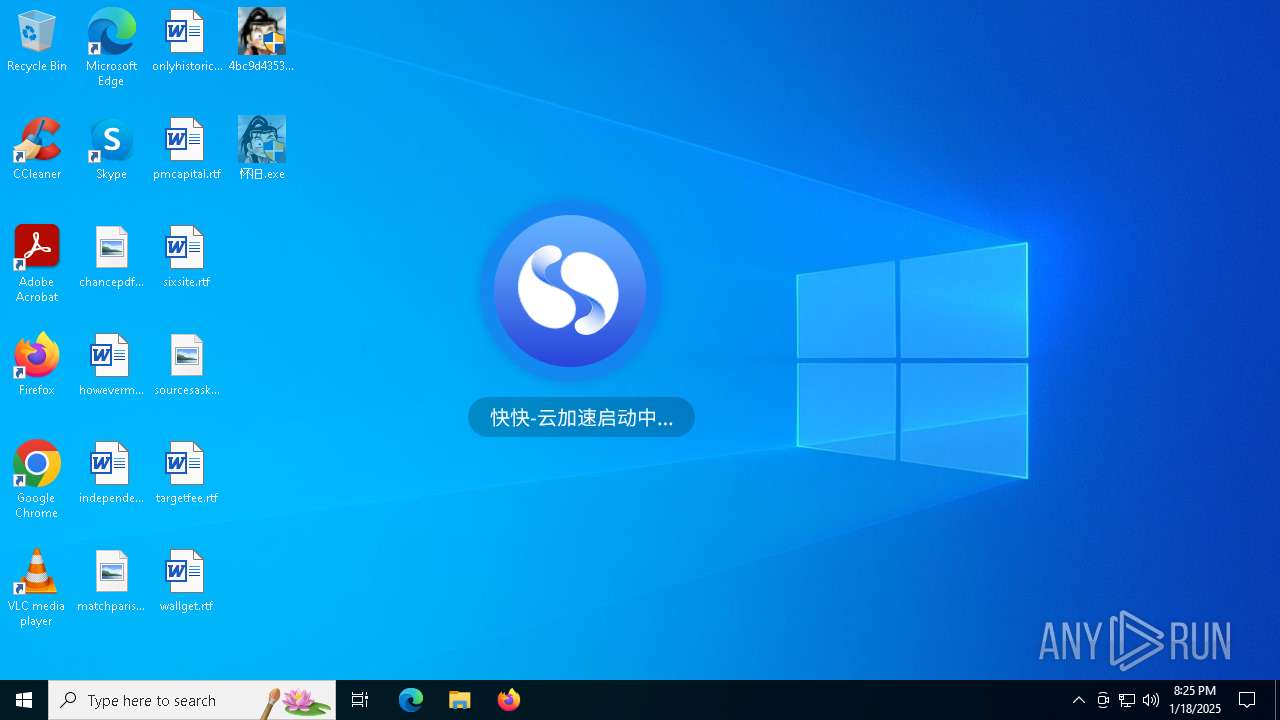
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3540 | "C:\Users\admin\Desktop\4bc9d43538c8550cf1015bd0cf789a1f9695275332976140ae5e9f341bda4147.exe" | C:\Users\admin\Desktop\4bc9d43538c8550cf1015bd0cf789a1f9695275332976140ae5e9f341bda4147.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Version: 1.0.0.3 Modules
| |||||||||||||||
| 3836 | C:\Users\admin\Desktop\怀旧.exe | C:\Users\admin\Desktop\怀旧.exe | 4bc9d43538c8550cf1015bd0cf789a1f9695275332976140ae5e9f341bda4147.exe | ||||||||||||
User: admin Company: TODO: <公司名> Integrity Level: HIGH Description: MLogin Exit code: 3221226505 Version: 1.0.0.1 Modules
| |||||||||||||||
| 4144 | "C:\Users\admin\Desktop\4bc9d43538c8550cf1015bd0cf789a1f9695275332976140ae5e9f341bda4147.exe" | C:\Users\admin\Desktop\4bc9d43538c8550cf1015bd0cf789a1f9695275332976140ae5e9f341bda4147.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.0.0.3 Modules
| |||||||||||||||
| 5732 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 3836 -s 648 | C:\Windows\SysWOW64\WerFault.exe | 怀旧.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 278
Read events
6 251
Write events
24
Delete events
3
Modification events
| (PID) Process: | (5732) WerFault.exe | Key: | \REGISTRY\A\{bb093f21-0469-942a-d3f2-656f126c8ca2}\Root\InventoryApplicationFile\怀旧.exe|81b15029bdd440f5 |
| Operation: | write | Name: | ProgramId |
Value: 00069deb4747a8fc079baff90408de3fd3c600000408 | |||
| (PID) Process: | (5732) WerFault.exe | Key: | \REGISTRY\A\{bb093f21-0469-942a-d3f2-656f126c8ca2}\Root\InventoryApplicationFile\怀旧.exe|81b15029bdd440f5 |
| Operation: | write | Name: | FileId |
Value: 0000d730d8e262775f06476caad4ce1fa625121949d9 | |||
| (PID) Process: | (5732) WerFault.exe | Key: | \REGISTRY\A\{bb093f21-0469-942a-d3f2-656f126c8ca2}\Root\InventoryApplicationFile\怀旧.exe|81b15029bdd440f5 |
| Operation: | write | Name: | LowerCaseLongPath |
Value: c:\users\admin\desktop\怀旧.exe | |||
| (PID) Process: | (5732) WerFault.exe | Key: | \REGISTRY\A\{bb093f21-0469-942a-d3f2-656f126c8ca2}\Root\InventoryApplicationFile\怀旧.exe|81b15029bdd440f5 |
| Operation: | write | Name: | LongPathHash |
Value: 怀旧.exe|81b15029bdd440f5 | |||
| (PID) Process: | (5732) WerFault.exe | Key: | \REGISTRY\A\{bb093f21-0469-942a-d3f2-656f126c8ca2}\Root\InventoryApplicationFile\怀旧.exe|81b15029bdd440f5 |
| Operation: | write | Name: | Name |
Value: 怀旧.exe | |||
| (PID) Process: | (5732) WerFault.exe | Key: | \REGISTRY\A\{bb093f21-0469-942a-d3f2-656f126c8ca2}\Root\InventoryApplicationFile\怀旧.exe|81b15029bdd440f5 |
| Operation: | write | Name: | OriginalFileName |
Value: mlogin.exe | |||
| (PID) Process: | (5732) WerFault.exe | Key: | \REGISTRY\A\{bb093f21-0469-942a-d3f2-656f126c8ca2}\Root\InventoryApplicationFile\怀旧.exe|81b15029bdd440f5 |
| Operation: | write | Name: | Publisher |
Value: todo: <公司名> | |||
| (PID) Process: | (5732) WerFault.exe | Key: | \REGISTRY\A\{bb093f21-0469-942a-d3f2-656f126c8ca2}\Root\InventoryApplicationFile\怀旧.exe|81b15029bdd440f5 |
| Operation: | write | Name: | Version |
Value: 1.0.0.1 | |||
| (PID) Process: | (5732) WerFault.exe | Key: | \REGISTRY\A\{bb093f21-0469-942a-d3f2-656f126c8ca2}\Root\InventoryApplicationFile\怀旧.exe|81b15029bdd440f5 |
| Operation: | write | Name: | BinFileVersion |
Value: 1.0.0.1 | |||
| (PID) Process: | (5732) WerFault.exe | Key: | \REGISTRY\A\{bb093f21-0469-942a-d3f2-656f126c8ca2}\Root\InventoryApplicationFile\怀旧.exe|81b15029bdd440f5 |
| Operation: | write | Name: | BinaryType |
Value: pe32_i386 | |||
Executable files
1
Suspicious files
3
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5732 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_怀旧.exe_3a6f9e8cdff2ed3c75c9bc37b286bc218ecaf_402a0698_1956ee0b-87d3-4731-8c3f-2e2ce9101bd8\Report.wer | — | |
MD5:— | SHA256:— | |||
| 3540 | 4bc9d43538c8550cf1015bd0cf789a1f9695275332976140ae5e9f341bda4147.exe | C:\Users\admin\AppData\Local\Temp\yjs_log\log.log | text | |
MD5:D3D16A011EE850EE79AE05184D426CD1 | SHA256:65C723DF5482D14F33689447D90E7C9929C2A3BFA08E02B68DB1ED991D4DB53C | |||
| 5732 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\怀旧.exe.3836.dmp | binary | |
MD5:2B4D006E004A7E57748D67C199C3A1BF | SHA256:8A614ECC71BBB76108CA3DB49DE673BF118AC40C1241624F0A40BCA555B7CA19 | |||
| 3540 | 4bc9d43538c8550cf1015bd0cf789a1f9695275332976140ae5e9f341bda4147.exe | C:\Users\admin\Desktop\怀旧.exe | executable | |
MD5:914DE53C08202C9D5F20D1ACF175A97F | SHA256:4101D2F5E29B2D58F2F9414BD6E2296EDF9333308C4620D2AA8A35F3A8FCCD9A | |||
| 5732 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER8439.tmp.xml | xml | |
MD5:0A283AAFE3950537DEF4DFEACD5F00CD | SHA256:0461670DD589C4FCFC2F68468843155705338615482C5CD9B1B1EBF33F45ABF6 | |||
| 5732 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER82FE.tmp.dmp | binary | |
MD5:763E507570DCE3430046BE605DD1BB8B | SHA256:3007DCE6F6EF2D5E55385F9BD5F910054AC4F519FF162EADB133188DD68490C3 | |||
| 5732 | WerFault.exe | C:\Windows\appcompat\Programs\Amcache.hve | binary | |
MD5:6B5AC80C4273D57562E6AE5FADC4D32E | SHA256:2473AD47E3F8E1F5EE419741CBC25D015725CCBD7B9448244C55D52DDDADEFAA | |||
| 5732 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER83F9.tmp.WERInternalMetadata.xml | xml | |
MD5:84164B9736A5BCAC724363590857BF80 | SHA256:EE6428F37CDE076281BD279AAB668DB057D56E0803DEF7484BFF8A4915BDC5AF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
37
DNS requests
11
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.173:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5780 | svchost.exe | GET | 200 | 23.48.23.173:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5780 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 104.126.37.129:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5780 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.173:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5780 | svchost.exe | 23.48.23.173:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5780 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
config.yunjiasu.kkidc.com |
| malicious |
watson.events.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
4bc9d43538c8550cf1015bd0cf789a1f9695275332976140ae5e9f341bda4147.exe | CheckHypeVRegistry2222 |
4bc9d43538c8550cf1015bd0cf789a1f9695275332976140ae5e9f341bda4147.exe | CheckHypeVRegistry2222 |