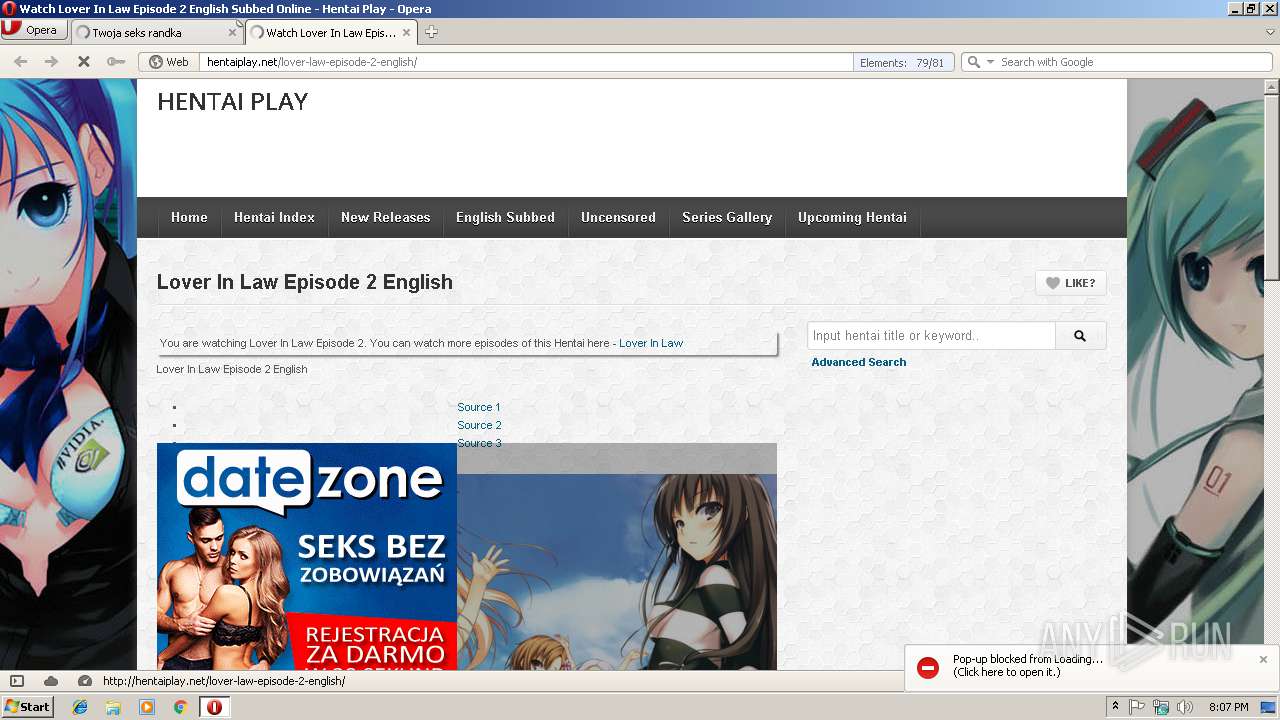
| URL: | http://hentaiplay.net/lover-law-episode-2-english/ |
| Full analysis: | https://app.any.run/tasks/73ff851c-1402-442c-b5d7-aaf4fdd1b119 |
| Verdict: | Suspicious activity |
| Analysis date: | December 23, 2018, 20:06:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6F1127343C32A8015EA1085F82F5AA1A |
| SHA1: | 4AA901C9565F58D11BBCA2331AA86B8778D1F0FE |
| SHA256: | 4BC188CFDF87974FB0597AEAC5C000E2993A7D9CC4E6A9CF5F9E5CE96EDF831B |
| SSDEEP: | 3:N1KWAllGTC5NBXWNK:CWegTCNwK |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Creates files in the user directory
- opera.exe (PID: 2952)
Connects to unusual port
- opera.exe (PID: 2952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
31
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2952 | "C:\Program Files\Opera\opera.exe" http://hentaiplay.net/lover-law-episode-2-english/ | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
Total events
302
Read events
241
Write events
61
Delete events
0
Modification events
| (PID) Process: | (2952) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe http://hentaiplay.net/lover-law-episode-2-english/ | |||
| (PID) Process: | (2952) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2952) opera.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: opera.exe | |||
Executable files
0
Suspicious files
59
Text files
62
Unknown types
74
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2952 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr9D11.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr9D22.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr9D71.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr0000V.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\DXA9P8DPN8BS8707LULE.temp | — | |
MD5:— | SHA256:— | |||
| 2952 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\oprAF44.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\autosave.win | text | |
MD5:— | SHA256:— | |||
| 2952 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\autosave.win.bak | text | |
MD5:— | SHA256:— | |||
| 2952 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 2952 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
177
TCP/UDP connections
133
DNS requests
77
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2952 | opera.exe | GET | — | 104.28.31.15:80 | http://hentaiplay.net/wp-content/plugins/wordpress-post-tabs/js/jquery.posttabs.js?ver=1.6.2 | US | — | — | whitelisted |
2952 | opera.exe | GET | — | 104.28.31.15:80 | http://hentaiplay.net/wp-content/plugins/wordpress-post-tabs/css/styles/default/style.css?ver=1.6.2 | US | — | — | whitelisted |
2952 | opera.exe | GET | — | 104.28.31.15:80 | http://hentaiplay.net/wp-content/plugins/addthis/css/output.css?ver=b6f93314c71f6df8e11e07e6d1ff3acc | US | — | — | whitelisted |
2952 | opera.exe | GET | — | 104.28.31.15:80 | http://hentaiplay.net/wp-content/uploads/favicon.ico | US | — | — | whitelisted |
2952 | opera.exe | GET | — | 104.28.31.15:80 | http://hentaiplay.net/wp-content/uploads/Kuroinu_Kedakaki_Seijo_wa_Hakudaku_ni_Somaru_Episode_6-1-160x90.jpg | US | — | — | whitelisted |
2952 | opera.exe | GET | — | 104.28.31.15:80 | http://hentaiplay.net/wp-content/themes/detube/style.css?ver=1.4.3 | US | — | — | whitelisted |
2952 | opera.exe | GET | — | 104.28.31.15:80 | http://hentaiplay.net/wp-content/uploads/Maken_no_Hime_wa_Ero_Ero_Desu_Episode_2-160x90.jpg | US | — | — | whitelisted |
2952 | opera.exe | GET | — | 104.28.31.15:80 | http://hentaiplay.net/wp-includes/js/jquery/ui/core.min.js?ver=1.11.4 | US | — | — | whitelisted |
2952 | opera.exe | GET | — | 104.28.31.15:80 | http://hentaiplay.net/wp-content/plugins/wp-pagenavi/pagenavi-css.css?ver=2.70 | US | — | — | whitelisted |
2952 | opera.exe | GET | — | 104.28.31.15:80 | http://hentaiplay.net/wp-content/plugins/ultimate-wp-query-search-filter/themes/default.css?ver=all | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2952 | opera.exe | 104.28.31.15:80 | hentaiplay.net | Cloudflare Inc | US | shared |
2952 | opera.exe | 185.26.182.93:80 | sitecheck2.opera.com | Opera Software AS | — | whitelisted |
2952 | opera.exe | 66.225.197.197:80 | crl4.digicert.com | CacheNetworks, Inc. | US | whitelisted |
2952 | opera.exe | 208.93.230.16:80 | st.chatango.com | Chatango LLC | US | unknown |
2952 | opera.exe | 216.58.205.234:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2952 | opera.exe | 52.222.161.54:443 | content.jwplatform.com | Amazon.com, Inc. | US | unknown |
2952 | opera.exe | 205.185.216.42:443 | ads.exosrv.com | Highwinds Network Group, Inc. | US | whitelisted |
2952 | opera.exe | 185.94.236.126:80 | adserver.juicyads.com | Mojohost B.v. | NL | unknown |
2952 | opera.exe | 23.210.248.44:80 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
2952 | opera.exe | 104.28.30.15:80 | hentaiplay.net | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hentaiplay.net |
| whitelisted |
sitecheck2.opera.com |
| whitelisted |
certs.opera.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
content.jwplatform.com |
| shared |
vjs.zencdn.net |
| whitelisted |
ads.exosrv.com |
| whitelisted |
st.chatango.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2952 | opera.exe | A Network Trojan was detected | SC BAD_UNKNOWN Trojan Unknown JS |
2952 | opera.exe | A Network Trojan was detected | SC BAD_UNKNOWN Trojan Unknown JS |