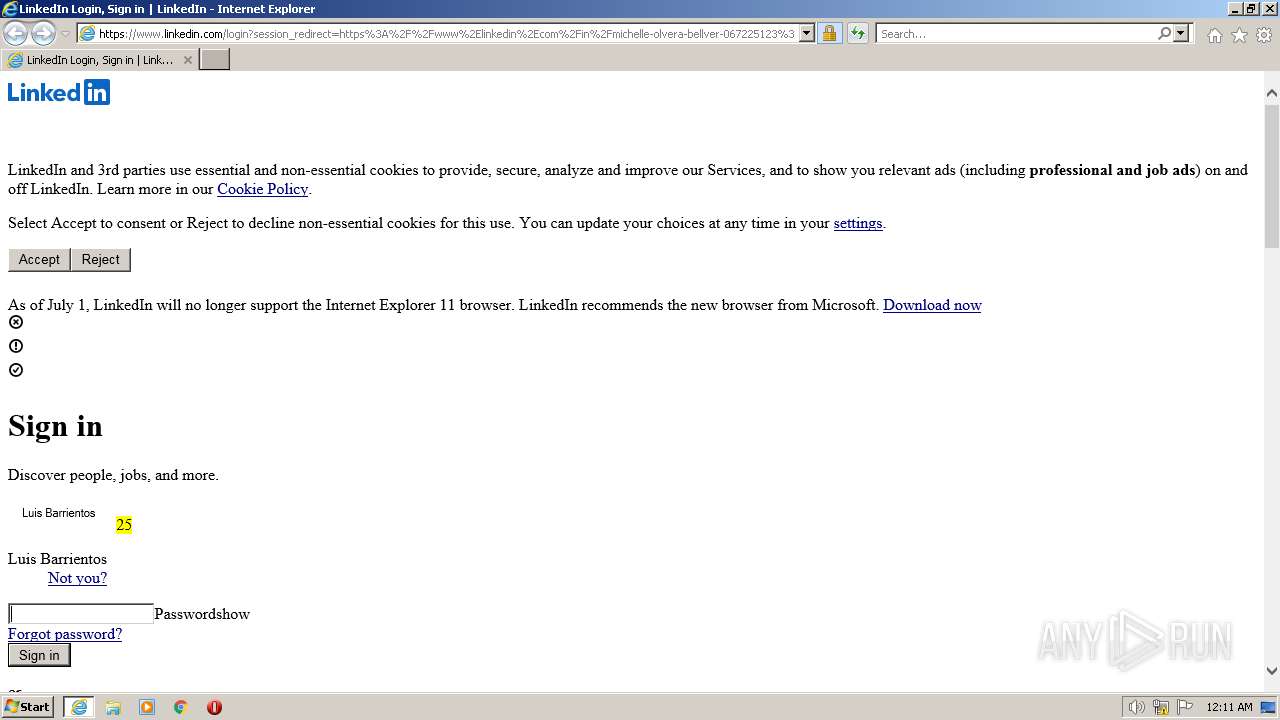
| URL: | https://www.linkedin.com/comm/in/michelle-olvera-bellver-067225123?midToken=AQGg__bSHlkXYw&midSig=1YyJ8WEhiR6qQ1&trk=eml-email_hire_inmail_initial_single_01-null-1-null&trkEmail=eml-email_hire_inmail_initial_single_01-null-1-null-null-8tl926%7Elj4psqwt%7E1o-null-neptune%2Fprofile%7Evanity%2Eview&lipi=urn%3Ali%3Apage%3Aemail_email_hire_inmail_initial_single_01%3B%2F7zy%2BZ37SLiSlDoiFYWG9g%3D%3D |
| Full analysis: | https://app.any.run/tasks/771dcab3-cc42-4935-afd2-ac21923fed18 |
| Verdict: | Malicious activity |
| Analysis date: | June 20, 2023, 23:11:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 80F824450940E0F1590D55A25CFF577D |
| SHA1: | E85AA9B8C283C503513A418BFD720E4FF6B8200B |
| SHA256: | 4BBEB83B93B590F6987C4A4548D09D249D61550D2D004D92762336B2626BD4D1 |
| SSDEEP: | 12:2ZBTRzboJemNZSTLQbiVSTLQbe4I35XorxldSTL7X7:29zQxqHQHqI35XotlkHv |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 2524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2524 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.linkedin.com/comm/in/michelle-olvera-bellver-067225123?midToken=AQGg__bSHlkXYw&midSig=1YyJ8WEhiR6qQ1&trk=eml-email_hire_inmail_initial_single_01-null-1-null&trkEmail=eml-email_hire_inmail_initial_single_01-null-1-null-null-8tl926%7Elj4psqwt%7E1o-null-neptune%2Fprofile%7Evanity%2Eview&lipi=urn%3Ali%3Apage%3Aemail_email_hire_inmail_initial_single_01%3B%2F7zy%2BZ37SLiSlDoiFYWG9g%3D%3D" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2612 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2524 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
9 799
Read events
9 698
Write events
101
Delete events
0
Modification events
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
10
Text files
23
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2524 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\urlblockindex[1].bin | binary | |
MD5:FA518E3DFAE8CA3A0E495460FD60C791 | SHA256:775853600060162C4B4E5F883F9FD5A278E61C471B3EE1826396B6D129499AA7 | |||
| 2524 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:1799F1287955C907F48333017D2FED25 | SHA256:71CB64618B3B93CF1BA379E2C9EB7AFEC97CD9362B06EC8408CC204AFE4E78CA | |||
| 2524 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\verDCB1.tmp | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 2612 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\8C6I63JI.txt | text | |
MD5:1574919ECC6D196F33417B6011FB5579 | SHA256:8A0D153EED0B67E117252EEF3AE718D7418E3E7A2A88588D1B8EDCDBF424EEAC | |||
| 2524 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:57CDF6110F9169470652840B9AD5174A | SHA256:E735BE26082EAEE491597B63AE68B20A2FB1CE4A580369357525A4DF60629FA1 | |||
| 2612 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\P246JZJN.txt | text | |
MD5:B07B13322C0BEA4643F97F3B064E67A0 | SHA256:02E07163677E967182F8ED69CBA6983B30D4229443F04F77D8CFF919B8829612 | |||
| 2612 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\R2575IKP.txt | text | |
MD5:3E12287B9F1E8B44EC1998D85568A309 | SHA256:2719DEA7BB20FA8E9B7263B7870C56FC314090C57D3B5A2325C7B86E3FC328AC | |||
| 2612 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\PAU3P32Q.txt | text | |
MD5:41F0DBB223399FC31264E5C8C26F9C60 | SHA256:A34A3DC943EAC1B435CEFD23382501D541E933902BDA1863D8F852B535D2D988 | |||
| 2612 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\login[1].htm | html | |
MD5:CC3FD374195CD10D1FAE747DBB2EF65B | SHA256:D7E3715FBC36998285BAC7FC6A41306E47BEE2E9BDD1319F465F89ED33F16AC8 | |||
| 2524 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\versionlist.xml | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
54
DNS requests
12
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2612 | iexplore.exe | GET | 200 | 8.241.11.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6d3fb5d6fdecd2a3 | US | compressed | 4.70 Kb | whitelisted |
2524 | iexplore.exe | GET | 200 | 8.241.11.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?59d339eb4d54cce4 | US | compressed | 4.70 Kb | whitelisted |
2524 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | binary | 1.47 Kb | whitelisted |
2524 | iexplore.exe | GET | 200 | 67.27.234.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6788adf694d356e3 | US | compressed | 4.70 Kb | whitelisted |
2524 | iexplore.exe | GET | 200 | 67.27.234.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0988c3d78d136b55 | US | compressed | 4.70 Kb | whitelisted |
2524 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
568 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2612 | iexplore.exe | 13.107.42.14:443 | www.linkedin.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | suspicious |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2612 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2612 | iexplore.exe | 67.27.234.126:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2524 | iexplore.exe | 67.27.234.126:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
2524 | iexplore.exe | 2.23.209.185:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
2524 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.linkedin.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
static.licdn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2612 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2612 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2612 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2612 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2612 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2612 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2612 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2524 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2524 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |