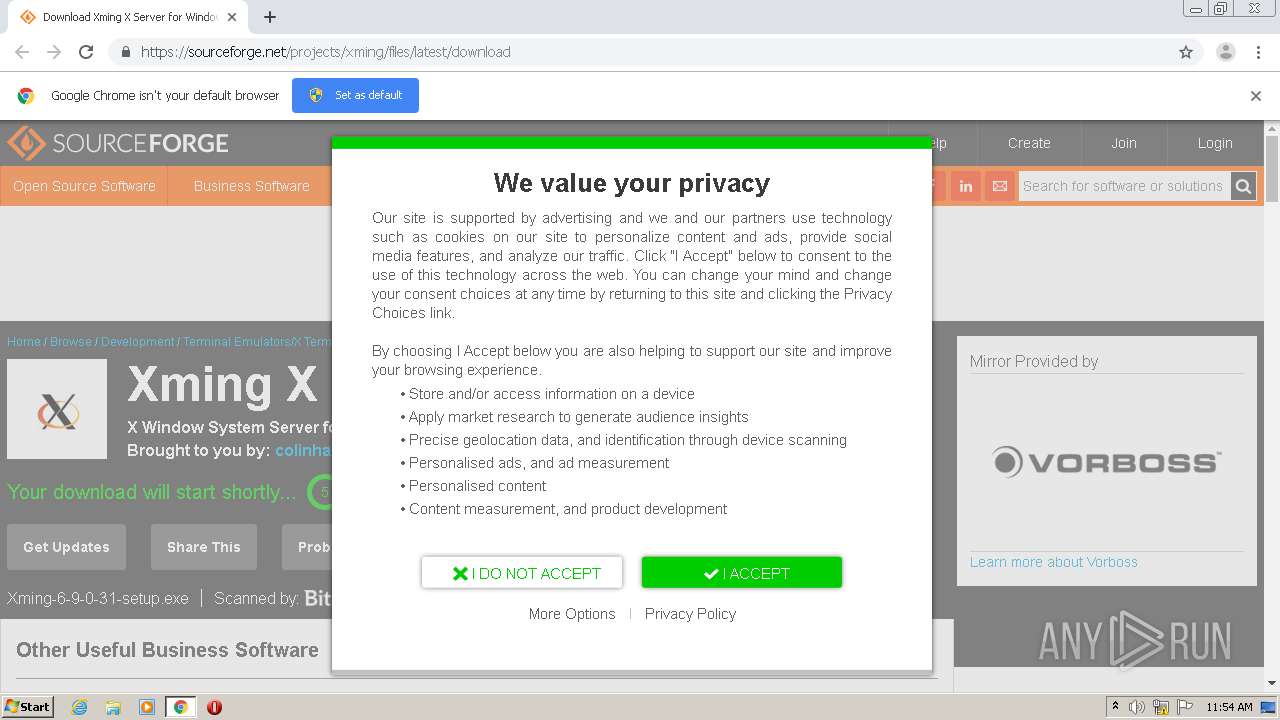
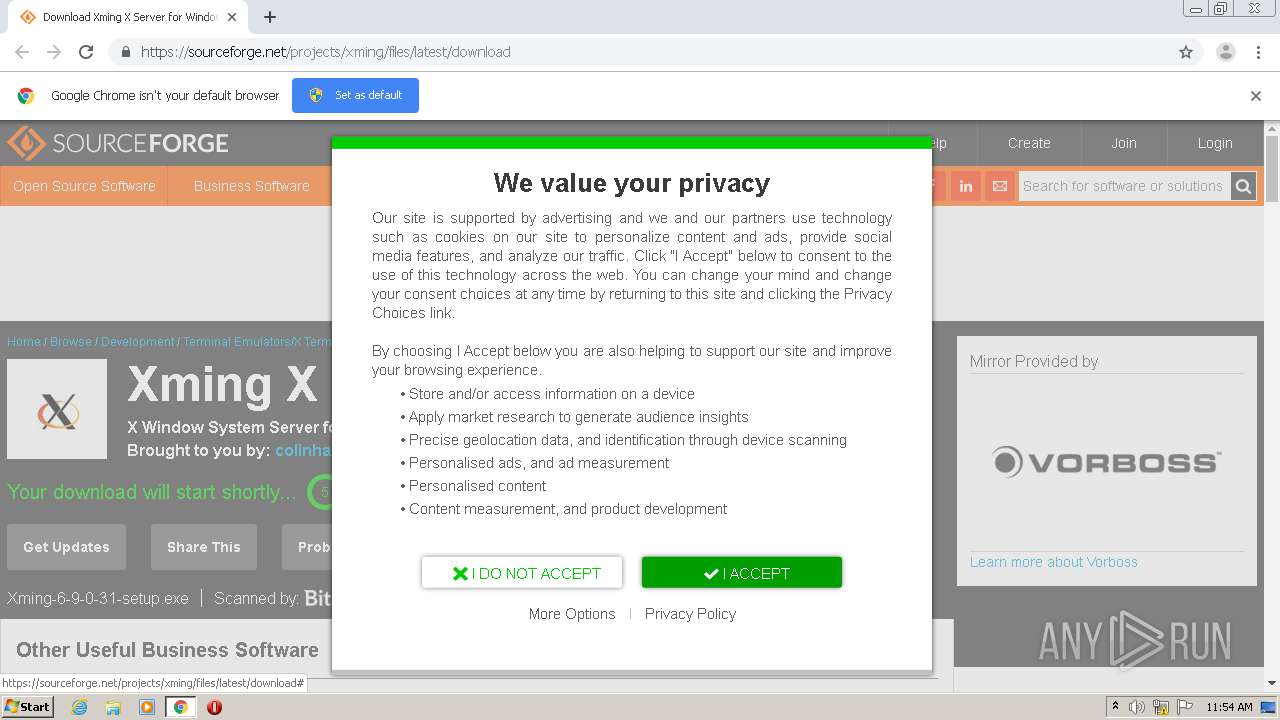
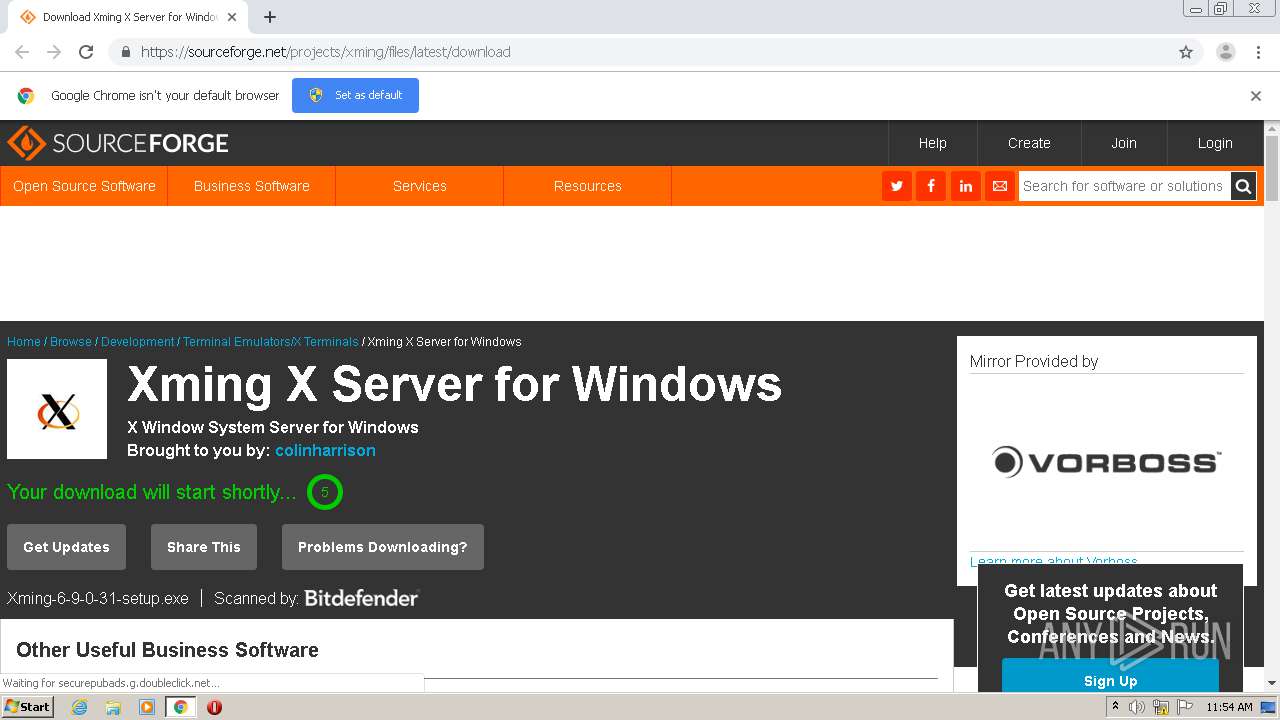
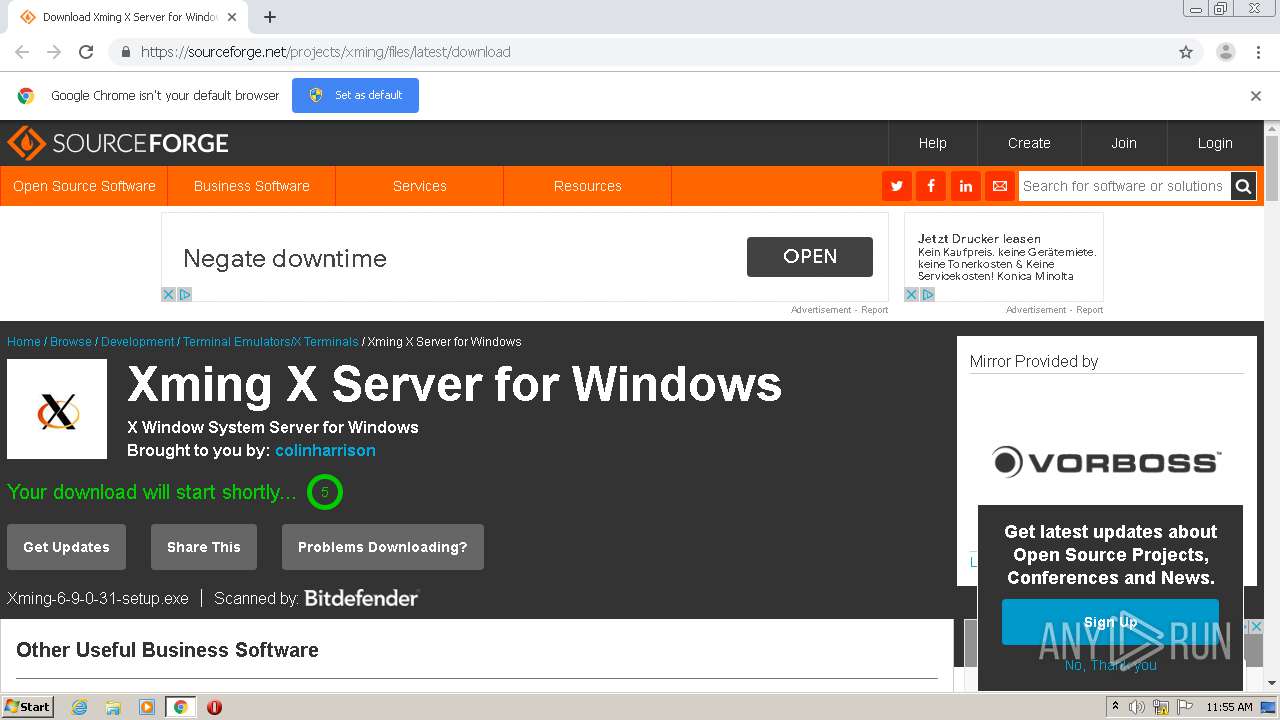
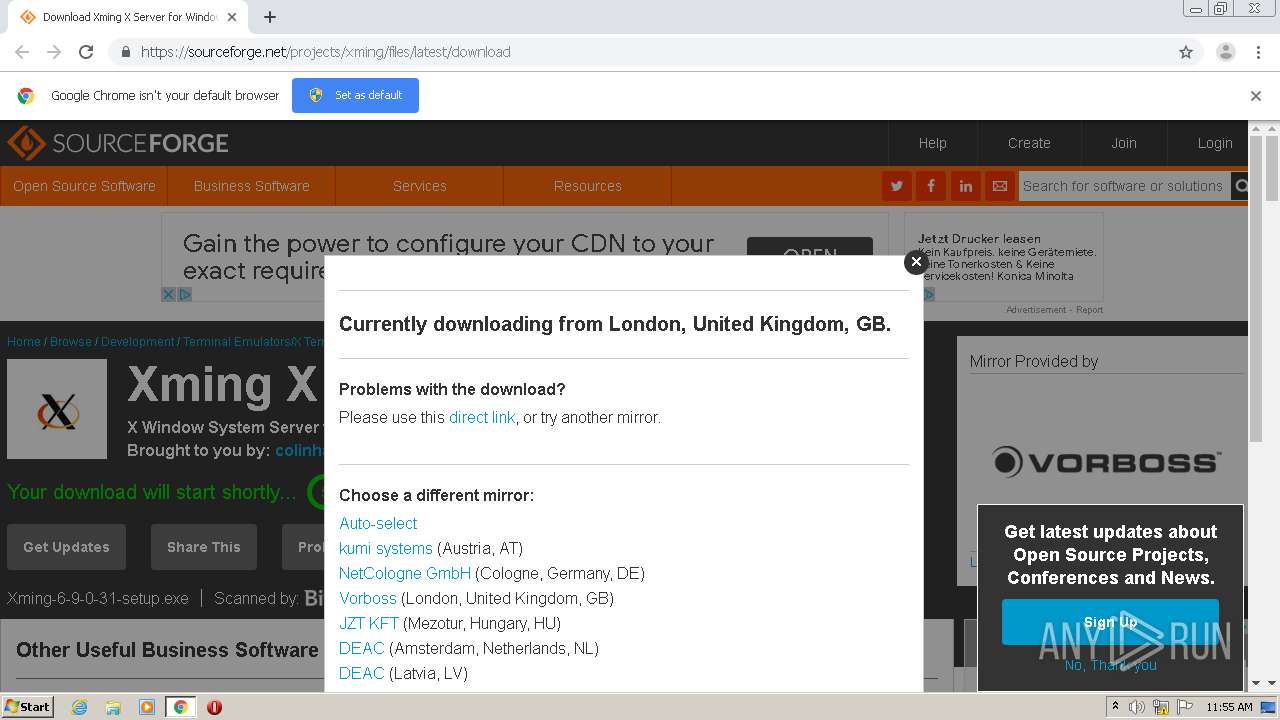
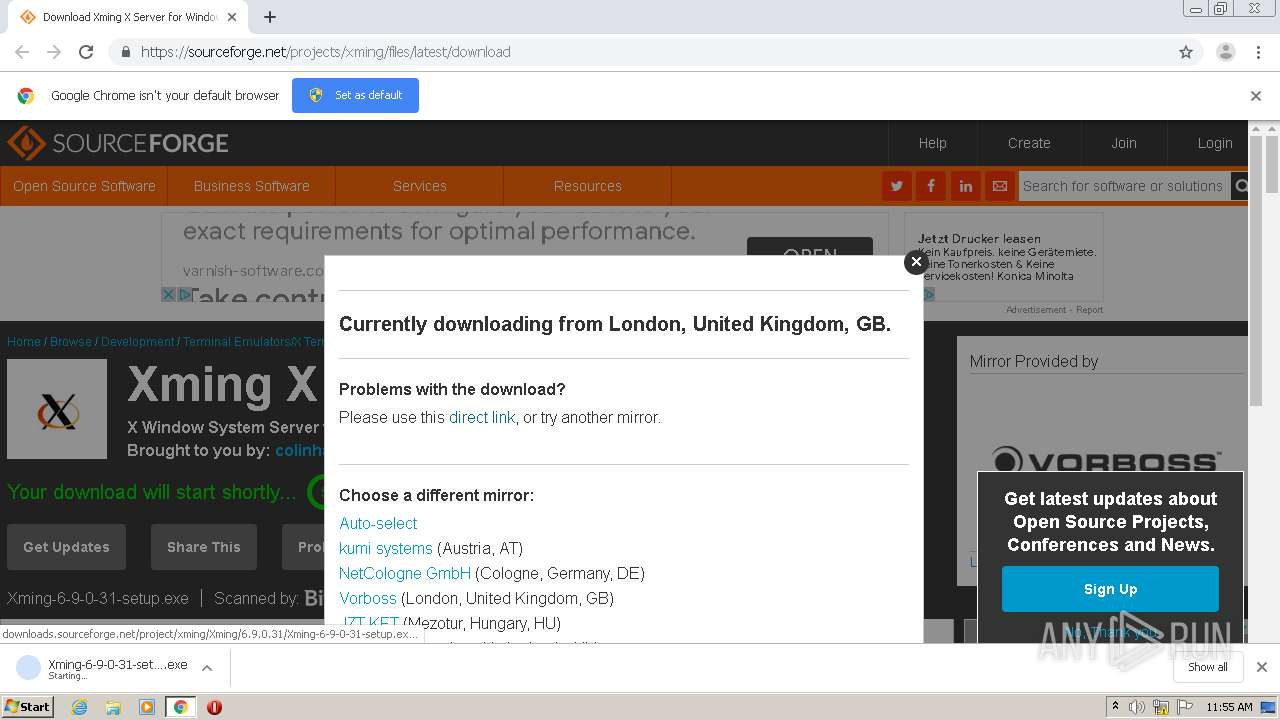
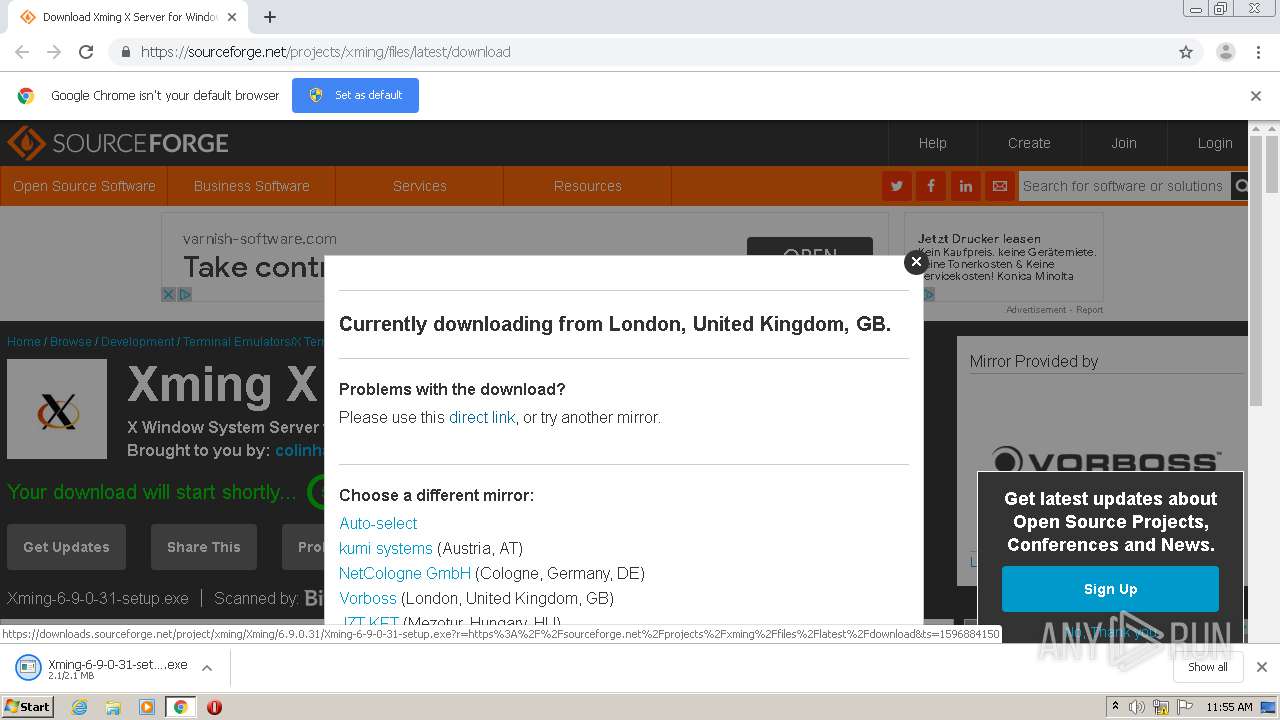
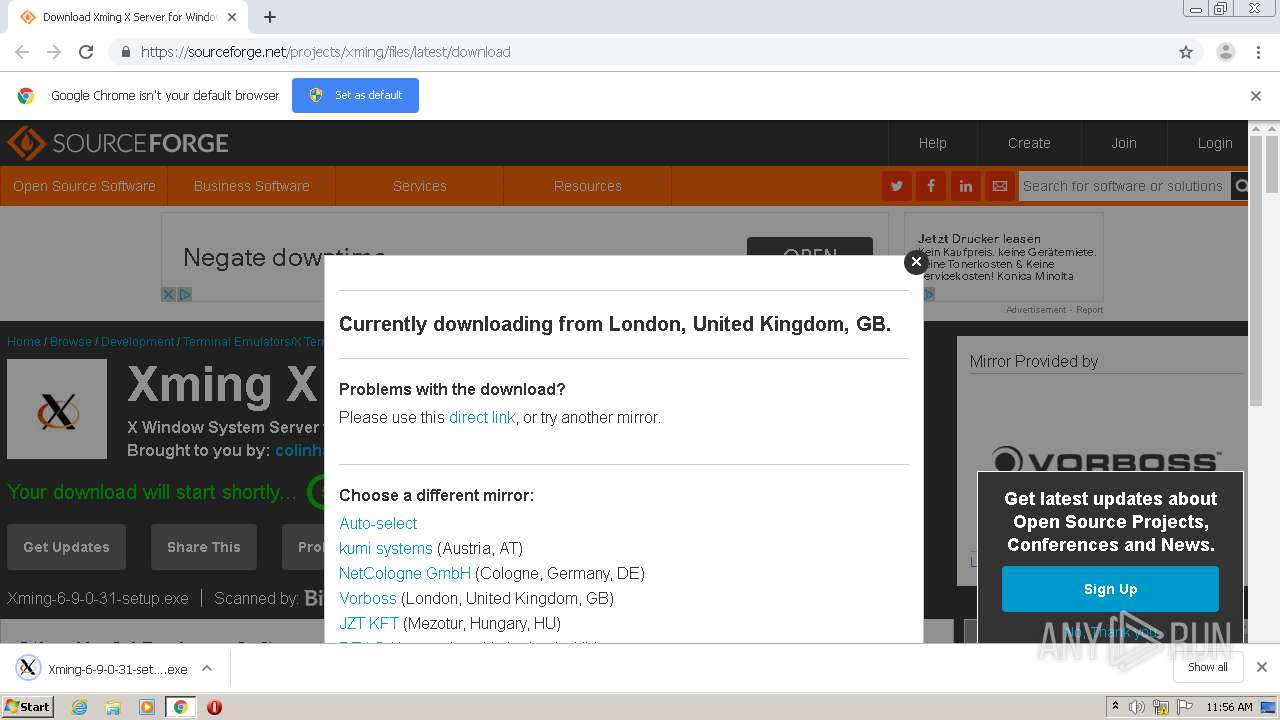
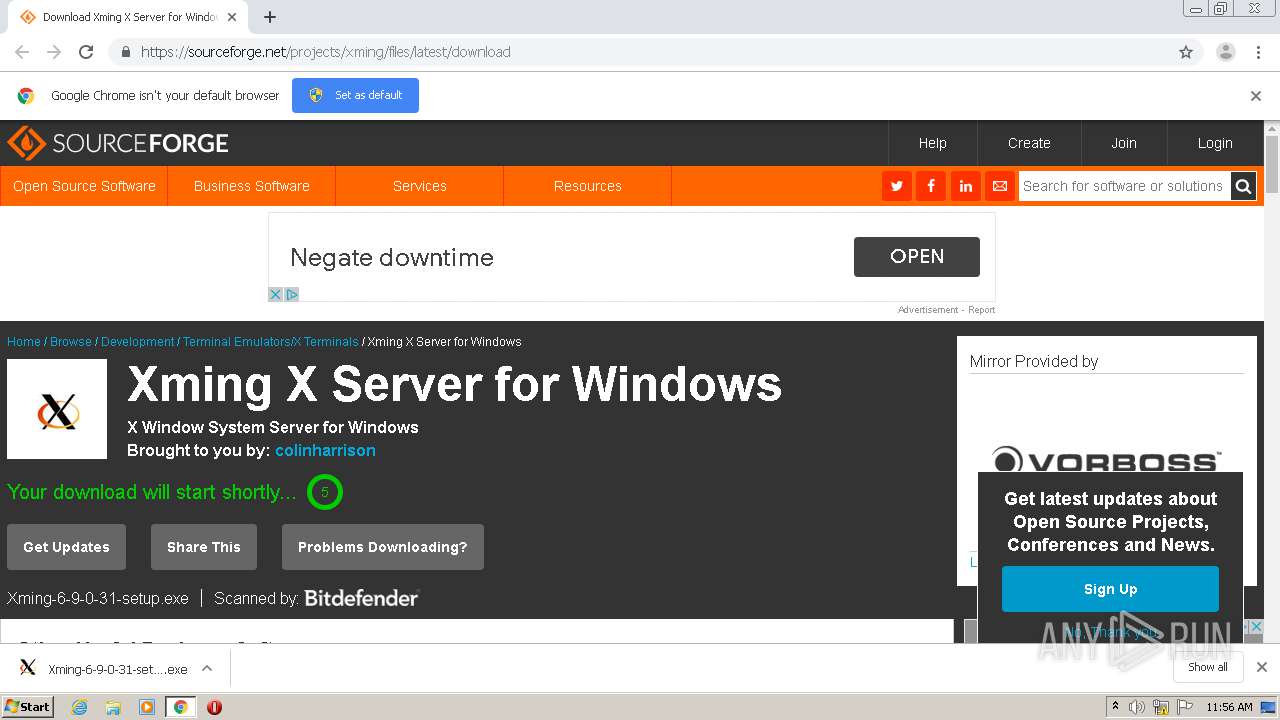
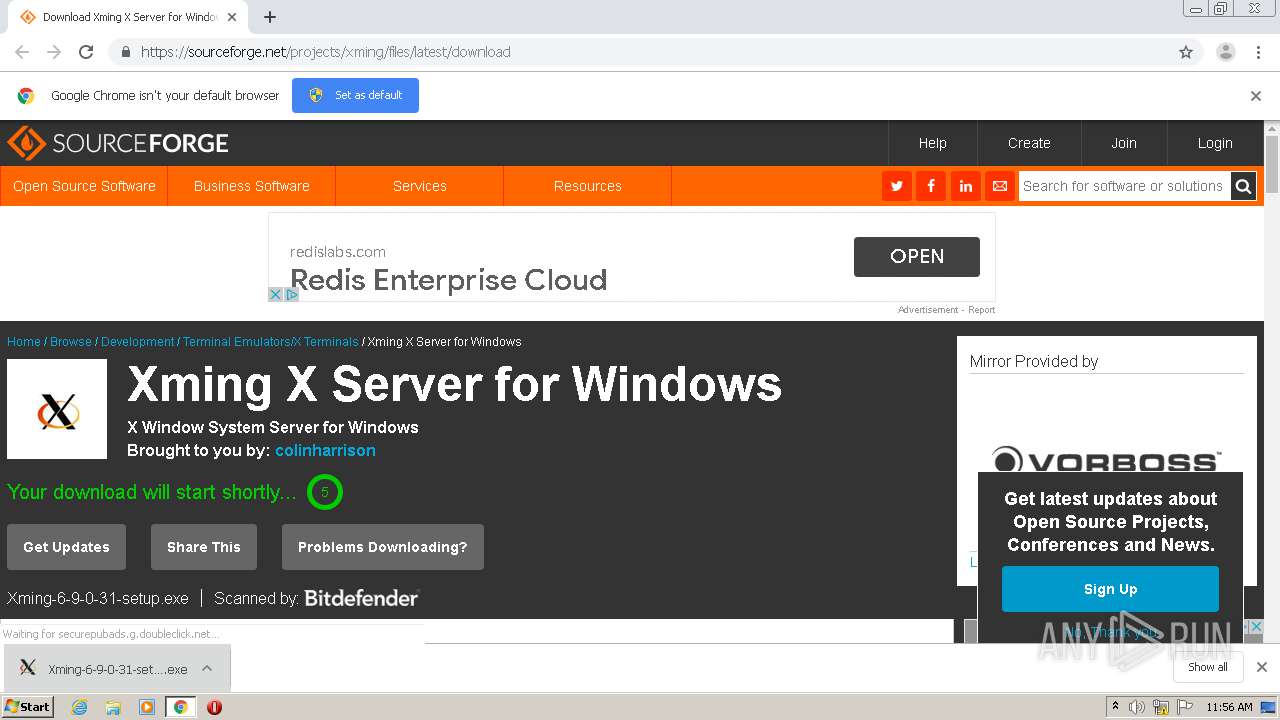
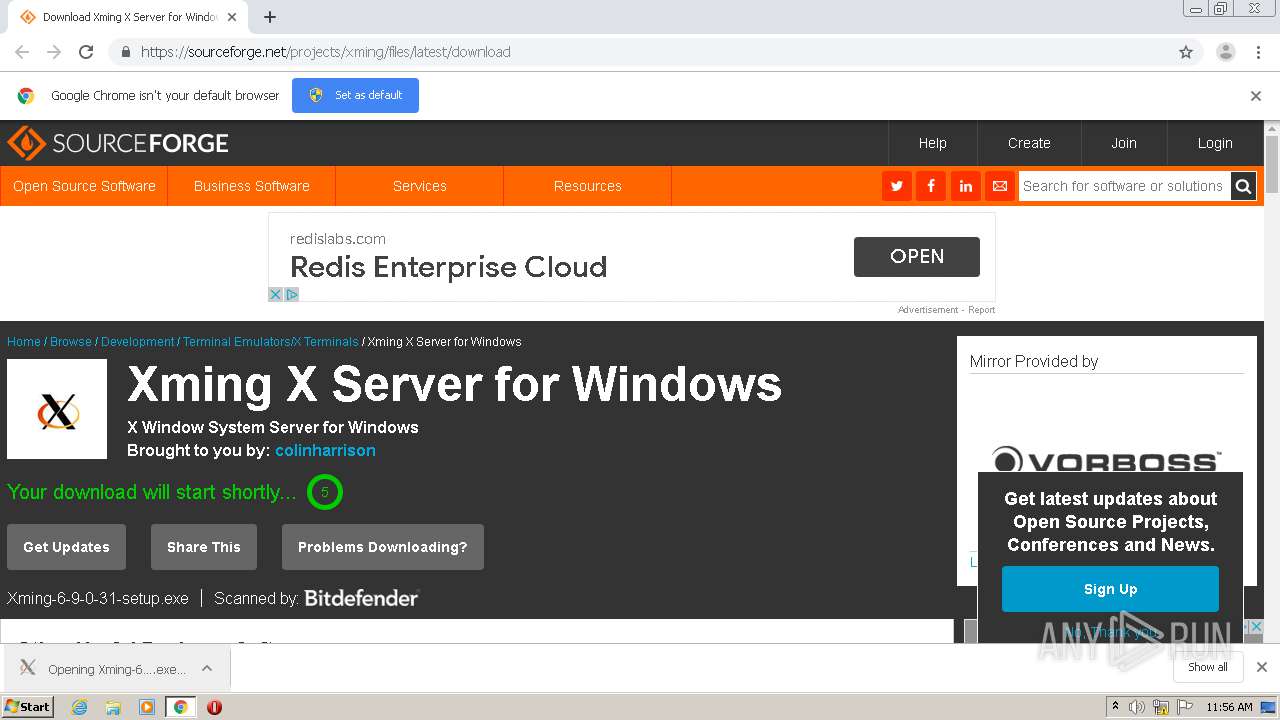
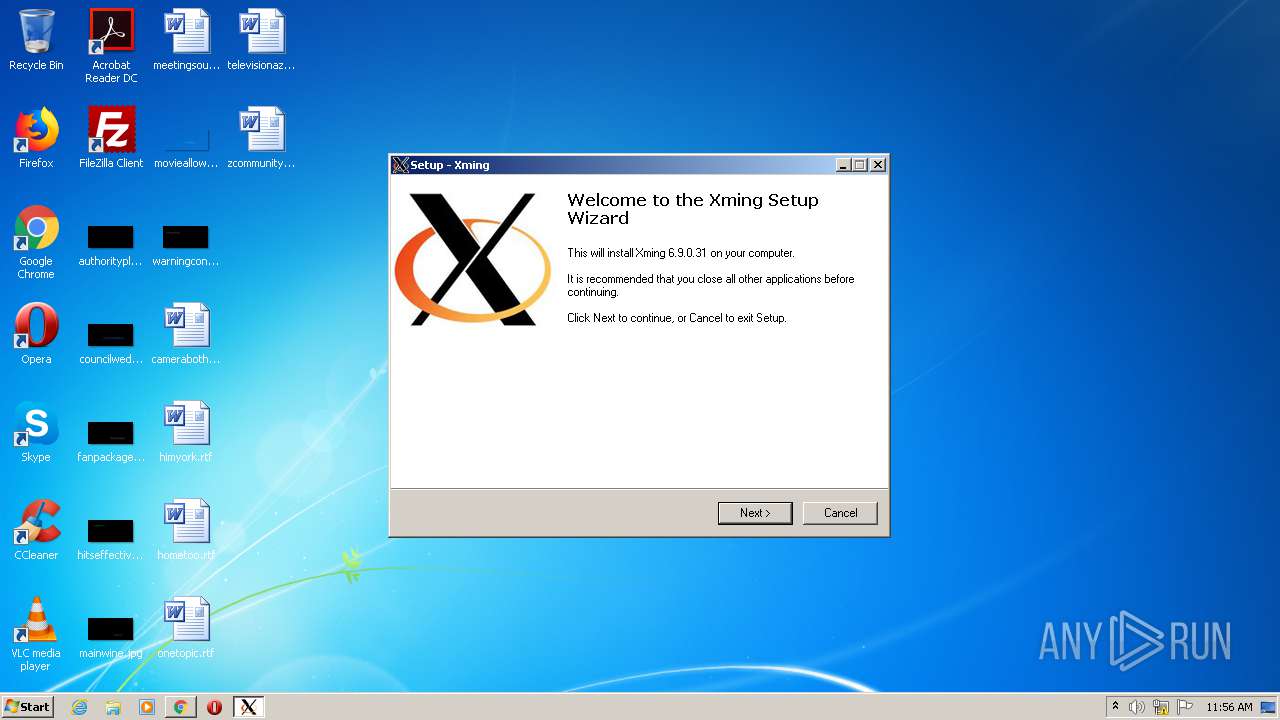
| URL: | https://sourceforge.net/projects/xming/files/latest/download |
| Full analysis: | https://app.any.run/tasks/1b406d3d-9743-41b6-be1b-3d7fe2906475 |
| Verdict: | Malicious activity |
| Analysis date: | August 08, 2020, 10:54:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D881EC98CDCB847EC17B0CFB587EB2C6 |
| SHA1: | 0E54A2BA8E5C7D38E5D87168F49E8729A269A423 |
| SHA256: | 4B9F724106A6109992609DBE6A673F8721CF38894BA69AA511D50803D01347C7 |
| SSDEEP: | 3:N8HCGSuLAuUt5hywz:2iGnCt5/z |
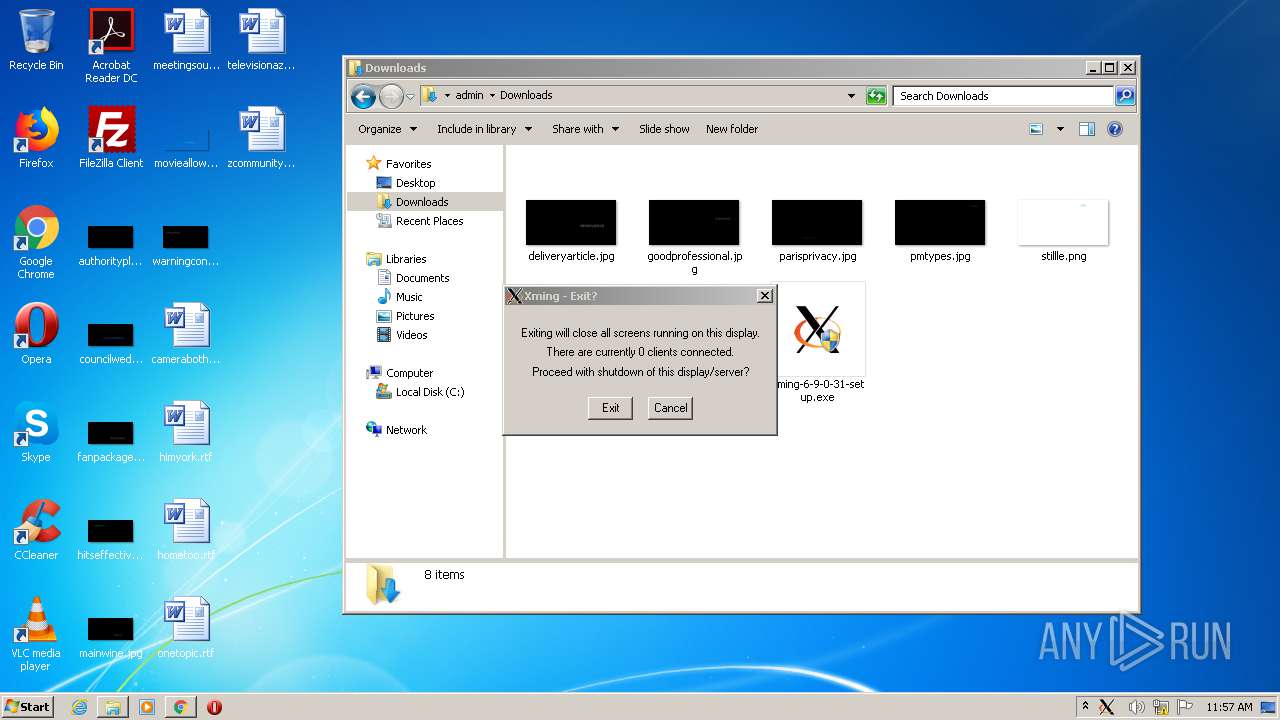
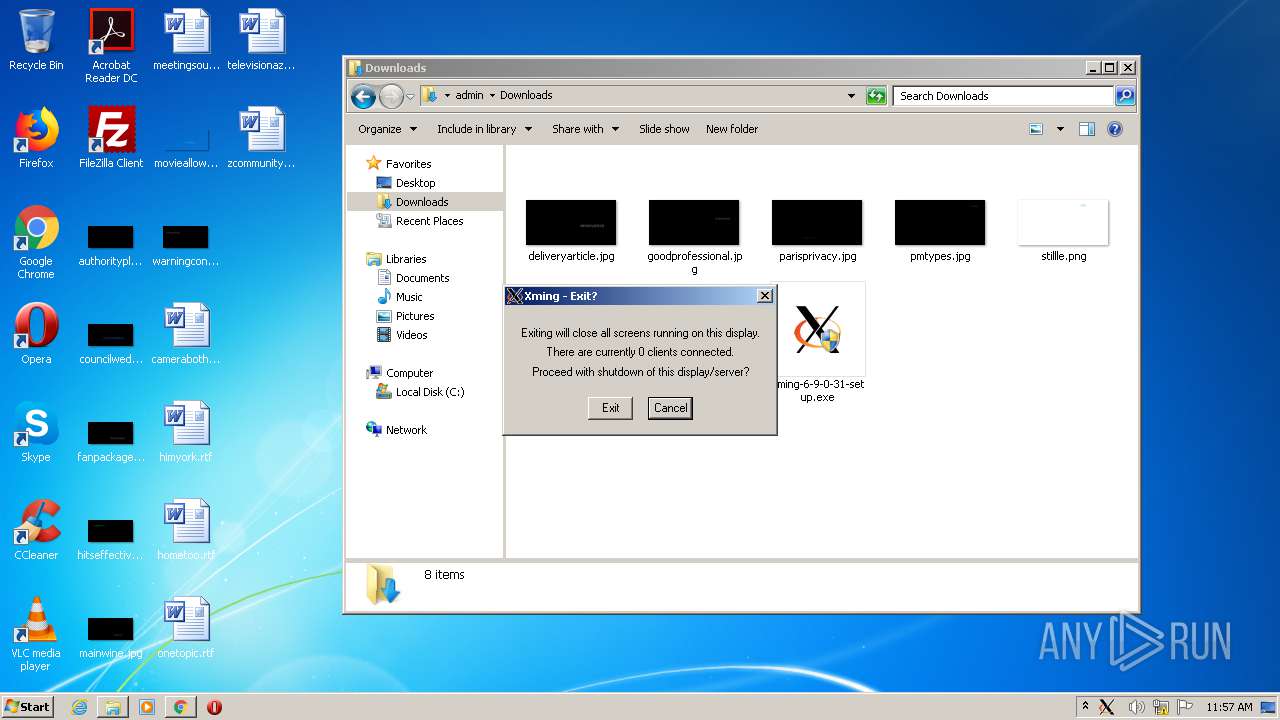
MALICIOUS
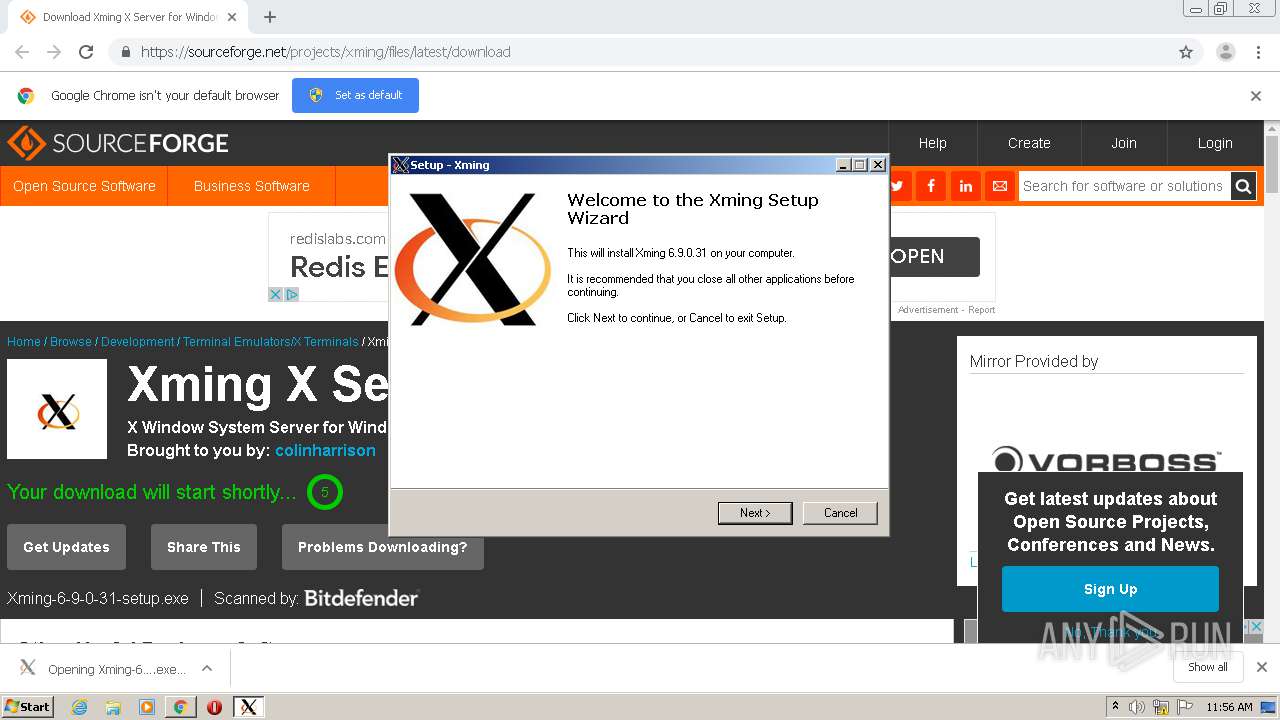
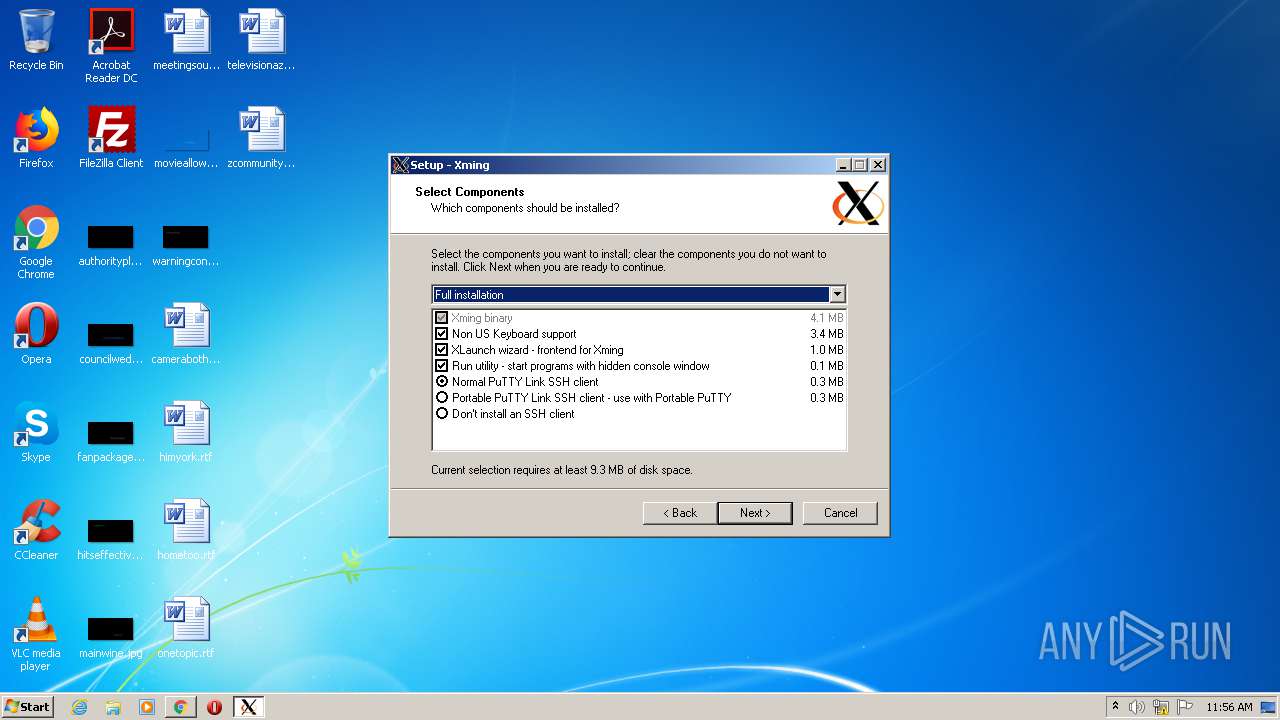
Application was dropped or rewritten from another process
- Xming-6-9-0-31-setup.exe (PID: 3332)
- xkbcomp.exe (PID: 3168)
- Xming.exe (PID: 3440)
- Xming-6-9-0-31-setup.exe (PID: 3864)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2508)
- chrome.exe (PID: 2812)
- is-1744M.tmp (PID: 3360)
- Xming-6-9-0-31-setup.exe (PID: 3332)
Modifies the open verb of a shell class
- is-1744M.tmp (PID: 3360)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 2812)
Reads settings of System Certificates
- chrome.exe (PID: 2508)
Reads the hosts file
- chrome.exe (PID: 2508)
- chrome.exe (PID: 2812)
Application launched itself
- chrome.exe (PID: 2812)
Loads dropped or rewritten executable
- is-1744M.tmp (PID: 3360)
Application was dropped or rewritten from another process
- is-1744M.tmp (PID: 3360)
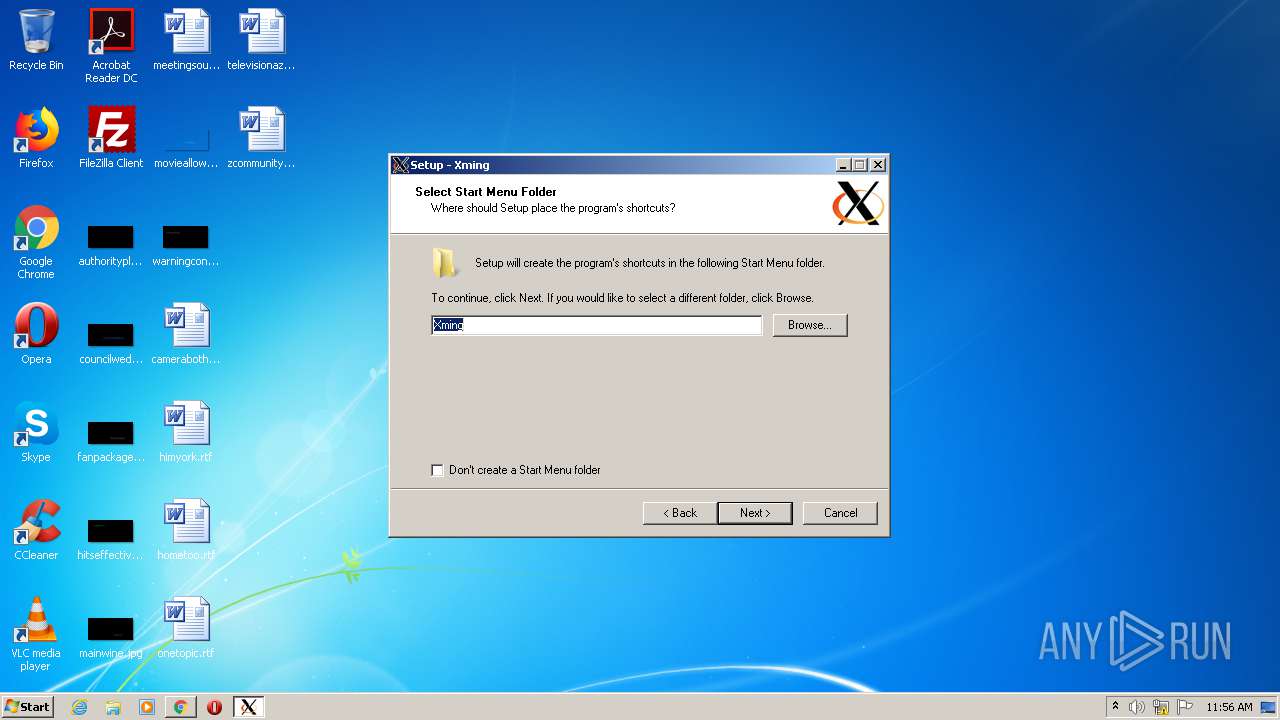
Creates a software uninstall entry
- is-1744M.tmp (PID: 3360)
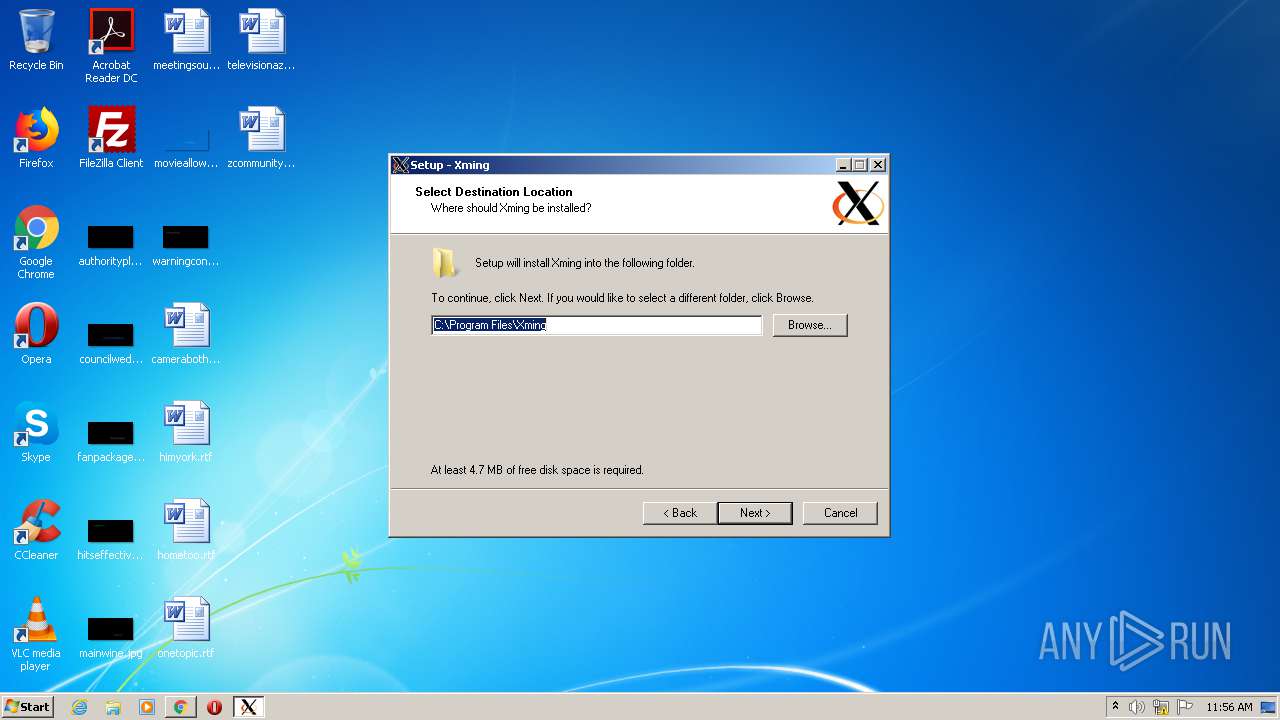
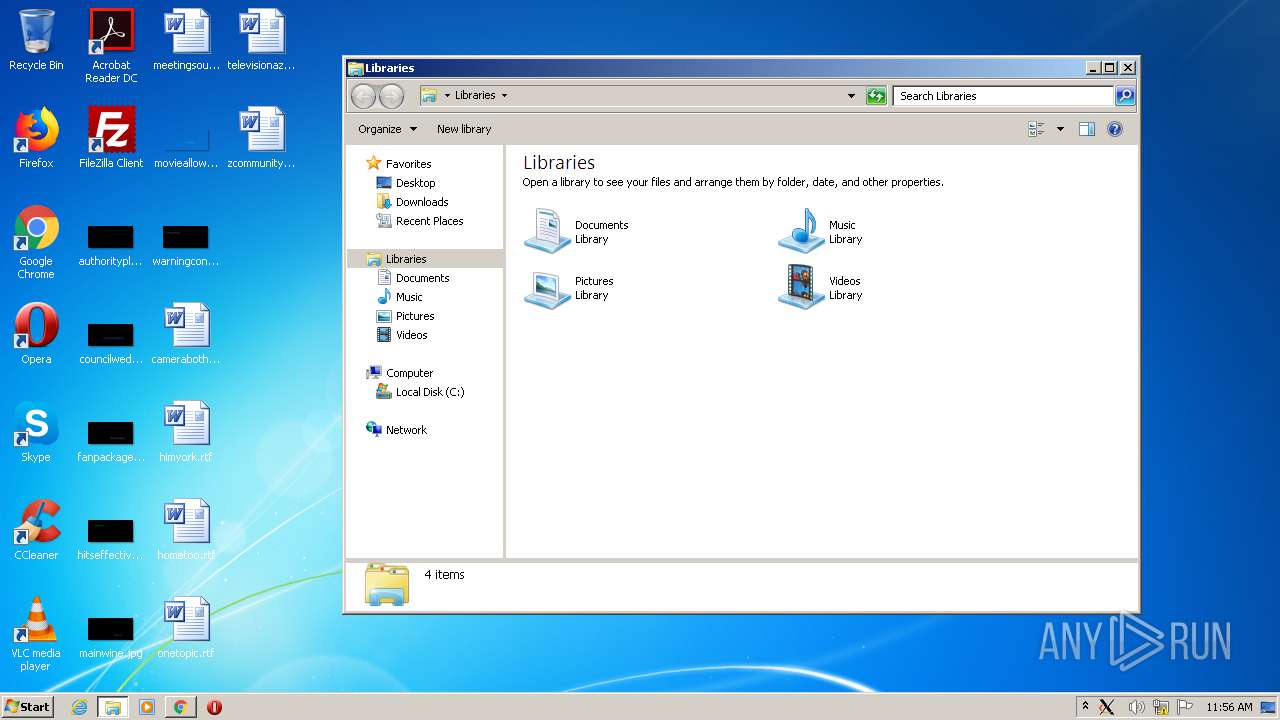
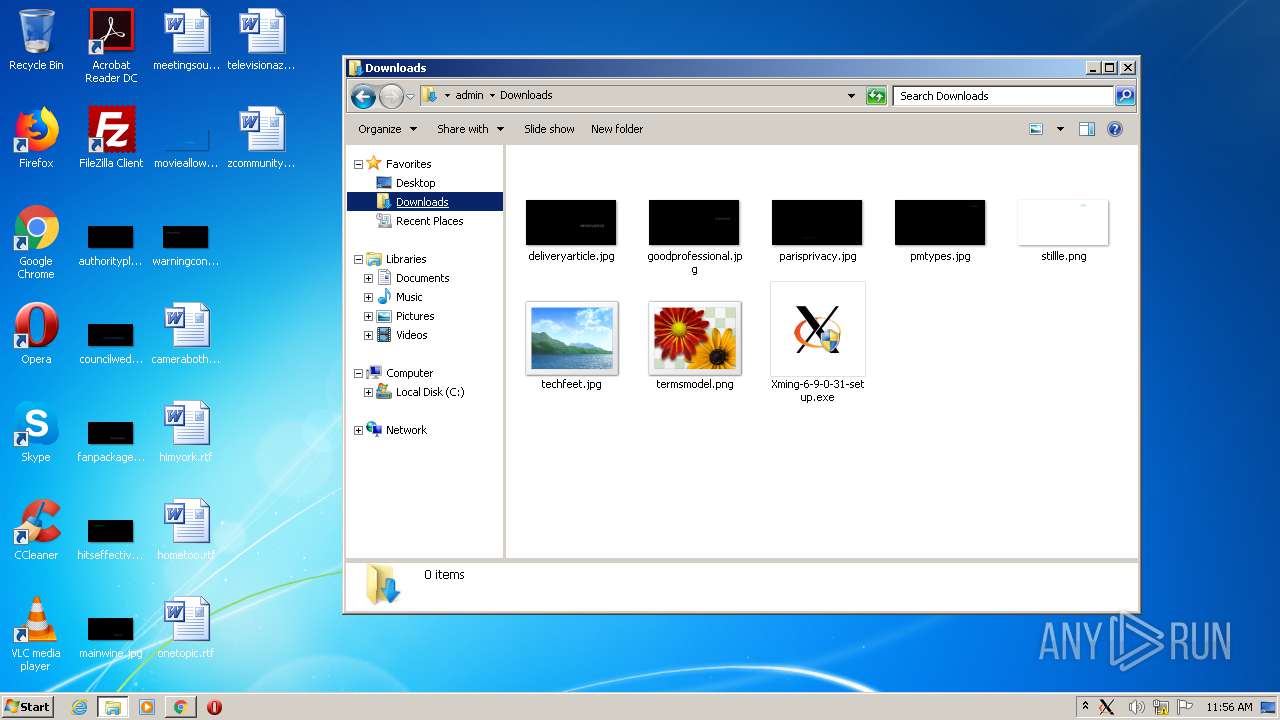
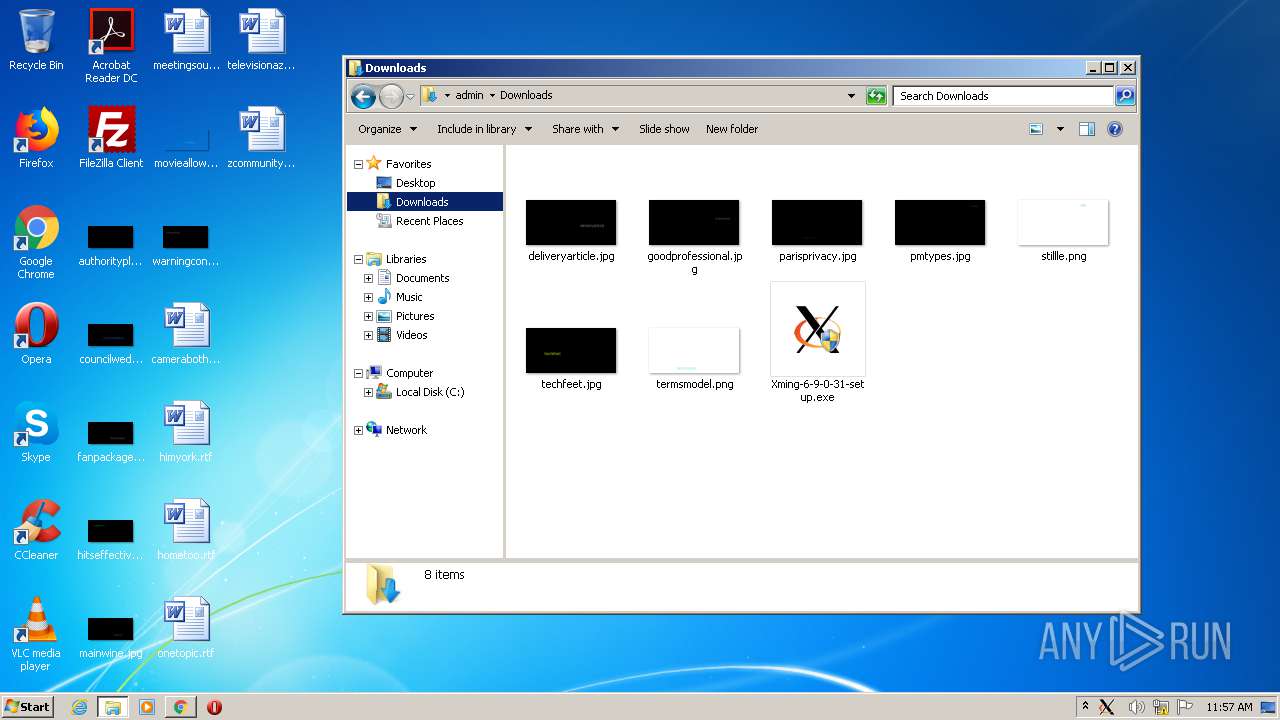
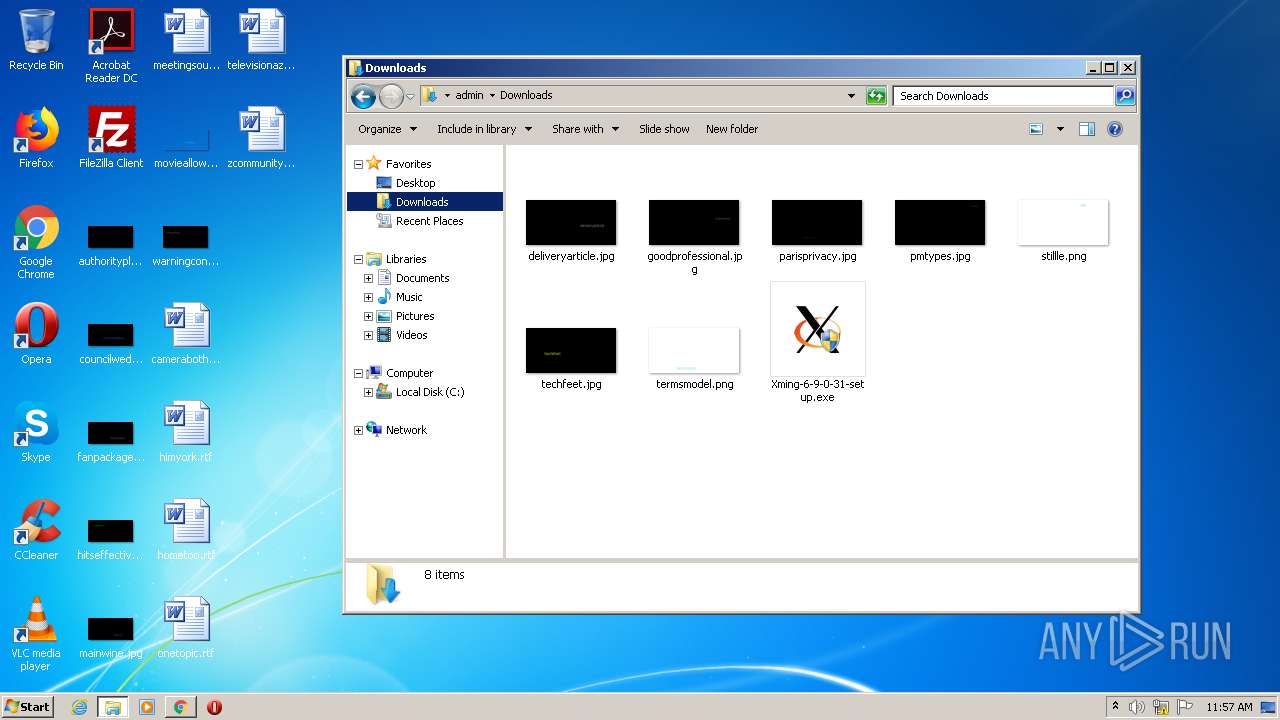
Manual execution by user
- explorer.exe (PID: 3000)
Creates files in the program directory
- is-1744M.tmp (PID: 3360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
73
Monitored processes
26
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,6165697419870280350,5409847168142258205,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10152598714754865149 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,6165697419870280350,5409847168142258205,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=15046129370237848943 --mojo-platform-channel-handle=508 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,6165697419870280350,5409847168142258205,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=17264247615348234890 --mojo-platform-channel-handle=3720 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,6165697419870280350,5409847168142258205,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17076721349063541152 --mojo-platform-channel-handle=1036 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,6165697419870280350,5409847168142258205,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=12395287539687432641 --mojo-platform-channel-handle=3576 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,6165697419870280350,5409847168142258205,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2211637283559919218 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3036 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,6165697419870280350,5409847168142258205,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=5278986067260240677 --mojo-platform-channel-handle=3412 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,6165697419870280350,5409847168142258205,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=17875942915449699808 --mojo-platform-channel-handle=1600 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,6165697419870280350,5409847168142258205,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=13983169277471138018 --mojo-platform-channel-handle=3672 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2816 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 409
Read events
1 240
Write events
164
Delete events
5
Modification events
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2812-13241357656743625 |
Value: 259 | |||
Executable files
16
Suspicious files
75
Text files
482
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0e0402b3-2707-476a-93d7-b92acee8a93e.tmp | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF19115b.TMP | text | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF19115b.TMP | text | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF19117b.TMP | text | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF191236.TMP | text | |
MD5:— | SHA256:— | |||
| 3844 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | gmc | |
MD5:B6D81B360A5672D80C27430F39153E2C | SHA256:30E14955EBF1352266DC2FF8067E68104607E750ABB9D3B36582B8AF909FCB58 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
93
DNS requests
57
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2508 | chrome.exe | 216.105.38.13:443 | sourceforge.net | American Internet Services, LLC. | US | malicious |
2508 | chrome.exe | 216.58.212.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2508 | chrome.exe | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2508 | chrome.exe | 172.217.23.109:443 | accounts.google.com | Google Inc. | US | suspicious |
2508 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
2508 | chrome.exe | 87.230.98.68:443 | consentmanager.mgr.consensu.org | Host Europe GmbH | DE | unknown |
2508 | chrome.exe | 172.217.18.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
— | — | 104.18.30.83:443 | c.sf-syn.com | Cloudflare Inc | US | unknown |
2508 | chrome.exe | 69.173.144.143:443 | fastlane.rubiconproject.com | — | US | unknown |
2508 | chrome.exe | 198.148.27.134:443 | bid.contextweb.com | Pulsepoint Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sourceforge.net |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
a.fsdn.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
consentmanager.mgr.consensu.org |
| whitelisted |
cdn.consentmanager.mgr.consensu.org |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
c.sf-syn.com |
| whitelisted |