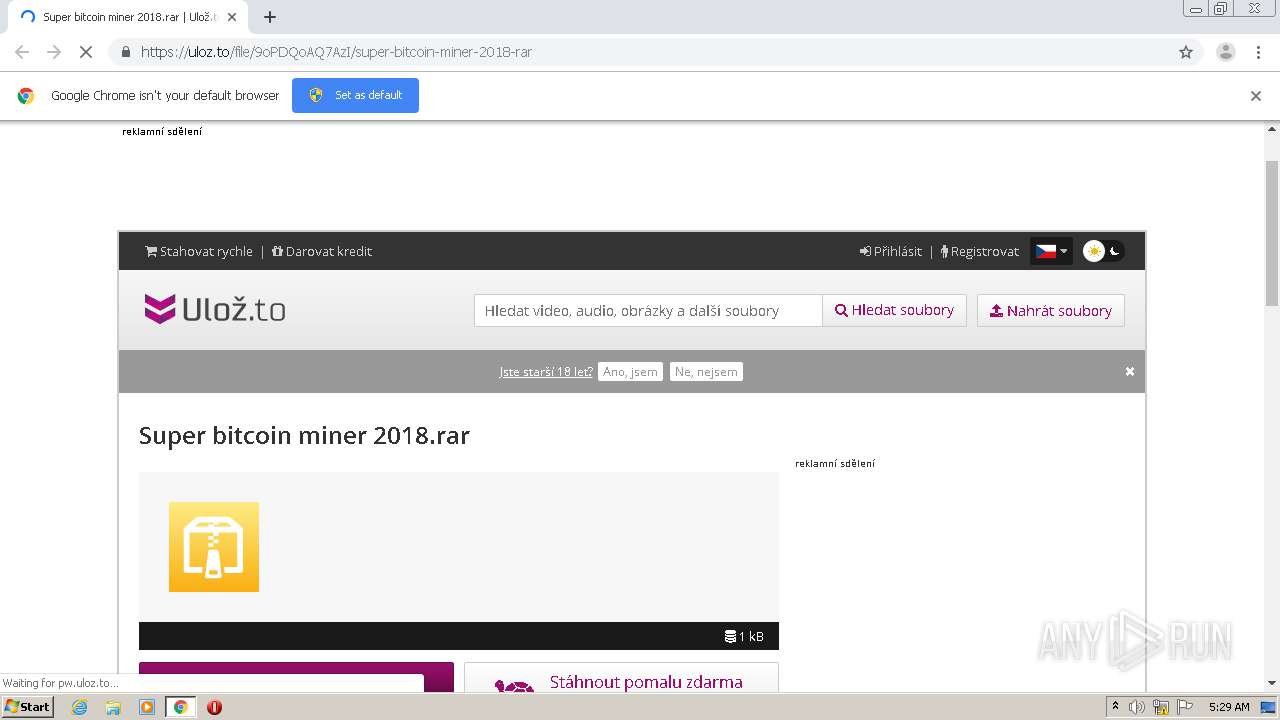
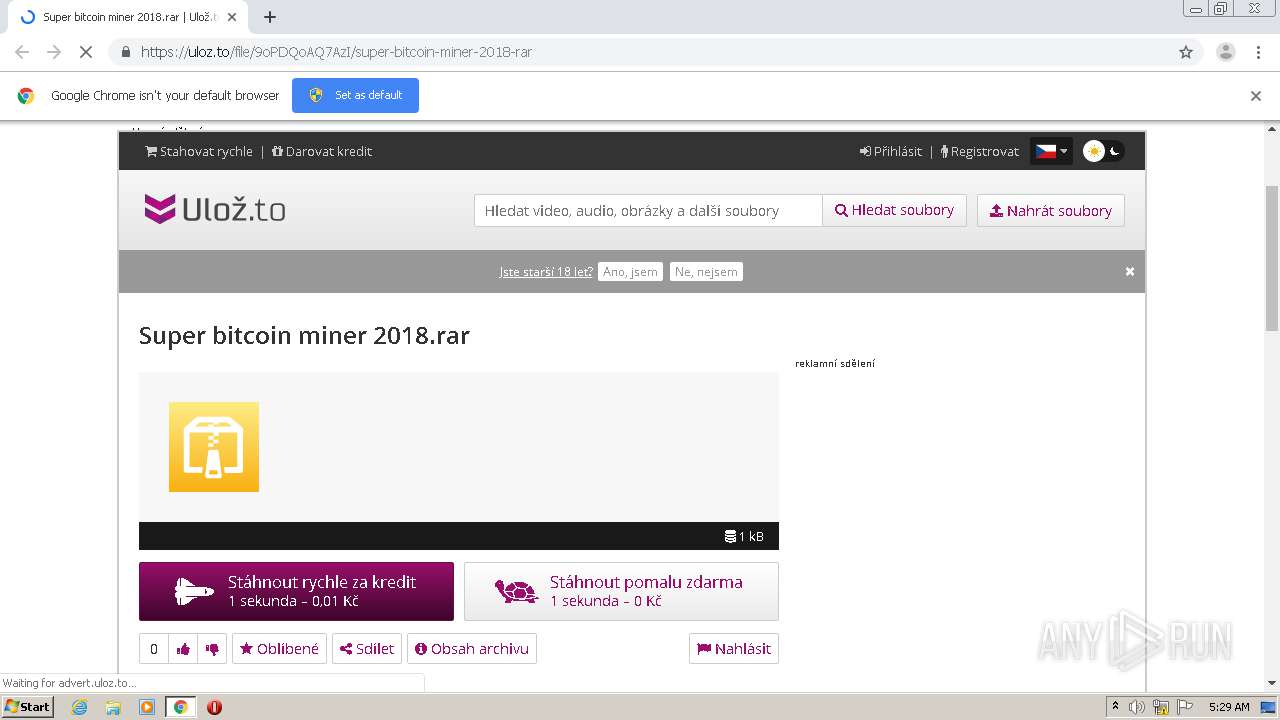
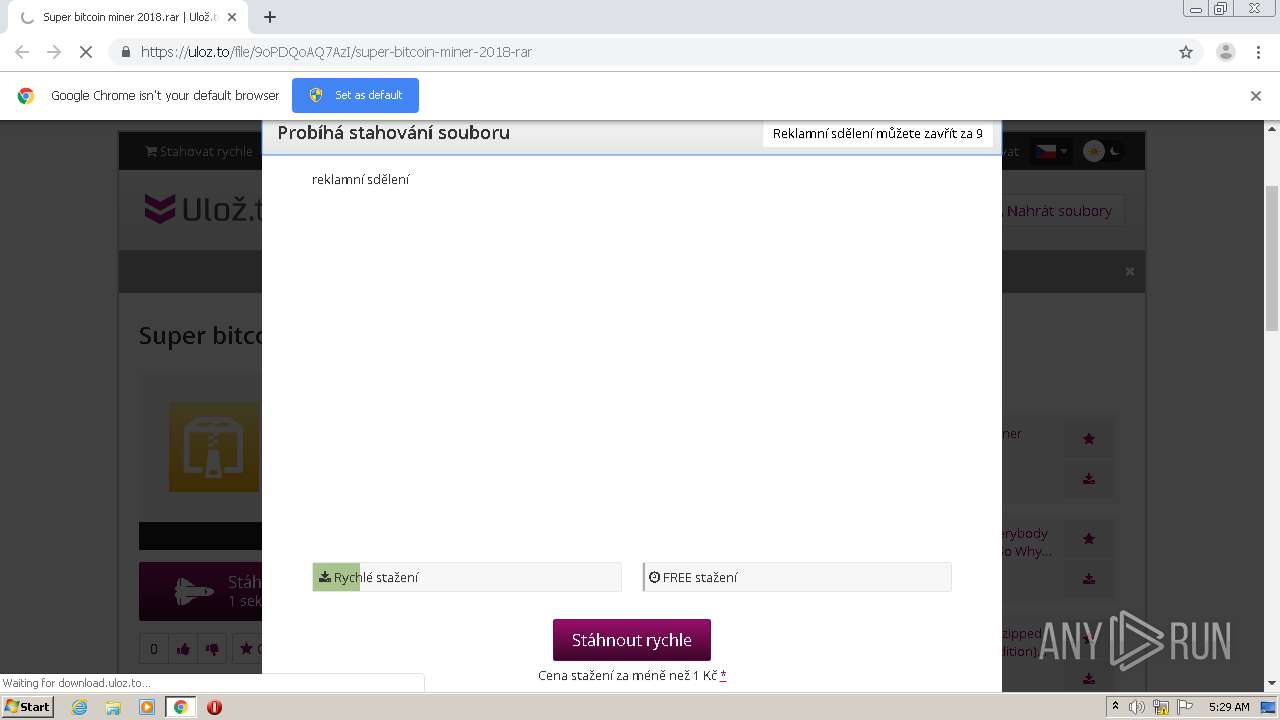
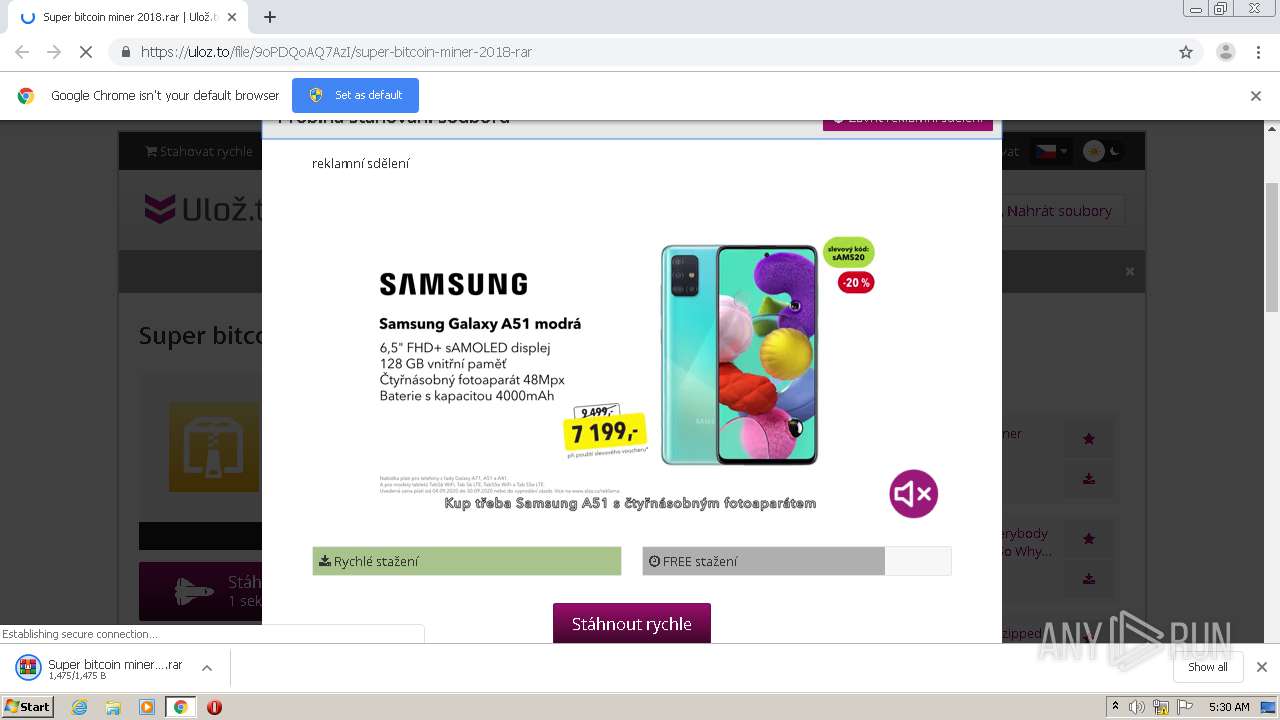
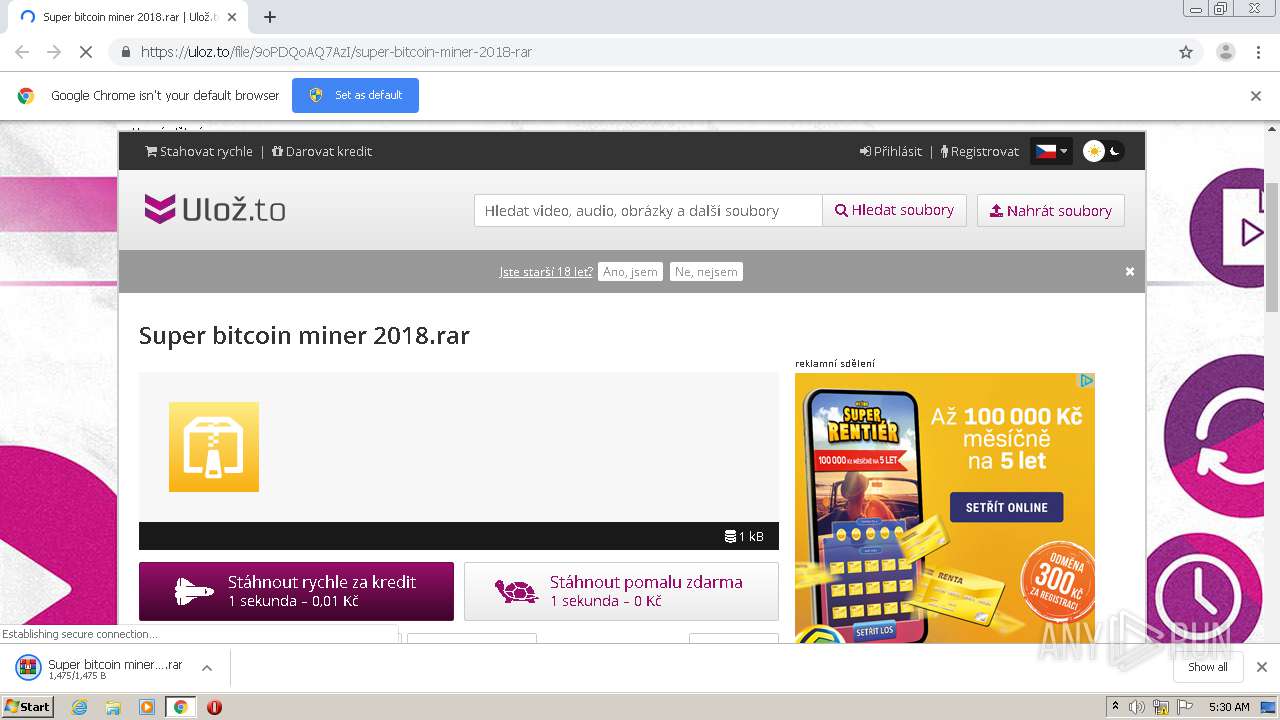
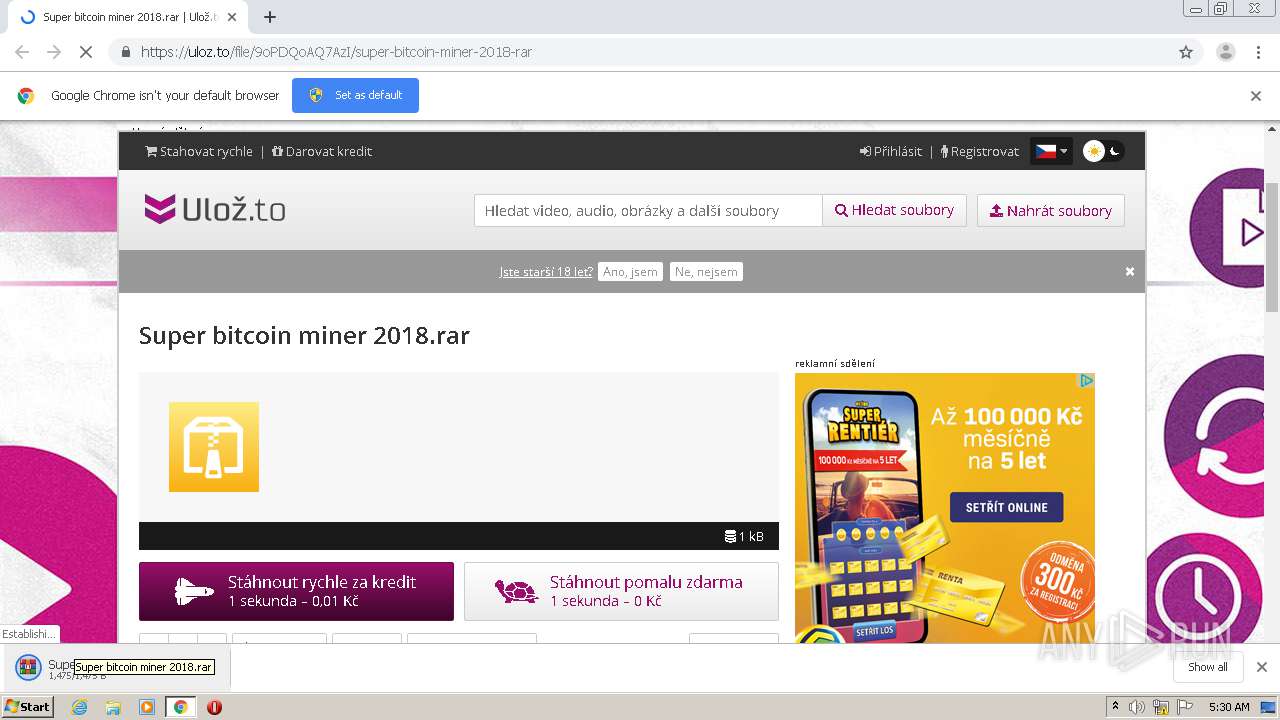
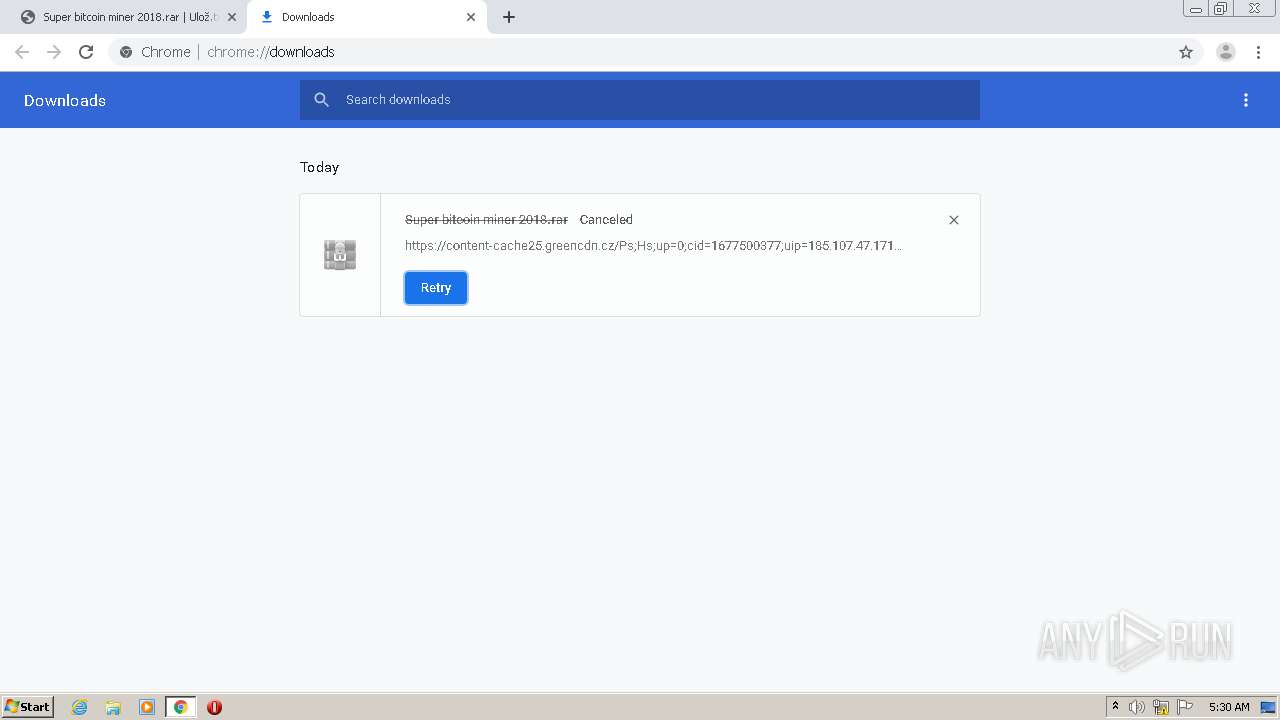
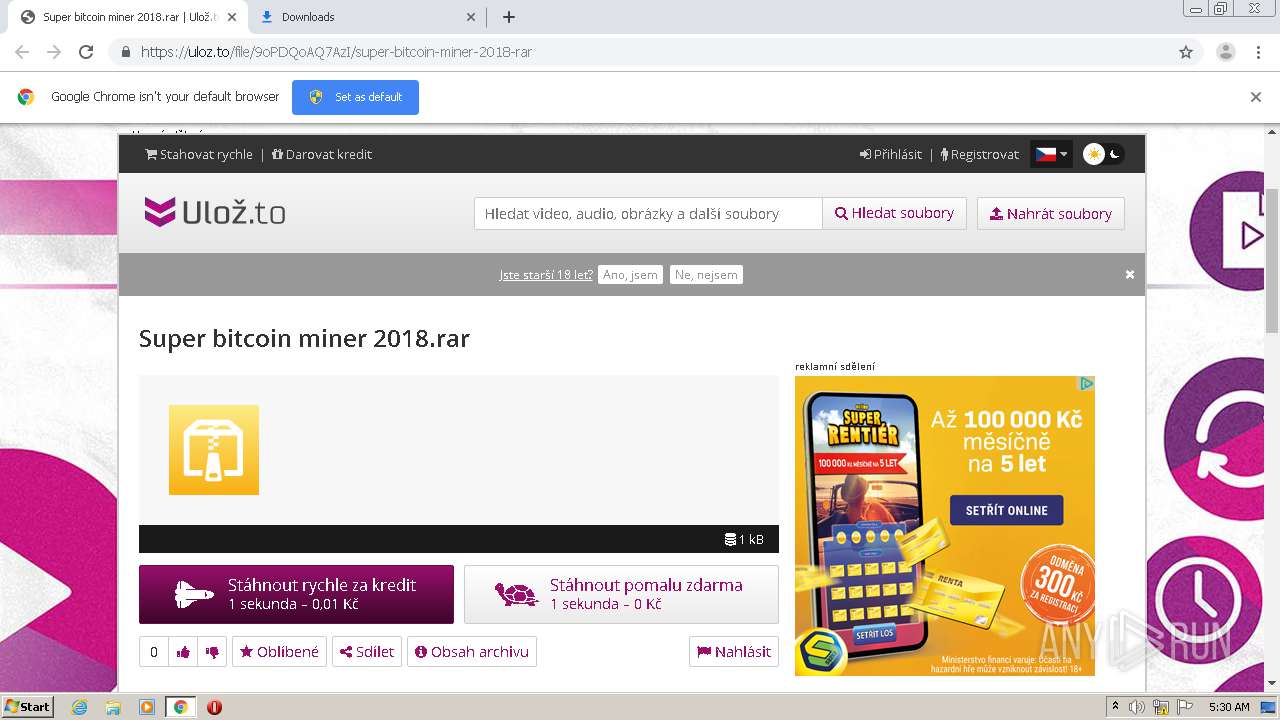
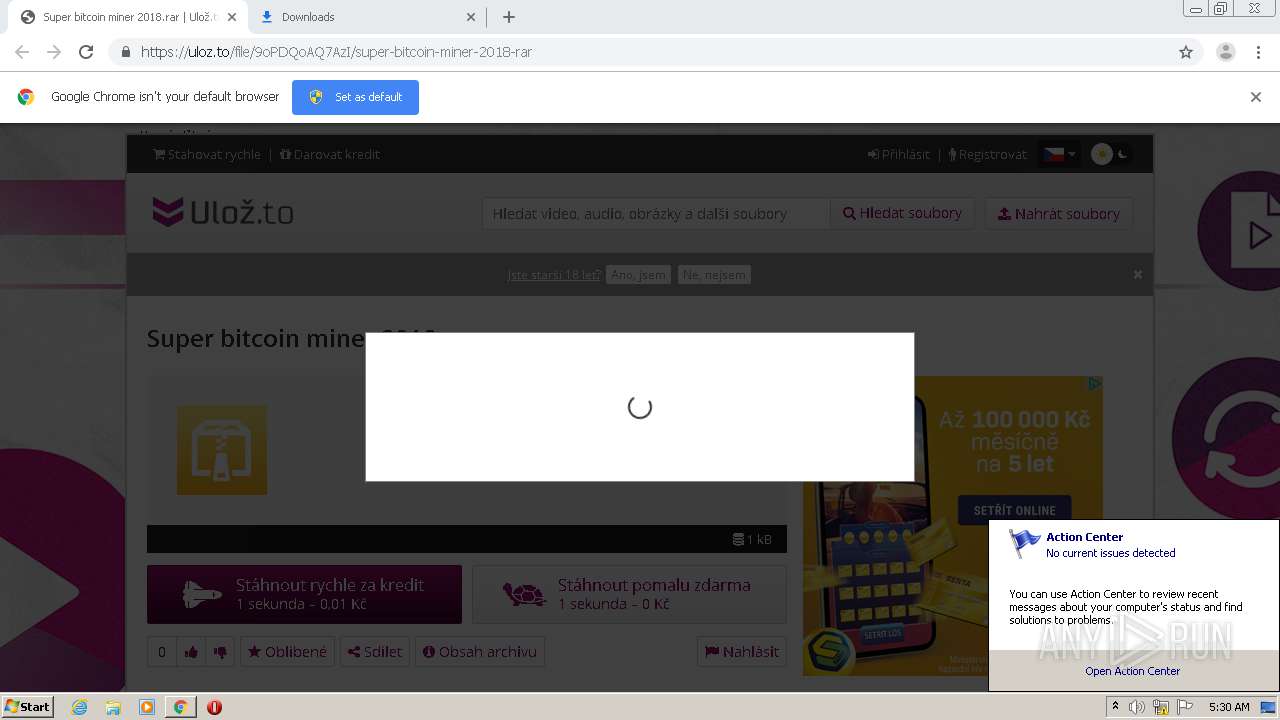
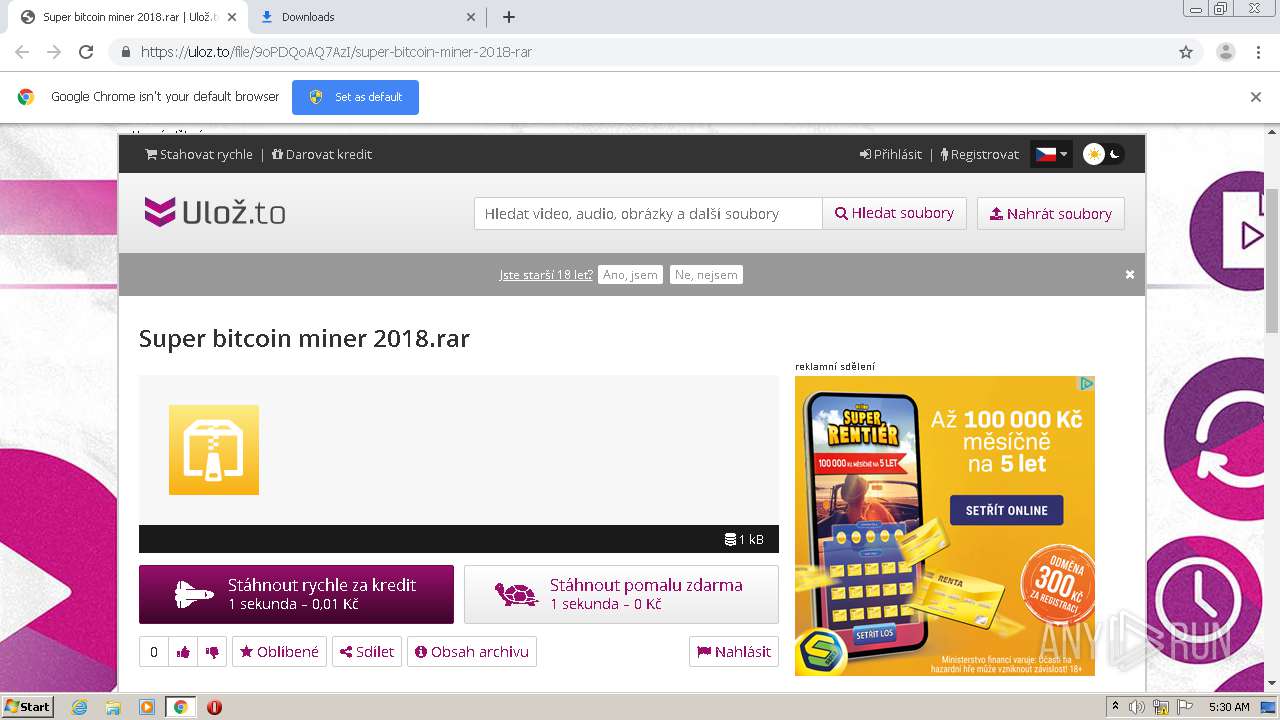
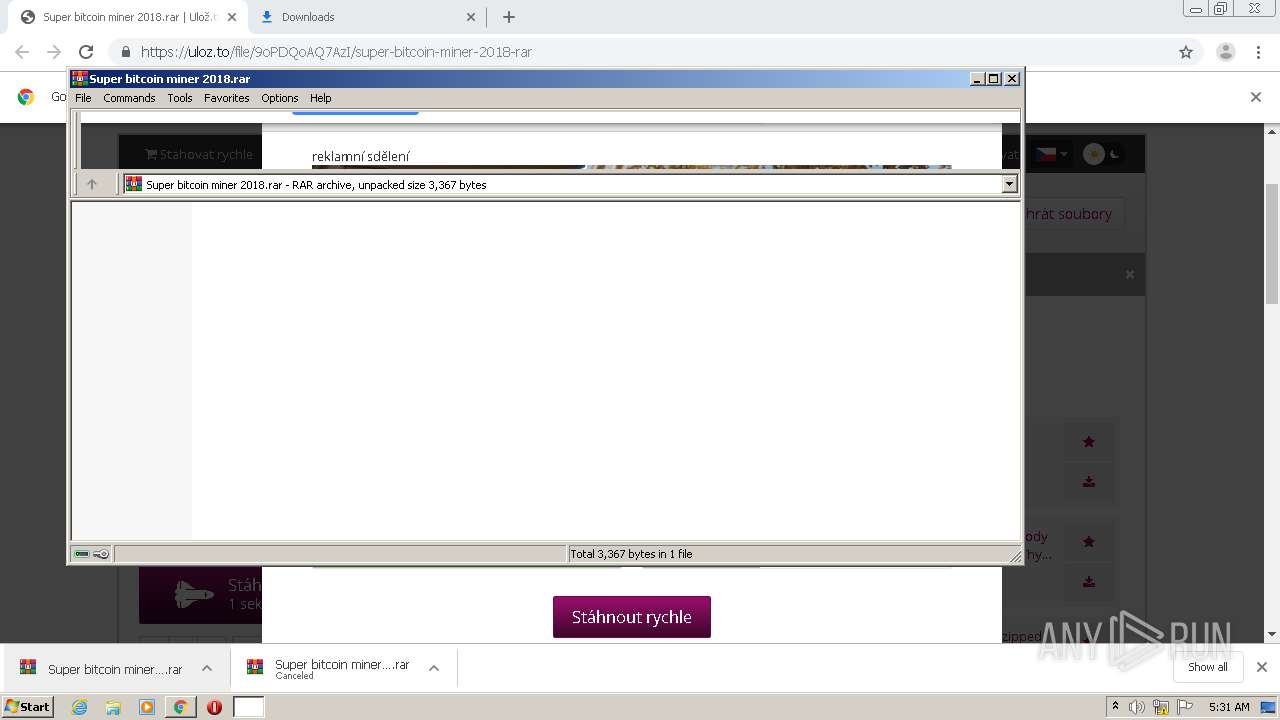
| URL: | https://uloz.to/file/9oPDQoAQ7AzI/super-bitcoin-miner-2018-rar |
| Full analysis: | https://app.any.run/tasks/a95d7411-d0f7-4c23-bb50-73b8b5bb6649 |
| Verdict: | Malicious activity |
| Analysis date: | October 02, 2020, 04:29:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CA5D70DA5CE30A8F68F4F1667CBE2511 |
| SHA1: | 0E4EB898B15980CBF5DF37429AA00884B45F1C3A |
| SHA256: | 4B9BBC68BD15CC36F97780FE70065FE30777D80D3418FF1C890DB72DE365CF3F |
| SSDEEP: | 3:N89IvcL0SWVsgKcfn:29t0SW+gXfn |
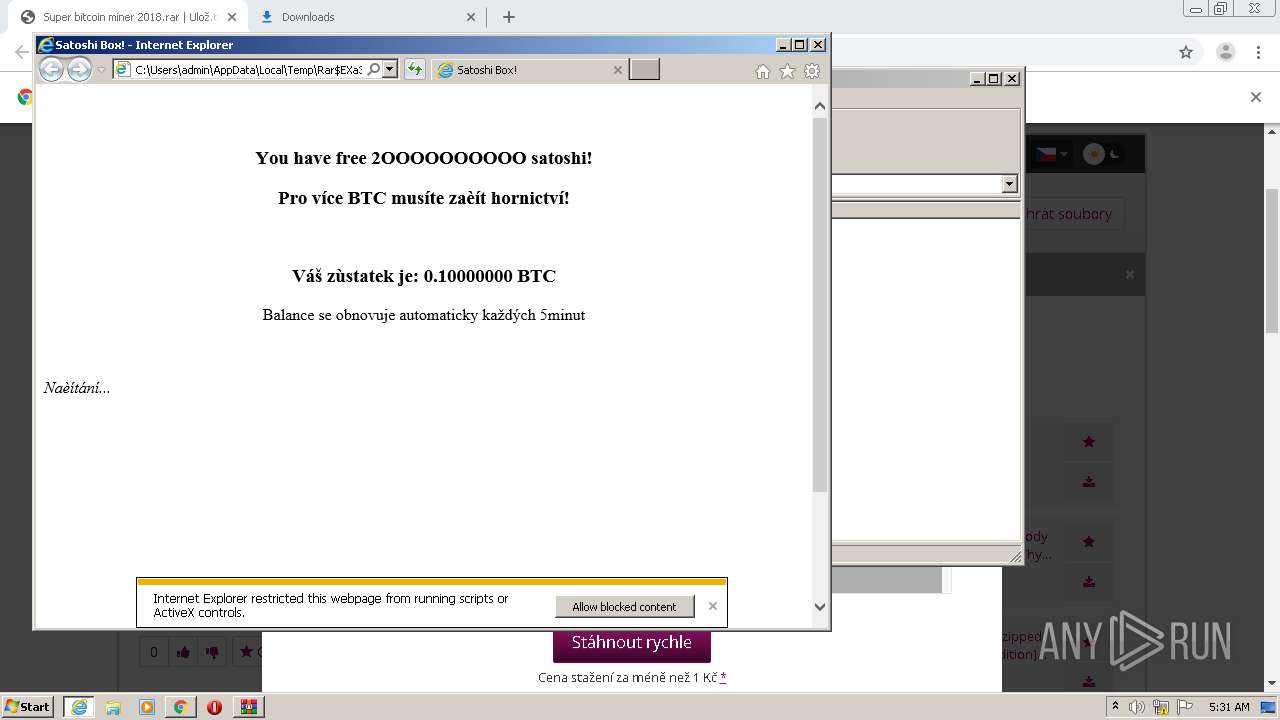
MALICIOUS
No malicious indicators.SUSPICIOUS
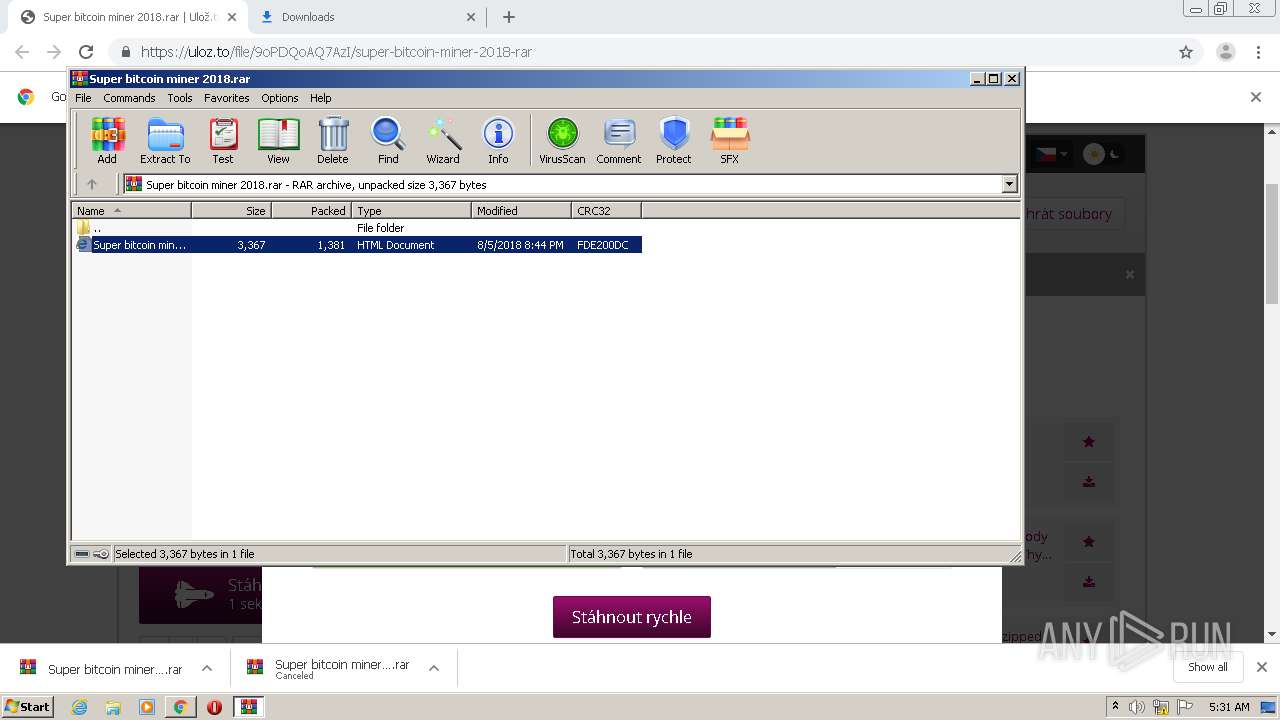
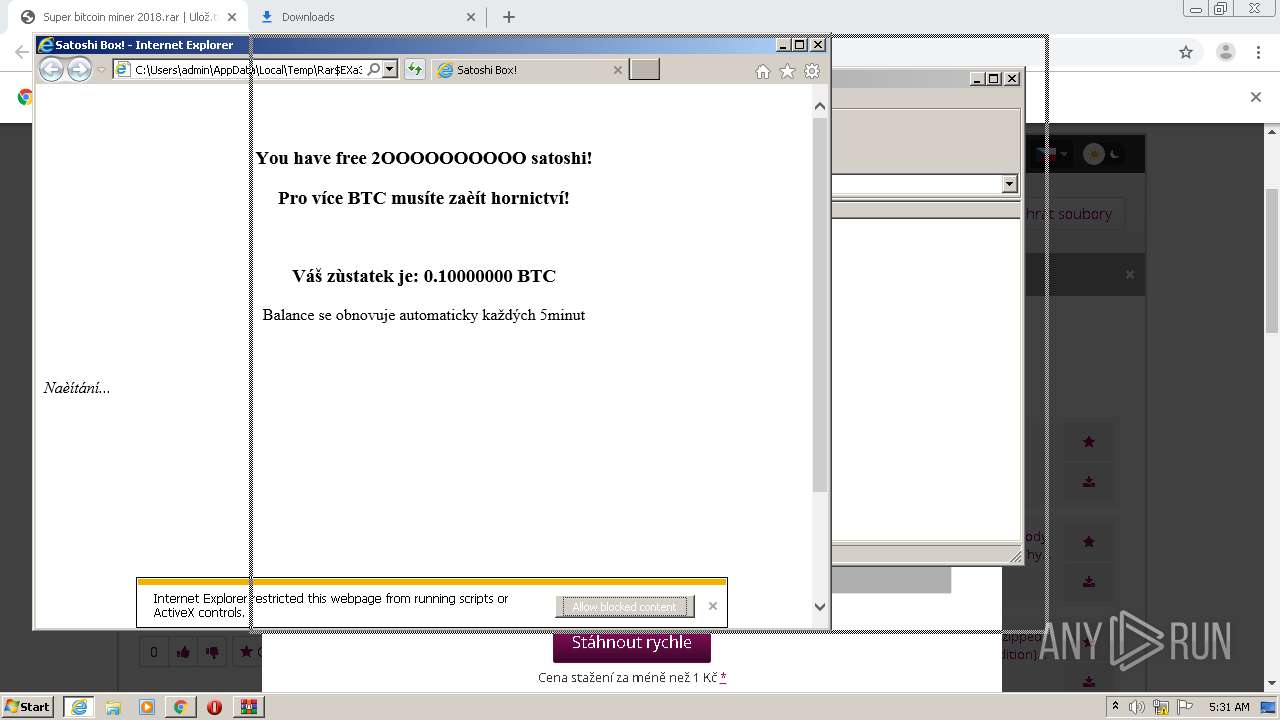
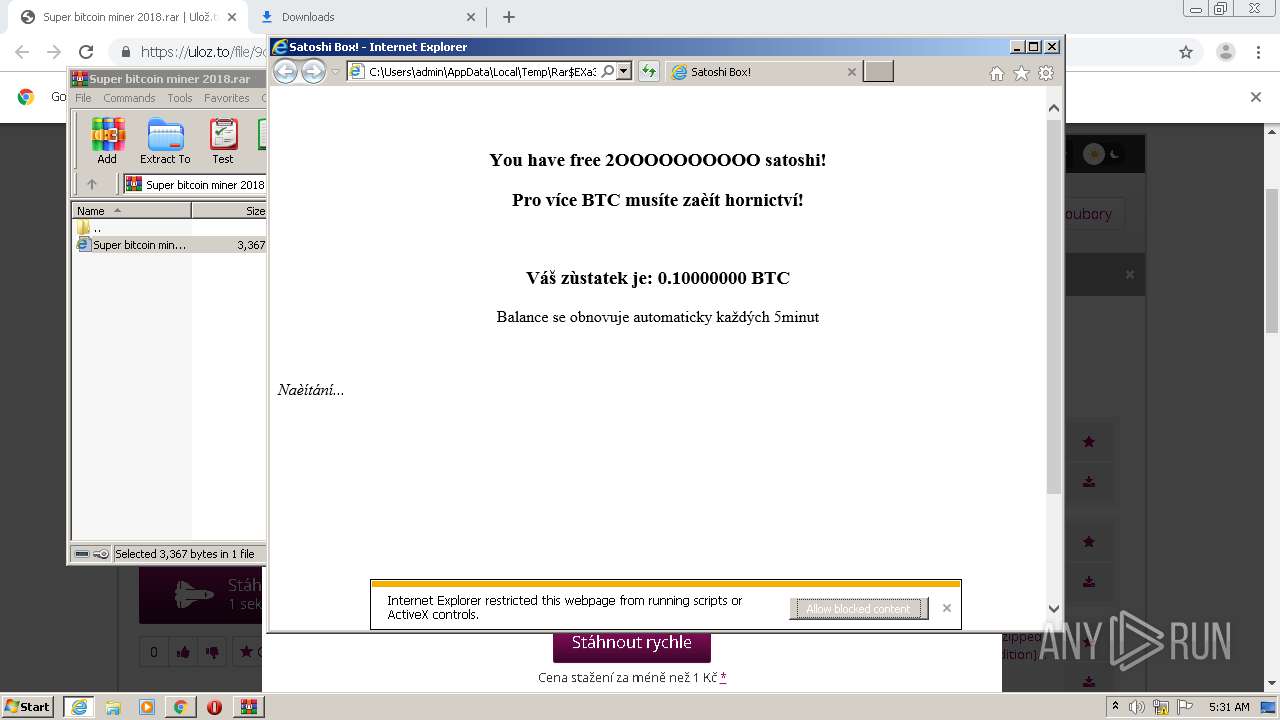
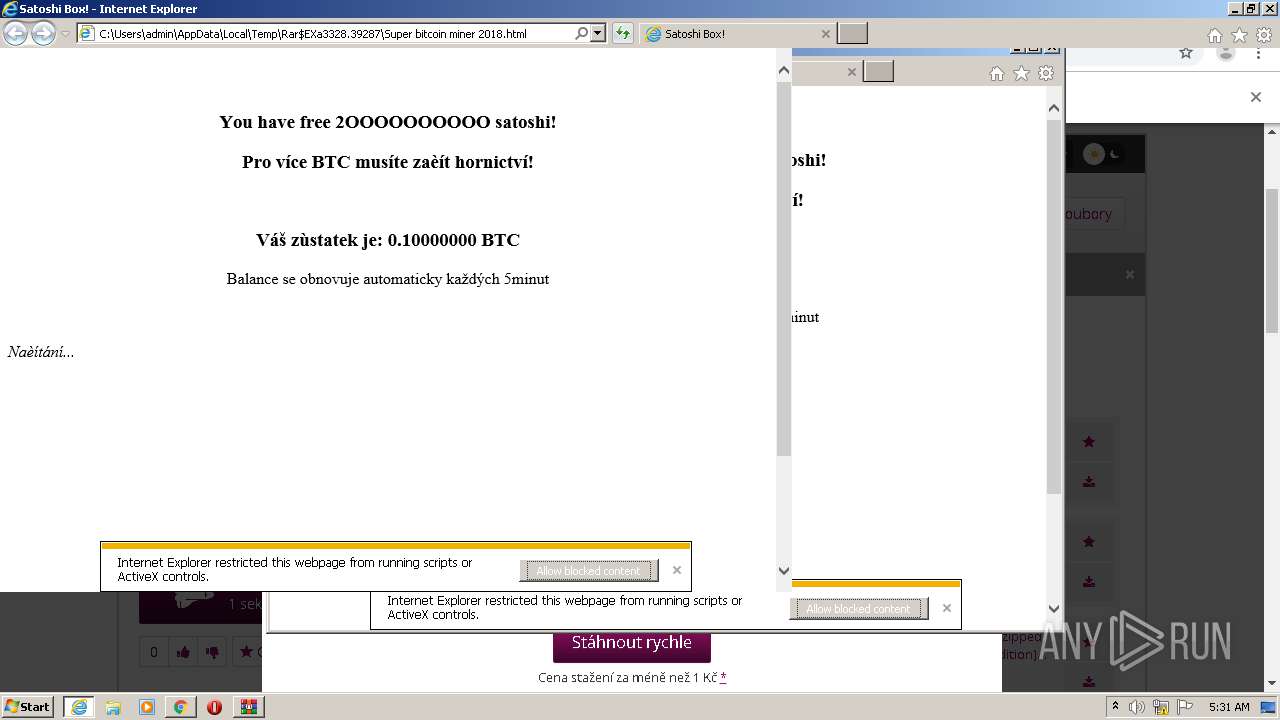
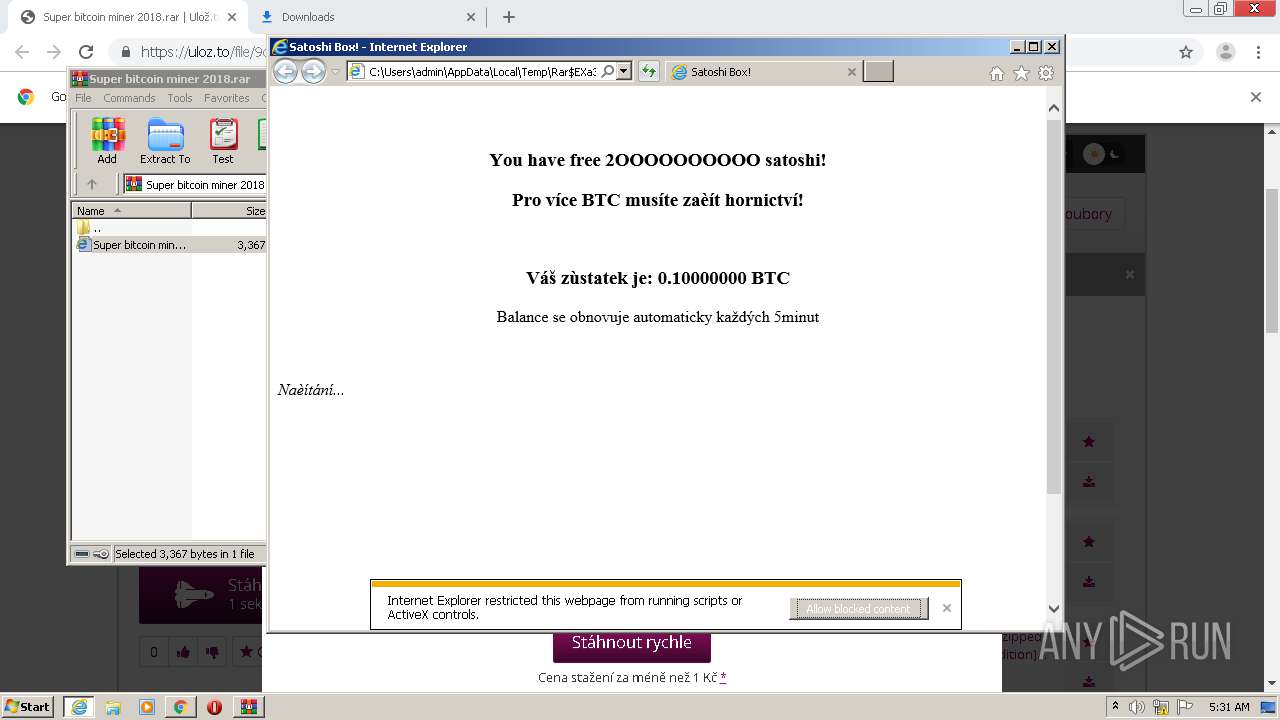
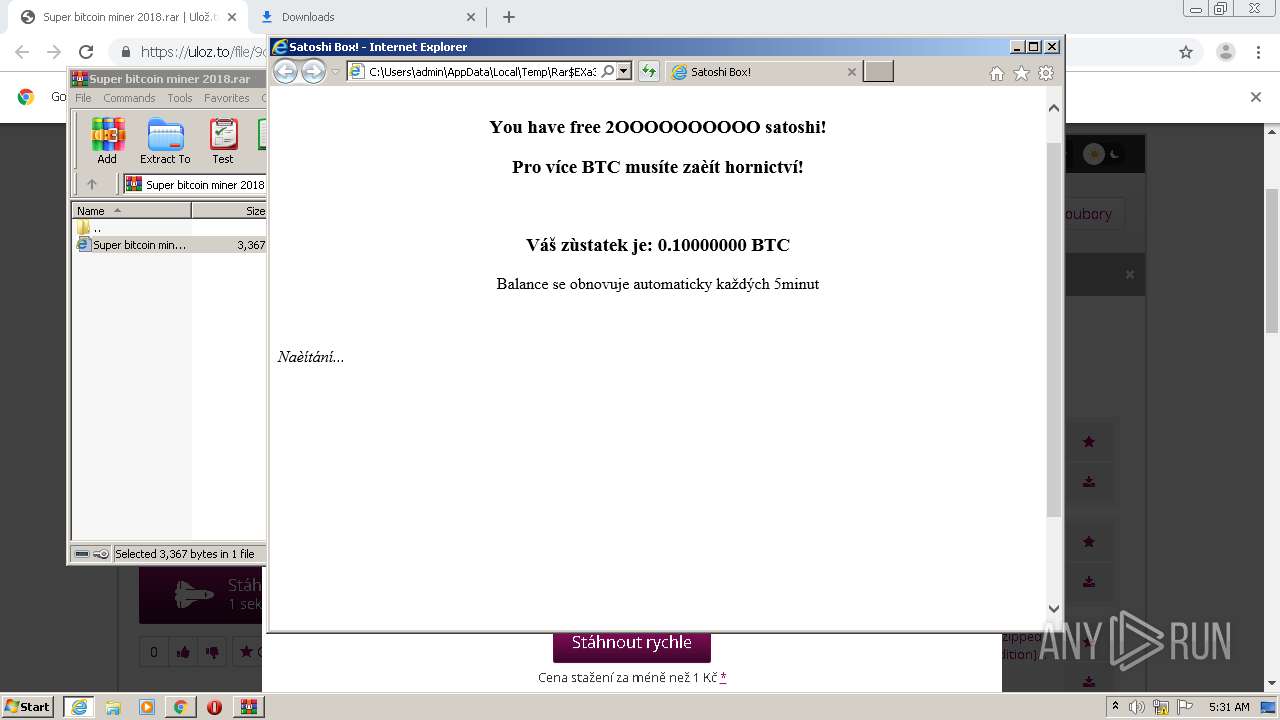
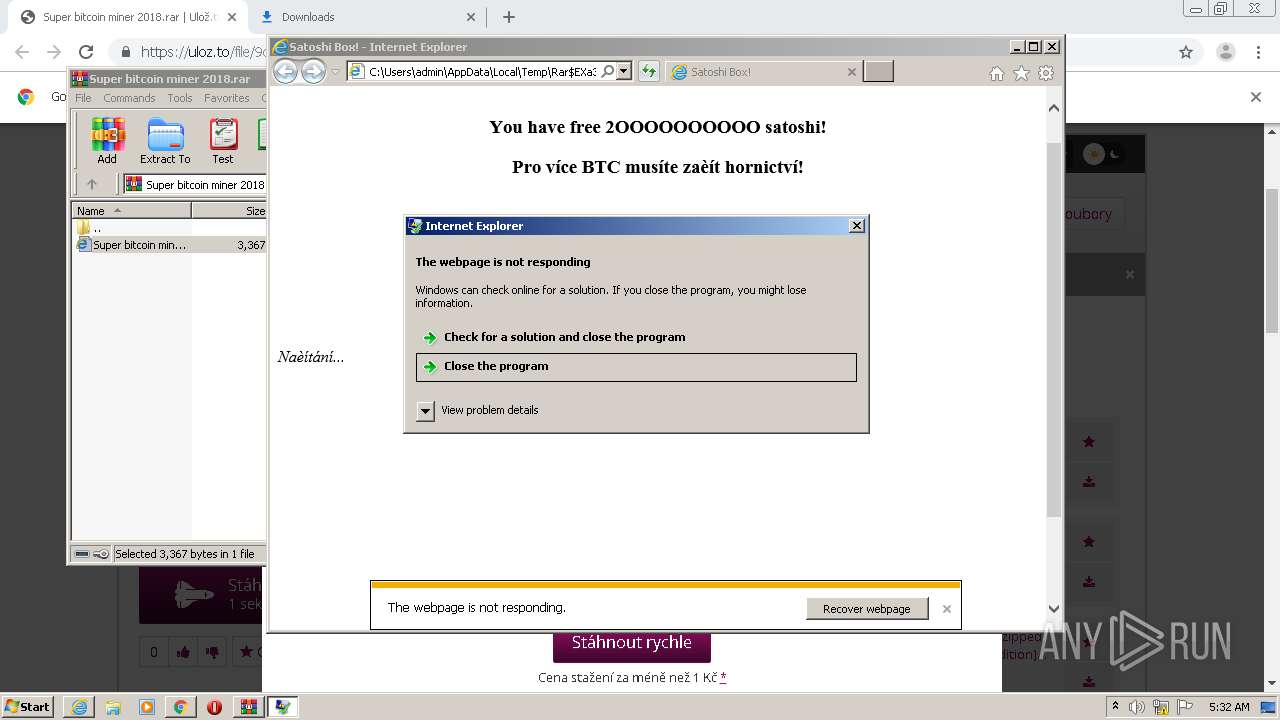
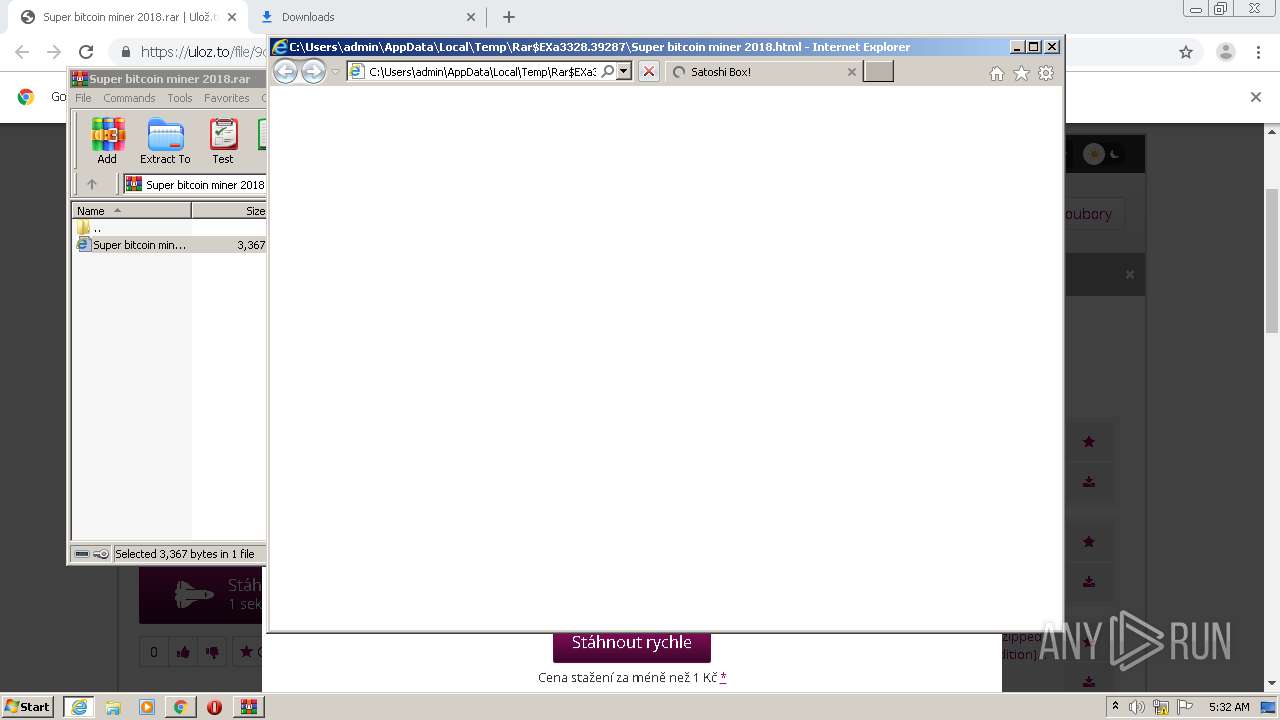
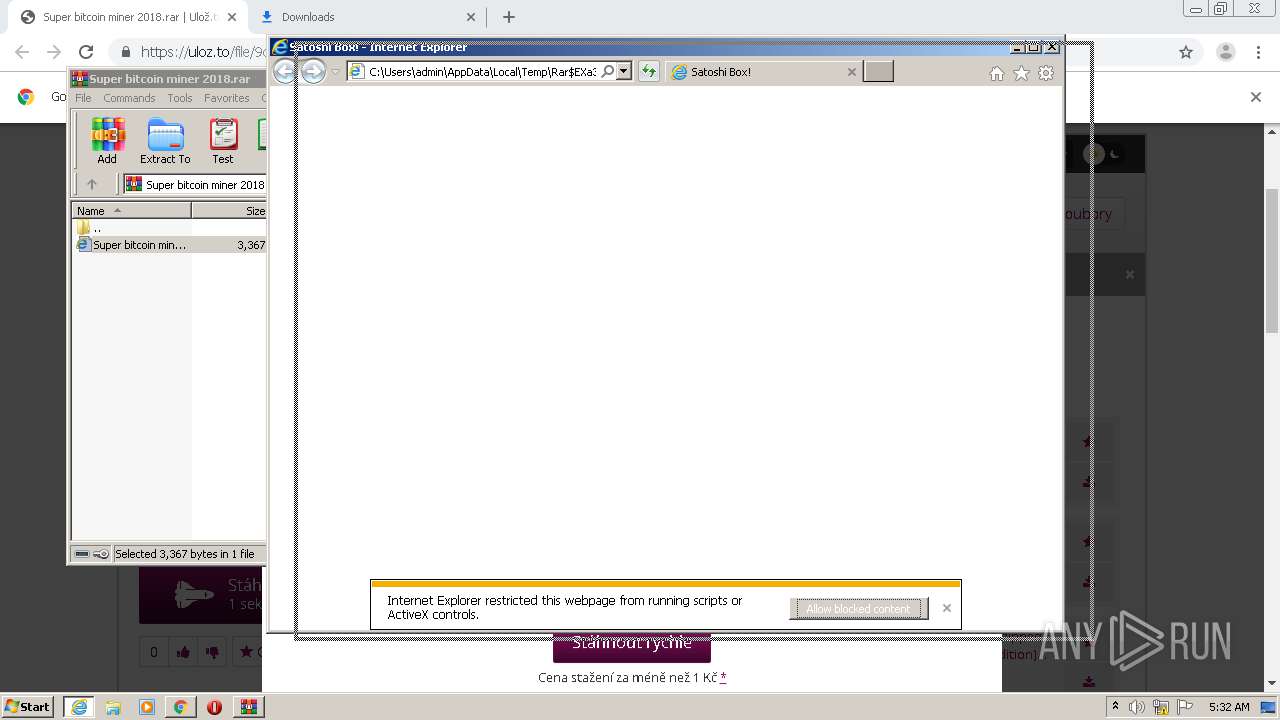
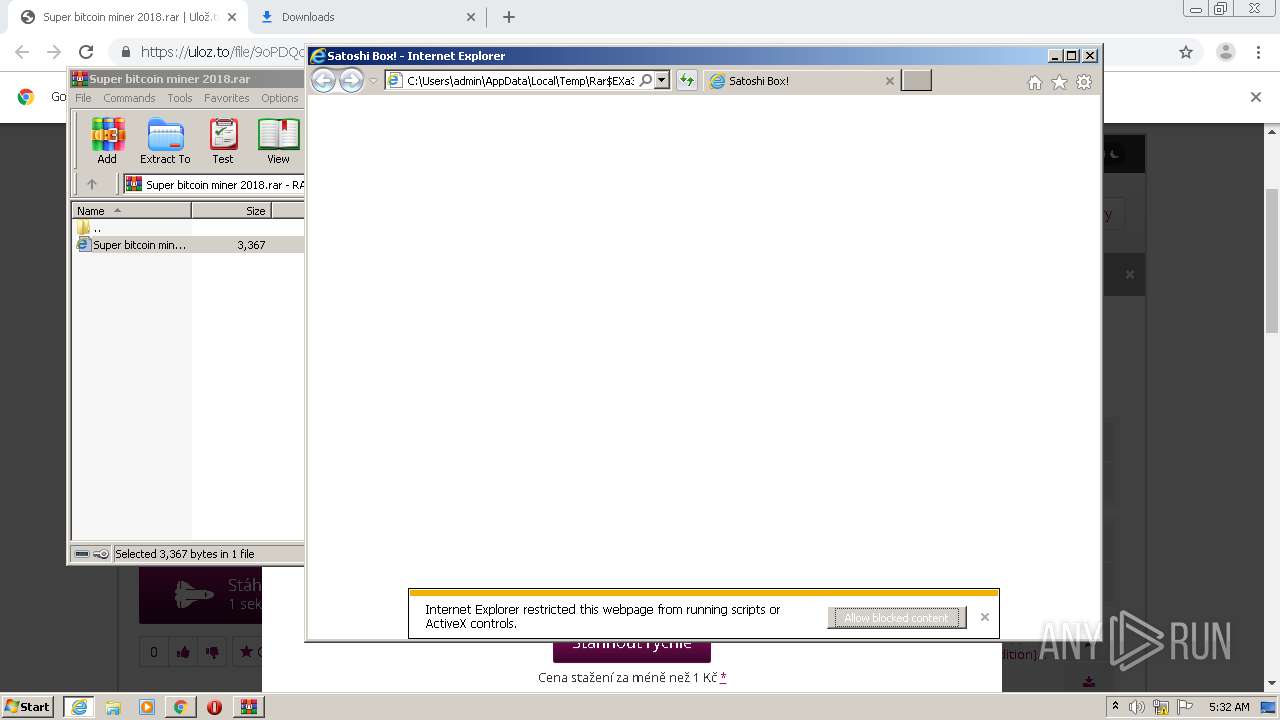
Starts Internet Explorer
- WinRAR.exe (PID: 3328)
INFO
Reads the hosts file
- chrome.exe (PID: 2100)
- chrome.exe (PID: 3280)
Reads Internet Cache Settings
- chrome.exe (PID: 2100)
- iexplore.exe (PID: 3120)
Changes internet zones settings
- iexplore.exe (PID: 3120)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1260)
- iexplore.exe (PID: 3120)
- iexplore.exe (PID: 3436)
Reads settings of System Certificates
- iexplore.exe (PID: 3120)
- iexplore.exe (PID: 1260)
- chrome.exe (PID: 3280)
- iexplore.exe (PID: 3436)
Changes settings of System certificates
- iexplore.exe (PID: 3120)
- iexplore.exe (PID: 1260)
- iexplore.exe (PID: 3436)
Reads internet explorer settings
- iexplore.exe (PID: 3648)
- iexplore.exe (PID: 3436)
- iexplore.exe (PID: 1260)
Application launched itself
- chrome.exe (PID: 2100)
- iexplore.exe (PID: 3120)
Creates files in the user directory
- iexplore.exe (PID: 3120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
68
Monitored processes
29
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,13749754958602634842,8883336083503721194,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1073530293066196056 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2180 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,13749754958602634842,8883336083503721194,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15189468638645001187 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4280 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,13749754958602634842,8883336083503721194,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=7572504380440100720 --mojo-platform-channel-handle=2100 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2180 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,13749754958602634842,8883336083503721194,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8869528793946208561 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3980 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1260 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3120 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 3489660927 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,13749754958602634842,8883336083503721194,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=3952898696269748840 --mojo-platform-channel-handle=4744 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,13749754958602634842,8883336083503721194,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5770617943709281061 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3032 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://uloz.to/file/9oPDQoAQ7AzI/super-bitcoin-miner-2018-rar" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,13749754958602634842,8883336083503721194,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=6330518156706747542 --mojo-platform-channel-handle=4888 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 501
Read events
3 193
Write events
296
Delete events
12
Modification events
| (PID) Process: | (2100) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2100) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2100) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2100) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2100-13246086584749125 |
Value: 259 | |||
| (PID) Process: | (2100) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2100) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2100) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2100) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (2100) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
81
Text files
103
Unknown types
23
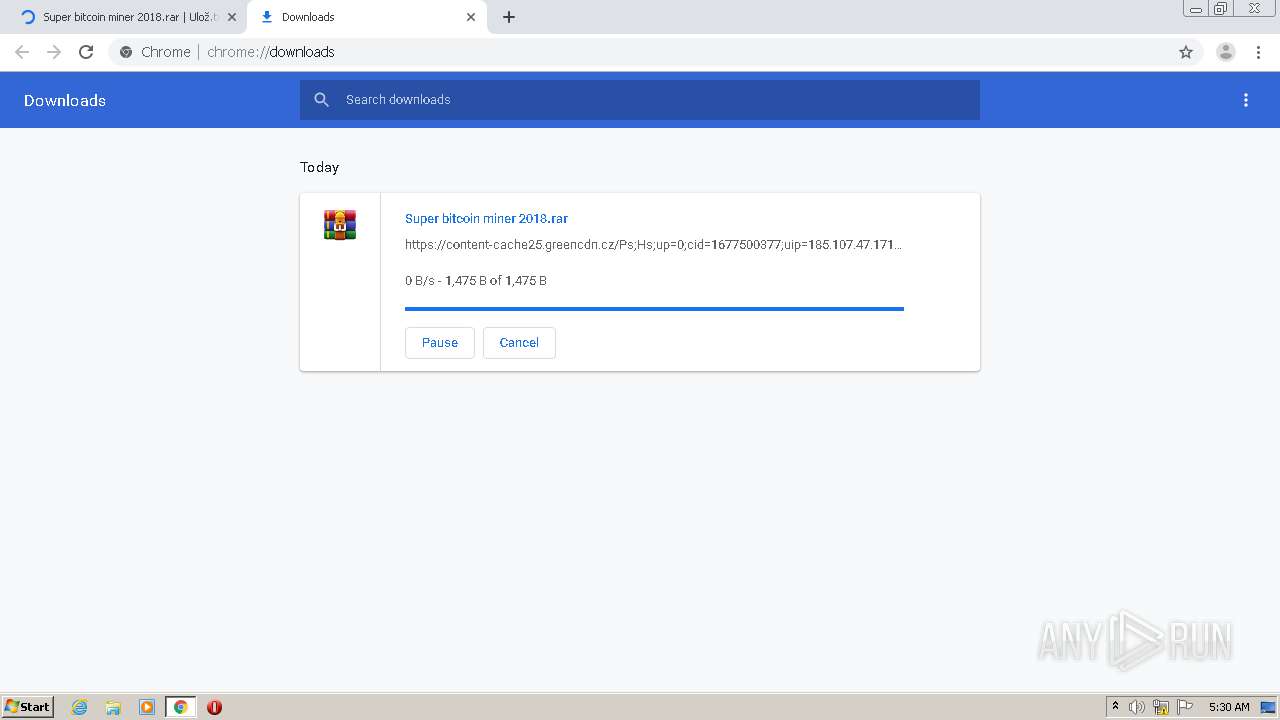
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F76ACB9-834.pma | — | |
MD5:— | SHA256:— | |||
| 2100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF3bbfe6.TMP | — | |
MD5:— | SHA256:— | |||
| 2100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f15968a5-73f0-4c79-b64c-8665c58d2bf3.tmp | — | |
MD5:— | SHA256:— | |||
| 2100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF3bc005.TMP | text | |
MD5:— | SHA256:— | |||
| 2100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF3bc043.TMP | text | |
MD5:— | SHA256:— | |||
| 2100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF3bbff5.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
132
DNS requests
82
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1260 | iexplore.exe | GET | 200 | 172.217.18.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEDM8p7YwCDvUCAAAAABXoPk%3D | US | der | 471 b | whitelisted |
3280 | chrome.exe | GET | 200 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
1056 | svchost.exe | GET | 200 | 2.20.242.11:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 781 b | whitelisted |
1260 | iexplore.exe | GET | 200 | 172.217.18.195:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1260 | iexplore.exe | GET | 200 | 172.217.18.195:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDqXuNQ97mPtAIAAAAAektt | US | der | 472 b | whitelisted |
1056 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
1260 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1056 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAKXB1YM1Knrv%2BJy8eCW2II%3D | US | der | 471 b | whitelisted |
1260 | iexplore.exe | GET | 200 | 172.217.18.195:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1260 | iexplore.exe | GET | 200 | 172.217.18.195:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3280 | chrome.exe | 77.48.29.200:443 | uloz.to | Liberty Global Operations B.V. | CZ | suspicious |
3280 | chrome.exe | 77.48.29.198:443 | static.uloz.to | Liberty Global Operations B.V. | CZ | unknown |
3280 | chrome.exe | 172.217.18.200:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3280 | chrome.exe | 216.58.204.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
3280 | chrome.exe | 93.99.2.40:443 | pw.uloz.to | Liberty Global Operations B.V. | CZ | unknown |
3280 | chrome.exe | 172.217.18.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3280 | chrome.exe | 216.58.198.195:443 | www.google.nl | Google Inc. | US | whitelisted |
3280 | chrome.exe | 77.48.29.196:443 | download.uloz.to | Liberty Global Operations B.V. | CZ | unknown |
3280 | chrome.exe | 95.168.199.179:443 | content-cache12.uloz.to | SuperNetwork s.r.o. | CZ | unknown |
3280 | chrome.exe | 95.168.199.183:443 | content-cache20.uloz.to | SuperNetwork s.r.o. | CZ | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
uloz.to |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
static.uloz.to |
| whitelisted |
thumbs.uloz.to |
| suspicious |
www.googletagmanager.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
pw.uloz.to |
| suspicious |
stats.g.doubleclick.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |