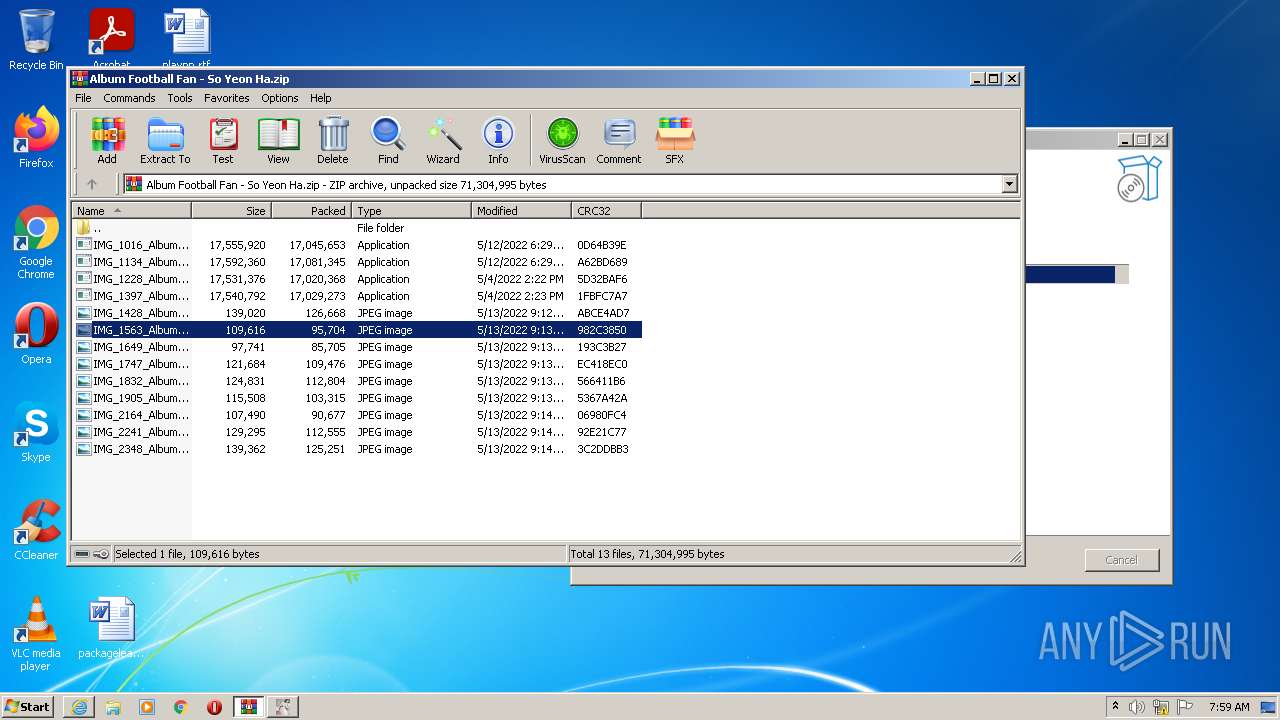
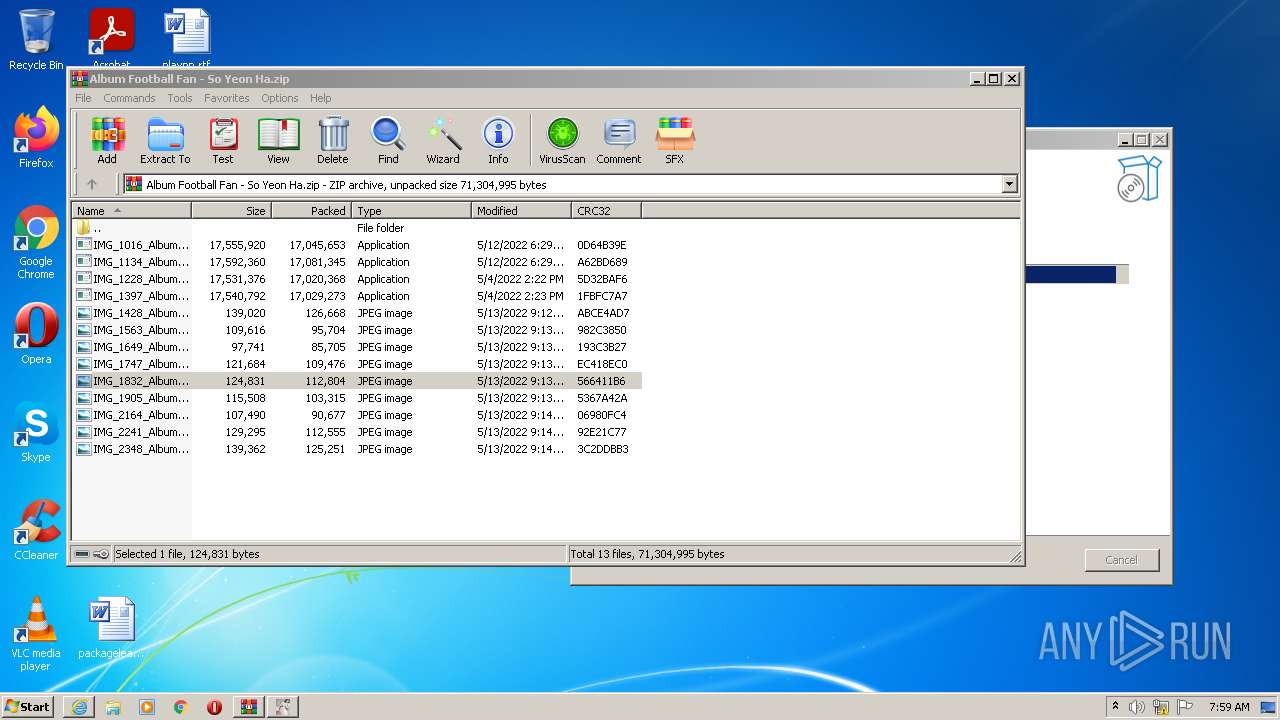
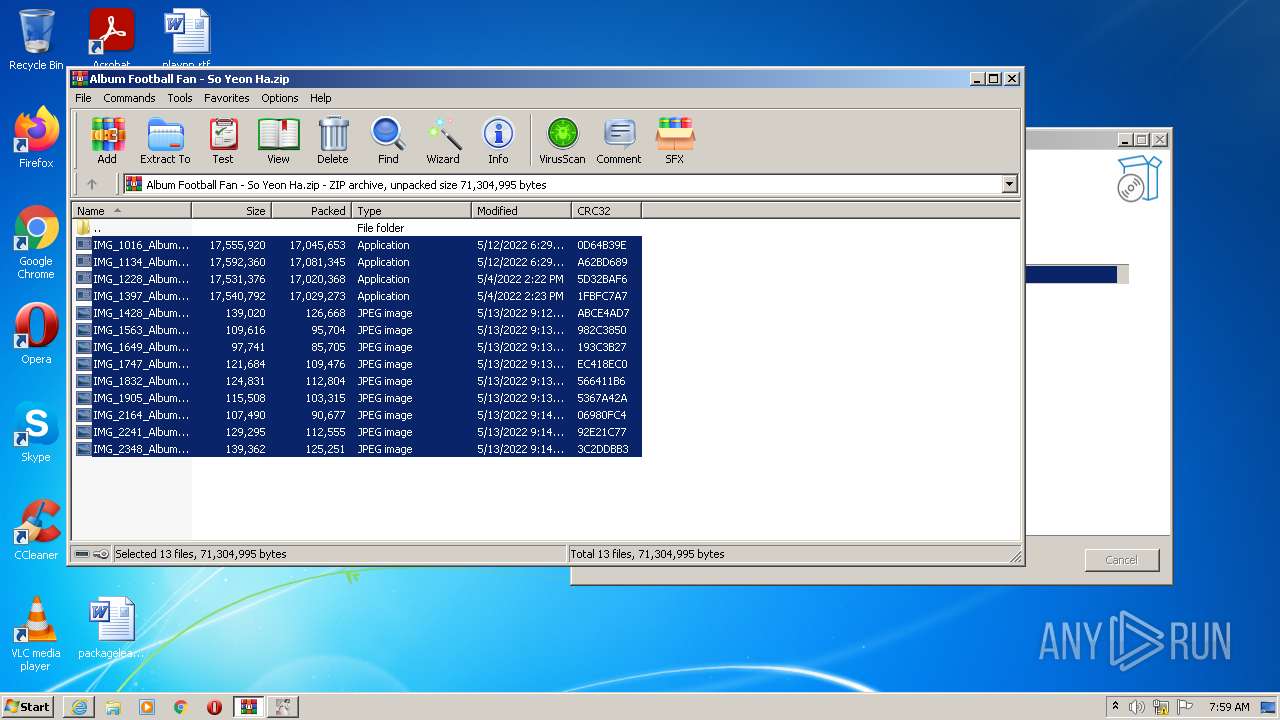
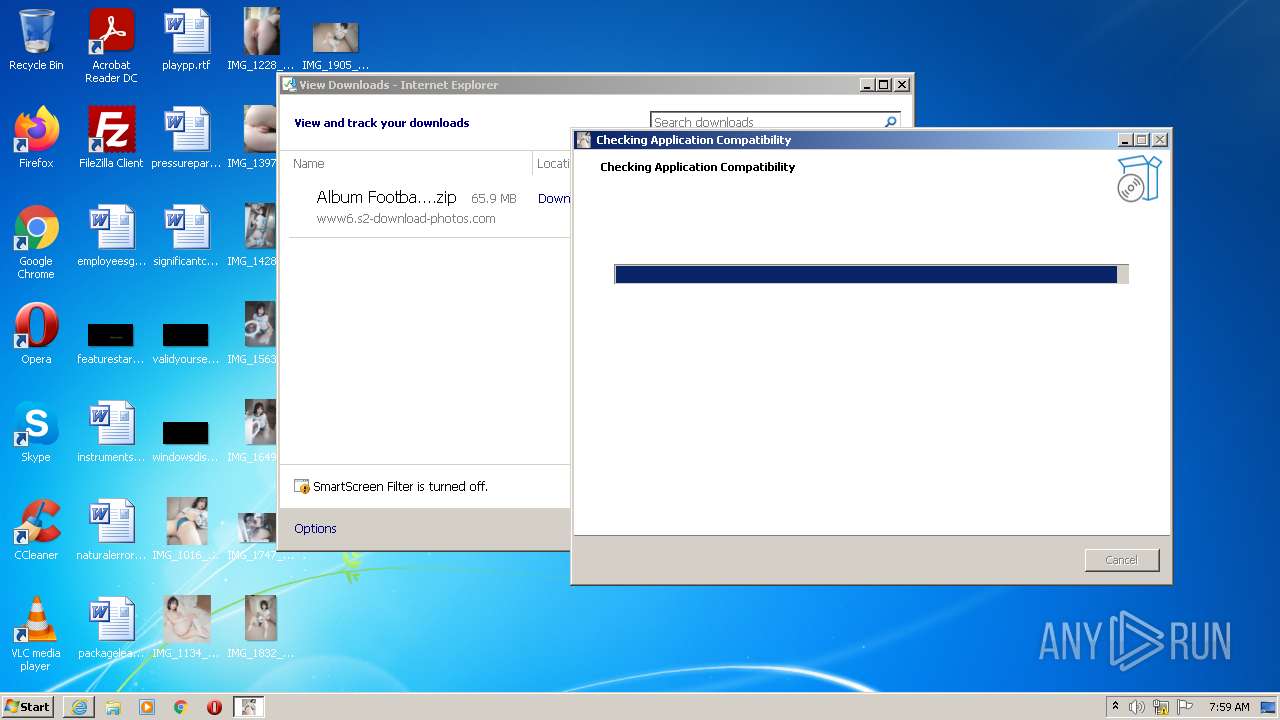
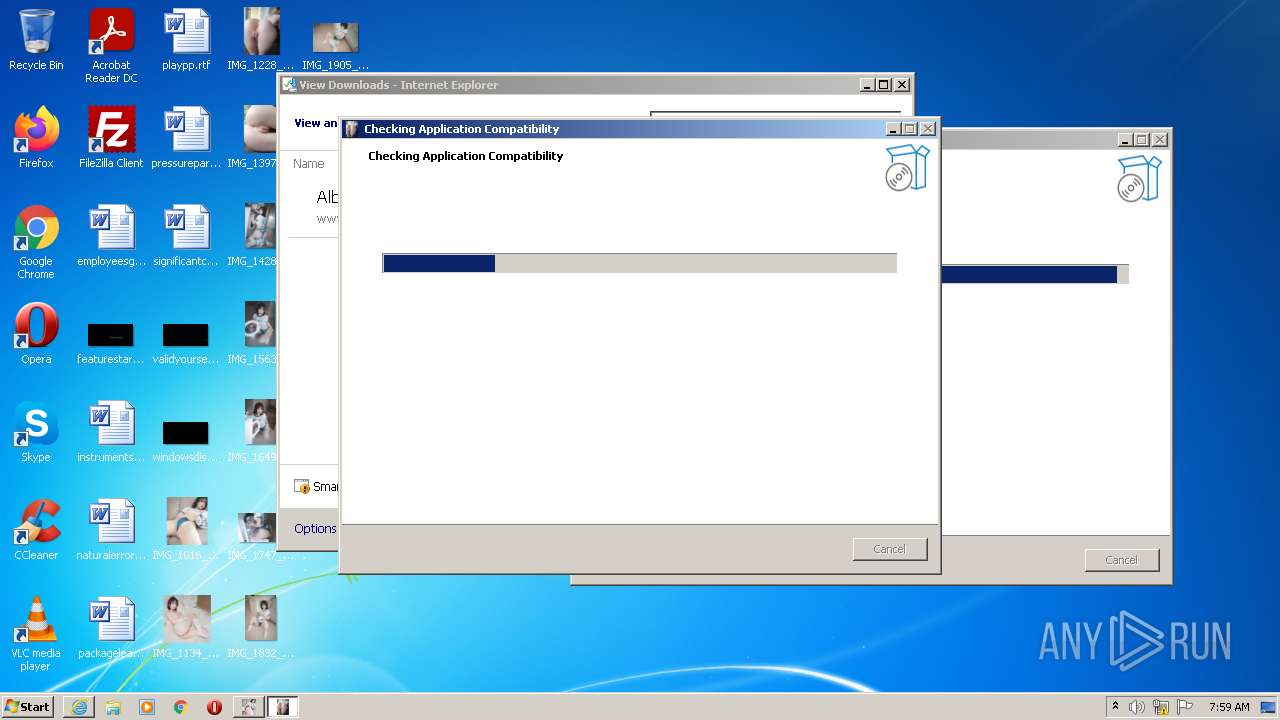
| URL: | https://s2-download-photos.com/download?r=girl/Album%20Football%20Fan%20-%20So%20Yeon%20Ha.zip |
| Full analysis: | https://app.any.run/tasks/f18427c1-ae50-49d9-ad11-39af6912e0d7 |
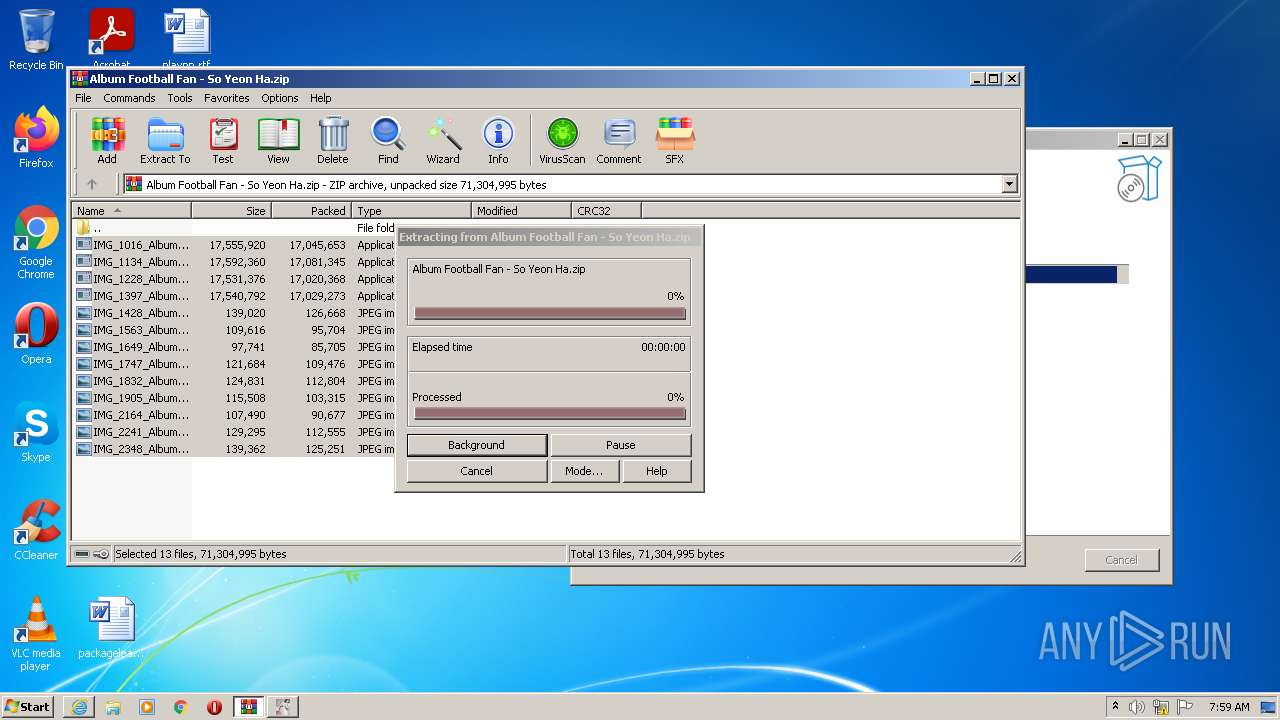
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2022, 06:58:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4352610A6F12DF775877A5E5330F35EE |
| SHA1: | 0873D44E0F9B3B2F945F85790322B67077FA0038 |
| SHA256: | 4B6071260EDA6DE5A48C725252F121C193C98F645859C429D9A9441910C2C3EF |
| SSDEEP: | 3:N8D0VNRHWKb/MX4s4VHrEFsfUn:2w5Nq4VV4Fscn |
MALICIOUS
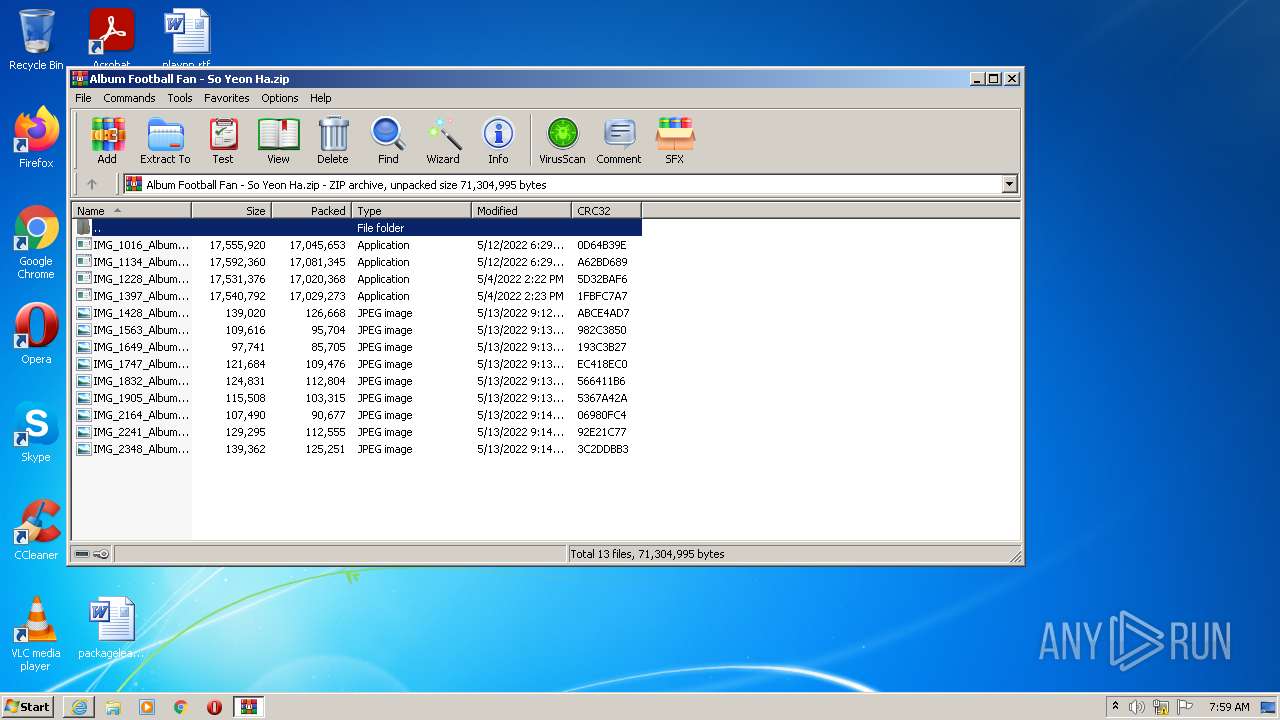
Drops executable file immediately after starts
- WinRAR.exe (PID: 2336)
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.exe (PID: 2492)
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.exe (PID: 2832)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.exe (PID: 2268)
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.tmp (PID: 2992)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.exe (PID: 1828)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.tmp (PID: 4092)
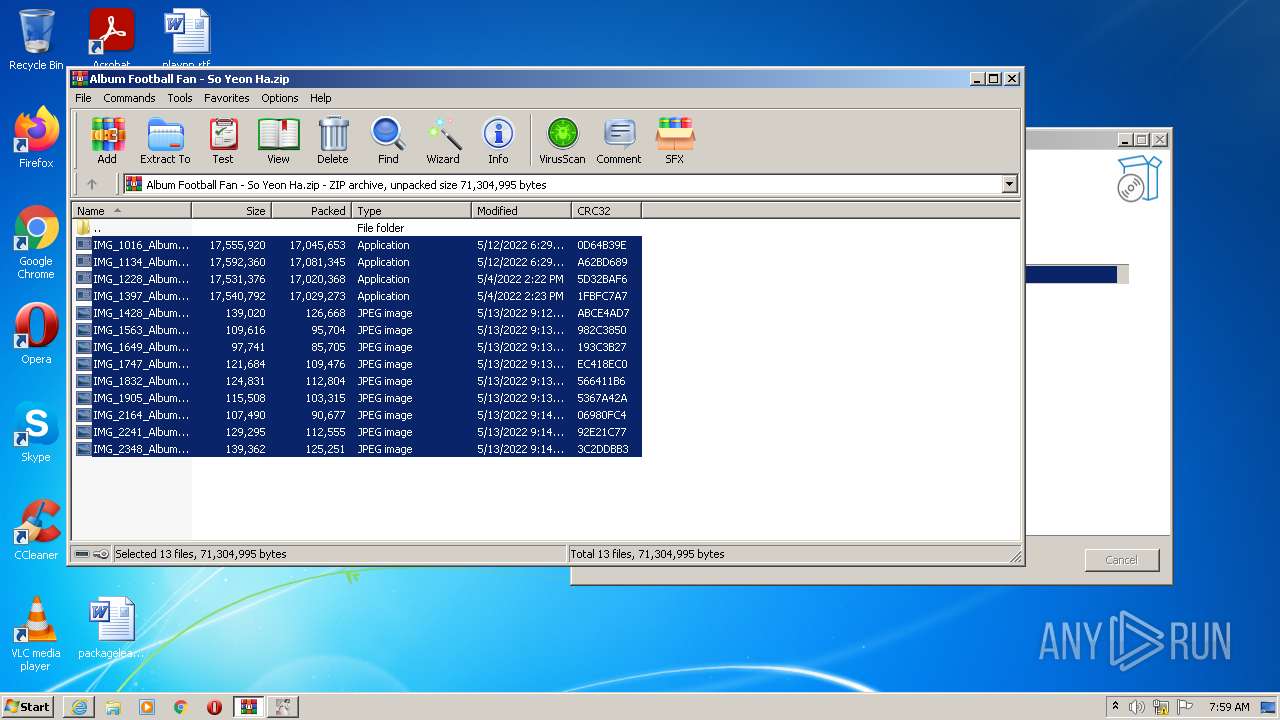
Application was dropped or rewritten from another process
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.exe (PID: 2492)
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.exe (PID: 2832)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.exe (PID: 2268)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.exe (PID: 1828)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 124)
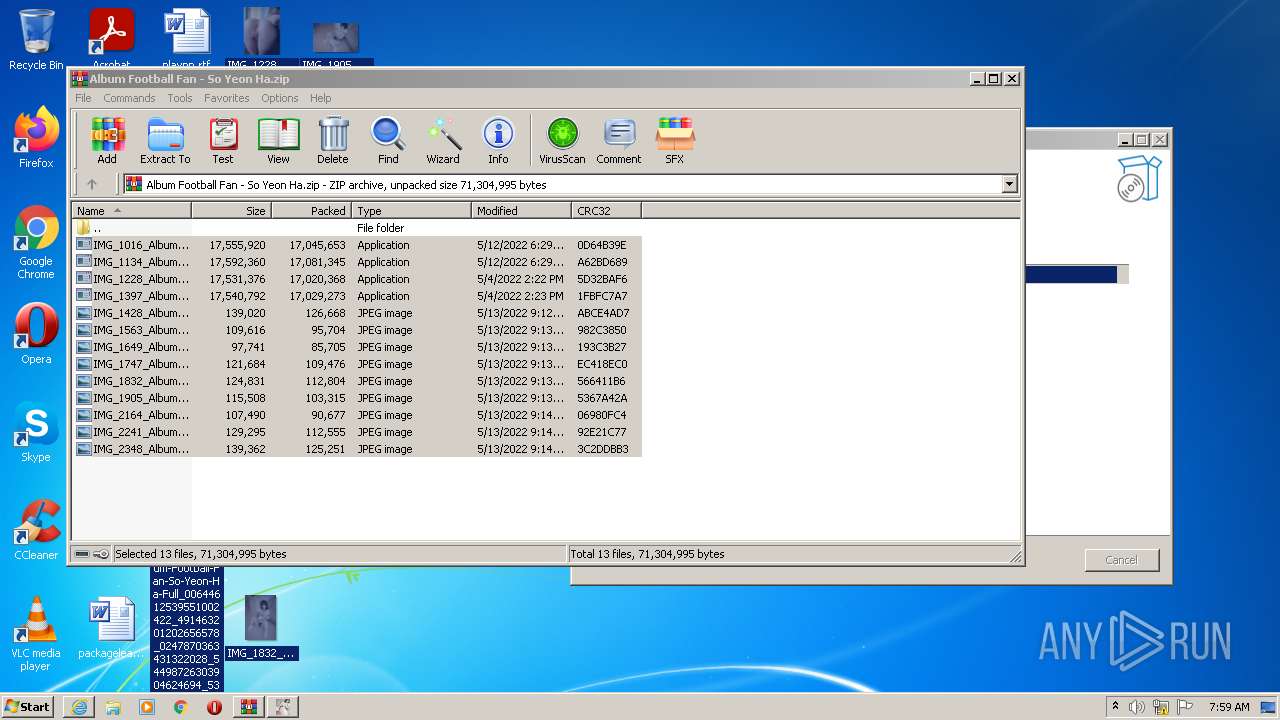
Reads the computer name
- WinRAR.exe (PID: 2336)
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.tmp (PID: 2648)
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.tmp (PID: 2992)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.tmp (PID: 3576)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.tmp (PID: 4092)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2336)
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.exe (PID: 2492)
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.exe (PID: 2832)
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.tmp (PID: 2992)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.exe (PID: 1828)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.exe (PID: 2268)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.tmp (PID: 4092)
Checks supported languages
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.exe (PID: 2492)
- WinRAR.exe (PID: 2336)
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.tmp (PID: 2648)
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.exe (PID: 2832)
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.tmp (PID: 2992)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.exe (PID: 2268)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.tmp (PID: 3576)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.exe (PID: 1828)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.tmp (PID: 4092)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2336)
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.exe (PID: 2492)
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.exe (PID: 2832)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.exe (PID: 2268)
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.tmp (PID: 2992)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.exe (PID: 1828)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.tmp (PID: 4092)
Reads Windows owner or organization settings
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.tmp (PID: 2648)
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.tmp (PID: 2992)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.tmp (PID: 3576)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.tmp (PID: 4092)
Reads the Windows organization settings
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.tmp (PID: 2648)
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.tmp (PID: 2992)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.tmp (PID: 3576)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.tmp (PID: 4092)
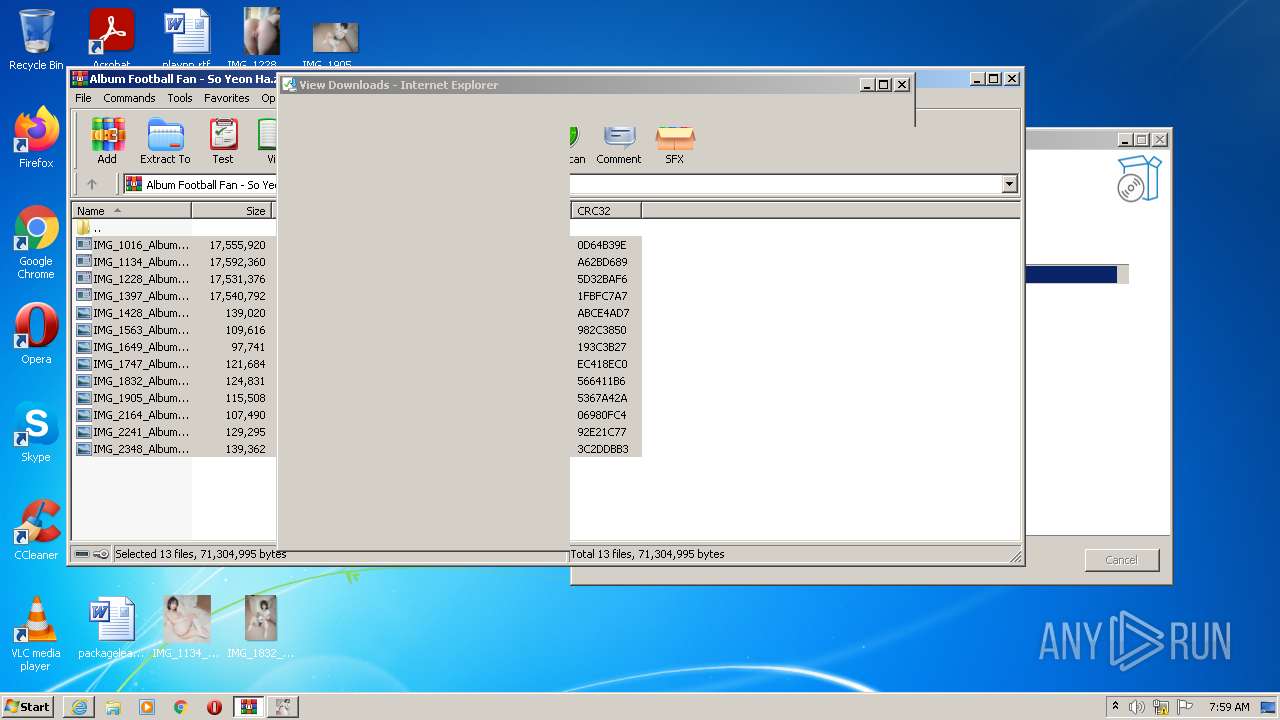
Executed via COM
- DllHost.exe (PID: 2892)
INFO
Reads the computer name
- iexplore.exe (PID: 116)
- iexplore.exe (PID: 124)
- DllHost.exe (PID: 2892)
Application launched itself
- iexplore.exe (PID: 116)
Checks supported languages
- iexplore.exe (PID: 116)
- iexplore.exe (PID: 124)
- DllHost.exe (PID: 2892)
Changes internet zones settings
- iexplore.exe (PID: 116)
Checks Windows Trust Settings
- iexplore.exe (PID: 124)
- iexplore.exe (PID: 116)
Reads settings of System Certificates
- iexplore.exe (PID: 124)
- iexplore.exe (PID: 116)
Reads the date of Windows installation
- iexplore.exe (PID: 116)
Modifies the phishing filter of IE
- iexplore.exe (PID: 116)
Application was dropped or rewritten from another process
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.tmp (PID: 2648)
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.tmp (PID: 2992)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.tmp (PID: 3576)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.tmp (PID: 4092)
Creates files in the user directory
- iexplore.exe (PID: 116)
Adds / modifies Windows certificates
- iexplore.exe (PID: 116)
Changes settings of System certificates
- iexplore.exe (PID: 116)
Dropped object may contain Bitcoin addresses
- IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.tmp (PID: 2992)
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.tmp (PID: 4092)
Manual execution by user
- IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.exe (PID: 2268)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
12
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://s2-download-photos.com/download?r=girl/Album%20Football%20Fan%20-%20So%20Yeon%20Ha.zip" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 124 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:116 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
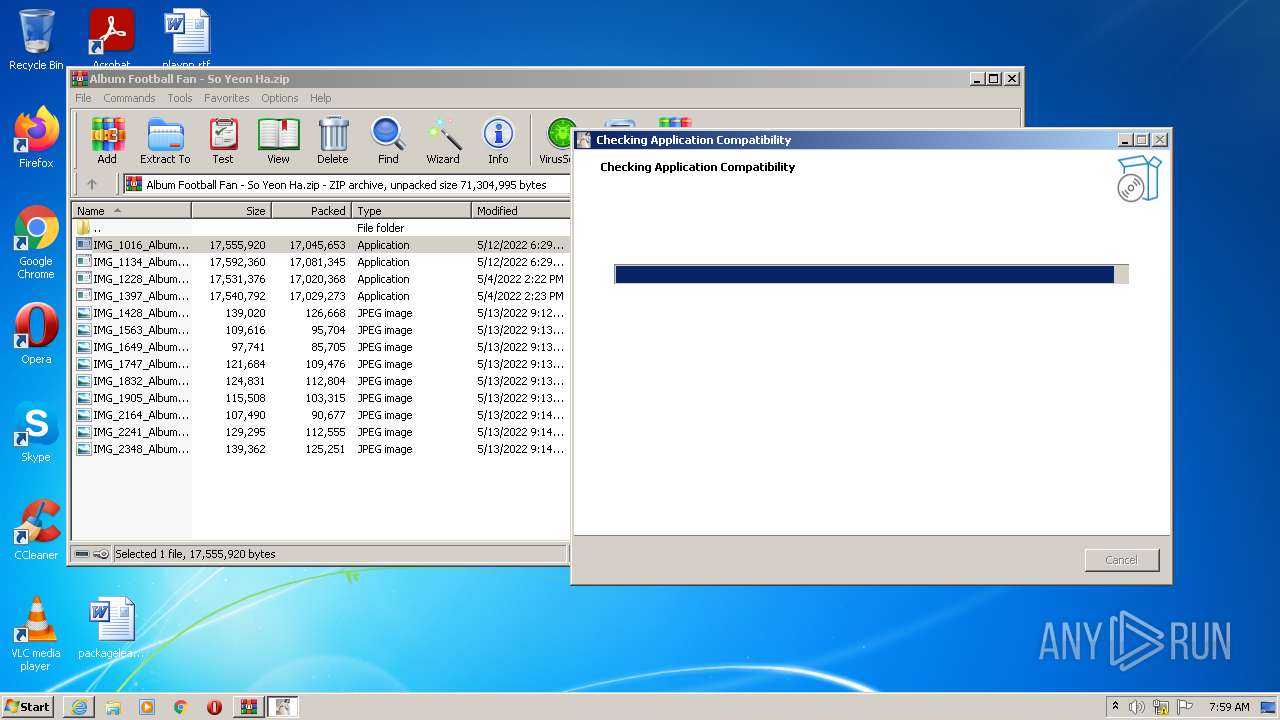
| 1828 | "C:\Users\admin\Desktop\IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.exe" /SILENT | C:\Users\admin\Desktop\IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.exe | IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.tmp | ||||||||||||
User: admin Company: MVO Software Integrity Level: MEDIUM Description: Rnews Setup Exit code: 0 Version: 13.19.237.0 Modules
| |||||||||||||||
| 2268 | "C:\Users\admin\Desktop\IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.exe" | C:\Users\admin\Desktop\IMG_1228_Album-Football-Fan-So-Yeon-Ha-Full_20781912737867958_61533946083242332060_47270218293192100_69301883248259038_4993075881594993_48847903510197779.exe | Explorer.EXE | ||||||||||||
User: admin Company: MVO Software Integrity Level: MEDIUM Description: Rnews Setup Exit code: 1 Version: 13.19.237.0 Modules
| |||||||||||||||
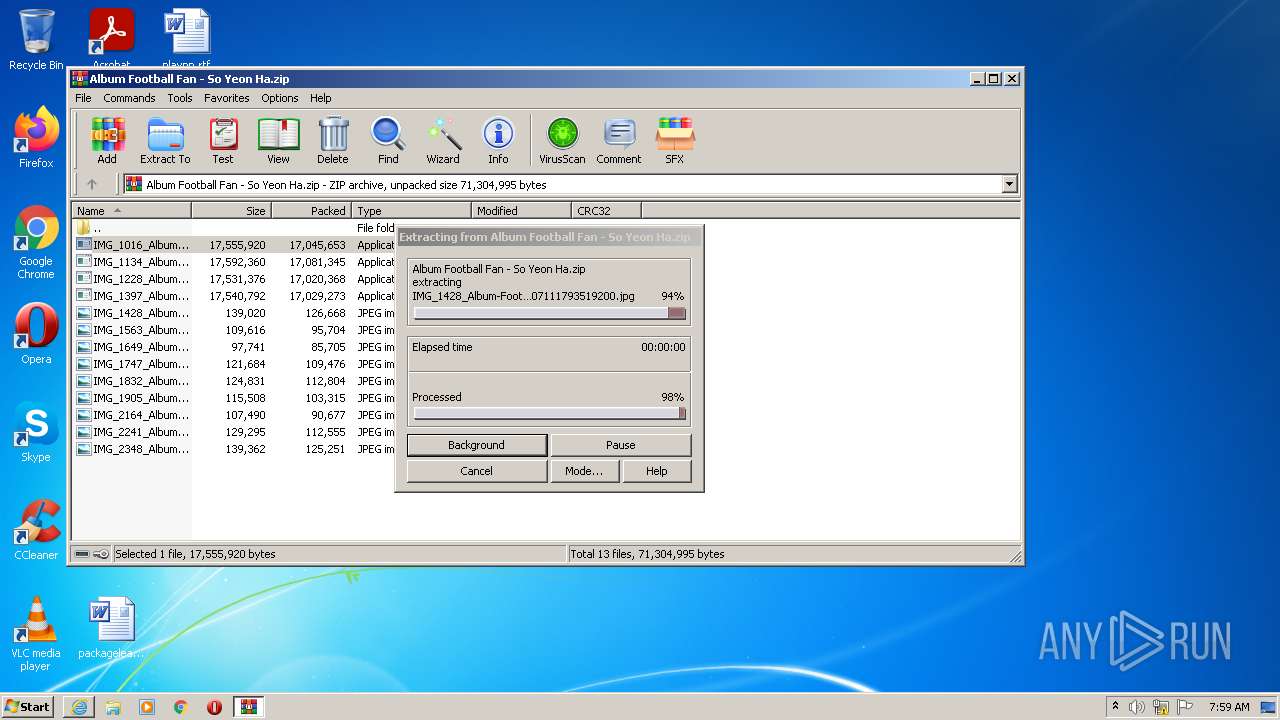
| 2336 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Album Football Fan - So Yeon Ha.zip" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
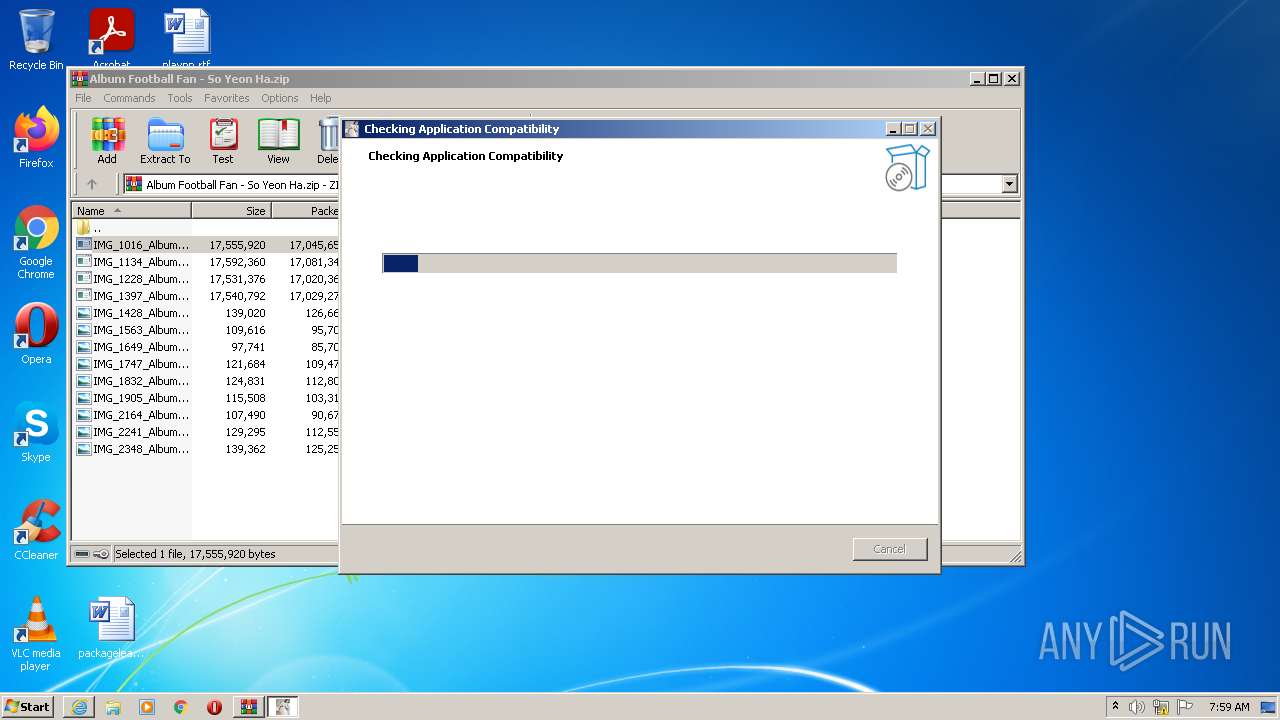
| 2492 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2336.49774\IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2336.49774\IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.exe | WinRAR.exe | ||||||||||||
User: admin Company: MVO Software Integrity Level: MEDIUM Description: Rnews Setup Exit code: 1 Version: 13.19.222.0 Modules
| |||||||||||||||
| 2648 | "C:\Users\admin\AppData\Local\Temp\is-5IN1H.tmp\IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.tmp" /SL5="$5014A,16593164,875520,C:\Users\admin\AppData\Local\Temp\Rar$EXa2336.49774\IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.exe" | C:\Users\admin\AppData\Local\Temp\is-5IN1H.tmp\IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.tmp | — | IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.exe | |||||||||||
User: admin Company: MVO Software Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2832 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2336.49774\IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.exe" /SILENT | C:\Users\admin\AppData\Local\Temp\Rar$EXa2336.49774\IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.exe | IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.tmp | ||||||||||||
User: admin Company: MVO Software Integrity Level: MEDIUM Description: Rnews Setup Exit code: 0 Version: 13.19.222.0 Modules
| |||||||||||||||
| 2892 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2992 | "C:\Users\admin\AppData\Local\Temp\is-8VO9D.tmp\IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.tmp" /SL5="$6014A,16593164,875520,C:\Users\admin\AppData\Local\Temp\Rar$EXa2336.49774\IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.exe" /SILENT | C:\Users\admin\AppData\Local\Temp\is-8VO9D.tmp\IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.tmp | IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.exe | ||||||||||||
User: admin Company: MVO Software Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
14 668
Read events
14 485
Write events
173
Delete events
10
Modification events
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 510006256 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30960864 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 810010006 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30960864 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
260
Suspicious files
13
Text files
1 333
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
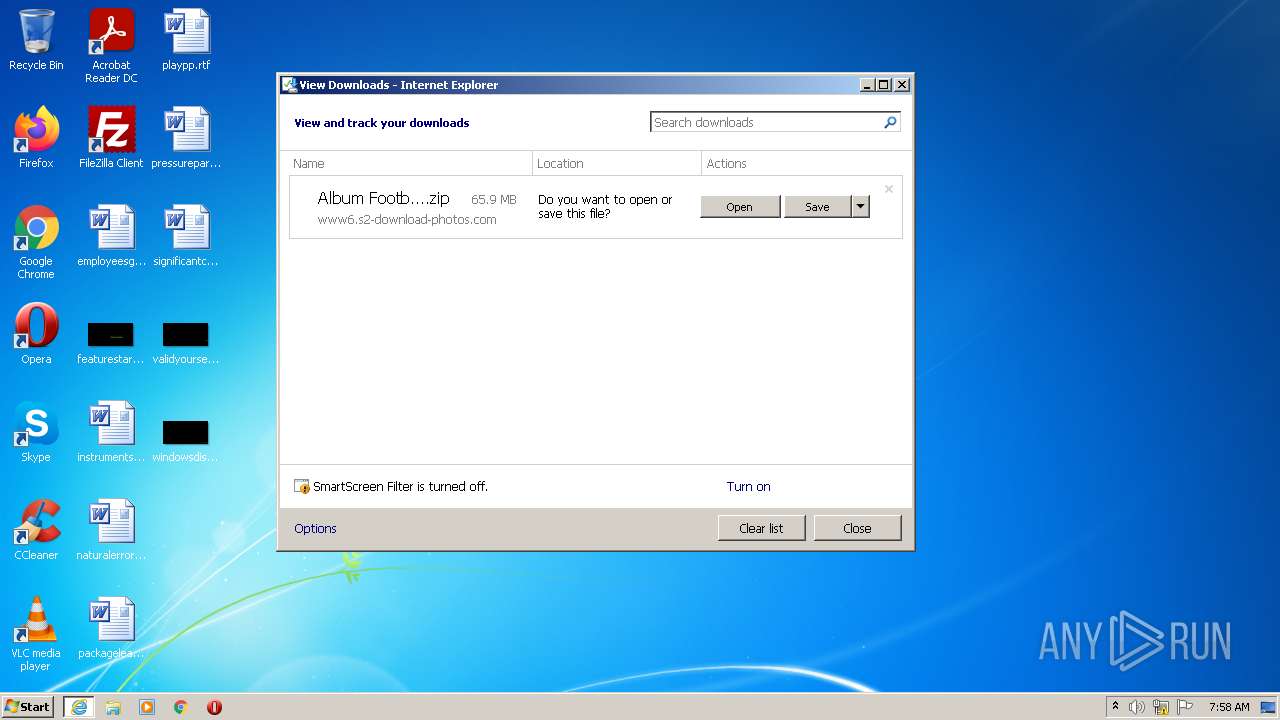
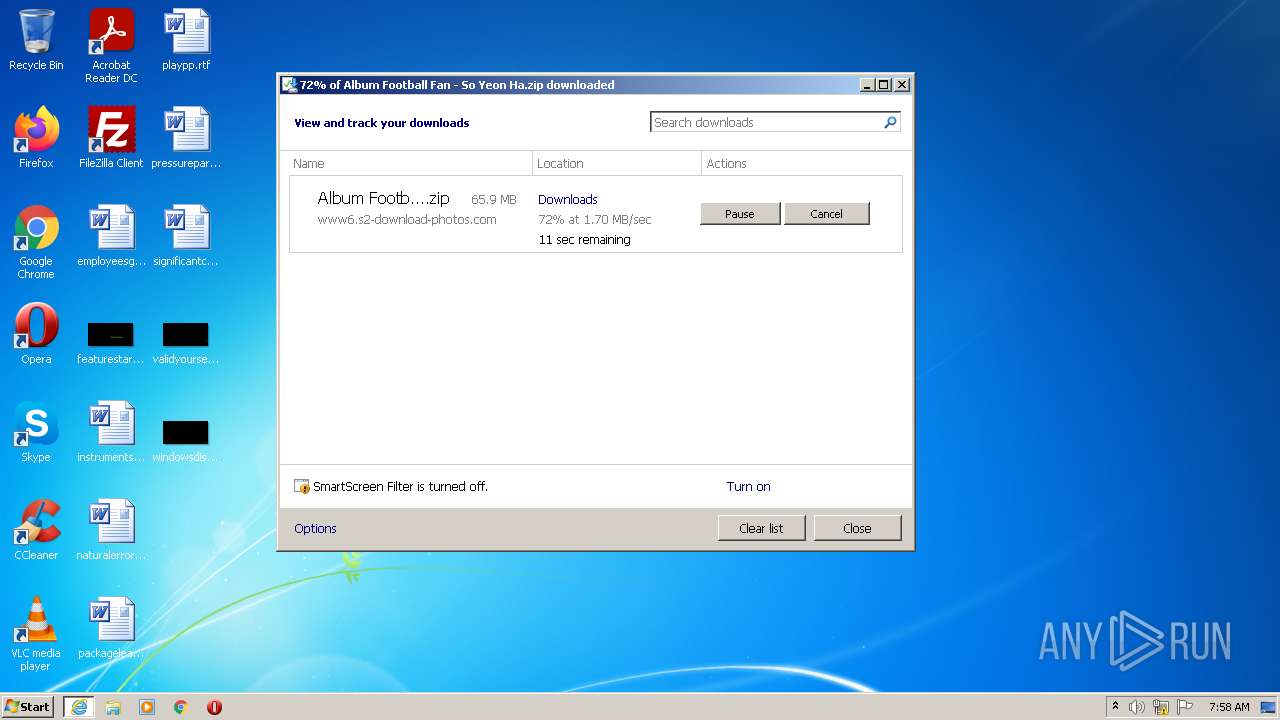
| 116 | iexplore.exe | C:\Users\admin\Downloads\Album Football Fan - So Yeon Ha.zip | — | |
MD5:— | SHA256:— | |||
| 124 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 124 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\82CB34DD3343FE727DF8890D352E0D8F | der | |
MD5:— | SHA256:— | |||
| 124 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\82CB34DD3343FE727DF8890D352E0D8F | binary | |
MD5:— | SHA256:— | |||
| 124 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\Album%20Football%20Fan%20-%20So%20Yeon%20Ha[1].zip | compressed | |
MD5:— | SHA256:— | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:— | SHA256:— | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:— | SHA256:— | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF409FE908FABA7090.TMP | gmc | |
MD5:— | SHA256:— | |||
| 2336 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2336.49774\IMG_1016_Album-Football-Fan-So-Yeon-Ha-Full_00644612539551002422_491463201202656578_0247870363431322028_54498726303904624694_5325788728527150766_061976142589443557.exe | executable | |
MD5:— | SHA256:— | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{5C09250B-D8D3-11EC-8C9F-1203334A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
26
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
124 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2f5555cb627e5a08 | US | compressed | 4.70 Kb | whitelisted |
124 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.78 Kb | whitelisted |
116 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
116 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
116 | iexplore.exe | 13.92.246.37:443 | query.prod.cms.msn.com | Microsoft Corporation | US | whitelisted |
124 | iexplore.exe | 172.67.186.43:443 | s2-download-photos.com | — | US | unknown |
124 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
124 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
116 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
124 | iexplore.exe | 104.21.19.125:443 | s2-download-photos.com | Cloudflare Inc | US | suspicious |
116 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
116 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
116 | iexplore.exe | 204.79.197.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
s2-download-photos.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
www6.s2-download-photos.com |
| unknown |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |