| File name: | c.exe |
| Full analysis: | https://app.any.run/tasks/8f3eb096-0bc4-47e6-b512-8ee8b521a71f |
| Verdict: | Malicious activity |
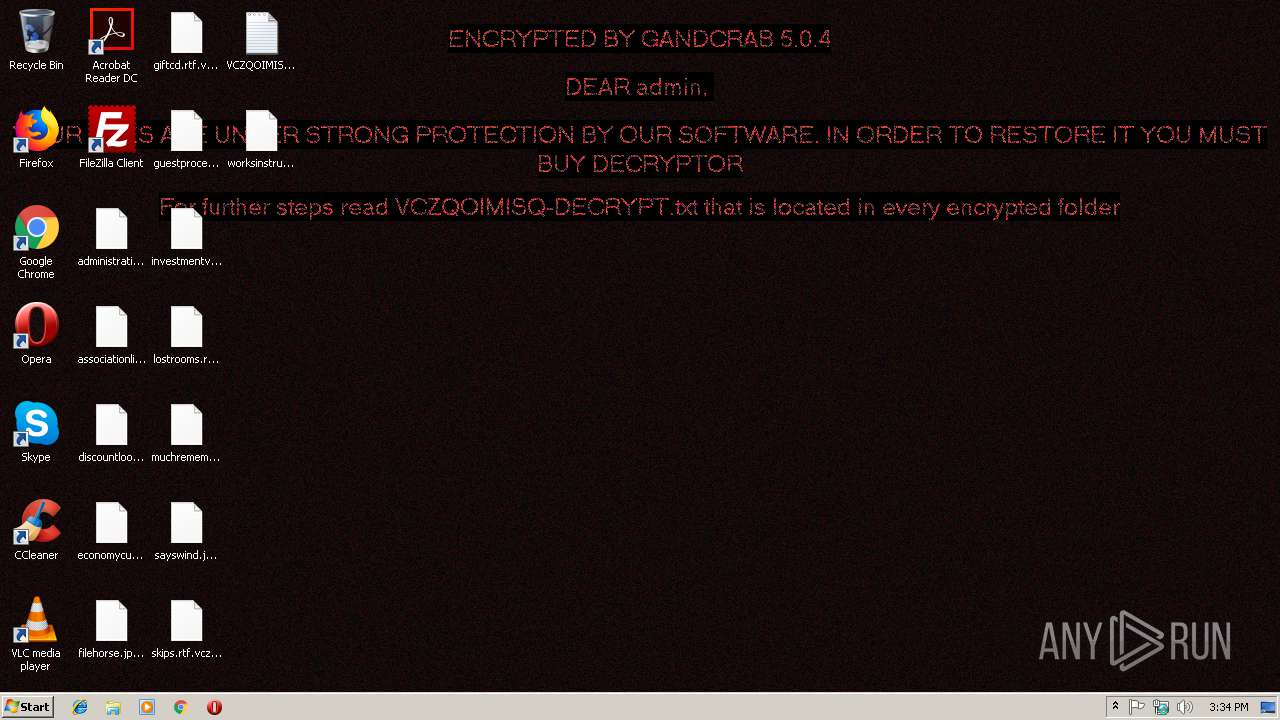
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
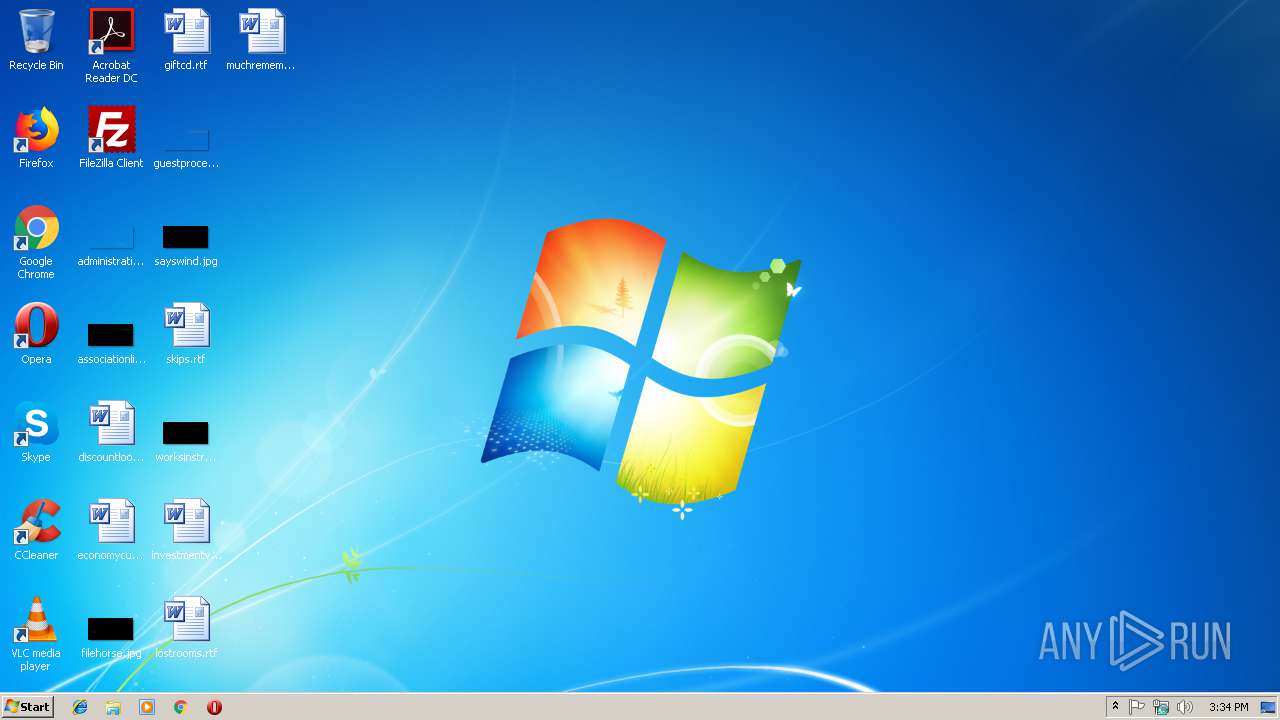
| Analysis date: | January 22, 2019, 15:34:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 24275604649AC0ABAFE99B981B914FBC |
| SHA1: | 818B0E3018AD27BE9887E9E5F4EF1971F422652C |
| SHA256: | 4B5FE7497864D07F78AF15FA3E1AA3702B303B89F9644624871D83DD0F484749 |
| SSDEEP: | 1536:JLMVCWvZ8URtqOz3d+1Qs6H9Mk2e3E2avMWC3yMgYxf6+okbdWsWjcdpKCaIxWzX:VM9ntZ3s1QJdnU2SQdf64ZZ8CaIxWec |
MALICIOUS
Writes file to Word startup folder
- c.exe (PID: 3508)
Renames files like Ransomware
- c.exe (PID: 3508)
Dropped file may contain instructions of ransomware
- c.exe (PID: 3508)
GandCrab keys found
- c.exe (PID: 3508)
Deletes shadow copies
- c.exe (PID: 3508)
Actions looks like stealing of personal data
- c.exe (PID: 3508)
SUSPICIOUS
Reads the cookies of Mozilla Firefox
- c.exe (PID: 3508)
Creates files like Ransomware instruction
- c.exe (PID: 3508)
Creates files in the user directory
- c.exe (PID: 3508)
INFO
Dropped object may contain TOR URL's
- c.exe (PID: 3508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:10:26 10:47:08+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 80896 |
| InitializedDataSize: | 68096 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6229 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Oct-2018 08:47:08 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 26-Oct-2018 08:47:08 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00013BE4 | 0x00013C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58693 |
.rdata | 0x00015000 | 0x00006B46 | 0x00006C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.59755 |
.data | 0x0001C000 | 0x000087F4 | 0x00006A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.15553 |
.rsrc | 0x00025000 | 0x000001E0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.7123 |
.reloc | 0x00026000 | 0x000013A8 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64868 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
MPR.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
WININET.dll |
ole32.dll |
Total processes
34
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3508 | "C:\Users\admin\AppData\Local\Temp\c.exe" | C:\Users\admin\AppData\Local\Temp\c.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3652 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | — | c.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
119
Read events
88
Write events
31
Delete events
0
Modification events
| (PID) Process: | (3508) c.exe | Key: | HKEY_CURRENT_USER\Software\ex_data\data |
| Operation: | write | Name: | ext |
Value: 2E00760063007A0071006F0069006D006900730071000000 | |||
| (PID) Process: | (3508) c.exe | Key: | HKEY_CURRENT_USER\Software\keys_data\data |
| Operation: | write | Name: | public |
Value: 0602000000A40000525341310008000001000100D7787FF5611B1CBEB060821B1B14FA86D82F7922AFD2A97351D827E88A53FD3662986EA83E5A587E38721253C1E4011C2CE8BDF2F848D6088921108F469A238D0F7F4050374B64318D824CB483DE3CEB7CA1B2807F5A453F757082B4A1CD0DF955CAB569A36DE52A7BBE7046833BC93A3CA7AA325978E4C7F2E139F0D55058F8FFD7624DB58F4D65B344AF8631332710DF4623118C1C4236C382C21289D4FCBBC872A63893114E700384F124422D5D56C48F9F2DE46ECF39176237DE4B03DB89178D857CC949C12B95E4216FE50658B12C03336E780B6185E69D0B5CF6699D642171FE858F51C3AA6C6372B412D2D5EA02531F951951056F993A69CEC2A2F6A1 | |||
| (PID) Process: | (3508) c.exe | Key: | HKEY_CURRENT_USER\Software\keys_data\data |
| Operation: | write | Name: | private |
Value: 940400004B2EA21DFF853787659679A615879829FBCF18DF330CFF7B9E2BB7E967E1775B7DB9780716262F2C78AADEEDD5BD79B8F803FB7D12974272585158B04DC00F1A17D63D3AF4C5D640C94E00F752A4B5A7A70962C7B4FED3DEAF4347D2CEB1BC6C9F3591F0348FF99D6B93900FB0677C500F25BB8253841E3647F8491C132CBDA353D29F31DFAB5A0DEE40D92B5E30E2000C2C0E3A043FFEE87E5F01161C12E164BDCEA64FB4E54BF7E86D962621AE95620B73DAF25B59A8CAFD686FE789CAC45B2A337378E3455DA985B3C307FE3093899E11C54B24399C96FC529B57EBCD7E2550821F33512FA0C8DCA6EB31E9113C01BDADE8960C40CB30A8BA6B70A2197859195E7CDB3AA38B0C376052FB4B1AF1E0E59658EF4929EA17FF3627ABD533D978157EFEA37EB550FDFEE92873DB67396B26829C4D954686C0FF8C174D93604564370400279014B78F8FB83088CA1456B166B45AFBEC1035EA82A01D8B86064465F3CFEE091C13173A92469A20E7A6DD0C18FCF1C56134CF8E0F412ADD01B7C190587F4712595D930B48D05ED56535AE7462595DF9A4E85887F23B45EB7DD17A68A860FA318B8FB4B6C875FC9BA863783DCCB740BC906A5ADA90EE8AD0A80DECEE2FFC1C0FA8FD0C656A0B633849F751E8BE6F44A97F3EA2E90DEB9D68C12EFAE3469DE4E321C4E9E6E00AEE796E14E147766BF903A4DD6C95CD235912F0A91A0D41C13AF49CDD1214EA2CD7A870E7DF380277CBC8D77A6DC6752641056BA7356F8D176BC4B56B0E57C7AA8A944DCD17AE74DB1595CAED402687790B5AA69922855947E755AF3F84C790D4312DFFBA55D5C82CCE6A27088EB9AB5ABA56273ED83982614E4780C28D58FF6F0A21B929D537694752C9CCBEFFBDC7A47B11ABFB43005973A2F66ACC279748436AB2A753437AFC88F3DF84708B0560B963EE6149F1D5C33AC4E2B991D01558741B54913B5B6399CE6E36CDBE2647214302D323A523254F7B0B7C36C44A9926697805D788A68F6B7B30B40E3ED4EECE9E2D2B402FA831FD37F9C0413300CEE6E53D9D47B9C888A425F1D8CD06C722DA2501B9F403EB3E166492D2947E279A0C406F895798980451A36BA3E19013C9585C47D37FE1E8F56F47CF7117FEF860458248C8C717480A8F75E740A637E2001ECD554BAC2D54FC4B70199986AB79128378A171ABF82AFF44A3701B93BEE92A32CE77E100A4188EB3C23B877CD187A796609ECDF287F9CD4FC937624CA374613708B9C5FB2F787BB88873B28C67C733CC233FEE5A79CBE5234FEFEB8B719748ECAB4E7AA19E9F165A0AF2DBF45AEC229F6F9BC8EA80BB05B277816592E357E520232470A69FD151C74609D347EA0DC021B7BDC87249BAFE479DAE8A9292FA9388ED317529AE1E874CFFC02D746EDB785FB748C17631BB806751FA63679AE188060F4803662024274D03FE9AD155A9FFD52EDC6D540407258FA097E87EE0B8F17CFDE5867141893B5B1D02464AC08387498DC5FDBC97130B2A003B4FF190540E196D51EAF02A8150BEDA39B6629D9EEA39F6BF8D73675DCC7BA7C98FB7BDE1ED526124D08DA04B1069D47814FE313C6447CD101A4D92A70B5B07D7D0E4402D3B5E972E0E4BFC6C7D61F38077E47876E8B574EF3F24EA630077663DA0F5230C8DD3850D5E3F43769802BAB90DFA34D69D2B4012D920F57A55133D3BB3A6FD94A91C8D0CE3BA9B2ECB5D24611ED8453E8088E9C70F2E45363701C8F84336F29DD4D9BB335008639A51972851BC243B5905193FA53D0B26B913C64E6AA44B9F8A51FE80529C2D93AB56B6F37ACAD5393E4B8DBA7B1F2379809DAC10B8451EAC39786AA31F6B4E2A999AE62EE25006D45CB2579143FE49D4B2088B3B8AB282E1E8FD2EEAD8C014CBCFED29E52E88F3FDA46387D2216BC8CFFCCD620A8038A84A69B05E5136265F788E91A70305CC9E3D15BD4F6E6DF6C7020E0E9BA8A5EAC3F06205577F9543C5BFD3500B3C6732B425B7794F04F6632ADFF0F8FB1B405D8D4580C93FA2DCFFF1CD875AAAA82FE2C5A79E8555AC305D7500C3CB0206823A44702DB074B731D79014E03C51EEC3C20170C4EBA5C6BE46942FECEAB5EDD8C6B452A0F2C7BDE1EE57286672325D2A1EA48AA56CB8F34A79D8A7DE5286678AD5D5C99069E66E5C4126942B8FE7B246E45E9F77E43EA36E5A64A288DF262702E77D6C9DBBD8C1A2EFC40F21F07BEFF75A4C4AD9EFF115624112FDD732025A2597FB78B58417A4A360108BFECD79E255BEF4898E984D8E5CFD61345295958C74656D313DADF6AECD553F7583B3AC493F8E2E0896E26605B53C2AB9A95176B28471C0E226AD2ED81BDF954DC982AFA6C1323516A8101C0ED668C735B8D765F7CAC5 | |||
| (PID) Process: | (3508) c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3508) c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3508) c.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\c_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3508) c.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\c_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3508) c.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\c_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3508) c.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\c_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3508) c.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\c_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
0
Suspicious files
269
Text files
204
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3508 | c.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | — | |
MD5:— | SHA256:— | |||
| 3508 | c.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobData | — | |
MD5:— | SHA256:— | |||
| 3508 | c.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobSettings | — | |
MD5:— | SHA256:— | |||
| 3508 | c.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\addressbook.acrodata | — | |
MD5:— | SHA256:— | |||
| 3508 | c.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\0FDED5CEB68C302B1CDB2BDDD9D0000E76539CB0.crl | — | |
MD5:— | SHA256:— | |||
| 3508 | c.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\CE338828149963DCEA4CD26BB86F0363B4CA0BA5.crl | — | |
MD5:— | SHA256:— | |||
| 3508 | c.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp.vczqoimisq | binary | |
MD5:— | SHA256:— | |||
| 3508 | c.exe | C:\Users\admin\.oracle_jre_usage\VCZQOIMISQ-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 3508 | c.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Forms\VCZQOIMISQ-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 3508 | c.exe | C:\Users\admin\VCZQOIMISQ-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3508 | c.exe | GET | — | 78.46.77.98:80 | http://www.2mmotorsport.biz/ | DE | — | — | suspicious |
3508 | c.exe | GET | — | 217.26.53.161:80 | http://www.haargenau.biz/ | CH | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3508 | c.exe | 78.46.77.98:80 | www.2mmotorsport.biz | Hetzner Online GmbH | DE | suspicious |
3508 | c.exe | 217.26.53.161:80 | www.haargenau.biz | Hostpoint AG | CH | malicious |
3508 | c.exe | 78.46.77.98:443 | www.2mmotorsport.biz | Hetzner Online GmbH | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.2mmotorsport.biz |
| unknown |
www.haargenau.biz |
| unknown |