| File name: | c.exe |
| Full analysis: | https://app.any.run/tasks/64e7cab9-689d-4121-a616-6f99e1d52f0b |
| Verdict: | Malicious activity |
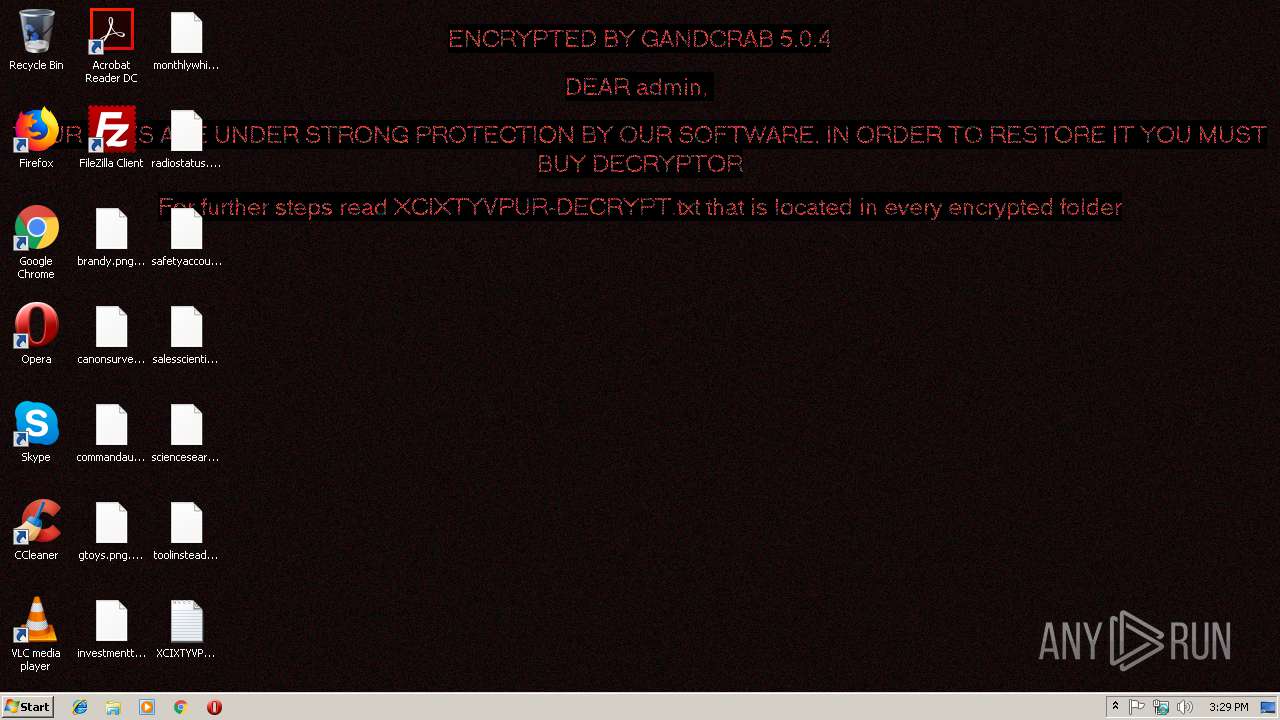
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
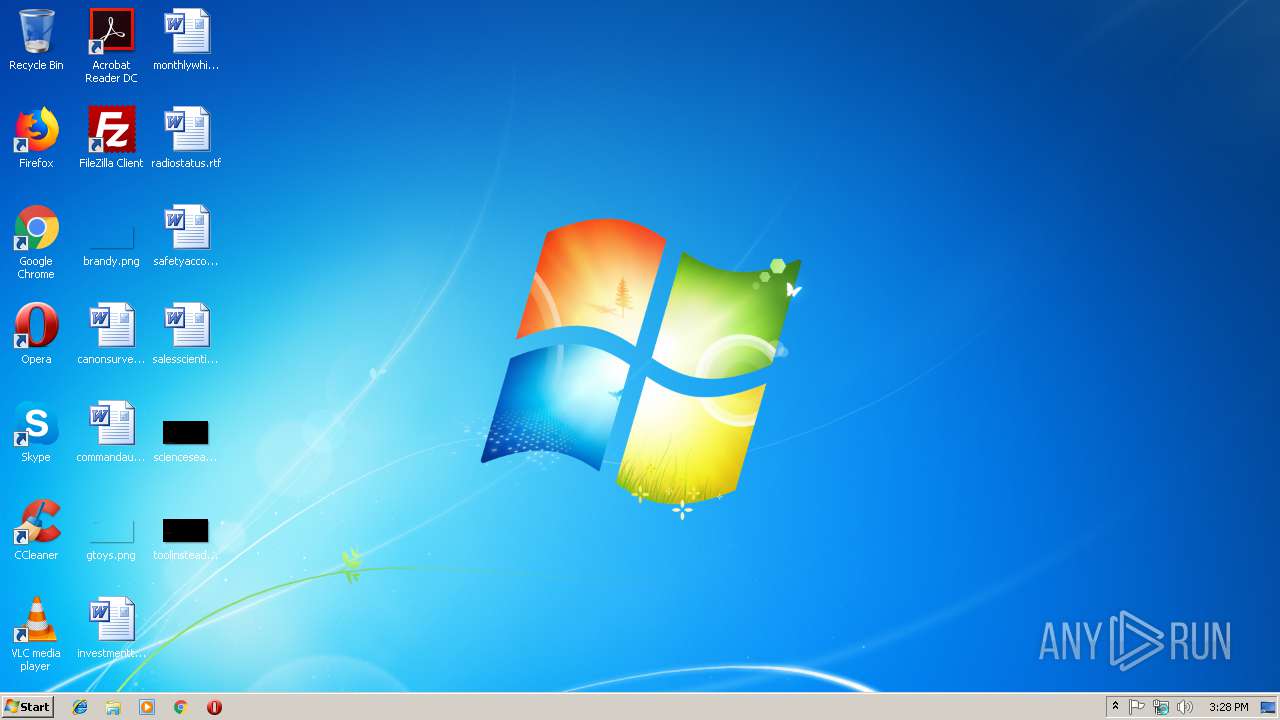
| Analysis date: | January 22, 2019, 15:28:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 24275604649AC0ABAFE99B981B914FBC |
| SHA1: | 818B0E3018AD27BE9887E9E5F4EF1971F422652C |
| SHA256: | 4B5FE7497864D07F78AF15FA3E1AA3702B303B89F9644624871D83DD0F484749 |
| SSDEEP: | 1536:JLMVCWvZ8URtqOz3d+1Qs6H9Mk2e3E2avMWC3yMgYxf6+okbdWsWjcdpKCaIxWzX:VM9ntZ3s1QJdnU2SQdf64ZZ8CaIxWec |
MALICIOUS
Connects to CnC server
- c.exe (PID: 3120)
GandCrab keys found
- c.exe (PID: 3120)
Actions looks like stealing of personal data
- c.exe (PID: 3120)
Writes file to Word startup folder
- c.exe (PID: 3120)
Renames files like Ransomware
- c.exe (PID: 3120)
Deletes shadow copies
- c.exe (PID: 3120)
Dropped file may contain instructions of ransomware
- c.exe (PID: 3120)
SUSPICIOUS
Reads the cookies of Mozilla Firefox
- c.exe (PID: 3120)
Creates files like Ransomware instruction
- c.exe (PID: 3120)
Creates files in the user directory
- c.exe (PID: 3120)
INFO
Dropped object may contain TOR URL's
- c.exe (PID: 3120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:10:26 10:47:08+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 80896 |
| InitializedDataSize: | 68096 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6229 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Oct-2018 08:47:08 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 26-Oct-2018 08:47:08 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00013BE4 | 0x00013C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58693 |
.rdata | 0x00015000 | 0x00006B46 | 0x00006C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.59755 |
.data | 0x0001C000 | 0x000087F4 | 0x00006A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.15553 |
.rsrc | 0x00025000 | 0x000001E0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.7123 |
.reloc | 0x00026000 | 0x000013A8 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64868 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
MPR.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
WININET.dll |
ole32.dll |
Total processes
34
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3120 | "C:\Users\admin\AppData\Local\Temp\c.exe" | C:\Users\admin\AppData\Local\Temp\c.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3404 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | — | c.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
119
Read events
88
Write events
31
Delete events
0
Modification events
| (PID) Process: | (3120) c.exe | Key: | HKEY_CURRENT_USER\Software\ex_data\data |
| Operation: | write | Name: | ext |
Value: 2E0078006300690078007400790076007000750072000000 | |||
| (PID) Process: | (3120) c.exe | Key: | HKEY_CURRENT_USER\Software\keys_data\data |
| Operation: | write | Name: | public |
Value: 0602000000A40000525341310008000001000100717C86D28F1676868E620CBE6D0A3FC55E82F0C5C56C173BF0EE5BAEDD08EE716544CA46AA269F77AB08C776A8F7C4FE7D053A07CE6BA5AB0C4E224963D6232CD4BE16C5965CAB2B408AC3F41385F37E46D9188C251564FD75FE2CAE348E0827D408DE8A4147DF1A1104501DD60C5919D32EE252EB90887A480A9536655693E7398229708529B19788EF99A63879DF005EA9746A382AF03872C6E0F6D4328B9F2AD21D91CB97A37E6524E093557F750651C494E1A816EB355C0836361A2A3B7968B68AD78FA71185364B8C55E22850709067C6EF7E5F08217C3BD6080885BB3F722B514E086167B91B127B7367167F1EA7921D28DC1940CA182729D3FAB54692 | |||
| (PID) Process: | (3120) c.exe | Key: | HKEY_CURRENT_USER\Software\keys_data\data |
| Operation: | write | Name: | private |
Value: 940400001B6E9E036CD87D63FDA73B16CFDEECB68FF1989D20D84C7635B40FD9EE9CF47FCDD957242C3FAC1A63FC278B0698BCB418996A0D6F6FA934090AA699A563AD9F1AA25A9F6BAB3B375CB9502D7F25B40B38733945EC267D09F2DF9AC669D85999DAEA702AD3E08D925F4B6370BAEB9BFB9F17F7B5E7DC1B618150602CE9F287849BA3B6046400AA238DC65ED772337DACF189AE3E063A3E5370EE9FD0972F0364564CA1B1C2B1698653FF18A52AD848FE25E25F7563D8A075A67BDC3440311FC8E091B1FDB276F6A2D04ED2B51650086FD04138B0B3BA9EDD0DA4DF1F0BE715D709CE629BAFCCC815B9889A286DA32058A1DD750412FC325792C0B70F50C6FB147778B91E5726EFF50542EF2FCD9D3EFEDB7F96DE7FF6AA207A4BDE2D1C8C1CE457E452E0F6B668E4437FE62E5E23A7102316D460797DEC4CB13FD7C8DF719AAC96E931751CBAC8B7F6256AA90E8B56D43BBAB8819C0CB794D4006ABB9A16586B31059937C1456B06A57398A5B9E3856A1391E1CC1E369D35BA51A537A25E6A36735307CA485D1D5E2BAE0D3539BCCE274CF2797E11E21CA3357E449E65FBB01460F3D1FC0DF35383881E08E048883287FCA544D3128BC2D53D21B321CD7F162C79E349433A4AE9B3667ACF3099ED790B948425EEFF0EAB330EDE2D3CD3115BB9EDCC6B2FE85771D4A2F65DE58A8A1D1D6A144B4034473275276CED06F9B5AB9E2F12D6B269B4DA35111980F853C1E36E67C717316745CE0F7E9E3BFEE4AC1FC28AB476575D9C8CCC2B0B1690129F293B374A76E50B21686169C75FEBAF04DB580BA2F8BDBF3B342D954D9B2FFC8E8348E235362A07D7CA73D69FBE6A5ED62B686241372B8677203097E12CA3253AC1D348FCF6735FB9779FBE67F0A00E63FACA9A953AB247D7E0379DE97720BE7FED48AD286769074D23E9446096C09F5A790ECFC9A9C967D8F006C3790EBC92A47B8F00A6D04529939CAEDED7A3DBD3169DC7341C6B7F89DA2868F20BC417F8772E7FFE951922FA58A6D2FE3BD1430EF29B5DFA6CF3285D999CCC4E28AA8816CC7685DA8B68D633EA99D88D86B5B167CABAC9D65DE79DF1153E5F0AA7C058533733B6243F249DDE45E6F6FFB98863EC7F1917F9689F7976FE72AD73D2B1B3DC9CFAD9FDDD668B0305D1BE42778F3DDFD248096D55338CF92554CE44E9D29103FCB31182E171911E454F44130165A01423F7FB165C5D687107104AF52C467F54E1D82A33C112EF0883C2F6BA91E145D085DA7F307625347911E7724E80E8B124B6A420D1F47DCE8C0DE2F5C2B44B2F0300A18C28882211620209D91B35AAA821CD09F4F460B5B19F20CEC1C0491EE8ACFED41E119D4A5EFEA9DBF7B821ABDBAA3EE374A3C301FB68E529AE58C44439C2CB56E56F3AF3C7AE029FC69365ECD97CEDD0ED596C4222AD45EBDCE6318FEE165E5F8637A6B88641181303DAB9E385DF0703D532871013196B00EC0A72649F4394BD9D4004547324AC55BAD014422CA9A125072443273C5D48008C5FD3B182A3191C8A611F448B7908F4AF01148532ABEEA0AD71778E10C190BFD19B2309C189D722302AC24F990AF8D5CA29B993910BF18699C455B0FA8FF9C4B5D954BC861ED1863692A72CBD0EFC4569D71FA149AB0BB8D5C04DC324AB22658BD3D037C0E9077EB738001383BA525C4FEE7066DAACAD30E4F081CDD2C8415678C516D9A6F98C63A79C67A911EE41526BD6C7BCFAF9AB045969C3183F142A729C76D0837B5995C255817998A580E9A63EB9BF4015529D2678F84C9CD4954B02CEA119A6A644752EA5BB0BEDED8037299C6510AC60E1749E4254C413B74C8D3231244337944F1279A246315416DEAB3F94CB8A05CD55EC423D4772CF4E0024991F38F18C3295AD145666940C2723B6E610DB0EF58263AA14F45549378758494D74BFE5FAF5EF670BDD408AA86373691DA79BE0FD08FF00C4D38A44EA0692E65E82EDDF372342457B8C86C3F31E7A7F10928EC780B91A98F18666FB93BFDF962B4F703A2CCA3D642B7DCADB9DF26D9947CE236D21A02B4274F94DFEC69043A1A000AFCE06430290FE8F359B3172874FEF0192C172E54FDA2AE8115365A5613CB32D70142A768147730E2F9CBECB58CB9FDD22C2EEA4572CBB4FEE36F55B88B4BAC918EEF9C674F49C289884A635C62855D83530250E905920FED596F61FB8F470EDE73FC360A035C5680EC9D8FDA295FDE4088243B3A434076471EAC297DED2F51F6C85EB2901CE350404B1C592692BDE627E5638D5045F16F871C3D76E958E4FA4FF1D3FD4ACEB876D53265676C13EBAAF89B2A389B540C6C67F2EFF03AADE4A6D5A3DFBF930D5F10739949743118AA7D56CFE176B46921BA8F287E520 | |||
| (PID) Process: | (3120) c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3120) c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3120) c.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\c_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3120) c.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\c_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3120) c.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\c_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3120) c.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\c_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3120) c.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\c_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
0
Suspicious files
275
Text files
204
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3120 | c.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | — | |
MD5:— | SHA256:— | |||
| 3120 | c.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobData | — | |
MD5:— | SHA256:— | |||
| 3120 | c.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobSettings | — | |
MD5:— | SHA256:— | |||
| 3120 | c.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\addressbook.acrodata | — | |
MD5:— | SHA256:— | |||
| 3120 | c.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\0FDED5CEB68C302B1CDB2BDDD9D0000E76539CB0.crl | — | |
MD5:— | SHA256:— | |||
| 3120 | c.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\CE338828149963DCEA4CD26BB86F0363B4CA0BA5.crl | — | |
MD5:— | SHA256:— | |||
| 3120 | c.exe | C:\Users\admin\AppData\XCIXTYVPUR-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 3120 | c.exe | C:\Users\admin\XCIXTYVPUR-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 3120 | c.exe | C:\Users\admin\.oracle_jre_usage\XCIXTYVPUR-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 3120 | c.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp.xcixtyvpur | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
5
DNS requests
3
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3120 | c.exe | GET | — | 217.26.53.161:80 | http://www.haargenau.biz/ | CH | — | — | malicious |
3120 | c.exe | GET | — | 78.46.77.98:80 | http://www.2mmotorsport.biz/ | DE | — | — | suspicious |
3120 | c.exe | GET | — | 74.220.215.73:80 | http://www.bizziniinfissi.com/ | US | — | — | malicious |
3120 | c.exe | POST | — | 217.26.53.161:80 | http://www.haargenau.biz/data/imgs/sethsoso.bmp | CH | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3120 | c.exe | 74.220.215.73:80 | www.bizziniinfissi.com | Unified Layer | US | malicious |
3120 | c.exe | 78.46.77.98:443 | www.2mmotorsport.biz | Hetzner Online GmbH | DE | suspicious |
3120 | c.exe | 78.46.77.98:80 | www.2mmotorsport.biz | Hetzner Online GmbH | DE | suspicious |
3120 | c.exe | 217.26.53.161:80 | www.haargenau.biz | Hostpoint AG | CH | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.2mmotorsport.biz |
| unknown |
www.haargenau.biz |
| unknown |
www.bizziniinfissi.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3120 | c.exe | A Network Trojan was detected | ET TROJAN [eSentire] Win32/GandCrab v4/5 Ransomware CnC Activity |
3120 | c.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
3120 | c.exe | A Network Trojan was detected | MALWARE [PTsecurity] GandCrab Ransomware HTTP |