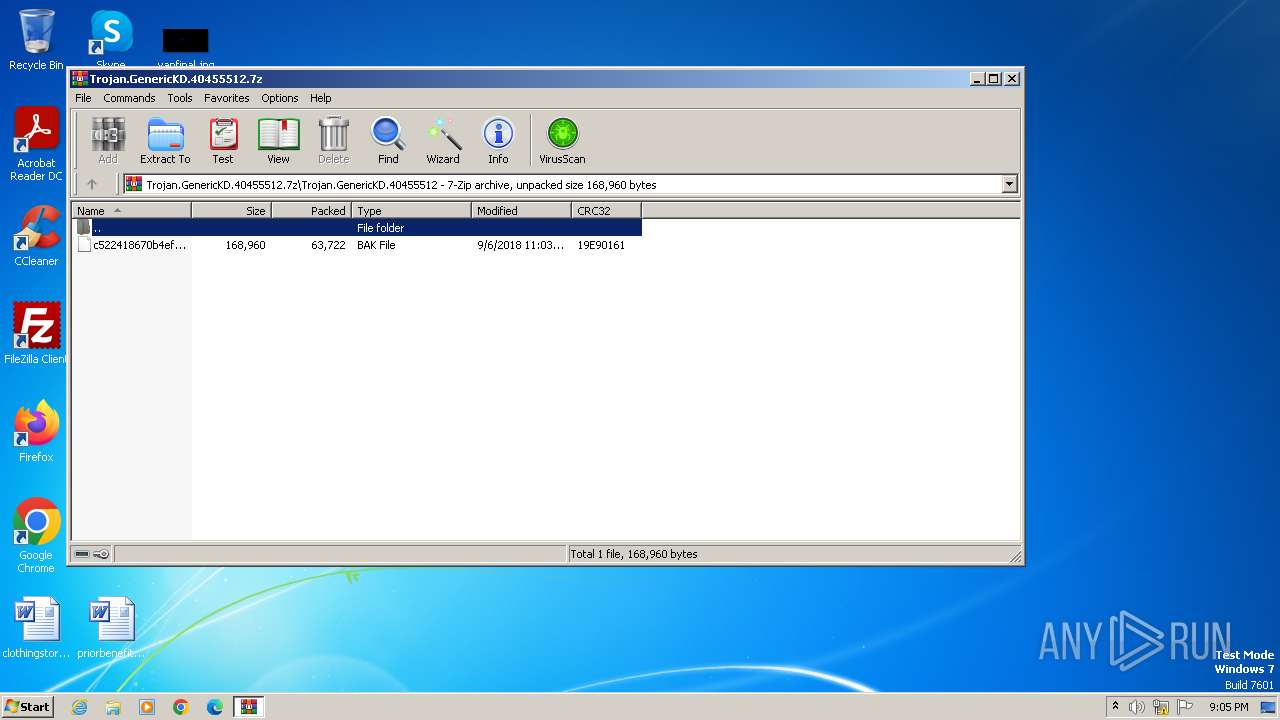
| File name: | Trojan.GenericKD.40455512.7z |
| Full analysis: | https://app.any.run/tasks/e6a0d429-e7eb-4933-b18e-7c3435fdd6d0 |
| Verdict: | Malicious activity |
| Analysis date: | November 20, 2023, 21:05:45 |
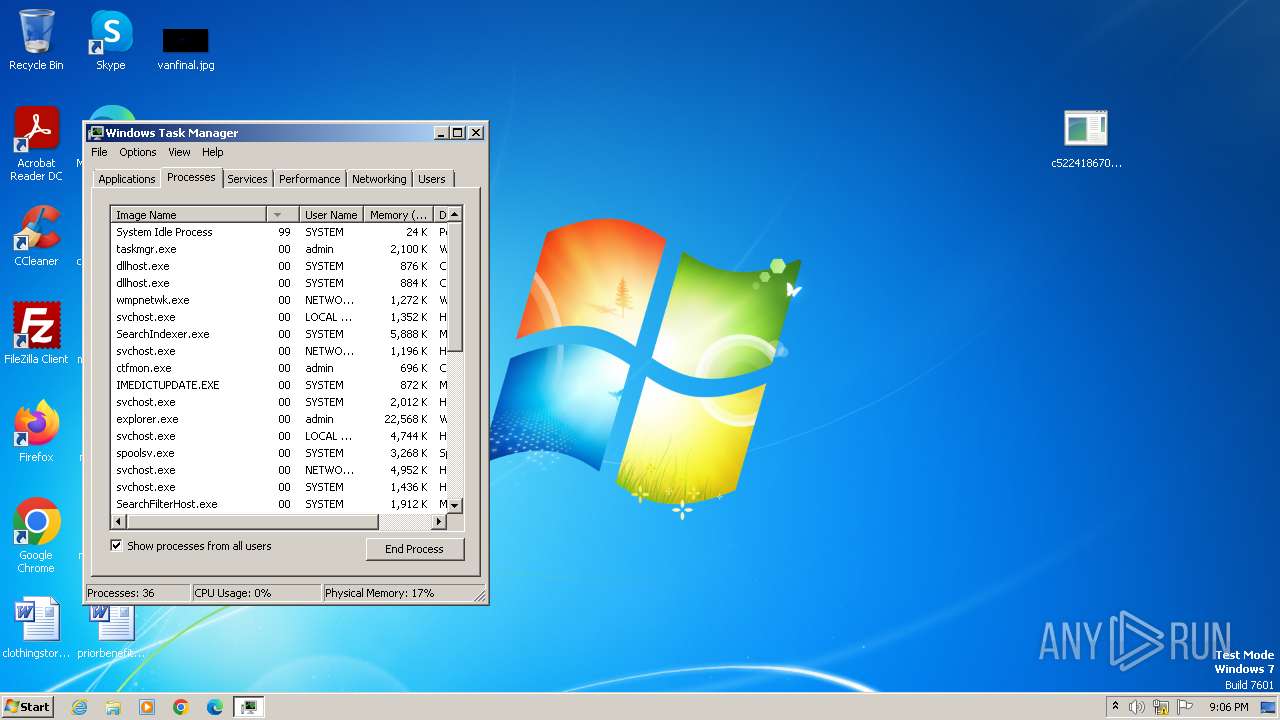
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 24A7127A6773AAA401CF9D5807502D10 |
| SHA1: | F8BF82B8E5129D28B7485CFDA9759A5B7C360B22 |
| SHA256: | 4B5E51DC48E623D96277709AEF5C209E770ECAF0910C2DE8958FAF9E4CAE0DF7 |
| SSDEEP: | 1536:cl5JpGYi/LzHXLT3U6cx9vcRasInHaSDa58M9E1ZGu:cl5JpI/nbA6cxy6atEzGu |
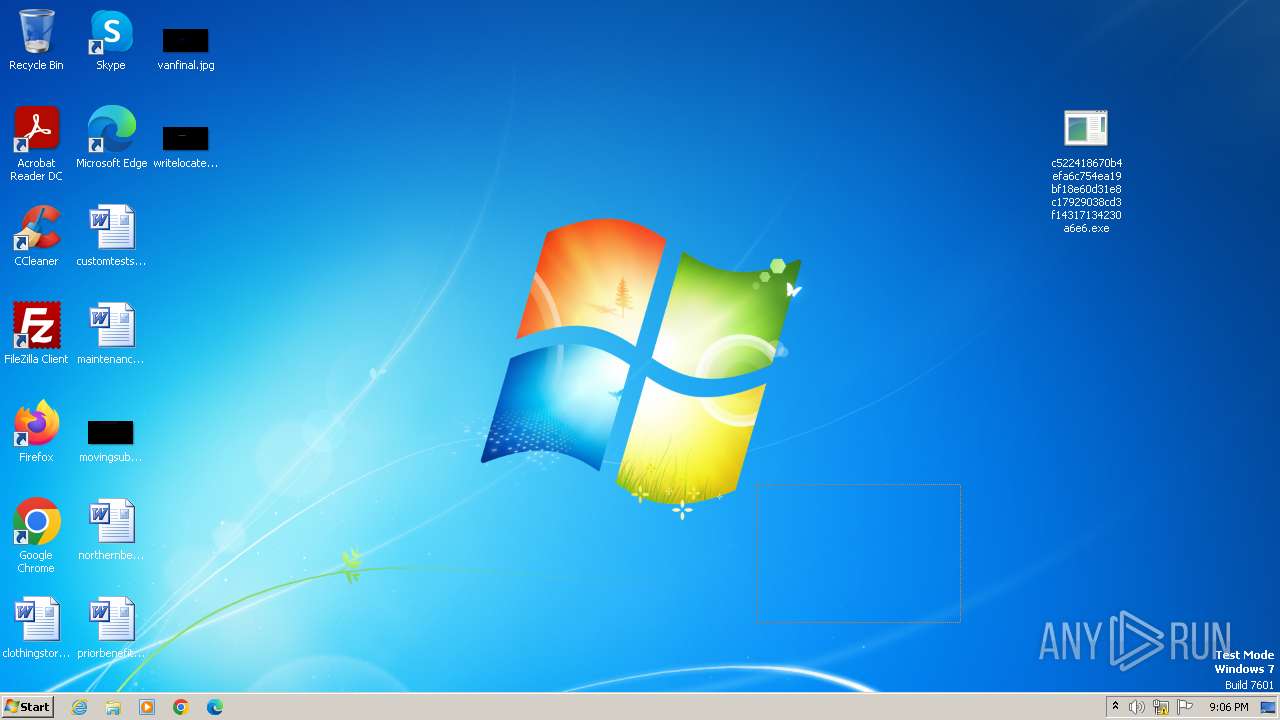
MALICIOUS
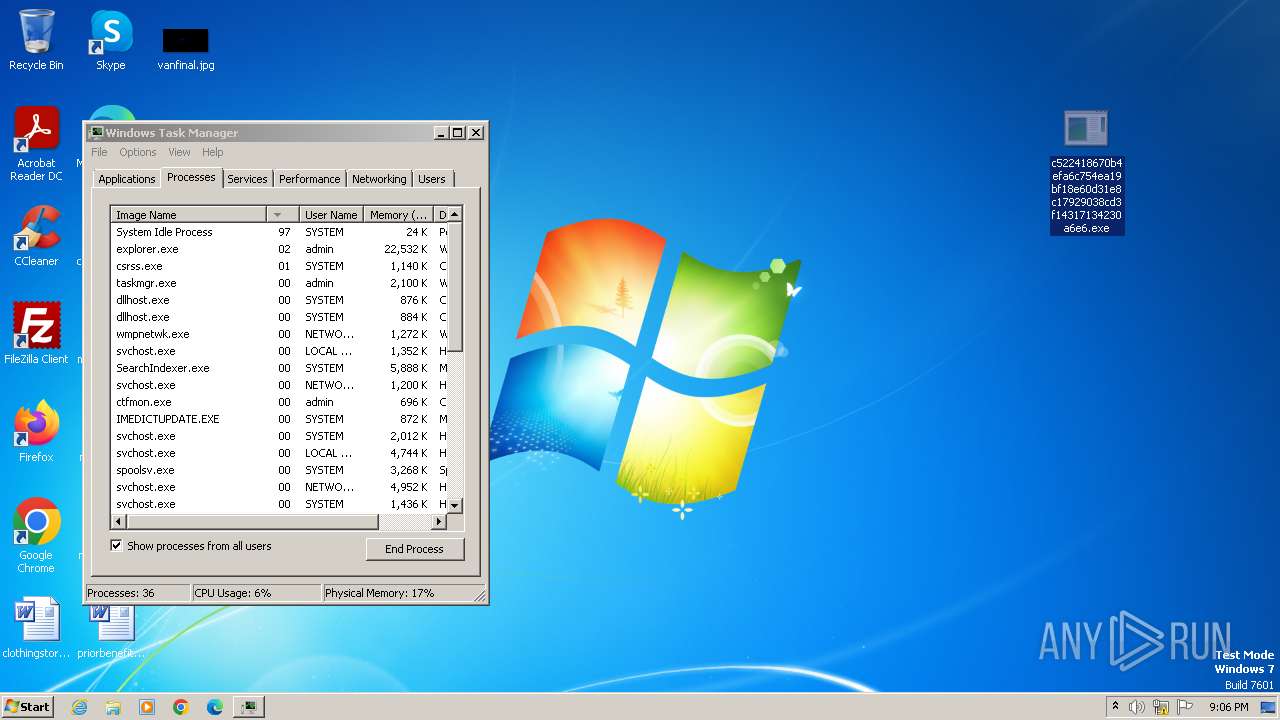
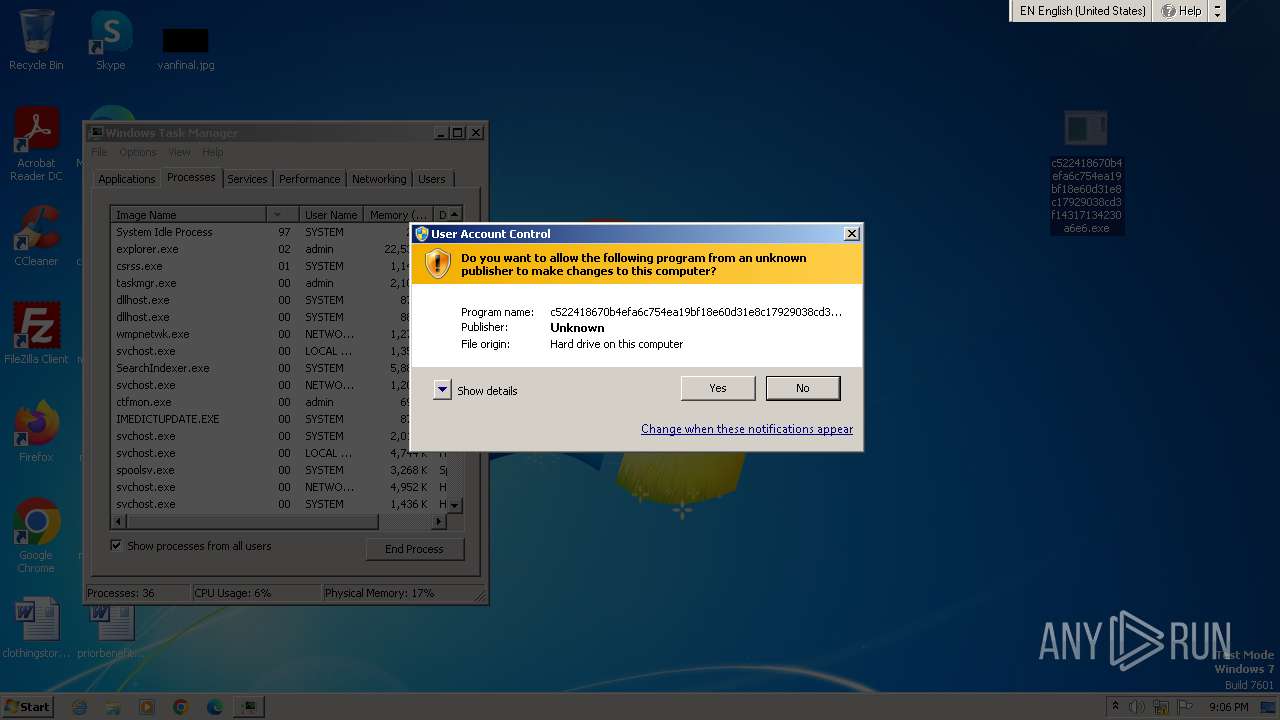
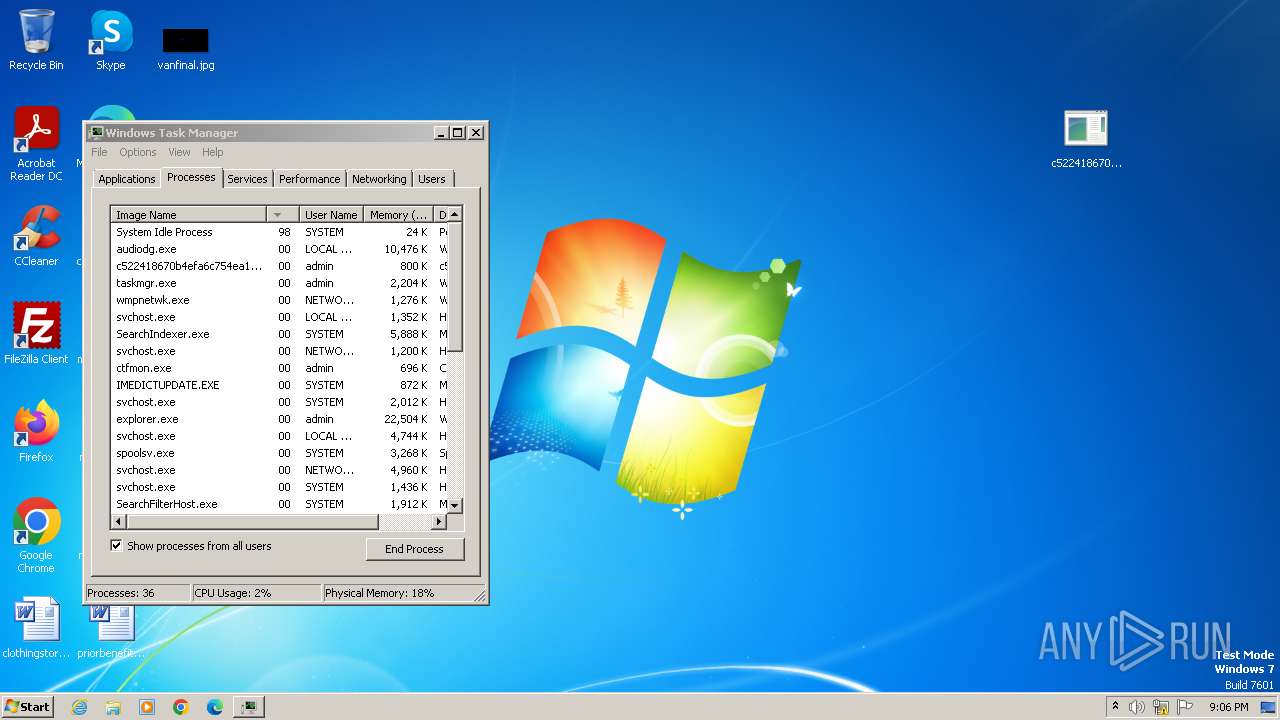
Drops the executable file immediately after the start
- c522418670b4efa6c754ea19bf18e60d31e8c17929038cd3f14317134230a6e6.exe (PID: 3760)
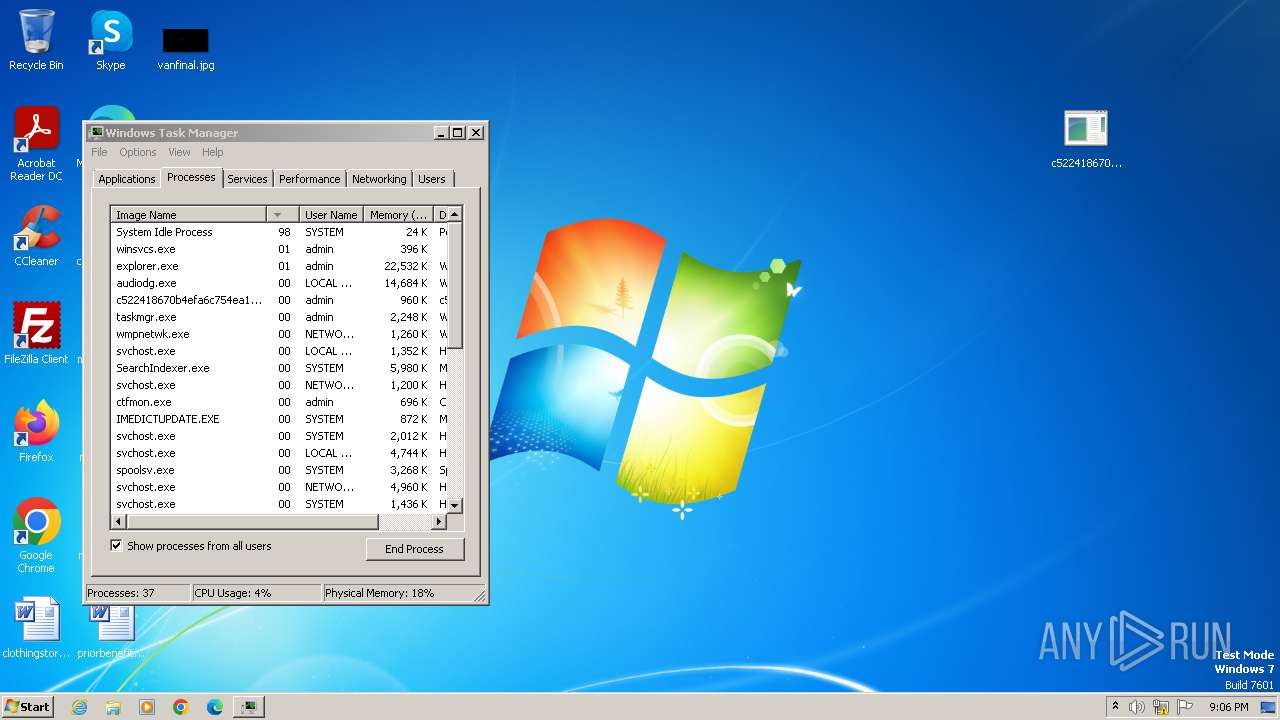
- winsvcs.exe (PID: 3020)
Create files in the Startup directory
- c522418670b4efa6c754ea19bf18e60d31e8c17929038cd3f14317134230a6e6.exe (PID: 3760)
SUSPICIOUS
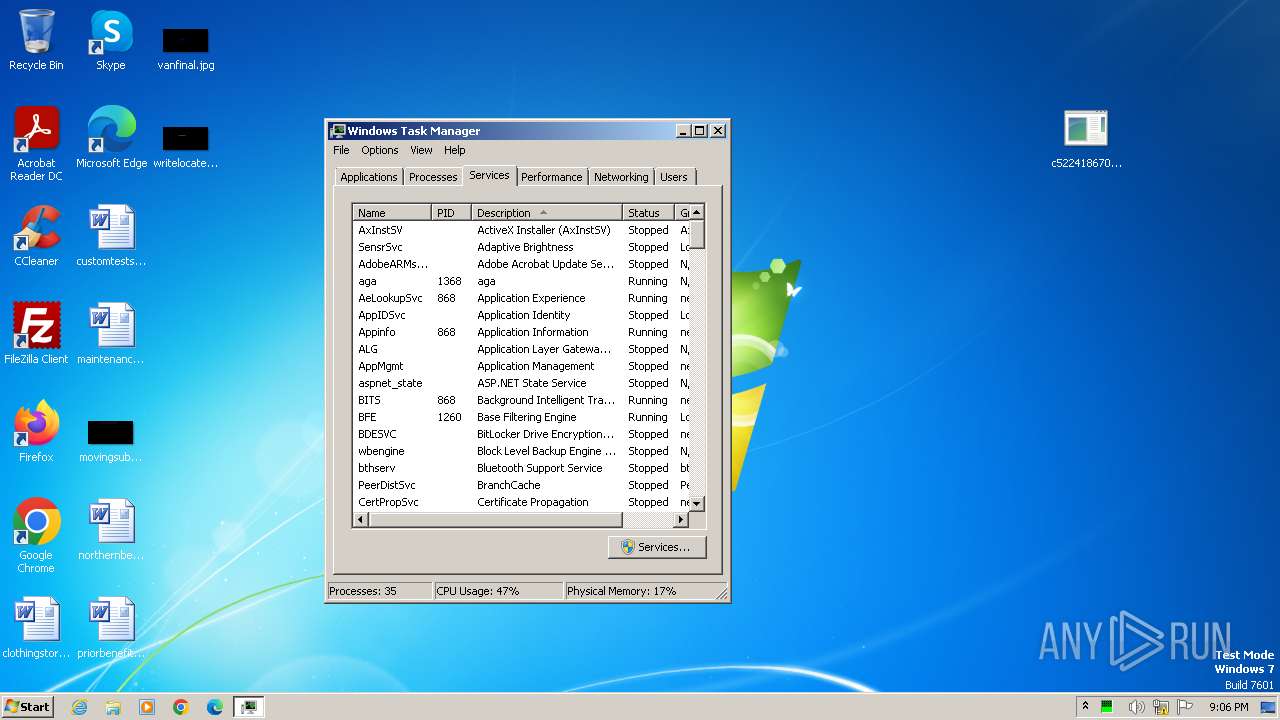
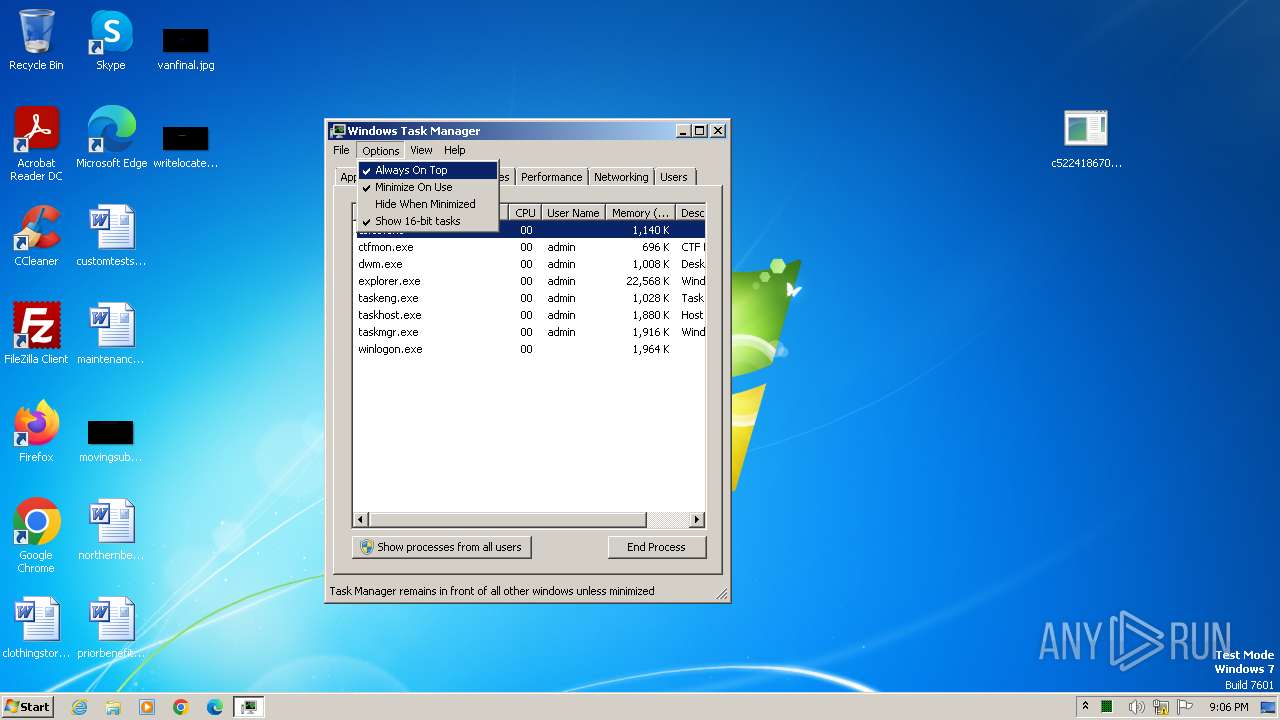
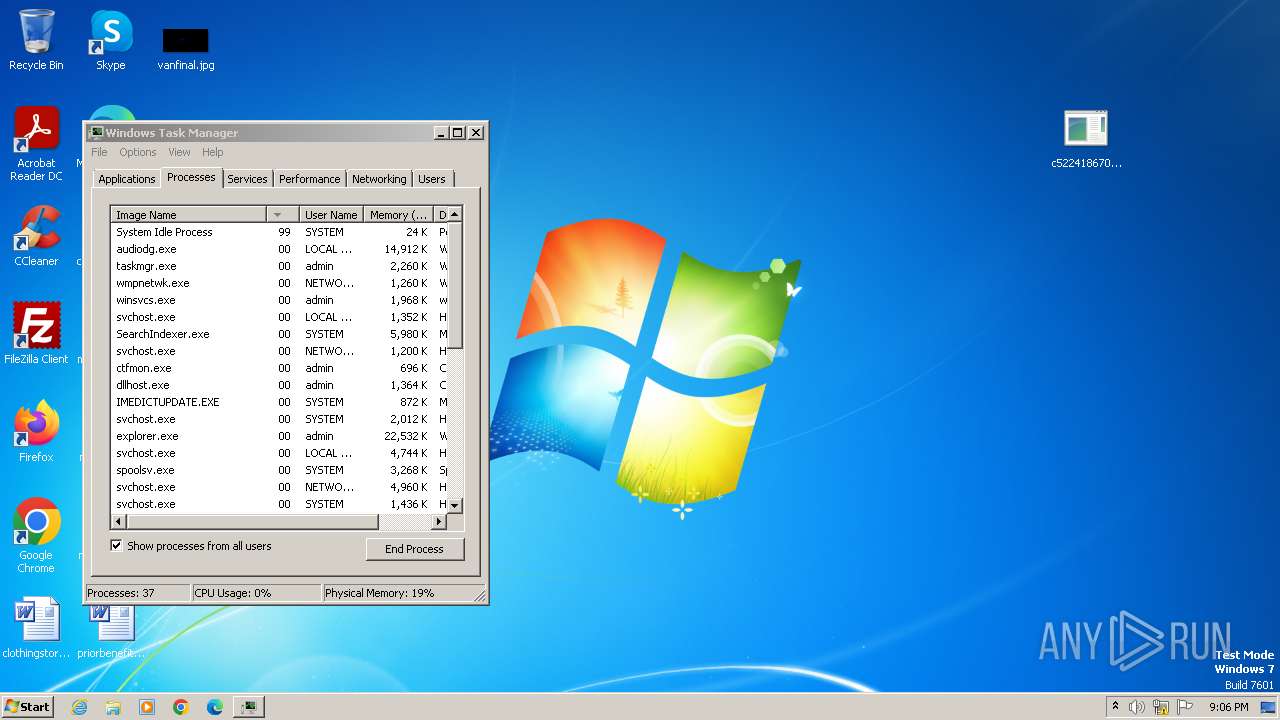
Reads the Internet Settings
- taskmgr.exe (PID: 3228)
- winsvcs.exe (PID: 3020)
Application launched itself
- taskmgr.exe (PID: 3228)
Starts itself from another location
- c522418670b4efa6c754ea19bf18e60d31e8c17929038cd3f14317134230a6e6.exe (PID: 3760)
INFO
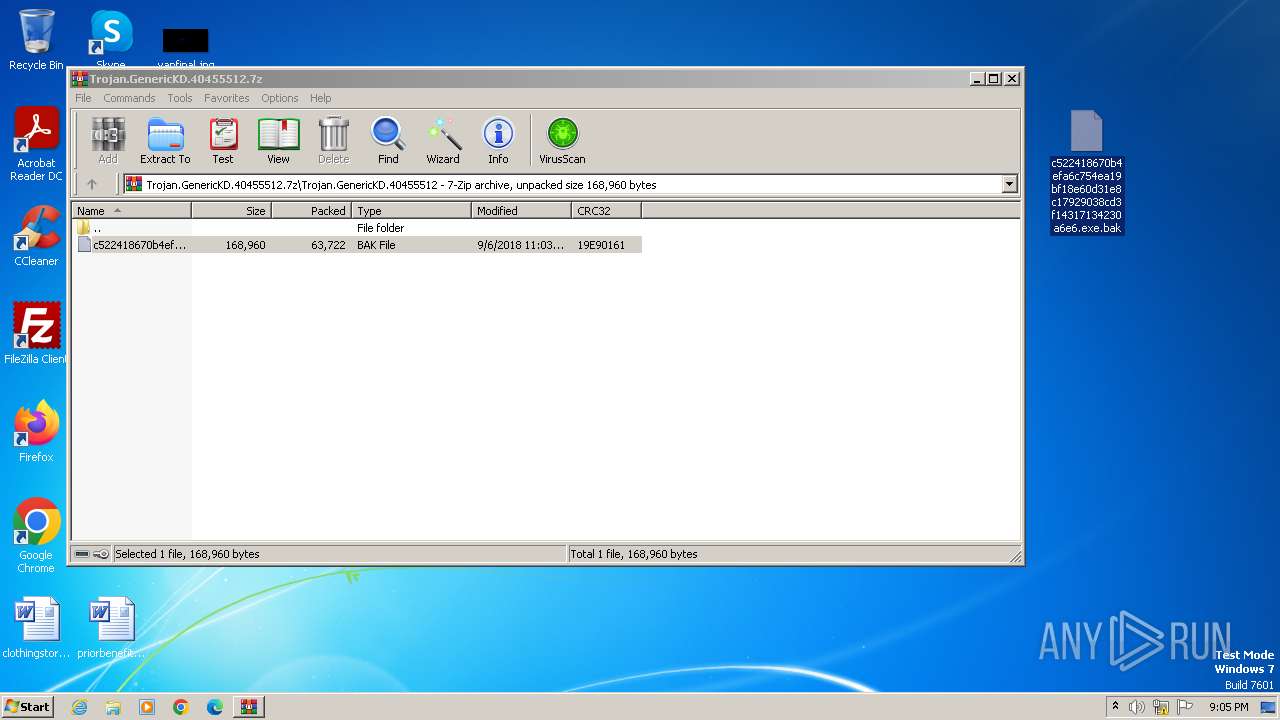
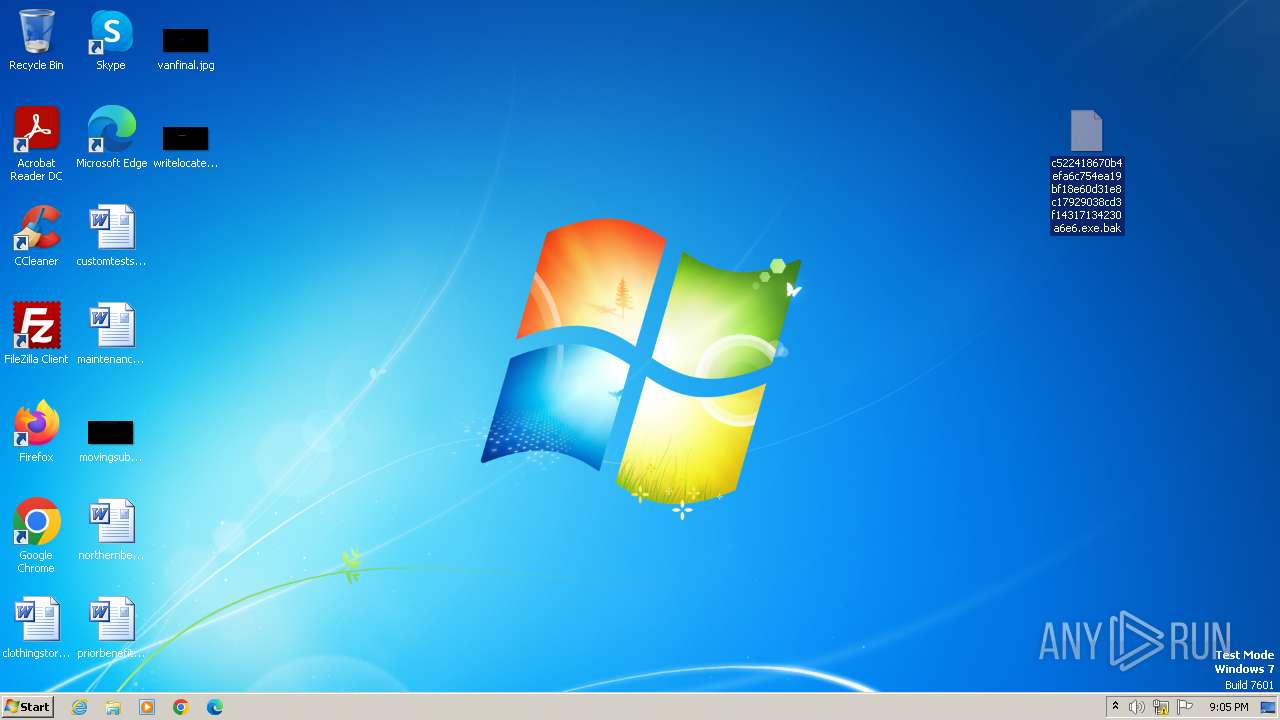
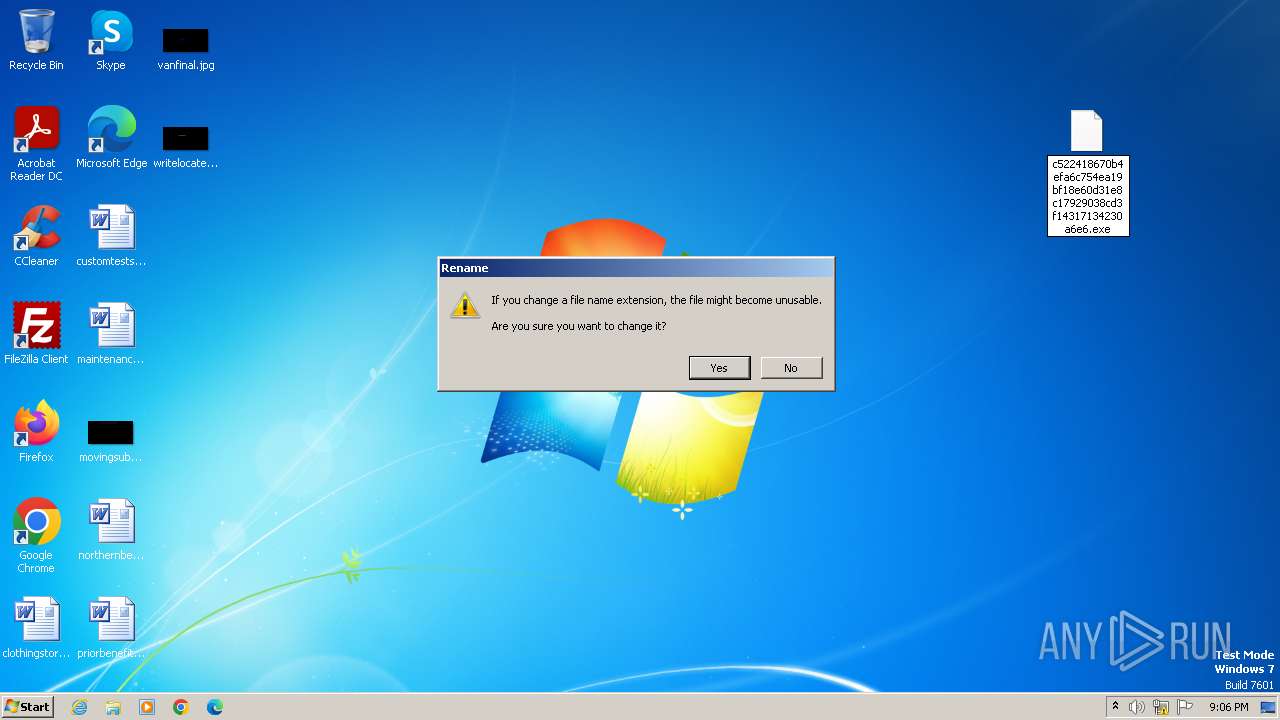
Manual execution by a user
- c522418670b4efa6c754ea19bf18e60d31e8c17929038cd3f14317134230a6e6.exe (PID: 3760)
- taskmgr.exe (PID: 3228)
- wmpnscfg.exe (PID: 1344)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3240)
Checks supported languages
- c522418670b4efa6c754ea19bf18e60d31e8c17929038cd3f14317134230a6e6.exe (PID: 3760)
- winsvcs.exe (PID: 3020)
- wmpnscfg.exe (PID: 1344)
Creates files in the program directory
- c522418670b4efa6c754ea19bf18e60d31e8c17929038cd3f14317134230a6e6.exe (PID: 3760)
Creates files or folders in the user directory
- winsvcs.exe (PID: 3020)
Checks proxy server information
- winsvcs.exe (PID: 3020)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 1344)
- winsvcs.exe (PID: 3020)
Reads the computer name
- wmpnscfg.exe (PID: 1344)
- winsvcs.exe (PID: 3020)
Create files in a temporary directory
- winsvcs.exe (PID: 3020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
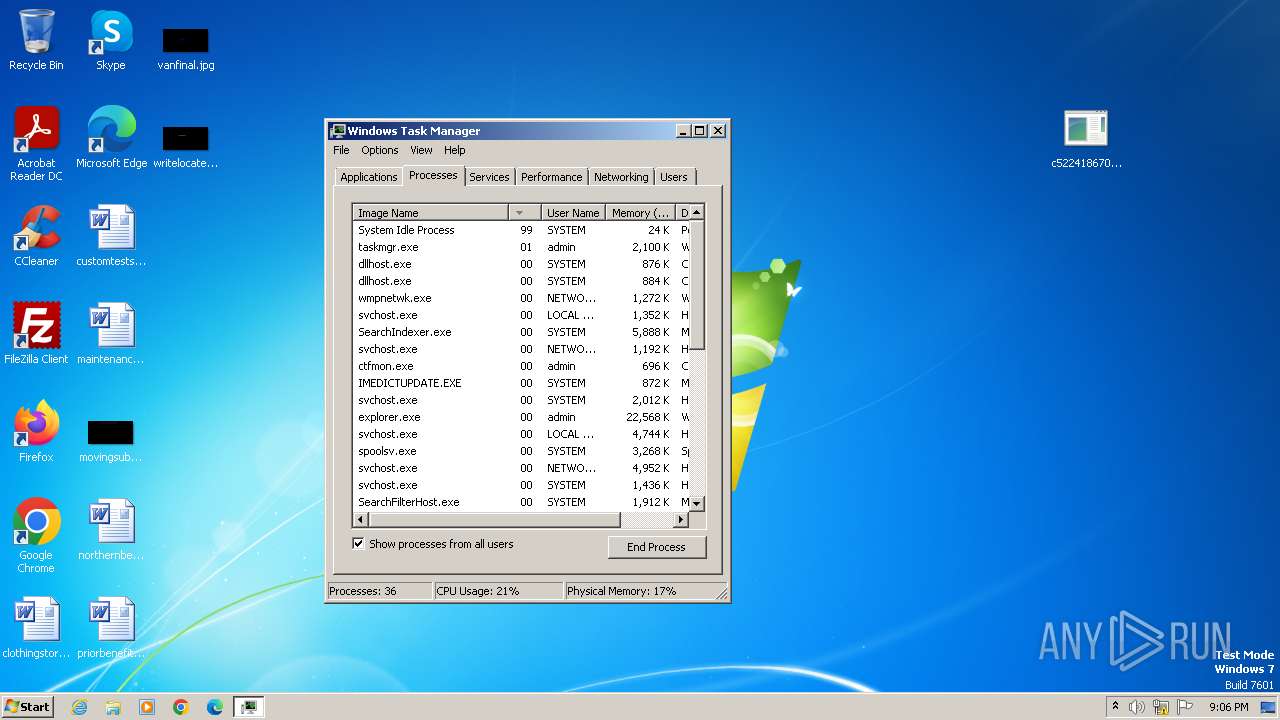
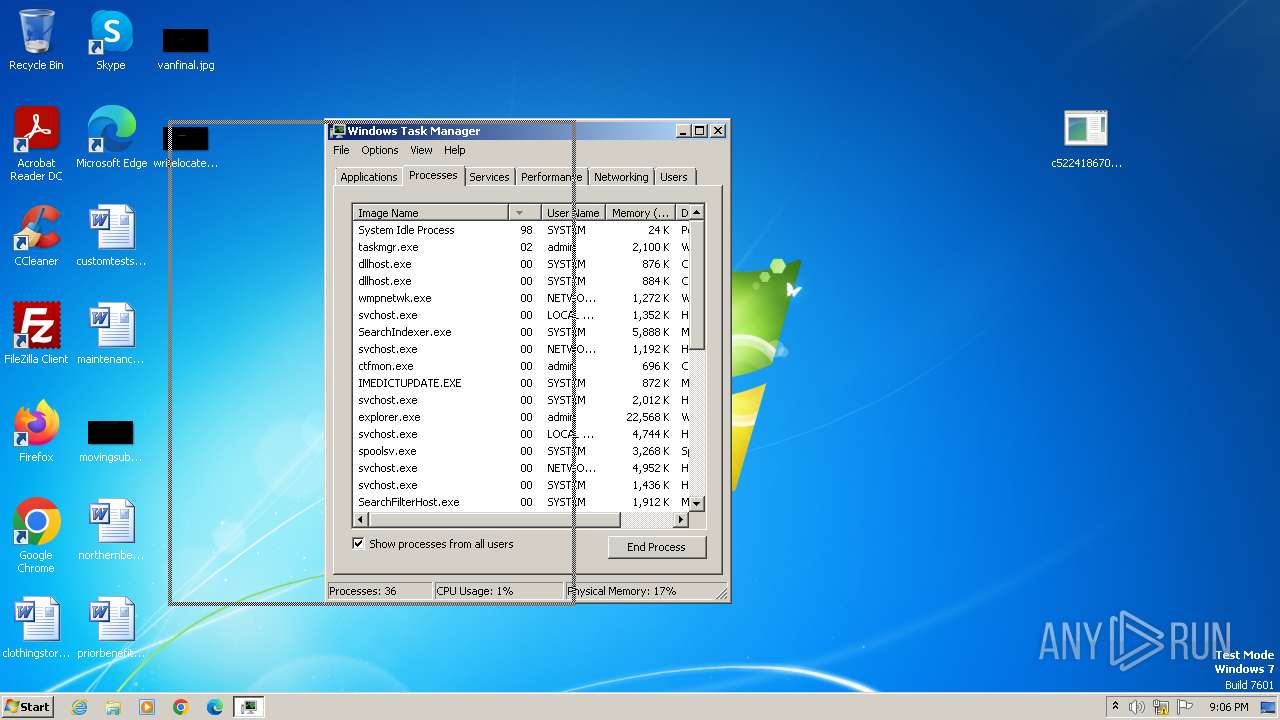
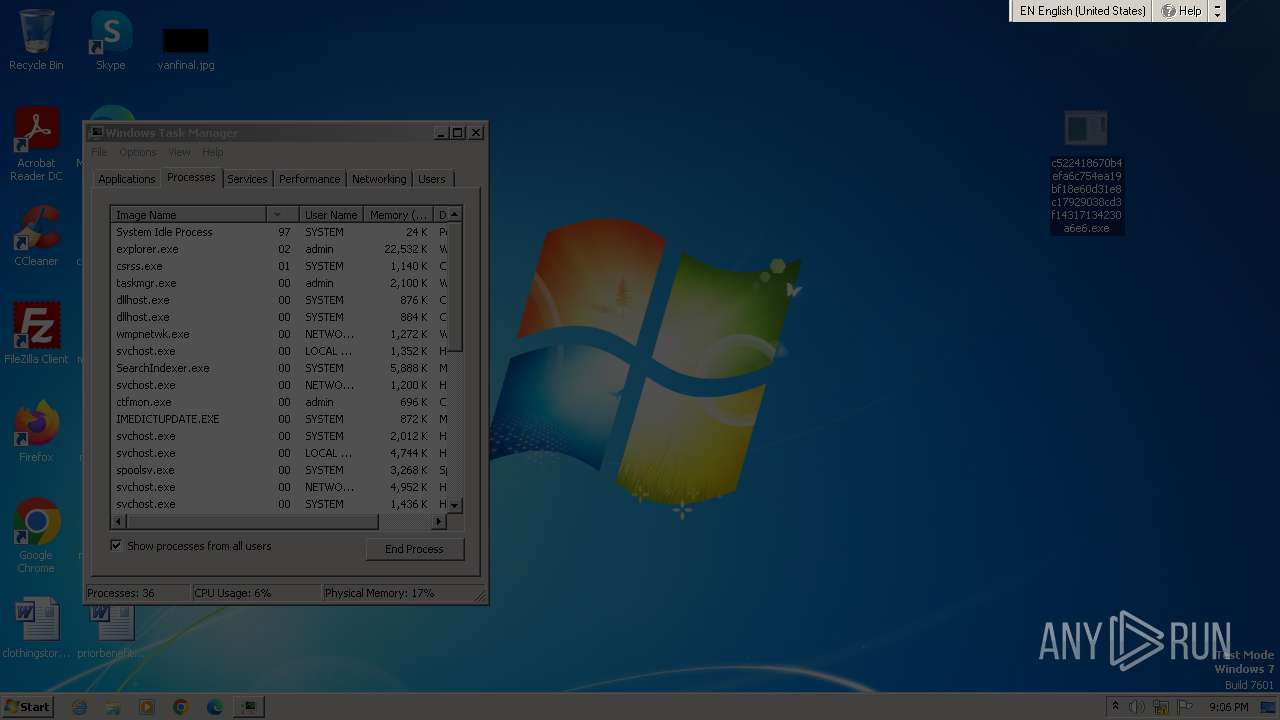
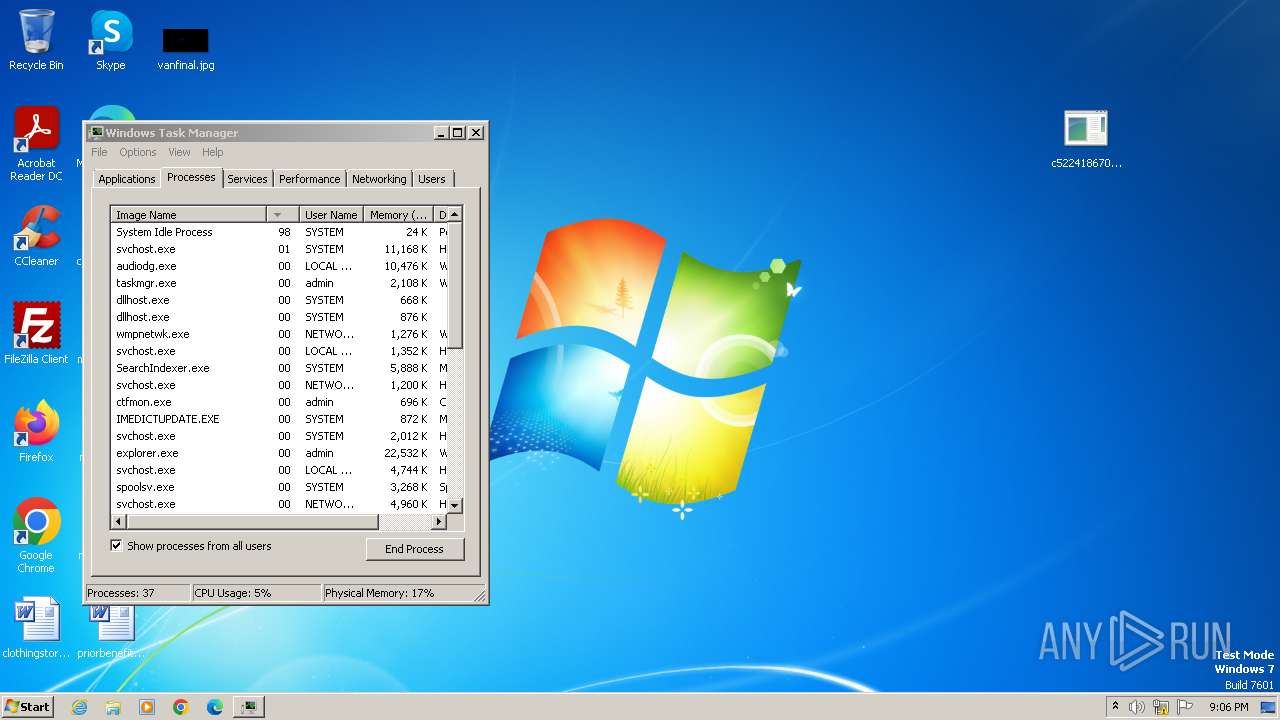
Total processes
50
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1344 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3020 | C:\Windows\T-95068078470687070\winsvcs.exe | C:\Windows\T-95068078470687070\winsvcs.exe | c522418670b4efa6c754ea19bf18e60d31e8c17929038cd3f14317134230a6e6.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
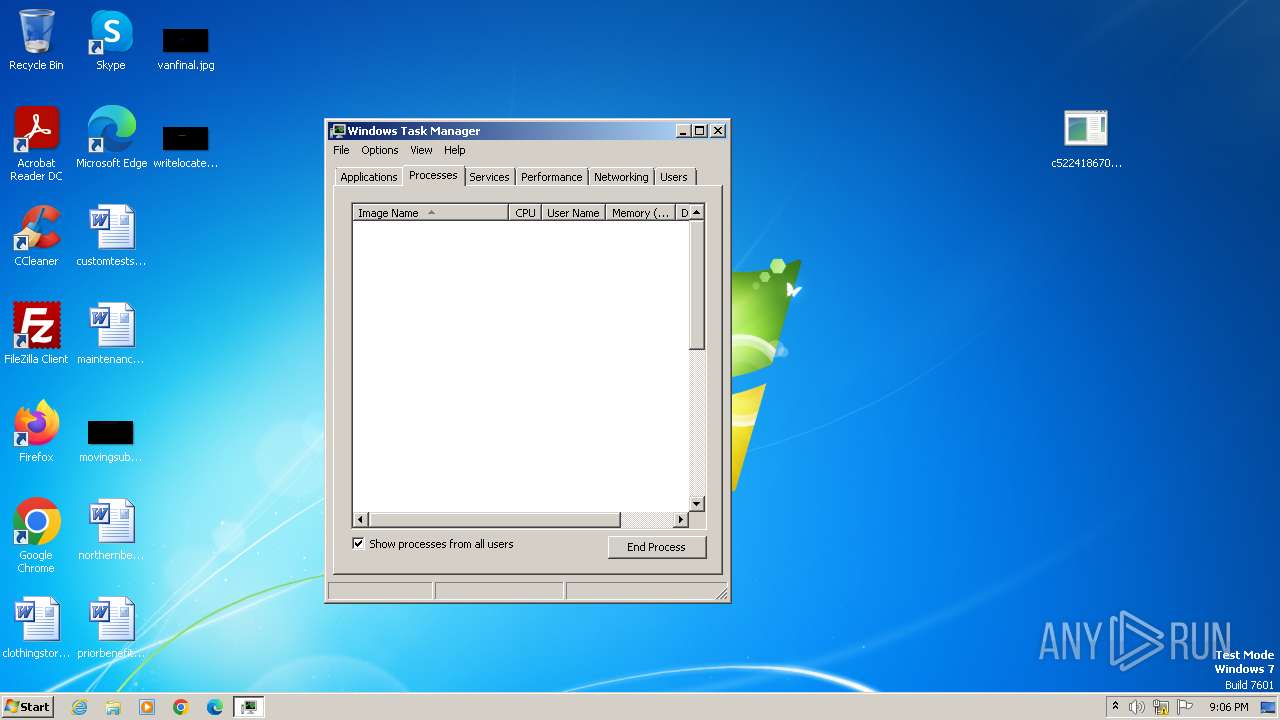
| 3228 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\System32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3240 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Trojan.GenericKD.40455512.7z" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3756 | "C:\Windows\system32\taskmgr.exe" /1 | C:\Windows\System32\taskmgr.exe | taskmgr.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3760 | "C:\Users\admin\Desktop\c522418670b4efa6c754ea19bf18e60d31e8c17929038cd3f14317134230a6e6.exe" | C:\Users\admin\Desktop\c522418670b4efa6c754ea19bf18e60d31e8c17929038cd3f14317134230a6e6.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
2 173
Read events
1 972
Write events
198
Delete events
3
Modification events
| (PID) Process: | (3240) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (3240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
6
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3020 | winsvcs.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Y71PY7ST.txt | text | |
MD5:8D11E47311BCD5B71D5BA39DEAAB1A51 | SHA256:D7823D6AD43A3D1D8E190192CA9F289CDD29D64BD26709D26274C96CD543615A | |||
| 3760 | c522418670b4efa6c754ea19bf18e60d31e8c17929038cd3f14317134230a6e6.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Startup\winsvcs.exe | executable | |
MD5:2337089F5225107923BD963581F8AB1E | SHA256:C522418670B4EFA6C754EA19BF18E60D31E8C17929038CD3F14317134230A6E6 | |||
| 3760 | c522418670b4efa6c754ea19bf18e60d31e8c17929038cd3f14317134230a6e6.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\winsvcs.exe | executable | |
MD5:2337089F5225107923BD963581F8AB1E | SHA256:C522418670B4EFA6C754EA19BF18E60D31E8C17929038CD3F14317134230A6E6 | |||
| 3240 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3240.33932\Trojan.GenericKD.40455512\c522418670b4efa6c754ea19bf18e60d31e8c17929038cd3f14317134230a6e6.exe.bak | executable | |
MD5:2337089F5225107923BD963581F8AB1E | SHA256:C522418670B4EFA6C754EA19BF18E60D31E8C17929038CD3F14317134230A6E6 | |||
| 3760 | c522418670b4efa6c754ea19bf18e60d31e8c17929038cd3f14317134230a6e6.exe | C:\ProgramData\Microsoft\Windows\Start Menu\winsvcs.exe | executable | |
MD5:2337089F5225107923BD963581F8AB1E | SHA256:C522418670B4EFA6C754EA19BF18E60D31E8C17929038CD3F14317134230A6E6 | |||
| 3760 | c522418670b4efa6c754ea19bf18e60d31e8c17929038cd3f14317134230a6e6.exe | C:\Windows\T-95068078470687070\winsvcs.exe | executable | |
MD5:2337089F5225107923BD963581F8AB1E | SHA256:C522418670B4EFA6C754EA19BF18E60D31E8C17929038CD3F14317134230A6E6 | |||
| 3020 | winsvcs.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\0Y81AWVH.txt | text | |
MD5:1DD359B1432D83D47043E3704006152B | SHA256:C4ECF8A413FD259D3E0427851957555EDD386711AF3857CA0F23B7E380A08915 | |||
| 3020 | winsvcs.exe | C:\Users\admin\AppData\Local\Temp\Windows Archive Manager.exe | executable | |
MD5:2337089F5225107923BD963581F8AB1E | SHA256:C522418670B4EFA6C754EA19BF18E60D31E8C17929038CD3F14317134230A6E6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
9
DNS requests
48
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3020 | winsvcs.exe | GET | 200 | 34.91.32.224:80 | http://ougohoueahgoushughoej.ru/t.php?total=1 | unknown | — | — | unknown |
3020 | winsvcs.exe | GET | 404 | 208.100.26.245:80 | http://ougohoueahgoushughoej.in/t.php?total=1 | unknown | html | 178 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3020 | winsvcs.exe | 92.63.197.48:80 | — | OOO SibirInvest | RU | unknown |
3020 | winsvcs.exe | 34.91.32.224:80 | ougohoueahgoushughoej.ru | GOOGLE-CLOUD-PLATFORM | NL | unknown |
3020 | winsvcs.exe | 208.100.26.245:80 | ougohoueahgoushughoej.in | STEADFAST | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
ougohoueahgoushughoej.ru |
| unknown |
ehouehfoueouheoueiuif.ru |
| unknown |
ieieieidiifigigididii.ru |
| unknown |
suohgorshohrsghhuodud.ru |
| unknown |
ruososososfgogoggugud.ru |
| unknown |
sorighosrhgosrhoududu.ru |
| unknown |
eoeoododoofnfnnfnfsur.ru |
| unknown |
ruurrifiiifigiaosaosd.ru |
| unknown |
auuauaugngnngduuzgjus.ru |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3020 | winsvcs.exe | A Network Trojan was detected | ET MALWARE Possible Compromised Host AnubisNetworks Sinkhole Cookie Value Snkz |
3020 | winsvcs.exe | A Network Trojan was detected | ET MALWARE Possible Compromised Host AnubisNetworks Sinkhole Cookie Value btst |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |