| File name: | Stoxxo.exe |
| Full analysis: | https://app.any.run/tasks/b56df8fc-e7ec-458f-a40d-90f7a9623076 |
| Verdict: | Malicious activity |
| Analysis date: | January 09, 2026, 19:27:21 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | EB04E87E43E3CF0B811C45CF6F2D0A44 |
| SHA1: | 199193E759E27C6E84B050987971E6251E8F3DE8 |
| SHA256: | 4B5E439ADD01077D01C60CD39ACA5019CA05E61F487FE5D730394D0FF14A6E5E |
| SSDEEP: | 98304:QNfqKk5BzIBwBAd4Ls07Ewl4Utpr8z7fL/pVEvvhXSukv5tJF9/GLEzbura02uDa:EubOsaKsYRnmK9h+s1EqVaC |
MALICIOUS
XORed URL has been found (YARA)
- Stoxxo.exe (PID: 7744)
SUSPICIOUS
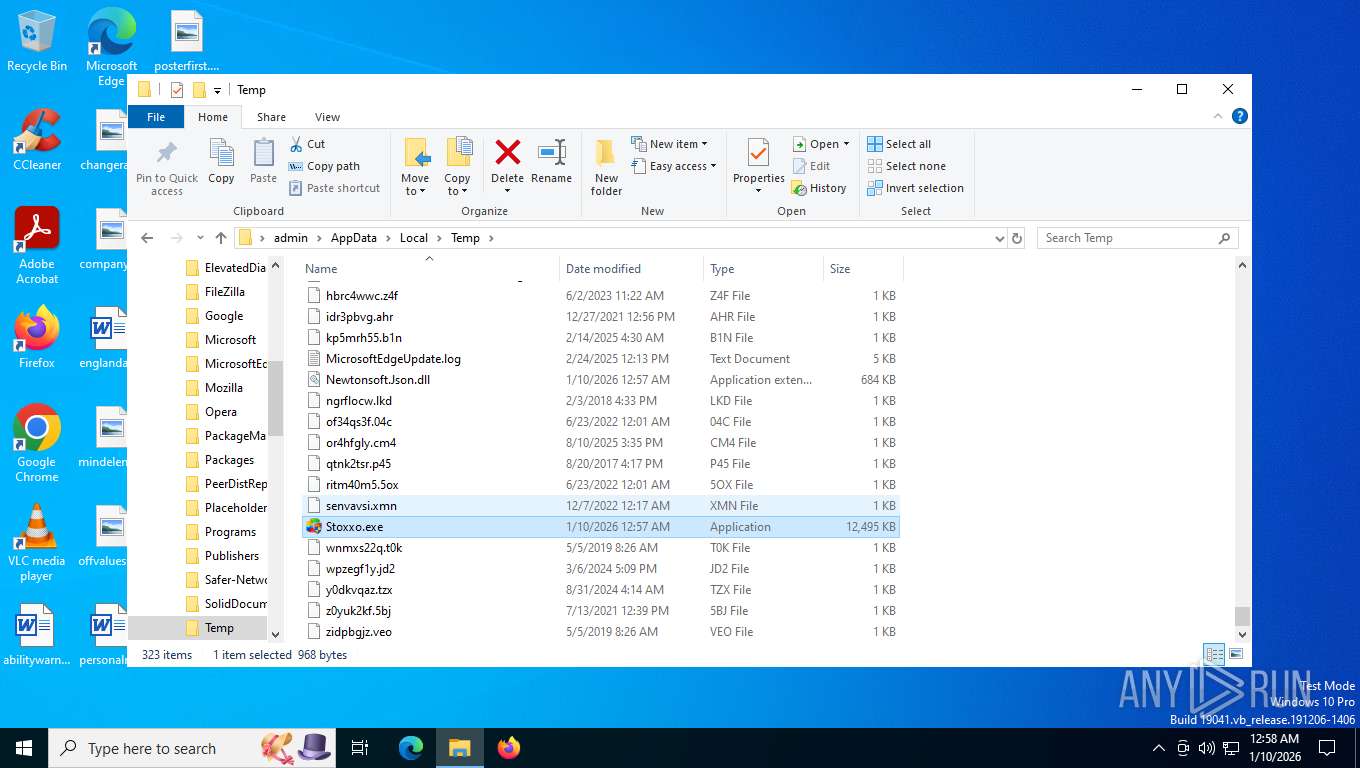
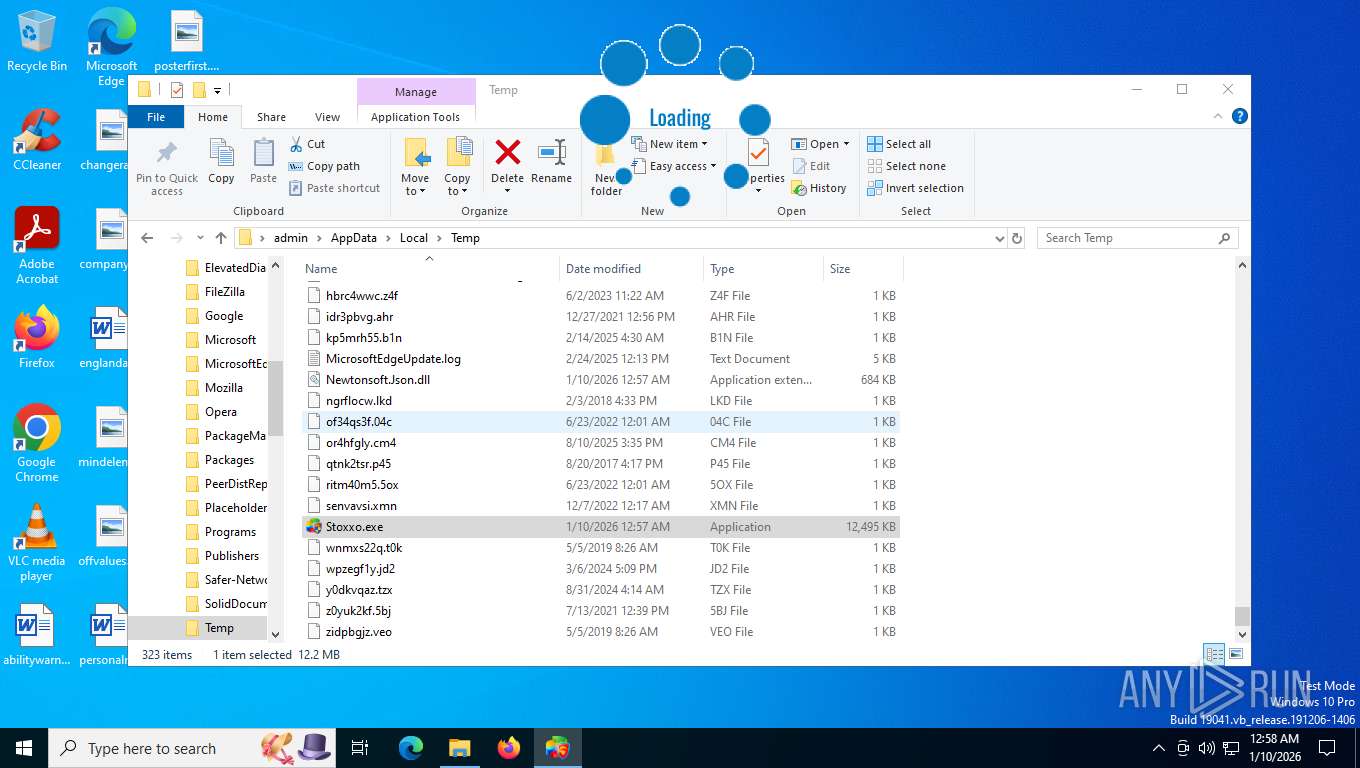
Executable content was dropped or overwritten
- Stoxxo.exe (PID: 7744)
There is functionality for taking screenshot (YARA)
- Stoxxo.exe (PID: 7744)
Possible usage of Discord/Telegram API has been detected (YARA)
- Stoxxo.exe (PID: 7744)
INFO
Reads the computer name
- Stoxxo.exe (PID: 7744)
- SystemSettings.exe (PID: 6188)
- Stoxxo.exe (PID: 4540)
Checks supported languages
- Stoxxo.exe (PID: 7744)
- SystemSettings.exe (PID: 6188)
- Stoxxo.exe (PID: 4540)
Reads the machine GUID from the registry
- Stoxxo.exe (PID: 7744)
- Stoxxo.exe (PID: 4540)
- SystemSettings.exe (PID: 6188)
Checks proxy server information
- Stoxxo.exe (PID: 7744)
Disables trace logs
- Stoxxo.exe (PID: 7744)
- Stoxxo.exe (PID: 4540)
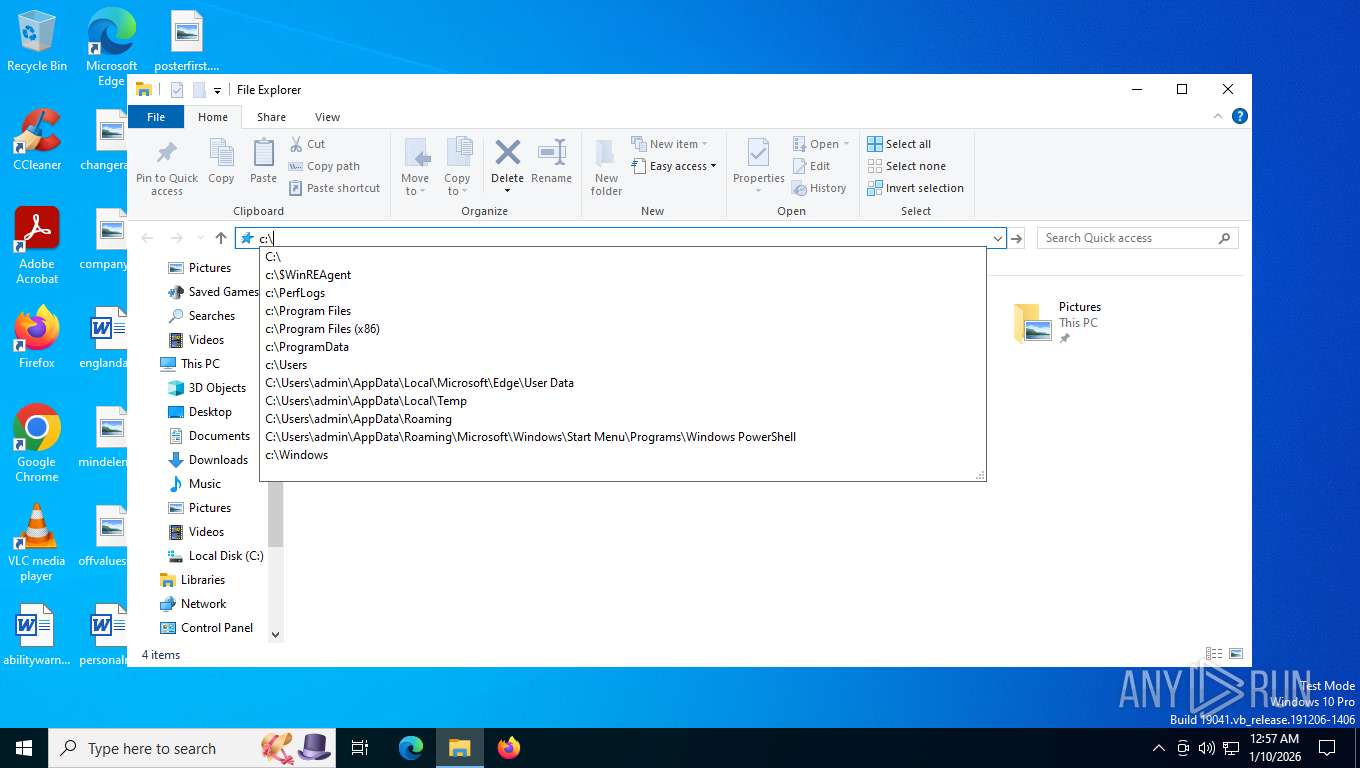
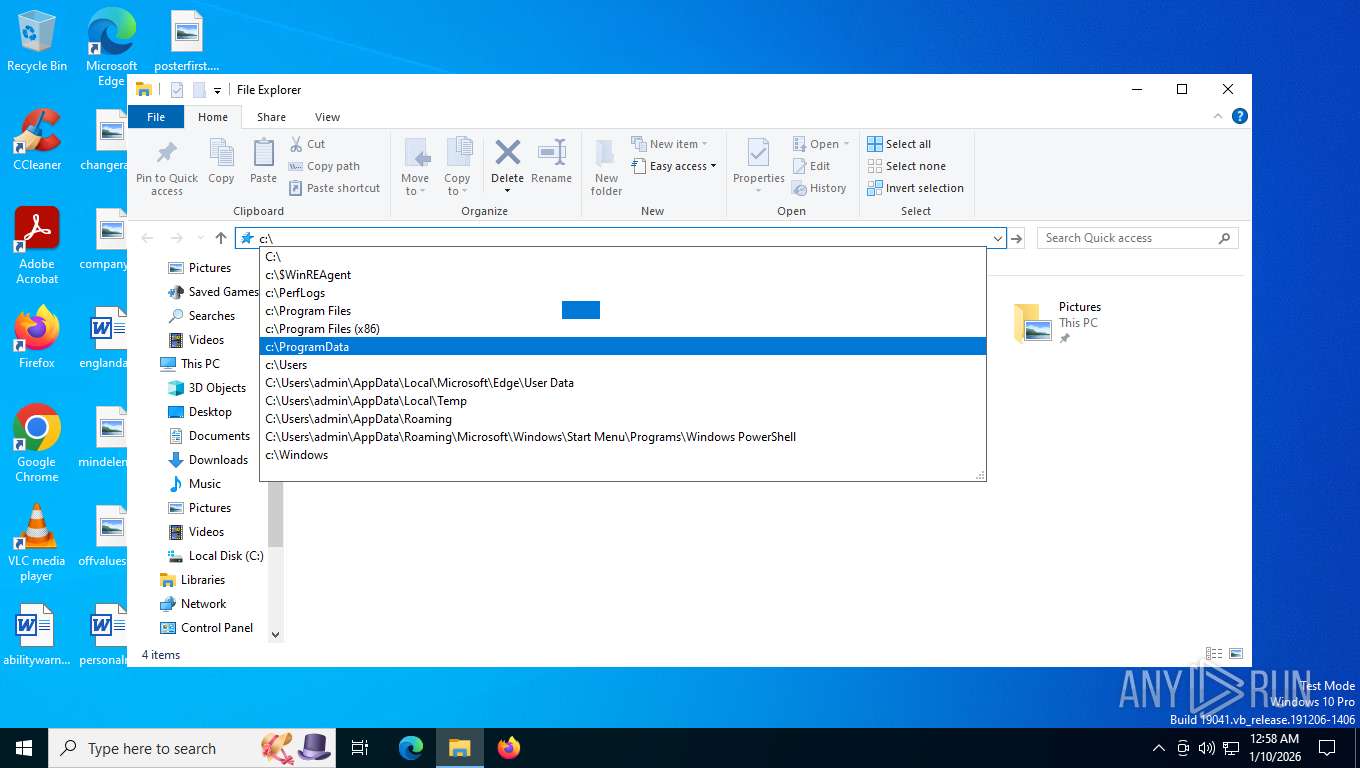
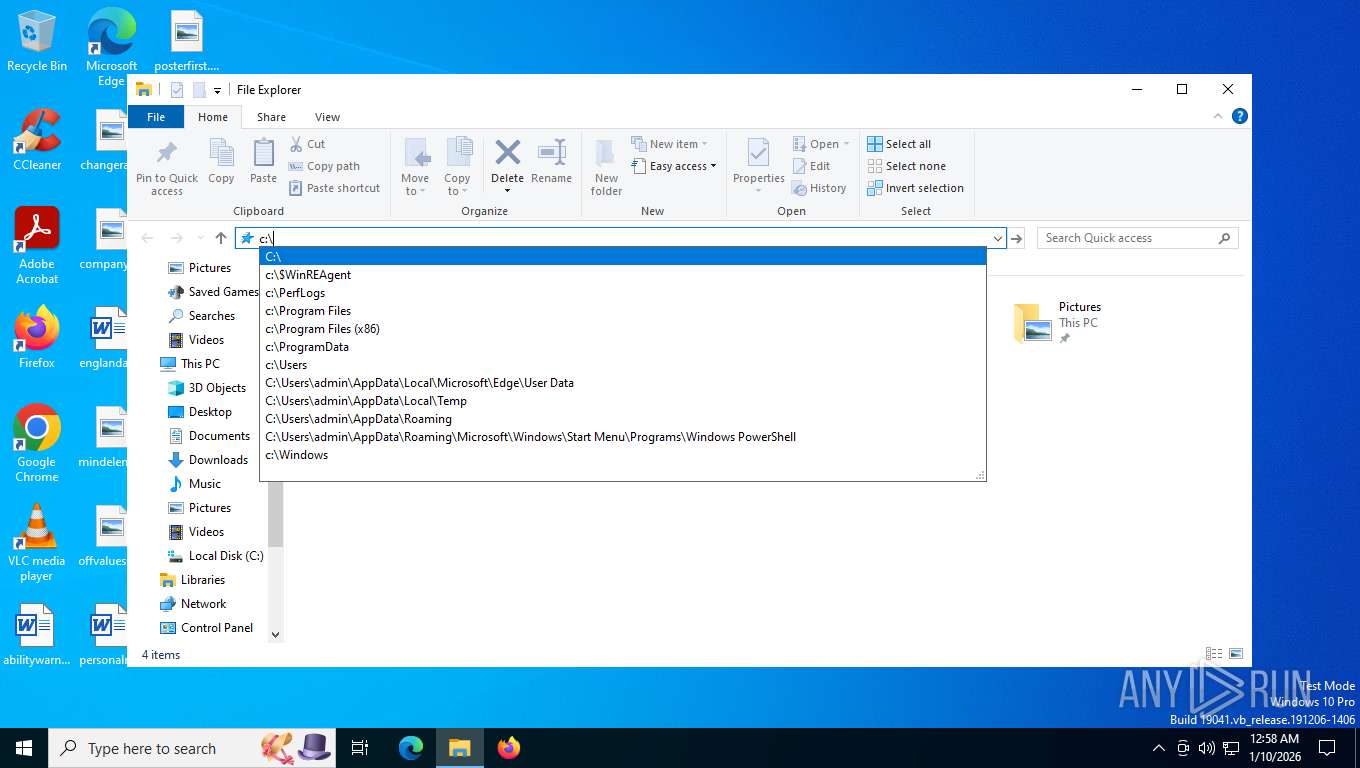
Reads Environment values
- Stoxxo.exe (PID: 7744)
- Stoxxo.exe (PID: 4540)
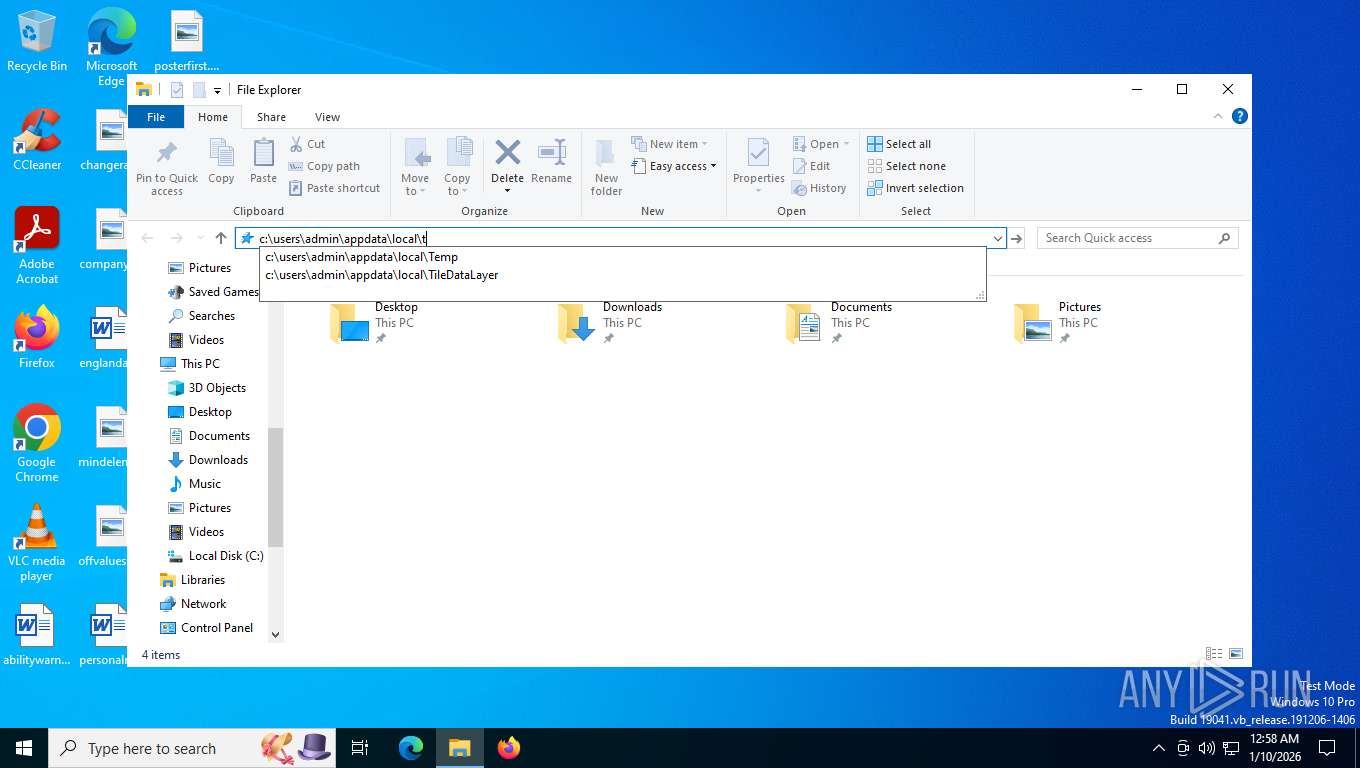
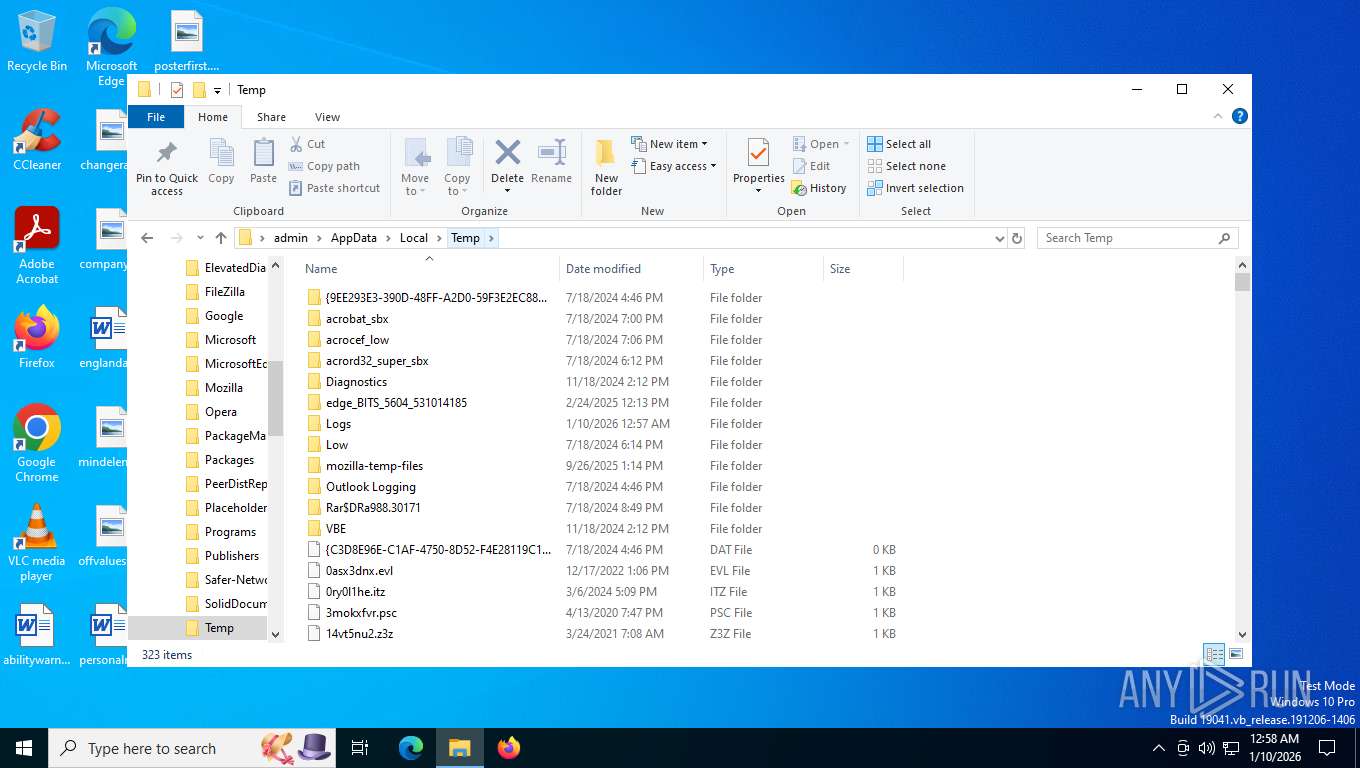
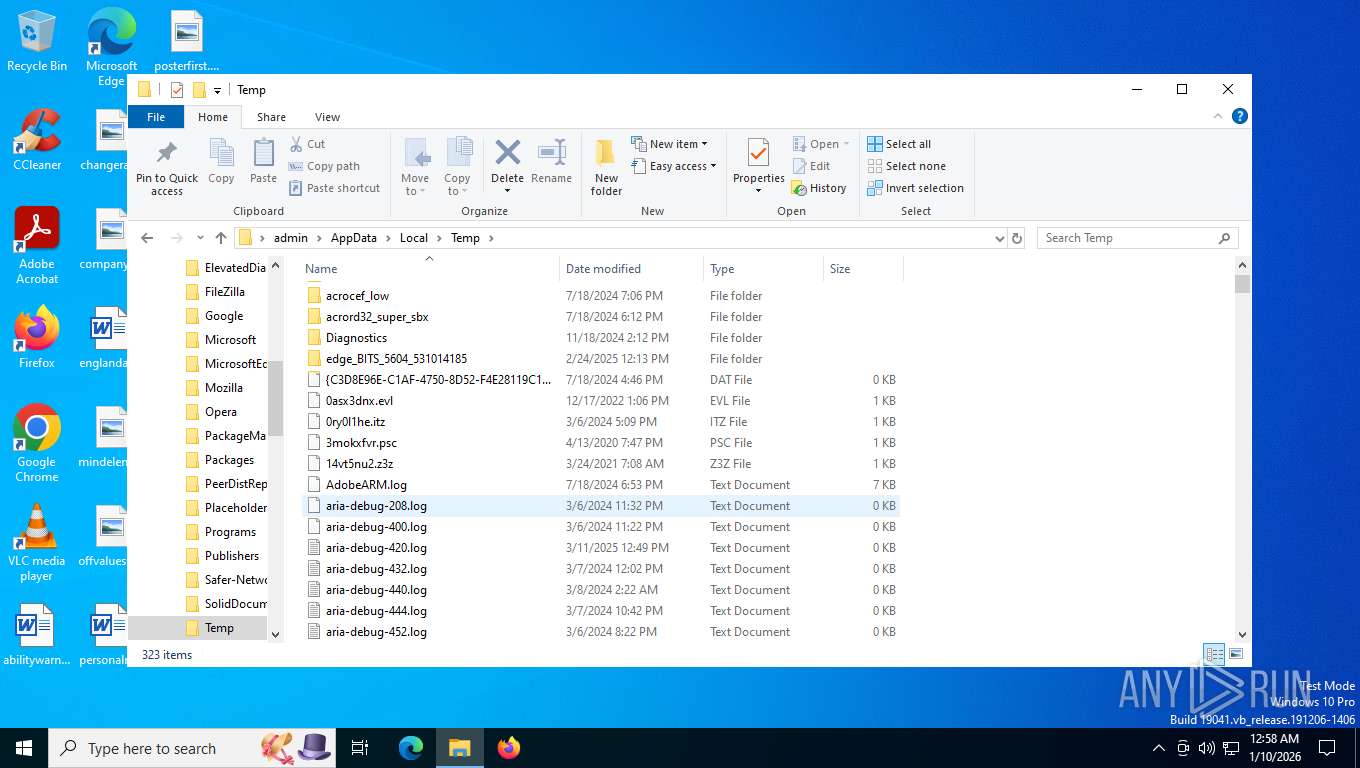
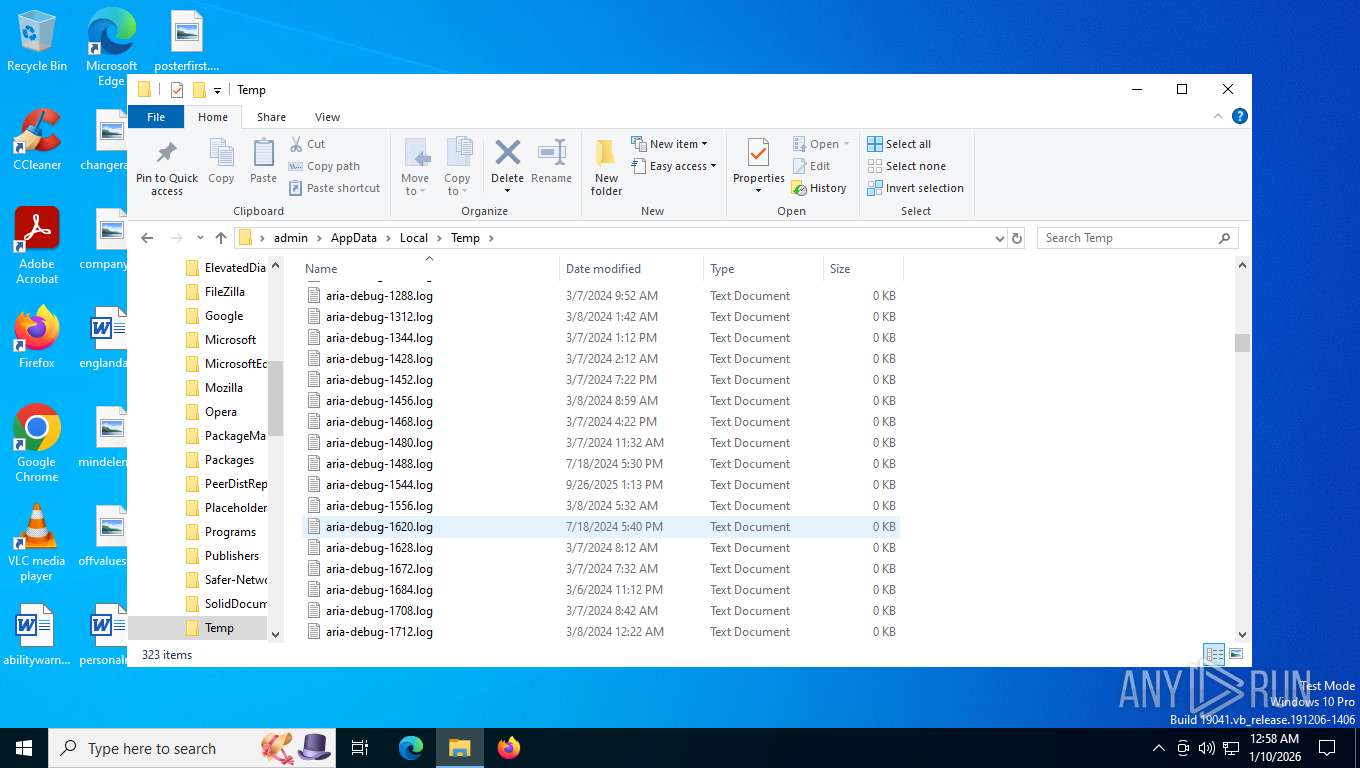
Create files in a temporary directory
- Stoxxo.exe (PID: 7744)
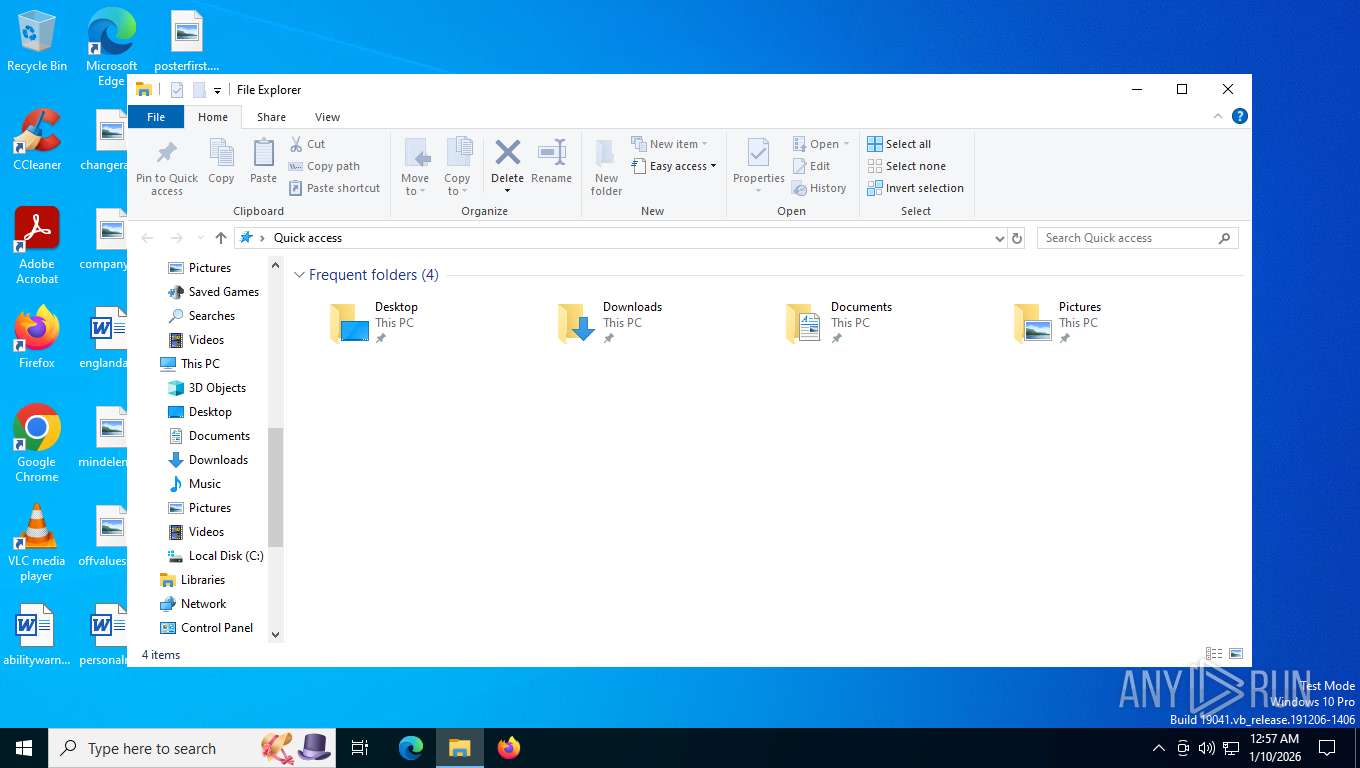
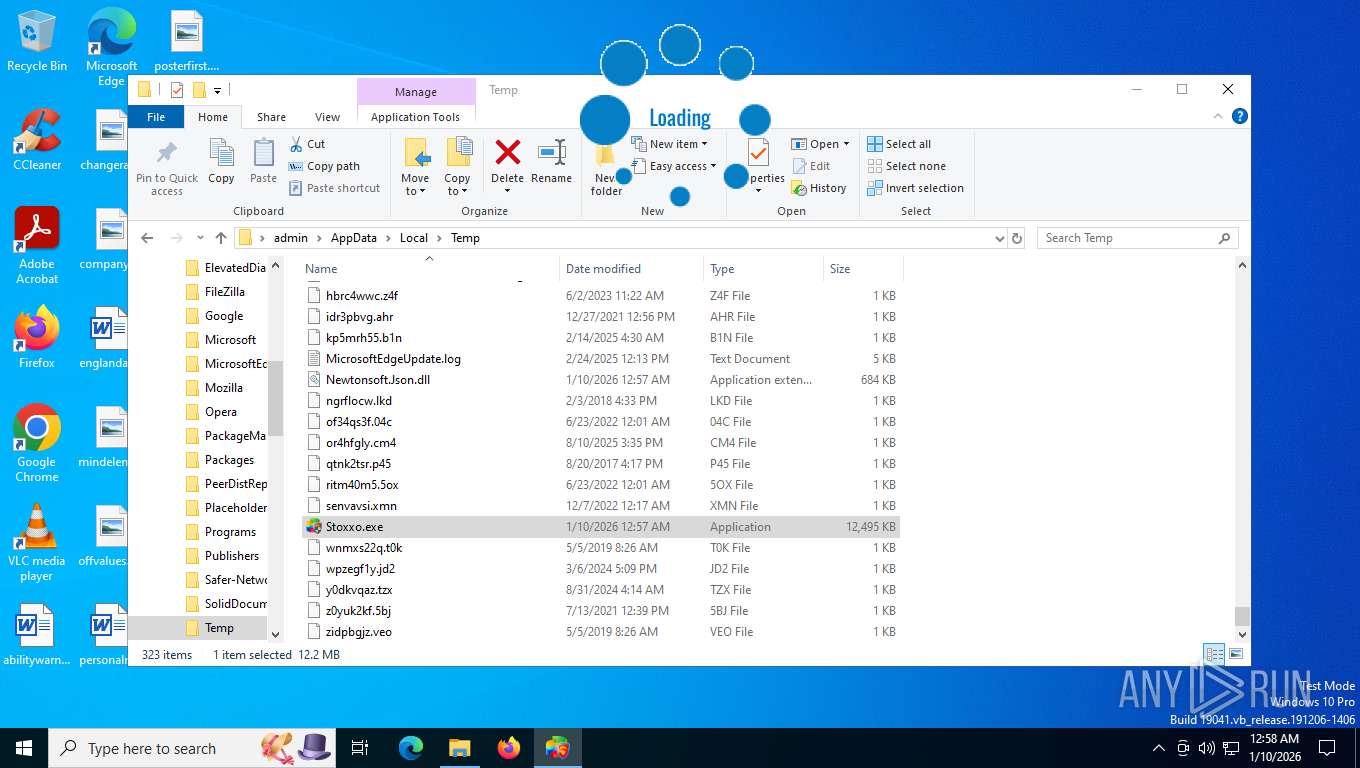
Manual execution by a user
- Stoxxo.exe (PID: 4540)
- Stoxxo.exe (PID: 7992)
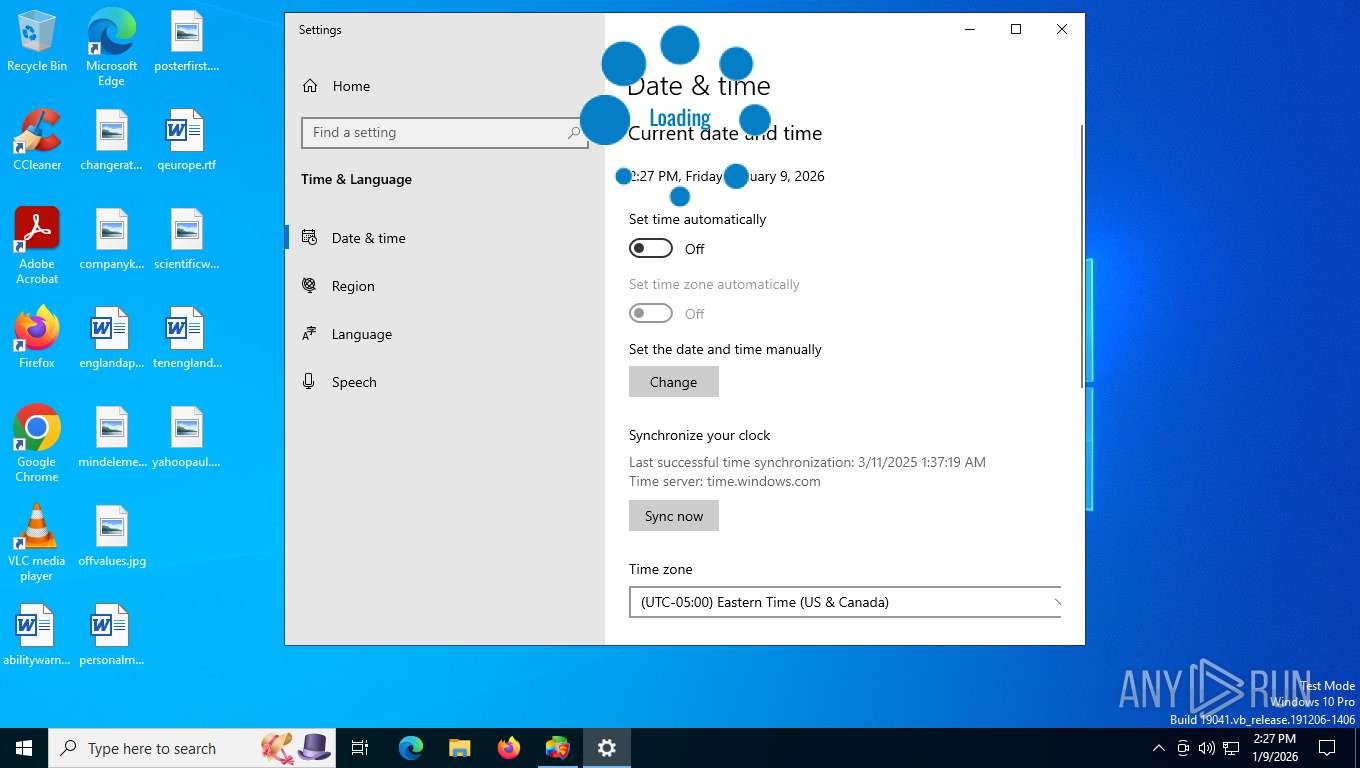
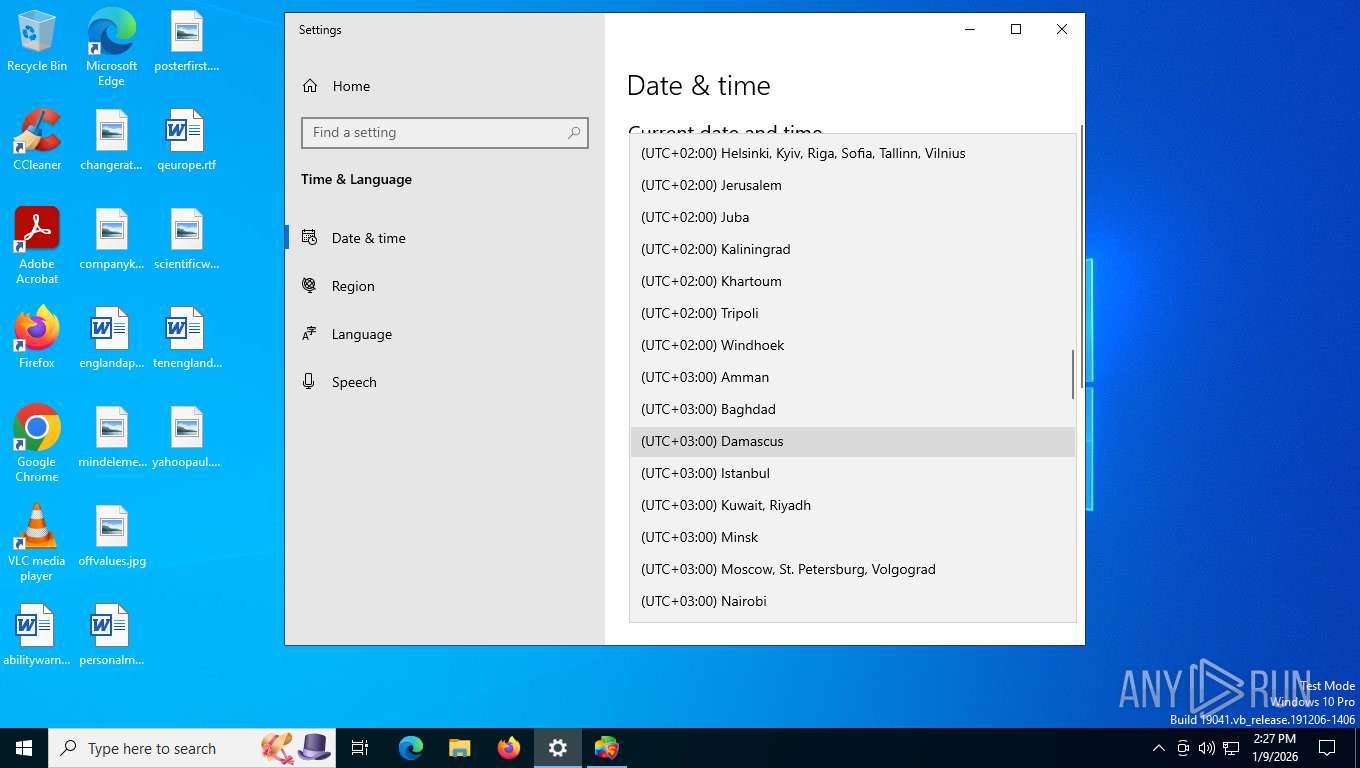
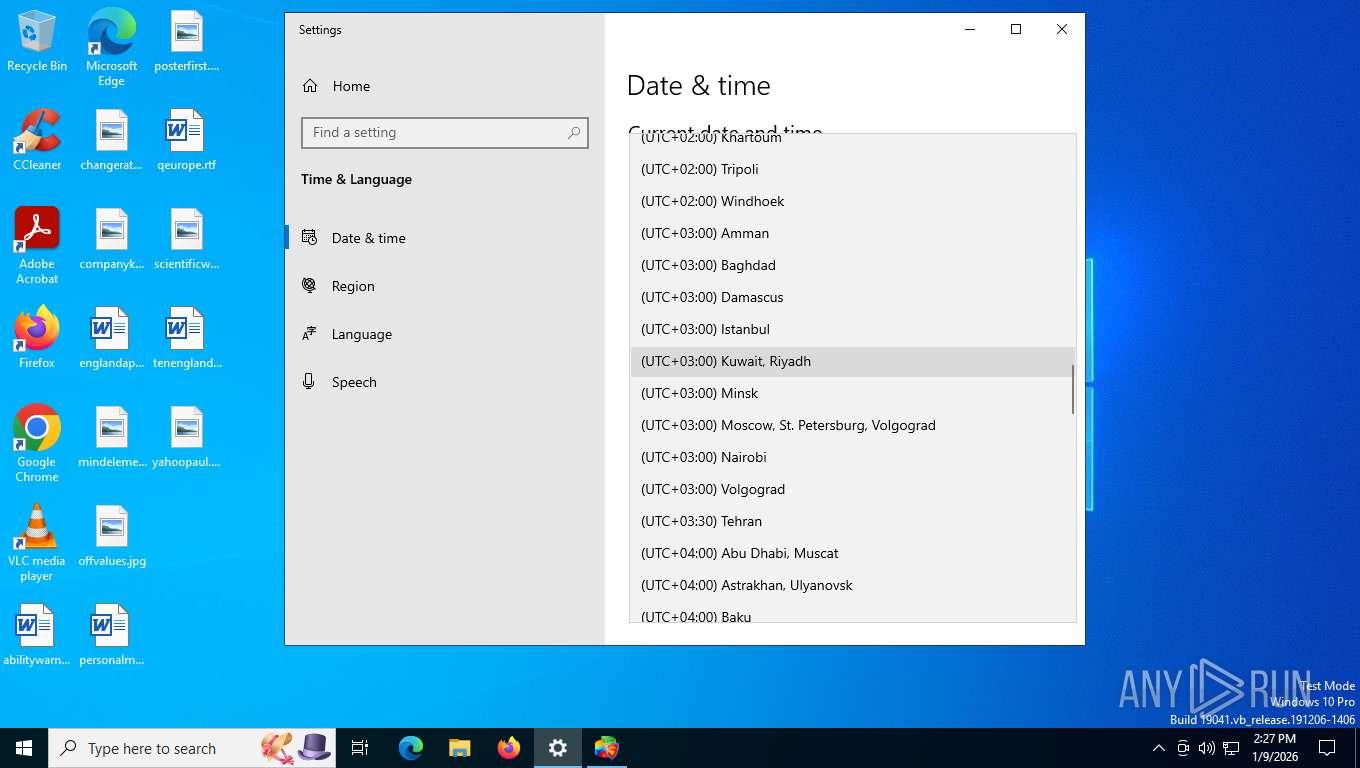
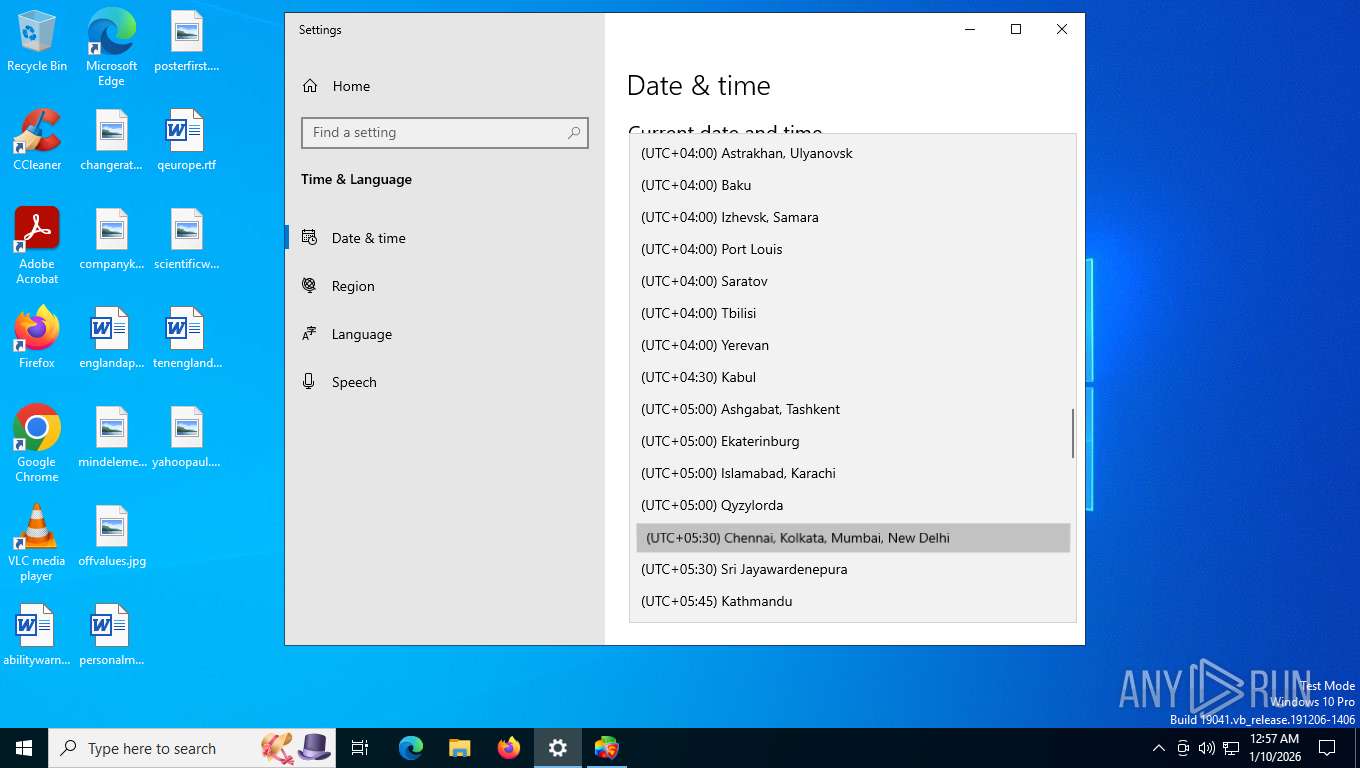
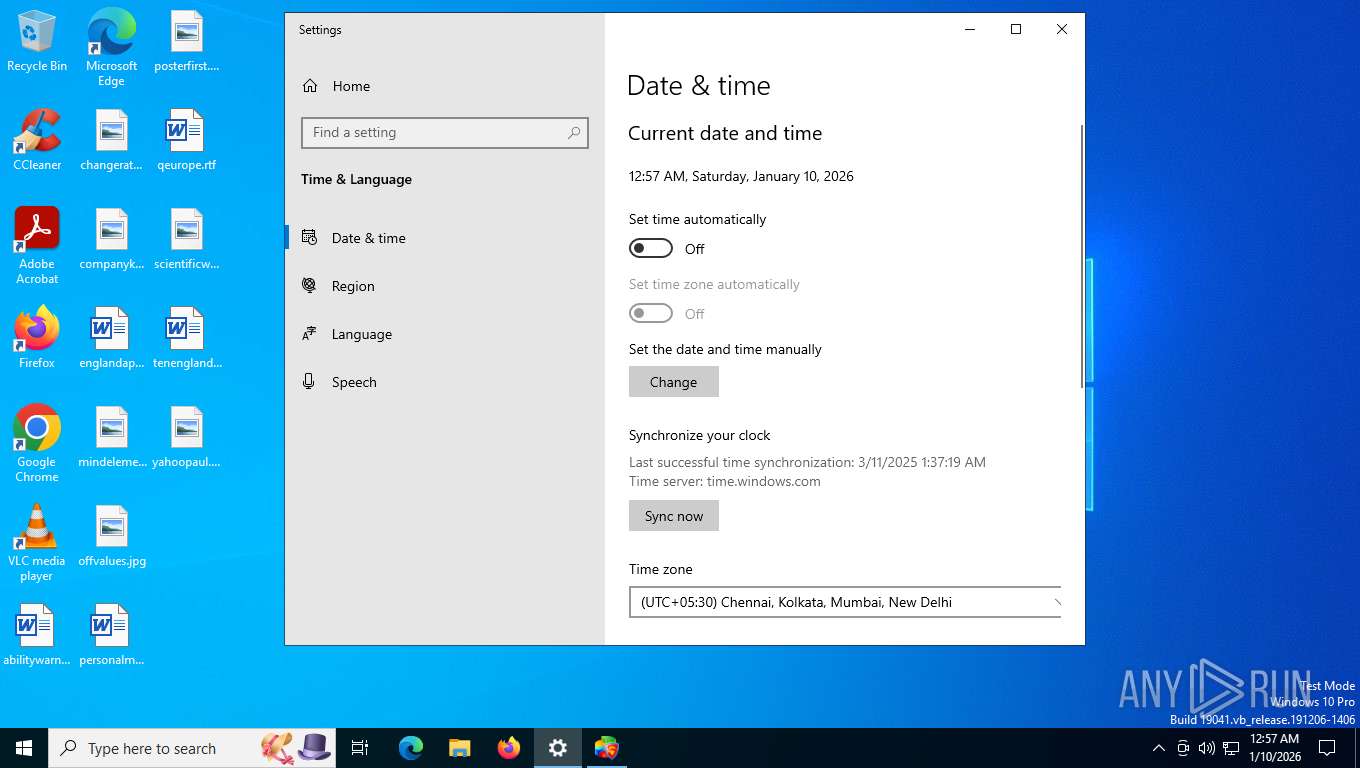
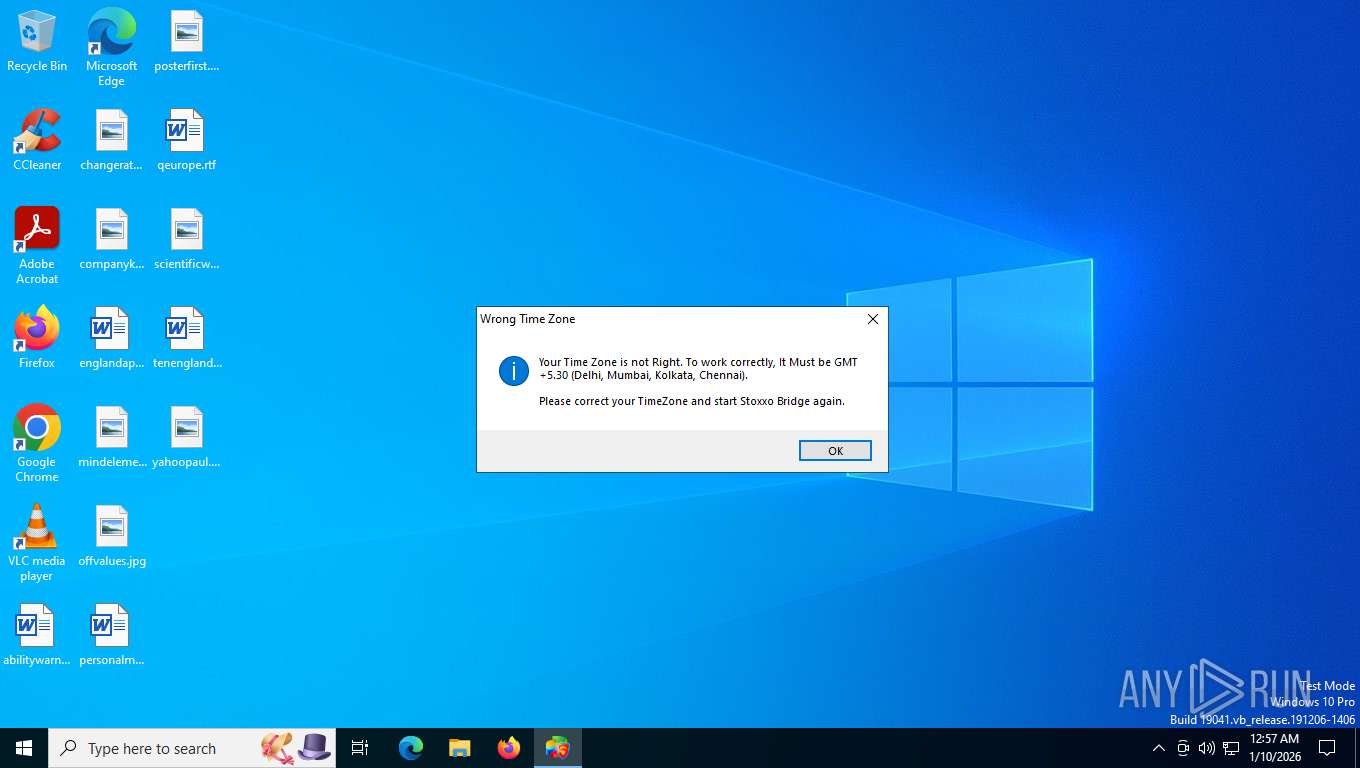
Reads the time zone
- SystemSettings.exe (PID: 6188)
Confuser has been detected (YARA)
- Stoxxo.exe (PID: 7744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(7744) Stoxxo.exe
Decrypted-URLs (1)https://kite.trade/connect/login6
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.3) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:02:06 19:01:54+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 12576768 |
| InitializedDataSize: | 205312 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc006de |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.2.701 |
| ProductVersionNumber: | 1.0.2.701 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Bridge the Trading applications such as AmiBroker, MT, NinjaTrader, TradingView etc to the supported brokers using their API. |
| CompanyName: | Algo Baba Private Limited |
| FileDescription: | Stoxxo Bridge |
| FileVersion: | 1.0.2.701 |
| InternalName: | Stoxxo.exe |
| LegalCopyright: | Copyright © 2020-2024 Algo Baba Private Limited |
| LegalTrademarks: | - |
| OriginalFileName: | Stoxxo.exe |
| ProductName: | Stoxxo Intelligent Trading Bridge |
| ProductVersion: | 1.0.2.701 |
| AssemblyVersion: | 1.0.2.701 |
Total processes
148
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
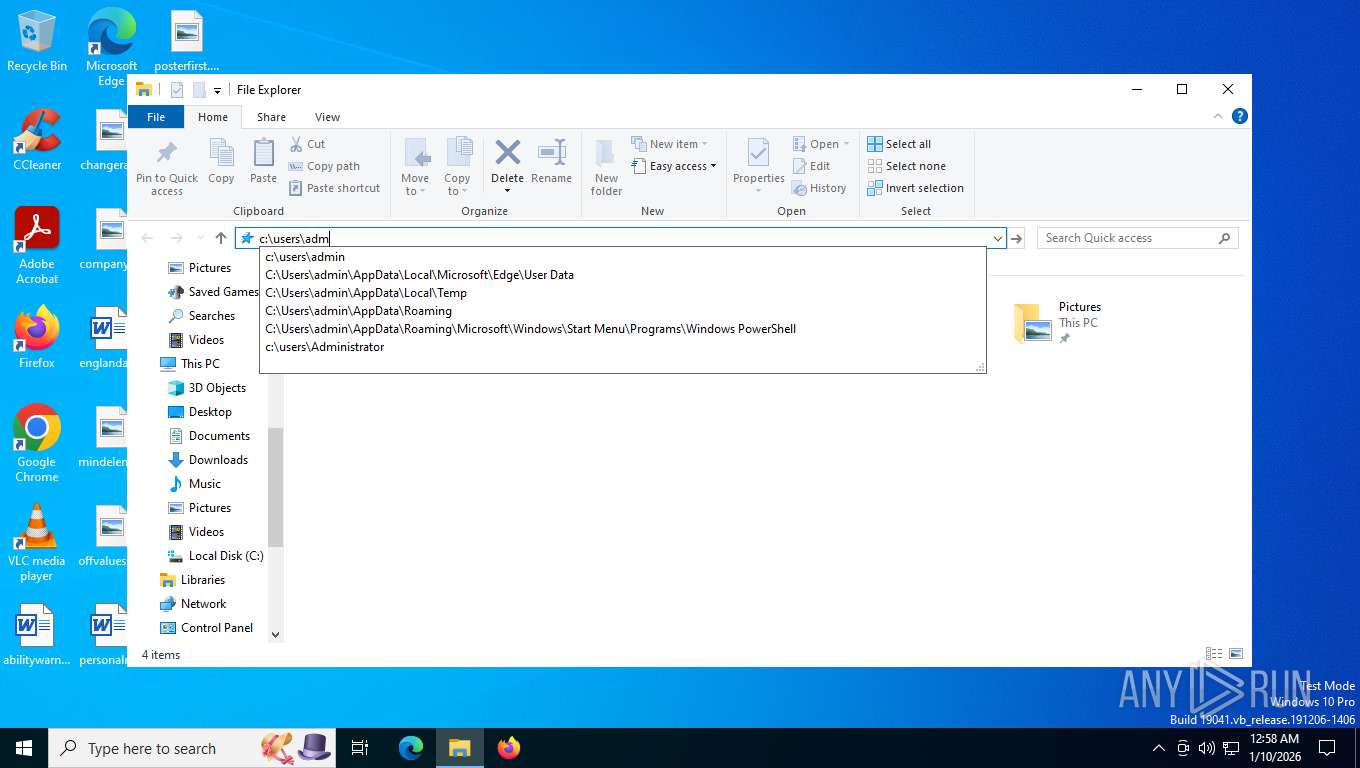
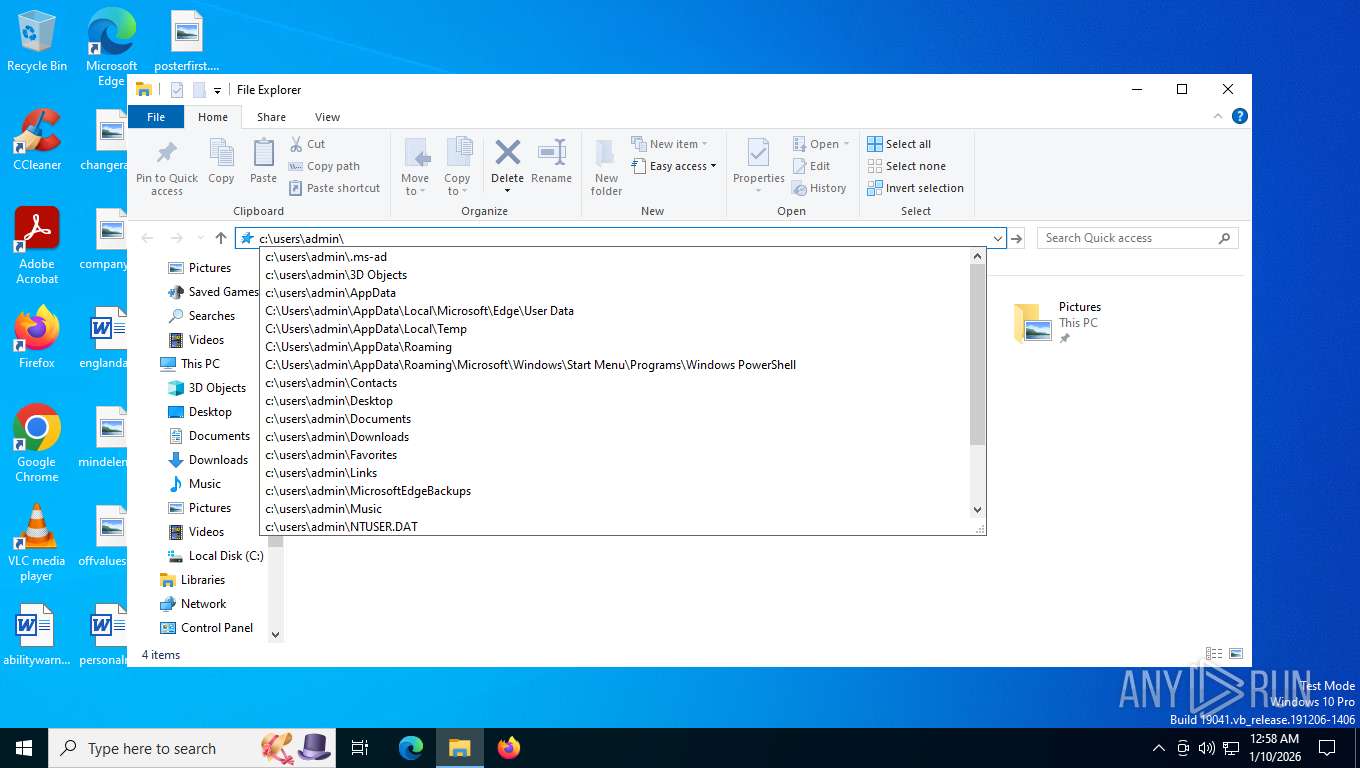
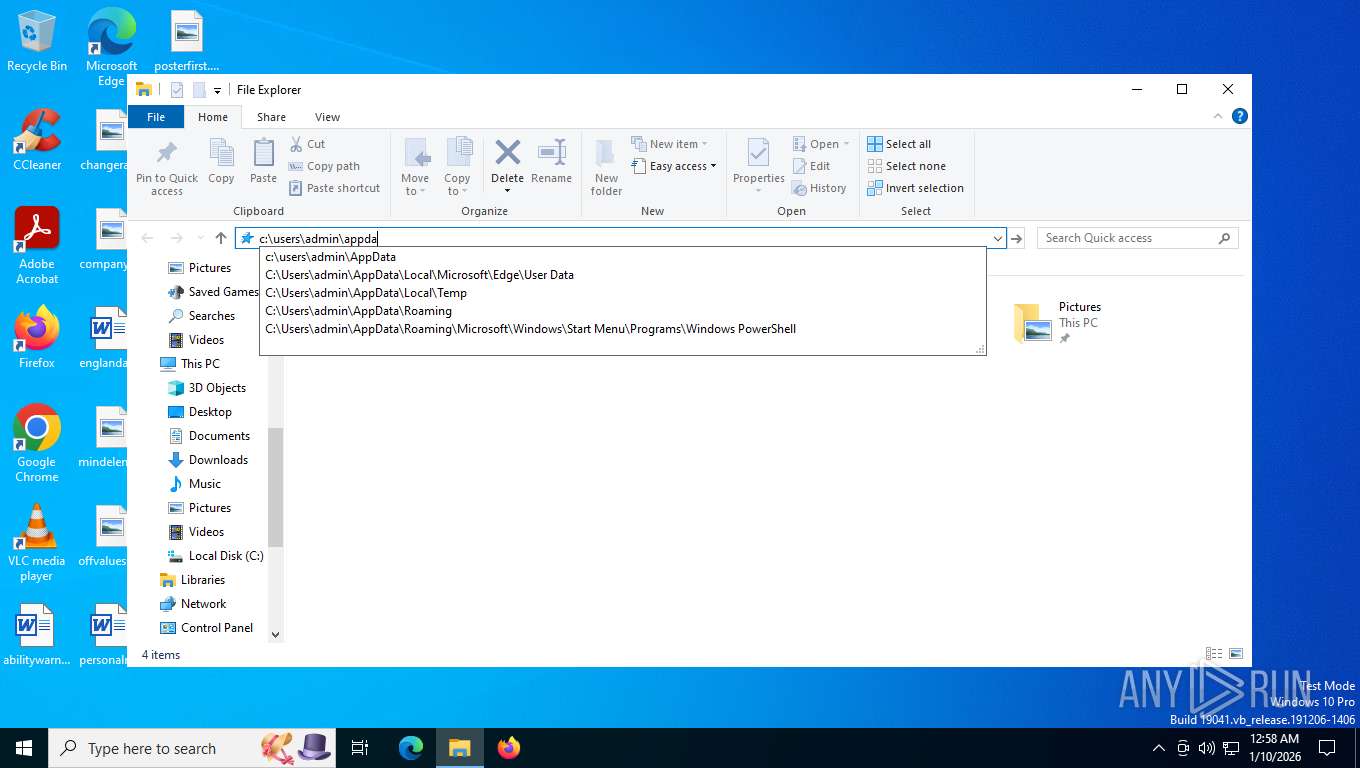
| 4540 | "C:\Users\admin\AppData\Local\Temp\Stoxxo.exe" | C:\Users\admin\AppData\Local\Temp\Stoxxo.exe | explorer.exe | ||||||||||||
User: admin Company: Algo Baba Private Limited Integrity Level: HIGH Description: Stoxxo Bridge Version: 1.0.2.701 Modules
| |||||||||||||||
| 6188 | "C:\Windows\ImmersiveControlPanel\SystemSettings.exe" -ServerName:microsoft.windows.immersivecontrolpanel | C:\Windows\ImmersiveControlPanel\SystemSettings.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Settings Exit code: 1 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7576 | "C:\Users\admin\AppData\Local\Temp\Stoxxo.exe" | C:\Users\admin\AppData\Local\Temp\Stoxxo.exe | — | explorer.exe | |||||||||||
User: admin Company: Algo Baba Private Limited Integrity Level: MEDIUM Description: Stoxxo Bridge Exit code: 3221226540 Version: 1.0.2.701 Modules
| |||||||||||||||
| 7744 | "C:\Users\admin\AppData\Local\Temp\Stoxxo.exe" | C:\Users\admin\AppData\Local\Temp\Stoxxo.exe | explorer.exe | ||||||||||||
User: admin Company: Algo Baba Private Limited Integrity Level: HIGH Description: Stoxxo Bridge Exit code: 0 Version: 1.0.2.701 Modules
xor-url(PID) Process(7744) Stoxxo.exe Decrypted-URLs (1)https://kite.trade/connect/login6 | |||||||||||||||
| 7960 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7992 | "C:\Users\admin\AppData\Local\Temp\Stoxxo.exe" | C:\Users\admin\AppData\Local\Temp\Stoxxo.exe | — | explorer.exe | |||||||||||
User: admin Company: Algo Baba Private Limited Integrity Level: MEDIUM Description: Stoxxo Bridge Exit code: 3221226540 Version: 1.0.2.701 Modules
| |||||||||||||||
Total events
5 383
Read events
5 366
Write events
17
Delete events
0
Modification events
| (PID) Process: | (7744) Stoxxo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Stoxxo_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7744) Stoxxo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Stoxxo_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7744) Stoxxo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Stoxxo_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7744) Stoxxo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Stoxxo_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (7744) Stoxxo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Stoxxo_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (7744) Stoxxo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Stoxxo_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (7744) Stoxxo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Stoxxo_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (7744) Stoxxo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Stoxxo_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7744) Stoxxo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Stoxxo_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7744) Stoxxo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Stoxxo_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
1
Suspicious files
9
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7744 | Stoxxo.exe | C:\Users\admin\AppData\Local\Temp\Newtonsoft.Json.dll | executable | |
MD5:6815034209687816D8CF401877EC8133 | SHA256:7F912B28A07C226E0BE3ACFB2F57F050538ABA0100FA1F0BF2C39F1A1F1DA814 | |||
| 6188 | SystemSettings.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:923557339A6325B66C5CD3143045F77B | SHA256:950F505F1DADD46830ED9E63FCE9A3D6C2F9D701ED11D8E07D776B12D34F4D52 | |||
| 6188 | SystemSettings.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\f18460fded109990.customDestinations-ms~RFffd81.TMP | binary | |
MD5:4FCB2A3EE025E4A10D21E1B154873FE2 | SHA256:90BF6BAA6F968A285F88620FBF91E1F5AA3E66E2BAD50FD16F37913280AD8228 | |||
| 6188 | SystemSettings.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_D53C01423A36DBCEB0BB7256A7DA6D8C | binary | |
MD5:A5FA3208D1E93F435385F31EE3B9DC04 | SHA256:0FF96E8CFBBC6AA62E8241545A495AC34B358CA157C5718F0CE047505E4584B4 | |||
| 6188 | SystemSettings.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:401CE1E84C35023D7D9C4F7F6C281C29 | SHA256:A7D90ACD81EA19E58094EBB1E07C26D8672F01AC7A0DB7BFD54CE409A545C377 | |||
| 7744 | Stoxxo.exe | C:\Users\admin\AppData\Local\Temp\Logs\09-Jan-2026\Log.dat | binary | |
MD5:5F44E8D89BC98171258D204CC07BF851 | SHA256:443EAC4923340D1EEBAC595788B178A474900C42E70CAE542E143AA9F0030679 | |||
| 6188 | SystemSettings.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_D53C01423A36DBCEB0BB7256A7DA6D8C | binary | |
MD5:D38D14AB3BBAFBA12AA859896FD7618F | SHA256:E2685BFCE53141980768115B2E88A3559170BCC697C48279AEB529086A1C9131 | |||
| 6188 | SystemSettings.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\LBNB1T728D4ZWX8P4KYW.temp | binary | |
MD5:4FCB2A3EE025E4A10D21E1B154873FE2 | SHA256:90BF6BAA6F968A285F88620FBF91E1F5AA3E66E2BAD50FD16F37913280AD8228 | |||
| 7744 | Stoxxo.exe | C:\Users\admin\AppData\Local\Temp\Logs\09-Jan-2026\GridLog.csv | text | |
MD5:1FB5FAECD7C82B2AAE061FE7E1DFB356 | SHA256:D51810FBE760C6572D13087830DBC73595AF47E8B1B64ABCC57D3EC7121E05B2 | |||
| 7744 | Stoxxo.exe | C:\Users\admin\AppData\Local\Temp\Logs\09-Jan-2026\ErrorLog.dat | binary | |
MD5:59A9EBC4B451EC25BC37E61B343F5D44 | SHA256:7725F901E73D91FC76F7CF74CCB33783DD83334EEBE4556E8A91ECC3125F8C1C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
36
DNS requests
19
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=562&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | unknown | — | — | whitelisted |
816 | RUXIMICS.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/RUXIM?os=Windows&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3623&OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&FlightRing=Retail&AttrDataVer=186&App=RUXIM&AppVer=&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
5636 | svchost.exe | GET | 200 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaasMedic?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&appVer=10.0.19041.3758&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4 | unknown | text | 3.41 Kb | whitelisted |
2224 | svchost.exe | POST | 200 | 20.190.160.65:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
5636 | svchost.exe | GET | 200 | 2.16.164.89:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.89:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5636 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
816 | RUXIMICS.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
816 | RUXIMICS.exe | GET | 200 | 2.16.164.89:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5636 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
816 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3412 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5636 | svchost.exe | 2.16.164.89:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 2.16.164.89:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
816 | RUXIMICS.exe | 2.16.164.89:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5636 | svchost.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
cxcs.microsoft.net |
| whitelisted |
www.nseindia.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7744 | Stoxxo.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host ZIP Request |