| File name: | VC_redist.x64.exe |
| Full analysis: | https://app.any.run/tasks/ef8b2f24-bf32-4b70-bfab-5f9c7e048ffd |
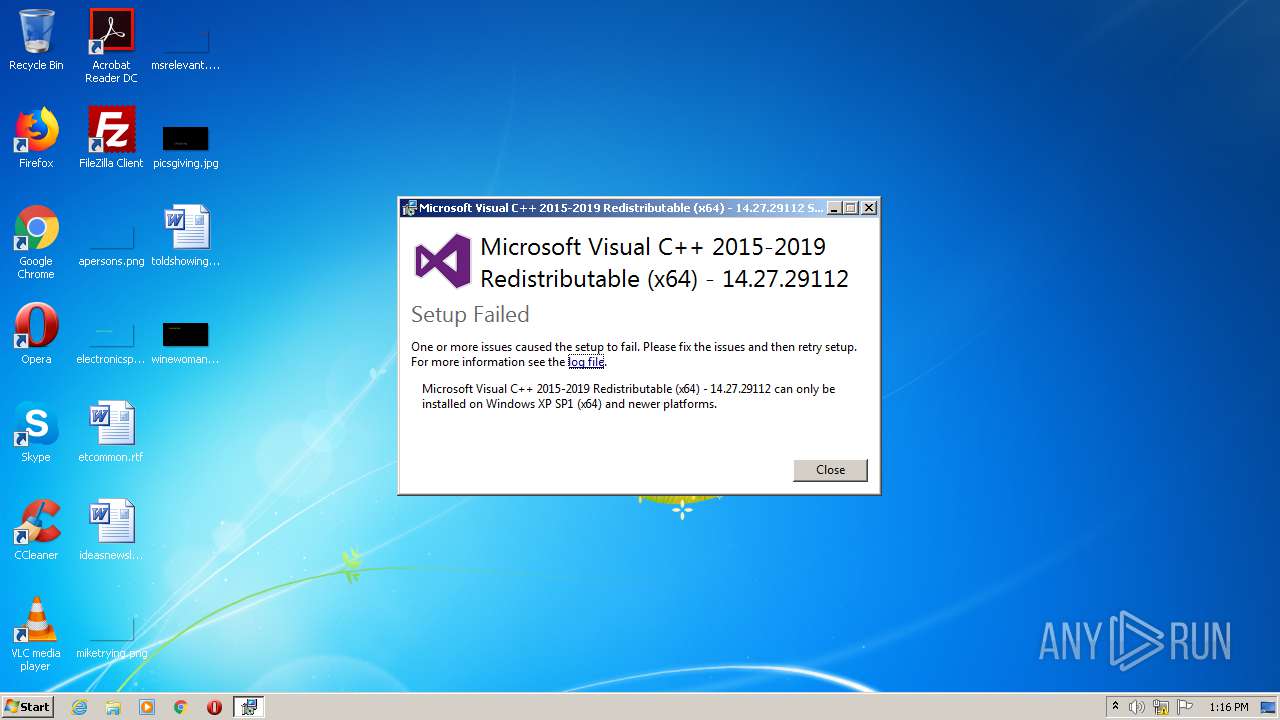
| Verdict: | No threats detected |
| Analysis date: | October 24, 2020, 12:15:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9F096B97D204078B443DBCBF18E0EBB0 |
| SHA1: | A55510A8C9708B2C68B39CD50BBCAF86E2C885F0 |
| SHA256: | 4B5890EB1AEFDF8DFA3234B5032147EB90F050C5758A80901B201AE969780107 |
| SSDEEP: | 196608:cRjJHflpQcIIS/Rj7BWl+aV8t8z72BxBwBgO4IWSCvG2hCsPOasObofyOrjLUclP:kBlptVYmfr7yBG/4I0vG2hJWjL5sKJ |
MALICIOUS
Loads dropped or rewritten executable
- VC_redist.x64.exe (PID: 1104)
Application was dropped or rewritten from another process
- VC_redist.x64.exe (PID: 1104)
SUSPICIOUS
Executable content was dropped or overwritten
- VC_redist.x64.exe (PID: 908)
- VC_redist.x64.exe (PID: 1104)
INFO
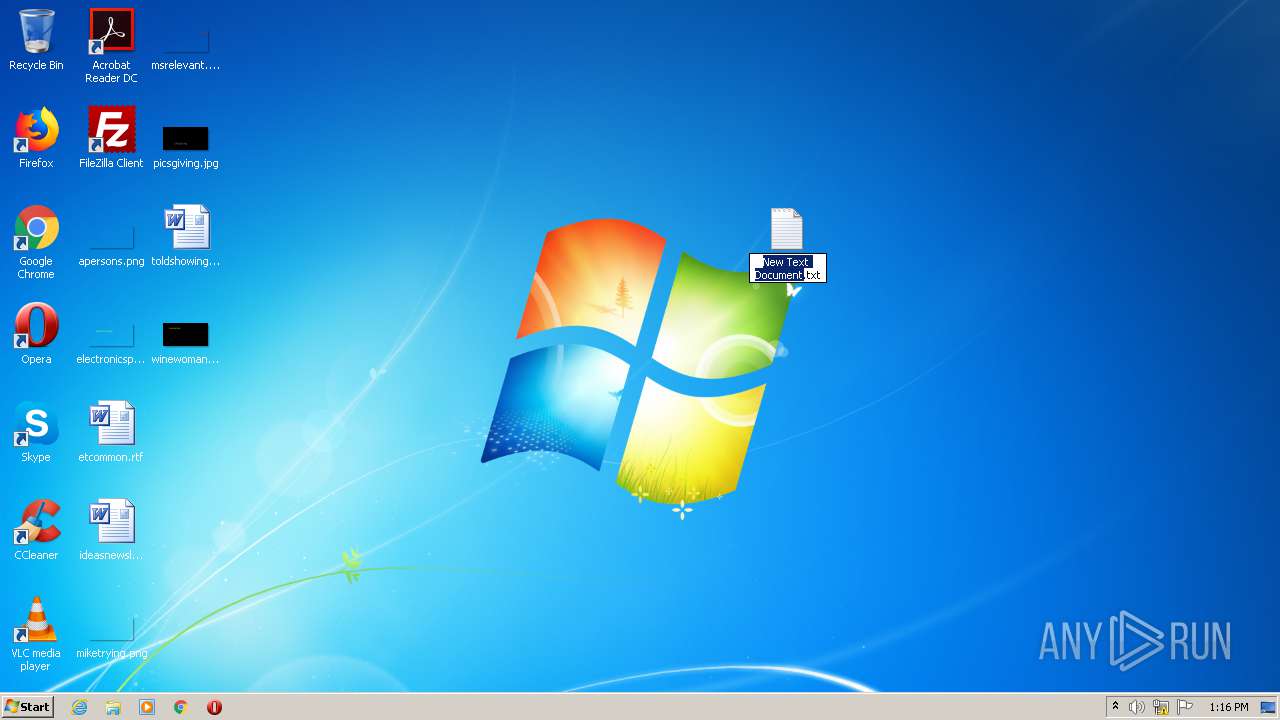
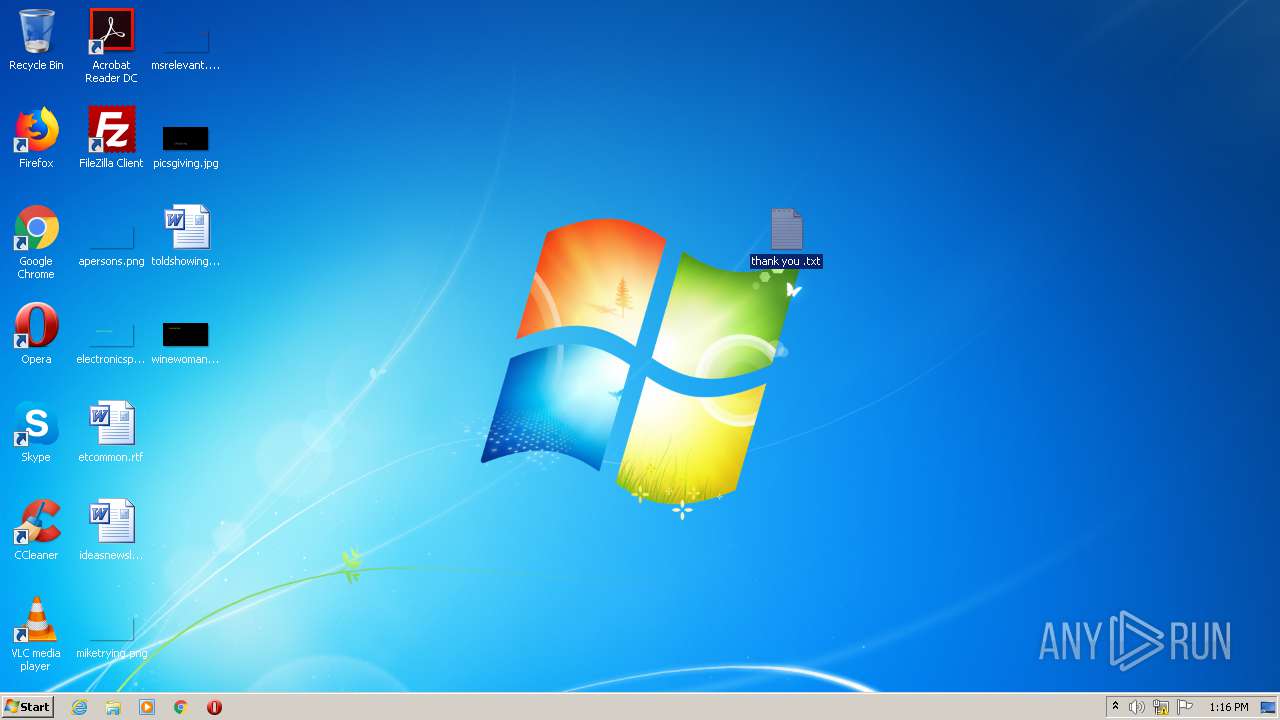
Manual execution by user
- NOTEPAD.EXE (PID: 884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:11:18 22:37:28+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 301056 |
| InitializedDataSize: | 161280 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e06d |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 14.27.29112.0 |
| ProductVersionNumber: | 14.27.29112.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft Visual C++ 2015-2019 Redistributable (x64) - 14.27.29112 |
| FileVersion: | 14.27.29112.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| OriginalFileName: | VC_redist.x64.exe |
| ProductName: | Microsoft Visual C++ 2015-2019 Redistributable (x64) - 14.27.29112 |
| ProductVersion: | 14.27.29112.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Nov-2017 21:37:28 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft Visual C++ 2015-2019 Redistributable (x64) - 14.27.29112 |
| FileVersion: | 14.27.29112.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| OriginalFilename: | VC_redist.x64.exe |
| ProductName: | Microsoft Visual C++ 2015-2019 Redistributable (x64) - 14.27.29112 |
| ProductVersion: | 14.27.29112.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 18-Nov-2017 21:37:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000497D7 | 0x00049800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56281 |
.rdata | 0x0004B000 | 0x0001EAF4 | 0x0001EC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.11341 |
.data | 0x0006A000 | 0x00001740 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.16545 |
.wixburn8 | 0x0006C000 | 0x00000038 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.7135 |
.tls | 0x0006D000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.gfids | 0x0006E000 | 0x000000E0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.00636 |
.rsrc | 0x0006F000 | 0x00003B1C | 0x00003C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.50547 |
.reloc | 0x00073000 | 0x00003D8C | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.77693 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.30829 | 1234 | Latin 1 / Western European | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
Cabinet.dll (delay-loaded) |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
40
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
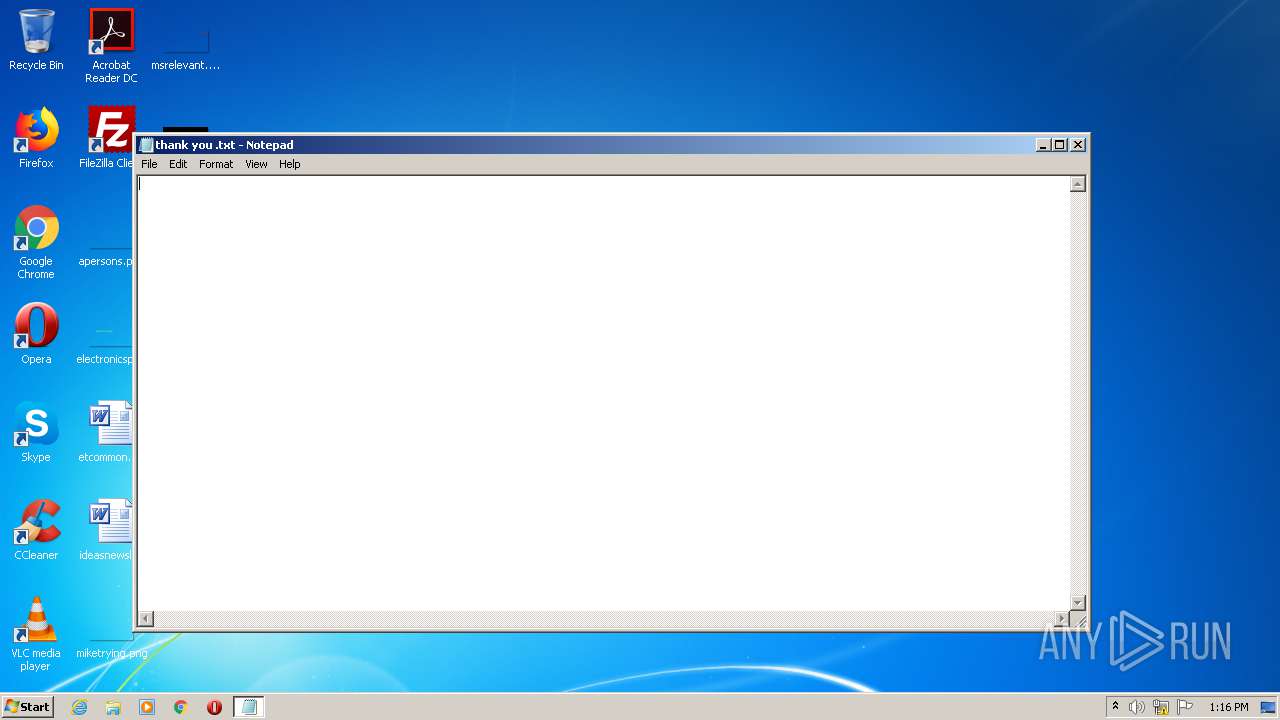
| 884 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\thank you .txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 908 | "C:\Users\admin\AppData\Local\Temp\VC_redist.x64.exe" | C:\Users\admin\AppData\Local\Temp\VC_redist.x64.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2015-2019 Redistributable (x64) - 14.27.29112 Exit code: 1 Version: 14.27.29112.0 Modules
| |||||||||||||||
| 1104 | "C:\Users\admin\AppData\Local\Temp\{8275FB5E-CA6A-4522-B023-07D9542AF7EE}\.cr\VC_redist.x64.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\VC_redist.x64.exe" -burn.filehandle.attached=148 -burn.filehandle.self=156 | C:\Users\admin\AppData\Local\Temp\{8275FB5E-CA6A-4522-B023-07D9542AF7EE}\.cr\VC_redist.x64.exe | VC_redist.x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2015-2019 Redistributable (x64) - 14.27.29112 Exit code: 1 Version: 14.27.29112.0 Modules
| |||||||||||||||
Total events
59
Read events
59
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
0
Text files
33
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 908 | VC_redist.x64.exe | C:\Users\admin\AppData\Local\Temp\{8275FB5E-CA6A-4522-B023-07D9542AF7EE}\.cr\VC_redist.x64.exe | executable | |
MD5:968E1C550C1254A3D5F63F4A78AC3B2B | SHA256:BD6E4DAE56565A5BE06B849A596FF2A552B2D89DE96014F0DBBCE5D8E4AB39F6 | |||
| 1104 | VC_redist.x64.exe | C:\Users\admin\AppData\Local\Temp\{6143044D-A0F1-49D7-84EA-0F02B99E0873}\.ba\license.rtf | text | |
MD5:2EABBB391ACB89942396DF5C1CA2BAD8 | SHA256:E3156D170014CED8D17A02B3C4FF63237615E5C2A8983B100A78CB1F881D6F38 | |||
| 1104 | VC_redist.x64.exe | C:\Users\admin\AppData\Local\Temp\{6143044D-A0F1-49D7-84EA-0F02B99E0873}\.ba\wixstdba.dll | executable | |
MD5:EAB9CAF4277829ABDF6223EC1EFA0EDD | SHA256:A4EFBDB2CE55788FFE92A244CB775EFD475526EF5B61AD78DE2BCDFADDAC7041 | |||
| 1104 | VC_redist.x64.exe | C:\Users\admin\AppData\Local\Temp\{6143044D-A0F1-49D7-84EA-0F02B99E0873}\.ba\1029\thm.wxl | xml | |
MD5:16343005D29EC431891B02F048C7F581 | SHA256:07FB3EC174F25DFBE532D9D739234D9DFDA8E9D34F01FE660C5B4D56989FA779 | |||
| 1104 | VC_redist.x64.exe | C:\Users\admin\AppData\Local\Temp\{6143044D-A0F1-49D7-84EA-0F02B99E0873}\.ba\logo.png | image | |
MD5:D6BD210F227442B3362493D046CEA233 | SHA256:335A256D4779EC5DCF283D007FB56FD8211BBCAF47DCD70FE60DED6A112744EF | |||
| 1104 | VC_redist.x64.exe | C:\Users\admin\AppData\Local\Temp\{6143044D-A0F1-49D7-84EA-0F02B99E0873}\.ba\thm.wxl | xml | |
MD5:FBFCBC4DACC566A3C426F43CE10907B6 | SHA256:70400F181D00E1769774FF36BCD8B1AB5FBC431418067D31B876D18CC04EF4CE | |||
| 1104 | VC_redist.x64.exe | C:\Users\admin\AppData\Local\Temp\{6143044D-A0F1-49D7-84EA-0F02B99E0873}\.ba\thm.xml | xml | |
MD5:F62729C6D2540015E072514226C121C7 | SHA256:F13BAE0EC08C91B4A315BB2D86EE48FADE597E7A5440DCE6F751F98A3A4D6916 | |||
| 1104 | VC_redist.x64.exe | C:\Users\admin\AppData\Local\Temp\{6143044D-A0F1-49D7-84EA-0F02B99E0873}\.ba\1036\thm.wxl | xml | |
MD5:7B46AE8698459830A0F9116BC27DE7DF | SHA256:704DDF2E60C1F292BE95C7C79EE48FE8BA8534CEB7CCF9A9EA68B1AD788AE9D4 | |||
| 1104 | VC_redist.x64.exe | C:\Users\admin\AppData\Local\Temp\{6143044D-A0F1-49D7-84EA-0F02B99E0873}\.ba\1028\thm.wxl | xml | |
MD5:472ABBEDCBAD24DBA5B5F5E8D02C340F | SHA256:8E2E660DFB66CB453E17F1B6991799678B1C8B350A55F9EBE2BA0028018A15AD | |||
| 1104 | VC_redist.x64.exe | C:\Users\admin\AppData\Local\Temp\{6143044D-A0F1-49D7-84EA-0F02B99E0873}\.ba\1031\license.rtf | text | |
MD5:C2CFA4CE43DFF1FCD200EDD2B1212F0A | SHA256:F861DB23B972FAAA54520558810387D742878947057CF853DC74E5F6432E6A1B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report