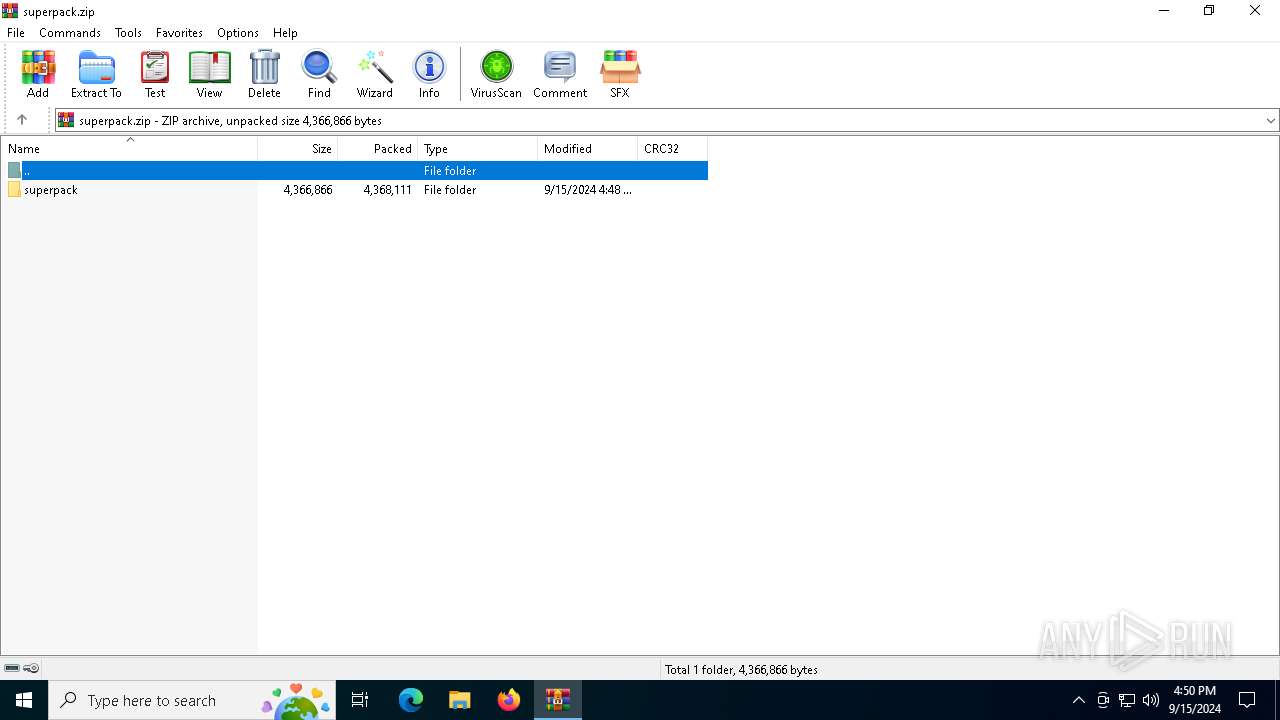
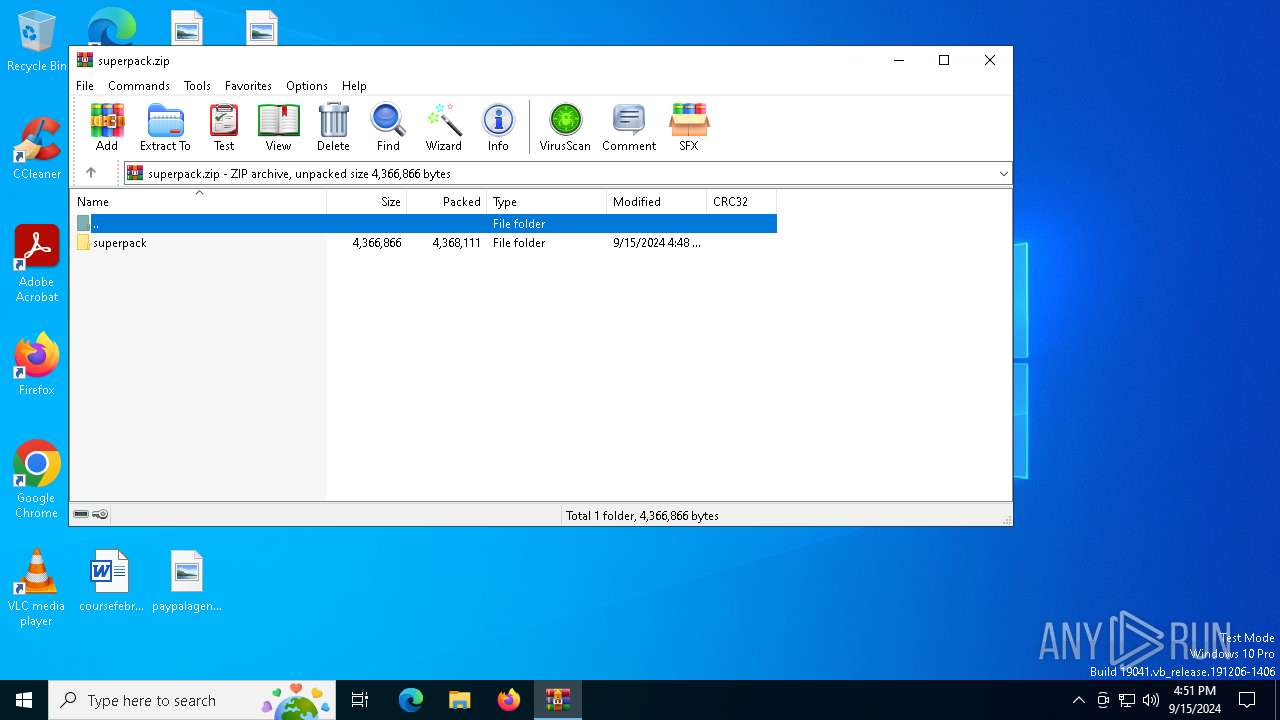
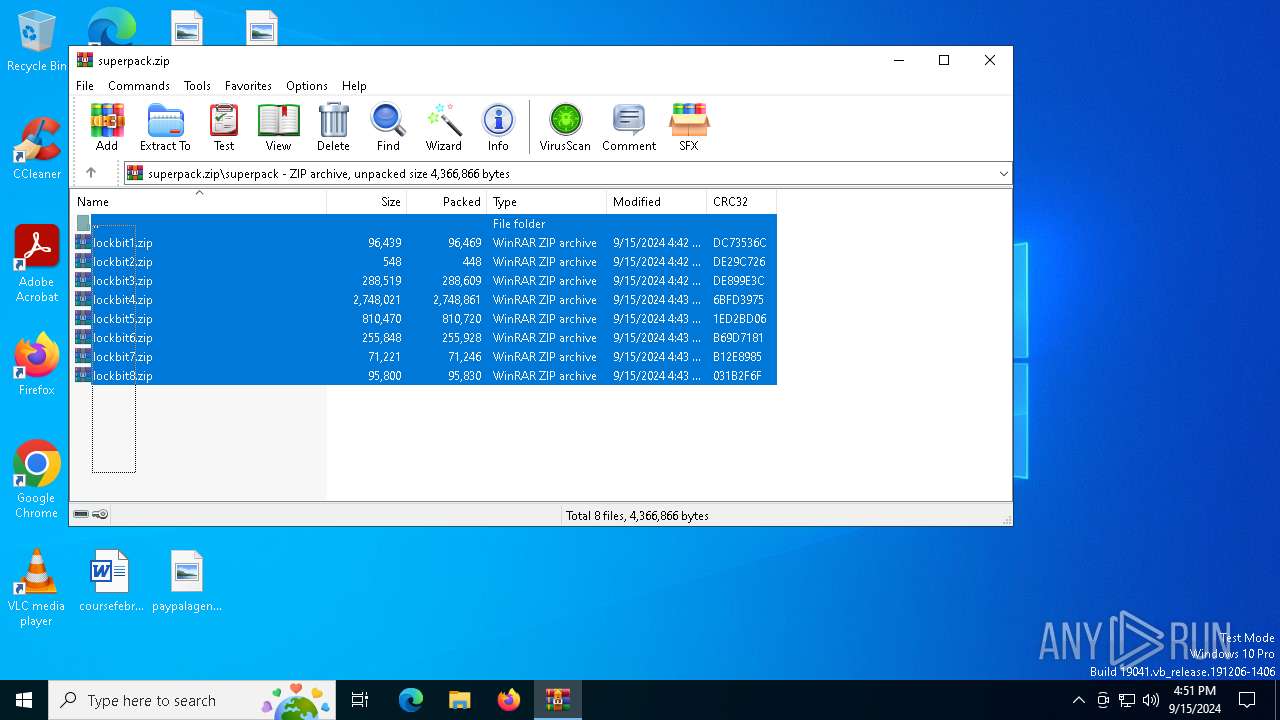
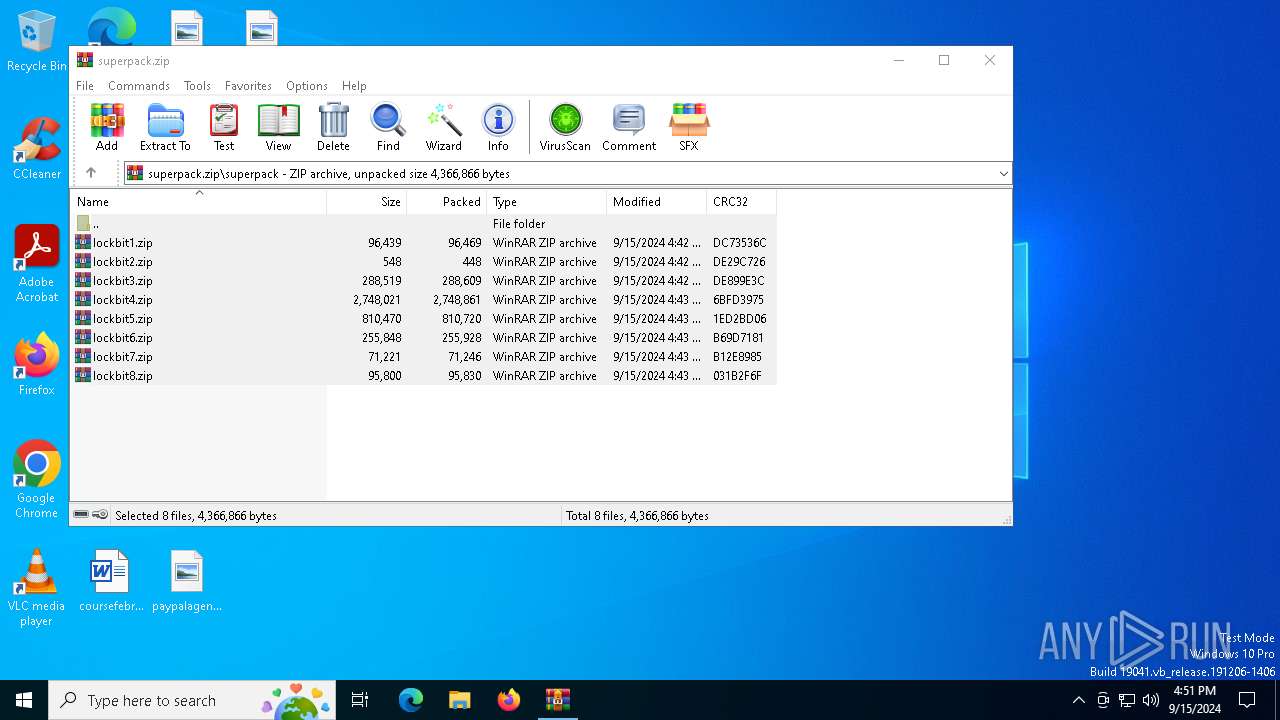
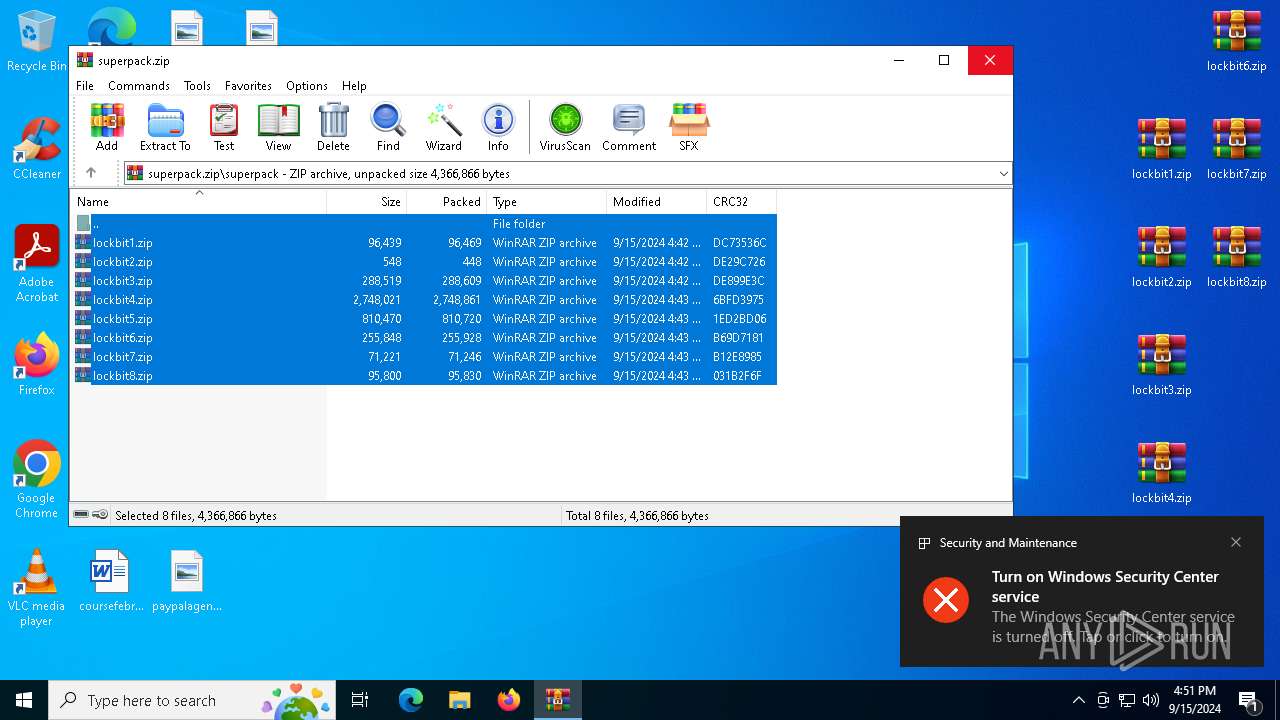
| File name: | superpack.zip |
| Full analysis: | https://app.any.run/tasks/bbffbc22-a279-4f25-b93b-076a40d90837 |
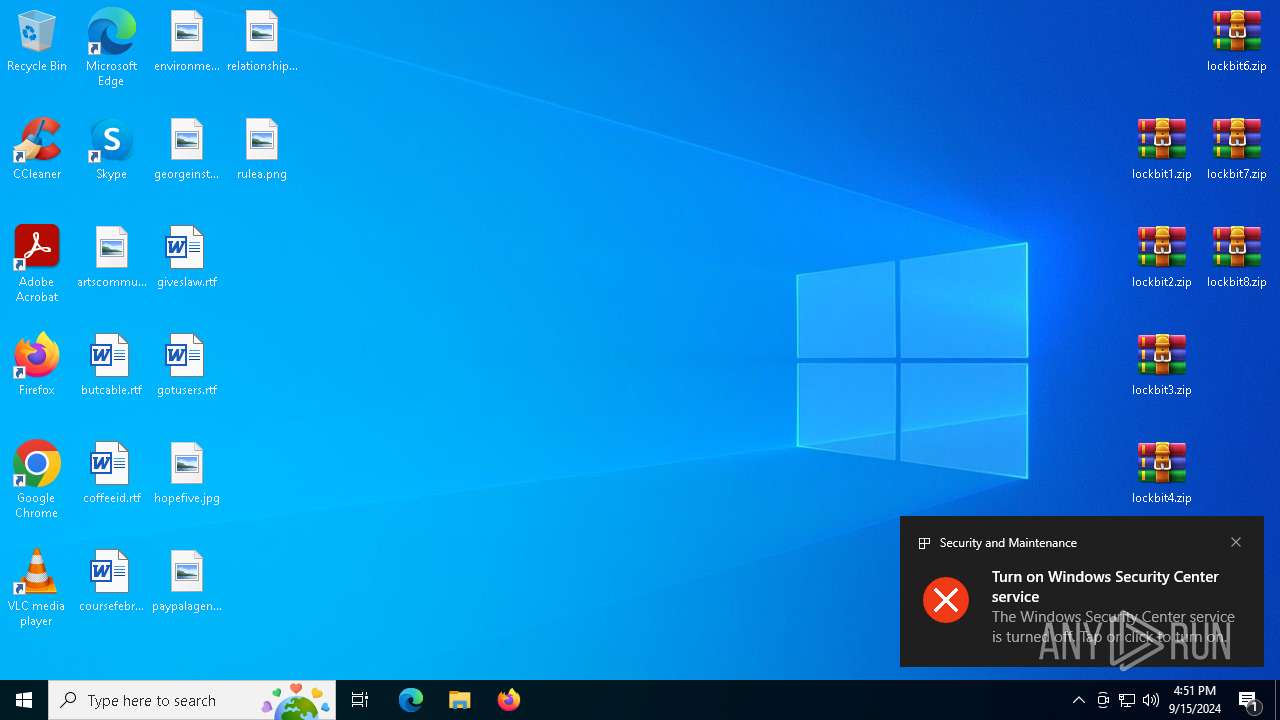
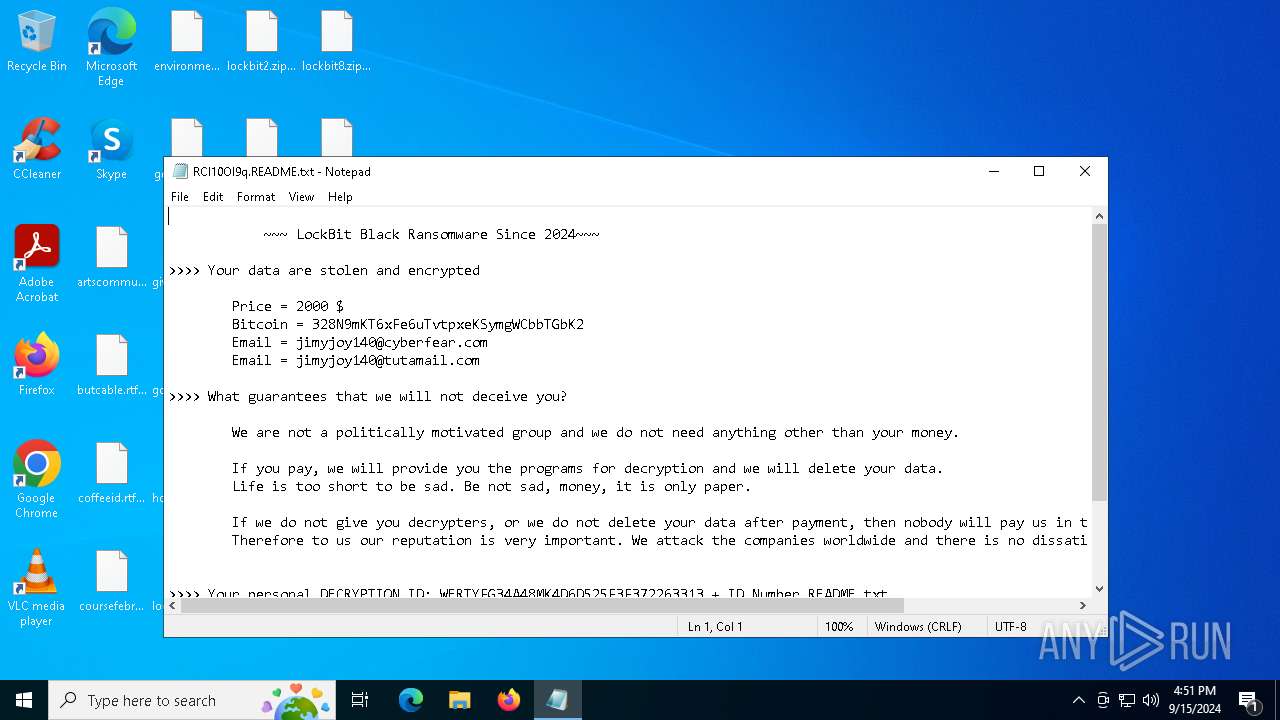
| Verdict: | Malicious activity |
| Threats: | LockBit, a ransomware variant, encrypts data on infected machines, demanding a ransom payment for decryption. Used in targeted attacks, It's a significant risk to organizations. |
| Analysis date: | September 15, 2024, 16:50:48 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | BCD3531661A89662E024A1ACD2D1E575 |
| SHA1: | 171FD7DDAF0893CE0D64669CF96D7AAA952D03AC |
| SHA256: | 4B4555286E0BEB08690A525A51A2B80C0239202EFBBFD8848B4038E71D9E12A9 |
| SSDEEP: | 98304:3xagM0+gSGf9R2yFwzWVLdCz1QFgtjYmuMUtxzXtEdiOB13R8GKAP0oAjVbWpRNP:MRnYw |
MALICIOUS
Known privilege escalation attack
- dllhost.exe (PID: 6684)
Renames files like ransomware
- 105912c9995a1d718c5442349d2cc4bb99426f75ff34554cdfd9a7272eeca398.exe (PID: 7056)
Actions looks like stealing of personal data
- 105912c9995a1d718c5442349d2cc4bb99426f75ff34554cdfd9a7272eeca398.exe (PID: 7056)
Steals credentials from Web Browsers
- 105912c9995a1d718c5442349d2cc4bb99426f75ff34554cdfd9a7272eeca398.exe (PID: 7056)
[YARA] LockBit is detected
- 105912c9995a1d718c5442349d2cc4bb99426f75ff34554cdfd9a7272eeca398.exe (PID: 7056)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3492)
- ShellExperienceHost.exe (PID: 5760)
Write to the desktop.ini file (may be used to cloak folders)
- 105912c9995a1d718c5442349d2cc4bb99426f75ff34554cdfd9a7272eeca398.exe (PID: 7056)
Executable content was dropped or overwritten
- 105912c9995a1d718c5442349d2cc4bb99426f75ff34554cdfd9a7272eeca398.exe (PID: 7056)
INFO
The process uses the downloaded file
- WinRAR.exe (PID: 1156)
- WinRAR.exe (PID: 3492)
- dllhost.exe (PID: 6684)
Manual execution by a user
- WinRAR.exe (PID: 3492)
- notepad.exe (PID: 1748)
- notepad.exe (PID: 2128)
- notepad.exe (PID: 6180)
- notepad.exe (PID: 5988)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3492)
Reads the computer name
- 105912c9995a1d718c5442349d2cc4bb99426f75ff34554cdfd9a7272eeca398.exe (PID: 4668)
- 105912c9995a1d718c5442349d2cc4bb99426f75ff34554cdfd9a7272eeca398.exe (PID: 7056)
- ShellExperienceHost.exe (PID: 5760)
Checks supported languages
- 105912c9995a1d718c5442349d2cc4bb99426f75ff34554cdfd9a7272eeca398.exe (PID: 4668)
- 105912c9995a1d718c5442349d2cc4bb99426f75ff34554cdfd9a7272eeca398.exe (PID: 7056)
- ShellExperienceHost.exe (PID: 5760)
Reads the machine GUID from the registry
- 105912c9995a1d718c5442349d2cc4bb99426f75ff34554cdfd9a7272eeca398.exe (PID: 4668)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 6684)
- notepad.exe (PID: 1748)
- notepad.exe (PID: 2128)
Creates files or folders in the user directory
- 105912c9995a1d718c5442349d2cc4bb99426f75ff34554cdfd9a7272eeca398.exe (PID: 7056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:09:15 17:48:44 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | superpack/ |
Total processes
134
Monitored processes
10
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1156 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\superpack.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1748 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\RCl10Ol9q.README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2128 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\RCl10Ol9q.README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
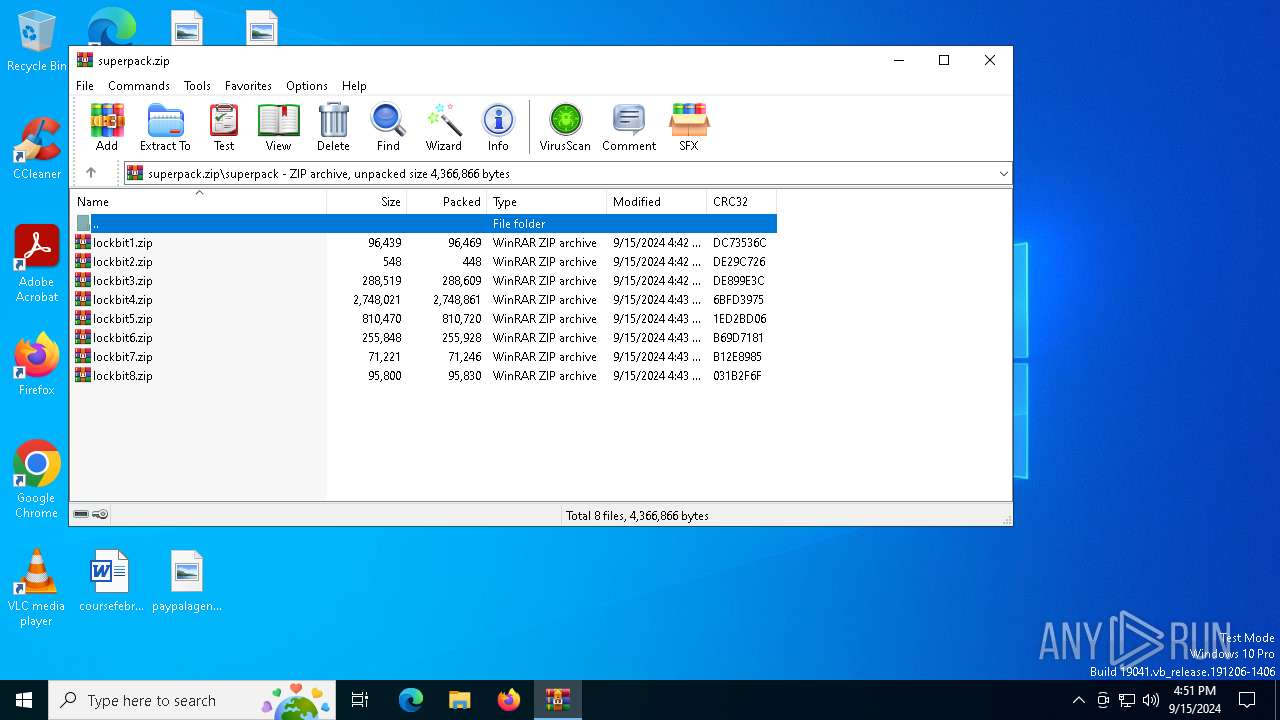
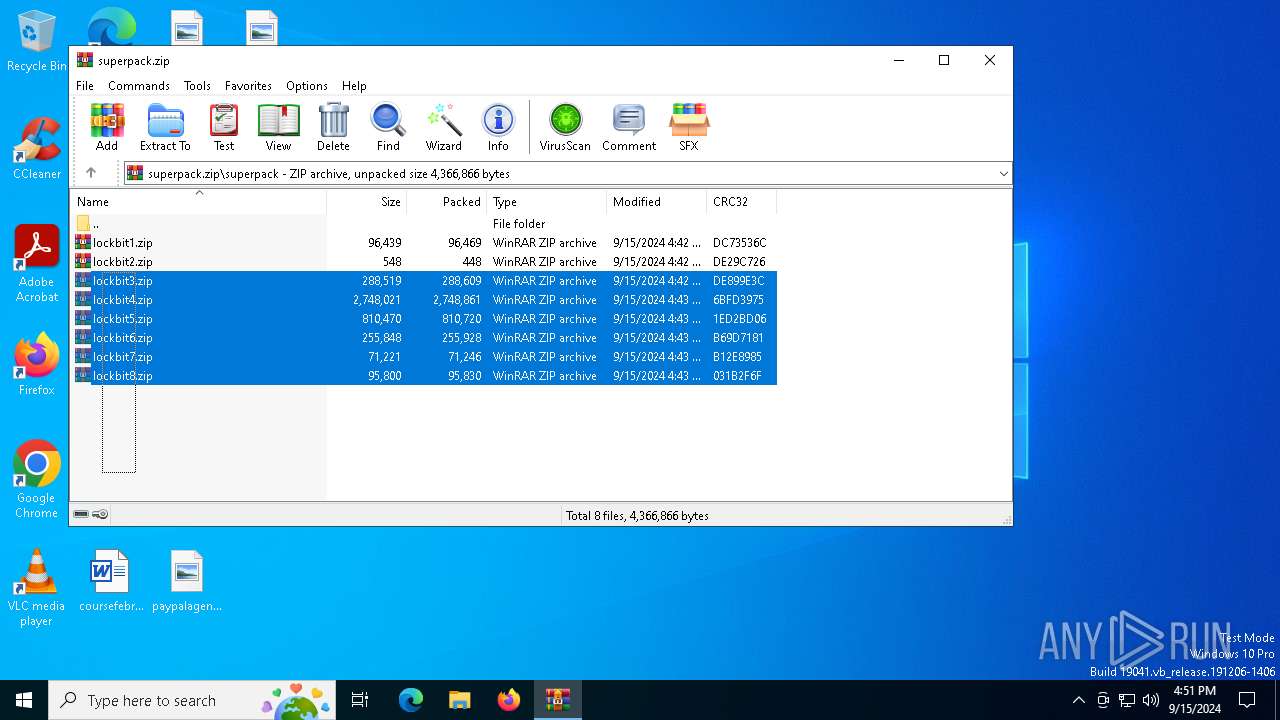
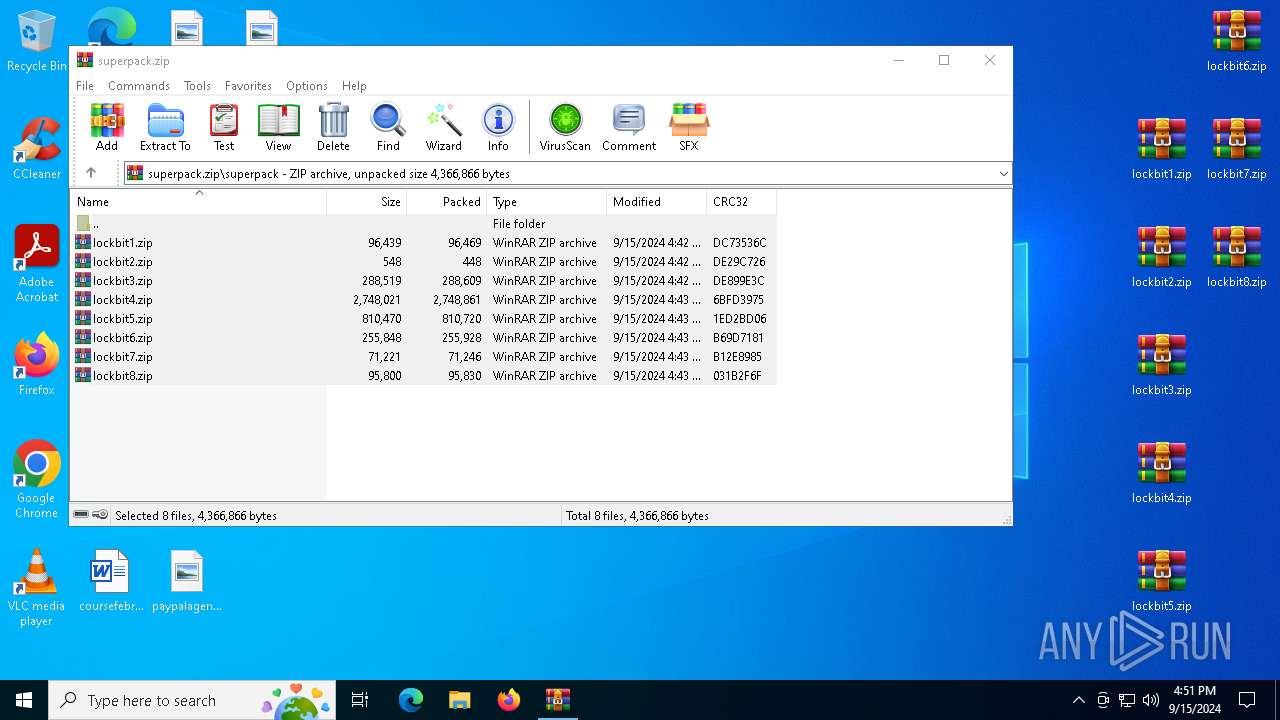
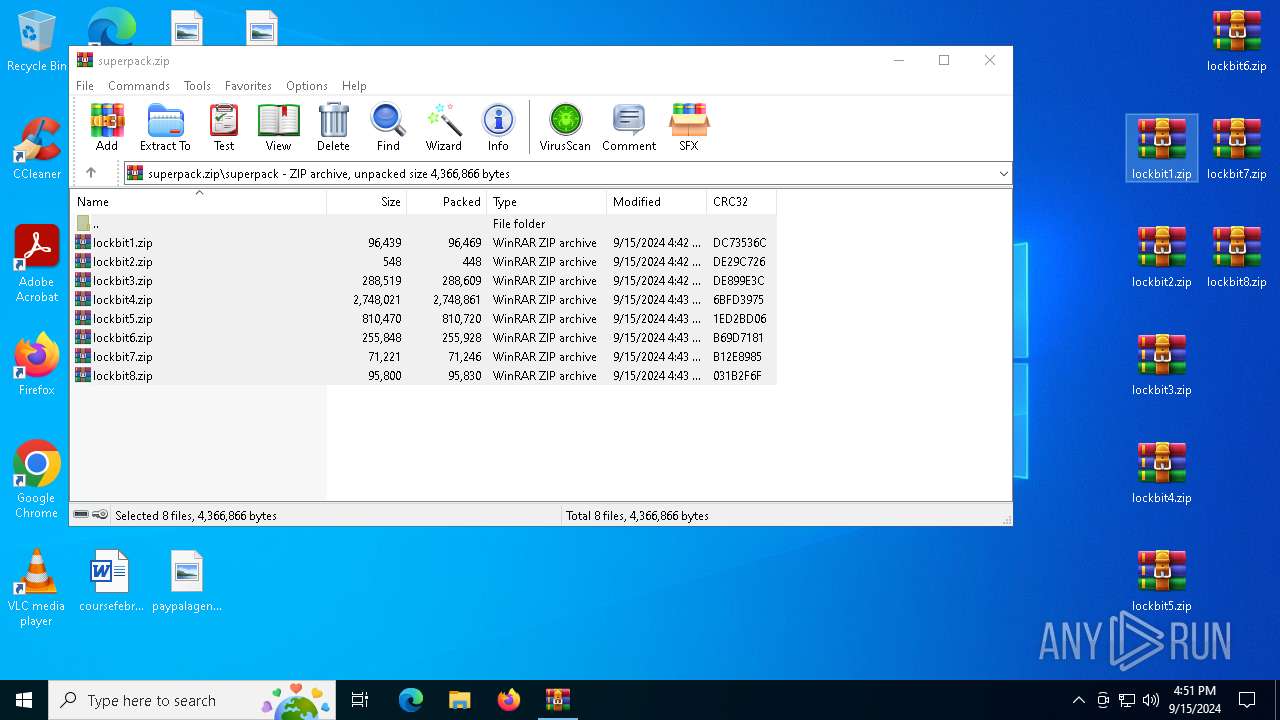
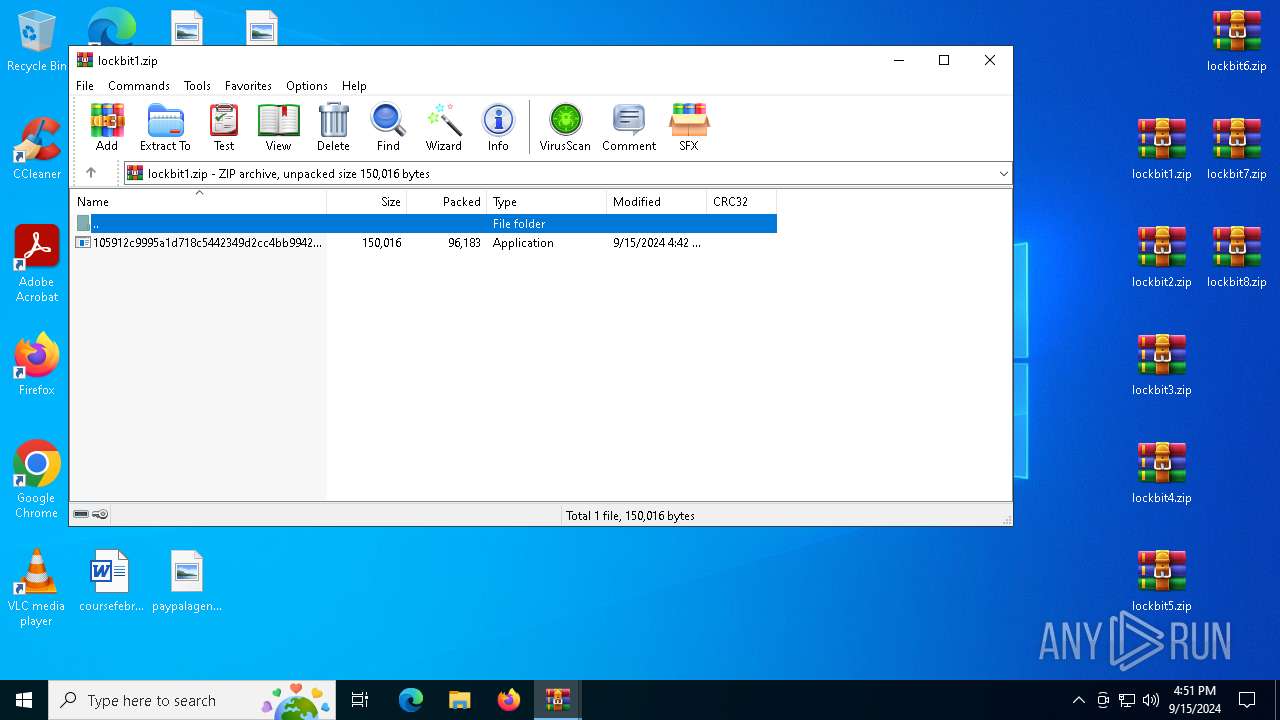
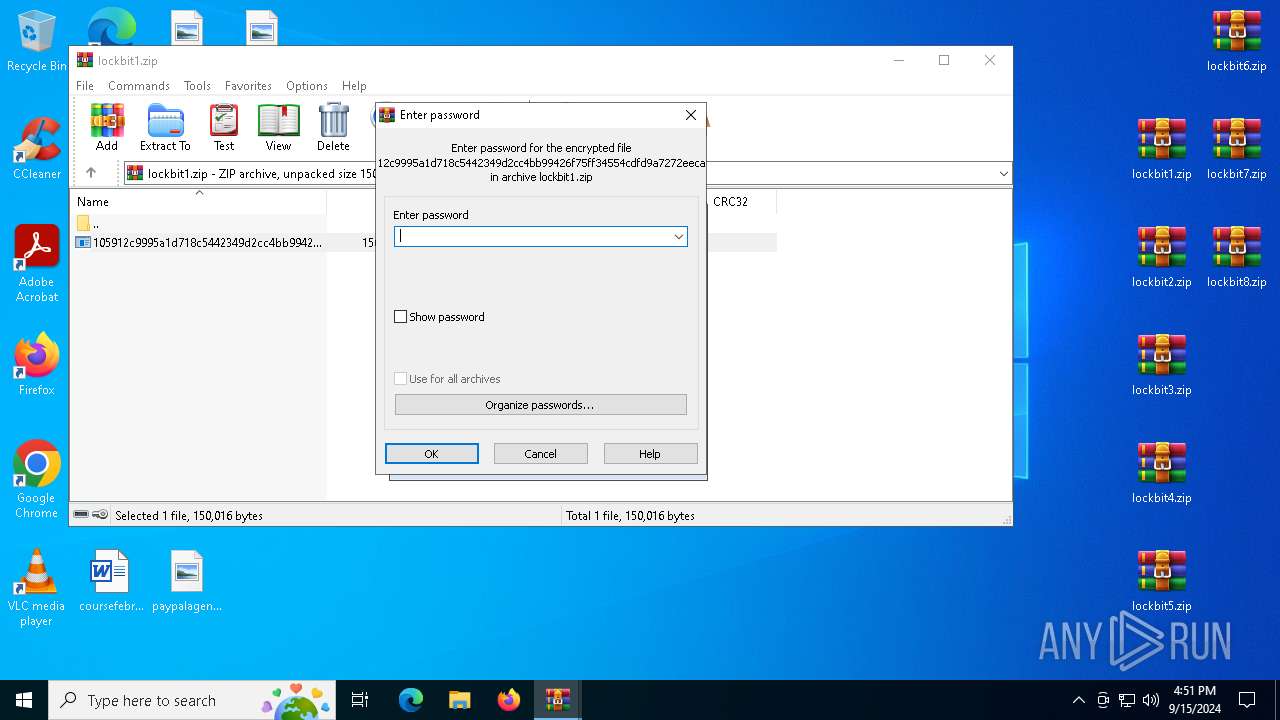
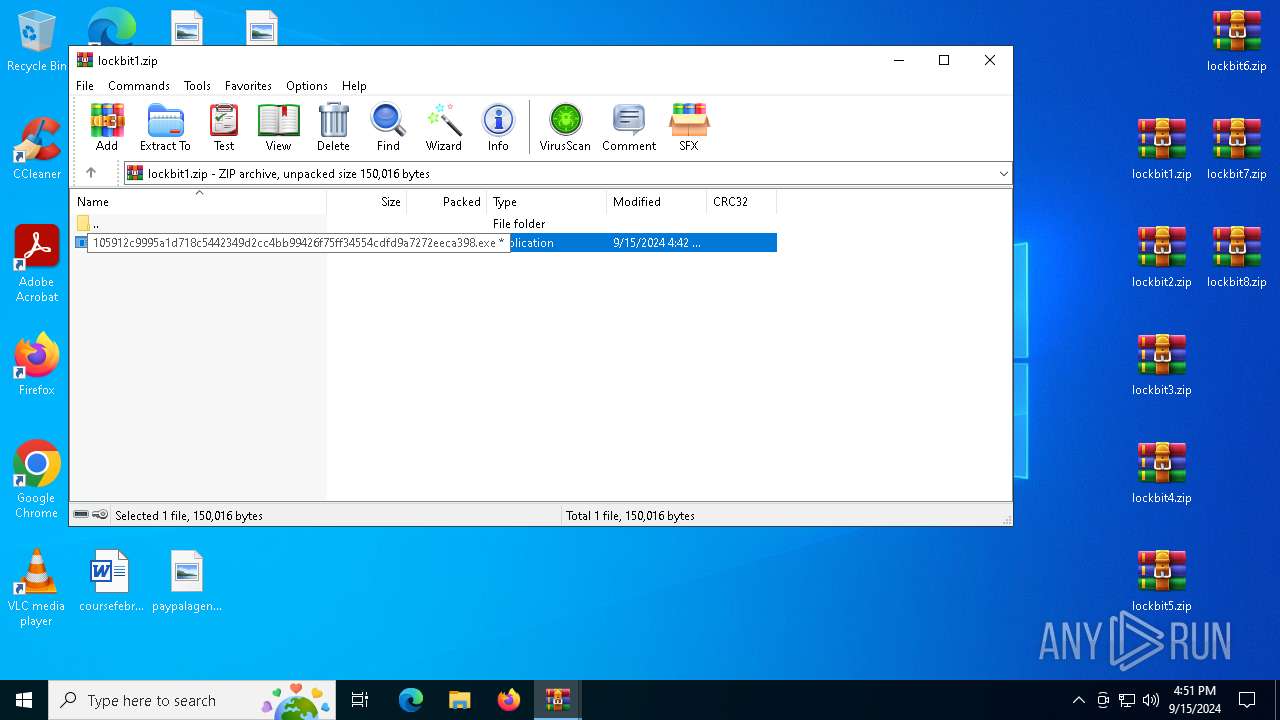
| 3492 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\lockbit1.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 4668 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3492.39131\105912c9995a1d718c5442349d2cc4bb99426f75ff34554cdfd9a7272eeca398.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb3492.39131\105912c9995a1d718c5442349d2cc4bb99426f75ff34554cdfd9a7272eeca398.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5760 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5988 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\RCl10Ol9q.README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6180 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\RCl10Ol9q.README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6684 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\SysWOW64\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7056 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3492.39131\105912c9995a1d718c5442349d2cc4bb99426f75ff34554cdfd9a7272eeca398.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb3492.39131\105912c9995a1d718c5442349d2cc4bb99426f75ff34554cdfd9a7272eeca398.exe | dllhost.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
Total events
5 497
Read events
5 460
Write events
37
Delete events
0
Modification events
| (PID) Process: | (1156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (1156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\superpack.zip | |||
| (PID) Process: | (1156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3492) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (3492) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\AppData\Local\Temp\superpack.zip | |||
| (PID) Process: | (3492) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\lockbit1.zip | |||
| (PID) Process: | (3492) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
Executable files
15
Suspicious files
467
Text files
532
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1156 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1156.38198\superpack\lockbit7.zip | compressed | |
MD5:217B3CD4A1C25C850602D6603E174599 | SHA256:342C7D2EEE21EA2586D240EE41BBB2FEB8C0E299A7DACDE4159A121F09AB5009 | |||
| 1156 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1156.38198\superpack\lockbit2.zip | compressed | |
MD5:288F6C5C1177E30D3E03B4E8A9B762BF | SHA256:55AC0CB2701ACC1BC2F5FCD7A823305612DC8EE2F329B29558852A31FDBDEB2F | |||
| 1156 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1156.38198\superpack\lockbit5.zip | compressed | |
MD5:101AB20C7BBA226D9D7E70BA2EA99BC8 | SHA256:DB5F6D69DAA363E367FCC74A6B5A209145F06F3ED94A582BB54CF22DB9A9F99F | |||
| 1156 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1156.38198\superpack\lockbit3.zip | compressed | |
MD5:10F4DB773C0827AF410523BCC6B29A5A | SHA256:3BFAE6517313E00B392B7391D091E95CF456950F60A598624E2D0170747F6615 | |||
| 1156 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1156.38198\superpack\lockbit4.zip | compressed | |
MD5:A9AC295E3C12E32985AADEAED78D3591 | SHA256:9E296B10C5C34881B13713E80FE2BE8FB1C1AC3E0930F71B37F448F93E15BFF3 | |||
| 1156 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1156.38198\superpack\lockbit6.zip | compressed | |
MD5:90533BFC7FE1AE3A20CBBA633CC8B6C4 | SHA256:67E10C5EDD46DF5582147C57C1122CDCFAD8FE42B635B358E75FFED02739EB0B | |||
| 1156 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1156.38198\superpack\lockbit1.zip | compressed | |
MD5:6BDB9E9ABC35BC32E5AFBCCF6F8D076F | SHA256:9E0522220D755C944CAD04E59DD5B7EF9202CA35E62FA87F2DF436226CCAC6F8 | |||
| 7056 | 105912c9995a1d718c5442349d2cc4bb99426f75ff34554cdfd9a7272eeca398.exe | C:\$Recycle.Bin\S-1-5-18\EEEEEEEEEEE | binary | |
MD5:694CBACCF8A71B51385FCCD21E1FF698 | SHA256:C761DEDA83DFA61D9E444B005C5D51BE4F6BB5E0BF406CAA3D1E3E2F336BA064 | |||
| 7056 | 105912c9995a1d718c5442349d2cc4bb99426f75ff34554cdfd9a7272eeca398.exe | C:\$Recycle.Bin\S-1-5-18\FFFFFFFFFFF | binary | |
MD5:694CBACCF8A71B51385FCCD21E1FF698 | SHA256:C761DEDA83DFA61D9E444B005C5D51BE4F6BB5E0BF406CAA3D1E3E2F336BA064 | |||
| 7056 | 105912c9995a1d718c5442349d2cc4bb99426f75ff34554cdfd9a7272eeca398.exe | C:\$Recycle.Bin\S-1-5-18\GGGGGGGGGGG | binary | |
MD5:694CBACCF8A71B51385FCCD21E1FF698 | SHA256:C761DEDA83DFA61D9E444B005C5D51BE4F6BB5E0BF406CAA3D1E3E2F336BA064 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
30
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7164 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7164 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6056 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6424 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 20.190.159.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3424 | svchost.exe | 20.190.159.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |