| File name: | yamlloadobf.exe |
| Full analysis: | https://app.any.run/tasks/5d0ff0cf-51a3-4c07-aeed-4e32dd6db802 |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 10:10:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | 1C10AD4521E5FB61B926F6185E3CA374 |
| SHA1: | 1BD4D7984279943731B6C46E50C8809470AC3DC0 |
| SHA256: | 4B3408970E43EF513F0B0F20B86DF10EADDED7537153A5F7A1928CB17C8EAE0E |
| SSDEEP: | 98304:kJ37WTsuDacbtDjHk9IRQJ+FgLHIcc1Umb1f83qgL/v1D0WRBUBY+E+b5dUJRw2l:d2OaZ2YBAHzcuXACN |
MALICIOUS
Creates a new folder (SCRIPT)
- wscript.exe (PID: 672)
SUSPICIOUS
Process drops python dynamic module
- yamlloadobf.exe (PID: 1532)
Process drops legitimate windows executable
- yamlloadobf.exe (PID: 1532)
Application launched itself
- yamlloadobf.exe (PID: 1532)
Executable content was dropped or overwritten
- yamlloadobf.exe (PID: 1532)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 672)
The process drops C-runtime libraries
- yamlloadobf.exe (PID: 1532)
Loads Python modules
- yamlloadobf.exe (PID: 6388)
The process executes VB scripts
- yamlloadobf.exe (PID: 6388)
Runs shell command (SCRIPT)
- wscript.exe (PID: 672)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 672)
Potential Corporate Privacy Violation
- yamlloadobf.exe (PID: 6388)
INFO
The sample compiled with english language support
- yamlloadobf.exe (PID: 1532)
Reads the computer name
- yamlloadobf.exe (PID: 1532)
Checks supported languages
- yamlloadobf.exe (PID: 1532)
Create files in a temporary directory
- yamlloadobf.exe (PID: 1532)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 5868)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 5332)
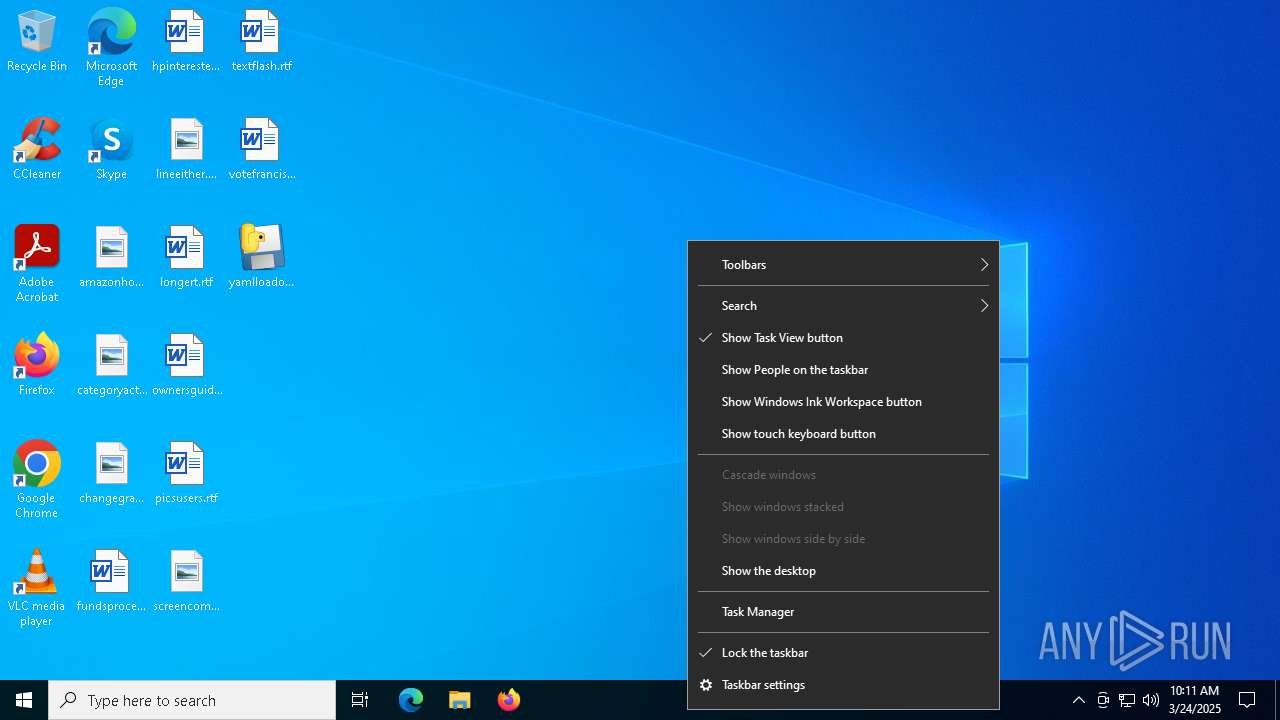
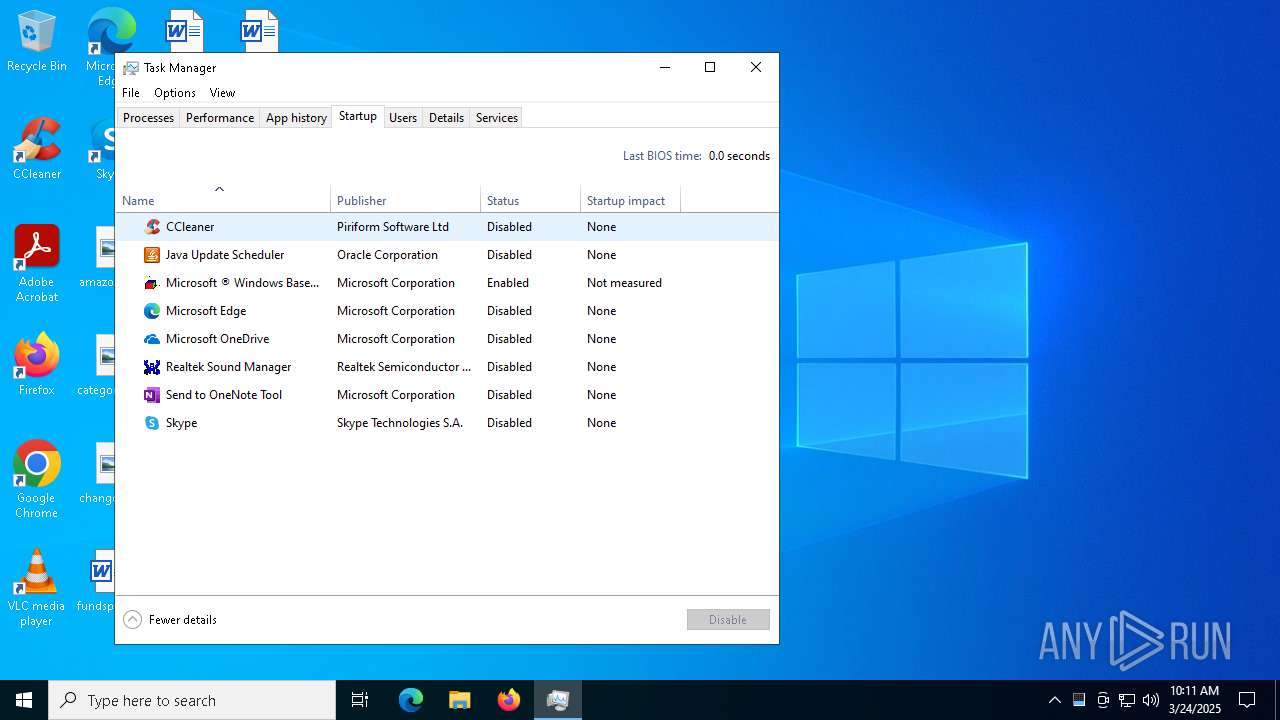
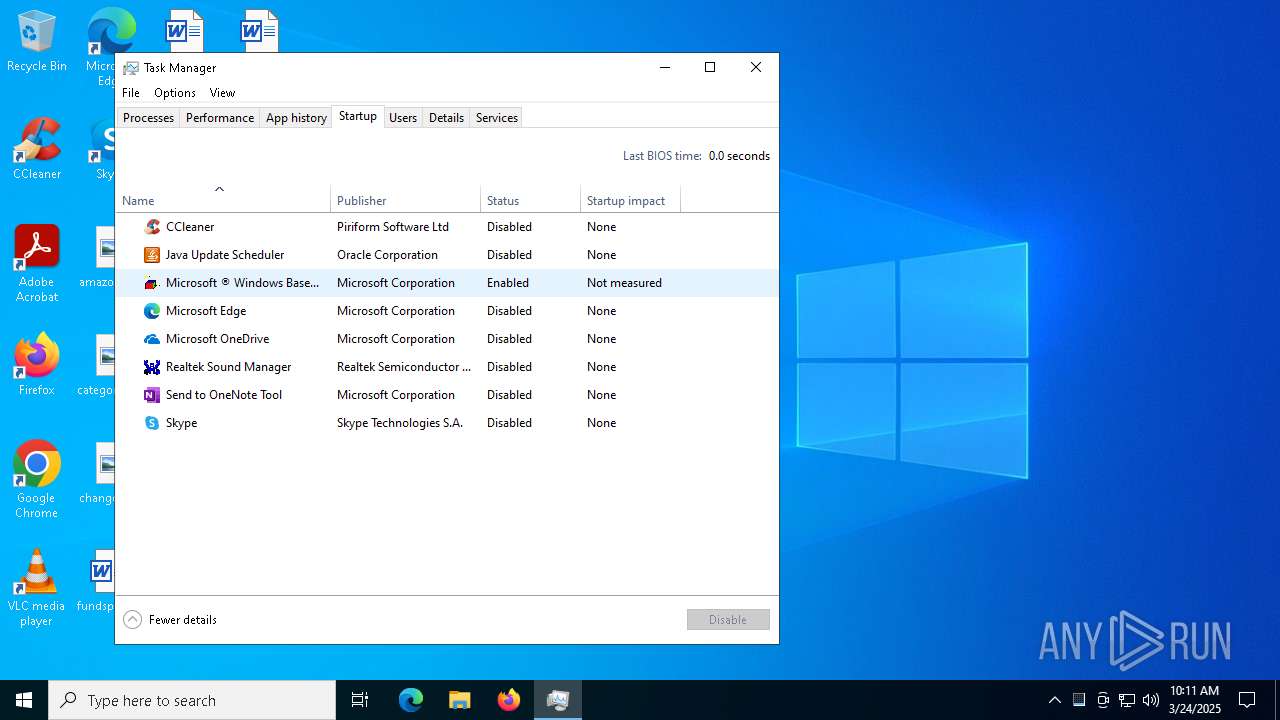
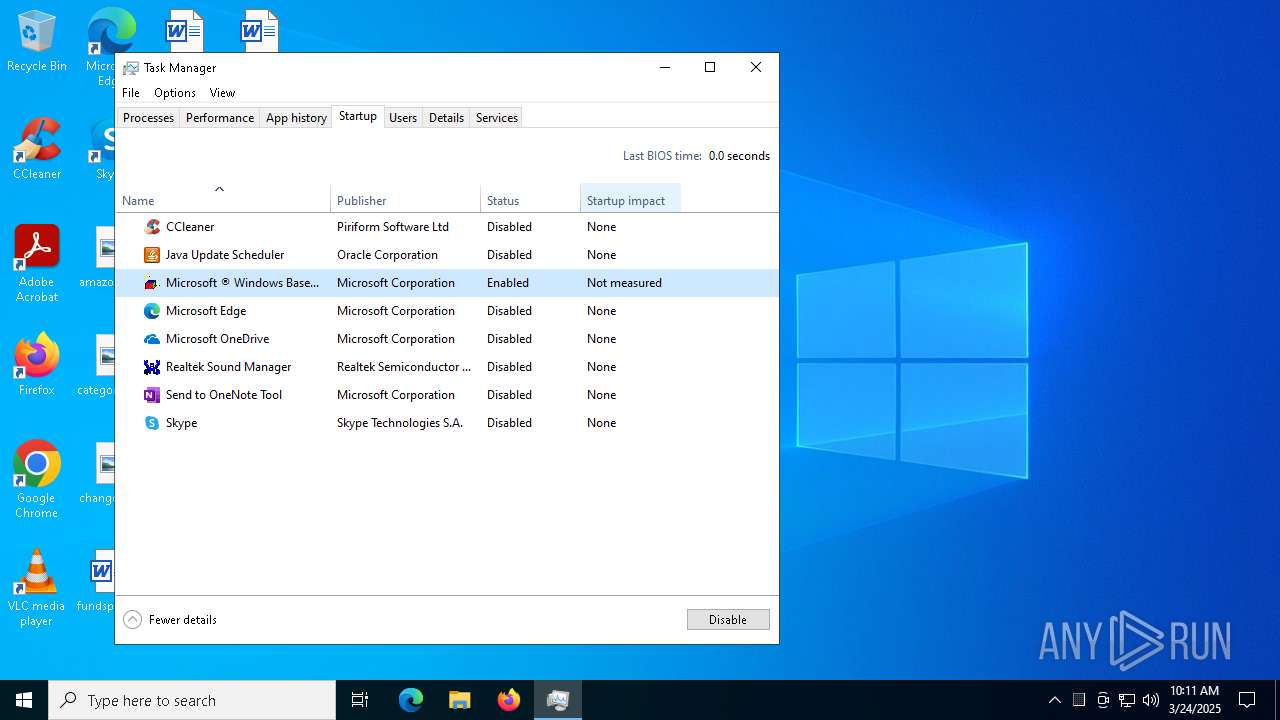
Manual execution by a user
- Taskmgr.exe (PID: 6032)
- Taskmgr.exe (PID: 4112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (57.6) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.9) |
| .exe | | | Generic Win/DOS Executable (2.6) |
| .exe | | | DOS Executable Generic (2.6) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:03:24 01:36:44+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.41 |
| CodeSize: | 172032 |
| InitializedDataSize: | 154624 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xce20 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
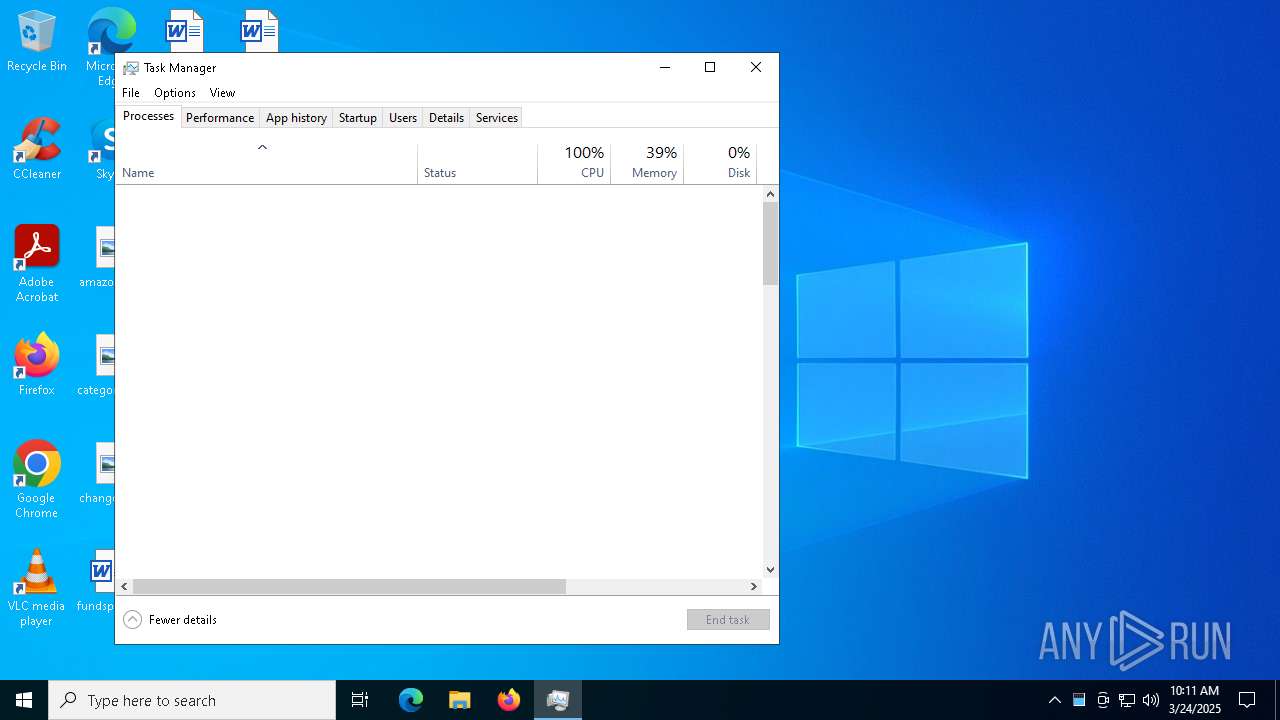
Total processes
141
Monitored processes
12
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 672 | wscript hidden.vbs | C:\Windows\System32\wscript.exe | — | yamlloadobf.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 904 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | "C:\Users\admin\Desktop\yamlloadobf.exe" | C:\Users\admin\Desktop\yamlloadobf.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3008 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4112 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4628 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5164 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5332 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5868 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 325
Read events
5 297
Write events
27
Delete events
1
Modification events
| (PID) Process: | (904) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (904) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (904) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5868) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5868) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5868) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3008) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3008) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3008) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5332) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
60
Suspicious files
7
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1532 | yamlloadobf.exe | C:\Users\admin\AppData\Local\Temp\_MEI15322\api-ms-win-core-console-l1-1-0.dll | executable | |
MD5:9313C86E7BAE859F0174A1C8B6ABA58B | SHA256:AF9675AC90BAE8A0D8623F6FDAFF9D39E1B8810E8E46A5B044BAAA3396E745B3 | |||
| 1532 | yamlloadobf.exe | C:\Users\admin\AppData\Local\Temp\_MEI15322\_queue.pyd | executable | |
MD5:F00133F7758627A15F2D98C034CF1657 | SHA256:35609869EDC57D806925EC52CCA9BC5A035E30D5F40549647D4DA6D7983F8659 | |||
| 1532 | yamlloadobf.exe | C:\Users\admin\AppData\Local\Temp\_MEI15322\_socket.pyd | executable | |
MD5:1EEA9568D6FDEF29B9963783827F5867 | SHA256:74181072392A3727049EA3681FE9E59516373809CED53E08F6DA7C496B76E117 | |||
| 1532 | yamlloadobf.exe | C:\Users\admin\AppData\Local\Temp\_MEI15322\_decimal.pyd | executable | |
MD5:65B4AB77D6C6231C145D3E20E7073F51 | SHA256:93EB9D1859EDCA1C29594491863BF3D72AF70B9A4240E0D9DD171F668F4F8614 | |||
| 1532 | yamlloadobf.exe | C:\Users\admin\AppData\Local\Temp\_MEI15322\_ssl.pyd | executable | |
MD5:208B0108172E59542260934A2E7CFA85 | SHA256:5160500474EC95D4F3AF7E467CC70CB37BEC1D12545F0299AAB6D69CEA106C69 | |||
| 1532 | yamlloadobf.exe | C:\Users\admin\AppData\Local\Temp\_MEI15322\_lzma.pyd | executable | |
MD5:E5ABC3A72996F8FDE0BCF709E6577D9D | SHA256:1796038480754A680F33A4E37C8B5673CC86C49281A287DC0C5CAE984D0CB4BB | |||
| 1532 | yamlloadobf.exe | C:\Users\admin\AppData\Local\Temp\_MEI15322\api-ms-win-core-file-l1-2-0.dll | executable | |
MD5:4A060EEC454C222A5381CD359DC00B81 | SHA256:E6B2B05E14A6C6F5381E8F4C7F4FD28A499246FB4C8EAFE1F08014B9273D70DF | |||
| 1532 | yamlloadobf.exe | C:\Users\admin\AppData\Local\Temp\_MEI15322\api-ms-win-core-errorhandling-l1-1-0.dll | executable | |
MD5:12EA48CE605EBB204A21AE7D86DB3417 | SHA256:189BBBD739526A986E53518865E741CDE8C5967AACD5ED687408CEC3D8781F1C | |||
| 1532 | yamlloadobf.exe | C:\Users\admin\AppData\Local\Temp\_MEI15322\api-ms-win-core-file-l1-1-0.dll | executable | |
MD5:4B328F140A3AE7FEDB21CA50CC23D938 | SHA256:E55B200643E8B078E7F5EB0C97DE44FEAD21B11D06590EBEDBCB84214D063345 | |||
| 1532 | yamlloadobf.exe | C:\Users\admin\AppData\Local\Temp\_MEI15322\api-ms-win-core-datetime-l1-1-0.dll | executable | |
MD5:854458AD55C39A9DFD1E350A51BE02B8 | SHA256:F918B0C45F59B2CB29F1EB3653D2F2679095E85E082A1198C933A76EDF1F33EF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
23
DNS requests
12
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.41.90:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.53.41.90:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6388 | yamlloadobf.exe | GET | 200 | 194.197.245.5:80 | http://194.197.245.5/tiev21p/juuso/payloads.yaml | unknown | — | — | unknown |
5164 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5868 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6668 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6668 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.53.41.90:80 | — | Akamai International B.V. | DE | unknown |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3216 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
6388 | yamlloadobf.exe | 194.197.245.5:80 | — | Telia Finland Oyj | FI | unknown |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5164 | backgroundTaskHost.exe | 20.74.47.205:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5164 | backgroundTaskHost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6388 | yamlloadobf.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Python Suspicious User Agent |
6388 | yamlloadobf.exe | A Network Trojan was detected | SUSPICIOUS [ANY.RUN] VBS is used to run Shell |