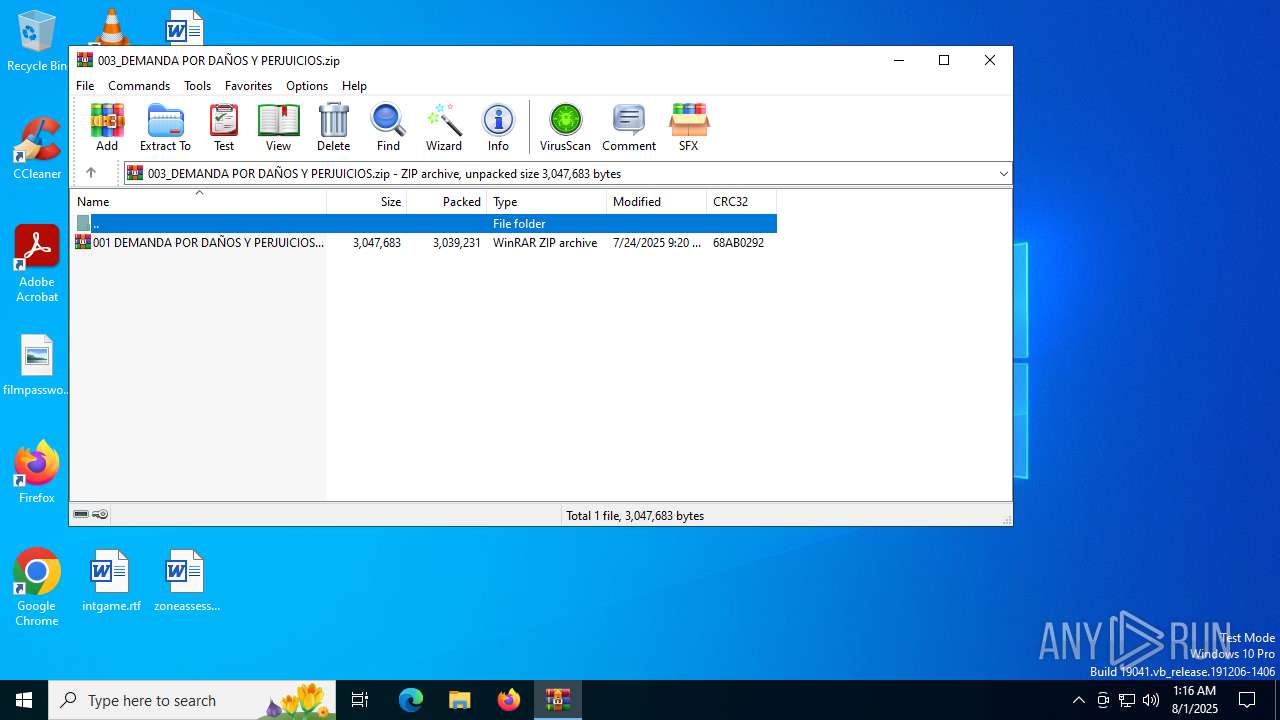
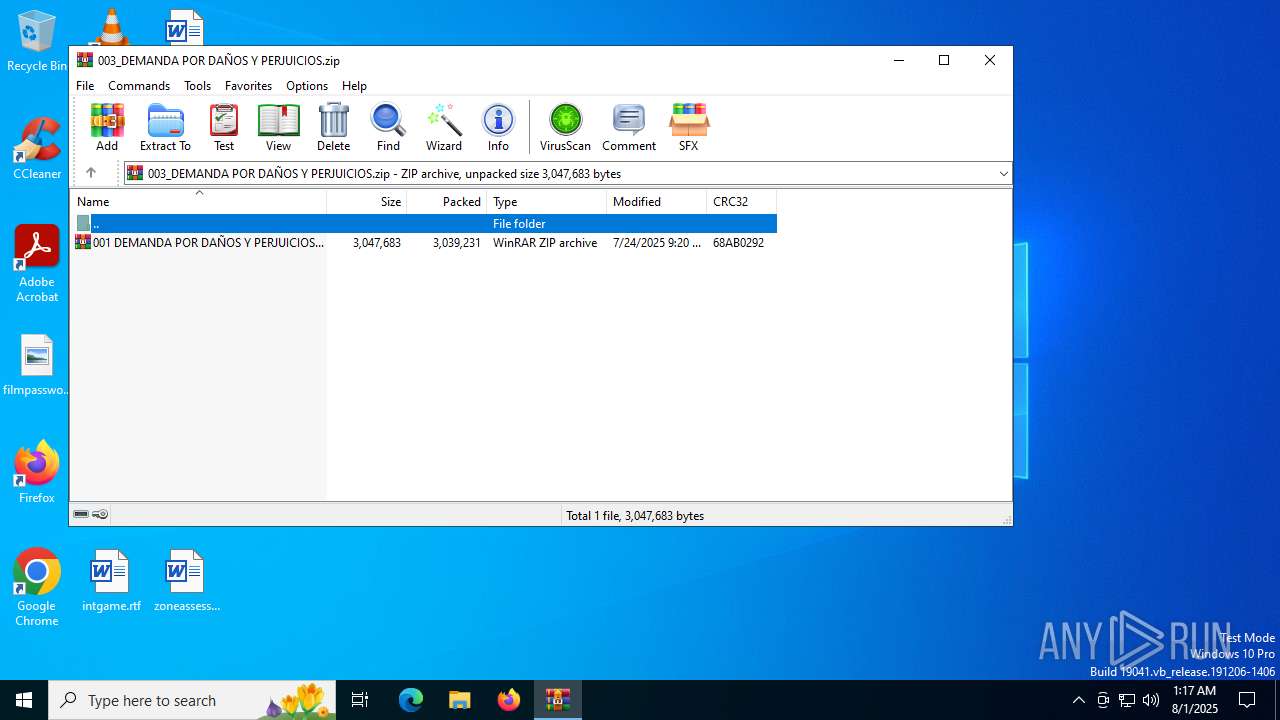
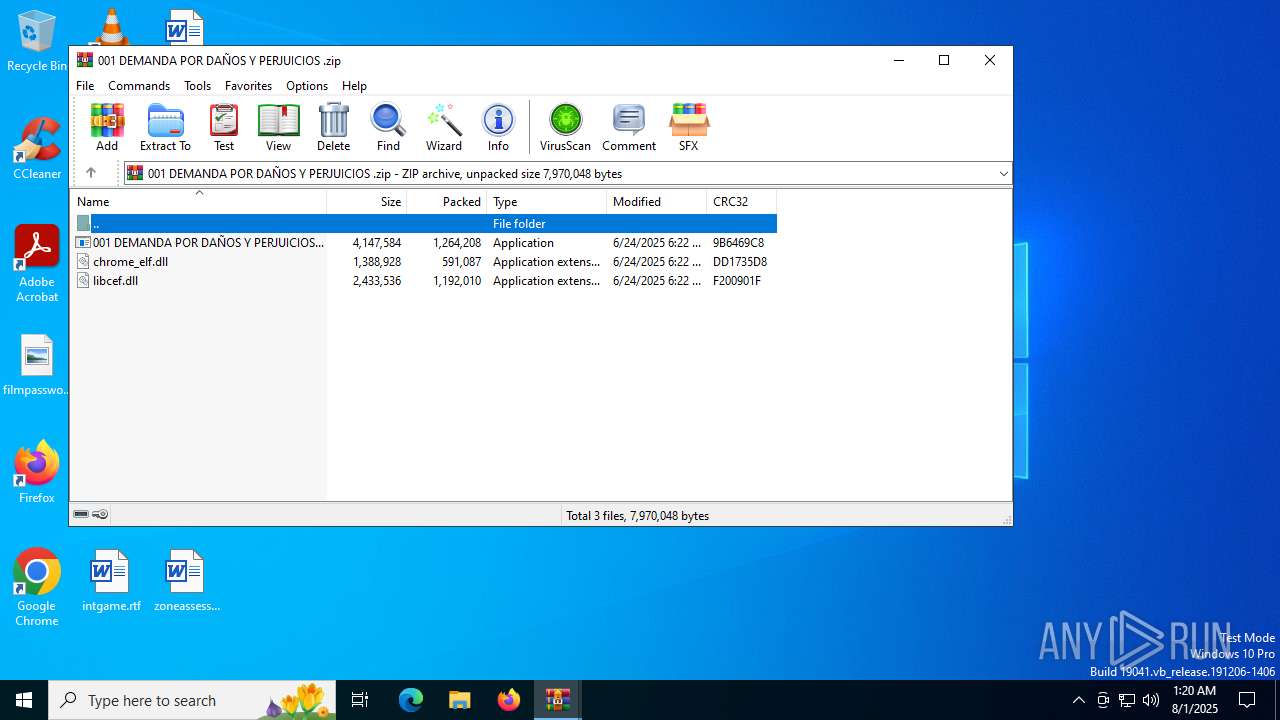
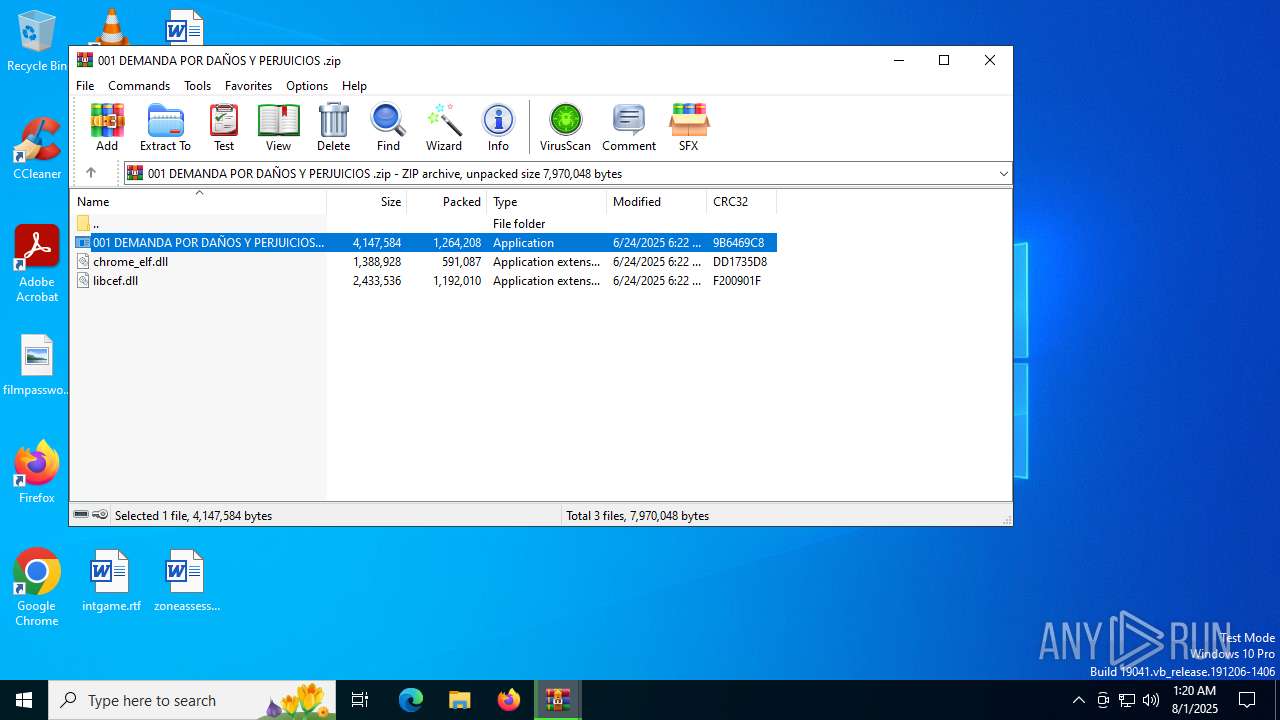
| File name: | 003_DEMANDA POR DAÑOS Y PERJUICIOS.zip |
| Full analysis: | https://app.any.run/tasks/6e496f0c-6a0e-450c-82c2-804368180ac3 |
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2025, 01:16:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 58C005F64F9423AFF1ED5AB021DE254C |
| SHA1: | C73DF86A2BF01C17558496E810786503BD42B08D |
| SHA256: | 4B336A687EFE5127F928D6F9530DEE1F0E2828974EFCACE35DD68106DE476ED3 |
| SSDEEP: | 98304:xS3peSdapLkdqxQcxvlNcbOI0NAbtov/GtbbT8jRtdm4pp5UjbdB+nSw8B4aV3cx:5spyX |
MALICIOUS
Changes the autorun value in the registry
- reg.exe (PID: 5496)
NESHTA mutex has been found
- aspnet_wp.exe (PID: 7016)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7032)
- WinRAR.exe (PID: 1324)
Application launched itself
- WinRAR.exe (PID: 1324)
Uses REG/REGEDIT.EXE to modify registry
- 001 DEMANDA POR DAÑOS Y PERJUICIOS .exe (PID: 4748)
Executable content was dropped or overwritten
- 001 DEMANDA POR DAÑOS Y PERJUICIOS .exe (PID: 4748)
- aspnet_wp.exe (PID: 7016)
Mutex name with non-standard characters
- aspnet_wp.exe (PID: 7016)
Process drops legitimate windows executable
- aspnet_wp.exe (PID: 7016)
INFO
Reads the software policy settings
- slui.exe (PID: 7004)
Checks proxy server information
- slui.exe (PID: 7004)
The sample compiled with english language support
- 001 DEMANDA POR DAÑOS Y PERJUICIOS .exe (PID: 4748)
- WinRAR.exe (PID: 1324)
- WinRAR.exe (PID: 7032)
- aspnet_wp.exe (PID: 7016)
Checks supported languages
- 001 DEMANDA POR DAÑOS Y PERJUICIOS .exe (PID: 4748)
- aspnet_wp.exe (PID: 7016)
Reads the computer name
- 001 DEMANDA POR DAÑOS Y PERJUICIOS .exe (PID: 4748)
Launching a file from a Registry key
- reg.exe (PID: 5496)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7032)
Create files in a temporary directory
- aspnet_wp.exe (PID: 7016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0809 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:07:24 09:20:48 |
| ZipCRC: | 0x68ab0292 |
| ZipCompressedSize: | 3039231 |
| ZipUncompressedSize: | 3047683 |
| ZipFileName: | 001 DEMANDA POR DA?OS Y PERJUICIOS .zip |
Total processes
150
Monitored processes
8
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
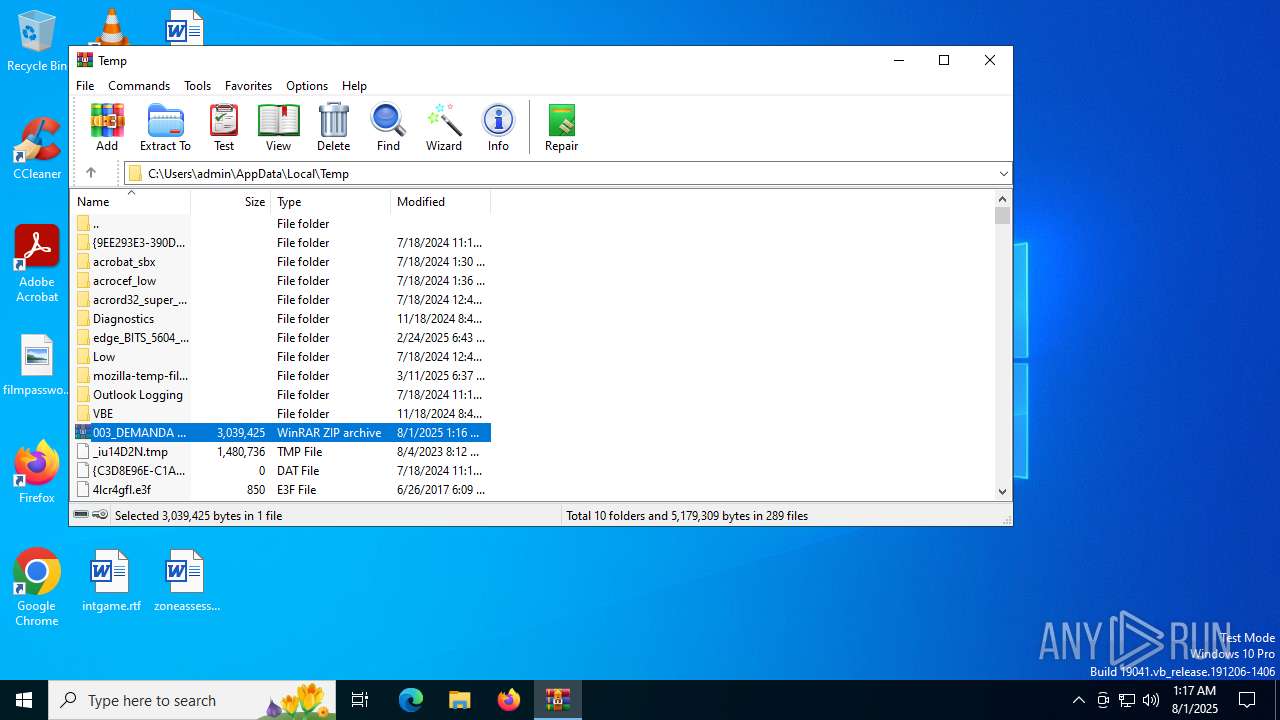
| 1324 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\003_DEMANDA POR DAÑOS Y PERJUICIOS.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
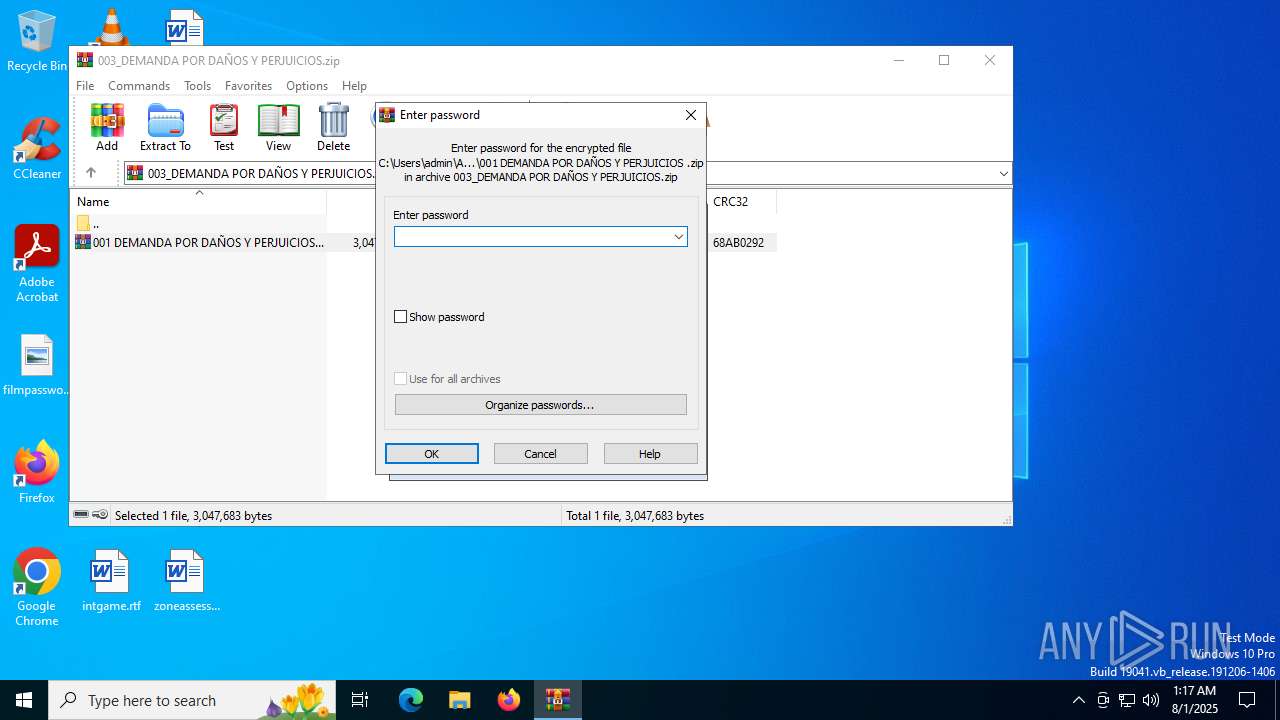
| 4748 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7032.3470\001 DEMANDA POR DAÑOS Y PERJUICIOS .exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7032.3470\001 DEMANDA POR DAÑOS Y PERJUICIOS .exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Server with Chromium Embedded Framework Exit code: 4294967295 Version: 122.1.9.1014+g7a7b938 Modules
| |||||||||||||||
| 5300 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 001 DEMANDA POR DAÑOS Y PERJUICIOS .exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5496 | "reg.exe" add HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v "001 DEMANDA POR DAÑOS Y PERJUICIOS " /t REG_SZ /d "cmd.exe /C start \"\" /D \"C:\Users\admin\AllowLeadingSignICustomQueryInterfacegetLatin1\" \"C:\Users\admin\AllowLeadingSignICustomQueryInterfacegetLatin1\001 DEMANDA POR DAÑOS Y PERJUICIOS .exe\"" /f | C:\Windows\System32\reg.exe | 001 DEMANDA POR DAÑOS Y PERJUICIOS .exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6808 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7004 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7016 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_wp.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_wp.exe | 001 DEMANDA POR DAÑOS Y PERJUICIOS .exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_wp.exe Exit code: 0 Version: 4.8.9220.0 built by: NET481REL1LAST_C Modules
| |||||||||||||||
| 7032 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIb1324.36181\001 DEMANDA POR DAÑOS Y PERJUICIOS .zip" | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
9 604
Read events
9 573
Write events
31
Delete events
0
Modification events
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\003_DEMANDA POR DAÑOS Y PERJUICIOS.zip | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
13
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7032 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7032.3470\001 DEMANDA POR DAÑOS Y PERJUICIOS .exe | executable | |
MD5:F1106955167B6F3E6F68091DE9AEF2C3 | SHA256:E93206261E3279C749CB753CE1DE2CF455BD79AA9A605E4105F60347C9E2E671 | |||
| 7032 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7032.3470\libcef.dll | executable | |
MD5:17634B5760D5E29F45D991C1C72F28E4 | SHA256:1E31F4B93C4C67A0EC999F1EBFC8FB7C21246DF49A11305AAEDDFE168BD56833 | |||
| 4748 | 001 DEMANDA POR DAÑOS Y PERJUICIOS .exe | C:\Users\admin\AllowLeadingSignICustomQueryInterfacegetLatin1\001 DEMANDA POR DAÑOS Y PERJUICIOS .exe | executable | |
MD5:F1106955167B6F3E6F68091DE9AEF2C3 | SHA256:E93206261E3279C749CB753CE1DE2CF455BD79AA9A605E4105F60347C9E2E671 | |||
| 7032 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7032.3470\chrome_elf.dll | executable | |
MD5:1D7710E5ECD11597BD6517C4FA6E8DFE | SHA256:14B84F518B6F74D5FA8585D0CA25D4465E5FEEEDD529D9FC4E6761549F815B0F | |||
| 7016 | aspnet_wp.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileSyncConfig.exe | executable | |
MD5:CFE72F9B68860FAC5E8033EE8FD0F607 | SHA256:1D986F0D2A001A4F236DAF1FEE0046AECE46635EB30F9AEBF9A4448755D29C0C | |||
| 7016 | aspnet_wp.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe | executable | |
MD5:109C91F7DE18292D3708971CAA6667D3 | SHA256:519C82F9ADA0D9B377705DA4C648A33714618DE8F3C63C4B6153140BDB3E4084 | |||
| 1324 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb1324.36181\001 DEMANDA POR DAÑOS Y PERJUICIOS .zip | compressed | |
MD5:06328E5753B95F6836E4CF0B610507FB | SHA256:E3B051094CEB87219FFAF6418D552AF5F07236AC73FC1ED85FB83942CEB12718 | |||
| 4748 | 001 DEMANDA POR DAÑOS Y PERJUICIOS .exe | C:\Users\admin\AllowLeadingSignICustomQueryInterfacegetLatin1\chrome_elf.dll | executable | |
MD5:1D7710E5ECD11597BD6517C4FA6E8DFE | SHA256:14B84F518B6F74D5FA8585D0CA25D4465E5FEEEDD529D9FC4E6761549F815B0F | |||
| 4748 | 001 DEMANDA POR DAÑOS Y PERJUICIOS .exe | C:\Users\admin\AllowLeadingSignICustomQueryInterfacegetLatin1\libcef.dll | executable | |
MD5:17634B5760D5E29F45D991C1C72F28E4 | SHA256:1E31F4B93C4C67A0EC999F1EBFC8FB7C21246DF49A11305AAEDDFE168BD56833 | |||
| 7016 | aspnet_wp.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\OneDriveUpdaterService.exe | executable | |
MD5:A762DE6C29873D113515DF2EAA50CAD7 | SHA256:8C19AA42EAD5D5706C7C5547D971D7A402BC1EAB01B4180909CD60E1DAD8AB07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
28
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.24.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3092 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1180 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 72.246.169.163:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
1180 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2524 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7124 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 184.24.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3092 | svchost.exe | 40.126.31.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |