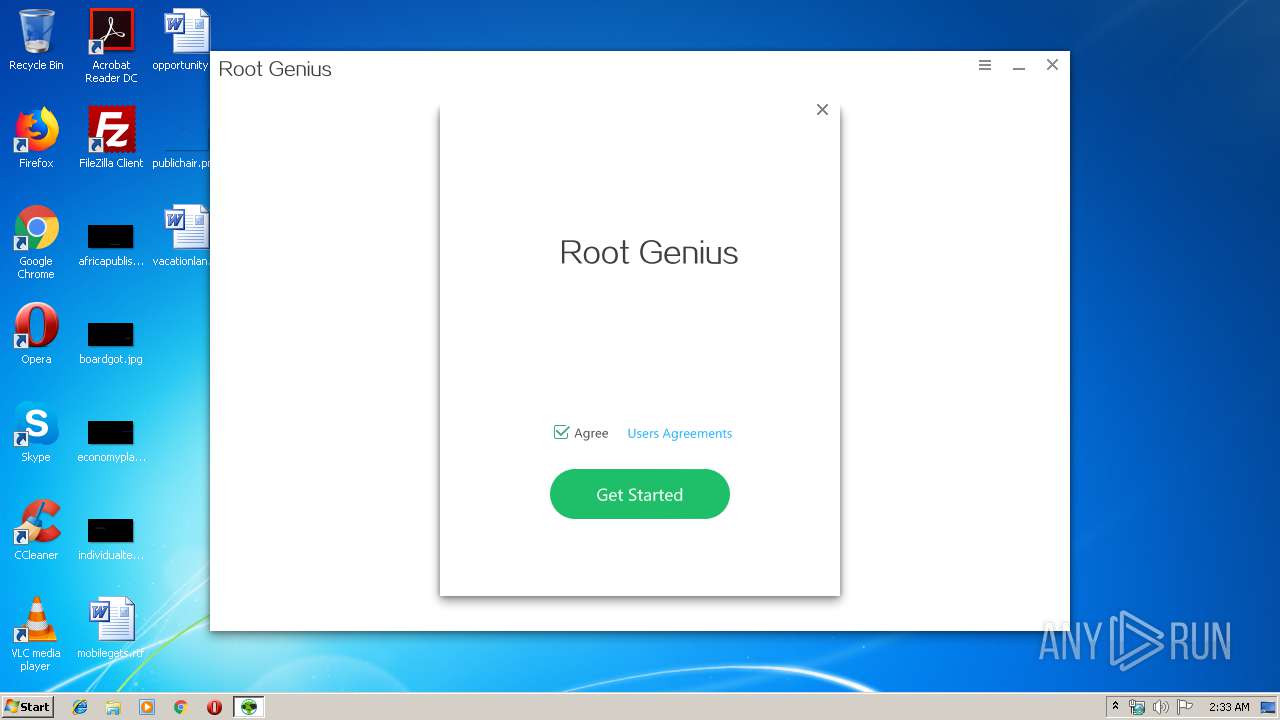
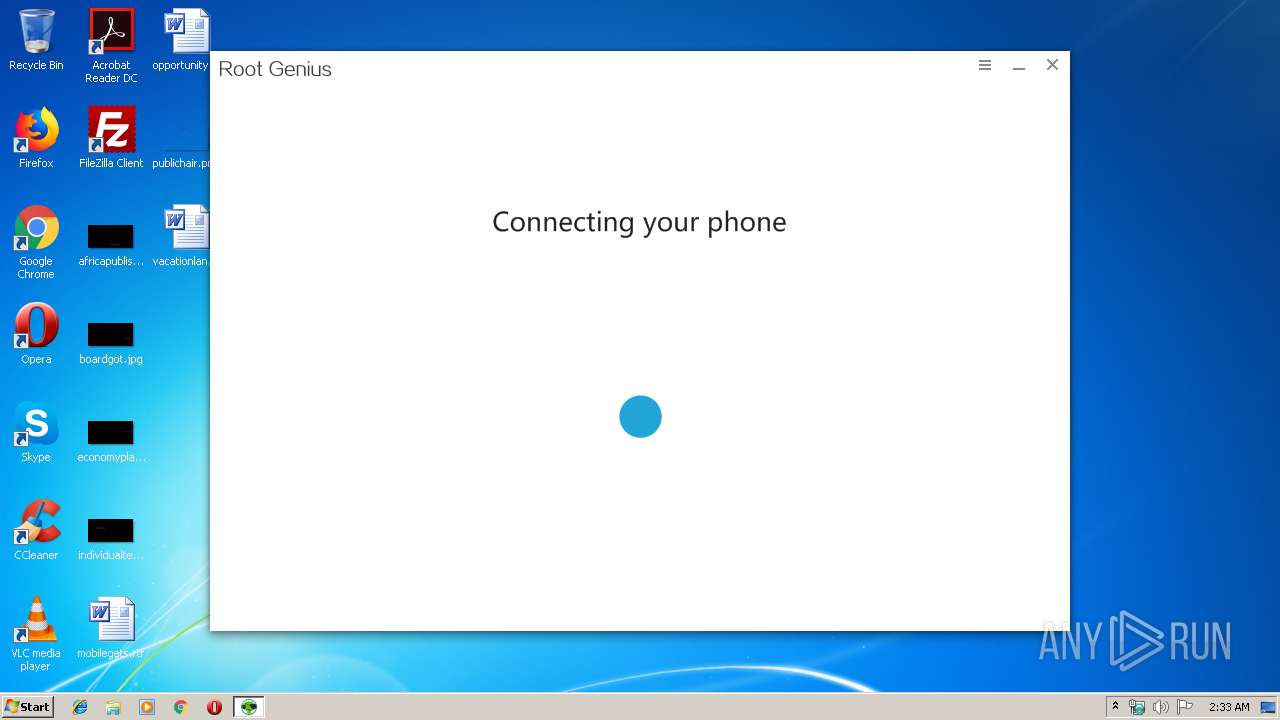
| File name: | RootGenius_en_3.1.7.exe |
| Full analysis: | https://app.any.run/tasks/5cf0795c-418b-4ce2-9150-d8ce22fe1bdc |
| Verdict: | Malicious activity |
| Analysis date: | April 24, 2019, 01:33:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 468094FCE116B917D41D0A3262A441FB |
| SHA1: | A60B3F1DF2112D35184A7549AEFDF30EA7E865B1 |
| SHA256: | 4B20A34B367D3CA36BF51EA8FCB551C31C2B6B3AA18781442FD39144DE6B6634 |
| SSDEEP: | 196608:EZ3w6lXae9fOd4X25zwBa6NFiu4iv9kjwiAkeRO:egkaeYdkEsBnAu4iVkjwf9O |
MALICIOUS
Loads dropped or rewritten executable
- shuame_helper.exe (PID: 3692)
- RootGenius_en_3.1.7.exe (PID: 3240)
- shuame_helper.exe (PID: 2492)
- shuame_helper.exe (PID: 3704)
- shuame_helper.exe (PID: 2728)
- shuame_helper.exe (PID: 3784)
- shuame_helper.exe (PID: 3744)
- shuame_helper.exe (PID: 3720)
- shuame_helper.exe (PID: 2660)
- shuame_helper.exe (PID: 3652)
- shuame_helper.exe (PID: 2620)
- shuame_helper.exe (PID: 3628)
- shuame_helper.exe (PID: 3800)
- shuame_helper.exe (PID: 3596)
- shuame_helper.exe (PID: 3900)
- shuame_helper.exe (PID: 3736)
- shuame_helper.exe (PID: 2516)
- shuame_helper.exe (PID: 3732)
- shuame_helper.exe (PID: 3520)
- shuame_helper.exe (PID: 3536)
- shuame_helper.exe (PID: 3664)
- shuame_helper.exe (PID: 3008)
- shuame_helper.exe (PID: 992)
- shuame_helper.exe (PID: 2696)
- shuame_helper.exe (PID: 2660)
- shuame_helper.exe (PID: 2576)
- shuame_helper.exe (PID: 2556)
Application was dropped or rewritten from another process
- shuame_helper.exe (PID: 3692)
- shuame_helper.exe (PID: 3704)
- shuame_helper.exe (PID: 2492)
- shuame_helper.exe (PID: 2728)
- shuame_helper.exe (PID: 3784)
- shuame_helper.exe (PID: 3744)
- shuame_helper.exe (PID: 3720)
- shuame_helper.exe (PID: 2660)
- shuame_helper.exe (PID: 3652)
- shuame_helper.exe (PID: 2620)
- shuame_helper.exe (PID: 3628)
- shuame_helper.exe (PID: 3800)
- shuame_helper.exe (PID: 3596)
- shuame_helper.exe (PID: 3900)
- shuame_helper.exe (PID: 3736)
- shuame_helper.exe (PID: 2696)
- shuame_helper.exe (PID: 3536)
- shuame_helper.exe (PID: 3732)
- shuame_helper.exe (PID: 3664)
- shuame_helper.exe (PID: 3520)
- shuame_helper.exe (PID: 3008)
- shuame_helper.exe (PID: 992)
- shuame_helper.exe (PID: 2556)
- shuame_helper.exe (PID: 2660)
- shuame_helper.exe (PID: 2576)
- shuame_helper.exe (PID: 2516)
SUSPICIOUS
Executable content was dropped or overwritten
- RootGenius_en_3.1.7.exe (PID: 3240)
Application launched itself
- shuame_helper.exe (PID: 3692)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:01 08:54:25+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 135680 |
| InitializedDataSize: | 7310336 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaa18 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.1.7.0 |
| ProductVersionNumber: | 3.1.7.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileDescription: | RootGenius |
| FileVersion: | 3.1.7 |
| InternalName: | RootGenius |
| LegalCopyright: | Copyright 2016 |
| OriginalFileName: | RootGenius.exe |
| ProductName: | RootGenius |
| ProductVersion: | 3.1.7 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Apr-2016 06:54:25 |
| Detected languages: |
|
| FileDescription: | RootGenius |
| FileVersion: | 3.1.7 |
| InternalName: | RootGenius |
| LegalCopyright: | Copyright 2016 |
| OriginalFilename: | RootGenius.exe |
| ProductName: | RootGenius |
| ProductVersion: | 3.1.7 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Apr-2016 06:54:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00021162 | 0x00021200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64483 |
.rdata | 0x00023000 | 0x0000966E | 0x00009800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.59789 |
.data | 0x0002D000 | 0x00003DC8 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.79774 |
.rsrc | 0x00031000 | 0x006EB6C4 | 0x006EB800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.98885 |
.reloc | 0x0071D000 | 0x00001EF8 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.51322 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.53367 | 38056 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 4.82822 | 9640 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
4 | 5.27705 | 4264 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
5 | 6.10967 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
6 | 7.96521 | 32271 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
7 | 2.11169 | 72 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
8 | 4.82822 | 9640 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
9 | 5.27705 | 4264 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
10 | 6.10967 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
Imports
KERNEL32.dll |
RootGenius.dll (delay-loaded) |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
dbghelp.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
AdbDoShell | 1 | 0x000213E5 |
AdbPull | 2 | 0x000213F5 |
AdbPush | 3 | 0x00021405 |
AdbWaitForDevice | 4 | 0x00021415 |
Total processes
82
Monitored processes
27
Malicious processes
3
Suspicious processes
24
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 992 | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe devices | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe | RootGenius_en_3.1.7.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2492 | adb fork-server server | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe | shuame_helper.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2516 | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe devices | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe | RootGenius_en_3.1.7.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2556 | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe devices | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe | RootGenius_en_3.1.7.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2576 | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe devices | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe | RootGenius_en_3.1.7.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2620 | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe devices | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe | RootGenius_en_3.1.7.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2660 | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe devices | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe | RootGenius_en_3.1.7.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2660 | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe devices | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe | RootGenius_en_3.1.7.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2696 | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe devices | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe | RootGenius_en_3.1.7.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2728 | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe devices | C:\Users\admin\AppData\Local\Temp\RootGenius\shuame_helper.exe | RootGenius_en_3.1.7.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
88
Read events
86
Write events
2
Delete events
0
Modification events
| (PID) Process: | (3240) RootGenius_en_3.1.7.exe | Key: | HKEY_CURRENT_USER\Software\RootGenius |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Local\Temp\RootGenius_en_3.1.7.exe | |||
| (PID) Process: | (3240) RootGenius_en_3.1.7.exe | Key: | HKEY_CURRENT_USER\Software\RootGenius |
| Operation: | write | Name: | license |
Value: true | |||
Executable files
10
Suspicious files
5
Text files
10
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3240 | RootGenius_en_3.1.7.exe | C:\Users\admin\AppData\Local\Temp\RootGenius\RootGenius.zip | — | |
MD5:— | SHA256:— | |||
| 3240 | RootGenius_en_3.1.7.exe | C:\Users\admin\AppData\Local\Temp\RootGenius\android_driver\devcon_x86.exe | executable | |
MD5:— | SHA256:— | |||
| 3240 | RootGenius_en_3.1.7.exe | C:\Users\admin\AppData\Local\Temp\RootGenius\Kinguser.zip | compressed | |
MD5:— | SHA256:— | |||
| 3240 | RootGenius_en_3.1.7.exe | C:\Users\admin\AppData\Local\Temp\RootGenius\Data\Bin\aapt | o | |
MD5:— | SHA256:— | |||
| 3240 | RootGenius_en_3.1.7.exe | C:\Users\admin\AppData\Local\Temp\RootGenius\Data\Apk\StayAwake.apk | java | |
MD5:— | SHA256:— | |||
| 3240 | RootGenius_en_3.1.7.exe | C:\Users\admin\AppData\Local\Temp\RootGenius\android_driver\devcon_x64.exe | executable | |
MD5:— | SHA256:— | |||
| 3240 | RootGenius_en_3.1.7.exe | C:\Users\admin\AppData\Local\Temp\RootGenius\Data\Bin\aapt-pie | o | |
MD5:— | SHA256:— | |||
| 3240 | RootGenius_en_3.1.7.exe | C:\Users\admin\AppData\Local\Temp\RootGenius\RootGeniusEx.zip | — | |
MD5:— | SHA256:— | |||
| 3240 | RootGenius_en_3.1.7.exe | C:\Users\admin\AppData\Local\Temp\RootGenius\Data\Bin\busybox | o | |
MD5:— | SHA256:— | |||
| 3240 | RootGenius_en_3.1.7.exe | C:\Users\admin\AppData\Local\Temp\RootGenius\Data\Res\placeholder_big.png | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
5
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3240 | RootGenius_en_3.1.7.exe | POST | — | 182.254.38.45:80 | http://client.shuame.com/api/root/optimize?versionName=RootGenius_en&versionCode=127 | CN | — | — | suspicious |
3240 | RootGenius_en_3.1.7.exe | POST | — | 182.254.38.45:80 | http://client.shuame.com/api/root/hotApp?versionName=RootGenius_en&versionCode=127 | CN | — | — | suspicious |
3240 | RootGenius_en_3.1.7.exe | POST | 200 | 182.254.38.45:80 | http://client.shuame.com/api/root/weakPerceptionApp?versionName=RootGenius_en&versionCode=127 | CN | text | 31 b | suspicious |
3240 | RootGenius_en_3.1.7.exe | POST | 200 | 203.195.128.118:80 | http://api1.rootjl.com/v2/root/cfg?versionName=RootGenius_en&versionCode=127 | CN | binary | 866 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3240 | RootGenius_en_3.1.7.exe | 203.195.128.118:80 | api1.rootjl.com | Shenzhen Tencent Computer Systems Company Limited | CN | suspicious |
3240 | RootGenius_en_3.1.7.exe | 182.254.38.45:80 | client.shuame.com | Shenzhen Tencent Computer Systems Company Limited | CN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
client.shuame.com |
| suspicious |
api1.rootjl.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3240 | RootGenius_en_3.1.7.exe | A Network Trojan was detected | SUSPICIOUS [PTsecurity] Win32/RootGenius.B potentially unsafe |
3240 | RootGenius_en_3.1.7.exe | A Network Trojan was detected | SUSPICIOUS [PTsecurity] Win32/RootGenius.B potentially unsafe |
3240 | RootGenius_en_3.1.7.exe | A Network Trojan was detected | SUSPICIOUS [PTsecurity] Win32/RootGenius.B potentially unsafe |
Process | Message |
|---|---|
RootGenius_en_3.1.7.exe | unzOpen C:\Users\admin\AppData\Local\Temp\RootGenius\RootGeniusEx.zip error
|