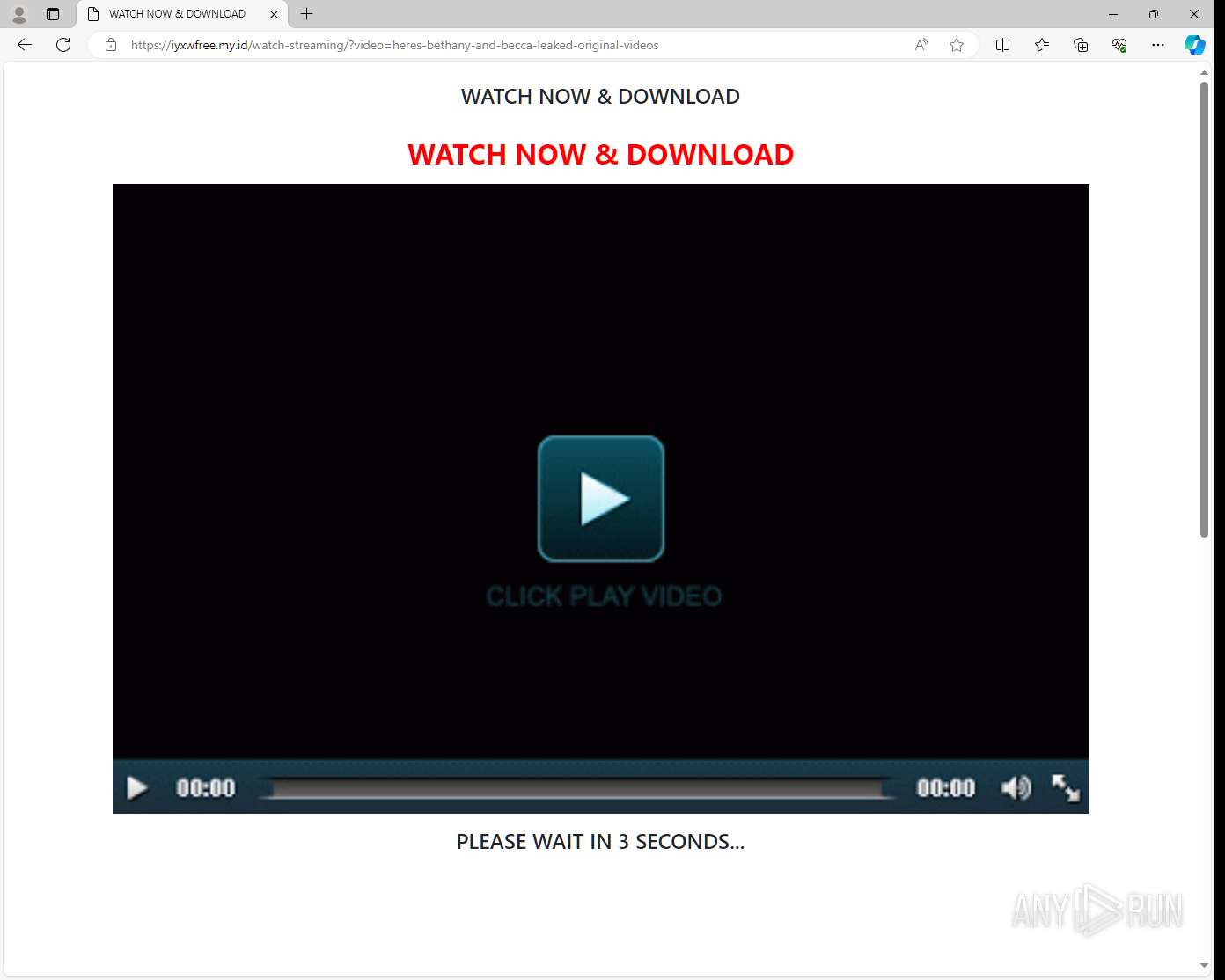
| URL: | https://iyxwfree.my.id/watch-streaming?video=heres-bethany-and-becca-leaked-original-videos |
| Full analysis: | https://app.any.run/tasks/76fb9422-4180-4bc7-a95c-d78924dfcb2f |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2024, 01:43:20 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| MD5: | 8D44AEF2AE946202D4A0B523F94F9443 |
| SHA1: | 9DF5E35014663AE171EF25D4933A7D103729C4BB |
| SHA256: | 4B1F14FB49D7CBDFC04BB30C1A3A4B622C5F79AF1991539B6CDA01D7A85025AA |
| SSDEEP: | 3:N8NhKgXhIKtfTW6ArEoIiBIaEI1IOkKW:2NjRIWb0EViBIwCxN |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
150
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 4792 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2604 --field-trial-handle=2320,i,16194277592197507296,15814343983252007256,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
21
Suspicious files
57
Text files
27
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000c2 | binary | |
MD5:8EFF0B8045FD1959E117F85654AE7770 | SHA256:89978E658E840B927DDDB5CB3A835C7D8526ECE79933BD9F3096B301FE1A8571 | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000c4 | text | |
MD5:F4A0131853AA84016FD818586064C744 | SHA256:123FAD0FF5231E01988CE0359286E9FF5BE359B8B32FC152BBEC7B46FF1B0A78 | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\TransportSecurity~RF2b689c.TMP | binary | |
MD5:15D26FA4E16467BE658F42074AC0DBAA | SHA256:D287407BD901A32E3F38F4392984507184D596C3694FAA69DD0B2E68F9F3A8FE | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000ba | text | |
MD5:DD3EECA5FFB3EA963B9AF996B9ACA024 | SHA256:1F9CDC6019DC1405CF0F8D65C872B95731A928E9684F5E1E717B5181BDB74184 | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\Network Persistent State | binary | |
MD5:ED74D0CC3CAB53CA501F3CD6C50FAA1A | SHA256:331BB0DA5A3BE7843A14503DA9547E7309F3631916C6112882FF36D75025E7EE | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\Network Persistent State~RF2b687c.TMP | binary | |
MD5:2A21453795942FD88CBB06714604B9FD | SHA256:5DFE0384325B556EE4B8668E502312B9BA6ADC298CD9213DDFA528CB959ADC06 | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000c1 | binary | |
MD5:993BF6E3C86DB617CD16243E688026D7 | SHA256:CF6C114528F5FA6C7D24A7C9D96B233A79A61B485C74BFC0F63983A66DDD40FC | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\36f3ef8e-0932-4673-aeef-cf0816e68d52.tmp | binary | |
MD5:54BC742D832B630B1D2CBE6BE7CB34DD | SHA256:26503AF1D5ADF82043D165526AB14D6953EDA0124267D7FF2CAE8E023393E896 | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000bc | compressed | |
MD5:C09E238DBF5B9860101E358526DFA45A | SHA256:B3ABE6CBBF1CE1AFD3CBB60037BAF559D3274CFB329D5B7818BD1BCE69DE1F95 | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000bf | text | |
MD5:F9061D7E183854972E9F7488FE60B987 | SHA256:F9844FF0341E6EEC8FA4A04BE795C9545717597FC1A4ED866D73CDECD5D5A1D0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
247
TCP/UDP connections
260
DNS requests
289
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 184.30.17.174:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | — | — | — |
— | — | GET | 403 | 142.250.185.68:443 | https://www.topcreativeformat.com/6e9f4b835ee9fdd1b0b8978e8d33d38d/invoke.js | unknown | — | — | — |
— | — | GET | 403 | 142.250.185.68:443 | https://pl22894307.highcpmgate.com/be/c8/7f/bec87f35ec8270a29a2e524c0fc6d21a.js | unknown | — | — | — |
— | — | GET | 403 | 142.250.185.68:443 | https://seduceboozeblackmail.com/81b0542cd4b8eb93ce90a4c5369a0a1c/invoke.js | unknown | — | — | — |
— | — | GET | 403 | 142.250.185.68:443 | https://www.topcreativeformat.com/73bcb27e6c0905b536753187dcc3ba9e/invoke.js | unknown | — | — | — |
4712 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4304 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2768 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4304 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | svchost.exe | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2768 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4304 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 224.0.0.251:5353 | — | — | — | unknown |
4792 | msedge.exe | 40.79.150.121:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | FR | unknown |
5988 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4792 | msedge.exe | 104.21.48.1:443 | iyxwfree.my.id | — | — | unknown |
2740 | svchost.exe | 184.28.90.27:443 | fs.microsoft.com | AKAMAI-AS | US | whitelisted |
4792 | msedge.exe | 104.18.10.207:443 | stackpath.bootstrapcdn.com | — | — | whitelisted |
4792 | msedge.exe | 192.243.61.227:443 | pl22894307.highcpmgate.com | DataWeb Global Group B.V. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
iyxwfree.my.id |
| unknown |
fs.microsoft.com |
| whitelisted |
stackpath.bootstrapcdn.com |
| whitelisted |
pl22894307.highcpmgate.com |
| unknown |
seduceboozeblackmail.com |
| unknown |
www.topcreativeformat.com |
| unknown |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Web apps custom Builder (.my .id) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Web apps custom Builder (.my .id) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (stackpath .bootstrapcdn .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (stackpath .bootstrapcdn .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (maxcdn .bootstrapcdn .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (maxcdn .bootstrapcdn .com) |