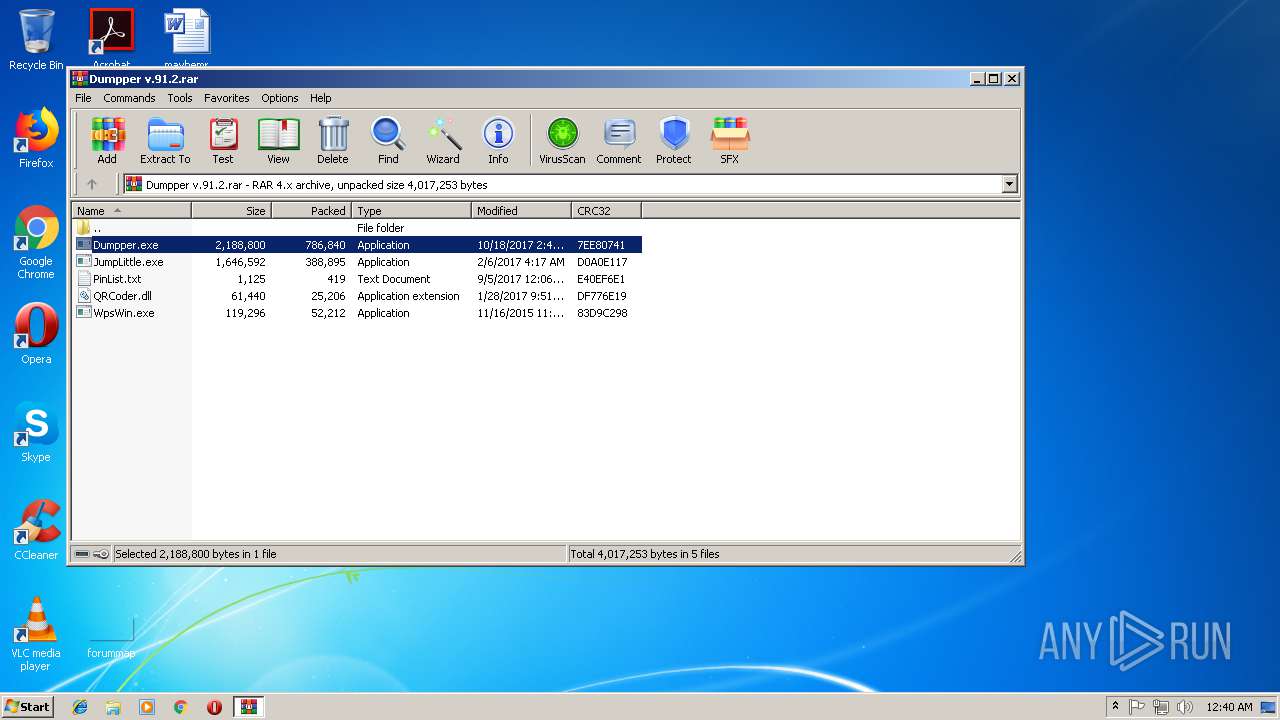
| File name: | Dumpper v.91.2.rar |
| Full analysis: | https://app.any.run/tasks/03696119-aa32-4b7a-bc8b-170a43a96098 |
| Verdict: | No threats detected |
| Analysis date: | September 10, 2018, 23:39:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | D97E232292F1E5C78140B30EC2072408 |
| SHA1: | 0C0D7D8F75F334F88CA22632B5EB63665B7CAFD9 |
| SHA256: | 4B185D9CB6F4BC1703A59DFFB9DF03502F62A0B2A26A25BA804799BA44D02698 |
| SSDEEP: | 24576:VsN2+HT23E73Arhuhob8xSwrRZONNi+pYLPcv0/gEWmq0aBoaord6H:oBzrkoigbR0SLPcYhqrBoBroH |
MALICIOUS
Application was dropped or rewritten from another process
- Dumpper.exe (PID: 2716)
- Dumpper.exe (PID: 1616)
- Dumpper.exe (PID: 1304)
- Dumpper.exe (PID: 2412)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 504)
INFO
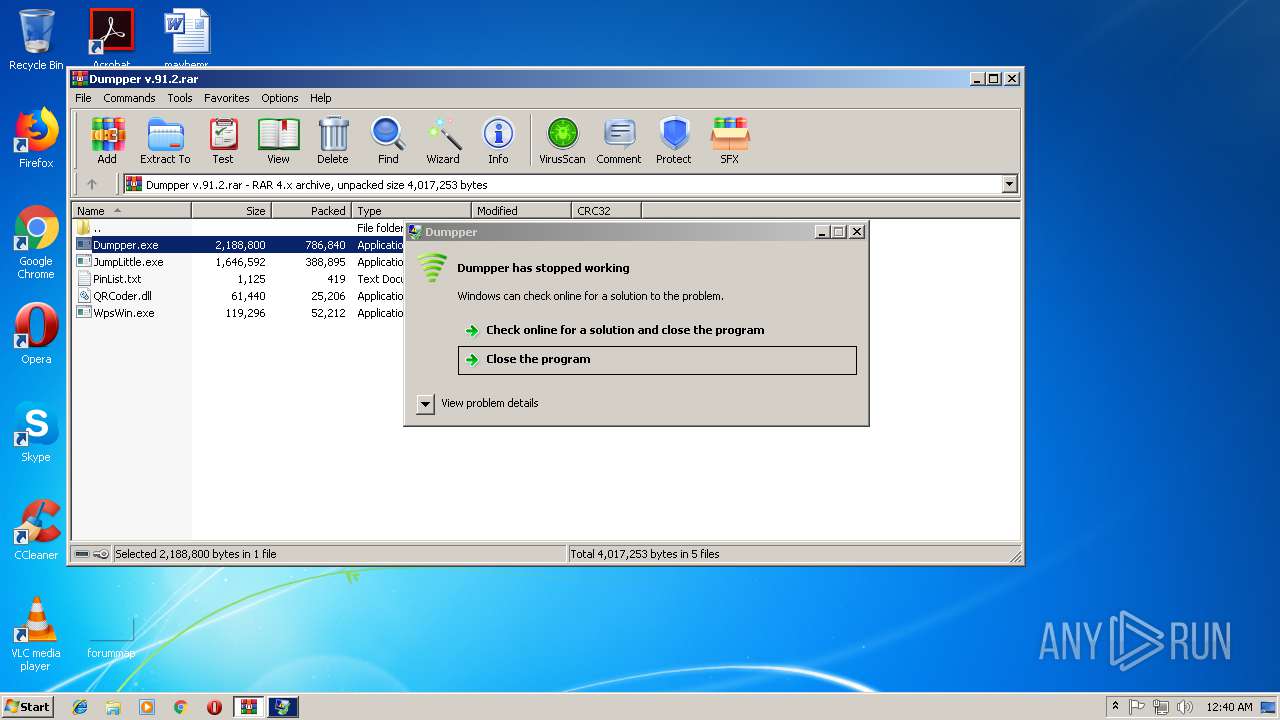
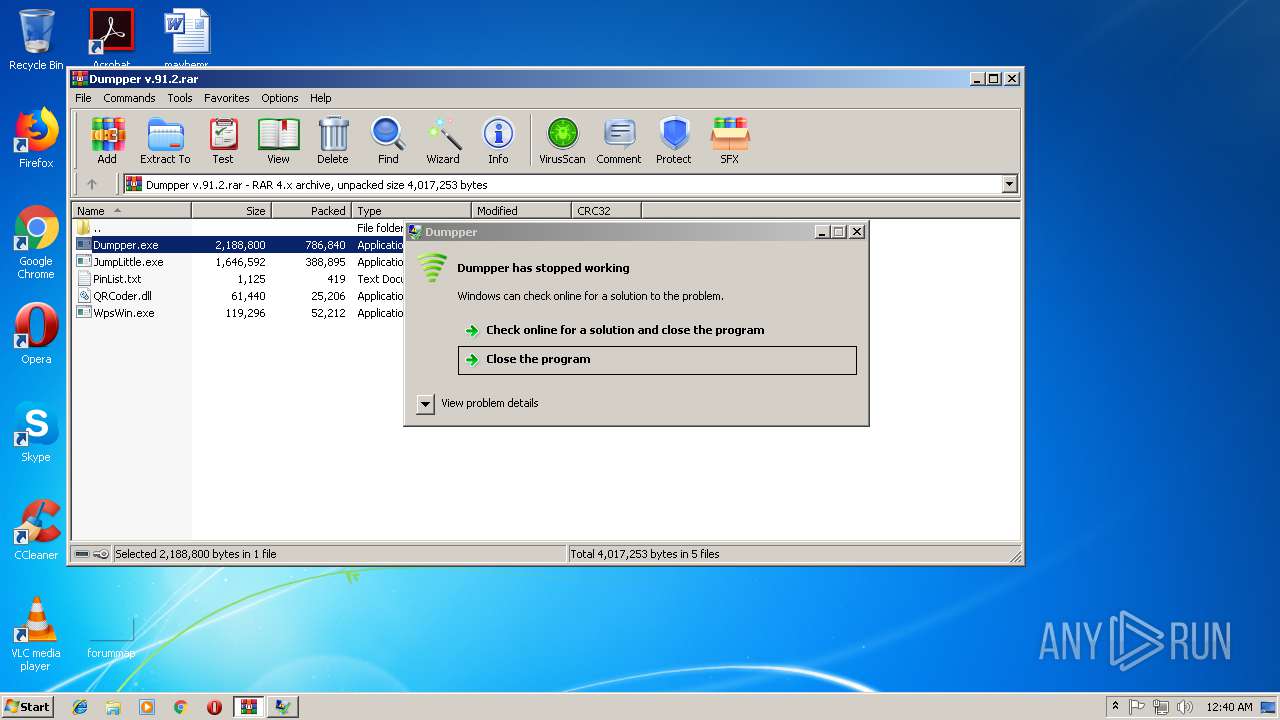
Application was crashed
- Dumpper.exe (PID: 2412)
- Dumpper.exe (PID: 2716)
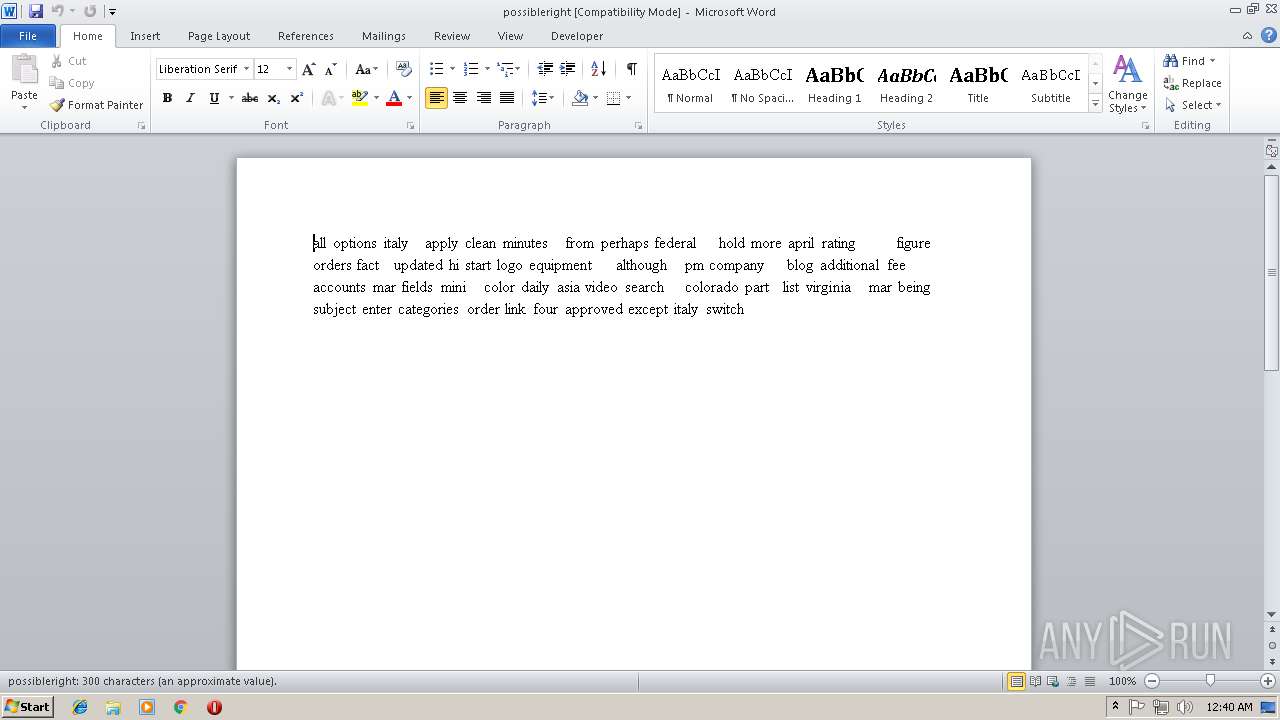
Creates files in the user directory
- WINWORD.EXE (PID: 1348)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
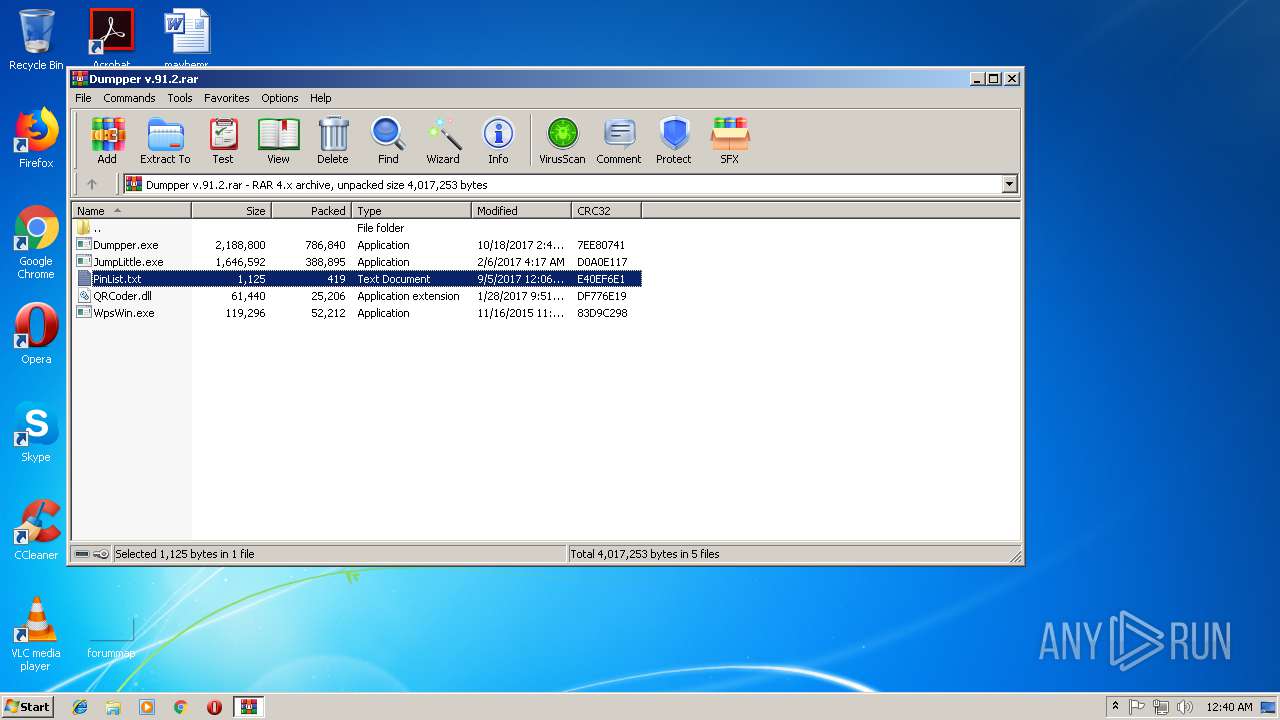
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 388930 |
|---|---|
| UncompressedSize: | 1646592 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2017:02:06 04:17:22 |
| PackingMethod: | Normal |
| ArchivedFileName: | JumpLittle.exe |
Total processes
48
Monitored processes
6
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
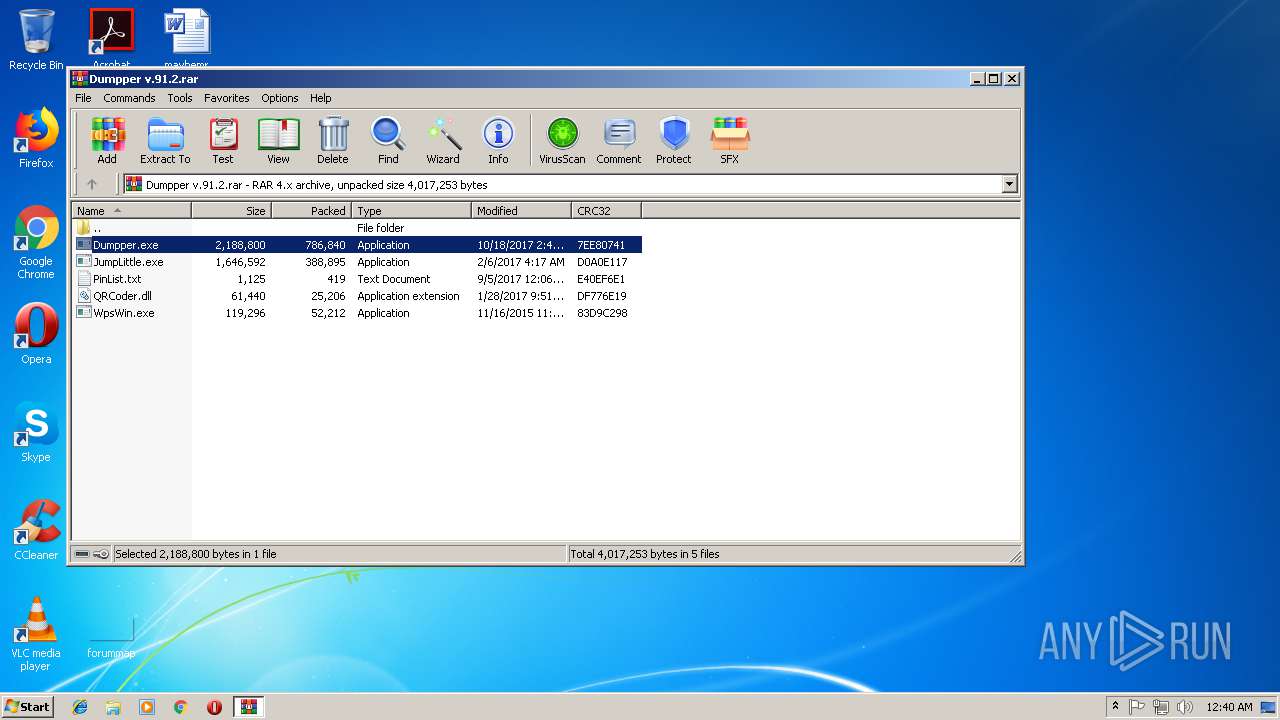
| 504 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Dumpper v.91.2.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1304 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa504.1608\Dumpper.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa504.1608\Dumpper.exe | — | WinRAR.exe | |||||||||||
User: admin Company: SkyTech Integrity Level: MEDIUM Description: Dumpper Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\possibleright.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1616 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa504.49811\Dumpper.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa504.49811\Dumpper.exe | — | WinRAR.exe | |||||||||||
User: admin Company: SkyTech Integrity Level: MEDIUM Description: Dumpper Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2412 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa504.1608\Dumpper.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa504.1608\Dumpper.exe | WinRAR.exe | ||||||||||||
User: admin Company: SkyTech Integrity Level: HIGH Description: Dumpper Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2716 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa504.49811\Dumpper.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa504.49811\Dumpper.exe | WinRAR.exe | ||||||||||||
User: admin Company: SkyTech Integrity Level: HIGH Description: Dumpper Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 432
Read events
1 062
Write events
358
Delete events
12
Modification events
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Dumpper v.91.2.rar | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
| (PID) Process: | (504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
8
Suspicious files
0
Text files
4
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1348 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR3F19.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1348 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{EF013237-90FF-433D-94E7-E29B4603CC1F}.tmp | — | |
MD5:— | SHA256:— | |||
| 1348 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{E9550A96-2AF4-471F-9804-0F3281C91B7B}.tmp | — | |
MD5:— | SHA256:— | |||
| 504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa504.49811\WpsWin.exe | executable | |
MD5:D474EAEB9542D2BE2AC1853936BB774B | SHA256:93229A919E830257DC87BFD9EC11E5E1DDFBF18425484E4450DB7329E6D0C1D8 | |||
| 504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa504.49811\Dumpper.exe | executable | |
MD5:9B8EB74FFE2C1C4EDC4AEEDCBA2B9612 | SHA256:01F5AFA3C3A9AA9D4AE51E3EEE5850A084AE516D2DCB84A0579C4B07FEE37F83 | |||
| 1348 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:2DBCC07DE338A0CE2F3C82CF0D3EAC54 | SHA256:031464EB68C2DE5D781EDF3575A7D9B1B78DC032C2DCF4EFE0BA3F0A2263FAFC | |||
| 504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa504.49811\JumpLittle.exe | executable | |
MD5:1E0FE724AC8EEE75461AA814C480705D | SHA256:177023C40080306164E32221C019B31DD91DF3F94DCE19A2416A74AE9061917F | |||
| 504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa504.1608\PinList.txt | text | |
MD5:DE26AD8D80DB7D2DAA87823C21292D4E | SHA256:92764E46DC115DB3D7DE64A053B1AB98DF03CAB9EF7F0C049CD745B618E924BF | |||
| 1348 | WINWORD.EXE | C:\Users\admin\Desktop\~$ssibleright.rtf | pgc | |
MD5:C5509B67D8389594EA50CFC9F3985F96 | SHA256:8C70379A37AFA08B18A242D492D8DE22A6B26BA3E4F19B82110FC5BE28CA0C68 | |||
| 1348 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:206236161DED6B89FE2B498145C22FC7 | SHA256:B34D5C7936B394AD21E659CDD00453DDAA79206BE154509F30B5C8C2BB5033BA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report