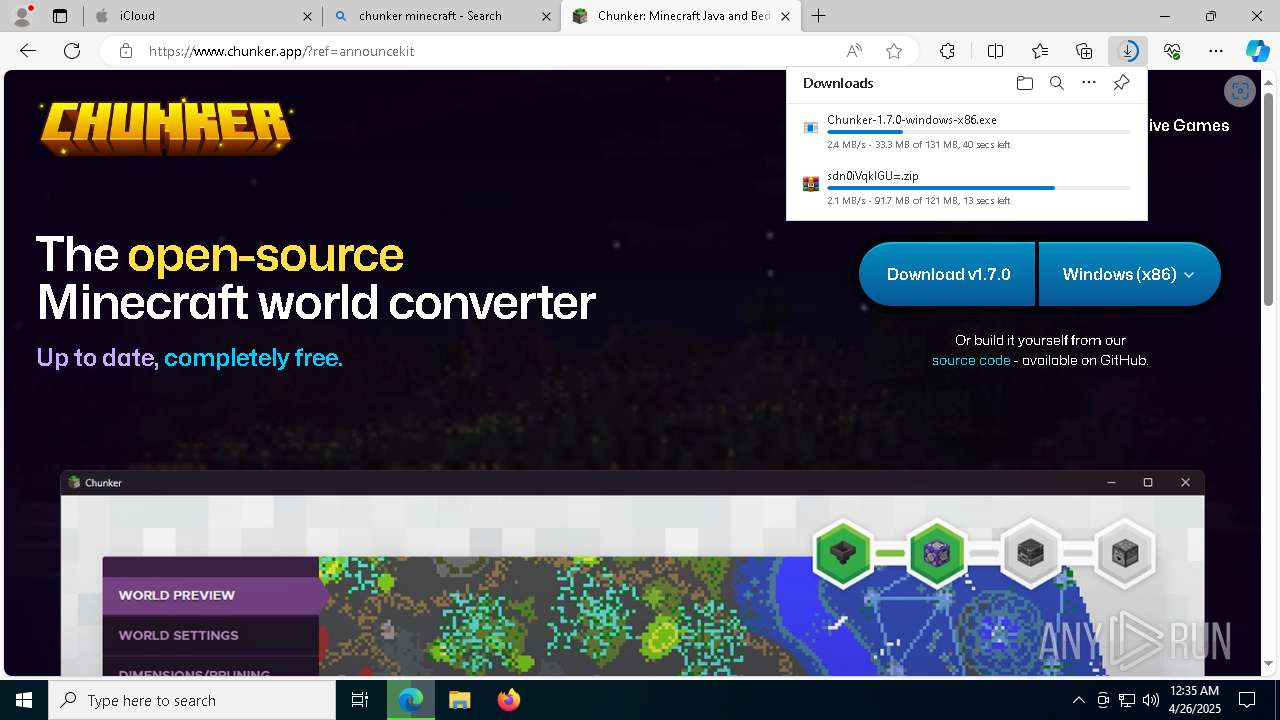
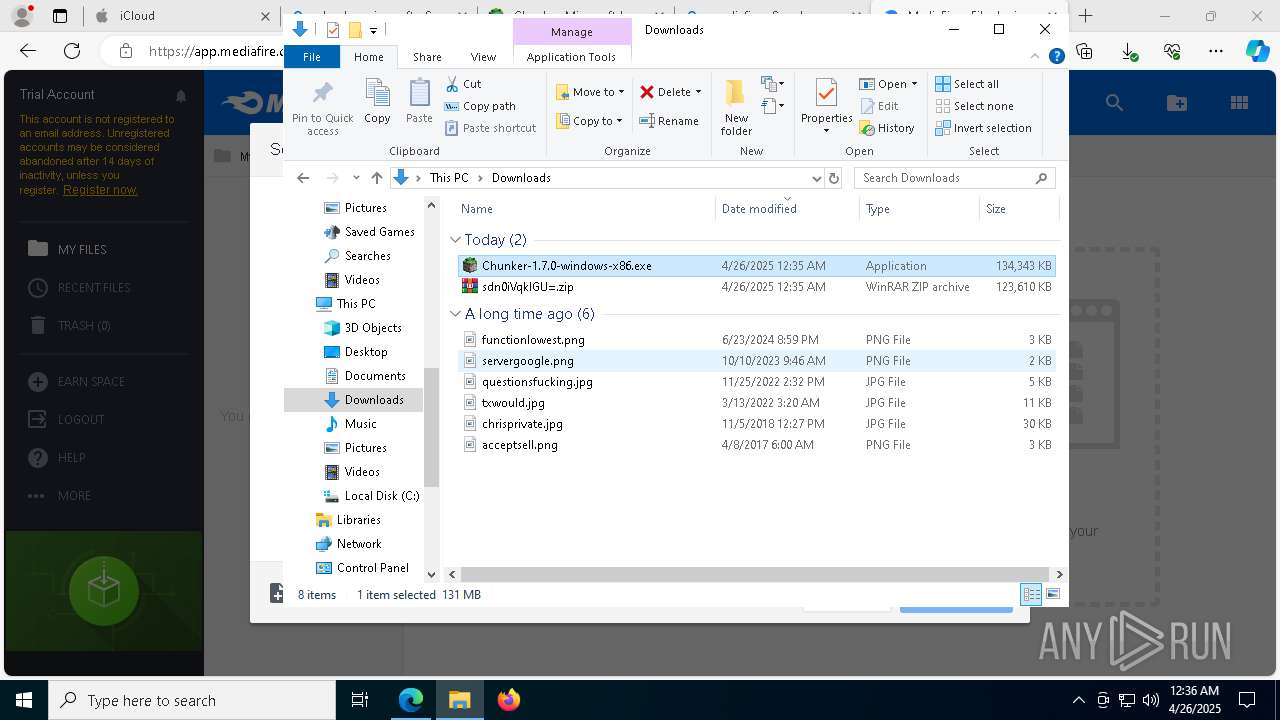
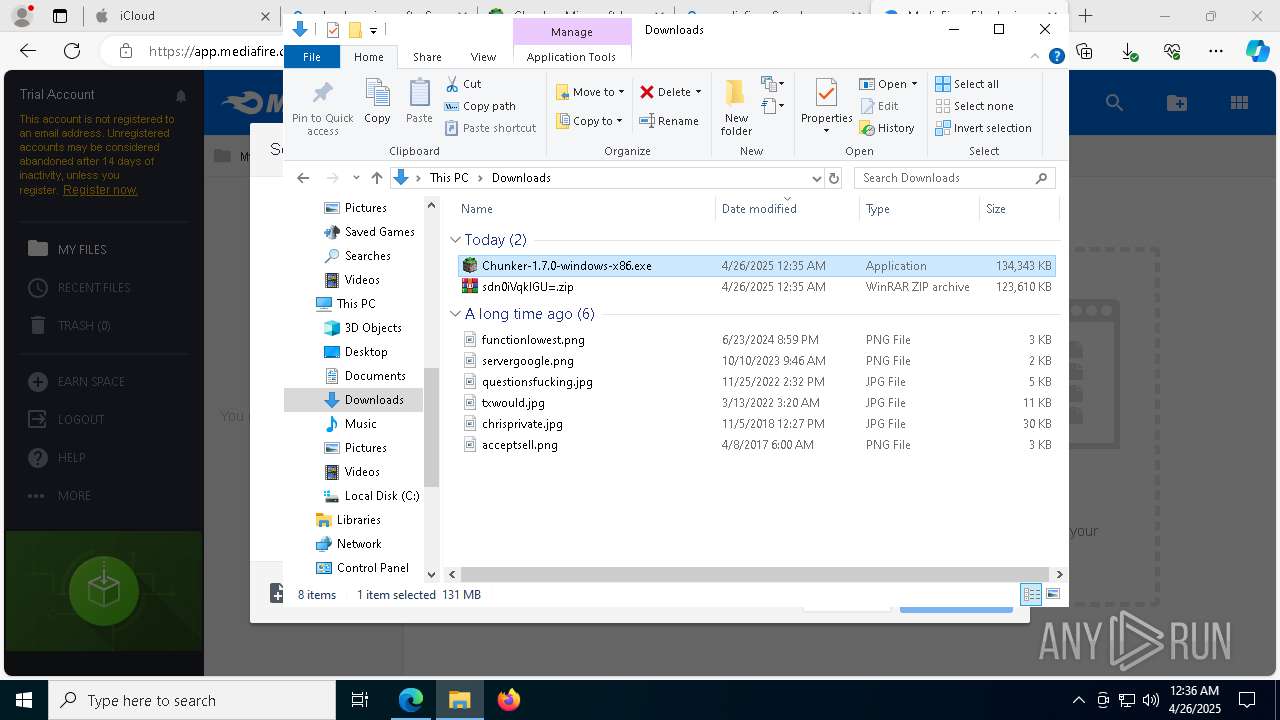
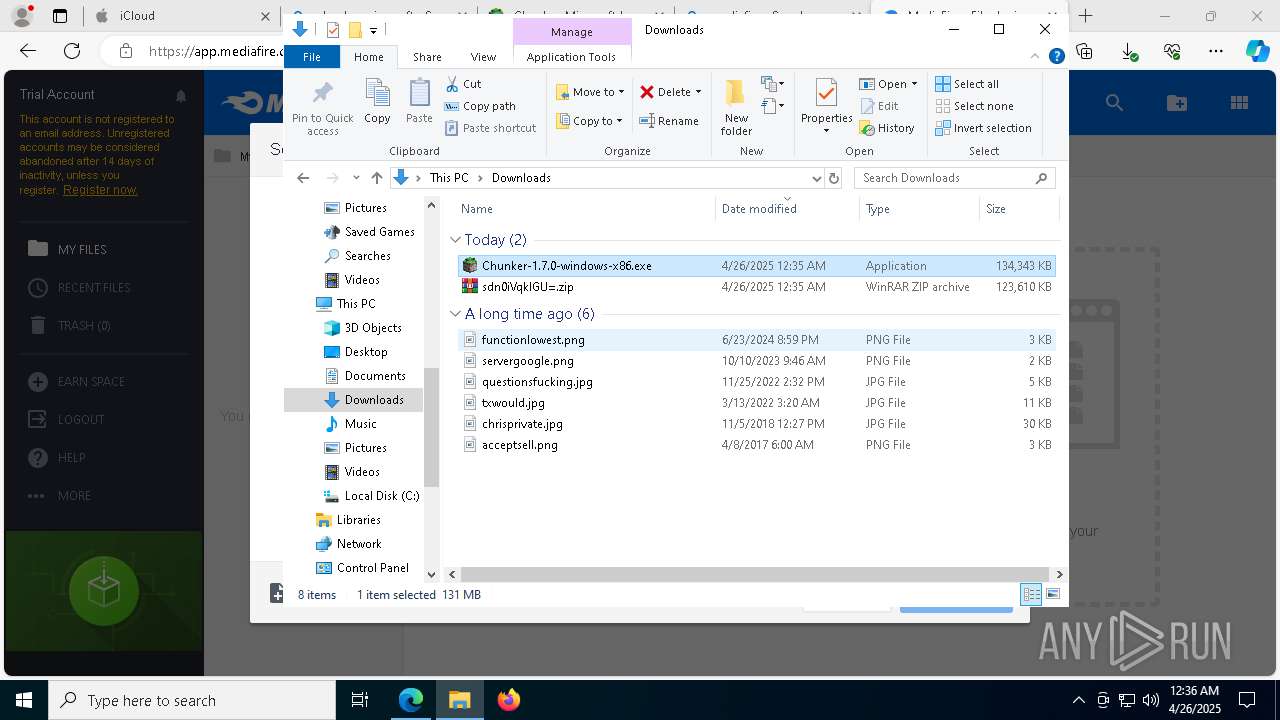
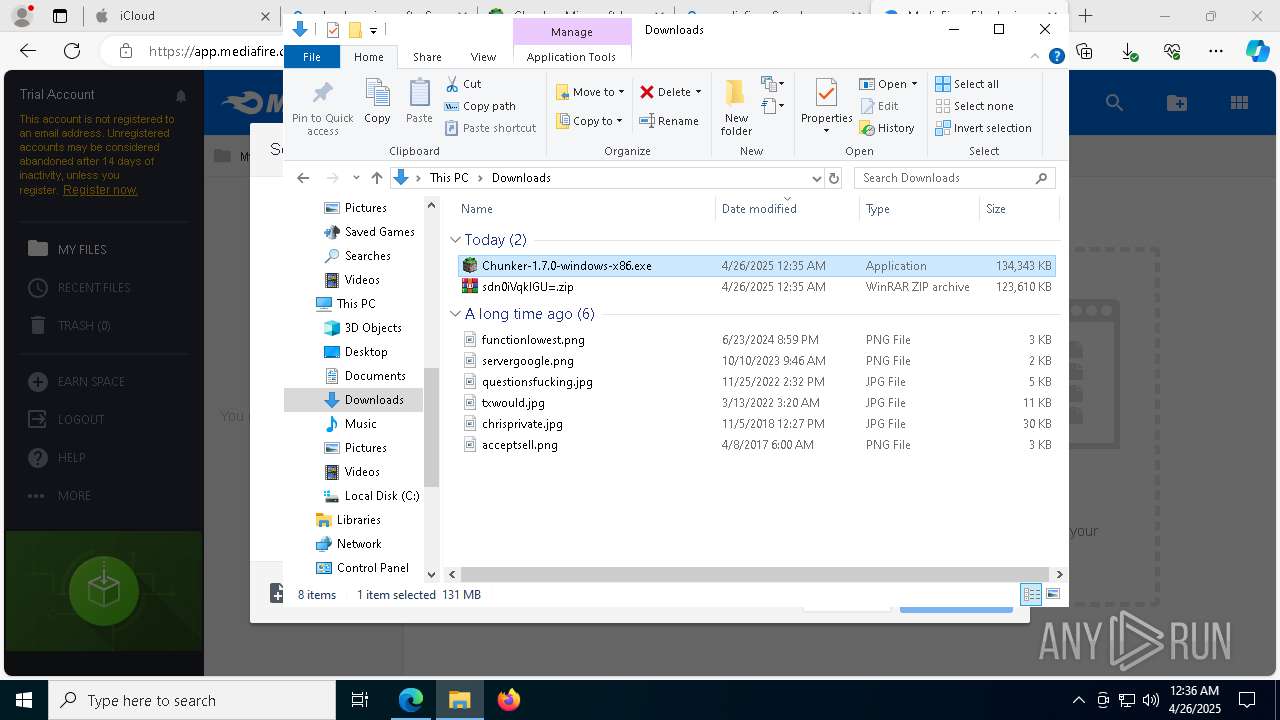
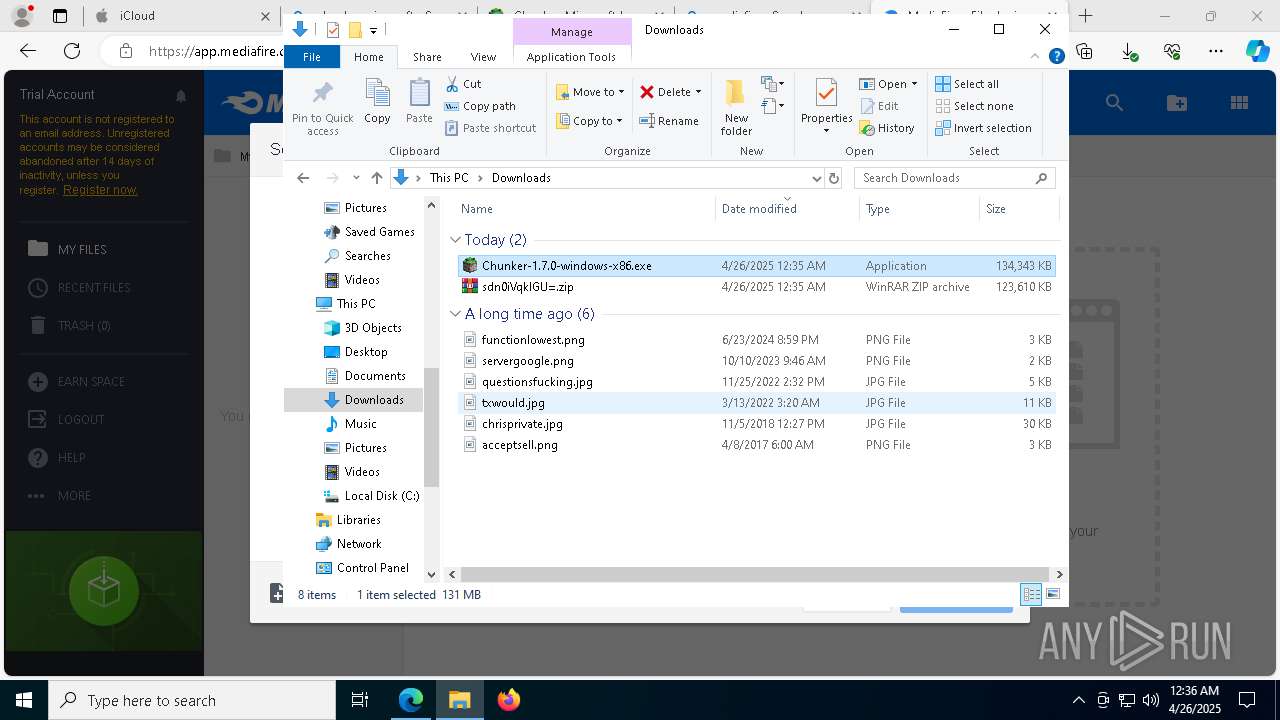
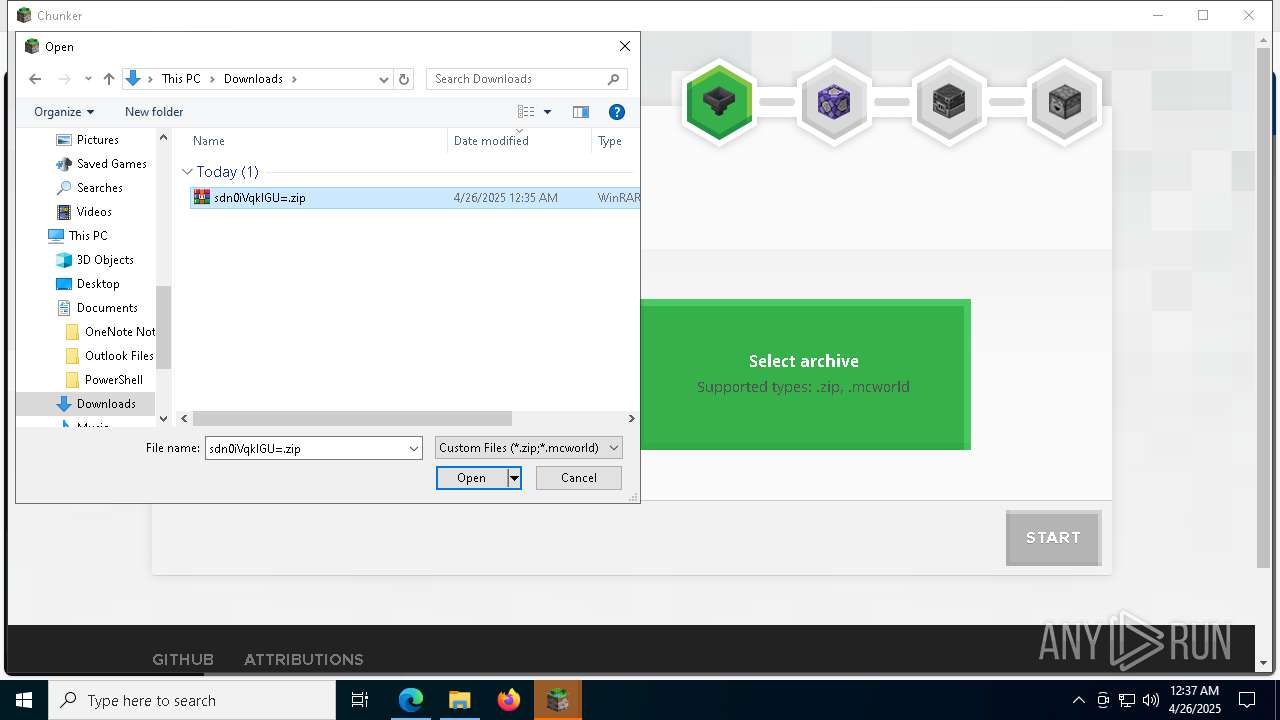
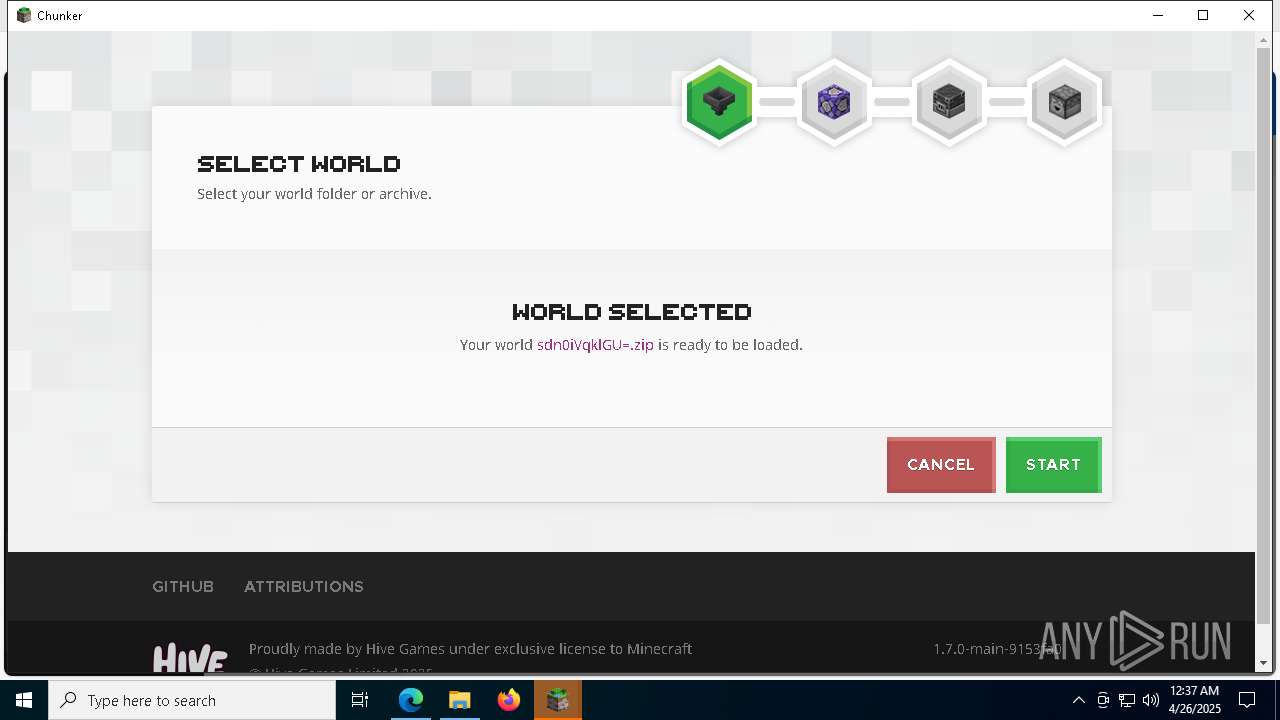
| URL: | https://www.icloud.com/attachment/?u=https%3A%2F%2Fcvws.icloud-content.com%2FB%2FAauJ6I-c1zTJcNK_FDCrCpk5ZFhbASznKuqLaow8QjKkpvmo985Pvu9x%2F%24%7Bf%7D%3Fo%3DAtjaZ0l8x3-sRr4LGbaiWpTJtqQwOuVNQyJvdhRbySiW%26v%3D1%26x%3D3%26a%3DCAogLGs-dGuTyf2mQaoGtdOW753Lrrx7FtRJWuLz4viGE-ISehCt-P305jIYrYj5yPAyIgEAKgkC6AMA_yALHY5SBDlkWFtaBE--73FqJ9zgUaN2wSWpaIqGZDBD1N5meFEnbw09ajbL56B6j0zK28jWE9krIXInaTRU6_AHOlC7bABKp6L9S3C6PODoN3edkFVjgwteKf09nXiL37SB%26e%3D1748204667%26fl%3D%26r%3DD883F3C3-21B8-4C13-A0AD-6170C515FB42-1%26k%3D%24%7Buk%7D%26ckc%3Dcom.apple.largeattachment%26ckz%3D410DC497-0207-4AD3-AA67-09FA04068049%26p%3D152%26s%3DxZBTZn3DgMK_WjJNGBIGhrgueLE&uk=7uwhydSZY5lJ1Zan7go2IA&f=sdn0iVqklGU%3D.zip&sz=126576627 |
| Full analysis: | https://app.any.run/tasks/a8b04d17-f964-4753-a251-7b7eed106fb1 |
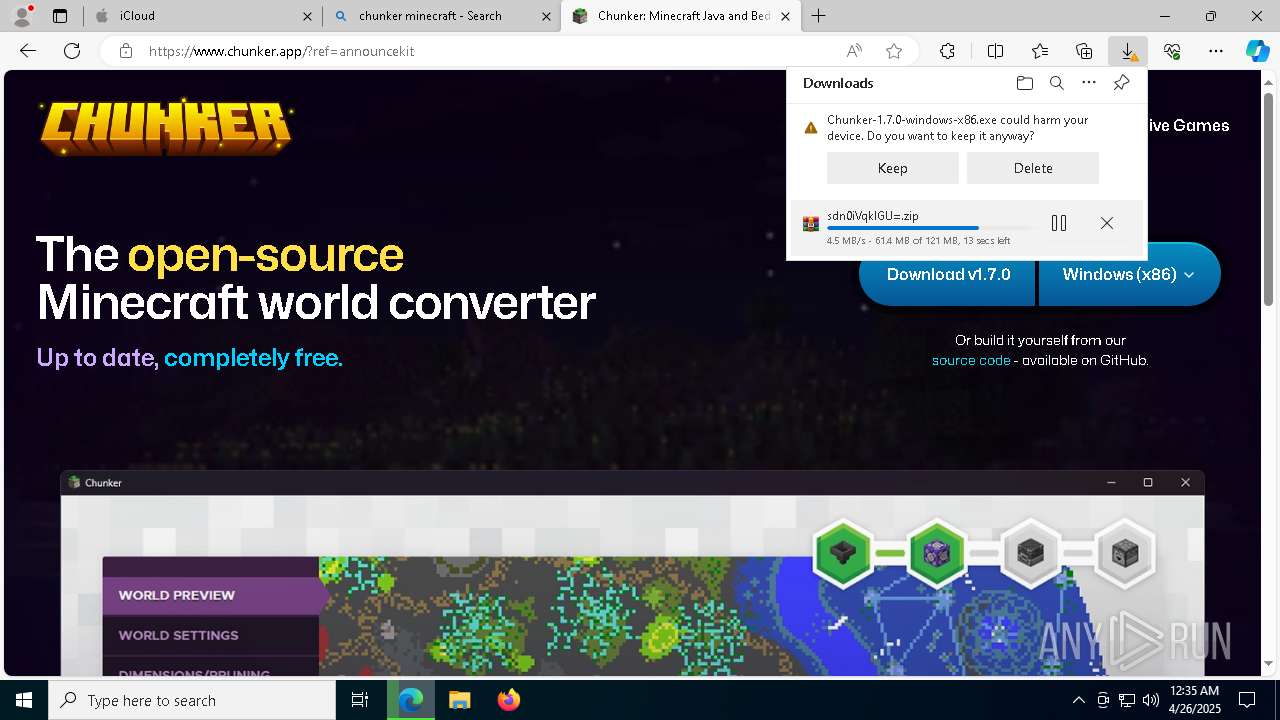
| Verdict: | Malicious activity |
| Analysis date: | April 26, 2025, 00:34:37 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 04415991A4C82E63634A5FE7CF14BDDD |
| SHA1: | EEE46FB62855A5B37C4D2DA640BBB69B80E92AE1 |
| SHA256: | 4B0E85B51E7985A1D0932D8A0BD302342B1F6CFB49CF77B8EC1C5CD15BEB316E |
| SSDEEP: | 12:2hCRGYOUNnbAAEWr221cwmifNYWVG11ogpscZ67f4xXTNwDMODPJQWcd6LVwfC:2cGElblEWr2KcwmmYS81pR67QRTSQODN |
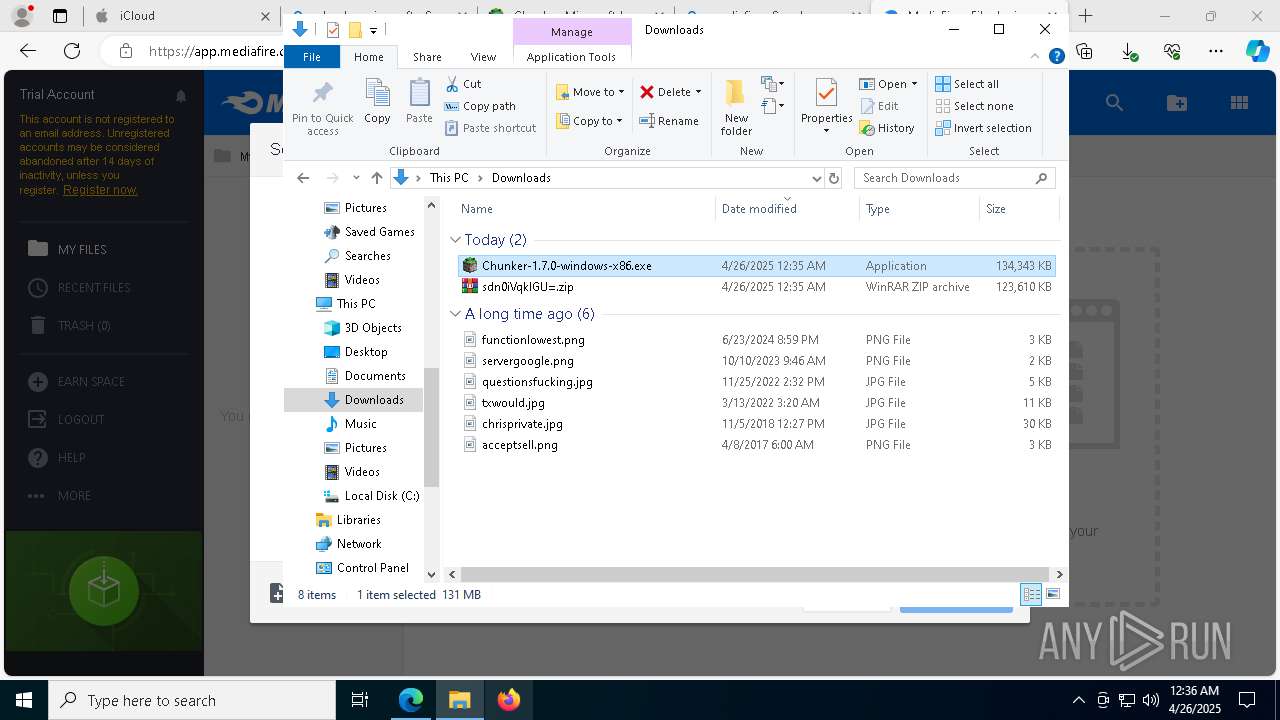
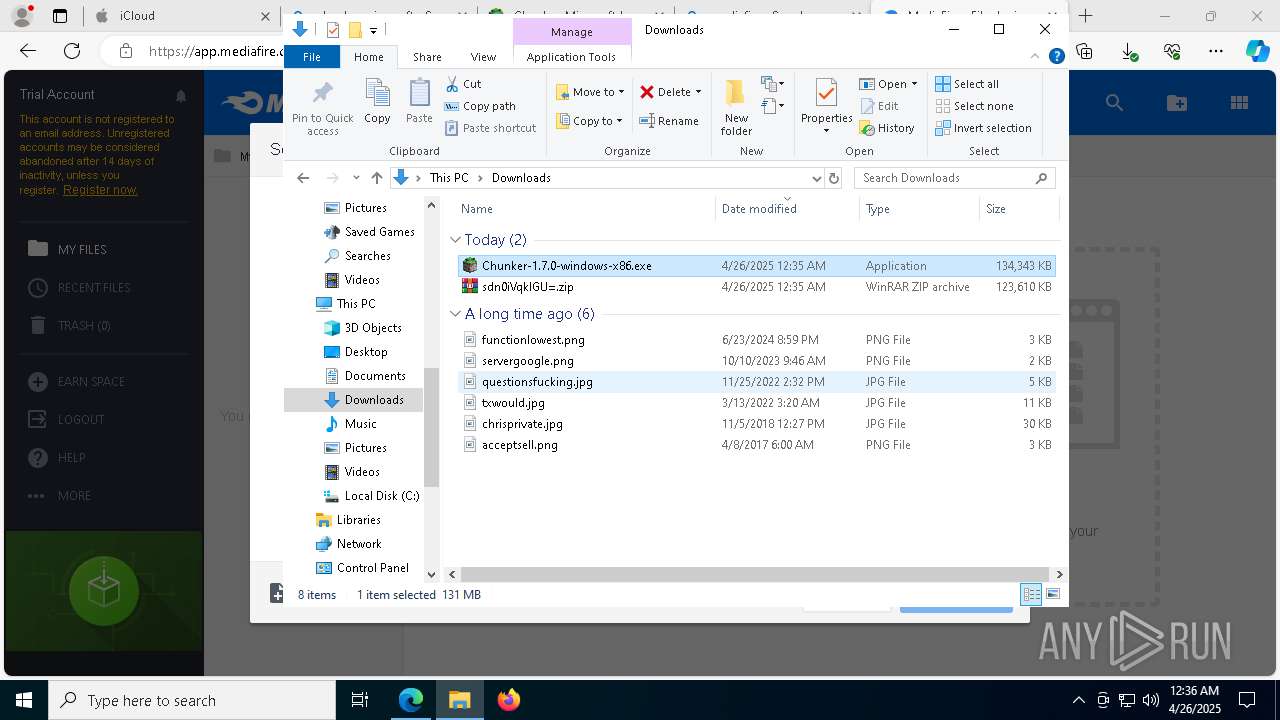
MALICIOUS
No malicious indicators.SUSPICIOUS
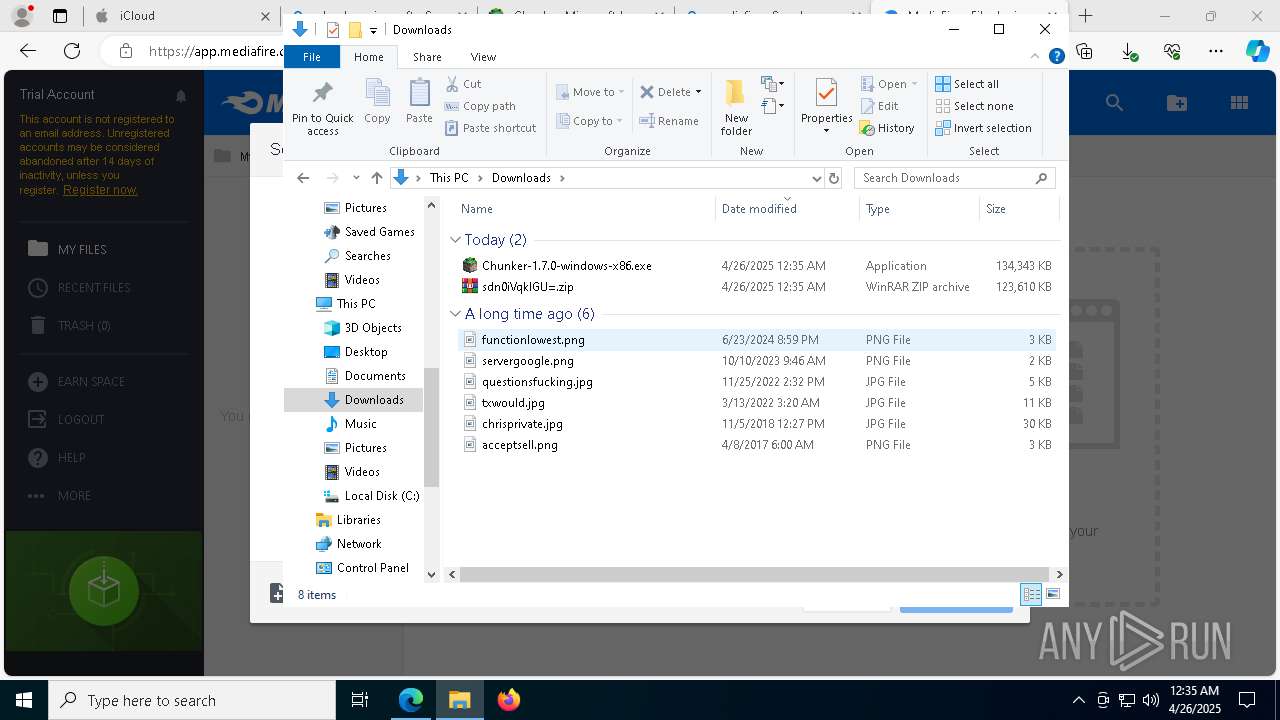
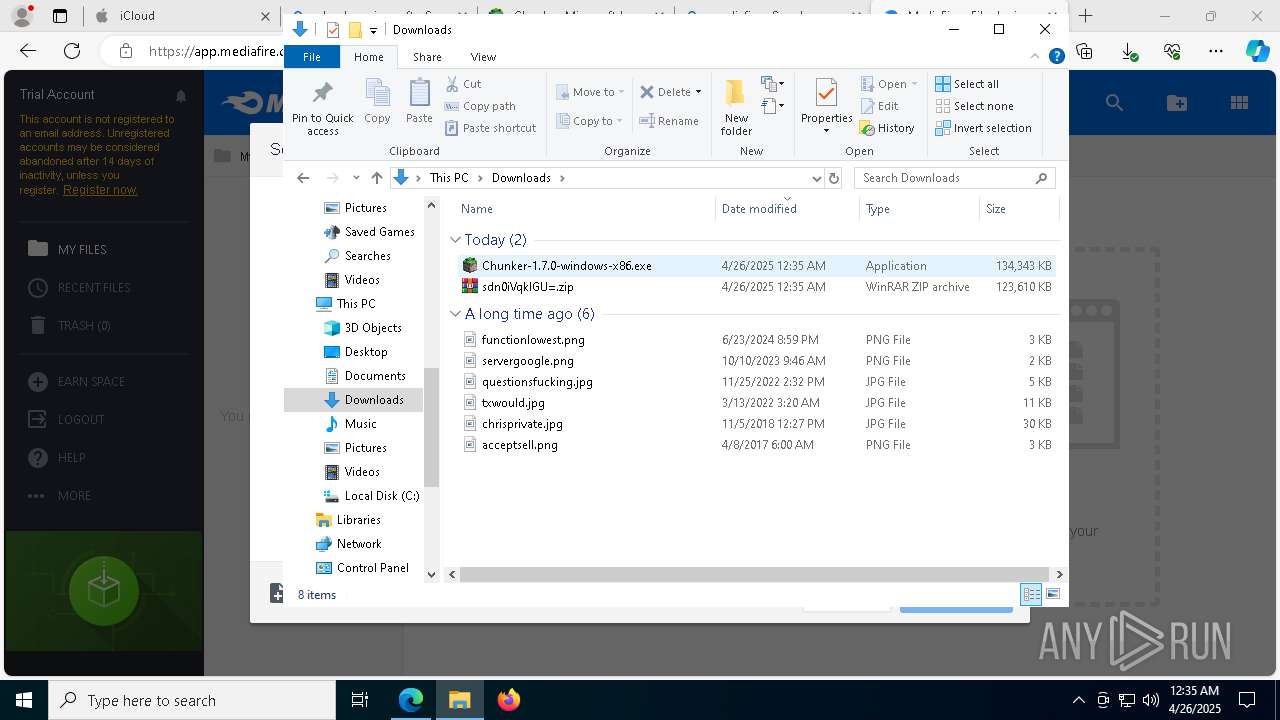
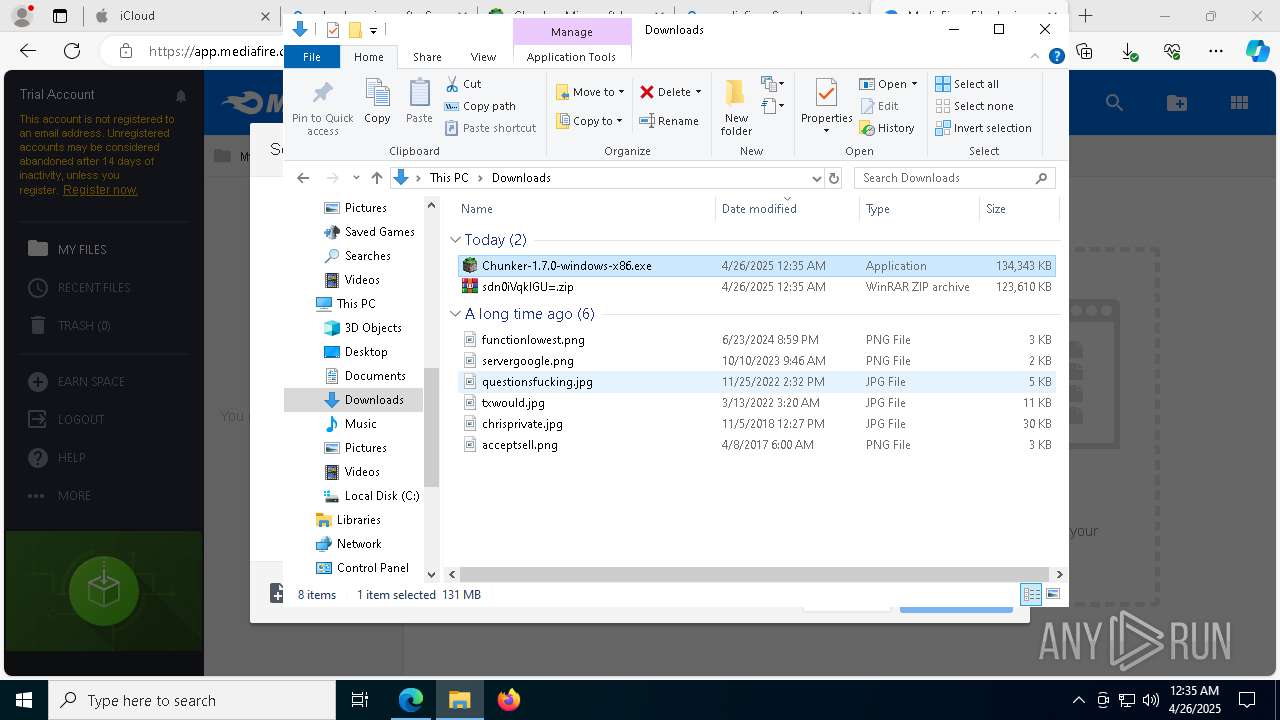
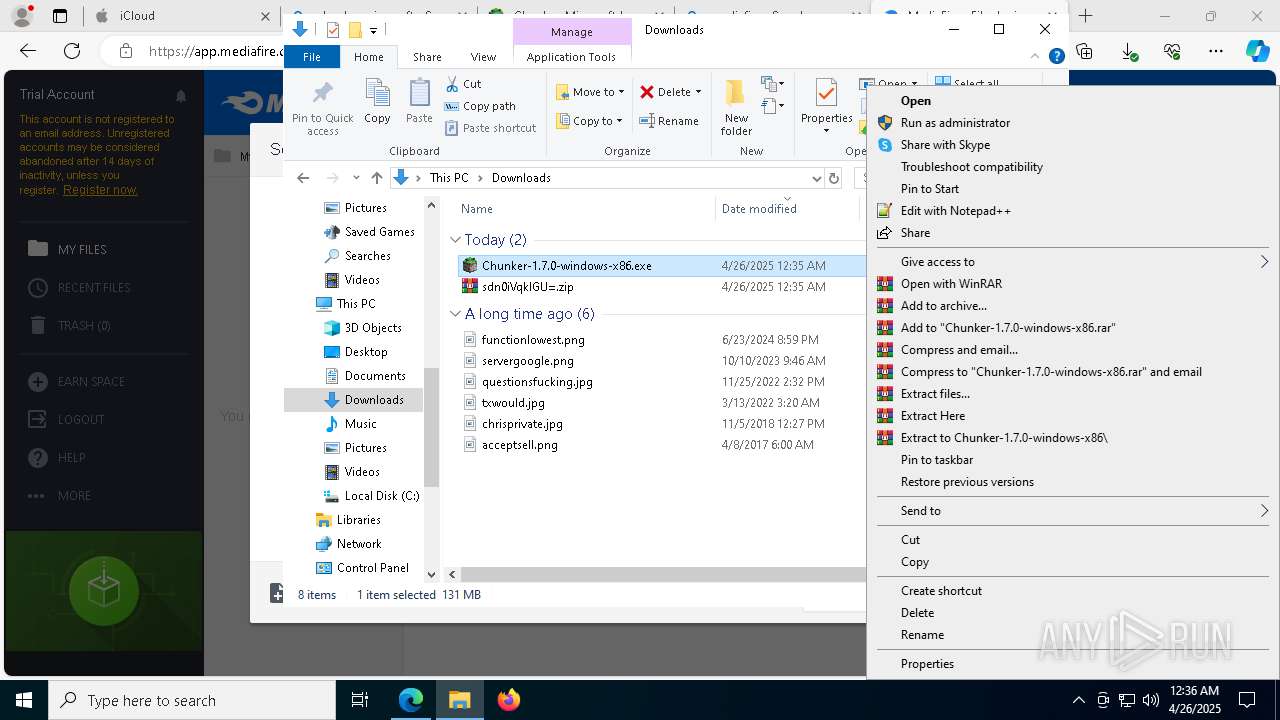
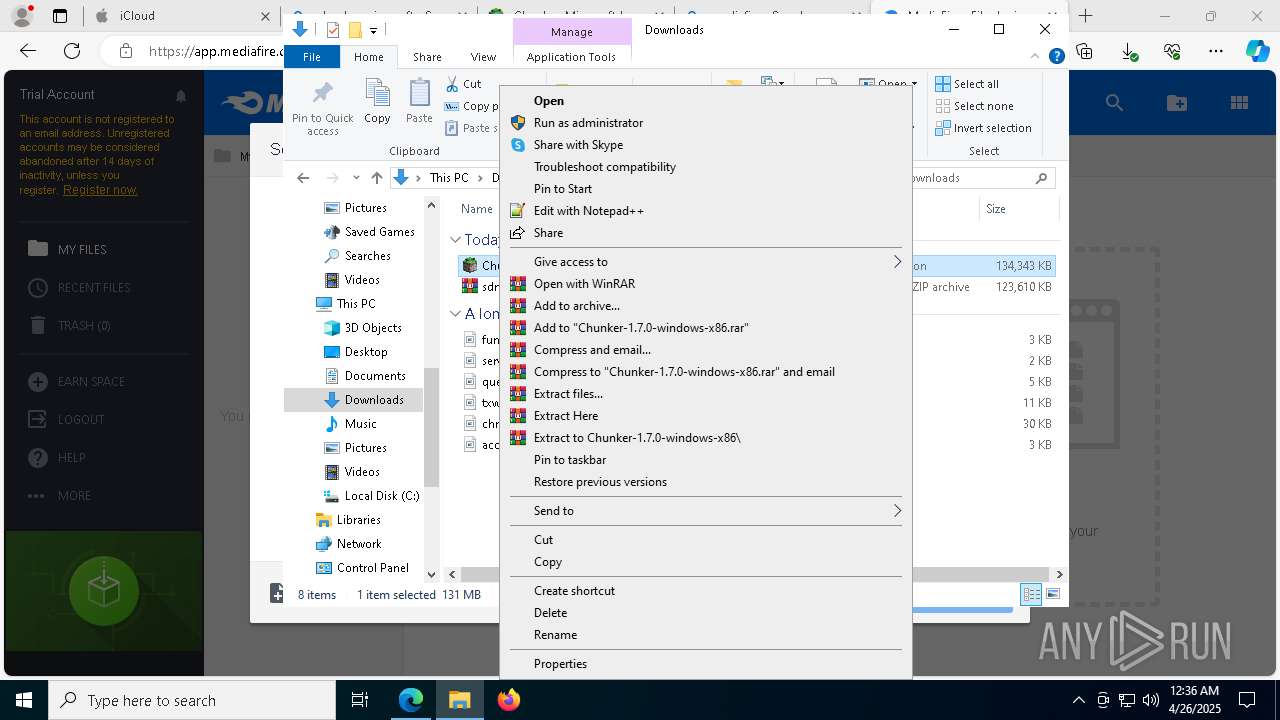
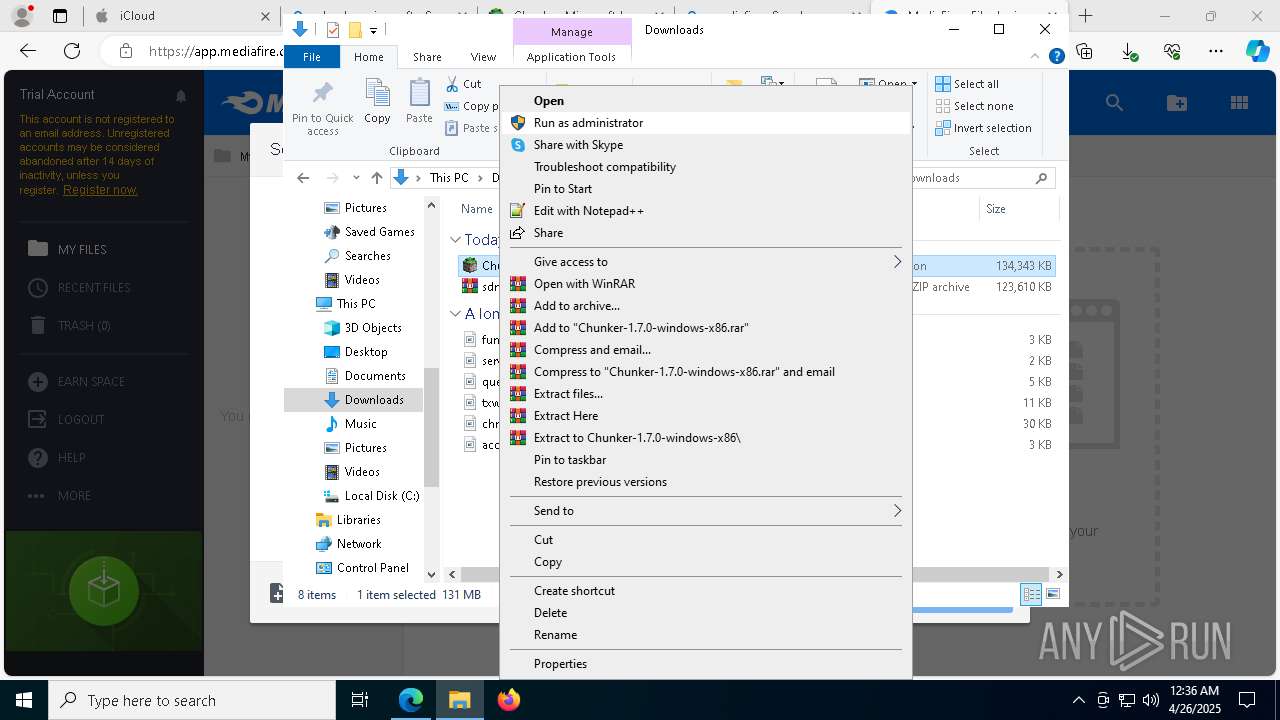
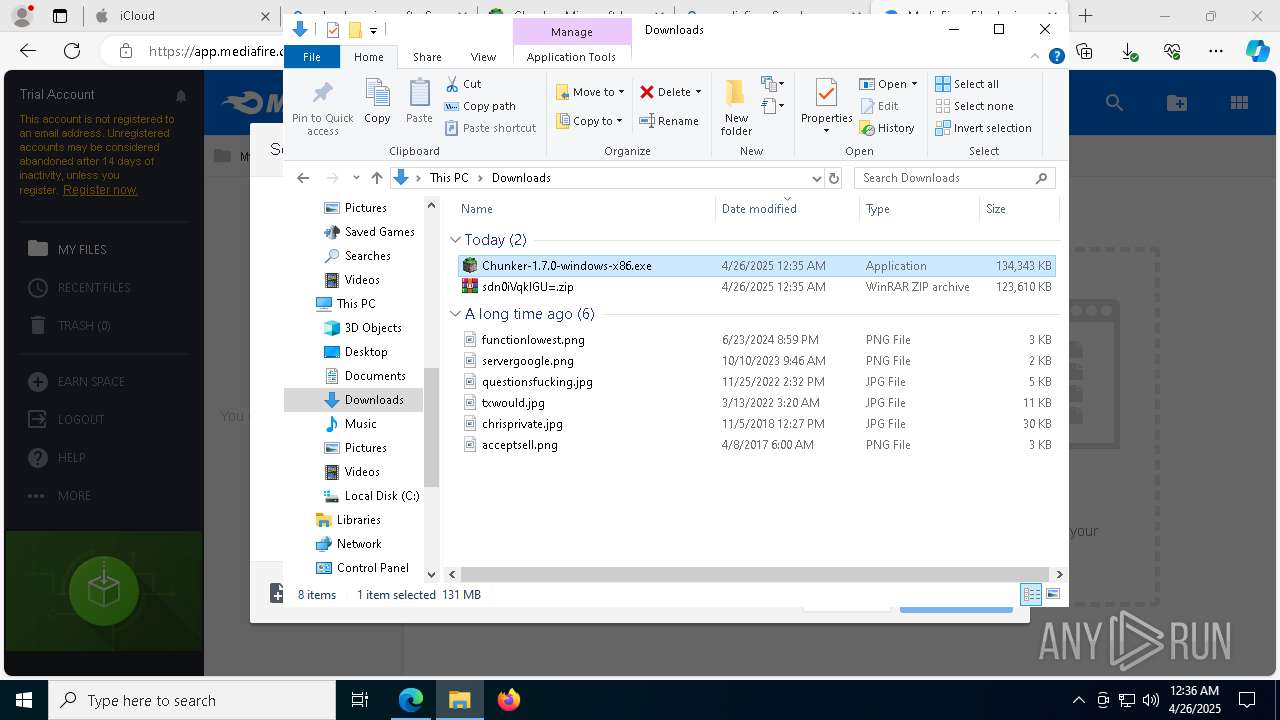
The process creates files with name similar to system file names
- Chunker-1.7.0-windows-x86.exe (PID: 8240)
Executable content was dropped or overwritten
- Chunker-1.7.0-windows-x86.exe (PID: 8240)
- Chunker-1.7.0-windows-x86.exe (PID: 1020)
- Chunker-1.7.0-windows-x86.exe (PID: 4812)
- Chunker-1.7.0-windows-x86.exe (PID: 8872)
There is functionality for taking screenshot (YARA)
- Chunker-1.7.0-windows-x86.exe (PID: 8240)
- Chunker-1.7.0-windows-x86.exe (PID: 1020)
- Chunker-1.7.0-windows-x86.exe (PID: 8872)
- Chunker-1.7.0-windows-x86.exe (PID: 4812)
Drops 7-zip archiver for unpacking
- Chunker-1.7.0-windows-x86.exe (PID: 1020)
- Chunker-1.7.0-windows-x86.exe (PID: 4812)
- Chunker-1.7.0-windows-x86.exe (PID: 8240)
- Chunker-1.7.0-windows-x86.exe (PID: 8872)
Malware-specific behavior (creating "System.dll" in Temp)
- Chunker-1.7.0-windows-x86.exe (PID: 4812)
- Chunker-1.7.0-windows-x86.exe (PID: 8240)
- Chunker-1.7.0-windows-x86.exe (PID: 1020)
- Chunker-1.7.0-windows-x86.exe (PID: 8872)
Process drops legitimate windows executable
- Chunker-1.7.0-windows-x86.exe (PID: 8240)
- Chunker-1.7.0-windows-x86.exe (PID: 8872)
- Chunker-1.7.0-windows-x86.exe (PID: 1020)
- Chunker-1.7.0-windows-x86.exe (PID: 4812)
The process drops C-runtime libraries
- Chunker-1.7.0-windows-x86.exe (PID: 8240)
- Chunker-1.7.0-windows-x86.exe (PID: 4812)
- Chunker-1.7.0-windows-x86.exe (PID: 8872)
- Chunker-1.7.0-windows-x86.exe (PID: 1020)
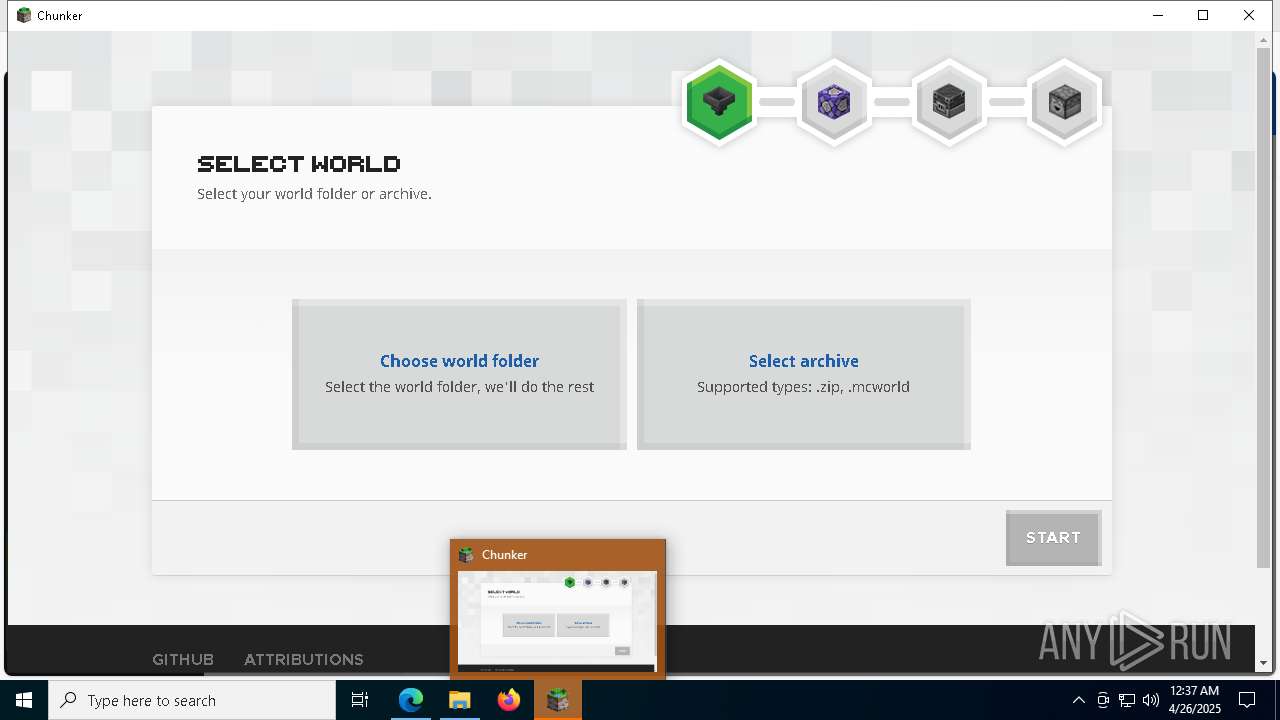
Application launched itself
- Chunker.exe (PID: 8032)
- Chunker.exe (PID: 8264)
- Chunker.exe (PID: 3332)
- chunker-cli.exe (PID: 5400)
- chunker-cli.exe (PID: 9720)
- Chunker.exe (PID: 8952)
INFO
Application launched itself
- msedge.exe (PID: 1852)
Checks supported languages
- identity_helper.exe (PID: 7868)
- Chunker-1.7.0-windows-x86.exe (PID: 8240)
Reads the computer name
- identity_helper.exe (PID: 7868)
- Chunker-1.7.0-windows-x86.exe (PID: 8240)
Executable content was dropped or overwritten
- msedge.exe (PID: 1852)
- msedge.exe (PID: 9588)
Reads security settings of Internet Explorer
- explorer.exe (PID: 5492)
Reads the software policy settings
- slui.exe (PID: 5304)
- explorer.exe (PID: 5492)
Reads Environment values
- identity_helper.exe (PID: 7868)
Checks proxy server information
- explorer.exe (PID: 5492)
Creates files or folders in the user directory
- explorer.exe (PID: 5492)
The sample compiled with english language support
- Chunker-1.7.0-windows-x86.exe (PID: 1020)
- Chunker-1.7.0-windows-x86.exe (PID: 4812)
- Chunker-1.7.0-windows-x86.exe (PID: 8240)
- Chunker-1.7.0-windows-x86.exe (PID: 8872)
- msedge.exe (PID: 9588)
Create files in a temporary directory
- Chunker-1.7.0-windows-x86.exe (PID: 8240)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
249
Monitored processes
113
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7952 --field-trial-handle=1964,i,10504878518341654231,11494734741647347263,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 896 | "C:\Users\admin\AppData\Local\Temp\2vYFJzbsBalGIxgxd0K1pZuJBXQ\Chunker.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\chunker-electron" --bypasscsp-schemes=session,static --fetch-schemes=session,static --field-trial-handle=1728,i,13993676497153309862,1734426279961309595,262144 --enable-features=PdfUseShowSaveFilePicker --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit --variations-seed-version --mojo-platform-channel-handle=2232 /prefetch:3 | C:\Users\admin\AppData\Local\Temp\2vYFJzbsBalGIxgxd0K1pZuJBXQ\Chunker.exe | — | Chunker.exe | |||||||||||
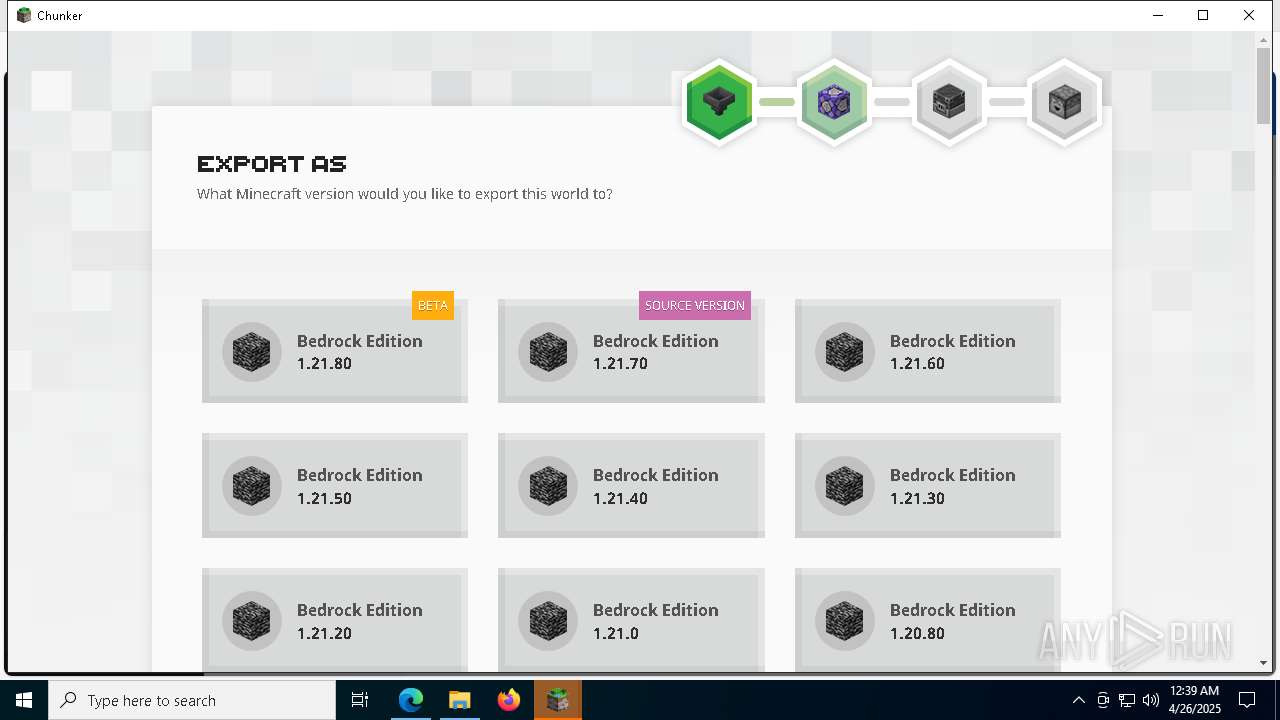
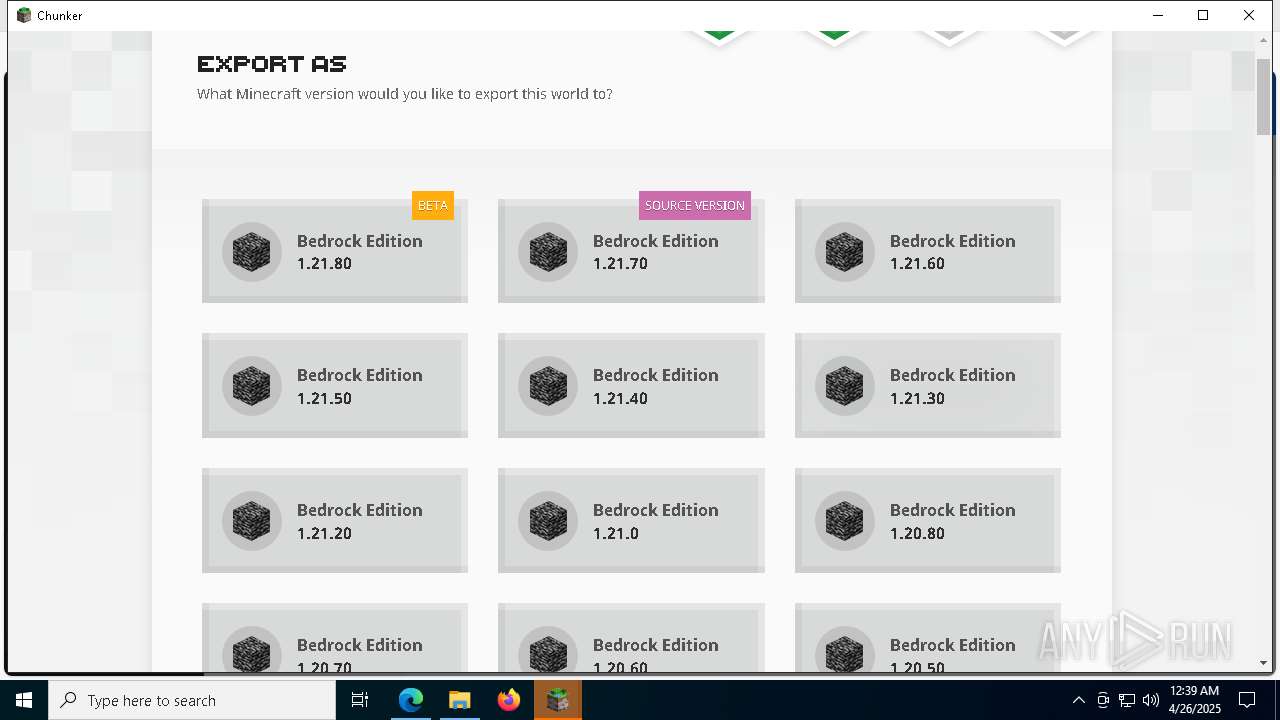
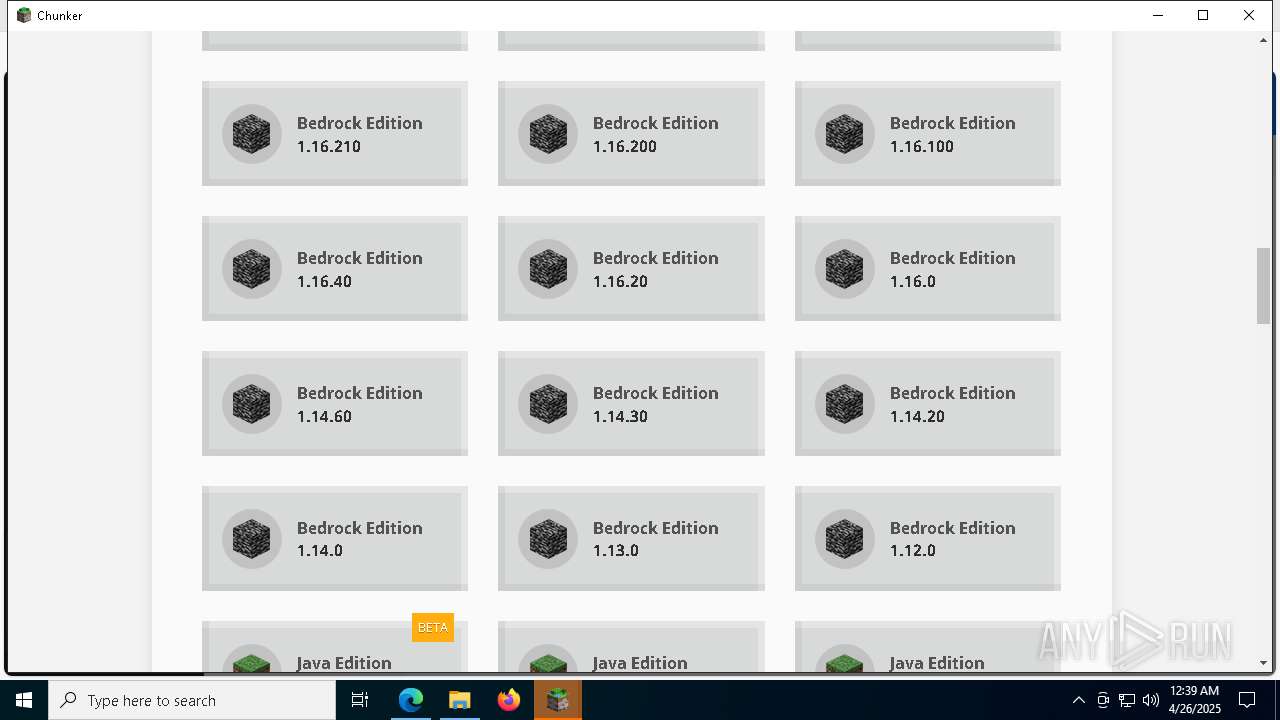
User: admin Company: Hive Games Limited Integrity Level: MEDIUM Description: Convert worlds between Java and Bedrock. Version: 1.7.0 Modules
| |||||||||||||||
| 976 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=8332 --field-trial-handle=1964,i,10504878518341654231,11494734741647347263,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1012 | "C:\Users\admin\AppData\Local\Temp\2vYFJzbsBalGIxgxd0K1pZuJBXQ\Chunker.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --user-data-dir="C:\Users\admin\AppData\Roaming\chunker-electron" --gpu-preferences=UAAAAAAAAADoAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=1728,i,13993676497153309862,1734426279961309595,262144 --enable-features=PdfUseShowSaveFilePicker --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit --variations-seed-version --mojo-platform-channel-handle=3344 /prefetch:8 | C:\Users\admin\AppData\Local\Temp\2vYFJzbsBalGIxgxd0K1pZuJBXQ\Chunker.exe | — | Chunker.exe | |||||||||||
User: admin Company: Hive Games Limited Integrity Level: MEDIUM Description: Convert worlds between Java and Bedrock. Exit code: 0 Version: 1.7.0 Modules
| |||||||||||||||
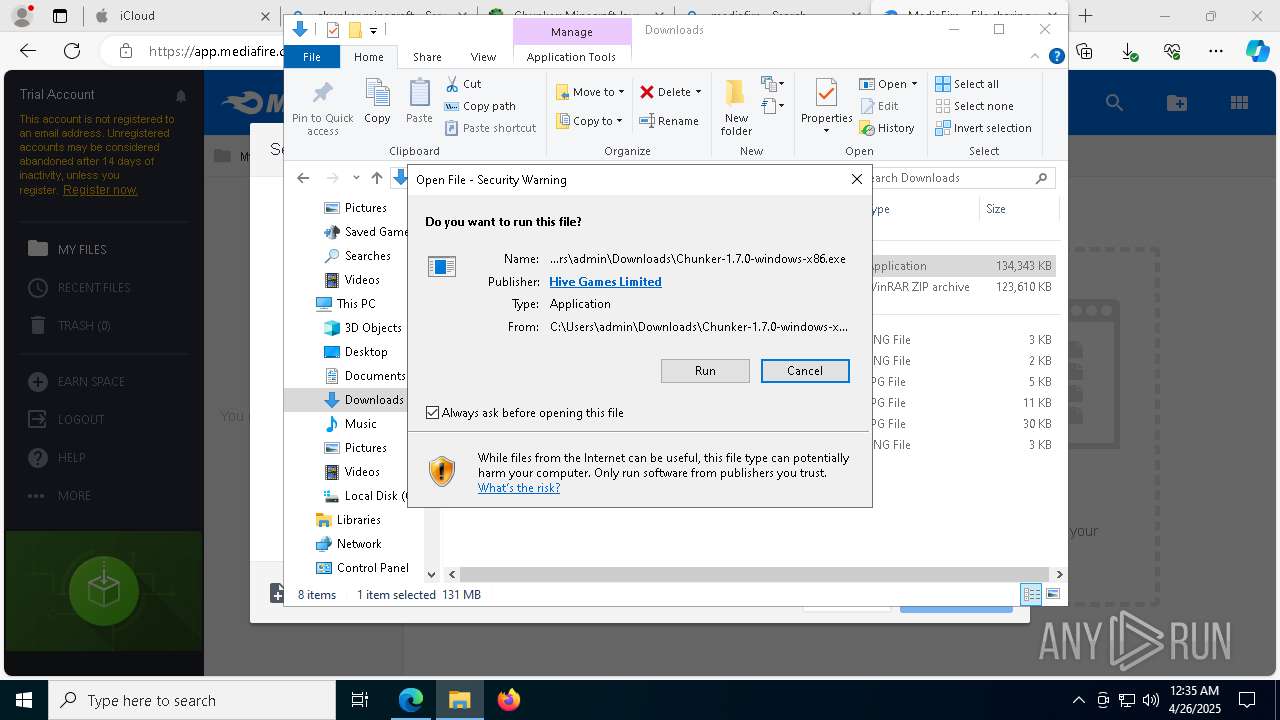
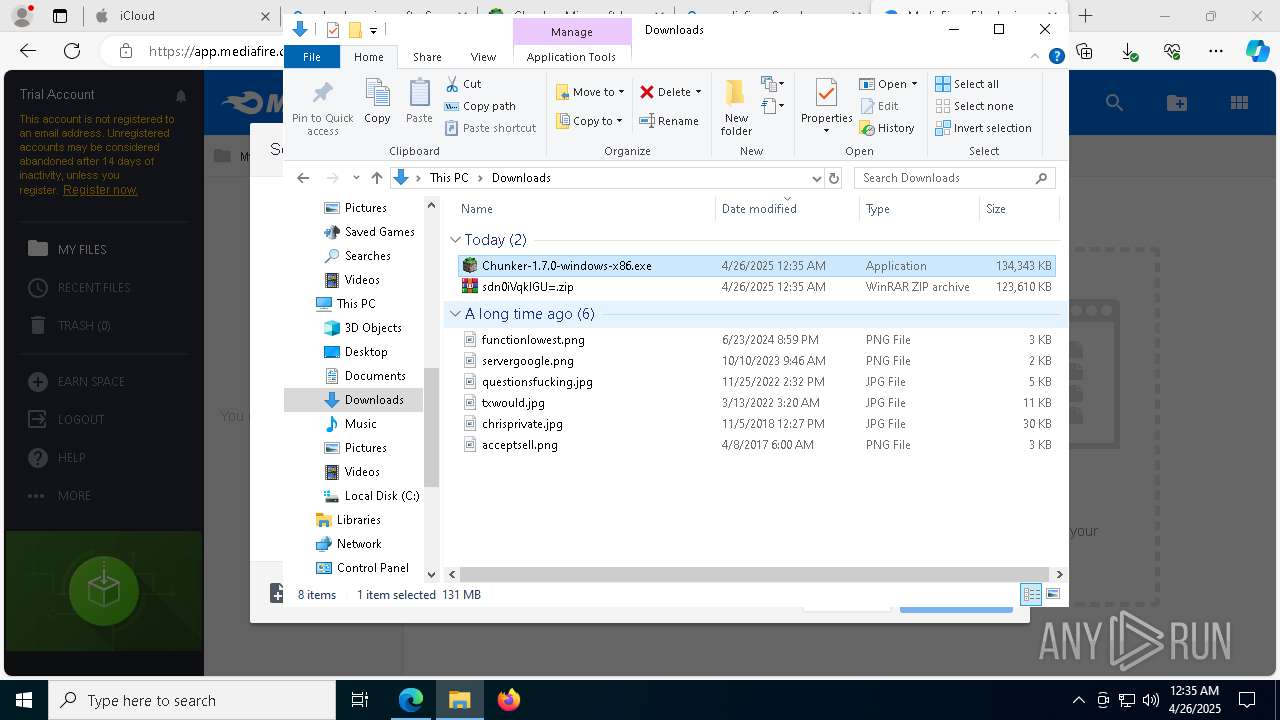
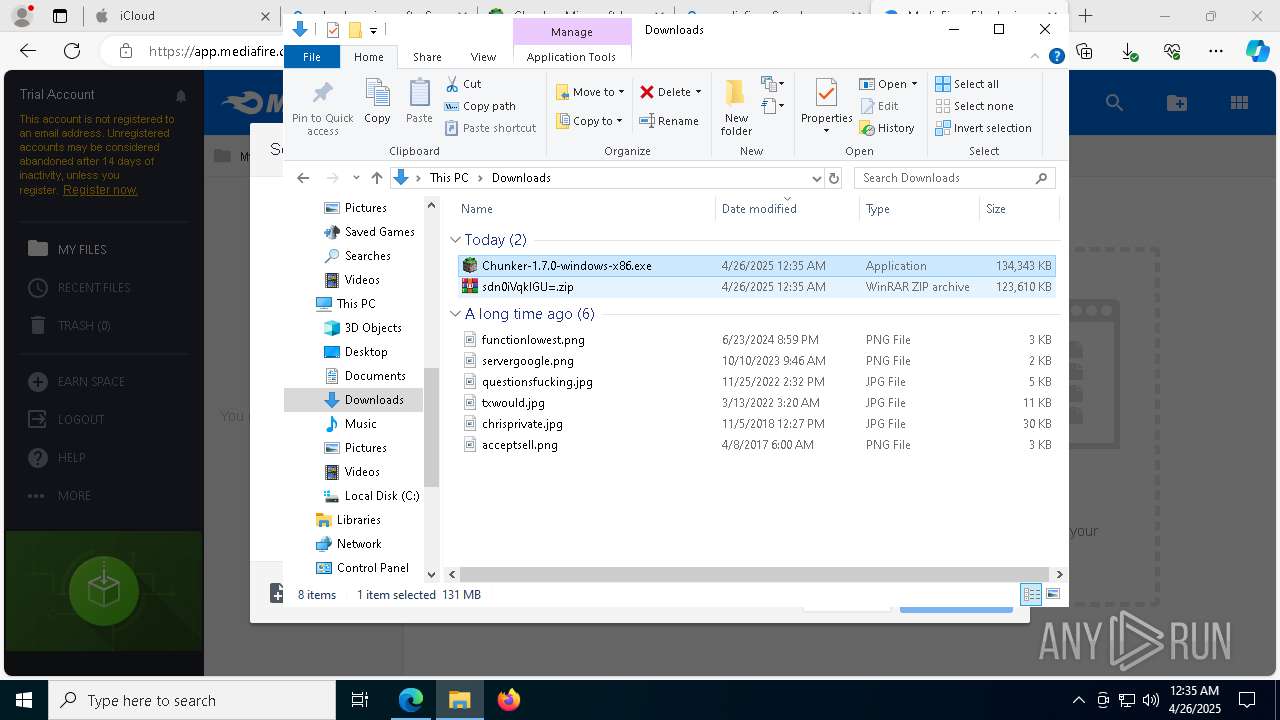
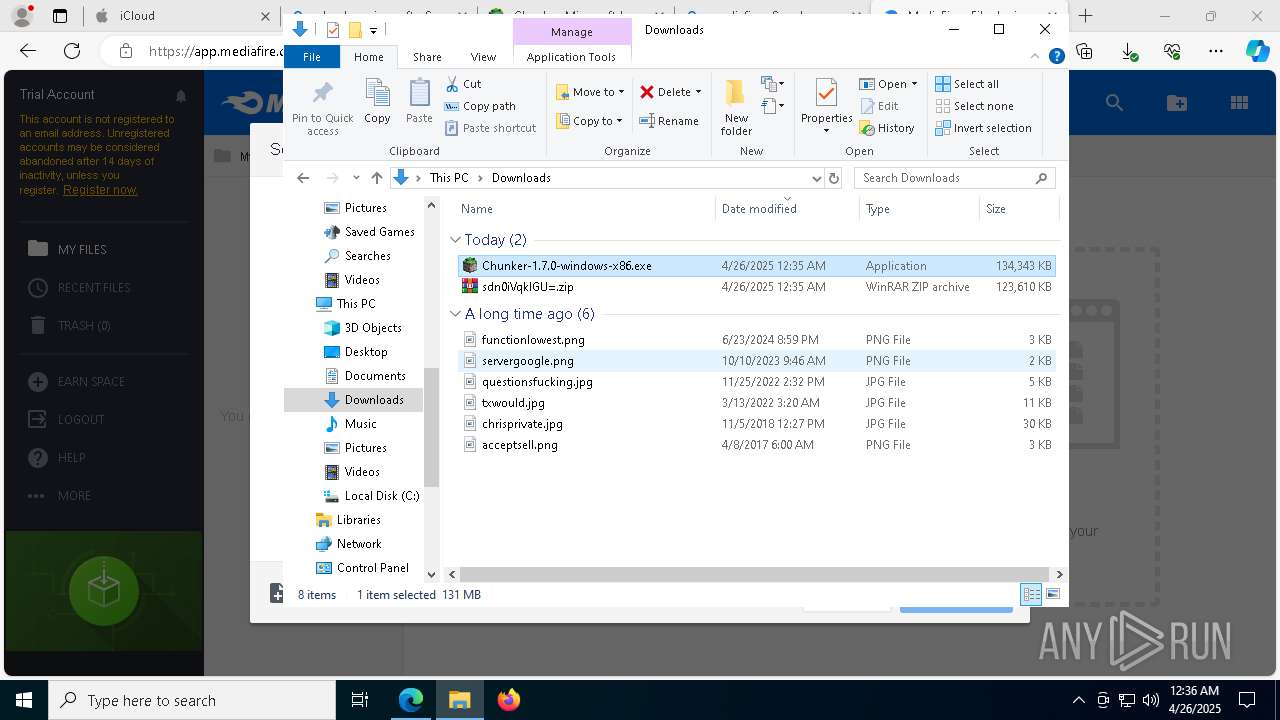
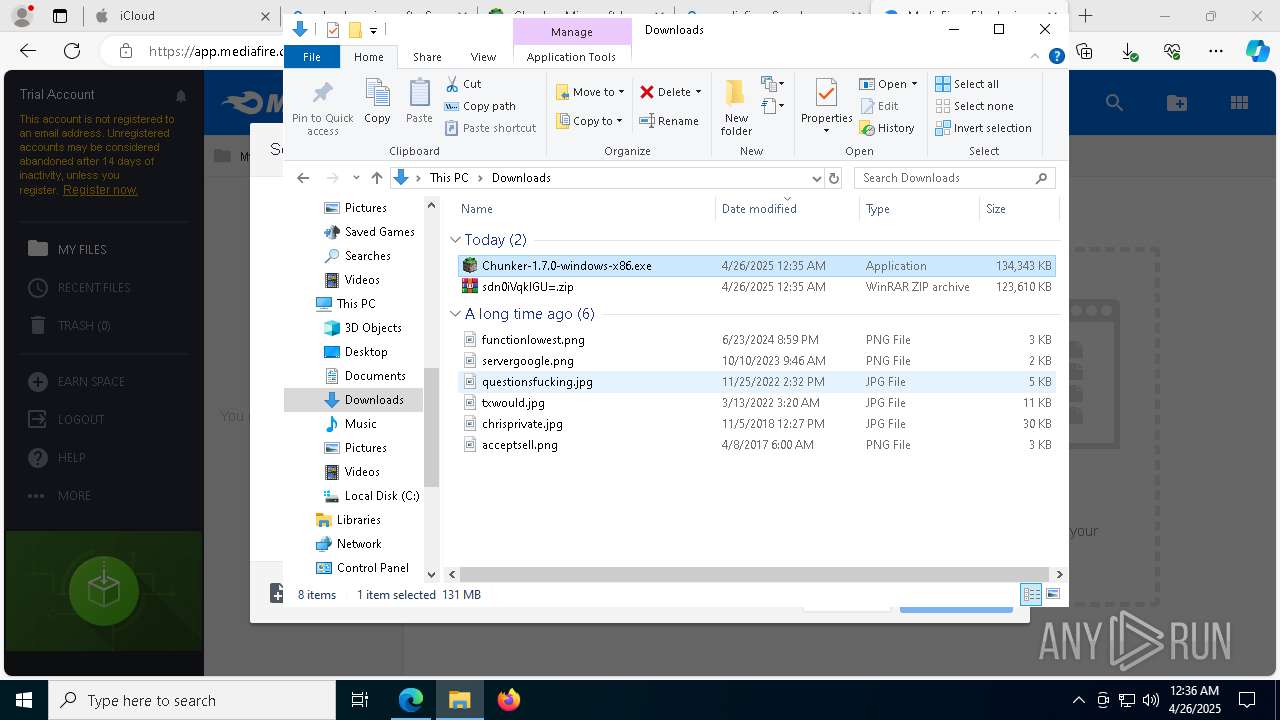
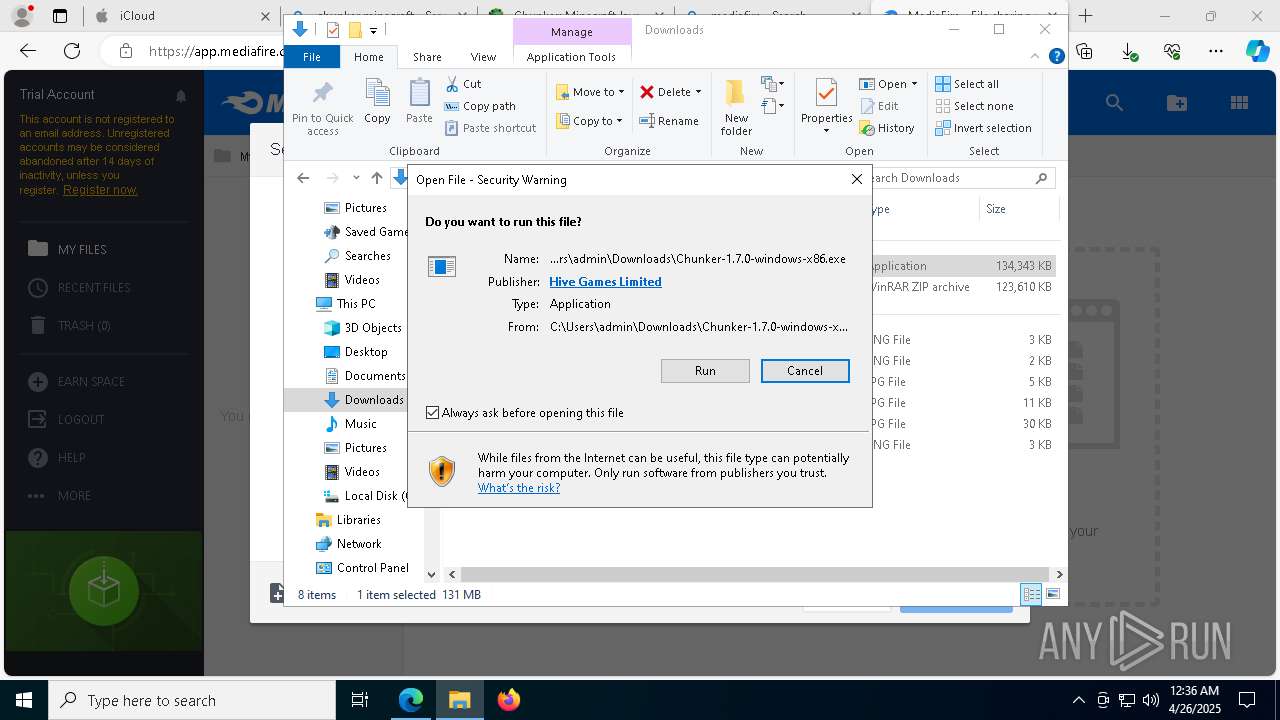
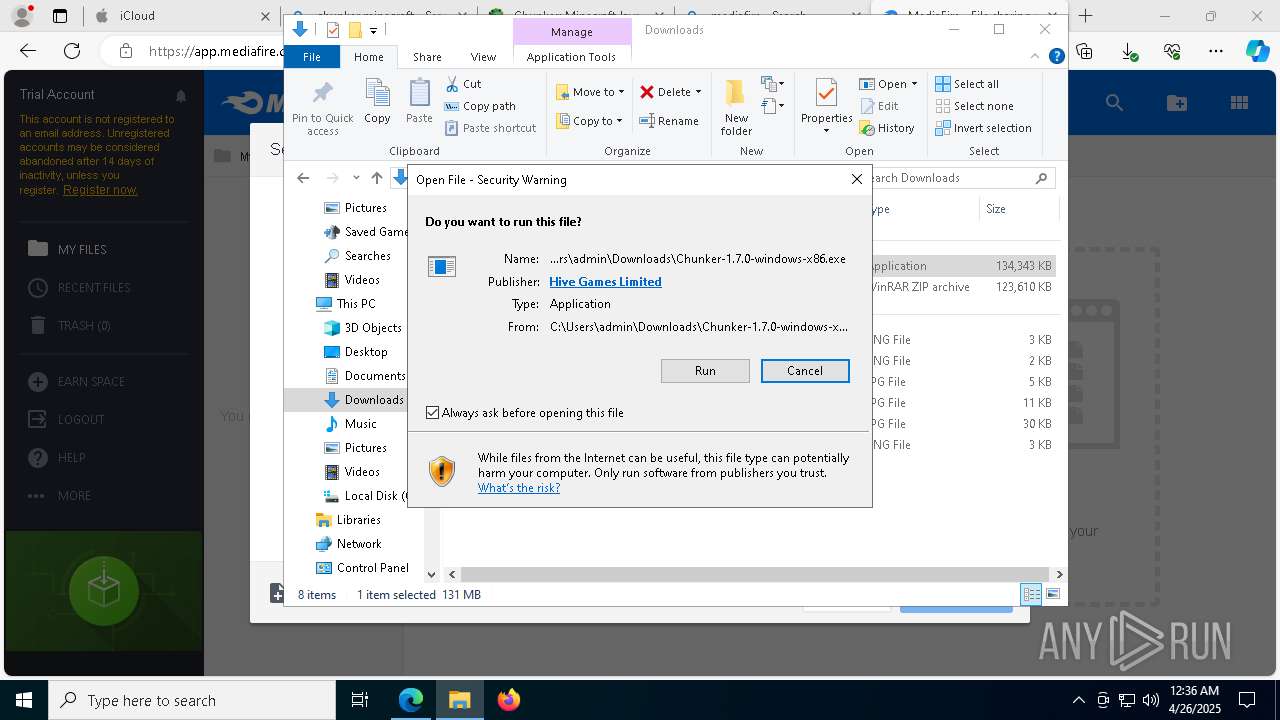
| 1020 | "C:\Users\admin\Downloads\Chunker-1.7.0-windows-x86.exe" | C:\Users\admin\Downloads\Chunker-1.7.0-windows-x86.exe | explorer.exe | ||||||||||||
User: admin Company: Hive Games Limited Integrity Level: MEDIUM Description: Convert worlds between Java and Bedrock. Version: 1.7.0 Modules
| |||||||||||||||
| 1272 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6040 --field-trial-handle=1964,i,10504878518341654231,11494734741647347263,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1272 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=37 --mojo-platform-channel-handle=7924 --field-trial-handle=1964,i,10504878518341654231,11494734741647347263,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1512 | "C:\Users\admin\AppData\Local\Temp\2vYFJzbsBalGIxgxd0K1pZuJBXQ\Chunker.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\chunker-electron" --bypasscsp-schemes=session,static --fetch-schemes=session,static --app-path="C:\Users\admin\AppData\Local\Temp\2vYFJzbsBalGIxgxd0K1pZuJBXQ\resources\app.asar" --enable-sandbox --disable-databases --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --field-trial-handle=1816,i,18404556994189535482,1354334808521908357,262144 --enable-features=PdfUseShowSaveFilePicker --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit --variations-seed-version --mojo-platform-channel-handle=2516 /prefetch:1 | C:\Users\admin\AppData\Local\Temp\2vYFJzbsBalGIxgxd0K1pZuJBXQ\Chunker.exe | — | Chunker.exe | |||||||||||
User: admin Company: Hive Games Limited Integrity Level: LOW Description: Convert worlds between Java and Bedrock. Version: 1.7.0 Modules
| |||||||||||||||
| 1616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=8984 --field-trial-handle=1964,i,10504878518341654231,11494734741647347263,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5588 --field-trial-handle=1964,i,10504878518341654231,11494734741647347263,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
65 774
Read events
65 297
Write events
264
Delete events
213
Modification events
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:000000000004030C |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (1852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1852) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4D1C7EE639922F00 | |||
| (PID) Process: | (1852) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 306587E639922F00 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:0000000000030276 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (1852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262924 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {677C1D40-6D2D-4842-B403-BF693D4C2F4A} | |||
| (PID) Process: | (1852) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262924 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1581691A-E5AE-478B-B8B1-BB4C8E1E224B} | |||
Executable files
777
Suspicious files
2 496
Text files
1 909
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b6bf.TMP | — | |
MD5:— | SHA256:— | |||
| 1852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b6cf.TMP | — | |
MD5:— | SHA256:— | |||
| 1852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b6cf.TMP | — | |
MD5:— | SHA256:— | |||
| 1852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b6cf.TMP | — | |
MD5:— | SHA256:— | |||
| 1852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b6bf.TMP | — | |
MD5:— | SHA256:— | |||
| 1852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
57
TCP/UDP connections
245
DNS requests
265
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6540 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
9088 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1746052150&P2=404&P3=2&P4=DEFjgV%2b4RJBCaZP%2fq0lBgvtF%2b66iFxAjQld2EGmK7GDxbiV7viVfDAFtf3Z4gDTAcFjcqSjqbr%2f5vkZDutgMyQ%3d%3d | unknown | — | — | whitelisted |
6540 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
9088 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1746052150&P2=404&P3=2&P4=DEFjgV%2b4RJBCaZP%2fq0lBgvtF%2b66iFxAjQld2EGmK7GDxbiV7viVfDAFtf3Z4gDTAcFjcqSjqbr%2f5vkZDutgMyQ%3d%3d | unknown | — | — | whitelisted |
5492 | explorer.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBTOQYLFSE5GO%2FpaRVfYu7d9gZEbQAQU2UEpsA8PY2zvadf1zSmepEhqMOYCEzMAAAAGShr6zwVhanQAAAAAAAY%3D | unknown | — | — | whitelisted |
5492 | explorer.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQQ9RoB7druAplRfZIM2Szg4IoTvQQUdpw2dBPRkH1hX7MC64D0mUulPoUCEzMAAmWDDQiiKc%2BjsLUAAAACZYM%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1852 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7332 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7332 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
www.icloud.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
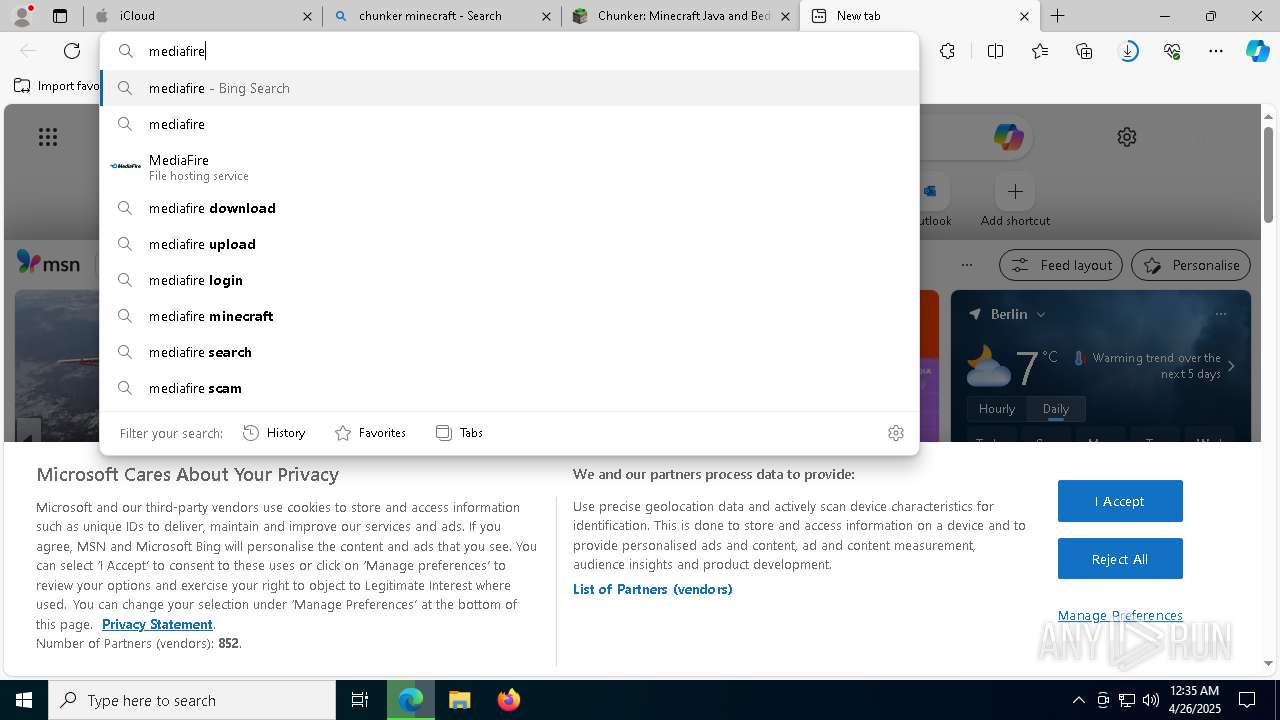
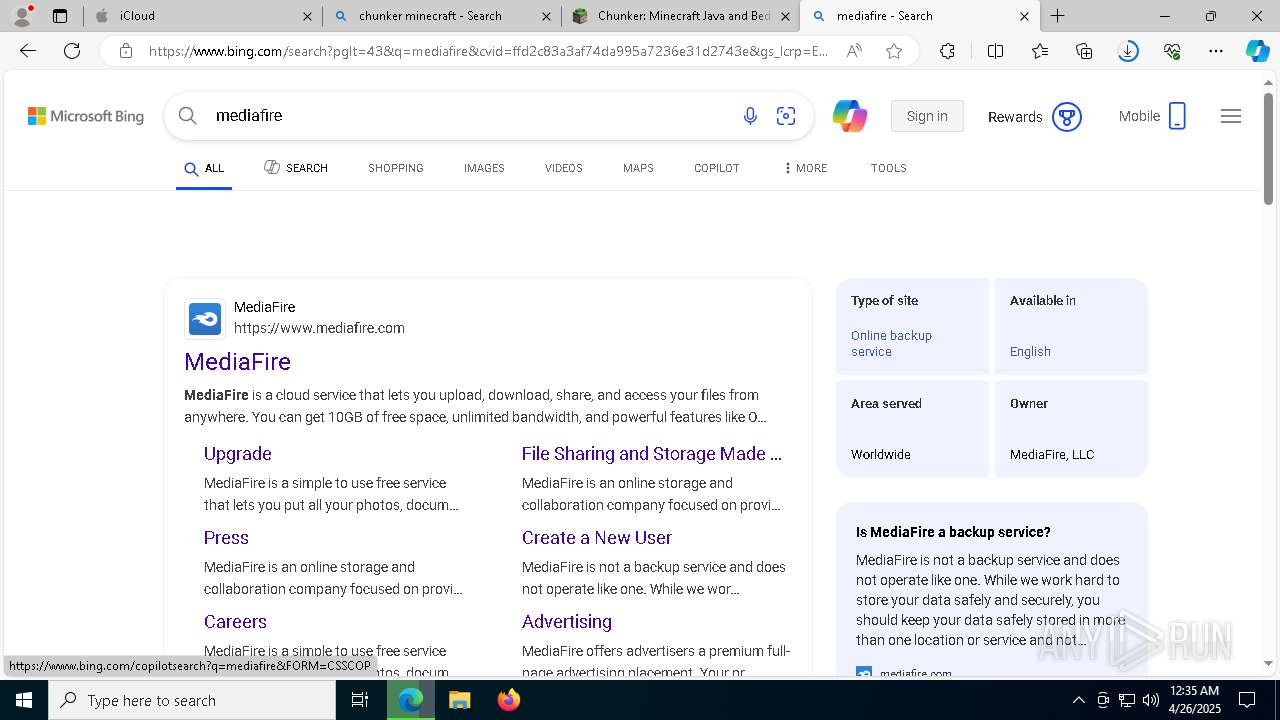
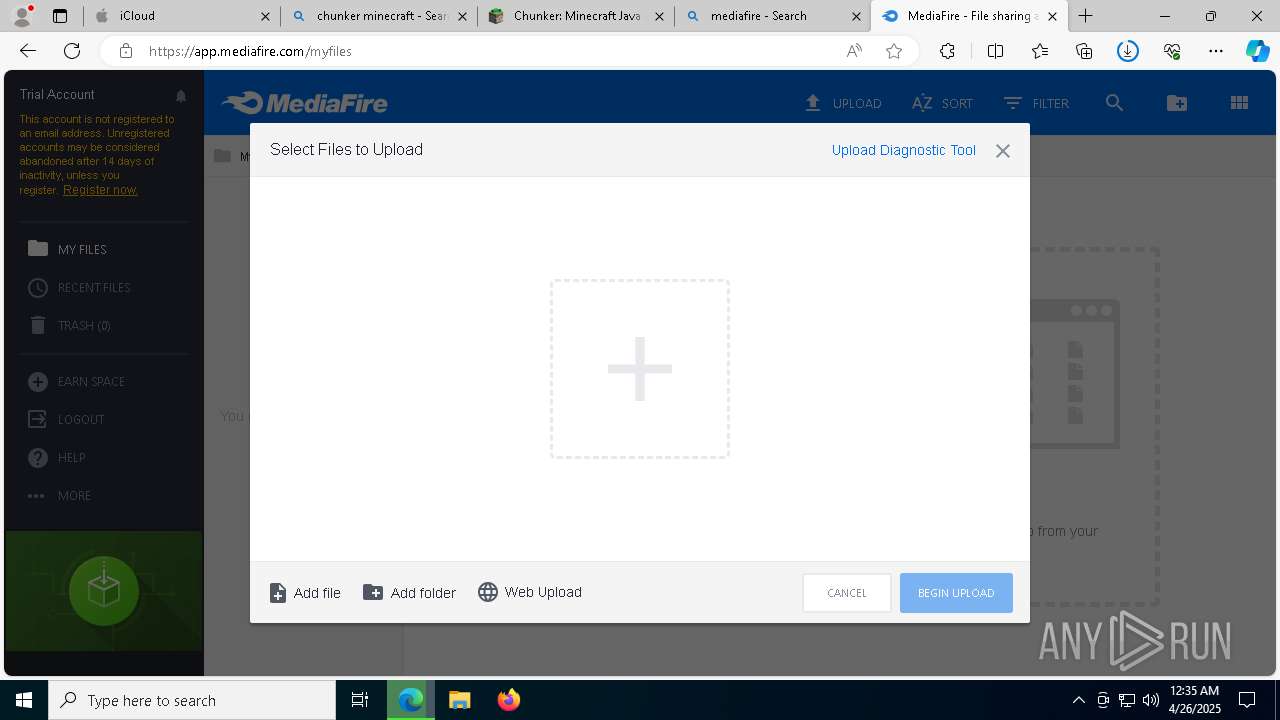
7332 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7332 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7332 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7332 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7332 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7332 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7332 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7332 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7332 | msedge.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (polyfill .io) in DNS Lookup |
7332 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |