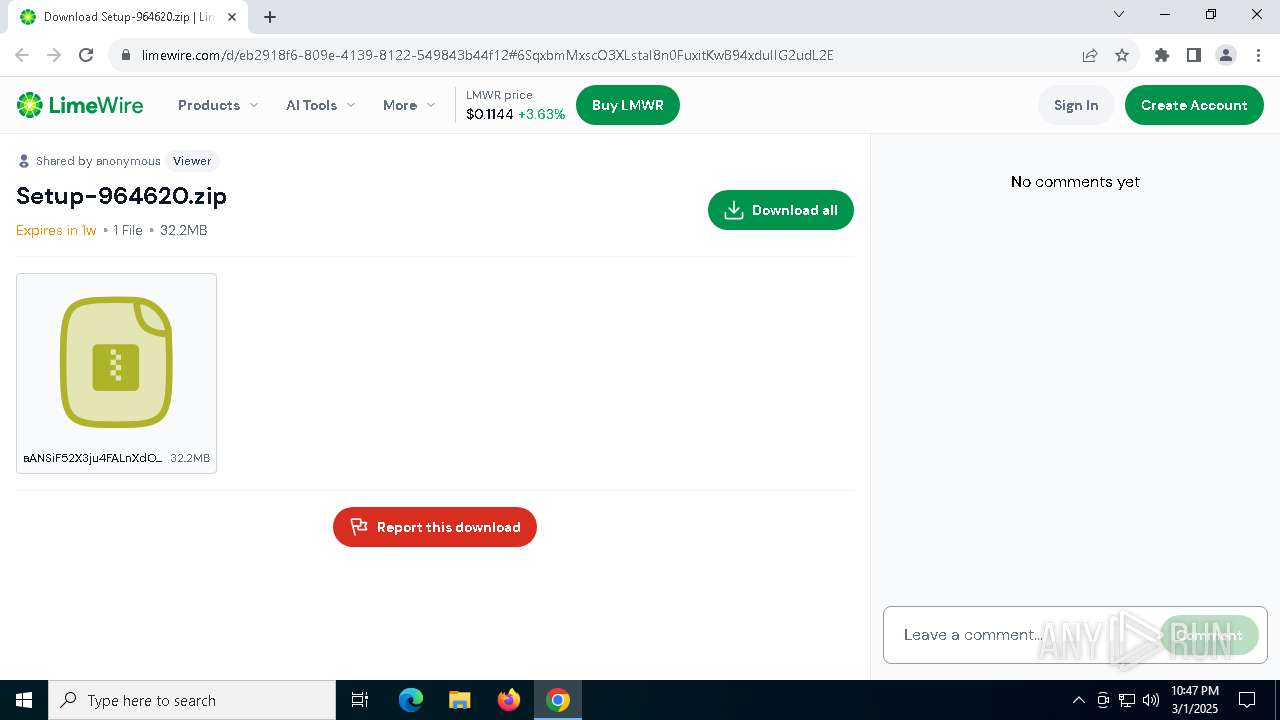
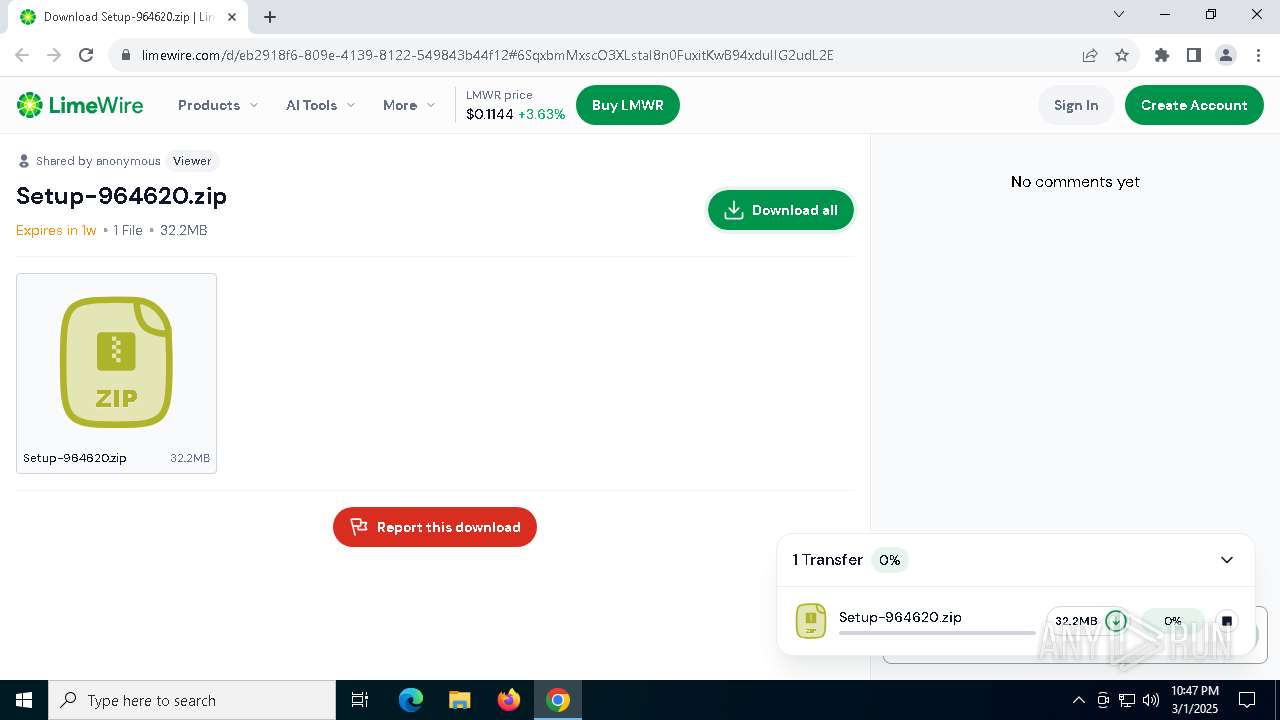
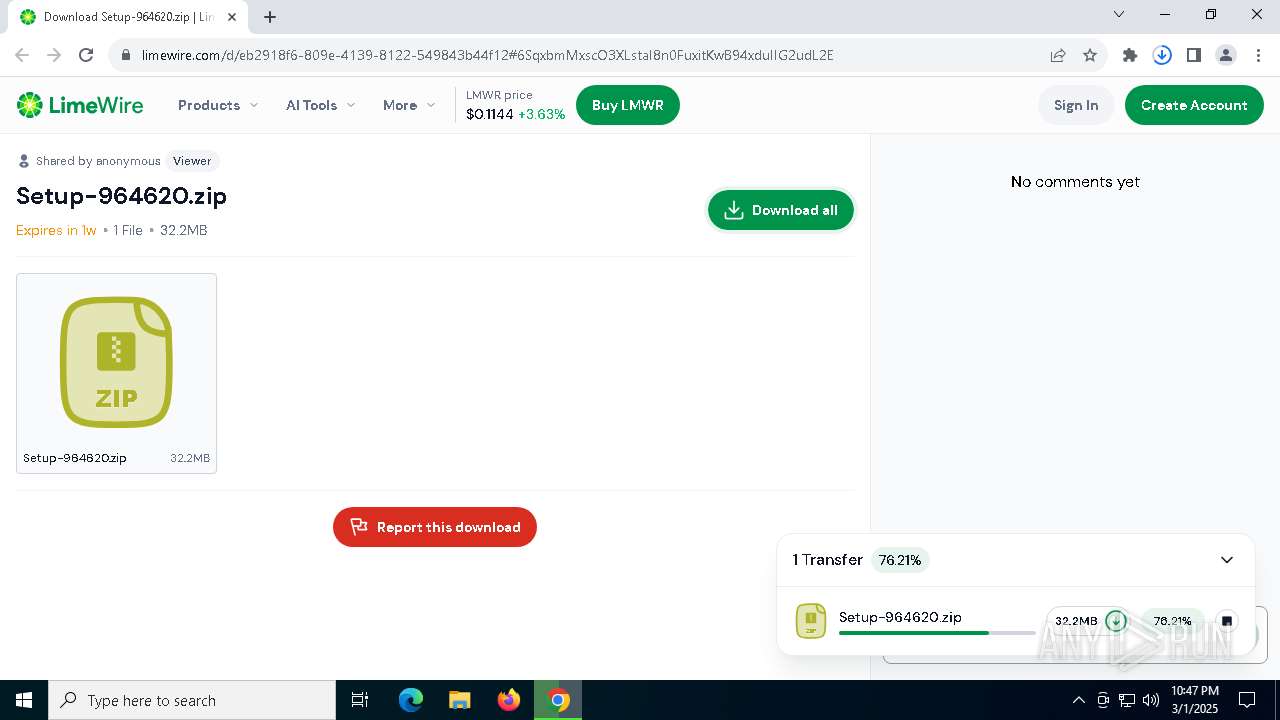
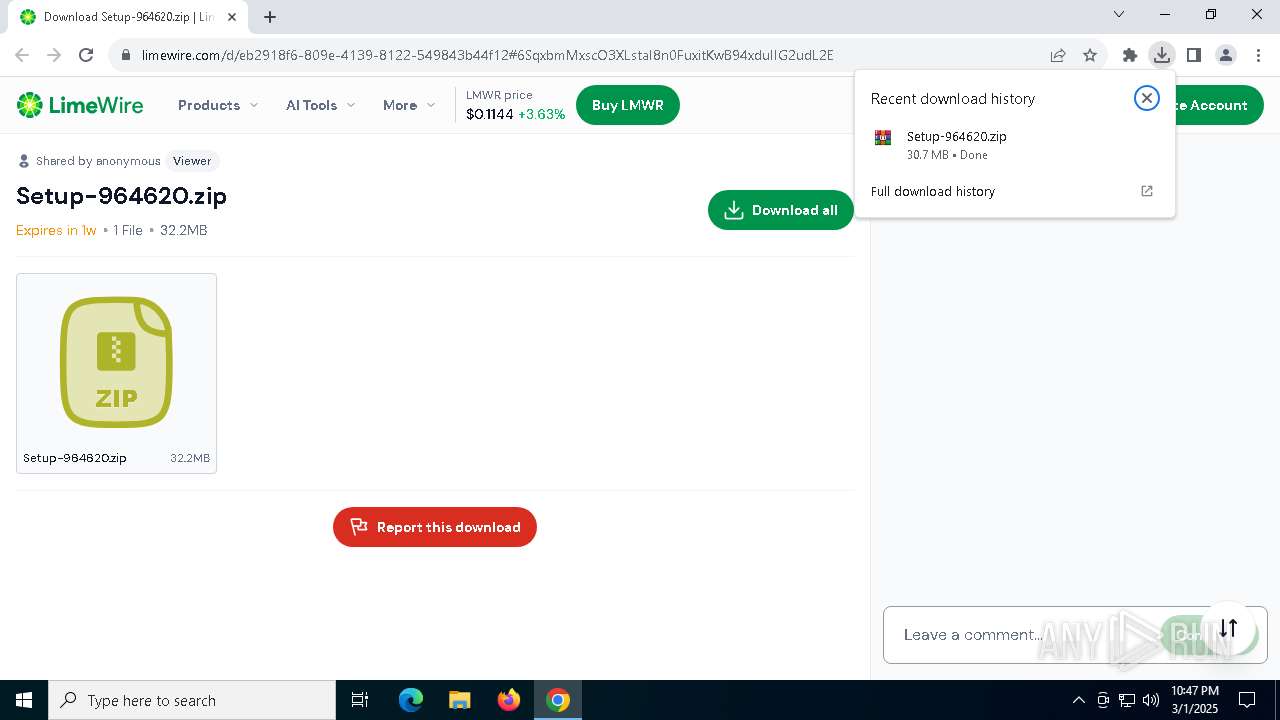
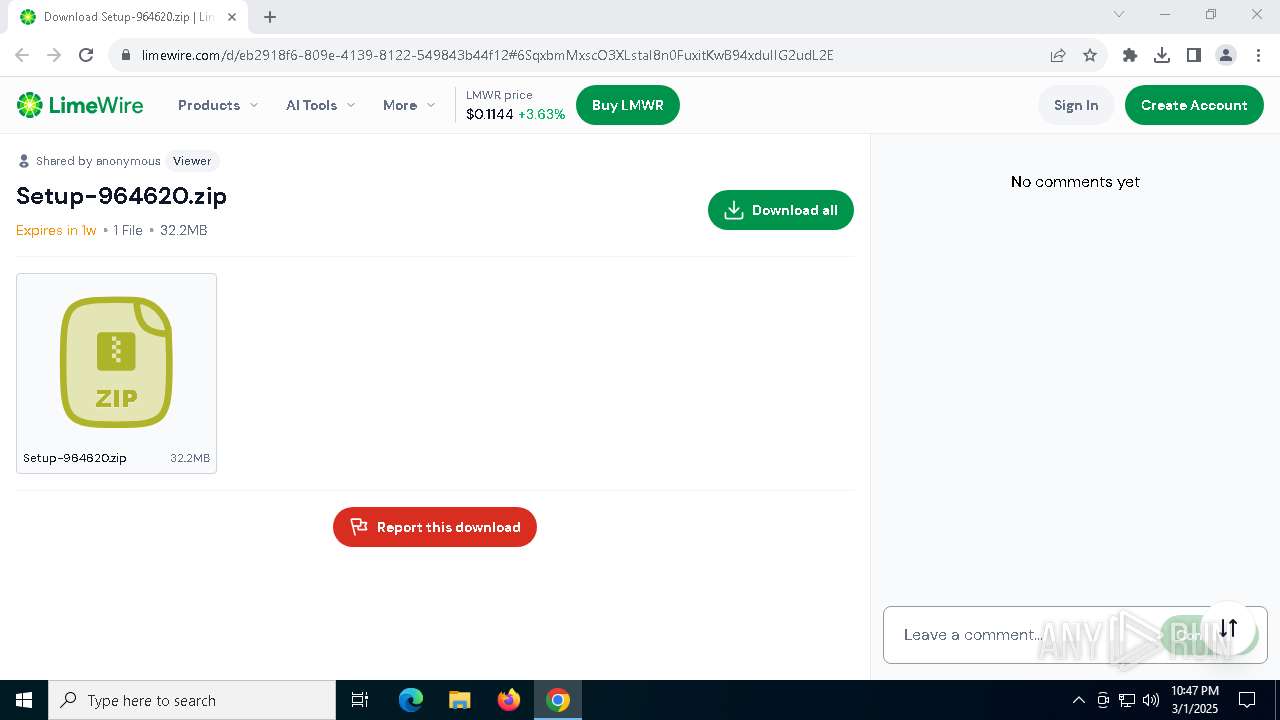
| URL: | https://limewire.com/d/eb2918f6-809e-4139-8122-549843b44f12#6SqxbmMxscO3XLstaI8n0FuxitKwB94xduIIG2udL2E |
| Full analysis: | https://app.any.run/tasks/d9abdcb1-958d-44fc-9db2-c7cbb83005e7 |
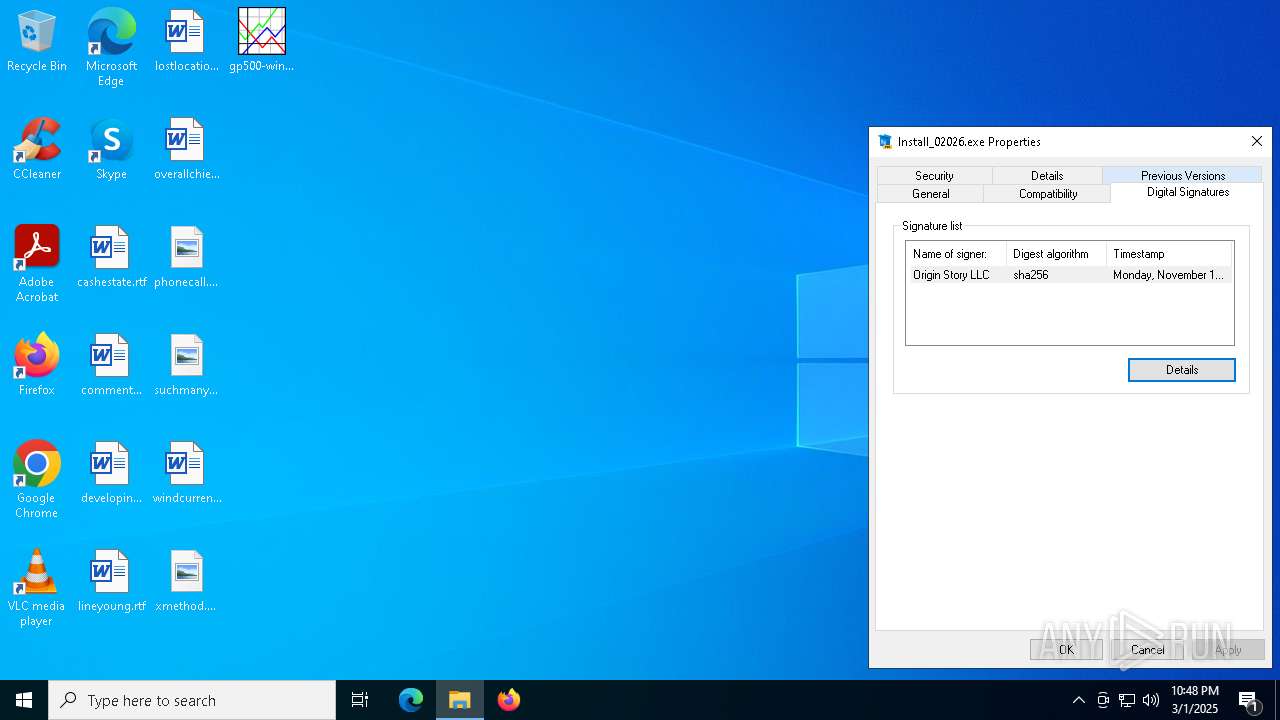
| Verdict: | Malicious activity |
| Analysis date: | March 01, 2025, 22:46:57 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
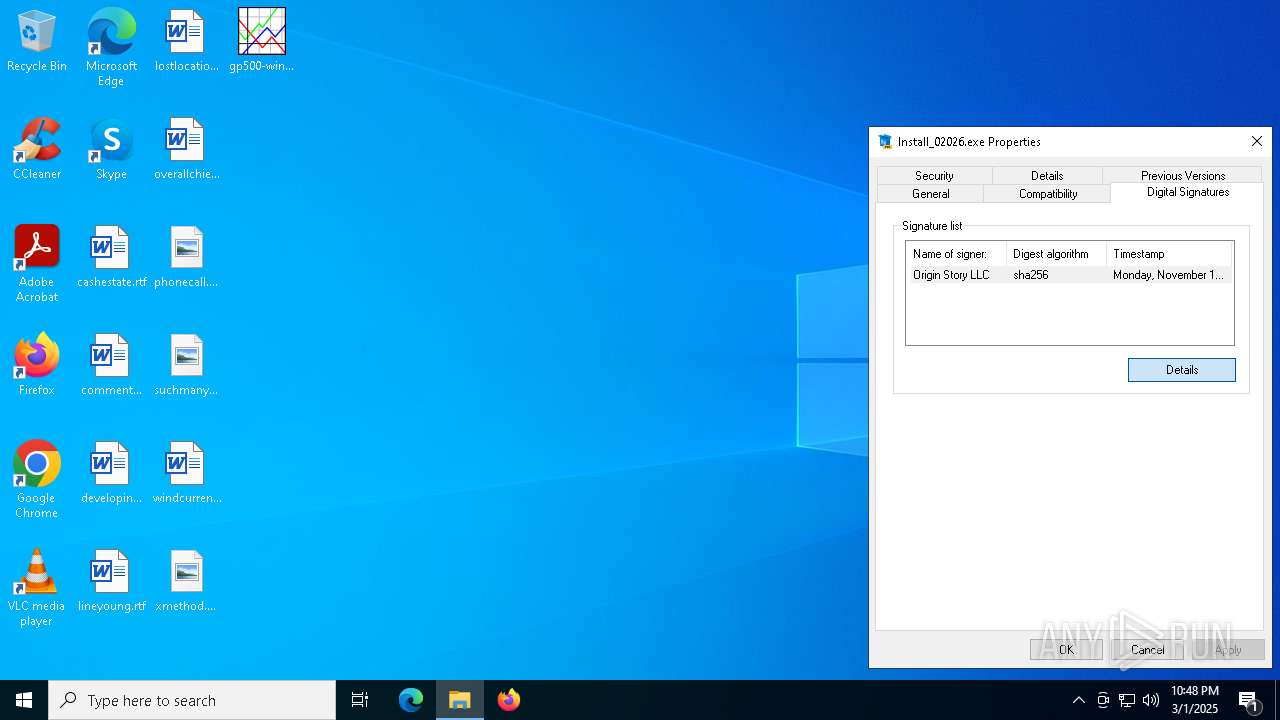
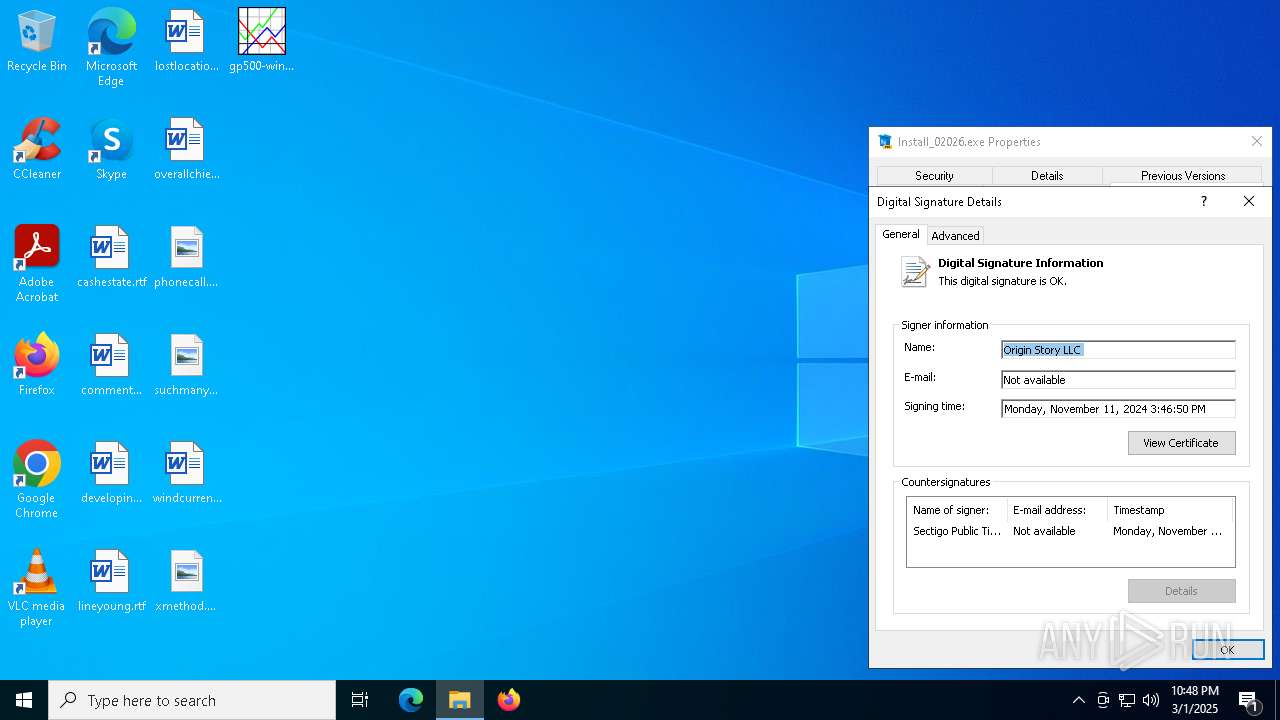
| MD5: | 6CEEC3554C86786C8FA05DB92F338676 |
| SHA1: | 70613DE69718DECF13823A12BB7FA6495641F962 |
| SHA256: | 4B0BD078E314FD4AC70A0777FE6FE968EF8C578A750BFA55A9DA8690CD39D321 |
| SSDEEP: | 3:N8MIA/enKOXtmRjcaYU2IfqWii8LedMRurdBQNigwn:2MIA/eKOdmRHgIfqVlWMIJmwgwn |
MALICIOUS
No malicious indicators.SUSPICIOUS
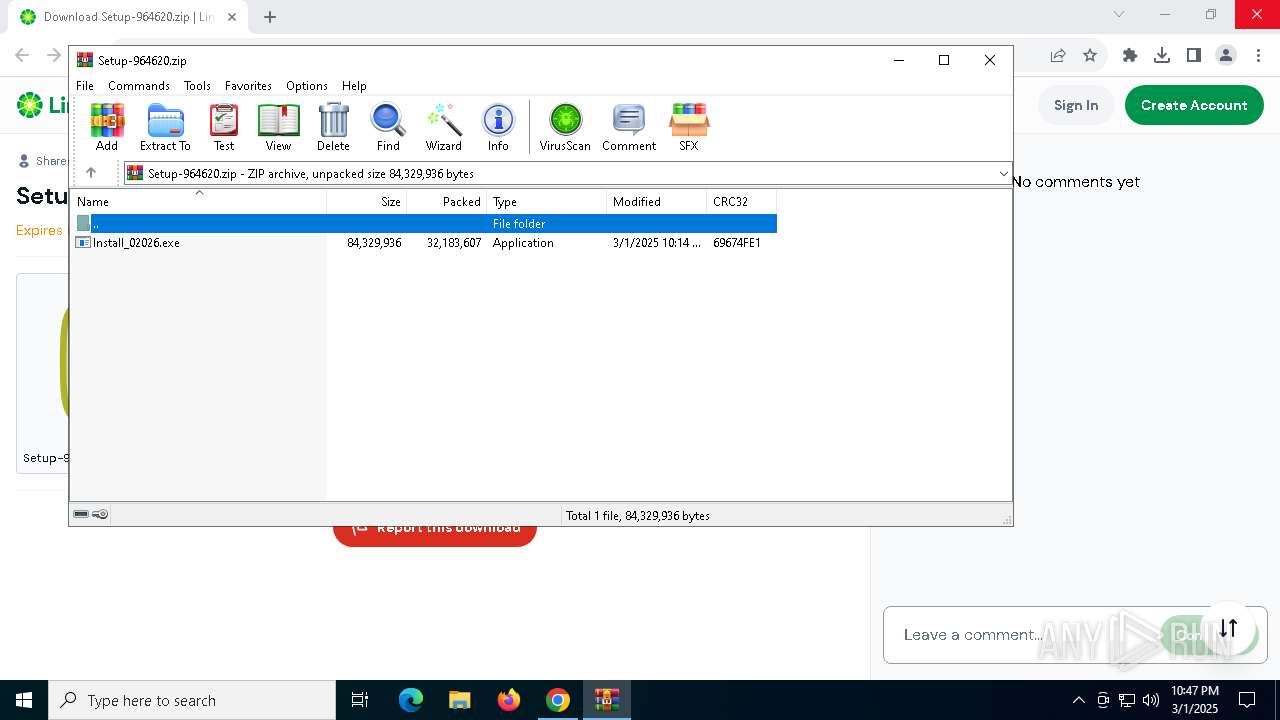
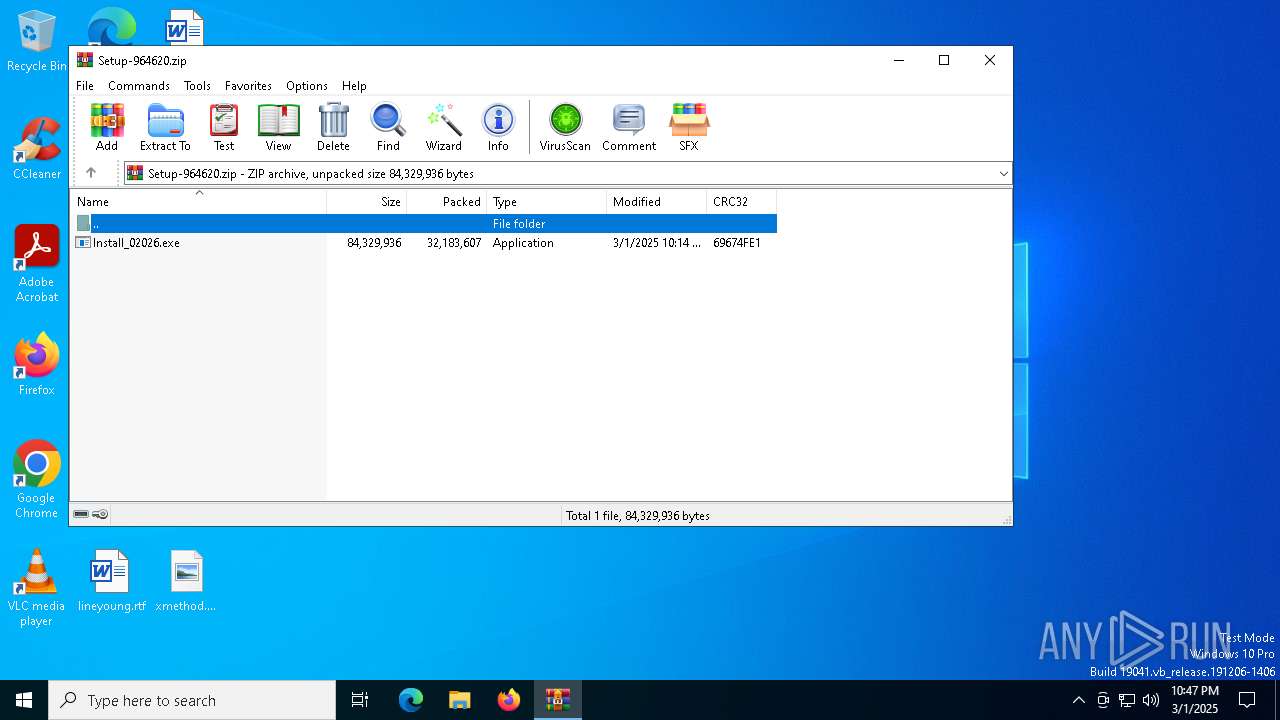
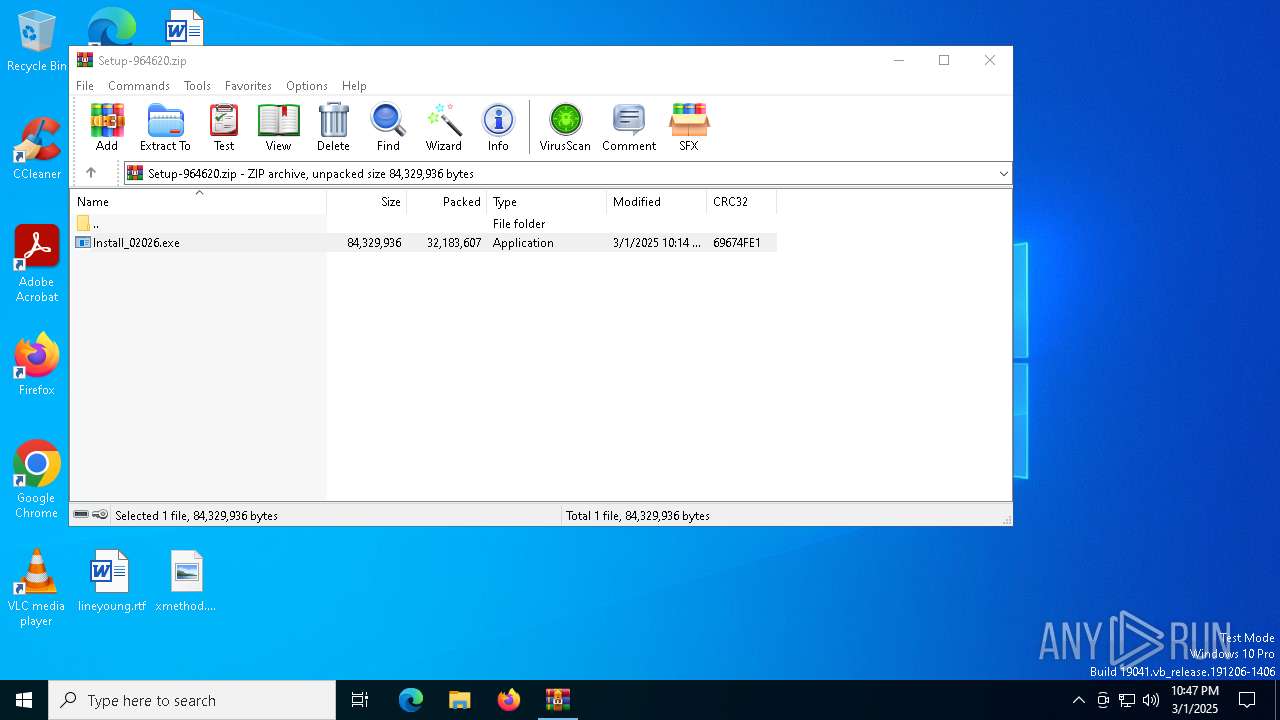
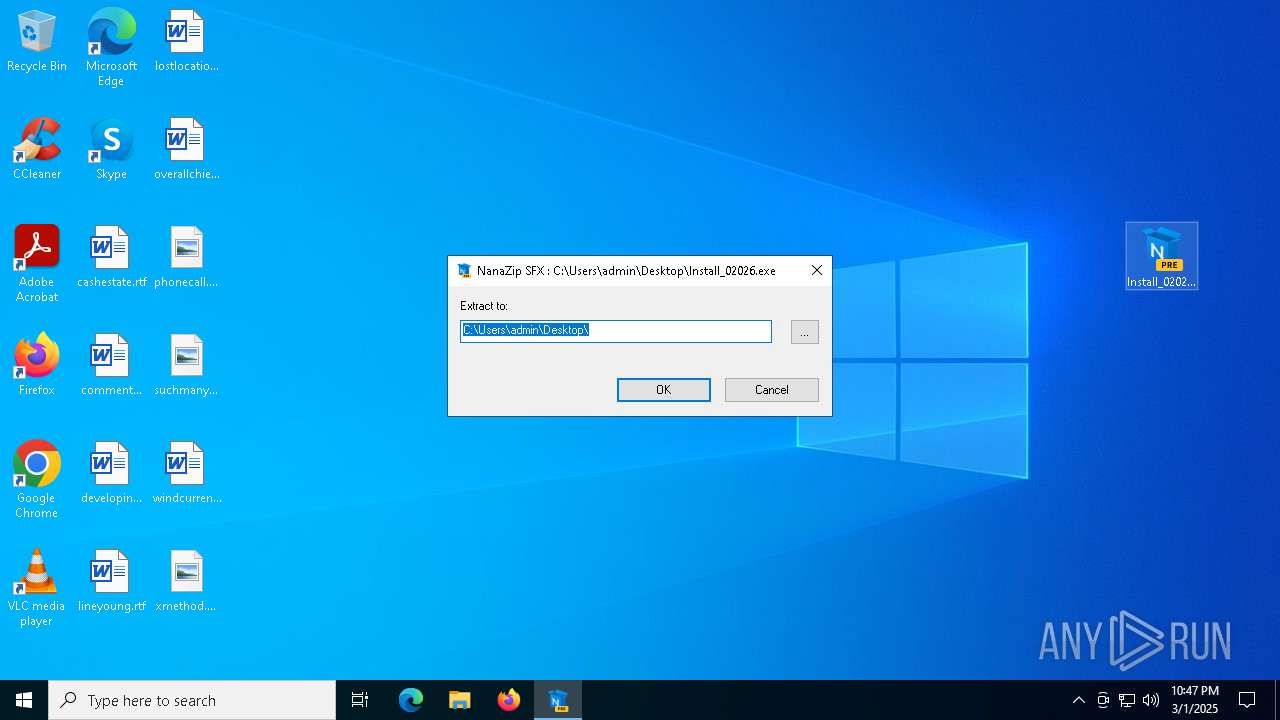
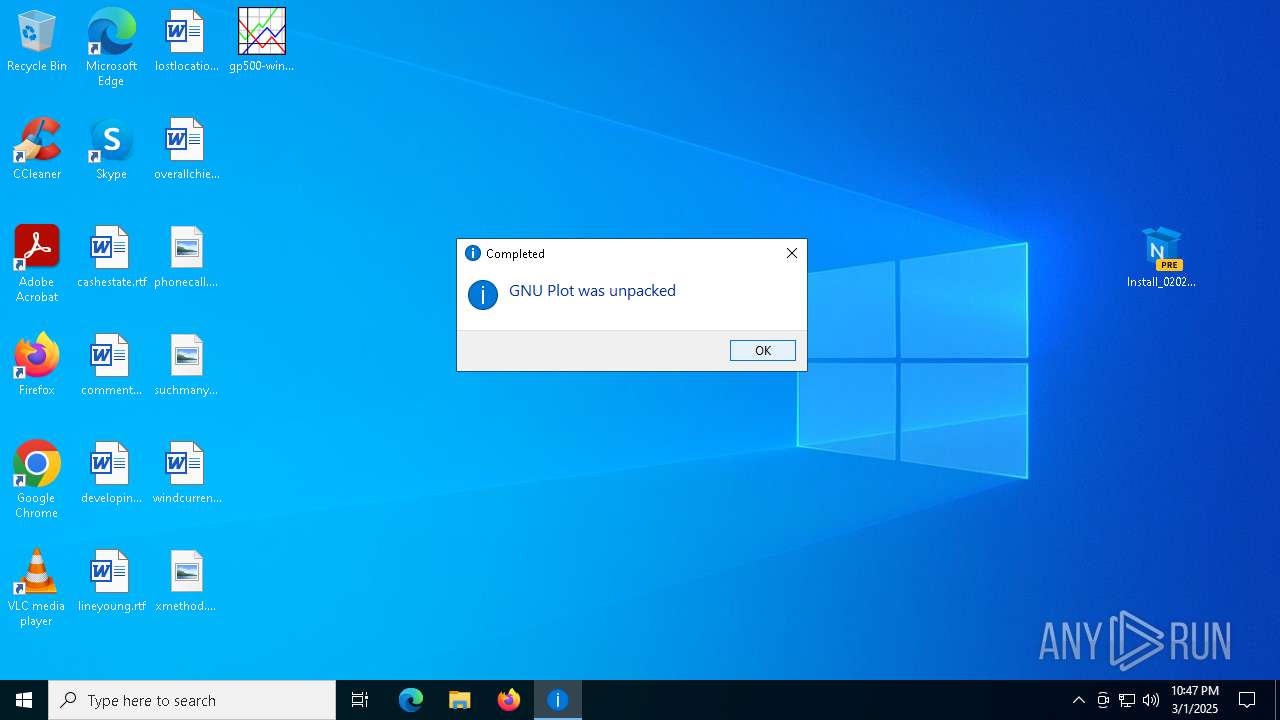
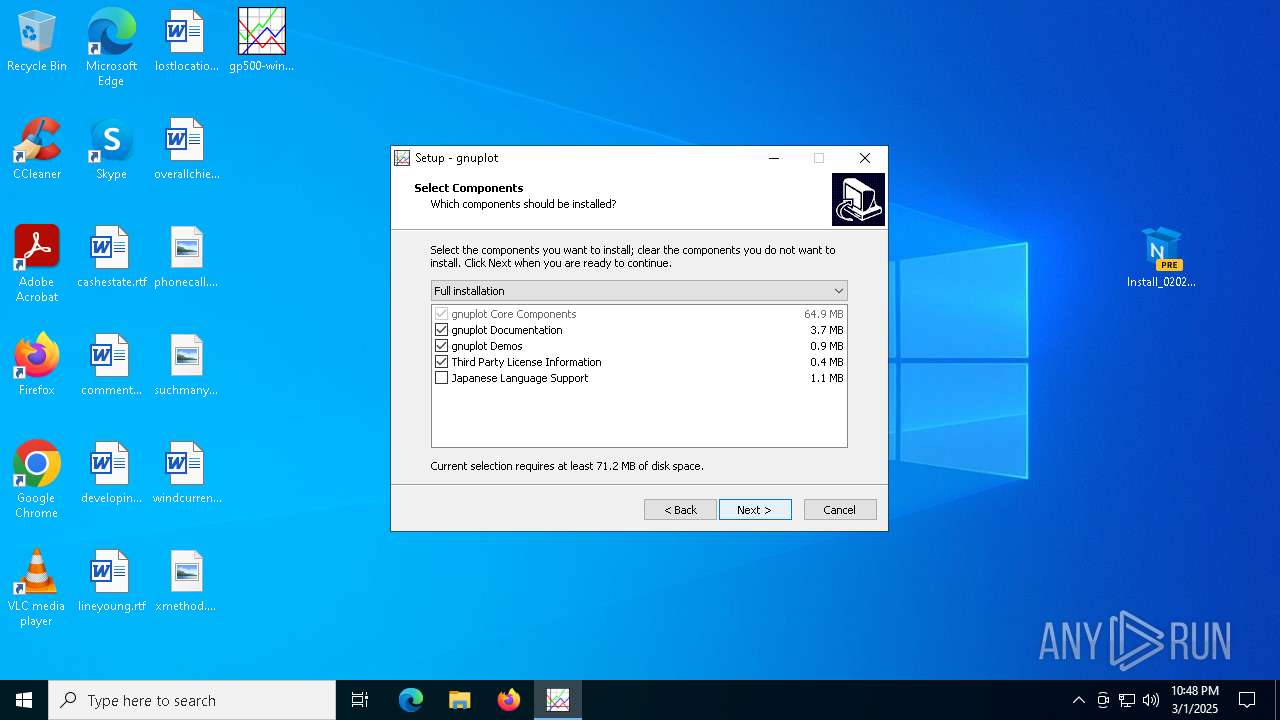
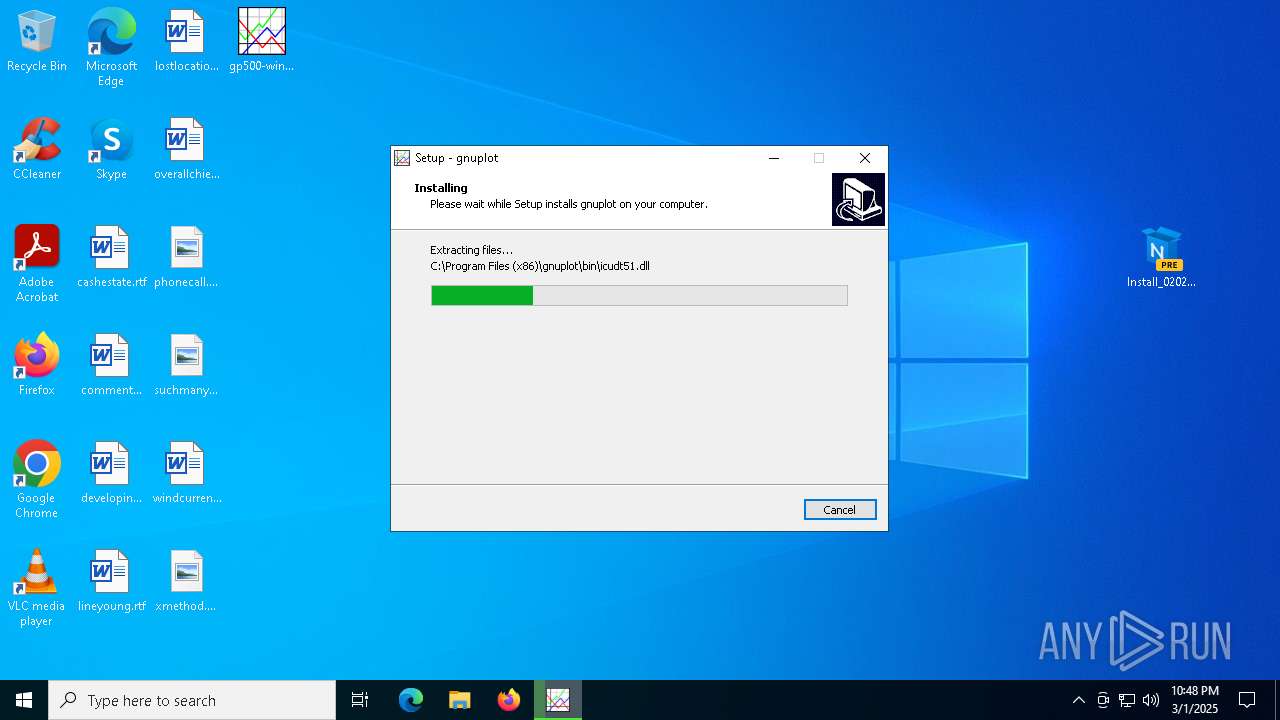
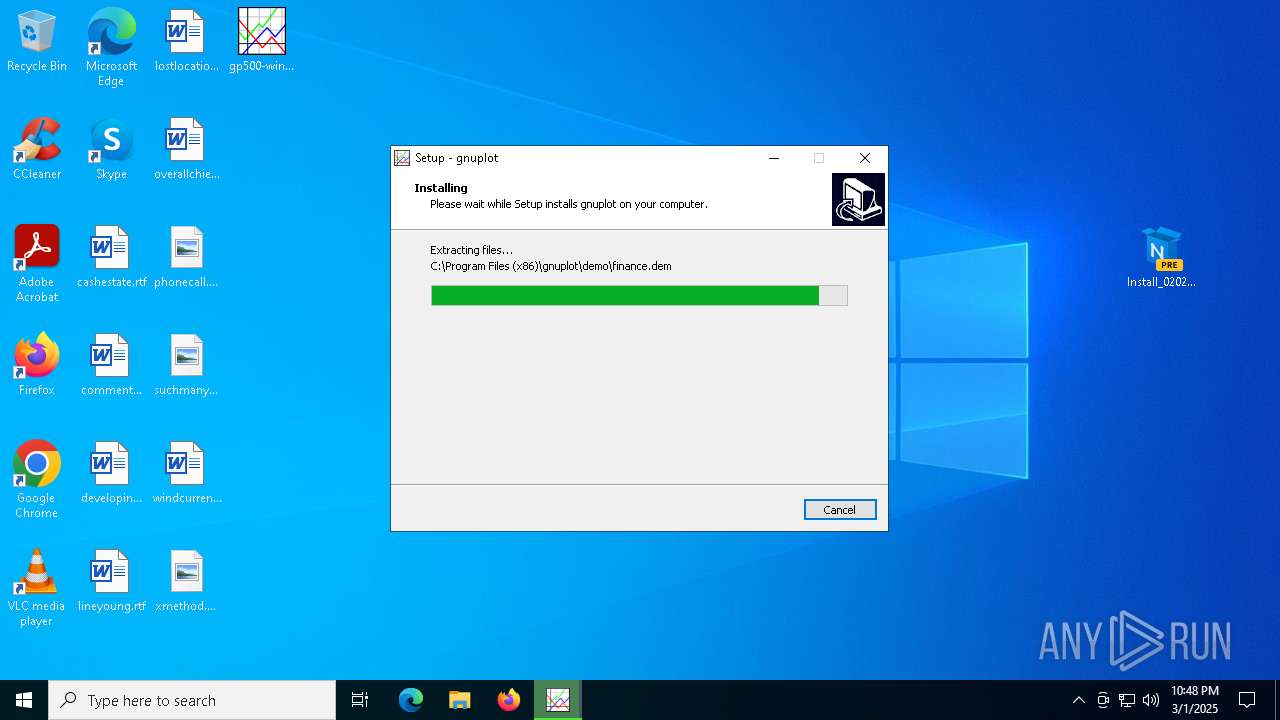
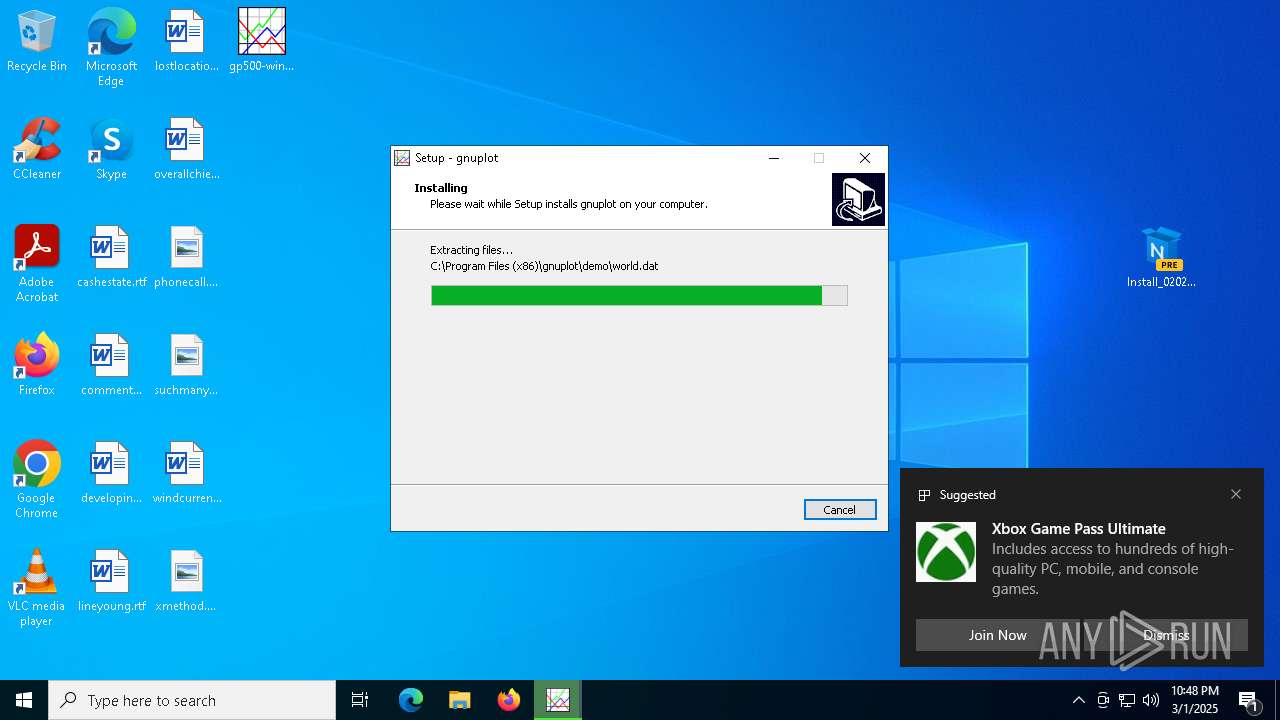
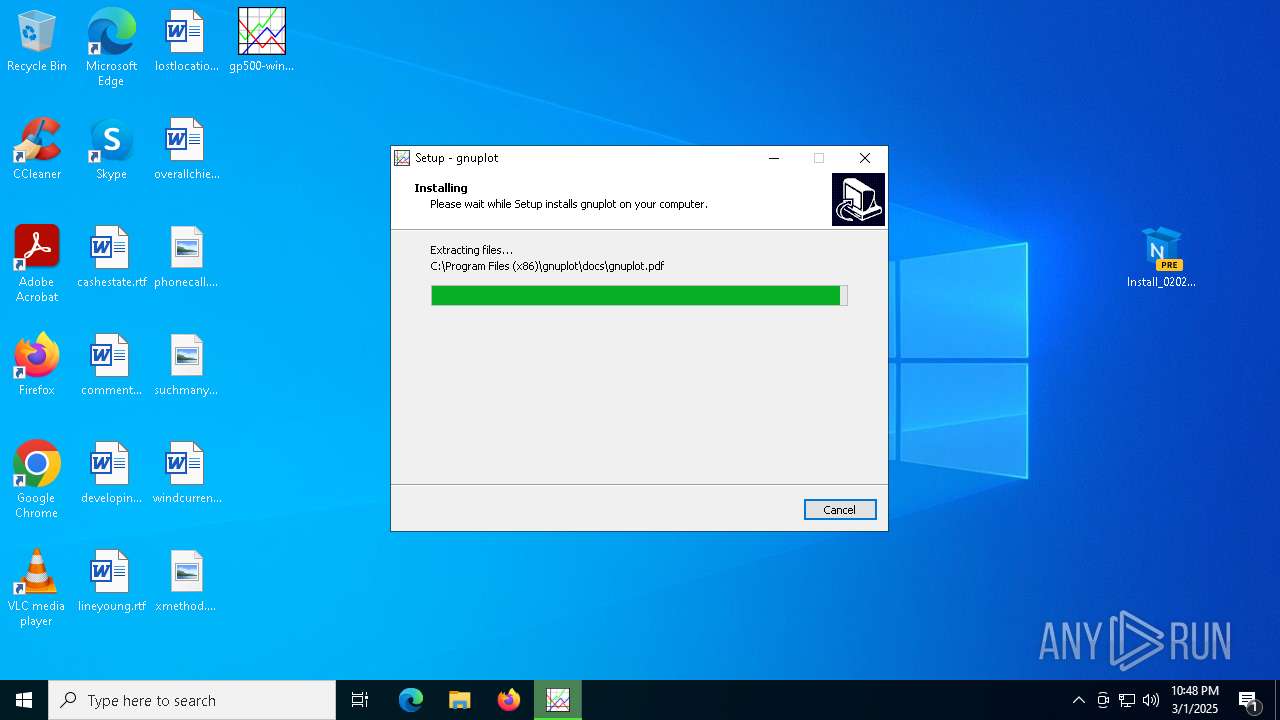
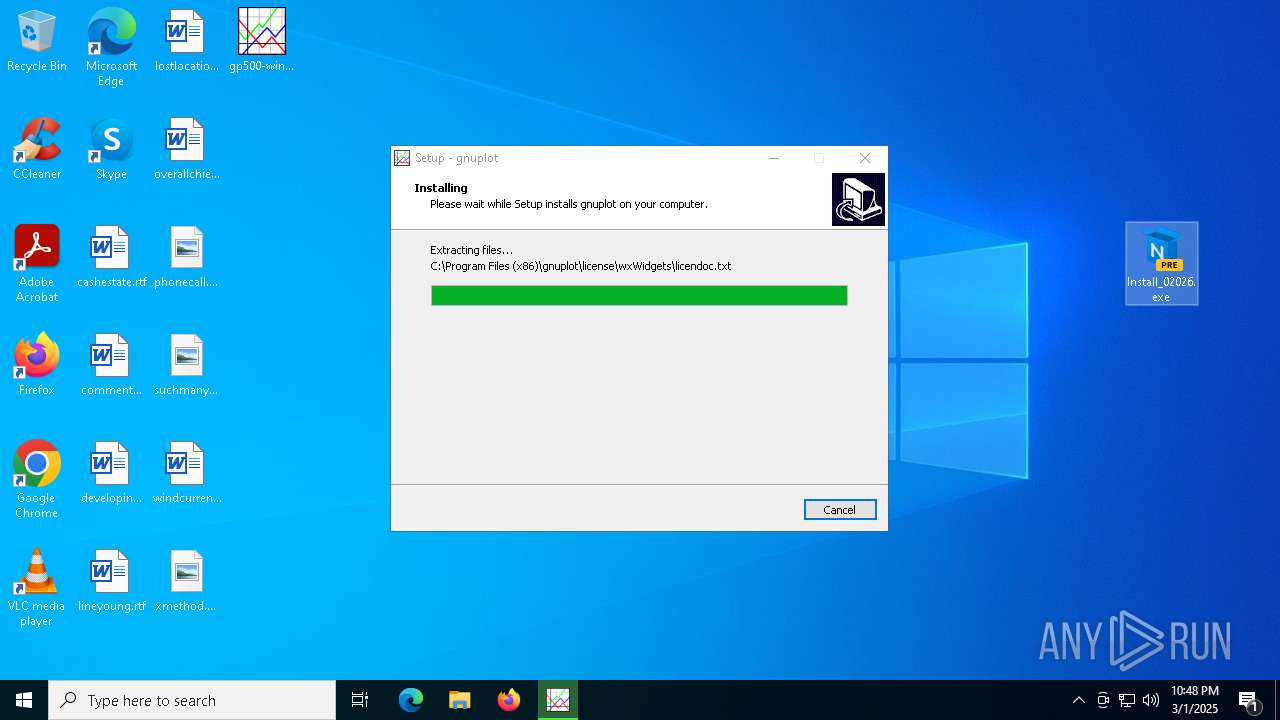
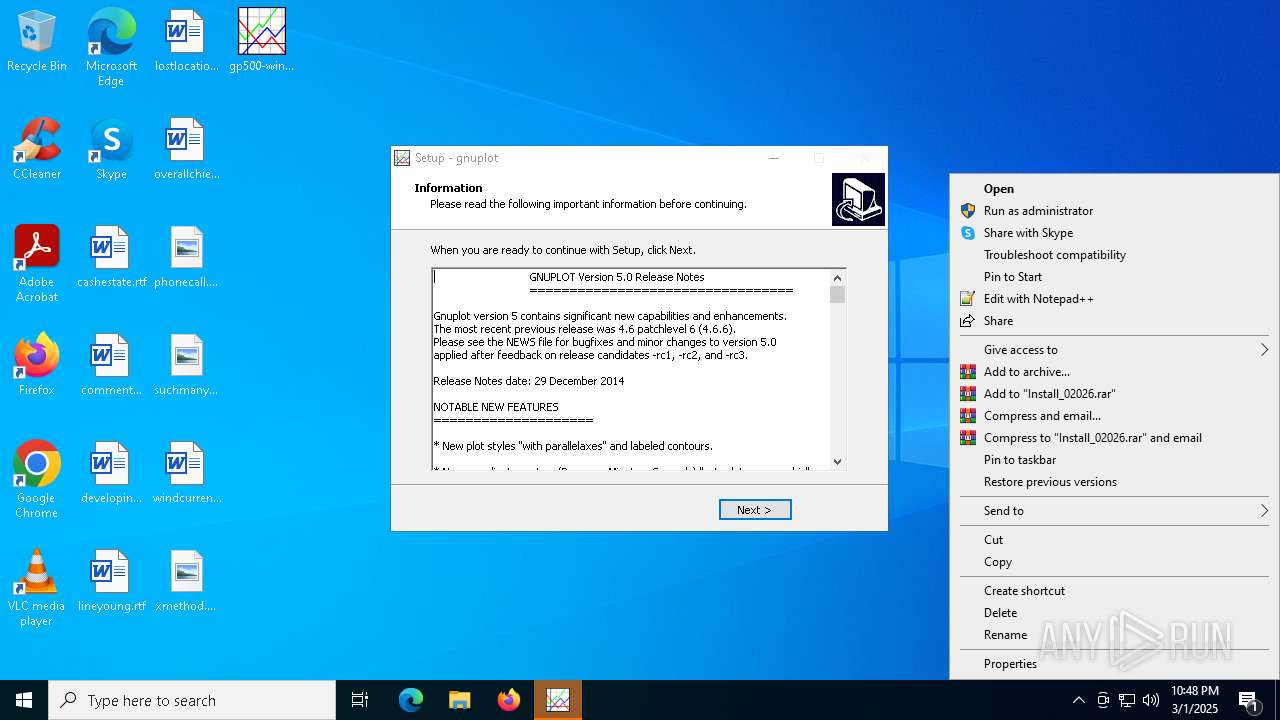
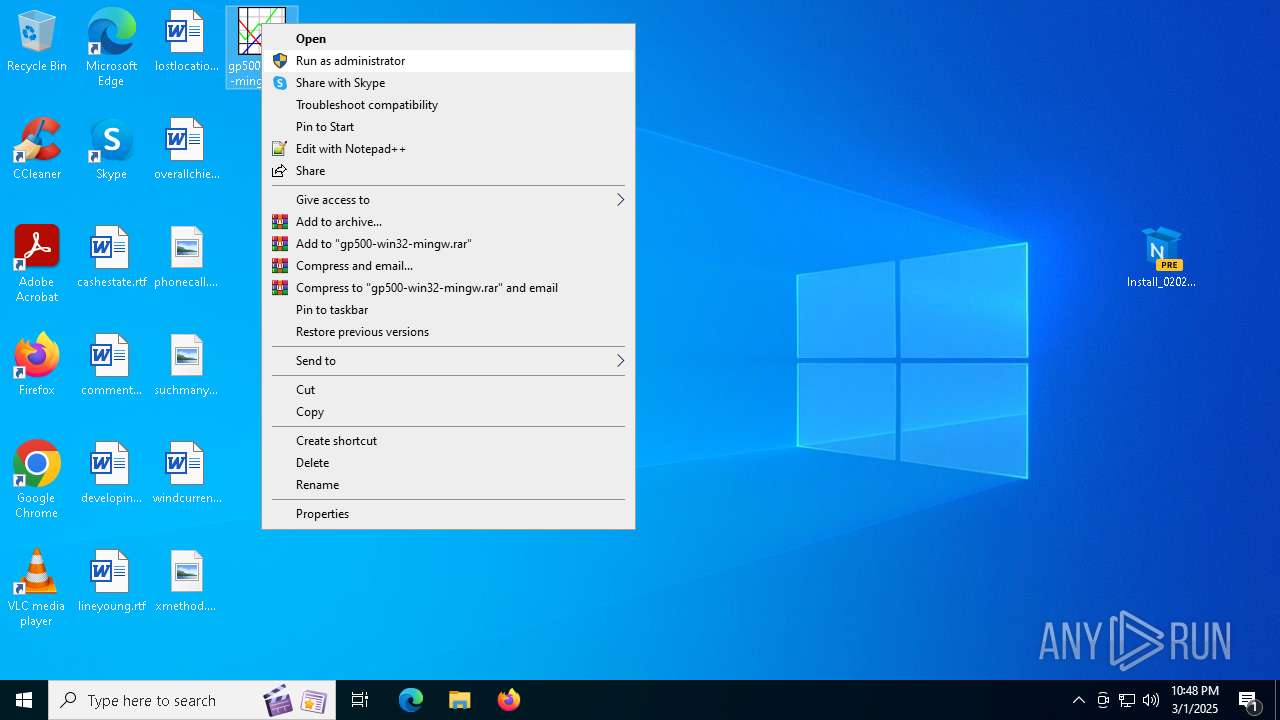
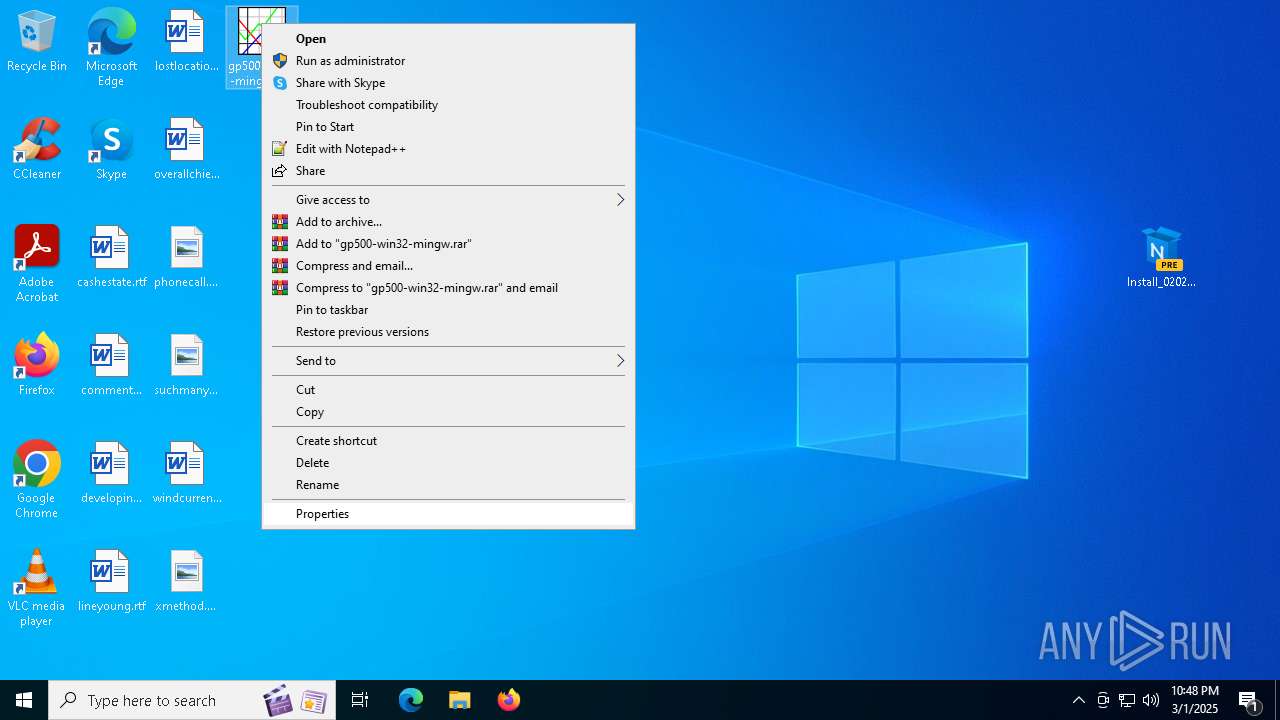
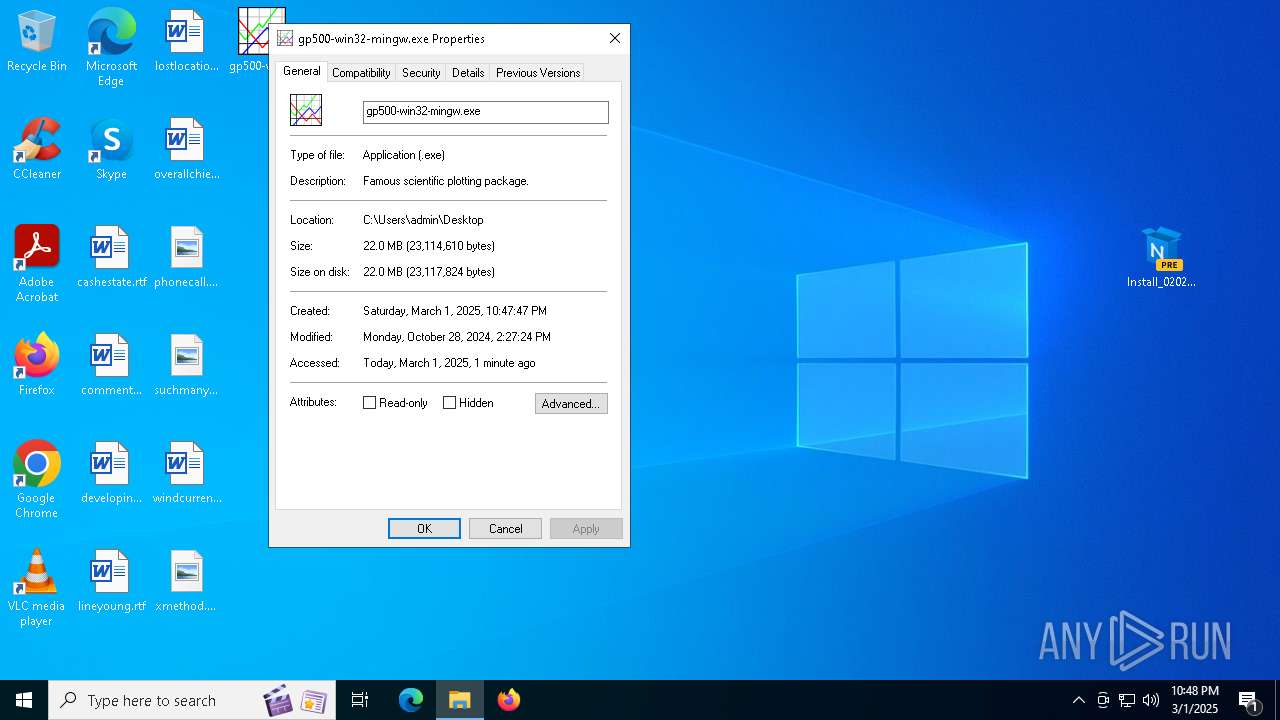
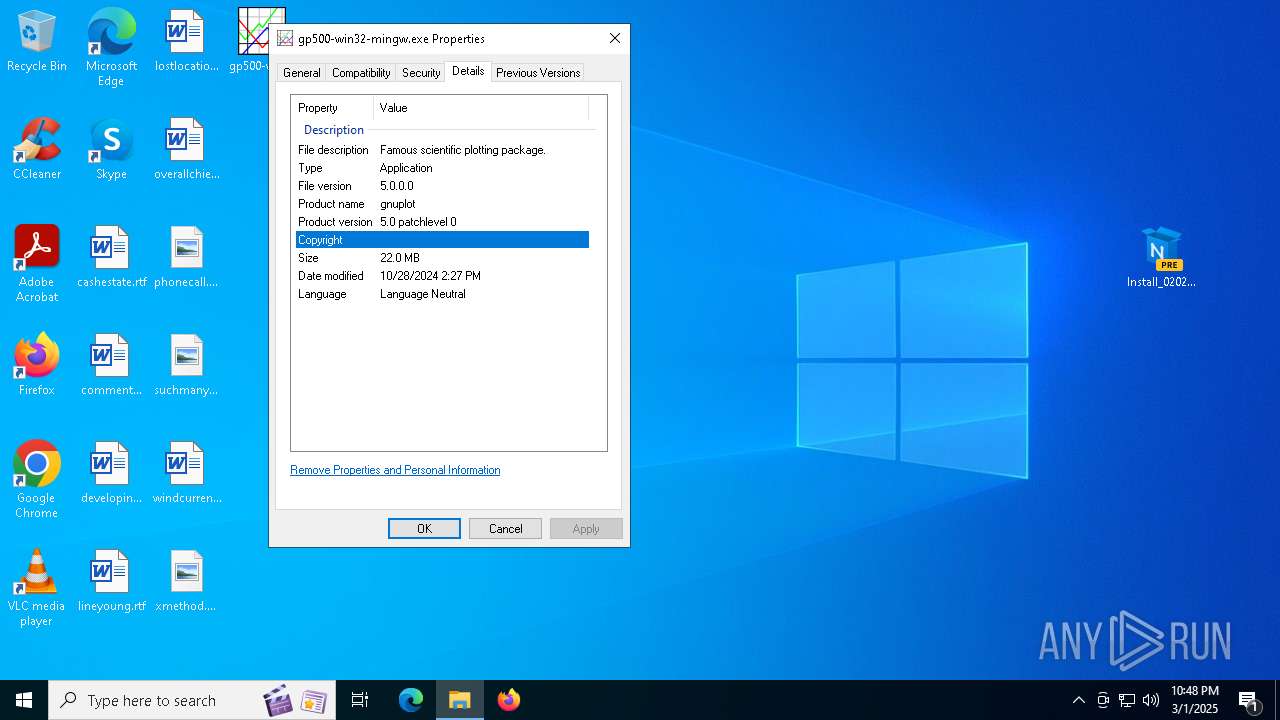
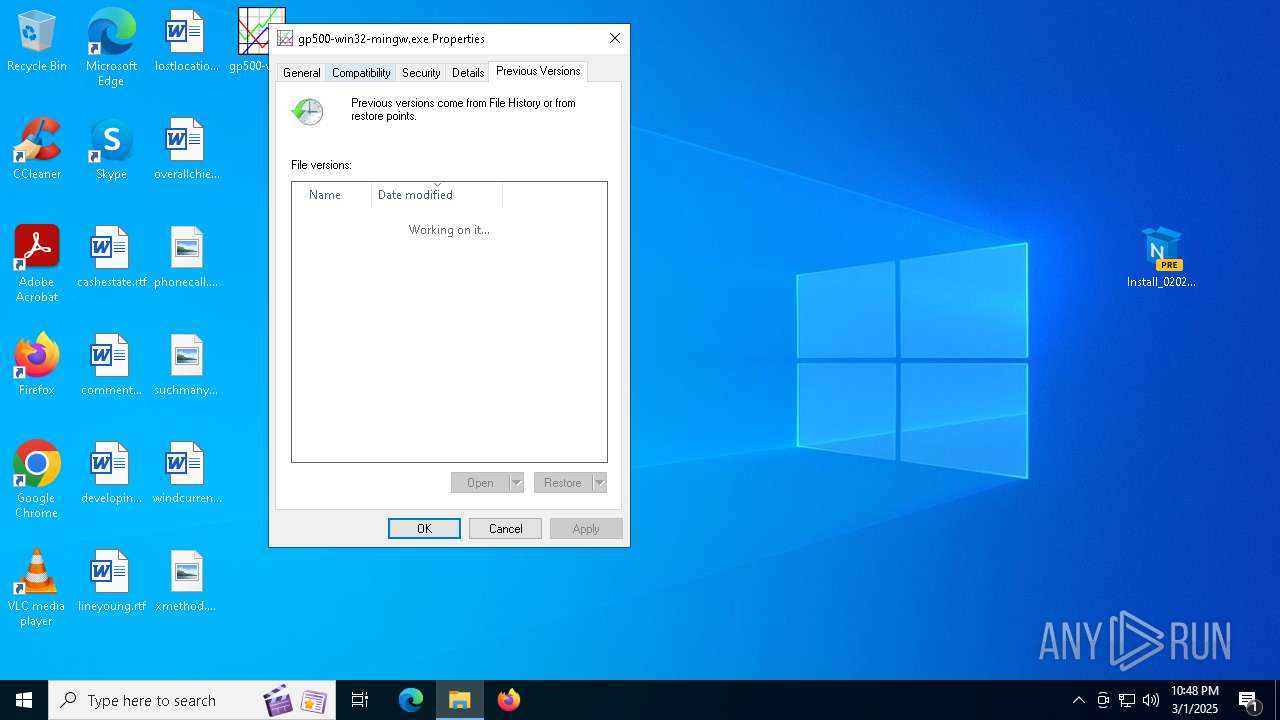
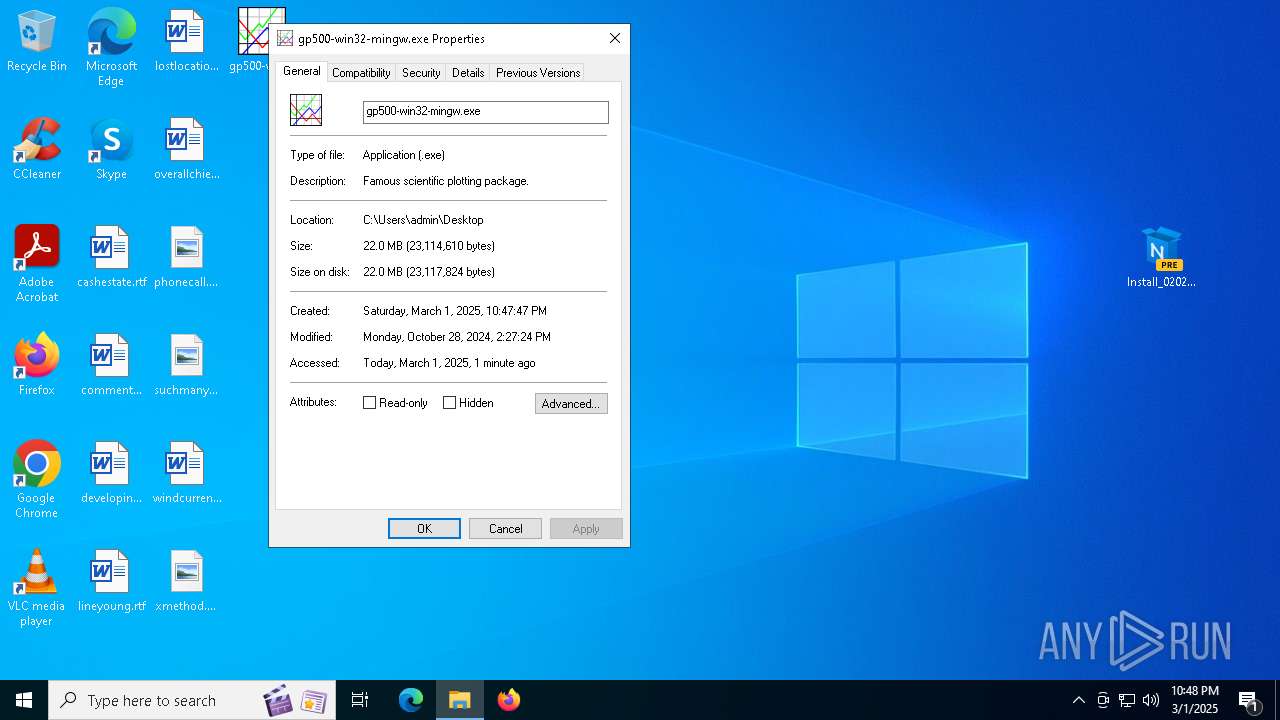
Executable content was dropped or overwritten
- Install_02026.exe (PID: 7384)
- gp500-win32-mingw.exe (PID: 8048)
- gp500-win32-mingw.exe (PID: 7560)
- gp500-win32-mingw.tmp (PID: 8144)
Reads security settings of Internet Explorer
- gp500-win32-mingw.tmp (PID: 2316)
- ShellExperienceHost.exe (PID: 6712)
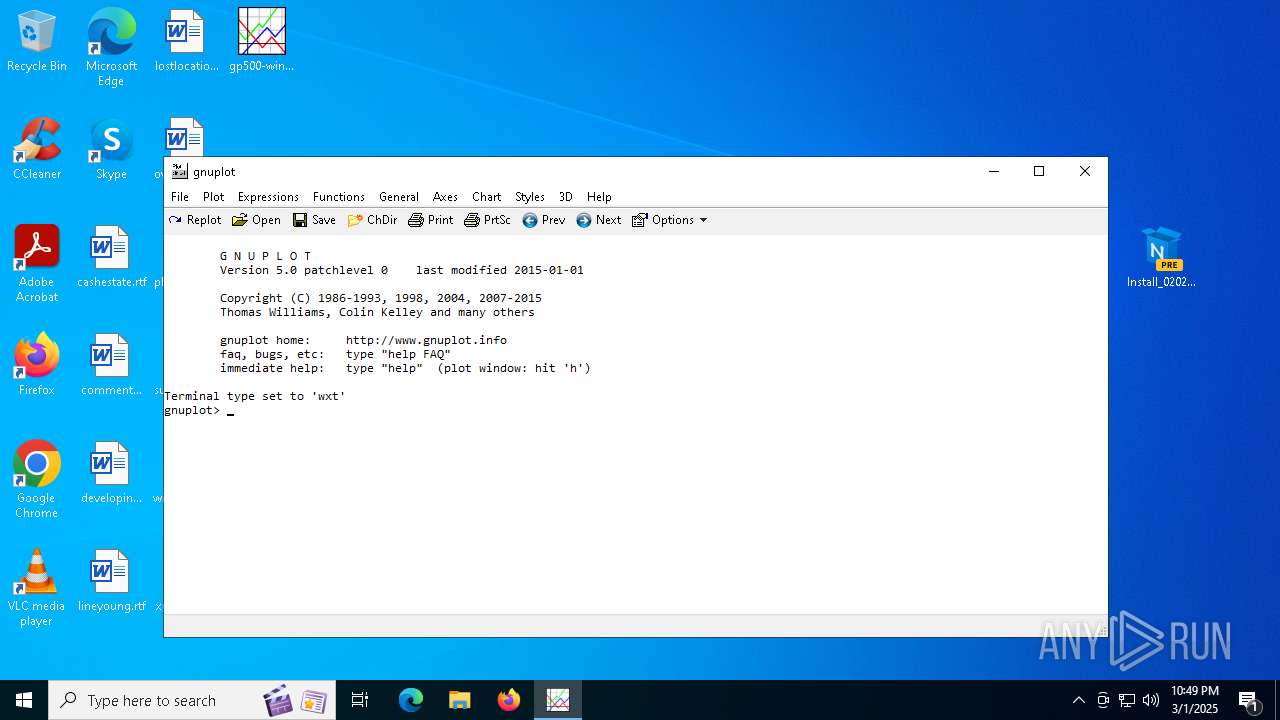
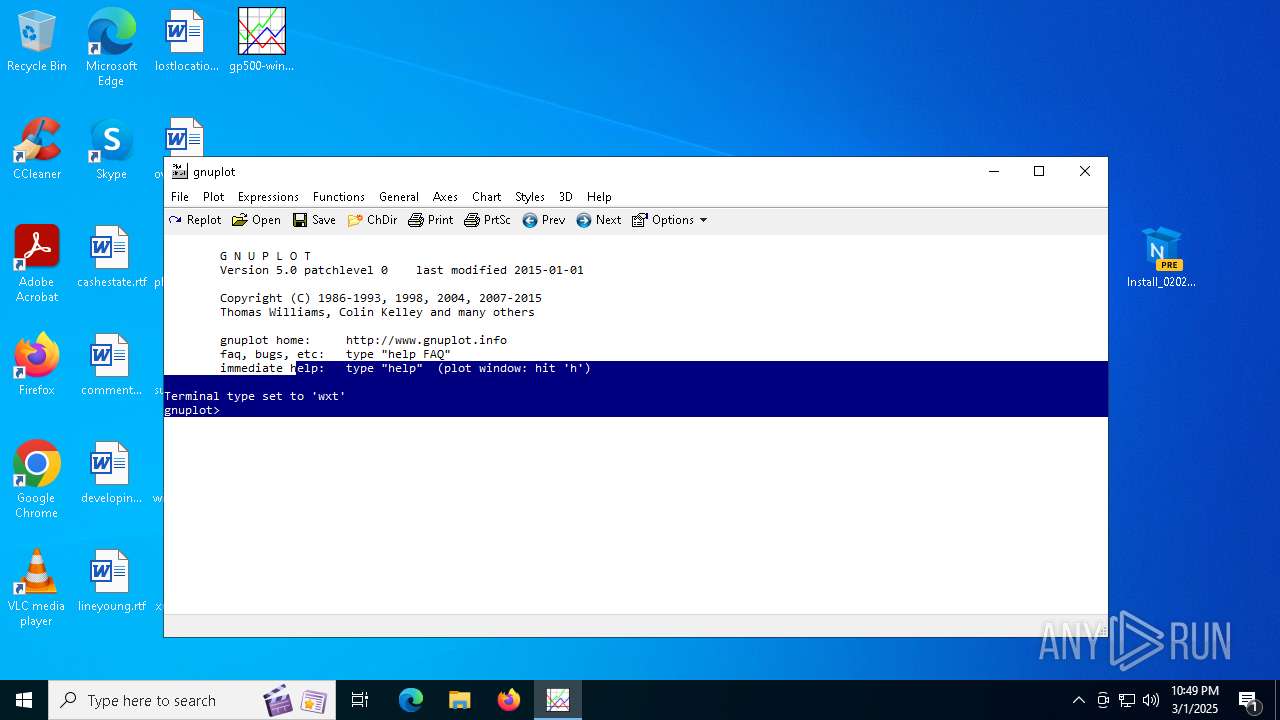
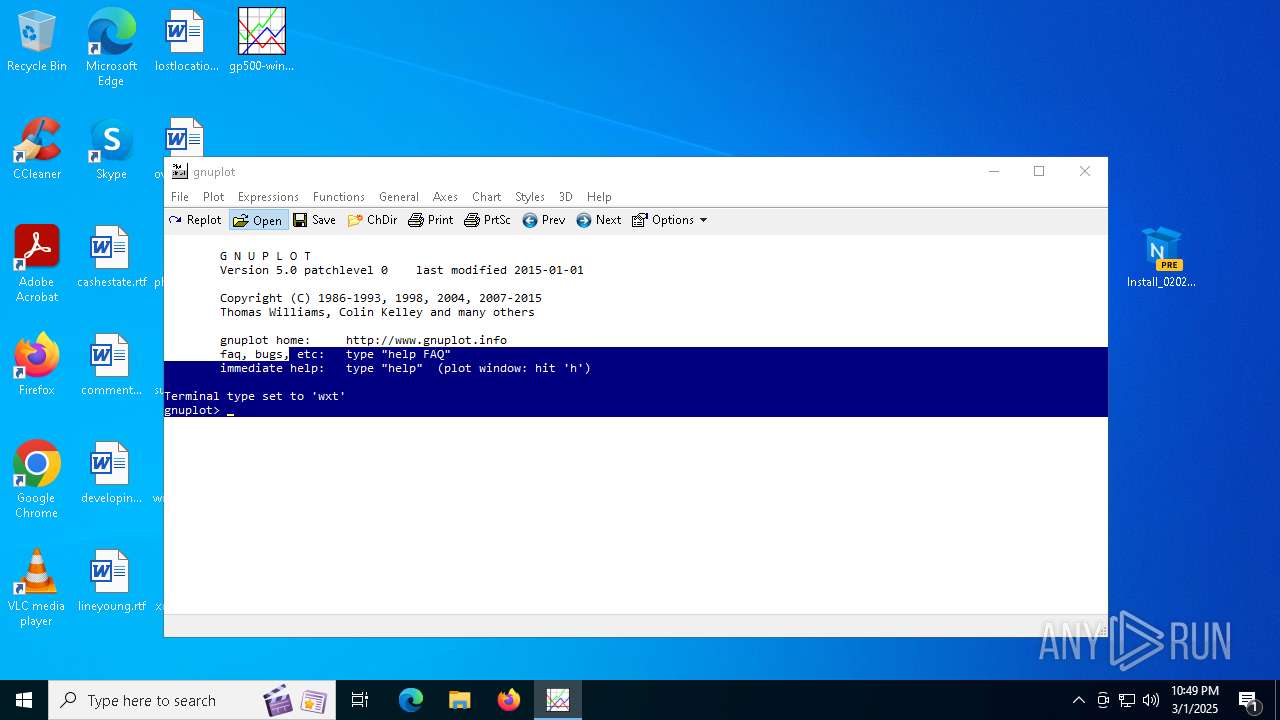
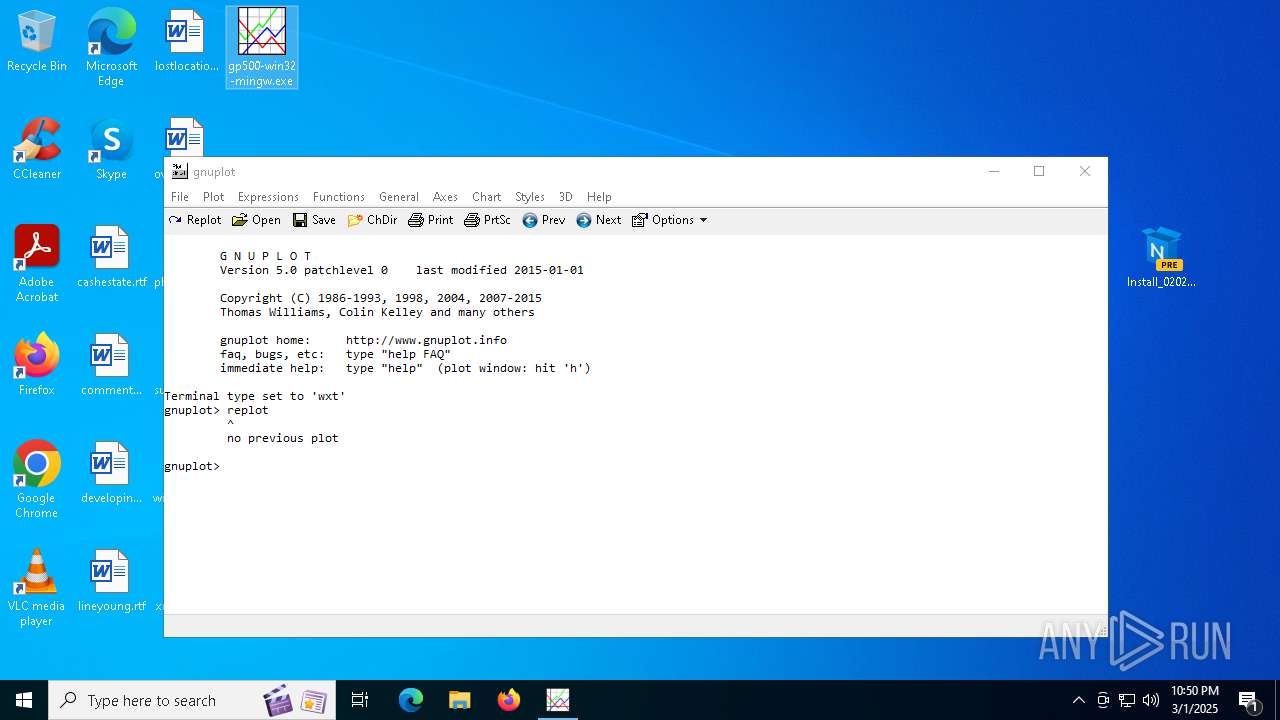
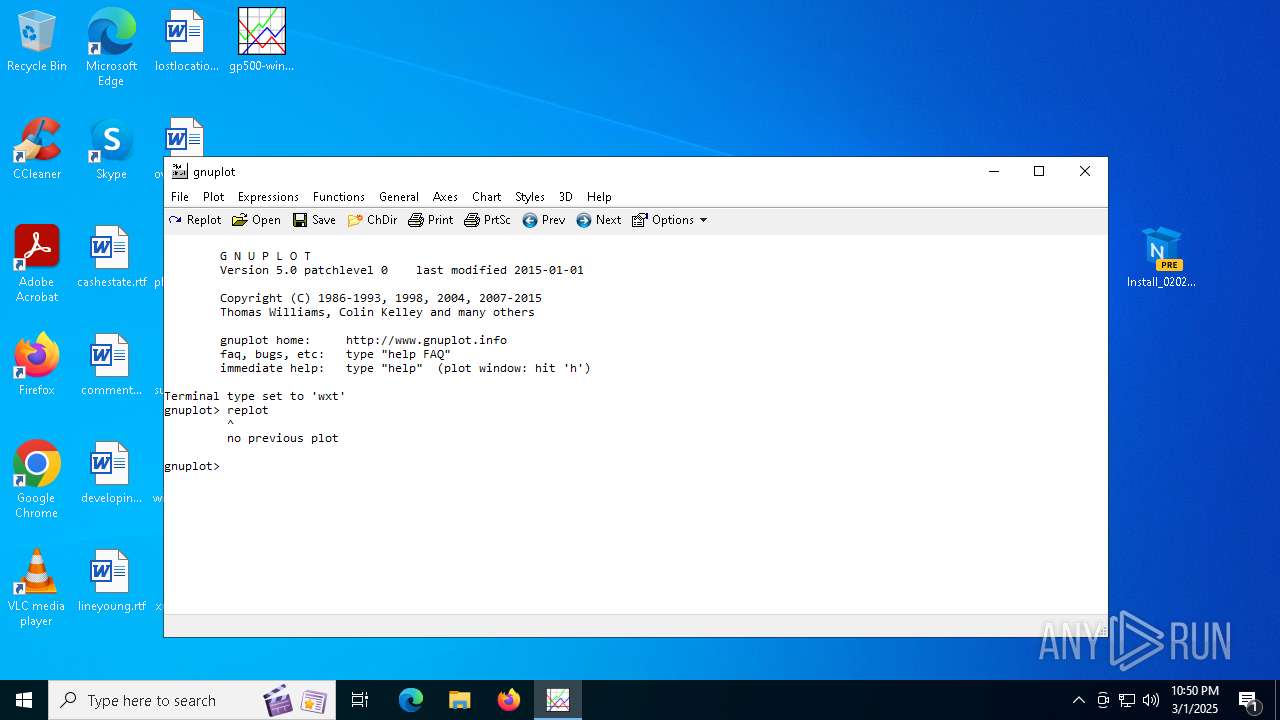
- wgnuplot.exe (PID: 7632)
Reads the Windows owner or organization settings
- gp500-win32-mingw.tmp (PID: 8144)
Process drops legitimate windows executable
- gp500-win32-mingw.tmp (PID: 8144)
Creates file in the systems drive root
- explorer.exe (PID: 5492)
SMB connection has been detected (probably for file transfer)
- explorer.exe (PID: 5492)
There is functionality for taking screenshot (YARA)
- wgnuplot.exe (PID: 7632)
INFO
Application launched itself
- chrome.exe (PID: 6540)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 1072)
- explorer.exe (PID: 5492)
- wgnuplot.exe (PID: 7632)
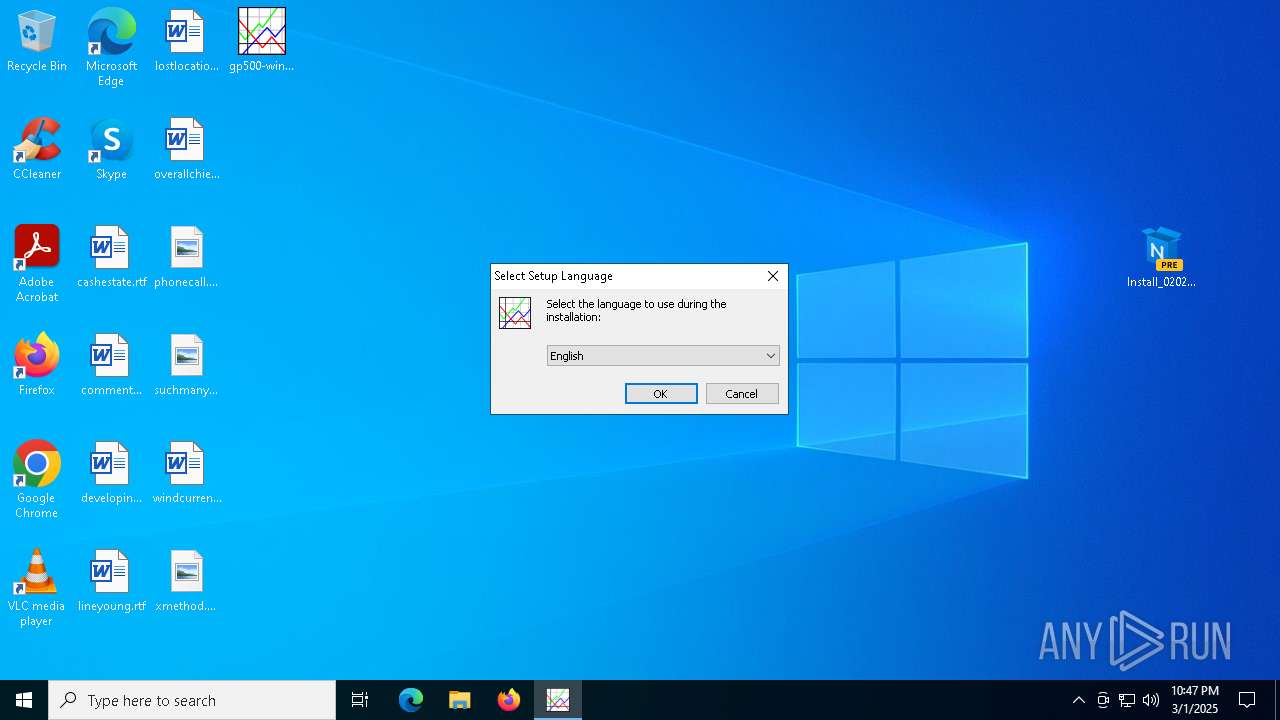
Checks supported languages
- SearchApp.exe (PID: 2924)
- Install_02026.exe (PID: 7384)
- gp500-win32-mingw.exe (PID: 7560)
- gp500-win32-mingw.tmp (PID: 8144)
- gp500-win32-mingw.tmp (PID: 2316)
- ShellExperienceHost.exe (PID: 6712)
- wgnuplot.exe (PID: 7632)
- gp500-win32-mingw.exe (PID: 8048)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 8184)
- BackgroundTransferHost.exe (PID: 1072)
- BackgroundTransferHost.exe (PID: 8176)
- BackgroundTransferHost.exe (PID: 2236)
- explorer.exe (PID: 5492)
- BackgroundTransferHost.exe (PID: 7364)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 1072)
- explorer.exe (PID: 5492)
- SearchApp.exe (PID: 2924)
- slui.exe (PID: 7608)
- slui.exe (PID: 7456)
Reads Microsoft Office registry keys
- chrome.exe (PID: 6540)
Reads the computer name
- Install_02026.exe (PID: 7384)
- gp500-win32-mingw.tmp (PID: 2316)
- gp500-win32-mingw.tmp (PID: 8144)
- ShellExperienceHost.exe (PID: 6712)
- wgnuplot.exe (PID: 7632)
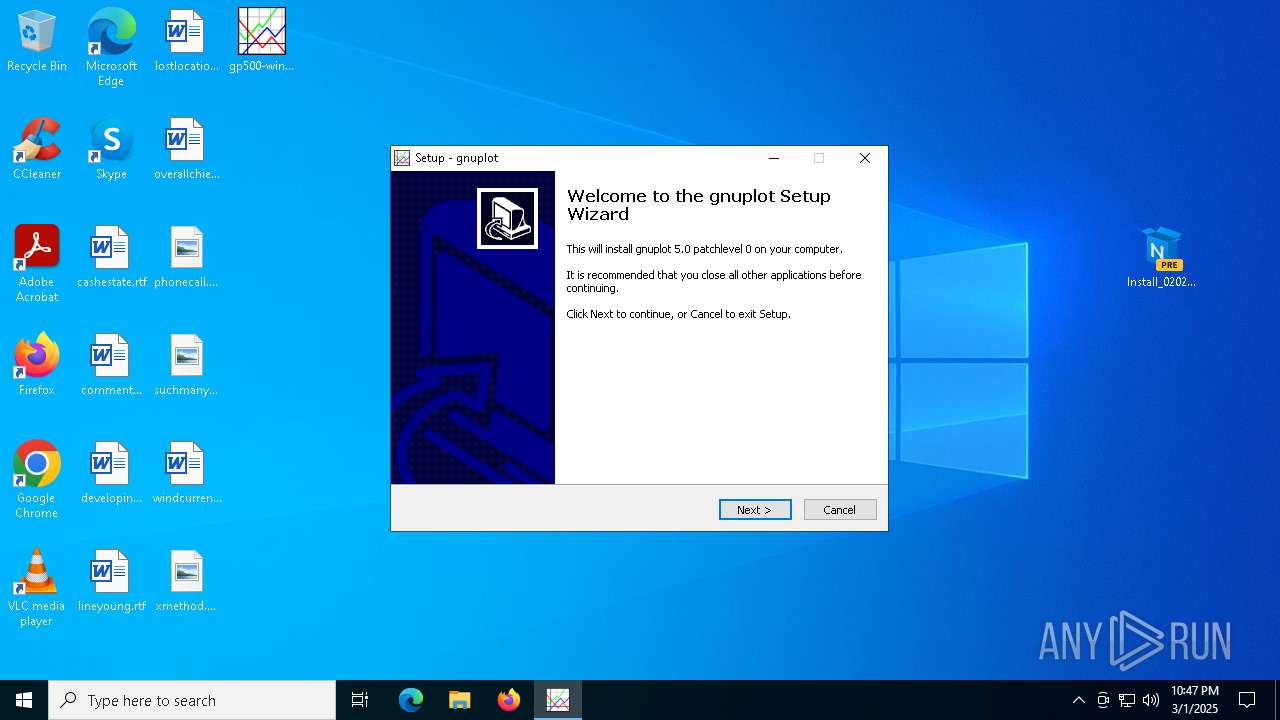
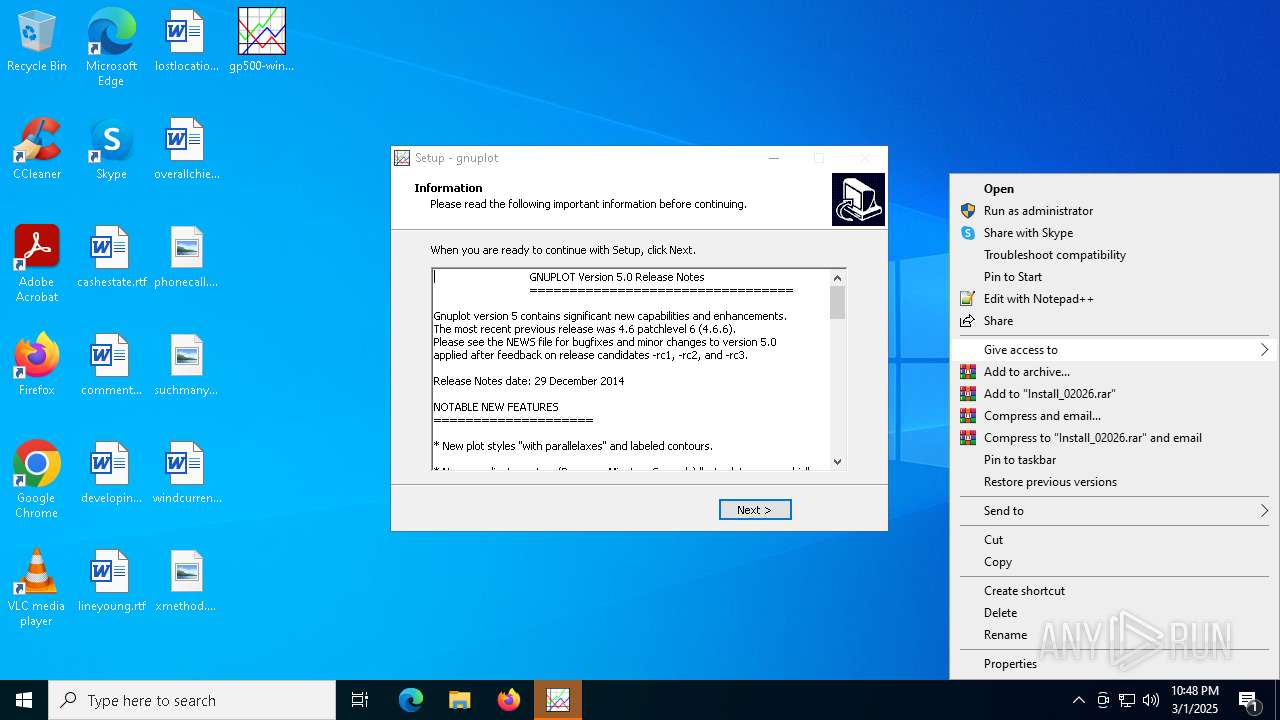
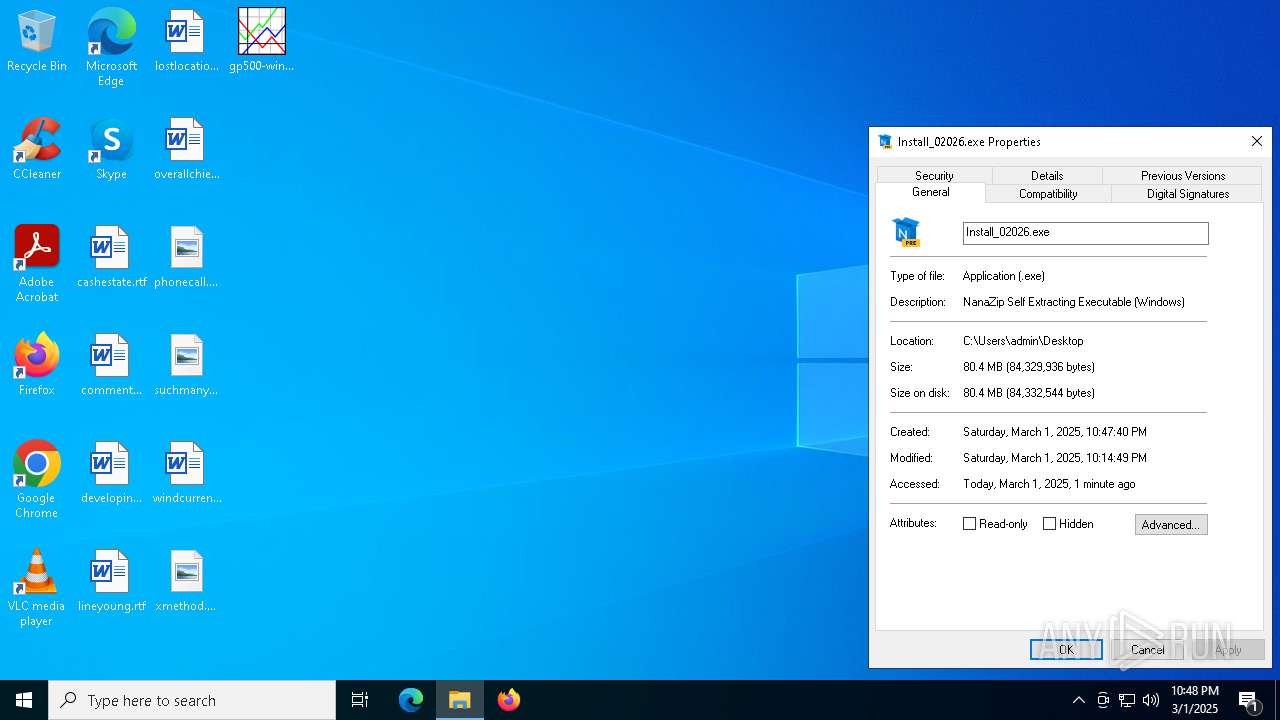
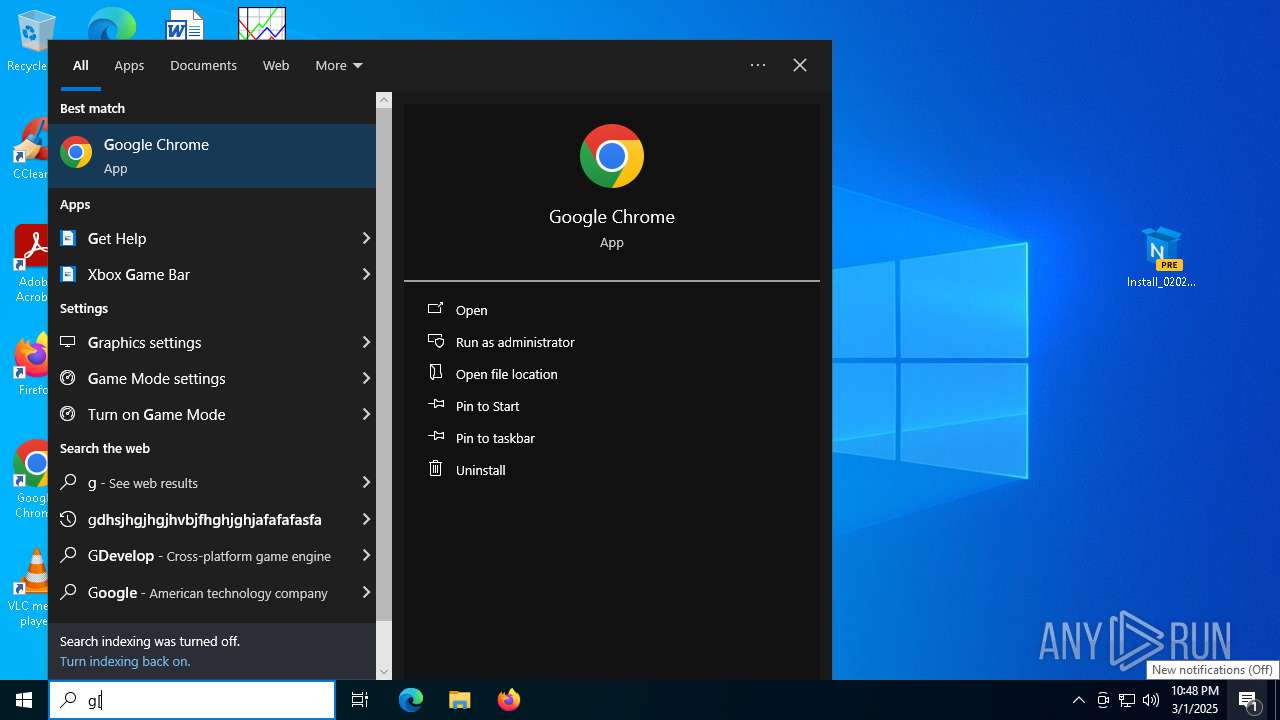
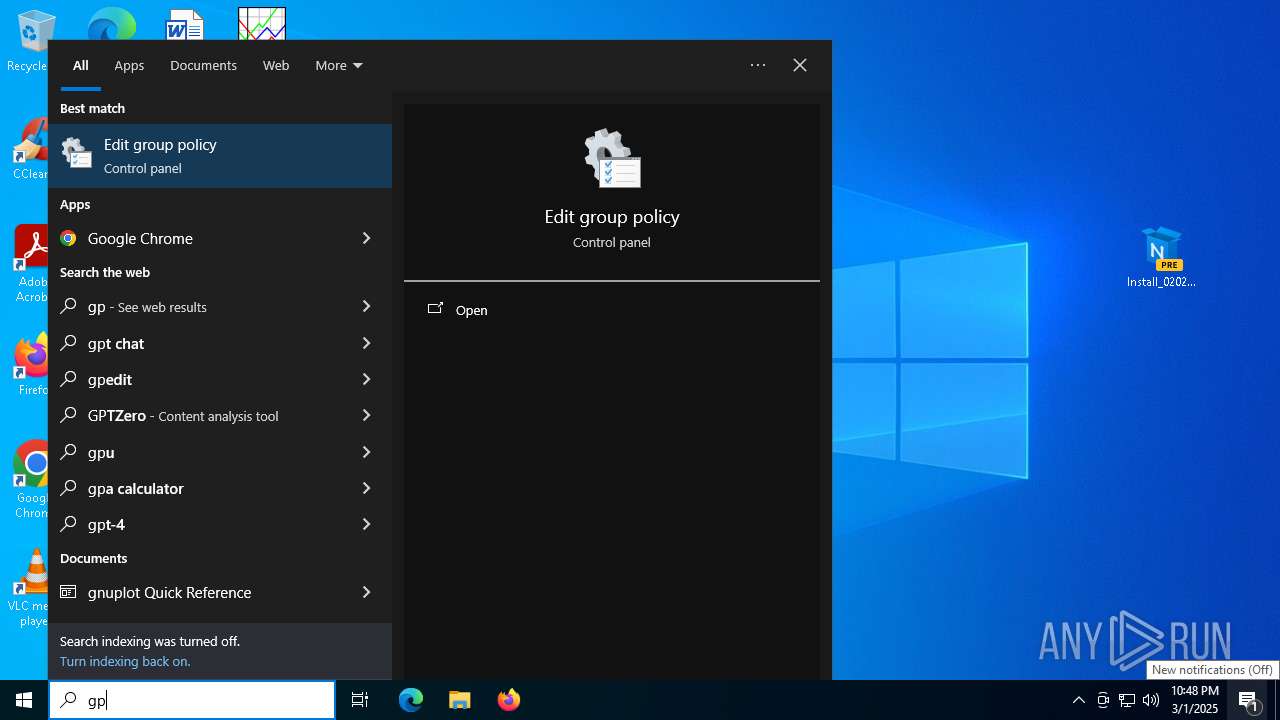
Manual execution by a user
- Install_02026.exe (PID: 7384)
- gp500-win32-mingw.exe (PID: 8048)
Process checks computer location settings
- gp500-win32-mingw.tmp (PID: 2316)
- SearchApp.exe (PID: 2924)
Create files in a temporary directory
- gp500-win32-mingw.exe (PID: 7560)
- gp500-win32-mingw.tmp (PID: 8144)
- gp500-win32-mingw.exe (PID: 8048)
The sample compiled with english language support
- gp500-win32-mingw.tmp (PID: 8144)
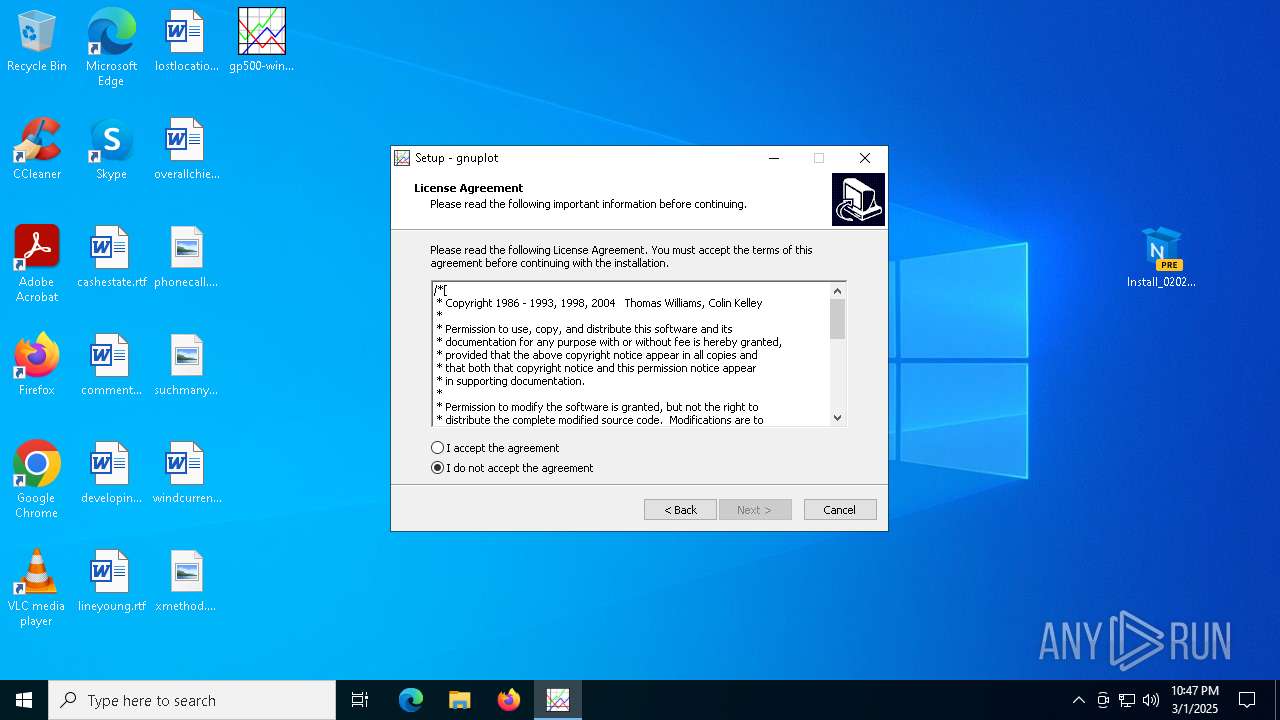
Detects InnoSetup installer (YARA)
- gp500-win32-mingw.exe (PID: 8048)
- gp500-win32-mingw.tmp (PID: 2316)
- gp500-win32-mingw.exe (PID: 7560)
- gp500-win32-mingw.tmp (PID: 8144)
Compiled with Borland Delphi (YARA)
- gp500-win32-mingw.exe (PID: 8048)
- gp500-win32-mingw.tmp (PID: 2316)
- gp500-win32-mingw.exe (PID: 7560)
- gp500-win32-mingw.tmp (PID: 8144)
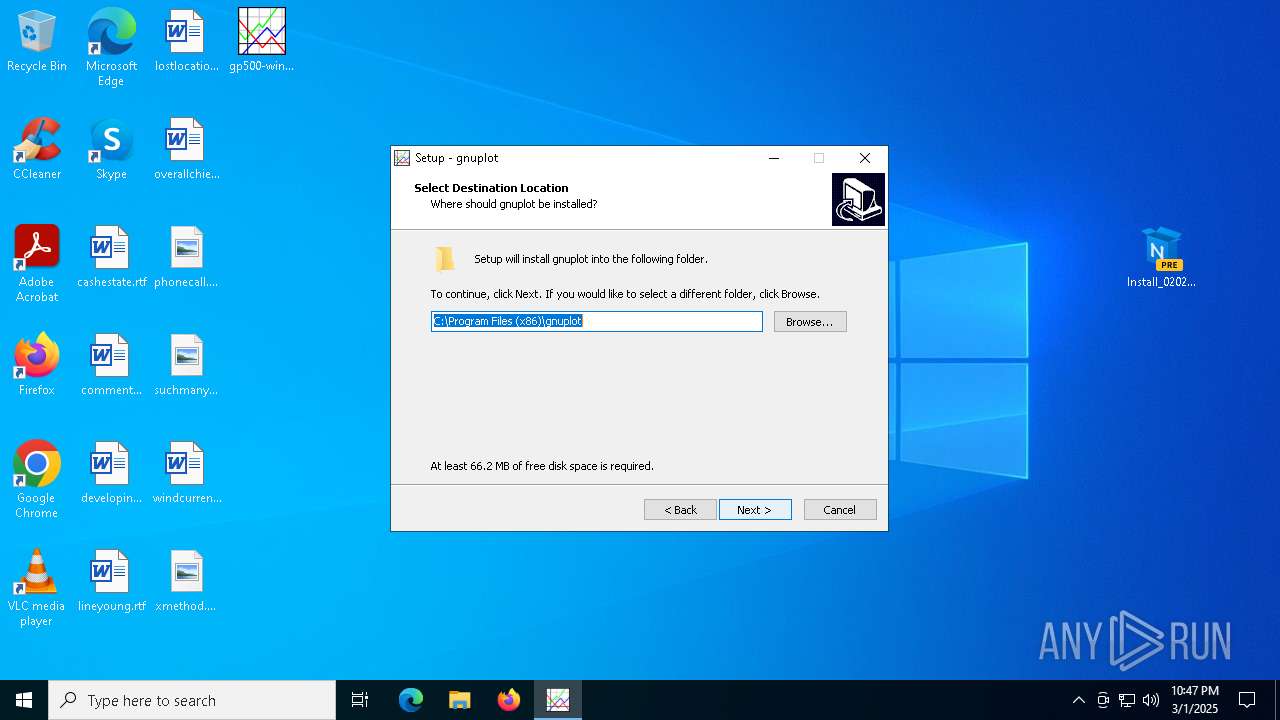
Creates files in the program directory
- gp500-win32-mingw.tmp (PID: 8144)
The sample compiled with german language support
- gp500-win32-mingw.tmp (PID: 8144)
Local mutex for internet shortcut management
- explorer.exe (PID: 5492)
Creates a software uninstall entry
- gp500-win32-mingw.tmp (PID: 8144)
Checks proxy server information
- explorer.exe (PID: 5492)
- slui.exe (PID: 7456)
- BackgroundTransferHost.exe (PID: 1072)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 2924)
The process uses Lua
- wgnuplot.exe (PID: 7632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
177
Monitored processes
32
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2176 --field-trial-handle=72,i,13946582011841688039,6934646391333994593,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1072 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=3040 --field-trial-handle=72,i,13946582011841688039,6934646391333994593,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2236 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2316 | "C:\Users\admin\AppData\Local\Temp\is-7N9FB.tmp\gp500-win32-mingw.tmp" /SL5="$D00BE,22675103,358400,C:\Users\admin\Desktop\gp500-win32-mingw.exe" | C:\Users\admin\AppData\Local\Temp\is-7N9FB.tmp\gp500-win32-mingw.tmp | — | gp500-win32-mingw.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x228,0x22c,0x230,0x204,0x234,0x7ffc8837dc40,0x7ffc8837dc4c,0x7ffc8837dc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2924 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Search application Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6280 --field-trial-handle=72,i,13946582011841688039,6934646391333994593,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=3700 --field-trial-handle=72,i,13946582011841688039,6934646391333994593,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=1780 --field-trial-handle=72,i,13946582011841688039,6934646391333994593,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
35 810
Read events
35 484
Write events
305
Delete events
21
Modification events
| (PID) Process: | (6540) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6540) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6540) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6540) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6540) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2924) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Feeds\DSB |
| Operation: | write | Name: | DynamicText |
Value: | |||
| (PID) Process: | (2924) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Feeds\DSB |
| Operation: | write | Name: | DynamicTextTruncated |
Value: | |||
| (PID) Process: | (2924) SearchApp.exe | Key: | \REGISTRY\A\{919c907a-b14a-1c2d-b076-c1402ff6e70c}\LocalState\DynamicSearchBox |
| Operation: | write | Name: | TelemetryID |
Value: 0000038404DAFB8ADB01 | |||
| (PID) Process: | (2924) SearchApp.exe | Key: | \REGISTRY\A\{919c907a-b14a-1c2d-b076-c1402ff6e70c}\LocalState\ConstraintIndex |
| Operation: | write | Name: | CurrentConstraintIndexCabPath |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C005000610063006B0061006700650073005C004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E005300650061007200630068005F006300770035006E003100680032007400780079006500770079005C004C006F00630061006C00530074006100740065005C0043006F006E00730074007200610069006E00740049006E006400650078005C0049006E007000750074005F007B00380033003200620036003800640032002D0037006600650032002D0034006500370031002D0061003300610064002D003200360031003600360062003600350036006500630036007D0000005F30F5DDFB8ADB01 | |||
| (PID) Process: | (2924) SearchApp.exe | Key: | \REGISTRY\A\{919c907a-b14a-1c2d-b076-c1402ff6e70c}\LocalState\AppsConstraintIndex |
| Operation: | write | Name: | LatestConstraintIndexFolder |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C005000610063006B0061006700650073005C004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E005300650061007200630068005F006300770035006E003100680032007400780079006500770079005C004C006F00630061006C00530074006100740065005C0043006F006E00730074007200610069006E00740049006E006400650078005C0041007000700073005F007B00310063006200370035003100350038002D0034003400360063002D0034003900390034002D0062006500650037002D003400330030003400360039003600310063003800660062007D0000000A58F5DDFB8ADB01 | |||
Executable files
97
Suspicious files
234
Text files
822
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10d8ed.TMP | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10d8ed.TMP | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10d8ed.TMP | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10d8ed.TMP | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10d8ed.TMP | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10d8fd.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
71
DNS requests
65
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5492 | explorer.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
1072 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5408 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5408 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5492 | explorer.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRd0JozUYXMqqW4y4zJTrLcMCRSkAQUgTKSQSsozUbIxKLGKjkS7EipPxQCEDY1ddK1HhyWpYhyH%2B0W7nU%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5492 | explorer.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEDPXCKiRQFMZ4qW70zm5rW4%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 20.190.160.132:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6540 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3008 | backgroundTaskHost.exe | 92.123.104.61:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5392 | chrome.exe | 142.251.18.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
5392 | chrome.exe | 104.22.37.240:443 | limewire.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
limewire.com |
| unknown |
accounts.google.com |
| whitelisted |
js.stripe.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
api.limewire.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5392 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
5392 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
5392 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
5392 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |