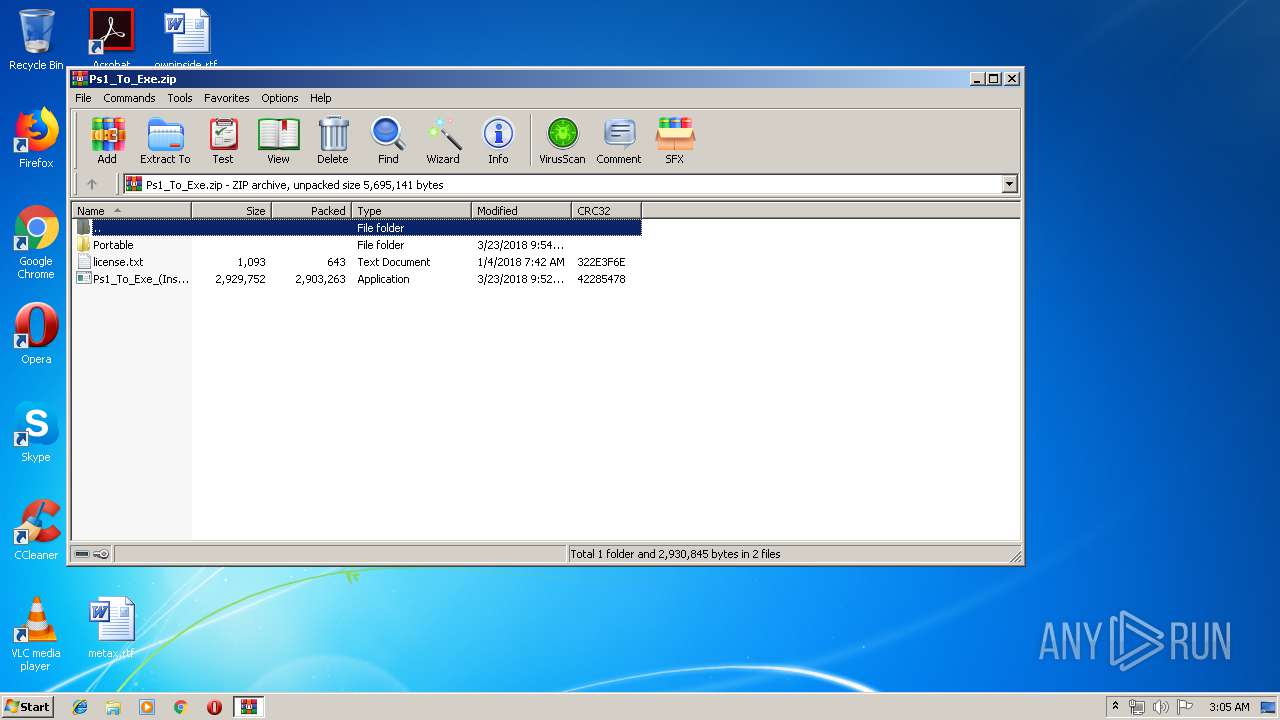
| download: | Ps1_To_Exe.zip |
| Full analysis: | https://app.any.run/tasks/f9bfecd9-61b8-449a-b623-a86afc11c404 |
| Verdict: | Malicious activity |
| Analysis date: | April 05, 2019, 02:04:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 8004BF2AFBE9FD79EC2B6BD901593C61 |
| SHA1: | 730175C12721B31ED570C57B676684F92BFE6030 |
| SHA256: | 4B0AAAE03F8E08F1986AA04CA09717FF64E7BCB4E6841FB585688A959F552DB6 |
| SSDEEP: | 98304:Gbula3kZHiu/FOuiVhz0i+d+FQEEKtzk1dvcnnkBfh/Lz/kprk0tdJI:Gbuk3AOy3d+FQSCnvcnoLr2VdW |
MALICIOUS
Application was dropped or rewritten from another process
- Ps1_To_Exe_(Installer).exe (PID: 3340)
- Ps1_To_Exe_(Installer).exe (PID: 3364)
- Ps1_To_Exe.exe (PID: 3400)
Loads dropped or rewritten executable
- Ps1_To_Exe.exe (PID: 3400)
SUSPICIOUS
Executable content was dropped or overwritten
- Ps1_To_Exe_(Installer).exe (PID: 3340)
- Ps1_To_Exe_(Installer).exe (PID: 3364)
- WinRAR.exe (PID: 2100)
- Ps1_To_Exe_(Installer).tmp (PID: 2884)
- Ps1_To_Exe.exe (PID: 3400)
Creates files in the user directory
- Ps1_To_Exe.exe (PID: 3400)
INFO
Application was dropped or rewritten from another process
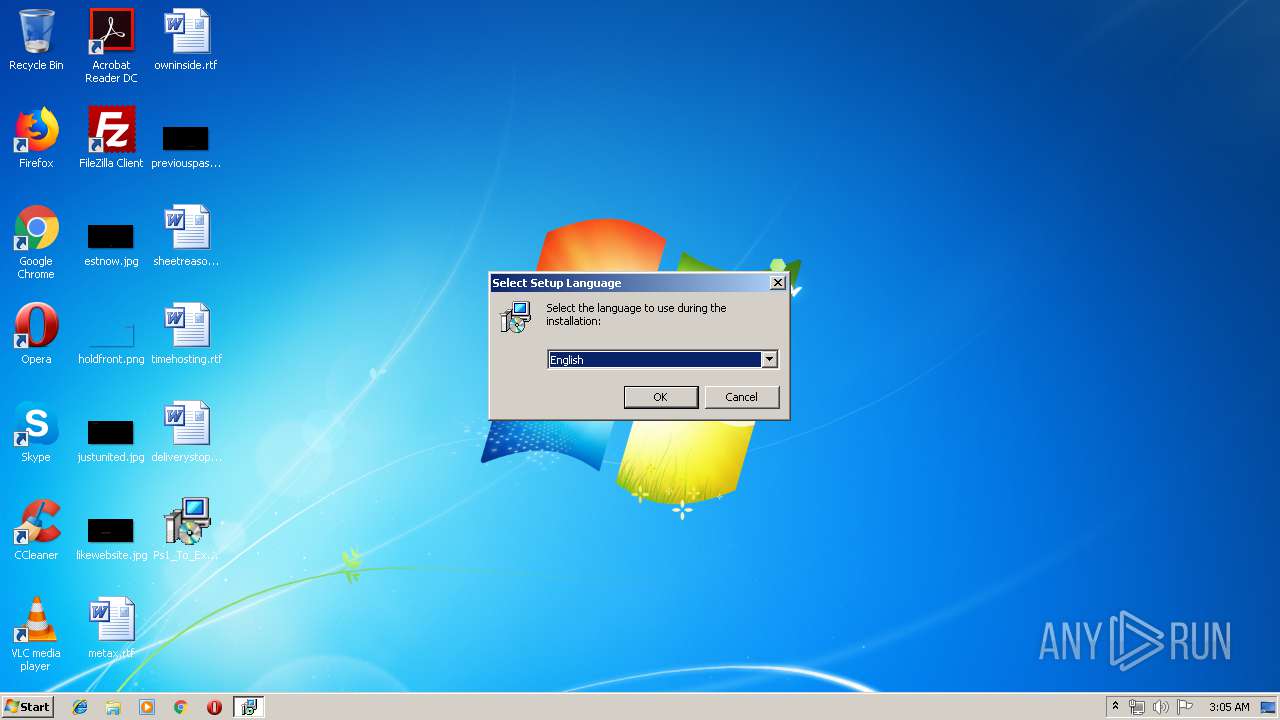
- Ps1_To_Exe_(Installer).tmp (PID: 796)
- Ps1_To_Exe_(Installer).tmp (PID: 2884)
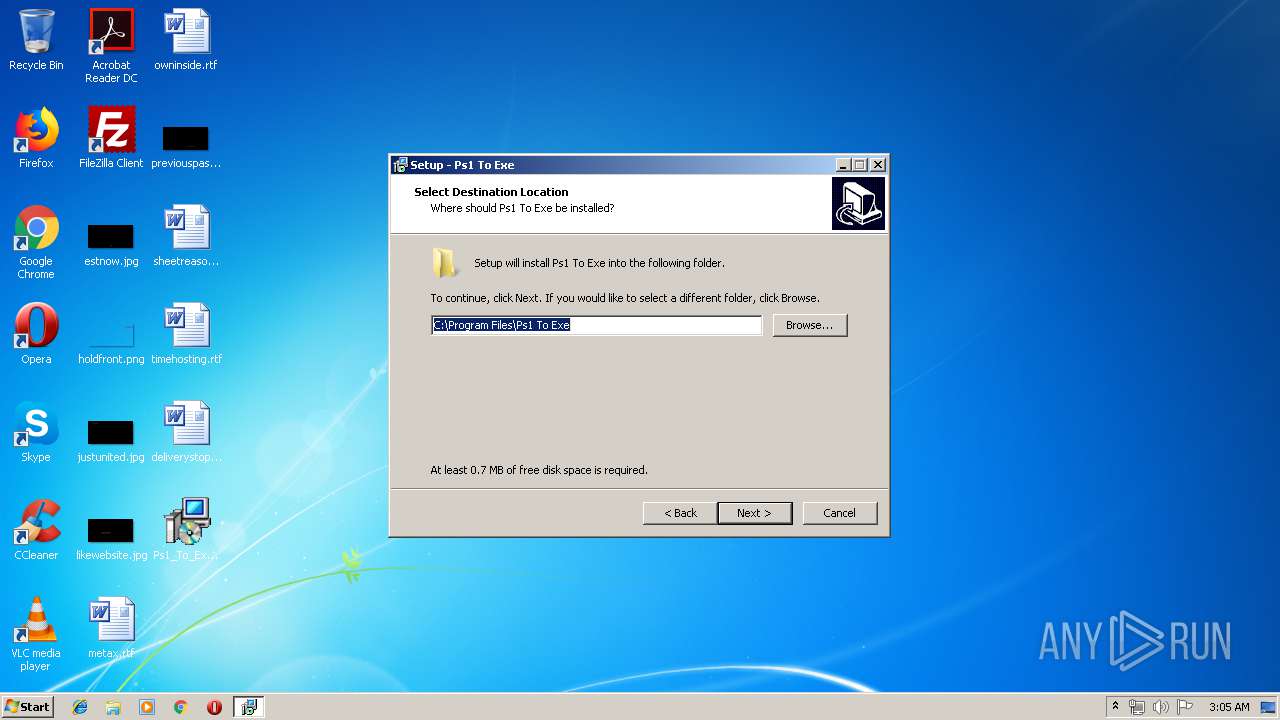
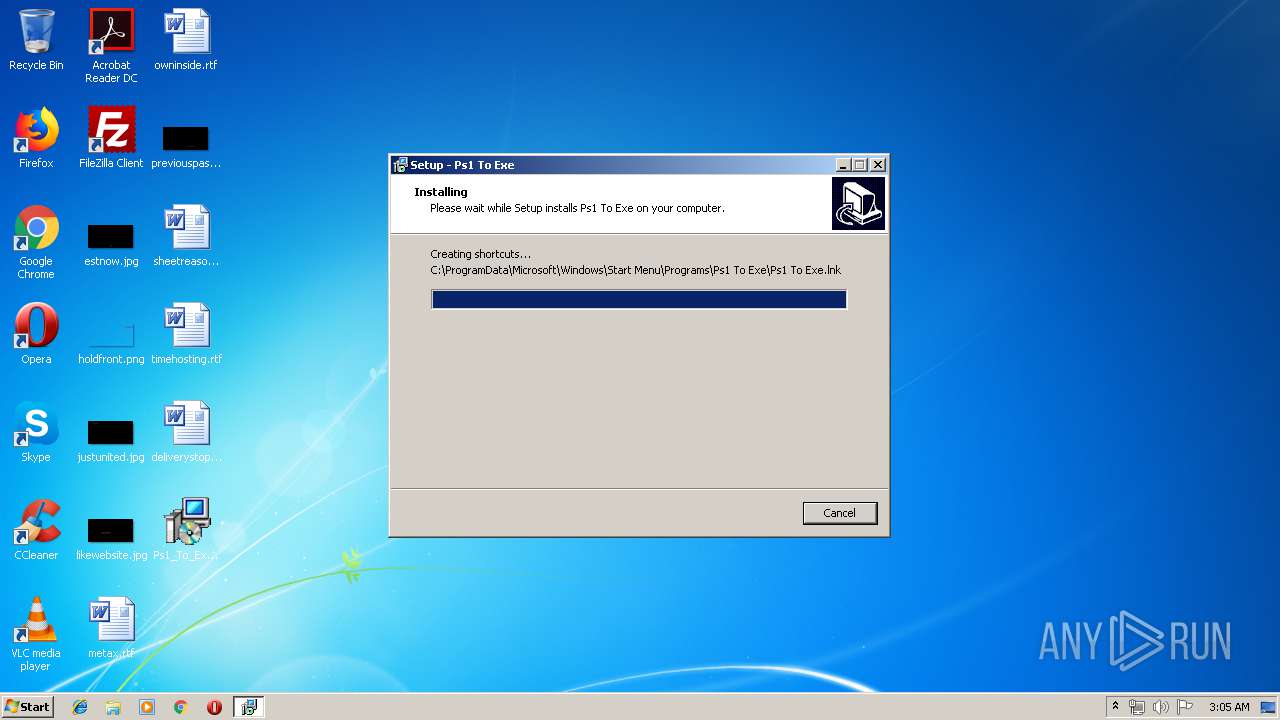
Creates files in the program directory
- Ps1_To_Exe_(Installer).tmp (PID: 2884)
Creates a software uninstall entry
- Ps1_To_Exe_(Installer).tmp (PID: 2884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:01:04 08:42:23 |
| ZipCRC: | 0x322e3f6e |
| ZipCompressedSize: | 643 |
| ZipUncompressedSize: | 1093 |
| ZipFileName: | license.txt |
Total processes
40
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
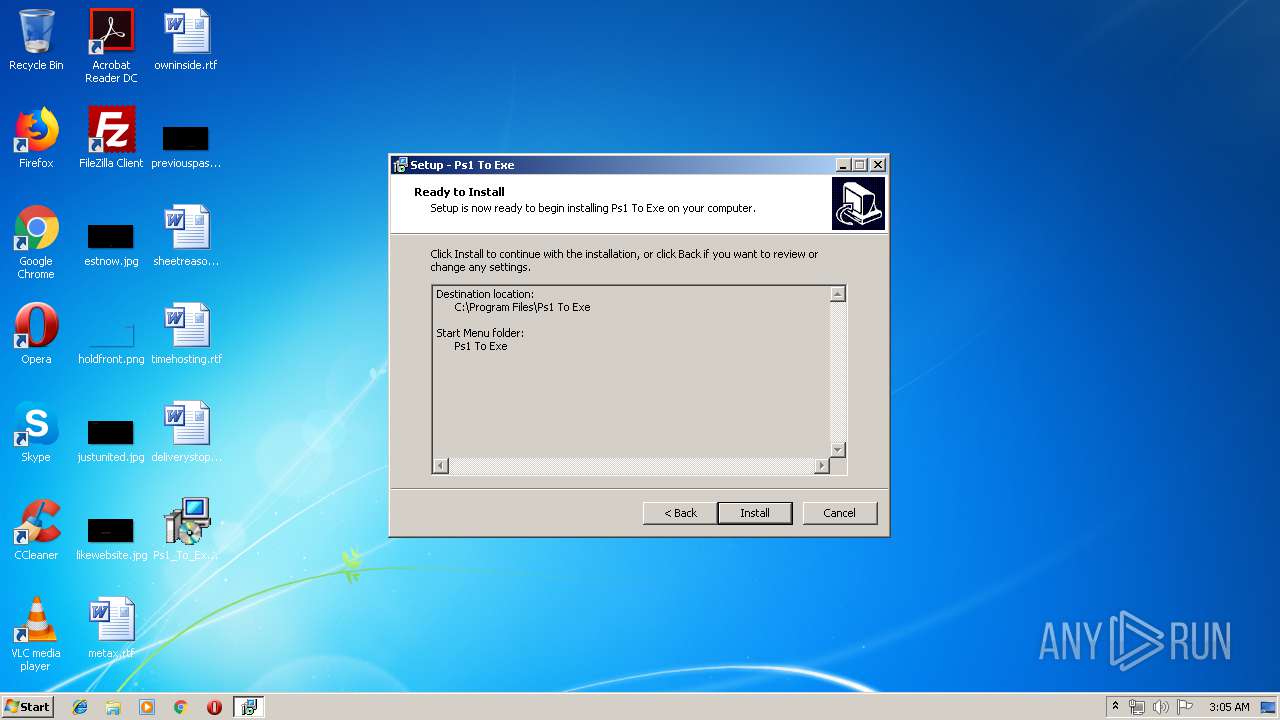
| 796 | "C:\Users\admin\AppData\Local\Temp\is-UTMLB.tmp\Ps1_To_Exe_(Installer).tmp" /SL5="$50158,2678835,57856,C:\Users\admin\Desktop\Ps1_To_Exe_(Installer).exe" | C:\Users\admin\AppData\Local\Temp\is-UTMLB.tmp\Ps1_To_Exe_(Installer).tmp | — | Ps1_To_Exe_(Installer).exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
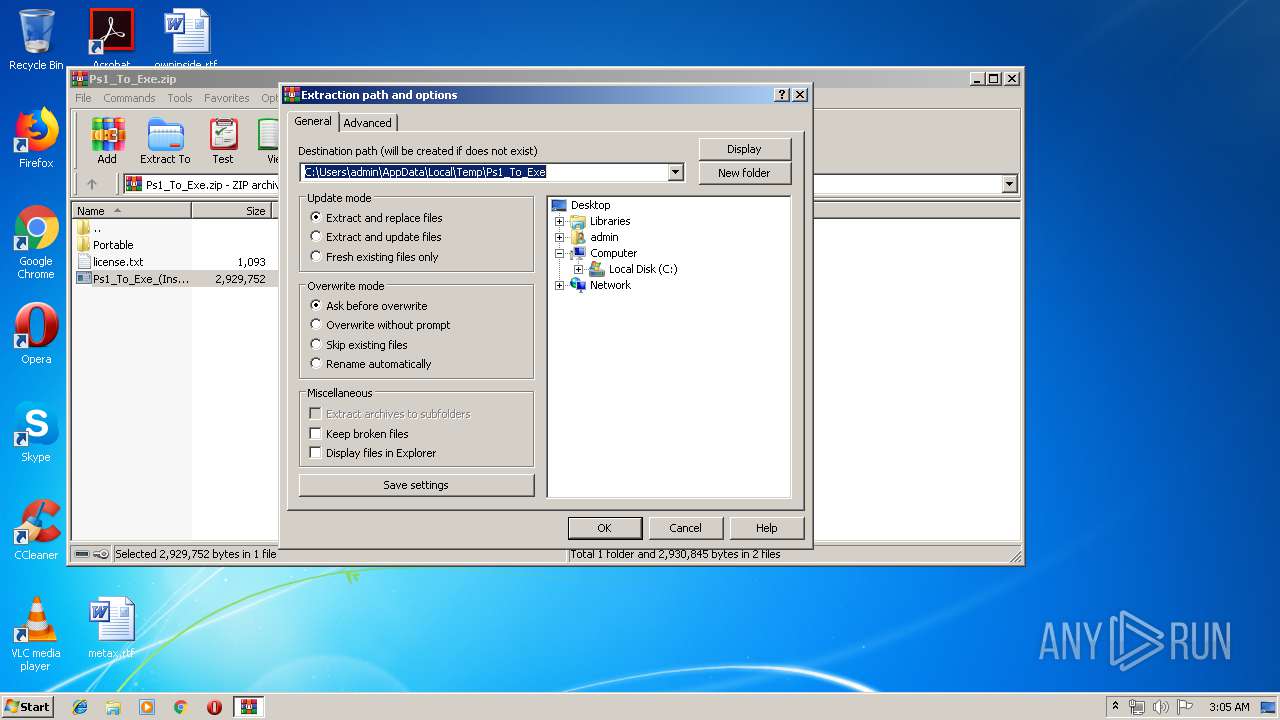
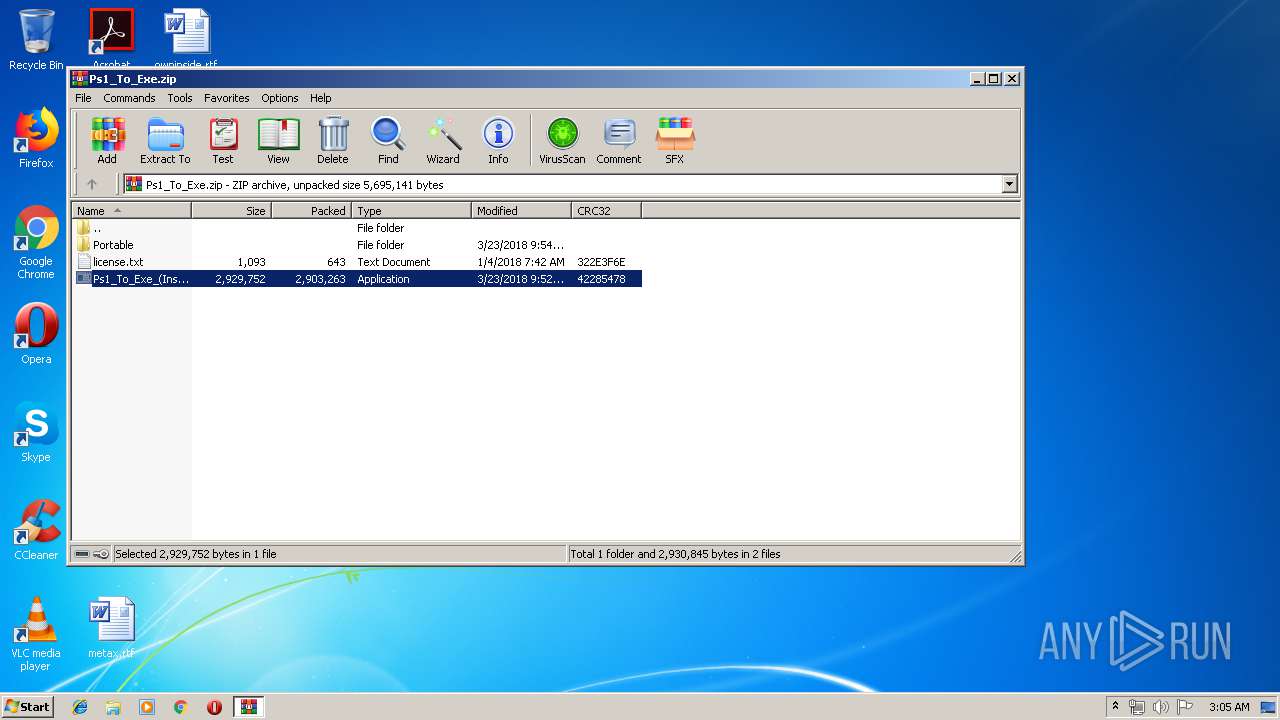
| 2100 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Ps1_To_Exe.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2884 | "C:\Users\admin\AppData\Local\Temp\is-PHCS7.tmp\Ps1_To_Exe_(Installer).tmp" /SL5="$7013C,2678835,57856,C:\Users\admin\Desktop\Ps1_To_Exe_(Installer).exe" /SPAWNWND=$40152 /NOTIFYWND=$50158 | C:\Users\admin\AppData\Local\Temp\is-PHCS7.tmp\Ps1_To_Exe_(Installer).tmp | Ps1_To_Exe_(Installer).exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
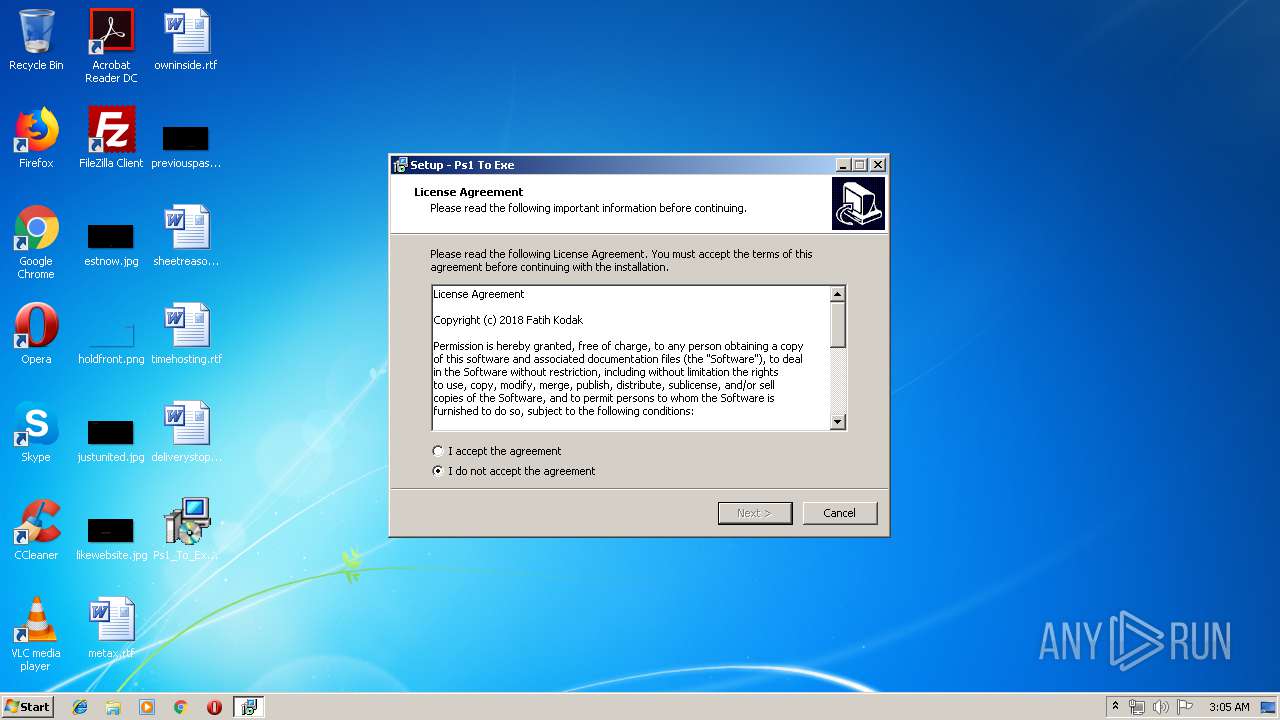
| 3340 | "C:\Users\admin\Desktop\Ps1_To_Exe_(Installer).exe" | C:\Users\admin\Desktop\Ps1_To_Exe_(Installer).exe | explorer.exe | ||||||||||||
User: admin Company: Fatih Kodak Integrity Level: MEDIUM Description: Ps1 To Exe Setup Exit code: 0 Version: 3.0.6.0 Modules
| |||||||||||||||
| 3364 | "C:\Users\admin\Desktop\Ps1_To_Exe_(Installer).exe" /SPAWNWND=$40152 /NOTIFYWND=$50158 | C:\Users\admin\Desktop\Ps1_To_Exe_(Installer).exe | Ps1_To_Exe_(Installer).tmp | ||||||||||||
User: admin Company: Fatih Kodak Integrity Level: HIGH Description: Ps1 To Exe Setup Exit code: 0 Version: 3.0.6.0 Modules
| |||||||||||||||
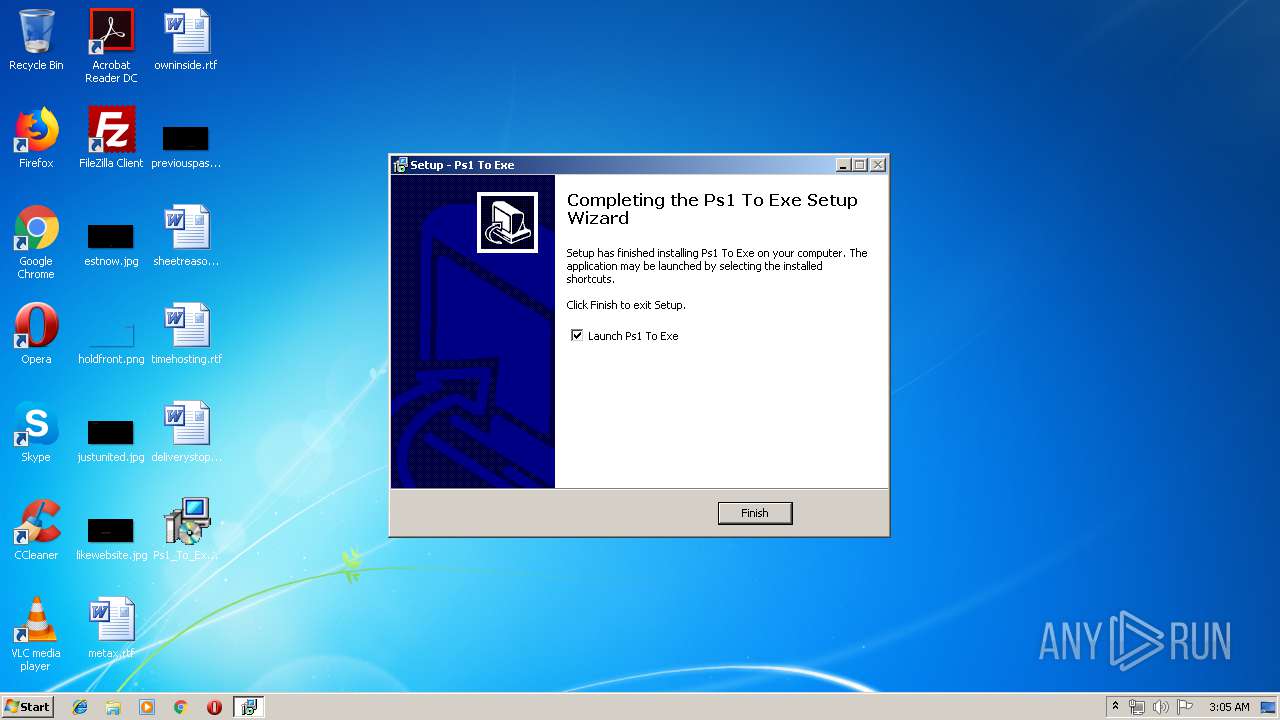
| 3400 | "C:\Program Files\Ps1 To Exe\Ps1_To_Exe.exe" | C:\Program Files\Ps1 To Exe\Ps1_To_Exe.exe | Ps1_To_Exe_(Installer).tmp | ||||||||||||
User: admin Company: Fatih Kodak Integrity Level: MEDIUM Description: Ps1 To Exe Exit code: 0 Version: 3.0.6 Modules
| |||||||||||||||
Total events
1 036
Read events
978
Write events
52
Delete events
6
Modification events
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Ps1_To_Exe.zip | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
| (PID) Process: | (2100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
Executable files
9
Suspicious files
0
Text files
14
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2884 | Ps1_To_Exe_(Installer).tmp | C:\Program Files\Ps1 To Exe\is-3P08J.tmp | — | |
MD5:— | SHA256:— | |||
| 2884 | Ps1_To_Exe_(Installer).tmp | C:\Program Files\Ps1 To Exe\is-GP6DR.tmp | — | |
MD5:— | SHA256:— | |||
| 2884 | Ps1_To_Exe_(Installer).tmp | C:\Program Files\Ps1 To Exe\unins000.exe | executable | |
MD5:E532B45CC101C199E2CD4DBF8B3EBE01 | SHA256:314B17576B002E8D8E49D4626765946292426ECDB5F1A369C3ED1A78525F2636 | |||
| 2884 | Ps1_To_Exe_(Installer).tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Ps1 To Exe\Ps1 To Exe.lnk | lnk | |
MD5:DEA78B4571228EE7368F78D89936F35B | SHA256:33D949CBCF1EDBDAE996DE0A05D36FFCE1F0EDFCD2F8E5EECC53D05E90FF05CA | |||
| 2884 | Ps1_To_Exe_(Installer).tmp | C:\Program Files\Ps1 To Exe\unins000.dat | dat | |
MD5:2C0FAB092C5EB84D9246F4C46997F2F6 | SHA256:63ABB45BAC20D7393E2B8367028E2BE652234A747CBB3A6B457039FB17E30D83 | |||
| 3400 | Ps1_To_Exe.exe | C:\Users\admin\AppData\Roaming\Ps1 To Exe\1327938842.ps1 | — | |
MD5:— | SHA256:— | |||
| 2884 | Ps1_To_Exe_(Installer).tmp | C:\Program Files\Ps1 To Exe\Ps1_To_Exe.exe | executable | |
MD5:AD435ABCE62FCE30C83BB071B0744299 | SHA256:D23296EE323AF2C8F2FEB4089D4F2E27696BB637F53090426BE8ED41D0CE9A60 | |||
| 3400 | Ps1_To_Exe.exe | C:\Users\admin\AppData\Roaming\Ps1 To Exe\lng\Português Brasileiro (Portuguese Brazilian).lng | text | |
MD5:738D25262870AE616C35B30F1E1FA2CF | SHA256:6DA3497851E445D238E14C9A40B9ED613DDFAB8DBCC778A1A78EFC072063985D | |||
| 3340 | Ps1_To_Exe_(Installer).exe | C:\Users\admin\AppData\Local\Temp\is-UTMLB.tmp\Ps1_To_Exe_(Installer).tmp | executable | |
MD5:832DAB307E54AA08F4B6CDD9B9720361 | SHA256:CC783A04CCBCA4EDD06564F8EC88FE5A15F1E3BB26CEC7DE5E090313520D98F3 | |||
| 2884 | Ps1_To_Exe_(Installer).tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Ps1 To Exe\Uninstall Ps1 To Exe.lnk | lnk | |
MD5:6B7B6D8F61E1A47998923C086FFBB132 | SHA256:ECAA77A93B324D94A2C328B5144CE8E596A979528455C0342147D6C7F6061FF5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3400 | Ps1_To_Exe.exe | GET | 200 | 185.21.102.73:80 | http://www.f2ko.de/updates/p2e.php?u=2 | DE | text | 400 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3400 | Ps1_To_Exe.exe | 185.21.102.73:80 | www.f2ko.de | Host Europe GmbH | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.f2ko.de |
| malicious |