| File name: | 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer |
| Full analysis: | https://app.any.run/tasks/4d7b0a3a-3119-471b-a658-939944668bea |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 17:27:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 2 sections |
| MD5: | 10FADB36A5F5391D9F8B9BBA772C1DB9 |
| SHA1: | 75D01345CD6376DB27DACB34FFA73B2C9D1BB98D |
| SHA256: | 4B03FE9113670BD4605511B5FC7F68BDE47B54D124EB3C291C4BC5ED353BF884 |
| SSDEEP: | 24576:KY+nqjgMAK2LBwVi6R39RdH9VXYBZjXNErfPgwo:T+nqjgMAK2LBwVi6R39PH9VXsZjXNCfY |
MALICIOUS
Starts NET.EXE for service management
- net.exe (PID: 1720)
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 6684)
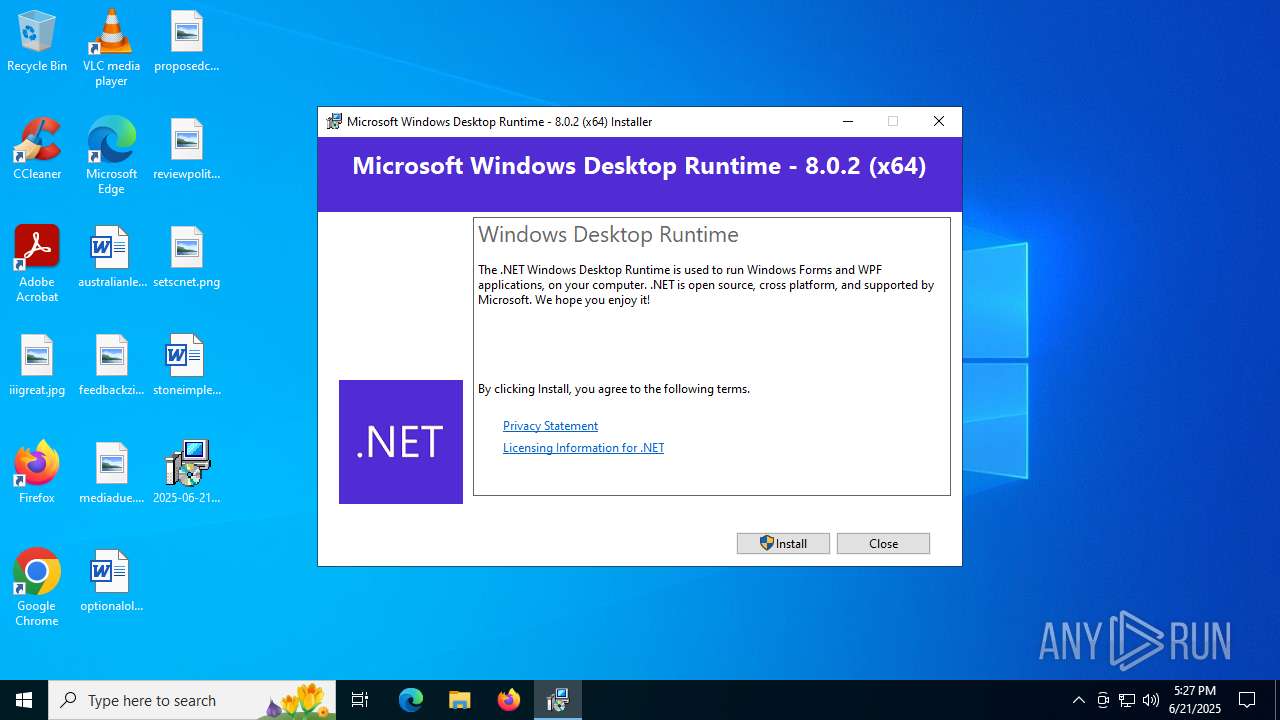
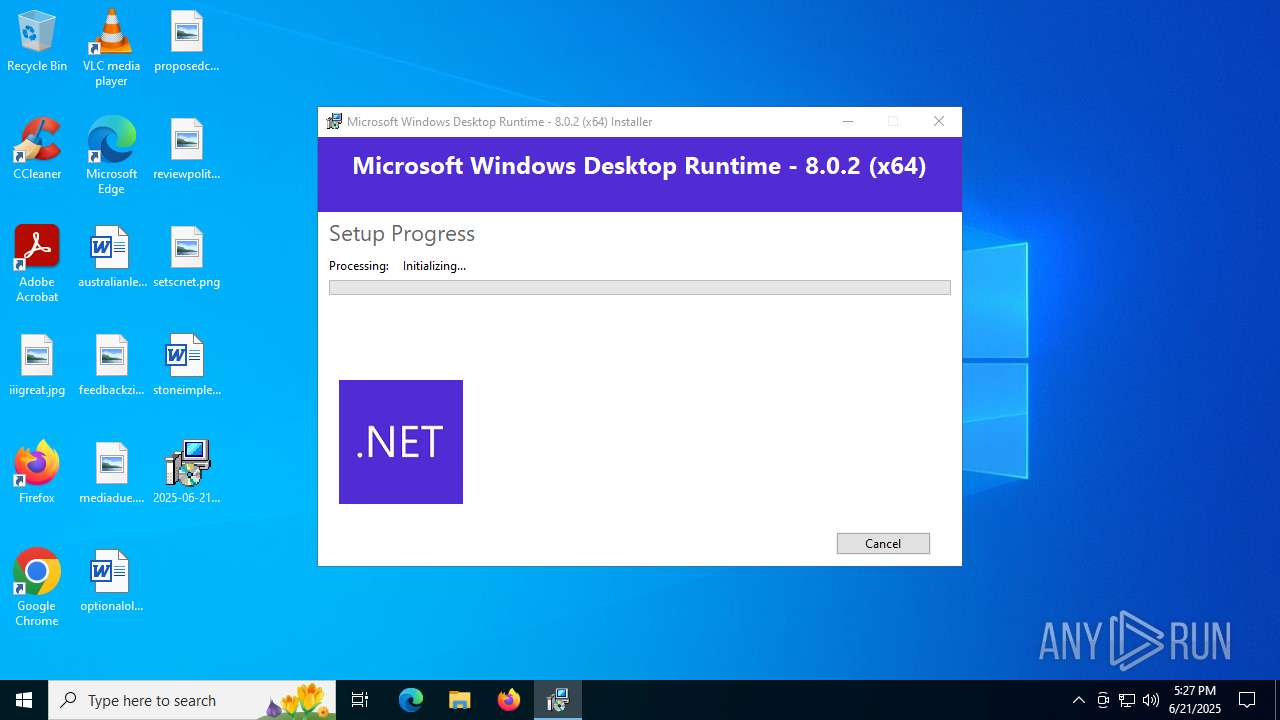
Changes the autorun value in the registry
- windowsdesktop-runtime-8.0.2-win-x64.exe (PID: 2124)
SUSPICIOUS
Starts a Microsoft application from unusual location
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 6684)
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 1700)
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 6260)
- windowsdesktop-runtime-8.0.2-win-x64.exe (PID: 2124)
Executable content was dropped or overwritten
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 6684)
- cmd.exe (PID: 6268)
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 1700)
- windowsdesktop-runtime-8.0.2-win-x64.exe (PID: 2124)
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 6260)
Process drops legitimate windows executable
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 1700)
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 6684)
- cmd.exe (PID: 6268)
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 6260)
- windowsdesktop-runtime-8.0.2-win-x64.exe (PID: 2124)
Executing commands from a ".bat" file
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 6684)
Starts CMD.EXE for commands execution
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 6684)
Searches for installed software
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 6260)
Reads security settings of Internet Explorer
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 6260)
Starts itself from another location
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 6260)
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 1700)
Creates a software uninstall entry
- windowsdesktop-runtime-8.0.2-win-x64.exe (PID: 2124)
INFO
Checks supported languages
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 6684)
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 1700)
- windowsdesktop-runtime-8.0.2-win-x64.exe (PID: 2124)
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 6260)
The sample compiled with chinese language support
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 6684)
Failed to create an executable file in Windows directory
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 6684)
The sample compiled with english language support
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 6684)
- cmd.exe (PID: 6268)
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 1700)
- windowsdesktop-runtime-8.0.2-win-x64.exe (PID: 2124)
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 6260)
Create files in a temporary directory
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 6684)
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 1700)
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 6260)
Reads the computer name
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 6260)
- windowsdesktop-runtime-8.0.2-win-x64.exe (PID: 2124)
Process checks computer location settings
- 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe (PID: 6260)
Creates files in the program directory
- windowsdesktop-runtime-8.0.2-win-x64.exe (PID: 2124)
Checks proxy server information
- slui.exe (PID: 2580)
Launching a file from a Registry key
- windowsdesktop-runtime-8.0.2-win-x64.exe (PID: 2124)
Reads the software policy settings
- slui.exe (PID: 2580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | DOS Executable Generic (100) |
|---|
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 0.37 |
| CodeSize: | 73728 |
| InitializedDataSize: | 41472 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x381db |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Windows, Chinese (Simplified) |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| Comments: | - |
Total processes
144
Monitored processes
10
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1700 | "C:\Users\admin\Desktop\2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe" | C:\Users\admin\Desktop\2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Desktop Runtime - 8.0.2 (x64) Exit code: 1 Version: 8.0.2.33318 Modules
| |||||||||||||||
| 1720 | net stop "Kingsoft AntiVirus Service" | C:\Windows\SysWOW64\net.exe | — | 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2124 | "C:\Users\admin\AppData\Local\Temp\{54A70FE9-9224-4FDC-BE9D-16F115ED1A38}\.be\windowsdesktop-runtime-8.0.2-win-x64.exe" -q -burn.elevated BurnPipe.{7BC8F05B-7649-4D3A-BE8D-B2B07E5E2EAA} {07FD80DF-E204-4C44-A892-ABCDE4DF512E} 6260 | C:\Users\admin\AppData\Local\Temp\{54A70FE9-9224-4FDC-BE9D-16F115ED1A38}\.be\windowsdesktop-runtime-8.0.2-win-x64.exe | 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Windows Desktop Runtime - 8.0.2 (x64) Exit code: 1 Version: 8.0.2.33318 Modules
| |||||||||||||||
| 2580 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3640 | C:\WINDOWS\system32\net1 stop "Kingsoft AntiVirus Service" | C:\Windows\SysWOW64\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4224 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5084 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6260 | "C:\Users\admin\AppData\Local\Temp\{1EA46257-2C38-4DBC-98B0-D9B1096321AE}\.cr\2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe" -burn.clean.room="C:\Users\admin\Desktop\2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe" -burn.filehandle.attached=596 -burn.filehandle.self=592 | C:\Users\admin\AppData\Local\Temp\{1EA46257-2C38-4DBC-98B0-D9B1096321AE}\.cr\2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe | 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Desktop Runtime - 8.0.2 (x64) Exit code: 1 Version: 8.0.2.33318 Modules
| |||||||||||||||
| 6268 | C:\WINDOWS\system32\cmd.exe /c C:\Users\admin\AppData\Local\Temp\$a6C18.bat | C:\Windows\SysWOW64\cmd.exe | 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6684 | "C:\Users\admin\Desktop\2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe" | C:\Users\admin\Desktop\2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Desktop Runtime - 8.0.2 (x64) Exit code: 0 Version: 8.0.2.33318 Modules
| |||||||||||||||
Total events
4 392
Read events
4 359
Write events
26
Delete events
7
Modification events
| (PID) Process: | (2124) windowsdesktop-runtime-8.0.2-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Installer\Dependencies\{63880b41-04fc-4f9b-92c4-4455c255eb8c}\Dependents\{63880b41-04fc-4f9b-92c4-4455c255eb8c} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2124) windowsdesktop-runtime-8.0.2-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Installer\Dependencies\{63880b41-04fc-4f9b-92c4-4455c255eb8c}\Dependents |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2124) windowsdesktop-runtime-8.0.2-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Installer\Dependencies\{63880b41-04fc-4f9b-92c4-4455c255eb8c} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2124) windowsdesktop-runtime-8.0.2-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{63880b41-04fc-4f9b-92c4-4455c255eb8c} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2124) windowsdesktop-runtime-8.0.2-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | delete value | Name: | {63880b41-04fc-4f9b-92c4-4455c255eb8c} |
Value: "C:\ProgramData\Package Cache\{63880b41-04fc-4f9b-92c4-4455c255eb8c}\windowsdesktop-runtime-8.0.2-win-x64.exe" /burn.runonce | |||
| (PID) Process: | (2124) windowsdesktop-runtime-8.0.2-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{63880b41-04fc-4f9b-92c4-4455c255eb8c} |
| Operation: | write | Name: | BundleCachePath |
Value: C:\ProgramData\Package Cache\{63880b41-04fc-4f9b-92c4-4455c255eb8c}\windowsdesktop-runtime-8.0.2-win-x64.exe | |||
| (PID) Process: | (2124) windowsdesktop-runtime-8.0.2-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{63880b41-04fc-4f9b-92c4-4455c255eb8c} |
| Operation: | write | Name: | BundleUpgradeCode |
Value: {7F5F299F-5EB1-6FC0-6D86-FB7931E33C68} | |||
| (PID) Process: | (2124) windowsdesktop-runtime-8.0.2-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{63880b41-04fc-4f9b-92c4-4455c255eb8c} |
| Operation: | write | Name: | BundleAddonCode |
Value: | |||
| (PID) Process: | (2124) windowsdesktop-runtime-8.0.2-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{63880b41-04fc-4f9b-92c4-4455c255eb8c} |
| Operation: | write | Name: | BundleDetectCode |
Value: | |||
| (PID) Process: | (2124) windowsdesktop-runtime-8.0.2-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{63880b41-04fc-4f9b-92c4-4455c255eb8c} |
| Operation: | write | Name: | BundlePatchCode |
Value: | |||
Executable files
7
Suspicious files
1
Text files
22
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6684 | 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe | C:\Users\admin\Desktop\2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe.exe | executable | |
MD5:68CD9B0B134AD40199C3744B150646A8 | SHA256:B5432EB3CB3123BC0EB6471A6FD3DCB3C2C69304649D0317B37EA8E2F8D68FA5 | |||
| 6684 | 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe | C:\Users\admin\AppData\Local\Temp\$a6C18.bat | text | |
MD5:01311D1BBAF56D675655E486C21660B6 | SHA256:9E70BF117901B363F5B12267ABD7787AB406FCC37907FA9B52D467FB2ADFBEEE | |||
| 6260 | 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe | C:\Users\admin\AppData\Local\Temp\{54A70FE9-9224-4FDC-BE9D-16F115ED1A38}\.ba\bg.png | image | |
MD5:9EB0320DFBF2BD541E6A55C01DDC9F20 | SHA256:9095BF7B6BAA0107B40A4A6D727215BE077133A190F4CA9BD89A176842141E79 | |||
| 6260 | 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe | C:\Users\admin\AppData\Local\Temp\{54A70FE9-9224-4FDC-BE9D-16F115ED1A38}\.ba\thm.wxl | xml | |
MD5:D5070CB3387A0A22B7046AE5AB53F371 | SHA256:81A68046B06E09385BE8449373E7CEB9E79F7724C3CF11F0B18A4489A8D4926A | |||
| 1700 | 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe | C:\Users\admin\AppData\Local\Temp\{1EA46257-2C38-4DBC-98B0-D9B1096321AE}\.cr\2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe | executable | |
MD5:68CD9B0B134AD40199C3744B150646A8 | SHA256:B5432EB3CB3123BC0EB6471A6FD3DCB3C2C69304649D0317B37EA8E2F8D68FA5 | |||
| 6260 | 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe | C:\Users\admin\AppData\Local\Temp\{54A70FE9-9224-4FDC-BE9D-16F115ED1A38}\.ba\thm.xml | xml | |
MD5:302563A713B142EE41B59E3EEAC53A90 | SHA256:83CA096F7BA2C83FC3B3AEB697B8139A788FA35EB8632943E26BB9FFF7C78E63 | |||
| 6260 | 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe | C:\Users\admin\AppData\Local\Temp\{54A70FE9-9224-4FDC-BE9D-16F115ED1A38}\.ba\wixstdba.dll | executable | |
MD5:4356EE50F0B1A878E270614780DDF095 | SHA256:41A8787FDC9467F563438DABA4131191AA1EB588A81BEB9A89FE8BD886C16104 | |||
| 6260 | 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe | C:\Users\admin\AppData\Local\Temp\{54A70FE9-9224-4FDC-BE9D-16F115ED1A38}\.ba\1029\thm.wxl | xml | |
MD5:27411946EF45B3B8236319421770E5AD | SHA256:C92D3EFD72D6D14148F9931128EE4143AFFD1DA517EB358AB88ED4138C1434A4 | |||
| 6260 | 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe | C:\Users\admin\AppData\Local\Temp\{54A70FE9-9224-4FDC-BE9D-16F115ED1A38}\.ba\1031\thm.wxl | xml | |
MD5:B45249A2238A5568B377E58D4CE89E9A | SHA256:0C4203A81DCD01D53378036AF78CFFCF9E9A5AF7754DFBDD56584AE74C21CC61 | |||
| 6260 | 2025-06-21_10fadb36a5f5391d9f8b9bba772c1db9_amadey_black-basta_coinminer_elex_luca-stealer.exe | C:\Users\admin\AppData\Local\Temp\{54A70FE9-9224-4FDC-BE9D-16F115ED1A38}\.ba\1033\thm.wxl | xml | |
MD5:D5070CB3387A0A22B7046AE5AB53F371 | SHA256:81A68046B06E09385BE8449373E7CEB9E79F7724C3CF11F0B18A4489A8D4926A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
19
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.55.104.190:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3396 | RUXIMICS.exe | GET | 200 | 23.55.104.190:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.55.104.190:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3396 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3396 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.55.104.190:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
1268 | svchost.exe | 23.55.104.190:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
3396 | RUXIMICS.exe | 23.55.104.190:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
5944 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |