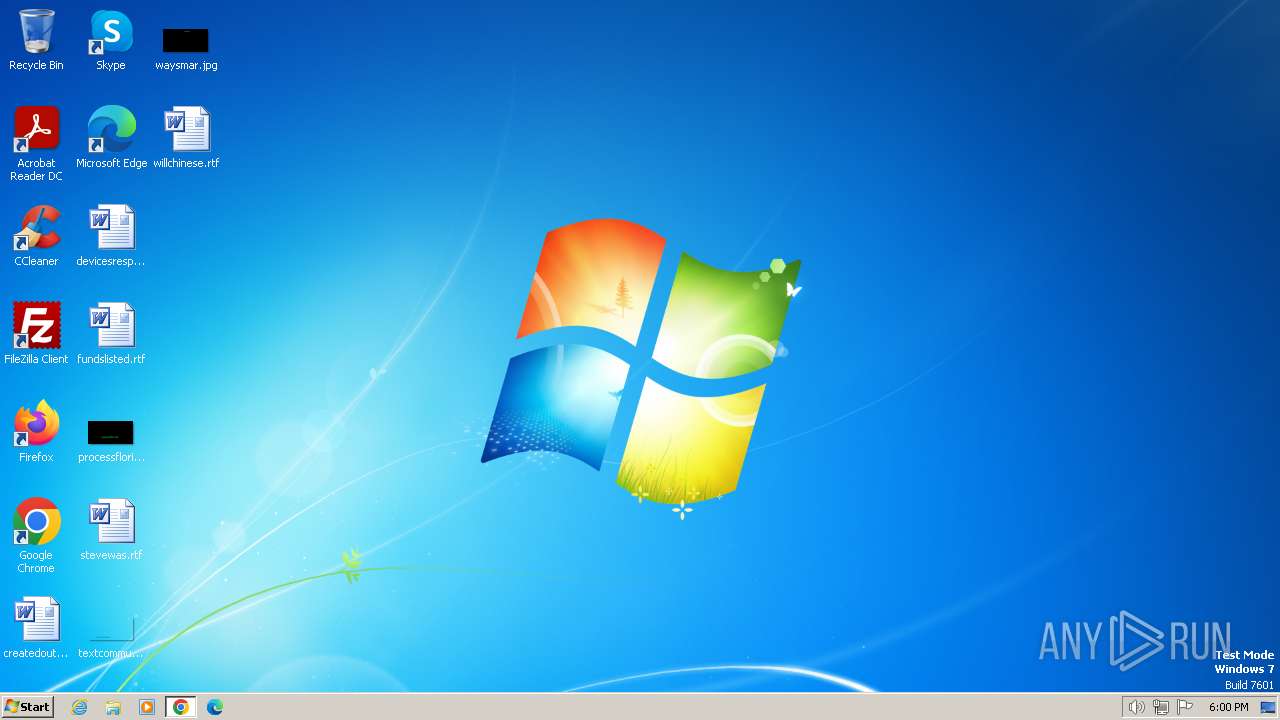
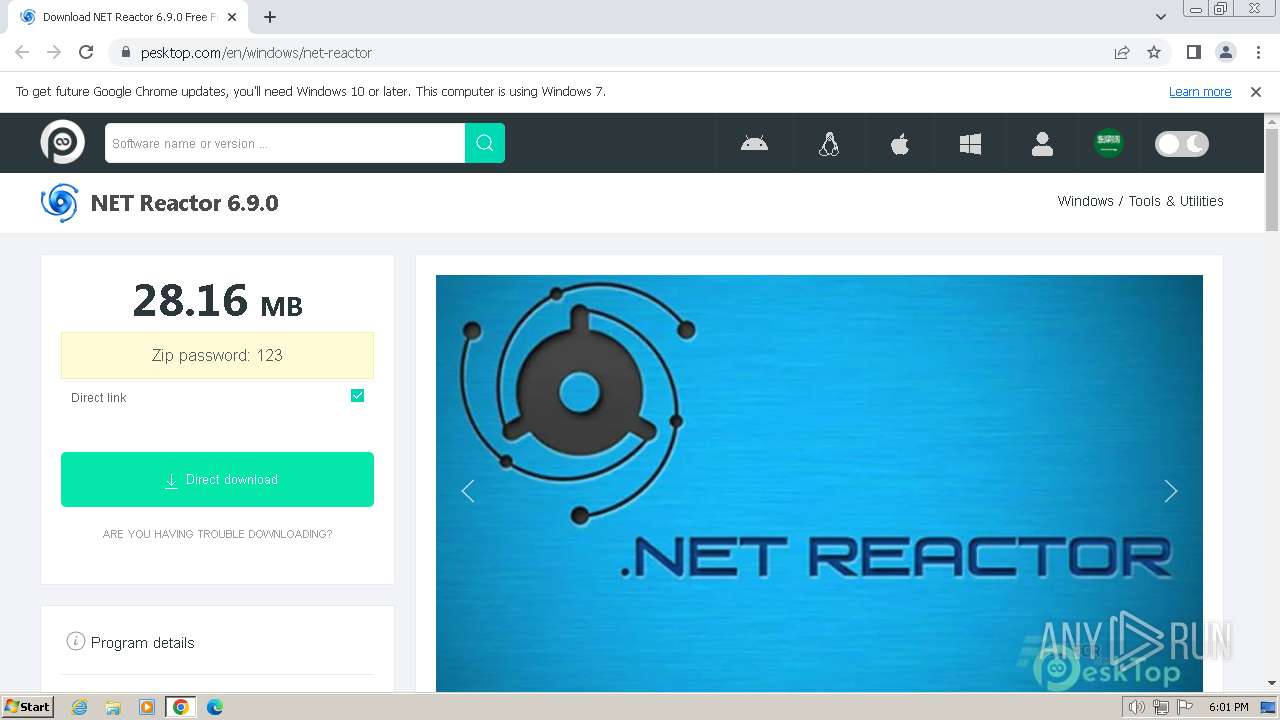
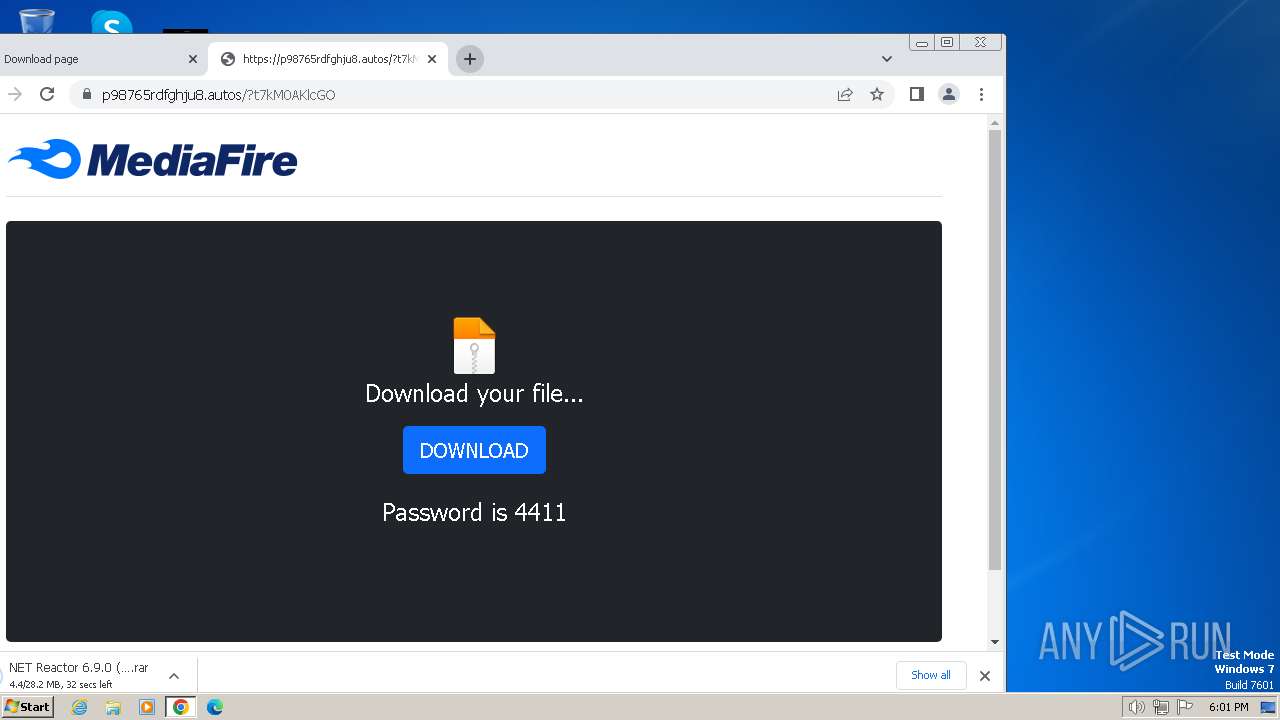
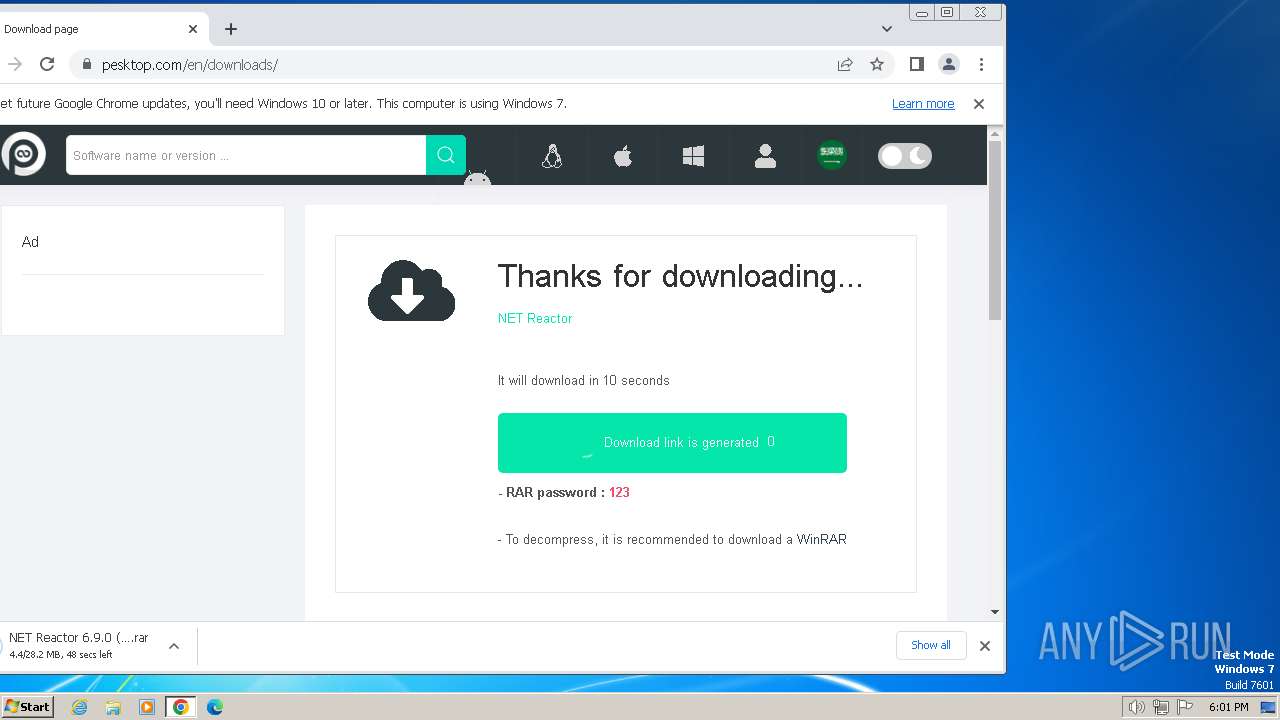
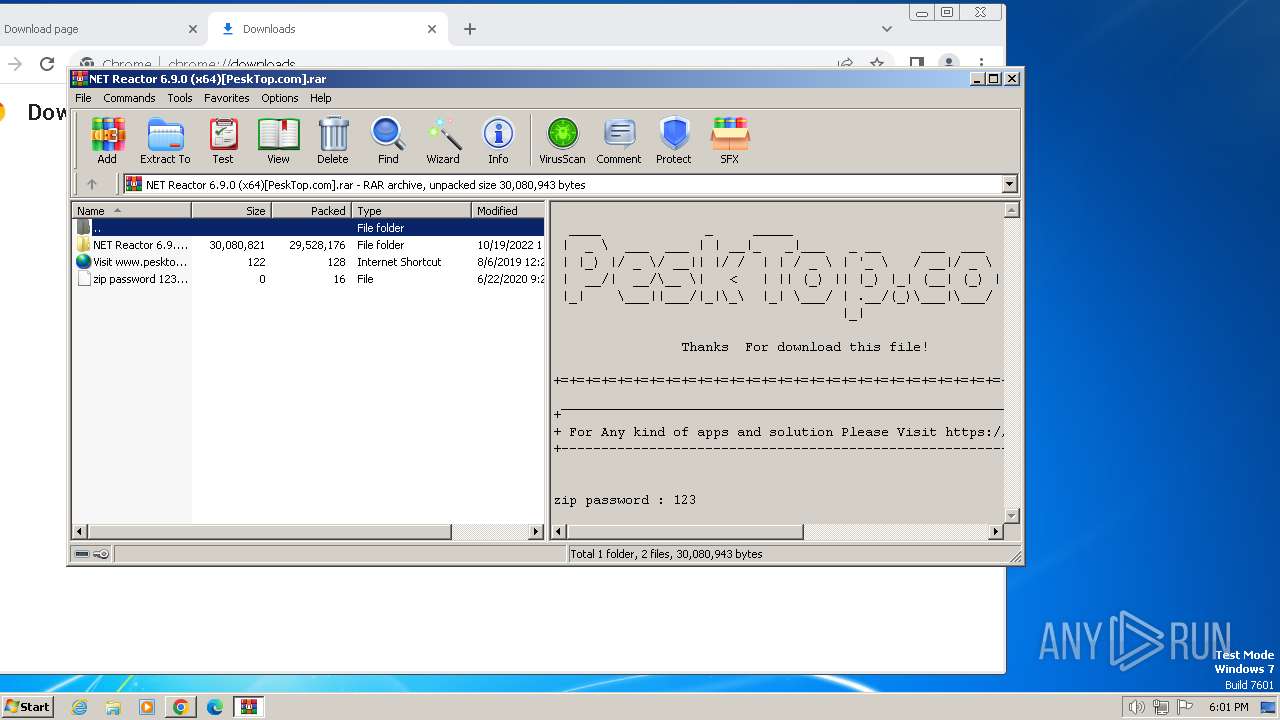
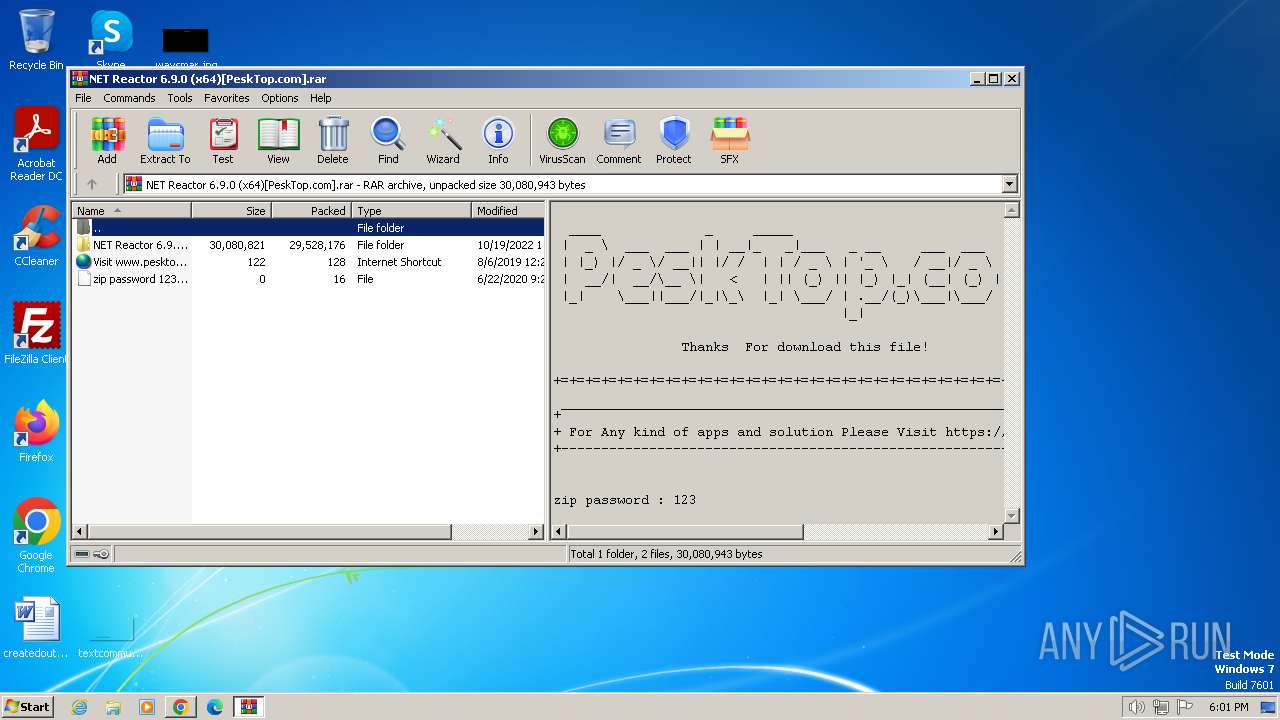
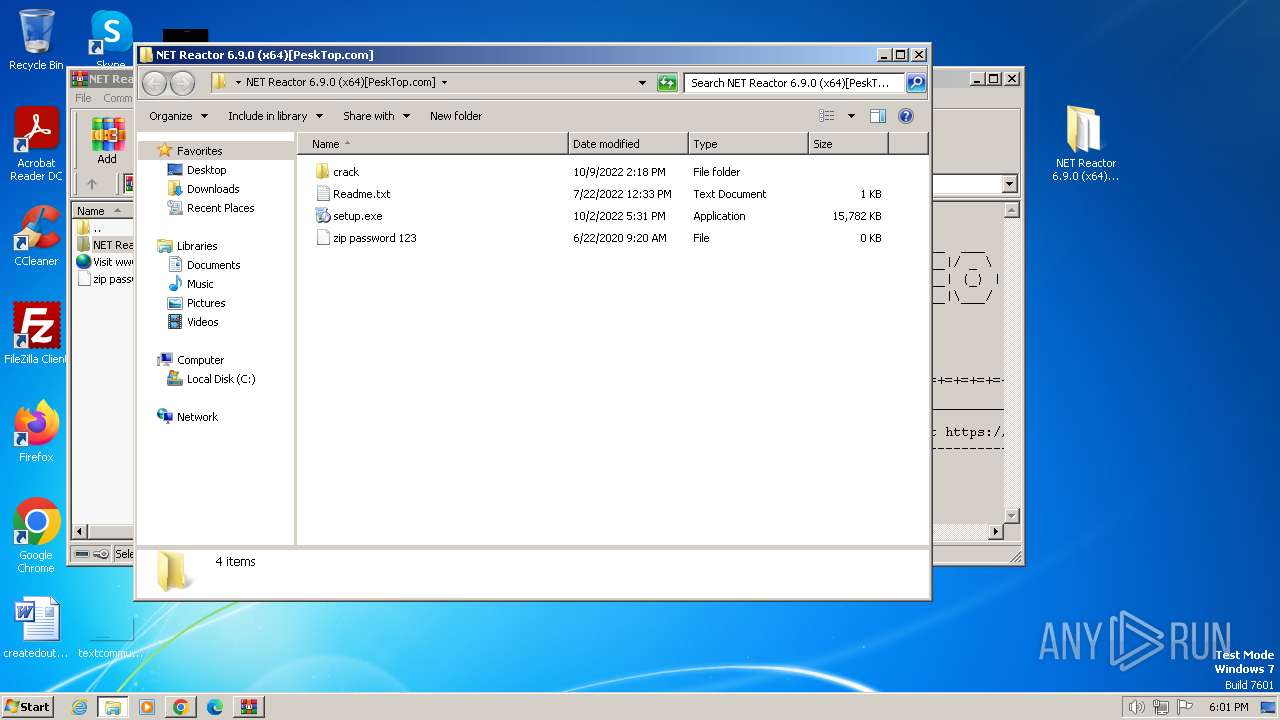
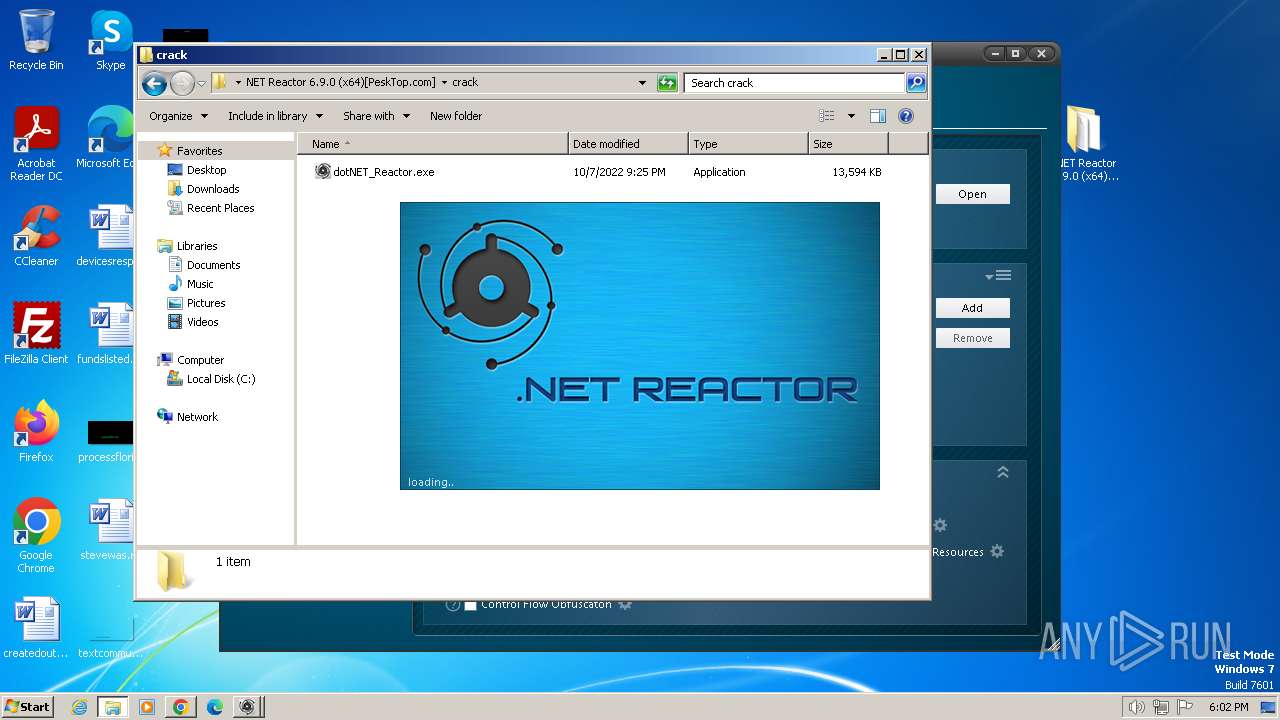
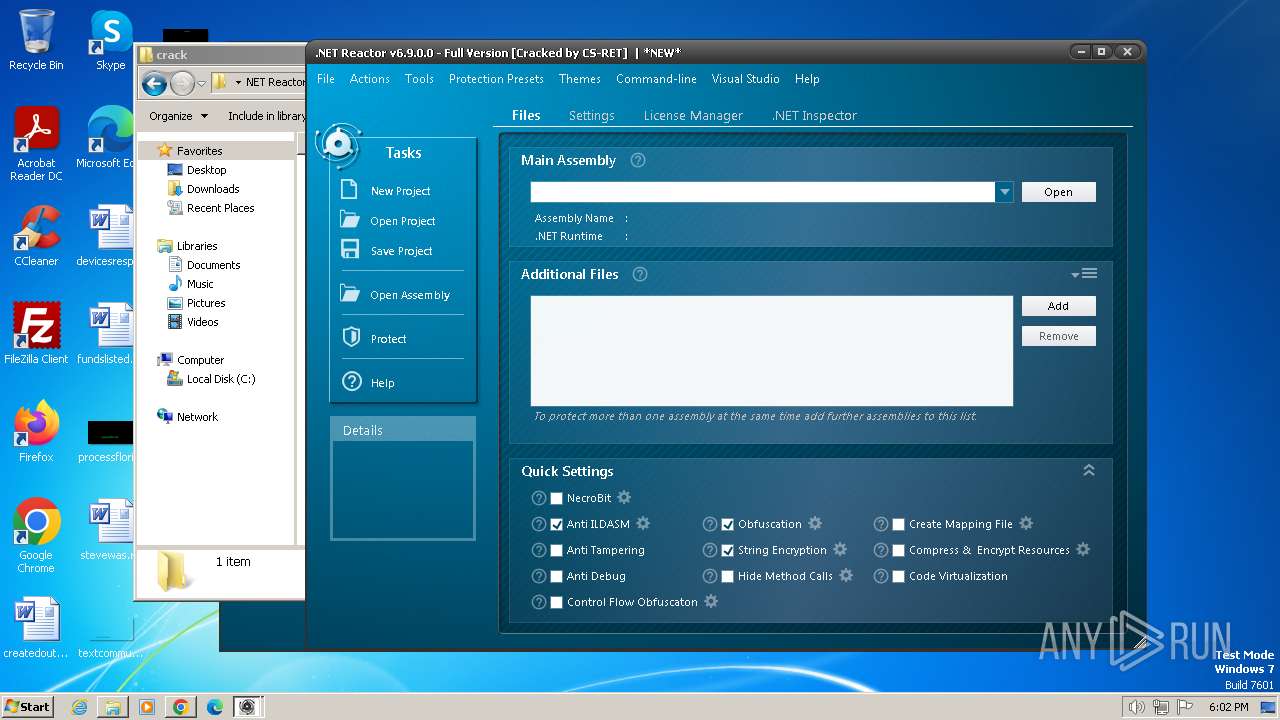
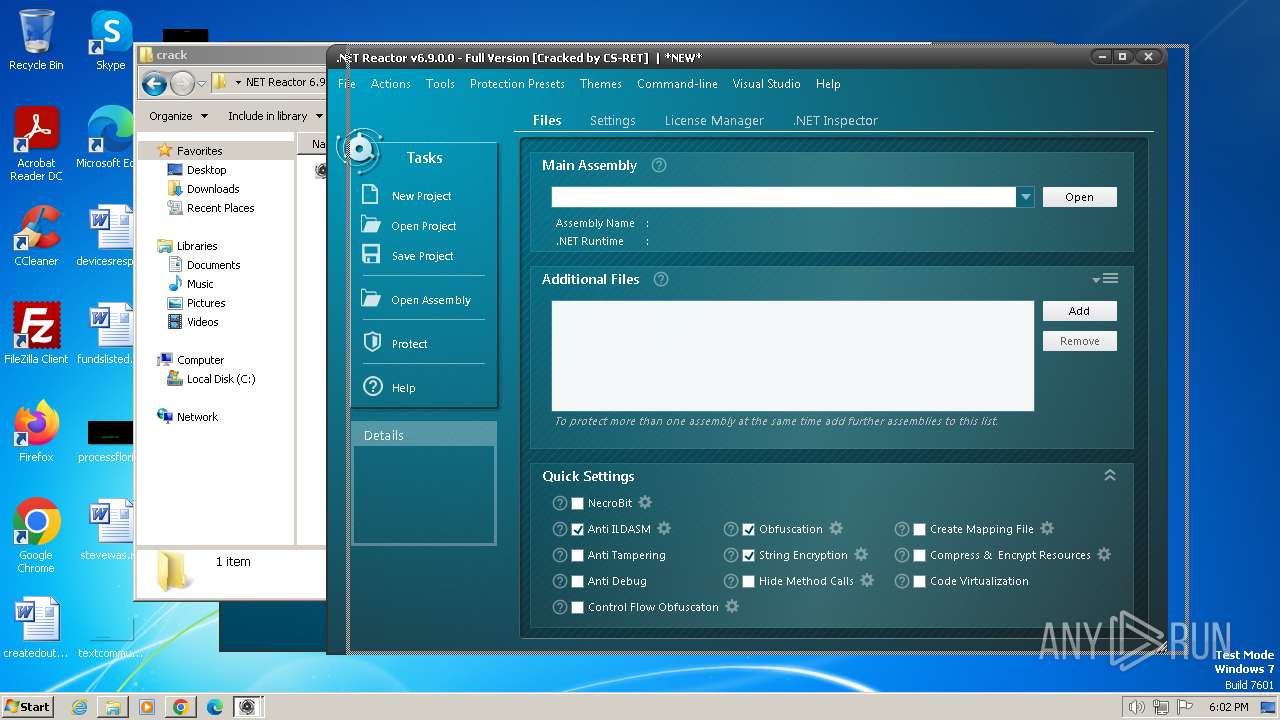
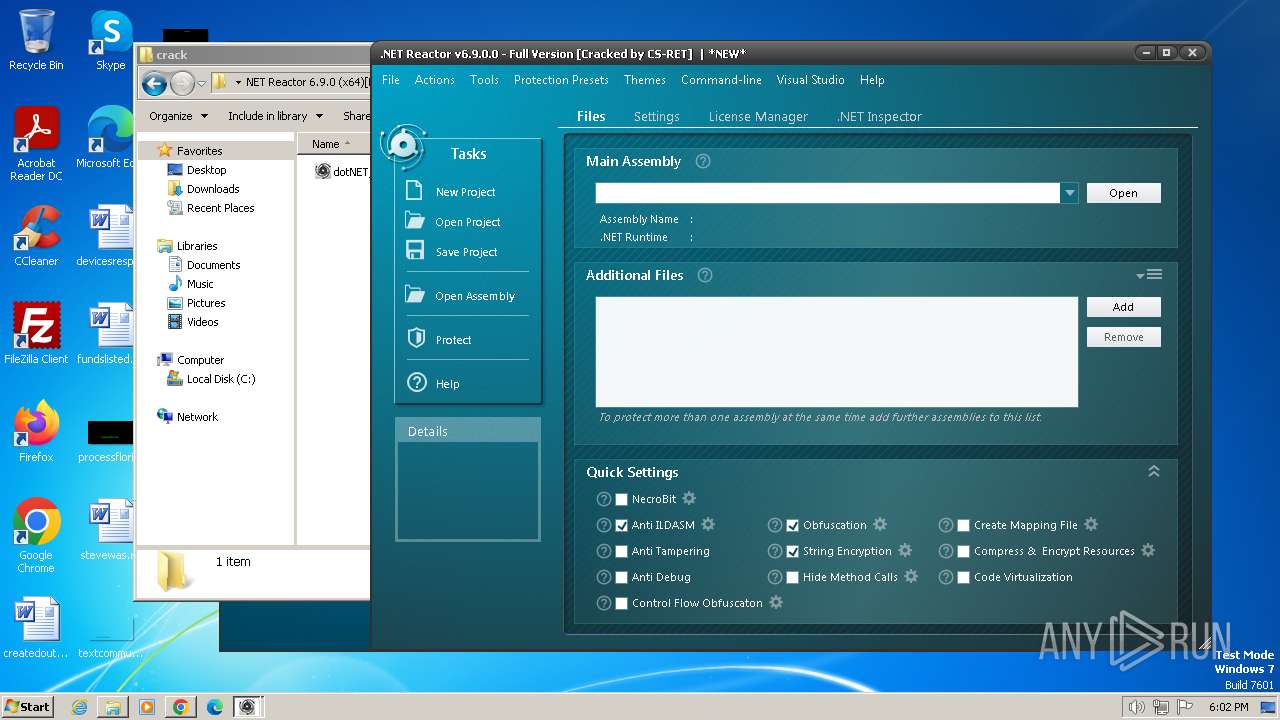
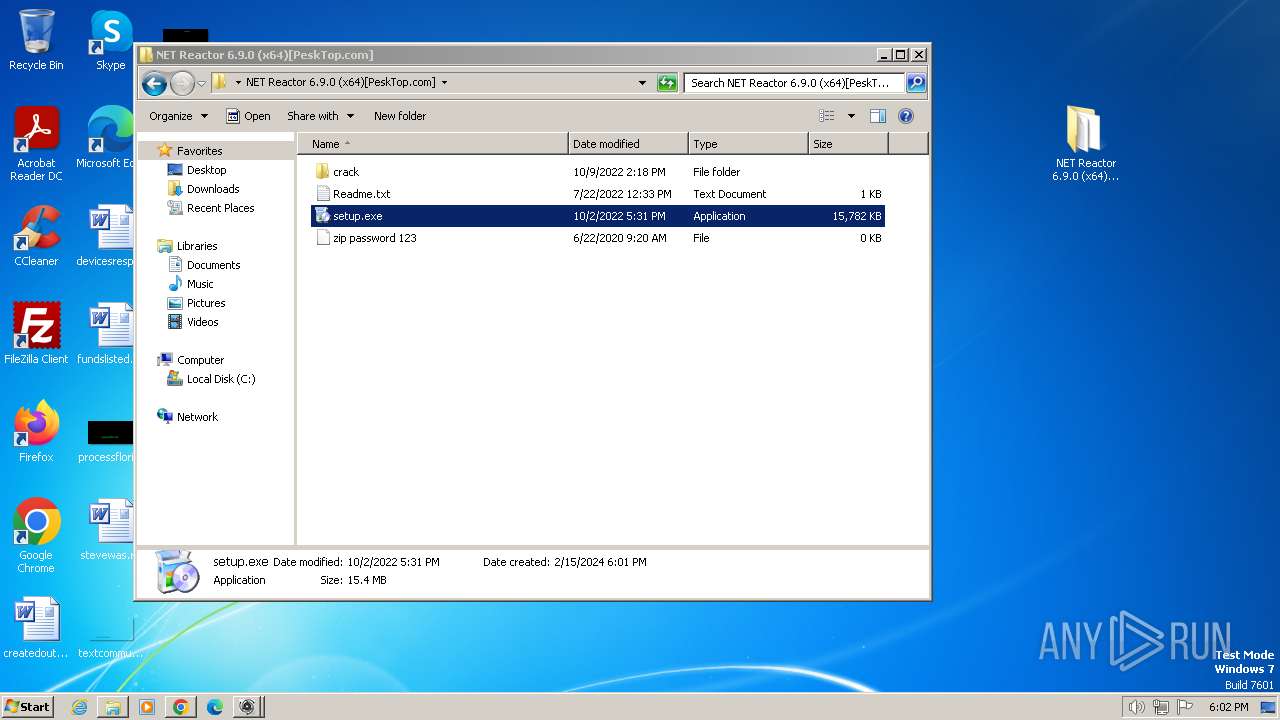
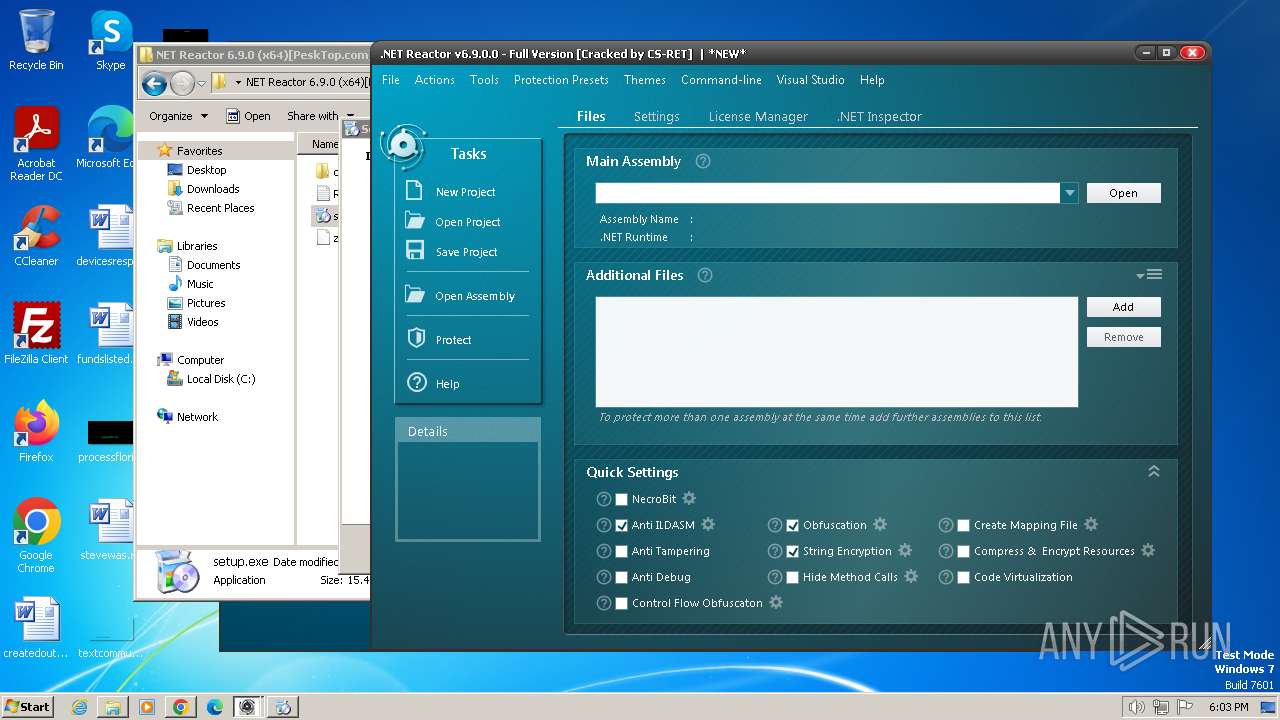
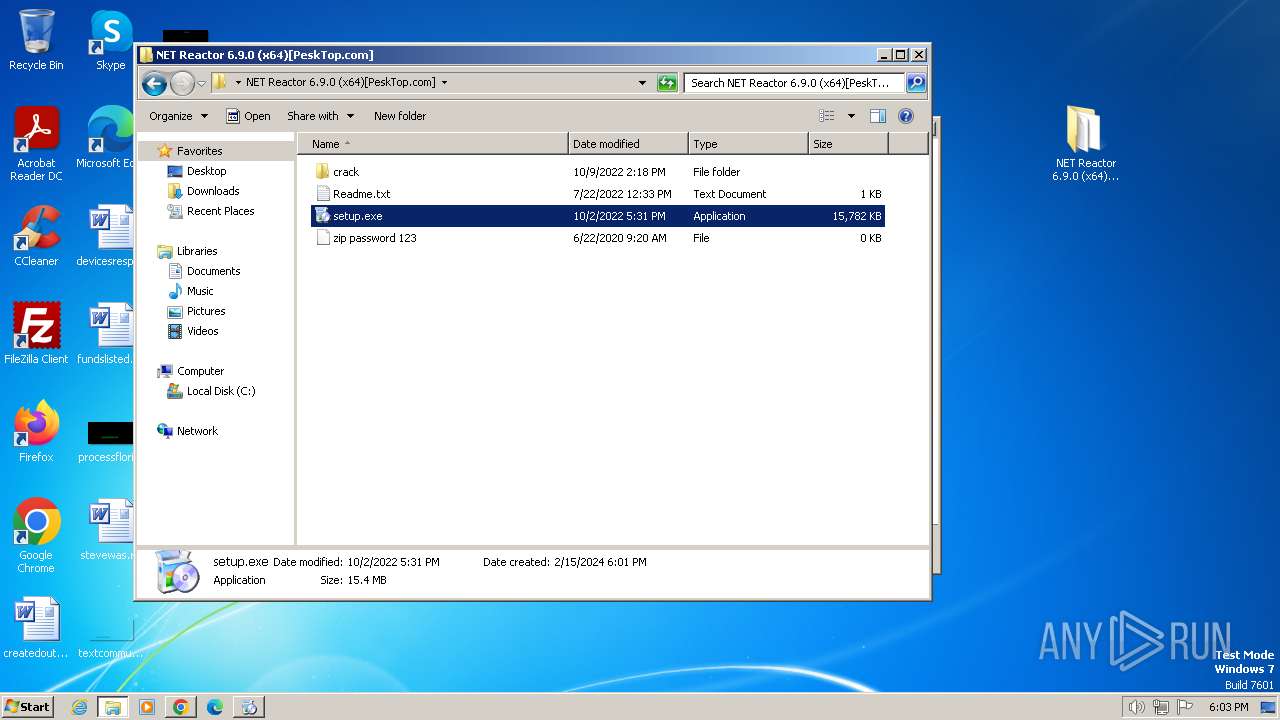
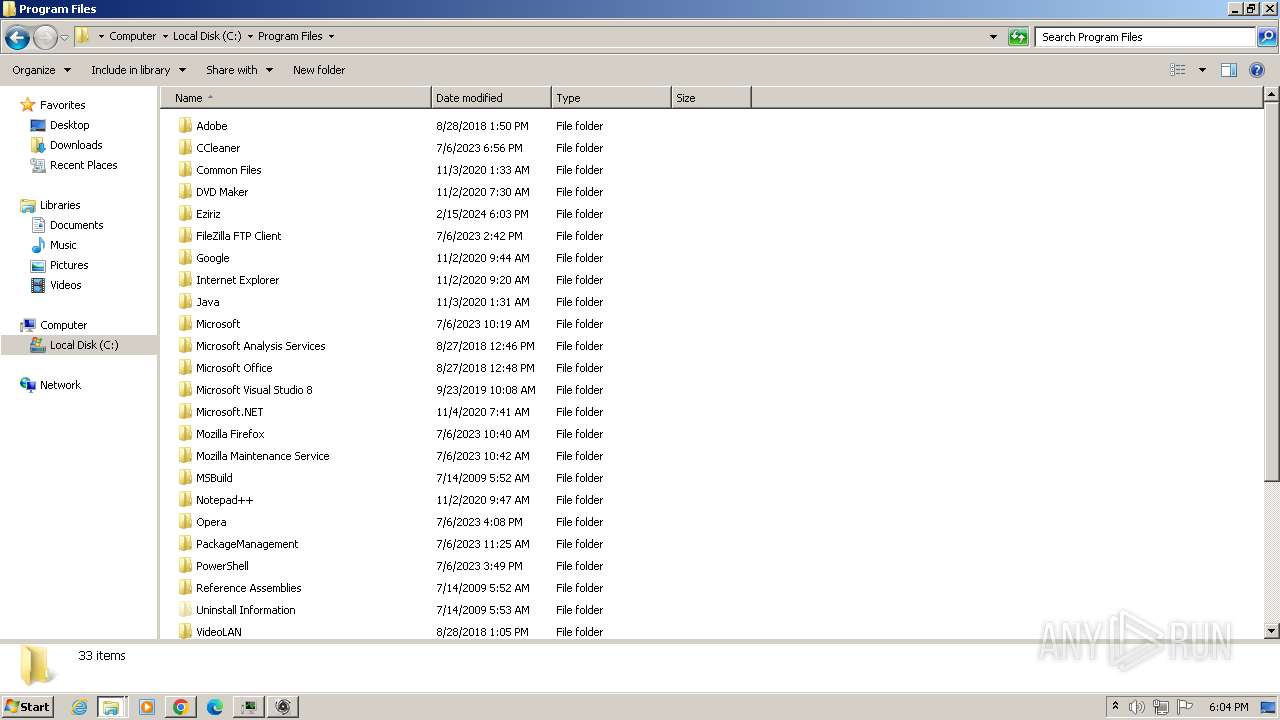
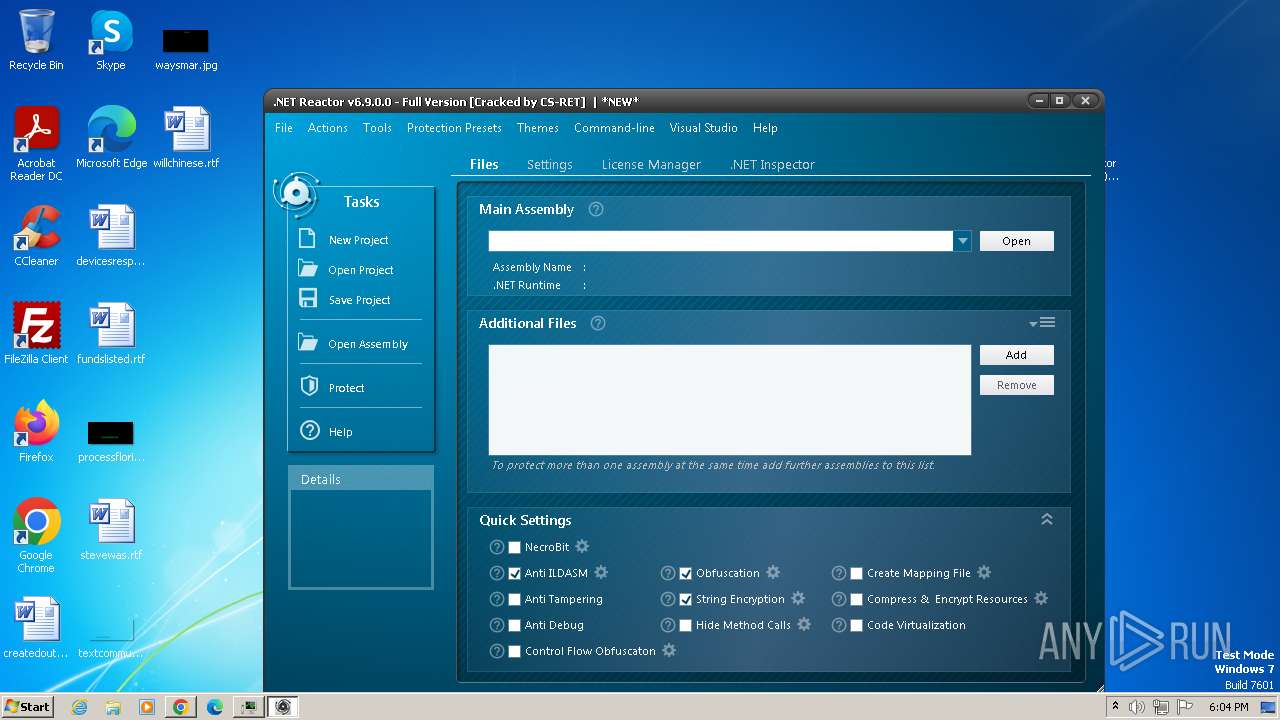
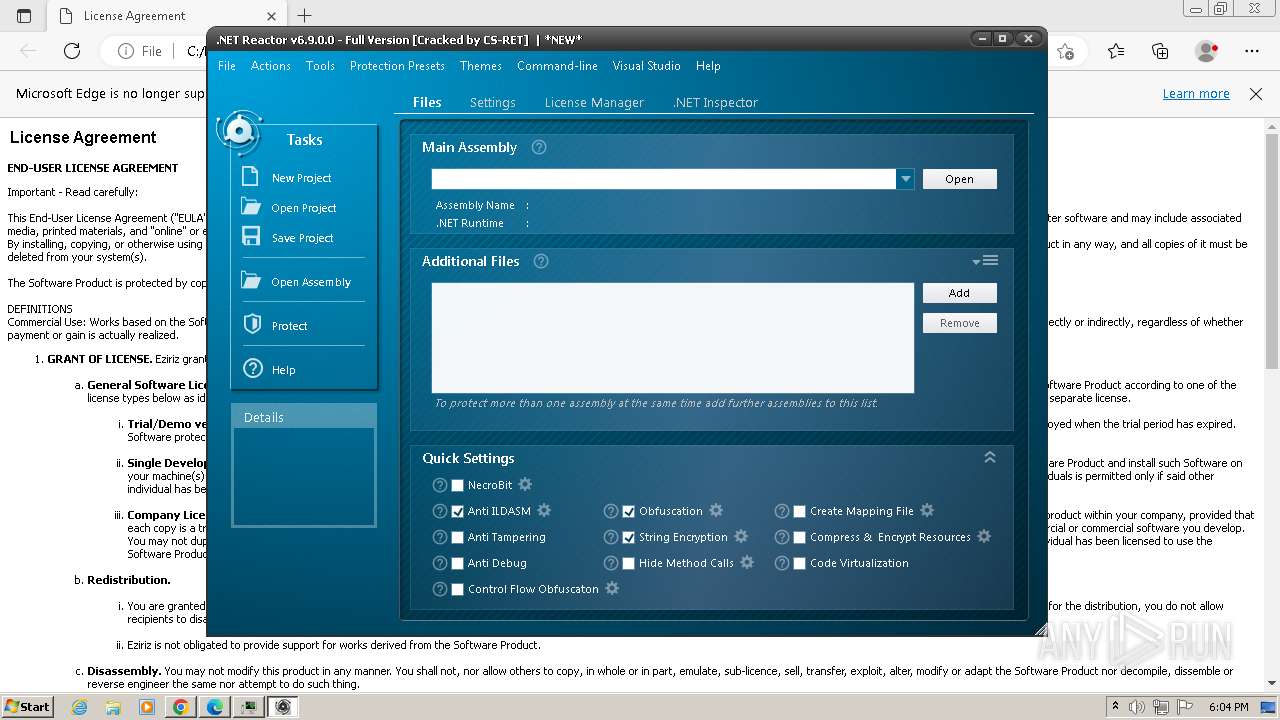
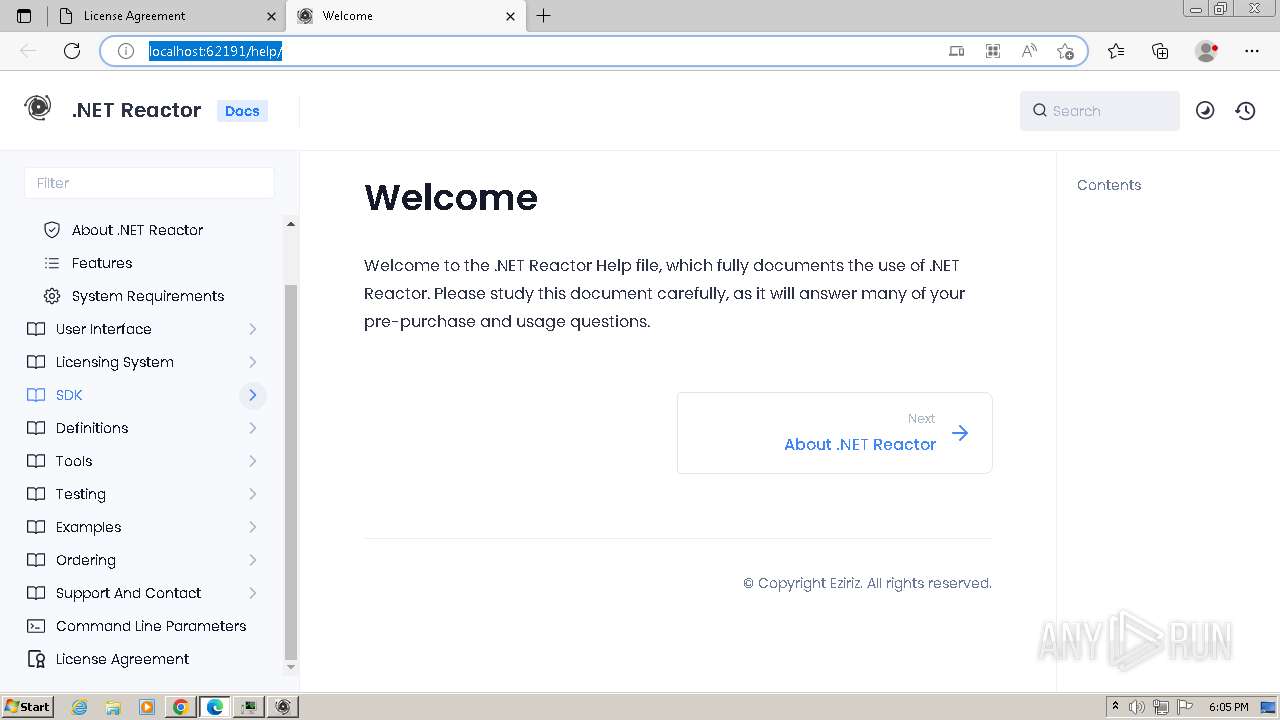
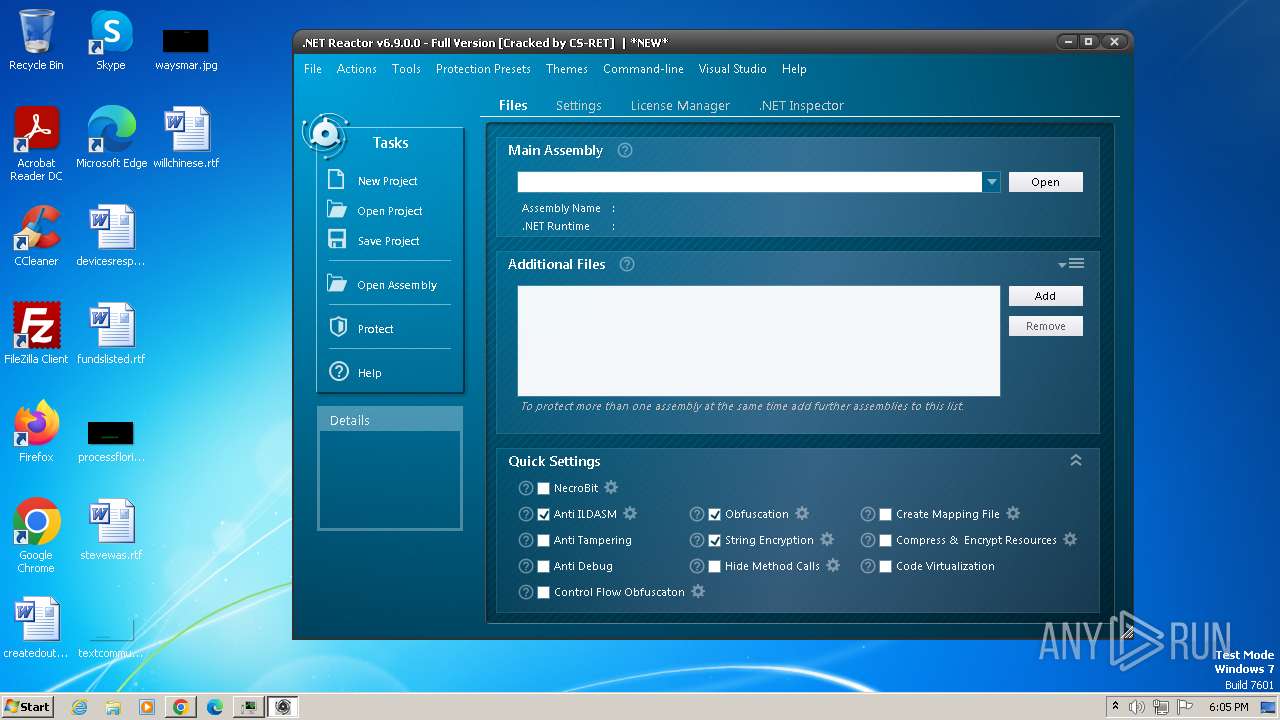
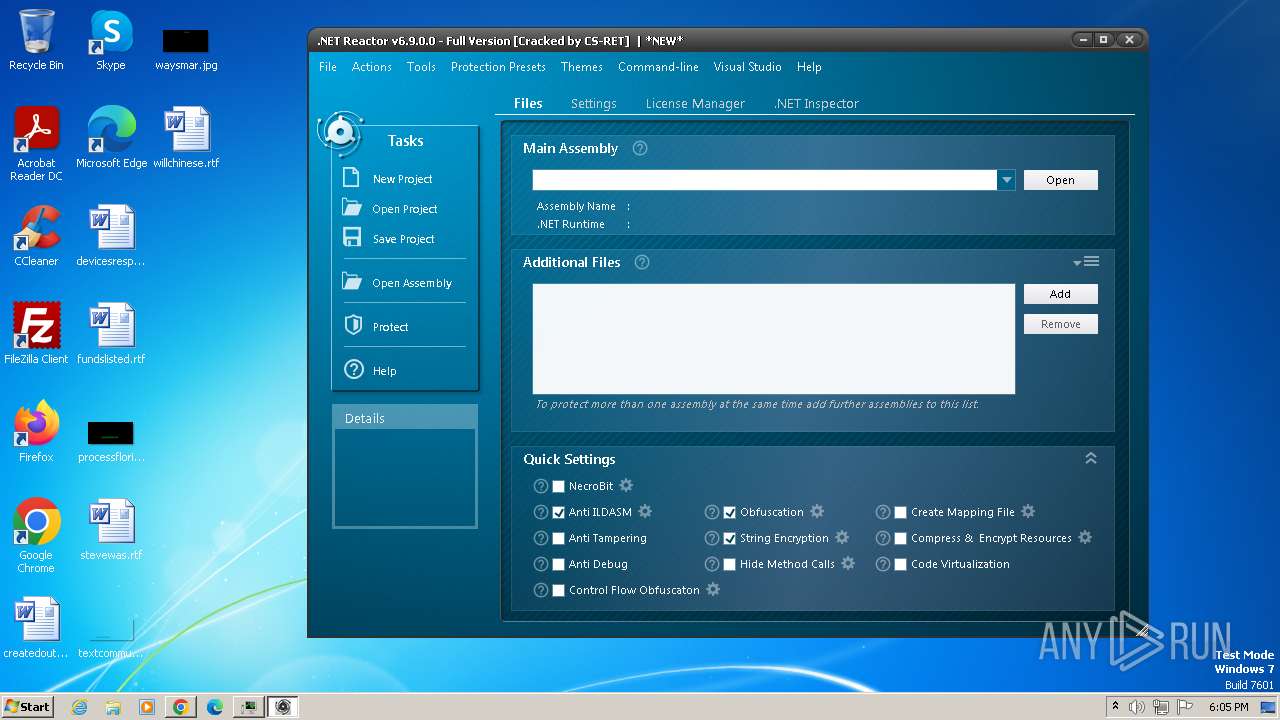
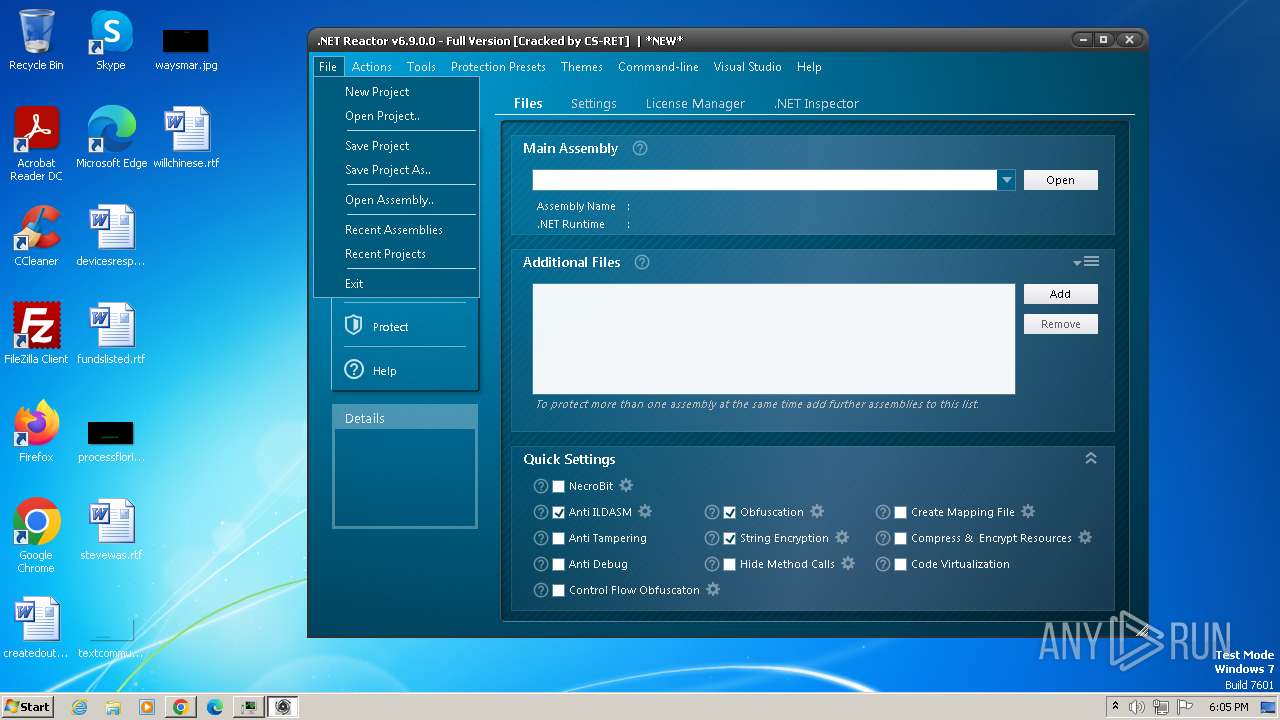
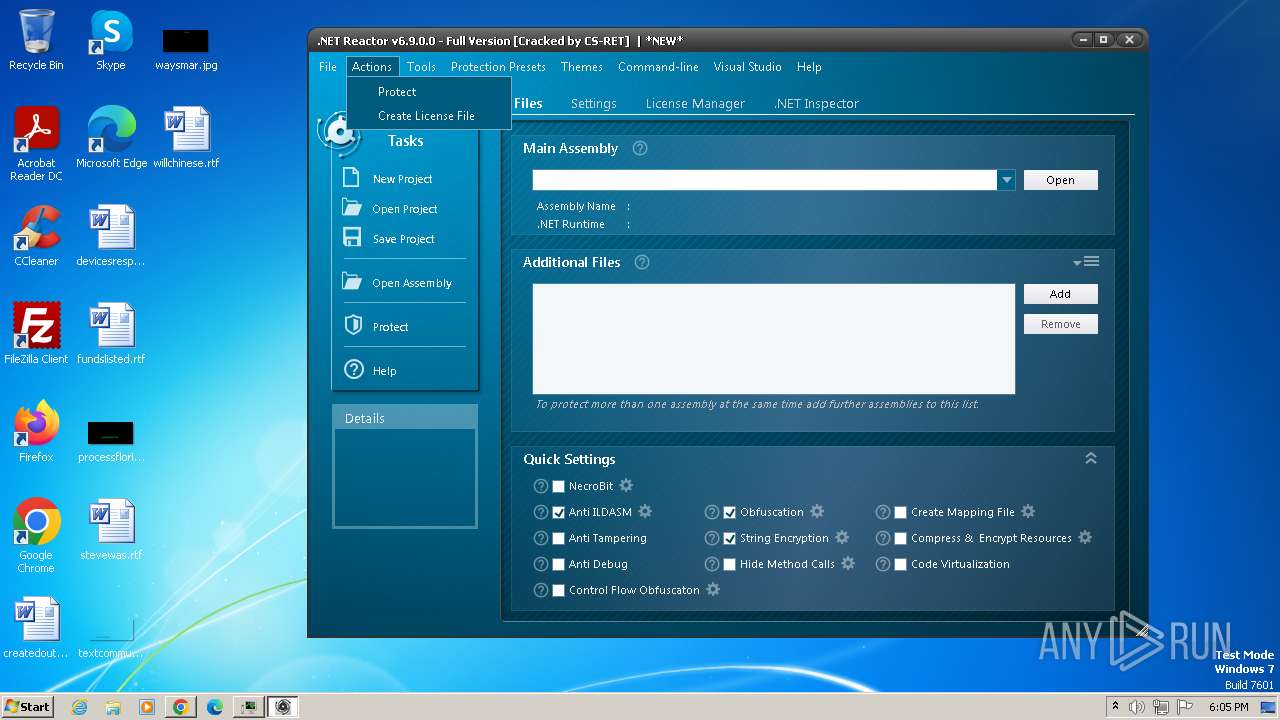
| URL: | https://pesktop.com/en/windows/net-reactor |
| Full analysis: | https://app.any.run/tasks/05d3c2e7-1a3f-421c-b1b3-54d520983b08 |
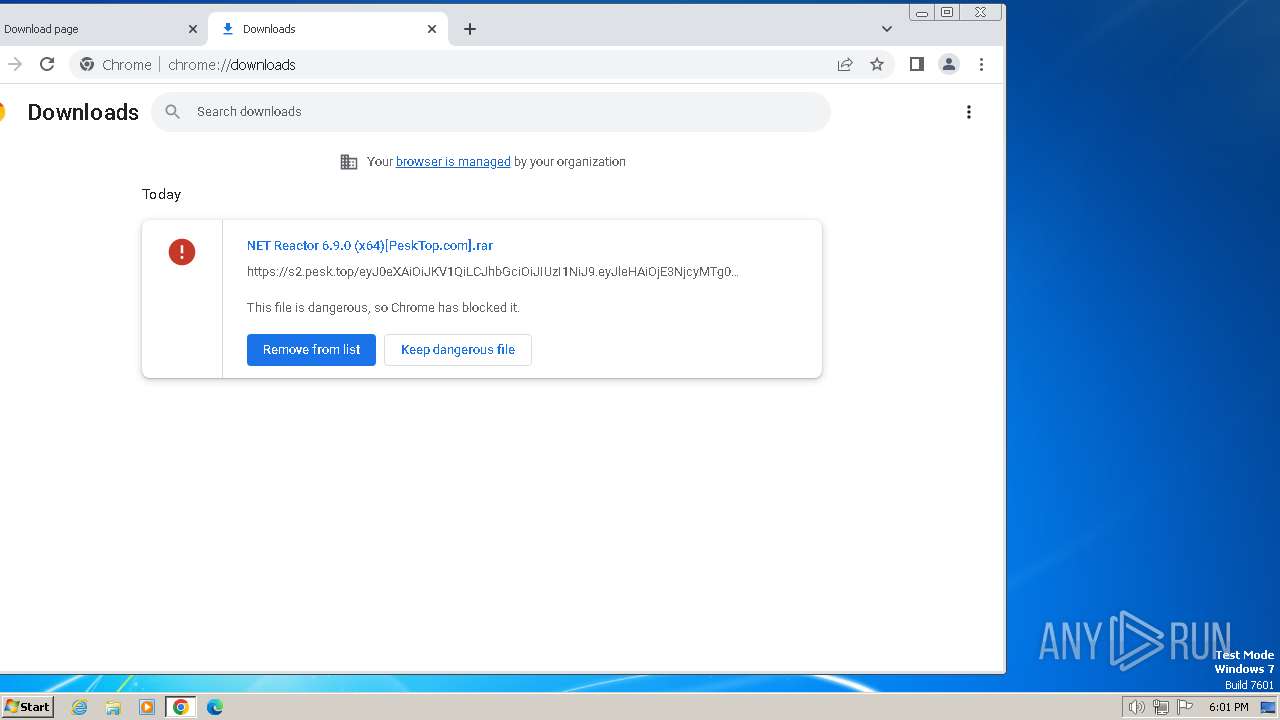
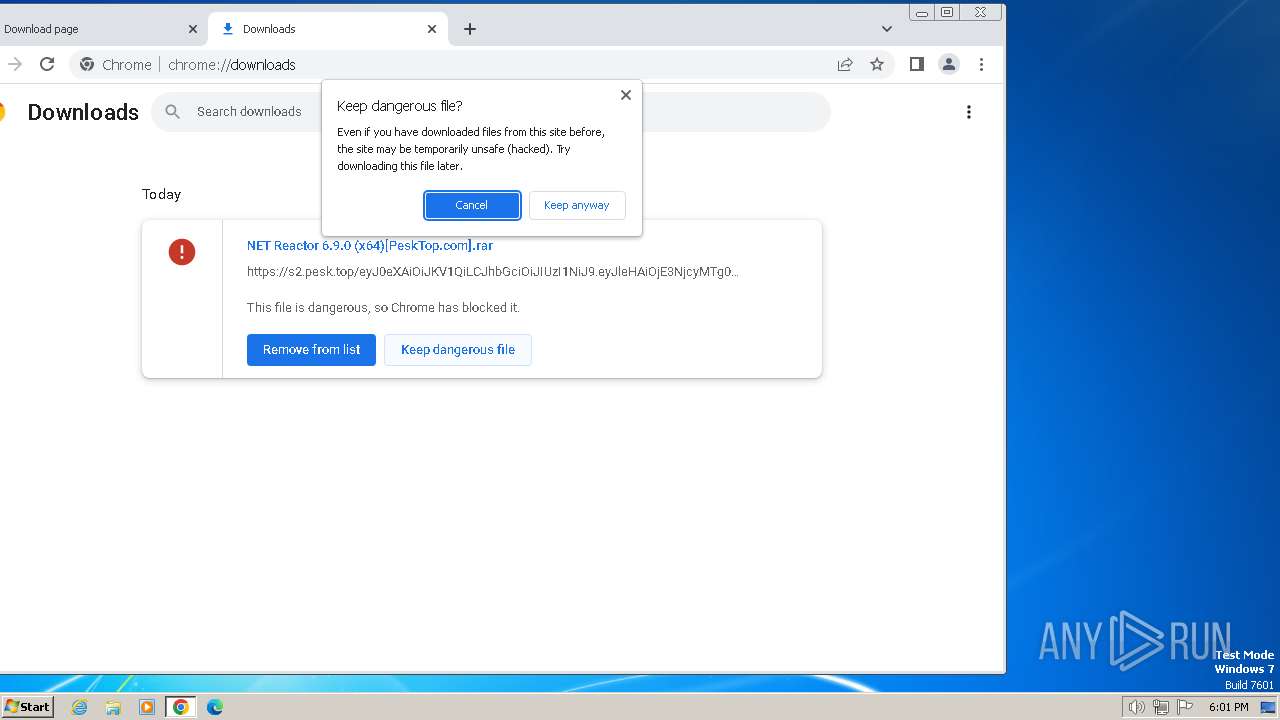
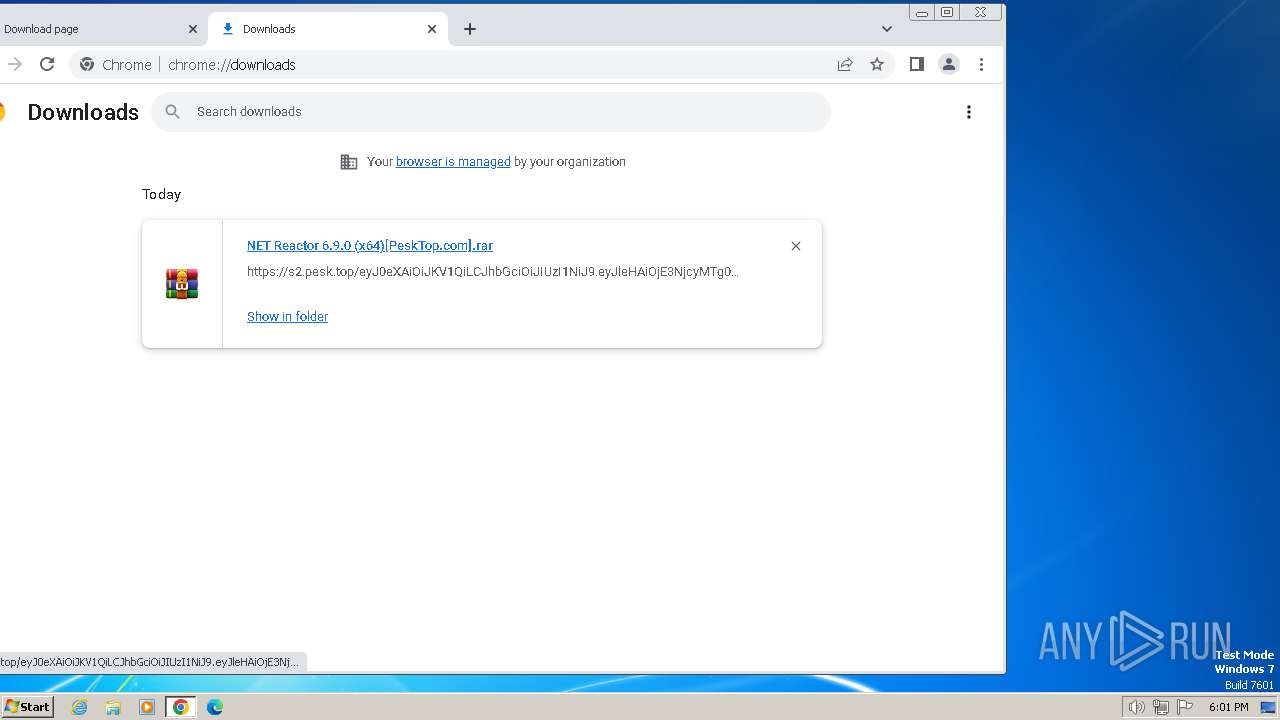
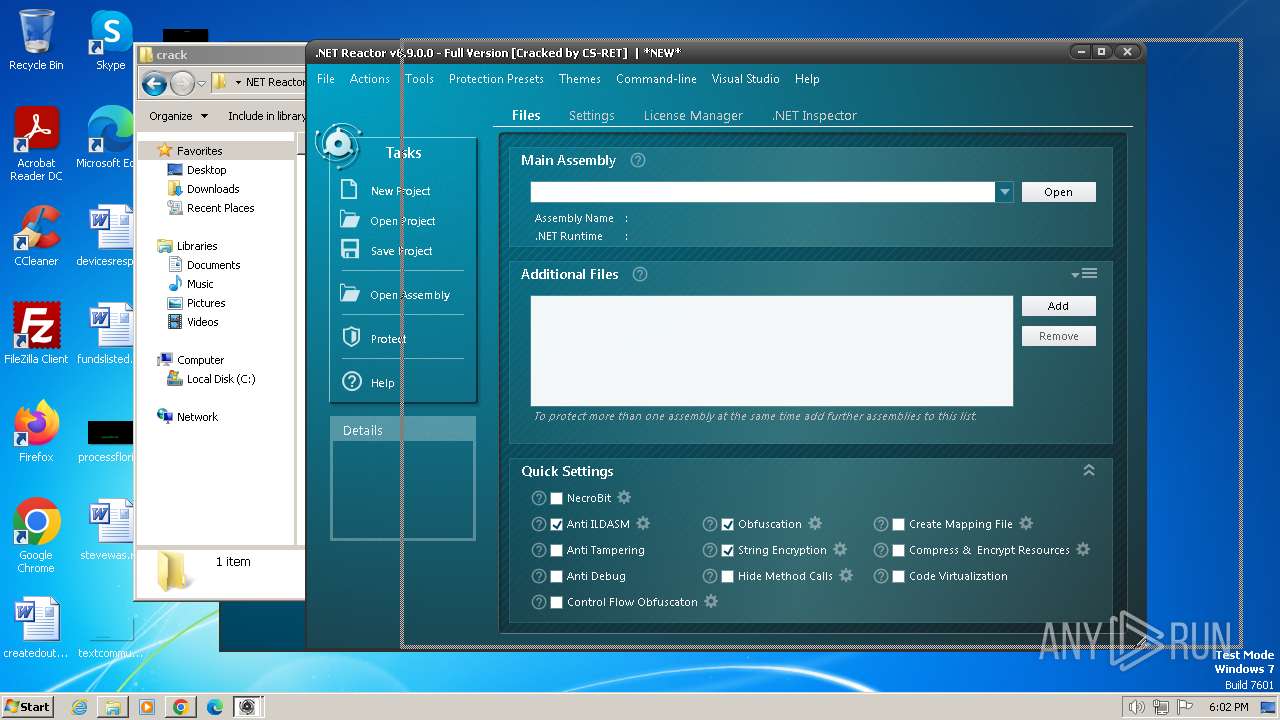
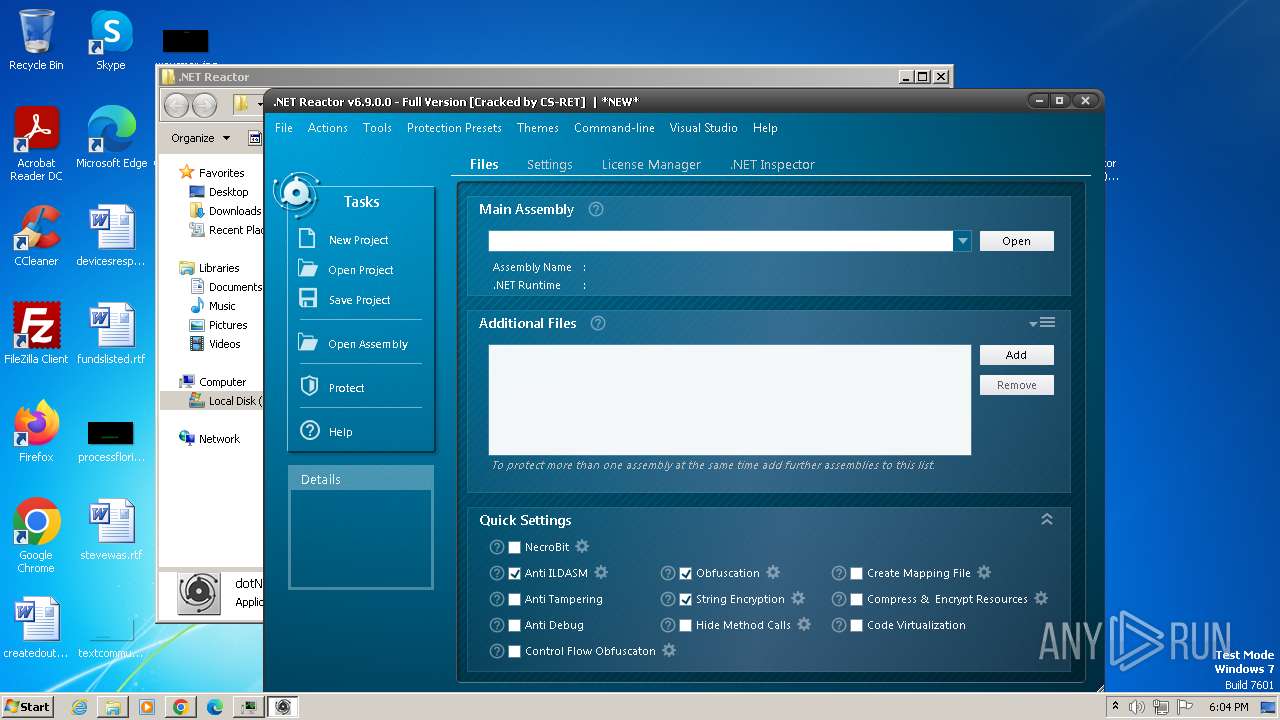
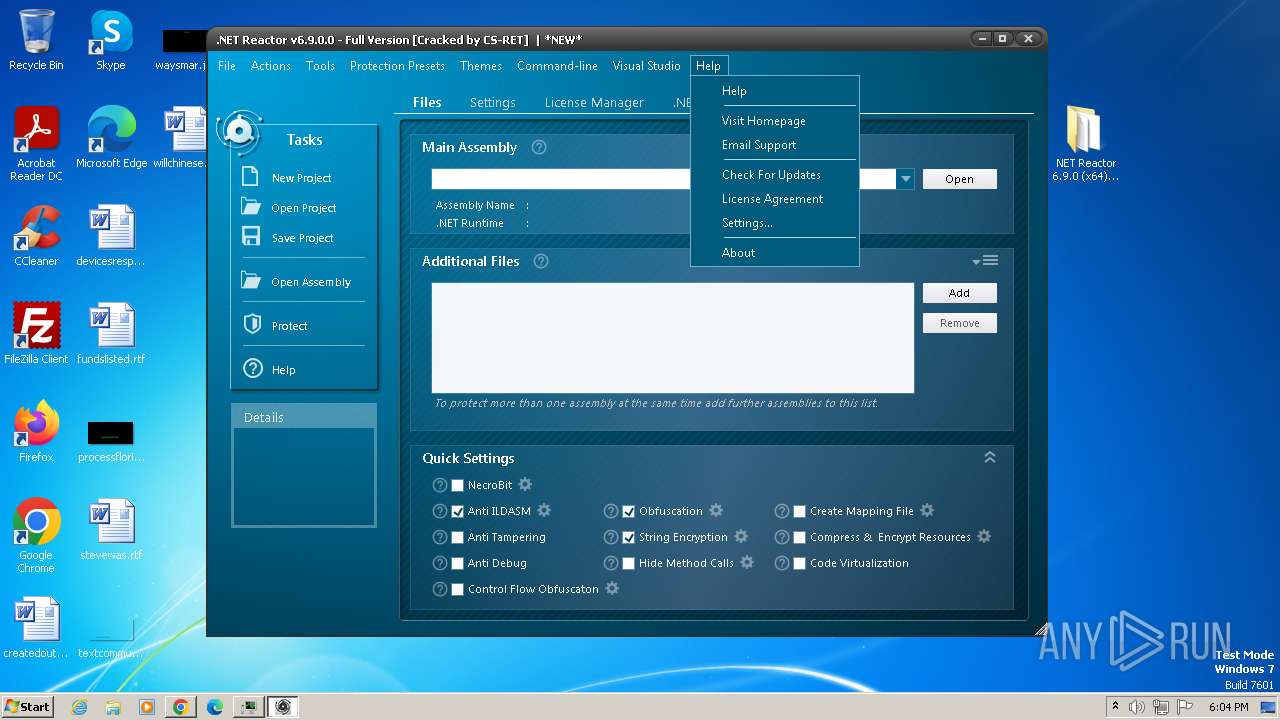
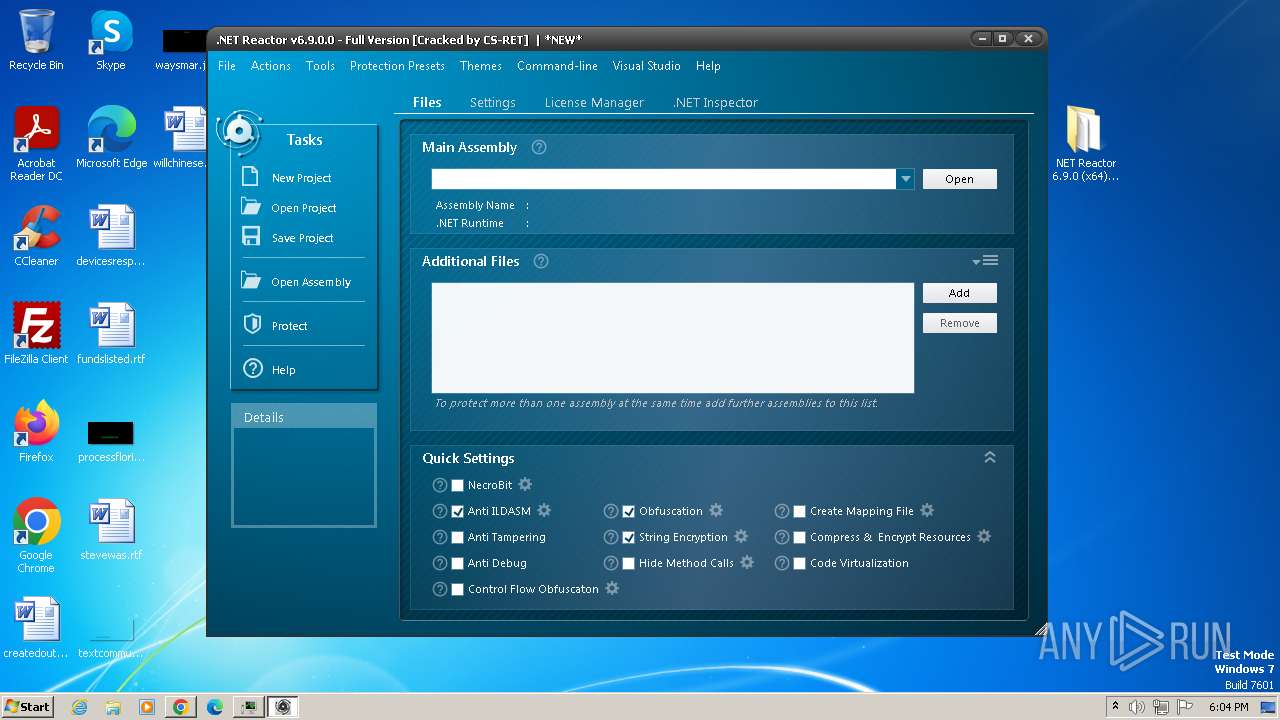
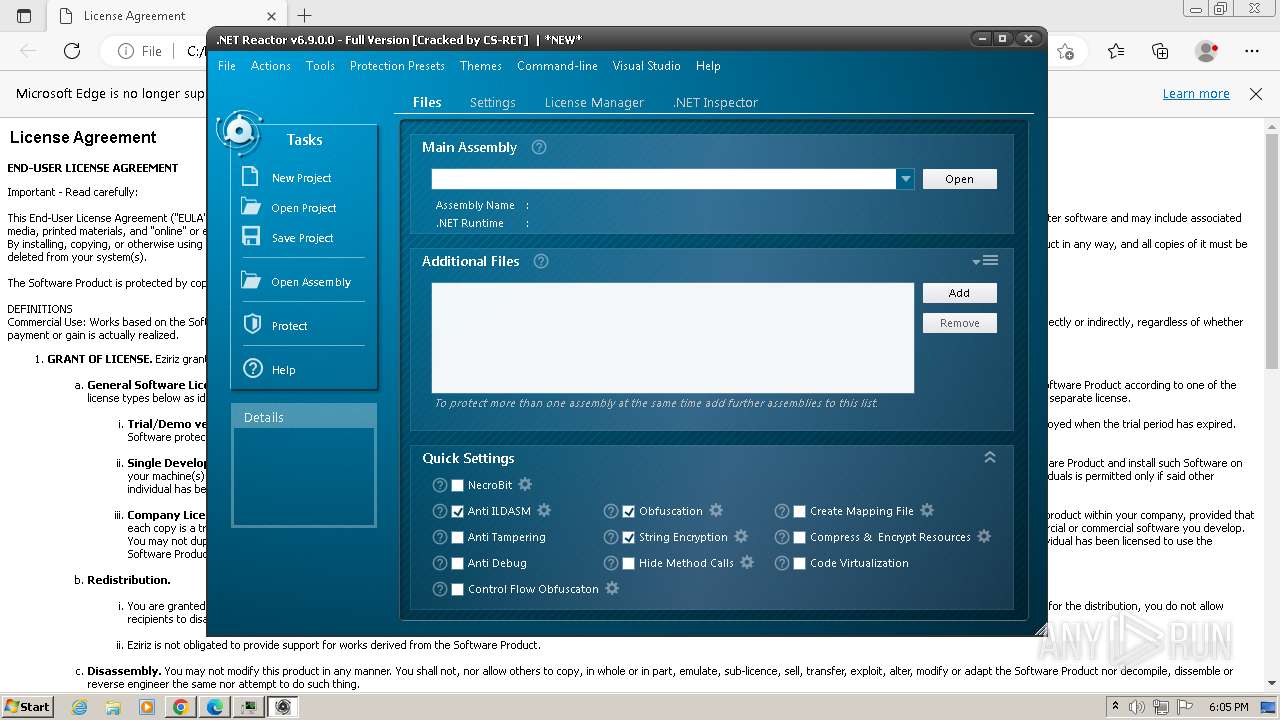
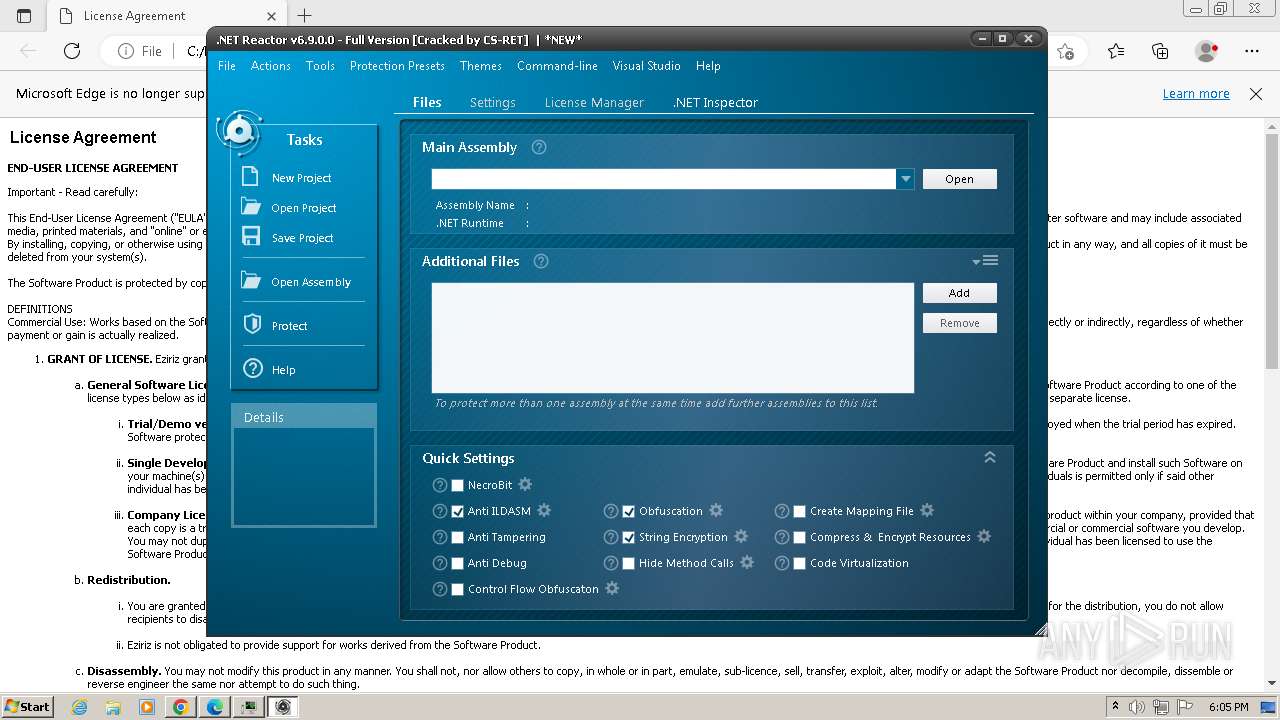
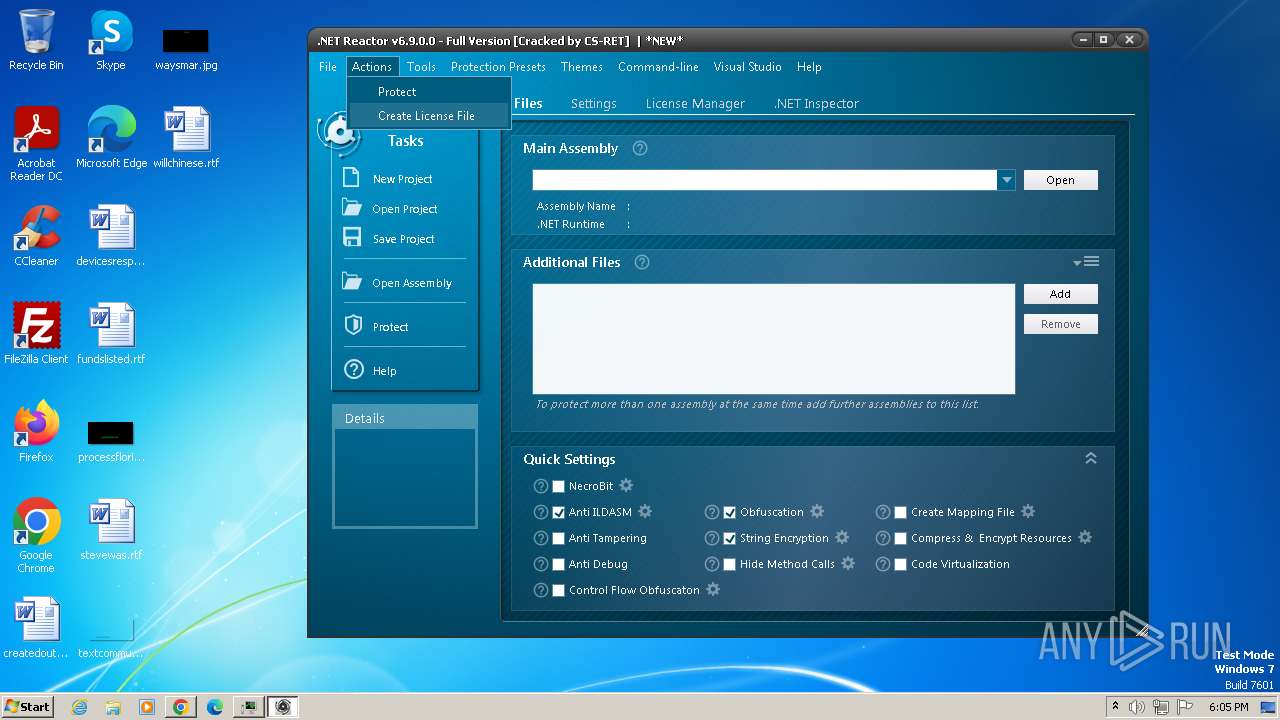
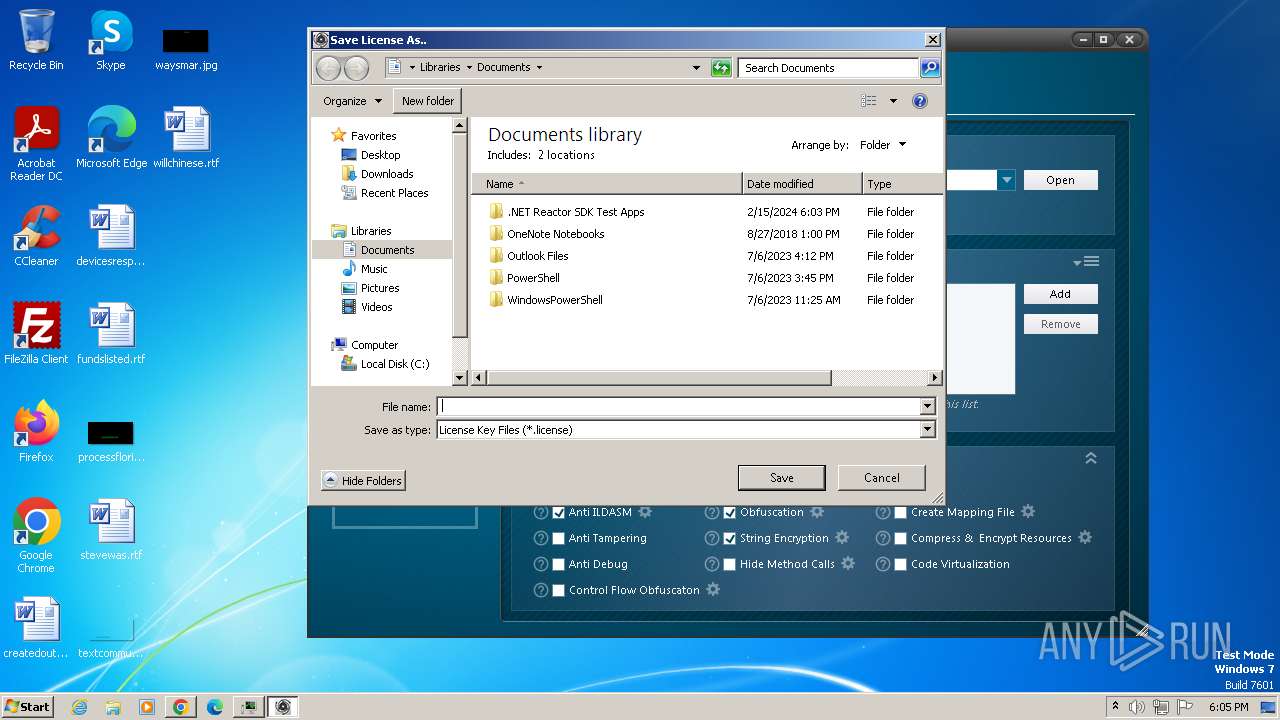
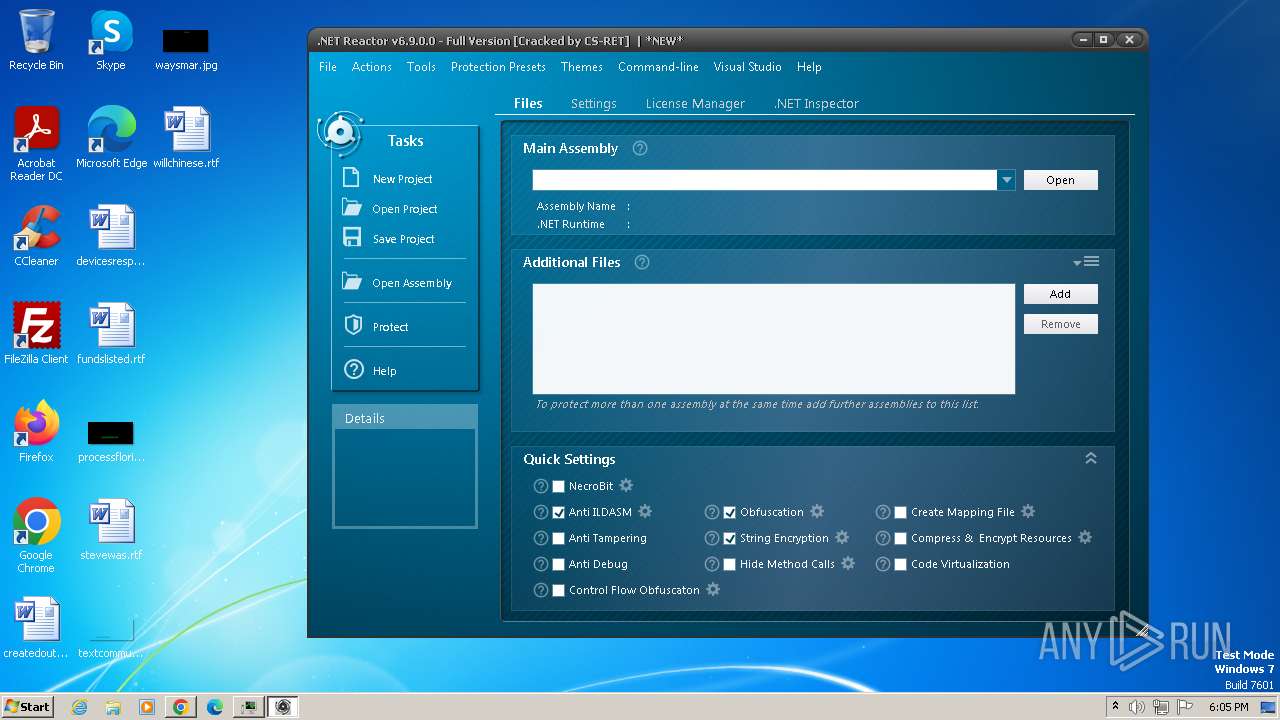
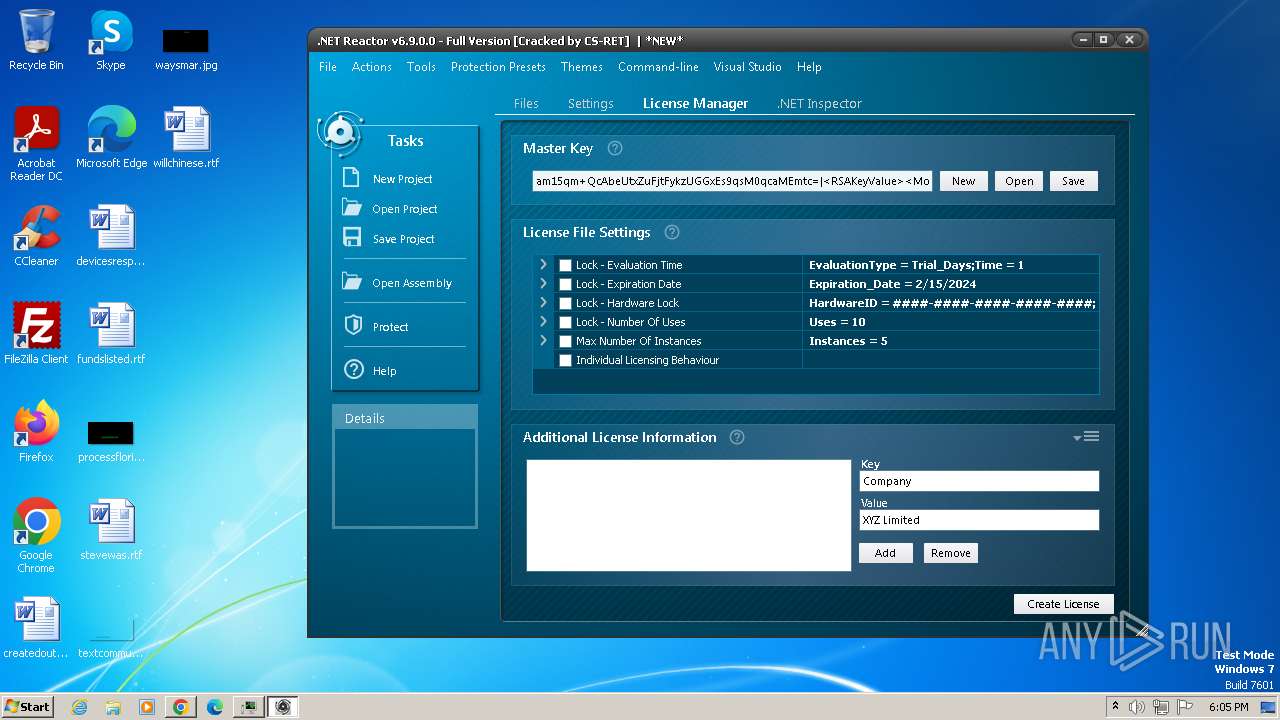
| Verdict: | Malicious activity |
| Analysis date: | February 15, 2024, 18:00:49 |
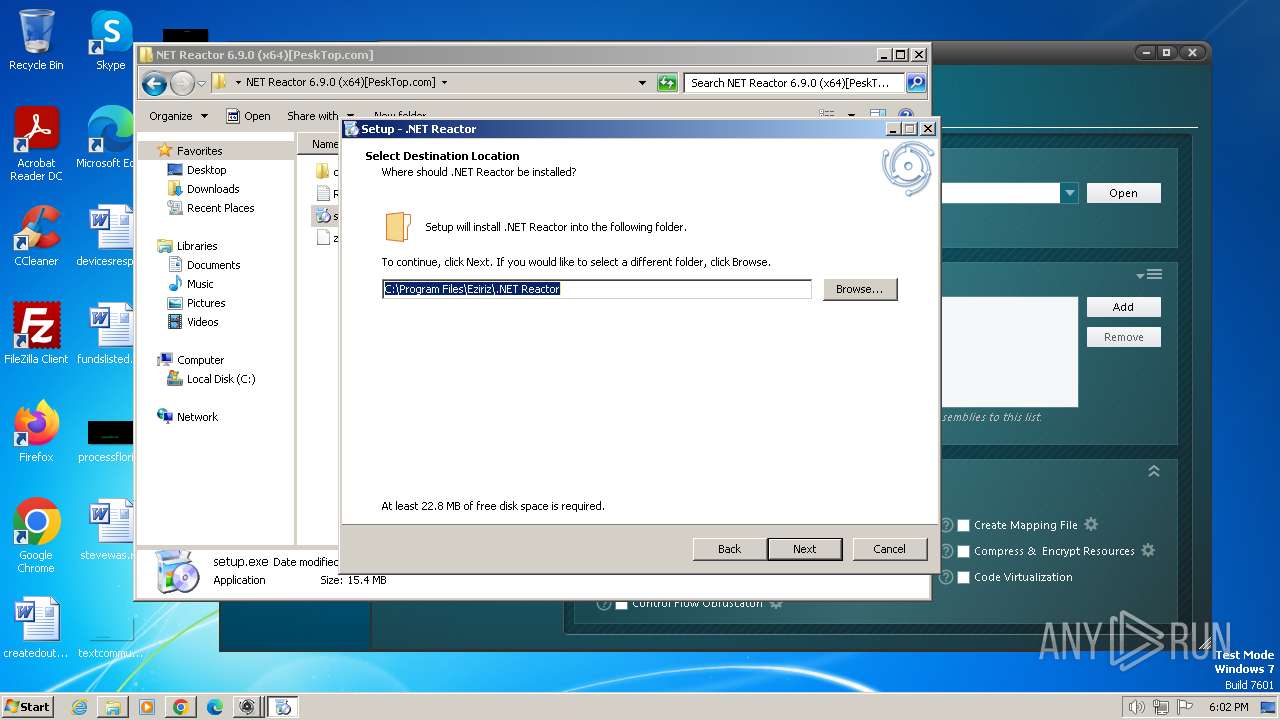
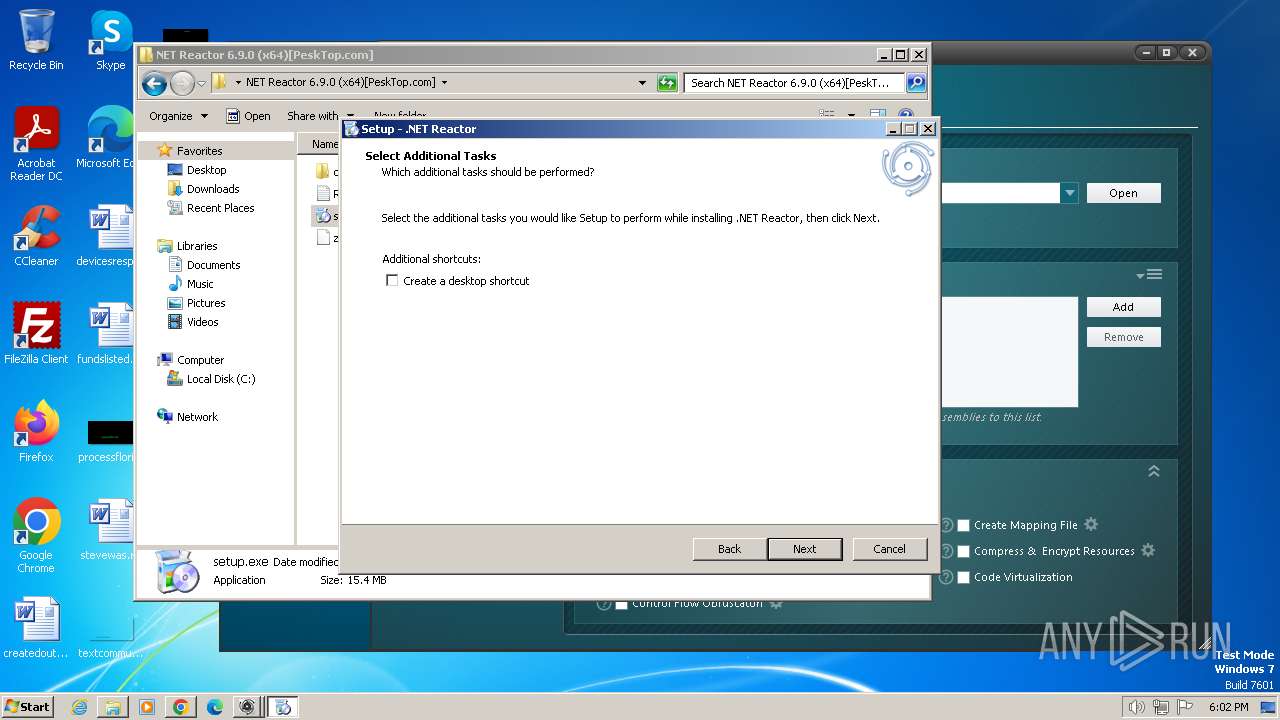
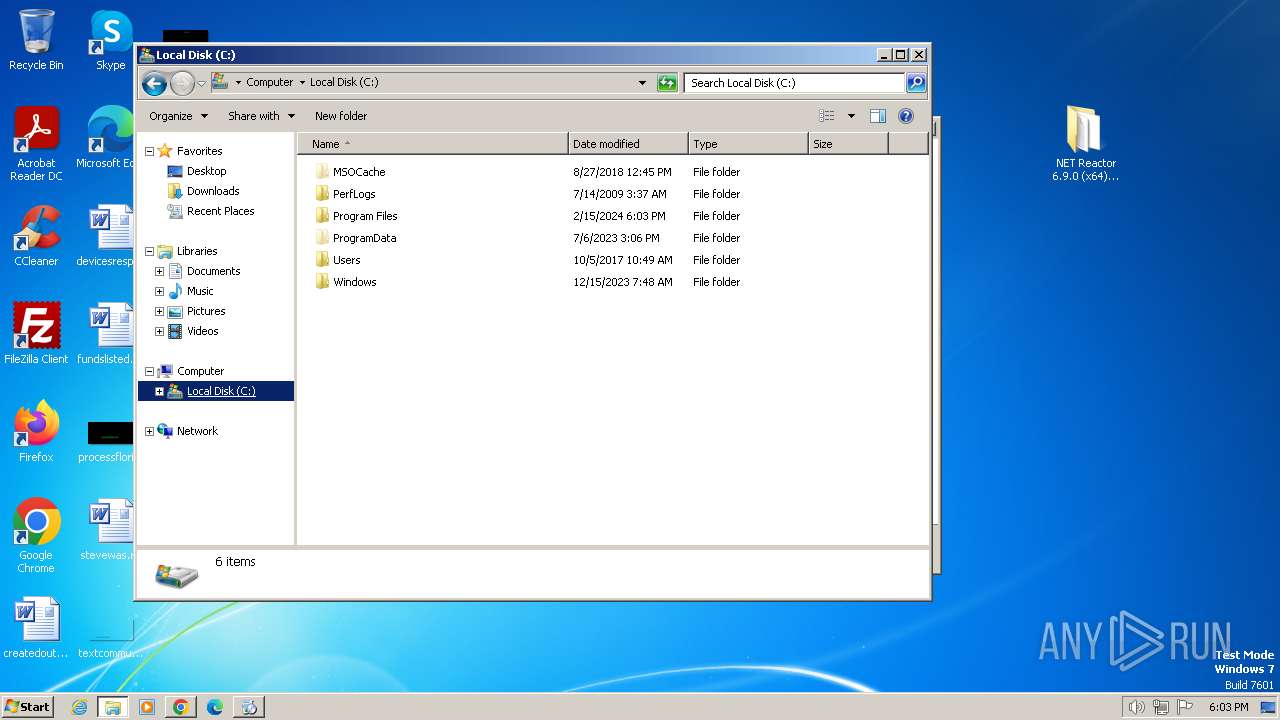
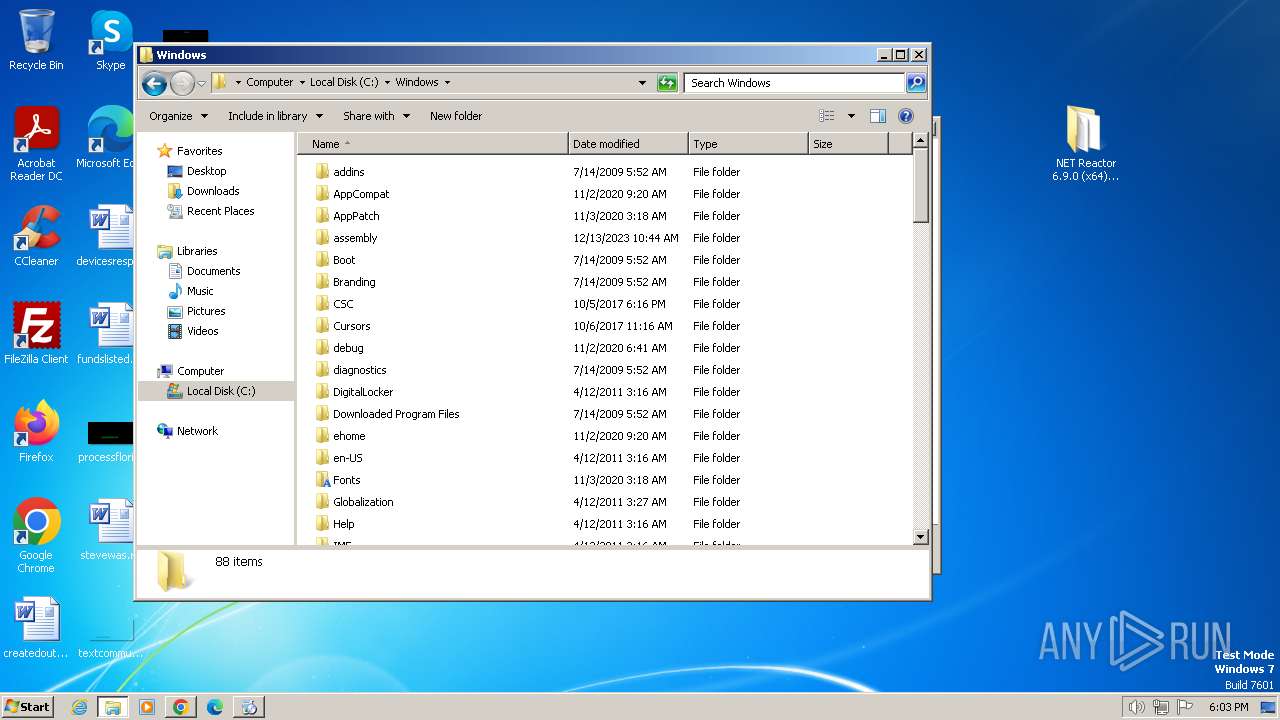
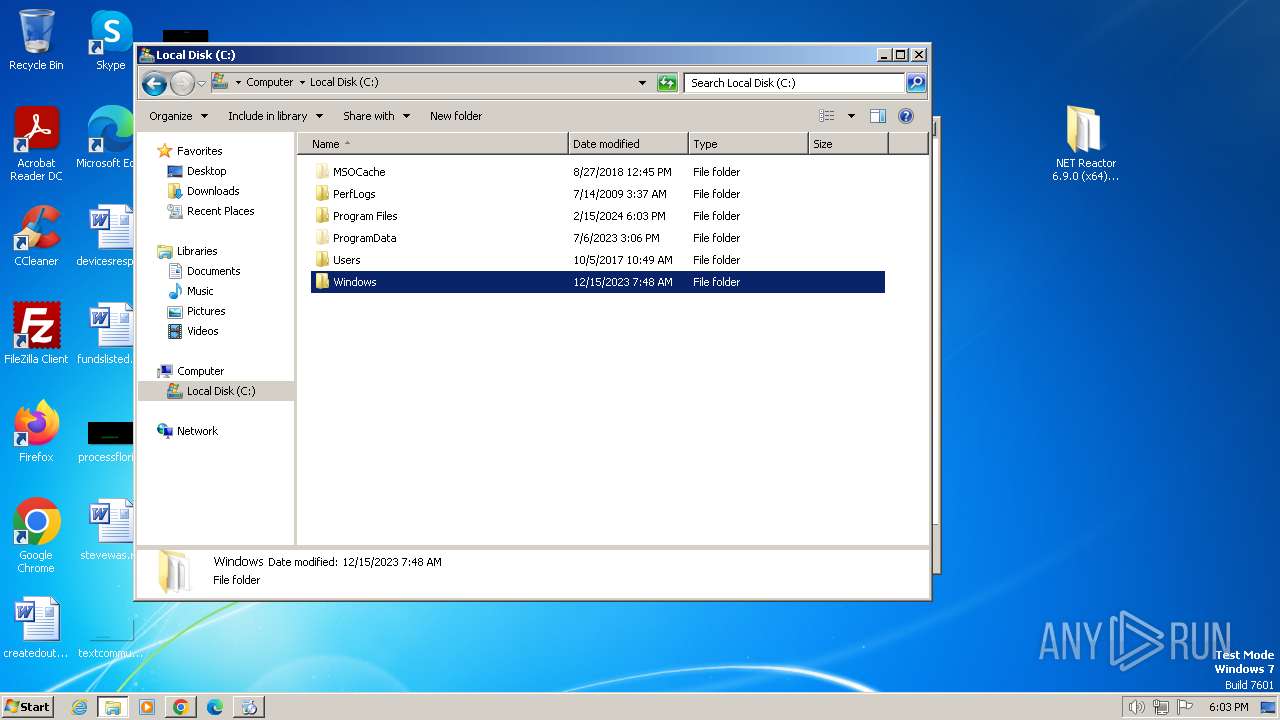
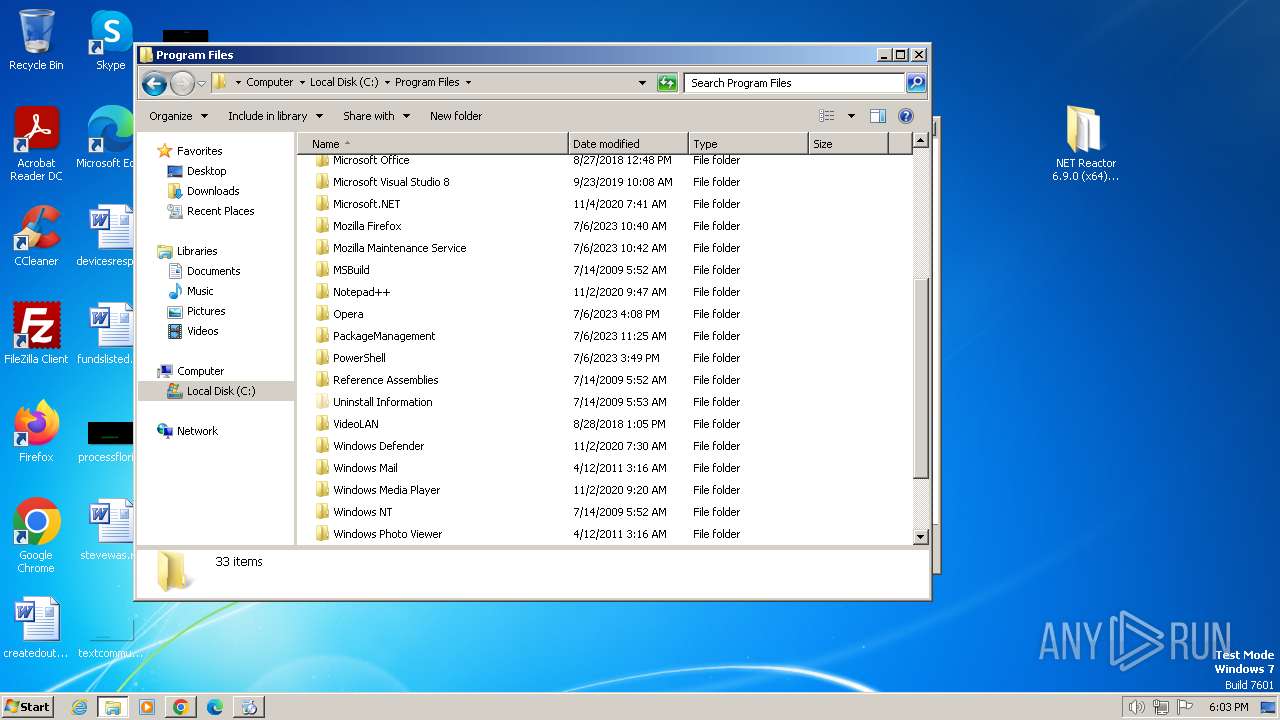
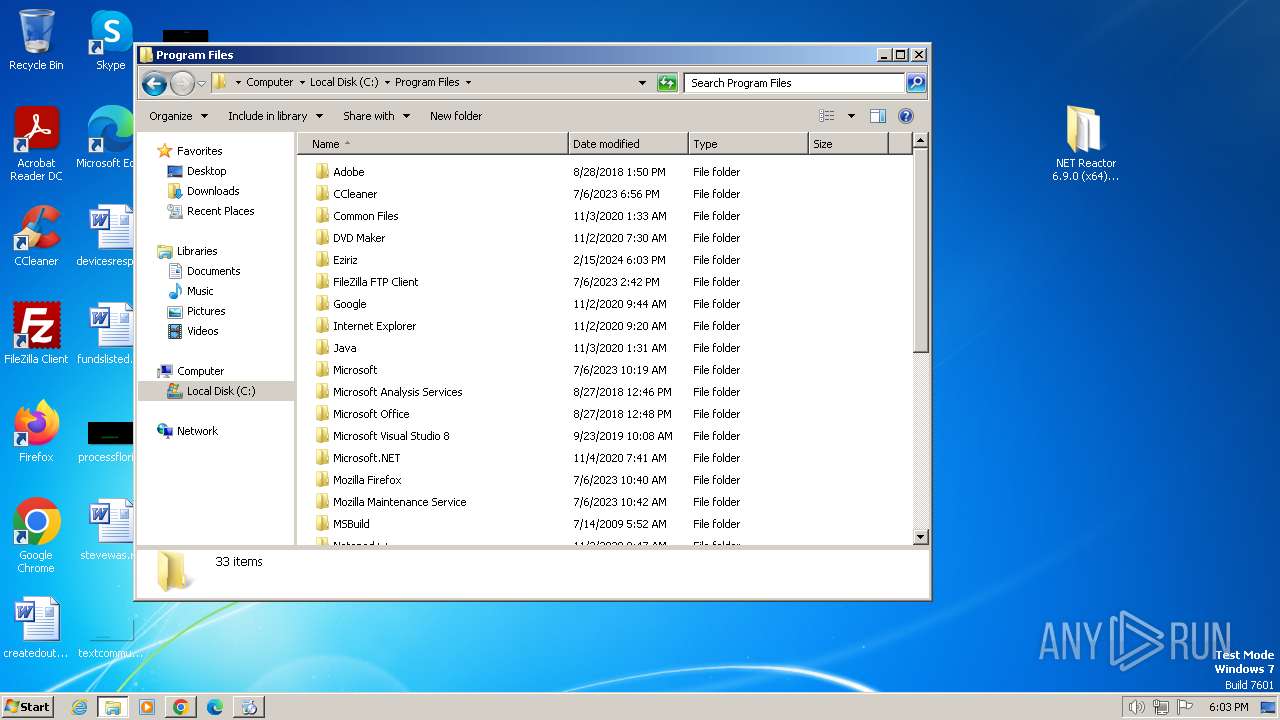
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7E3766947CA7D9CA47F173E87211E5C2 |
| SHA1: | CB41CF21DFDDA77C427B6BA9EB01096445F3E1AB |
| SHA256: | 4AF93DD959A190F8466E7E248935D31DCC50026701C1B89EF8D06D0495A9F6B4 |
| SSDEEP: | 3:N8EiVLKKFSML8eqRKX:2E2LKKF/L8fM |
MALICIOUS
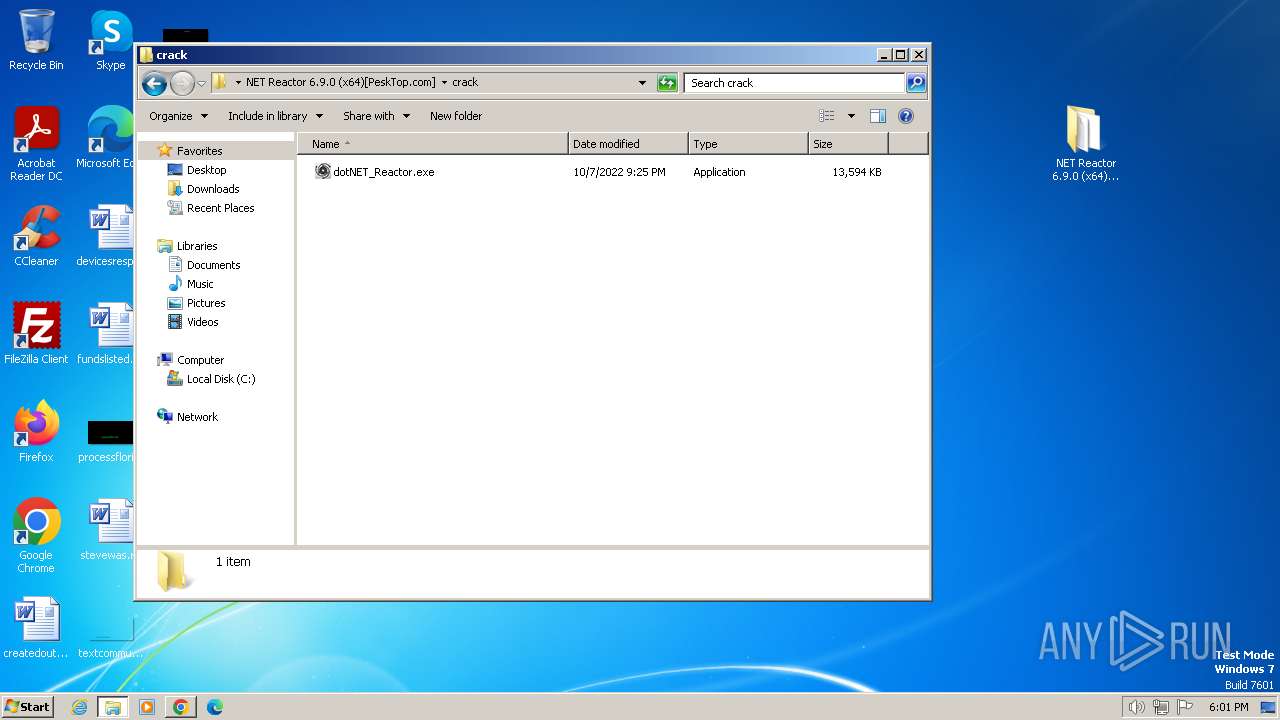
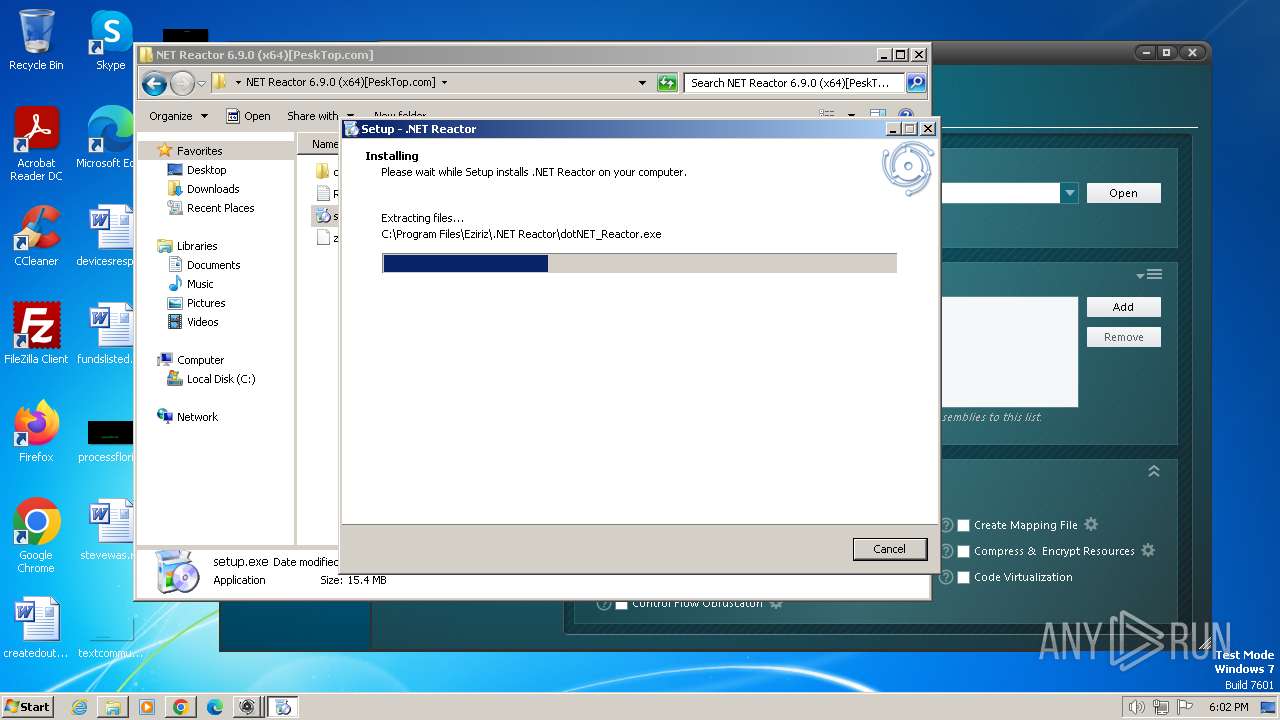
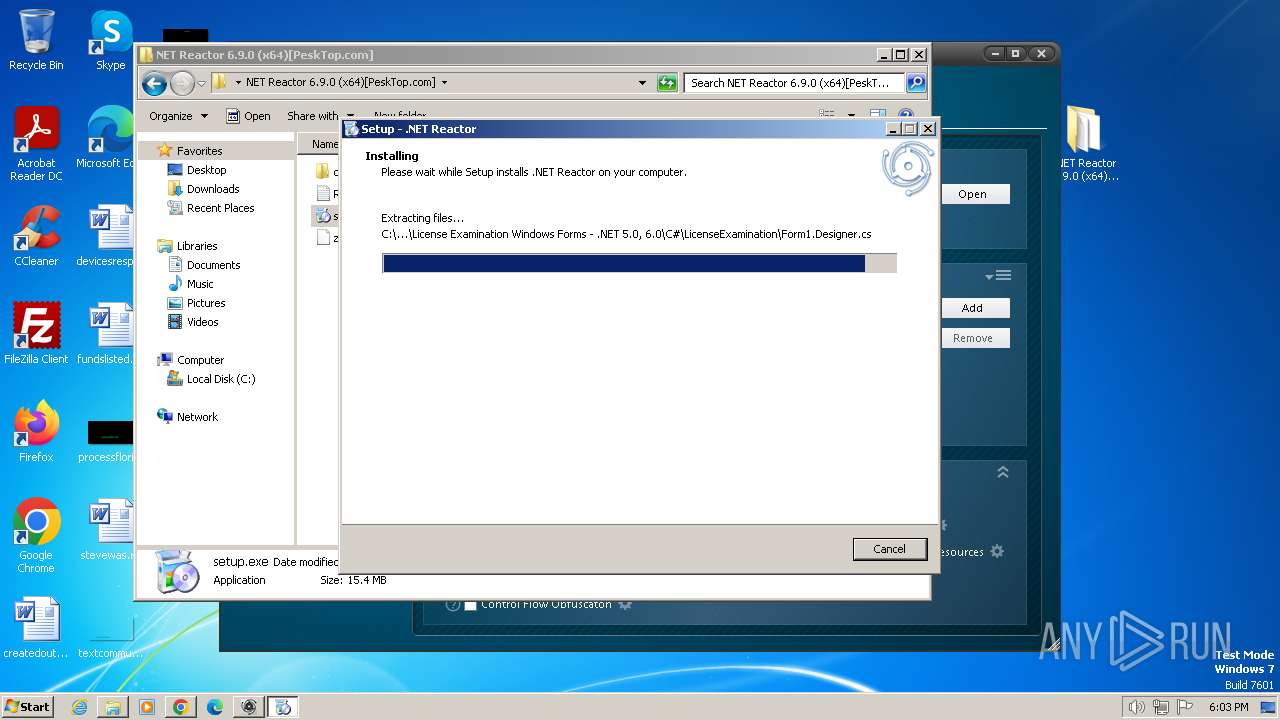
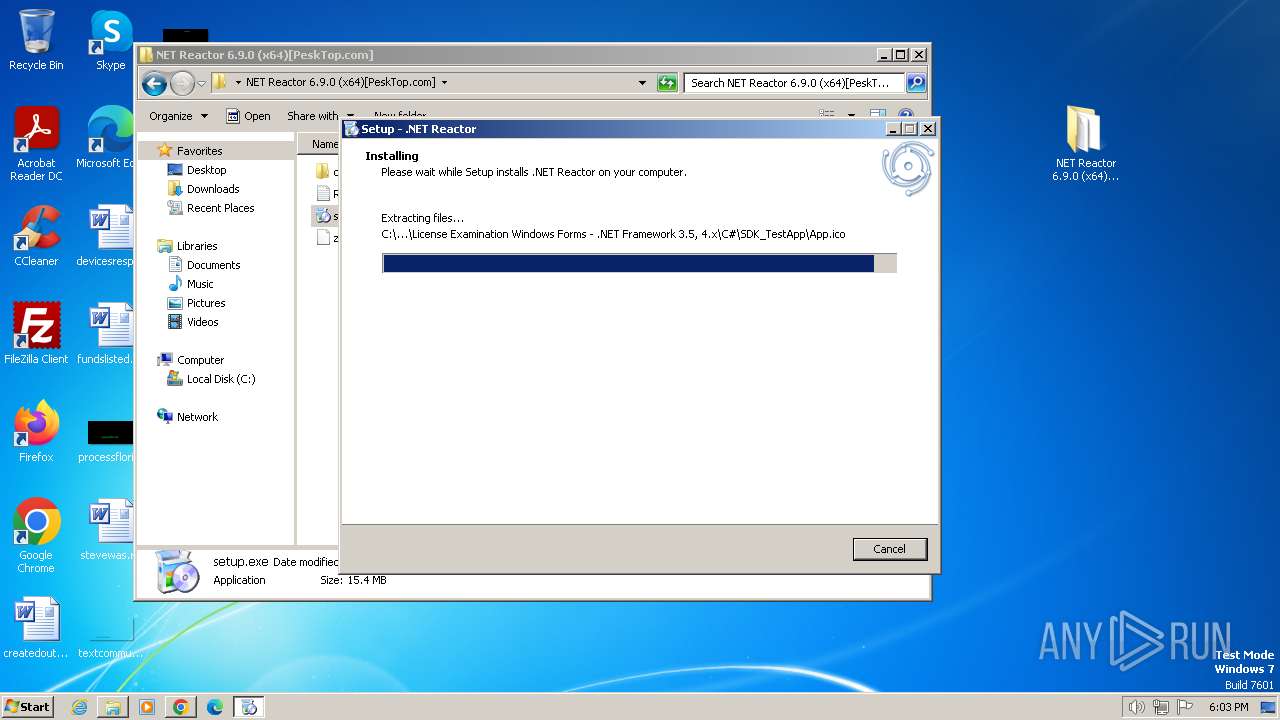
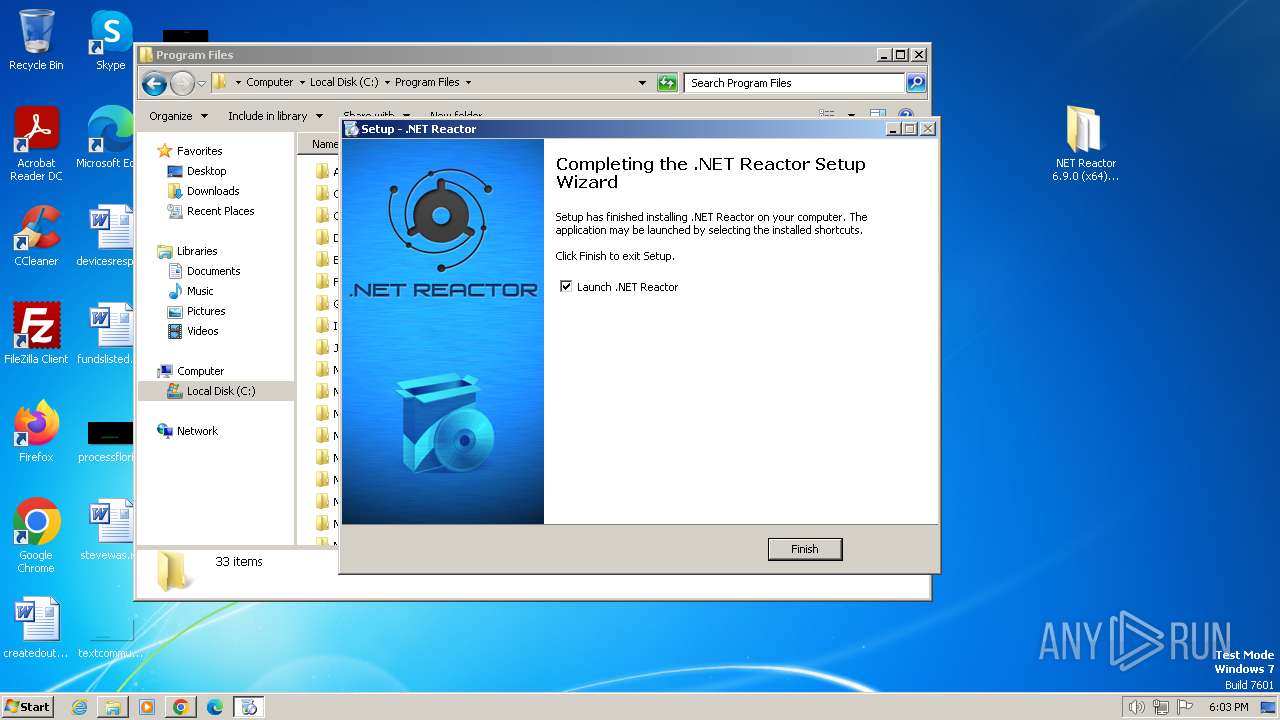
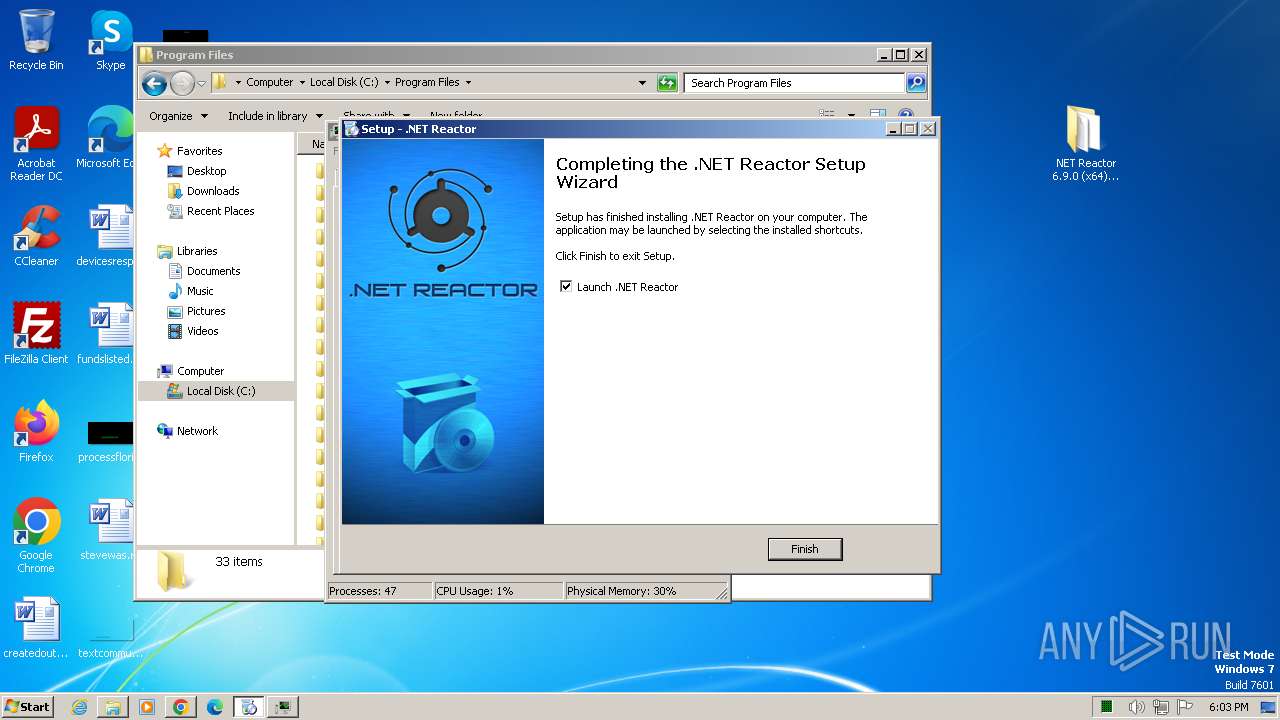
Drops the executable file immediately after the start
- setup.exe (PID: 992)
- setup.exe (PID: 664)
- setup.tmp (PID: 1392)
- REACTOR_HELP.exe (PID: 452)
SUSPICIOUS
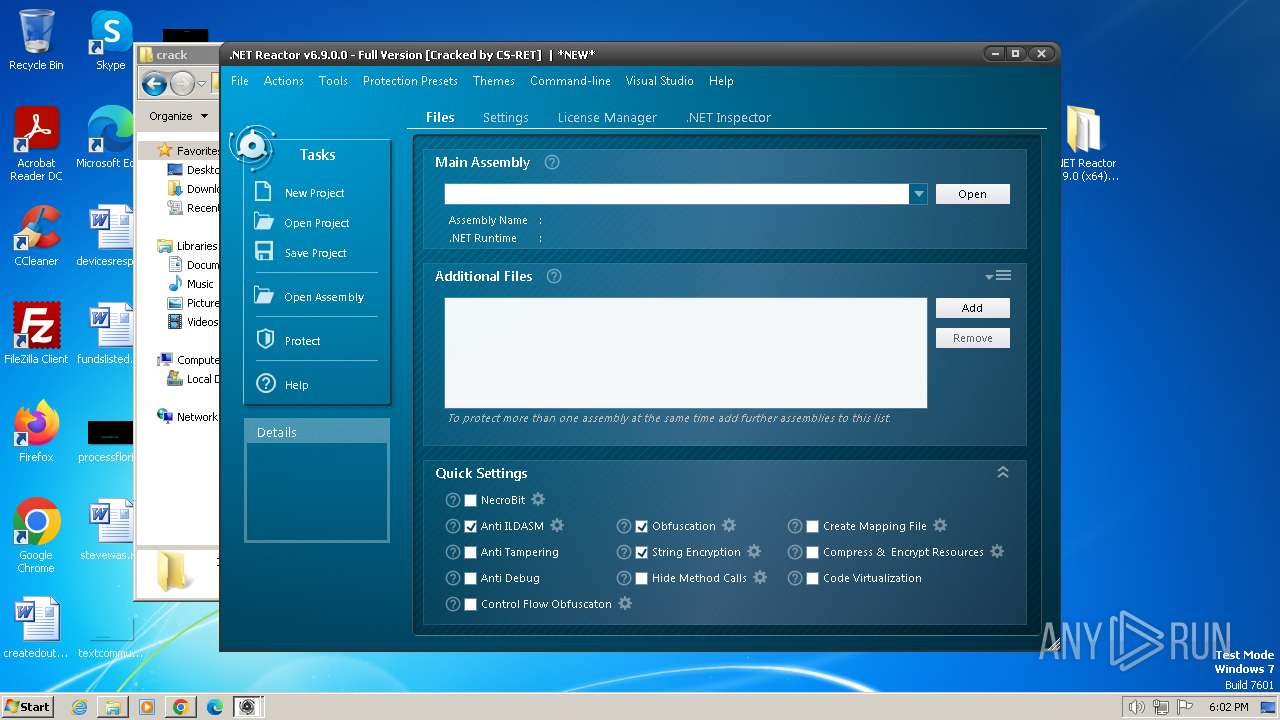
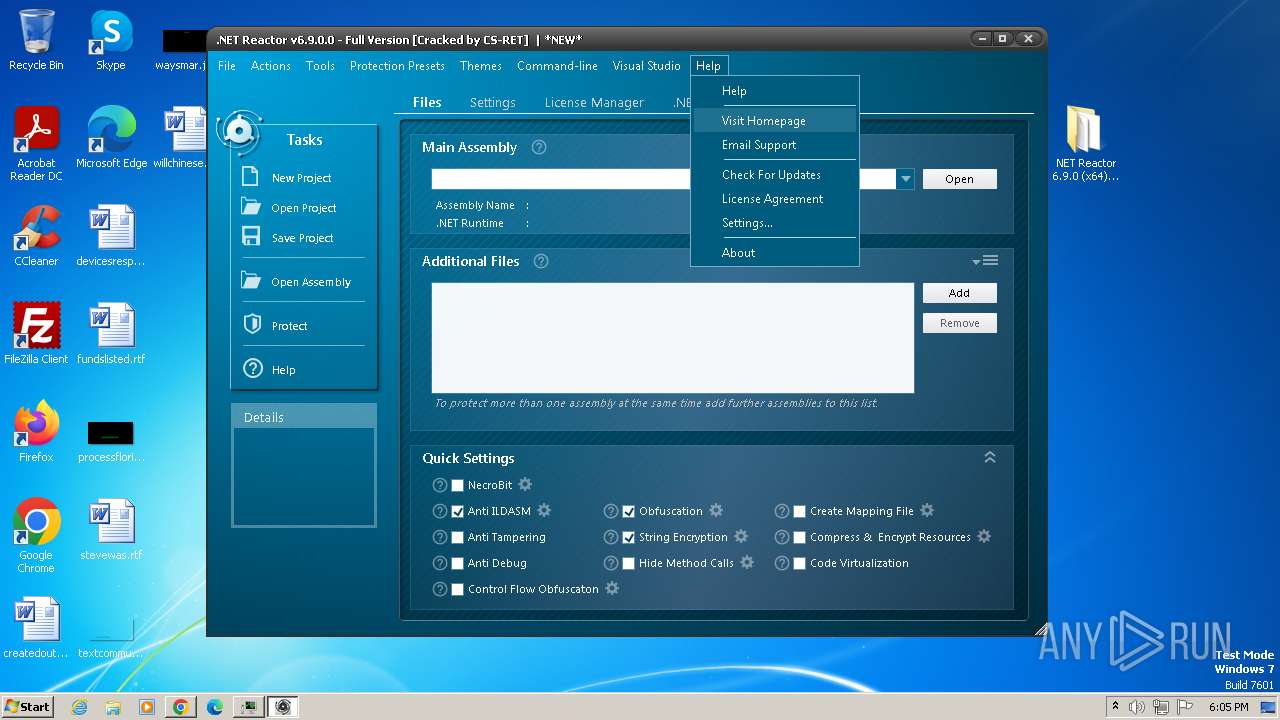
Reads the Internet Settings
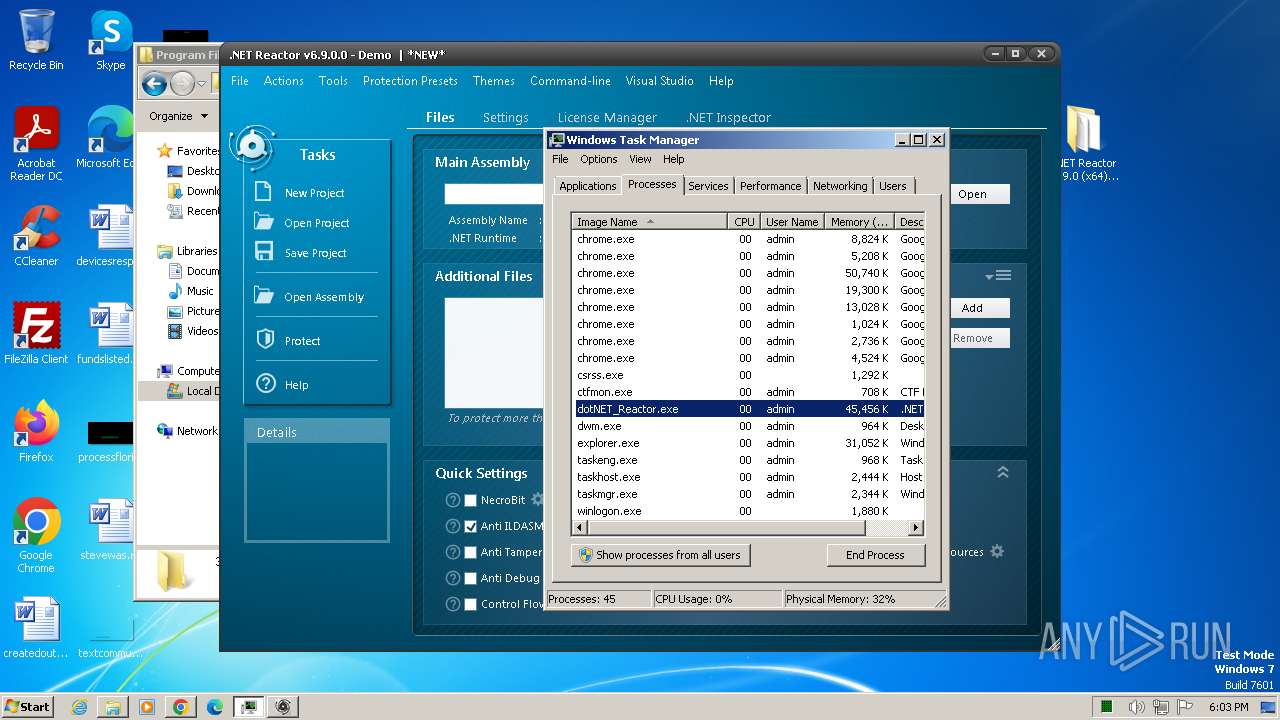
- dotNET_Reactor.exe (PID: 884)
- dotNET_Reactor.exe (PID: 1576)
- dotNET_Reactor.exe (PID: 3256)
- REACTOR_HELP.exe (PID: 452)
- REACTOR_HELP.exe (PID: 2040)
- dotNET_Reactor.exe (PID: 4004)
Executable content was dropped or overwritten
- setup.exe (PID: 992)
- setup.exe (PID: 664)
- setup.tmp (PID: 1392)
- REACTOR_HELP.exe (PID: 452)
Reads the Windows owner or organization settings
- setup.tmp (PID: 1392)
Starts itself from another location
- REACTOR_HELP.exe (PID: 452)
Reads security settings of Internet Explorer
- REACTOR_HELP.exe (PID: 452)
- dotNET_Reactor.exe (PID: 3256)
INFO
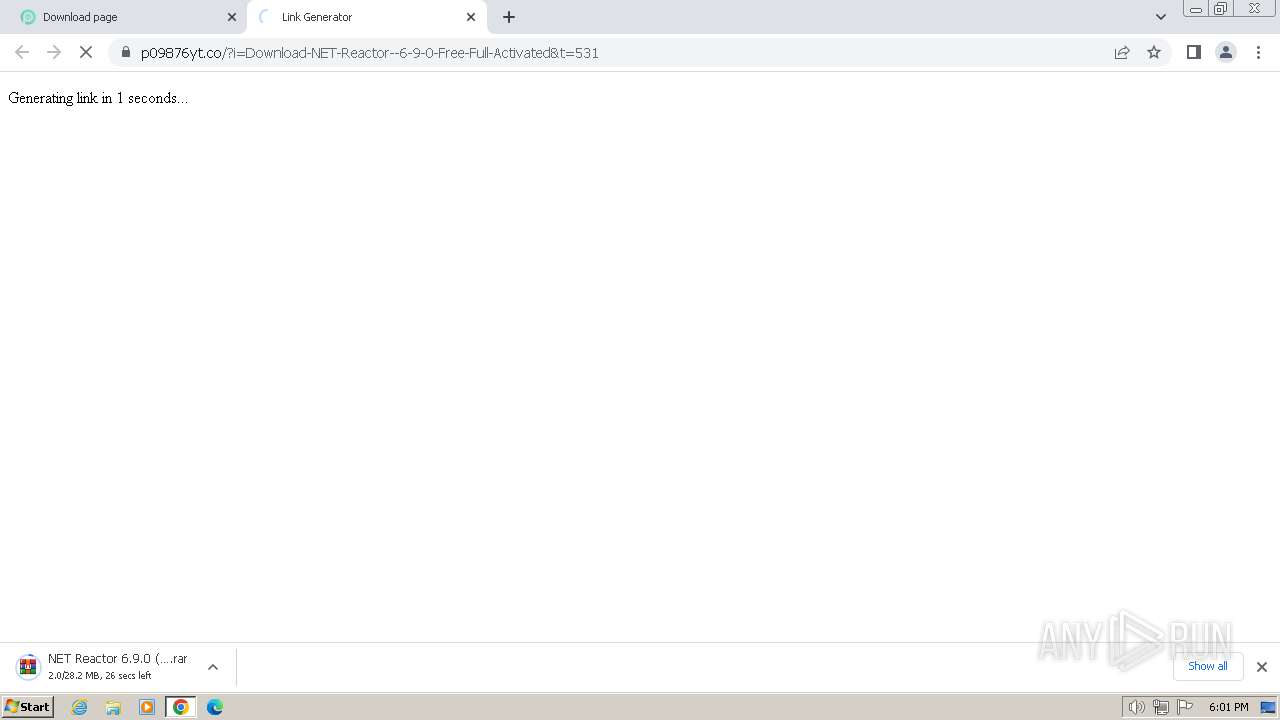
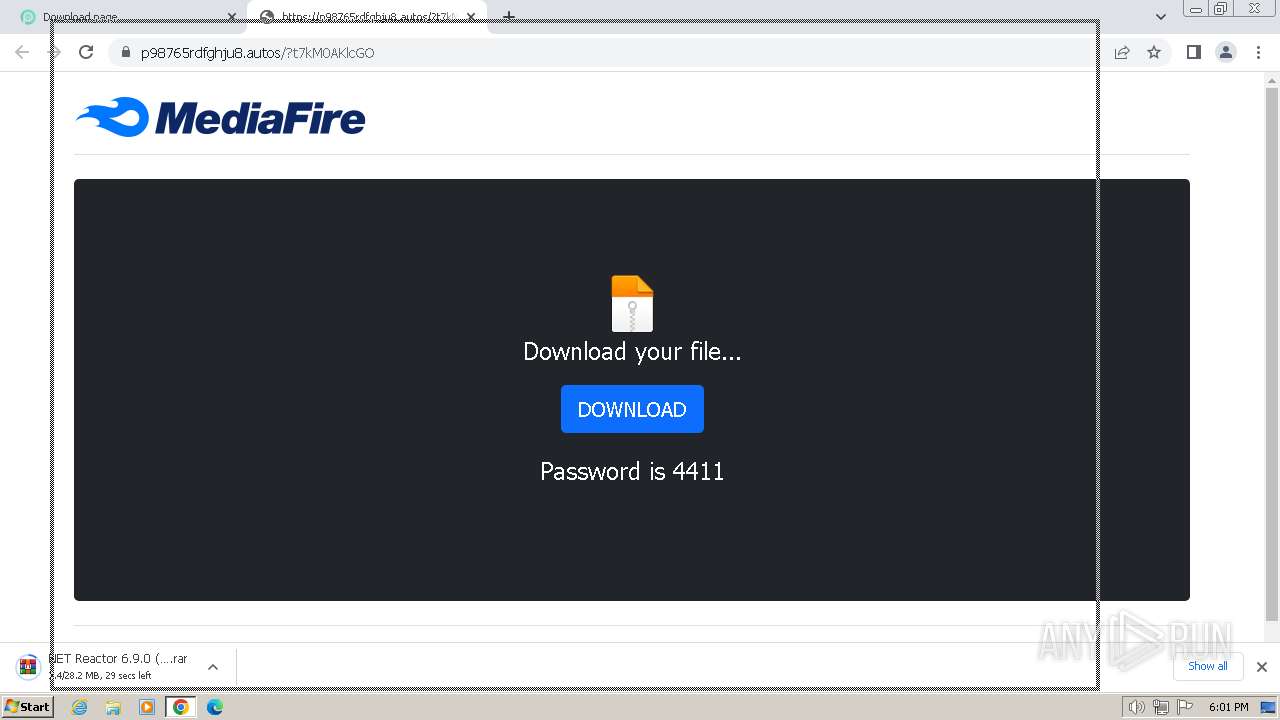
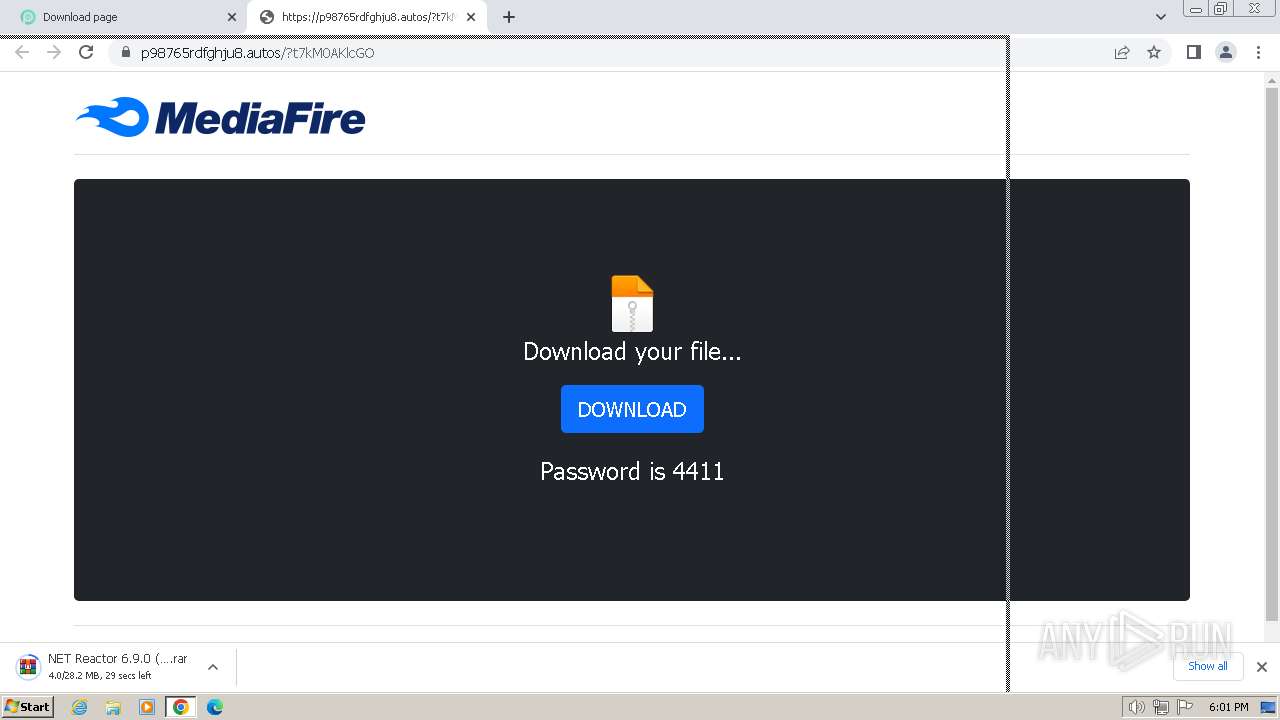
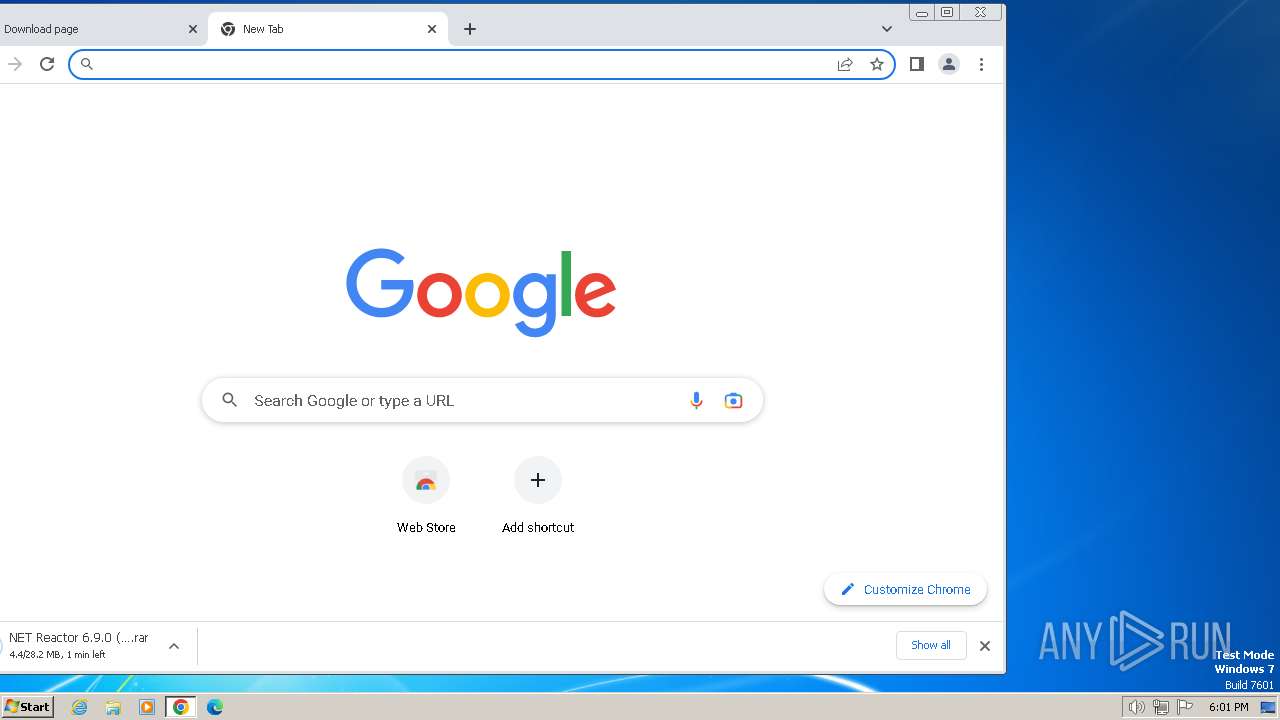
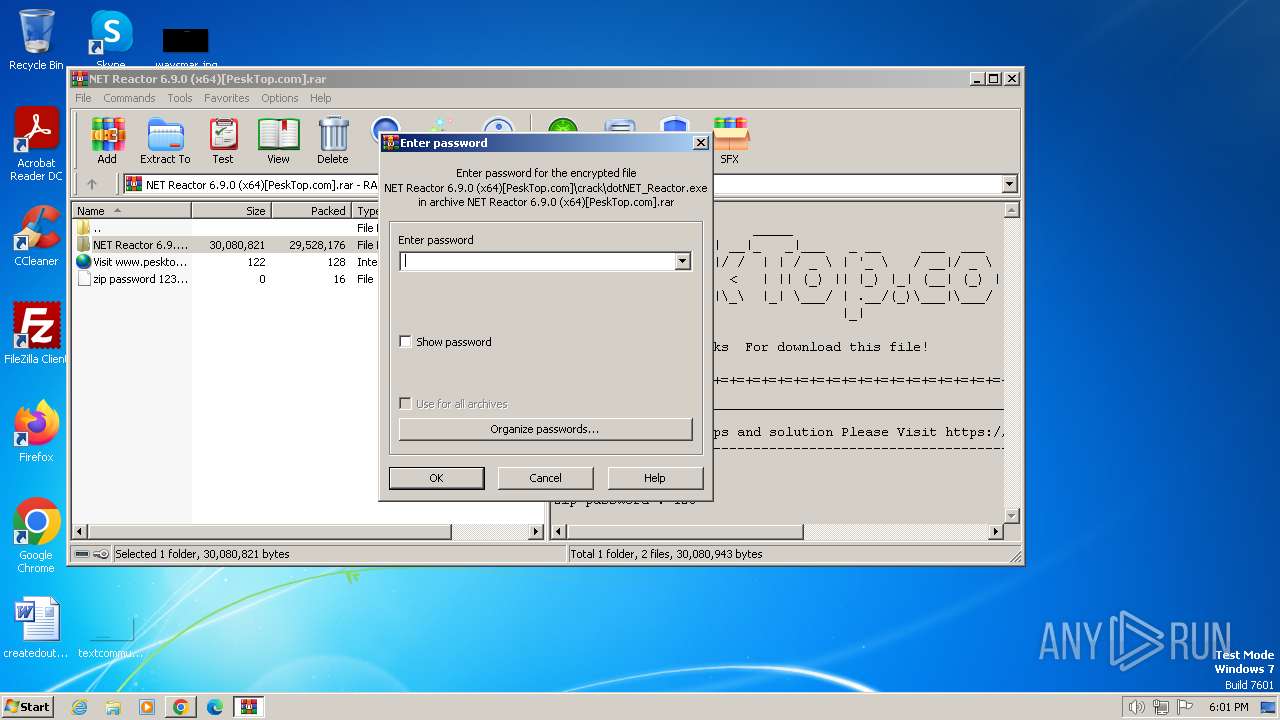
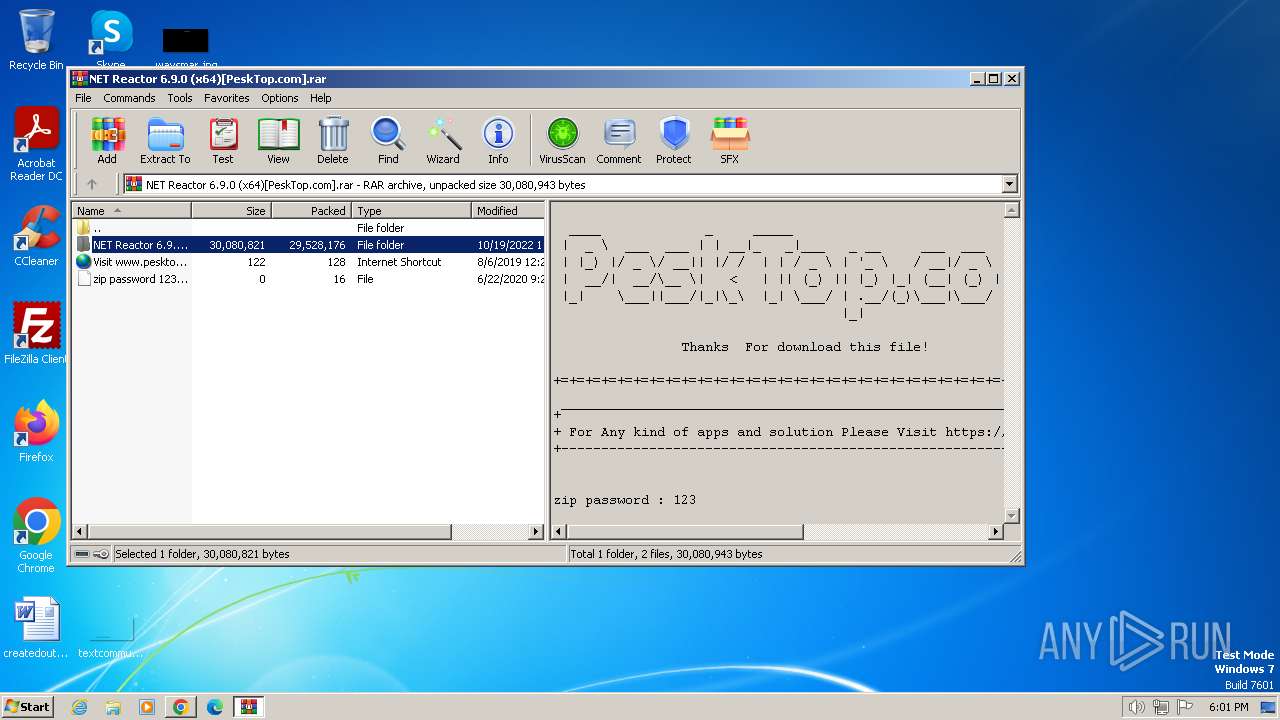
The process uses the downloaded file
- chrome.exe (PID: 3808)
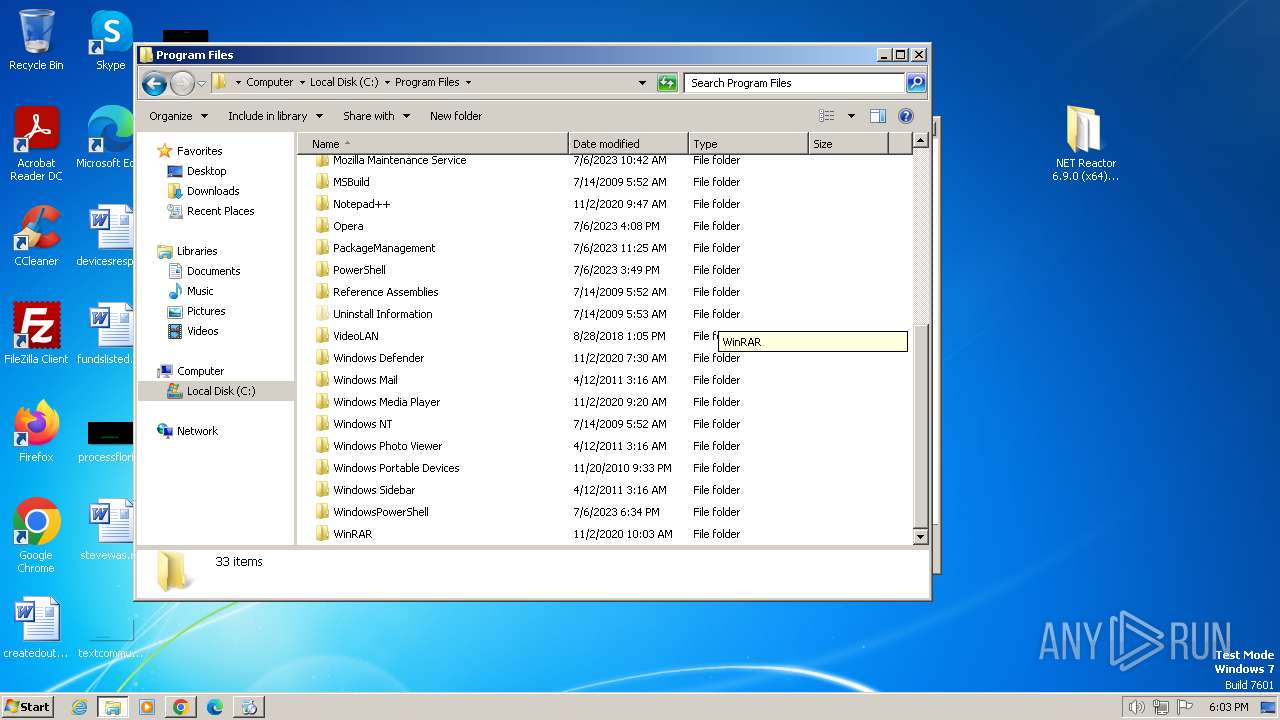
- WinRAR.exe (PID: 3524)
Reads the machine GUID from the registry
- dotNET_Reactor.exe (PID: 884)
- dotNET_Reactor.exe (PID: 1576)
- dotNET_Reactor.exe (PID: 4004)
- dotNET_Reactor.exe (PID: 3256)
- REACTOR_HELP.exe (PID: 2040)
Reads the computer name
- dotNET_Reactor.exe (PID: 1576)
- setup.tmp (PID: 552)
- setup.tmp (PID: 1392)
- dotNET_Reactor.exe (PID: 4004)
- dotNET_Reactor.exe (PID: 3256)
- dotNET_Reactor.exe (PID: 884)
- REACTOR_HELP.exe (PID: 452)
- REACTOR_HELP.exe (PID: 2040)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3524)
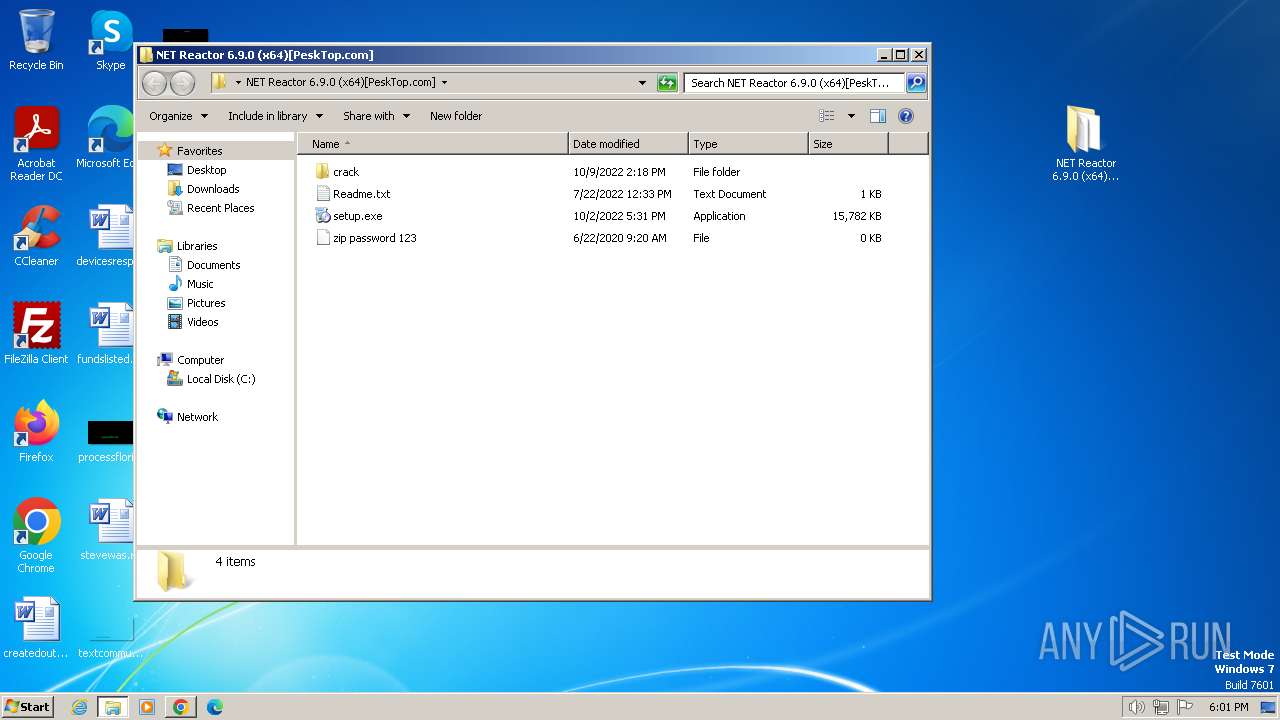
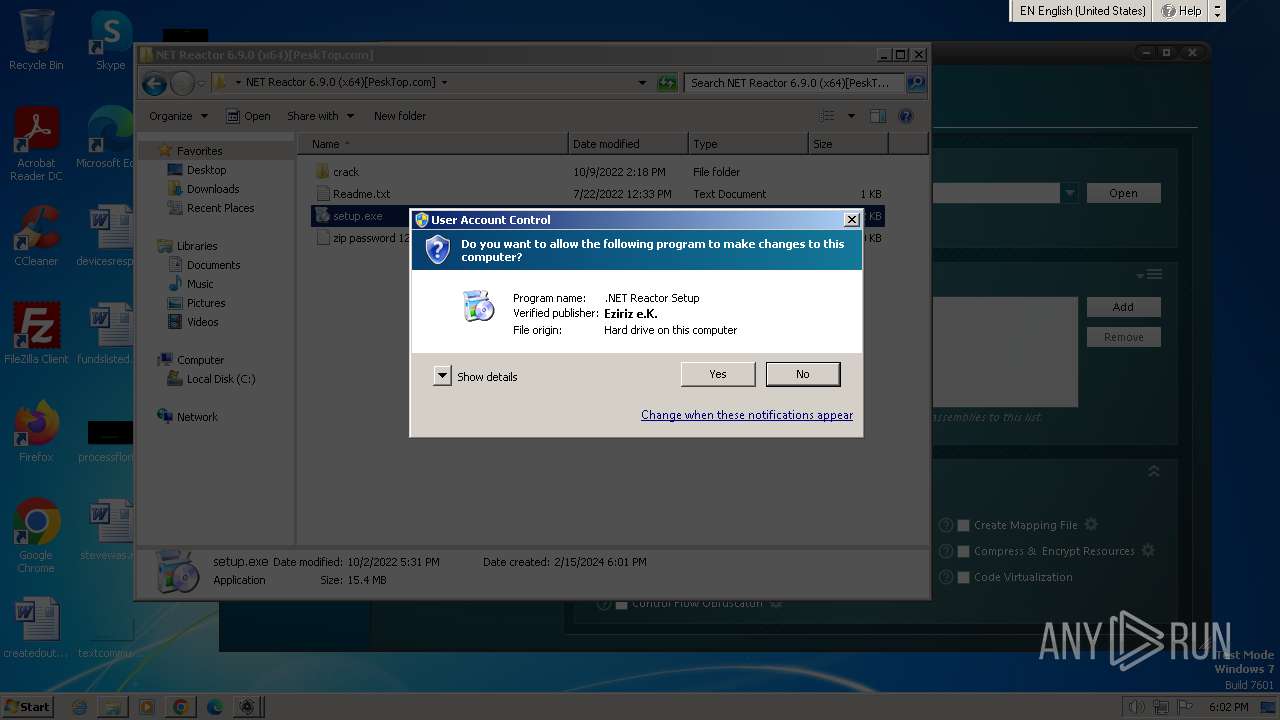
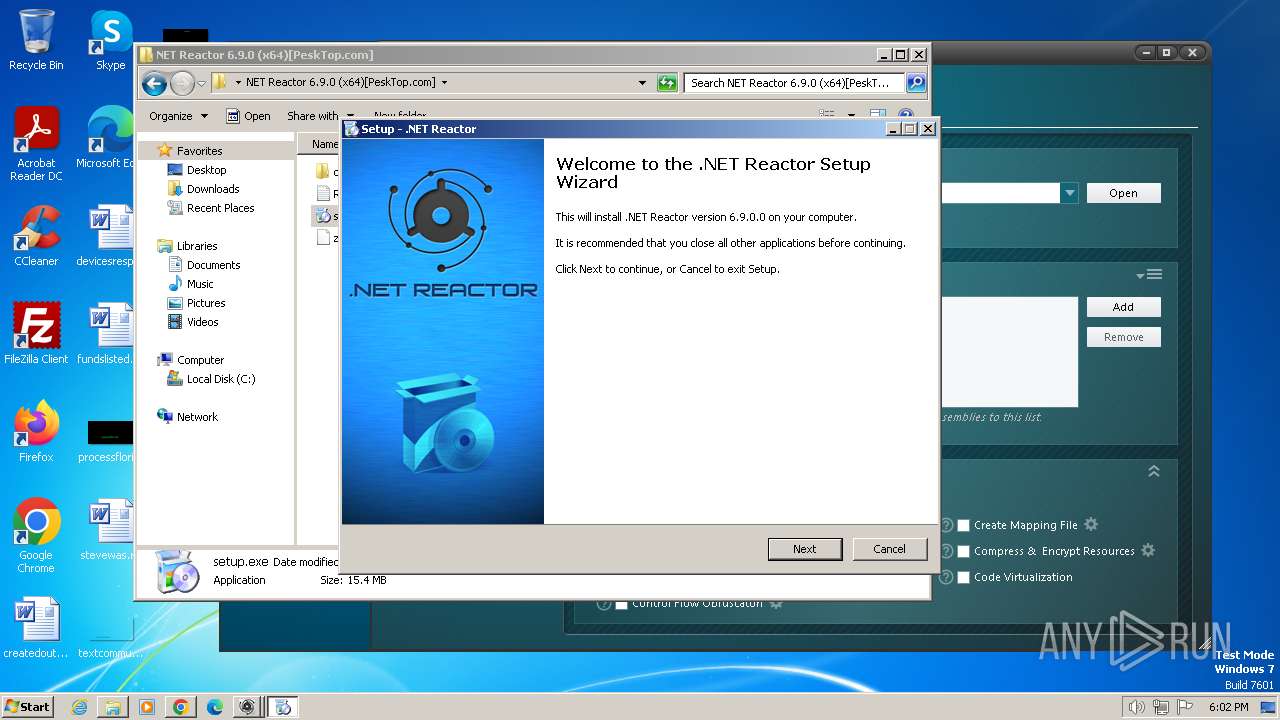
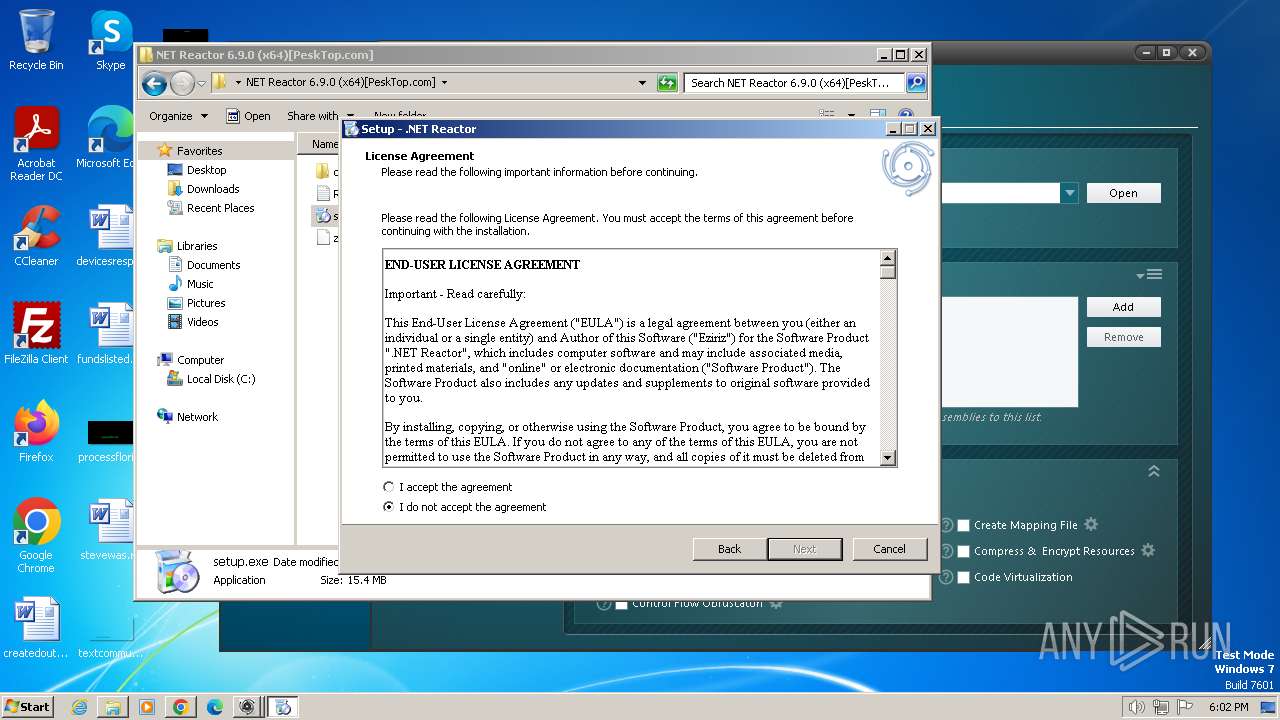
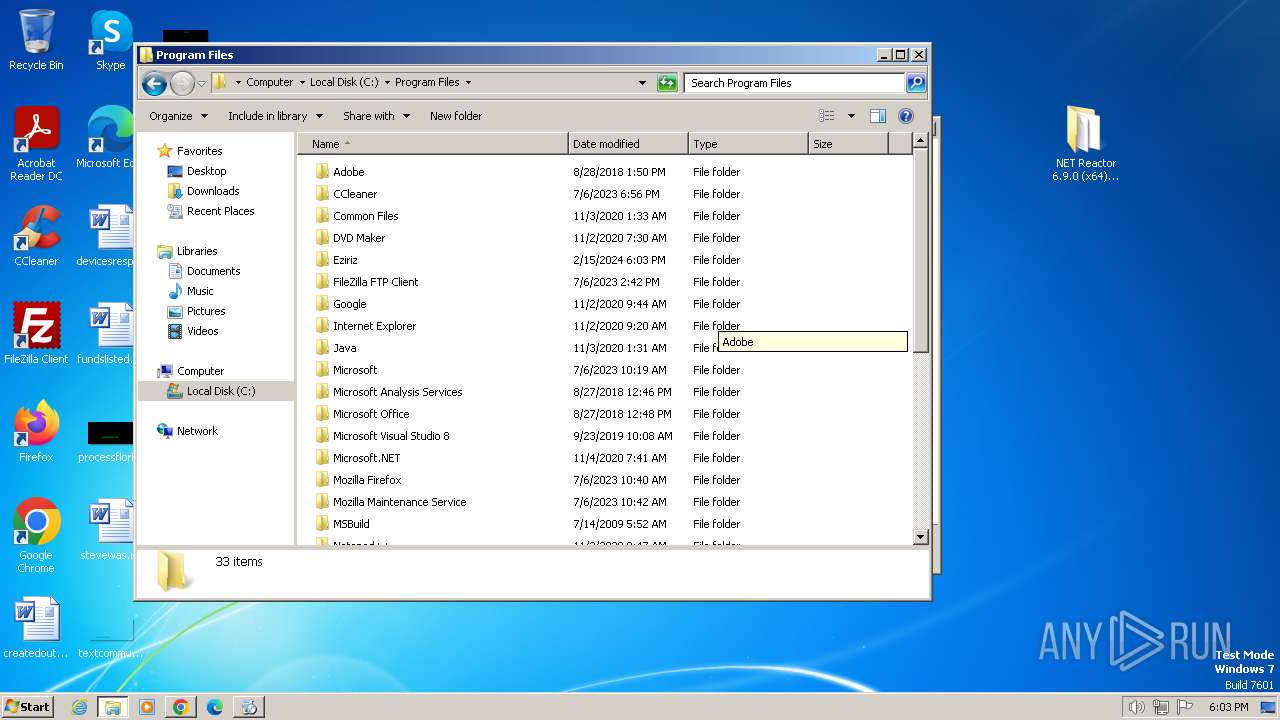
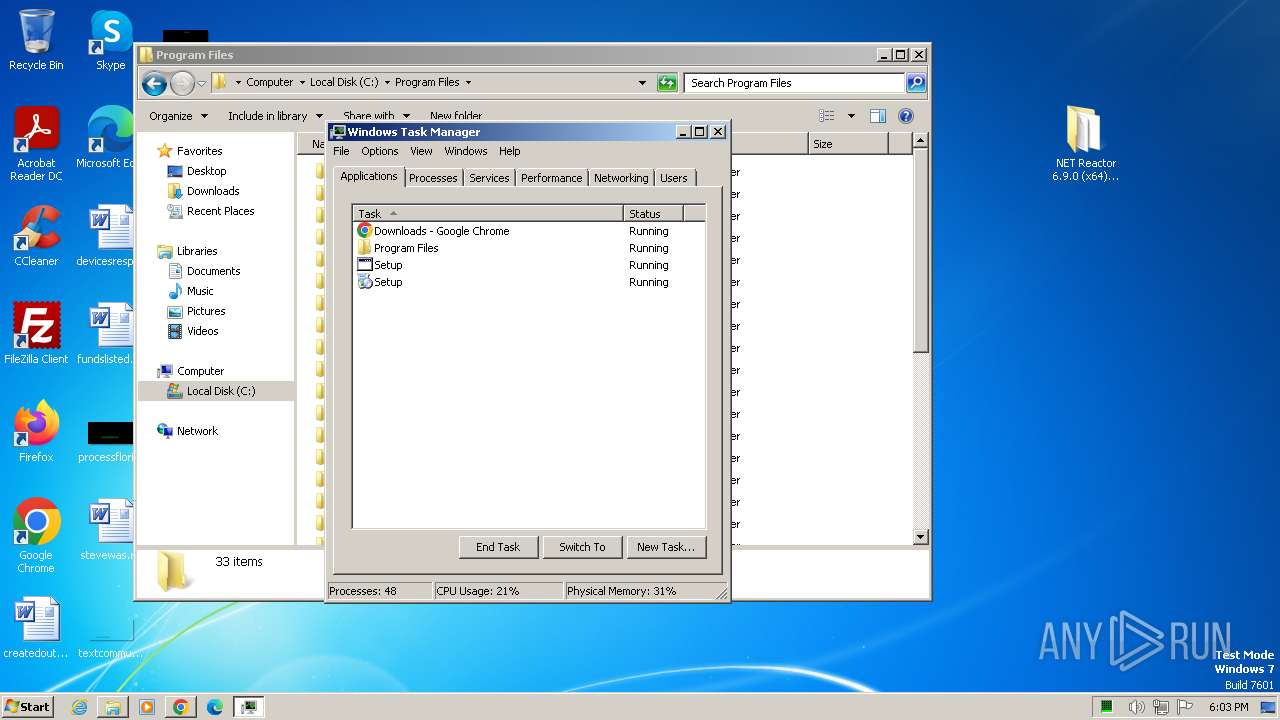
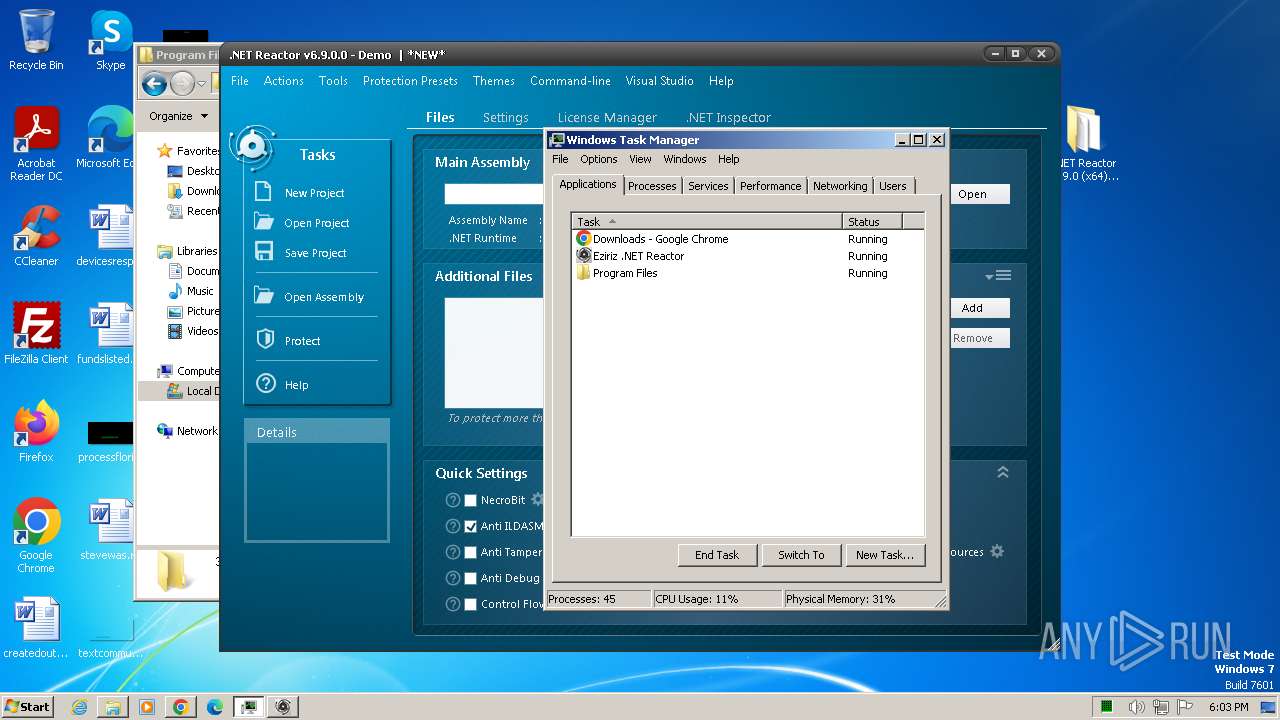
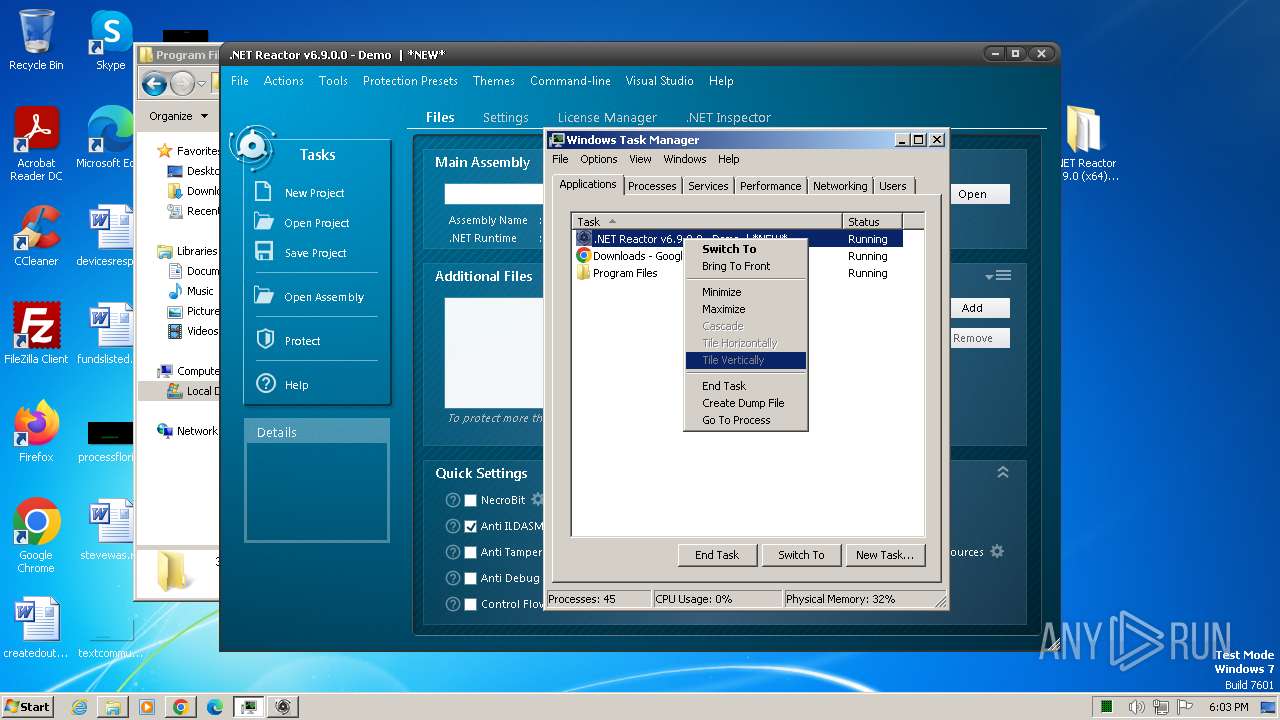
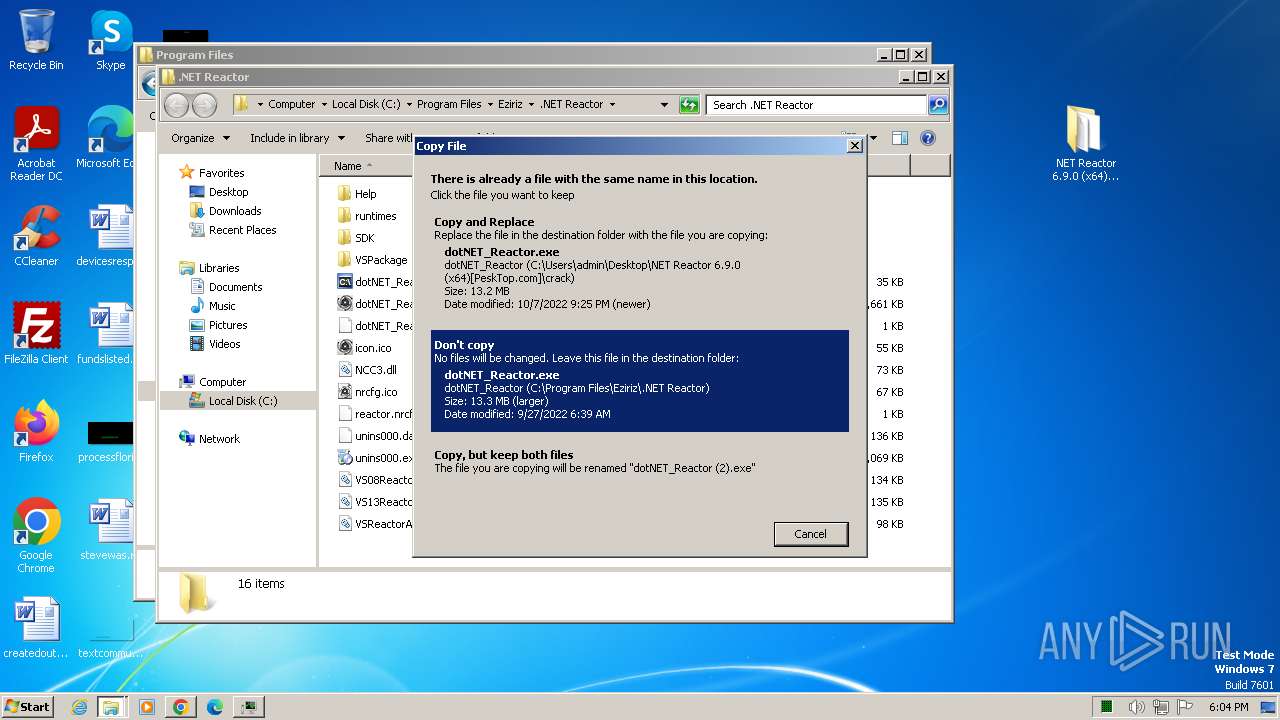
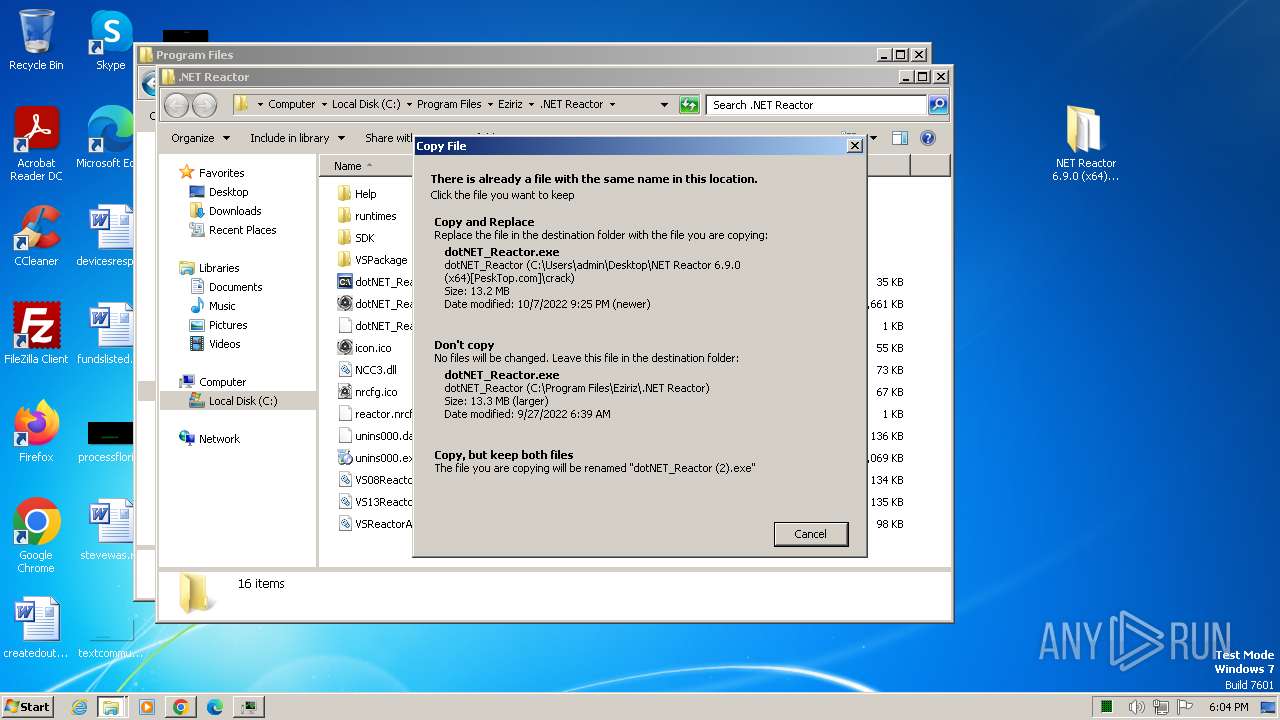
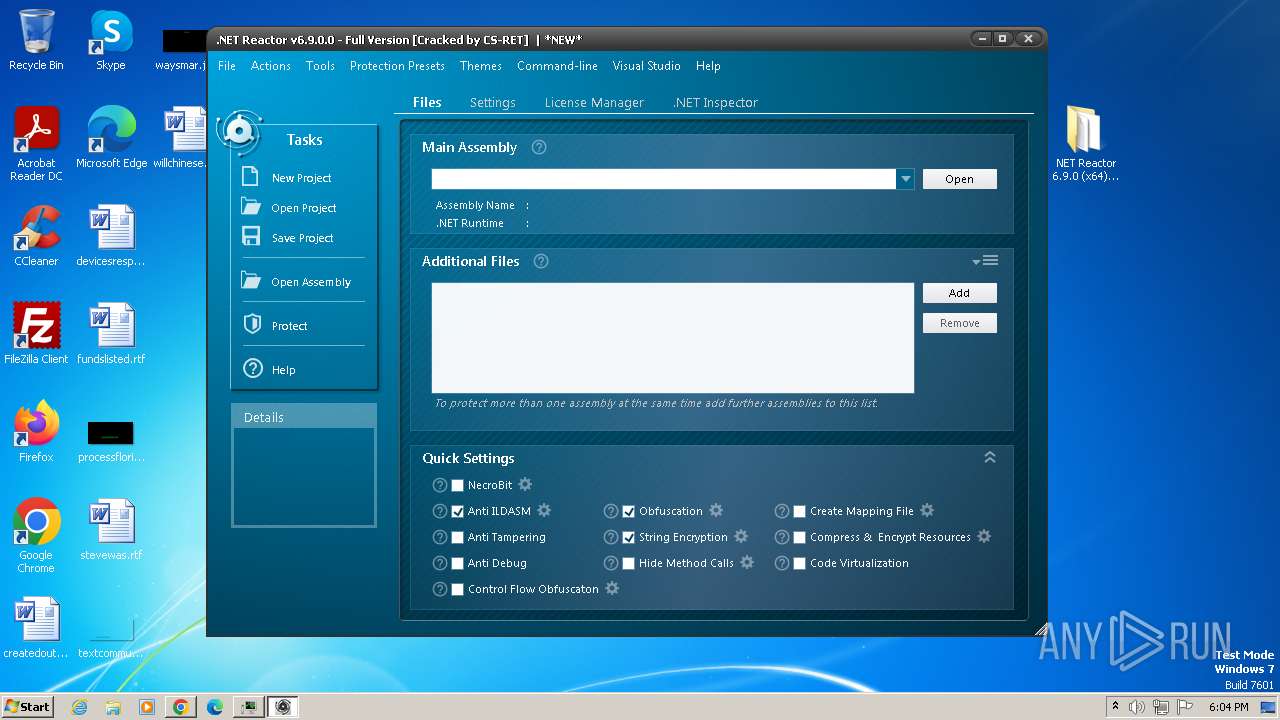
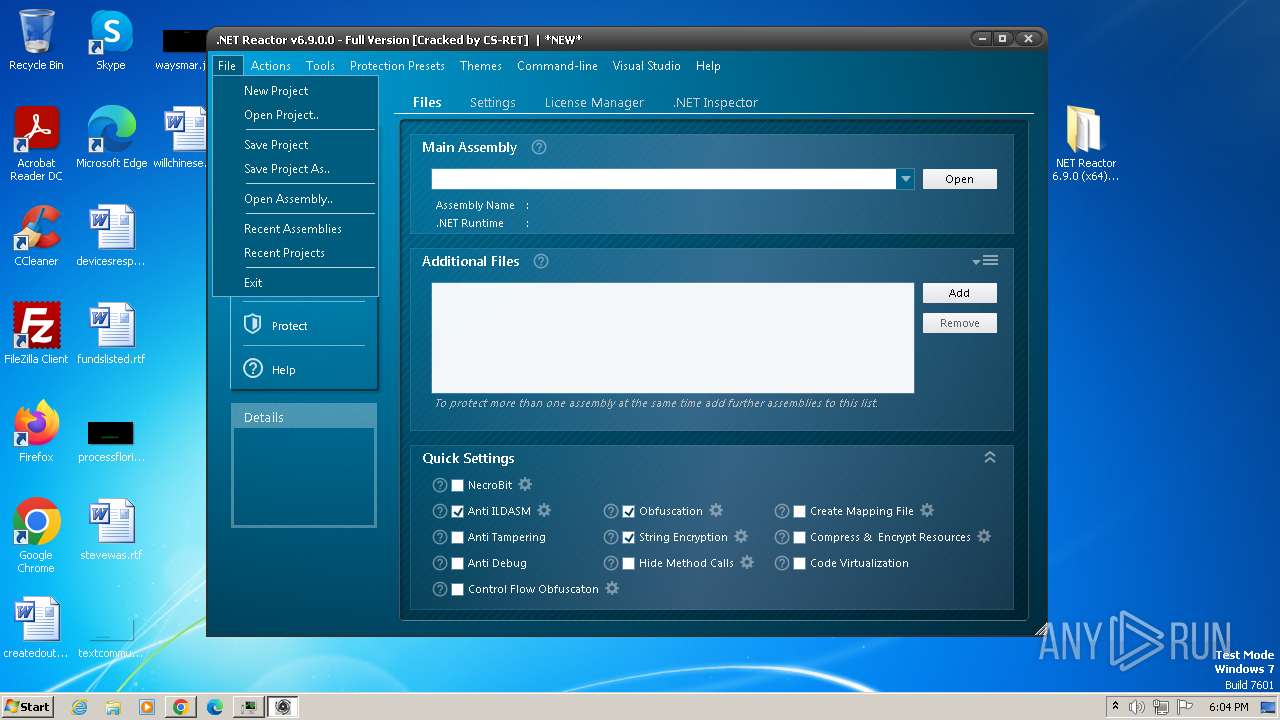
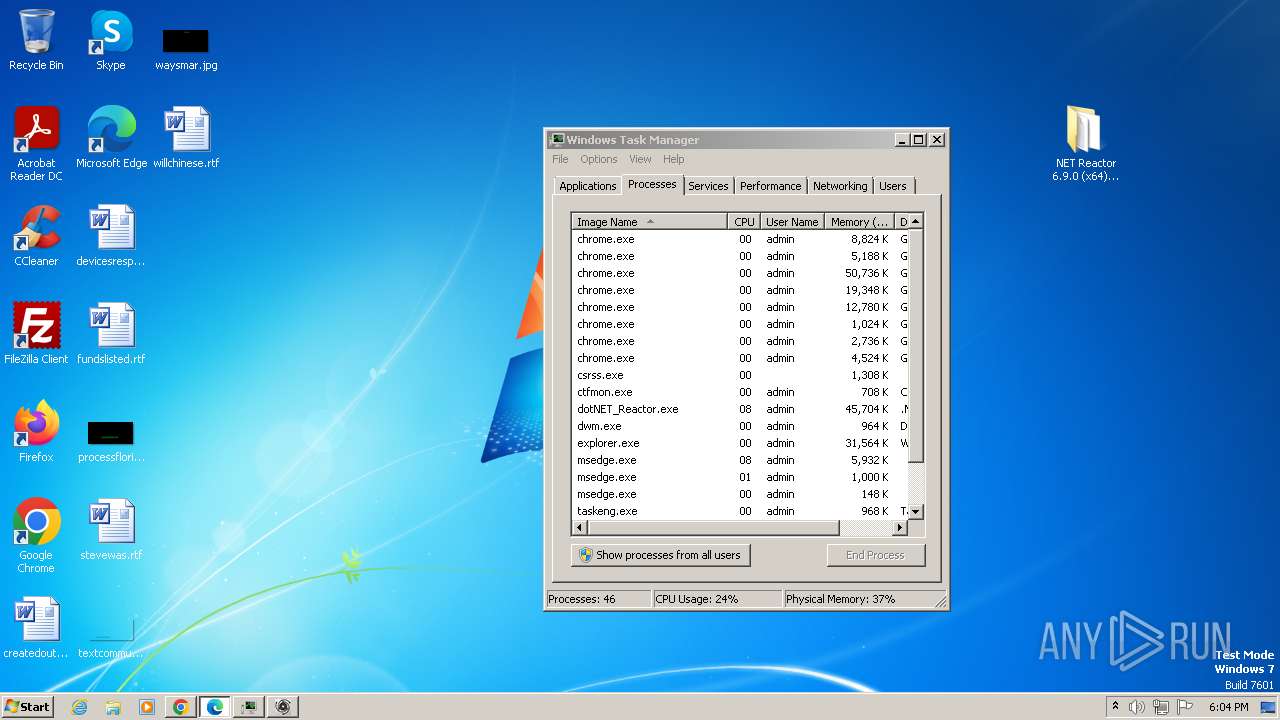
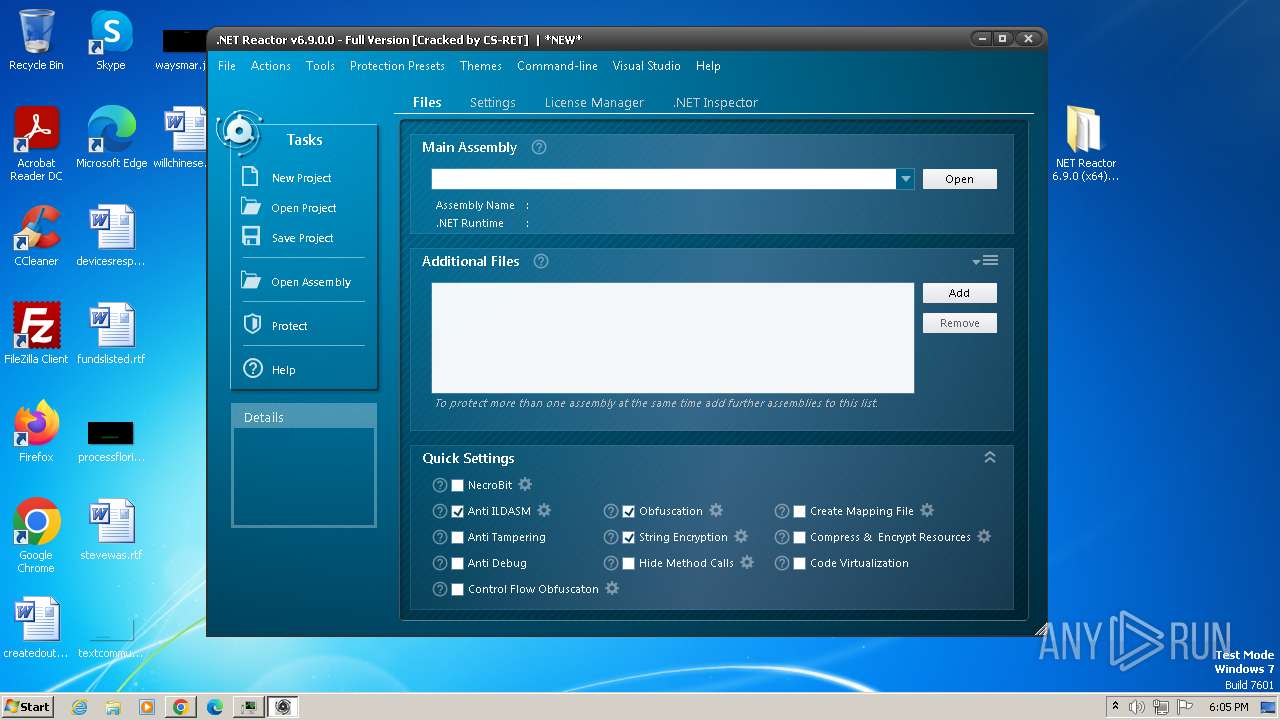
Manual execution by a user
- dotNET_Reactor.exe (PID: 884)
- dotNET_Reactor.exe (PID: 1576)
- setup.exe (PID: 992)
- taskmgr.exe (PID: 2960)
- dotNET_Reactor.exe (PID: 3256)
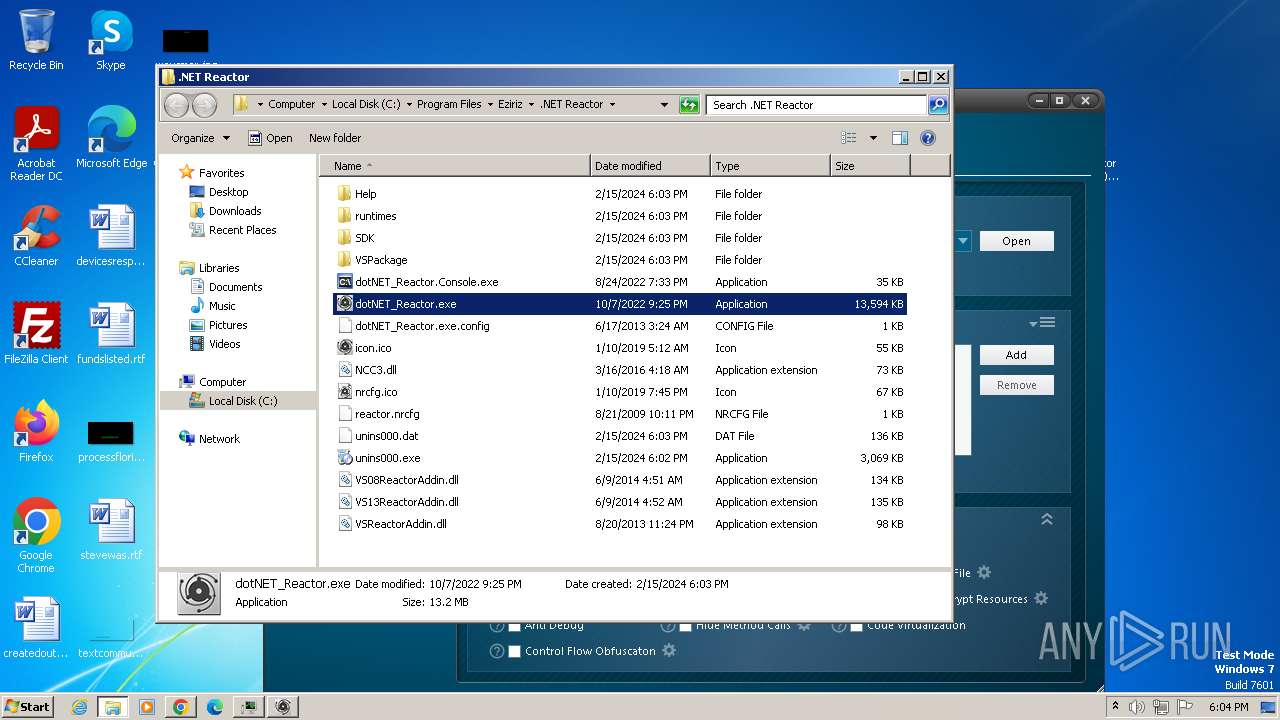
Creates files or folders in the user directory
- dotNET_Reactor.exe (PID: 884)
- dotNET_Reactor.exe (PID: 1576)
- dotNET_Reactor.exe (PID: 4004)
- REACTOR_HELP.exe (PID: 452)
- dotNET_Reactor.exe (PID: 3256)
- REACTOR_HELP.exe (PID: 2040)
Application launched itself
- chrome.exe (PID: 3240)
- msedge.exe (PID: 1348)
- msedge.exe (PID: 2068)
Checks supported languages
- dotNET_Reactor.exe (PID: 1576)
- setup.exe (PID: 992)
- setup.tmp (PID: 552)
- setup.exe (PID: 664)
- dotNET_Reactor.exe (PID: 4004)
- dotNET_Reactor.exe (PID: 3256)
- REACTOR_HELP.exe (PID: 452)
- dotNET_Reactor.exe (PID: 884)
- setup.tmp (PID: 1392)
- REACTOR_HELP.exe (PID: 2040)
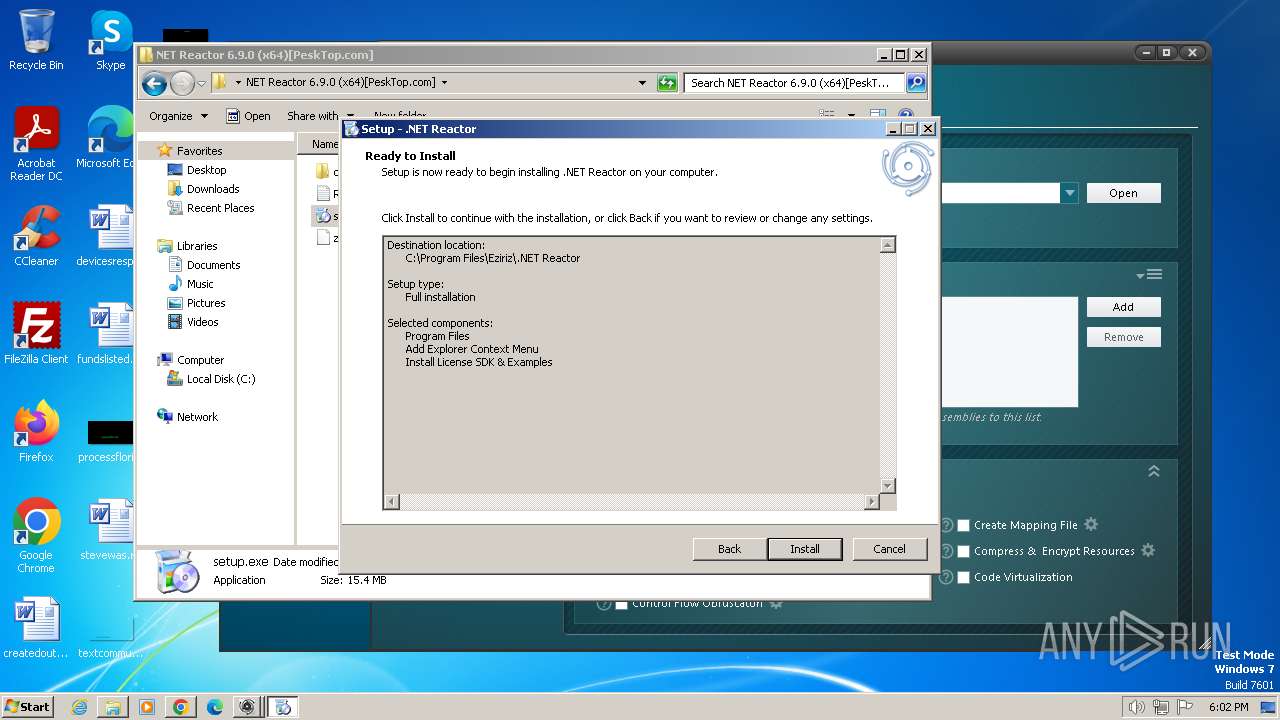
Create files in a temporary directory
- setup.exe (PID: 992)
- setup.exe (PID: 664)
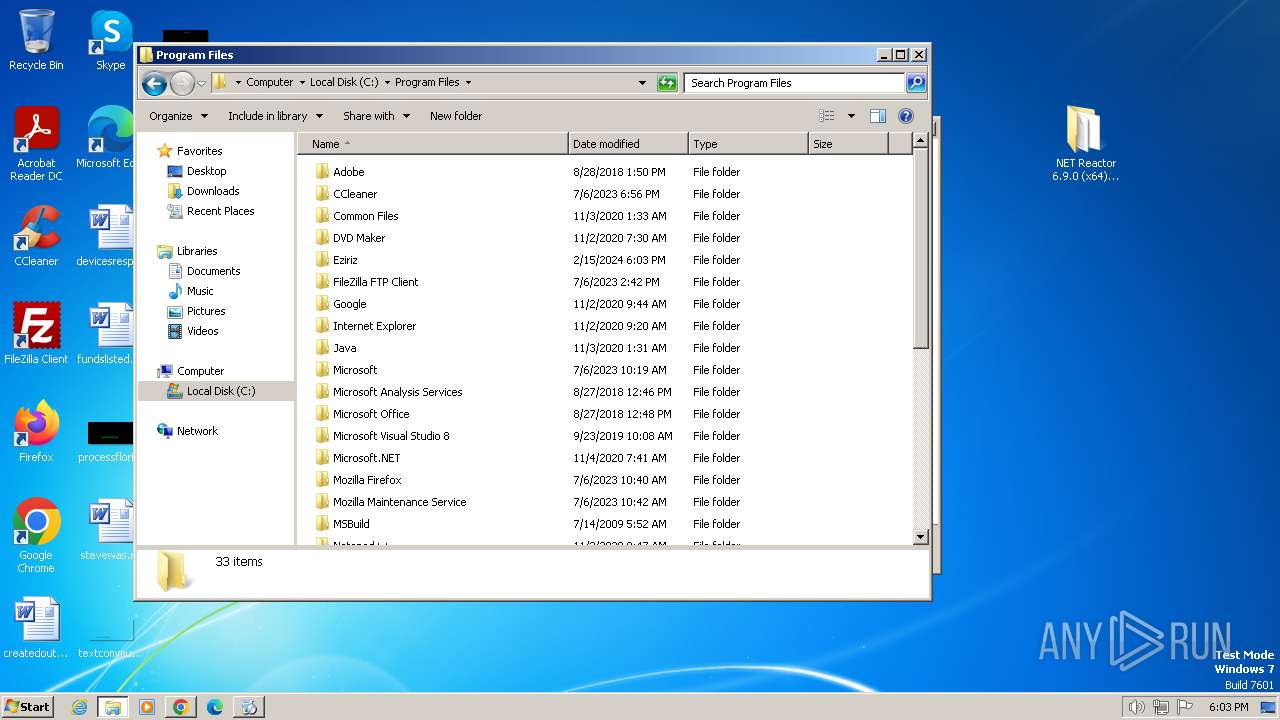
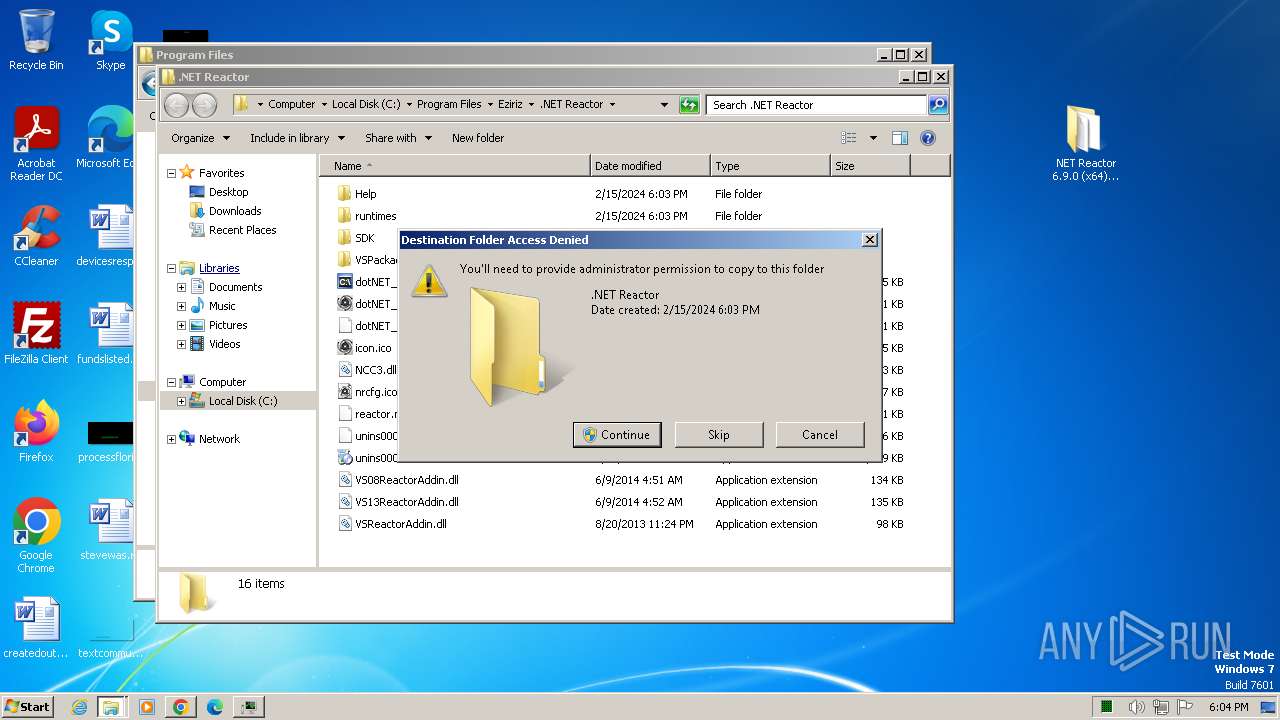
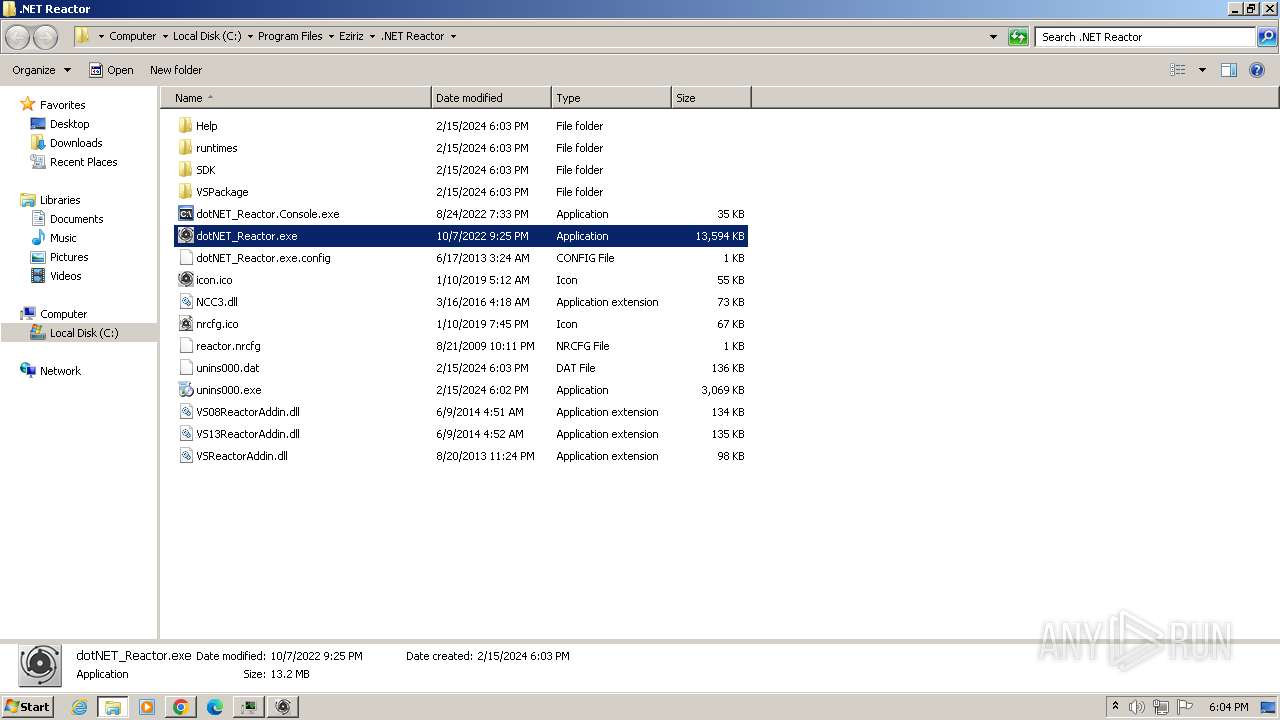
Creates files in the program directory
- setup.tmp (PID: 1392)
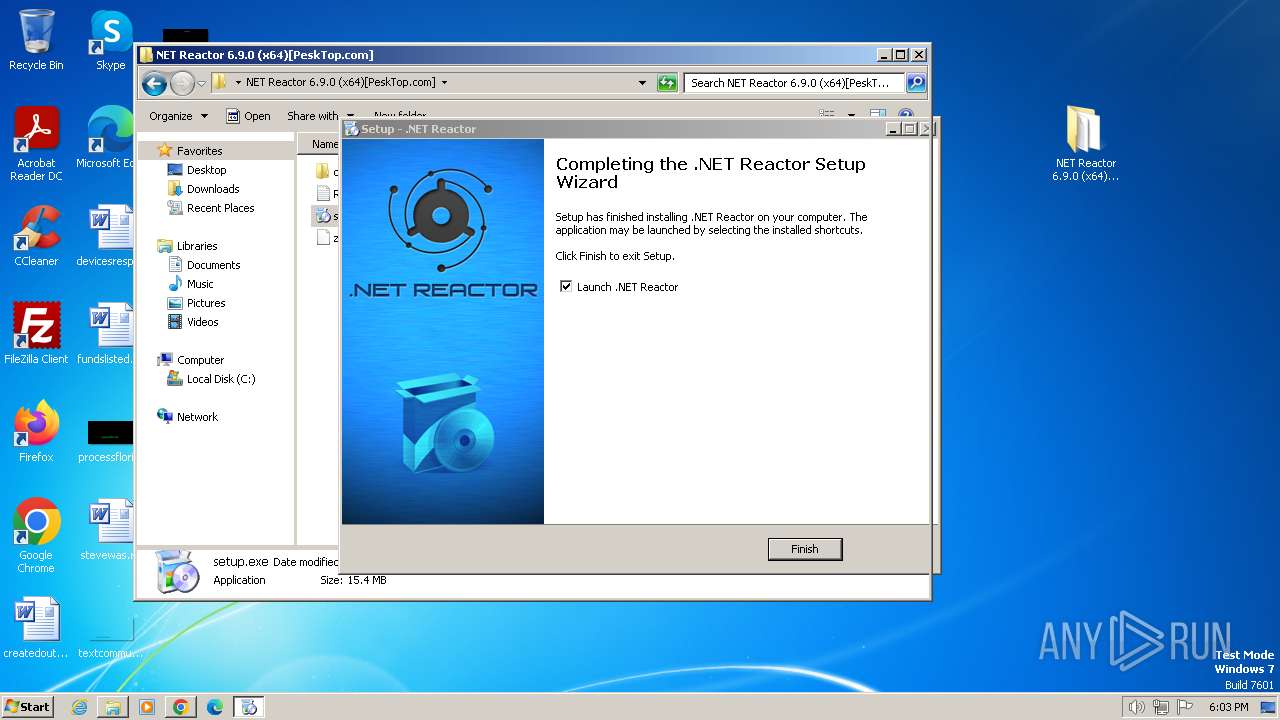
Creates a software uninstall entry
- setup.tmp (PID: 1392)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3524)
Reads Environment values
- REACTOR_HELP.exe (PID: 2040)
- dotNET_Reactor.exe (PID: 3256)
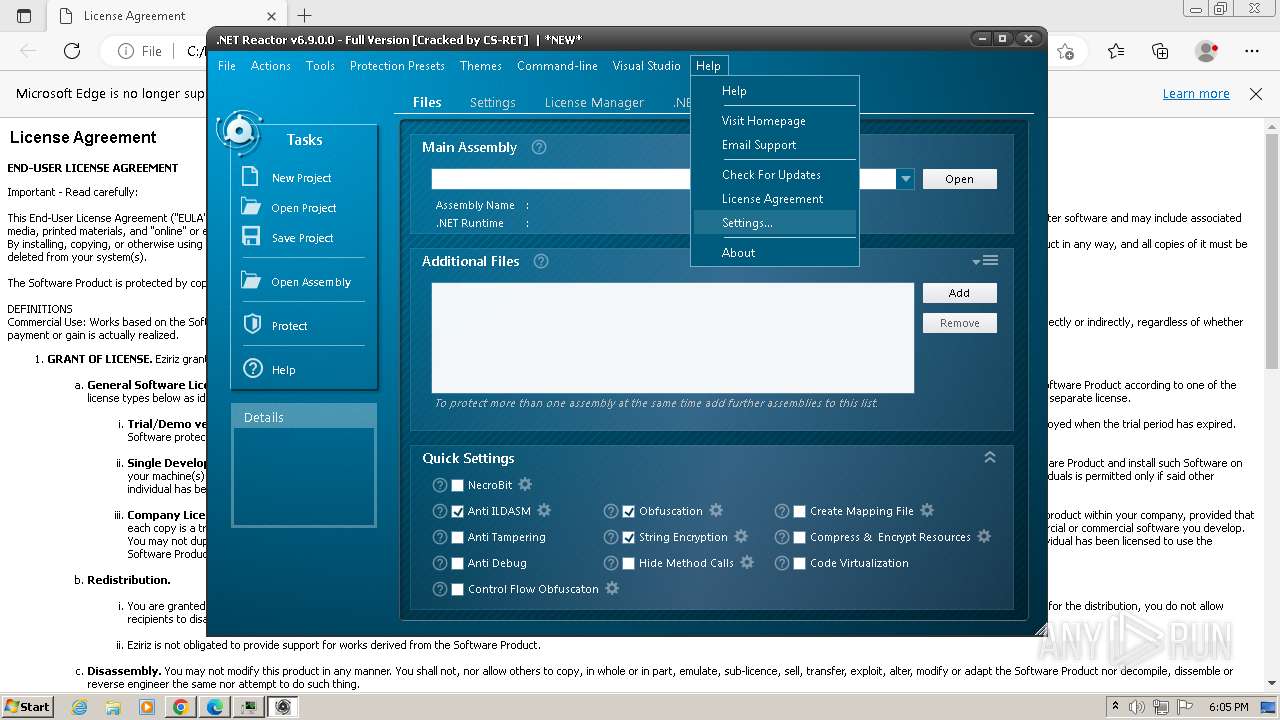
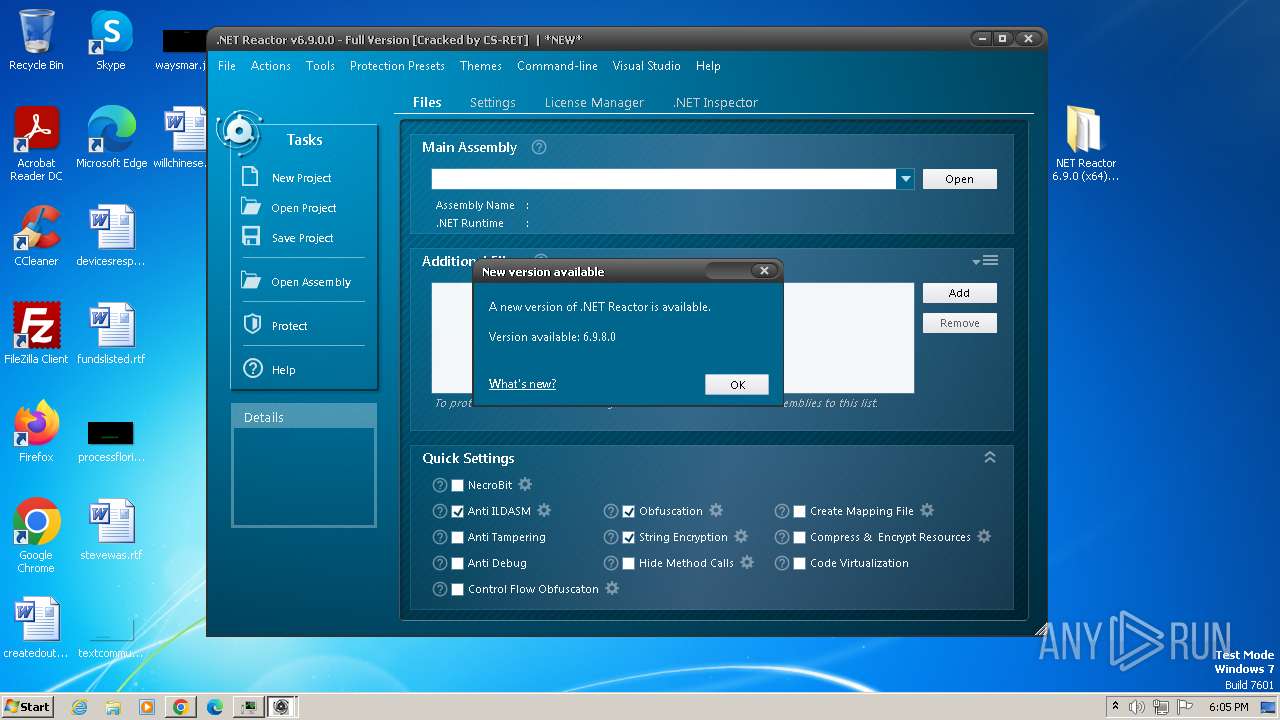
Checks proxy server information
- dotNET_Reactor.exe (PID: 3256)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
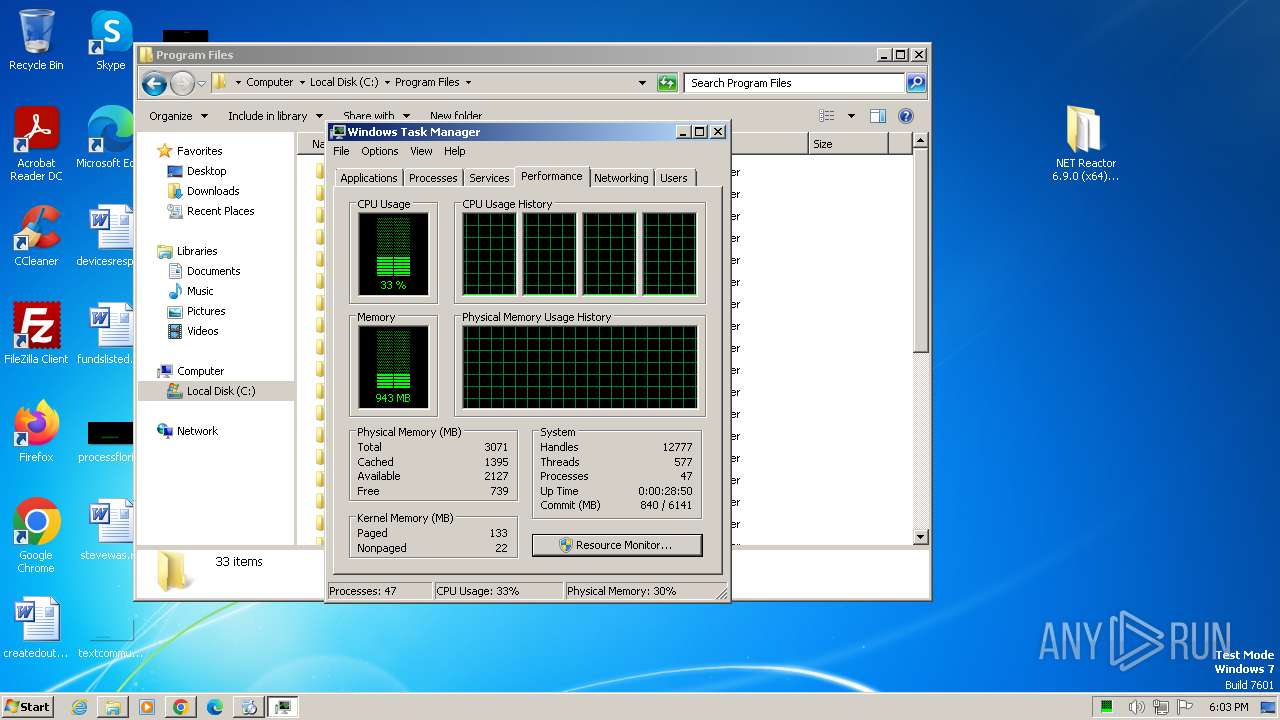
Total processes
108
Monitored processes
57
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
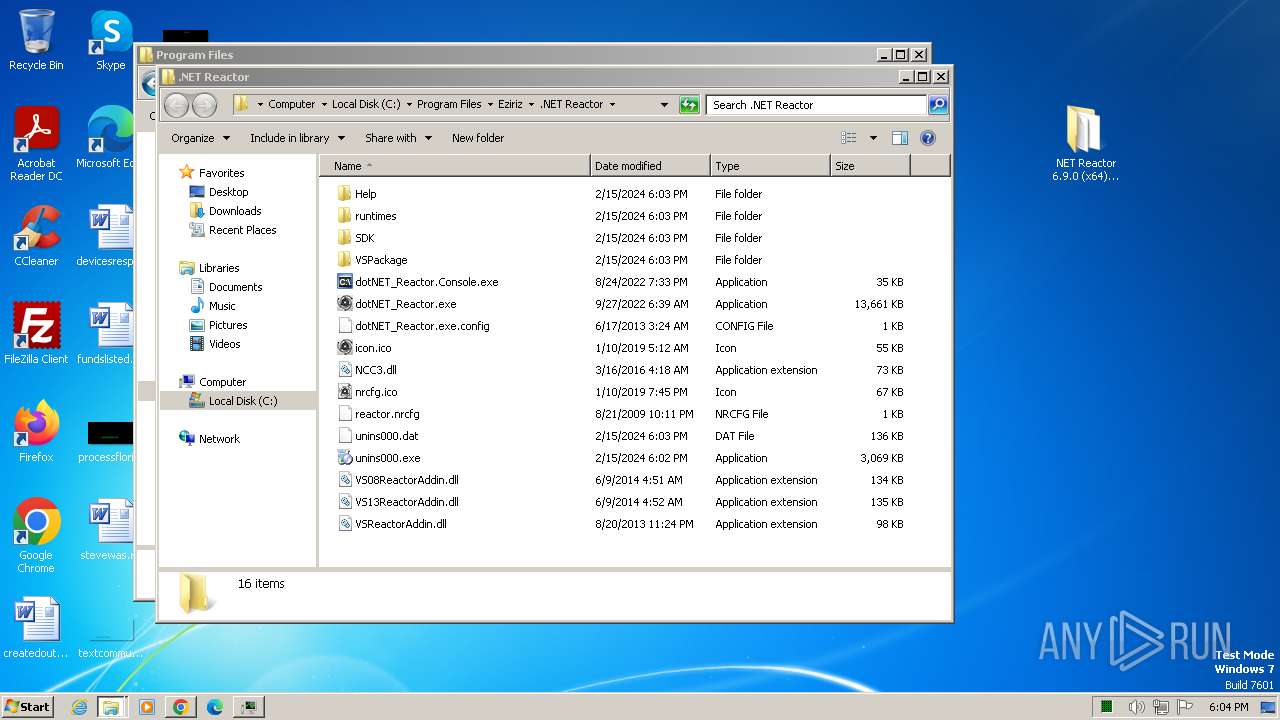
| 452 | "C:\Program Files\Eziriz\.NET Reactor\Help\REACTOR_HELP.exe" | C:\Program Files\Eziriz\.NET Reactor\Help\REACTOR_HELP.exe | dotNET_Reactor.exe | ||||||||||||
User: admin Company: Eziriz Integrity Level: MEDIUM Description: REACTOR_HELP Exit code: 0 Version: 1.0.0.38 Modules
| |||||||||||||||
| 552 | "C:\Users\admin\AppData\Local\Temp\is-14TS5.tmp\setup.tmp" /SL5="$D0162,14979712,785920,C:\Users\admin\Desktop\NET Reactor 6.9.0 (x64)[PeskTop.com]\setup.exe" | C:\Users\admin\AppData\Local\Temp\is-14TS5.tmp\setup.tmp | — | setup.exe | |||||||||||
User: admin Company: Eziriz Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
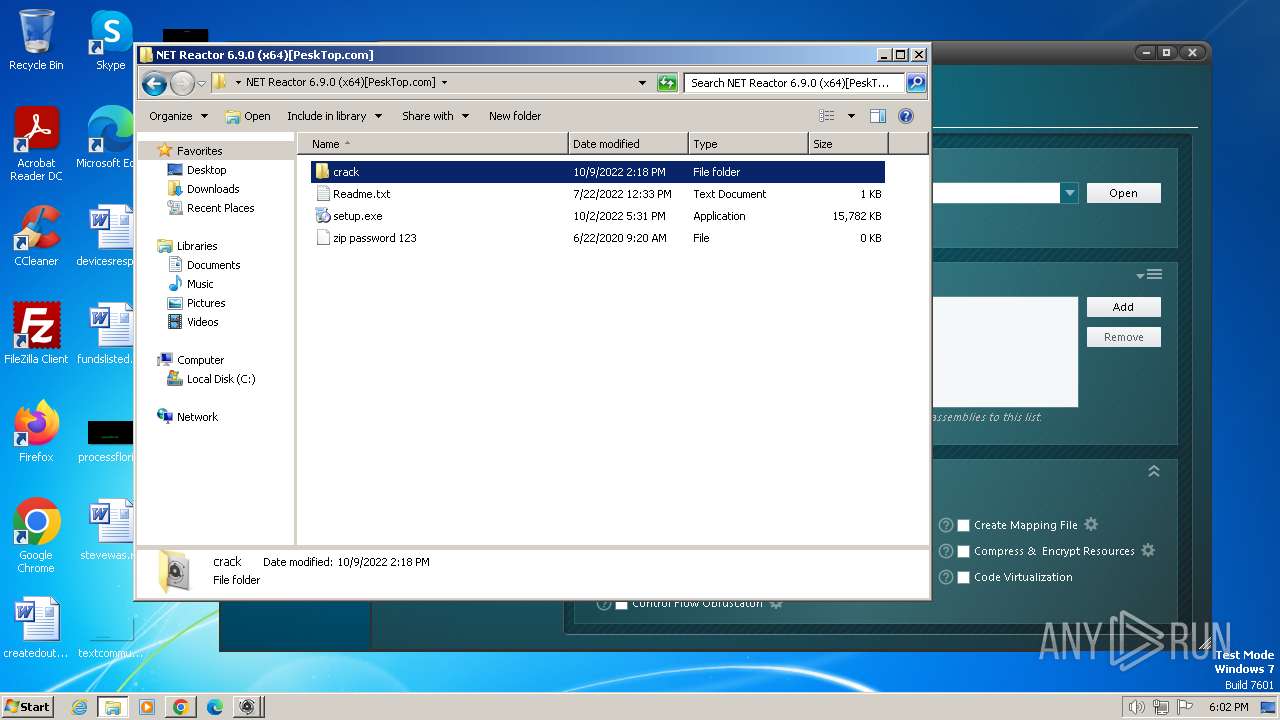
| 664 | "C:\Users\admin\Desktop\NET Reactor 6.9.0 (x64)[PeskTop.com]\setup.exe" /SPAWNWND=$1C0150 /NOTIFYWND=$D0162 | C:\Users\admin\Desktop\NET Reactor 6.9.0 (x64)[PeskTop.com]\setup.exe | setup.tmp | ||||||||||||
User: admin Company: Eziriz Integrity Level: HIGH Description: .NET Reactor Setup Exit code: 0 Version: 6.9.0.0 Modules
| |||||||||||||||
| 748 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1500 --field-trial-handle=1428,i,12861036811296109975,16540313707963390949,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
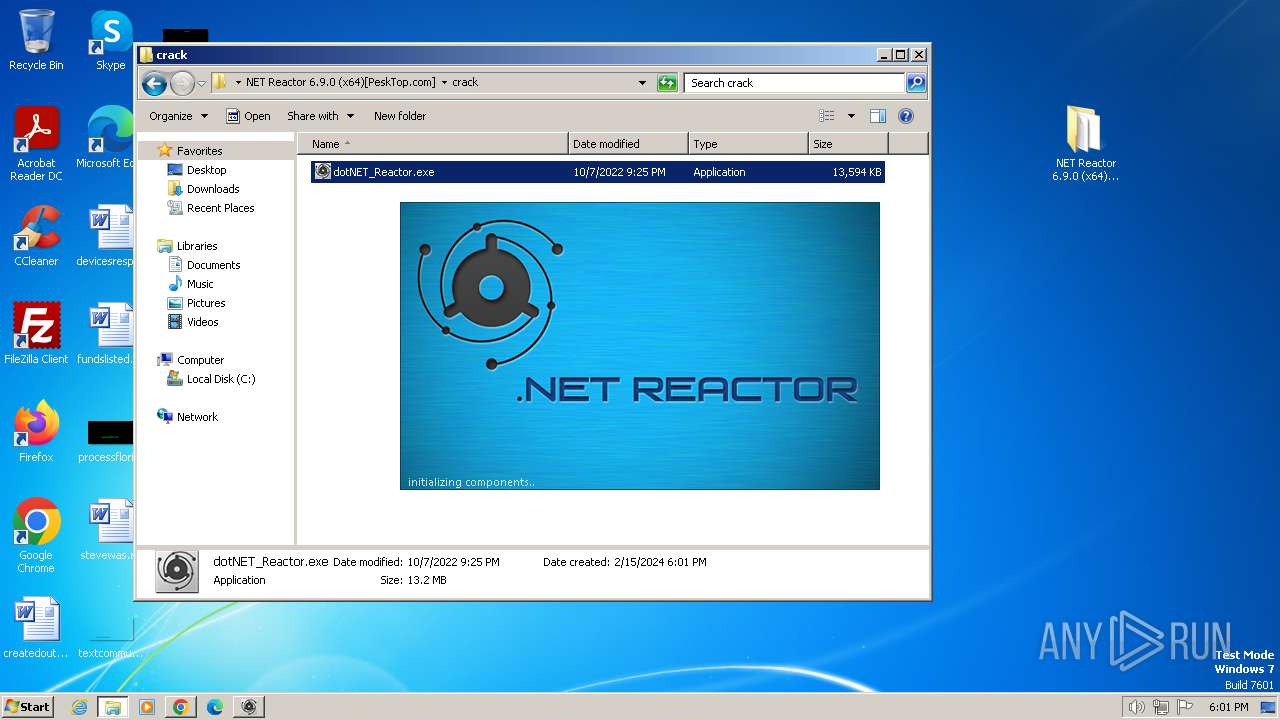
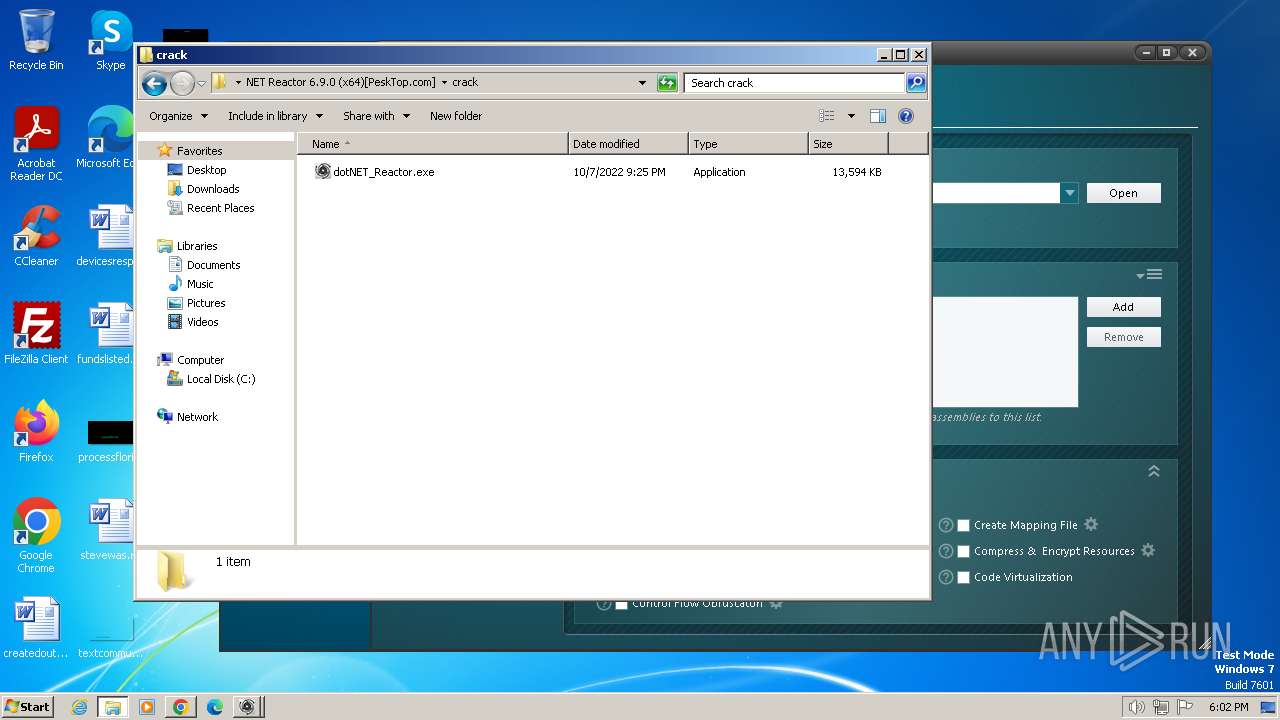
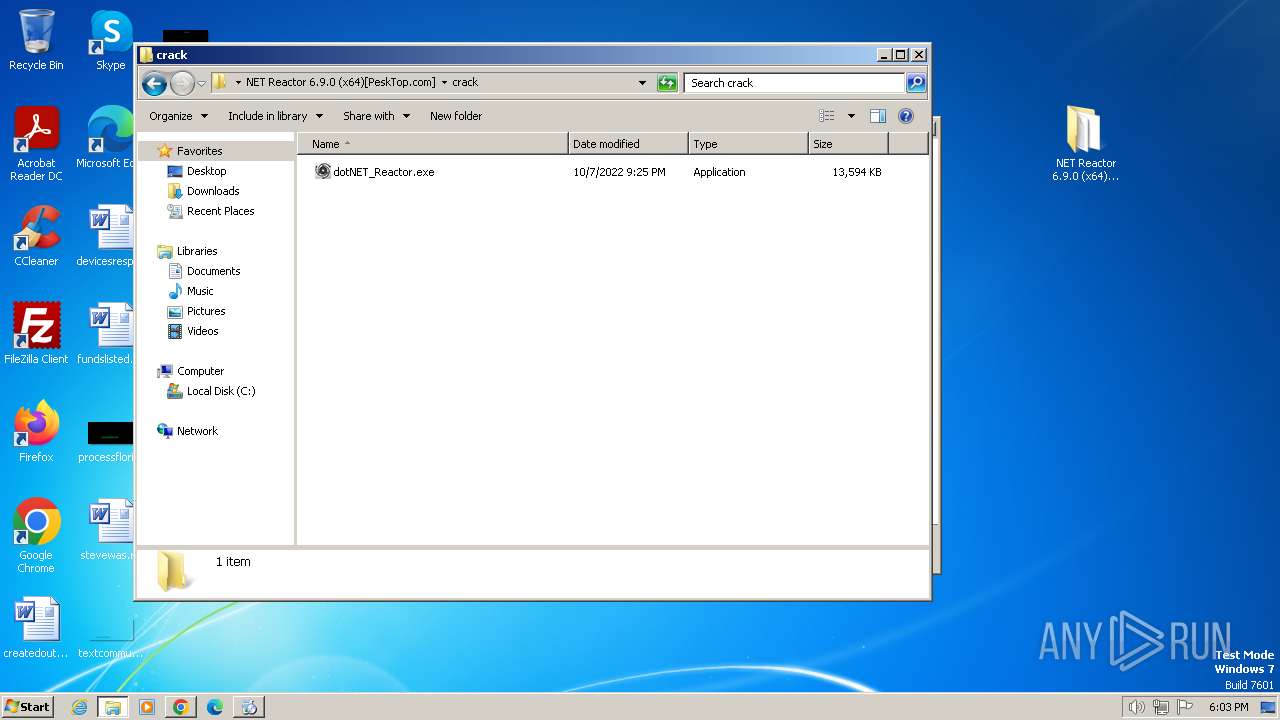
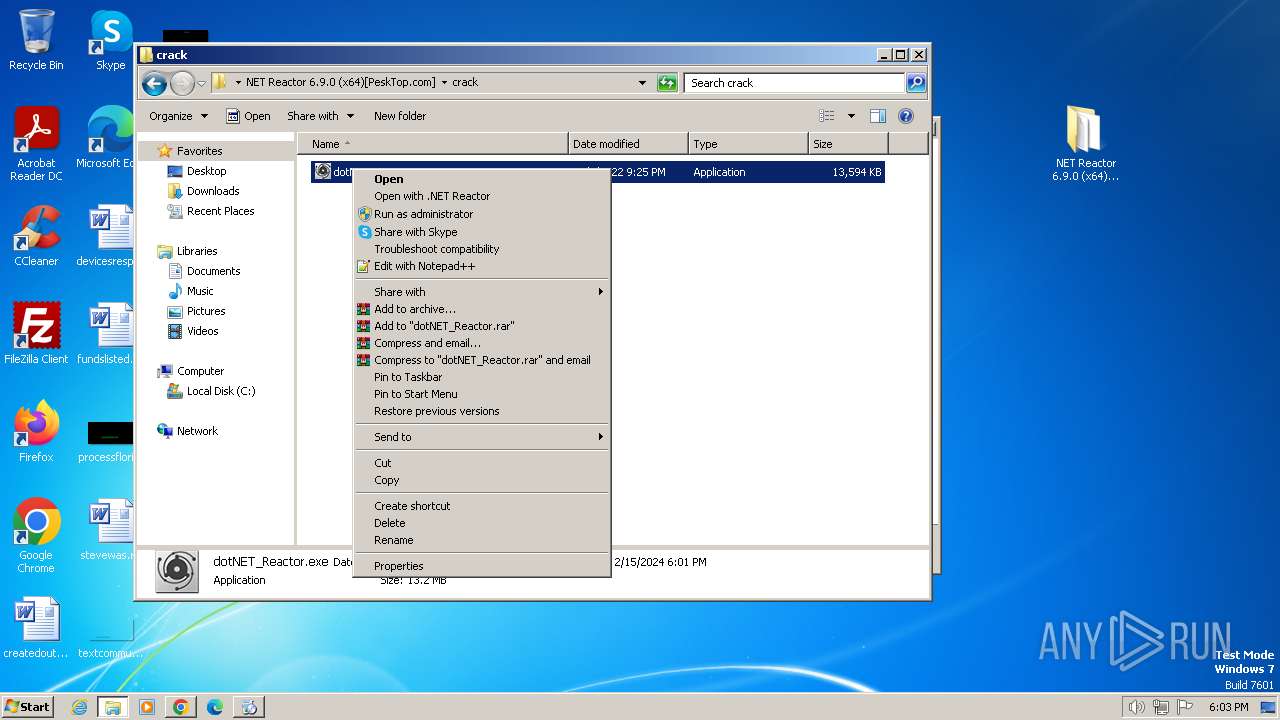
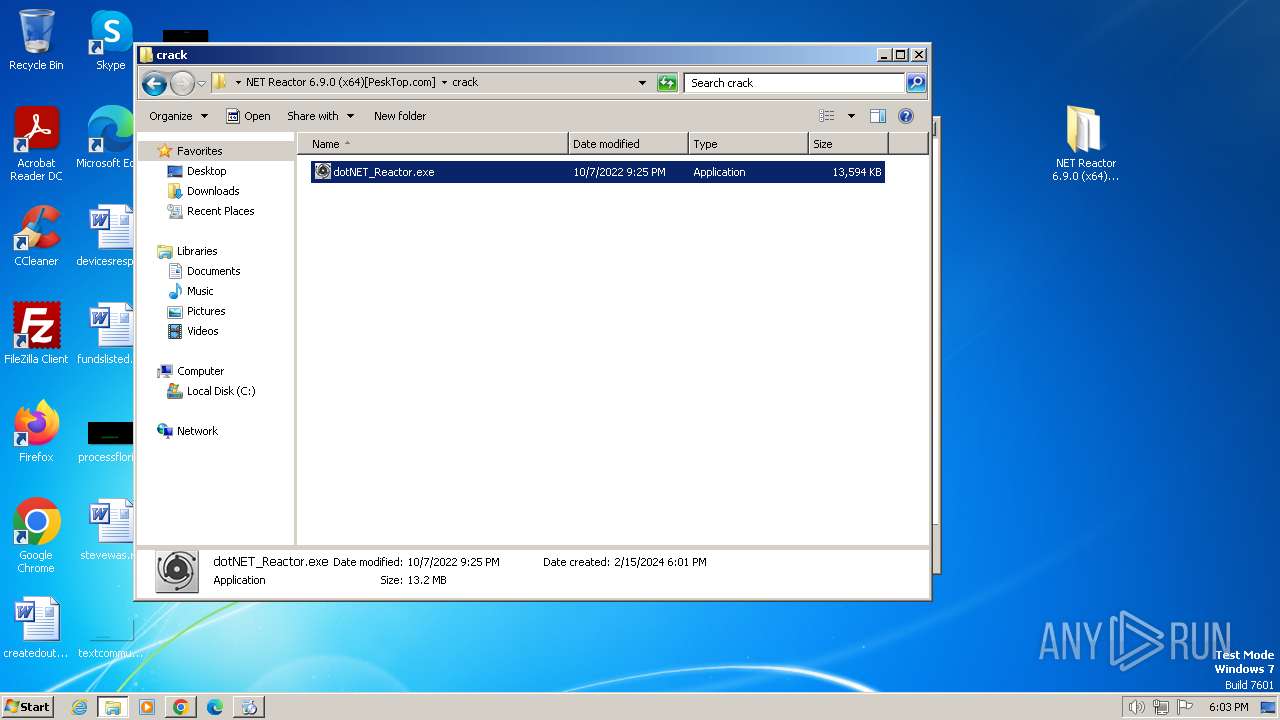
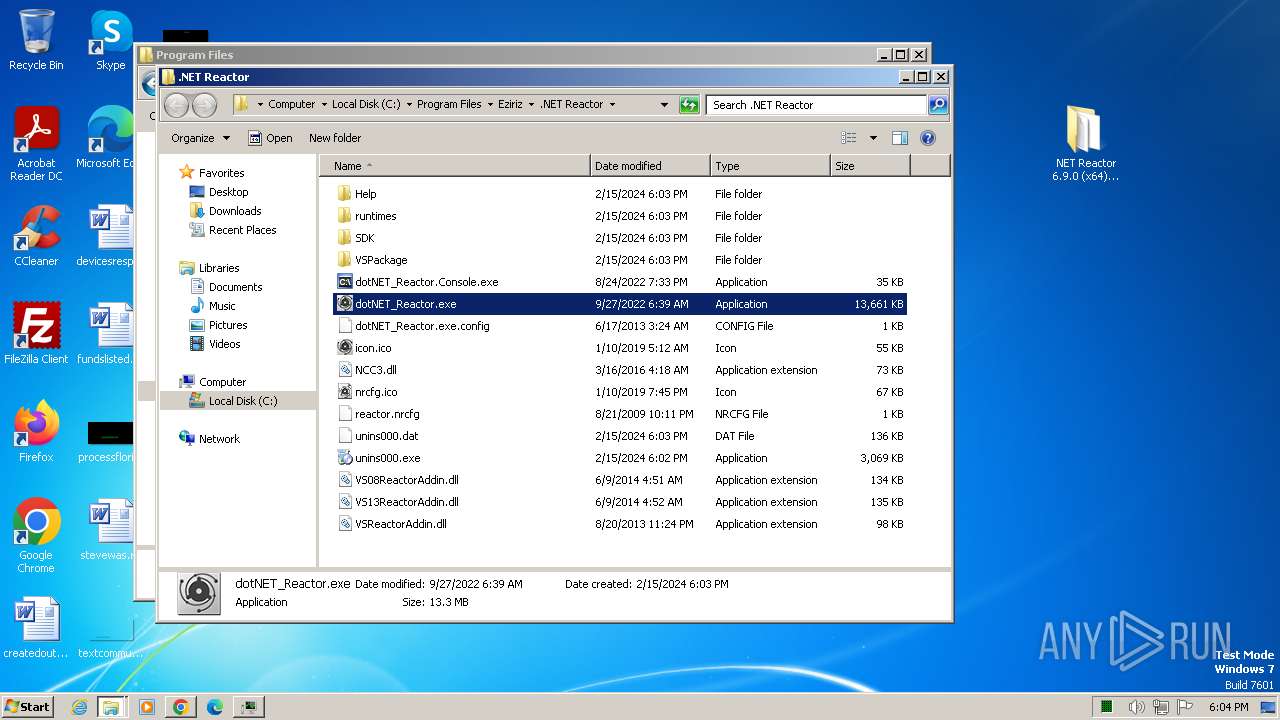
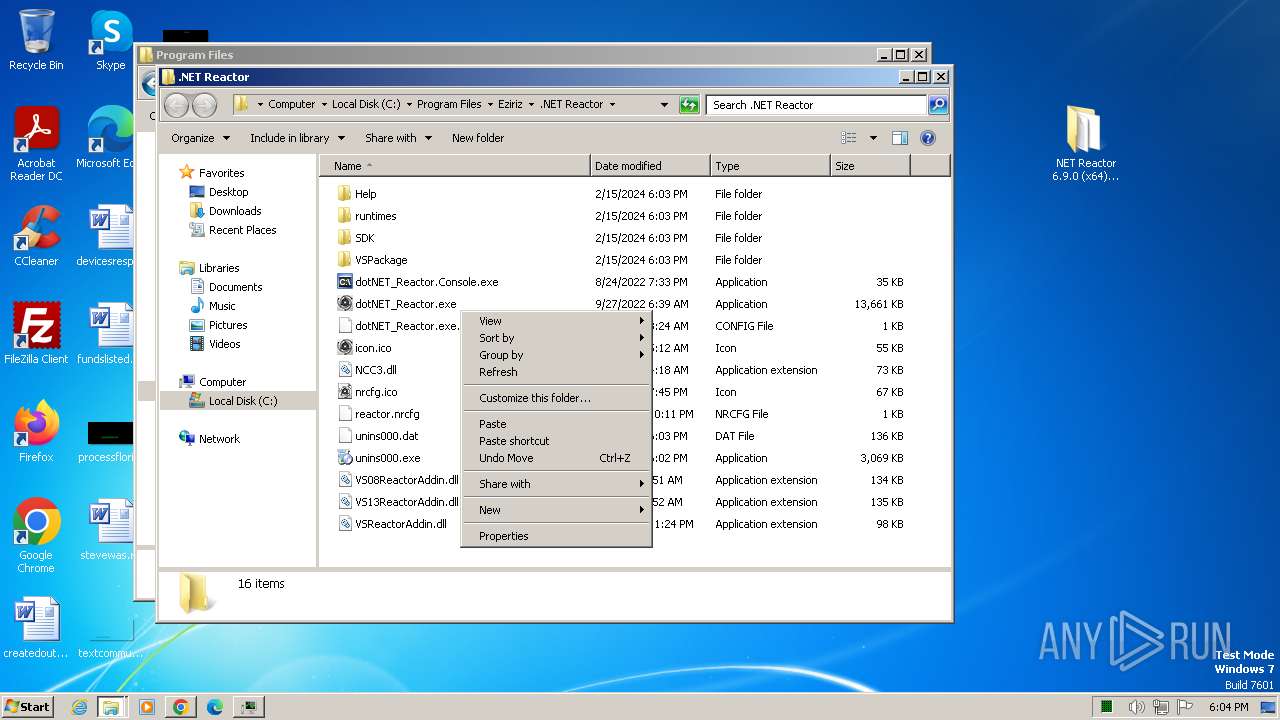
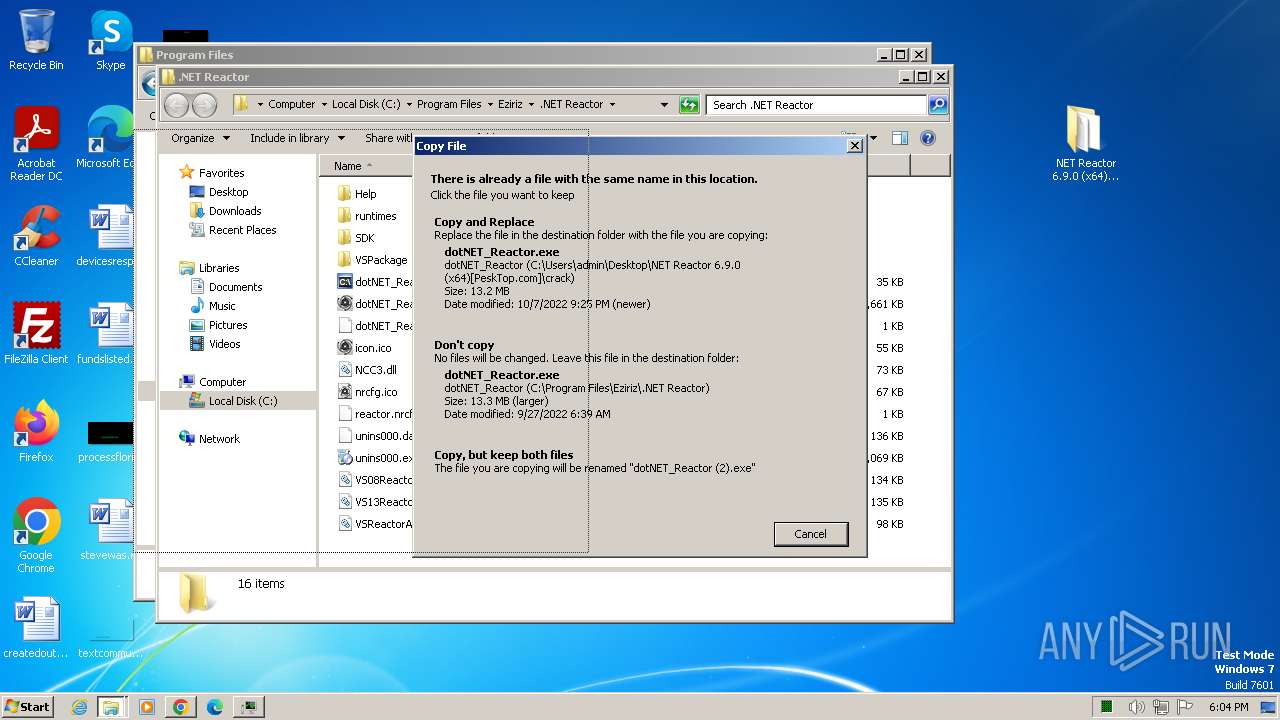
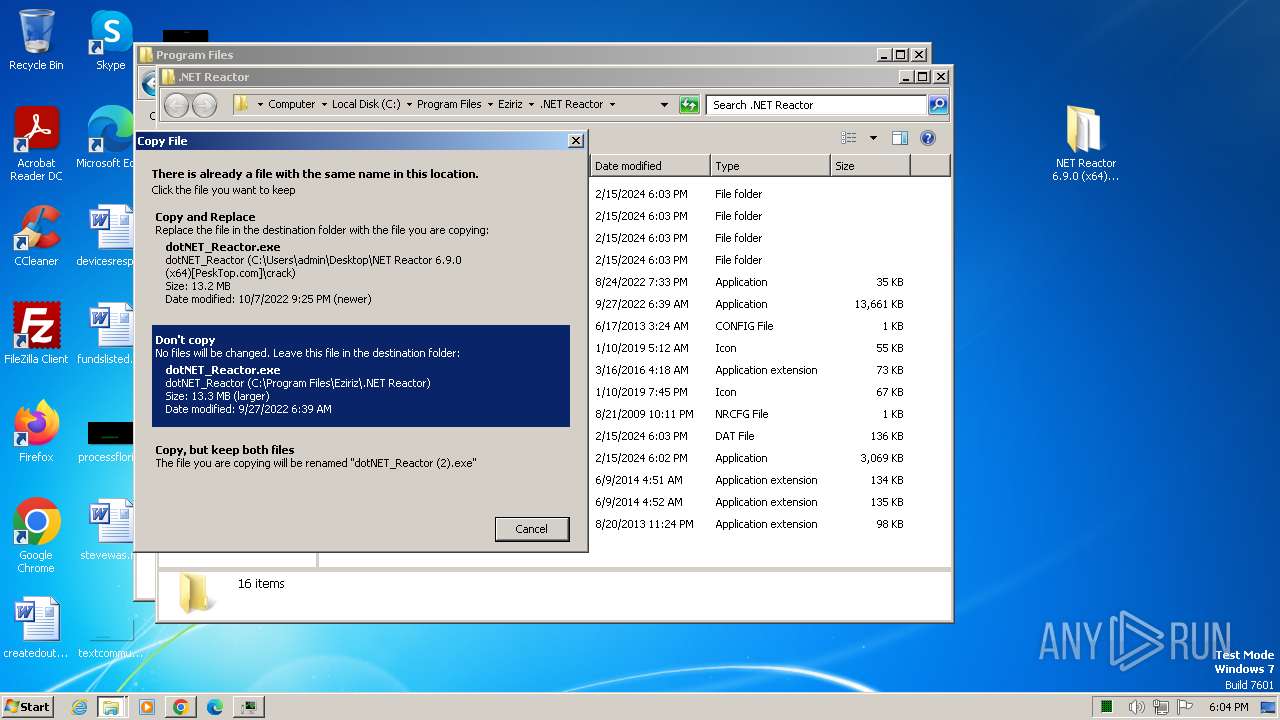
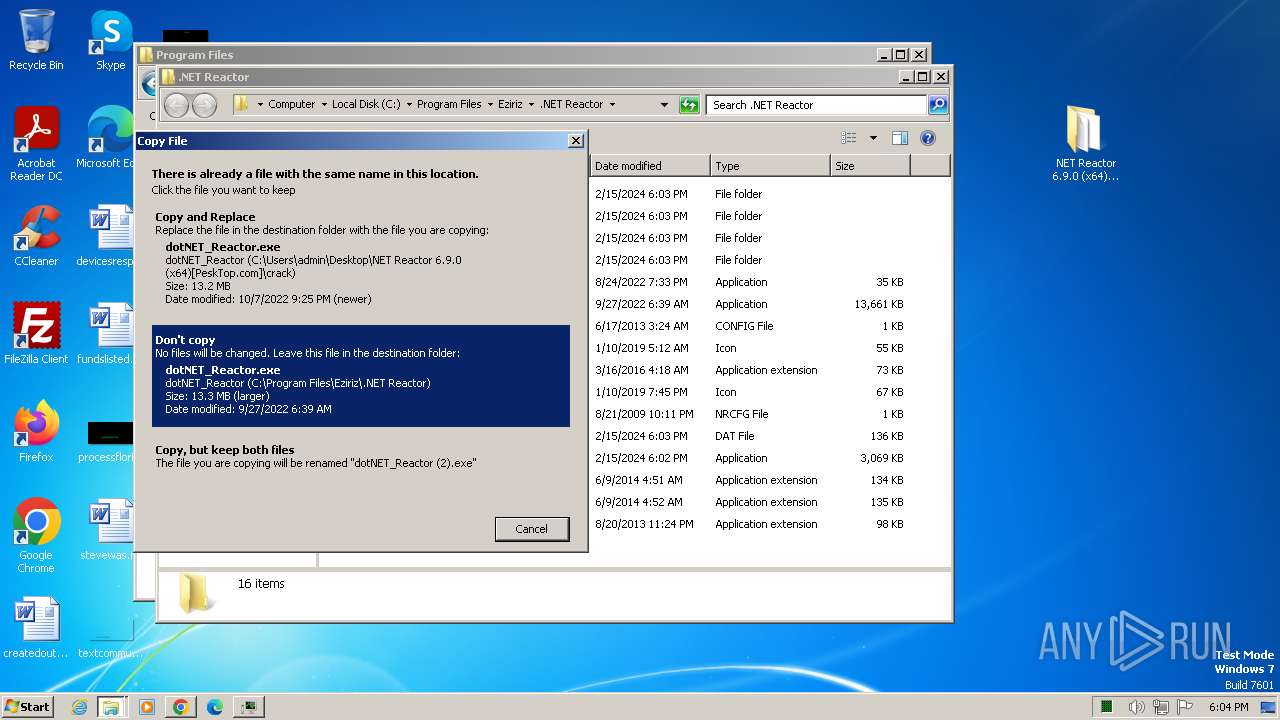
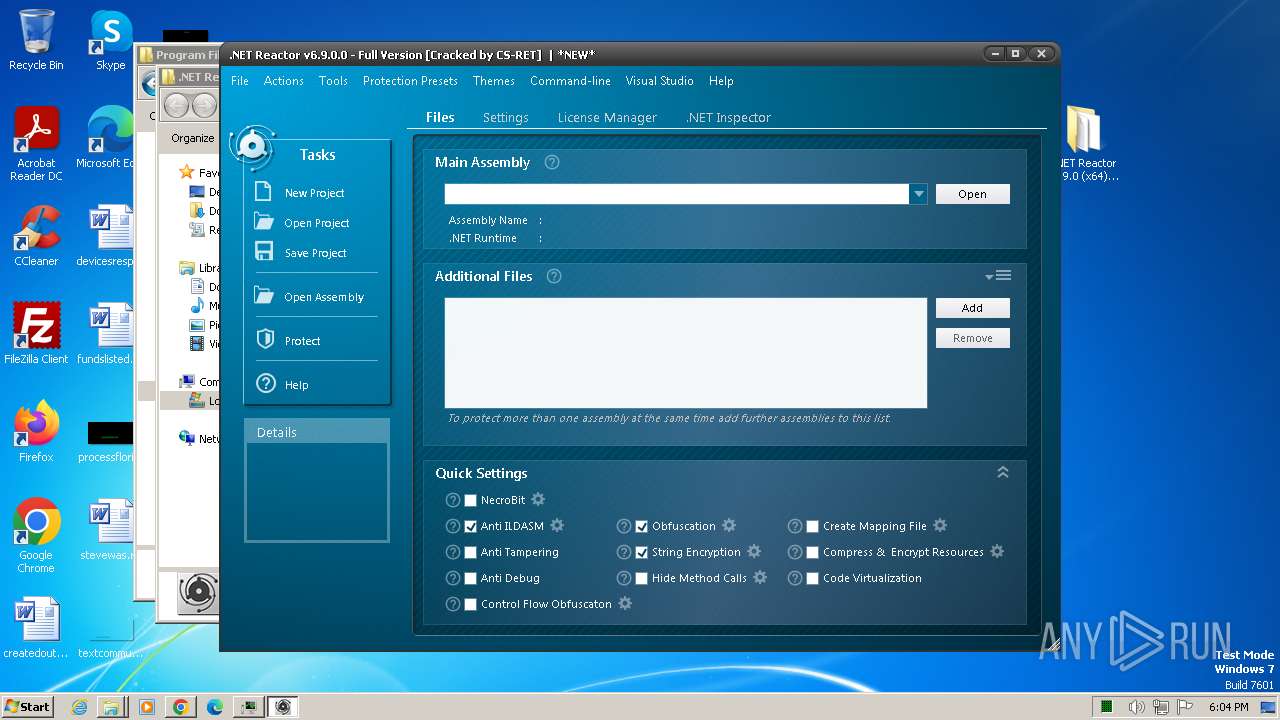
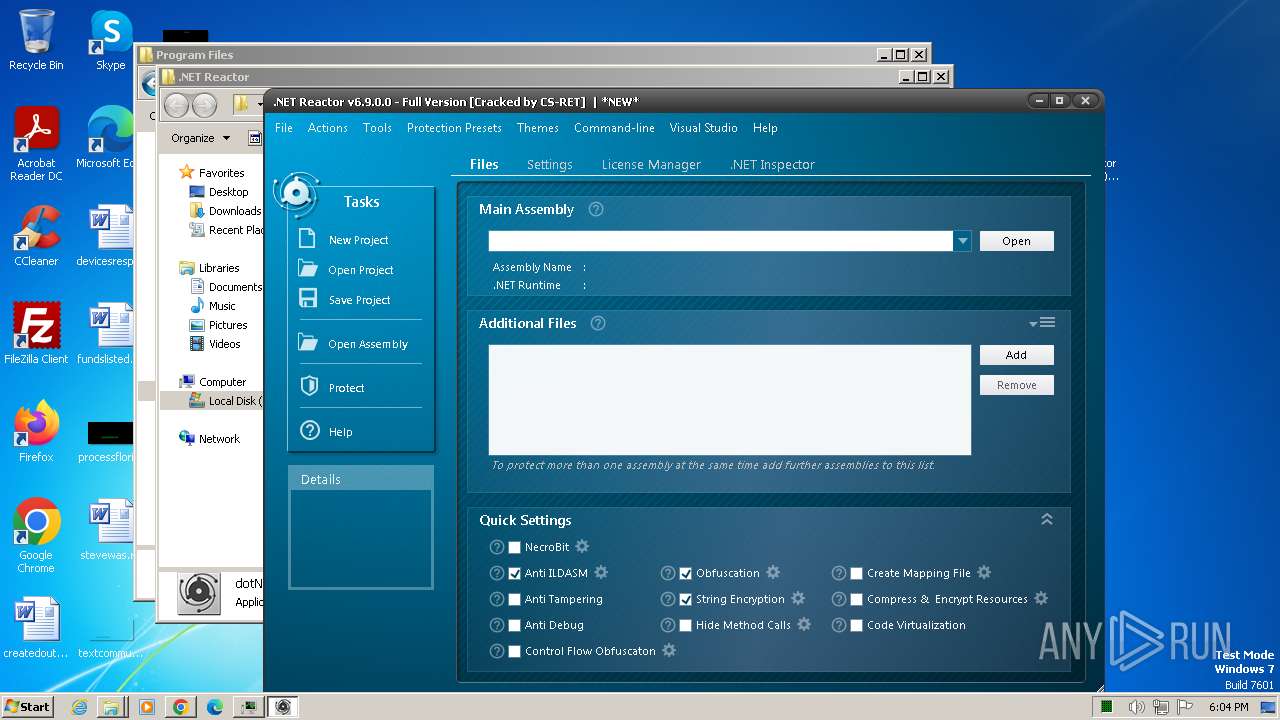
| 884 | "C:\Users\admin\Desktop\NET Reactor 6.9.0 (x64)[PeskTop.com]\crack\dotNET_Reactor.exe" | C:\Users\admin\Desktop\NET Reactor 6.9.0 (x64)[PeskTop.com]\crack\dotNET_Reactor.exe | — | explorer.exe | |||||||||||
User: admin Company: EZIRIZ Integrity Level: MEDIUM Description: .NET Reactor Exit code: 0 Version: 6.9.0.0 Modules
| |||||||||||||||
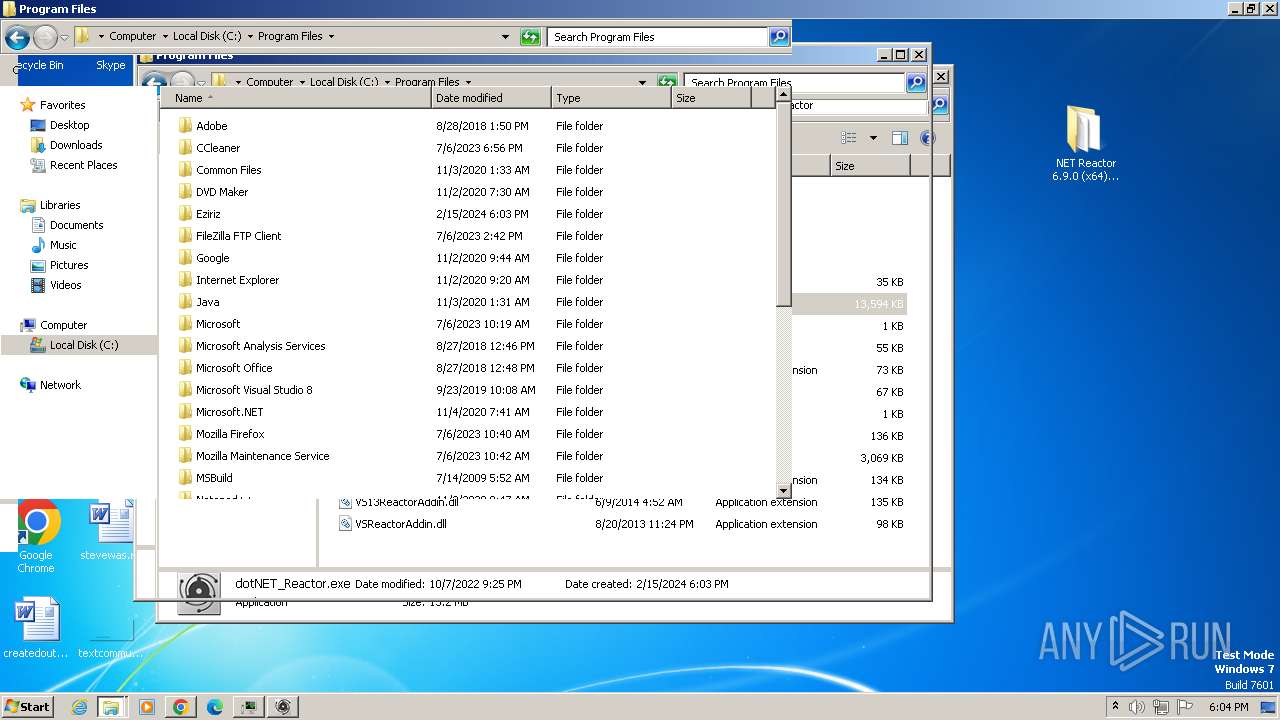
| 992 | "C:\Users\admin\Desktop\NET Reactor 6.9.0 (x64)[PeskTop.com]\setup.exe" | C:\Users\admin\Desktop\NET Reactor 6.9.0 (x64)[PeskTop.com]\setup.exe | explorer.exe | ||||||||||||
User: admin Company: Eziriz Integrity Level: MEDIUM Description: .NET Reactor Setup Exit code: 0 Version: 6.9.0.0 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3720 --field-trial-handle=1428,i,12861036811296109975,16540313707963390949,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1020 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1648 --field-trial-handle=1428,i,12861036811296109975,16540313707963390949,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3616 --field-trial-handle=1428,i,12861036811296109975,16540313707963390949,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
32 346
Read events
32 039
Write events
281
Delete events
26
Modification events
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
171
Suspicious files
122
Text files
529
Unknown types
45
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17ef03.TMP | — | |
MD5:— | SHA256:— | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF17ef22.TMP | text | |
MD5:ADB669AB4CD1C63883C64FB0DBA2C7DA | SHA256:18BFF89047EC5B122573D089B3DC7A7DD14A5A7A515B2D8141584B41E723253F | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF17f099.TMP | text | |
MD5:C5B082BC8EA6A9BD1DC6782C00A79605 | SHA256:6168A9E585264DE05DEE1B67427B1BC277F1B83B9297184EFACC5D3BB061ABDE | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF17f57b.TMP | — | |
MD5:— | SHA256:— | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF180a4c.TMP | — | |
MD5:— | SHA256:— | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
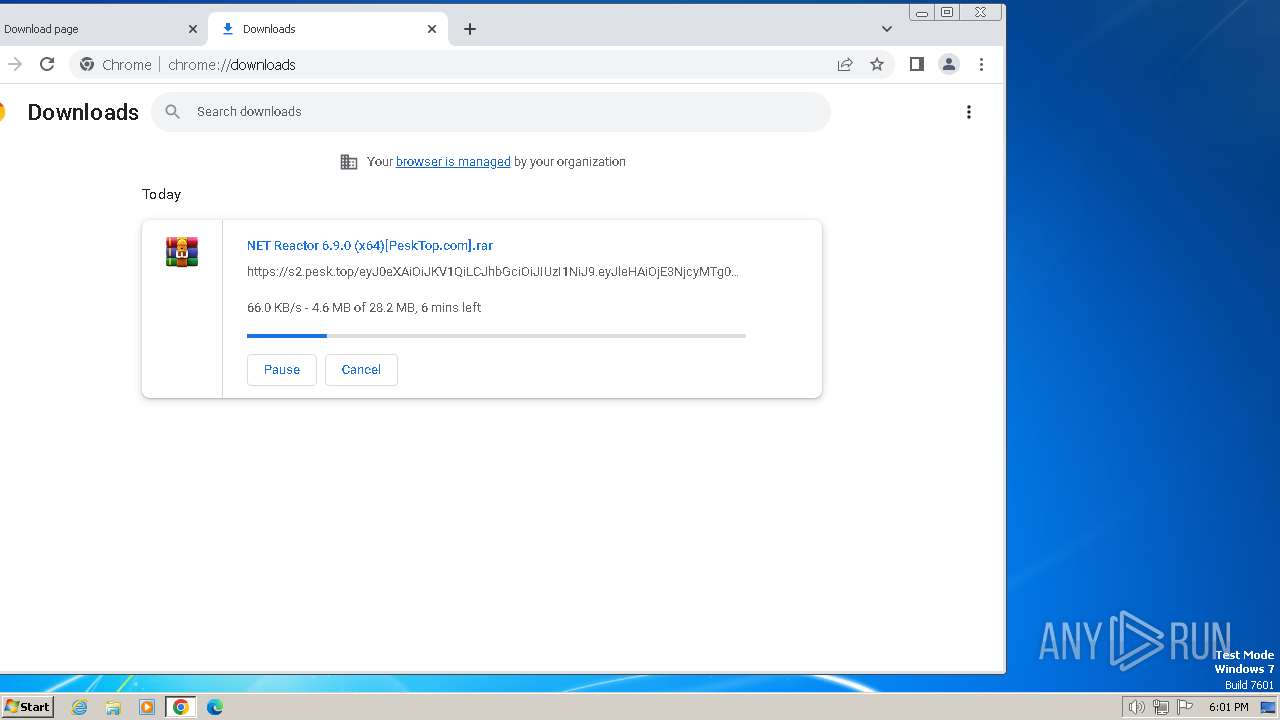
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
42
DNS requests
48
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | unknown |
856 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | binary | 3.07 Kb | unknown |
3256 | dotNET_Reactor.exe | GET | 200 | 81.169.145.150:80 | http://www.eziriz.com/downloads/version.txt | unknown | text | 7 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3240 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
2752 | chrome.exe | 64.233.184.84:443 | accounts.google.com | GOOGLE | US | unknown |
2752 | chrome.exe | 104.21.14.3:443 | pesktop.com | CLOUDFLARENET | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2752 | chrome.exe | 35.190.80.1:443 | a.nel.cloudflare.com | GOOGLE | US | unknown |
2752 | chrome.exe | 172.67.133.149:443 | pesktop.com | CLOUDFLARENET | US | unknown |
2752 | chrome.exe | 142.250.181.234:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
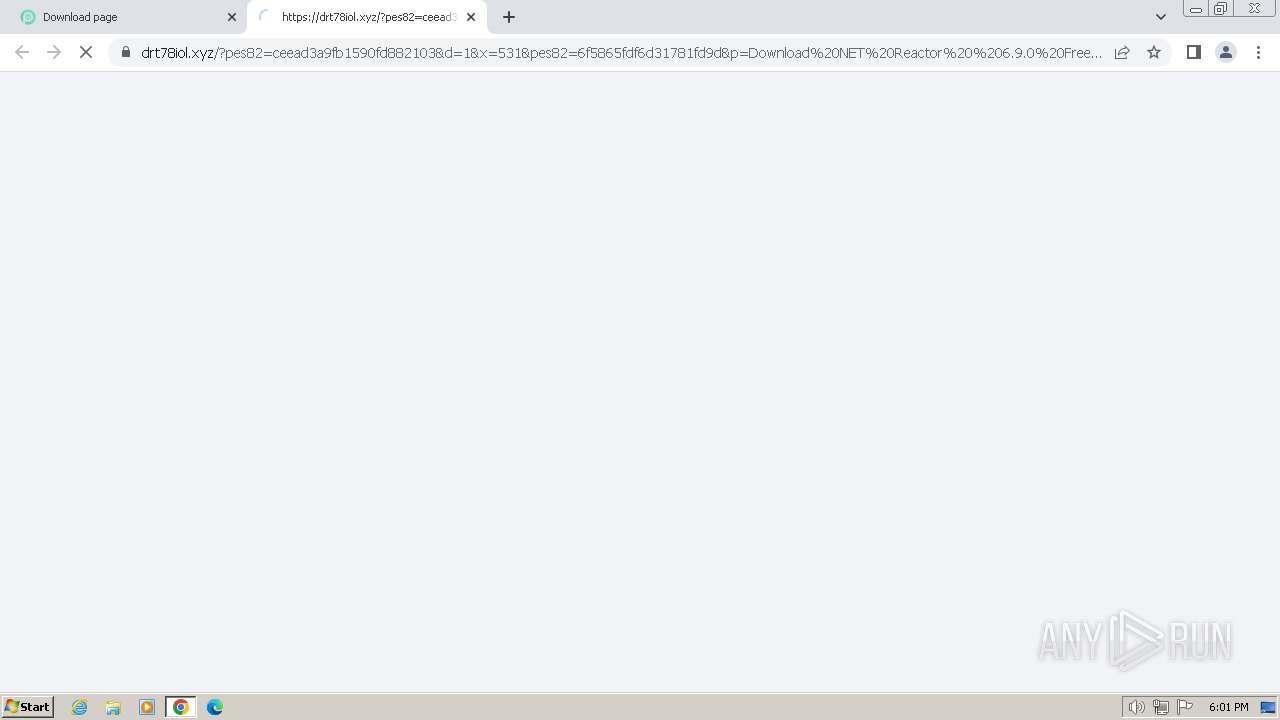
2752 | chrome.exe | 188.114.96.3:443 | drt78iol.xyz | CLOUDFLARENET | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
pesktop.com |
| unknown |
analytics.pesktop.com |
| unknown |
a.nel.cloudflare.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
drt78iol.xyz |
| unknown |
href.li |
| shared |
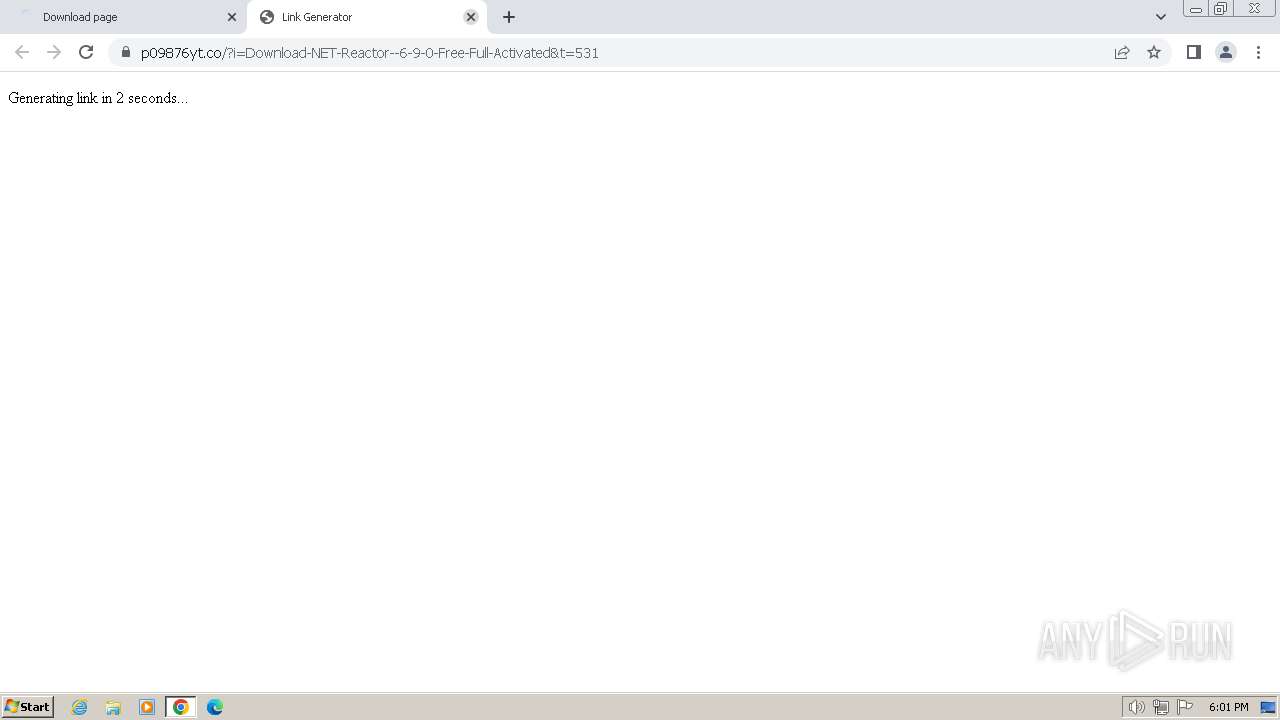
p09876yt.co |
| unknown |
www.google.com |
| whitelisted |
s2.pesk.top |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2752 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
2752 | chrome.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
3256 | dotNET_Reactor.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] Received IP address from server as result of HTTP request |
5 ETPRO signatures available at the full report
Process | Message |
|---|---|
msedge.exe | [0215/180511.817:ERROR:exception_handler_server.cc(527)] ConnectNamedPipe: The pipe is being closed. (0xE8)
|