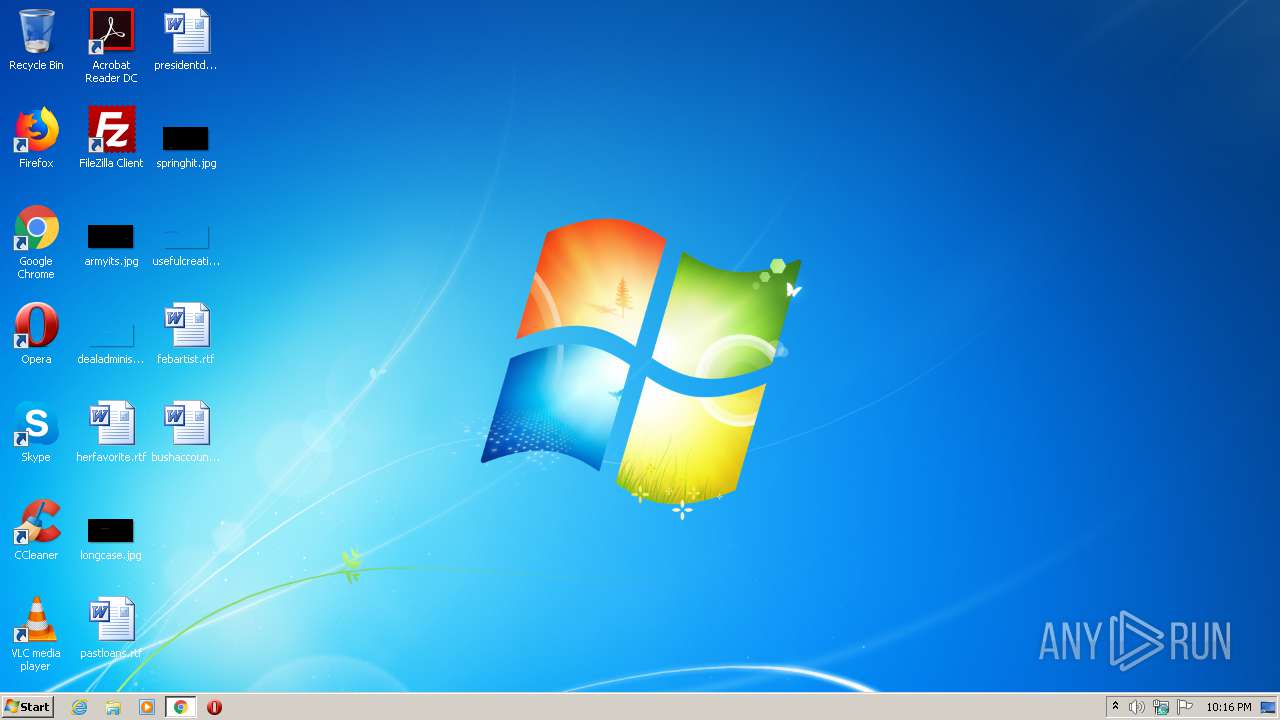
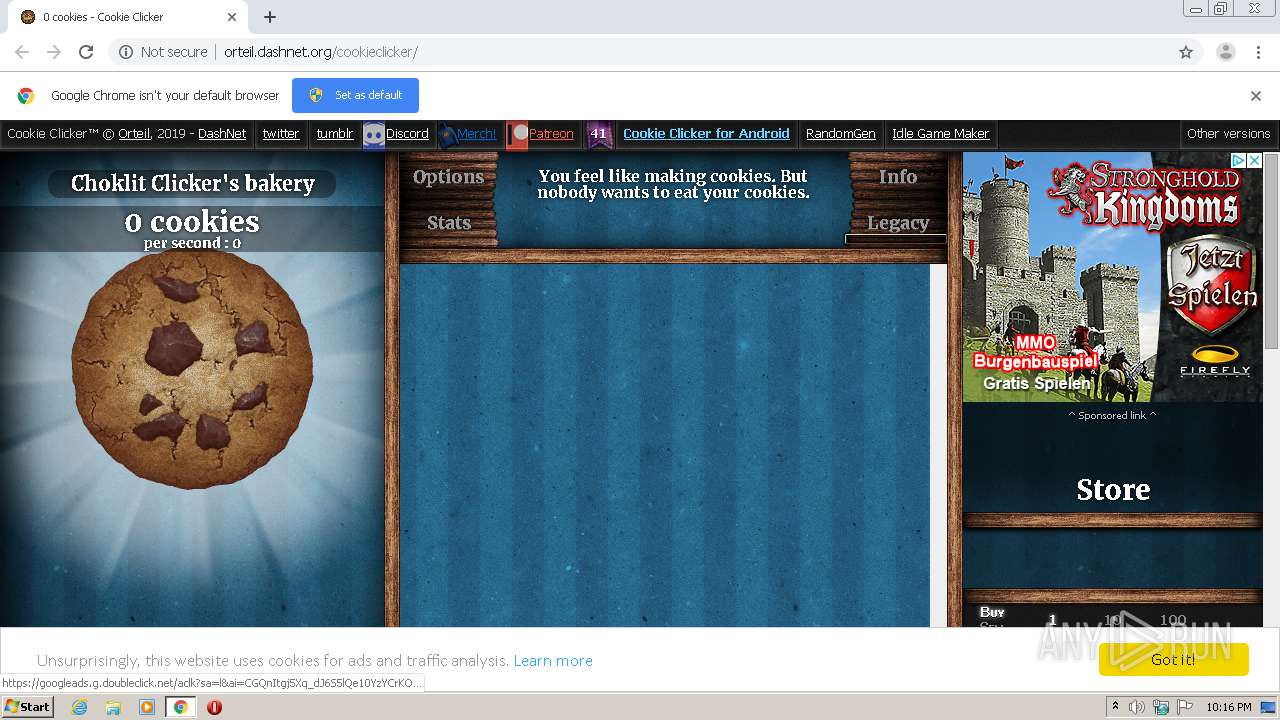
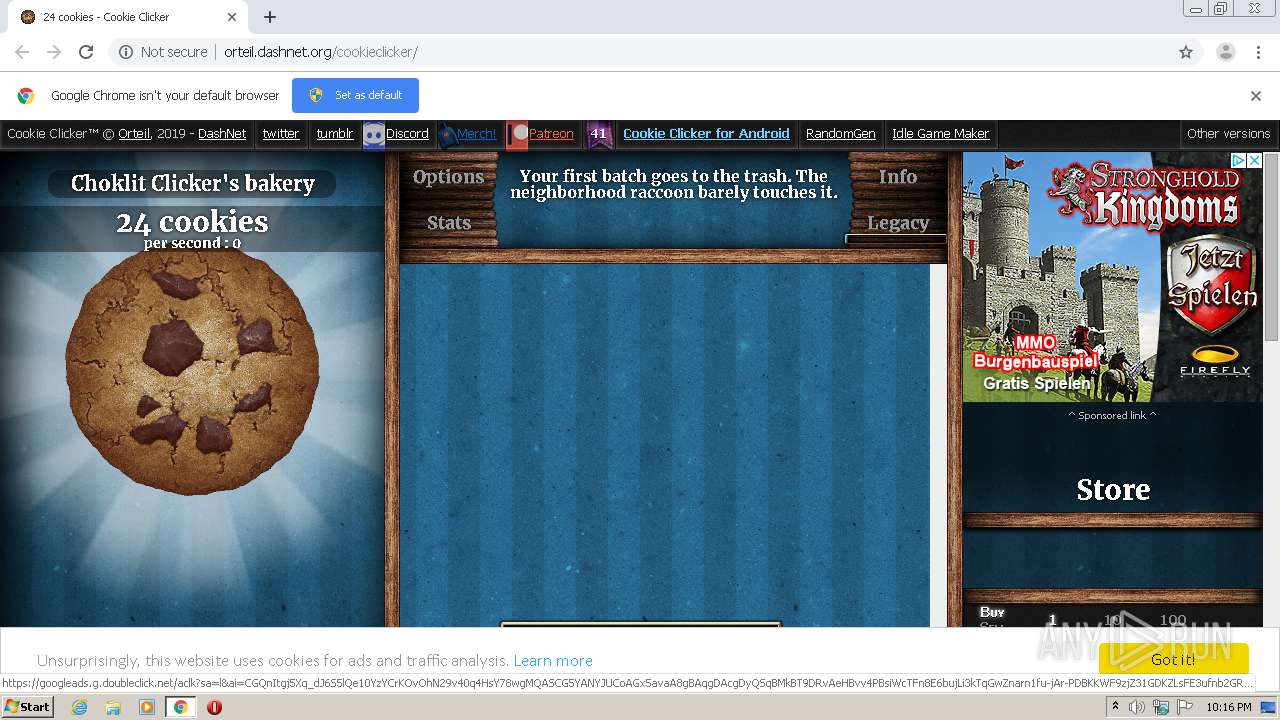
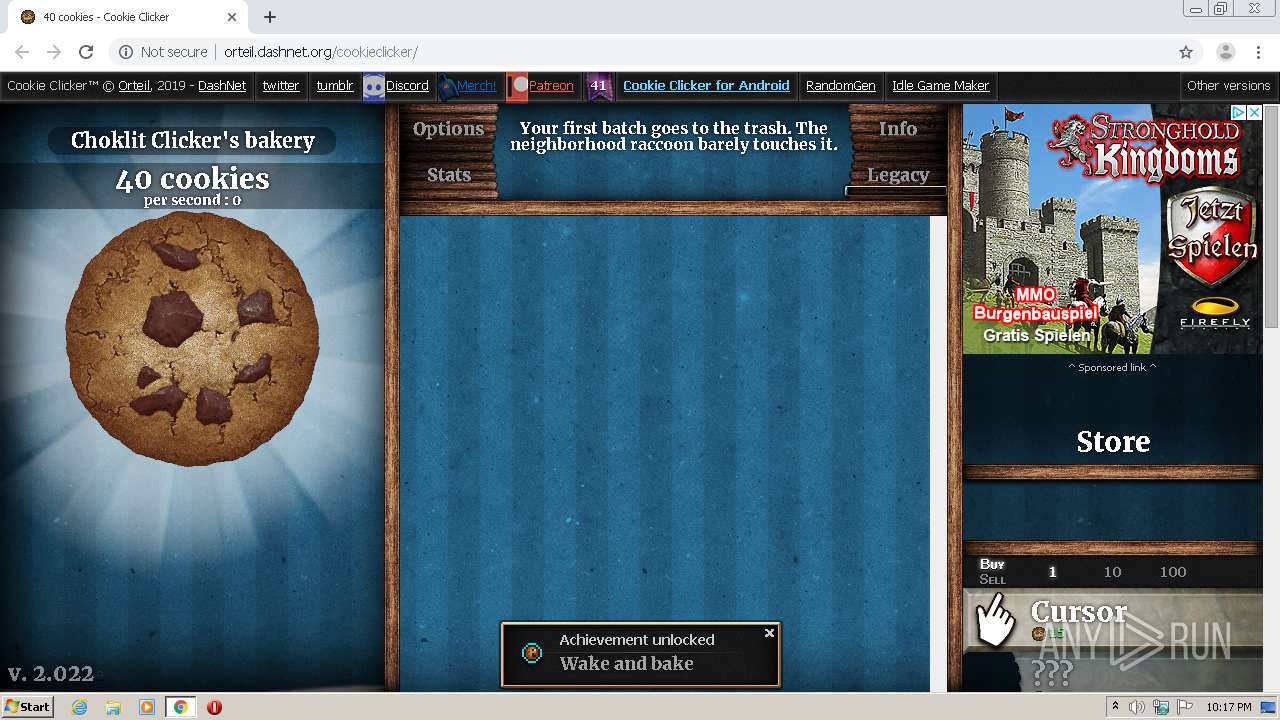
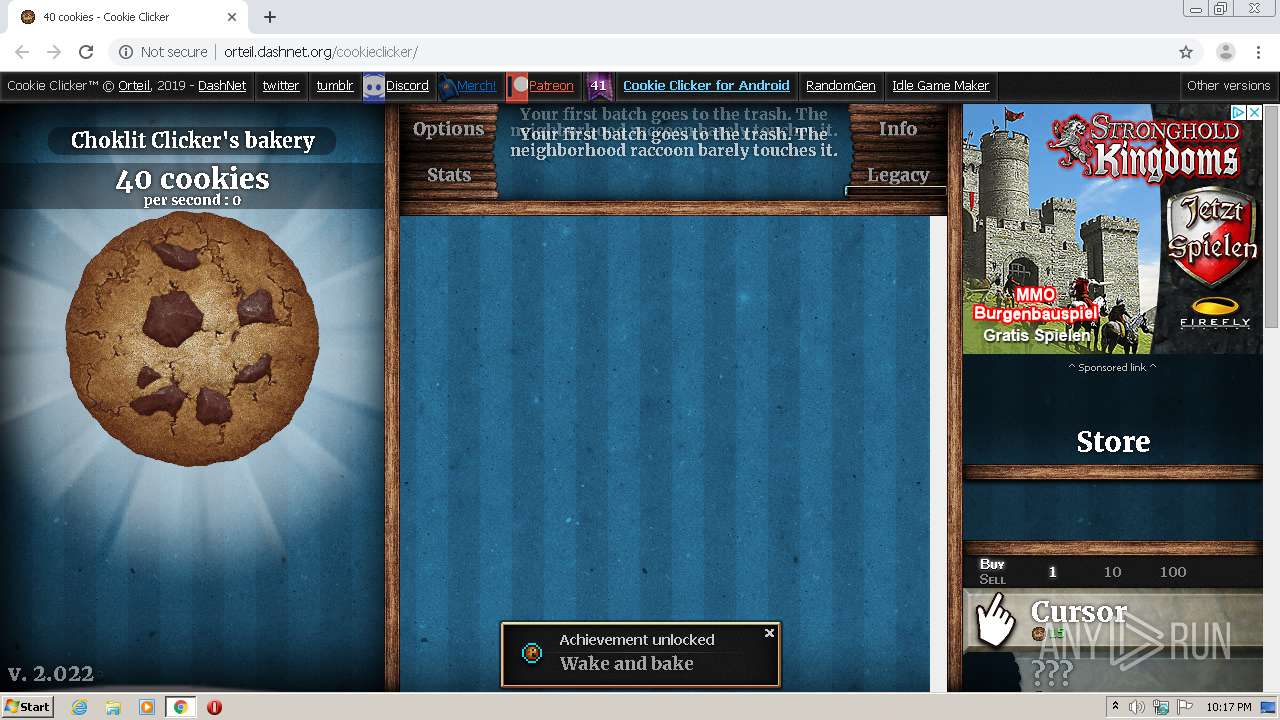
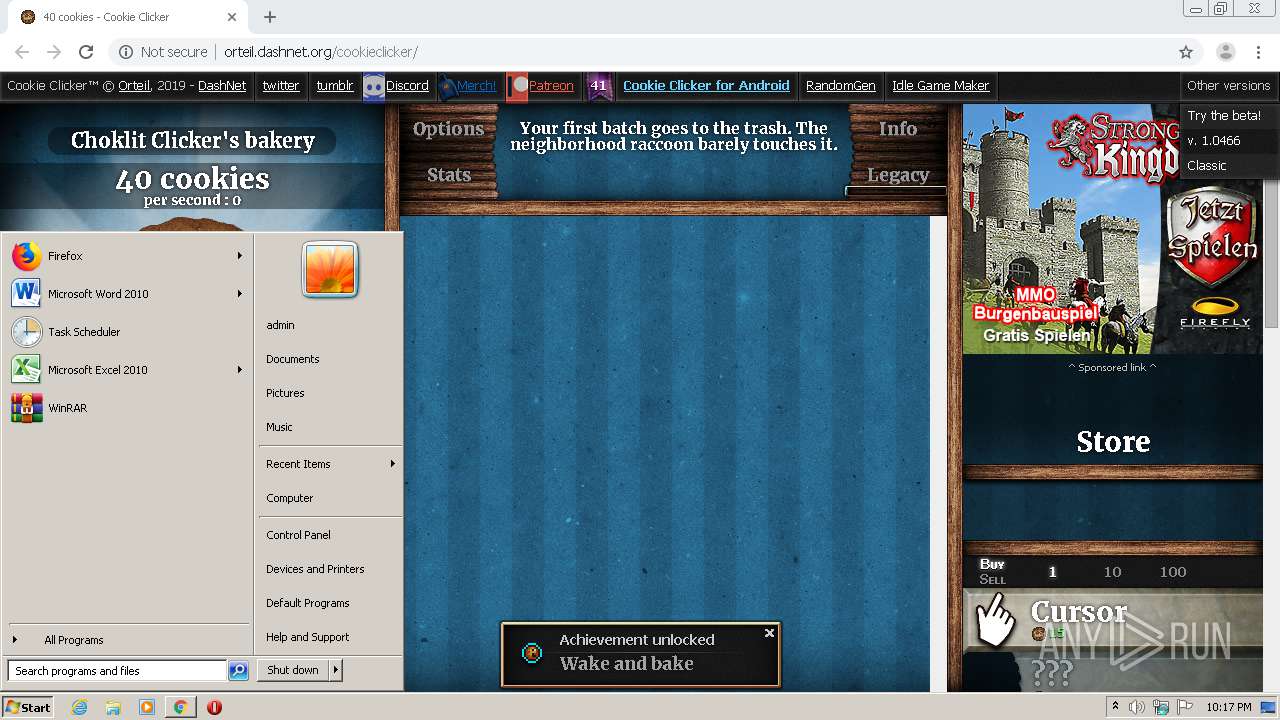
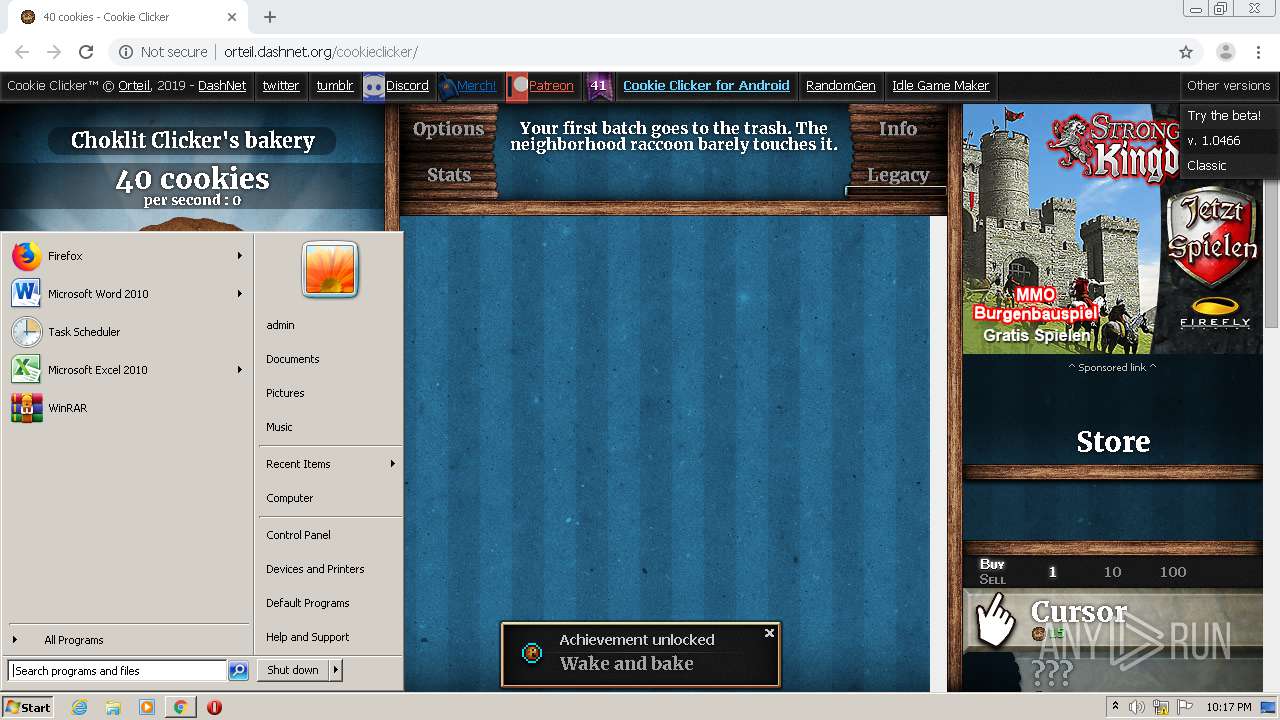
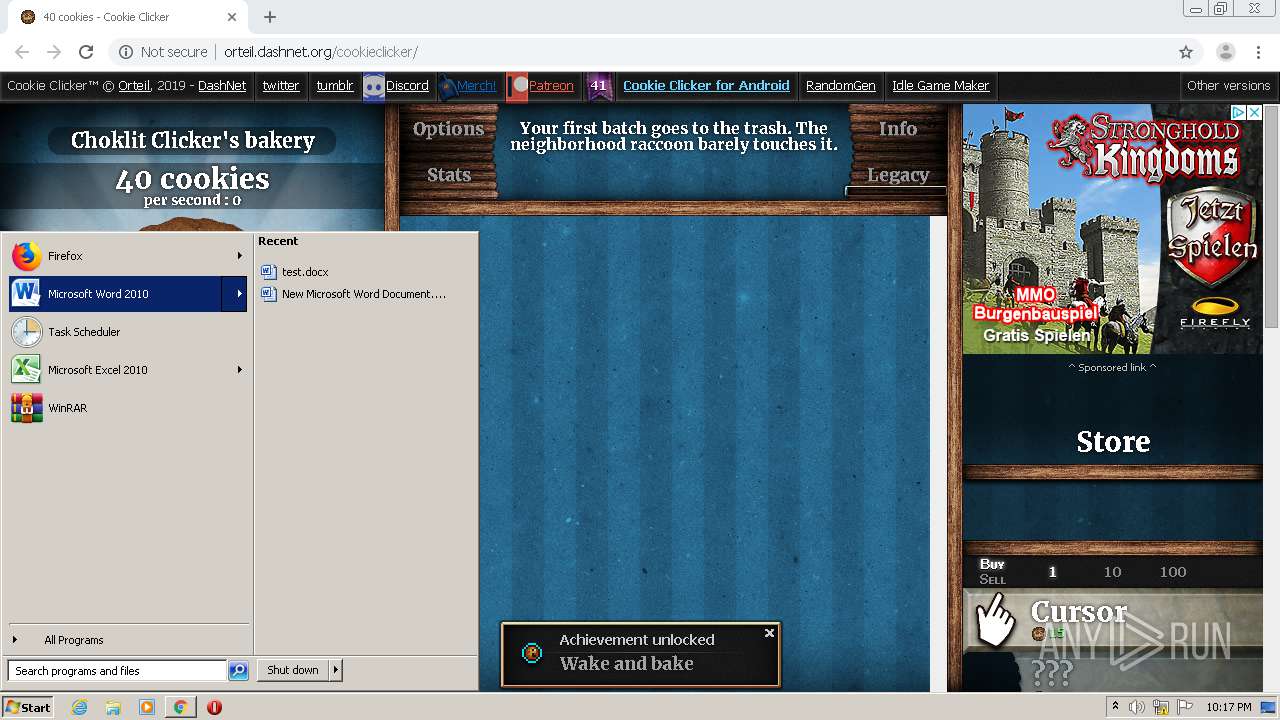
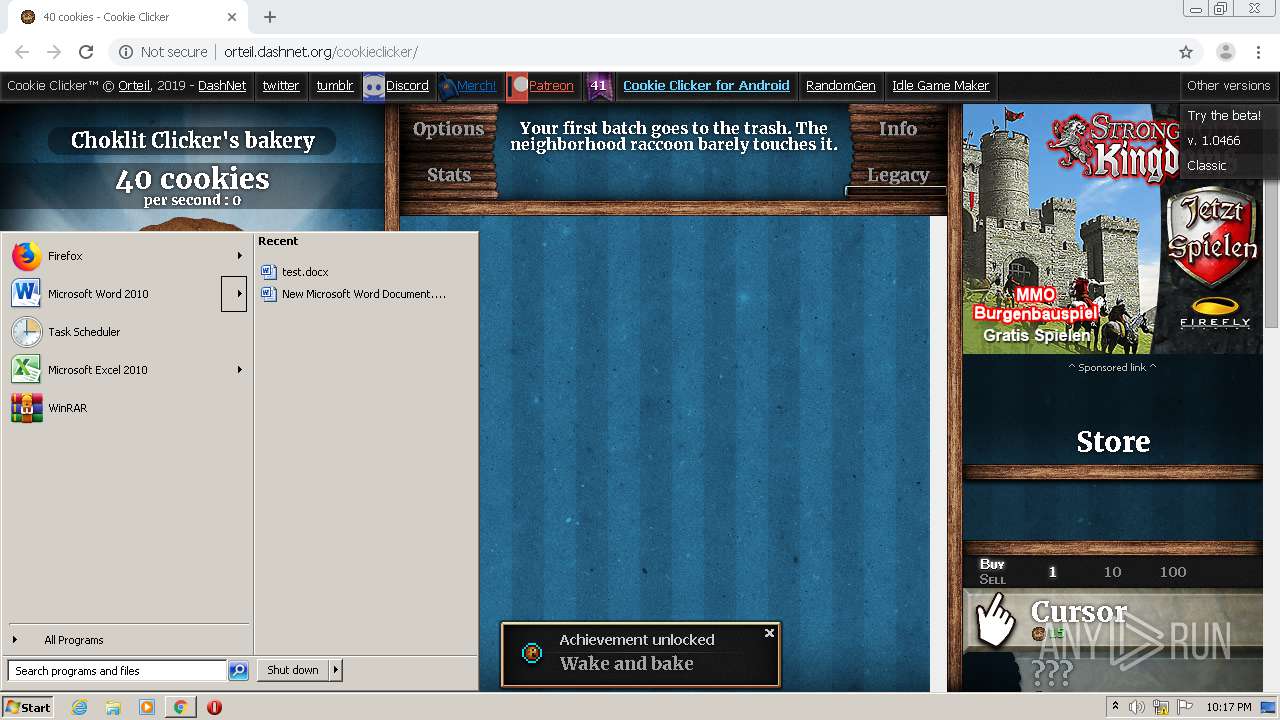
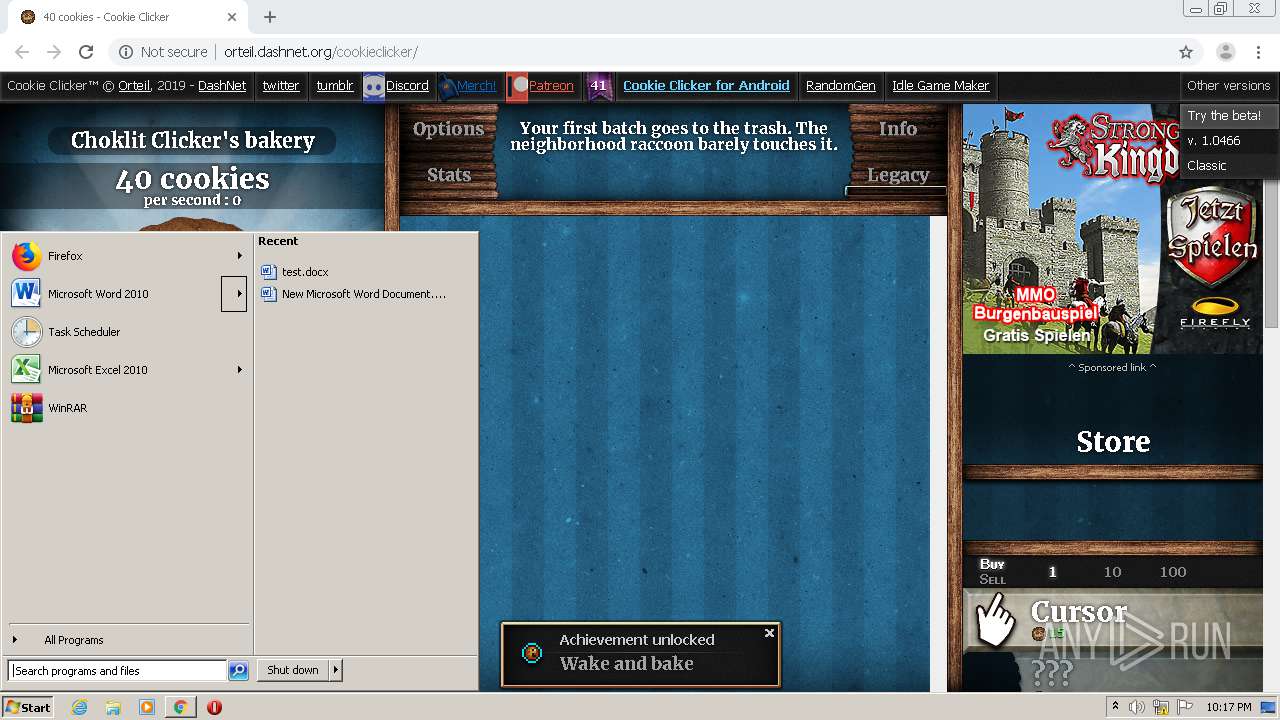
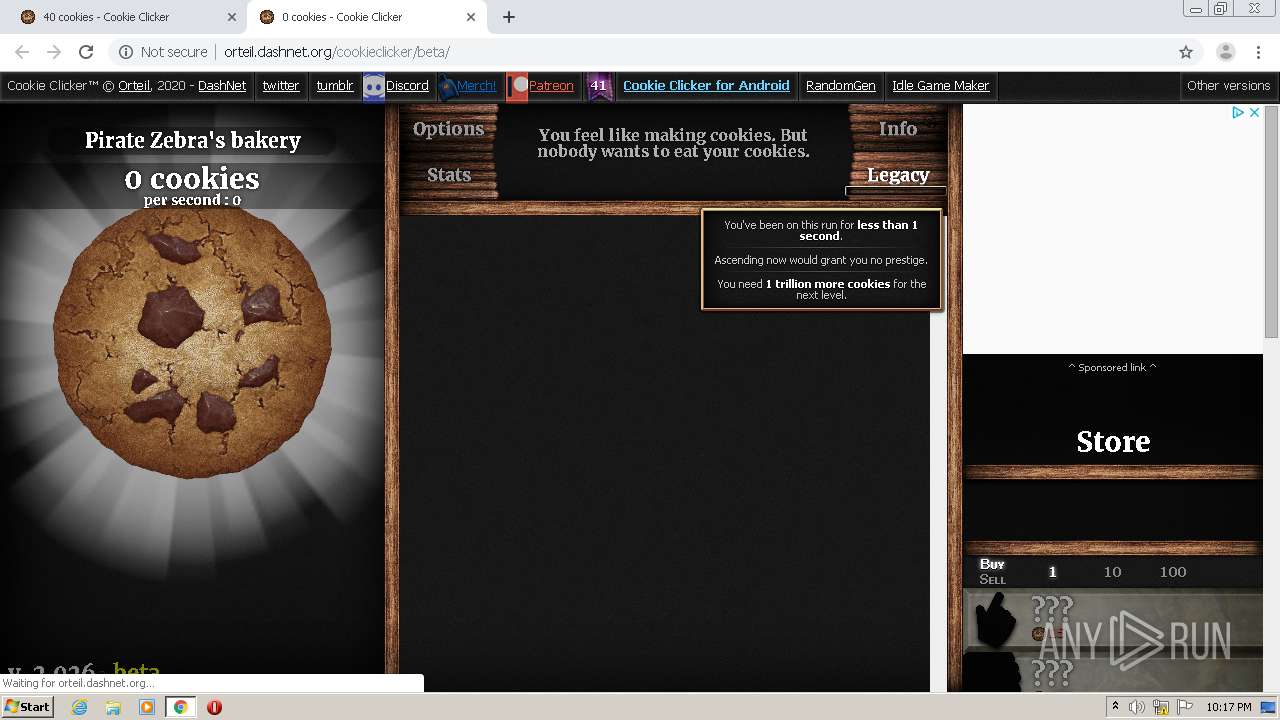
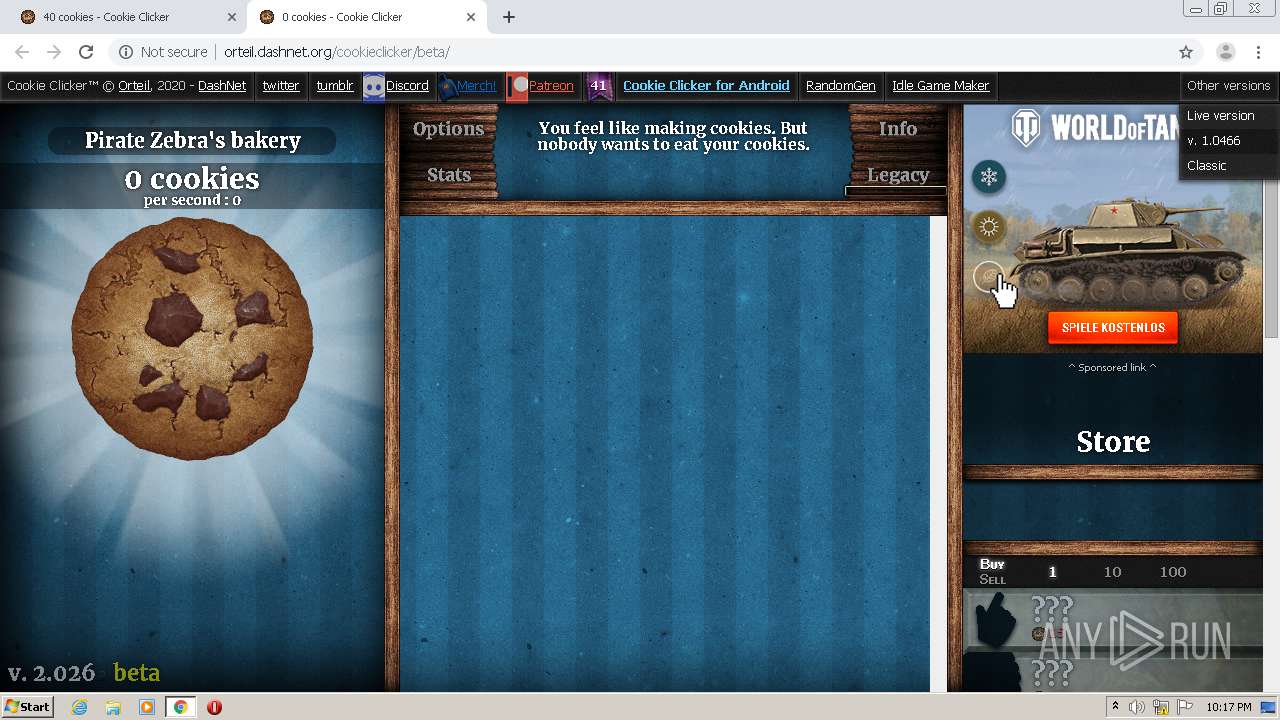
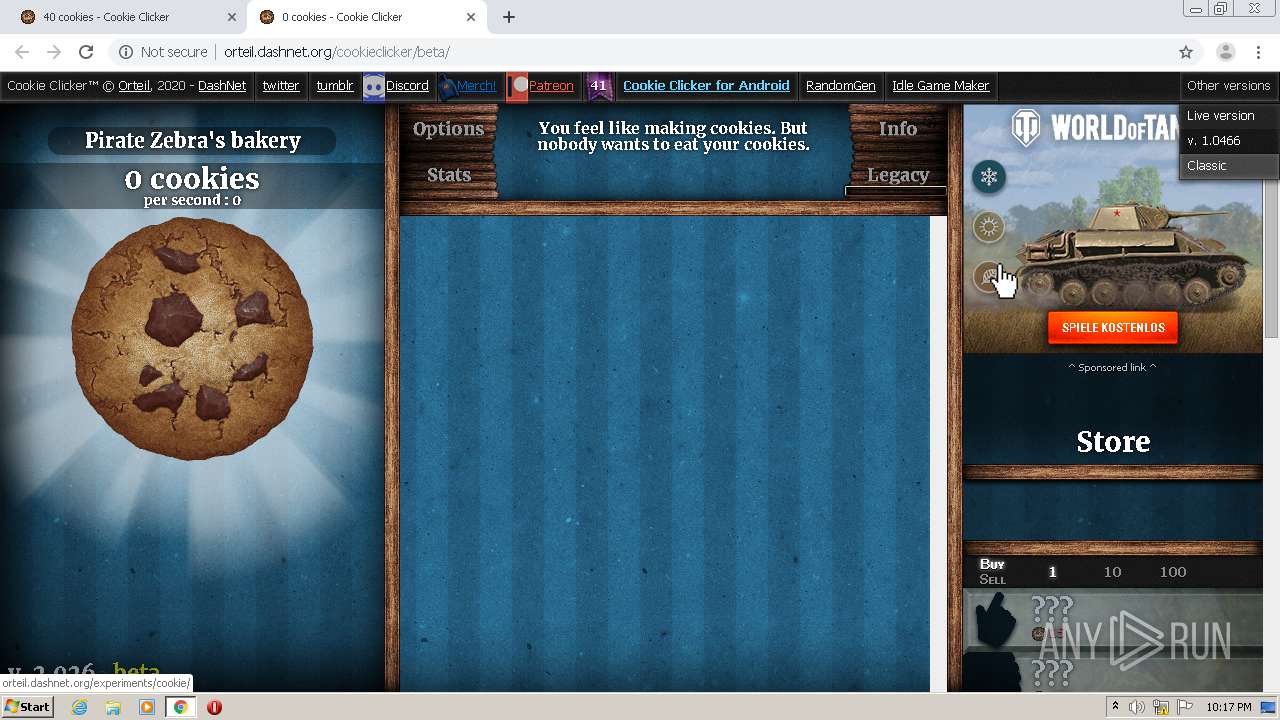
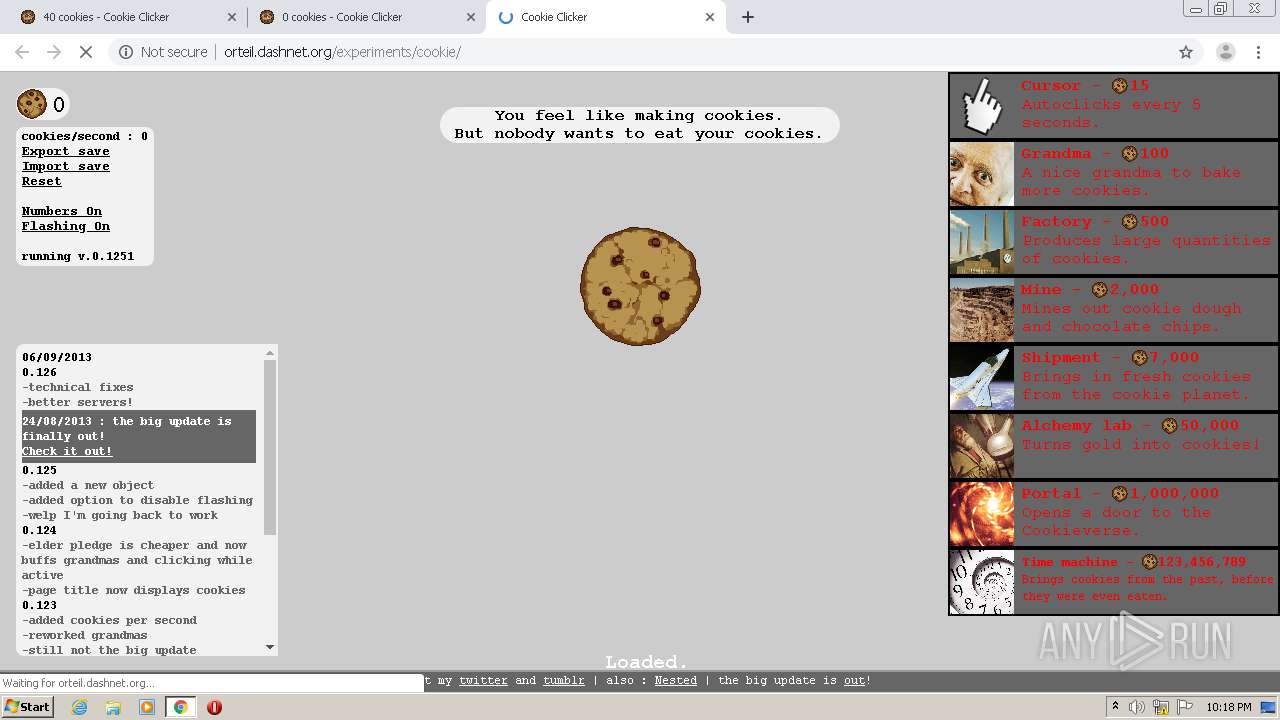
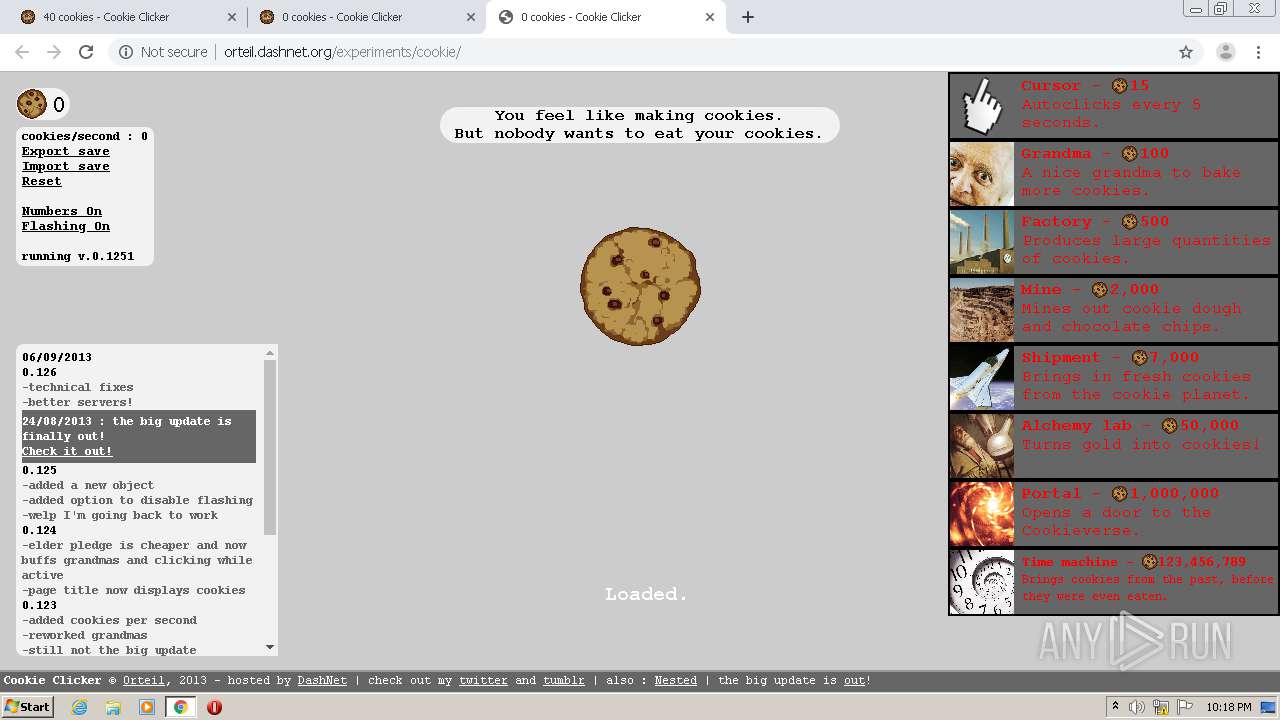
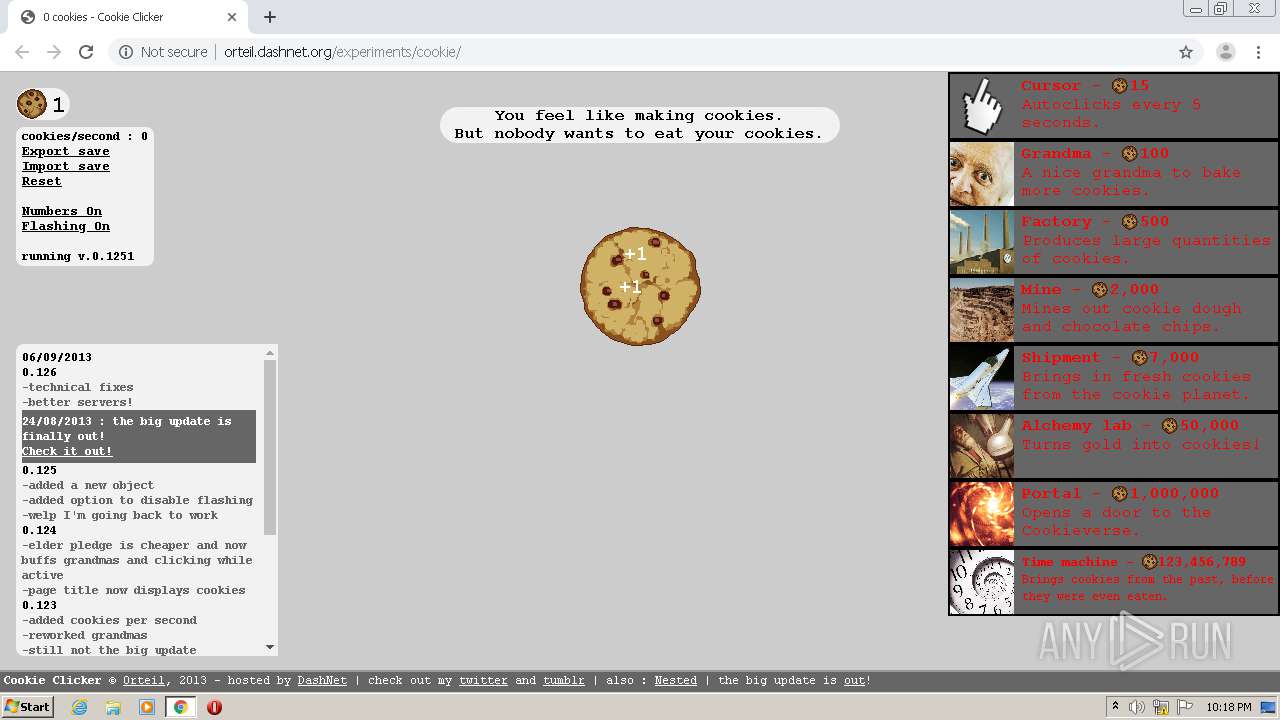
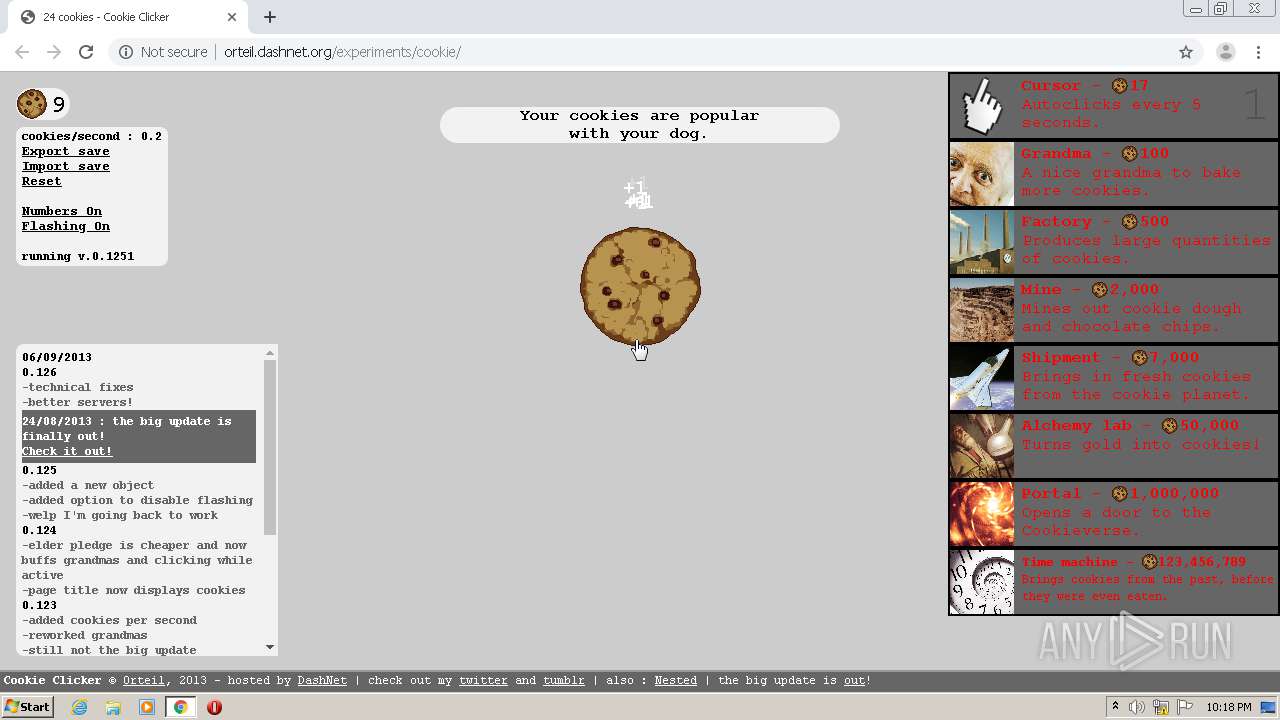
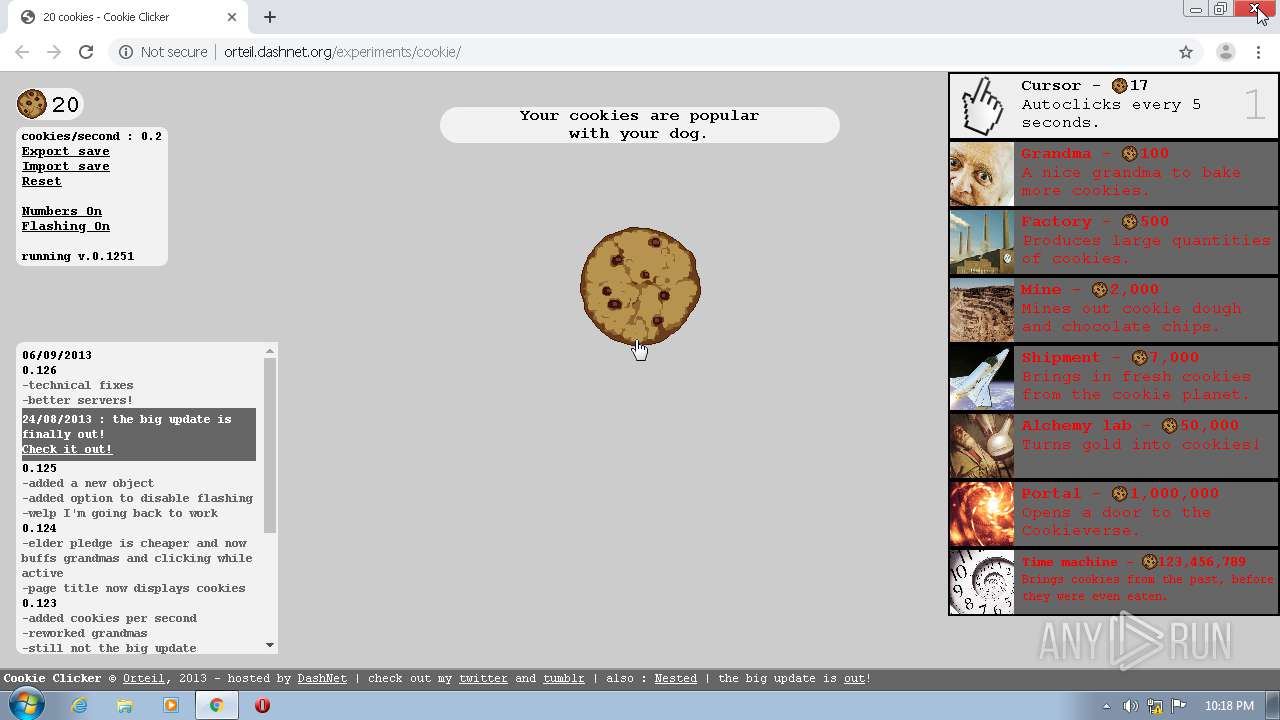
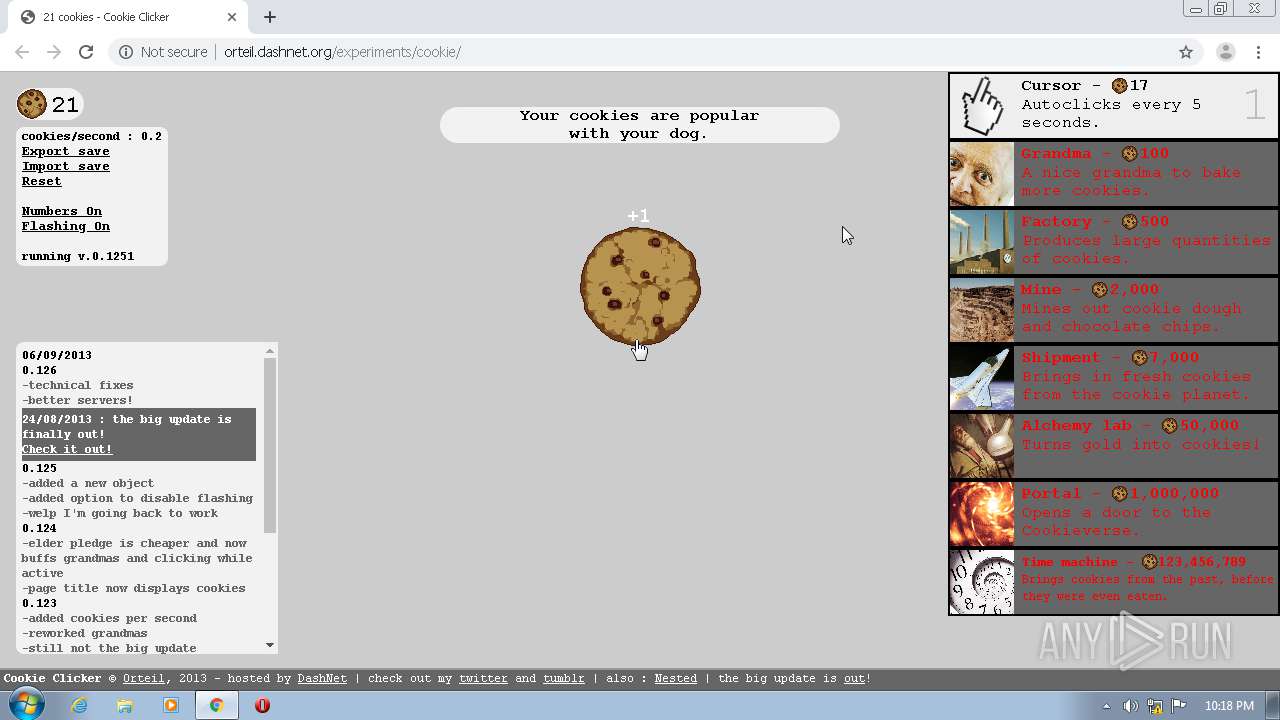
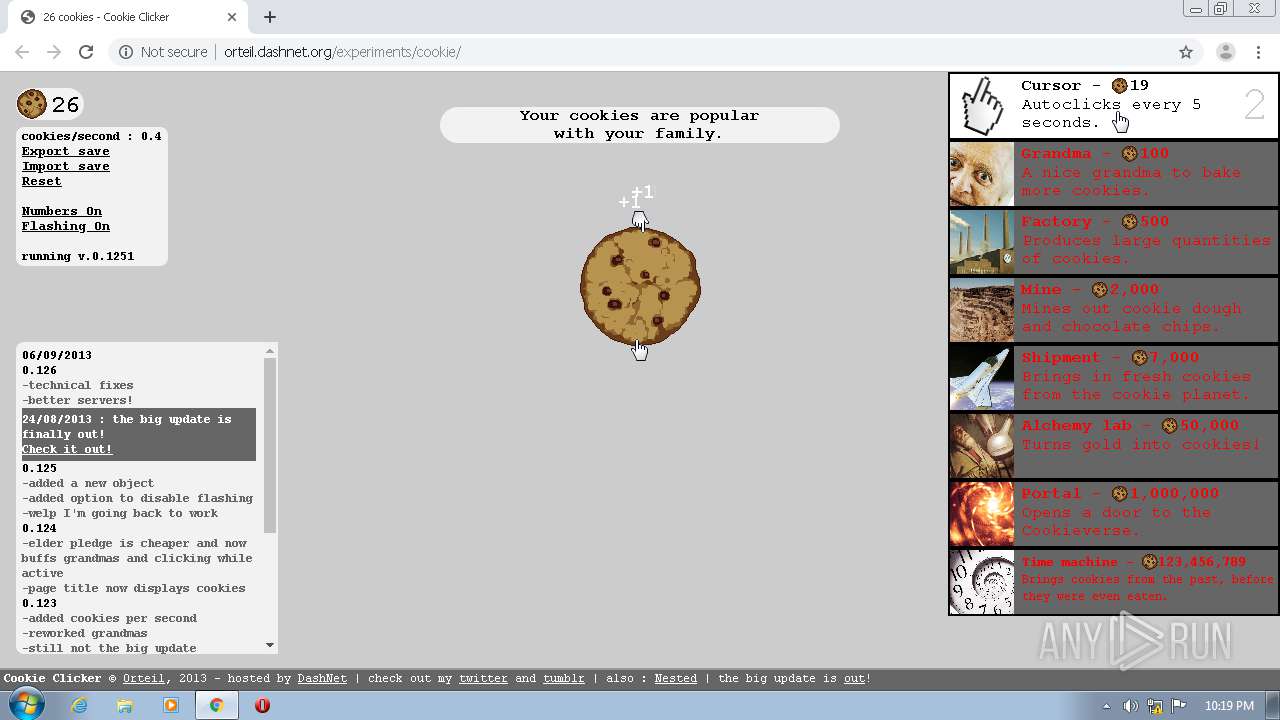
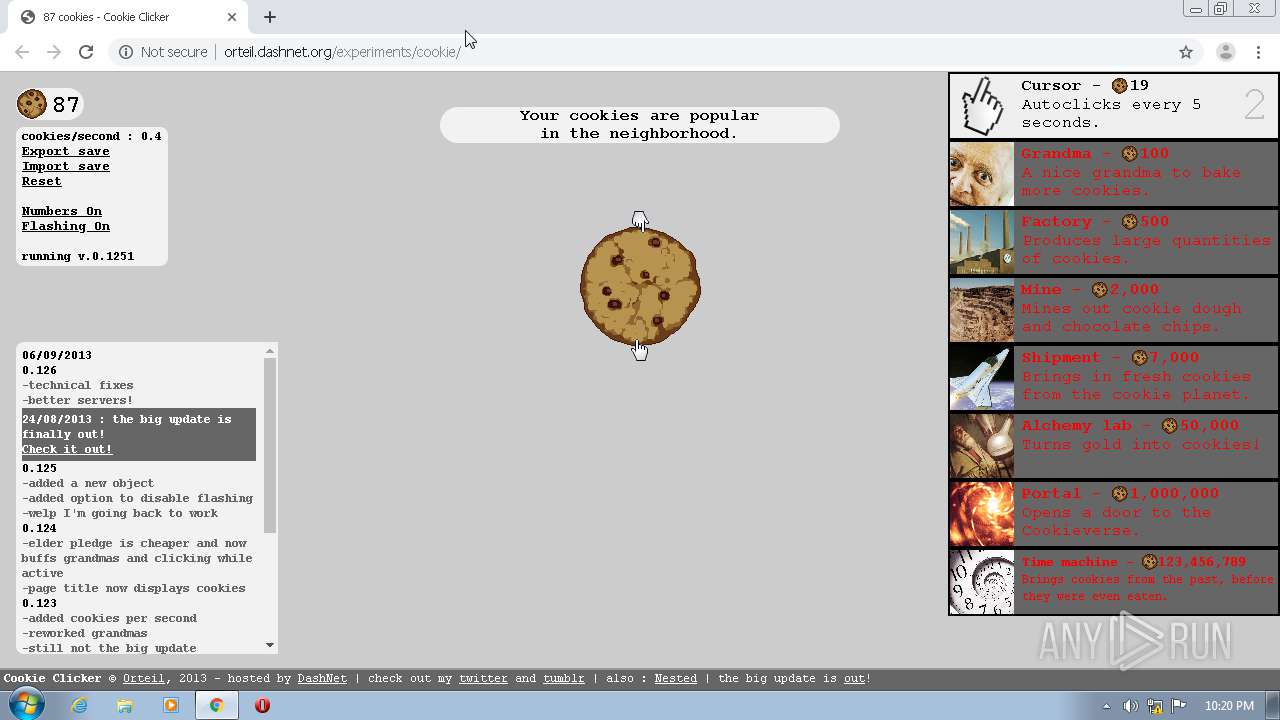
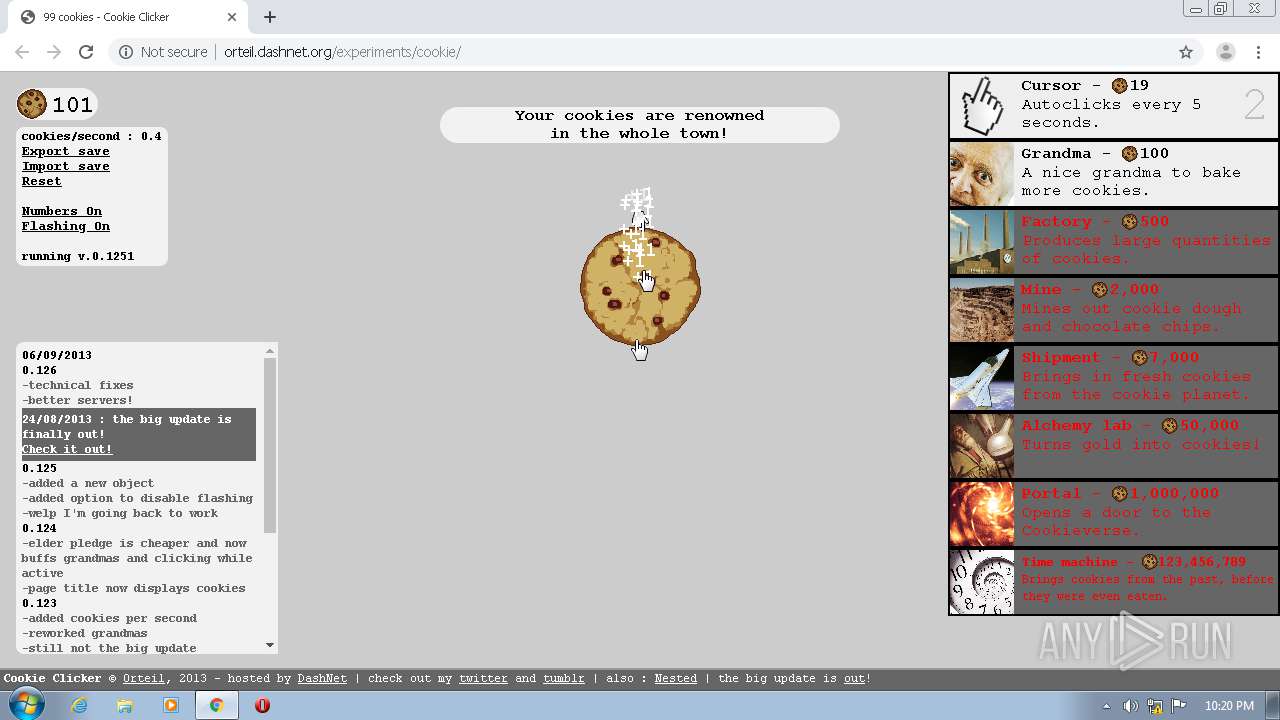
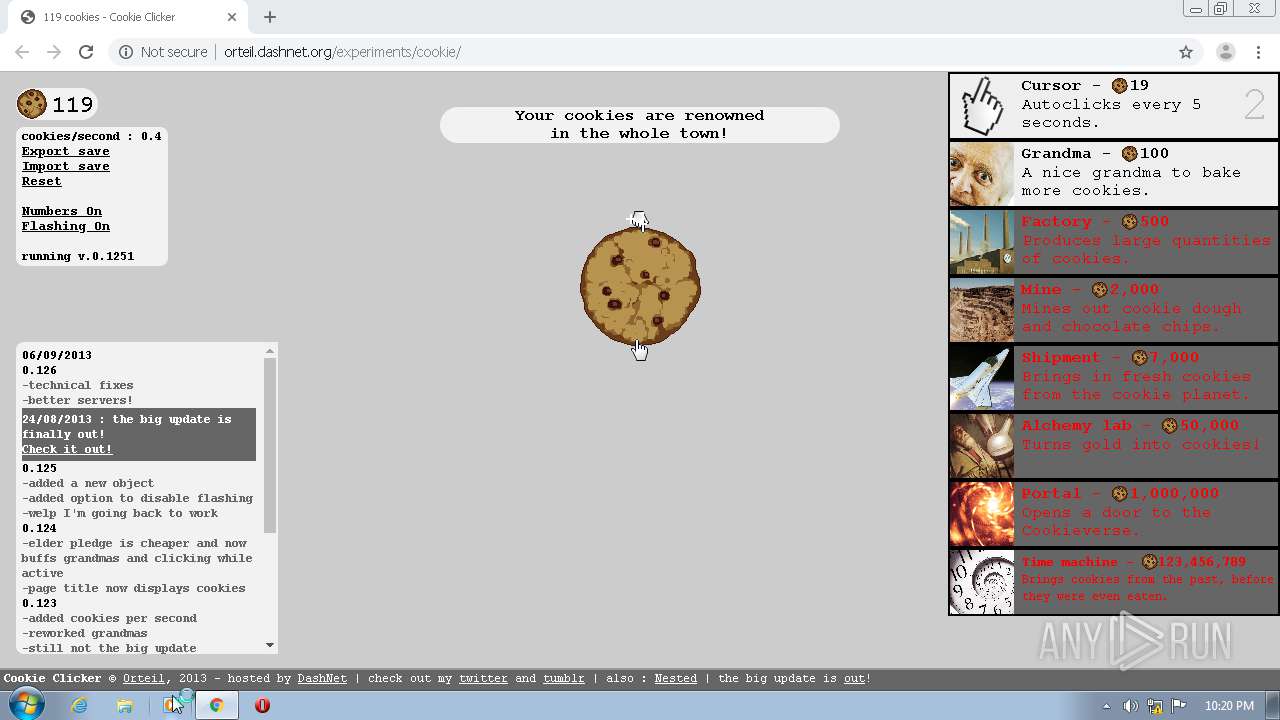
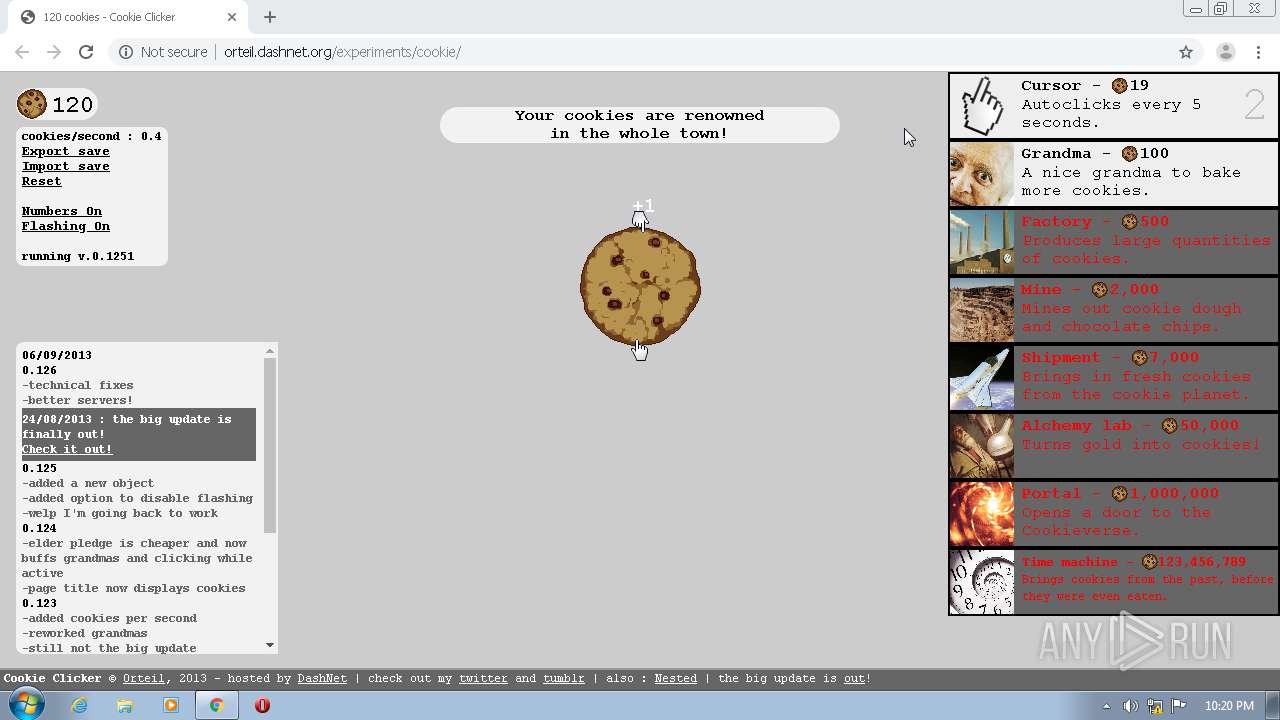
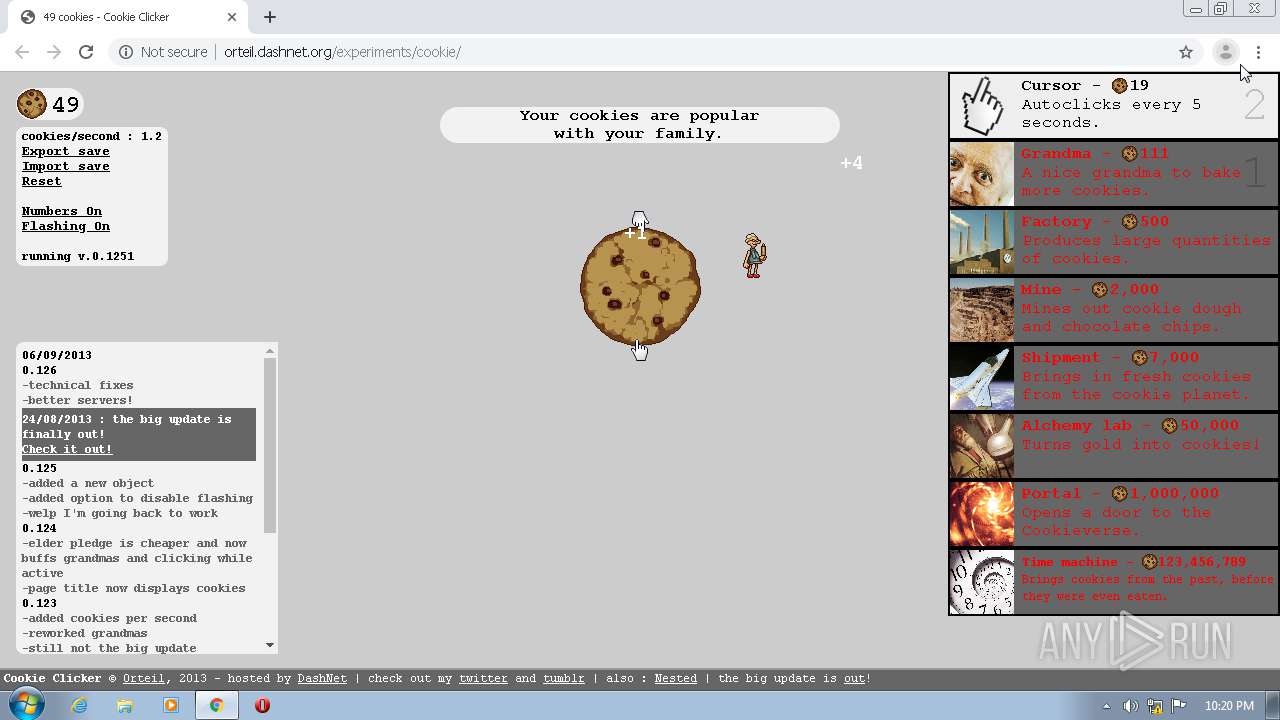
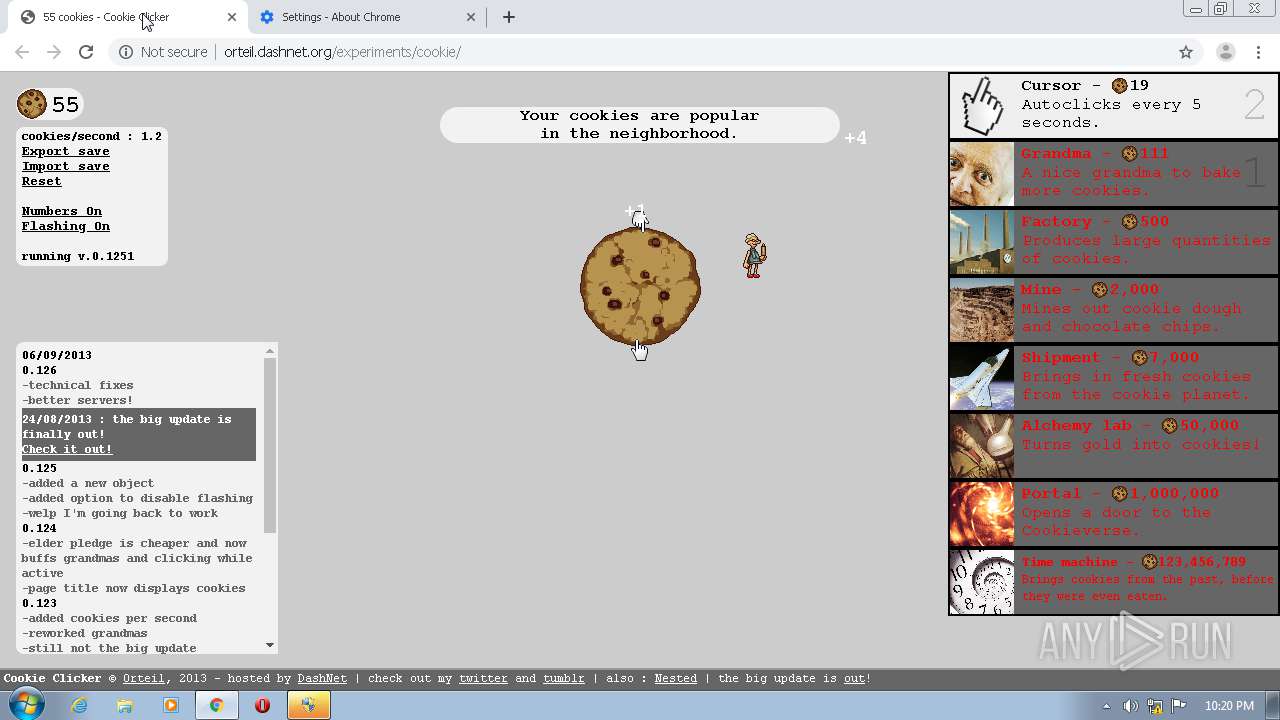
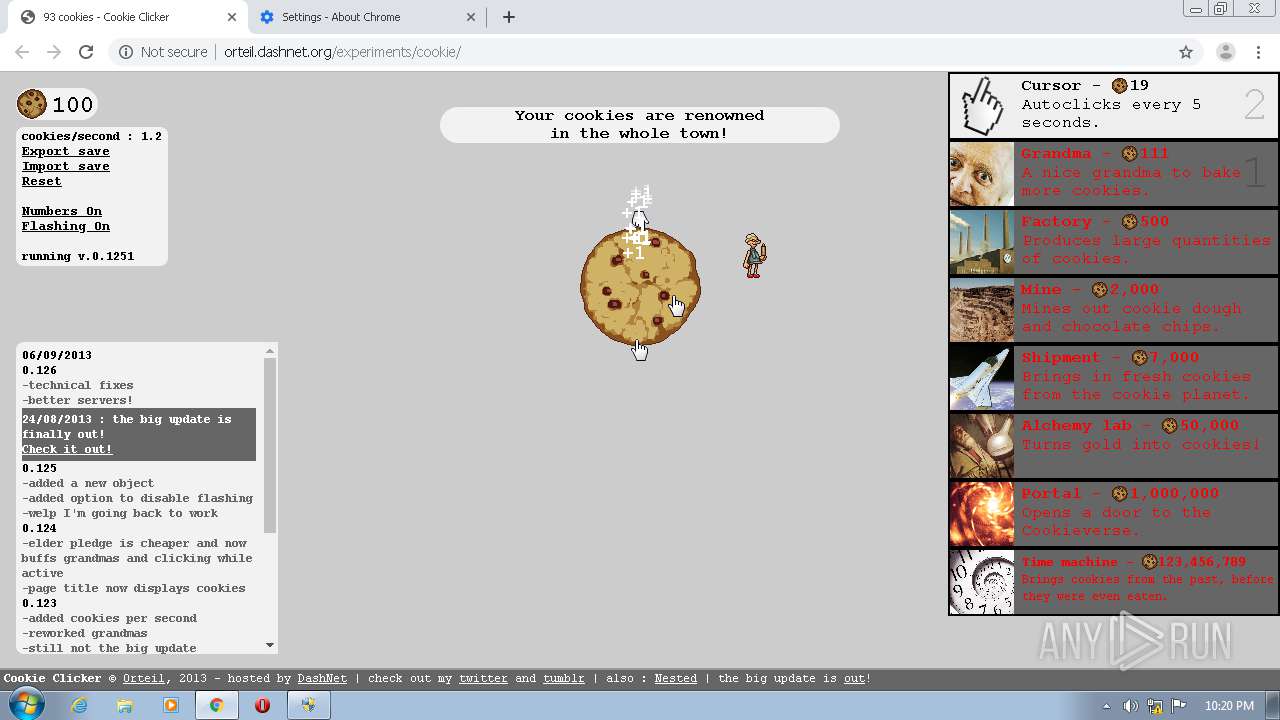
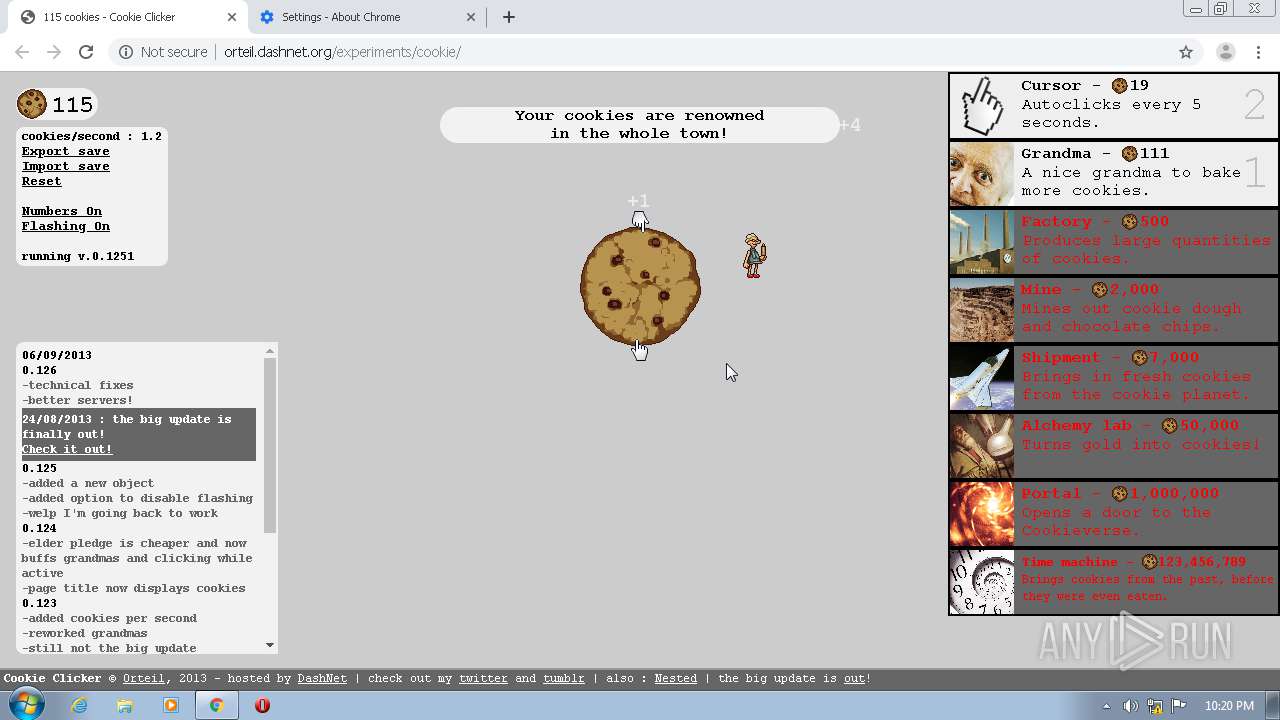
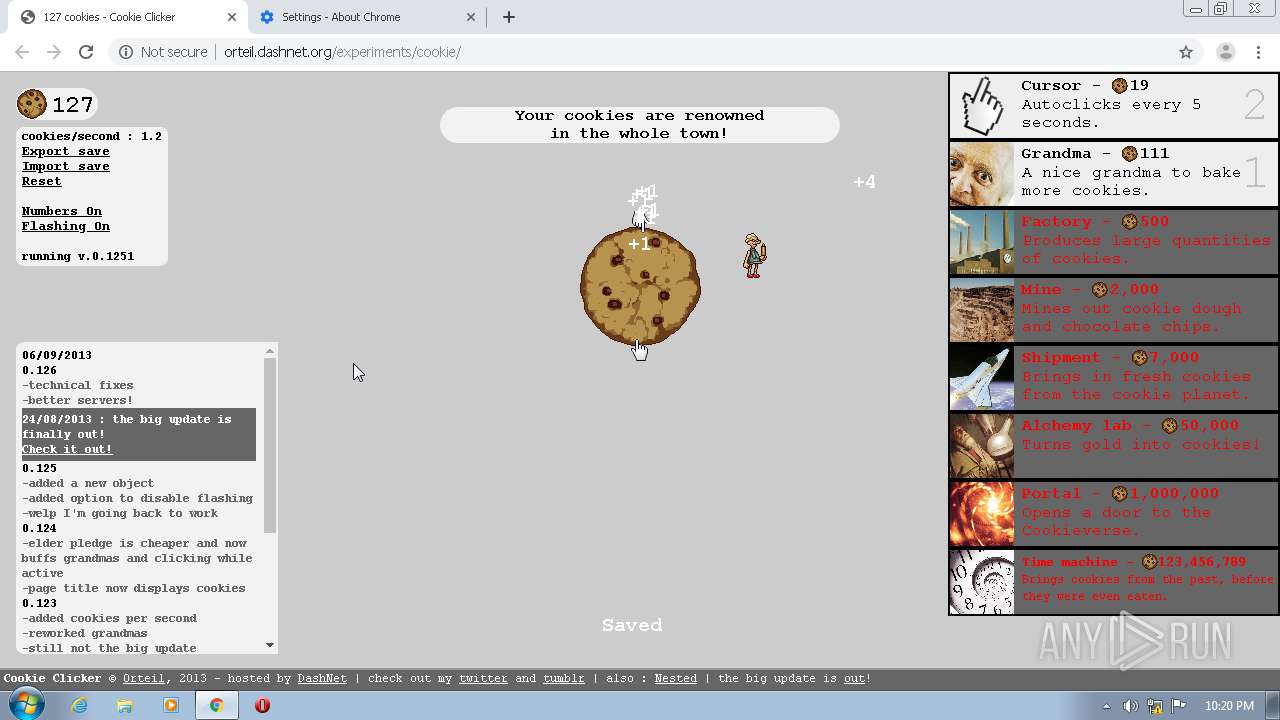
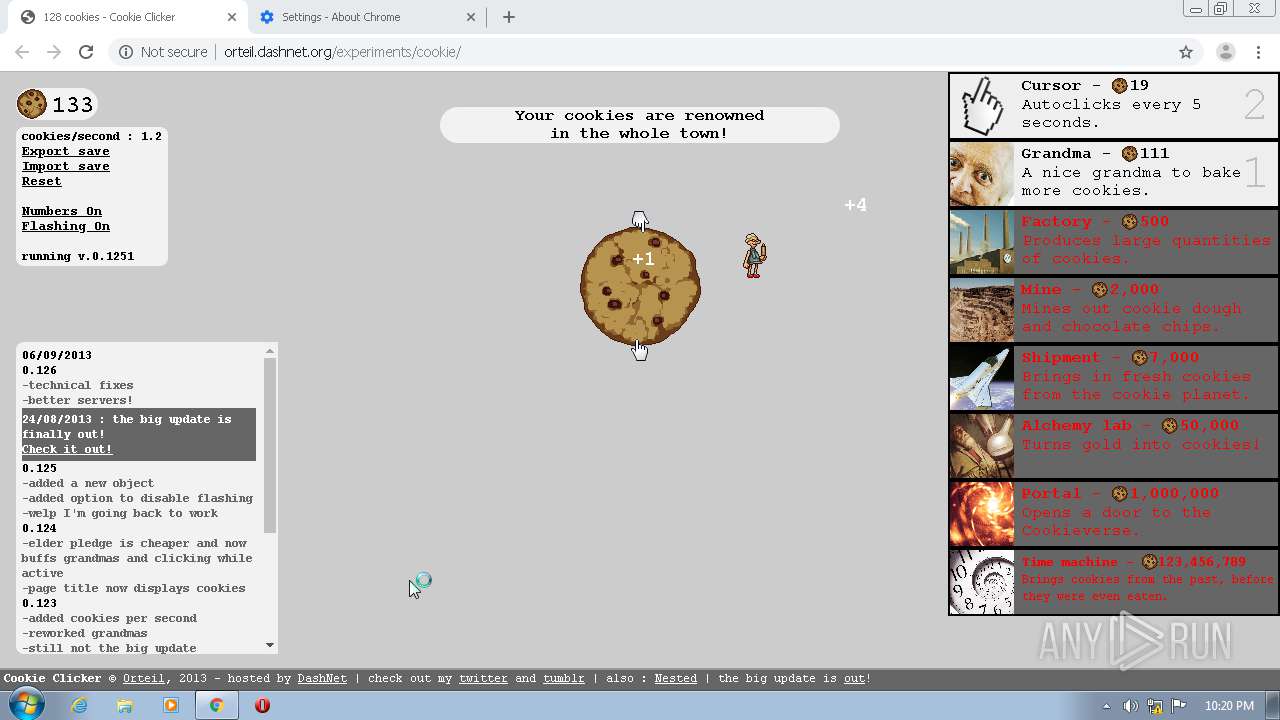
| URL: | http://orteil.dashnet.org/cookieclicker/ |
| Full analysis: | https://app.any.run/tasks/141cfa2f-b39d-44a8-9640-cb016e22773f |
| Verdict: | Malicious activity |
| Analysis date: | June 28, 2020, 21:16:21 |
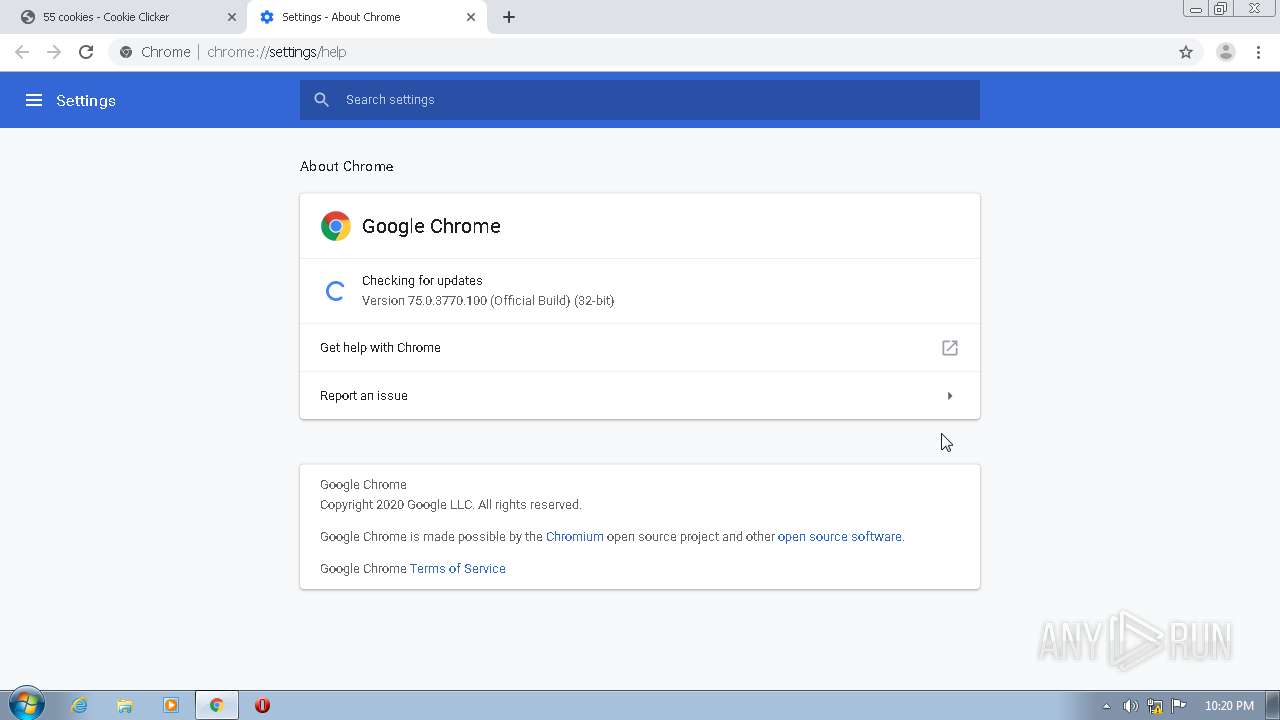
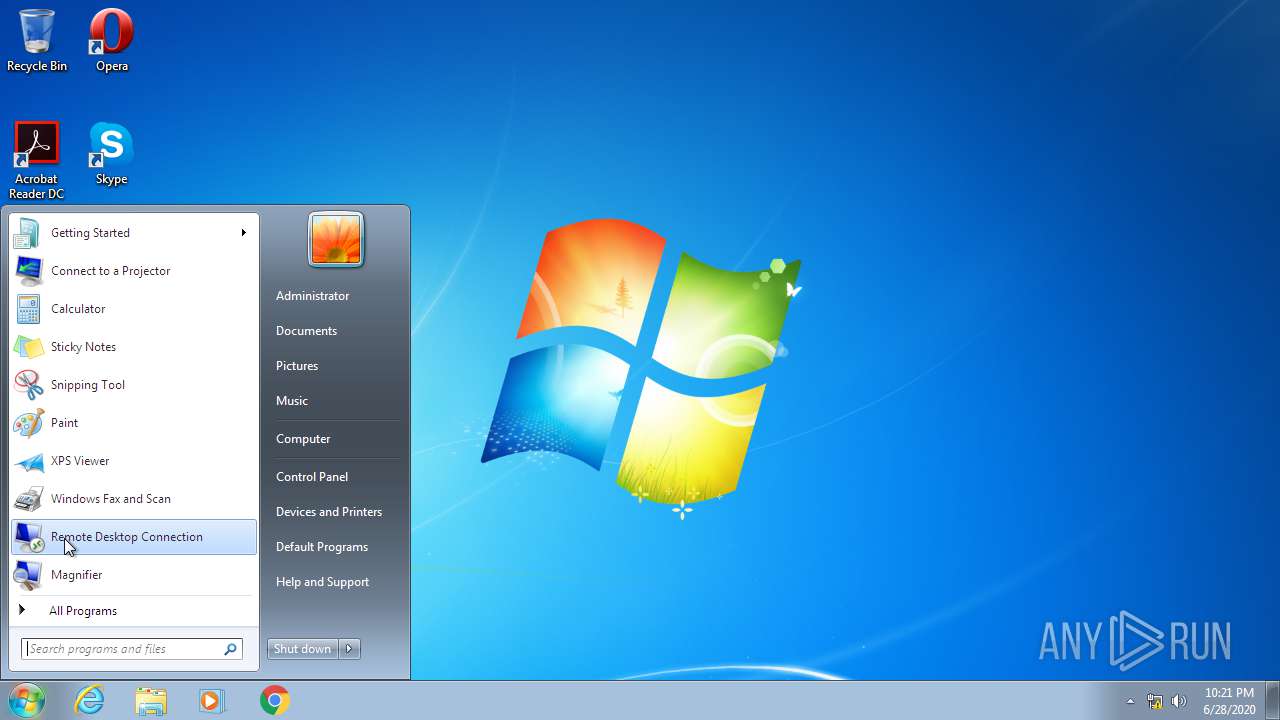
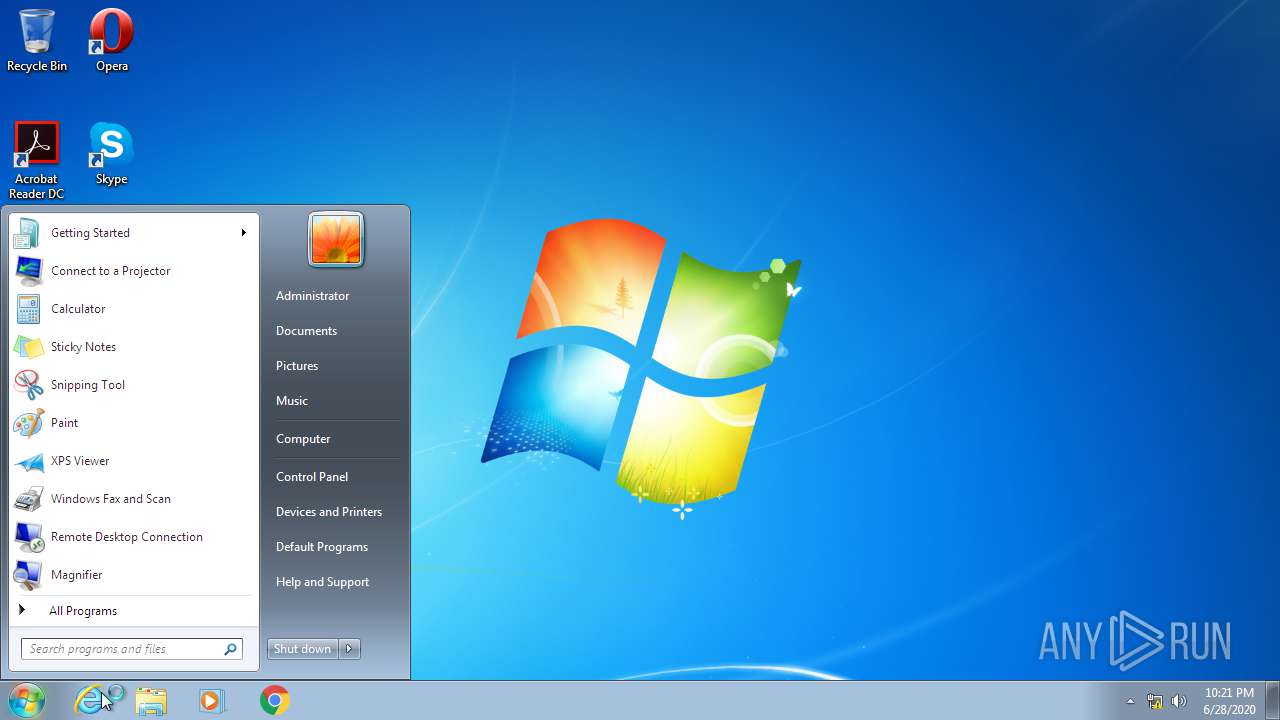
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EA4E016F4F1D0EC45892FC548BA3E3CD |
| SHA1: | 867A1A24A364115396090B3C883DF9FB7DDA8A0B |
| SHA256: | 4AEA372F9B6340FB914B808EDEE4731E9104B4BC28731BEBE6542F0C9078255B |
| SSDEEP: | 3:N1KRX7AYG5XK:CZ7 |
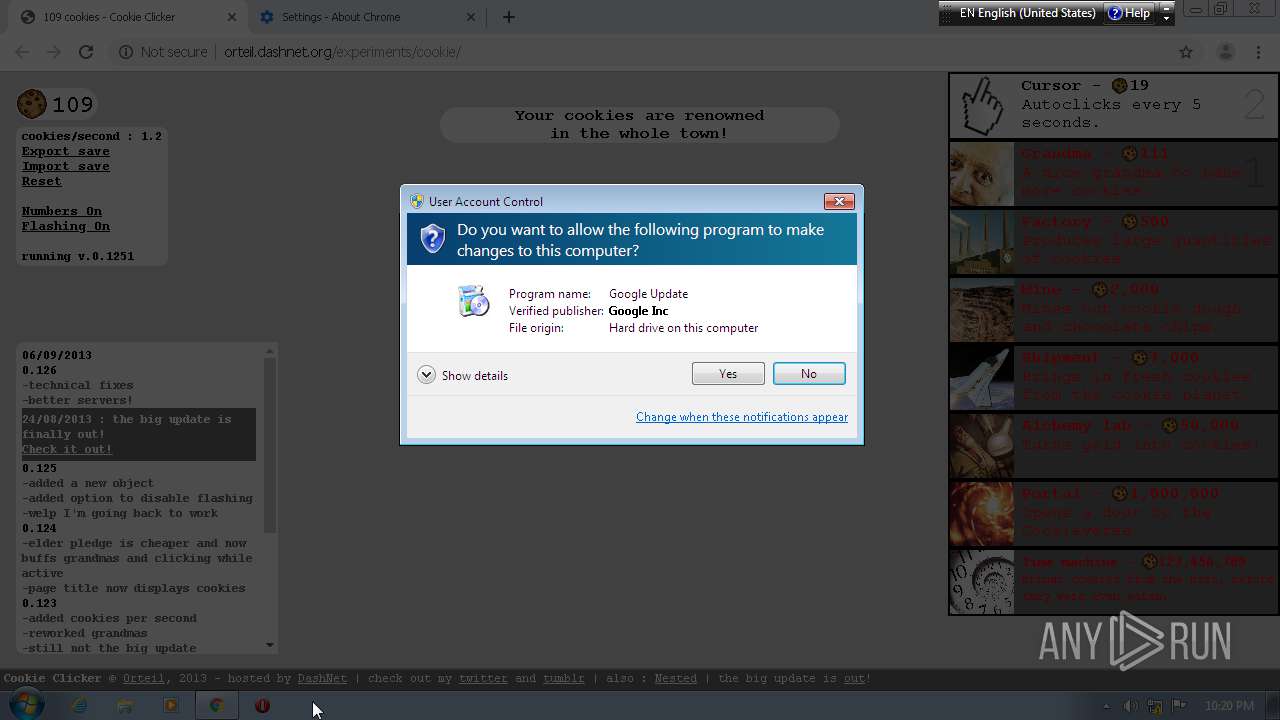
MALICIOUS
Changes internet zones settings
- ie4uinit.exe (PID: 3524)
Loads the Task Scheduler COM API
- rundll32.exe (PID: 3860)
Changes settings of System certificates
- GoogleUpdate.exe (PID: 2372)
SUSPICIOUS
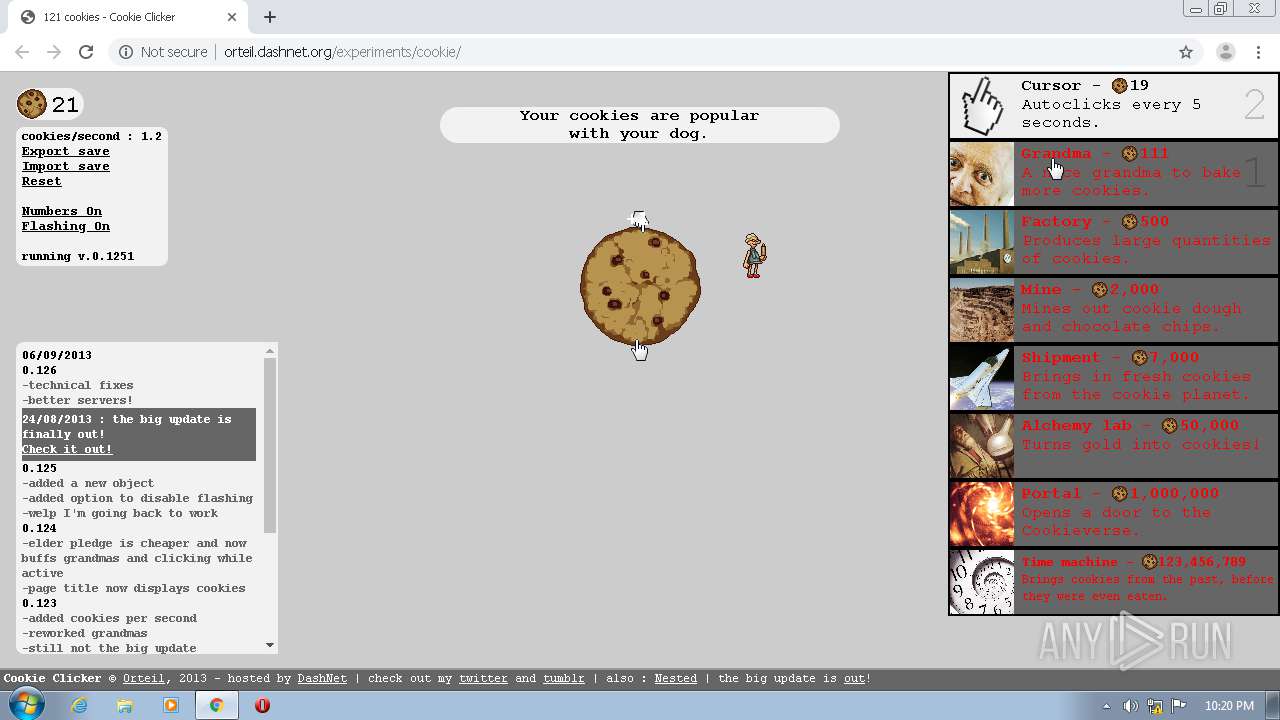
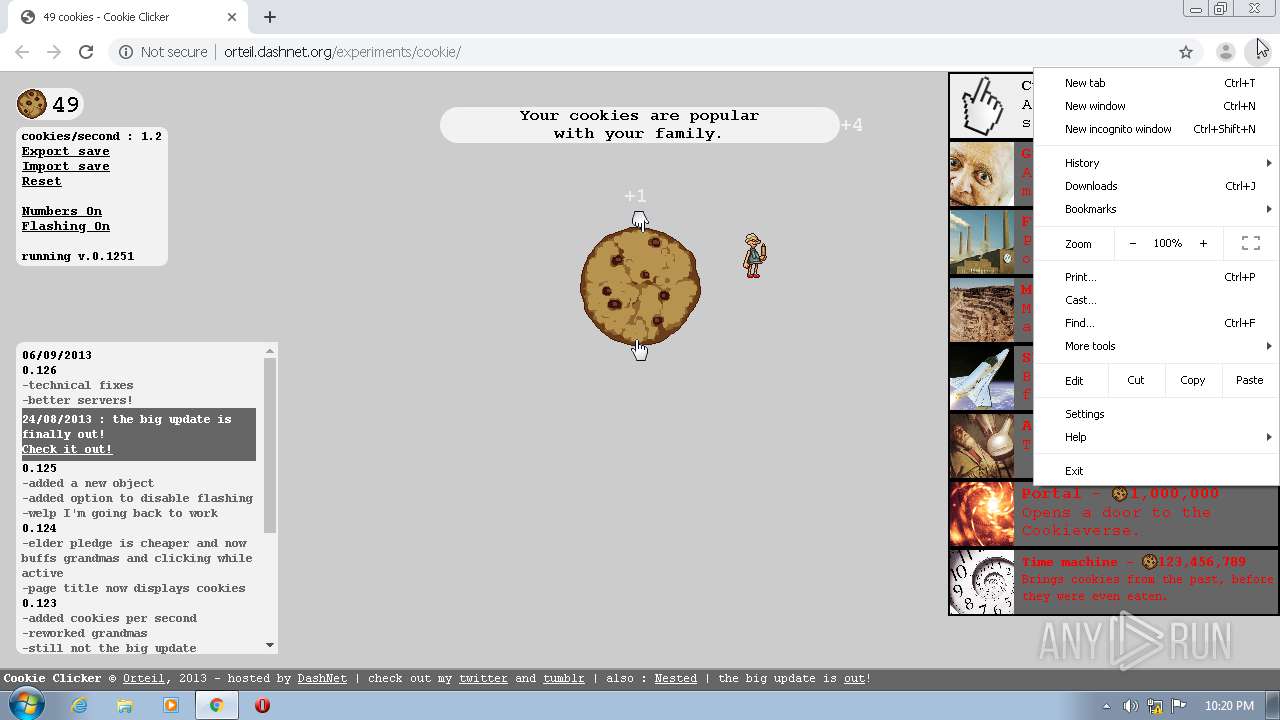
Modifies files in Chrome extension folder
- chrome.exe (PID: 1108)
Executed via COM
- GoogleUpdateOnDemand.exe (PID: 3340)
- GoogleUpdateBroker.exe (PID: 2380)
- GoogleUpdateBroker.exe (PID: 3384)
Executed as Windows Service
- taskhost.exe (PID: 552)
Uses RUNDLL32.EXE to load library
- ie4uinit.exe (PID: 3524)
- rundll32.exe (PID: 3860)
Reads Internet Cache Settings
- taskhost.exe (PID: 552)
Application launched itself
- rundll32.exe (PID: 3860)
Creates files in the program directory
- ie4uinit.exe (PID: 3524)
- chrmstp.exe (PID: 2888)
Writes to a desktop.ini file (may be used to cloak folders)
- ie4uinit.exe (PID: 3524)
Adds / modifies Windows certificates
- GoogleUpdate.exe (PID: 2372)
INFO
Reads the hosts file
- chrome.exe (PID: 1108)
- chrome.exe (PID: 3968)
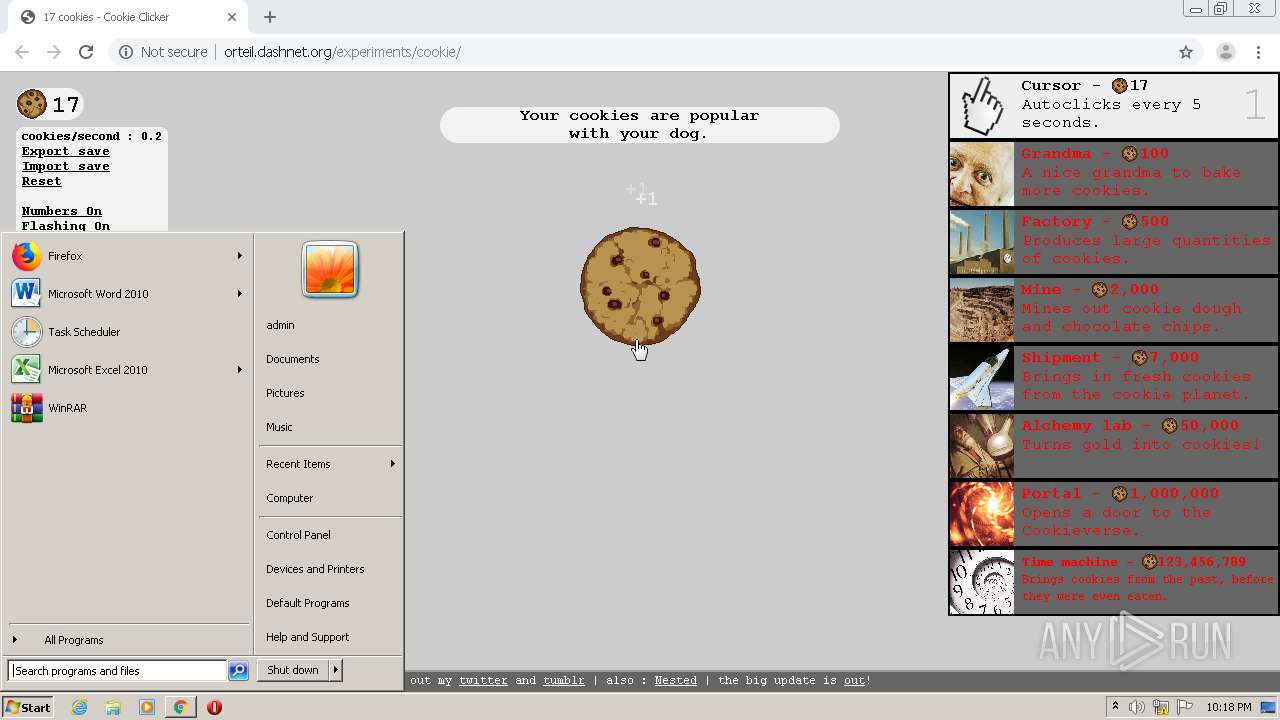
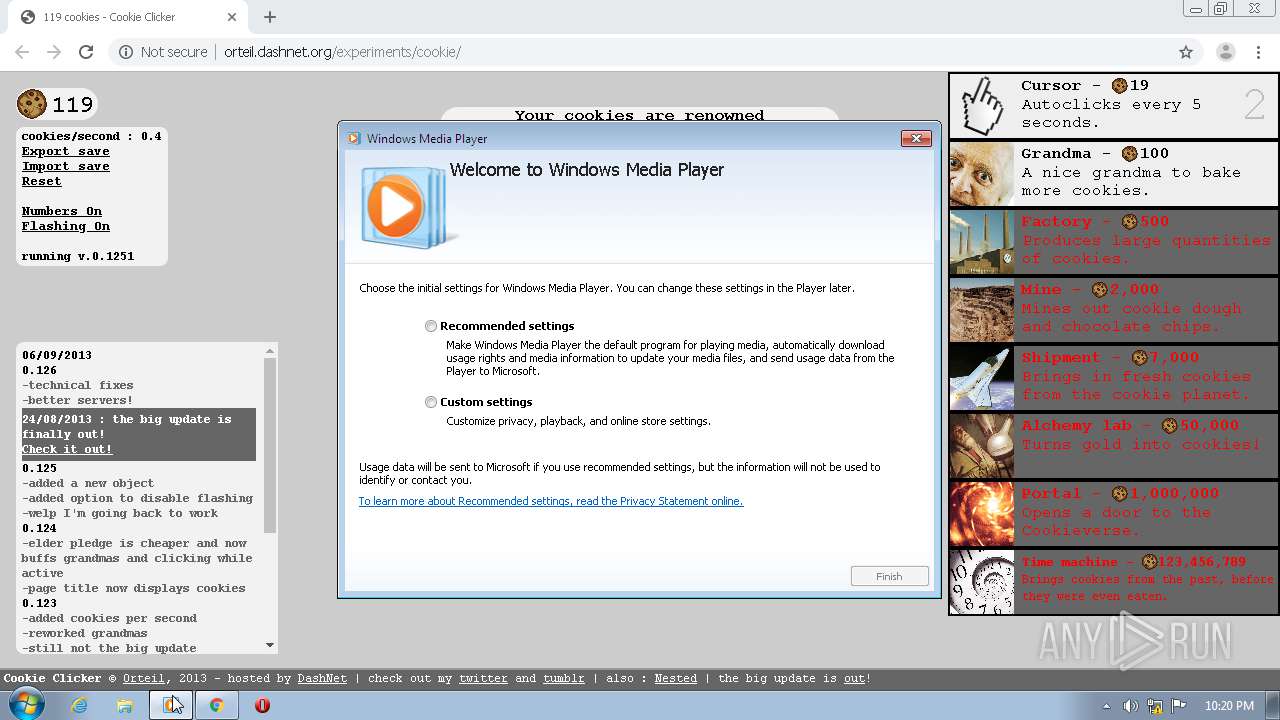
Manual execution by user
- wmplayer.exe (PID: 3880)
- ie4uinit.exe (PID: 3524)
- ie4uinit.exe (PID: 3092)
- chrmstp.exe (PID: 2888)
- magnify.exe (PID: 3112)
Modifies the open verb of a shell class
- chrome.exe (PID: 1108)
Creates files in the user directory
- chrome.exe (PID: 1108)
Application launched itself
- chrome.exe (PID: 1108)
Reads settings of System Certificates
- GoogleUpdate.exe (PID: 2372)
- chrome.exe (PID: 3968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
118
Monitored processes
60
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,6123668606600939325,2916419232929547174,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16614093606006237589 --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1012 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,6123668606600939325,2916419232929547174,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8392188676303480423 --renderer-client-id=38 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4176 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 552 | "taskhost.exe" | C:\Windows\system32\taskhost.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,6123668606600939325,2916419232929547174,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=198764737458443453 --mojo-platform-channel-handle=4696 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,6123668606600939325,2916419232929547174,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18012965771991322684 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,6123668606600939325,2916419232929547174,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11521221199875818610 --mojo-platform-channel-handle=3688 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://orteil.dashnet.org/cookieclicker/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,6123668606600939325,2916419232929547174,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11073877029846990326 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,6123668606600939325,2916419232929547174,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15147833539974016704 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3324 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,6123668606600939325,2916419232929547174,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8691506714229739313 --mojo-platform-channel-handle=2484 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 122
Read events
1 430
Write events
1 676
Delete events
16
Modification events
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1108-13237852595045000 |
Value: 259 | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1108) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1108-13237852595045000 |
Value: 259 | |||
Executable files
0
Suspicious files
198
Text files
417
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EF908B3-454.pma | — | |
MD5:— | SHA256:— | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFf6911.TMP | text | |
MD5:— | SHA256:— | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFf6911.TMP | text | |
MD5:— | SHA256:— | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFf6911.TMP | text | |
MD5:— | SHA256:— | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1108 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFf6b15.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
152
TCP/UDP connections
107
DNS requests
70
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3968 | chrome.exe | GET | 200 | 213.186.33.107:80 | http://orteil.dashnet.org/cookieclicker/style.css?v=2.050 | FR | text | 11.9 Kb | malicious |
3968 | chrome.exe | GET | 200 | 172.217.21.226:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 40.3 Kb | whitelisted |
3968 | chrome.exe | GET | 200 | 213.186.33.107:80 | http://orteil.dashnet.org/cookieclicker/img/sparkles.jpg | FR | image | 15.5 Kb | malicious |
3968 | chrome.exe | GET | 200 | 213.186.33.107:80 | http://orteil.dashnet.org/cookieclicker/img/spinnyBig.png | FR | image | 5.27 Kb | malicious |
3968 | chrome.exe | GET | 200 | 213.186.33.107:80 | http://orteil.dashnet.org/cookieclicker/img/patreon.png | FR | image | 2.36 Kb | malicious |
3968 | chrome.exe | GET | 200 | 213.186.33.107:80 | http://orteil.dashnet.org/cookieclicker/img/spinnySmall.png | FR | image | 2.75 Kb | malicious |
3968 | chrome.exe | GET | 307 | 213.186.33.107:80 | http://orteil.dashnet.org/cookieclicker/ | FR | html | 116 b | malicious |
3968 | chrome.exe | GET | 200 | 213.186.33.107:80 | http://orteil.dashnet.org/cookieclicker/showads.js | FR | text | 198 b | malicious |
3968 | chrome.exe | GET | 200 | 213.186.33.107:80 | http://orteil.dashnet.org/cookieclicker/img/darkNoiseTopBar.jpg | FR | image | 8.33 Kb | malicious |
3968 | chrome.exe | GET | 200 | 213.186.33.107:80 | http://orteil.dashnet.org/cookieclicker/img/darkNoise.jpg | FR | image | 52.9 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3968 | chrome.exe | 172.217.21.225:443 | tpc.googlesyndication.com | Google Inc. | US | whitelisted |
3968 | chrome.exe | 172.217.18.98:443 | adservice.google.de | Google Inc. | US | whitelisted |
3968 | chrome.exe | 172.217.23.100:443 | www.google.com | Google Inc. | US | whitelisted |
3968 | chrome.exe | 172.217.16.130:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
3968 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3968 | chrome.exe | 213.186.33.107:80 | orteil.dashnet.org | OVH SAS | FR | malicious |
3968 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
3968 | chrome.exe | 104.16.133.229:80 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
3968 | chrome.exe | 216.58.208.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3968 | chrome.exe | 172.217.21.226:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
orteil.dashnet.org |
| malicious |
accounts.google.com |
| shared |
cdnjs.cloudflare.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
dashnet.org |
| whitelisted |
discordapp.com |
| whitelisted |
orteil42.tumblr.com |
| whitelisted |