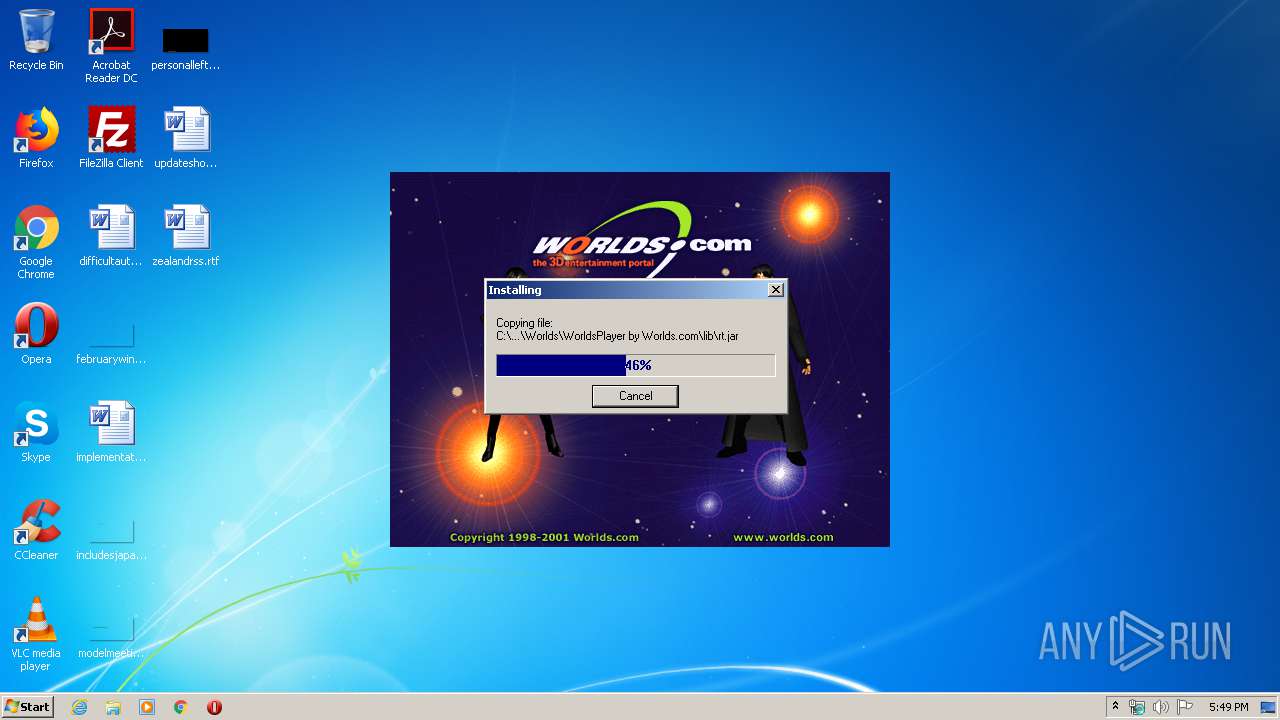
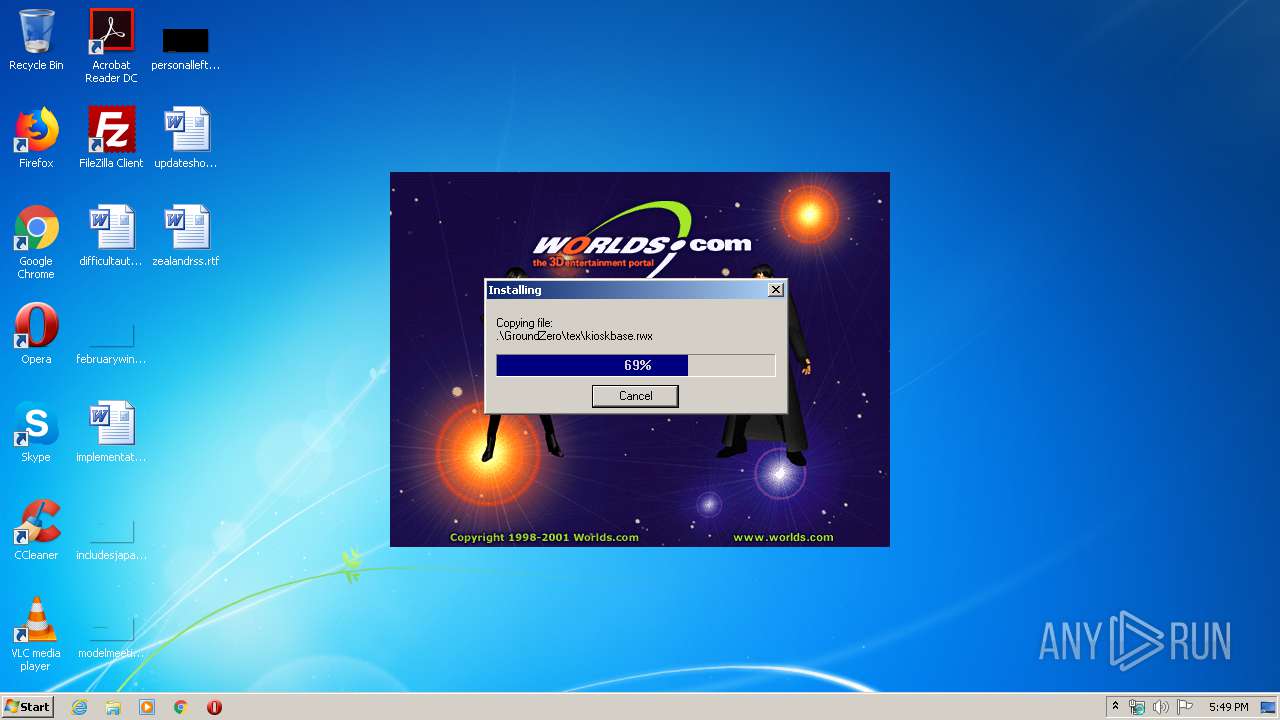
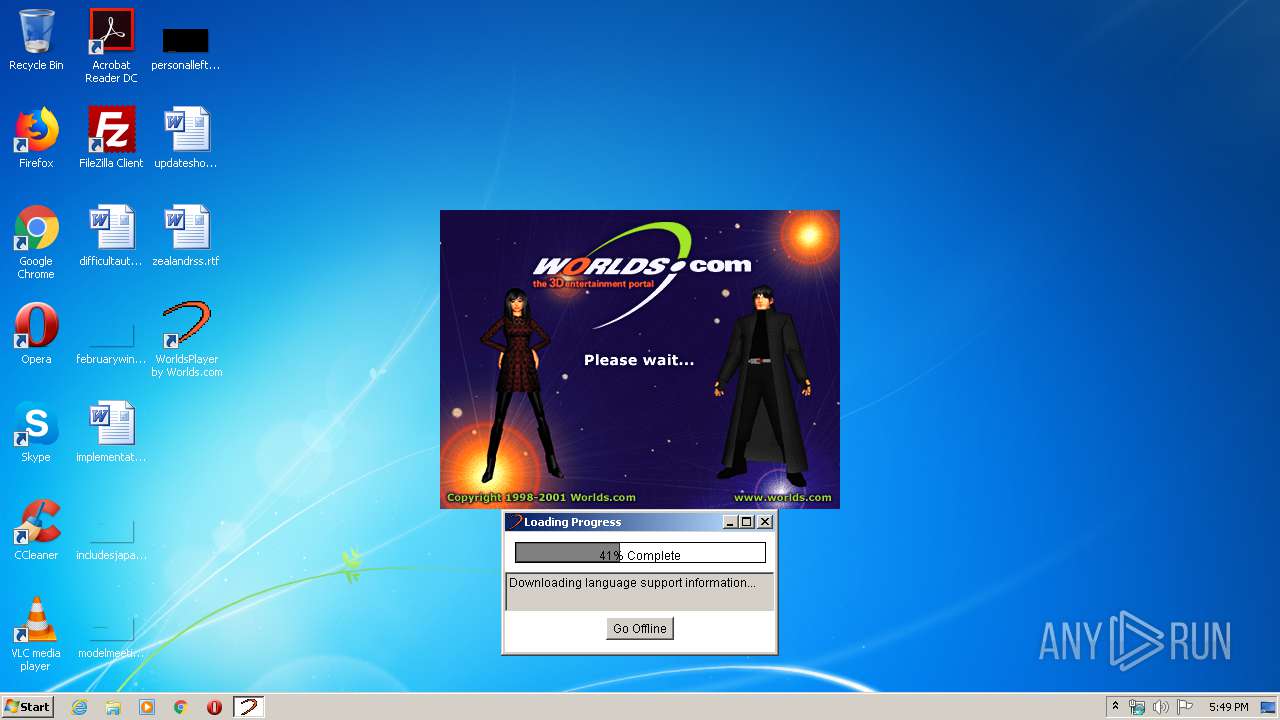
| download: | Worlds1890.exe |
| Full analysis: | https://app.any.run/tasks/bb0042db-5343-4ef5-ac54-cc36276028cb |
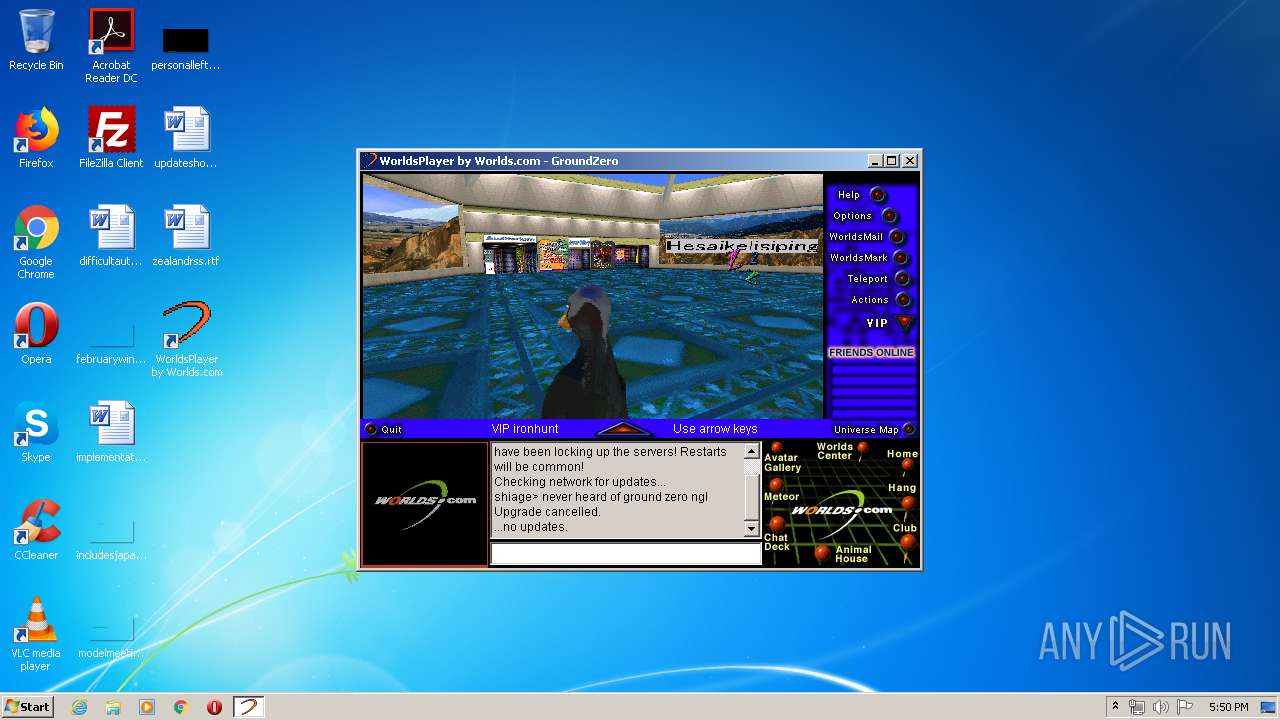
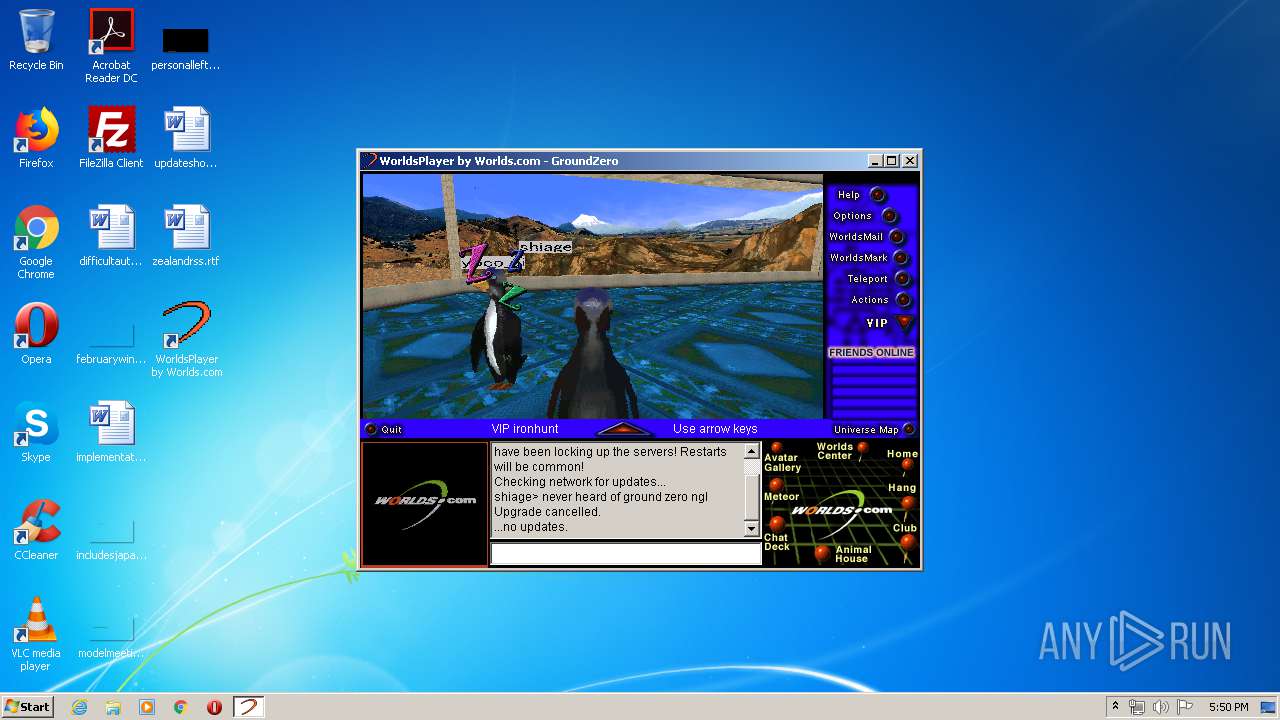
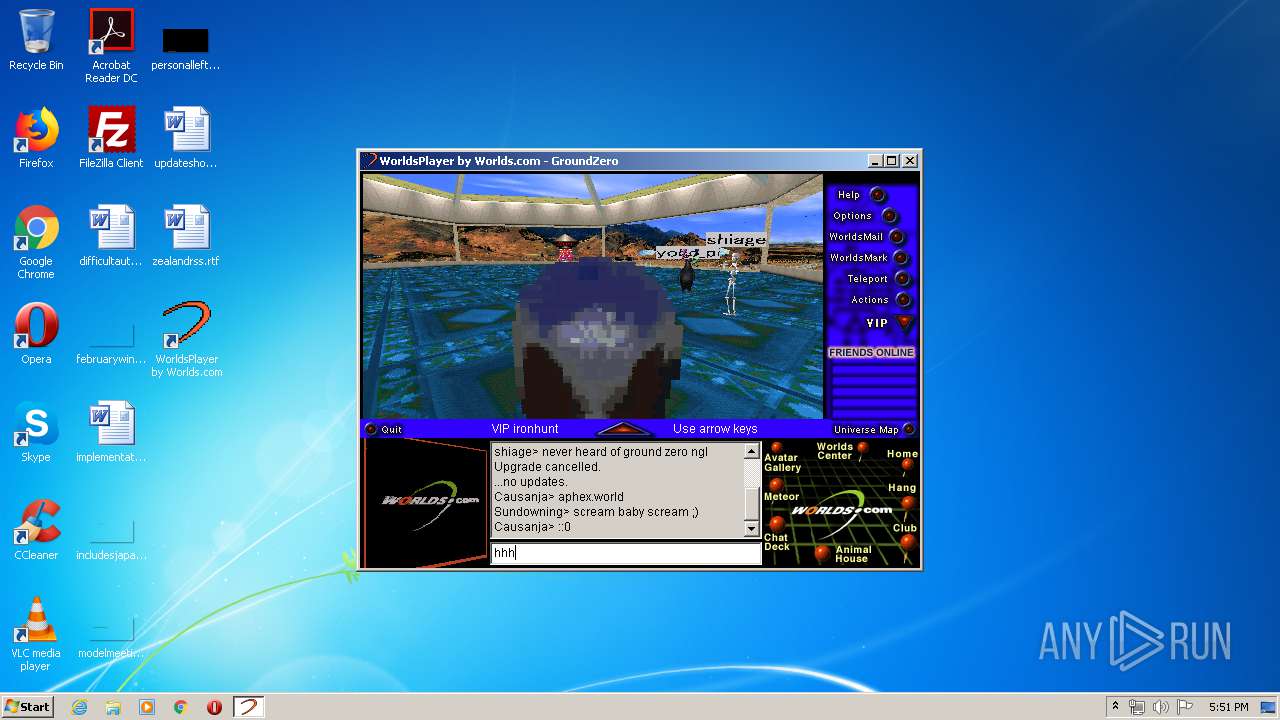
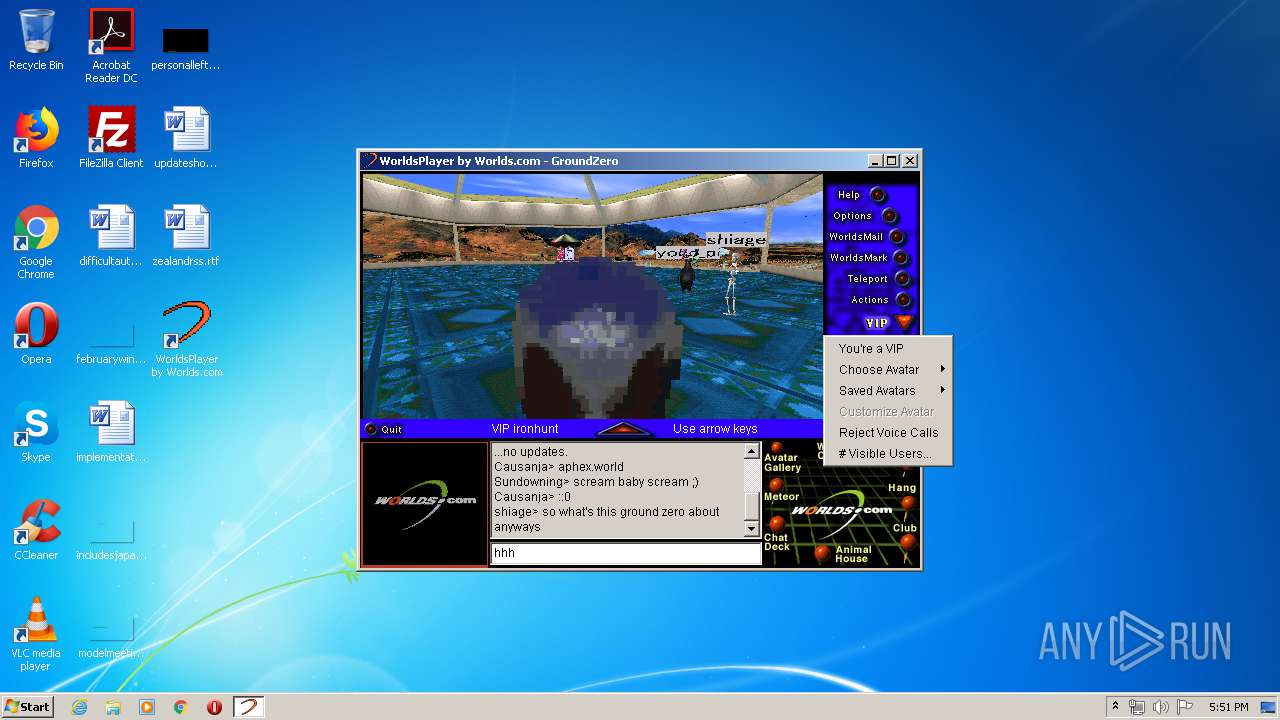
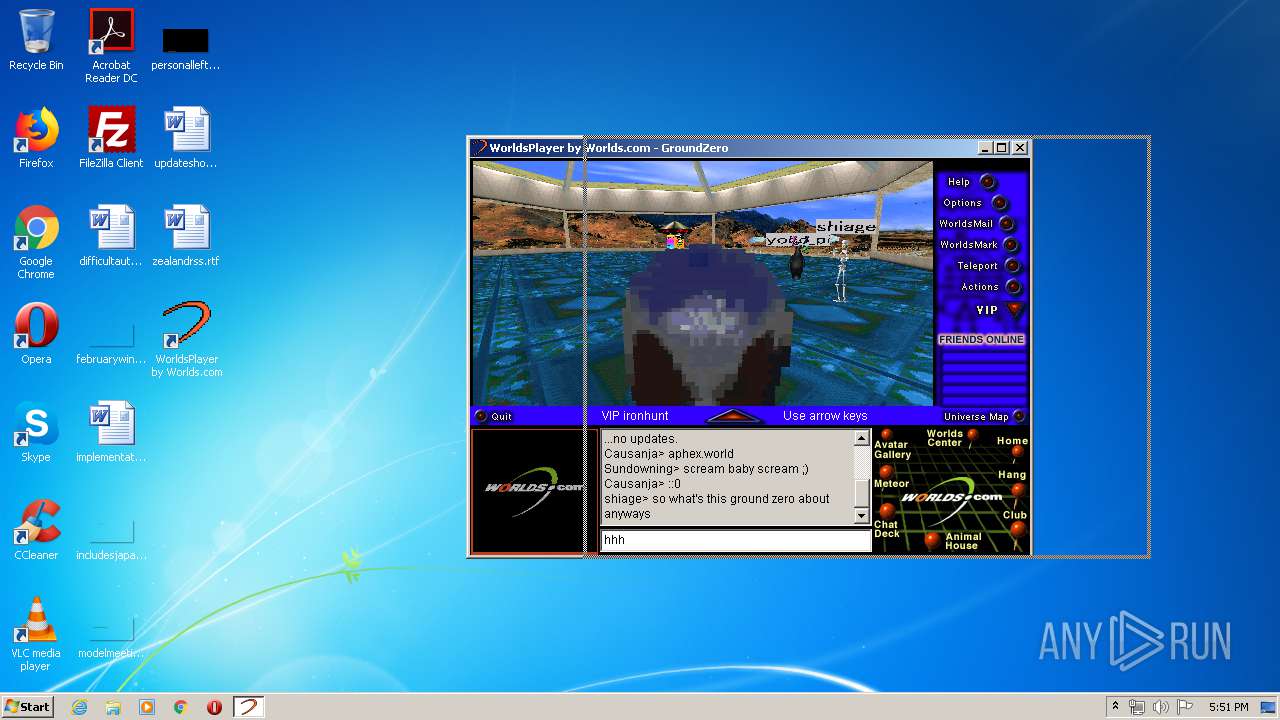
| Verdict: | Malicious activity |
| Analysis date: | May 09, 2020, 16:48:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5ADD493B8108F0FC812D1E34B451D5B9 |
| SHA1: | A3DF75BB321660EDA6B7635A5631A19A39B1024D |
| SHA256: | 4AE3FCF6FE9C79E54FBAB12CC70CB3E24AB5EE9A31AE0068AD02269355B1E7AA |
| SSDEEP: | 196608:l3rw5tJ4Htrf4iT6TcEInbkkshgcFncWhVN6v+q9n/J/ILX30bv82nNlFbZI:l3rw5LSkiTbupcWLsvL9ns0bUUrFbO |
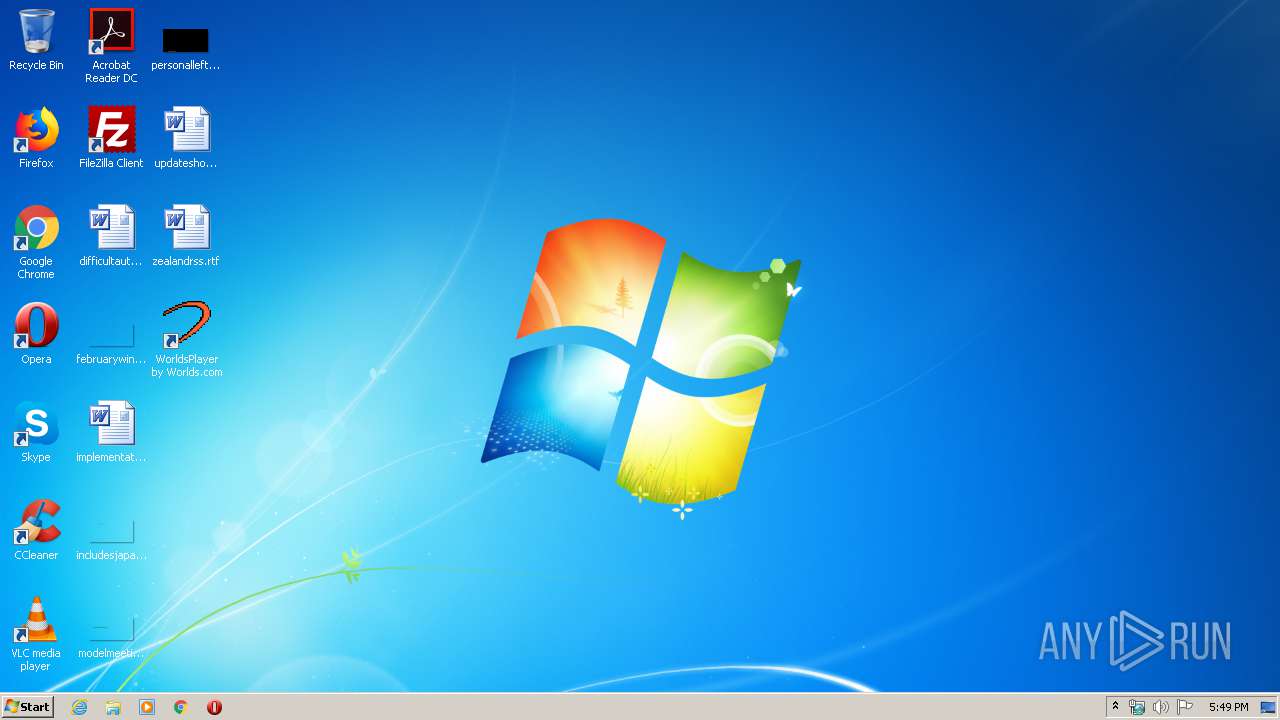
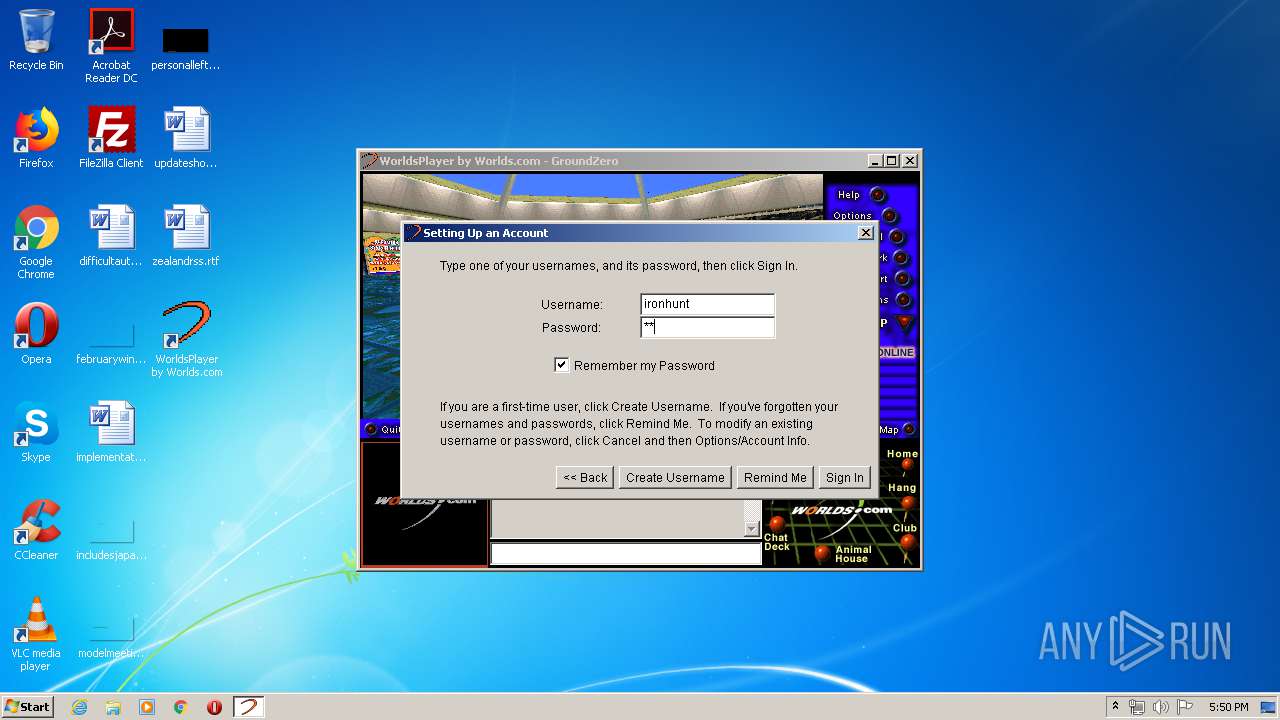
MALICIOUS
Loads dropped or rewritten executable
- Worlds1890.exe (PID: 3636)
- first.exe (PID: 2348)
- run.exe (PID: 2900)
- javaw.exe (PID: 3448)
- GROUND~1.EXE (PID: 2064)
Application was dropped or rewritten from another process
- run.exe (PID: 2900)
- javaw.exe (PID: 3448)
SUSPICIOUS
Creates files in the Windows directory
- Worlds1890.exe (PID: 3636)
- first.exe (PID: 2348)
- GROUND~1.EXE (PID: 2064)
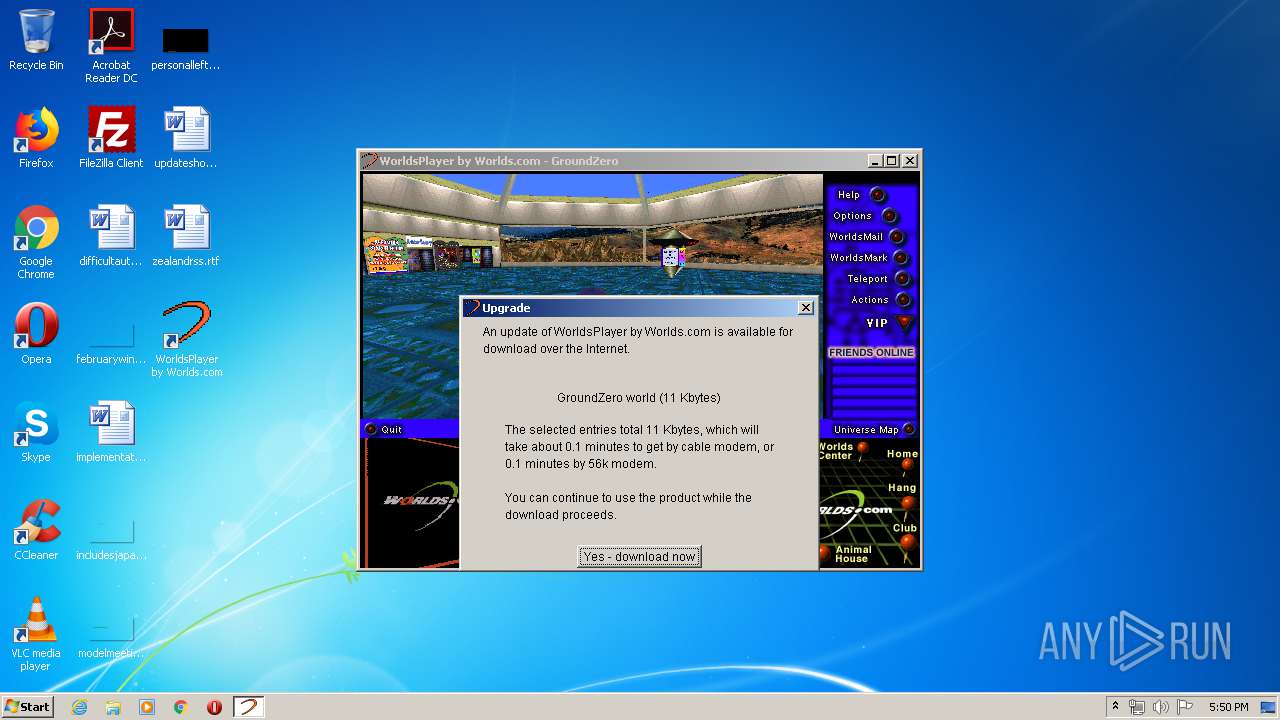
Executable content was dropped or overwritten
- Worlds1890.exe (PID: 3636)
- first.exe (PID: 2348)
- GROUND~1.EXE (PID: 2064)
Removes files from Windows directory
- Worlds1890.exe (PID: 3636)
- first.exe (PID: 2348)
- GROUND~1.EXE (PID: 2064)
Starts itself from another location
- Worlds1890.exe (PID: 3636)
- first.exe (PID: 2348)
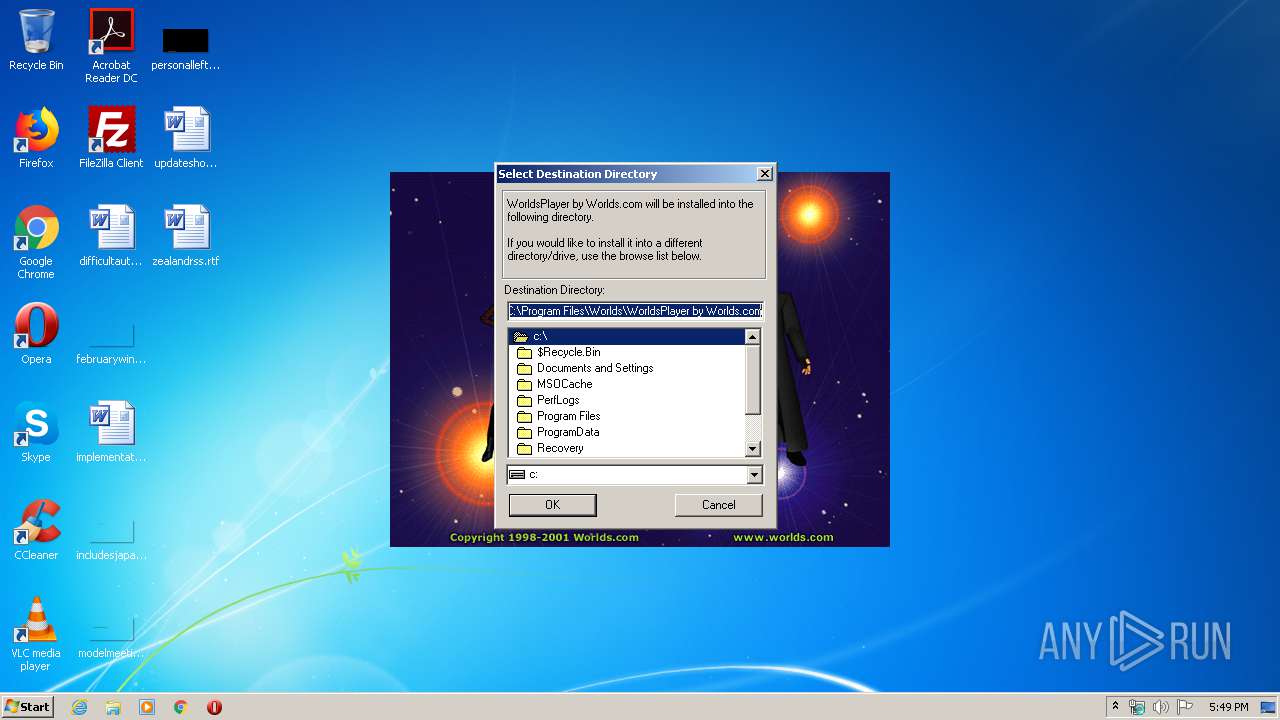
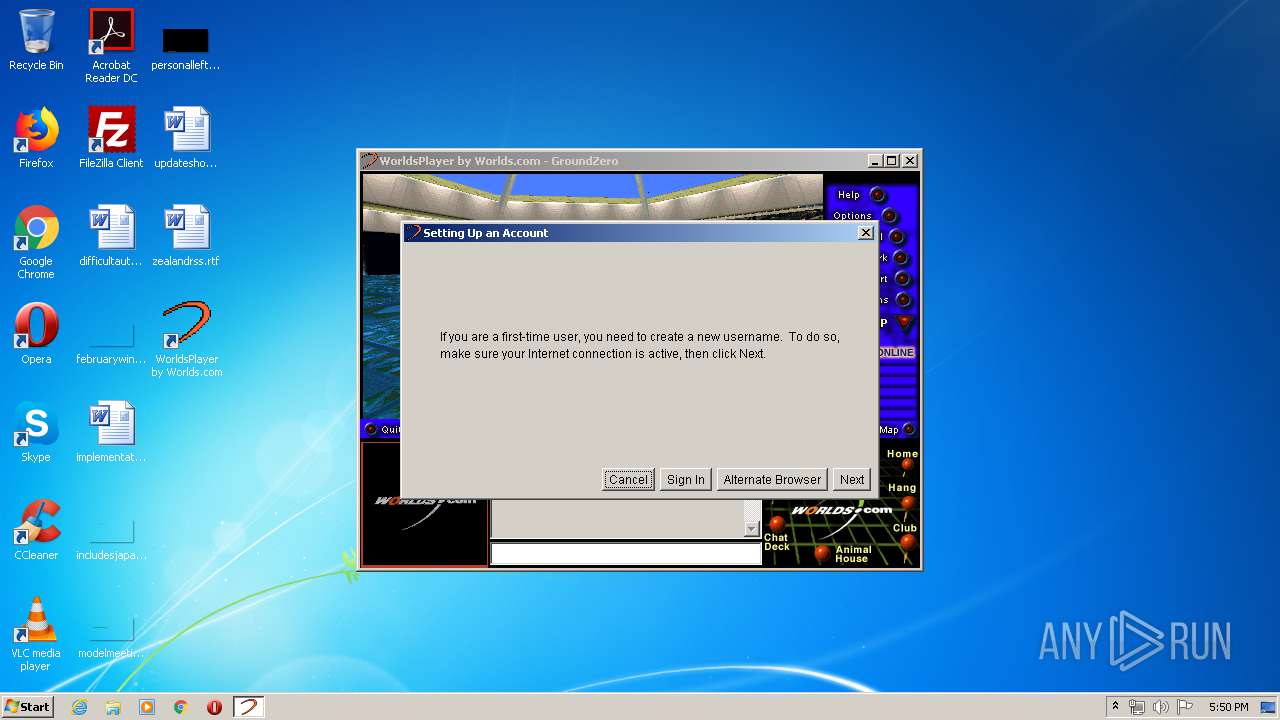
Creates a software uninstall entry
- first.exe (PID: 2348)
Modifies the open verb of a shell class
- first.exe (PID: 2348)
Reads internet explorer settings
- javaw.exe (PID: 3448)
Creates files in the program directory
- GROUND~1.EXE (PID: 2064)
- first.exe (PID: 2348)
- javaw.exe (PID: 3448)
Reads Internet Cache Settings
- javaw.exe (PID: 3448)
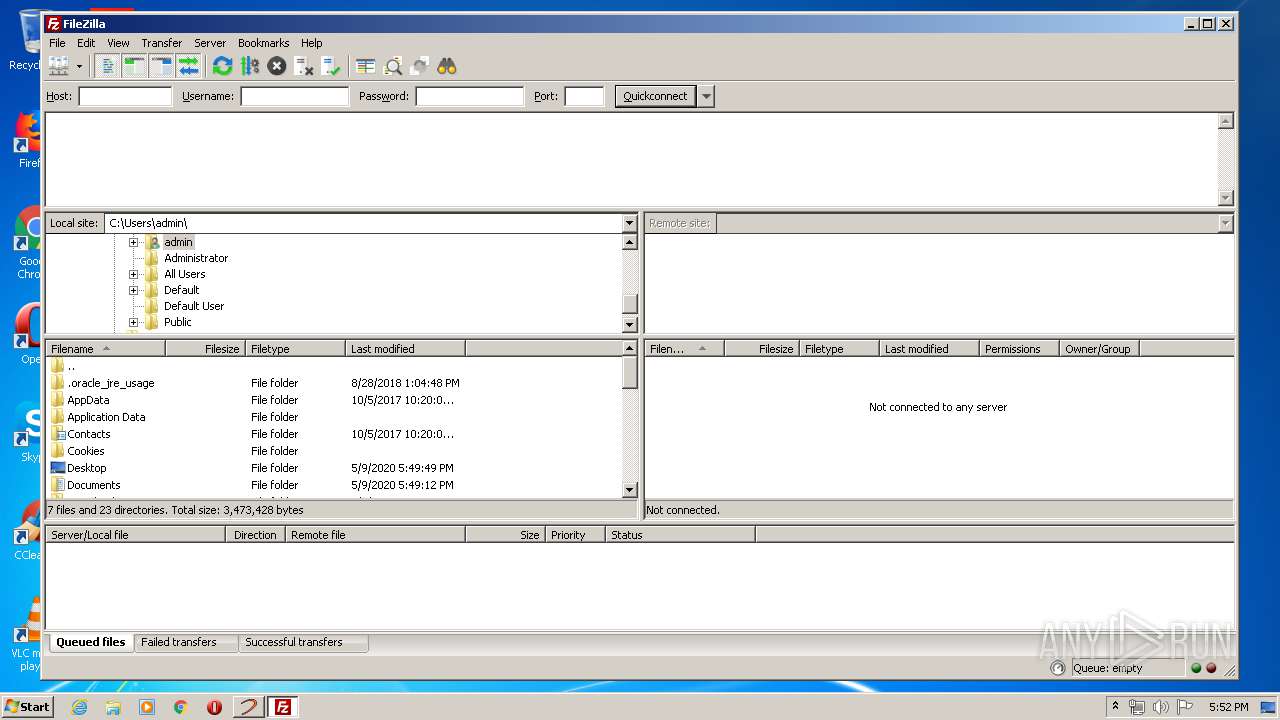
Creates files in the user directory
- filezilla.exe (PID: 4052)
INFO
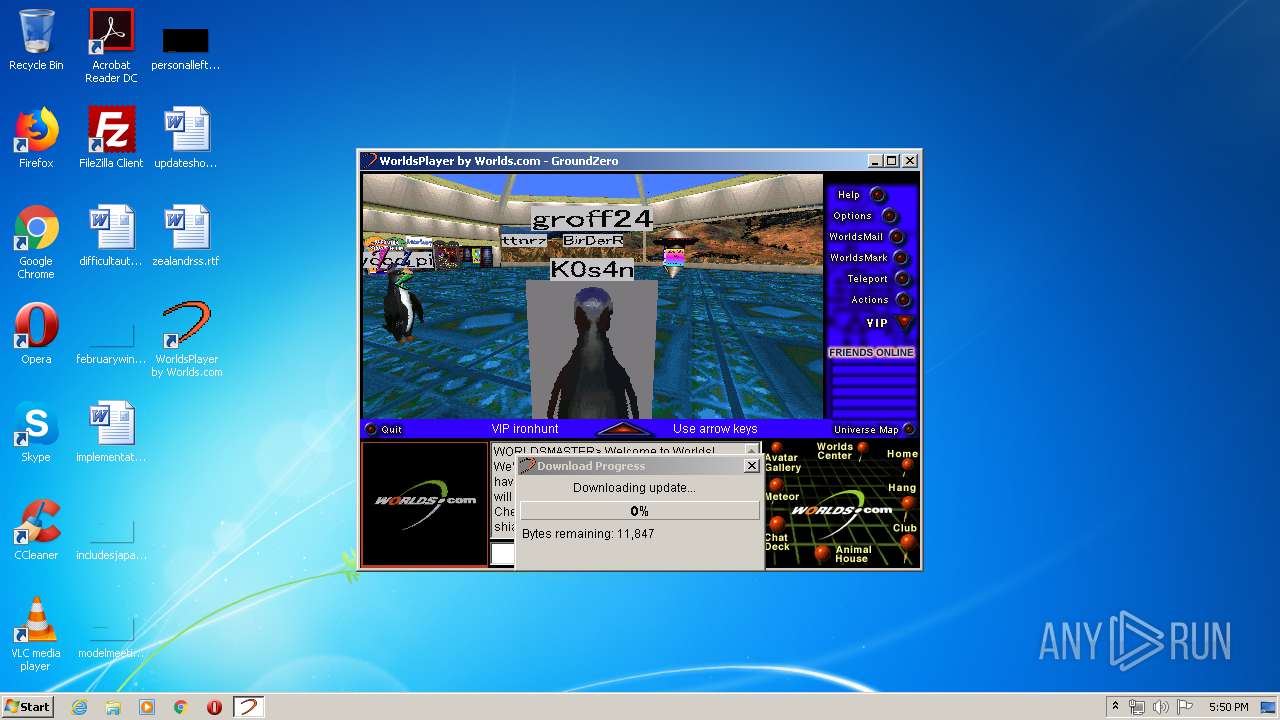
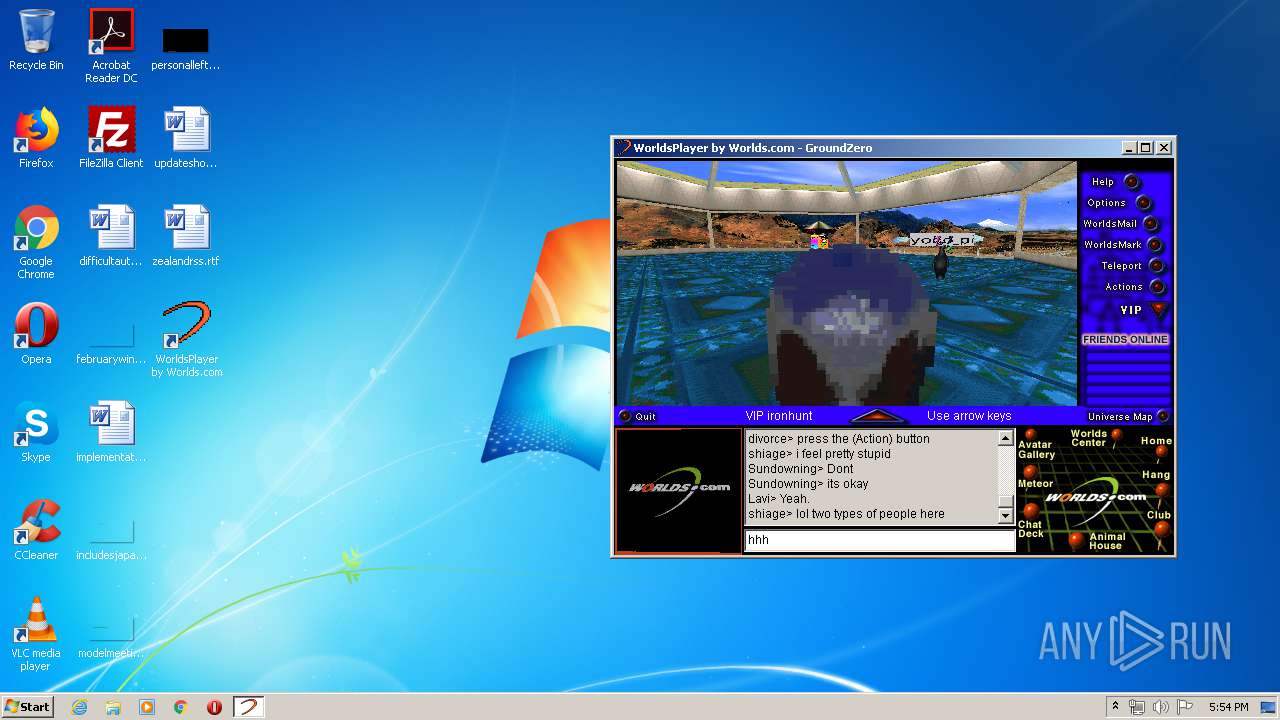
Drops Coronavirus (possible) decoy
- javaw.exe (PID: 3448)
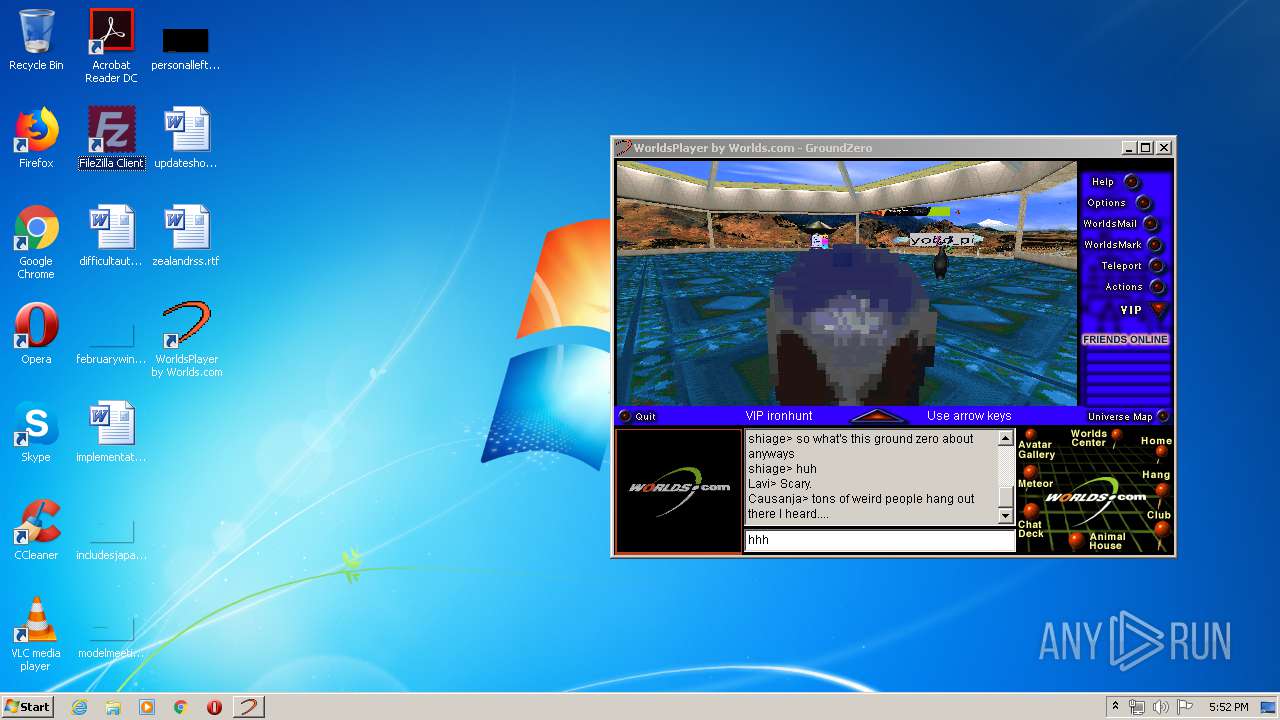
Manual execution by user
- filezilla.exe (PID: 4052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ 4.x (63.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (14.8) |
| .exe | | | Win64 Executable (generic) (13.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.1) |
| .exe | | | Win32 Executable (generic) (2.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1997:06:17 00:43:16+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 4.2 |
| CodeSize: | 15872 |
| InitializedDataSize: | 11776 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x31e0 |
| OSVersion: | 4 |
| ImageVersion: | 4 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Jun-1997 22:43:16 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 16-Jun-1997 22:43:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00003D44 | 0x00003E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4352 |
.rdata | 0x00005000 | 0x000003A9 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.83701 |
.data | 0x00006000 | 0x00001578 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.65504 |
.idata | 0x00008000 | 0x000007DA | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.0361 |
.rsrc | 0x00009000 | 0x0000039C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.18331 |
.reloc | 0x0000A000 | 0x00000682 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.32619 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.37233 | 744 | UNKNOWN | English - United States | RT_ICON |
108 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
GDI32.dll |
KERNEL32.dll |
USER32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
_MainWndProc@16 | 1 | 0x00002839 |
_StubFileWrite@12 | 2 | 0x00002D52 |
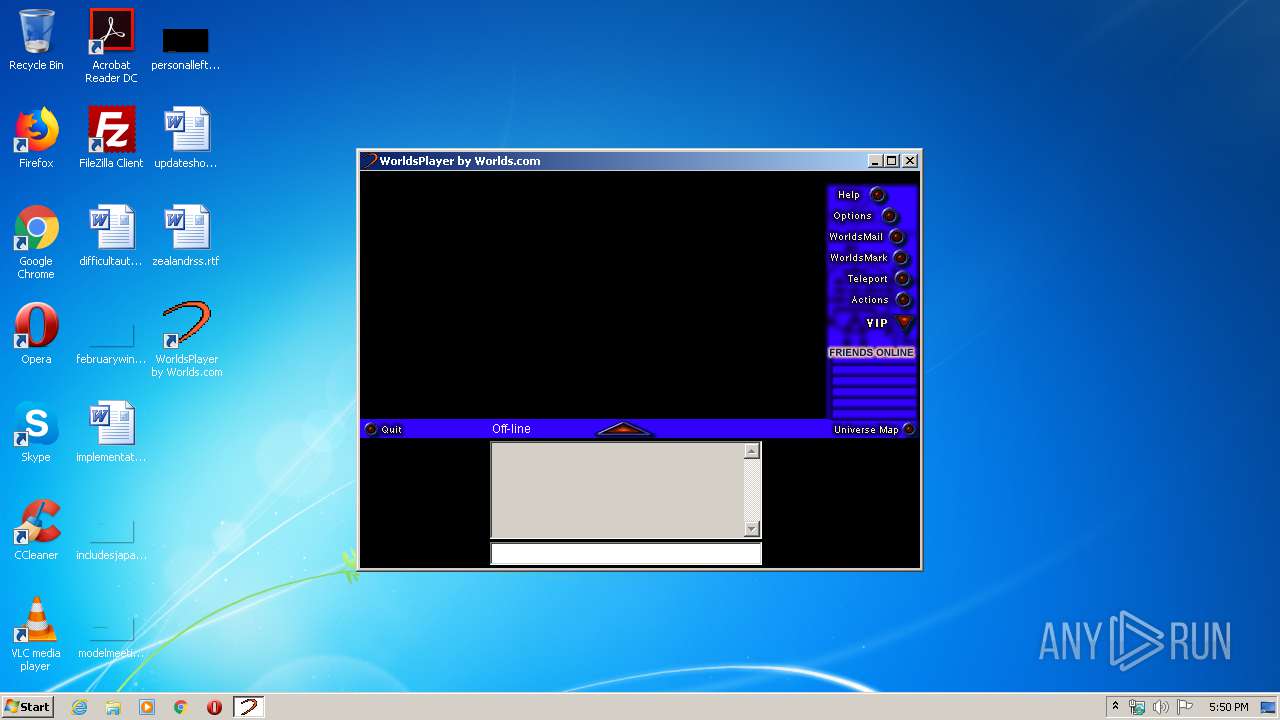
Total processes
53
Monitored processes
7
Malicious processes
5
Suspicious processes
0
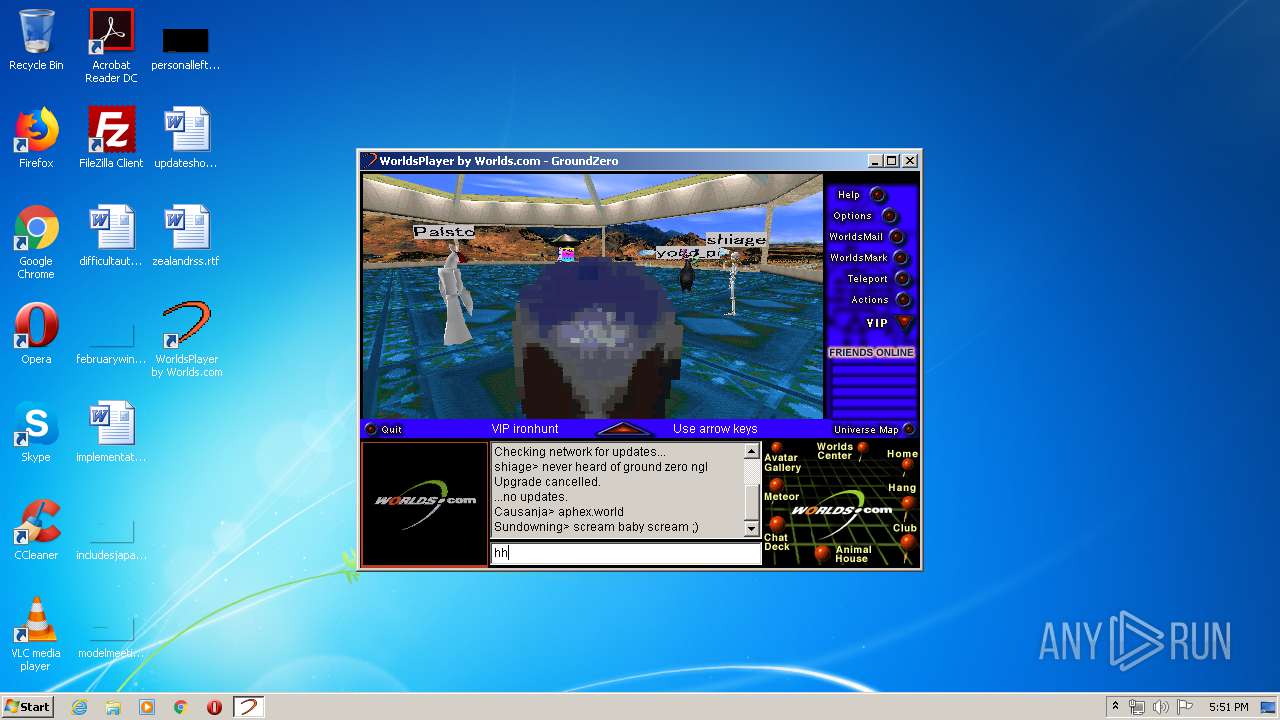
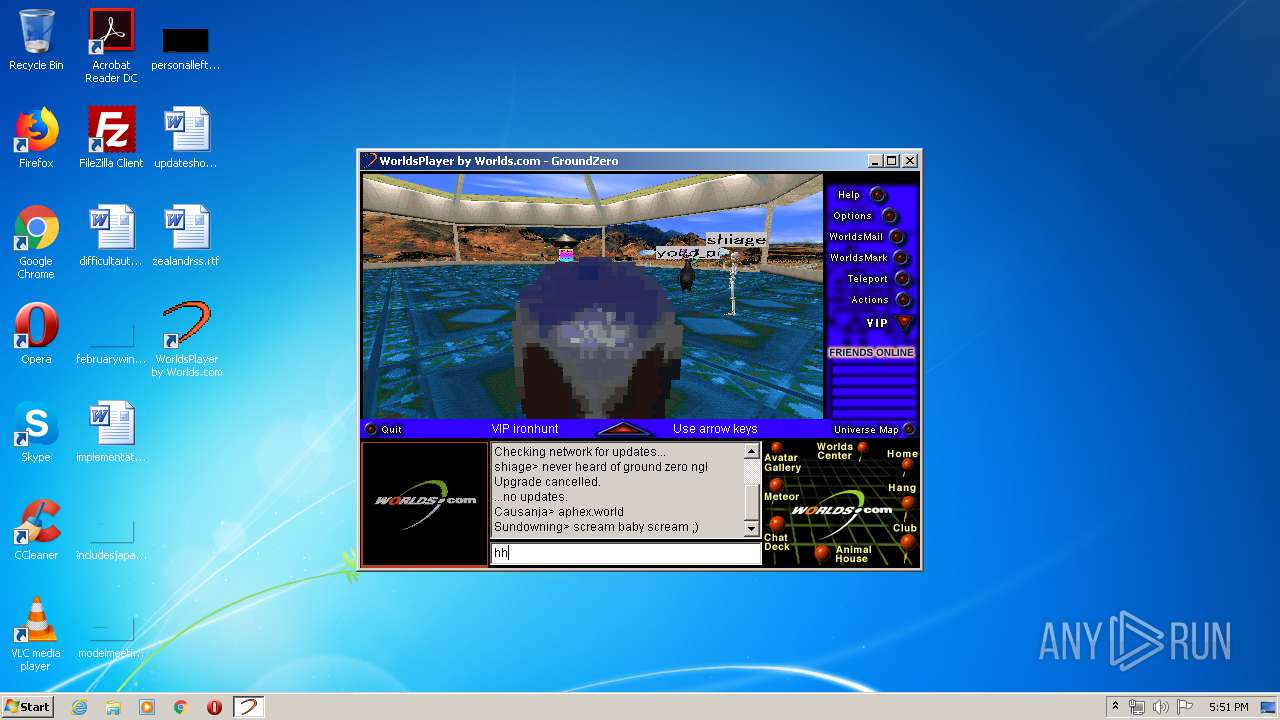
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2064 | "C:\Users\admin\AppData\Local\Temp\GLF8732.tmp\GROUND~1.EXE" | C:\Users\admin\AppData\Local\Temp\GLF8732.tmp\GROUND~1.EXE | first.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2348 | "C:\Users\admin\AppData\Local\Temp\GLF8732.tmp\first.exe" | C:\Users\admin\AppData\Local\Temp\GLF8732.tmp\first.exe | Worlds1890.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2900 | "C:\PROGRA~1\Worlds\WORLDS~1.COM\run.exe" | C:\PROGRA~1\Worlds\WORLDS~1.COM\run.exe | — | first.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3096 | "C:\Users\admin\AppData\Local\Temp\Worlds1890.exe" | C:\Users\admin\AppData\Local\Temp\Worlds1890.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
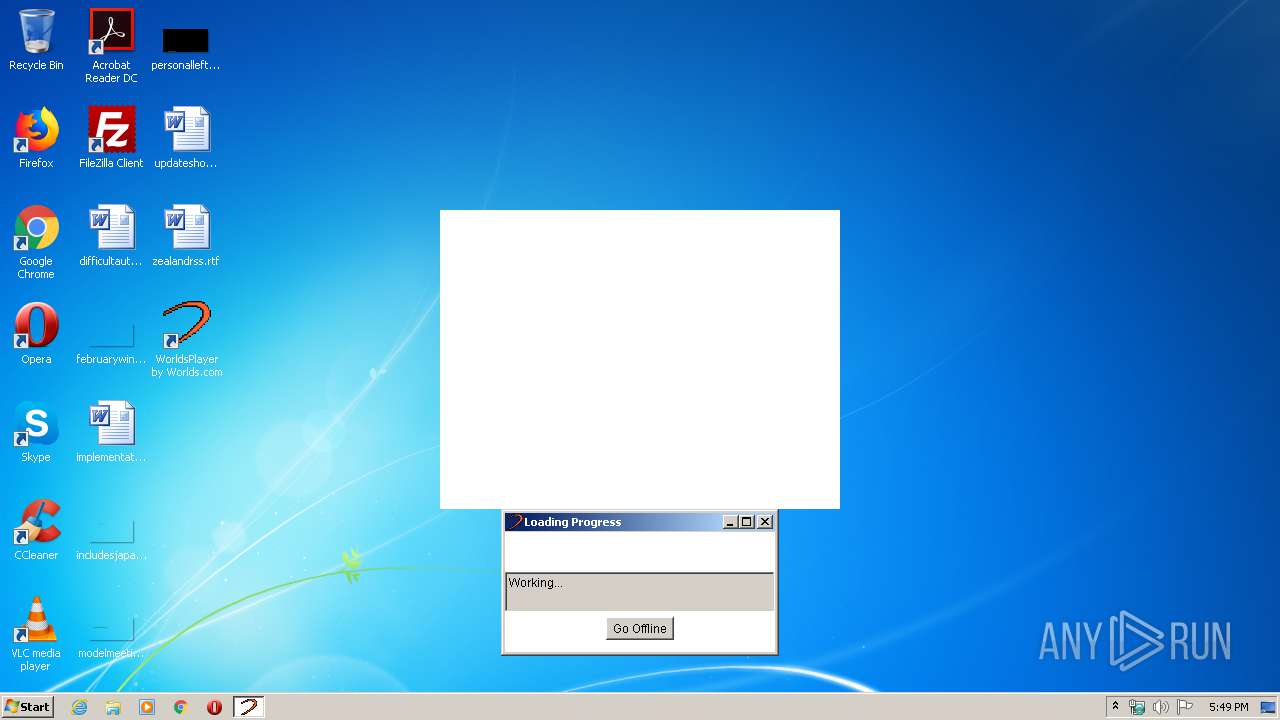
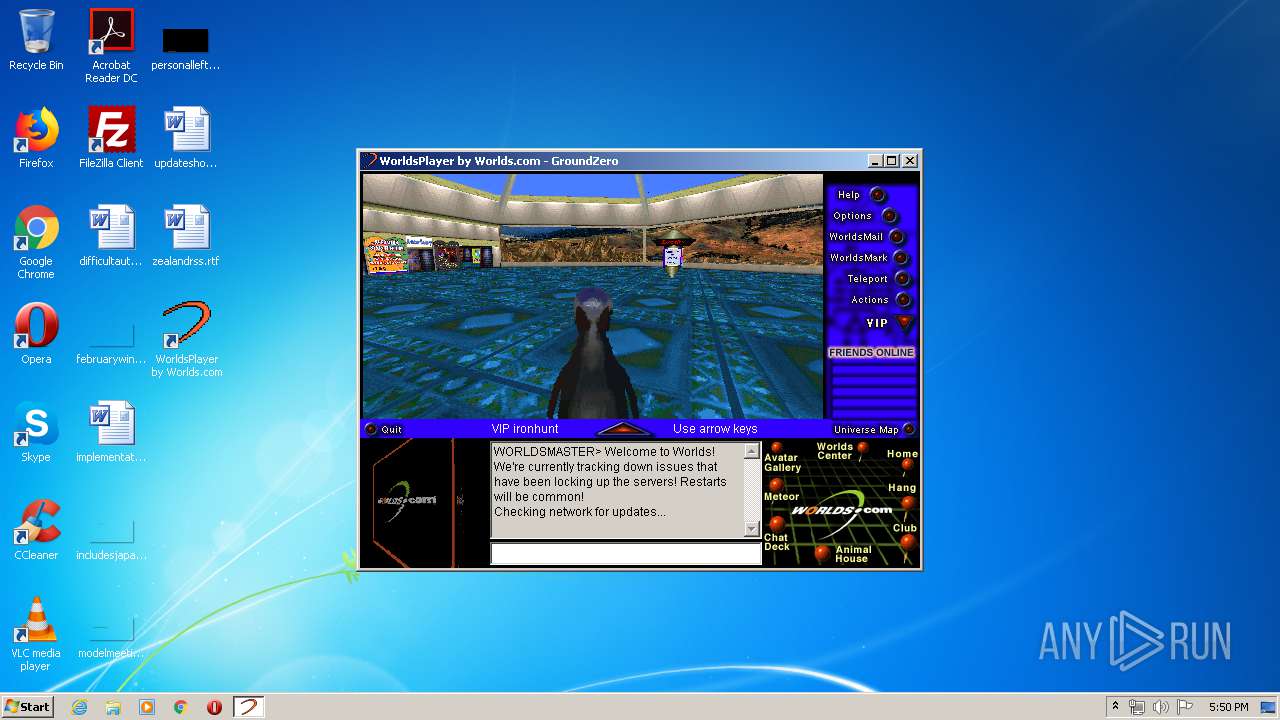
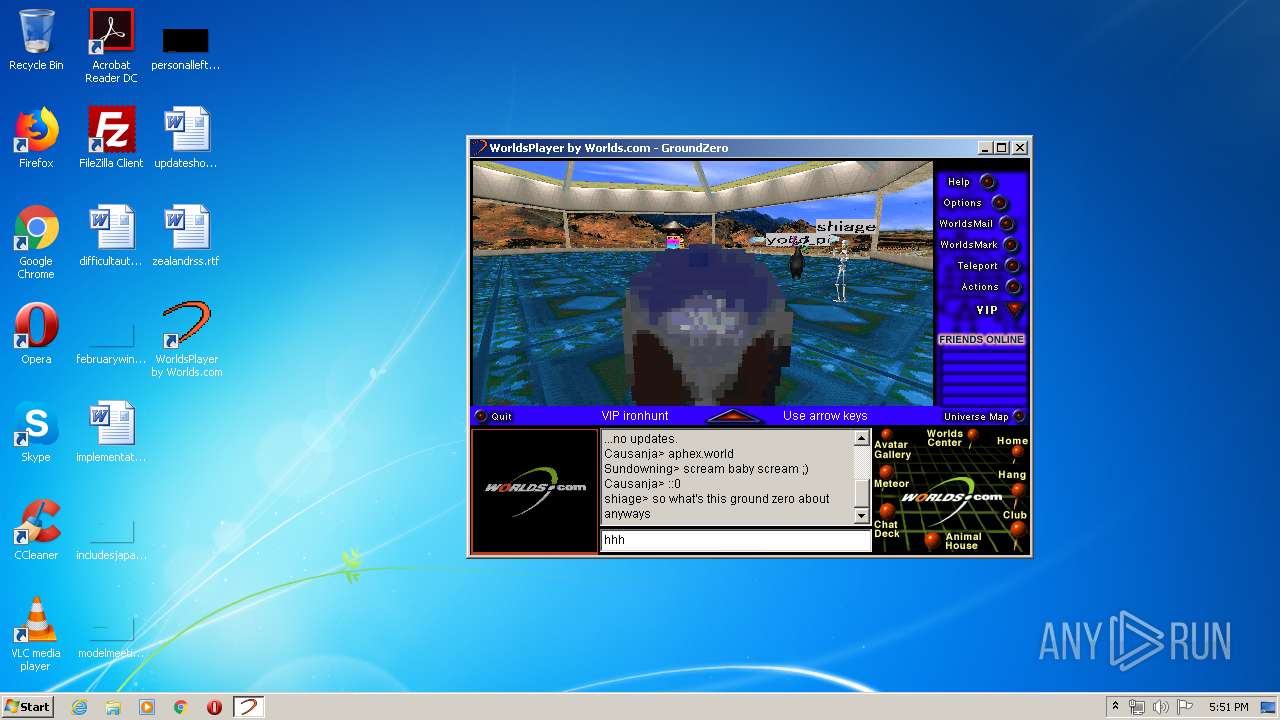
| 3448 | "C:\Program Files\Worlds\WorldsPlayer by Worlds.com\bin\javaw.exe" -Xbootclasspath:lib\i18ncls.zip;lib\rt.jar -cp .;lib\gammacls.zip NET.worlds.console.Gamma -home . -dllpath bin | C:\Program Files\Worlds\WorldsPlayer by Worlds.com\bin\javaw.exe | run.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3636 | "C:\Users\admin\AppData\Local\Temp\Worlds1890.exe" | C:\Users\admin\AppData\Local\Temp\Worlds1890.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4052 | "C:\Program Files\FileZilla FTP Client\filezilla.exe" | C:\Program Files\FileZilla FTP Client\filezilla.exe | — | explorer.exe | |||||||||||
User: admin Company: FileZilla Project Integrity Level: MEDIUM Description: FileZilla FTP Client Exit code: 0 Version: 3, 36, 0, 0 Modules
| |||||||||||||||
Total events
28 358
Read events
28 319
Write events
39
Delete events
0
Modification events
| (PID) Process: | (3636) Worlds1890.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3636) Worlds1890.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2348) first.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Windows\System32\msvcrt.dll |
Value: 2 | |||
| (PID) Process: | (2348) first.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall |
| Operation: | write | Name: | DisplayName |
Value: WorldsPlayer by Worlds.com | |||
| (PID) Process: | (2348) first.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall |
| Operation: | write | Name: | UninstallString |
Value: C:\Windows\system32\UN-GAMMA.EXE C:\PROGRA~1\Worlds\WORLDS~1.COM\INSTALL.LOG | |||
| (PID) Process: | (2348) first.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.world |
| Operation: | write | Name: | |
Value: Gamma.Browser | |||
| (PID) Process: | (2348) first.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.world |
| Operation: | write | Name: | Content Type |
Value: application/x-gamma-world | |||
| (PID) Process: | (2348) first.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\world |
| Operation: | write | Name: | |
Value: URL: WorldsPlayer WORLD File | |||
| (PID) Process: | (2348) first.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\world |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (2348) first.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\world\shell\open\command |
| Operation: | write | Name: | |
Value: "C:\PROGRA~1\Worlds\WORLDS~1.COM\bin\gdkup.exe" "%1" | |||
Executable files
51
Suspicious files
233
Text files
235
Unknown types
109
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3636 | Worlds1890.exe | C:\Users\admin\AppData\Local\Temp\GLF8732.tmp\~GLH0000.TMP | — | |
MD5:— | SHA256:— | |||
| 3636 | Worlds1890.exe | C:\Users\admin\AppData\Local\Temp\GLF8732.tmp\~GLH0001.TMP | — | |
MD5:— | SHA256:— | |||
| 3636 | Worlds1890.exe | C:\Users\admin\AppData\Local\Temp\GLF8732.tmp\~GLH0002.TMP | — | |
MD5:— | SHA256:— | |||
| 3636 | Worlds1890.exe | C:\Users\admin\AppData\Local\Temp\GLF8732.tmp\mmedia\~GLH0003.TMP | — | |
MD5:— | SHA256:— | |||
| 2348 | first.exe | C:\Users\admin\AppData\Local\Temp\~GLH0001.TMP | — | |
MD5:— | SHA256:— | |||
| 2348 | first.exe | C:\Users\admin\AppData\Local\Temp\~GLH0002.TMP | — | |
MD5:— | SHA256:— | |||
| 2348 | first.exe | C:\Users\admin\AppData\Local\Temp\~GLH0003.TMP | — | |
MD5:— | SHA256:— | |||
| 2348 | first.exe | C:\Program Files\Worlds\WorldsPlayer by Worlds.com\~GLH0005.TMP | — | |
MD5:— | SHA256:— | |||
| 2348 | first.exe | C:\Program Files\Worlds\WorldsPlayer by Worlds.com\~GLH0006.TMP | — | |
MD5:— | SHA256:— | |||
| 2348 | first.exe | C:\Program Files\Worlds\WorldsPlayer by Worlds.com\~GLH0007.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
407
TCP/UDP connections
255
DNS requests
13
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
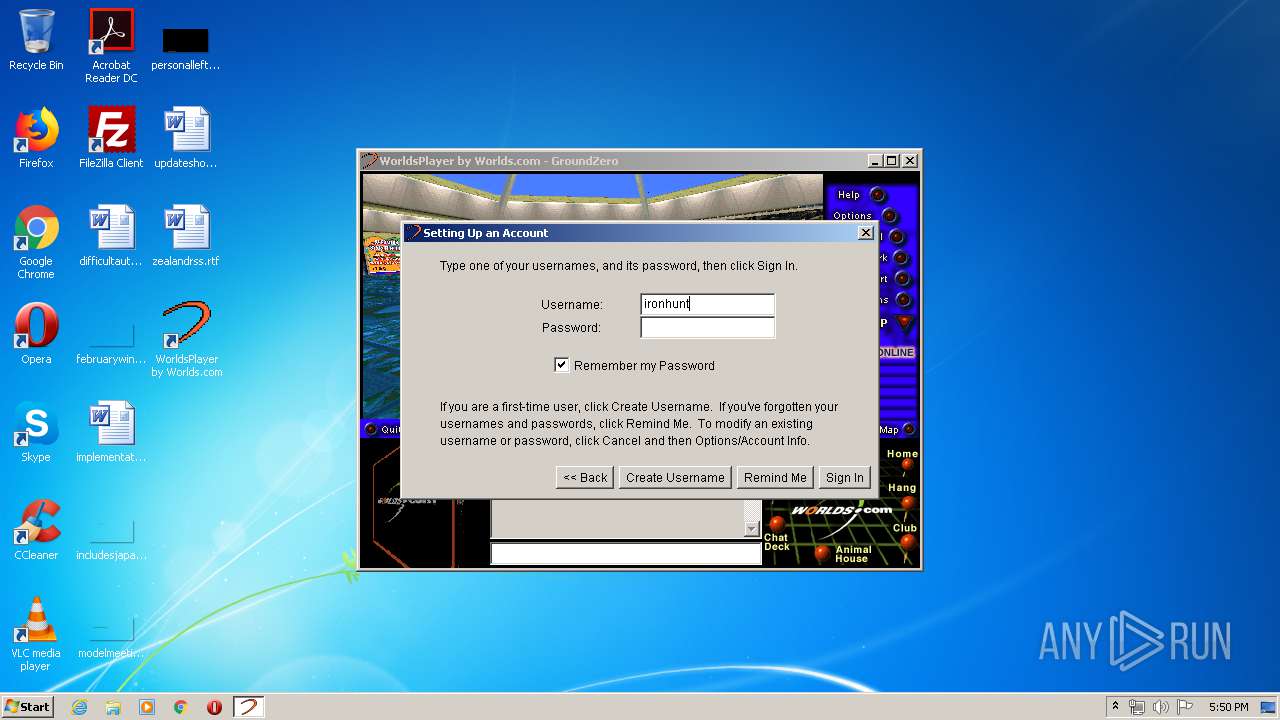
3448 | javaw.exe | GET | 302 | 209.240.84.122:80 | http://209.240.84.122/3DCDup/actions/actions.dat | US | html | 234 b | suspicious |
3448 | javaw.exe | GET | 200 | 142.44.227.102:80 | http://cache.worlds.com/3DCDup/I18N/languages.lst | CA | text | 137 b | suspicious |
3448 | javaw.exe | GET | 302 | 209.240.84.122:80 | http://209.240.84.122/3DCDup/tables/tables.dat | US | html | 232 b | suspicious |
3448 | javaw.exe | GET | 302 | 209.240.84.122:80 | http://209.240.84.122/3DCDup/I18N/fonts.lst | US | html | 229 b | suspicious |
3448 | javaw.exe | GET | 200 | 142.44.227.102:80 | http://cache.worlds.com/3DCDup/tables/tables.dat | CA | binary | 41.7 Kb | suspicious |
3448 | javaw.exe | GET | 200 | 142.44.227.102:80 | http://cache.worlds.com/3DCDup/avatar/avatars.dat | CA | text | 160 Kb | suspicious |
3448 | javaw.exe | GET | 302 | 209.240.84.122:80 | http://209.240.84.122/3DCDup/I18N/languages.lst | US | html | 233 b | suspicious |
3448 | javaw.exe | GET | 200 | 142.44.227.102:80 | http://cache.worlds.com/3DCDup/actions/actions.dat | CA | text | 1.38 Kb | suspicious |
3448 | javaw.exe | GET | 200 | 209.240.84.122:80 | http://cube02.us.worlds.net/cgi-bin/clock/clock.pl | US | html | 170 b | suspicious |
3448 | javaw.exe | GET | 302 | 209.240.84.122:80 | http://209.240.84.122/3DCDup/avatar/avatars.dat | US | html | 233 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3448 | javaw.exe | 209.240.84.122:80 | www-static.us.worlds.net | ipHouse | US | suspicious |
3448 | javaw.exe | 142.44.227.102:80 | us1.worlds.net | OVH SAS | CA | suspicious |
3448 | javaw.exe | 167.114.150.60:37 | time.worlds.net | OVH SAS | CA | suspicious |
3448 | javaw.exe | 209.240.84.122:6650 | www-static.us.worlds.net | ipHouse | US | suspicious |
3448 | javaw.exe | 209.240.84.122:5673 | www-static.us.worlds.net | ipHouse | US | suspicious |
— | — | 209.240.84.122:80 | www-static.us.worlds.net | ipHouse | US | suspicious |
— | — | 142.44.227.102:80 | us1.worlds.net | OVH SAS | CA | suspicious |
3448 | javaw.exe | 167.114.150.60:80 | time.worlds.net | OVH SAS | CA | suspicious |
3448 | javaw.exe | 66.177.24.186:80 | www.badsworld.com | Comcast Cable Communications, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
us1.worlds.net |
| whitelisted |
cache.worlds.com |
| suspicious |
www-static.us.worlds.net |
| suspicious |
cube02.us.worlds.net |
| suspicious |
time.worlds.net |
| suspicious |
www.3dcd.com |
| suspicious |
www-dynamic.us.worlds.net |
| suspicious |
www.badsworld.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3448 | javaw.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
3448 | javaw.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
3448 | javaw.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |