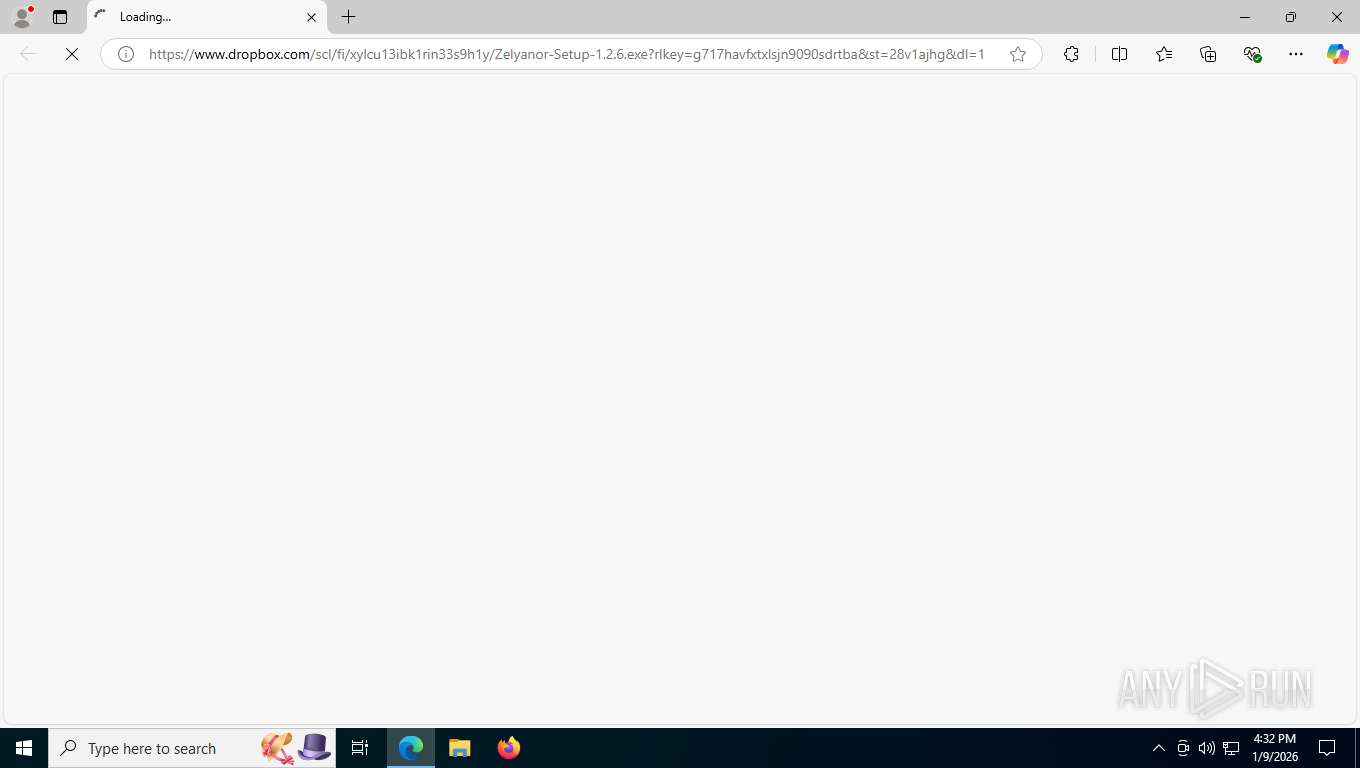
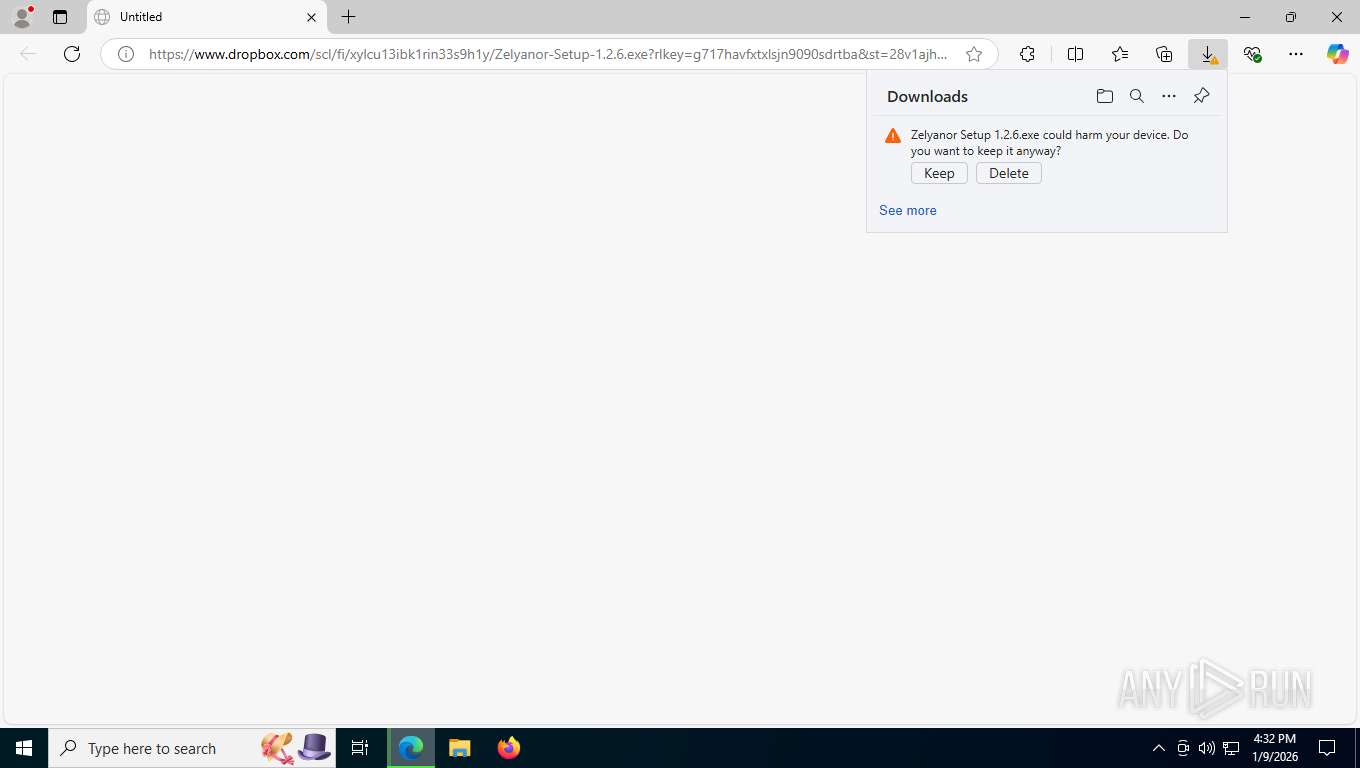
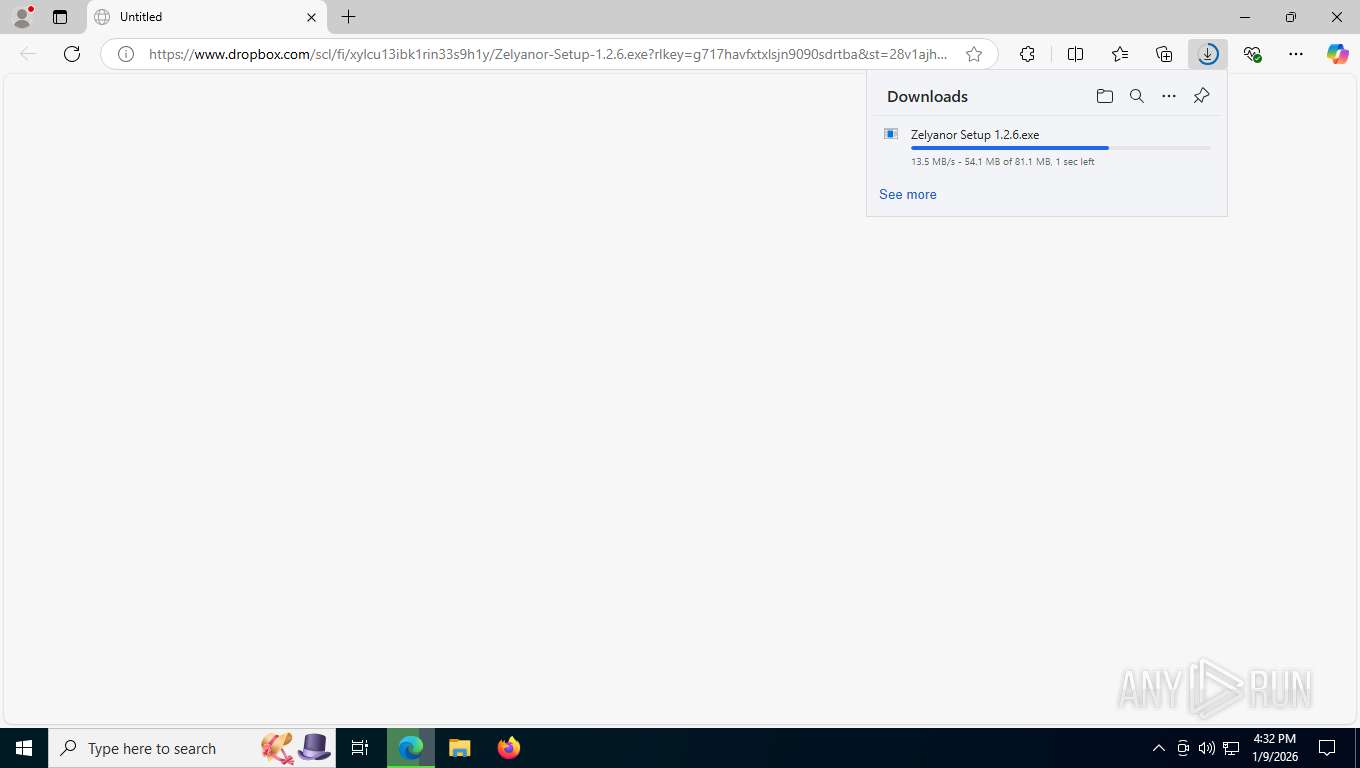
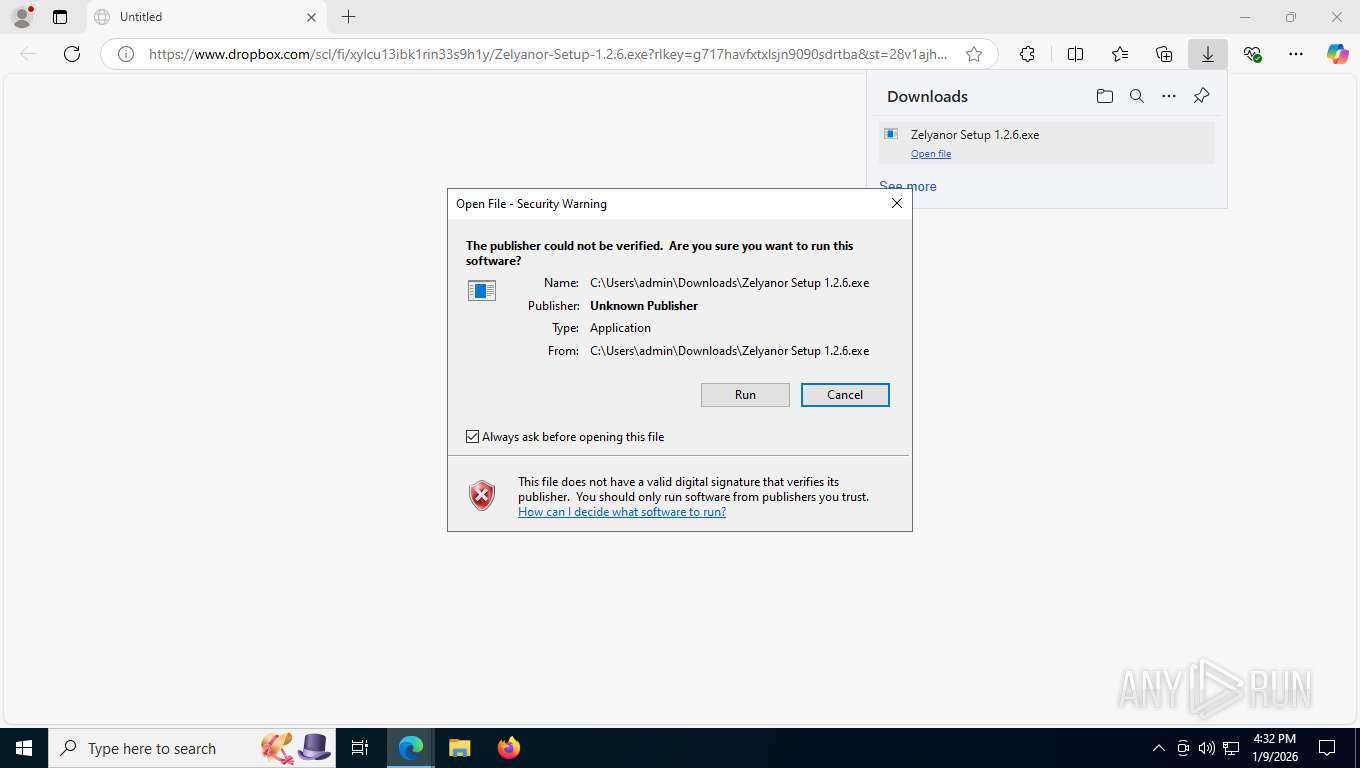
| URL: | https://www.dropbox.com/scl/fi/xylcu13ibk1rin33s9h1y/Zelyanor-Setup-1.2.6.exe?rlkey=g717havfxtxlsjn9090sdrtba&st=28v1ajhg&dl=1 |
| Full analysis: | https://app.any.run/tasks/fb15090f-719c-4d11-889f-a030c4fad8ba |
| Verdict: | Malicious activity |
| Analysis date: | January 09, 2026, 21:32:01 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A92EE53E6352E11D8648D5314E8C4708 |
| SHA1: | A8C88AD5AB9D43C1E2E881EE6A795AF3C020F991 |
| SHA256: | 4AC7D6F1E44D116C6078160D149EDD4CD14D03406563C3DF45BDF0347DDA53A3 |
| SSDEEP: | 3:N8DSLcVHGkG63b0bNwI3cpV5IZxySadNIoVPkD/XPWBWUn:2OLHkZRL5IfkgIC/XPGWUn |
MALICIOUS
Changes powershell execution policy (Unrestricted)
- Zelyanor.exe (PID: 8816)
Get Video Controller Information (POWERSHELL)
- Zelyanor.exe (PID: 8816)
Get Monitor Information (POWERSHELL)
- Zelyanor.exe (PID: 8816)
Collects BIOS Properties (Win32_BIOS) (SCRIPT)
- powershell.exe (PID: 8596)
SUSPICIOUS
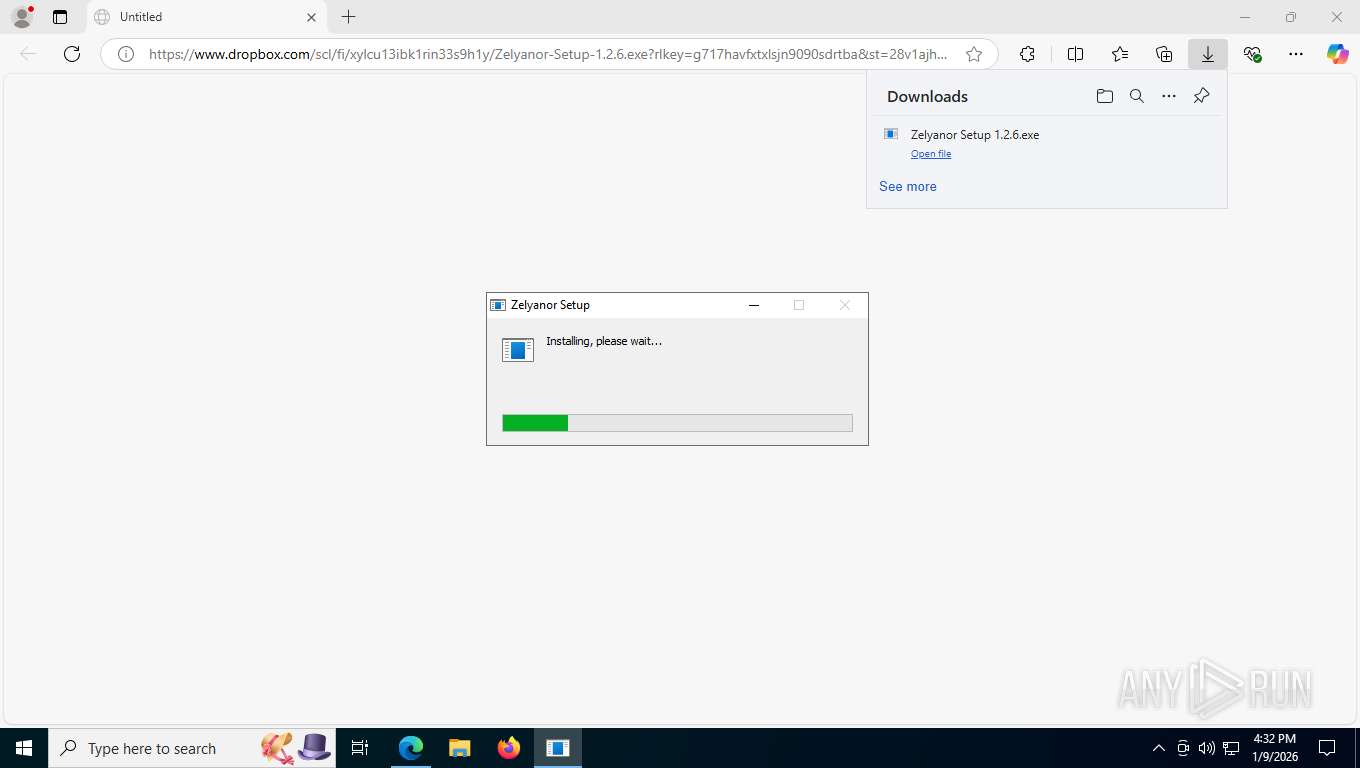
The process creates files with name similar to system file names
- Zelyanor Setup 1.2.6.exe (PID: 8544)
Malware-specific behavior (creating "System.dll" in Temp)
- Zelyanor Setup 1.2.6.exe (PID: 8544)
Get information on the list of running processes
- Zelyanor Setup 1.2.6.exe (PID: 8544)
- cmd.exe (PID: 8580)
Starts CMD.EXE for commands execution
- Zelyanor Setup 1.2.6.exe (PID: 8544)
- Zelyanor.exe (PID: 8816)
Drops 7-zip archiver for unpacking
- Zelyanor Setup 1.2.6.exe (PID: 8544)
Reads security settings of Internet Explorer
- Zelyanor Setup 1.2.6.exe (PID: 8544)
Executable content was dropped or overwritten
- Zelyanor Setup 1.2.6.exe (PID: 8544)
Process drops legitimate windows executable
- Zelyanor Setup 1.2.6.exe (PID: 8544)
The process hides Powershell's copyright startup banner
- Zelyanor.exe (PID: 8816)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 8232)
- cmd.exe (PID: 7164)
- cmd.exe (PID: 10624)
- cmd.exe (PID: 10836)
- cmd.exe (PID: 11096)
- cmd.exe (PID: 9896)
- cmd.exe (PID: 10184)
- cmd.exe (PID: 11240)
The process bypasses the loading of PowerShell profile settings
- Zelyanor.exe (PID: 8816)
Starts POWERSHELL.EXE for commands execution
- Zelyanor.exe (PID: 8816)
Probably obfuscated PowerShell command line is found
- Zelyanor.exe (PID: 8816)
Starts application with an unusual extension
- cmd.exe (PID: 9168)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 8616)
Obfuscation pattern (POWERSHELL)
- powershell.exe (PID: 8784)
Application launched itself
- Zelyanor.exe (PID: 8816)
INFO
Application launched itself
- msedge.exe (PID: 7500)
Create files in a temporary directory
- Zelyanor Setup 1.2.6.exe (PID: 8544)
Checks supported languages
- Zelyanor Setup 1.2.6.exe (PID: 8544)
- identity_helper.exe (PID: 7400)
- Zelyanor.exe (PID: 8816)
- chcp.com (PID: 7368)
- Zelyanor.exe (PID: 9084)
- Zelyanor.exe (PID: 2224)
Reads the computer name
- identity_helper.exe (PID: 7400)
- Zelyanor Setup 1.2.6.exe (PID: 8544)
- Zelyanor.exe (PID: 8816)
- Zelyanor.exe (PID: 9084)
- Zelyanor.exe (PID: 2224)
Reads Environment values
- identity_helper.exe (PID: 7400)
- Zelyanor.exe (PID: 8816)
The sample compiled with english language support
- Zelyanor Setup 1.2.6.exe (PID: 8544)
Creates a software uninstall entry
- Zelyanor Setup 1.2.6.exe (PID: 8544)
Creates files or folders in the user directory
- Zelyanor Setup 1.2.6.exe (PID: 8544)
- Zelyanor.exe (PID: 8816)
Manual execution by a user
- Zelyanor.exe (PID: 8816)
Process checks computer location settings
- Zelyanor.exe (PID: 8816)
Reads product name
- Zelyanor.exe (PID: 8816)
Changes the display of characters in the console
- cmd.exe (PID: 9168)
Reads the machine GUID from the registry
- Zelyanor.exe (PID: 8816)
Search a value from a registry key
- powershell.exe (PID: 5284)
Checks proxy server information
- Zelyanor.exe (PID: 8816)
- slui.exe (PID: 9900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
265
Monitored processes
113
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 508 | C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe -NoProfile -NoLogo -InputFormat Text -ExecutionPolicy Unrestricted -Command "Add-Type -AssemblyName System.Windows.Forms; [System.Windows.Forms.SystemInformation]::TerminalServerSession" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Zelyanor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1204 | taskkill /F /T /IM "watcher.exe" | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1524 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1836 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2224 | "C:\Users\admin\AppData\Local\Programs\Zelyanor\Zelyanor.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\Zelyanor" --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=2532,i,4327944926283592126,13326615993384225158,262144 --enable-features=PdfUseShowSaveFilePicker --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit --variations-seed-version --mojo-platform-channel-handle=2528 /prefetch:2 | C:\Users\admin\AppData\Local\Programs\Zelyanor\Zelyanor.exe | — | Zelyanor.exe | |||||||||||
User: admin Company: FallikGames Integrity Level: LOW Description: SetupofZelyanor Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 2252 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6180,i,2405880508027499661,419952745945557524,262144 --variations-seed-version --mojo-platform-channel-handle=6152 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2284 | C:\WINDOWS\system32\cmd.exe /d /s /c "WHERE smartctl 2>nul" | C:\Windows\System32\cmd.exe | — | Zelyanor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2368 | taskkill /F /T /IM "mitmweb.exe" | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2668 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7844,i,2405880508027499661,419952745945557524,262144 --variations-seed-version --mojo-platform-channel-handle=7452 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
92 155
Read events
92 143
Write events
12
Delete events
0
Modification events
| (PID) Process: | (8544) Zelyanor Setup 1.2.6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\792baca7-78a1-5eef-9c16-9c42ad6bb508 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Local\Programs\Zelyanor | |||
| (PID) Process: | (8544) Zelyanor Setup 1.2.6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\792baca7-78a1-5eef-9c16-9c42ad6bb508 |
| Operation: | write | Name: | KeepShortcuts |
Value: true | |||
| (PID) Process: | (8544) Zelyanor Setup 1.2.6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\792baca7-78a1-5eef-9c16-9c42ad6bb508 |
| Operation: | write | Name: | ShortcutName |
Value: Zelyanor | |||
| (PID) Process: | (8544) Zelyanor Setup 1.2.6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\792baca7-78a1-5eef-9c16-9c42ad6bb508 |
| Operation: | write | Name: | DisplayName |
Value: Zelyanor 1.0.0 | |||
| (PID) Process: | (8544) Zelyanor Setup 1.2.6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\792baca7-78a1-5eef-9c16-9c42ad6bb508 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Users\admin\AppData\Local\Programs\Zelyanor\Uninstall Zelyanor.exe" /currentuser | |||
| (PID) Process: | (8544) Zelyanor Setup 1.2.6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\792baca7-78a1-5eef-9c16-9c42ad6bb508 |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Users\admin\AppData\Local\Programs\Zelyanor\Uninstall Zelyanor.exe" /currentuser /S | |||
| (PID) Process: | (8544) Zelyanor Setup 1.2.6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\792baca7-78a1-5eef-9c16-9c42ad6bb508 |
| Operation: | write | Name: | DisplayVersion |
Value: 1.0.0 | |||
| (PID) Process: | (8544) Zelyanor Setup 1.2.6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\792baca7-78a1-5eef-9c16-9c42ad6bb508 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\AppData\Local\Programs\Zelyanor\Zelyanor.exe,0 | |||
| (PID) Process: | (8544) Zelyanor Setup 1.2.6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\792baca7-78a1-5eef-9c16-9c42ad6bb508 |
| Operation: | write | Name: | Publisher |
Value: FallikGames | |||
| (PID) Process: | (8544) Zelyanor Setup 1.2.6.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\792baca7-78a1-5eef-9c16-9c42ad6bb508 |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
Executable files
29
Suspicious files
56
Text files
435
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFfdd37.TMP | — | |
MD5:— | SHA256:— | |||
| 7500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFfdd47.TMP | — | |
MD5:— | SHA256:— | |||
| 7500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFfdd47.TMP | — | |
MD5:— | SHA256:— | |||
| 7500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFfdd57.TMP | — | |
MD5:— | SHA256:— | |||
| 7500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFfdd57.TMP | — | |
MD5:— | SHA256:— | |||
| 7500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFfdd47.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
78
TCP/UDP connections
66
DNS requests
72
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7840 | msedge.exe | GET | 200 | 162.125.72.15:443 | https://ucf87a7a697dd81756a7eb25bf81.dl.dropboxusercontent.com/cd/0/get/C4o5Xaqi4HXHZztEeSaEGv0f2hyLSI9r0bWh67Un5mJgqAGu-Z7r0D4Dv1qJyVfq_MudPszOM8dY2sUuwLcjXQO7bJ715zr4YBkUQsKoFVmeWgivbYDA4eVn1IfOYxXtsKdETZUFnbViSKH9He2pYHA7/file?dl=1 | US | — | — | unknown |
7840 | msedge.exe | GET | 302 | 162.125.72.18:443 | https://www.dropbox.com/scl/fi/xylcu13ibk1rin33s9h1y/Zelyanor-Setup-1.2.6.exe?rlkey=g717havfxtxlsjn9090sdrtba&st=28v1ajhg&dl=1 | US | — | — | unknown |
7840 | msedge.exe | GET | 304 | 150.171.28.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | US | — | — | whitelisted |
7840 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=65&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1741678270&lafgdate=0 | US | text | 768 b | whitelisted |
7840 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:36YfvEk4v4Ysg0R2rOtwHNMw0EdfHPwvYGDi78GKipA&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 100 b | whitelisted |
7840 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
7840 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=65&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1767994328&lafgdate=0 | US | text | 4.54 Kb | whitelisted |
7840 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/extensionwebstorebase/v1/crx?os=win&arch=x64&os_arch=x86_64&nacl_arch=x86-64&prod=edgecrx&prodchannel=&prodversion=133.0.3065.92&lang=en-US&acceptformat=crx3,puff&x=id%3Djmjflgjpcpepeafmmgdpfkogkghcpiha%26v%3D1.2.1%26installedby%3Dother%26uc%26ping%3Dr%253D540%2526e%253D1 | US | xml | 413 b | whitelisted |
7840 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/entityextractiontemplates/api/v1/assets/find-assets?name=edge_hub_apps_manifest_gz&version=4.11.*&channel=stable&key=d414dd4f9db345fa8003e32adc81b362 | US | text | 266 b | whitelisted |
7840 | msedge.exe | POST | 200 | 216.58.206.35:443 | https://update.googleapis.com/service/update2/json?cup2key=14:Mn2KFtttoN0iZXTqBzzBn11xXKRPMFwU5dhSTMn3E3Y&cup2hreq=622429b6c2d72d41974476b871c6a811f98de184434a79cf3b4a862938ca079b | US | text | 889 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5604 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5824 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7840 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7840 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7840 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7840 | msedge.exe | 162.125.72.18:443 | www.dropbox.com | DROPBOX | US | whitelisted |
7840 | msedge.exe | 104.18.22.222:443 | copilot.microsoft.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.dropbox.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
ucf87a7a697dd81756a7eb25bf81.dl.dropboxusercontent.com |
| unknown |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET INFO EXE - Served Attached HTTP |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |