| File name: | 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit |
| Full analysis: | https://app.any.run/tasks/7a60be5d-64f3-47e6-b37c-6428bf02cdc7 |
| Verdict: | Malicious activity |
| Threats: | LockBit, a ransomware variant, encrypts data on infected machines, demanding a ransom payment for decryption. Used in targeted attacks, It's a significant risk to organizations. |
| Analysis date: | March 24, 2025, 15:28:12 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 117417884271B3F761735F43504C8167 |
| SHA1: | 47BB4D43D6796322F2C9BFCD906AAA7798D3ED59 |
| SHA256: | 4AC3D4758249746BDBA91B9226DCB4F59EE5D616096AC15C287D3FFCA86BC746 |
| SSDEEP: | 3072:3mhXodguLP/5qUpfDT6zT73wCJhsH+aOM3Anu:rKzTfaOMy |
MALICIOUS
Known privilege escalation attack
- dllhost.exe (PID: 5404)
Renames files like ransomware
- 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe (PID: 2236)
RANSOMWARE has been detected
- 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe (PID: 2236)
Steals credentials from Web Browsers
- 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe (PID: 2236)
Actions looks like stealing of personal data
- 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe (PID: 2236)
[YARA] LockBit is detected
- 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe (PID: 2236)
SUSPICIOUS
Write to the desktop.ini file (may be used to cloak folders)
- 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe (PID: 2236)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 5576)
INFO
Reads security settings of Internet Explorer
- dllhost.exe (PID: 5404)
Checks supported languages
- 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe (PID: 2108)
- 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe (PID: 2236)
- ShellExperienceHost.exe (PID: 5576)
- SearchApp.exe (PID: 2568)
Reads the computer name
- 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe (PID: 2108)
- 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe (PID: 2236)
- ShellExperienceHost.exe (PID: 5576)
- SearchApp.exe (PID: 2568)
Reads the machine GUID from the registry
- 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe (PID: 2108)
- SearchApp.exe (PID: 2568)
Creates files in the program directory
- 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe (PID: 2236)
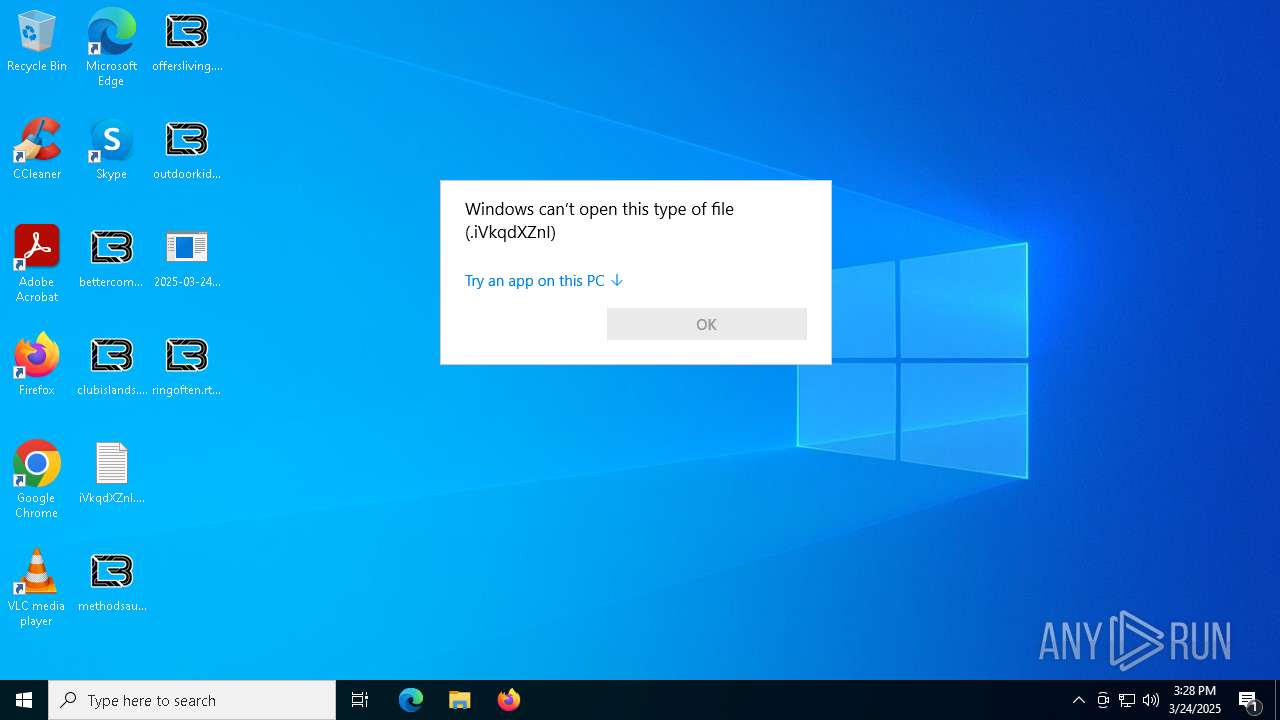
Manual execution by a user
- OpenWith.exe (PID: 5260)
- OpenWith.exe (PID: 5984)
- notepad.exe (PID: 1272)
- OpenWith.exe (PID: 4448)
- OpenWith.exe (PID: 856)
- OpenWith.exe (PID: 6344)
- OpenWith.exe (PID: 2644)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 5260)
- OpenWith.exe (PID: 4448)
- OpenWith.exe (PID: 5984)
- OpenWith.exe (PID: 856)
- OpenWith.exe (PID: 6344)
- OpenWith.exe (PID: 2644)
Creates files or folders in the user directory
- 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe (PID: 2236)
Create files in a temporary directory
- 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe (PID: 2236)
Checks proxy server information
- SearchApp.exe (PID: 2568)
Process checks computer location settings
- SearchApp.exe (PID: 2568)
Reads the software policy settings
- SearchApp.exe (PID: 2568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:09:09 01:27:01+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.12 |
| CodeSize: | 99328 |
| InitializedDataSize: | 50688 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1946f |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
137
Monitored processes
12
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Downloads\starslength.png.iVkqdXZnI | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1272 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Downloads\iVkqdXZnI.README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2108 | "C:\Users\admin\Desktop\2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe" | C:\Users\admin\Desktop\2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2236 | "C:\Users\admin\Desktop\2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe" | C:\Users\admin\Desktop\2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe | dllhost.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 2568 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2644 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Downloads\quiteenvironment.jpg.iVkqdXZnI | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4448 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Downloads\noticeupon.png.iVkqdXZnI | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5260 | "C:\WINDOWS\System32\OpenWith.exe" C:\Users\admin\Downloads\unitedrated.png.iVkqdXZnI | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5404 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\SysWOW64\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5576 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 905
Read events
10 850
Write events
54
Delete events
1
Modification events
| (PID) Process: | (5404) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (5576) ShellExperienceHost.exe | Key: | \REGISTRY\A\{040f20b7-15c8-f992-6978-0dcb41a913a3}\LocalState |
| Operation: | write | Name: | PeekBadges |
Value: 5B005D00000049BBCE62D19CDB01 | |||
| (PID) Process: | (4448) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.iVkqdXZnI\OpenWithProgids |
| Operation: | write | Name: | iVkqdXZnI |
Value: | |||
| (PID) Process: | (5984) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.iVkqdXZnI\OpenWithProgids |
| Operation: | write | Name: | iVkqdXZnI |
Value: | |||
| (PID) Process: | (5260) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.iVkqdXZnI\OpenWithProgids |
| Operation: | write | Name: | iVkqdXZnI |
Value: | |||
| (PID) Process: | (856) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.iVkqdXZnI\OpenWithProgids |
| Operation: | write | Name: | iVkqdXZnI |
Value: | |||
| (PID) Process: | (6344) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.iVkqdXZnI\OpenWithProgids |
| Operation: | write | Name: | iVkqdXZnI |
Value: | |||
| (PID) Process: | (2644) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.iVkqdXZnI\OpenWithProgids |
| Operation: | write | Name: | iVkqdXZnI |
Value: | |||
| (PID) Process: | (2568) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\SearchSettings |
| Operation: | write | Name: | SafeSearchMode |
Value: 1 | |||
| (PID) Process: | (2568) SearchApp.exe | Key: | \REGISTRY\A\{9afb95de-ea6d-1ae7-e936-2bf9e3fb1bc9}\LocalState |
| Operation: | write | Name: | BINGIDENTITY_PROP_USEREMAIL |
Value: 000091C8B198D19CDB01 | |||
Executable files
23
Suspicious files
1 911
Text files
2 120
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2236 | 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe | C:\$Recycle.Bin\S-1-5-18\NNNNNNNNNNN | binary | |
MD5:345D1E7D913F1FE6B174110EEA3FE700 | SHA256:F71A97D734FDFBCFCB8C96F950A4E281FD6073D15892C2E7056C5CE3702CD608 | |||
| 2236 | 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe | C:\$Recycle.Bin\S-1-5-18\IIIIIIIIIII | binary | |
MD5:345D1E7D913F1FE6B174110EEA3FE700 | SHA256:F71A97D734FDFBCFCB8C96F950A4E281FD6073D15892C2E7056C5CE3702CD608 | |||
| 2236 | 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe | C:\Users\iVkqdXZnI.README.txt | text | |
MD5:57CD2F1290F2ED4234B7FAD8E2F9D3D5 | SHA256:4541156F3F2F1FD37C72F72F4FC8EC41CD078696BF4A52AF0EA099B436D2A1A6 | |||
| 2236 | 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe | C:\$Recycle.Bin\S-1-5-18\FFFFFFFFFFF | binary | |
MD5:345D1E7D913F1FE6B174110EEA3FE700 | SHA256:F71A97D734FDFBCFCB8C96F950A4E281FD6073D15892C2E7056C5CE3702CD608 | |||
| 2236 | 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe | C:\$Recycle.Bin\S-1-5-18\DDDDDDDDDDD | binary | |
MD5:345D1E7D913F1FE6B174110EEA3FE700 | SHA256:F71A97D734FDFBCFCB8C96F950A4E281FD6073D15892C2E7056C5CE3702CD608 | |||
| 2236 | 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe | C:\iVkqdXZnI.README.txt | text | |
MD5:57CD2F1290F2ED4234B7FAD8E2F9D3D5 | SHA256:4541156F3F2F1FD37C72F72F4FC8EC41CD078696BF4A52AF0EA099B436D2A1A6 | |||
| 2236 | 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe | C:\$Recycle.Bin\S-1-5-18\CCCCCCCCCCC | binary | |
MD5:345D1E7D913F1FE6B174110EEA3FE700 | SHA256:F71A97D734FDFBCFCB8C96F950A4E281FD6073D15892C2E7056C5CE3702CD608 | |||
| 2236 | 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe | C:\$Recycle.Bin\S-1-5-18\EEEEEEEEEEE | binary | |
MD5:345D1E7D913F1FE6B174110EEA3FE700 | SHA256:F71A97D734FDFBCFCB8C96F950A4E281FD6073D15892C2E7056C5CE3702CD608 | |||
| 2236 | 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe | C:\$Recycle.Bin\S-1-5-18\BBBBBBBBBBB | binary | |
MD5:345D1E7D913F1FE6B174110EEA3FE700 | SHA256:F71A97D734FDFBCFCB8C96F950A4E281FD6073D15892C2E7056C5CE3702CD608 | |||
| 2236 | 2025-03-24_117417884271b3f761735f43504c8167_darkside_lockbit.exe | C:\$Recycle.Bin\S-1-5-18\GGGGGGGGGGG | binary | |
MD5:345D1E7D913F1FE6B174110EEA3FE700 | SHA256:F71A97D734FDFBCFCB8C96F950A4E281FD6073D15892C2E7056C5CE3702CD608 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
20
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.122.30:443 | https://www.bing.com/manifest/threshold.appcache | unknown | text | 3.46 Kb | whitelisted |
— | — | GET | 200 | 2.19.122.30:443 | https://www.bing.com/rb/18/jnc,nj/6hU_LneafI_NFLeDvM367ebFaKQ.js?bu=DyIrb3t-gQF4cnWyAbUBK6UBK7gB&or=w | unknown | binary | 21.3 Kb | whitelisted |
— | — | GET | 200 | 2.19.122.33:443 | https://www.bing.com/rb/6i/ortl,cc,nc/fvNdnrKxhhxDQUEi09cCaSWpzzE.css?bu=CbYMygq7DMoKvwzKCsoKygrKCg&or=w | unknown | text | 428 Kb | whitelisted |
— | — | GET | 200 | 2.19.122.34:443 | https://www.bing.com/rb/16/jnc,nj/pNXV2ymlrFEAOVLUgJkRBRwYFkY.js?bu=Diozf4wBkwGWAYkBggGGAcQBxwEzuwHKAQ&or=w | unknown | binary | 21.7 Kb | whitelisted |
— | — | GET | 200 | 2.19.122.30:443 | https://www.bing.com/AS/API/WindowsCortanaPane/V2/Init | unknown | html | 127 Kb | whitelisted |
— | — | GET | 200 | 2.19.122.22:443 | https://www.bing.com/rb/19/cir3,ortl,cc,nc/vOJNaIfAXvJzmnBm845ss-M9YR8.css?bu=B4QDRvEC1gFkZI8D&or=w | unknown | text | 5.97 Kb | whitelisted |
— | — | GET | 200 | 2.19.122.32:443 | https://www.bing.com/rb/19/cir3,ortl,cc,nc/FgBbpIj0thGWZOh_xFnM9i4O7ek.css?bu=C_QJ-AOrBcoKrgmYCbcHZGRkZA&or=w | unknown | text | 19.8 Kb | whitelisted |
— | — | POST | 204 | 2.19.122.23:443 | https://www.bing.com/threshold/xls.aspx | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.122.27:443 | https://www.bing.com/rb/3C/ortl,cc,nc/AptopUBu7_oVDubJxwvaIprW-lI.css?bu=A4gCjAKPAg&or=w | unknown | text | 15.5 Kb | whitelisted |
— | — | GET | 200 | 2.19.122.30:443 | https://www.bing.com/rp/-iNIzuEypRdgRJ6xnyVHizZ3bpM.br.js | unknown | binary | 17.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2568 | SearchApp.exe | 2.19.96.128:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |