| File name: | FLOCOXOCO.exe |
| Full analysis: | https://app.any.run/tasks/48c8bc81-c794-40d3-bc24-9df59166cf16 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 13:54:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6ED75E7116B518246938786FF3780AA2 |
| SHA1: | BE0953FF45DECAF6A0F5621F26C64DFC2D4B5EE3 |
| SHA256: | 4A9F6B288FEA001124952319DADEA7E590BDF1C4D13FA0FEC39E4B9BAD9A909B |
| SSDEEP: | 98304:UpDZ5Q2hJ3kl5P6n7UwSDR5izwdOCTicqPHUmkl76TltQcTPtD6AN0FB7ghE:q5QOkl5P6g3izwdOCTi7PHUmklqltTM |
MALICIOUS
Writes to a start menu file
- Folds0Aapis.exe (PID: 2232)
SUSPICIOUS
Reads internet explorer settings
- FLOCOXOCO.exe (PID: 3744)
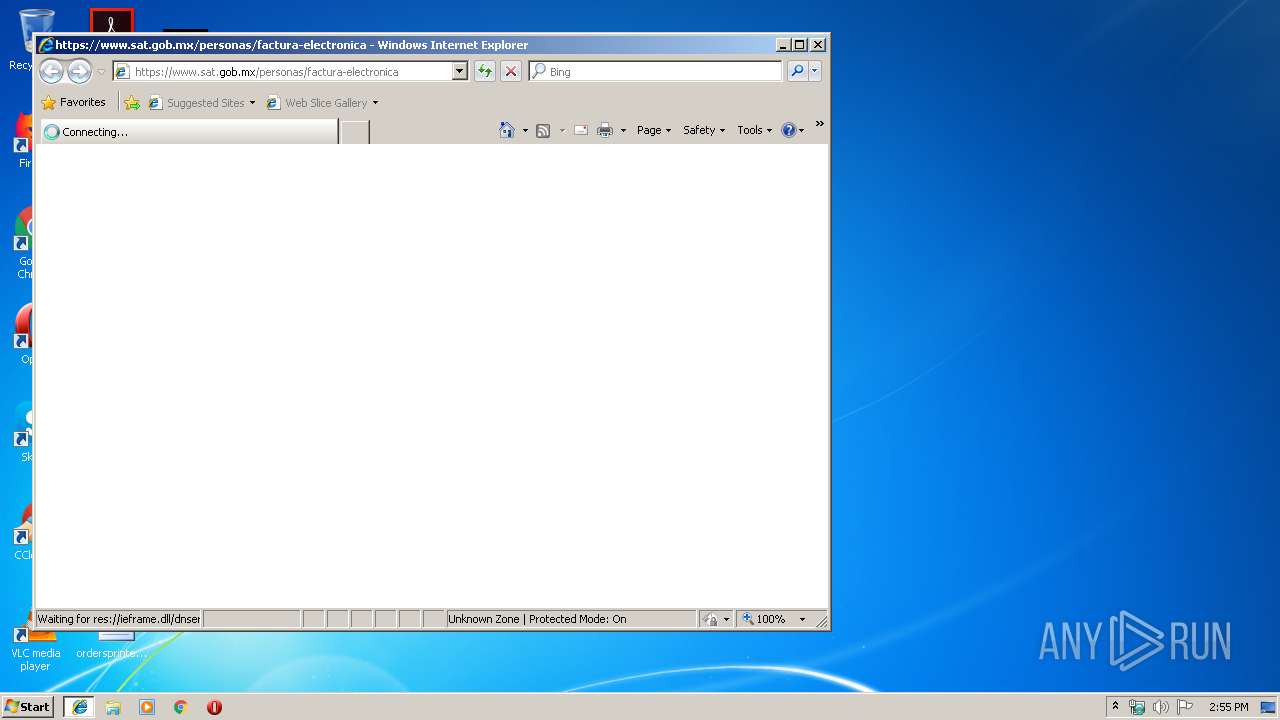
Starts Internet Explorer
- FLOCOXOCO.exe (PID: 3744)
Creates files in the user directory
- FLOCOXOCO.exe (PID: 3744)
- Folds0Aapis.exe (PID: 2232)
Executable content was dropped or overwritten
- Folds0Aapis.exe (PID: 2232)
Reads Environment values
- Folds0Aapis.exe (PID: 2232)
INFO
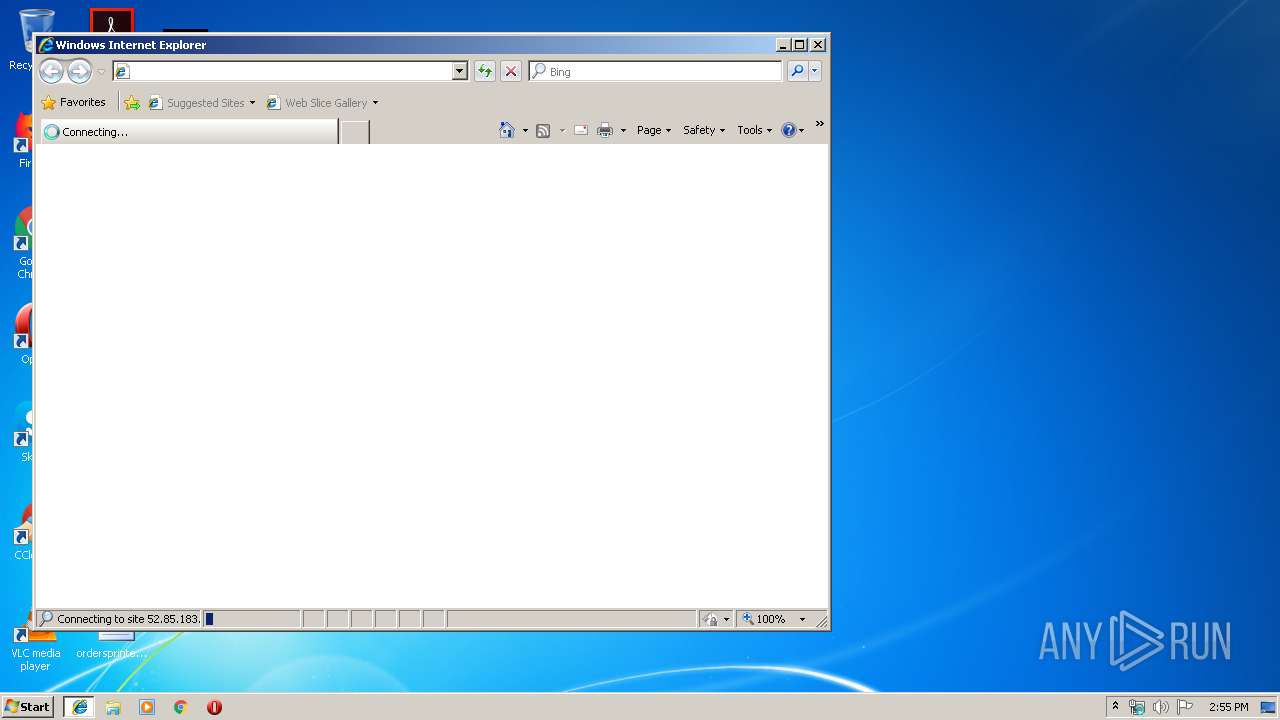
Reads internet explorer settings
- iexplore.exe (PID: 2592)
Creates files in the user directory
- iexplore.exe (PID: 2592)
Changes internet zones settings
- iexplore.exe (PID: 2424)
Reads Internet Cache Settings
- iexplore.exe (PID: 2592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (45.2) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (43.6) |
| .exe | | | Win32 Executable (generic) (4.7) |
| .exe | | | Win16/32 Executable Delphi generic (2.1) |
| .exe | | | Generic Win/DOS Executable (2.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:18 06:51:37+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 5854208 |
| InitializedDataSize: | 987648 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5962e0 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileDescription: | FLOCOXOCO |
| FileVersion: | 1.0.0.0 |
| ProductName: | FLOCOXOCO |
| ProductVersion: | 1.0.0.0 |
| ProgramID: | com.embarcadero.FLOCOXOCO |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Jul-2019 04:51:37 |
| Detected languages: |
|
| FileDescription: | FLOCOXOCO |
| FileVersion: | 1.0.0.0 |
| ProductName: | FLOCOXOCO |
| ProductVersion: | 1.0.0.0 |
| ProgramID: | com.embarcadero.FLOCOXOCO |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 11 |
| Time date stamp: | 18-Jul-2019 04:51:37 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0058CF78 | 0x0058D000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.48944 |
.itext | 0x0058E000 | 0x0000838C | 0x00008400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.84154 |
.data | 0x00597000 | 0x00016BA4 | 0x00016C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.7348 |
.bss | 0x005AE000 | 0x0001B7F0 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x005CA000 | 0x000057B2 | 0x00005800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.32585 |
.didata | 0x005D0000 | 0x00000BBA | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.30774 |
.edata | 0x005D1000 | 0x0000009B | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.94231 |
.tls | 0x005D2000 | 0x00000054 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x005D3000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.35484 |
.reloc | 0x005D4000 | 0x0006C3DC | 0x0006C400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.722 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.27093 | 1803 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.20666 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 3.00046 | 308 | UNKNOWN | English - United States | RT_CURSOR |
4 | 2.56318 | 308 | UNKNOWN | English - United States | RT_CURSOR |
5 | 2.6949 | 308 | UNKNOWN | English - United States | RT_CURSOR |
6 | 2.62527 | 308 | UNKNOWN | English - United States | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | English - United States | RT_CURSOR |
8 | 1.77511 | 308 | UNKNOWN | English - United States | RT_CURSOR |
9 | 2.6633 | 308 | UNKNOWN | English - United States | RT_CURSOR |
3682 | 2.04342 | 76 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
URLMON.DLL |
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
gdiplus.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
msvcrt.dll |
netapi32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x005B163C |
__dbk_fcall_wrapper | 2 | 0x00011520 |
TMethodImplementationIntercept | 3 | 0x000CE4D0 |
Total processes
35
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2232 | "C:\Users\admin\AppData\Roaming\Sadminx\Folds0Aapis.exe" | C:\Users\admin\AppData\Roaming\Sadminx\Folds0Aapis.exe | FLOCOXOCO.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: AdrikTools Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2424 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | FLOCOXOCO.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2424 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3744 | "C:\Users\admin\AppData\Local\Temp\FLOCOXOCO.exe" | C:\Users\admin\AppData\Local\Temp\FLOCOXOCO.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: FLOCOXOCO Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 658
Read events
1 553
Write events
105
Delete events
0
Modification events
| (PID) Process: | (2424) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2424) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2424) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2424) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2424) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2424) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000077000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2424) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {AB98093B-A963-11E9-B506-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2424) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2424) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (2424) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070700040012000D0037001000CD03 | |||
Executable files
1
Suspicious files
2
Text files
20
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2424 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2424 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3744 | FLOCOXOCO.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@dropbox[1].txt | — | |
MD5:— | SHA256:— | |||
| 3744 | FLOCOXOCO.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@www.dropbox[1].txt | — | |
MD5:— | SHA256:— | |||
| 2592 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2424 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Feeds Cache\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 2424 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].png | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
| 2592 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3744 | FLOCOXOCO.exe | C:\Users\admin\AppData\Roaming\Sadminx\Folds0Aapis.exe | — | |
MD5:— | SHA256:— | |||
| 2592 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U7R8ZLRM\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
9
DNS requests
8
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3744 | FLOCOXOCO.exe | GET | 200 | 107.180.51.87:80 | http://foliofiscalcomprobantes.com/superp/index.php | US | — | — | suspicious |
2424 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2424 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2592 | iexplore.exe | 52.85.183.52:443 | www.sat.gob.mx | Amazon.com, Inc. | US | unknown |
3744 | FLOCOXOCO.exe | 162.125.66.1:443 | www.dropbox.com | Dropbox, Inc. | DE | shared |
3744 | FLOCOXOCO.exe | 162.125.66.6:443 | uc7ff6c05a3cf5dad0f8c3f58447.dl.dropboxusercontent.com | Dropbox, Inc. | DE | shared |
2592 | iexplore.exe | 52.85.183.116:443 | www.sat.gob.mx | Amazon.com, Inc. | US | unknown |
3744 | FLOCOXOCO.exe | 107.180.51.87:80 | foliofiscalcomprobantes.com | GoDaddy.com, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.sat.gob.mx |
| whitelisted |
www.dropbox.com |
| shared |
uc7ff6c05a3cf5dad0f8c3f58447.dl.dropboxusercontent.com |
| malicious |
foliofiscalcomprobantes.com |
| suspicious |
noismx5ny8xoc8ymde5.serveminecraft.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3744 | FLOCOXOCO.exe | Potential Corporate Privacy Violation | SUSPICIOUS [PTsecurity] Dropbox SSL Payload Request |