| File name: | CapCut_7418125124962107397_installer.exe |
| Full analysis: | https://app.any.run/tasks/526b355f-ffd2-46d0-8a72-06bb5f06507d |
| Verdict: | Malicious activity |
| Analysis date: | February 06, 2025, 21:43:04 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | C91E097550EA6CCEDF592D8B83414E0D |
| SHA1: | 021F3F26D86F98AF28DC987BAAD8714F64867207 |
| SHA256: | 4A9D815F284ADDA187982E2B24DA2BEAAD860739BC4B4CB1CF26408E7C221DD6 |
| SSDEEP: | 98304:hVb9nzGB0LtahqQP4CK+0TTdui7ej1EfTwb+4TA3SkFYInoeHaEfjhNkhooy7qsY:4Zotwoe |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process creates files with name similar to system file names
- CapCut_7418125124962107397_installer.exe (PID: 6224)
- app_package_6a3e547b88.exe (PID: 5252)
Executable content was dropped or overwritten
- CapCut_7418125124962107397_installer.exe (PID: 6224)
- app_package_6a3e547b88.exe (PID: 5252)
There is functionality for taking screenshot (YARA)
- CapCut_7418125124962107397_installer.exe (PID: 6224)
- app_package_6a3e547b88.exe (PID: 5252)
Process drops legitimate windows executable
- app_package_6a3e547b88.exe (PID: 5252)
Creates a software uninstall entry
- app_package_6a3e547b88.exe (PID: 5252)
Drops 7-zip archiver for unpacking
- app_package_6a3e547b88.exe (PID: 5252)
The process drops C-runtime libraries
- app_package_6a3e547b88.exe (PID: 5252)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 2072)
- cmd.exe (PID: 5544)
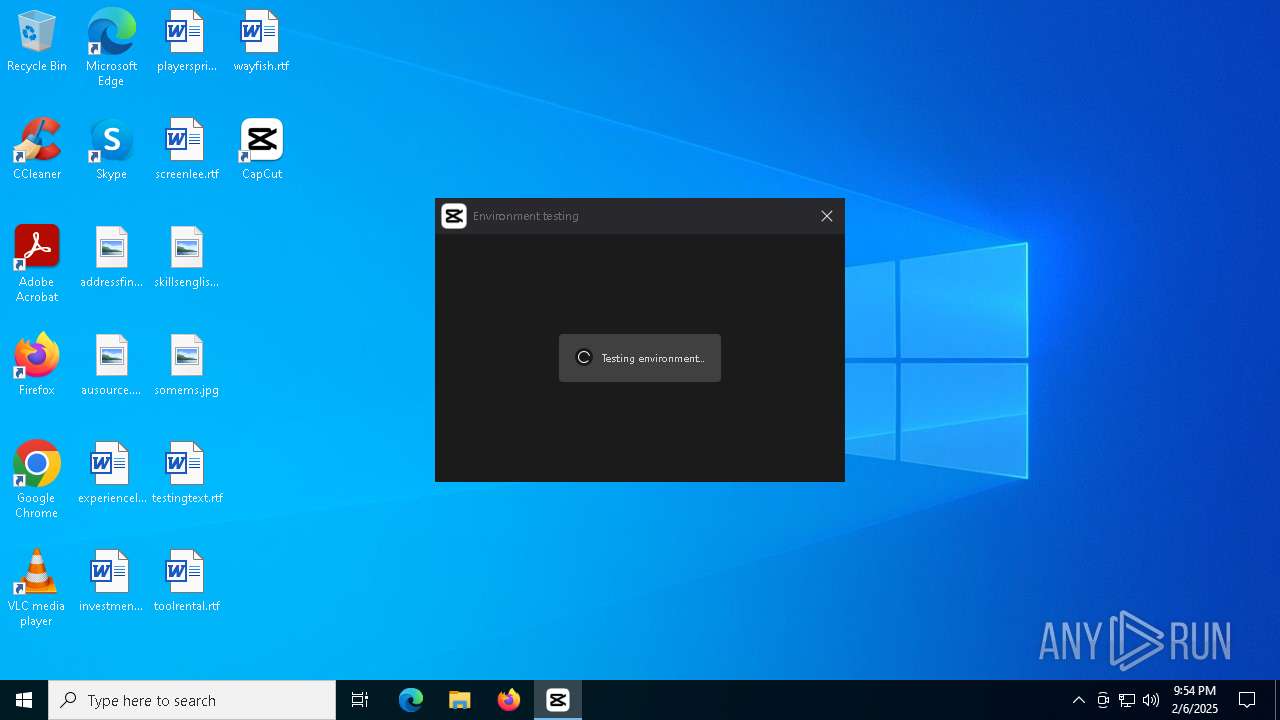
Application launched itself
- CapCut.exe (PID: 4968)
Starts CMD.EXE for commands execution
- CapCut.exe (PID: 4968)
- VEDetector.exe (PID: 6468)
Malware-specific behavior (creating "System.dll" in Temp)
- CapCut_7418125124962107397_installer.exe (PID: 6224)
INFO
Checks supported languages
- CapCut_7418125124962107397_installer.exe (PID: 6224)
- app_package_6a3e547b88.exe (PID: 5252)
Create files in a temporary directory
- CapCut_7418125124962107397_installer.exe (PID: 6224)
- app_package_6a3e547b88.exe (PID: 5252)
Reads the computer name
- CapCut_7418125124962107397_installer.exe (PID: 6224)
- app_package_6a3e547b88.exe (PID: 5252)
The sample compiled with english language support
- CapCut_7418125124962107397_installer.exe (PID: 6224)
- app_package_6a3e547b88.exe (PID: 5252)
Creates files or folders in the user directory
- CapCut_7418125124962107397_installer.exe (PID: 6224)
- app_package_6a3e547b88.exe (PID: 5252)
- BackgroundTransferHost.exe (PID: 5000)
Process checks whether UAC notifications are on
- app_package_6a3e547b88.exe (PID: 5252)
The sample compiled with chinese language support
- app_package_6a3e547b88.exe (PID: 5252)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 6848)
- BackgroundTransferHost.exe (PID: 5000)
- BackgroundTransferHost.exe (PID: 1760)
- BackgroundTransferHost.exe (PID: 6380)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 5000)
Qt framework related mutex has been found
- CapCut.exe (PID: 4968)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 5000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 22:26:14+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 473088 |
| UninitializedDataSize: | 16384 |
| EntryPoint: | 0x338f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
174
Monitored processes
21
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1216 | "C:\Users\admin\AppData\Local\CapCut\Apps\\CapCut.exe" | C:\Users\admin\AppData\Local\CapCut\Apps\CapCut.exe | — | CapCut_7418125124962107397_installer.exe | |||||||||||
User: admin Company: ByteDance Pte. Ltd. Integrity Level: HIGH Description: CapCut Exit code: 0 Version: 1.0.0.000000 Modules
| |||||||||||||||
| 1760 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2072 | C:\WINDOWS\System32\cmd.exe /c wmic csproduct get Name,UUID /value | C:\Windows\System32\cmd.exe | — | VEDetector.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 2828 | "C:\Users\admin\AppData\Local\Temp\CapCut_7418125124962107397_installer.exe" | C:\Users\admin\AppData\Local\Temp\CapCut_7418125124962107397_installer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4076 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | UCPDMgr.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4516 | "C:\WINDOWS\system32\UCPDMgr.exe" | C:\Windows\System32\UCPDMgr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: User Choice Protection Manager Exit code: 0 Version: 1.0.0.414301 Modules
| |||||||||||||||
| 4764 | C:\Users\admin\AppData\Local\CapCut\Apps\5.5.0.2028\parfait_crash_handler.exe "--database=C:\Users\admin\AppData\Local\CapCut\User Data\Crash\\" "--metrics-dir=C:\Users\admin\AppData\Local\CapCut\User Data\Crash\\" --annotation=crop_type=6 --annotation=enable_crash_event=true --annotation=execute-if-childprocess-crash=true --annotation=is_debug=false --annotation=main_pid=4968 "--annotation=os_version=Windows NT 10.0.19045" --annotation=parfait_version=1.5.9.0 "--annotation=posthandler-copy-dir=C:\Users\admin\AppData\Local\CapCut\User Data\Crash/crash_post_reports" --annotation=posthandler-process-path=C:/Users/admin/AppData/Local/CapCut/Apps/5.5.0.2028/VECrashHandler.exe --annotation=posthandler-wait-result=true --annotation=posthandler-wait-timeout=120 --initial-client-data=0xee0,0xed8,0x1068,0xfd8,0xfb8,0x7ff81a41eff0,0x7ff81a41f008,0x7ff81a41f020 | C:\Users\admin\AppData\Local\CapCut\Apps\5.5.0.2028\parfait_crash_handler.exe | — | CapCut.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.5.9.0 | |||||||||||||||
| 4968 | "C:\Users\admin\AppData\Local\CapCut\Apps\5.5.0.2028\CapCut.exe" | C:\Users\admin\AppData\Local\CapCut\Apps\5.5.0.2028\CapCut.exe | CapCut.exe | ||||||||||||
User: admin Company: ByteDance Integrity Level: HIGH Exit code: 0 Version: 5.5.0.2028 Modules
| |||||||||||||||
| 5000 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5252 | "C:\Users\admin\AppData\Local\app_shell_cache_562354\app_package_6a3e547b88.exe" /s /create_desktop=1 /install_path="C:\Users\admin\AppData\Local\CapCut\Apps" | C:\Users\admin\AppData\Local\app_shell_cache_562354\app_package_6a3e547b88.exe | CapCut_7418125124962107397_installer.exe | ||||||||||||
User: admin Company: Bytedance Pte. Ltd. Integrity Level: HIGH Description: CapCut Exit code: 0 Version: 5.5.0.2028 Modules
| |||||||||||||||
Total events
13 659
Read events
13 609
Write events
47
Delete events
3
Modification events
| (PID) Process: | (6848) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6848) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6848) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5000) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5000) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5000) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1760) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1760) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1760) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6380) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
737
Suspicious files
3 531
Text files
2 665
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6224 | CapCut_7418125124962107397_installer.exe | C:\Users\admin\AppData\Local\app_shell_cache_562354\app_package_6a3e547b88.exe | — | |
MD5:— | SHA256:— | |||
| 5252 | app_package_6a3e547b88.exe | C:\Users\admin\AppData\Local\CapCut\Apps\202526214558176_1\JYPacket\5.5.0.2028\Qt\labs\lottieqt\qmldir | text | |
MD5:B34B3E3D0388BEAF6B85BE20E03B24A2 | SHA256:6DFC8F328EF1EDB7EE62E24326EF53849A33FD7A102B9260244366ACEBBB4BAD | |||
| 6224 | CapCut_7418125124962107397_installer.exe | C:\Users\admin\AppData\Local\Temp\nsv72E2.tmp\res.zip | compressed | |
MD5:23E2490706D024BD70CCB906EBF0B62D | SHA256:FBB054F0880B81DE92BE6A9500C6757F4E1A3E8E335E31821D76B49DE8375C8C | |||
| 6224 | CapCut_7418125124962107397_installer.exe | C:\Users\admin\AppData\Local\Temp\speech_synthesis_en.png | image | |
MD5:7E0FCA9AFBA9A7FBC15D378B8E550BAA | SHA256:49D5FA943BCEC39D1244E6C69801F20B5F9D01FC89D6F260236A3C1255B5FC98 | |||
| 5252 | app_package_6a3e547b88.exe | C:\Users\admin\AppData\Local\Temp\E9DDA433-AA83-40F3-BEA5-93BAD32DD698\7zip.dll | executable | |
MD5:2D97C2E0353CB0C63212ECACD326BB17 | SHA256:FE604C8747171A85F883B08FCAF32A64D59FF7C7ED89E862AD252D366AB66368 | |||
| 6224 | CapCut_7418125124962107397_installer.exe | C:\Users\admin\AppData\Local\Temp\intelligent_subtitles_en.png | image | |
MD5:C51D1976F87828C0DCA46EF4D0243614 | SHA256:463A0C124A0925FBB341855685B2B58525B100108D271679F2F95398D5F6C618 | |||
| 5252 | app_package_6a3e547b88.exe | C:\Users\admin\AppData\Local\CapCut\Apps\202526214558176_1\JYPacket\5.5.0.2028\QtQuick\Scene2D\qmldir | text | |
MD5:5638D561733AD99570A6DA240342B5D1 | SHA256:60F82CCB5031F5BDAF6D269989F3A4A135C5E217A28E31246A69300CE9D99865 | |||
| 5252 | app_package_6a3e547b88.exe | C:\Users\admin\AppData\Local\CapCut\Apps\202526214558176_1\JYPacket\5.5.0.2028\Resources\aigc_text_template\depends | text | |
MD5:CA5A01FDBE070DEED2541250838735A3 | SHA256:BADE222C94A89D0B0FF2E98A83F18C6FFA969ED538DF85A7F452D6652E83F3E4 | |||
| 5252 | app_package_6a3e547b88.exe | C:\Users\admin\AppData\Local\CapCut\Apps\202526214558176_1\JYPacket\5.5.0.2028\Qt\labs\qmlmodels\qmldir | text | |
MD5:F8CAABE387B9335513086CD8D51D7FC9 | SHA256:270E3A26813B510675D9873531F85608482C4641802DA6F7F577624B1A7D7EC3 | |||
| 6224 | CapCut_7418125124962107397_installer.exe | C:\Users\admin\AppData\Local\Temp\nsv72E2.tmp\shell_downloader.dll | executable | |
MD5:C052C0A2ED833D924B7799625413AC1C | SHA256:098972CF9DDC9D574130E025A252A99B278DE9CC0AE700ACFB8C935C24EB1172 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
88
DNS requests
43
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.14:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4536 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4536 | svchost.exe | GET | 200 | 2.16.241.14:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6192 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6192 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6016 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6872 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.14:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4536 | svchost.exe | 2.16.241.14:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.21.65.153:443 | www.bing.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4536 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6224 | CapCut_7418125124962107397_installer.exe | 2.19.96.248:443 | editor-api-sg.capcut.com | Akamai International B.V. | DE | unknown |
6224 | CapCut_7418125124962107397_installer.exe | 2.16.238.20:443 | maliva-mcs.byteoversea.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
editor-api-sg.capcut.com |
| unknown |
maliva-mcs.byteoversea.com |
| whitelisted |
sf16-va.tiktokcdn.com |
| whitelisted |
sgali-mcs.byteoversea.com |
| whitelisted |
lf16-capcut.faceulv.com |
| unknown |
Threats
Process | Message |
|---|---|
CapCut_7418125124962107397_installer.exe | checkBoxCreateShortcut status:1
|