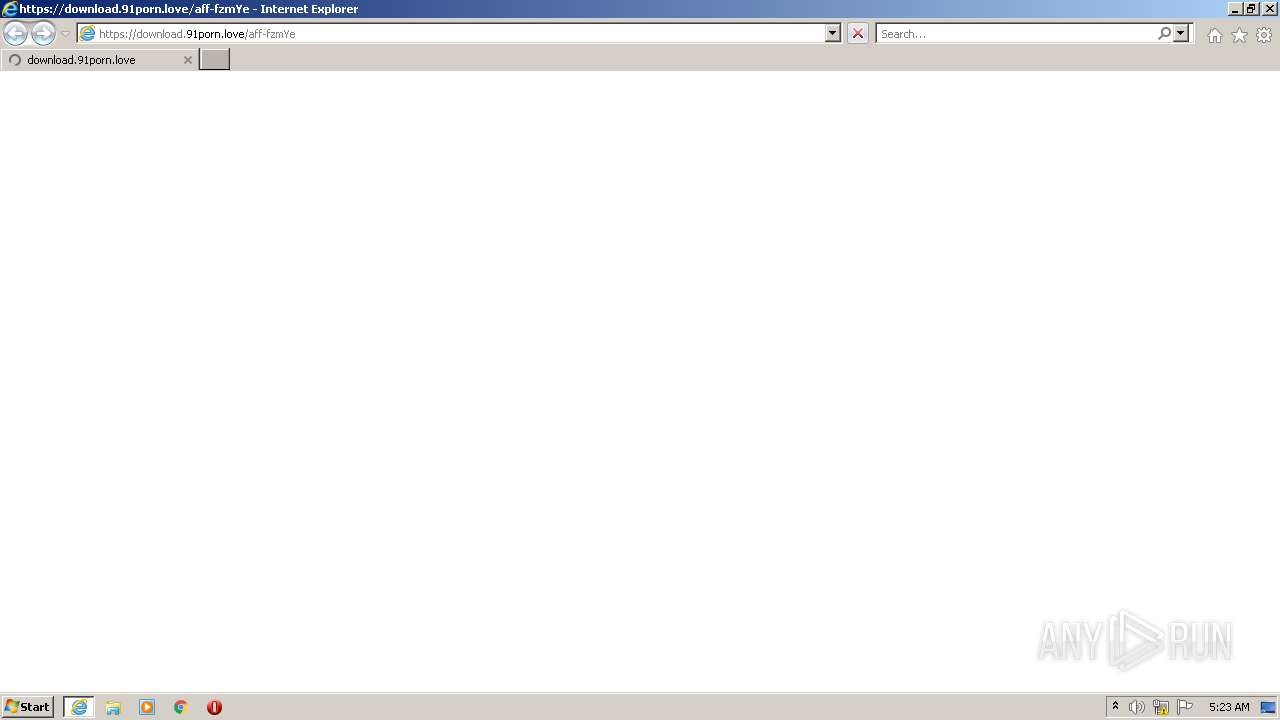
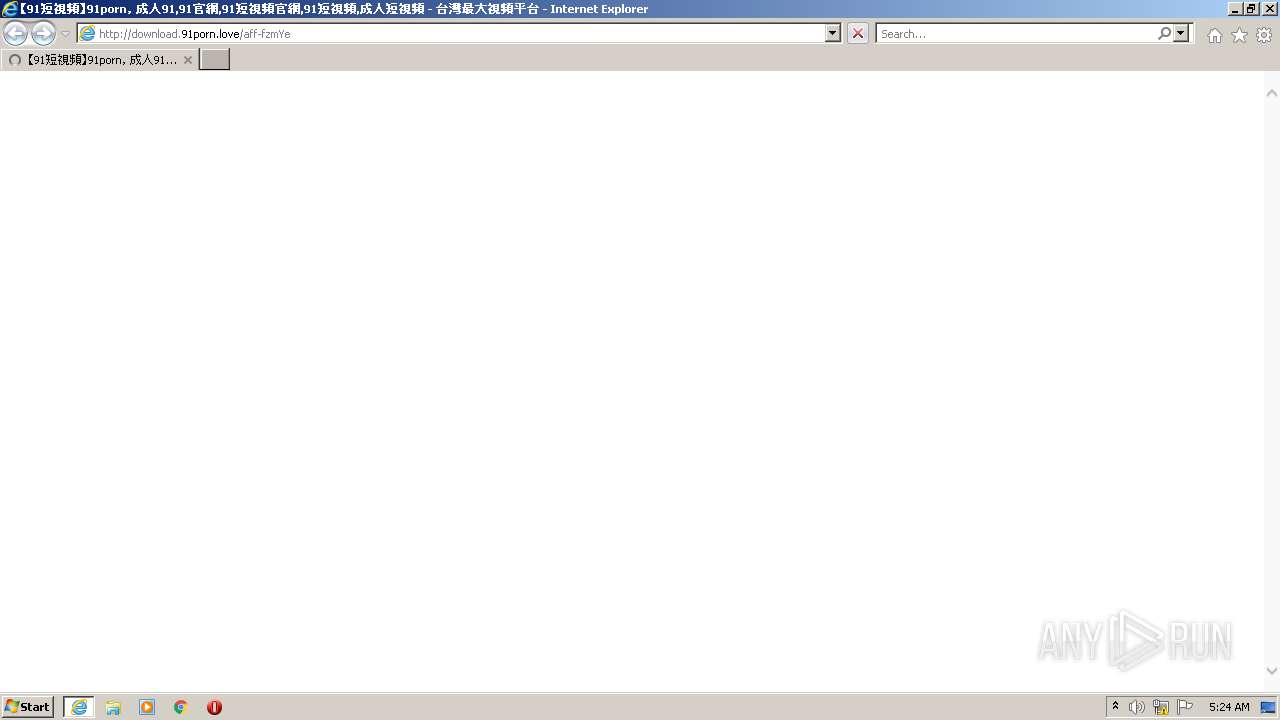
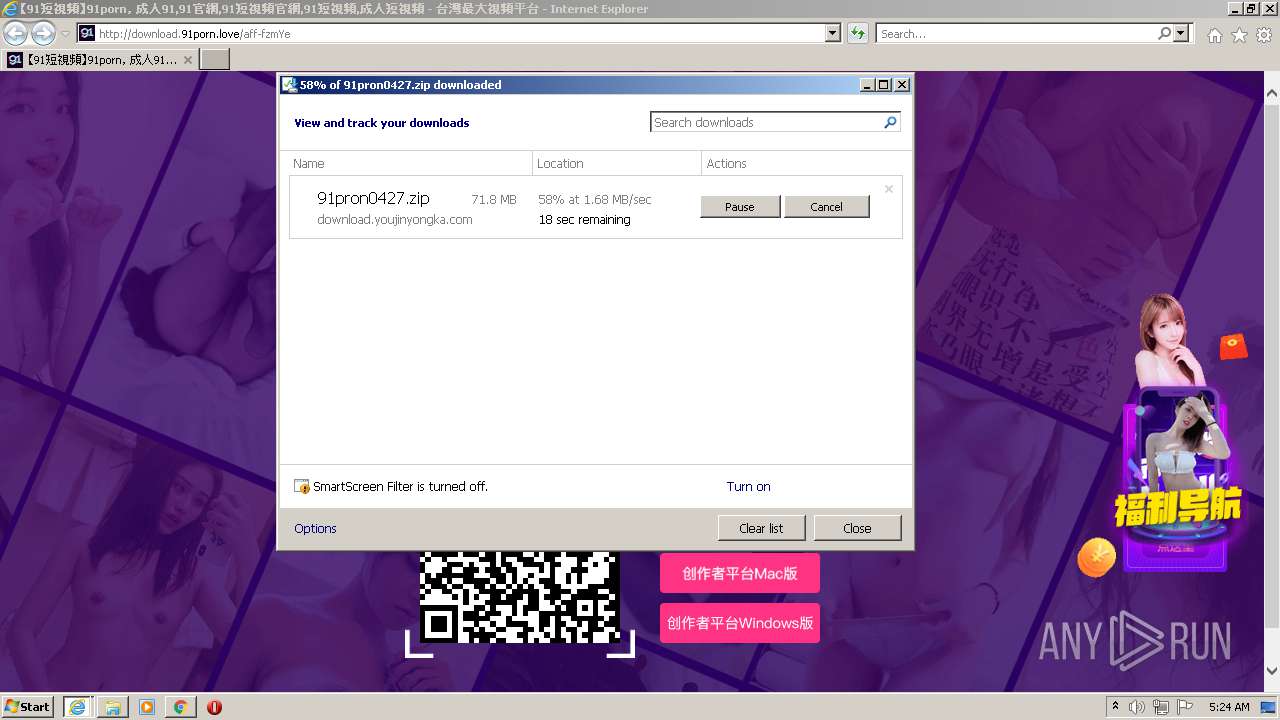
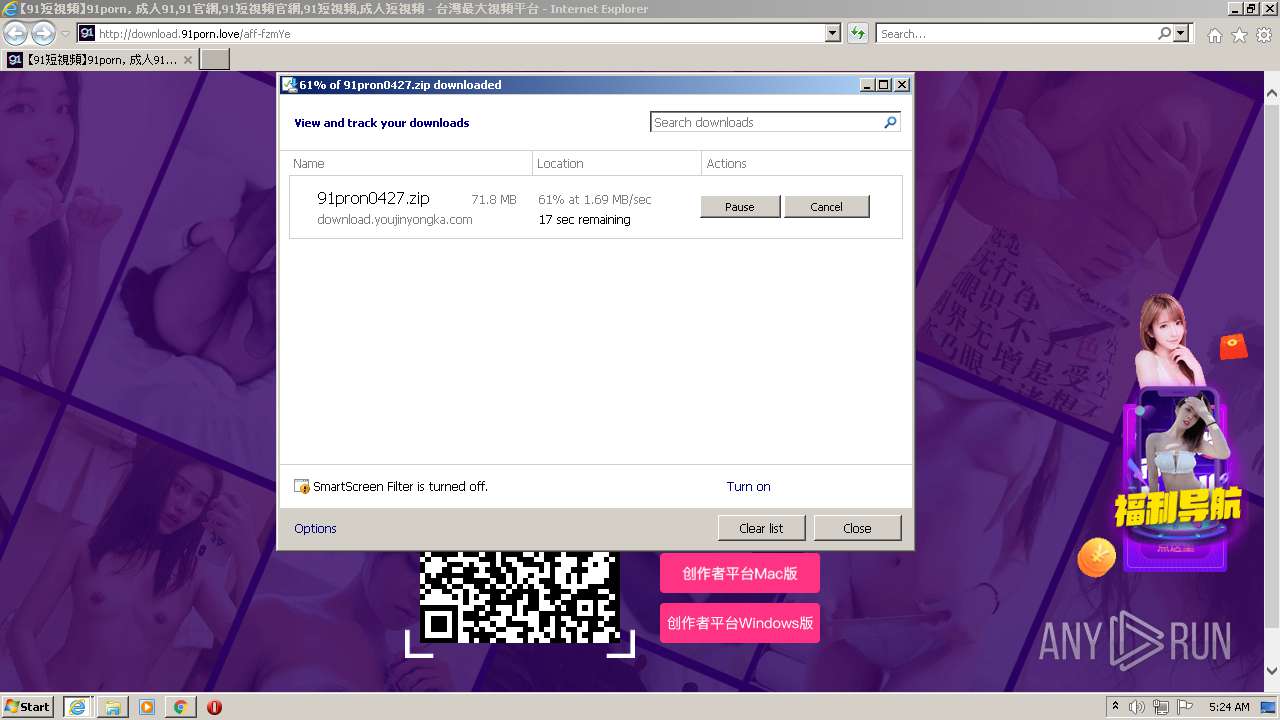
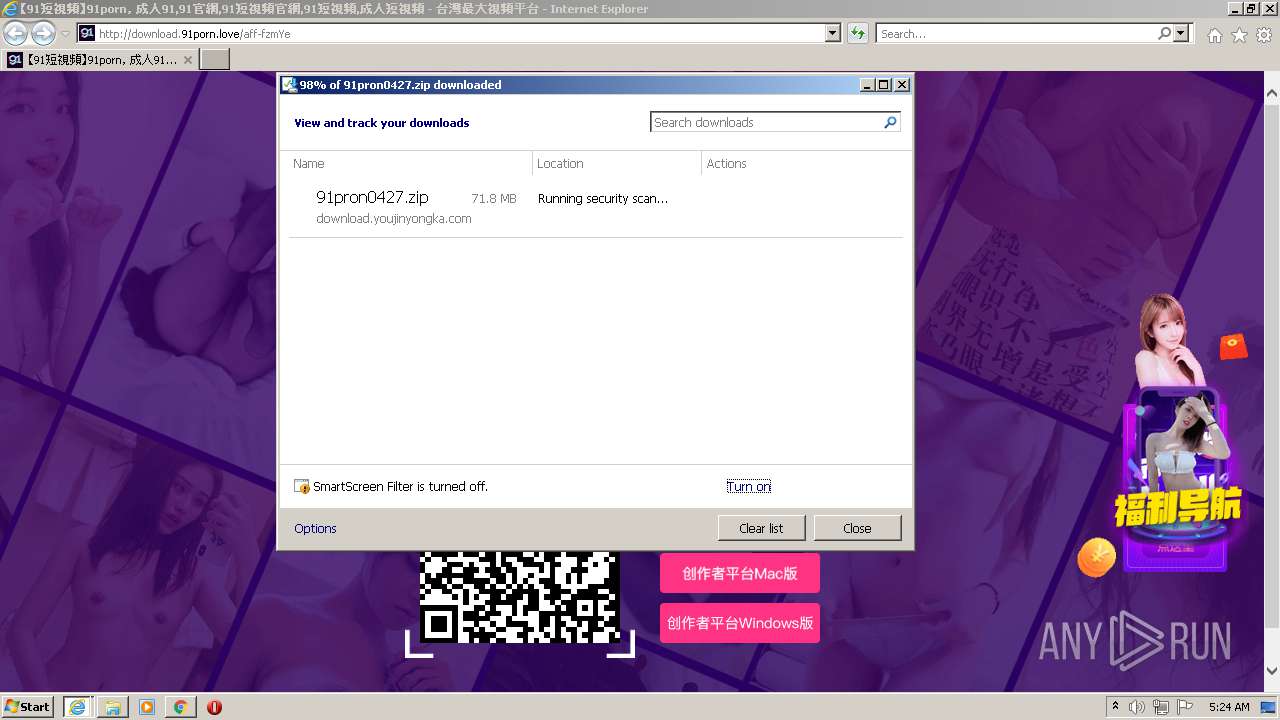
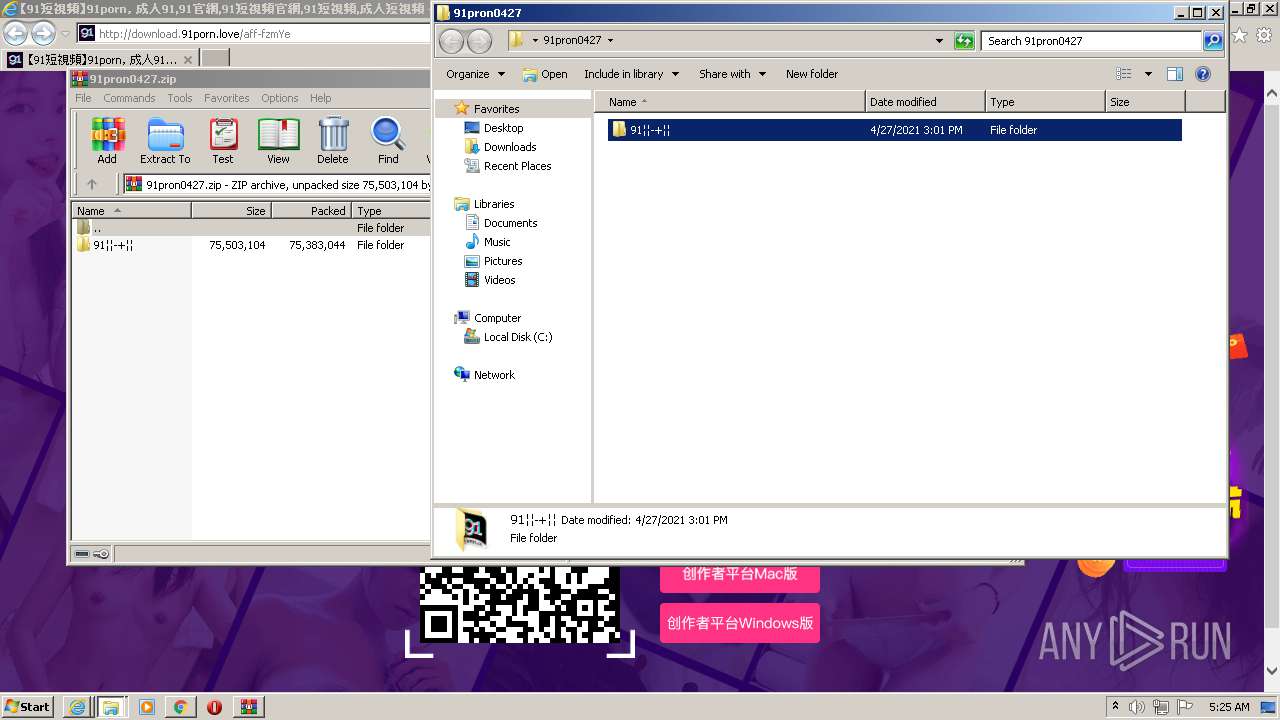
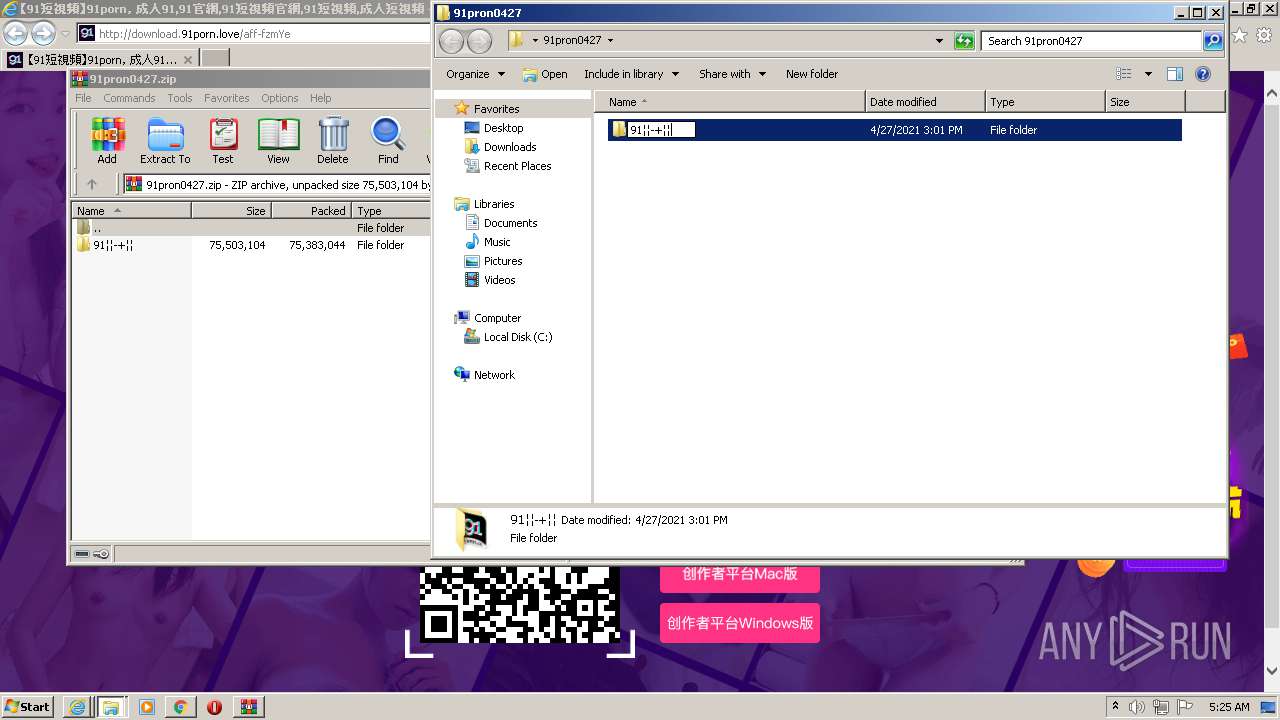
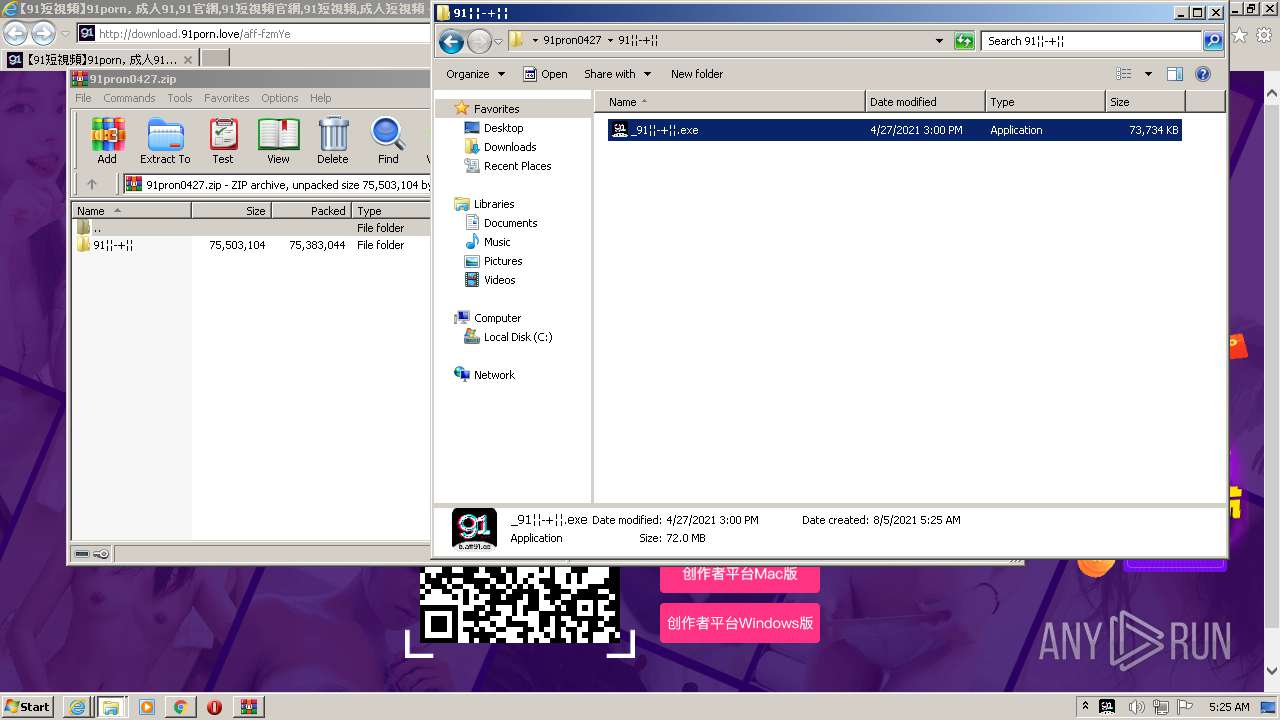
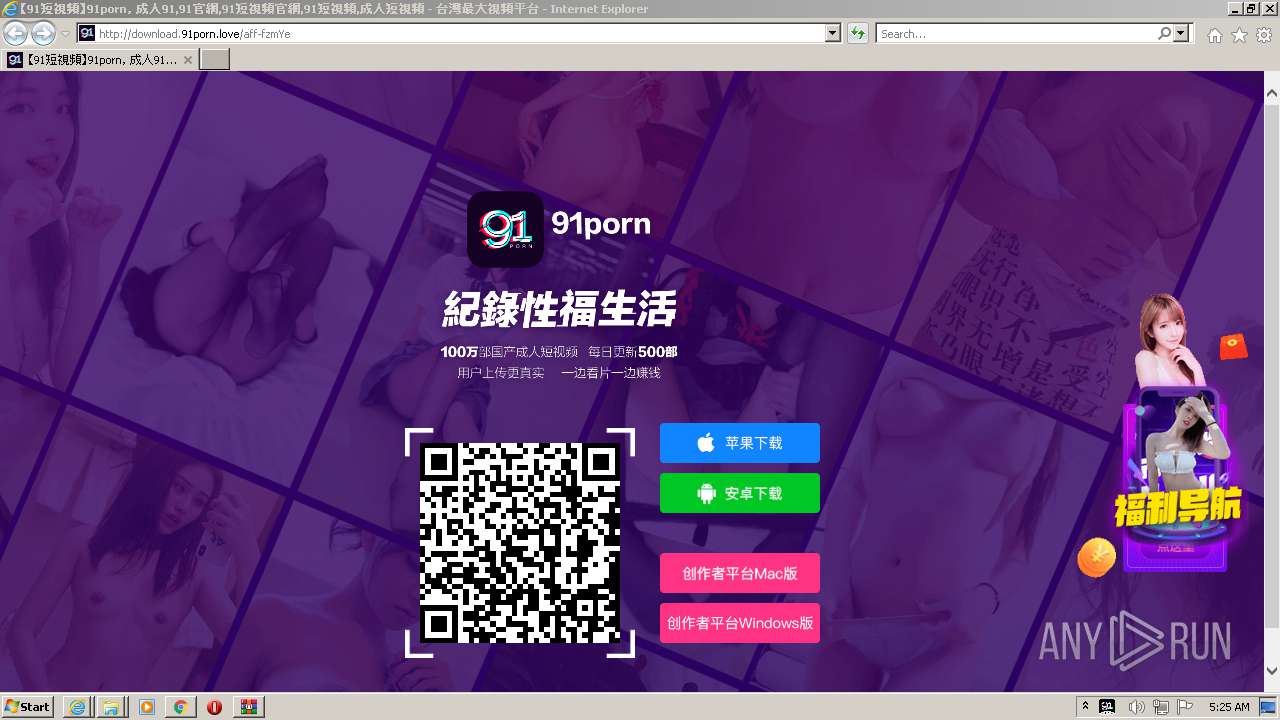
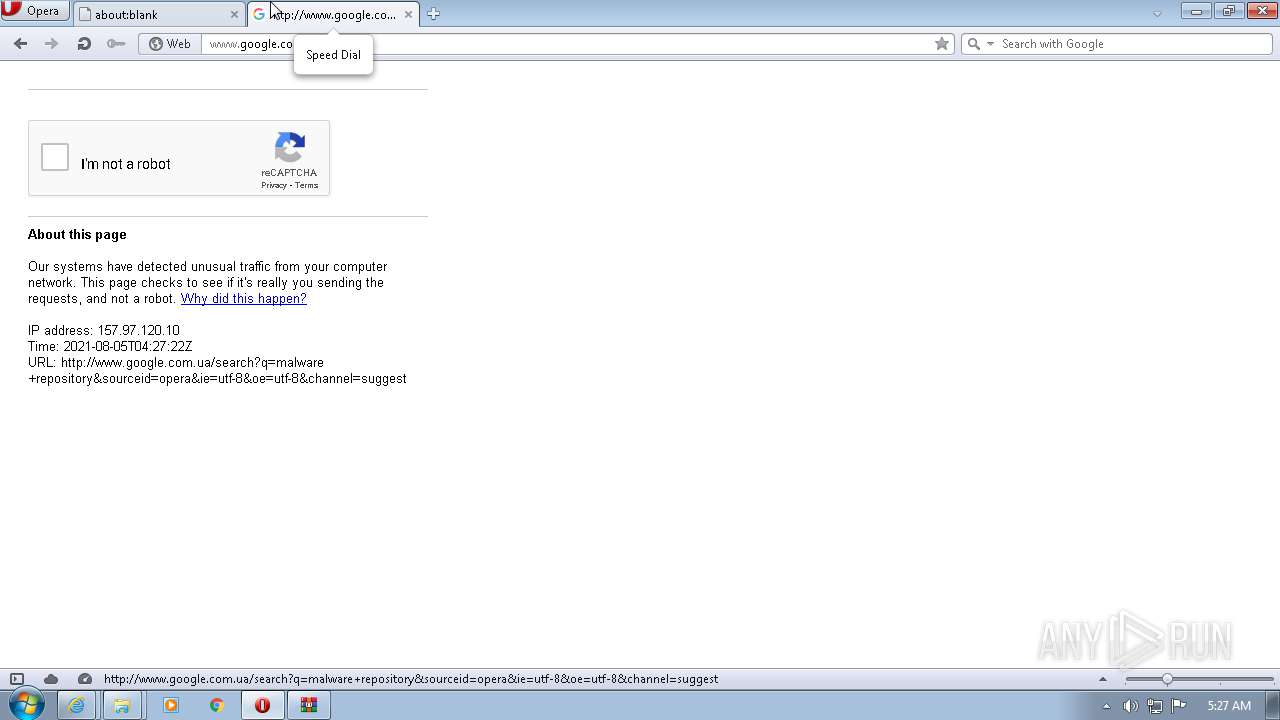
| URL: | https://download.91porn.love/aff-fzmYe |
| Full analysis: | https://app.any.run/tasks/9342bd40-b808-4f4c-80a7-0d96b42766d6 |
| Verdict: | Malicious activity |
| Analysis date: | August 05, 2021, 04:23:41 |
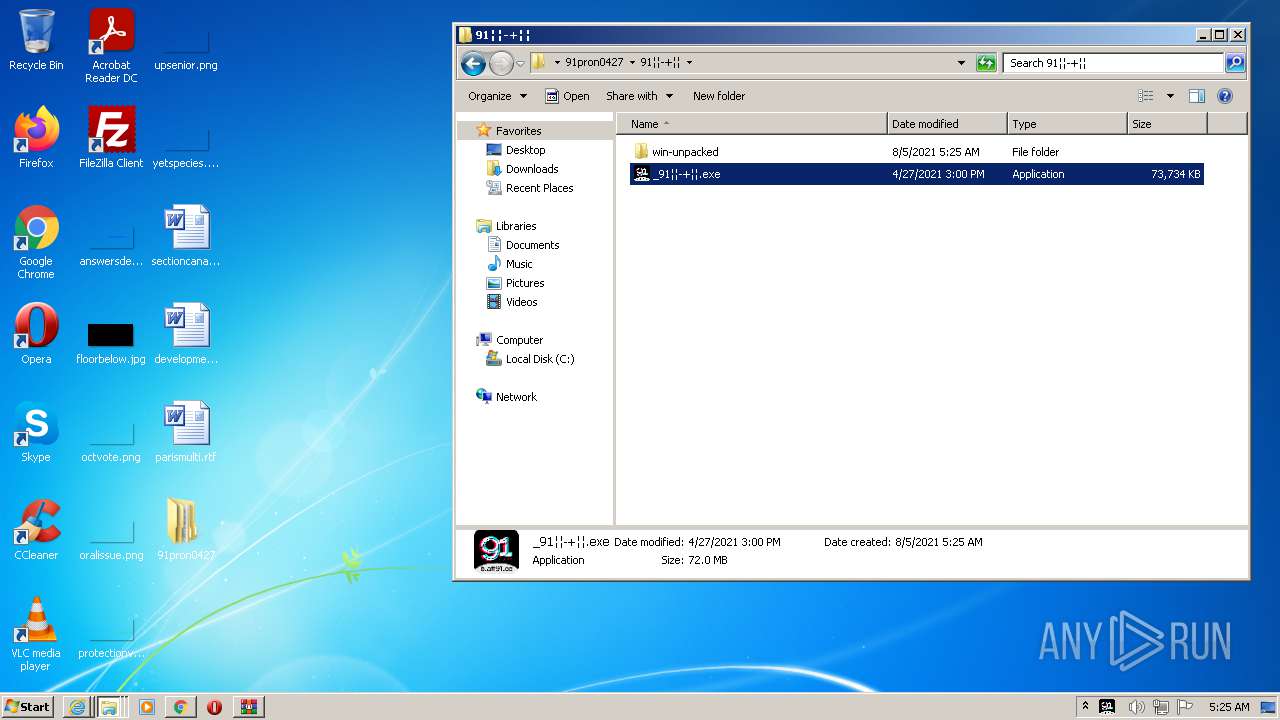
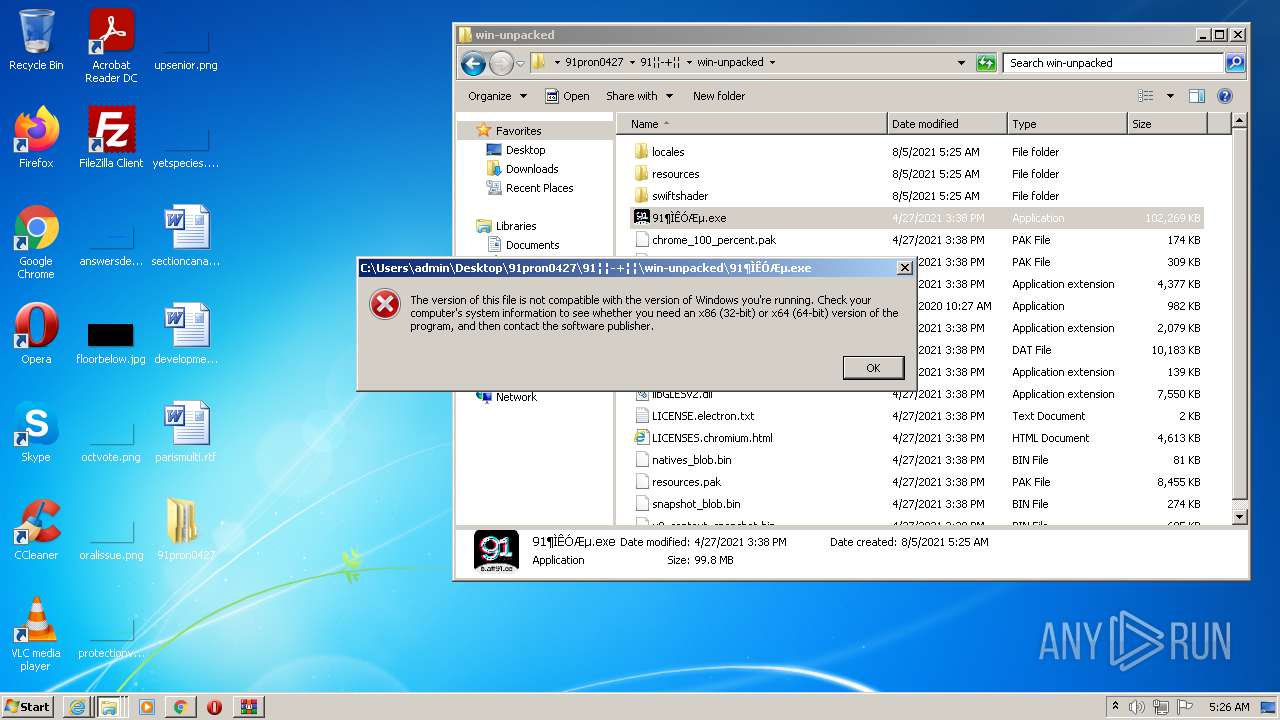
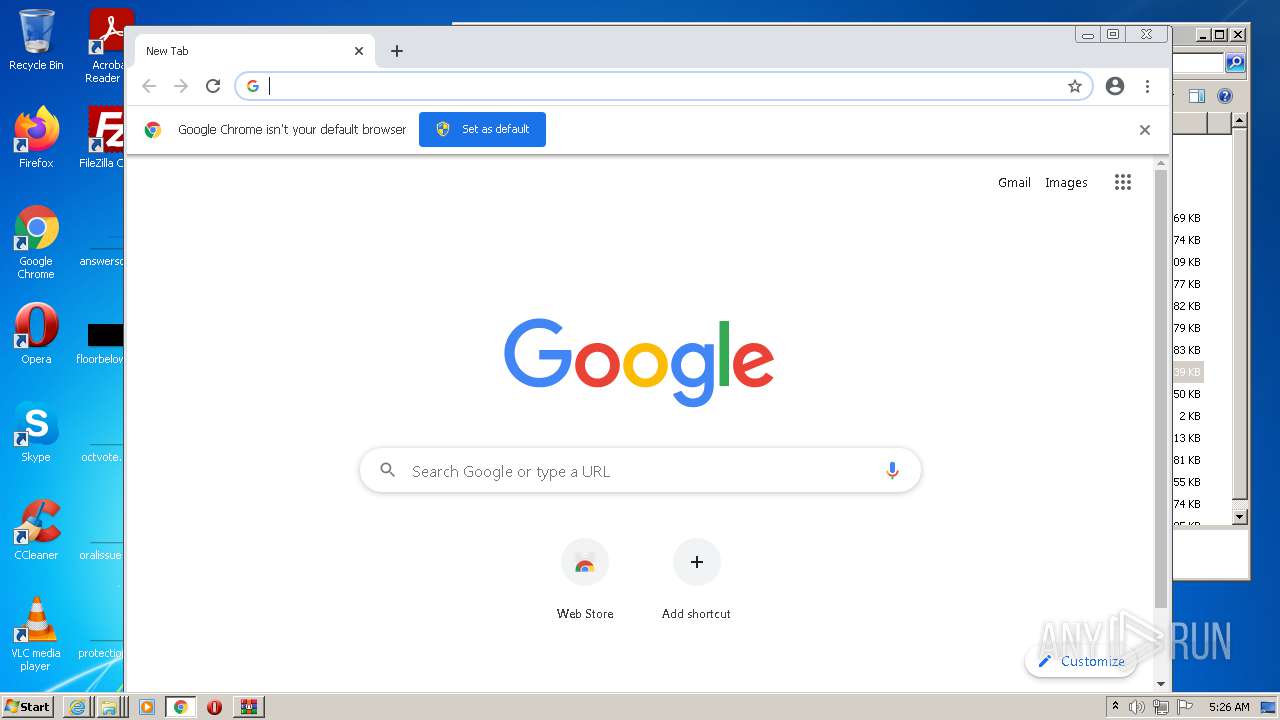
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 729A6AA12086299860FDE885D8C14DB9 |
| SHA1: | AB7FC812564AF189ECAF9925A102E29094E70E55 |
| SHA256: | 4A9CFCF22E7791A3F9ABBECF31DC8C886389CCBF2A5DDF2194C2EBFC51F10C48 |
| SSDEEP: | 3:N8SEliSEn:2SKiSc |
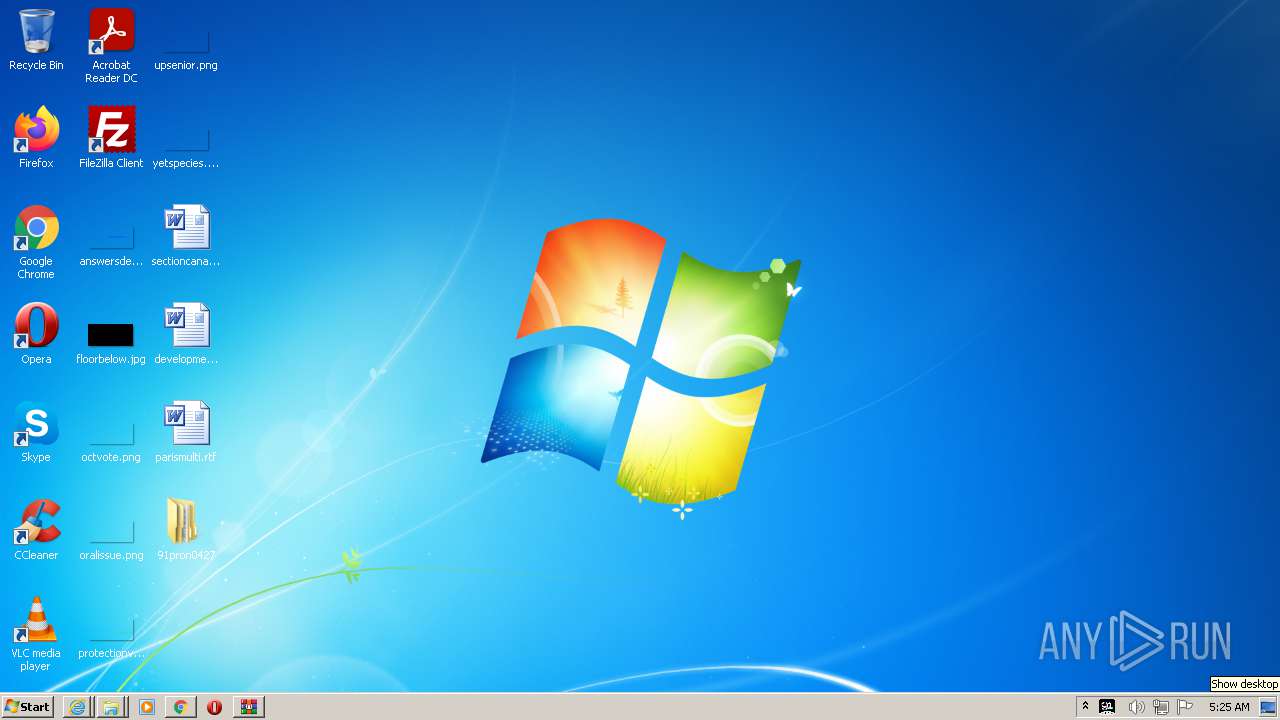
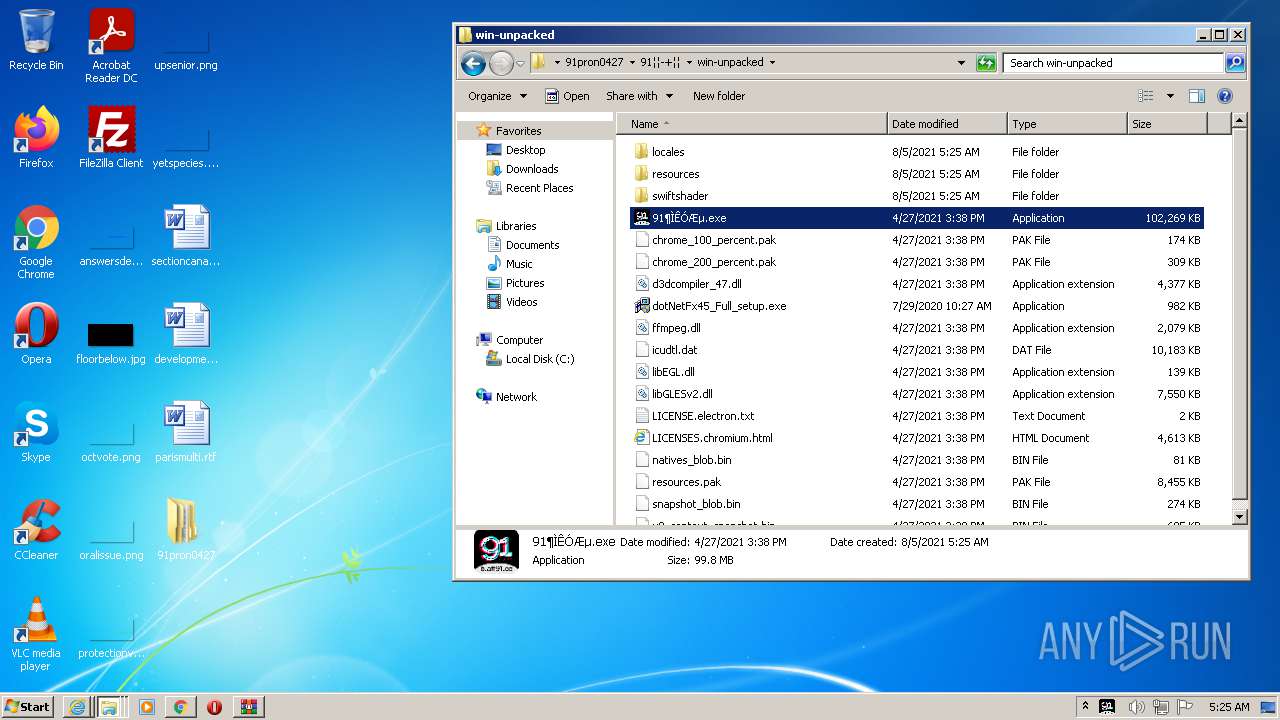
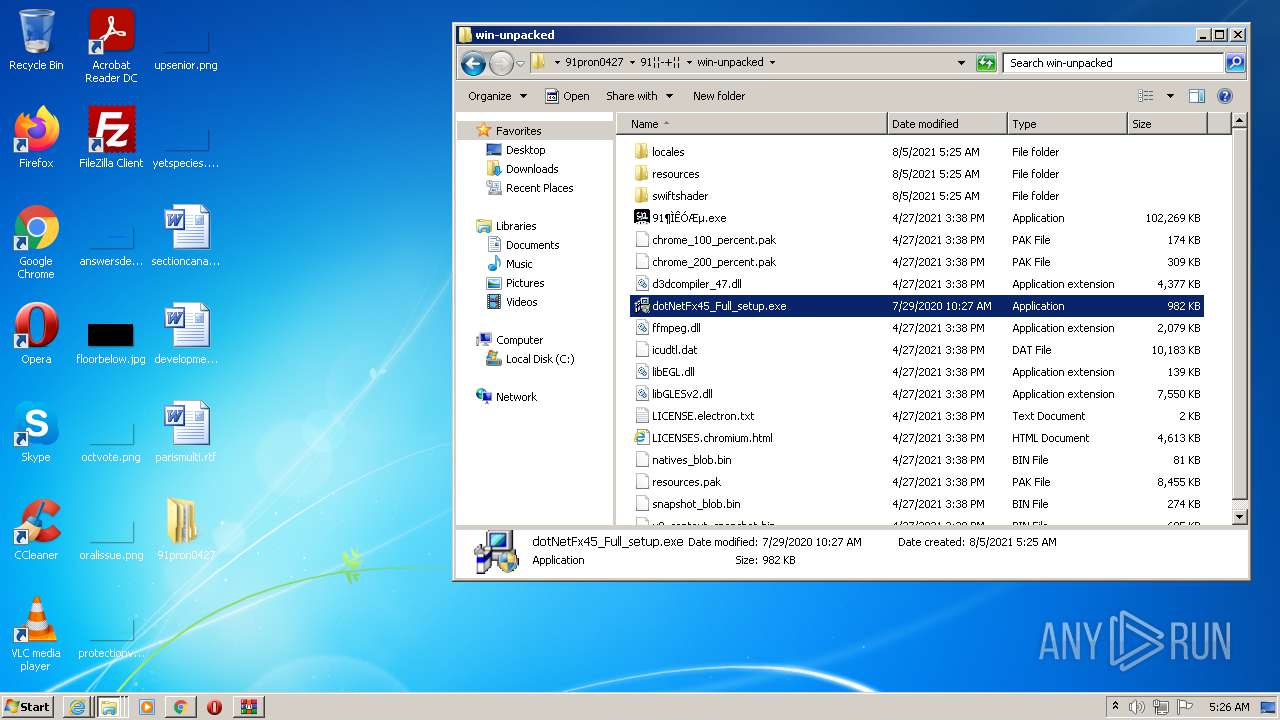
MALICIOUS
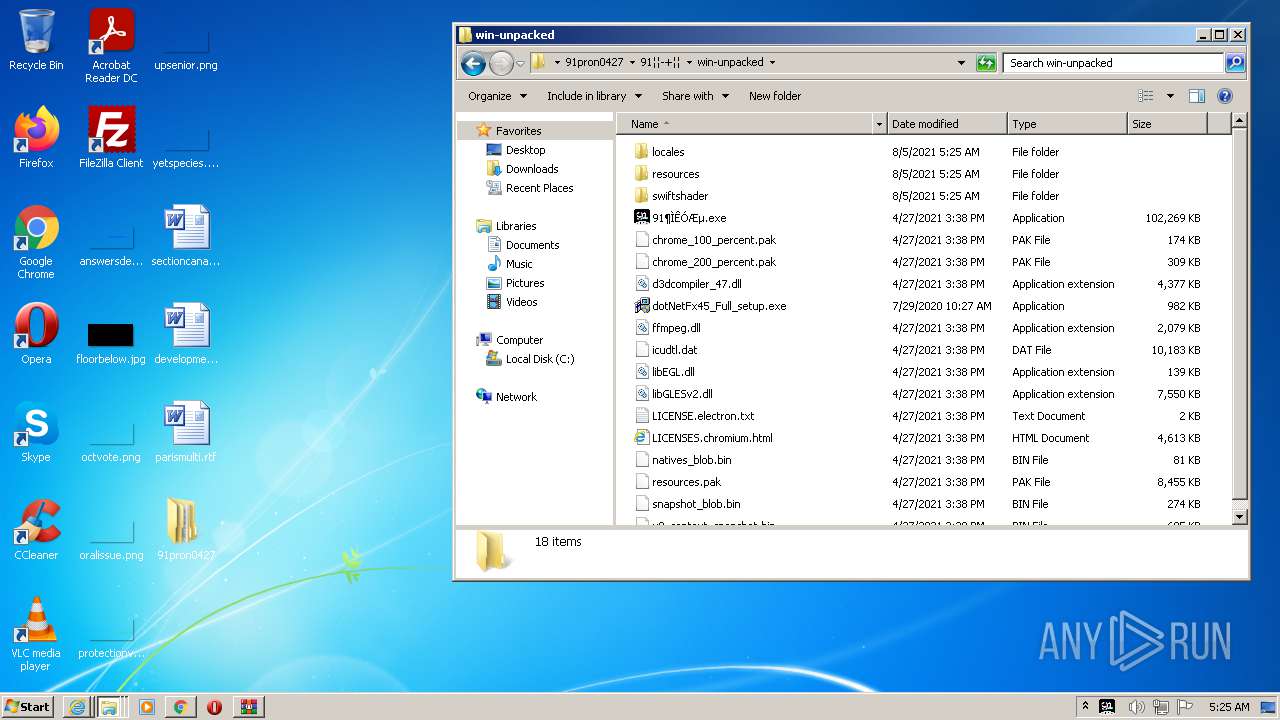
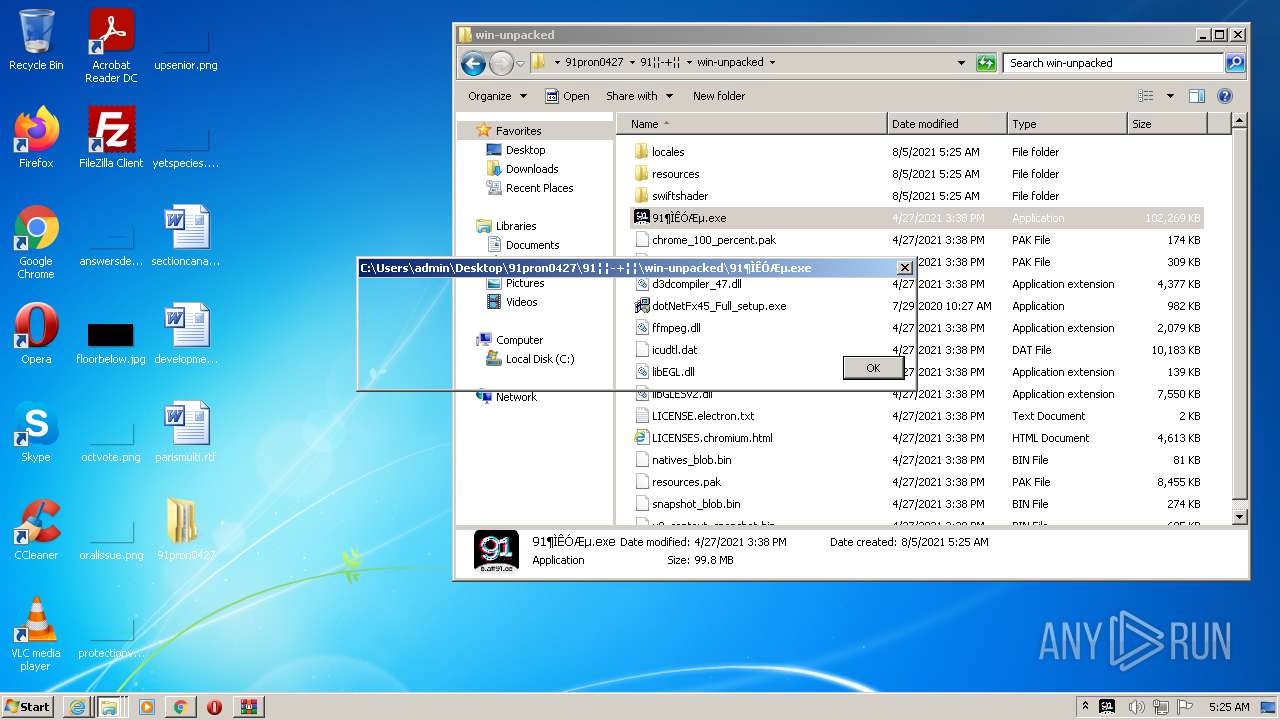
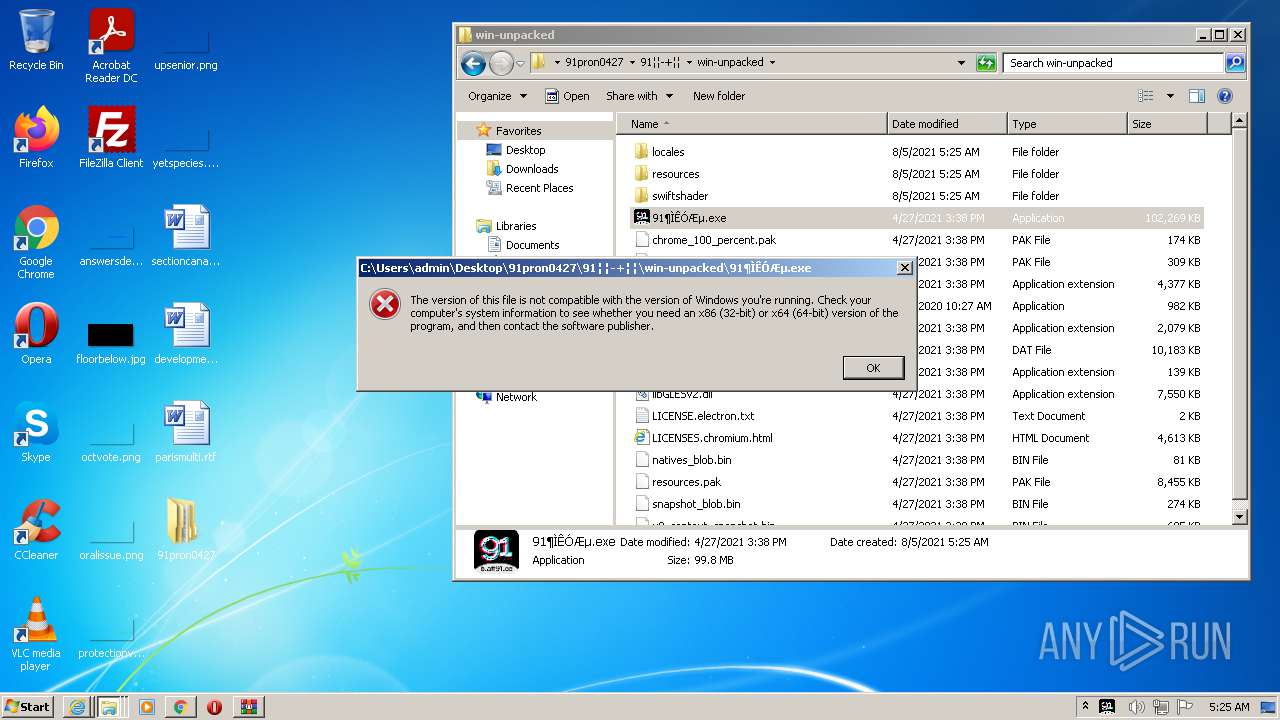
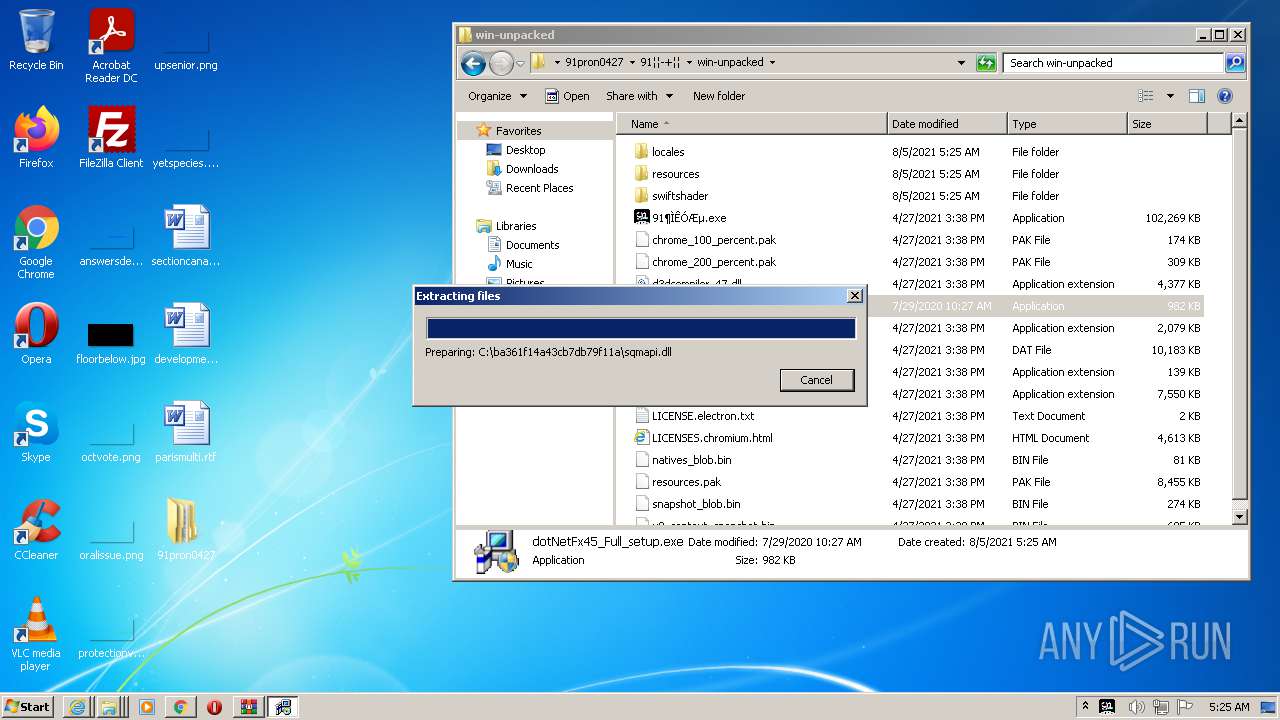
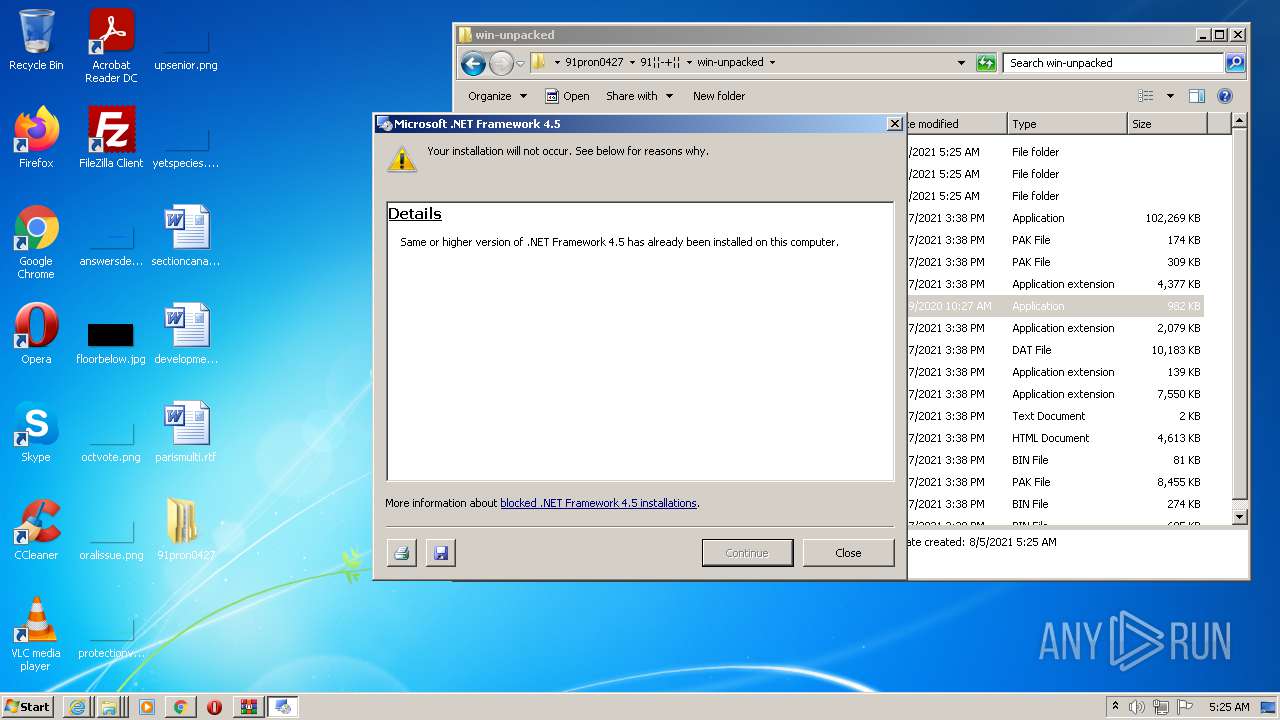
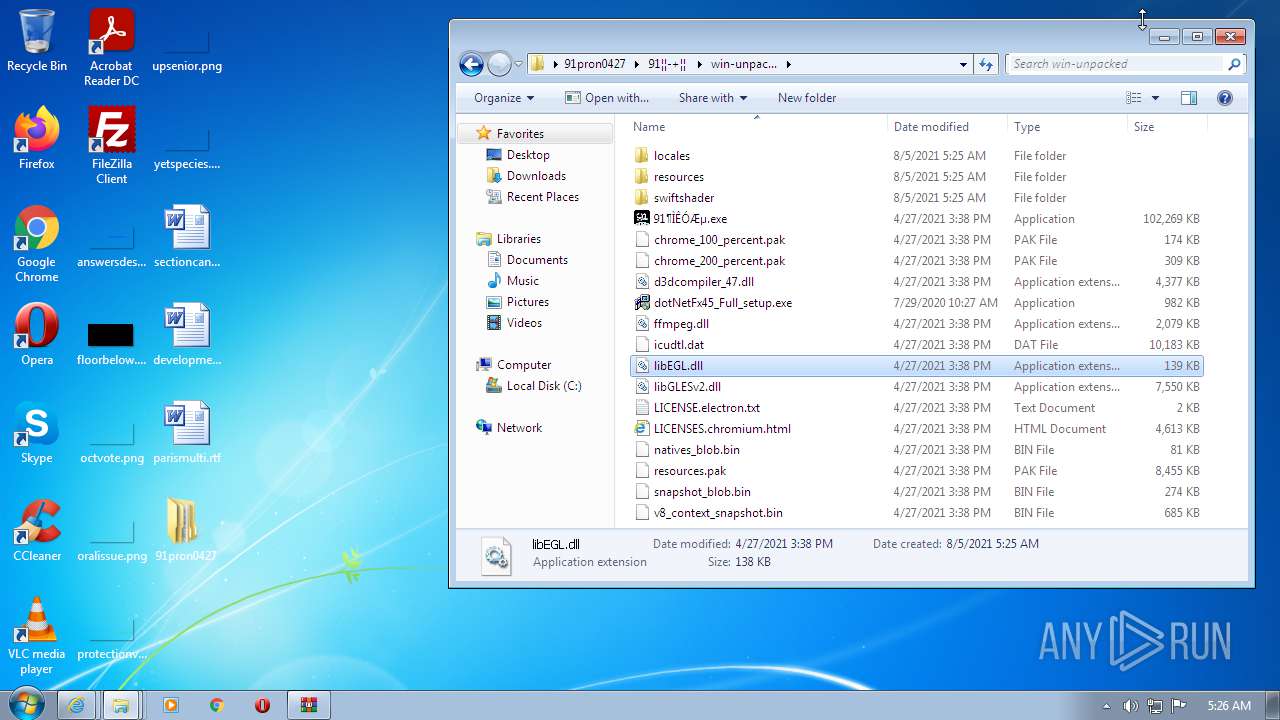
Application was dropped or rewritten from another process
- dotNetFx45_Full_setup.exe (PID: 2500)
- dotNetFx45_Full_setup.exe (PID: 2276)
- Setup.exe (PID: 3808)
Actions looks like stealing of personal data
- dotNetFx45_Full_setup.exe (PID: 2276)
Loads dropped or rewritten executable
- Setup.exe (PID: 3808)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3092)
- iexplore.exe (PID: 3228)
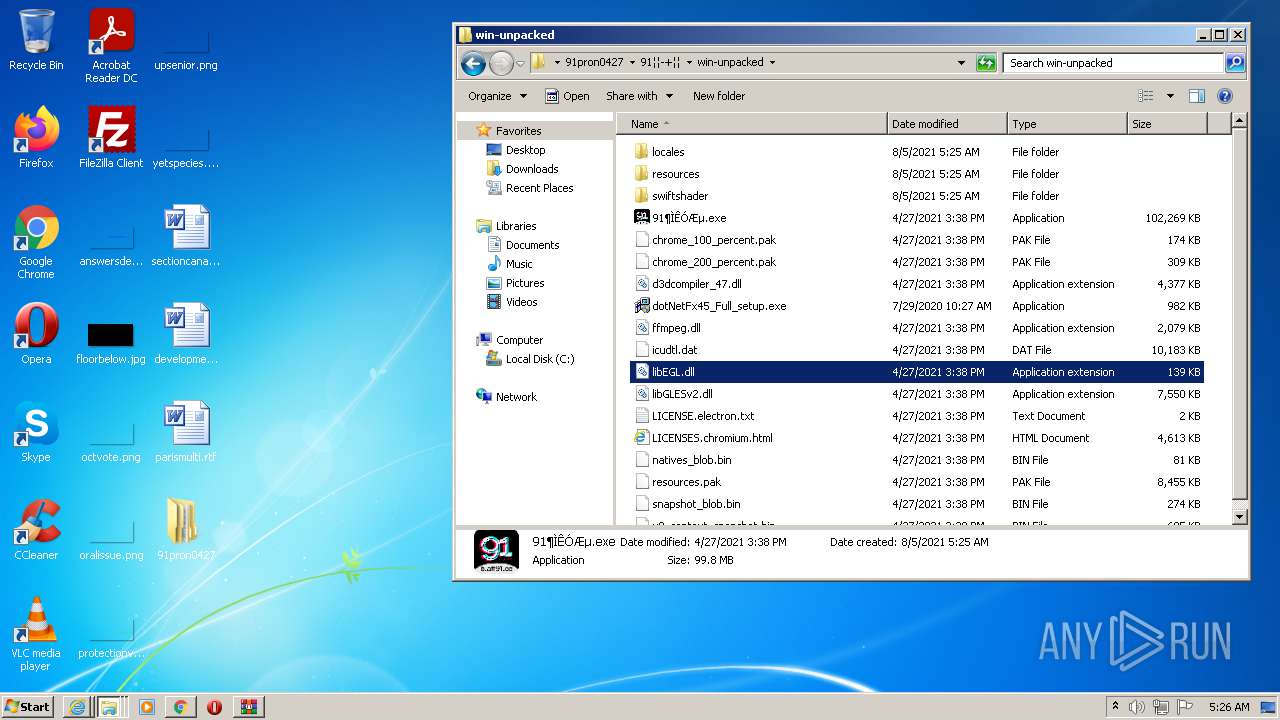
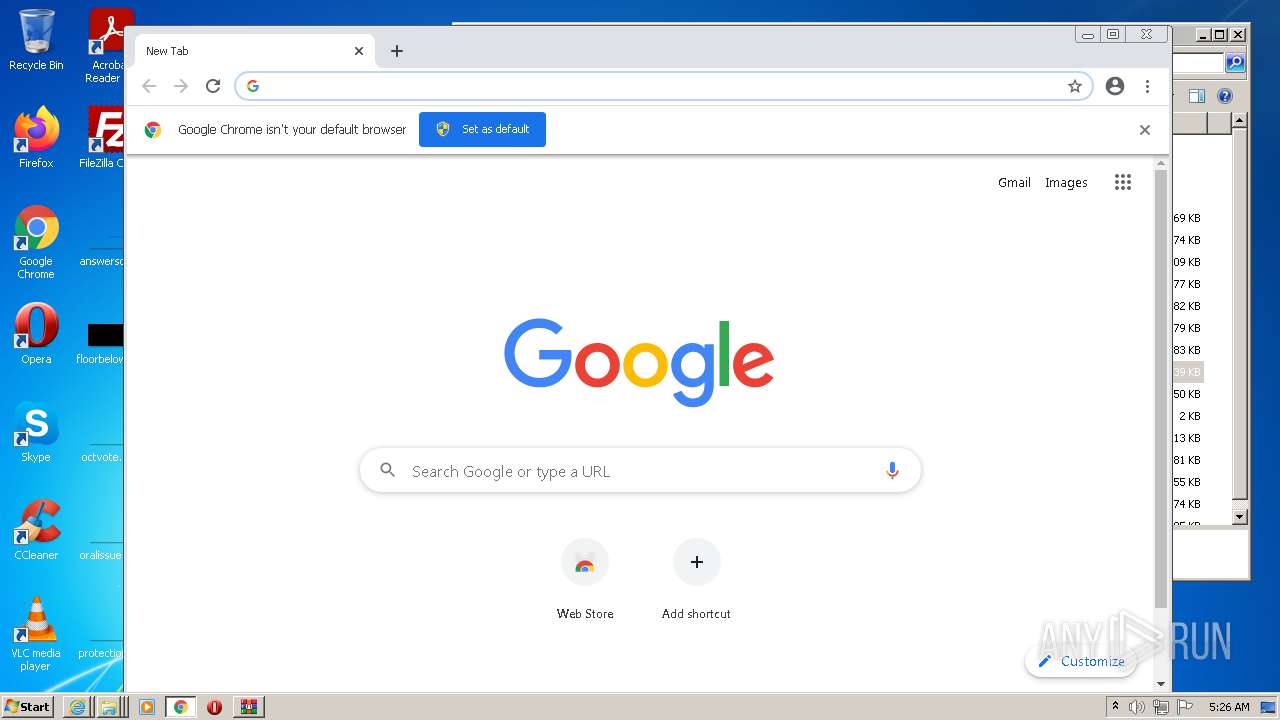
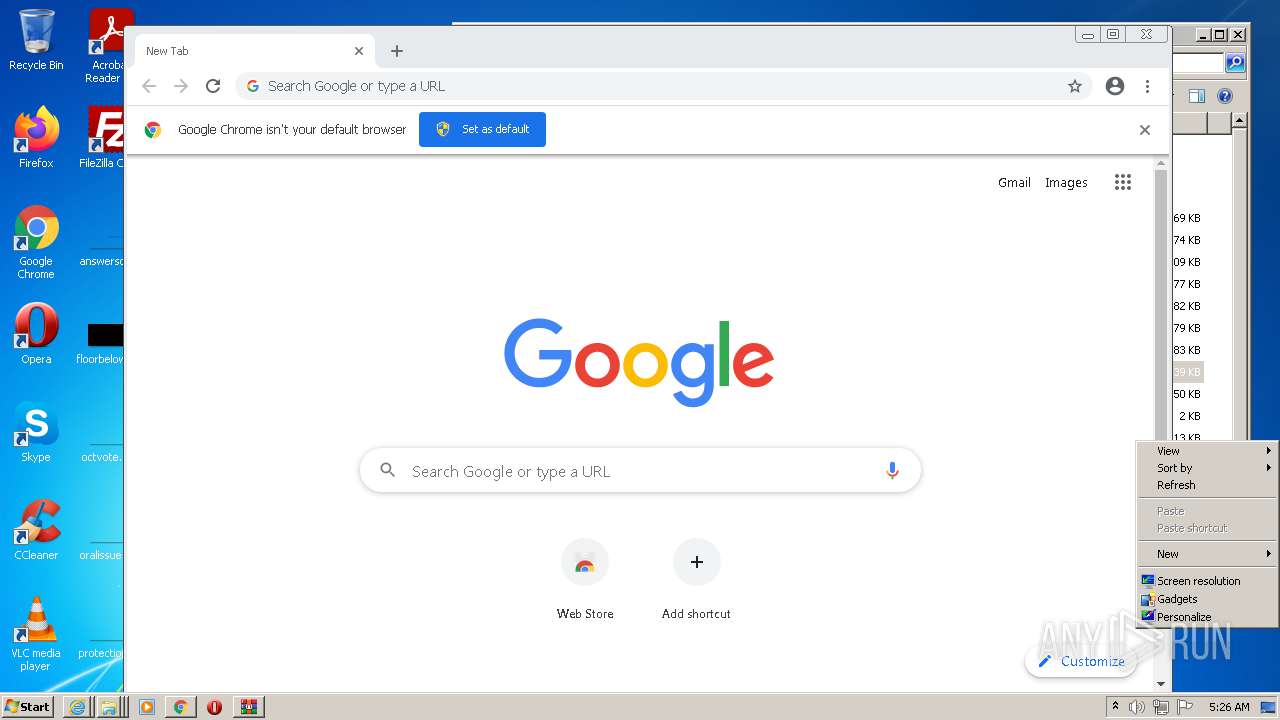
Modifies files in Chrome extension folder
- chrome.exe (PID: 2652)
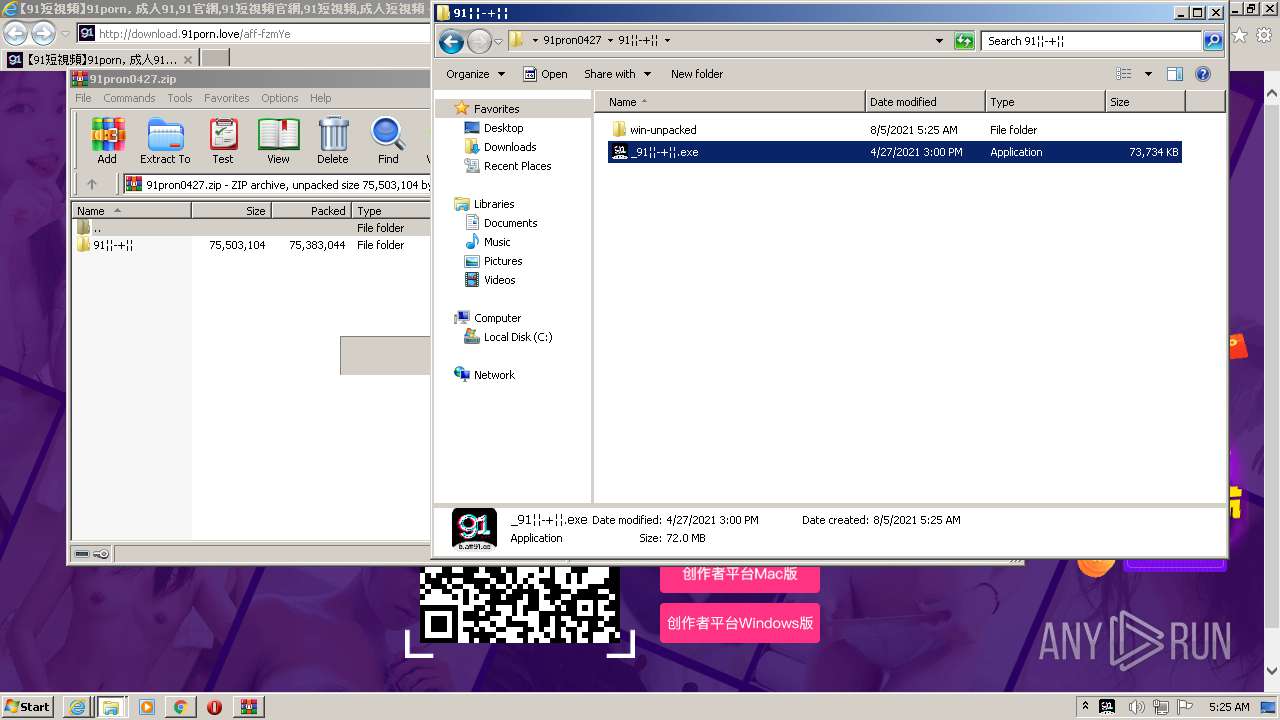
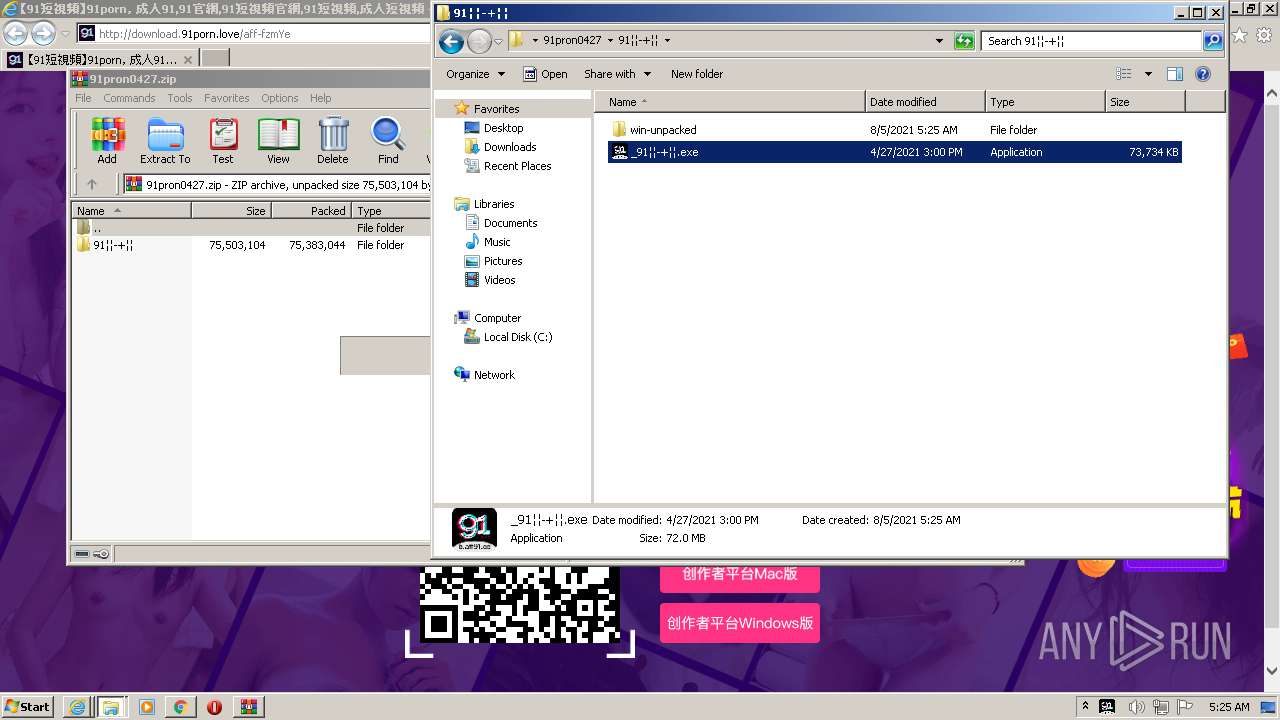
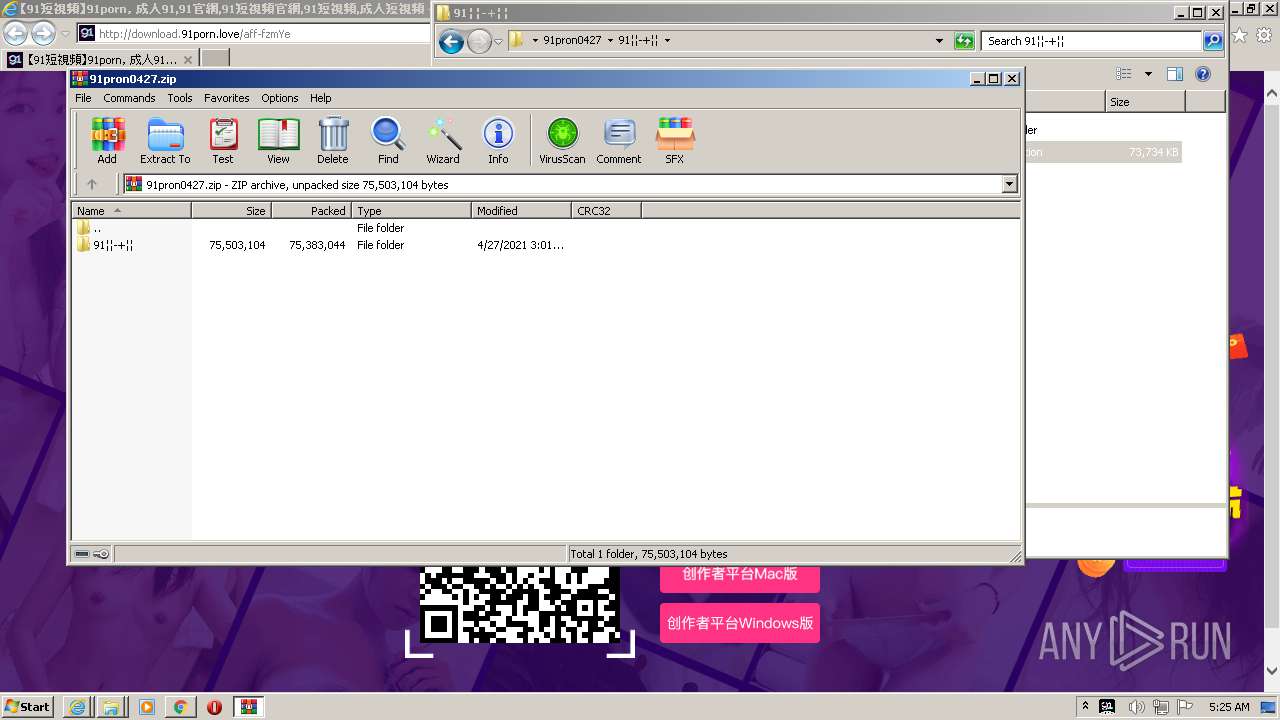
Checks supported languages
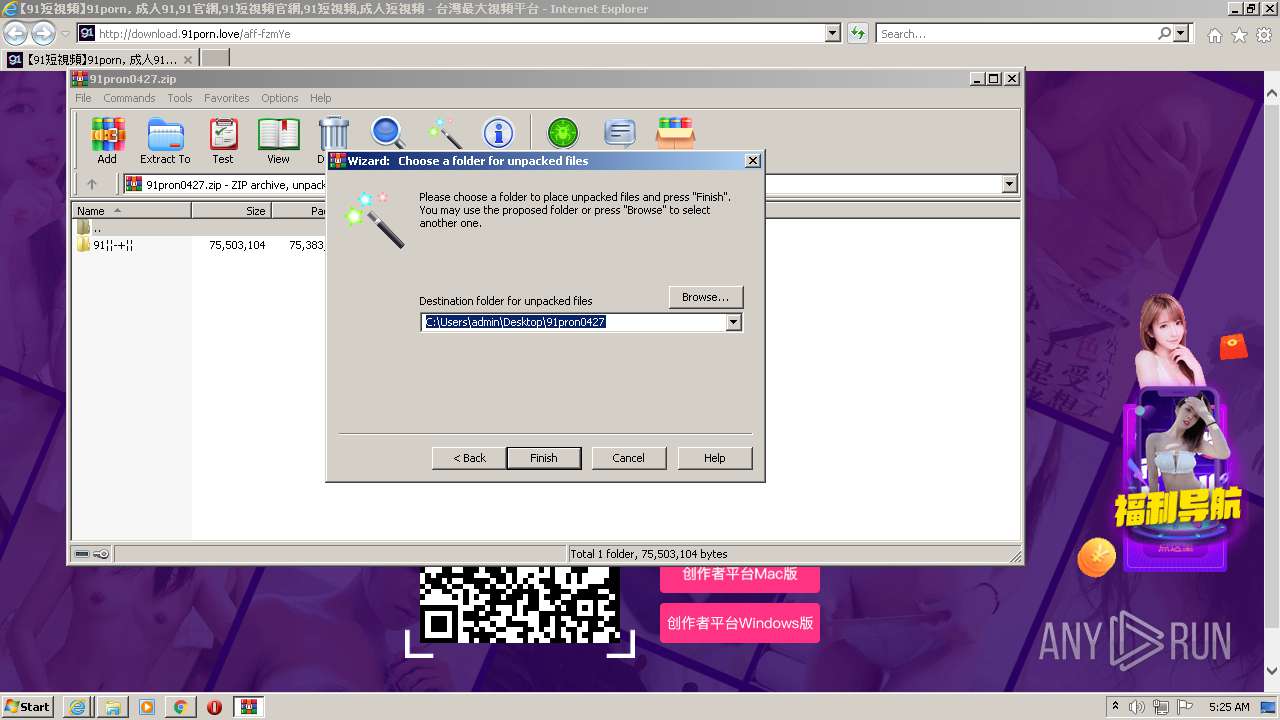
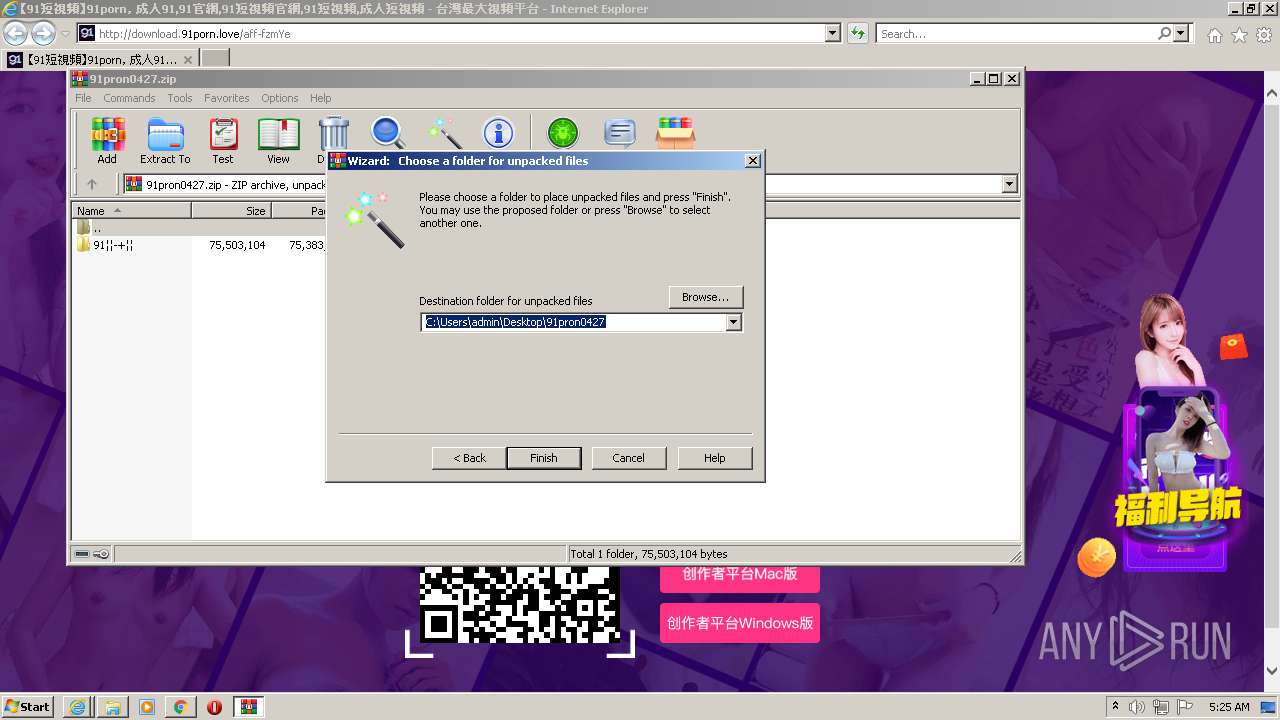
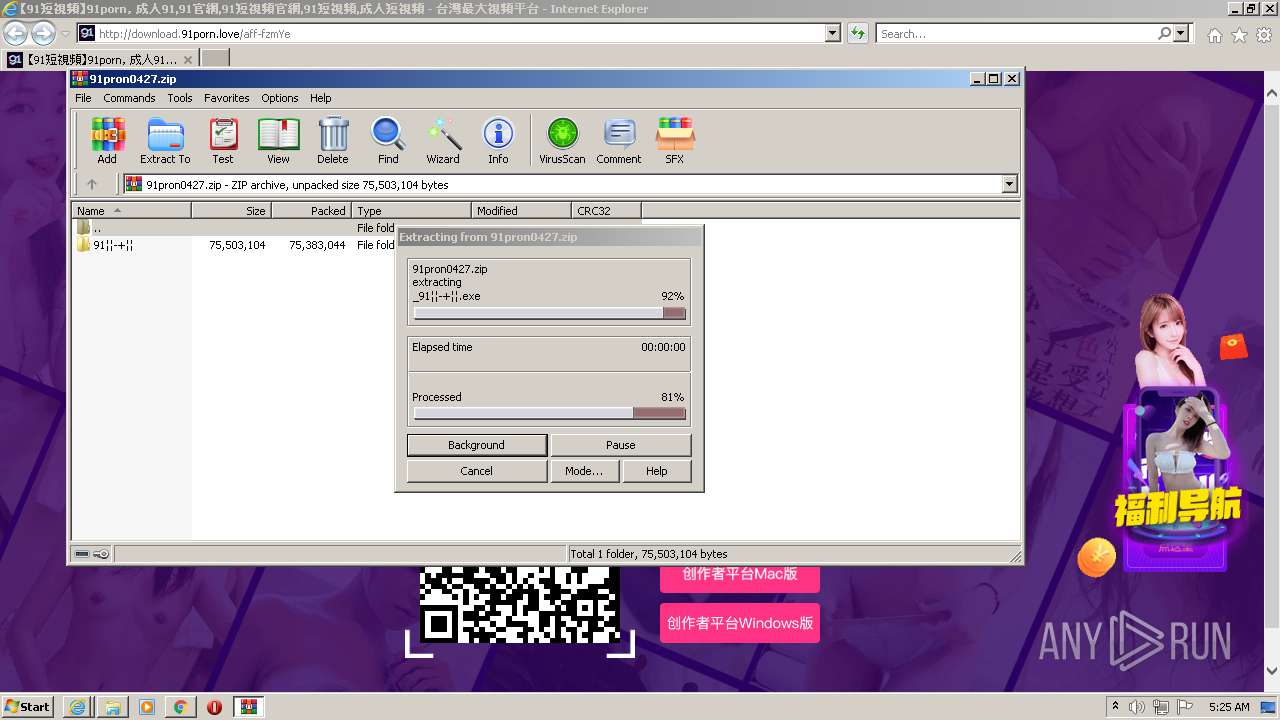
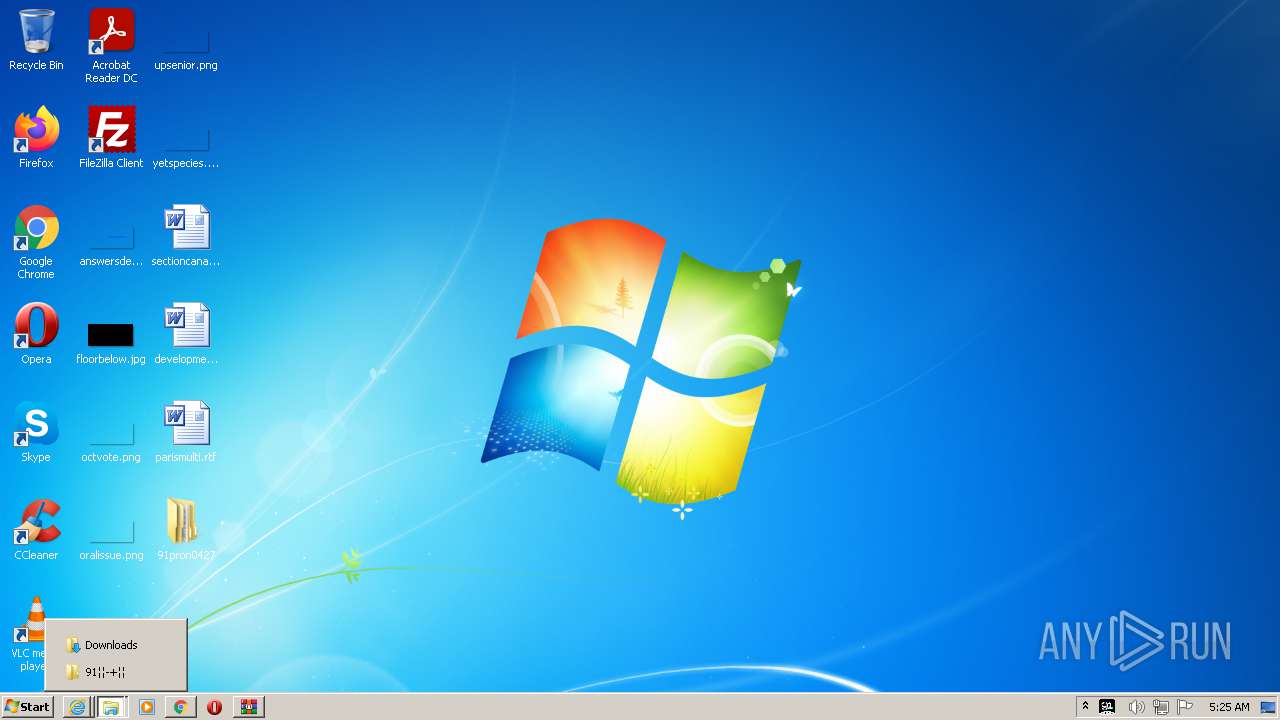
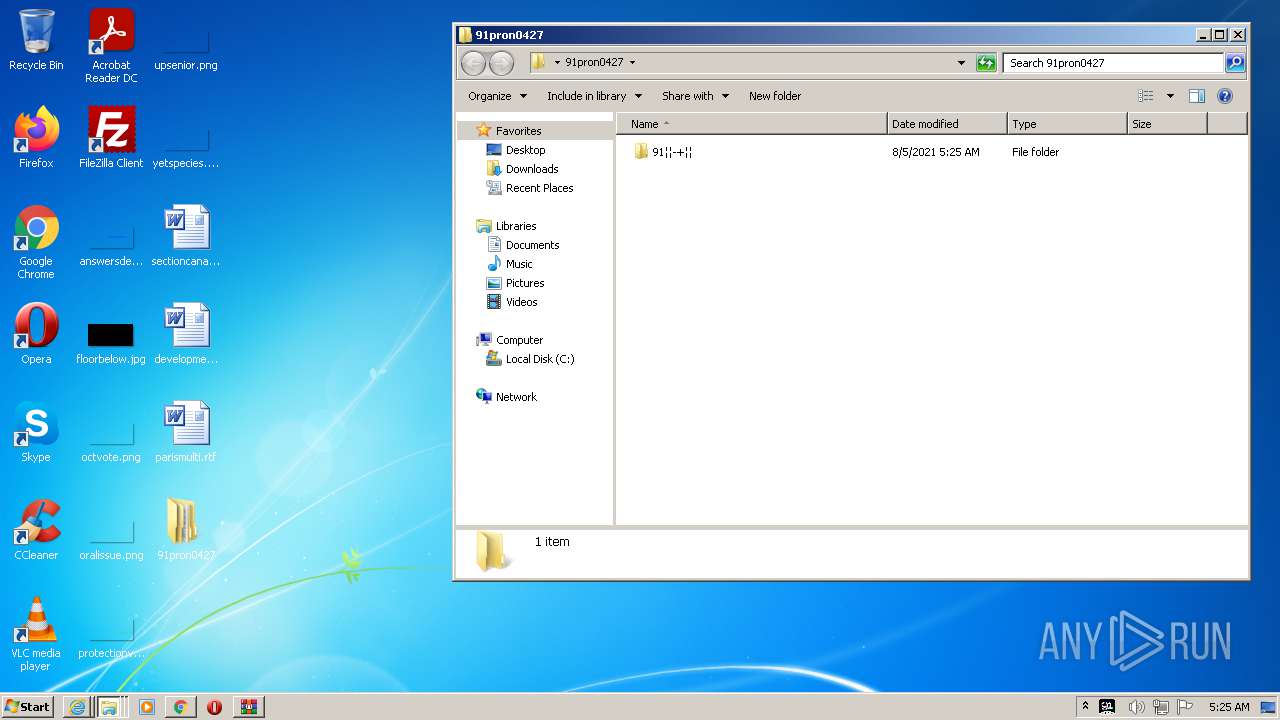
- WinRAR.exe (PID: 4056)
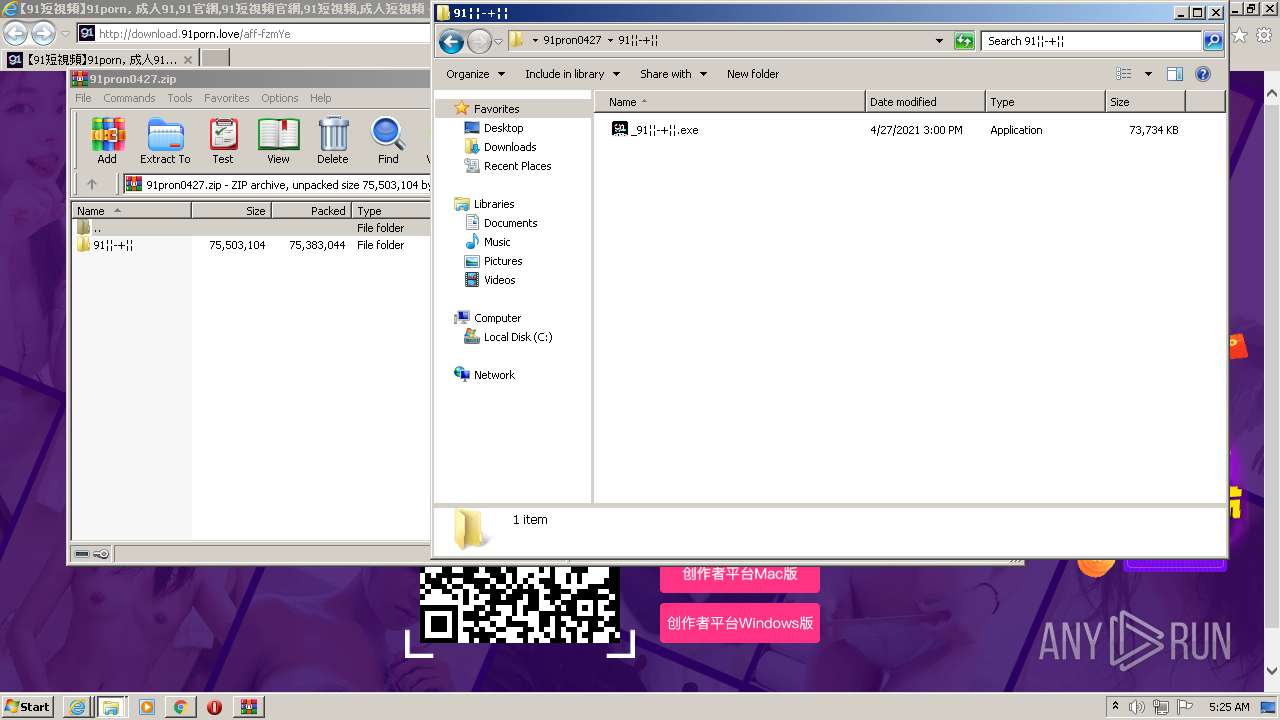
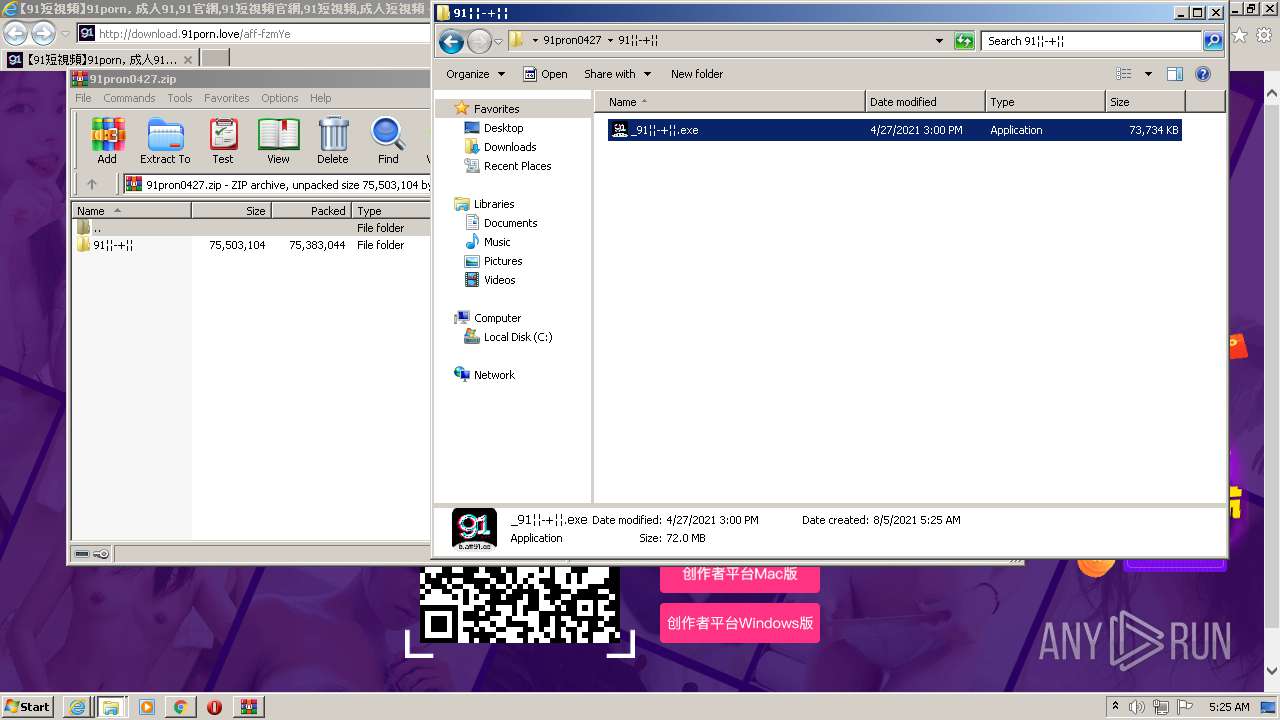
- _91��-+��.exe (PID: 3180)
- _91��-+��.exe (PID: 4080)
- dotNetFx45_Full_setup.exe (PID: 2276)
- Setup.exe (PID: 3808)
Reads the computer name
- WinRAR.exe (PID: 4056)
- _91��-+��.exe (PID: 3180)
- _91��-+��.exe (PID: 4080)
- dotNetFx45_Full_setup.exe (PID: 2276)
- Setup.exe (PID: 3808)
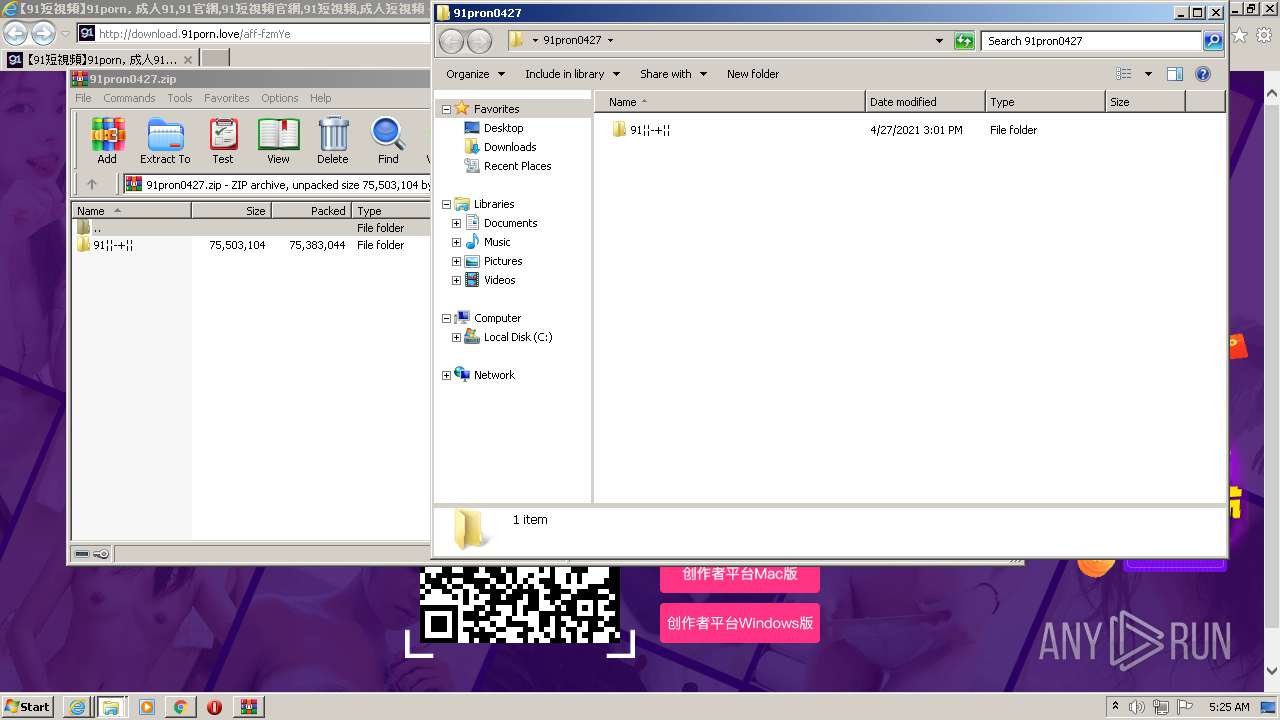
Creates files in the program directory
- _91��-+��.exe (PID: 3180)
Application launched itself
- _91��-+��.exe (PID: 3180)
Drops a file with too old compile date
- _91��-+��.exe (PID: 4080)
- dotNetFx45_Full_setup.exe (PID: 2276)
Executable content was dropped or overwritten
- _91��-+��.exe (PID: 4080)
- dotNetFx45_Full_setup.exe (PID: 2276)
Drops a file that was compiled in debug mode
- _91��-+��.exe (PID: 4080)
- dotNetFx45_Full_setup.exe (PID: 2276)
Reads CPU info
- Setup.exe (PID: 3808)
INFO
Checks supported languages
- iexplore.exe (PID: 3228)
- iexplore.exe (PID: 3092)
- explorer.exe (PID: 772)
- chrome.exe (PID: 2652)
- chrome.exe (PID: 1208)
- chrome.exe (PID: 3024)
- chrome.exe (PID: 1136)
- chrome.exe (PID: 2604)
- chrome.exe (PID: 2132)
- chrome.exe (PID: 1020)
- chrome.exe (PID: 2028)
- chrome.exe (PID: 1384)
- chrome.exe (PID: 1636)
- chrome.exe (PID: 3152)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 3764)
- chrome.exe (PID: 2336)
- WISPTIS.EXE (PID: 4012)
- chrome.exe (PID: 3508)
- chrome.exe (PID: 3764)
- chrome.exe (PID: 3688)
- chrome.exe (PID: 2472)
- chrome.exe (PID: 2456)
- chrome.exe (PID: 2188)
- chrome.exe (PID: 116)
- chrome.exe (PID: 2996)
- opera.exe (PID: 3520)
- chrome.exe (PID: 3240)
Application launched itself
- iexplore.exe (PID: 3228)
- chrome.exe (PID: 2652)
Reads the computer name
- iexplore.exe (PID: 3092)
- iexplore.exe (PID: 3228)
- explorer.exe (PID: 772)
- chrome.exe (PID: 1136)
- chrome.exe (PID: 3024)
- chrome.exe (PID: 2604)
- chrome.exe (PID: 2652)
- chrome.exe (PID: 3152)
- WISPTIS.EXE (PID: 4012)
- chrome.exe (PID: 3508)
- chrome.exe (PID: 2472)
- chrome.exe (PID: 3764)
- chrome.exe (PID: 3240)
- opera.exe (PID: 3520)
Reads settings of System Certificates
- iexplore.exe (PID: 3092)
- iexplore.exe (PID: 3228)
- chrome.exe (PID: 1136)
Checks Windows Trust Settings
- iexplore.exe (PID: 3228)
- iexplore.exe (PID: 3092)
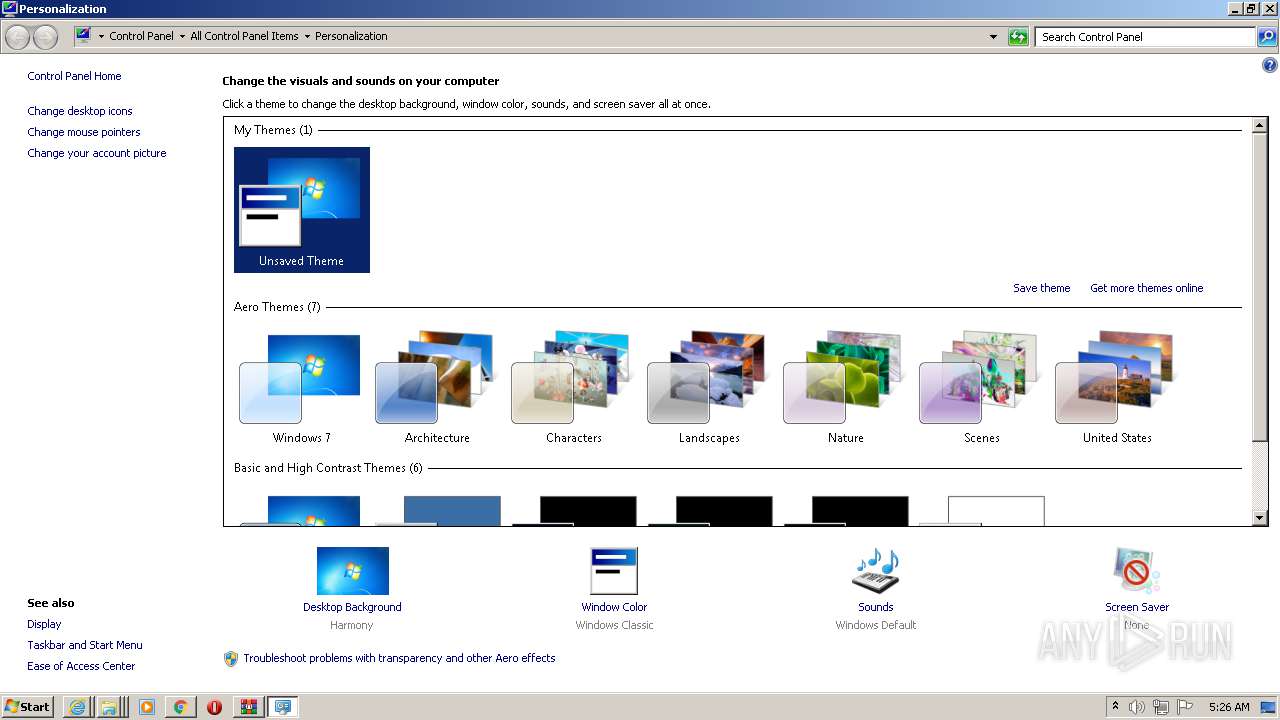
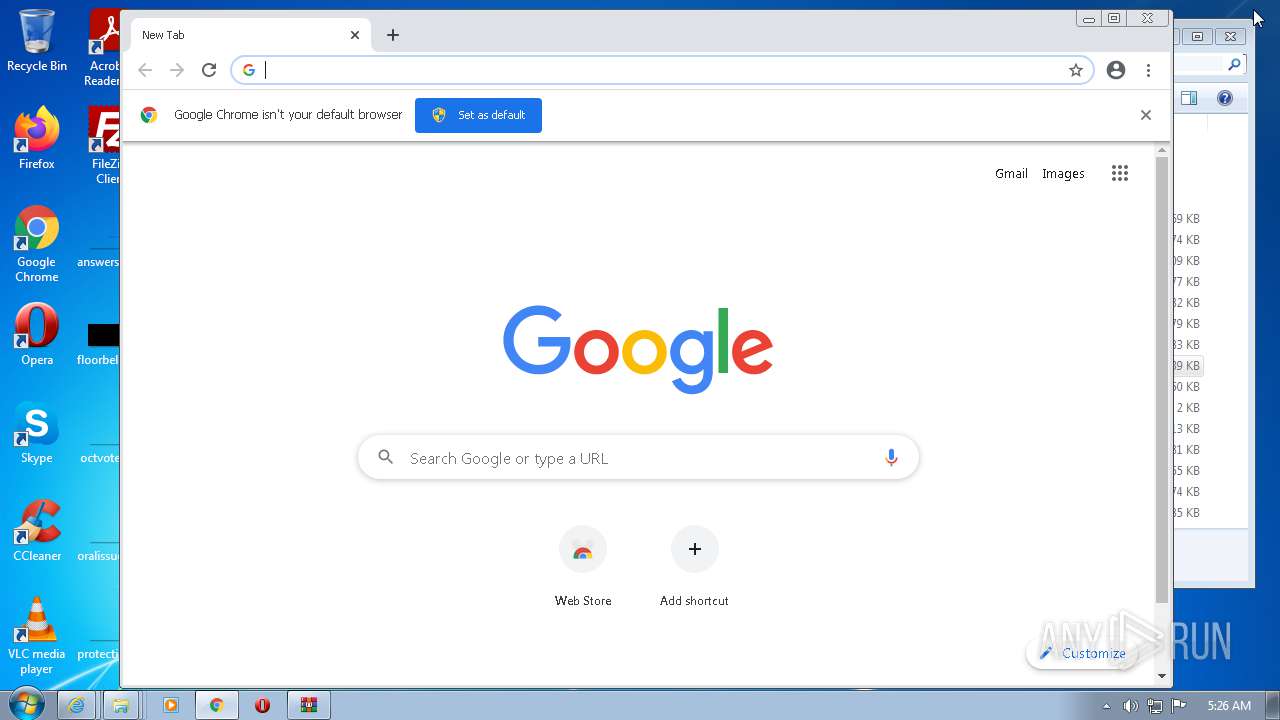
Manual execution by user
- chrome.exe (PID: 2652)
- explorer.exe (PID: 772)
- _91��-+��.exe (PID: 3180)
- dotNetFx45_Full_setup.exe (PID: 2500)
- dotNetFx45_Full_setup.exe (PID: 2276)
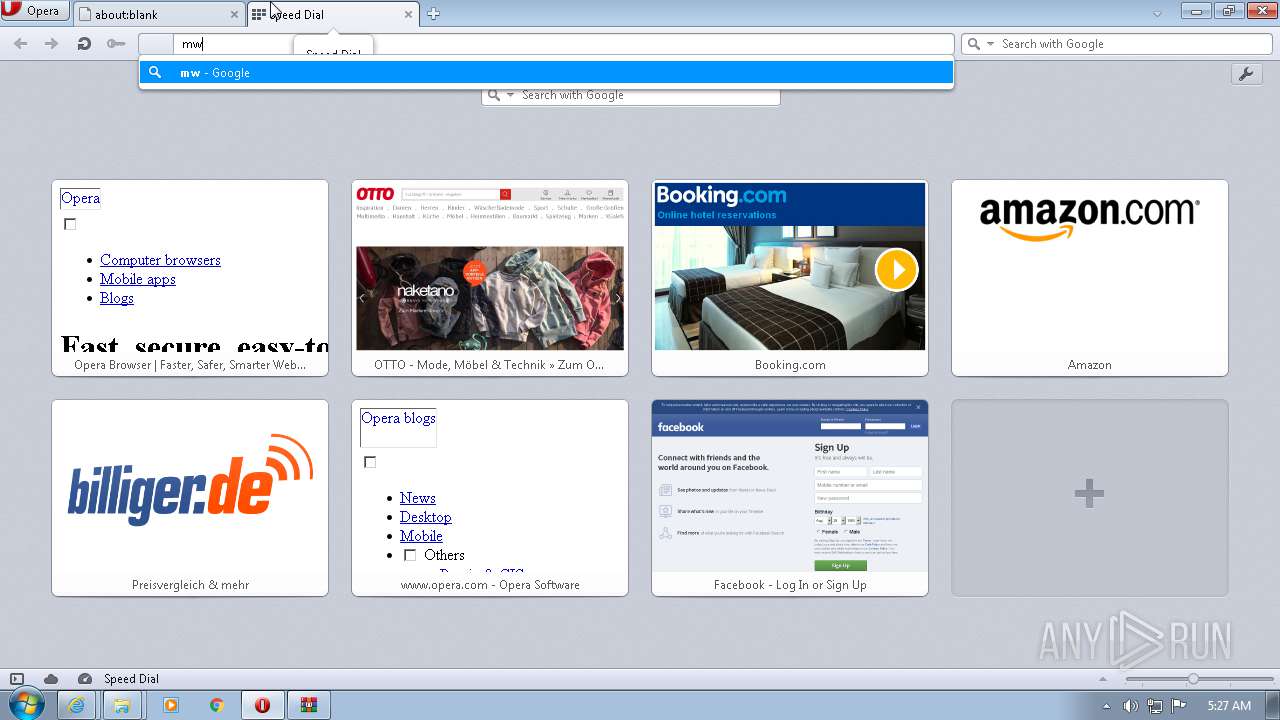
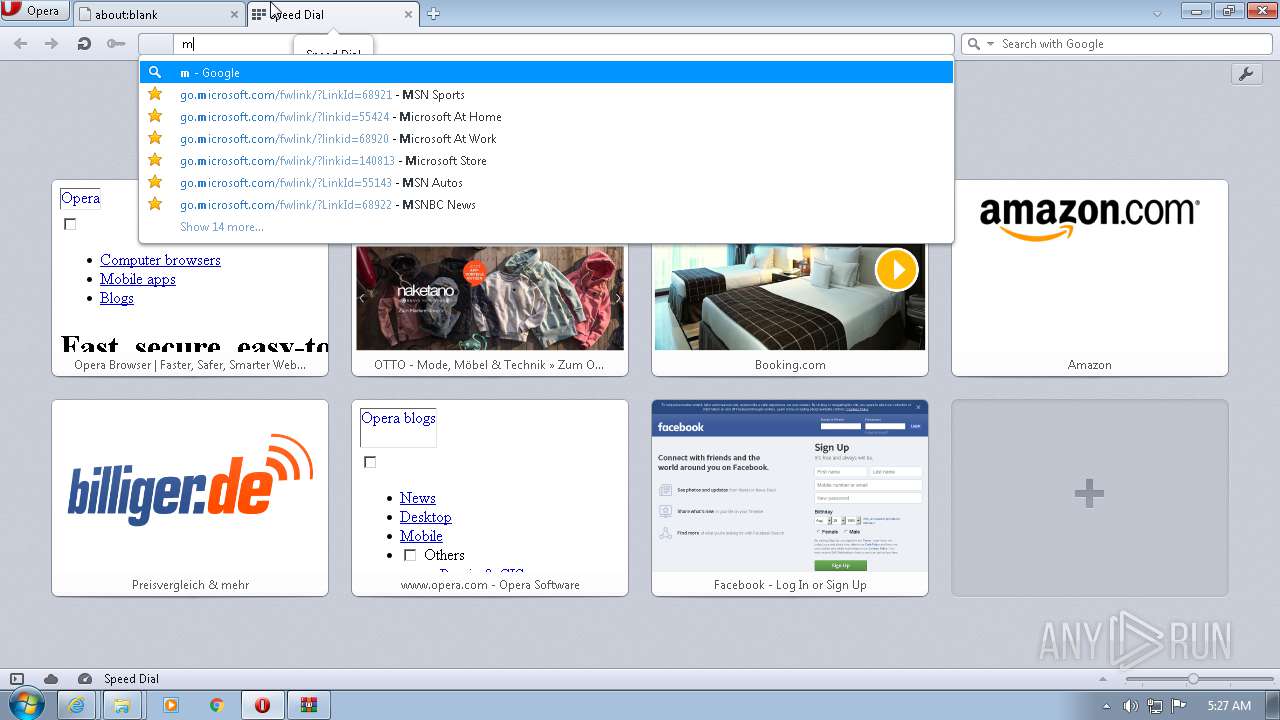
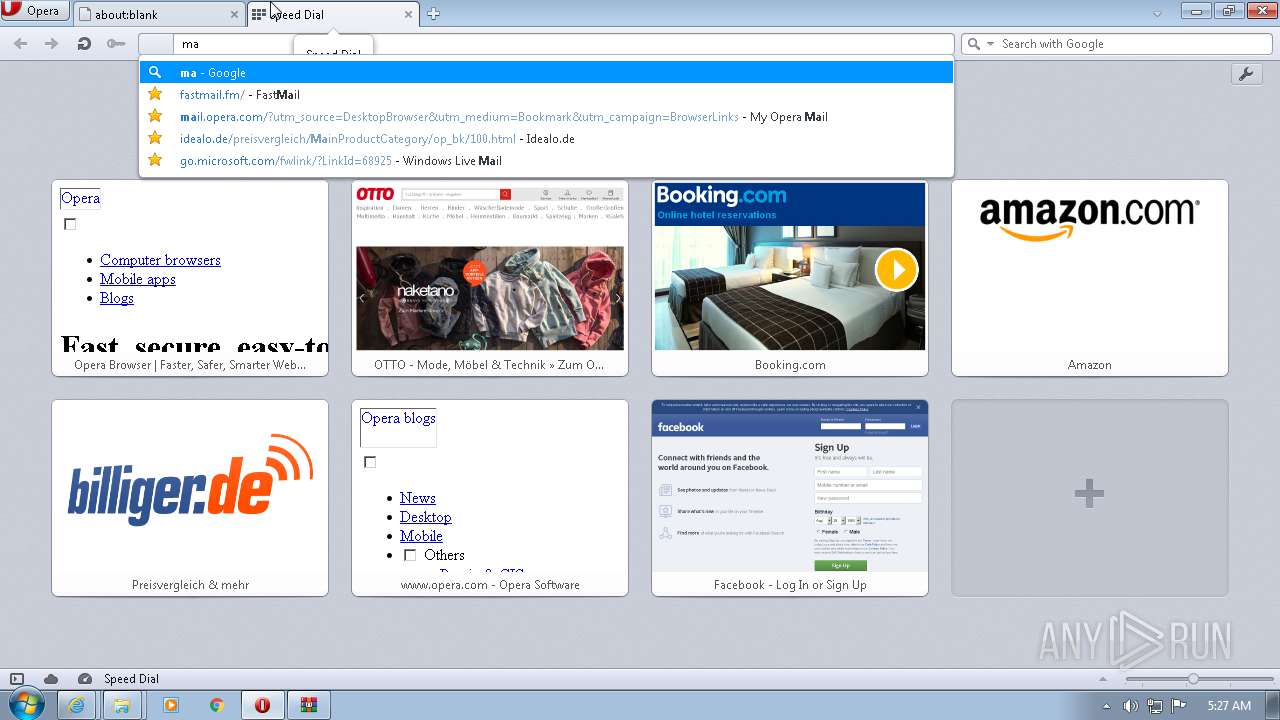
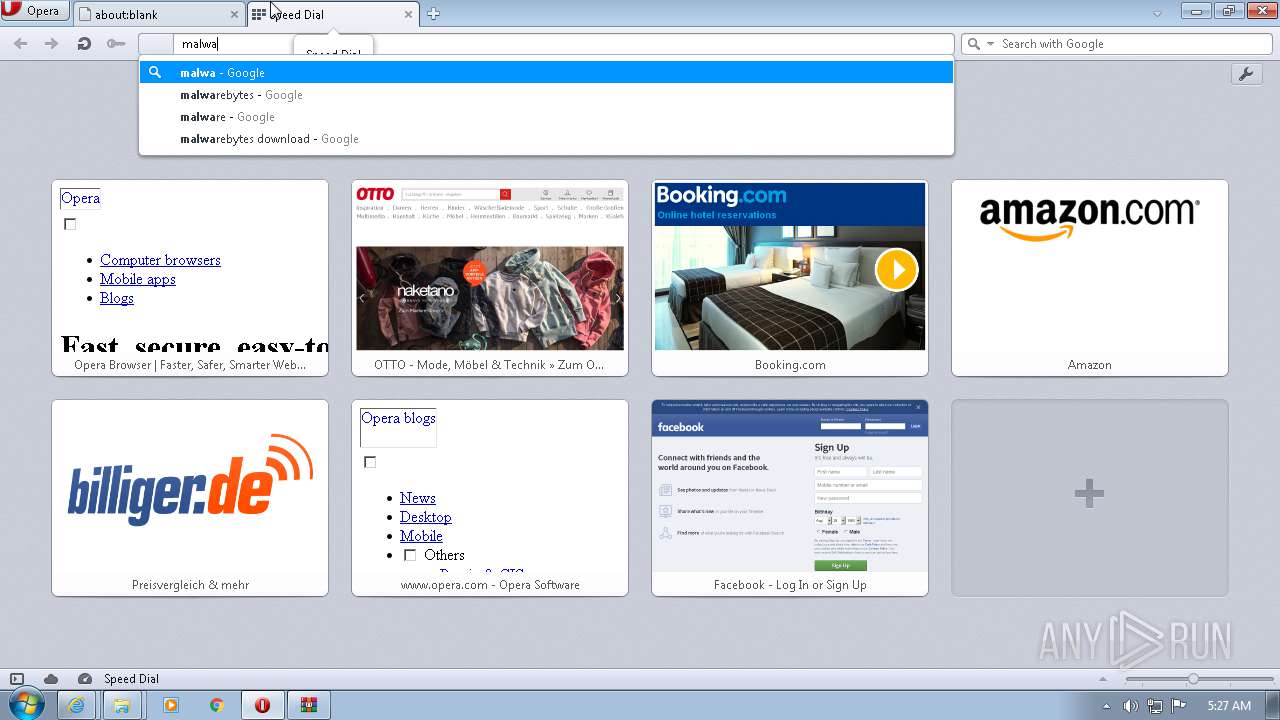
- opera.exe (PID: 3520)
Changes internet zones settings
- iexplore.exe (PID: 3228)
Creates files in the user directory
- iexplore.exe (PID: 3092)
- iexplore.exe (PID: 3228)
- opera.exe (PID: 3520)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3228)
Reads the hosts file
- chrome.exe (PID: 1136)
- chrome.exe (PID: 2652)
Reads internet explorer settings
- iexplore.exe (PID: 3092)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3228)
- opera.exe (PID: 3520)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3228)
Changes settings of System certificates
- iexplore.exe (PID: 3228)
Reads the date of Windows installation
- chrome.exe (PID: 2472)
- opera.exe (PID: 3520)
Check for Java to be installed
- opera.exe (PID: 3520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
89
Monitored processes
35
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1044,15123803744887713622,1695156051670308454,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2784 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 772 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,15123803744887713622,1695156051670308454,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2920 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1044,15123803744887713622,1695156051670308454,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1436 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6a94d988,0x6a94d998,0x6a94d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,15123803744887713622,1695156051670308454,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,15123803744887713622,1695156051670308454,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2800 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,15123803744887713622,1695156051670308454,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,15123803744887713622,1695156051670308454,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1860 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1044,15123803744887713622,1695156051670308454,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1580 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
31 712
Read events
31 189
Write events
514
Delete events
9
Modification events
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30902705 | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30902705 | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
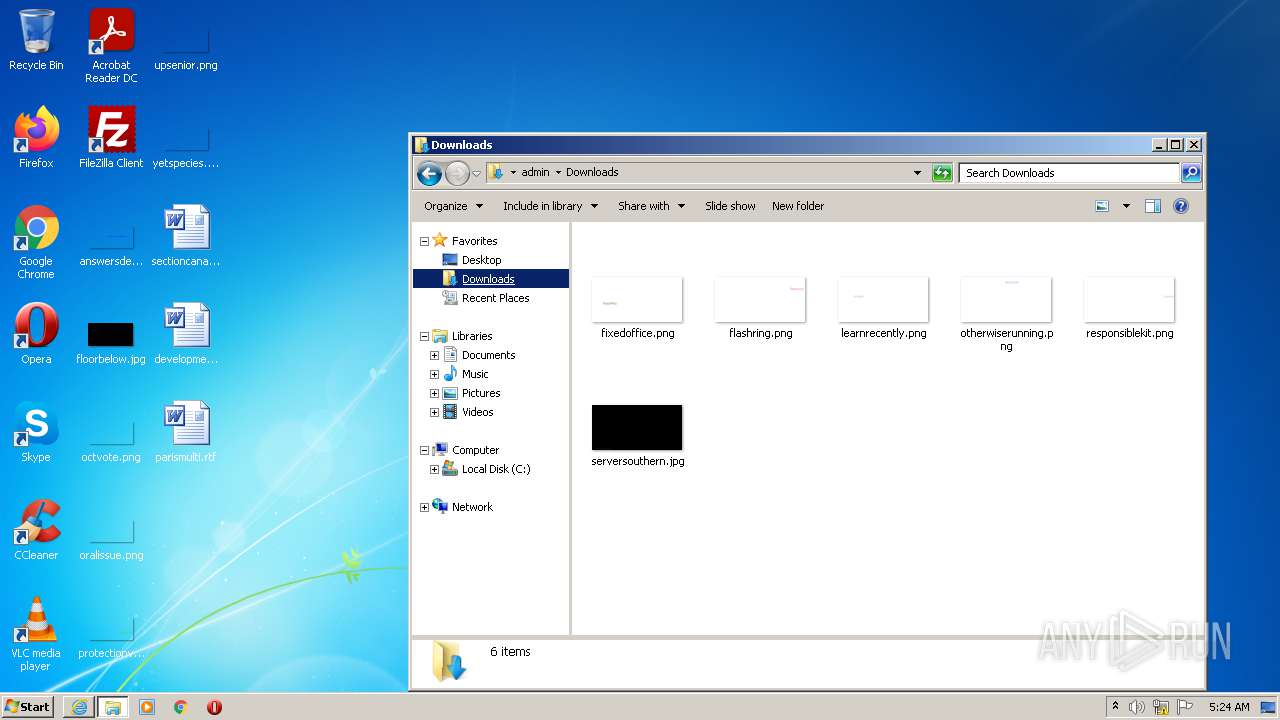
Executable files
37
Suspicious files
102
Text files
402
Unknown types
93
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3092 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B039FEA45CB4CC4BBACFC013C7C55604_ACB084F1532E23E916946A083A45F6BF | der | |
MD5:— | SHA256:— | |||
| 3092 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 3092 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:— | SHA256:— | |||
| 3092 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3092 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\tg-group[1].png | image | |
MD5:— | SHA256:— | |||
| 3092 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B039FEA45CB4CC4BBACFC013C7C55604_ACB084F1532E23E916946A083A45F6BF | binary | |
MD5:— | SHA256:— | |||
| 3092 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E87CE99F124623F95572A696C80EFCAF_7549F91459BF77025A5A3302615B87B5 | der | |
MD5:— | SHA256:— | |||
| 3092 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 3092 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\aff-fzmYe[1].htm | html | |
MD5:— | SHA256:— | |||
| 3092 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
111
TCP/UDP connections
114
DNS requests
52
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3092 | iexplore.exe | GET | 200 | 104.21.74.218:80 | http://download.91porn.love/static/images/index/business-bg2.png | US | image | 76.0 Kb | unknown |
3092 | iexplore.exe | GET | 200 | 104.21.74.218:80 | http://download.91porn.love/aff-fzmYe | US | html | 5.72 Kb | unknown |
3092 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSXi0cW5bD2WLrmnasWibg2OuPDpgQUVXRPsnJP9WC6UNHX5lFcmgGHGtcCEAeqTWMJIwb1FN8aMF%2BWt3I%3D | US | der | 471 b | whitelisted |
3092 | iexplore.exe | GET | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCBwXmOUIIn%2FAoAAAAA8rrr | US | der | 472 b | whitelisted |
3092 | iexplore.exe | GET | 200 | 104.21.74.218:80 | http://download.91porn.love/static/images/index/tg-group.png | US | image | 3.38 Kb | unknown |
3092 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ5rEWLwbJFq%2FmAU80sm7E%3D | US | der | 471 b | whitelisted |
3228 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
3092 | iexplore.exe | GET | 200 | 104.21.74.218:80 | http://download.91porn.love/static/images/index/bg.png | US | image | 733 Kb | unknown |
3092 | iexplore.exe | GET | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3092 | iexplore.exe | GET | 200 | 104.21.74.218:80 | http://download.91porn.love/static/images/index/qrcode-box.png | US | image | 316 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | — | — | US | whitelisted |
3092 | iexplore.exe | 104.21.74.218:443 | download.91porn.love | Cloudflare Inc | US | unknown |
3092 | iexplore.exe | 2.16.186.25:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
3092 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3092 | iexplore.exe | 104.21.74.218:80 | download.91porn.love | Cloudflare Inc | US | unknown |
3092 | iexplore.exe | 142.250.185.72:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
3092 | iexplore.exe | 151.101.1.229:443 | cdn.jsdelivr.net | Fastly | US | suspicious |
3092 | iexplore.exe | 104.18.20.226:80 | ocsp2.globalsign.com | Cloudflare Inc | US | shared |
3092 | iexplore.exe | 216.58.212.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3228 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.91porn.love |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oss.huaweiyiyao.com |
| suspicious |
www.googletagmanager.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
Threats
Process | Message |
|---|---|
Setup.exe | The operation completed successfully.
|