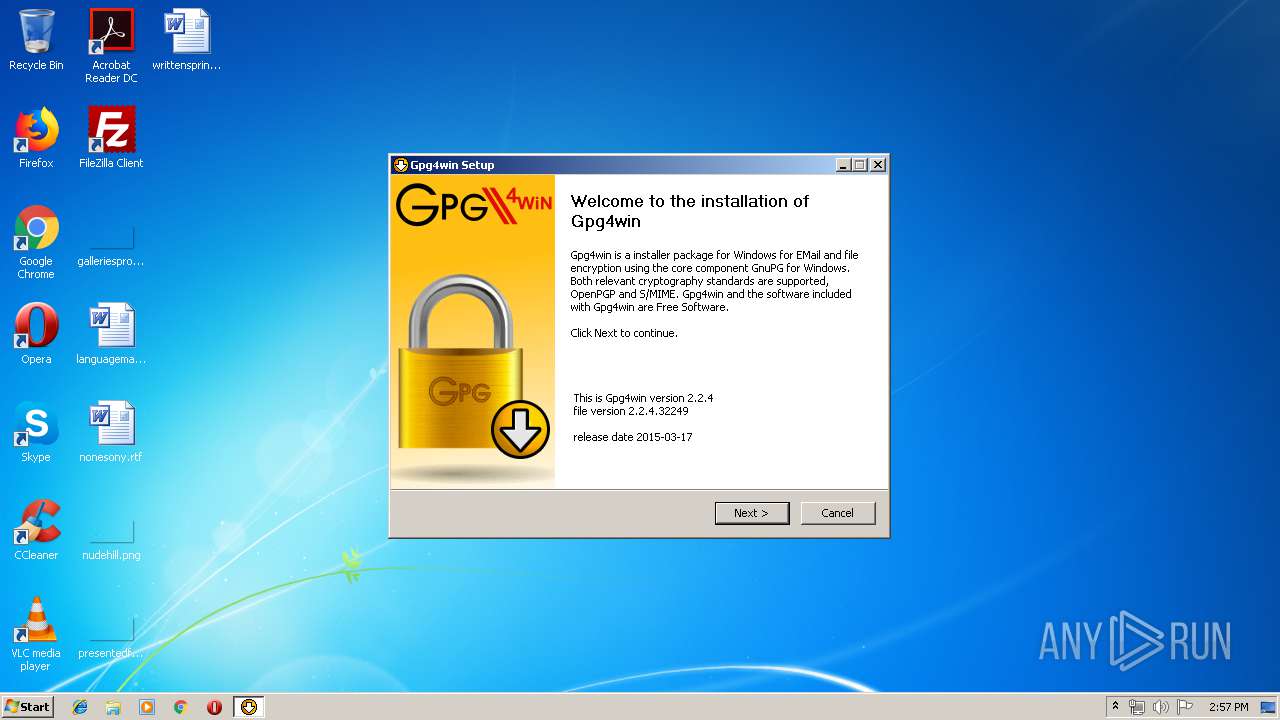
| File name: | gpg4win-vanilla-2.2.4.exe |
| Full analysis: | https://app.any.run/tasks/85ba75f7-b8e1-4651-b900-78b4978150c5 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 13:56:53 |
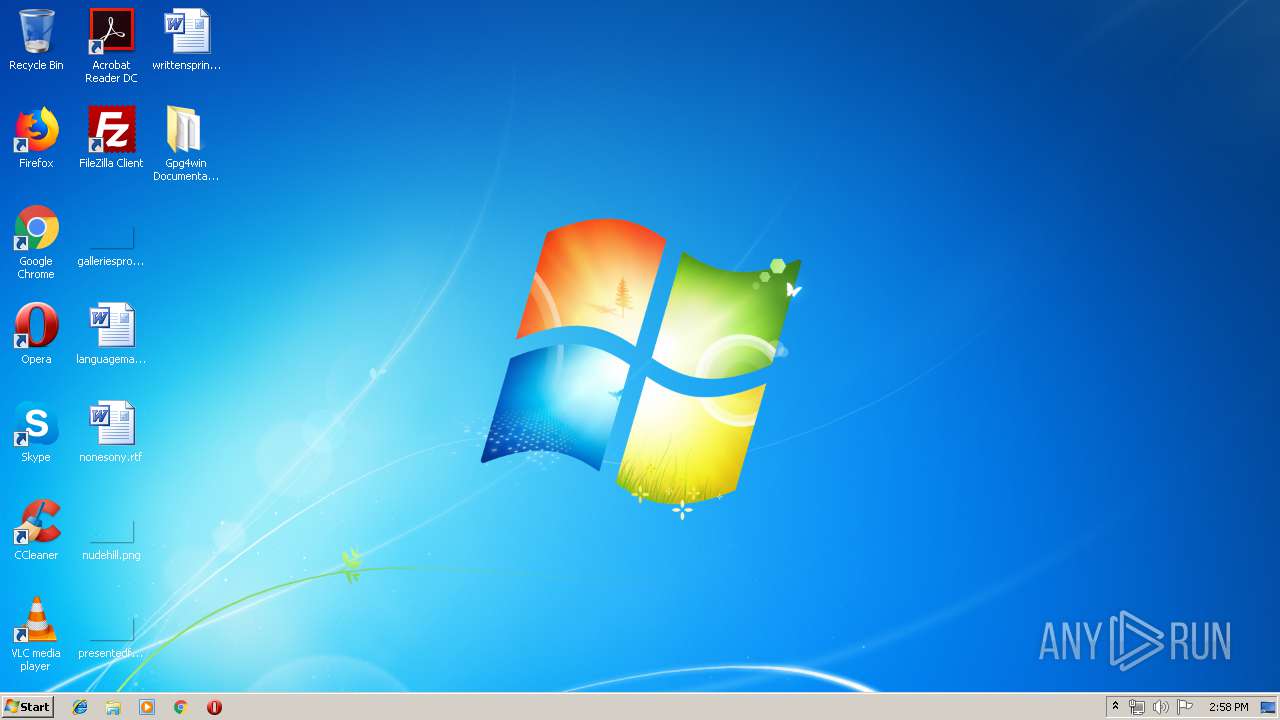
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 827C0D36B22BFDBC8AB95B891687B19C |
| SHA1: | 5A702C1B357BE6427D96B772F673840E2762D222 |
| SHA256: | 4A8A3CB9D3BA8EA2F23E45C6A3D4B2E074B22D692044D4778D51695DF67488A7 |
| SSDEEP: | 98304:OhUVJV0sCpNpeO0AqAAPeYbN/iseSqOgBiPGboUsRQuXViy:OhOOp7hbqAAPemN/taTBiPbUXuXVj |
MALICIOUS
Loads dropped or rewritten executable
- gpg4win-vanilla-2.2.4.exe (PID: 3992)
- dirmngr.exe (PID: 2584)
Application was dropped or rewritten from another process
- dirmngr.exe (PID: 2584)
SUSPICIOUS
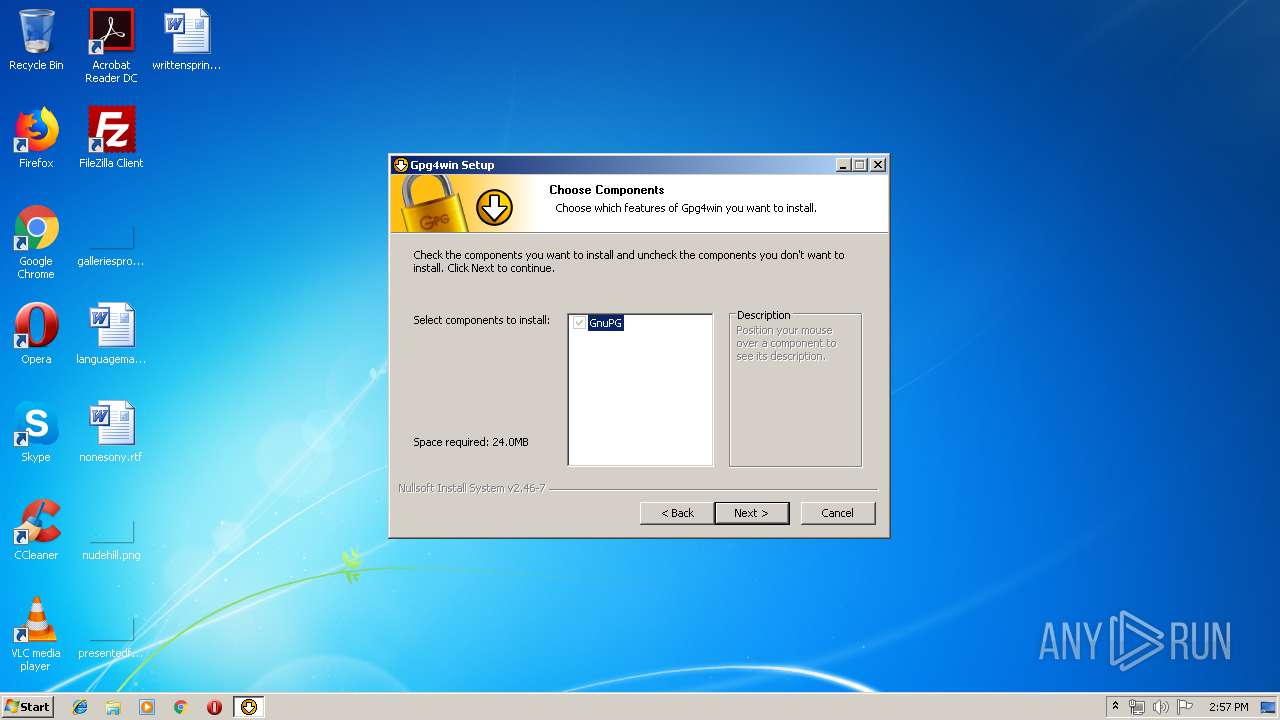
Executable content was dropped or overwritten
- gpg4win-vanilla-2.2.4.exe (PID: 3992)
Executed as Windows Service
- dirmngr.exe (PID: 2584)
Creates files in the Windows directory
- dirmngr.exe (PID: 2584)
Creates a software uninstall entry
- gpg4win-vanilla-2.2.4.exe (PID: 3992)
Creates files in the program directory
- gpg4win-vanilla-2.2.4.exe (PID: 3992)
INFO
Dropped object may contain Bitcoin addresses
- gpg4win-vanilla-2.2.4.exe (PID: 3992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (91.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.3) |
| .exe | | | Win64 Executable (generic) (3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:01:05 19:21:23+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.22 |
| CodeSize: | 35328 |
| InitializedDataSize: | 20480 |
| UninitializedDataSize: | 109568 |
| EntryPoint: | 0x4327 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.4.32249 |
| ProductVersionNumber: | 2.2.4.32249 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
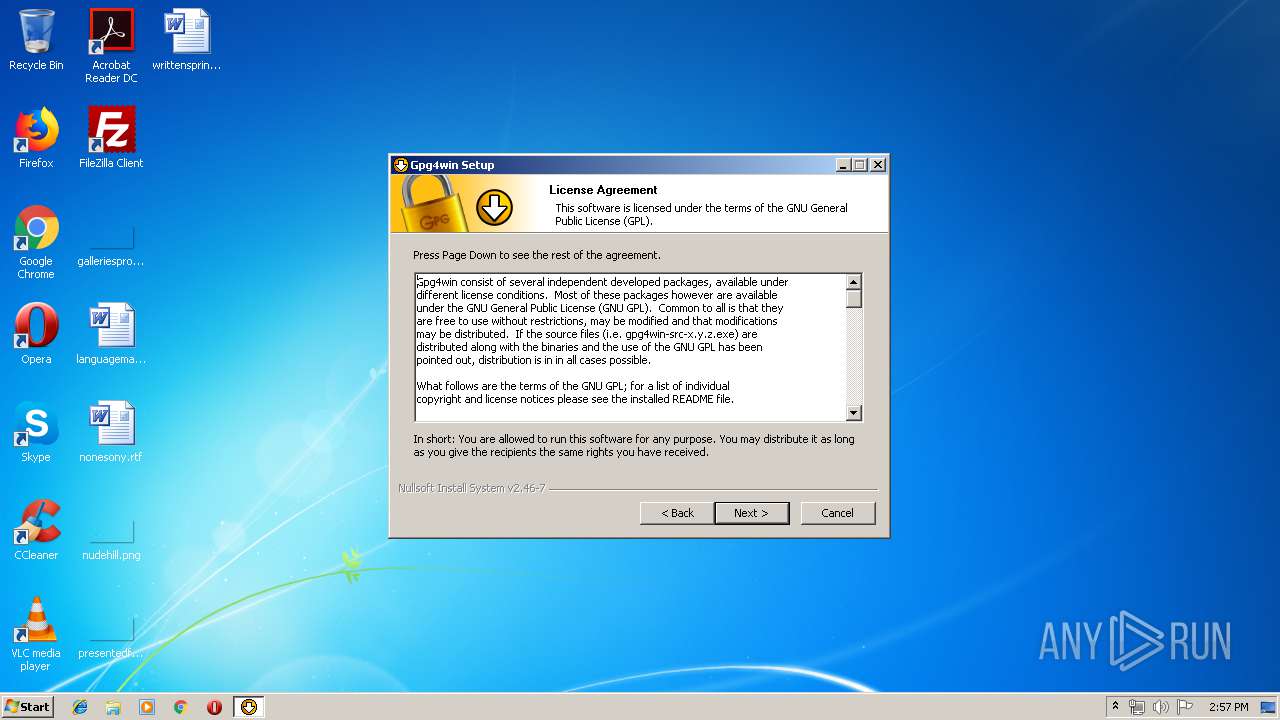
| Comments: | GPG4Win is Free Software; you can redistribute it and/or modify it under the terms of the GNU General Public License. You should have received a copy of the GNU General Public License along with this software; if not, write to the Free Software Foundation, Inc., 51 Franklin Street, Fifth Floor, Boston, MA 02110-1301, USA |
| CompanyName: | g10 Code GmbH |
| FileDescription: | Gpg4win: The GNU Privacy Guard and Tools for Windows |
| FileVersion: | 2.2.4.32249 |
| LegalCopyright: | Copyright (C) 2008 g10 Code GmbH |
| LegalTrademarks: | - |
| ProductName: | GPG4Win (2.2.4) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Jan-2012 18:21:23 |
| Detected languages: |
|
| Comments: | GPG4Win is Free Software; you can redistribute it and/or modify it under the terms of the GNU General Public License. You should have received a copy of the GNU General Public License along with this software; if not, write to the Free Software Foundation, Inc., 51 Franklin Street, Fifth Floor, Boston, MA 02110-1301, USA |
| CompanyName: | g10 Code GmbH |
| FileDescription: | Gpg4win: The GNU Privacy Guard and Tools for Windows |
| FileVersion: | 2.2.4.32249 |
| LegalCopyright: | Copyright (C) 2008 g10 Code GmbH |
| LegalTrademarks: | - |
| ProductName: | GPG4Win (2.2.4) |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 05-Jan-2012 18:21:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00008844 | 0x00008A00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.97387 |
.data | 0x0000A000 | 0x0000008C | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.18031 |
.rdata | 0x0000B000 | 0x00002394 | 0x00002400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.89911 |
.bss | 0x0000E000 | 0x0001ABD0 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00029000 | 0x00001304 | 0x00001400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.23715 |
.ndata | 0x0002B000 | 0x0000B000 | 0x00000400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00036000 | 0x00005F90 | 0x00006000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.68674 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21979 | 960 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.70233 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 2.42478 | 1128 | UNKNOWN | English - United States | RT_ICON |
102 | 2.70702 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.45849 | 48 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.71935 | 356 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.68101 | 582 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.84976 | 260 | UNKNOWN | English - United States | RT_DIALOG |
107 | 2.52183 | 160 | UNKNOWN | English - United States | RT_DIALOG |
110 | 2.82633 | 1638 | UNKNOWN | English - United States | RT_BITMAP |
Imports
ADVAPI32.dll |
COMCTL32.DLL |
GDI32.dll |
KERNEL32.dll |
SHELL32.DLL |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
40
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
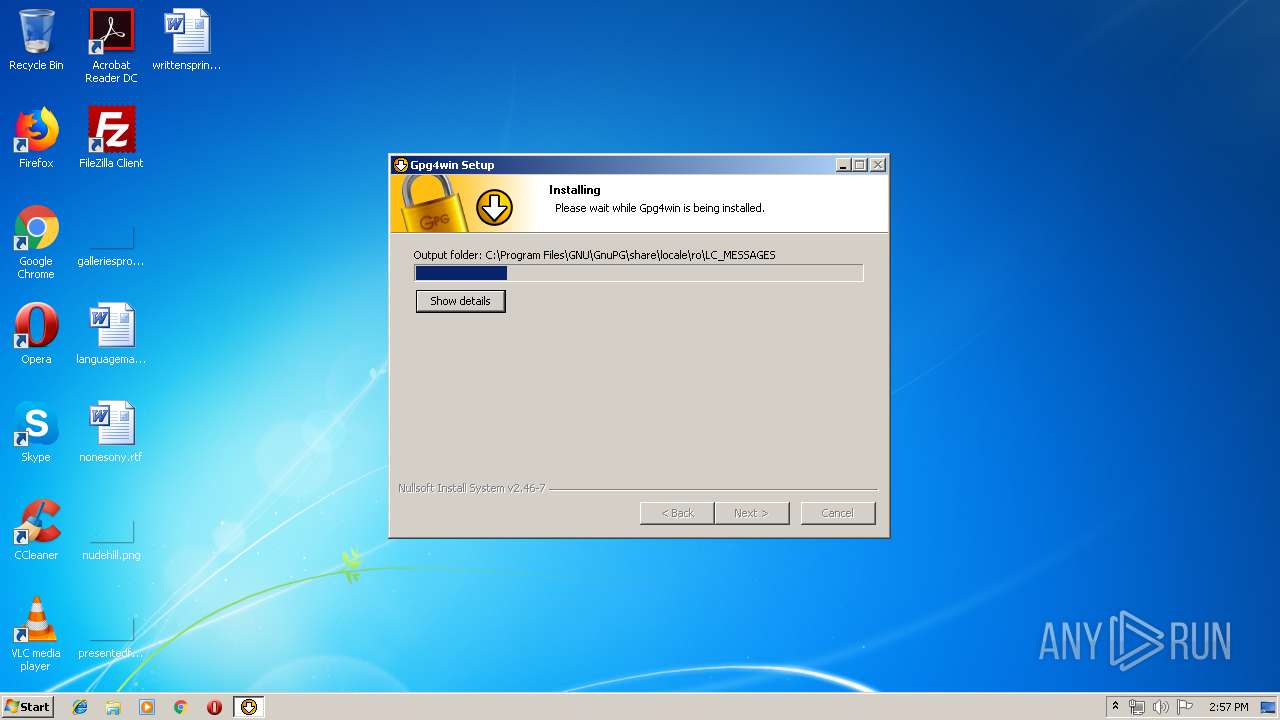
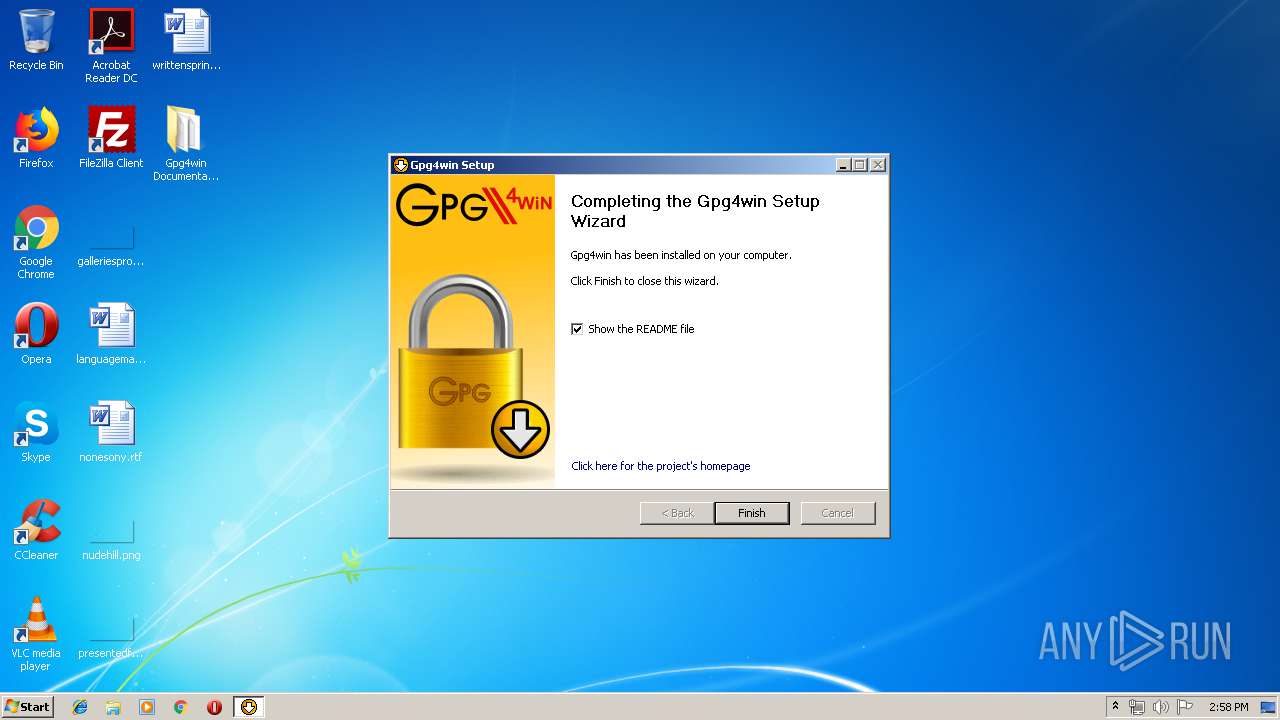
| 608 | "C:\Users\admin\AppData\Local\Temp\gpg4win-vanilla-2.2.4.exe" | C:\Users\admin\AppData\Local\Temp\gpg4win-vanilla-2.2.4.exe | — | explorer.exe | |||||||||||
User: admin Company: g10 Code GmbH Integrity Level: MEDIUM Description: Gpg4win: The GNU Privacy Guard and Tools for Windows Exit code: 0 Version: 2.2.4.32249 | |||||||||||||||
| 2584 | "C:\Program Files\GNU\GnuPG\dirmngr.exe" --service | C:\Program Files\GNU\GnuPG\dirmngr.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 3992 | "C:\Users\admin\AppData\Local\Temp\gpg4win-vanilla-2.2.4.exe" | C:\Users\admin\AppData\Local\Temp\gpg4win-vanilla-2.2.4.exe | explorer.exe | ||||||||||||
User: admin Company: g10 Code GmbH Integrity Level: HIGH Description: Gpg4win: The GNU Privacy Guard and Tools for Windows Exit code: 0 Version: 2.2.4.32249 Modules
| |||||||||||||||
Total events
367
Read events
352
Write events
15
Delete events
0
Modification events
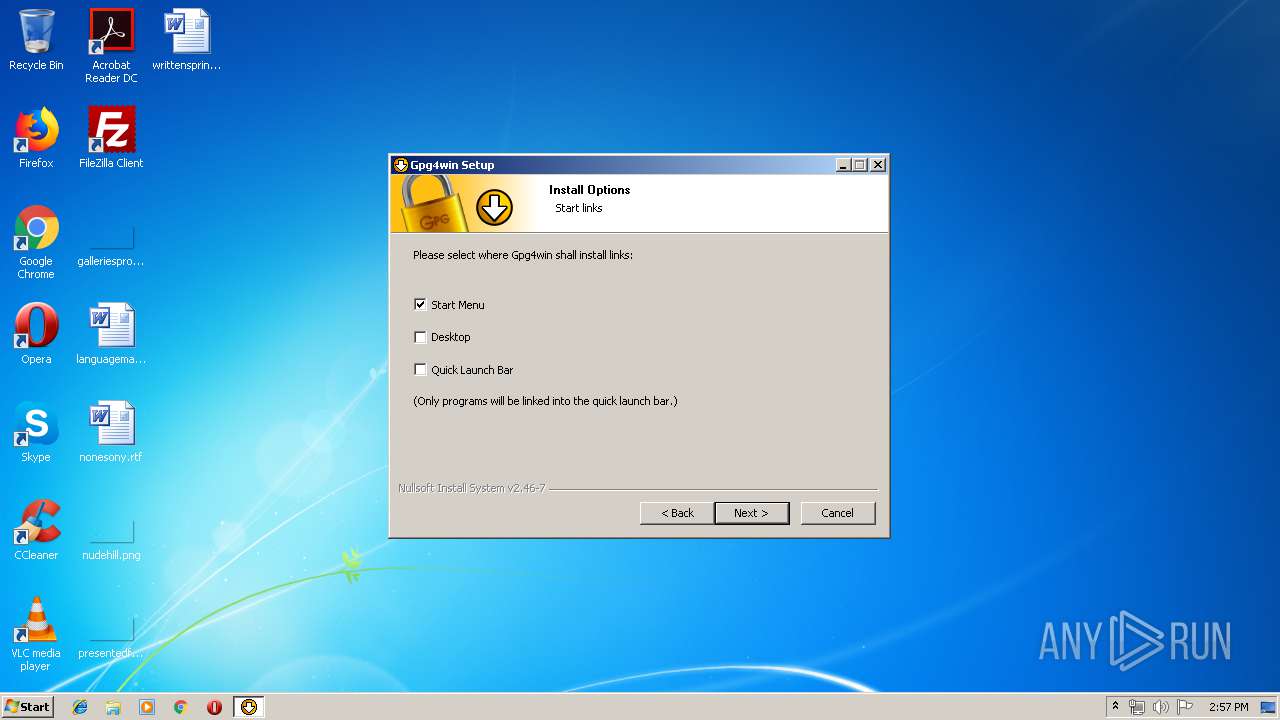
| (PID) Process: | (3992) gpg4win-vanilla-2.2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GNU\GnuPG |
| Operation: | write | Name: | Install Directory |
Value: C:\Program Files\GNU\GnuPG | |||
| (PID) Process: | (3992) gpg4win-vanilla-2.2.4.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager\Environment |
| Operation: | write | Name: | Path |
Value: C:\ProgramData\Oracle\Java\javapath;%SystemRoot%\system32;%SystemRoot%;%SystemRoot%\System32\Wbem;%SYSTEMROOT%\System32\WindowsPowerShell\v1.0\;C:\Program Files\GNU\GnuPG\pub | |||
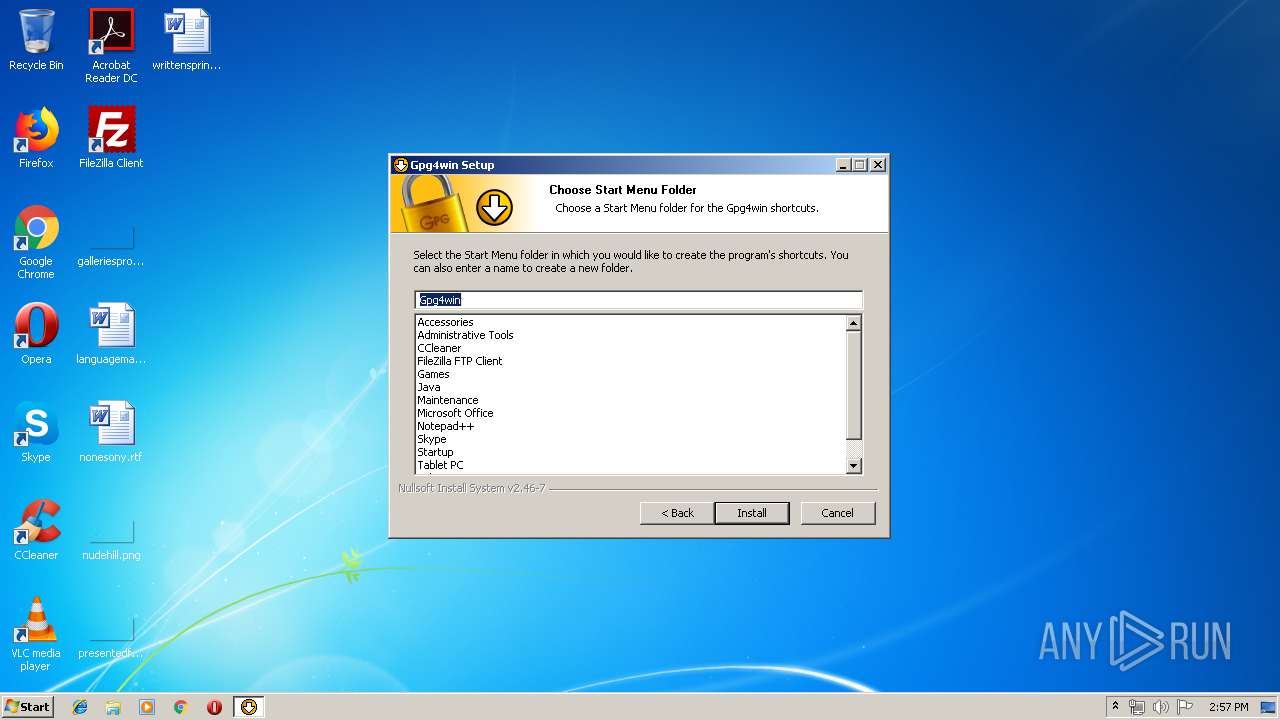
| (PID) Process: | (3992) gpg4win-vanilla-2.2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GNU\GPG4Win |
| Operation: | write | Name: | Start Menu Folder |
Value: Gpg4win | |||
| (PID) Process: | (3992) gpg4win-vanilla-2.2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\GPG4Win |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\GNU\GnuPG\gpg4win-uninstall.exe" | |||
| (PID) Process: | (3992) gpg4win-vanilla-2.2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\GPG4Win |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\GNU\GnuPG | |||
| (PID) Process: | (3992) gpg4win-vanilla-2.2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\GPG4Win |
| Operation: | write | Name: | DisplayName |
Value: Gpg4win (2.2.4) | |||
| (PID) Process: | (3992) gpg4win-vanilla-2.2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\GPG4Win |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\GNU\GnuPG\bin\kleopatra.exe,0 | |||
| (PID) Process: | (3992) gpg4win-vanilla-2.2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\GPG4Win |
| Operation: | write | Name: | DisplayVersion |
Value: 2.2.4 | |||
| (PID) Process: | (3992) gpg4win-vanilla-2.2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\GPG4Win |
| Operation: | write | Name: | Publisher |
Value: The Gpg4win Project | |||
| (PID) Process: | (3992) gpg4win-vanilla-2.2.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\GPG4Win |
| Operation: | write | Name: | URLInfoAbout |
Value: http://www.gpg4win.org/ | |||
Executable files
62
Suspicious files
1
Text files
125
Unknown types
41
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3992 | gpg4win-vanilla-2.2.4.exe | C:\Users\admin\AppData\Local\Temp\nsu17D8.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 3992 | gpg4win-vanilla-2.2.4.exe | C:\Program Files\GNU\GnuPG\share\gpg4win\README.ar.txt | text | |
MD5:— | SHA256:— | |||
| 3992 | gpg4win-vanilla-2.2.4.exe | C:\Users\admin\AppData\Local\Temp\nsu17D8.tmp\installer-options.ini | text | |
MD5:— | SHA256:— | |||
| 3992 | gpg4win-vanilla-2.2.4.exe | C:\Users\admin\AppData\Local\Temp\nsu17D8.tmp\LangDLL.dll | executable | |
MD5:A151552574A6FC66D75DA0BF310B5DBA | SHA256:8A8658072B9DD118E79262F981127F98A4BCB897661751C0676B18BA1DEBAE10 | |||
| 3992 | gpg4win-vanilla-2.2.4.exe | C:\Users\admin\AppData\Local\Temp\nsu17D8.tmp\modern-wizard.bmp | image | |
MD5:25A4FC8820A41371E58D37B17064A96A | SHA256:A9B7C0AA93E9003DDAF0D0E8CD1881867ED9FA500618E4AAD44E1875DC5FBD92 | |||
| 3992 | gpg4win-vanilla-2.2.4.exe | C:\Users\admin\AppData\Local\Temp\nsu17D8.tmp\InstallOptions.dll | executable | |
MD5:AC2BEDA92A01B0DC99D3A6E98B954215 | SHA256:B0F50EF565B5029115AC35EA93BBDAF9614300B64C5B8DF473AAEB375FA59374 | |||
| 3992 | gpg4win-vanilla-2.2.4.exe | C:\Users\admin\AppData\Local\Temp\nsu17D8.tmp\modern-header.bmp | image | |
MD5:C8B840FD47CE34873B1EA59FB6042ADD | SHA256:34226B711A19FCDA61DFA9E968E1665C71449400FF2D9D204F7EFD4B1EEC0F6E | |||
| 3992 | gpg4win-vanilla-2.2.4.exe | C:\Program Files\GNU\GnuPG\share\gpg4win\README.fr.txt | text | |
MD5:— | SHA256:— | |||
| 3992 | gpg4win-vanilla-2.2.4.exe | C:\Program Files\GNU\GnuPG\share\gpg4win\README.it.txt | text | |
MD5:— | SHA256:— | |||
| 3992 | gpg4win-vanilla-2.2.4.exe | C:\Program Files\GNU\GnuPG\share\gpg4win\README.ru.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report