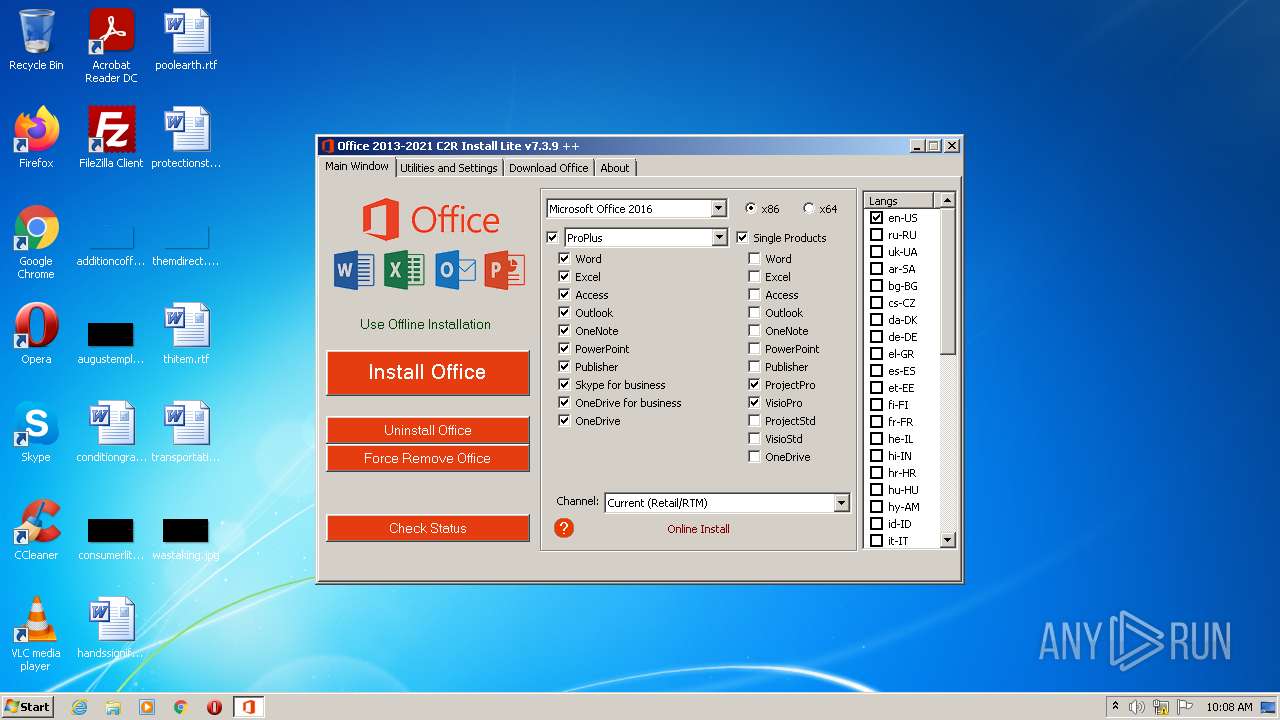
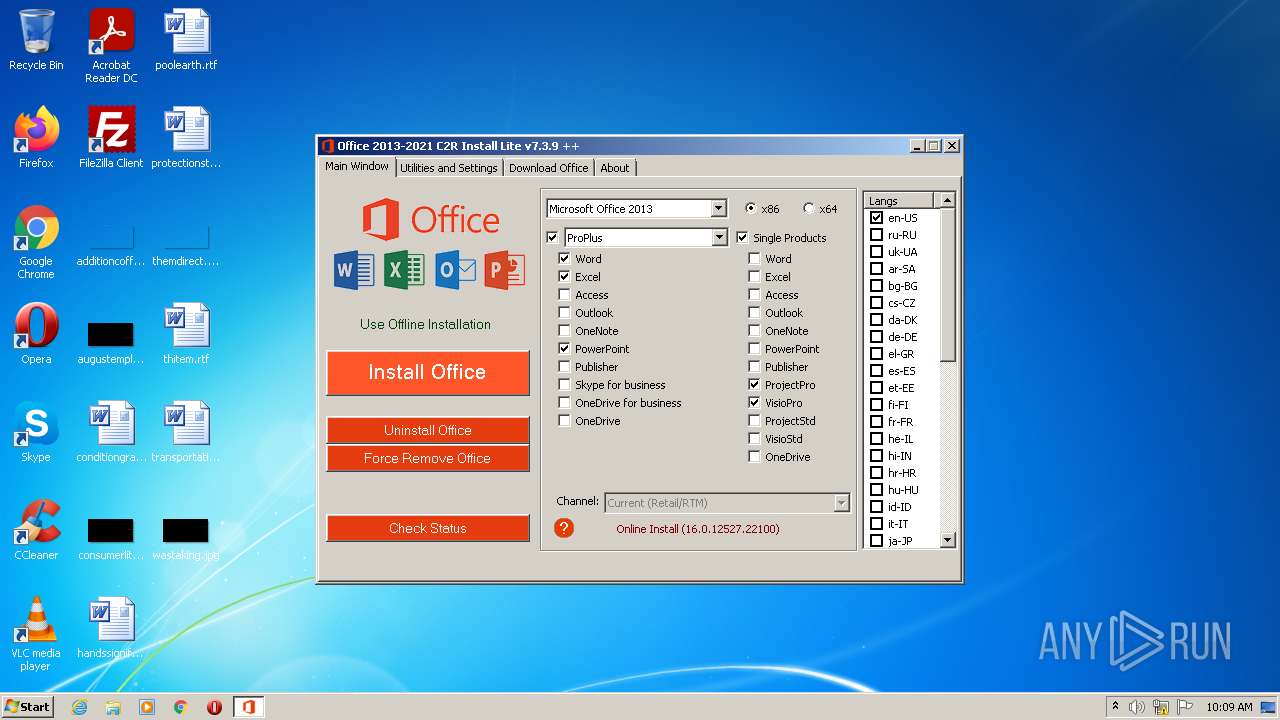
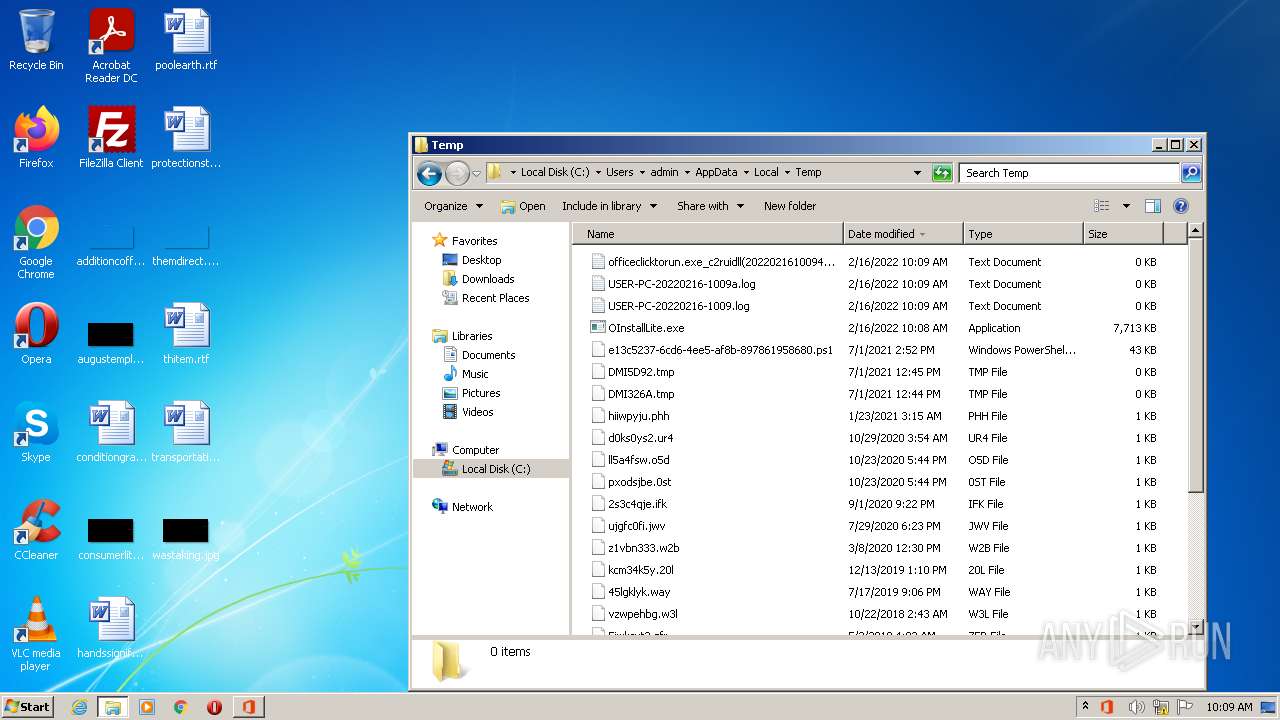
| File name: | OInstallLite.exe |
| Full analysis: | https://app.any.run/tasks/106acb6e-0e11-4f0b-bd5d-d6a2a8f062f0 |
| Verdict: | Malicious activity |
| Analysis date: | February 16, 2022, 10:08:34 |
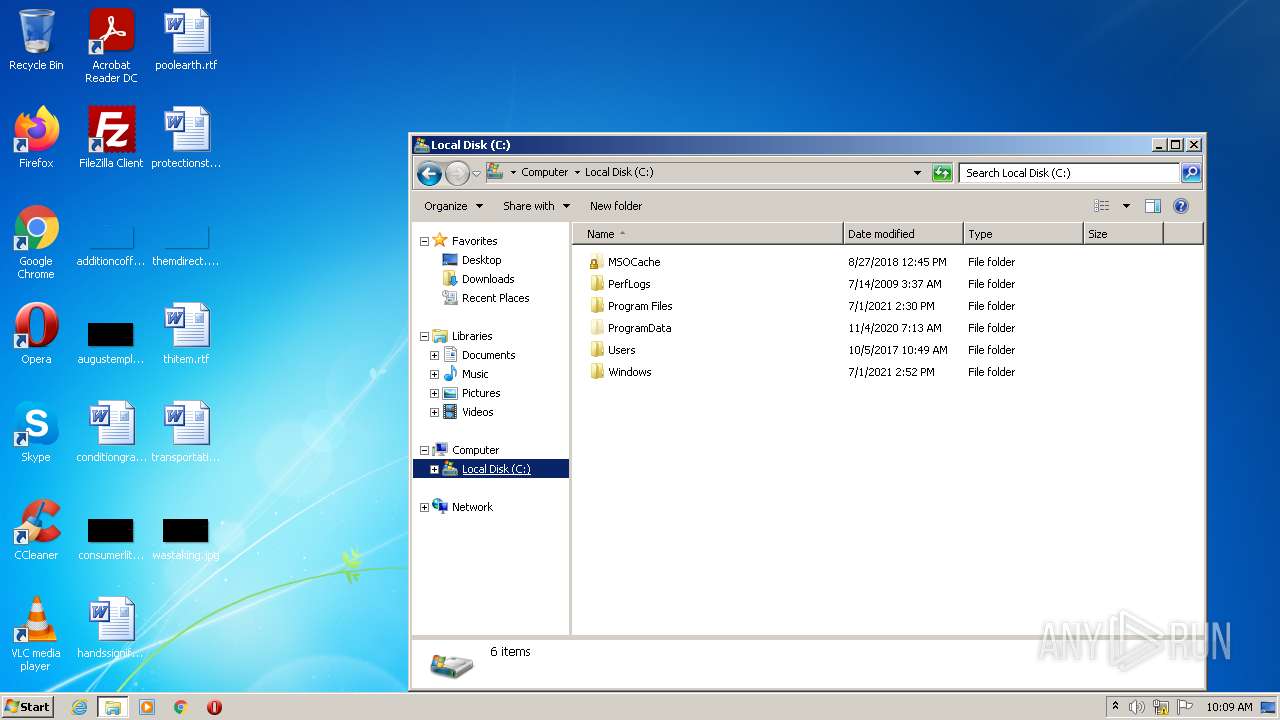
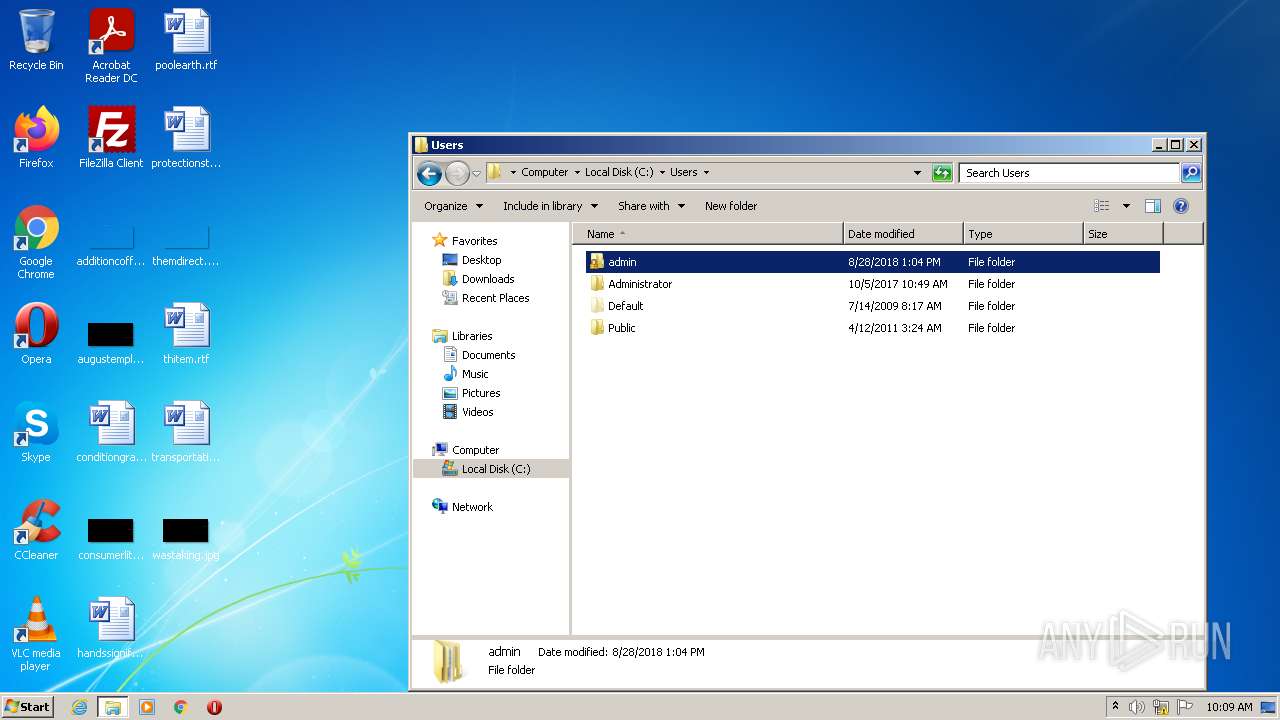
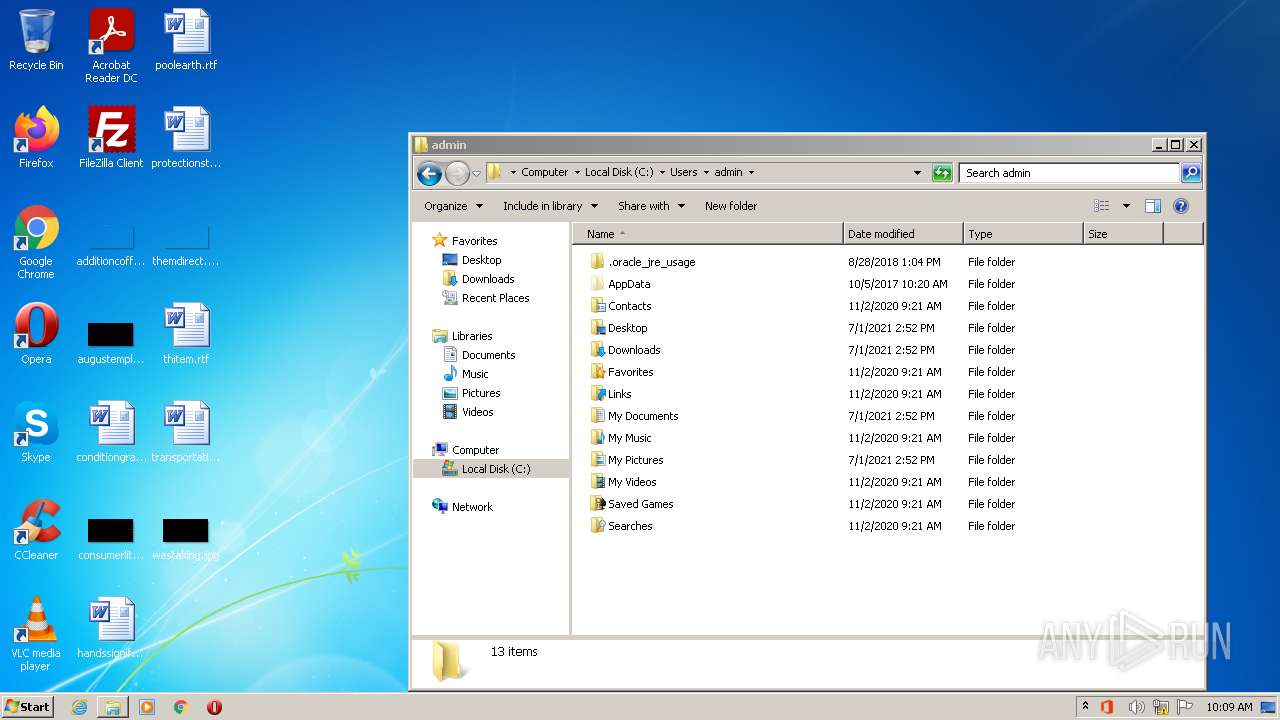
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | B70F0484C45C885DF6E0D13C5FE7151C |
| SHA1: | E81FCD272A0B240DF3F465F7580D677AB3FEC787 |
| SHA256: | 4A81E8451C0A16B9A133CFF53D5AA739F032AE4D40F867130A55A4F6399CA464 |
| SSDEEP: | 196608:2xrxV4J+9/UKA43Mu29Xm2LJZJTFTDxC7Q:mQoeX2EJRDMM |
MALICIOUS
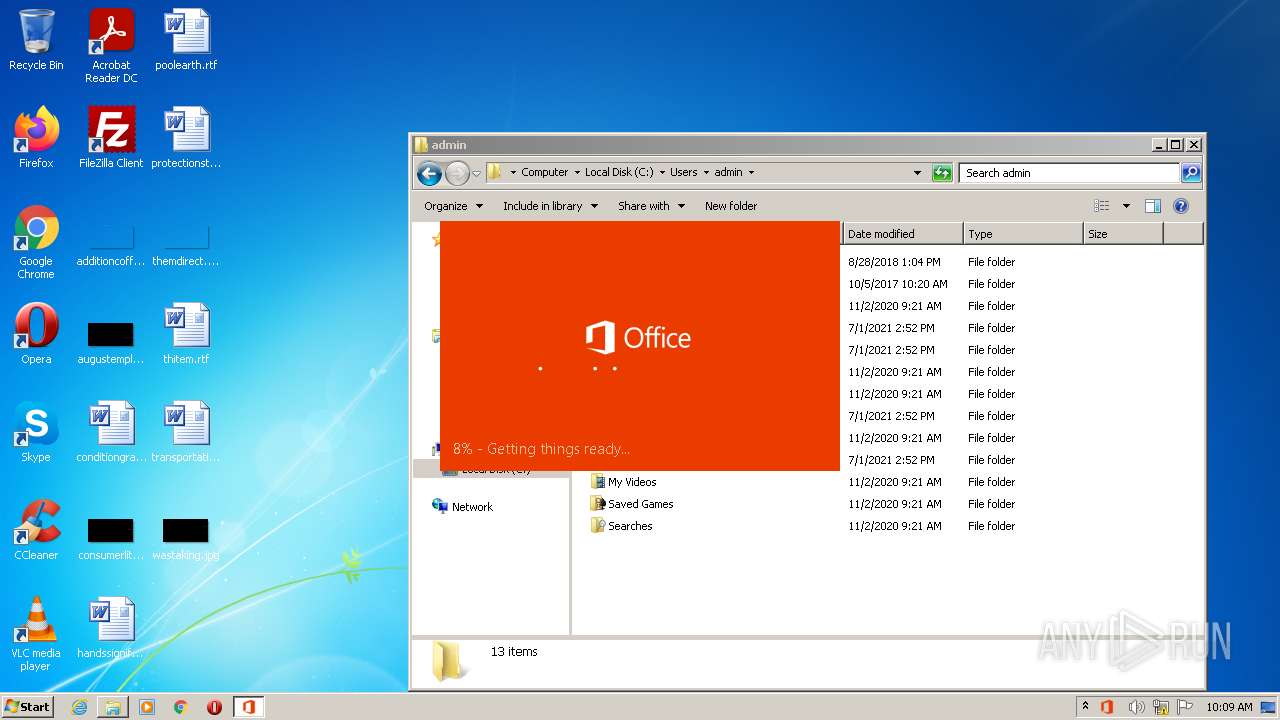
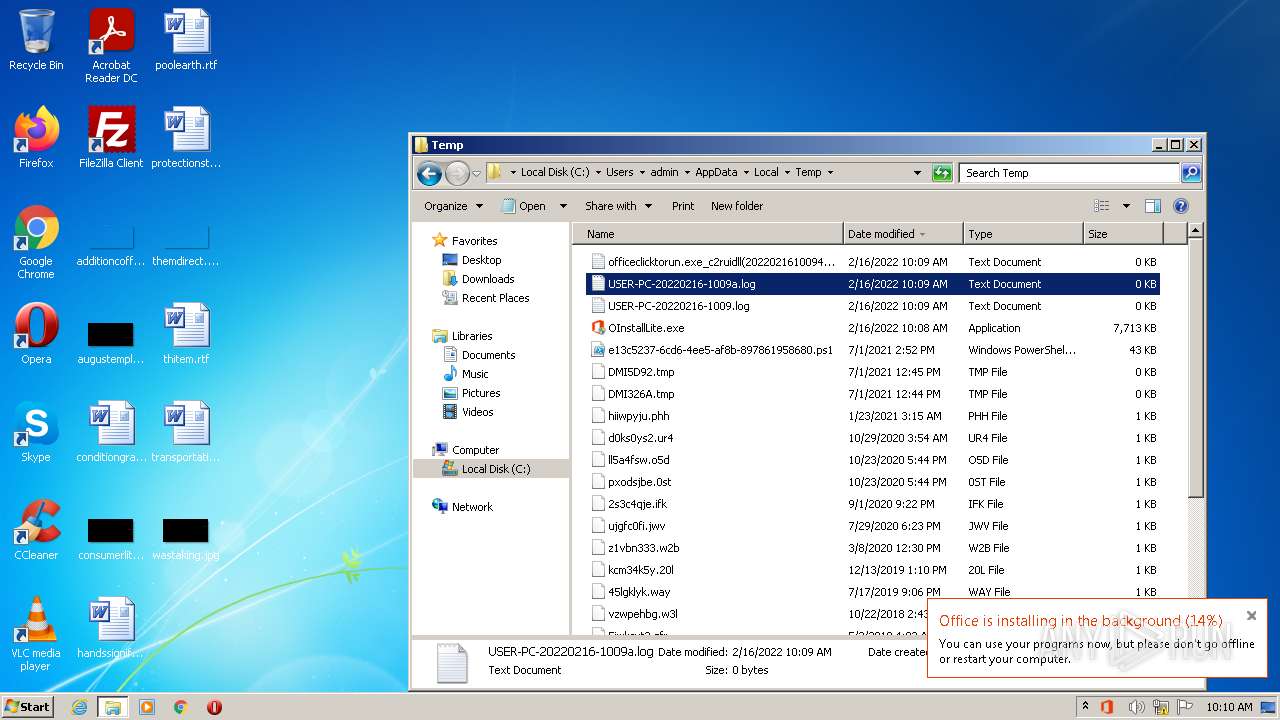
Drops executable file immediately after starts
- OInstallLite.exe (PID: 2244)
- files.dat (PID: 2736)
Application was dropped or rewritten from another process
- files.dat (PID: 2736)
- setup.exe (PID: 3388)
- OfficeClickToRun.exe (PID: 2124)
- OfficeClickToRun.exe (PID: 1044)
- perfboost.exe (PID: 3092)
- AppVShNotify.exe (PID: 3360)
Actions looks like stealing of personal data
- cmd.exe (PID: 712)
Loads dropped or rewritten executable
- OfficeClickToRun.exe (PID: 2124)
- OfficeClickToRun.exe (PID: 1044)
- perfboost.exe (PID: 3092)
- AppVShNotify.exe (PID: 3360)
SUSPICIOUS
Executable content was dropped or overwritten
- OInstallLite.exe (PID: 2244)
- files.dat (PID: 2736)
- setup.exe (PID: 3388)
- OfficeClickToRun.exe (PID: 2124)
Reads the computer name
- OInstallLite.exe (PID: 2244)
- powershell.exe (PID: 1424)
- powershell.exe (PID: 1612)
- setup.exe (PID: 3388)
- OfficeClickToRun.exe (PID: 1044)
- OfficeClickToRun.exe (PID: 2124)
- perfboost.exe (PID: 3092)
- AppVShNotify.exe (PID: 3360)
Drops a file that was compiled in debug mode
- OInstallLite.exe (PID: 2244)
- files.dat (PID: 2736)
- setup.exe (PID: 3388)
- OfficeClickToRun.exe (PID: 2124)
Starts application with an unusual extension
- cmd.exe (PID: 2812)
Executes PowerShell scripts
- OInstallLite.exe (PID: 2244)
Checks supported languages
- OInstallLite.exe (PID: 2244)
- cmd.exe (PID: 2812)
- files.dat (PID: 2736)
- powershell.exe (PID: 1424)
- powershell.exe (PID: 1612)
- setup.exe (PID: 3388)
- cmd.exe (PID: 712)
- OfficeClickToRun.exe (PID: 1044)
- OfficeClickToRun.exe (PID: 2124)
- perfboost.exe (PID: 3092)
- AppVShNotify.exe (PID: 3360)
Reads Environment values
- OInstallLite.exe (PID: 2244)
- powershell.exe (PID: 1424)
Starts CMD.EXE for commands execution
- OInstallLite.exe (PID: 2244)
Creates a directory in Program Files
- setup.exe (PID: 3388)
- OfficeClickToRun.exe (PID: 2124)
Creates files in the program directory
- setup.exe (PID: 3388)
- OfficeClickToRun.exe (PID: 2124)
Executed as Windows Service
- OfficeClickToRun.exe (PID: 2124)
Creates files in the Windows directory
- OfficeClickToRun.exe (PID: 2124)
- OfficeClickToRun.exe (PID: 1044)
Searches for installed software
- setup.exe (PID: 3388)
Removes files from Windows directory
- OfficeClickToRun.exe (PID: 2124)
Creates a software uninstall entry
- OfficeClickToRun.exe (PID: 2124)
Starts Internet Explorer
- MSOXMLED.EXE (PID: 1688)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2640)
- iexplore.exe (PID: 3948)
INFO
Checks Windows Trust Settings
- powershell.exe (PID: 1424)
- powershell.exe (PID: 1612)
- setup.exe (PID: 3388)
- OfficeClickToRun.exe (PID: 2124)
- iexplore.exe (PID: 848)
Checks supported languages
- expand.exe (PID: 2368)
- explorer.exe (PID: 2680)
- NOTEPAD.EXE (PID: 2968)
- MSOXMLED.EXE (PID: 1688)
- NOTEPAD.EXE (PID: 1592)
- iexplore.exe (PID: 848)
- iexplore.exe (PID: 2640)
- iexplore.exe (PID: 3948)
Reads Microsoft Office registry keys
- setup.exe (PID: 3388)
- OfficeClickToRun.exe (PID: 1044)
- perfboost.exe (PID: 3092)
- OfficeClickToRun.exe (PID: 2124)
Dropped object may contain Bitcoin addresses
- expand.exe (PID: 2368)
- OfficeClickToRun.exe (PID: 2124)
Reads settings of System Certificates
- setup.exe (PID: 3388)
- OfficeClickToRun.exe (PID: 2124)
- iexplore.exe (PID: 848)
Manual execution by user
- explorer.exe (PID: 2680)
- NOTEPAD.EXE (PID: 2968)
- NOTEPAD.EXE (PID: 1592)
- MSOXMLED.EXE (PID: 1688)
- perfboost.exe (PID: 3092)
Reads the computer name
- explorer.exe (PID: 2680)
- MSOXMLED.EXE (PID: 1688)
- iexplore.exe (PID: 848)
- iexplore.exe (PID: 2640)
- iexplore.exe (PID: 3948)
Application launched itself
- iexplore.exe (PID: 848)
Changes internet zones settings
- iexplore.exe (PID: 848)
Reads internet explorer settings
- iexplore.exe (PID: 2640)
- iexplore.exe (PID: 3948)
Reads the date of Windows installation
- iexplore.exe (PID: 848)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (76) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.6) |
| .exe | | | Generic Win/DOS Executable (5.6) |
| .exe | | | DOS Executable Generic (5.6) |
EXIF
EXE
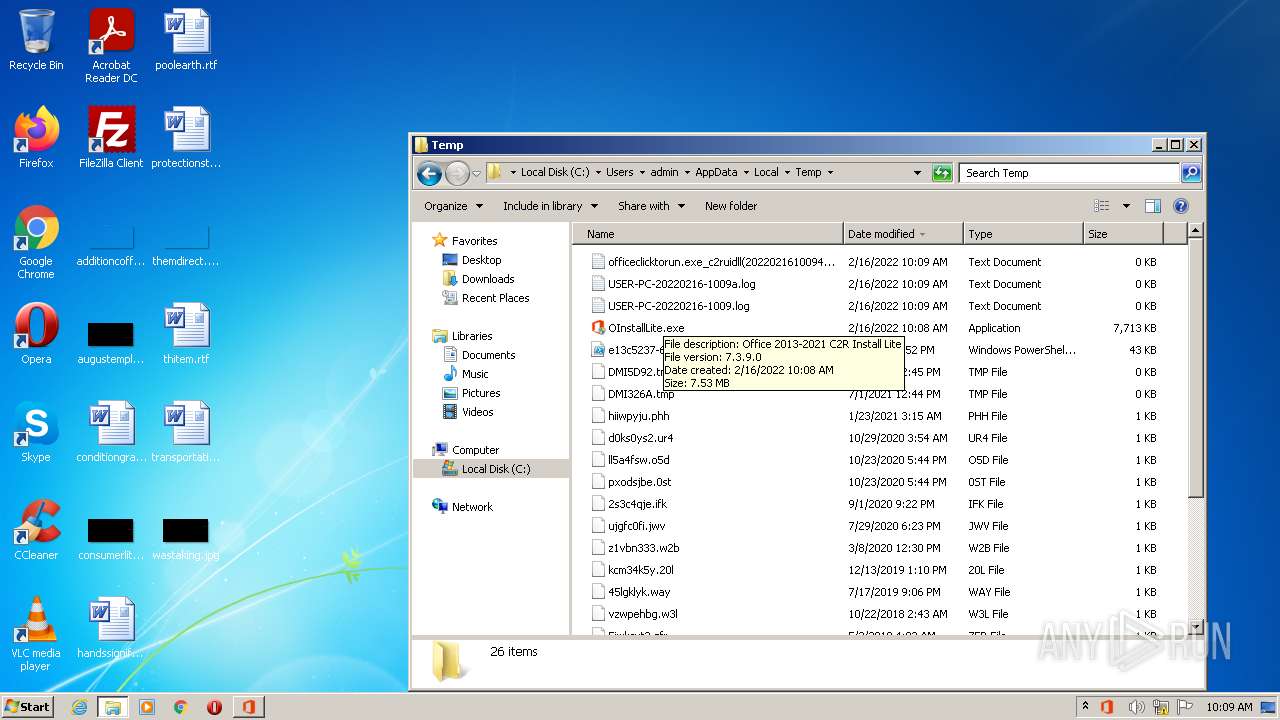
| FileDescription: | Office 2013-2021 C2R Install Lite |
|---|---|
| ProductName: | Office 2013-2021 C2R Install Lite |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Unknown |
| FileOS: | Unknown (0) |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 7.3.9.0 |
| FileVersionNumber: | 7.3.9.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1208020 |
| UninitializedDataSize: | 11104256 |
| InitializedDataSize: | 90112 |
| CodeSize: | 7802880 |
| LinkerVersion: | 2.5 |
| PEType: | PE32 |
| TimeStamp: | 2022:01:15 10:22:36+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Jan-2022 09:22:36 |
| Detected languages: |
|
| ProductName: | Office 2013-2021 C2R Install Lite |
| FileDescription: | Office 2013-2021 C2R Install Lite |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 15-Jan-2022 09:22:36 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00A97000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00A98000 | 0x00771000 | 0x00770200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.93935 |
.rsrc | 0x01209000 | 0x00016000 | 0x00015200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.97027 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.94291 | 1117 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 1.96082 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 2.20562 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 2.87138 | 1128 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
GDI32.DLL |
ICMP.DLL |
IMAGEHLP.DLL |
IPHLPAPI.DLL |
KERNEL32.DLL |
MSI.DLL |
MSVCRT.dll |
NETAPI32.DLL |
Total processes
69
Monitored processes
20
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
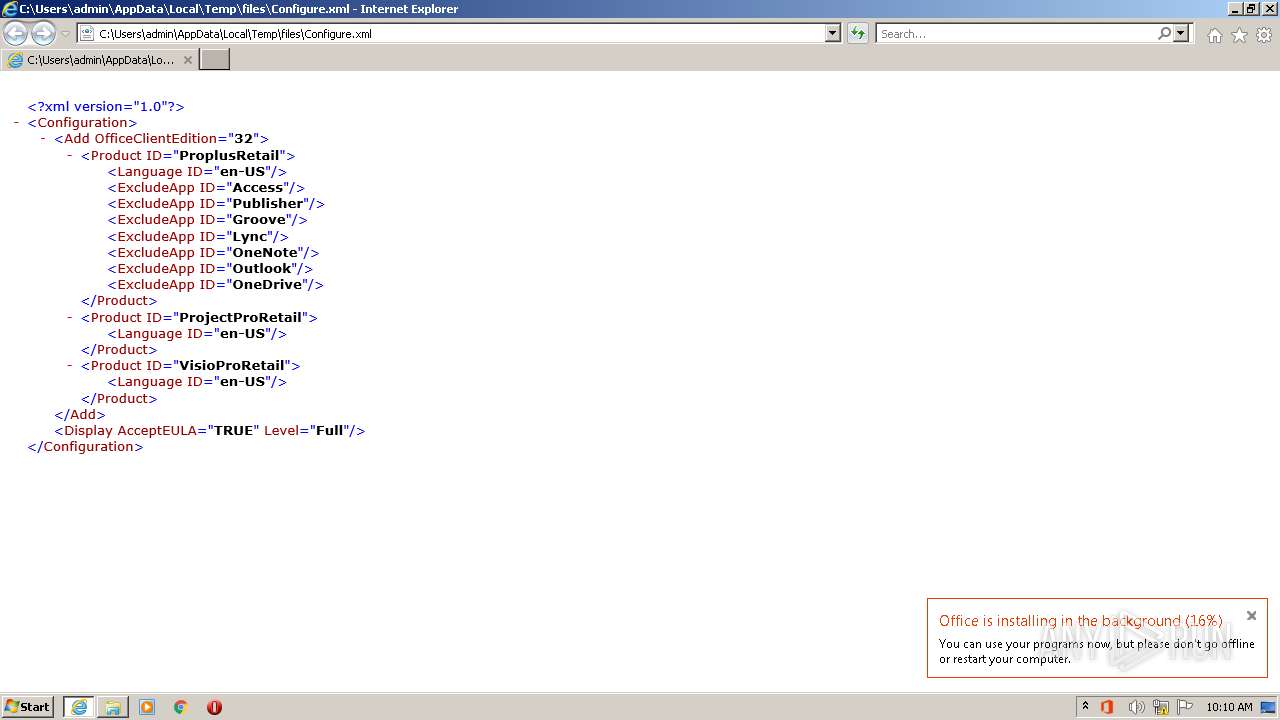
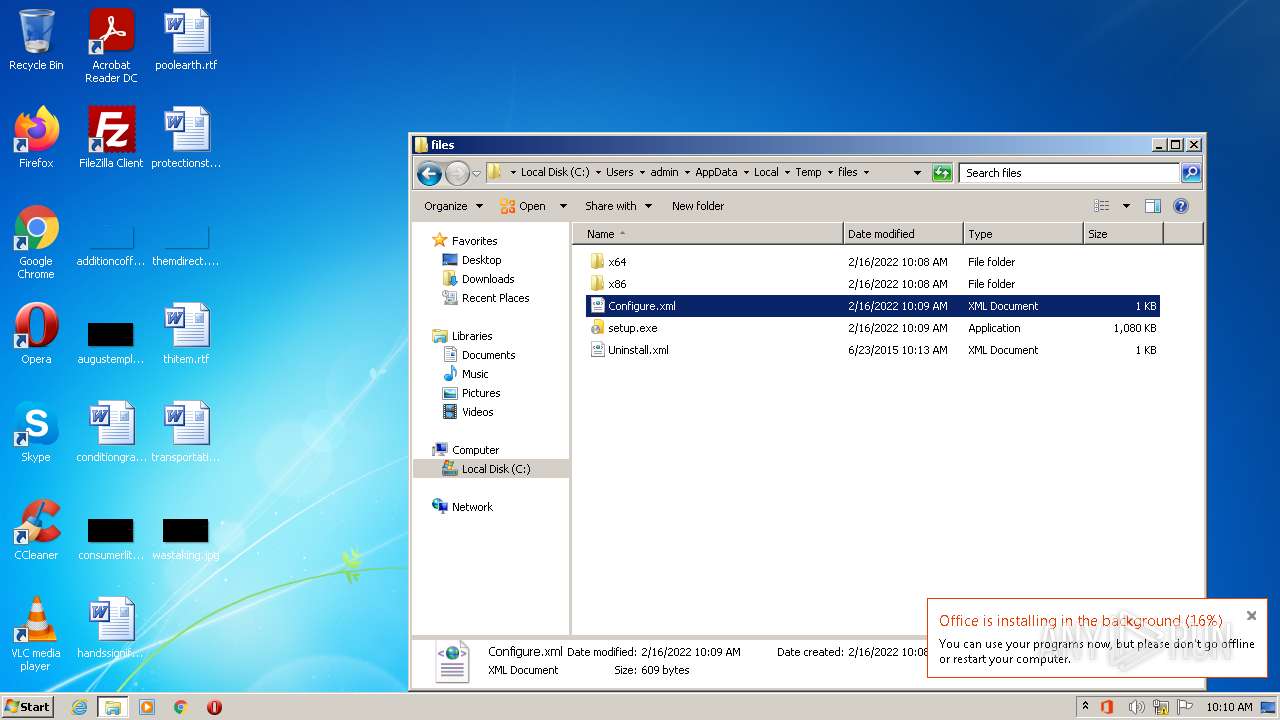
| 712 | "C:\Windows\System32\cmd.exe" /D /c C:\Users\admin\AppData\Local\Temp\files\Setup.exe /configure Configure.xml | C:\Windows\System32\cmd.exe | OInstallLite.exe | ||||||||||||
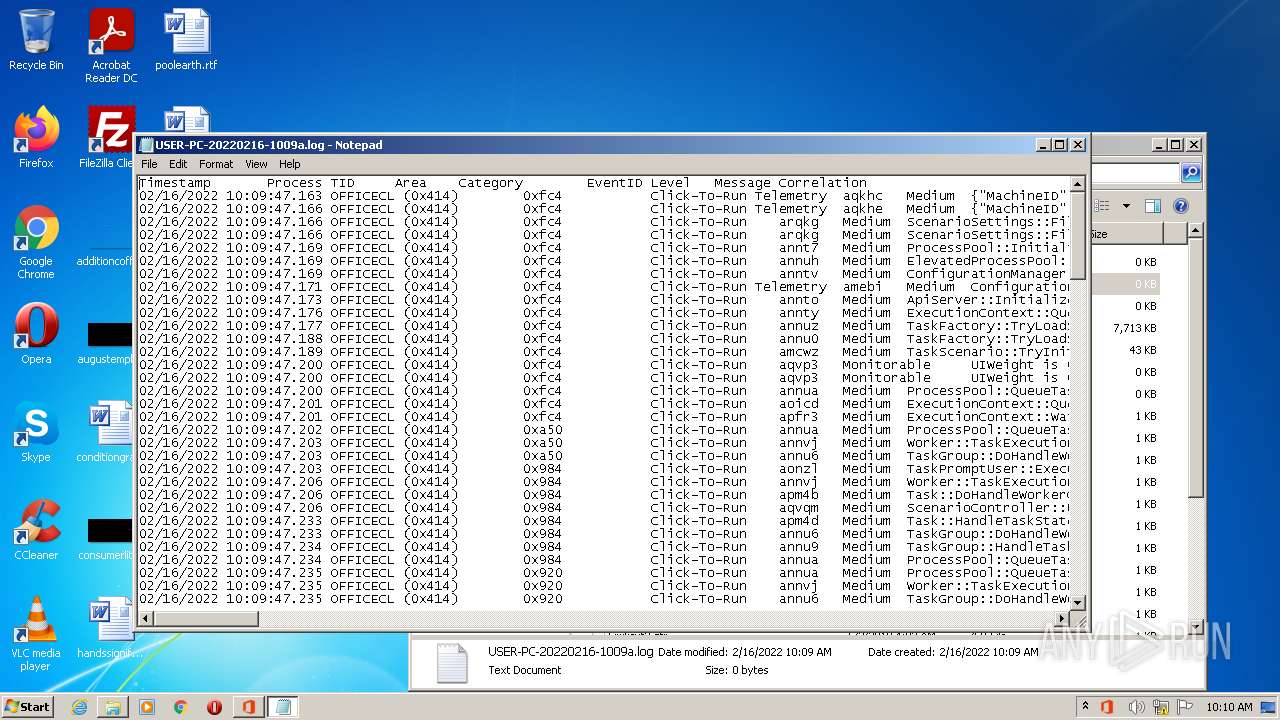
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 848 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | MSOXMLED.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1044 | OfficeClickToRun.exe scenario=unknown scenariosubtype=odtCDN acceptalleulas="True" cdnbaseurl="http://officecdn.microsoft.com/pr/39168D7E-077B-48E7-872C-B232C3E72675" productreleaseid="none" culture="en-us" baseurl="http://officecdn.microsoft.com/pr/39168D7E-077B-48E7-872C-B232C3E72675" lcid="1033" platform="x86" mediatype="CDN" updatesenabled="True" autoUpgrade="True" proplusretail.excludedapps="access,publisher,groove,lync,onenote,outlook" version="15.0.5423.1000" productstoadd="ProplusRetail_en-us_x-none|ProjectProRetail_en-us_x-none|VisioProRetail_en-us_x-none" trackedduration=34141 | C:\Program Files\Microsoft Office 15\ClientX86\OfficeClickToRun.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Office Click-to-Run Exit code: 0 Version: 15.0.5337.1000 Modules
| |||||||||||||||
| 1424 | "powershell" -command "& { (New-Object Net.WebClient).DownloadFile('http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32.cab', 'C:\Users\admin\AppData\Local\Temp\over660481\v32.cab') }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | OInstallLite.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
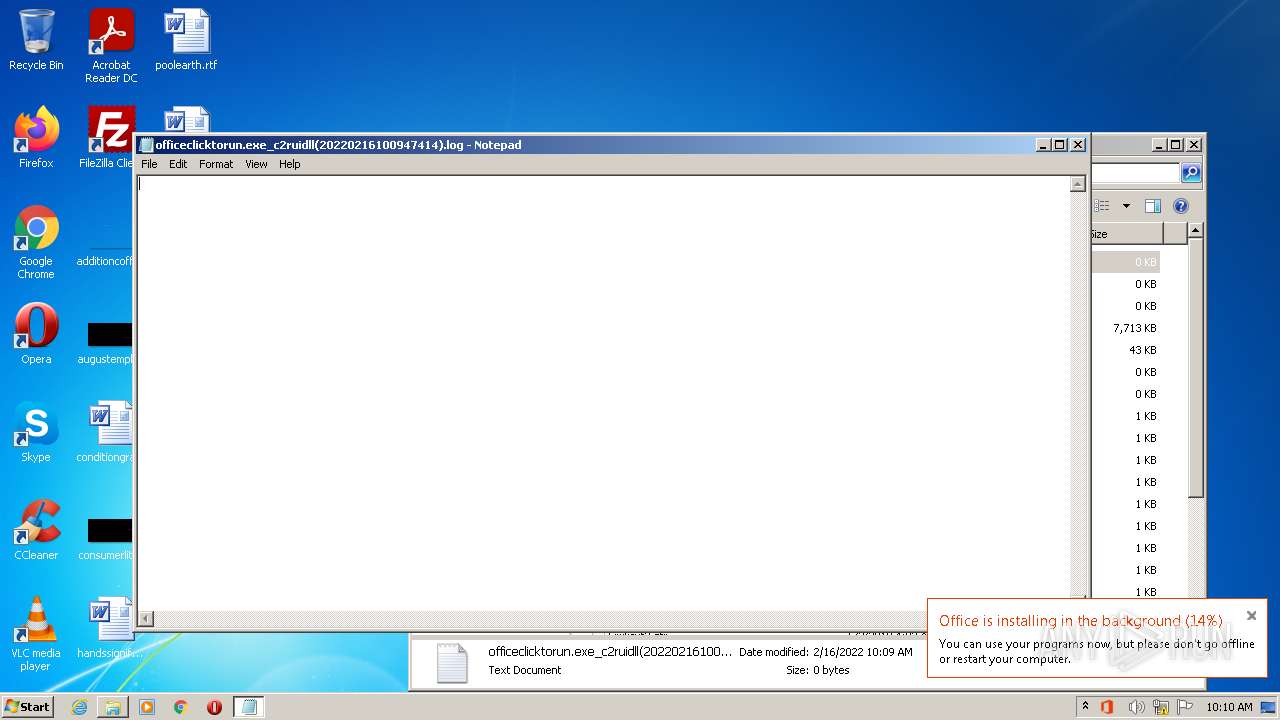
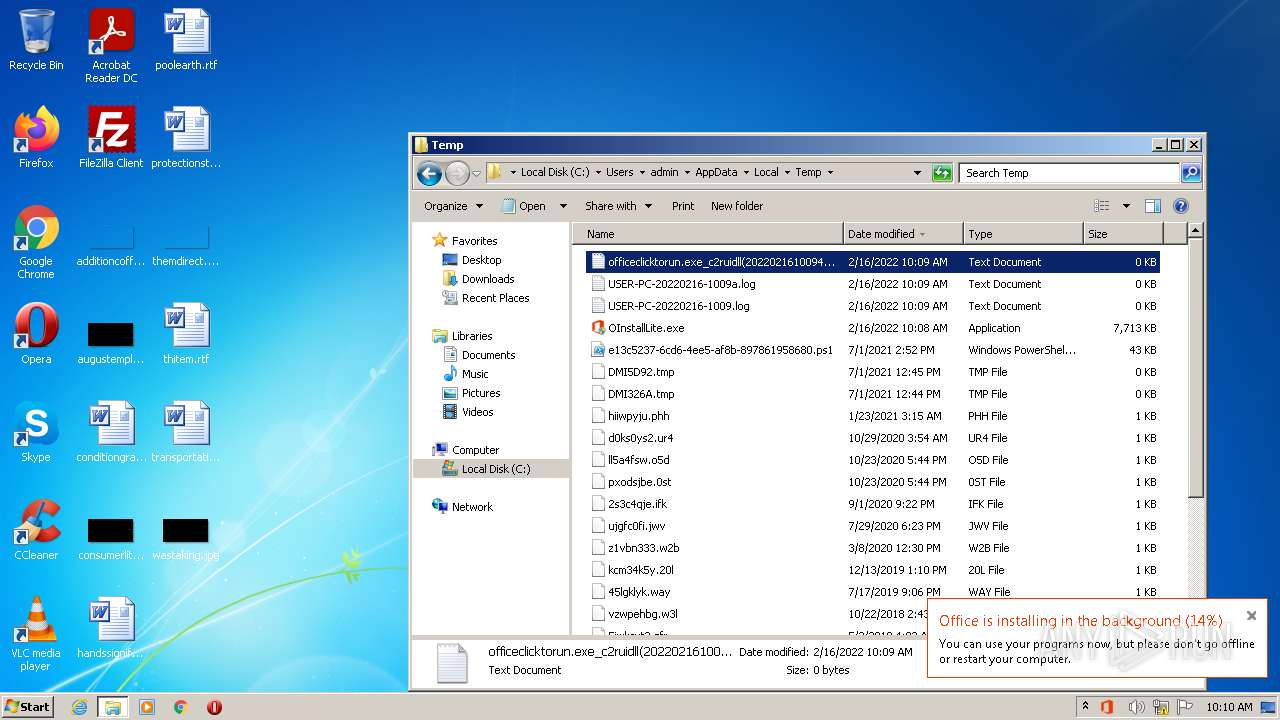
| 1592 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\officeclicktorun.exe_c2ruidll(20220216100947414).log | C:\Windows\system32\NOTEPAD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1612 | "powershell" -command "& { Get-Content C:\Users\admin\AppData\Local\Temp\over660481\VersionDescriptor.xml | Set-Content -Encoding ASCII v32.txt } | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | OInstallLite.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1688 | "C:\Program Files\Common Files\Microsoft Shared\OFFICE14\MSOXMLED.EXE" /verb open "C:\Users\admin\AppData\Local\Temp\files\Configure.xml" | C:\Program Files\Common Files\Microsoft Shared\OFFICE14\MSOXMLED.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: XML Editor Exit code: 0 Version: 14.0.4750.1000 Modules
| |||||||||||||||
| 1828 | "C:\Users\admin\AppData\Local\Temp\OInstallLite.exe" | C:\Users\admin\AppData\Local\Temp\OInstallLite.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: Office 2013-2021 C2R Install Lite Exit code: 3221226540 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Microsoft Office 15\ClientX86\OfficeClickToRun.exe" /service | C:\Program Files\Microsoft Office 15\ClientX86\OfficeClickToRun.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Office Click-to-Run Exit code: 0 Version: 15.0.5337.1000 Modules
| |||||||||||||||
| 2244 | "C:\Users\admin\AppData\Local\Temp\OInstallLite.exe" | C:\Users\admin\AppData\Local\Temp\OInstallLite.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: Office 2013-2021 C2R Install Lite Exit code: 0 Modules
| |||||||||||||||
Total events
29 356
Read events
28 334
Write events
964
Delete events
58
Modification events
| (PID) Process: | (1424) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1424) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1424) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1424) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (1424) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1424) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1424) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1424) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1424) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1424) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
Executable files
171
Suspicious files
132
Text files
93
Unknown types
80
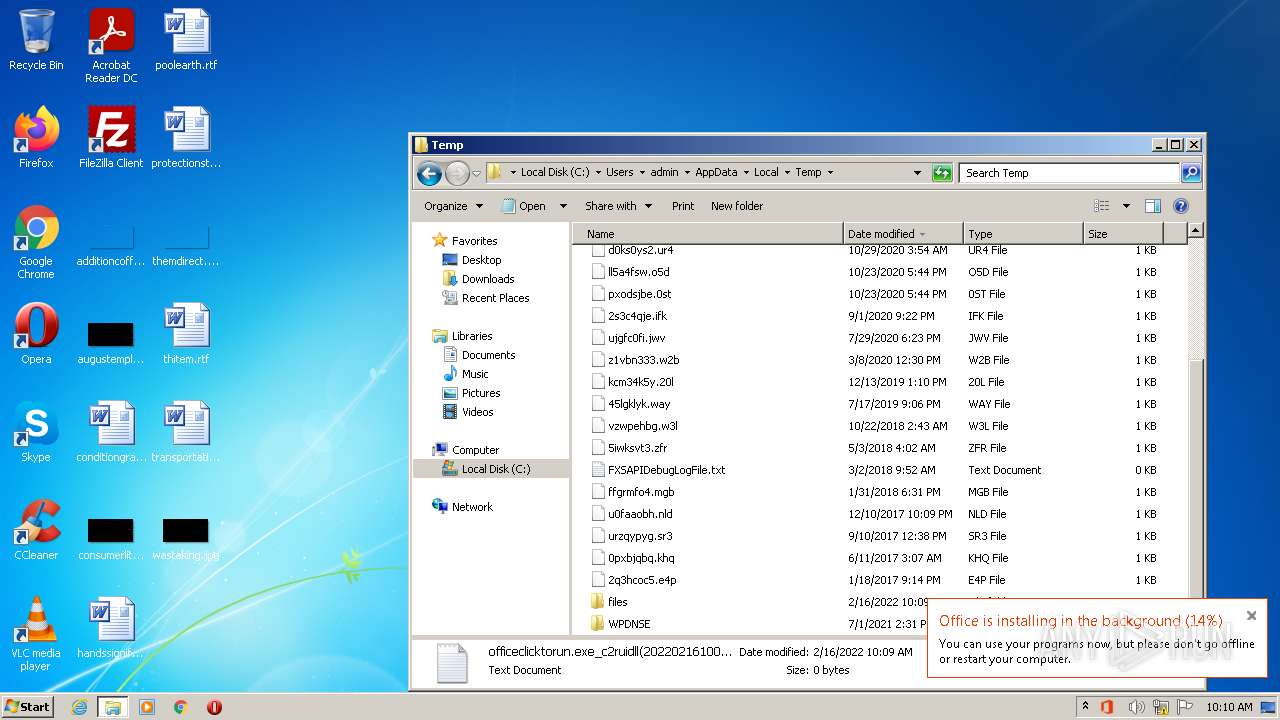
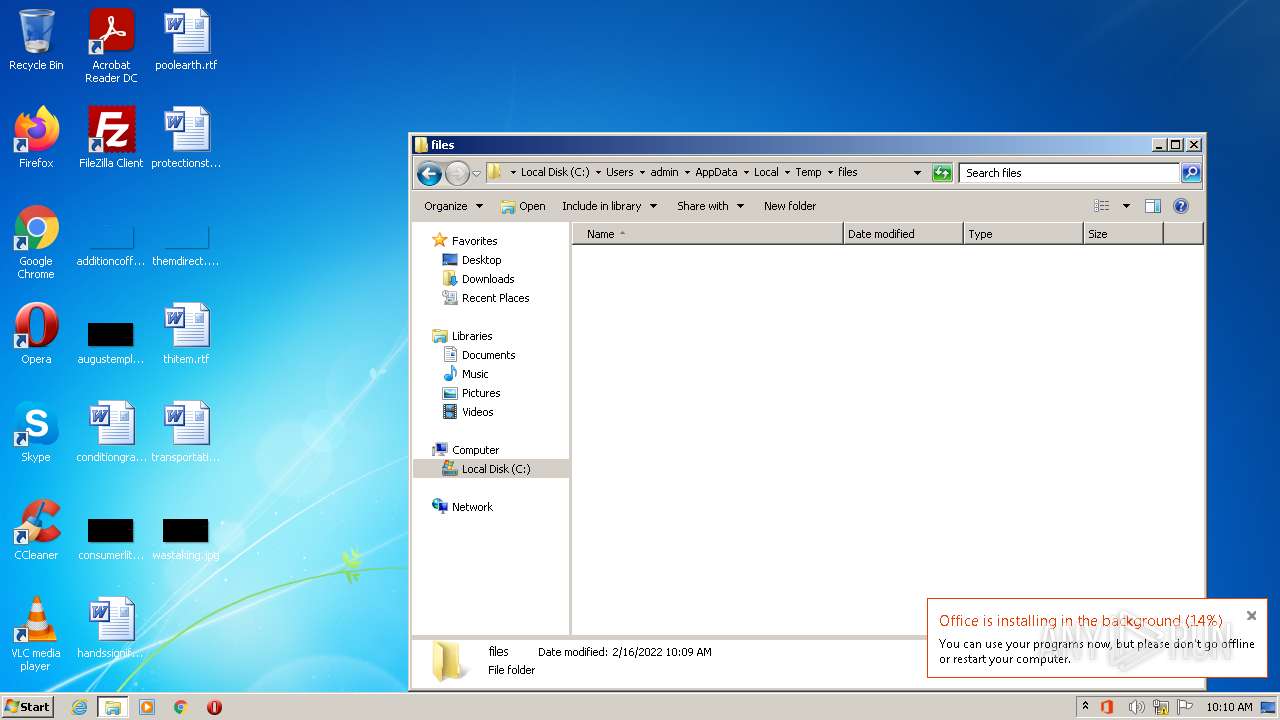
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2368 | expand.exe | C:\Users\admin\AppData\Local\Temp\over660481\VersionDescriptor.xml | xml | |
MD5:— | SHA256:— | |||
| 2368 | expand.exe | C:\Windows\Logs\DPX\setupact.log | text | |
MD5:— | SHA256:— | |||
| 3388 | setup.exe | C:\Users\admin\AppData\Local\Temp\OfficeC2RB946F05D-A783-43F2-8F25-8DFC0FDB06B7\v32.cab | compressed | |
MD5:— | SHA256:— | |||
| 1424 | powershell.exe | C:\Users\admin\AppData\Local\Temp\over660481\v32.cab | compressed | |
MD5:— | SHA256:— | |||
| 2368 | expand.exe | C:\Users\admin\AppData\Local\Temp\over660481\$dpx$.tmp\5efec63a82659e46933d491b07481a8b.tmp | xml | |
MD5:— | SHA256:— | |||
| 1612 | powershell.exe | C:\Users\admin\AppData\Local\Temp\over660481\v32.txt | xml | |
MD5:— | SHA256:— | |||
| 1424 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ehlbyg1x.zca.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2736 | files.dat | C:\Users\admin\AppData\Local\Temp\files\x64\msvcr100.dll | executable | |
MD5:DF3CA8D16BDED6A54977B30E66864D33 | SHA256:1D1A1AE540BA132F998D60D3622F0297B6E86AE399332C3B47462D7C0F560A36 | |||
| 1424 | powershell.exe | C:\Users\admin\AppData\Local\Temp\j2creufv.15i.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1424 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1 364
TCP/UDP connections
37
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1424 | powershell.exe | GET | 301 | 184.87.212.60:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32.cab | US | — | — | whitelisted |
3388 | setup.exe | GET | 301 | 184.30.24.56:80 | http://officecdn.microsoft.com/pr/39168D7E-077B-48E7-872C-B232C3E72675/Office/Data/v32.cab | US | — | — | whitelisted |
3388 | setup.exe | GET | — | 2.16.186.90:80 | http://officecdn.microsoft.com.edgesuite.net/pr/39168D7E-077B-48E7-872C-B232C3E72675/Office/Data/v32.cab | unknown | — | — | whitelisted |
3388 | setup.exe | GET | 301 | 184.30.24.56:80 | http://officecdn.microsoft.com/pr/39168D7E-077B-48E7-872C-B232C3E72675/Office/Data/v32.cab | US | — | — | whitelisted |
3388 | setup.exe | GET | 301 | 184.30.24.56:80 | http://officecdn.microsoft.com/pr/39168D7E-077B-48E7-872C-B232C3E72675/Office/Data/15.0.5423.1000/i321033.cab | US | — | — | whitelisted |
3388 | setup.exe | GET | — | 2.16.186.90:80 | http://officecdn.microsoft.com.edgesuite.net/pr/39168D7E-077B-48E7-872C-B232C3E72675/Office/Data/15.0.5423.1000/i321033.cab | unknown | — | — | whitelisted |
3388 | setup.exe | GET | 301 | 184.30.24.56:80 | http://officecdn.microsoft.com/pr/39168D7E-077B-48E7-872C-B232C3E72675/Office/Data/15.0.5423.1000/i321033.cab | US | — | — | whitelisted |
3388 | setup.exe | GET | — | 2.16.186.90:80 | http://officecdn.microsoft.com.edgesuite.net/pr/39168D7E-077B-48E7-872C-B232C3E72675/Office/Data/15.0.5423.1000/i321033.cab | unknown | — | — | whitelisted |
3388 | setup.exe | GET | — | 2.16.186.90:80 | http://officecdn.microsoft.com.edgesuite.net/pr/39168D7E-077B-48E7-872C-B232C3E72675/Office/Data/15.0.5423.1000/i321033.cab | unknown | — | — | whitelisted |
3388 | setup.exe | GET | 301 | 184.30.24.56:80 | http://officecdn.microsoft.com/pr/39168D7E-077B-48E7-872C-B232C3E72675/Office/Data/15.0.5423.1000/i321033.cab | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1424 | powershell.exe | 184.87.212.60:80 | officecdn.microsoft.com | Bharti Airtel Ltd., Telemedia Services | US | suspicious |
1424 | powershell.exe | 92.123.195.121:80 | officecdn.microsoft.com.edgesuite.net | Akamai International B.V. | — | suspicious |
3388 | setup.exe | 184.30.24.56:80 | officecdn.microsoft.com | GTT Communications Inc. | US | unknown |
3388 | setup.exe | 2.16.186.90:80 | officecdn.microsoft.com.edgesuite.net | Akamai International B.V. | — | whitelisted |
3388 | setup.exe | 2.16.186.81:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
3388 | setup.exe | 2.18.233.62:80 | www.microsoft.com | Akamai International B.V. | — | whitelisted |
3388 | setup.exe | 178.18.231.171:80 | crl.microsoft.com | Peering Ltd | RU | suspicious |
2124 | OfficeClickToRun.exe | 2.16.186.90:80 | officecdn.microsoft.com.edgesuite.net | Akamai International B.V. | — | whitelisted |
2124 | OfficeClickToRun.exe | 104.84.56.60:80 | officecdn.microsoft.com | Vodafone NZ Ltd. | US | unknown |
2124 | OfficeClickToRun.exe | 2.18.233.62:80 | www.microsoft.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
officecdn.microsoft.com |
| whitelisted |
officecdn.microsoft.com.edgesuite.net |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |