| File name: | MrsMajor 3.0.exe |
| Full analysis: | https://app.any.run/tasks/de120a4e-b6a5-43b4-8a58-5990dac994a2 |
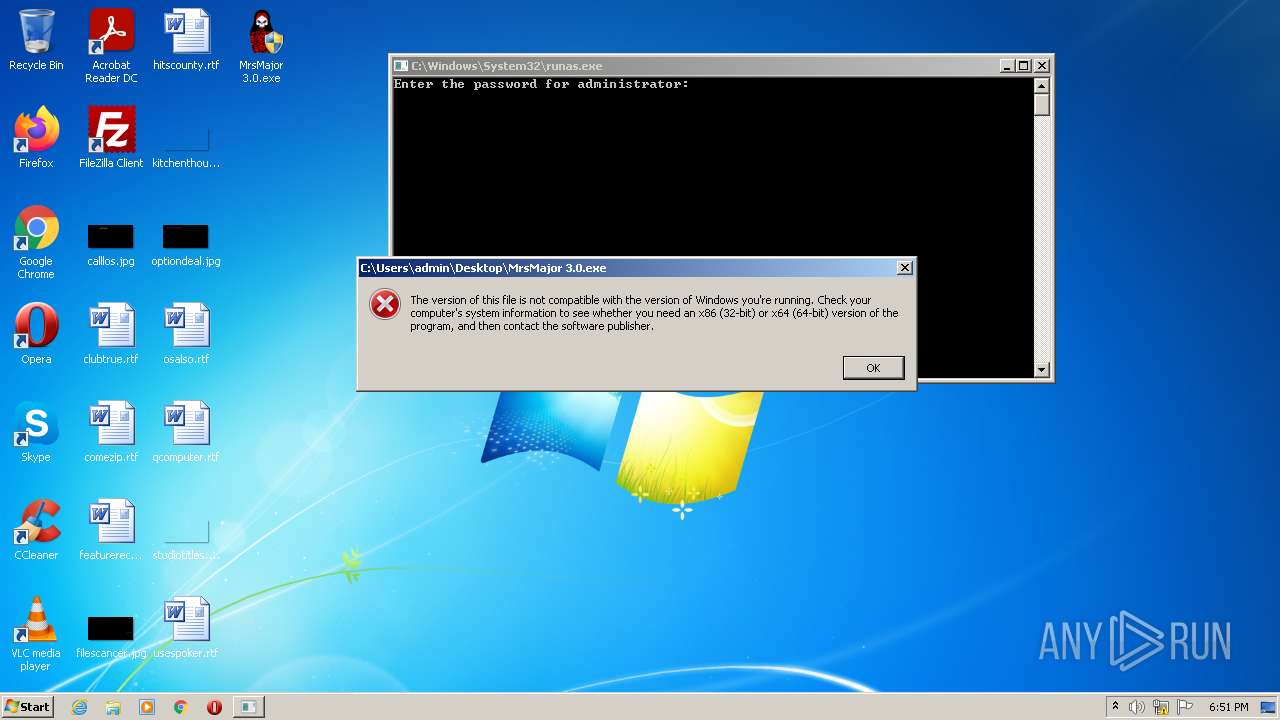
| Verdict: | Malicious activity |
| Analysis date: | January 31, 2022, 18:51:20 |
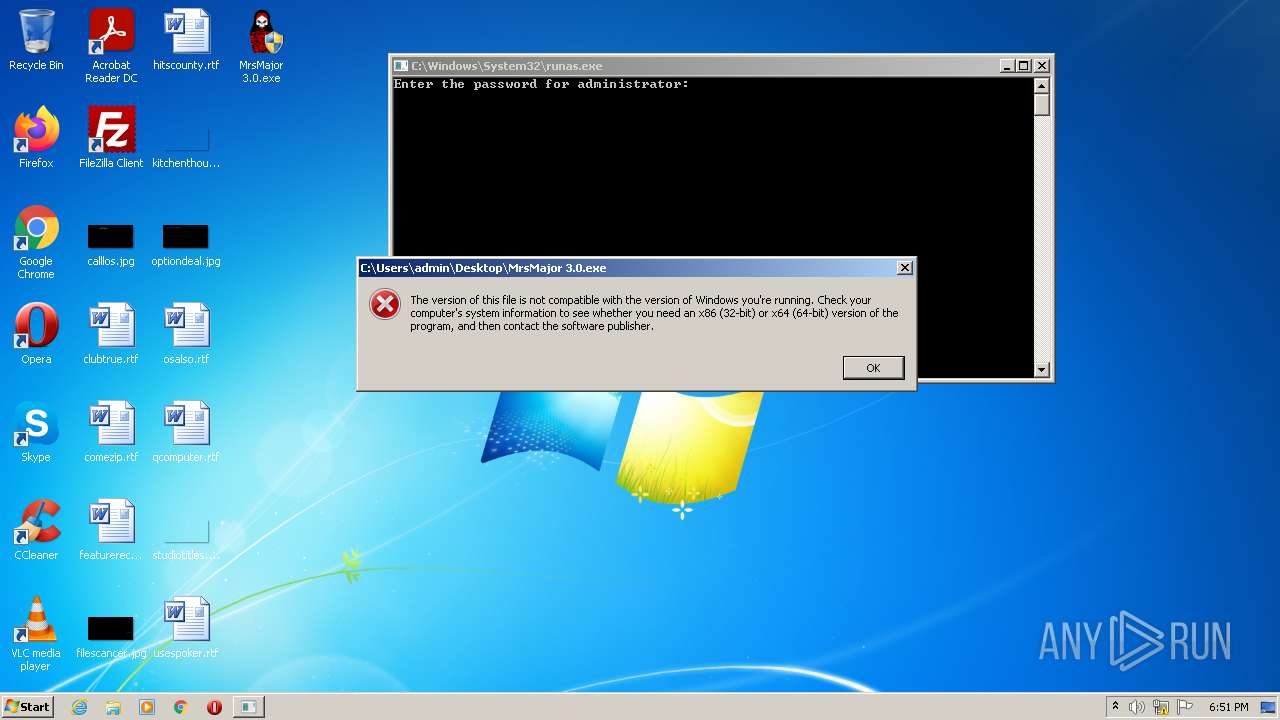
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | 35A27D088CD5BE278629FAE37D464182 |
| SHA1: | D5A291FADEAD1F2A0CF35082012FE6F4BF22A3AB |
| SHA256: | 4A75F2DB1DBD3C1218BB9994B7E1C690C4EDD4E0C1A675DE8D2A127611173E69 |
| SSDEEP: | 6144:Th3idhONY259BH1DzJ5PzVNtGgc+F9TBd096cTKAsLEbqqbd+VWM8AHiKn9SlXNA:Th3iXPw9Tc6kVXMHHLEf8l7 |
MALICIOUS
Loads the Task Scheduler COM API
- CCleaner.exe (PID: 1552)
- CCleaner.exe (PID: 1588)
Drops executable file immediately after starts
- CCleaner.exe (PID: 1588)
Loads dropped or rewritten executable
- CCleaner.exe (PID: 1588)
SUSPICIOUS
Checks supported languages
- CCleaner.exe (PID: 1552)
- CCleaner.exe (PID: 1588)
Reads the computer name
- CCleaner.exe (PID: 1552)
- CCleaner.exe (PID: 1588)
Reads Environment values
- CCleaner.exe (PID: 1552)
- CCleaner.exe (PID: 1588)
Executed via Task Scheduler
- CCleaner.exe (PID: 1588)
Creates files in the program directory
- CCleaner.exe (PID: 1588)
Executable content was dropped or overwritten
- CCleaner.exe (PID: 1588)
Drops a file that was compiled in debug mode
- CCleaner.exe (PID: 1588)
Reads CPU info
- CCleaner.exe (PID: 1588)
Reads internet explorer settings
- CCleaner.exe (PID: 1588)
Reads the date of Windows installation
- CCleaner.exe (PID: 1588)
Creates files in the user directory
- CCleaner.exe (PID: 1588)
Reads Microsoft Outlook installation path
- CCleaner.exe (PID: 1588)
Searches for installed software
- CCleaner.exe (PID: 1588)
INFO
Checks supported languages
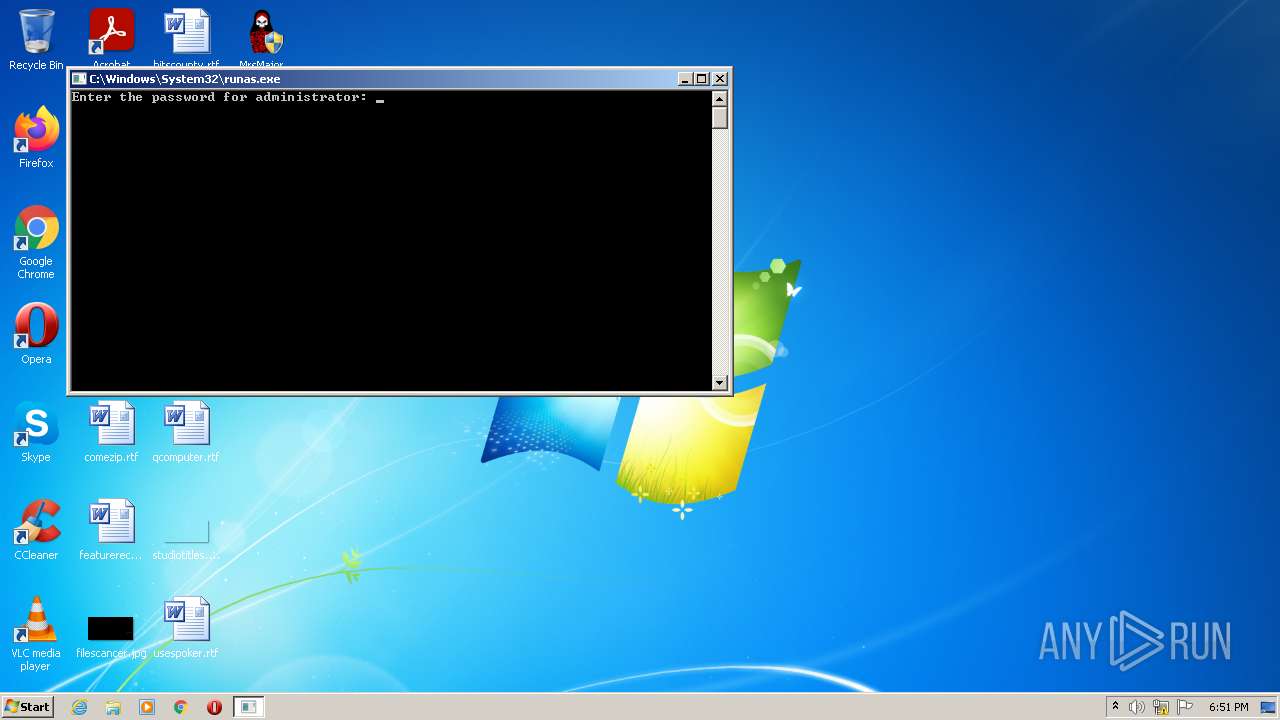
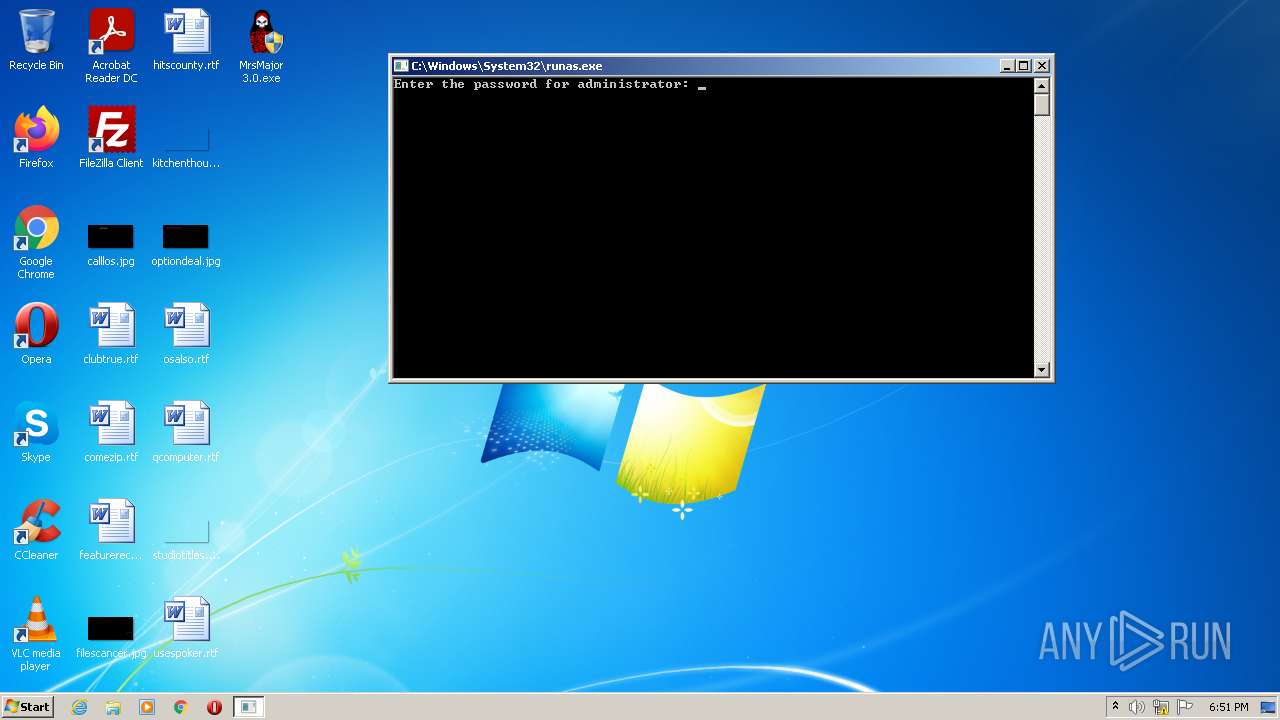
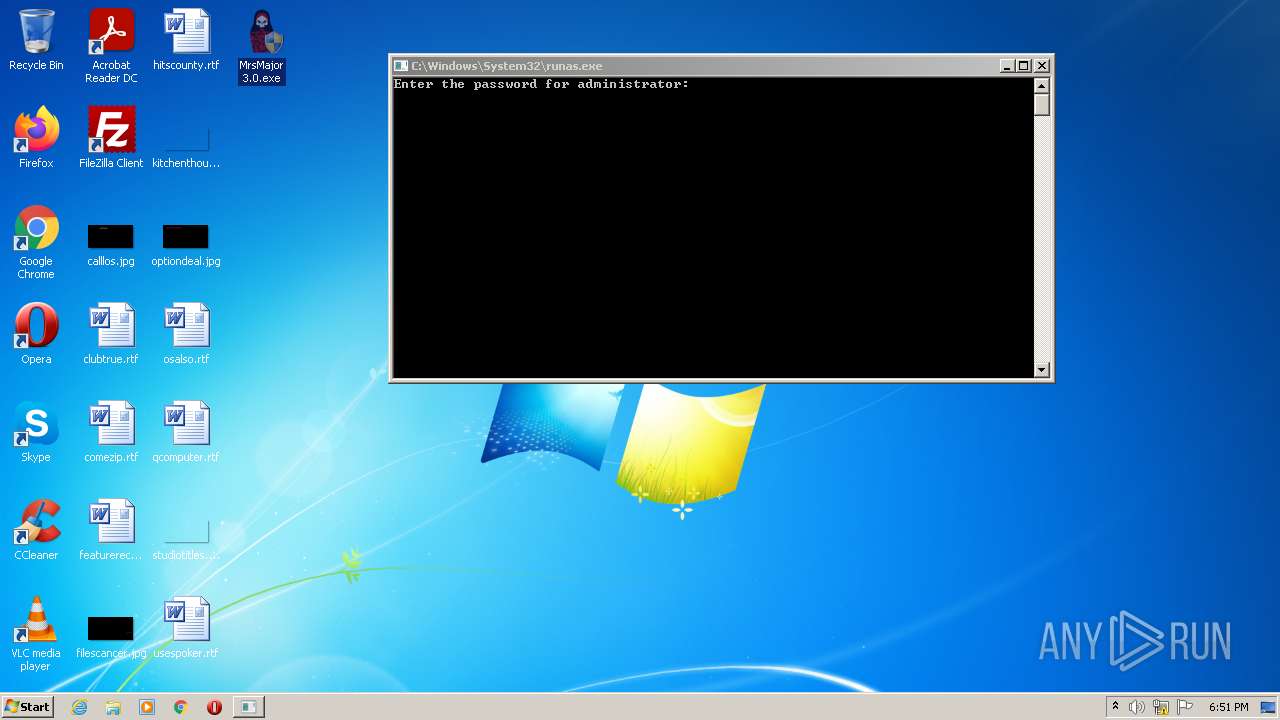
- runas.exe (PID: 3820)
Reads the computer name
- runas.exe (PID: 3820)
Manual execution by user
- CCleaner.exe (PID: 1552)
Reads the hosts file
- CCleaner.exe (PID: 1588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.2) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| LegalCopyright: | Elektro Berkay / MoonCon / Tobiaddr0c |
|---|---|
| CompanyName: | Mnc 2020 |
| FileDescription: | Watch out |
| InternalName: | MrsMajor3.0 |
| OriginalFileName: | MrsMajor3.0.exe |
| ProductName: | MrsMajor |
| ProductVersion: | 3.0.0.0 |
| FileVersion: | 3.0.0.0 |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows 16-bit |
| FileFlags: | Debug, Pre-release, Private build |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 3.0.0.0 |
| FileVersionNumber: | 3.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.2 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1000 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 303104 |
| CodeSize: | 86528 |
| LinkerVersion: | 2.5 |
| PEType: | PE32+ |
| TimeStamp: | 2018:02:01 21:47:38+01:00 |
| MachineType: | AMD AMD64 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_AMD64 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Feb-2018 20:47:38 |
| Detected languages: |
|
| FileVersion: | 3.0.0.0 |
| ProductVersion: | 3.0.0.0 |
| ProductName: | MrsMajor |
| OriginalFilename: | MrsMajor3.0.exe |
| InternalName: | MrsMajor3.0 |
| FileDescription: | Watch out |
| CompanyName: | Mnc 2020 |
| LegalCopyright: | Elektro Berkay / MoonCon / Tobiaddr0c |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_AMD64 |
| Number of sections: | 6 |
| Time date stamp: | 01-Feb-2018 20:47:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00F0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x000051B9 | 0x00005200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.51773 |
.text | 0x00007000 | 0x0000FE95 | 0x00010000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.32926 |
.rdata | 0x00017000 | 0x00004AFD | 0x00004C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.64587 |
.pdata | 0x0001C000 | 0x00001098 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.83793 |
.data | 0x0001E000 | 0x000022E8 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.33464 |
.rsrc | 0x00021000 | 0x00042B18 | 0x00042C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.73 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.08821 | 672 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 2.79176 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.00991 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 3.08466 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 3.23732 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 3.58808 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
0BDA4881AEC6D1D3F6BA8D898EA65736 | 3.41938 | 18 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
2855F9C724606CE6DB5F95894F566EB1 | 6.51392 | 118 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
5444BAD06F | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
74176EB43CC954ADED023546303A45C122B1D6F2 | 7.99158 | 19764 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.dll |
OLE32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
USER32.DLL |
WINMM.DLL |
msvcrt.dll |
Total processes
41
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1552 | "C:\Program Files\CCleaner\CCleaner.exe" | C:\Program Files\CCleaner\CCleaner.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: MEDIUM Description: CCleaner Exit code: 0 Version: 5.74.0.8198 Modules
| |||||||||||||||
| 1588 | "C:\Program Files\CCleaner\CCleaner.exe" /uac | C:\Program Files\CCleaner\CCleaner.exe | taskeng.exe | ||||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5.74.0.8198 Modules
| |||||||||||||||
| 3820 | "C:\Windows\System32\runas.exe" /user:administrator "C:\Users\admin\Desktop\MrsMajor 3.0.exe" | C:\Windows\System32\runas.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Run As Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 537
Read events
4 413
Write events
93
Delete events
31
Modification events
| (PID) Process: | (1588) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Piriform\CCleaner |
| Operation: | write | Name: | UpdateBackground |
Value: 0 | |||
| (PID) Process: | (1588) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Piriform\CCleaner |
| Operation: | write | Name: | FTU |
Value: 02/11/2020|7|1 | |||
| (PID) Process: | (1588) CCleaner.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1588) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1588) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1588) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1588) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1588) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1588) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1588) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
2
Suspicious files
3
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1588 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\SA0MVRQWTS1IEEBHKU5H.temp | binary | |
MD5:— | SHA256:— | |||
| 1588 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ed7a5cc3cca8d52a.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1588 | CCleaner.exe | C:\Program Files\CCleaner\gcapi_16436551151588.dll | executable | |
MD5:F637D5D3C3A60FDDB5DD397556FE9B1D | SHA256:641B843CB6EE7538EC267212694C9EF0616B9AC9AB14A0ABD7CF020678D50B02 | |||
| 1588 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ed7a5cc3cca8d52a.customDestinations-ms~RF146715.TMP | binary | |
MD5:DBCF3C75A775F497C840EDB11D040D59 | SHA256:5D78C6A7022210BD2FFBCA2F520A32122C94B7FF54D414CD73637CC0FB2CD687 | |||
| 1588 | CCleaner.exe | C:\Program Files\CCleaner\gcapi_dll.dll | executable | |
MD5:F637D5D3C3A60FDDB5DD397556FE9B1D | SHA256:641B843CB6EE7538EC267212694C9EF0616B9AC9AB14A0ABD7CF020678D50B02 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
77
DNS requests
5
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 404 | 92.123.225.75:80 | http://ncc.avast.com/ncc.txt | unknown | xml | 341 b | whitelisted |
1588 | CCleaner.exe | GET | 404 | 151.101.2.202:80 | http://www.ccleaner.com/auto?a=0&p=cc&v=5.74.8198&l=1033&lk=&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-HZ8S&o=6.1W3&au=0&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gd=19ce970b-f6c0-4a09-bae4-274b971730e0 | US | xml | 341 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1588 | CCleaner.exe | 5.62.25.43:443 | shepherd.ff.avast.com | iomart Cloud Services Limited. | GB | unknown |
1588 | CCleaner.exe | 5.62.40.21:443 | shepherd.ff.avast.com | AVAST Software s.r.o. | DE | unknown |
— | — | 151.101.66.202:443 | www.ccleaner.com | Fastly | US | suspicious |
1588 | CCleaner.exe | 5.62.38.143:443 | ipm-provider.ff.avast.com | AVAST Software s.r.o. | NL | unknown |
1588 | CCleaner.exe | 151.101.66.202:443 | www.ccleaner.com | Fastly | US | suspicious |
— | — | 92.123.225.75:80 | ncc.avast.com | Akamai International B.V. | — | whitelisted |
— | — | 69.94.68.205:443 | analytics.ff.avast.com | OLM, LLC | US | unknown |
1588 | CCleaner.exe | 151.101.2.202:80 | www.ccleaner.com | Fastly | US | suspicious |
1588 | CCleaner.exe | 151.101.2.202:443 | www.ccleaner.com | Fastly | US | suspicious |
— | — | 69.94.76.79:443 | ipm-provider.ff.avast.com | OLM, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ncc.avast.com |
| whitelisted |
analytics.ff.avast.com |
| whitelisted |
www.ccleaner.com |
| whitelisted |
ipm-provider.ff.avast.com |
| whitelisted |
shepherd.ff.avast.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1588 | CCleaner.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
Process | Message |
|---|---|
CCleaner.exe | Failed to open log file 'C:\Program Files\CCleaner' |
CCleaner.exe | startCheckingLicense()
|
CCleaner.exe | Using Sciter version 4.4.4.4-r8057
|
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | observing CurrentIndex changed - 0
|
CCleaner.exe | observing CurrentIndex changed - Context.FirstTime=true CurrentIndex=0 LastIndex=4
|
CCleaner.exe | observing currentResultDetails changed - None
|
CCleaner.exe | SetStrings - Live Region updated: ,
|
CCleaner.exe | observing currentModeType changed - Preview
|