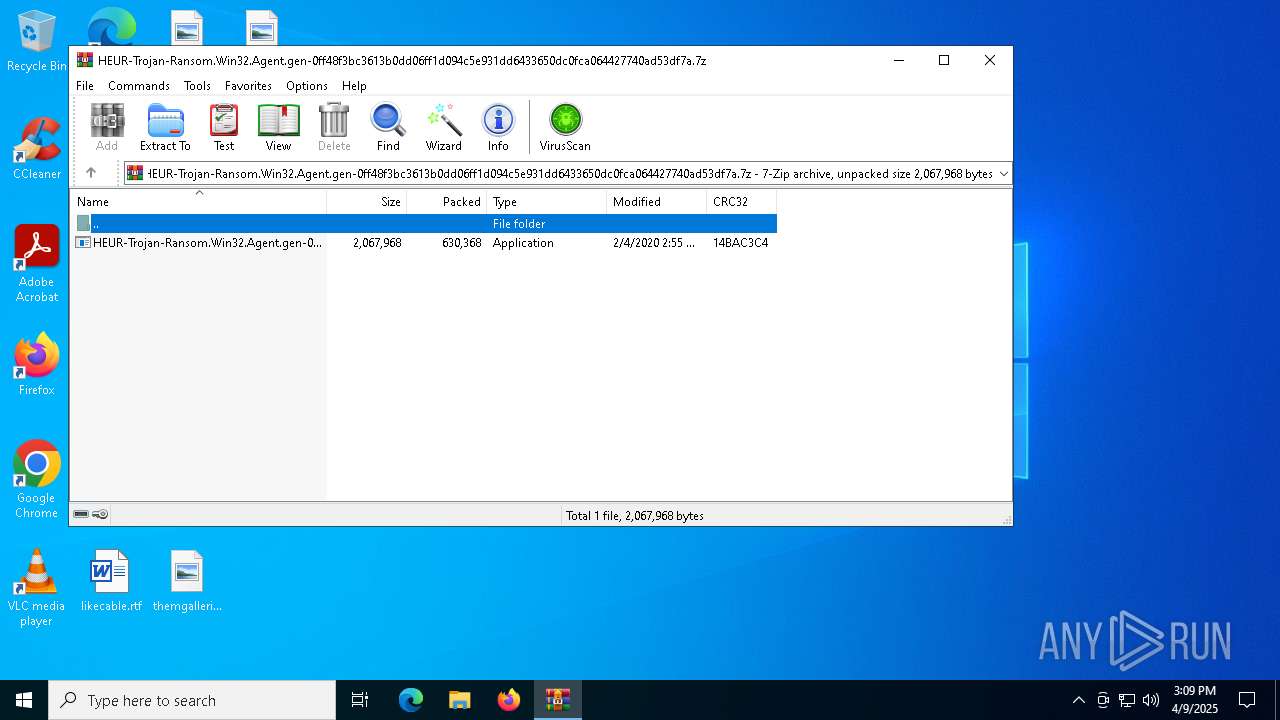
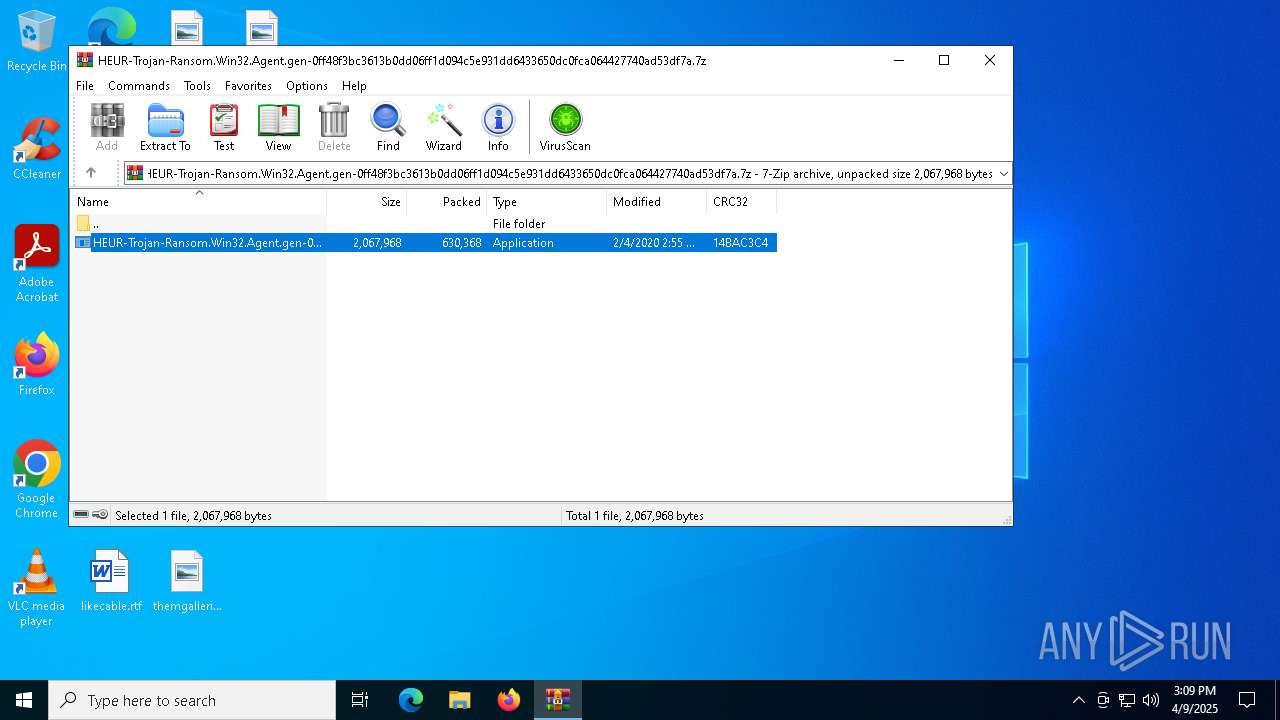
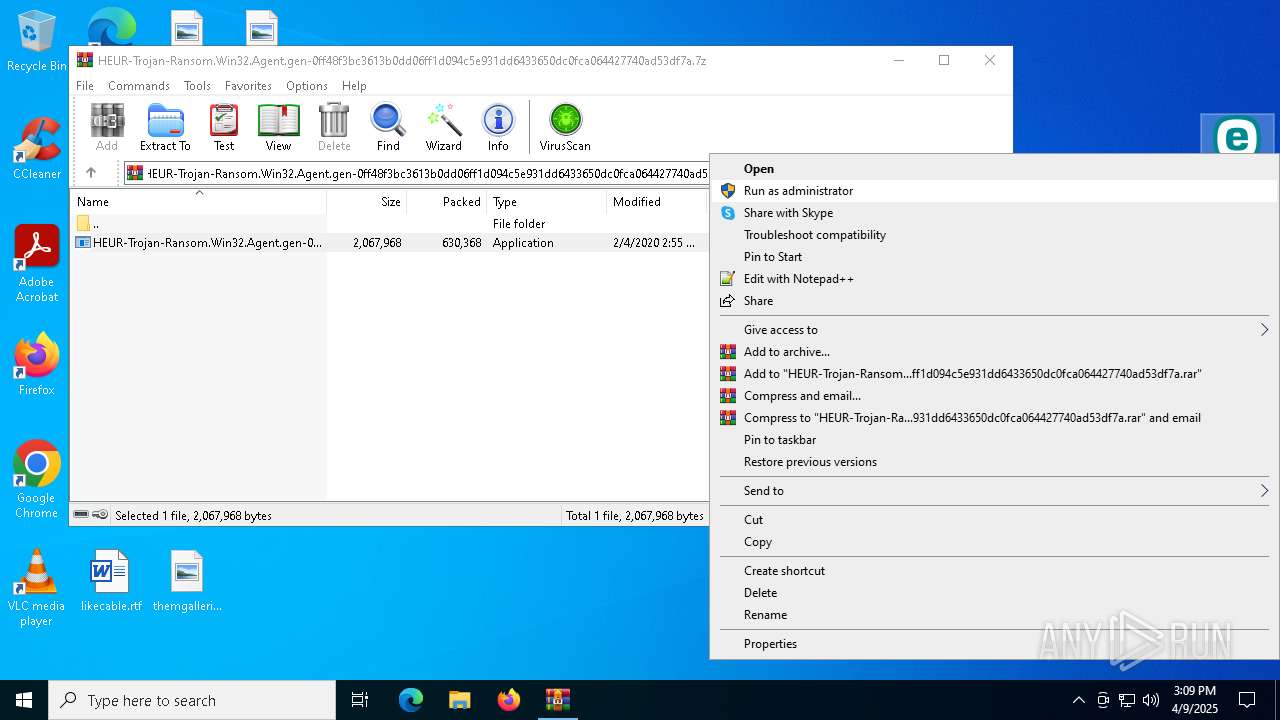
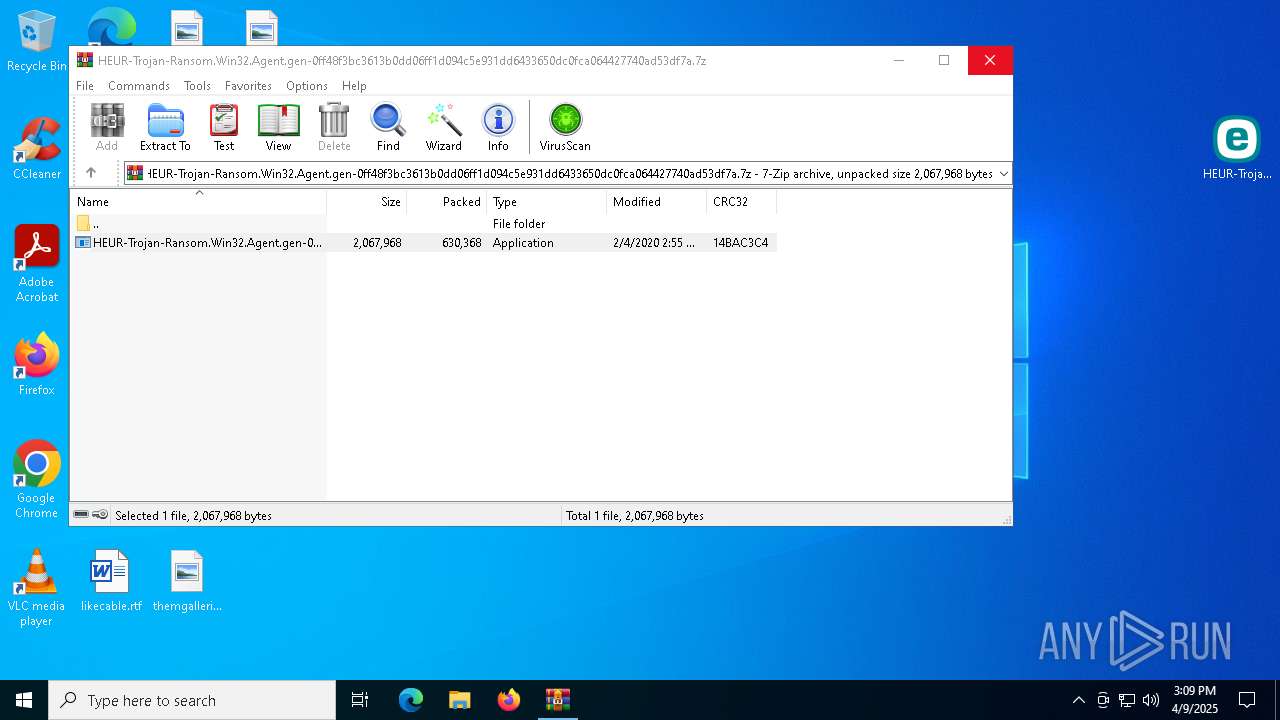
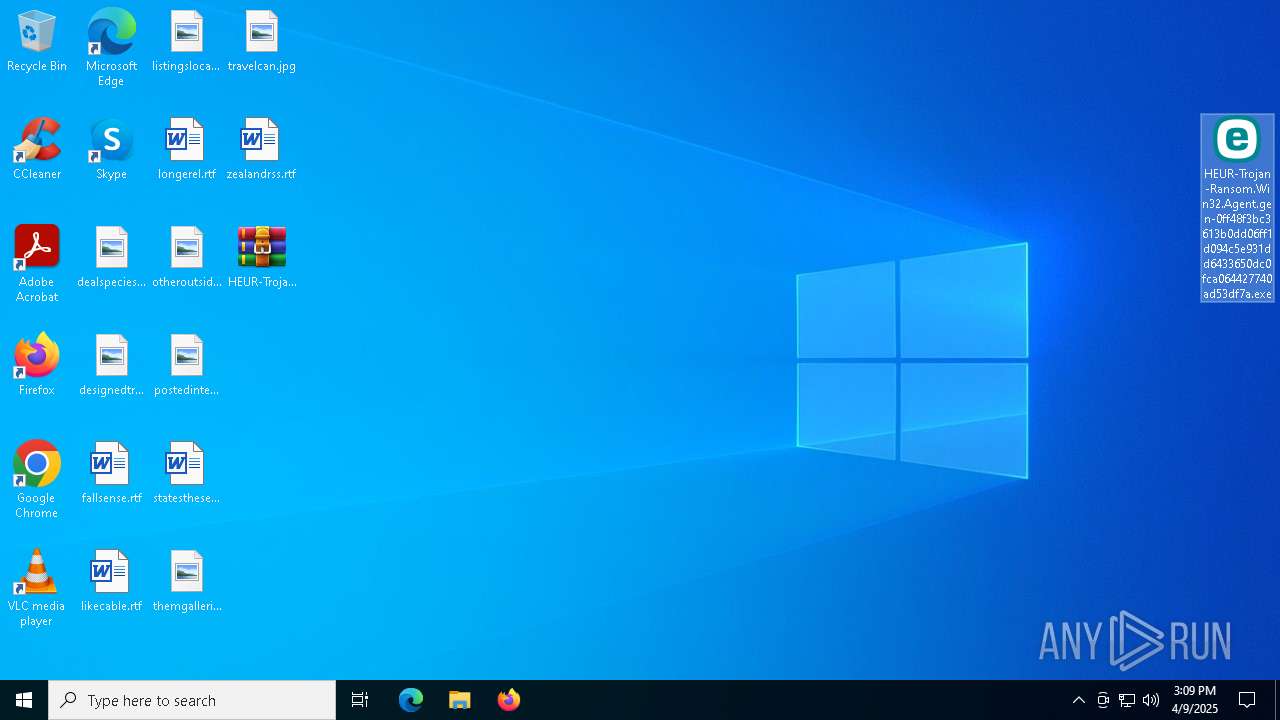
| File name: | HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.7z |
| Full analysis: | https://app.any.run/tasks/5066e003-077d-4bad-966d-aa51b833505e |
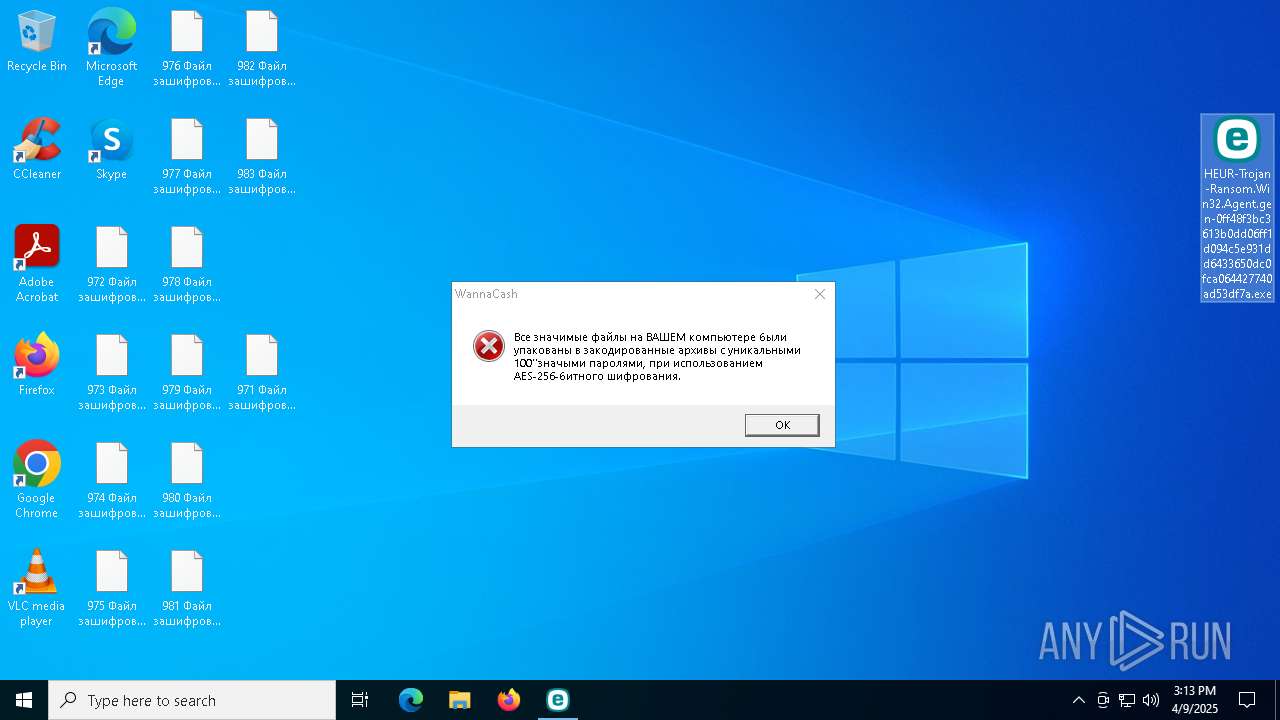
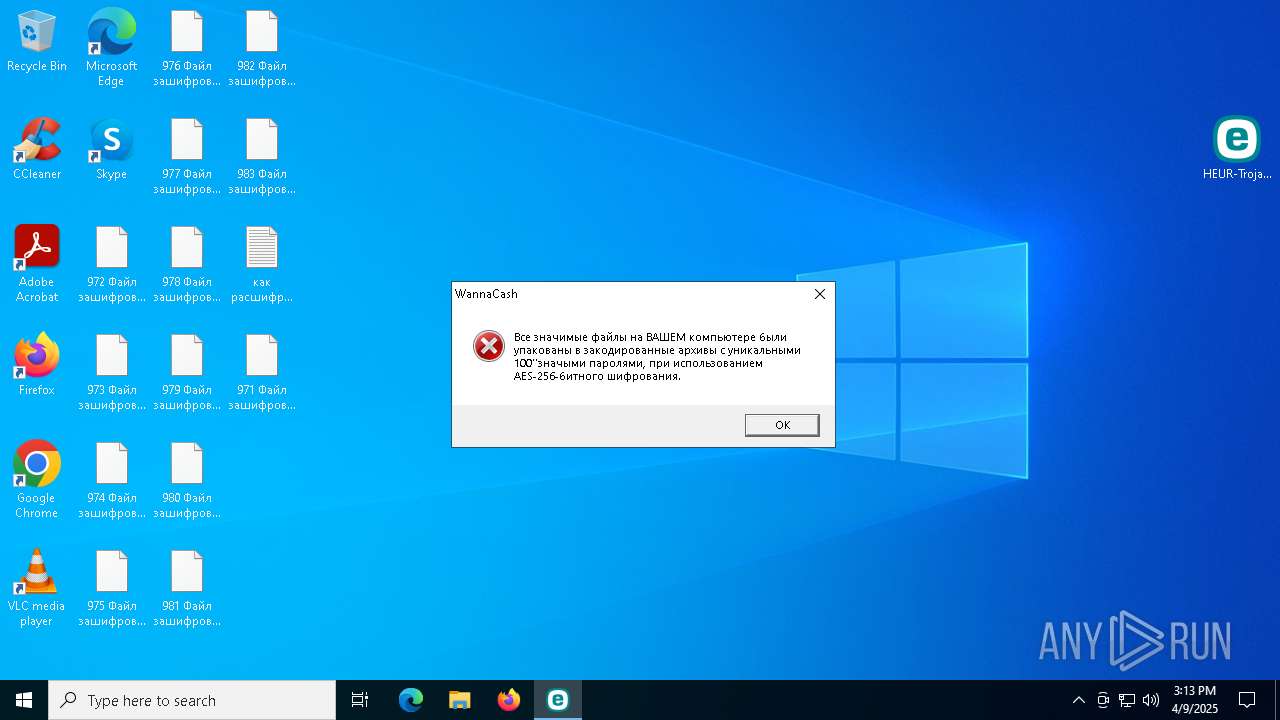
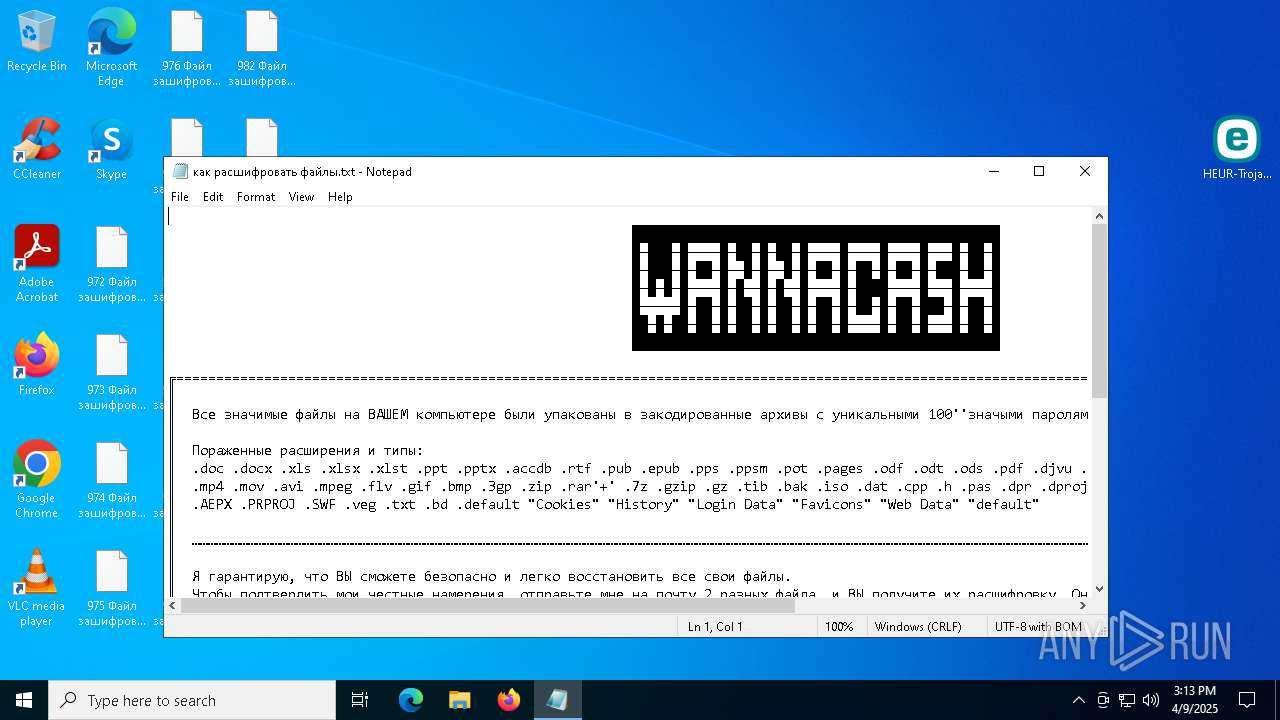
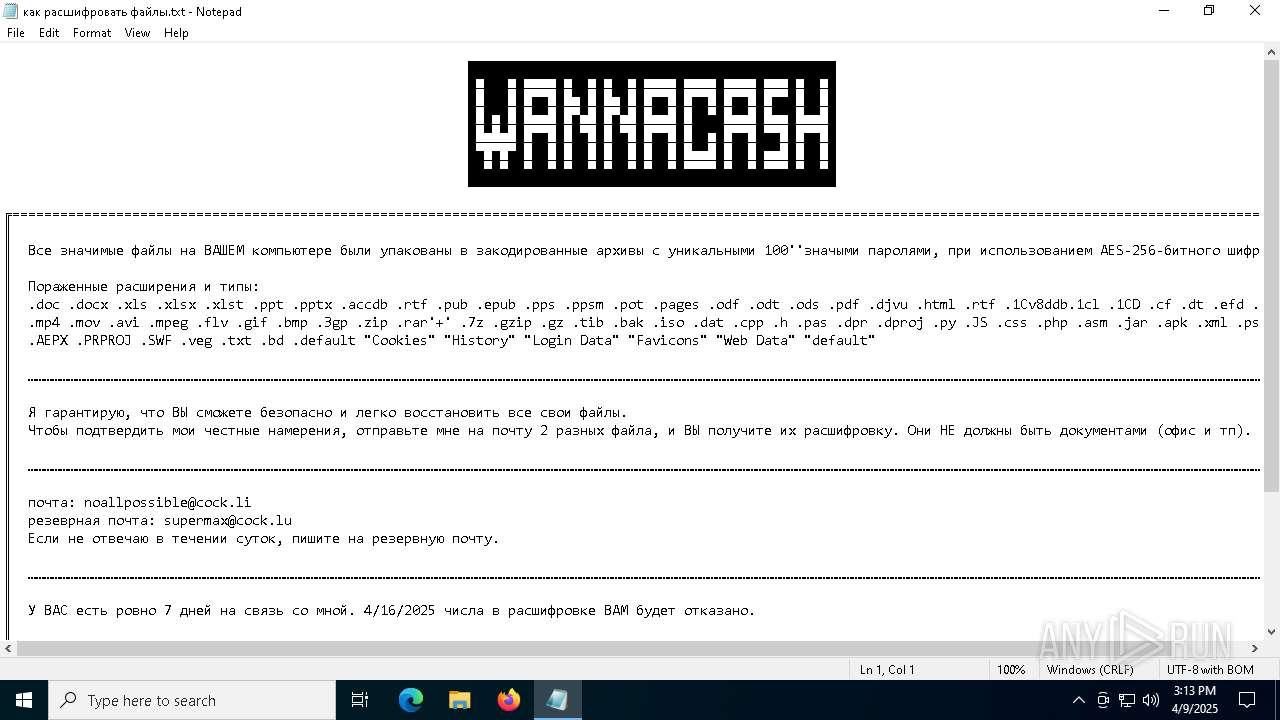
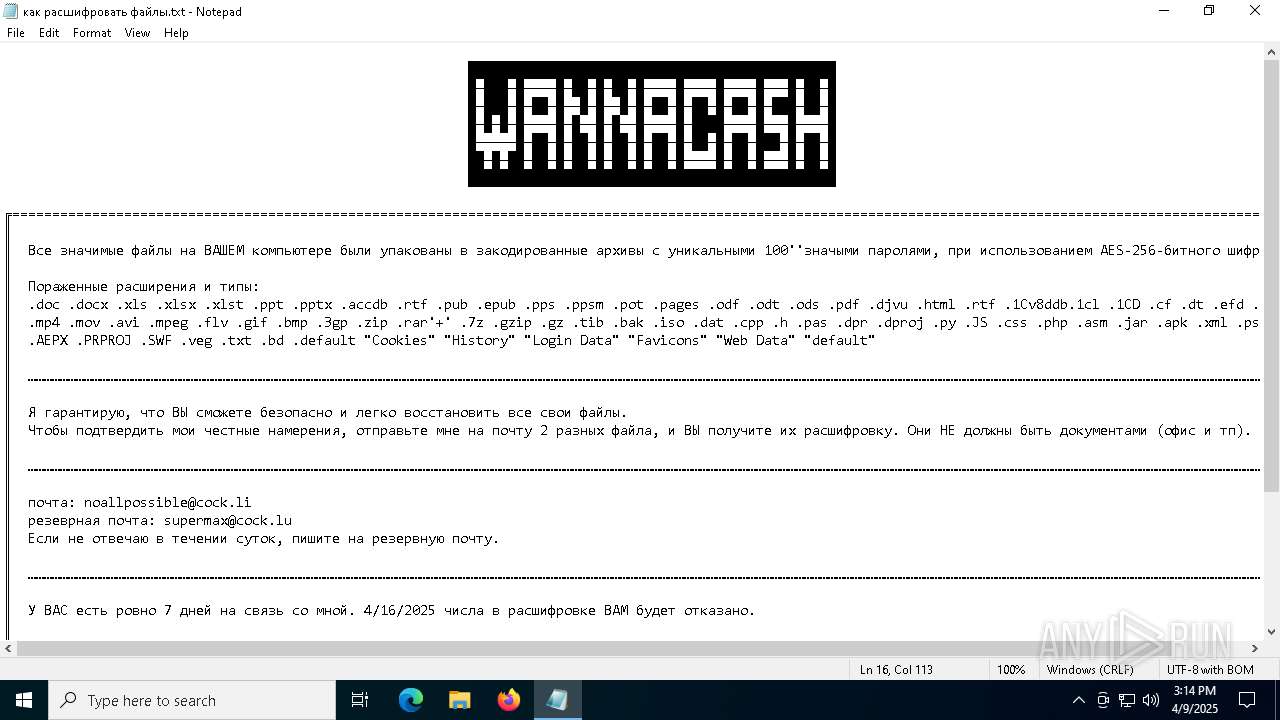
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | April 09, 2025, 15:09:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 25CB7E99376B212BC2BAA1A05FAE3BB4 |
| SHA1: | CA3190651F6F32FF0864F2DA2D4232302E3E7079 |
| SHA256: | 4A707C7DED13622496234421FE841C68B373C79F748041601C6E6CF372AC07BA |
| SSDEEP: | 24576:1JFLKIMs+GdAzTqlzwav7ybQIOMYq9IIKjARxSjGU0G5eD3vMg5zPMlhAJs3WHv:1JFLKIMs+GmzTqlzwav7ybQIOMYquI+U |
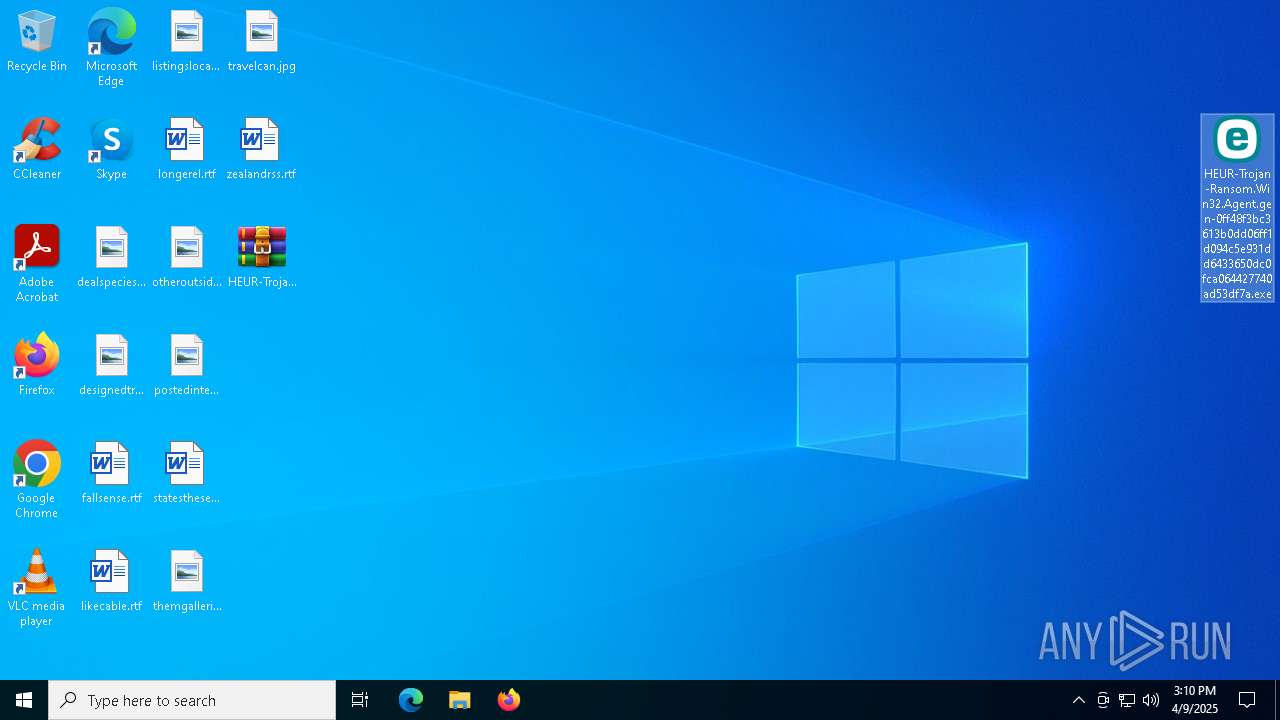
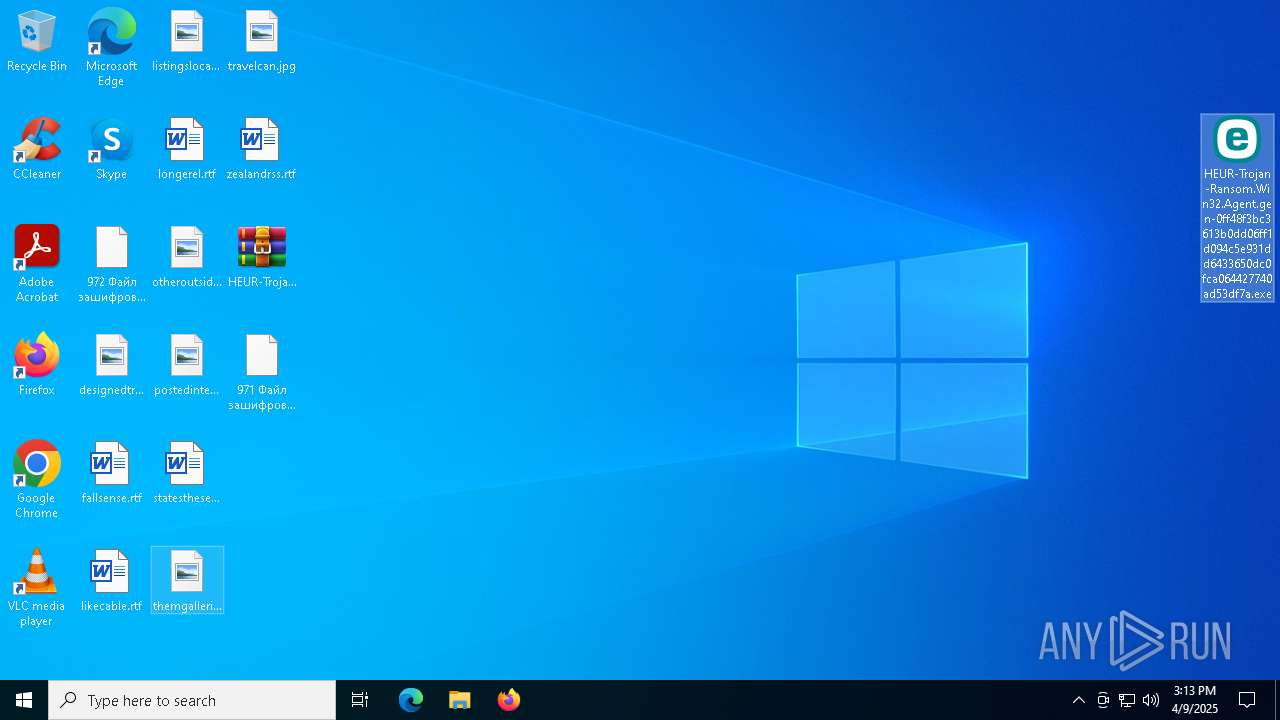
MALICIOUS
Actions looks like stealing of personal data
- HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe (PID: 7808)
- Rar.exe (PID: 7356)
- Rar.exe (PID: 6480)
- Rar.exe (PID: 7216)
- Rar.exe (PID: 6148)
- Rar.exe (PID: 5260)
- Rar.exe (PID: 472)
- Rar.exe (PID: 1348)
- Rar.exe (PID: 7988)
- Rar.exe (PID: 2908)
- Rar.exe (PID: 8108)
- Rar.exe (PID: 6808)
- Rar.exe (PID: 6132)
- Rar.exe (PID: 6300)
- Rar.exe (PID: 2148)
- Rar.exe (PID: 1764)
- Rar.exe (PID: 7476)
- Rar.exe (PID: 6828)
- Rar.exe (PID: 6676)
- Rar.exe (PID: 2040)
- Rar.exe (PID: 7768)
- Rar.exe (PID: 4692)
- Rar.exe (PID: 7692)
- Rar.exe (PID: 7740)
- Rar.exe (PID: 7956)
- Rar.exe (PID: 8016)
- Rar.exe (PID: 7212)
- Rar.exe (PID: 3240)
- Rar.exe (PID: 7400)
- Rar.exe (PID: 5756)
- Rar.exe (PID: 7532)
- Rar.exe (PID: 7656)
- Rar.exe (PID: 7780)
- Rar.exe (PID: 7940)
- Rar.exe (PID: 5728)
- Rar.exe (PID: 5988)
- Rar.exe (PID: 5668)
- Rar.exe (PID: 7460)
- Rar.exe (PID: 2240)
- Rar.exe (PID: 1096)
- Rar.exe (PID: 6028)
- Rar.exe (PID: 744)
- Rar.exe (PID: 7624)
- Rar.exe (PID: 4152)
- Rar.exe (PID: 5868)
- Rar.exe (PID: 7020)
- Rar.exe (PID: 7804)
- Rar.exe (PID: 8004)
- Rar.exe (PID: 7012)
- Rar.exe (PID: 7648)
- Rar.exe (PID: 3884)
- Rar.exe (PID: 1660)
- Rar.exe (PID: 5544)
- Rar.exe (PID: 4000)
- Rar.exe (PID: 8052)
- Rar.exe (PID: 6816)
- Rar.exe (PID: 5360)
- Rar.exe (PID: 6940)
- Rar.exe (PID: 7520)
- Rar.exe (PID: 7512)
- Rar.exe (PID: 7196)
- Rar.exe (PID: 7924)
- Rar.exe (PID: 6560)
- Rar.exe (PID: 5776)
- Rar.exe (PID: 7200)
- Rar.exe (PID: 8172)
- Rar.exe (PID: 8136)
- Rar.exe (PID: 7036)
- Rar.exe (PID: 8100)
- Rar.exe (PID: 1628)
- Rar.exe (PID: 3396)
- Rar.exe (PID: 7760)
- Rar.exe (PID: 7592)
- Rar.exe (PID: 5936)
- Rar.exe (PID: 6272)
- Rar.exe (PID: 4380)
- Rar.exe (PID: 3268)
- Rar.exe (PID: 2236)
- Rar.exe (PID: 3896)
- Rar.exe (PID: 7172)
- Rar.exe (PID: 4212)
- Rar.exe (PID: 4408)
- Rar.exe (PID: 7696)
- Rar.exe (PID: 7788)
- Rar.exe (PID: 1676)
- Rar.exe (PID: 6136)
- Rar.exe (PID: 3024)
- Rar.exe (PID: 5596)
- Rar.exe (PID: 2800)
- Rar.exe (PID: 5036)
- Rar.exe (PID: 5800)
- Rar.exe (PID: 8088)
- Rar.exe (PID: 7728)
- Rar.exe (PID: 2504)
- Rar.exe (PID: 5720)
- Rar.exe (PID: 8152)
- Rar.exe (PID: 644)
- Rar.exe (PID: 7944)
- Rar.exe (PID: 1020)
- Rar.exe (PID: 7344)
- Rar.exe (PID: 7440)
- Rar.exe (PID: 6264)
- Rar.exe (PID: 4868)
- Rar.exe (PID: 7732)
- Rar.exe (PID: 7960)
- Rar.exe (PID: 8180)
- Rar.exe (PID: 8160)
- Rar.exe (PID: 7616)
- Rar.exe (PID: 924)
- Rar.exe (PID: 5600)
- Rar.exe (PID: 7224)
- Rar.exe (PID: 456)
- Rar.exe (PID: 5204)
- Rar.exe (PID: 8876)
- Rar.exe (PID: 10072)
- Rar.exe (PID: 9516)
- Rar.exe (PID: 9768)
- Rar.exe (PID: 9832)
- Rar.exe (PID: 9380)
- Rar.exe (PID: 2084)
- Rar.exe (PID: 9320)
- Rar.exe (PID: 9920)
Modifies files in the Chrome extension folder
- Rar.exe (PID: 6148)
- Rar.exe (PID: 7216)
- HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe (PID: 7808)
- Rar.exe (PID: 6480)
- Rar.exe (PID: 5260)
- Rar.exe (PID: 472)
- Rar.exe (PID: 1348)
- Rar.exe (PID: 7988)
- Rar.exe (PID: 6300)
- Rar.exe (PID: 2908)
- Rar.exe (PID: 8108)
SUSPICIOUS
Executable content was dropped or overwritten
- HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe (PID: 7808)
Reads security settings of Internet Explorer
- HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe (PID: 7808)
Reads browser cookies
- Rar.exe (PID: 8640)
- Rar.exe (PID: 9076)
Checks for external IP
- svchost.exe (PID: 2196)
- HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe (PID: 7808)
Potential Corporate Privacy Violation
- HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe (PID: 7808)
- svchost.exe (PID: 2196)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3156)
Create files in a temporary directory
- HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe (PID: 7808)
Reads the computer name
- HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe (PID: 7808)
Checks supported languages
- HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe (PID: 7808)
- Rar.exe (PID: 8020)
- Rar.exe (PID: 7920)
- Rar.exe (PID: 8104)
- Rar.exe (PID: 8184)
- Rar.exe (PID: 5164)
- Rar.exe (PID: 2088)
- Rar.exe (PID: 5640)
- Rar.exe (PID: 2564)
- Rar.exe (PID: 7480)
- Rar.exe (PID: 7428)
- Rar.exe (PID: 1328)
- Rar.exe (PID: 6576)
- Rar.exe (PID: 7536)
- Rar.exe (PID: 1196)
- Rar.exe (PID: 7712)
- Rar.exe (PID: 7664)
- Rar.exe (PID: 7204)
- Rar.exe (PID: 8128)
- Rar.exe (PID: 5280)
- Rar.exe (PID: 1188)
- Rar.exe (PID: 6644)
- Rar.exe (PID: 3304)
- Rar.exe (PID: 7928)
- Rar.exe (PID: 7336)
- Rar.exe (PID: 7552)
- Rar.exe (PID: 6068)
- Rar.exe (PID: 5984)
- Rar.exe (PID: 5024)
- Rar.exe (PID: 3020)
- Rar.exe (PID: 7340)
- Rar.exe (PID: 7792)
- Rar.exe (PID: 780)
- Rar.exe (PID: 7596)
- Rar.exe (PID: 7948)
- Rar.exe (PID: 8012)
- Rar.exe (PID: 7912)
- Rar.exe (PID: 5380)
- Rar.exe (PID: 8176)
- Rar.exe (PID: 5772)
- Rar.exe (PID: 1228)
- Rar.exe (PID: 6744)
- Rar.exe (PID: 7356)
- Rar.exe (PID: 7468)
- Rar.exe (PID: 6148)
- Rar.exe (PID: 7508)
- Rar.exe (PID: 5260)
- Rar.exe (PID: 7416)
- Rar.exe (PID: 1244)
- Rar.exe (PID: 6480)
- Rar.exe (PID: 7216)
- Rar.exe (PID: 7660)
- Rar.exe (PID: 472)
- Rar.exe (PID: 7988)
- Rar.exe (PID: 1348)
- Rar.exe (PID: 2908)
- Rar.exe (PID: 8108)
- Rar.exe (PID: 6808)
- Rar.exe (PID: 6132)
- Rar.exe (PID: 6300)
- Rar.exe (PID: 2148)
- Rar.exe (PID: 1764)
- Rar.exe (PID: 7476)
- Rar.exe (PID: 7380)
- Rar.exe (PID: 6828)
- Rar.exe (PID: 2040)
- Rar.exe (PID: 7768)
- Rar.exe (PID: 4692)
- Rar.exe (PID: 7692)
- Rar.exe (PID: 7740)
- Rar.exe (PID: 6676)
- Rar.exe (PID: 7956)
- Rar.exe (PID: 7992)
- Rar.exe (PID: 4980)
- Rar.exe (PID: 7212)
- Rar.exe (PID: 4608)
- Rar.exe (PID: 8016)
- Rar.exe (PID: 3240)
- Rar.exe (PID: 864)
- Rar.exe (PID: 7400)
- Rar.exe (PID: 1128)
- Rar.exe (PID: 5756)
- Rar.exe (PID: 6456)
- Rar.exe (PID: 7532)
- Rar.exe (PID: 5556)
- Rar.exe (PID: 7656)
- Rar.exe (PID: 7780)
- Rar.exe (PID: 7208)
- Rar.exe (PID: 720)
- Rar.exe (PID: 7528)
- Rar.exe (PID: 7940)
- Rar.exe (PID: 8096)
- Rar.exe (PID: 5988)
- Rar.exe (PID: 5728)
- Rar.exe (PID: 5668)
- Rar.exe (PID: 7464)
- Rar.exe (PID: 7460)
- Rar.exe (PID: 2240)
- Rar.exe (PID: 1096)
- Rar.exe (PID: 6028)
- Rar.exe (PID: 744)
- Rar.exe (PID: 5228)
- Rar.exe (PID: 7628)
- Rar.exe (PID: 7624)
- Rar.exe (PID: 6268)
- Rar.exe (PID: 4152)
- Rar.exe (PID: 7884)
- Rar.exe (PID: 3900)
- Rar.exe (PID: 5868)
- Rar.exe (PID: 6112)
- Rar.exe (PID: 7020)
- Rar.exe (PID: 8072)
- Rar.exe (PID: 1748)
- Rar.exe (PID: 4112)
- Rar.exe (PID: 7524)
- Rar.exe (PID: 684)
- Rar.exe (PID: 2984)
- Rar.exe (PID: 7648)
- Rar.exe (PID: 6388)
- Rar.exe (PID: 7348)
- Rar.exe (PID: 7804)
- Rar.exe (PID: 7012)
- Rar.exe (PID: 8052)
- Rar.exe (PID: 7724)
- Rar.exe (PID: 8004)
- Rar.exe (PID: 1660)
- Rar.exe (PID: 5392)
- Rar.exe (PID: 5544)
- Rar.exe (PID: 4000)
- Rar.exe (PID: 6816)
- Rar.exe (PID: 3884)
- Rar.exe (PID: 7472)
- Rar.exe (PID: 5360)
- Rar.exe (PID: 6940)
- Rar.exe (PID: 7520)
- Rar.exe (PID: 7512)
- Rar.exe (PID: 7200)
- Rar.exe (PID: 7924)
- Rar.exe (PID: 7196)
- Rar.exe (PID: 6560)
- Rar.exe (PID: 8172)
- Rar.exe (PID: 5776)
- Rar.exe (PID: 7036)
- Rar.exe (PID: 8100)
- Rar.exe (PID: 4696)
- Rar.exe (PID: 1628)
- Rar.exe (PID: 8136)
- Rar.exe (PID: 1012)
- Rar.exe (PID: 3396)
- Rar.exe (PID: 7760)
- Rar.exe (PID: 7680)
- Rar.exe (PID: 6272)
- Rar.exe (PID: 3268)
- Rar.exe (PID: 8112)
- Rar.exe (PID: 4408)
- Rar.exe (PID: 7716)
- Rar.exe (PID: 4380)
- Rar.exe (PID: 3896)
- Rar.exe (PID: 7172)
- Rar.exe (PID: 4212)
- Rar.exe (PID: 6136)
- Rar.exe (PID: 2236)
- Rar.exe (PID: 3008)
- Rar.exe (PID: 7696)
- Rar.exe (PID: 7776)
- Rar.exe (PID: 7788)
- Rar.exe (PID: 1676)
- Rar.exe (PID: 2616)
- Rar.exe (PID: 6768)
- Rar.exe (PID: 3024)
- Rar.exe (PID: 2664)
- Rar.exe (PID: 7228)
- Rar.exe (PID: 4040)
- Rar.exe (PID: 2800)
- Rar.exe (PID: 5596)
- Rar.exe (PID: 7968)
- Rar.exe (PID: 5800)
- Rar.exe (PID: 8088)
- Rar.exe (PID: 7728)
- Rar.exe (PID: 644)
- Rar.exe (PID: 856)
- Rar.exe (PID: 7944)
- Rar.exe (PID: 6540)
- Rar.exe (PID: 5720)
- Rar.exe (PID: 2504)
- Rar.exe (PID: 7344)
- Rar.exe (PID: 7440)
- Rar.exe (PID: 2092)
- Rar.exe (PID: 4868)
- Rar.exe (PID: 7616)
- Rar.exe (PID: 7960)
- Rar.exe (PID: 6708)
- Rar.exe (PID: 924)
- Rar.exe (PID: 8180)
- Rar.exe (PID: 8160)
- Rar.exe (PID: 7224)
- Rar.exe (PID: 5600)
- Rar.exe (PID: 456)
- Rar.exe (PID: 5112)
- Rar.exe (PID: 5204)
- Rar.exe (PID: 7584)
- Rar.exe (PID: 8044)
- Rar.exe (PID: 7800)
- Rar.exe (PID: 904)
- Rar.exe (PID: 8156)
- Rar.exe (PID: 7220)
- Rar.exe (PID: 7456)
- Rar.exe (PID: 7996)
- Rar.exe (PID: 2268)
- Rar.exe (PID: 5136)
- Rar.exe (PID: 5528)
- Rar.exe (PID: 7148)
- Rar.exe (PID: 960)
- Rar.exe (PID: 1164)
- Rar.exe (PID: 7700)
- Rar.exe (PID: 7972)
- Rar.exe (PID: 7976)
- Rar.exe (PID: 2108)
- Rar.exe (PID: 6208)
- Rar.exe (PID: 6156)
- Rar.exe (PID: 1568)
- Rar.exe (PID: 6416)
- Rar.exe (PID: 8024)
- Rar.exe (PID: 7620)
- Rar.exe (PID: 7412)
- Rar.exe (PID: 6040)
- Rar.exe (PID: 2772)
- Rar.exe (PID: 736)
- Rar.exe (PID: 5892)
- Rar.exe (PID: 7612)
- Rar.exe (PID: 7180)
- Rar.exe (PID: 8060)
- Rar.exe (PID: 2332)
- Rar.exe (PID: 1240)
- Rar.exe (PID: 4188)
- Rar.exe (PID: 7248)
- Rar.exe (PID: 7688)
- Rar.exe (PID: 7544)
- Rar.exe (PID: 8168)
- Rar.exe (PID: 5008)
- Rar.exe (PID: 5400)
- Rar.exe (PID: 6584)
- Rar.exe (PID: 7084)
- Rar.exe (PID: 8148)
- Rar.exe (PID: 680)
- Rar.exe (PID: 4892)
- Rar.exe (PID: 7608)
- Rar.exe (PID: 4784)
- Rar.exe (PID: 5200)
- Rar.exe (PID: 1324)
- Rar.exe (PID: 4688)
- Rar.exe (PID: 4284)
- Rar.exe (PID: 2420)
- Rar.exe (PID: 4220)
- Rar.exe (PID: 7376)
- Rar.exe (PID: 6660)
- Rar.exe (PID: 6592)
- Rar.exe (PID: 2284)
- Rar.exe (PID: 7916)
- Rar.exe (PID: 8068)
- Rar.exe (PID: 7408)
- Rar.exe (PID: 8116)
- Rar.exe (PID: 1912)
- Rar.exe (PID: 8084)
- Rar.exe (PID: 4056)
- Rar.exe (PID: 6700)
- Rar.exe (PID: 4376)
- Rar.exe (PID: 7640)
- Rar.exe (PID: 7936)
- Rar.exe (PID: 3176)
- Rar.exe (PID: 2552)
- Rar.exe (PID: 7652)
- Rar.exe (PID: 8120)
- Rar.exe (PID: 7488)
- Rar.exe (PID: 7436)
- Rar.exe (PID: 4464)
- Rar.exe (PID: 6852)
- Rar.exe (PID: 4012)
- Rar.exe (PID: 3032)
- Rar.exe (PID: 2152)
- Rar.exe (PID: 5624)
- Rar.exe (PID: 7424)
- Rar.exe (PID: 7736)
- Rar.exe (PID: 4304)
- Rar.exe (PID: 7708)
- Rar.exe (PID: 6736)
- Rar.exe (PID: 6988)
- Rar.exe (PID: 8164)
- Rar.exe (PID: 8008)
- Rar.exe (PID: 7288)
- Rar.exe (PID: 6752)
- Rar.exe (PID: 3828)
- Rar.exe (PID: 6248)
- Rar.exe (PID: 6740)
- Rar.exe (PID: 4652)
- Rar.exe (PID: 7984)
- Rar.exe (PID: 2104)
- Rar.exe (PID: 4452)
- Rar.exe (PID: 6468)
- Rar.exe (PID: 7668)
- Rar.exe (PID: 7964)
- Rar.exe (PID: 976)
- Rar.exe (PID: 7756)
- Rar.exe (PID: 7104)
- Rar.exe (PID: 3800)
- Rar.exe (PID: 7280)
- Rar.exe (PID: 8076)
- Rar.exe (PID: 1040)
- Rar.exe (PID: 5956)
- Rar.exe (PID: 7556)
- Rar.exe (PID: 1804)
- Rar.exe (PID: 3620)
- Rar.exe (PID: 1812)
- Rar.exe (PID: 7392)
- Rar.exe (PID: 6512)
- Rar.exe (PID: 632)
- Rar.exe (PID: 900)
- Rar.exe (PID: 7704)
- Rar.exe (PID: 6572)
- Rar.exe (PID: 2780)
- Rar.exe (PID: 5344)
- Rar.exe (PID: 6044)
- Rar.exe (PID: 4988)
- Rar.exe (PID: 4976)
- Rar.exe (PID: 7252)
- Rar.exe (PID: 5588)
- Rar.exe (PID: 7720)
- Rar.exe (PID: 3956)
- Rar.exe (PID: 1088)
- Rar.exe (PID: 4448)
- Rar.exe (PID: 240)
- Rar.exe (PID: 5364)
- Rar.exe (PID: 4016)
- Rar.exe (PID: 7764)
- Rar.exe (PID: 232)
- Rar.exe (PID: 7320)
- Rar.exe (PID: 7844)
- Rar.exe (PID: 7232)
- Rar.exe (PID: 5744)
- Rar.exe (PID: 7452)
- Rar.exe (PID: 5436)
- Rar.exe (PID: 1052)
- Rar.exe (PID: 6072)
- Rar.exe (PID: 3300)
- Rar.exe (PID: 2432)
- Rar.exe (PID: 4180)
- Rar.exe (PID: 7192)
- Rar.exe (PID: 8092)
- Rar.exe (PID: 4572)
- Rar.exe (PID: 2096)
- Rar.exe (PID: 7404)
- Rar.exe (PID: 1600)
- Rar.exe (PID: 7600)
- Rar.exe (PID: 7360)
- Rar.exe (PID: 7396)
- Rar.exe (PID: 3768)
- Rar.exe (PID: 3888)
- Rar.exe (PID: 920)
- Rar.exe (PID: 7856)
- Rar.exe (PID: 6048)
- Rar.exe (PID: 7864)
- Rar.exe (PID: 4884)
- Rar.exe (PID: 7384)
- Rar.exe (PID: 5452)
- Rar.exe (PID: 7908)
- Rar.exe (PID: 2516)
- Rar.exe (PID: 3804)
- Rar.exe (PID: 3968)
- Rar.exe (PID: 6256)
- Rar.exe (PID: 2776)
- Rar.exe (PID: 2340)
- Rar.exe (PID: 2896)
- Rar.exe (PID: 7516)
- Rar.exe (PID: 5072)
- Rar.exe (PID: 7576)
- Rar.exe (PID: 5056)
- Rar.exe (PID: 6980)
- Rar.exe (PID: 8080)
- Rar.exe (PID: 896)
- Rar.exe (PID: 2596)
- Rar.exe (PID: 7372)
- Rar.exe (PID: 5680)
- Rar.exe (PID: 6344)
- Rar.exe (PID: 2192)
- Rar.exe (PID: 6476)
- Rar.exe (PID: 3016)
- Rar.exe (PID: 8000)
- Rar.exe (PID: 4728)
- Rar.exe (PID: 7364)
- Rar.exe (PID: 6800)
- Rar.exe (PID: 7672)
- Rar.exe (PID: 5304)
- Rar.exe (PID: 8056)
- Rar.exe (PID: 1136)
- Rar.exe (PID: 5176)
- Rar.exe (PID: 3132)
- Rar.exe (PID: 6872)
- Rar.exe (PID: 6244)
- Rar.exe (PID: 8040)
- Rar.exe (PID: 7820)
- Rar.exe (PID: 4528)
- Rar.exe (PID: 2796)
- Rar.exe (PID: 7840)
- Rar.exe (PID: 4920)
- Rar.exe (PID: 7548)
- Rar.exe (PID: 7824)
- Rar.exe (PID: 968)
- Rar.exe (PID: 6436)
- Rar.exe (PID: 776)
- Rar.exe (PID: 4120)
- Rar.exe (PID: 8064)
- Rar.exe (PID: 6656)
- Rar.exe (PID: 7752)
- Rar.exe (PID: 7816)
- Rar.exe (PID: 6384)
- Rar.exe (PID: 4756)
- Rar.exe (PID: 2288)
- Rar.exe (PID: 7880)
- Rar.exe (PID: 5020)
- Rar.exe (PID: 1452)
- Rar.exe (PID: 1184)
- Rar.exe (PID: 5384)
- Rar.exe (PID: 7176)
- Rar.exe (PID: 5256)
- Rar.exe (PID: 5952)
- Rar.exe (PID: 7144)
- Rar.exe (PID: 5084)
- Rar.exe (PID: 7000)
- Rar.exe (PID: 2692)
- Rar.exe (PID: 5796)
- Rar.exe (PID: 8036)
- Rar.exe (PID: 3124)
- Rar.exe (PID: 5188)
- Rar.exe (PID: 7860)
- Rar.exe (PID: 8140)
- Rar.exe (PID: 6712)
- Rar.exe (PID: 2064)
- Rar.exe (PID: 300)
- Rar.exe (PID: 3012)
- Rar.exe (PID: 4620)
- Rar.exe (PID: 1672)
- Rar.exe (PID: 5812)
- Rar.exe (PID: 8032)
- Rar.exe (PID: 3796)
- Rar.exe (PID: 660)
- Rar.exe (PID: 872)
- Rar.exe (PID: 2600)
- Rar.exe (PID: 4724)
- Rar.exe (PID: 6652)
- Rar.exe (PID: 6036)
- Rar.exe (PID: 6964)
- Rar.exe (PID: 4172)
- Rar.exe (PID: 7636)
- Rar.exe (PID: 6032)
- Rar.exe (PID: 7324)
- Rar.exe (PID: 5960)
- Rar.exe (PID: 6184)
- Rar.exe (PID: 536)
- Rar.exe (PID: 7540)
- Rar.exe (PID: 6252)
- Rar.exe (PID: 7952)
- Rar.exe (PID: 4268)
- Rar.exe (PID: 540)
- Rar.exe (PID: 7300)
- Rar.exe (PID: 1272)
- Rar.exe (PID: 672)
- Rar.exe (PID: 7828)
- Rar.exe (PID: 7272)
- Rar.exe (PID: 5044)
- Rar.exe (PID: 132)
- Rar.exe (PID: 7292)
- Rar.exe (PID: 5512)
- Rar.exe (PID: 2416)
- Rar.exe (PID: 7304)
- Rar.exe (PID: 7492)
- Rar.exe (PID: 7784)
- Rar.exe (PID: 8188)
- Rar.exe (PID: 7484)
- Rar.exe (PID: 236)
- Rar.exe (PID: 4428)
- Rar.exe (PID: 8288)
- Rar.exe (PID: 8608)
- Rar.exe (PID: 8768)
- Rar.exe (PID: 8692)
- Rar.exe (PID: 8924)
- Rar.exe (PID: 9004)
- Rar.exe (PID: 9084)
- Rar.exe (PID: 7444)
- Rar.exe (PID: 8244)
- Rar.exe (PID: 8848)
- Rar.exe (PID: 8596)
- Rar.exe (PID: 8616)
- Rar.exe (PID: 8700)
- Rar.exe (PID: 9096)
- Rar.exe (PID: 8940)
- Rar.exe (PID: 9024)
- Rar.exe (PID: 8264)
- Rar.exe (PID: 8436)
- Rar.exe (PID: 8480)
- Rar.exe (PID: 8344)
- Rar.exe (PID: 8504)
- Rar.exe (PID: 8672)
- Rar.exe (PID: 8724)
- Rar.exe (PID: 9104)
- Rar.exe (PID: 9192)
- Rar.exe (PID: 8564)
- Rar.exe (PID: 8720)
- Rar.exe (PID: 8836)
- Rar.exe (PID: 8880)
- Rar.exe (PID: 9100)
- Rar.exe (PID: 8220)
- Rar.exe (PID: 8652)
- Rar.exe (PID: 8512)
- Rar.exe (PID: 8300)
- Rar.exe (PID: 8440)
- Rar.exe (PID: 8628)
- Rar.exe (PID: 9000)
- Rar.exe (PID: 9152)
- Rar.exe (PID: 9204)
- Rar.exe (PID: 9016)
- Rar.exe (PID: 9148)
- Rar.exe (PID: 8408)
- Rar.exe (PID: 8584)
- Rar.exe (PID: 8732)
- Rar.exe (PID: 8784)
- Rar.exe (PID: 4348)
- Rar.exe (PID: 9188)
- Rar.exe (PID: 8224)
- Rar.exe (PID: 8576)
- Rar.exe (PID: 8680)
- Rar.exe (PID: 8888)
- Rar.exe (PID: 8868)
- Rar.exe (PID: 9076)
- Rar.exe (PID: 5964)
- Rar.exe (PID: 812)
- Rar.exe (PID: 8232)
- Rar.exe (PID: 8360)
- Rar.exe (PID: 8632)
- Rar.exe (PID: 8736)
- Rar.exe (PID: 9052)
- Rar.exe (PID: 8976)
- Rar.exe (PID: 9044)
- Rar.exe (PID: 8272)
- Rar.exe (PID: 8276)
- Rar.exe (PID: 8568)
- Rar.exe (PID: 8636)
- Rar.exe (PID: 8668)
- Rar.exe (PID: 7268)
- Rar.exe (PID: 7296)
- Rar.exe (PID: 9176)
- Rar.exe (PID: 8592)
- Rar.exe (PID: 8696)
- Rar.exe (PID: 8644)
- Rar.exe (PID: 8796)
- Rar.exe (PID: 8956)
- Rar.exe (PID: 8932)
- Rar.exe (PID: 9184)
- Rar.exe (PID: 8364)
- Rar.exe (PID: 8604)
- Rar.exe (PID: 8816)
- Rar.exe (PID: 8952)
- Rar.exe (PID: 8896)
- Rar.exe (PID: 8444)
- Rar.exe (PID: 8392)
- Rar.exe (PID: 8600)
- Rar.exe (PID: 8852)
- Rar.exe (PID: 8804)
- Rar.exe (PID: 9040)
- Rar.exe (PID: 3976)
- Rar.exe (PID: 9212)
- Rar.exe (PID: 8752)
- Rar.exe (PID: 8916)
- Rar.exe (PID: 7504)
- Rar.exe (PID: 8548)
- Rar.exe (PID: 7152)
- Rar.exe (PID: 8708)
- Rar.exe (PID: 9028)
- Rar.exe (PID: 8388)
- Rar.exe (PID: 8376)
- Rar.exe (PID: 8748)
- Rar.exe (PID: 8336)
- Rar.exe (PID: 7244)
- Rar.exe (PID: 8384)
- Rar.exe (PID: 8484)
- Rar.exe (PID: 8516)
- Rar.exe (PID: 6904)
- Rar.exe (PID: 8728)
- Rar.exe (PID: 8928)
- Rar.exe (PID: 8212)
- Rar.exe (PID: 5864)
- Rar.exe (PID: 8612)
- Rar.exe (PID: 8316)
- Rar.exe (PID: 9116)
- Rar.exe (PID: 5404)
- Rar.exe (PID: 9168)
- Rar.exe (PID: 8864)
- Rar.exe (PID: 8660)
- Rar.exe (PID: 8572)
- Rar.exe (PID: 9208)
- Rar.exe (PID: 8428)
- Rar.exe (PID: 8560)
- Rar.exe (PID: 8824)
- Rar.exe (PID: 8964)
- Rar.exe (PID: 6820)
- Rar.exe (PID: 8348)
- Rar.exe (PID: 7100)
- Rar.exe (PID: 4244)
- Rar.exe (PID: 8656)
- Rar.exe (PID: 8788)
- Rar.exe (PID: 8464)
- Rar.exe (PID: 1300)
- Rar.exe (PID: 9020)
- Rar.exe (PID: 7260)
- Rar.exe (PID: 4944)
- Rar.exe (PID: 8684)
- Rar.exe (PID: 9032)
- Rar.exe (PID: 8884)
- Rar.exe (PID: 8468)
- Rar.exe (PID: 7264)
- Rar.exe (PID: 4276)
- Rar.exe (PID: 8284)
- Rar.exe (PID: 8840)
- Rar.exe (PID: 8624)
- Rar.exe (PID: 8396)
- Rar.exe (PID: 9060)
- Rar.exe (PID: 8320)
- Rar.exe (PID: 8808)
- Rar.exe (PID: 5308)
- Rar.exe (PID: 8744)
- Rar.exe (PID: 8268)
- Rar.exe (PID: 2408)
- Rar.exe (PID: 8324)
- Rar.exe (PID: 8332)
- Rar.exe (PID: 4164)
- Rar.exe (PID: 8676)
- Rar.exe (PID: 6620)
- Rar.exe (PID: 8492)
- Rar.exe (PID: 8980)
- Rar.exe (PID: 9156)
- Rar.exe (PID: 8240)
- Rar.exe (PID: 8028)
- Rar.exe (PID: 8432)
- Rar.exe (PID: 8472)
- Rar.exe (PID: 6472)
- Rar.exe (PID: 9160)
- Rar.exe (PID: 8832)
- Rar.exe (PID: 9180)
- Rar.exe (PID: 8704)
- Rar.exe (PID: 8476)
- Rar.exe (PID: 8340)
- Rar.exe (PID: 8508)
- Rar.exe (PID: 9064)
- Rar.exe (PID: 4200)
- Rar.exe (PID: 8228)
- Rar.exe (PID: 8380)
- Rar.exe (PID: 8904)
- Rar.exe (PID: 8308)
- Rar.exe (PID: 8648)
- Rar.exe (PID: 7276)
- Rar.exe (PID: 5048)
- Rar.exe (PID: 8920)
- Rar.exe (PID: 9048)
- Rar.exe (PID: 8948)
- Rar.exe (PID: 8856)
- Rar.exe (PID: 9124)
- Rar.exe (PID: 7368)
- Rar.exe (PID: 9312)
- Rar.exe (PID: 9472)
- Rar.exe (PID: 9392)
- Rar.exe (PID: 9552)
- Rar.exe (PID: 8900)
- Rar.exe (PID: 8216)
- Rar.exe (PID: 9800)
- Rar.exe (PID: 9884)
- Rar.exe (PID: 10044)
- Rar.exe (PID: 10124)
- Rar.exe (PID: 4108)
- Rar.exe (PID: 9632)
- Rar.exe (PID: 6900)
- Rar.exe (PID: 9656)
- Rar.exe (PID: 9728)
- Rar.exe (PID: 9304)
- Rar.exe (PID: 9384)
- Rar.exe (PID: 9372)
- Rar.exe (PID: 9572)
- Rar.exe (PID: 9636)
- Rar.exe (PID: 9756)
- Rar.exe (PID: 10020)
- Rar.exe (PID: 10184)
- Rar.exe (PID: 9500)
- Rar.exe (PID: 9900)
- Rar.exe (PID: 9508)
- Rar.exe (PID: 9592)
- Rar.exe (PID: 8664)
- Rar.exe (PID: 10080)
- Rar.exe (PID: 9356)
- Rar.exe (PID: 9568)
- Rar.exe (PID: 10072)
- Rar.exe (PID: 9996)
- Rar.exe (PID: 9348)
- Rar.exe (PID: 9112)
- Rar.exe (PID: 9324)
- Rar.exe (PID: 9640)
- Rar.exe (PID: 9768)
- Rar.exe (PID: 9832)
- Rar.exe (PID: 9920)
- Rar.exe (PID: 9380)
- Rar.exe (PID: 9516)
- Rar.exe (PID: 9504)
- Rar.exe (PID: 2084)
- Rar.exe (PID: 9320)
- Rar.exe (PID: 9276)
- Rar.exe (PID: 9588)
- Rar.exe (PID: 9376)
- Rar.exe (PID: 9364)
- Rar.exe (PID: 9664)
- Rar.exe (PID: 9764)
- Rar.exe (PID: 9716)
- Rar.exe (PID: 9748)
- Rar.exe (PID: 9936)
- Rar.exe (PID: 9968)
- Rar.exe (PID: 9976)
- Rar.exe (PID: 10160)
- Rar.exe (PID: 9484)
- Rar.exe (PID: 9844)
- Rar.exe (PID: 9992)
- Rar.exe (PID: 9772)
- Rar.exe (PID: 9872)
- Rar.exe (PID: 10088)
- Rar.exe (PID: 10136)
- Rar.exe (PID: 10168)
- Rar.exe (PID: 9624)
- Rar.exe (PID: 9684)
- Rar.exe (PID: 9828)
- Rar.exe (PID: 10116)
- Rar.exe (PID: 9264)
- Rar.exe (PID: 9340)
- Rar.exe (PID: 8776)
- Rar.exe (PID: 9732)
- Rar.exe (PID: 10132)
- Rar.exe (PID: 9256)
- Rar.exe (PID: 9420)
- Rar.exe (PID: 9788)
- Rar.exe (PID: 10120)
- Rar.exe (PID: 9616)
- Rar.exe (PID: 9776)
- Rar.exe (PID: 9988)
- Rar.exe (PID: 9328)
- Rar.exe (PID: 9960)
- Rar.exe (PID: 10112)
- Rar.exe (PID: 8540)
- Rar.exe (PID: 9824)
- Rar.exe (PID: 9972)
- Rar.exe (PID: 10188)
- Rar.exe (PID: 9600)
- Rar.exe (PID: 9752)
- Rar.exe (PID: 9888)
- Rar.exe (PID: 10200)
- Rar.exe (PID: 10012)
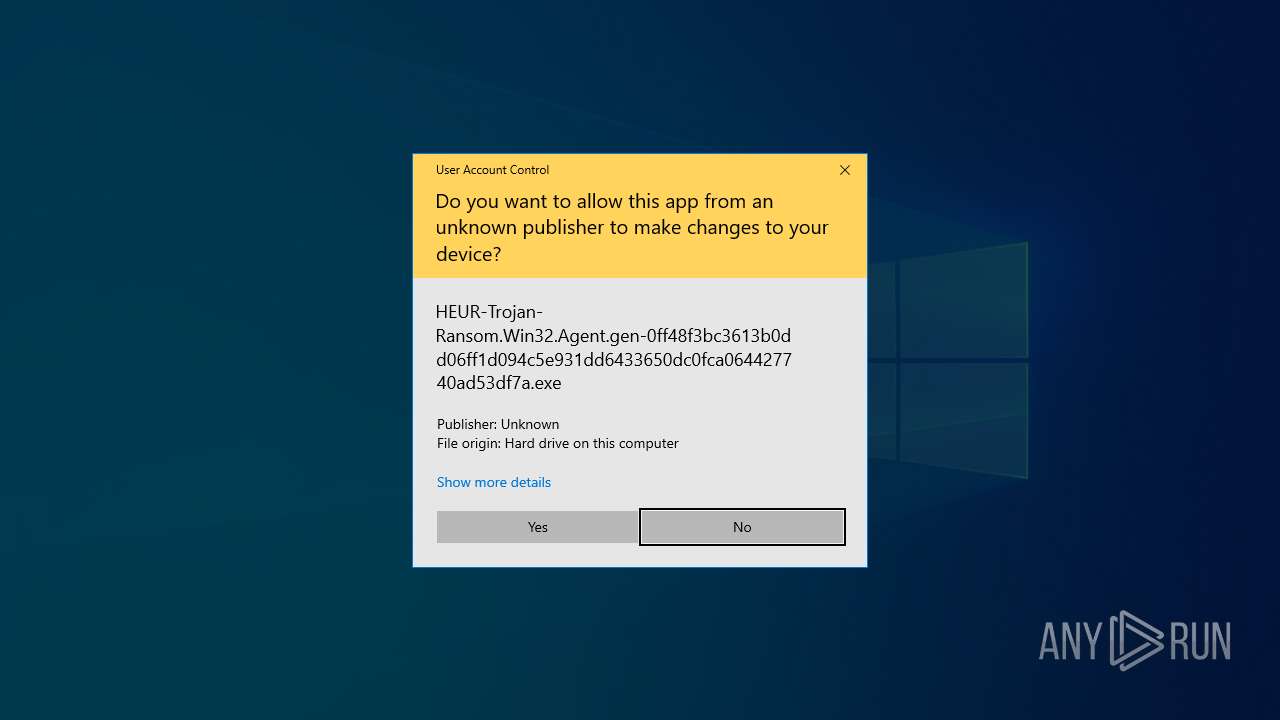
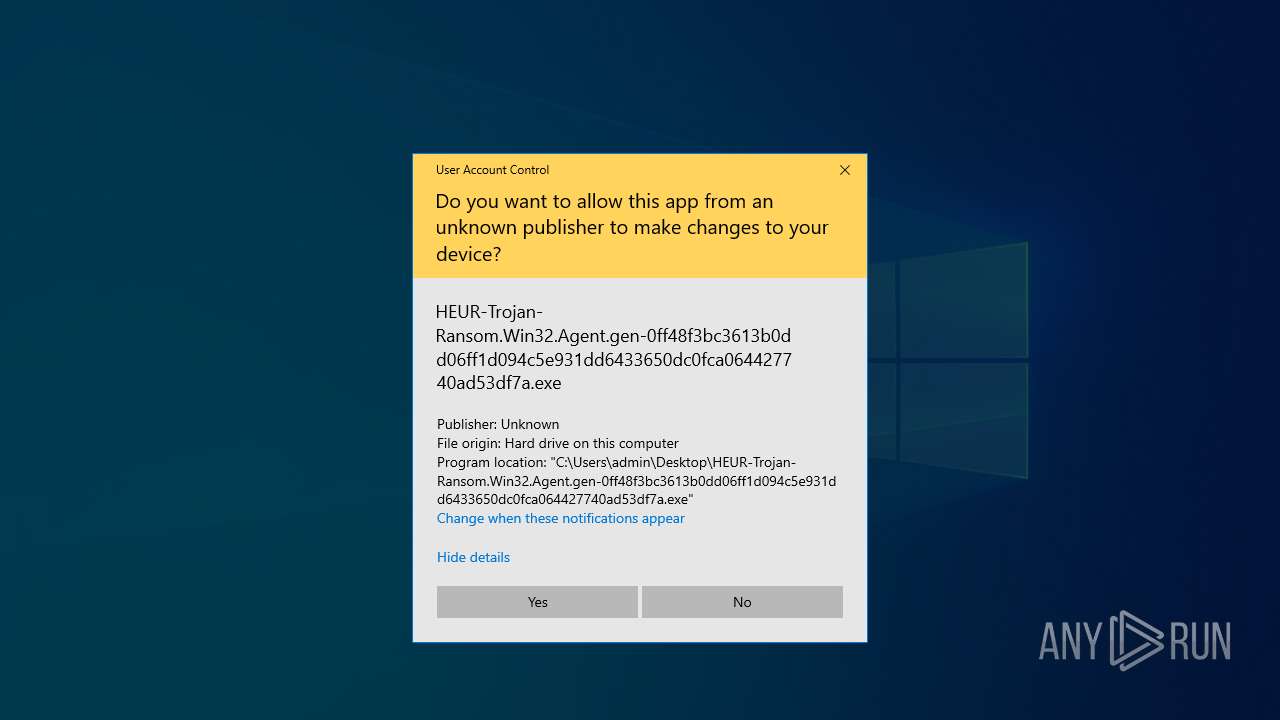
Manual execution by a user
- HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe (PID: 7808)
- notepad.exe (PID: 9316)
Process checks computer location settings
- HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe (PID: 7808)
The sample compiled with english language support
- HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe (PID: 7808)
Reads the machine GUID from the registry
- Rar.exe (PID: 7920)
- Rar.exe (PID: 8020)
- Rar.exe (PID: 8104)
- Rar.exe (PID: 8184)
- Rar.exe (PID: 2088)
- Rar.exe (PID: 5164)
- Rar.exe (PID: 5640)
- Rar.exe (PID: 2564)
- Rar.exe (PID: 7480)
- Rar.exe (PID: 7428)
- Rar.exe (PID: 1328)
- Rar.exe (PID: 6576)
- Rar.exe (PID: 7536)
- Rar.exe (PID: 1196)
- Rar.exe (PID: 7712)
- Rar.exe (PID: 7664)
- Rar.exe (PID: 7204)
- Rar.exe (PID: 8128)
- Rar.exe (PID: 5280)
- Rar.exe (PID: 1188)
- Rar.exe (PID: 3304)
- Rar.exe (PID: 7928)
- Rar.exe (PID: 7340)
- Rar.exe (PID: 6068)
- Rar.exe (PID: 5984)
- Rar.exe (PID: 6644)
- Rar.exe (PID: 3020)
- Rar.exe (PID: 7336)
- Rar.exe (PID: 7552)
- Rar.exe (PID: 5024)
- Rar.exe (PID: 7792)
- Rar.exe (PID: 780)
- Rar.exe (PID: 7596)
- Rar.exe (PID: 7948)
- Rar.exe (PID: 8012)
- Rar.exe (PID: 7912)
- Rar.exe (PID: 5380)
- Rar.exe (PID: 8176)
- Rar.exe (PID: 1228)
- Rar.exe (PID: 5772)
- Rar.exe (PID: 6744)
- Rar.exe (PID: 7416)
- Rar.exe (PID: 7468)
- Rar.exe (PID: 7356)
- Rar.exe (PID: 7508)
- Rar.exe (PID: 6148)
- Rar.exe (PID: 5260)
- Rar.exe (PID: 1244)
- Rar.exe (PID: 6480)
- Rar.exe (PID: 7216)
- Rar.exe (PID: 472)
- Rar.exe (PID: 7988)
- Rar.exe (PID: 7660)
- Rar.exe (PID: 1348)
- Rar.exe (PID: 2908)
- Rar.exe (PID: 8108)
- Rar.exe (PID: 6808)
- Rar.exe (PID: 6300)
- Rar.exe (PID: 6132)
- Rar.exe (PID: 1764)
- Rar.exe (PID: 7380)
- Rar.exe (PID: 7476)
- Rar.exe (PID: 6828)
- Rar.exe (PID: 2148)
- Rar.exe (PID: 6676)
- Rar.exe (PID: 2040)
- Rar.exe (PID: 7768)
- Rar.exe (PID: 4692)
- Rar.exe (PID: 7692)
- Rar.exe (PID: 7956)
- Rar.exe (PID: 4980)
- Rar.exe (PID: 8016)
- Rar.exe (PID: 7992)
- Rar.exe (PID: 7212)
- Rar.exe (PID: 7740)
- Rar.exe (PID: 6456)
- Rar.exe (PID: 3240)
- Rar.exe (PID: 864)
- Rar.exe (PID: 7400)
- Rar.exe (PID: 1128)
- Rar.exe (PID: 4608)
- Rar.exe (PID: 7532)
- Rar.exe (PID: 7656)
- Rar.exe (PID: 7780)
- Rar.exe (PID: 7208)
- Rar.exe (PID: 720)
- Rar.exe (PID: 5756)
- Rar.exe (PID: 7528)
- Rar.exe (PID: 5556)
- Rar.exe (PID: 8096)
- Rar.exe (PID: 5728)
- Rar.exe (PID: 5668)
- Rar.exe (PID: 7940)
- Rar.exe (PID: 5988)
- Rar.exe (PID: 7464)
- Rar.exe (PID: 7460)
- Rar.exe (PID: 6028)
- Rar.exe (PID: 2240)
- Rar.exe (PID: 744)
- Rar.exe (PID: 6268)
- Rar.exe (PID: 7628)
- Rar.exe (PID: 7624)
- Rar.exe (PID: 1096)
- Rar.exe (PID: 4152)
- Rar.exe (PID: 5228)
- Rar.exe (PID: 8072)
- Rar.exe (PID: 1748)
- Rar.exe (PID: 7884)
- Rar.exe (PID: 3900)
- Rar.exe (PID: 7020)
- Rar.exe (PID: 5868)
- Rar.exe (PID: 6112)
- Rar.exe (PID: 7348)
- Rar.exe (PID: 4112)
- Rar.exe (PID: 684)
- Rar.exe (PID: 7524)
- Rar.exe (PID: 2984)
- Rar.exe (PID: 6388)
- Rar.exe (PID: 7804)
- Rar.exe (PID: 8004)
- Rar.exe (PID: 7012)
- Rar.exe (PID: 8052)
- Rar.exe (PID: 7648)
- Rar.exe (PID: 7724)
- Rar.exe (PID: 3884)
- Rar.exe (PID: 1660)
- Rar.exe (PID: 5392)
- Rar.exe (PID: 5544)
- Rar.exe (PID: 4000)
- Rar.exe (PID: 7472)
- Rar.exe (PID: 5360)
- Rar.exe (PID: 6940)
- Rar.exe (PID: 7520)
- Rar.exe (PID: 6816)
- Rar.exe (PID: 7200)
- Rar.exe (PID: 7196)
- Rar.exe (PID: 6560)
- Rar.exe (PID: 7924)
- Rar.exe (PID: 5776)
- Rar.exe (PID: 7512)
- Rar.exe (PID: 8172)
- Rar.exe (PID: 8136)
- Rar.exe (PID: 7036)
- Rar.exe (PID: 4696)
- Rar.exe (PID: 8100)
- Rar.exe (PID: 1012)
- Rar.exe (PID: 7760)
- Rar.exe (PID: 7680)
- Rar.exe (PID: 7592)
- Rar.exe (PID: 1628)
- Rar.exe (PID: 5936)
- Rar.exe (PID: 3396)
- Rar.exe (PID: 4380)
- Rar.exe (PID: 6272)
- Rar.exe (PID: 3268)
- Rar.exe (PID: 8112)
- Rar.exe (PID: 7716)
- Rar.exe (PID: 3896)
- Rar.exe (PID: 7172)
- Rar.exe (PID: 4212)
- Rar.exe (PID: 4408)
- Rar.exe (PID: 2236)
- Rar.exe (PID: 6136)
- Rar.exe (PID: 3008)
- Rar.exe (PID: 7696)
- Rar.exe (PID: 7776)
- Rar.exe (PID: 1676)
- Rar.exe (PID: 7788)
- Rar.exe (PID: 2616)
- Rar.exe (PID: 6768)
- Rar.exe (PID: 3024)
- Rar.exe (PID: 5596)
- Rar.exe (PID: 2664)
- Rar.exe (PID: 4040)
- Rar.exe (PID: 7228)
- Rar.exe (PID: 5036)
- Rar.exe (PID: 856)
- Rar.exe (PID: 5800)
- Rar.exe (PID: 8088)
- Rar.exe (PID: 7728)
- Rar.exe (PID: 2800)
- Rar.exe (PID: 7968)
- Rar.exe (PID: 644)
- Rar.exe (PID: 7944)
- Rar.exe (PID: 8152)
- Rar.exe (PID: 2504)
- Rar.exe (PID: 6540)
- Rar.exe (PID: 1020)
- Rar.exe (PID: 7344)
- Rar.exe (PID: 7440)
- Rar.exe (PID: 6264)
- Rar.exe (PID: 4868)
- Rar.exe (PID: 2092)
- Rar.exe (PID: 5720)
- Rar.exe (PID: 7732)
- Rar.exe (PID: 7616)
- Rar.exe (PID: 7960)
- Rar.exe (PID: 6708)
- Rar.exe (PID: 8180)
- Rar.exe (PID: 8160)
- Rar.exe (PID: 924)
- Rar.exe (PID: 5204)
- Rar.exe (PID: 7224)
- Rar.exe (PID: 5600)
- Rar.exe (PID: 456)
- Rar.exe (PID: 5324)
- Rar.exe (PID: 7800)
- Rar.exe (PID: 7996)
- Rar.exe (PID: 7220)
- Rar.exe (PID: 904)
- Rar.exe (PID: 7456)
- Rar.exe (PID: 5112)
- Rar.exe (PID: 7584)
- Rar.exe (PID: 8156)
- Rar.exe (PID: 2268)
- Rar.exe (PID: 7700)
- Rar.exe (PID: 5528)
- Rar.exe (PID: 7148)
- Rar.exe (PID: 7644)
- Rar.exe (PID: 960)
- Rar.exe (PID: 1164)
- Rar.exe (PID: 5136)
- Rar.exe (PID: 7972)
- Rar.exe (PID: 2108)
- Rar.exe (PID: 7976)
- Rar.exe (PID: 6208)
- Rar.exe (PID: 6824)
- Rar.exe (PID: 6156)
- Rar.exe (PID: 7256)
- Rar.exe (PID: 1568)
- Rar.exe (PID: 6416)
- Rar.exe (PID: 2316)
- Rar.exe (PID: 736)
- Rar.exe (PID: 8024)
- Rar.exe (PID: 1276)
- Rar.exe (PID: 8132)
- Rar.exe (PID: 5892)
- Rar.exe (PID: 6040)
- Rar.exe (PID: 7412)
- Rar.exe (PID: 2772)
- Rar.exe (PID: 1240)
- Rar.exe (PID: 4188)
- Rar.exe (PID: 7612)
- Rar.exe (PID: 7180)
- Rar.exe (PID: 2332)
- Rar.exe (PID: 8060)
- Rar.exe (PID: 8168)
- Rar.exe (PID: 7248)
- Rar.exe (PID: 2152)
- Rar.exe (PID: 5400)
- Rar.exe (PID: 7688)
- Rar.exe (PID: 5008)
- Rar.exe (PID: 6876)
- Rar.exe (PID: 7084)
- Rar.exe (PID: 6584)
- Rar.exe (PID: 8148)
- Rar.exe (PID: 7544)
- Rar.exe (PID: 7420)
- Rar.exe (PID: 7184)
- Rar.exe (PID: 4688)
- Rar.exe (PID: 4892)
- Rar.exe (PID: 7608)
- Rar.exe (PID: 5200)
- Rar.exe (PID: 680)
- Rar.exe (PID: 1324)
- Rar.exe (PID: 4284)
- Rar.exe (PID: 4784)
- Rar.exe (PID: 4220)
- Rar.exe (PID: 2284)
- Rar.exe (PID: 2420)
- Rar.exe (PID: 516)
- Rar.exe (PID: 7376)
- Rar.exe (PID: 6660)
- Rar.exe (PID: 7604)
- Rar.exe (PID: 4996)
- Rar.exe (PID: 7916)
- Rar.exe (PID: 8068)
- Rar.exe (PID: 8116)
- Rar.exe (PID: 7408)
- Rar.exe (PID: 496)
- Rar.exe (PID: 7620)
- Rar.exe (PID: 1912)
- Rar.exe (PID: 6592)
- Rar.exe (PID: 8084)
- Rar.exe (PID: 7936)
- Rar.exe (PID: 2552)
- Rar.exe (PID: 6700)
- Rar.exe (PID: 7652)
- Rar.exe (PID: 4376)
- Rar.exe (PID: 7640)
- Rar.exe (PID: 3176)
- Rar.exe (PID: 4056)
- Rar.exe (PID: 7436)
- Rar.exe (PID: 8120)
- Rar.exe (PID: 7488)
- Rar.exe (PID: 4464)
- Rar.exe (PID: 6852)
- Rar.exe (PID: 4012)
- Rar.exe (PID: 7932)
- Rar.exe (PID: 6988)
- Rar.exe (PID: 7424)
- Rar.exe (PID: 6080)
- Rar.exe (PID: 7736)
- Rar.exe (PID: 7708)
- Rar.exe (PID: 4304)
- Rar.exe (PID: 3032)
- Rar.exe (PID: 6736)
- Rar.exe (PID: 5624)
- Rar.exe (PID: 6724)
- Rar.exe (PID: 3028)
- Rar.exe (PID: 8164)
- Rar.exe (PID: 8008)
- Rar.exe (PID: 6248)
- Rar.exe (PID: 6752)
- Rar.exe (PID: 7288)
- Rar.exe (PID: 5116)
- Rar.exe (PID: 7668)
- Rar.exe (PID: 6740)
- Rar.exe (PID: 2104)
- Rar.exe (PID: 7984)
- Rar.exe (PID: 4452)
- Rar.exe (PID: 3828)
- Rar.exe (PID: 7684)
- Rar.exe (PID: 7280)
- Rar.exe (PID: 5352)
- Rar.exe (PID: 7756)
- Rar.exe (PID: 976)
- Rar.exe (PID: 5408)
- Rar.exe (PID: 7104)
- Rar.exe (PID: 3800)
- Rar.exe (PID: 6468)
- Rar.exe (PID: 7964)
- Rar.exe (PID: 1812)
- Rar.exe (PID: 5956)
- Rar.exe (PID: 1388)
- Rar.exe (PID: 1040)
- Rar.exe (PID: 8076)
- Rar.exe (PID: 7556)
- Rar.exe (PID: 1804)
- Rar.exe (PID: 3620)
- Rar.exe (PID: 2780)
- Rar.exe (PID: 5172)
- Rar.exe (PID: 632)
- Rar.exe (PID: 6512)
- Rar.exe (PID: 7704)
- Rar.exe (PID: 900)
- Rar.exe (PID: 5344)
- Rar.exe (PID: 7392)
- Rar.exe (PID: 6044)
- Rar.exe (PID: 7252)
- Rar.exe (PID: 5588)
- Rar.exe (PID: 7720)
- Rar.exe (PID: 4988)
- Rar.exe (PID: 3956)
- Rar.exe (PID: 6572)
- Rar.exe (PID: 3992)
- Rar.exe (PID: 4976)
- Rar.exe (PID: 4016)
- Rar.exe (PID: 1088)
- Rar.exe (PID: 4448)
- Rar.exe (PID: 5364)
- Rar.exe (PID: 240)
- Rar.exe (PID: 7764)
- Rar.exe (PID: 7500)
- Rar.exe (PID: 7844)
- Rar.exe (PID: 7320)
- Rar.exe (PID: 668)
- Rar.exe (PID: 5744)
- Rar.exe (PID: 7232)
- Rar.exe (PID: 232)
- Rar.exe (PID: 6072)
- Rar.exe (PID: 7192)
- Rar.exe (PID: 1052)
- Rar.exe (PID: 3300)
- Rar.exe (PID: 6424)
- Rar.exe (PID: 2432)
- Rar.exe (PID: 7452)
- Rar.exe (PID: 5436)
- Rar.exe (PID: 1600)
- Rar.exe (PID: 2096)
- Rar.exe (PID: 4572)
- Rar.exe (PID: 7404)
- Rar.exe (PID: 4648)
- Rar.exe (PID: 7864)
- Rar.exe (PID: 7600)
- Rar.exe (PID: 4180)
- Rar.exe (PID: 8092)
- Rar.exe (PID: 7360)
- Rar.exe (PID: 3768)
- Rar.exe (PID: 7396)
- Rar.exe (PID: 3888)
- Rar.exe (PID: 920)
- Rar.exe (PID: 6256)
- Rar.exe (PID: 7856)
- Rar.exe (PID: 6404)
- Rar.exe (PID: 6048)
- Rar.exe (PID: 4884)
- Rar.exe (PID: 2516)
- Rar.exe (PID: 7908)
- Rar.exe (PID: 7632)
- Rar.exe (PID: 3804)
- Rar.exe (PID: 2644)
- Rar.exe (PID: 7388)
- Rar.exe (PID: 7384)
- Rar.exe (PID: 3968)
- Rar.exe (PID: 7284)
- Rar.exe (PID: 5740)
- Rar.exe (PID: 2776)
- Rar.exe (PID: 2340)
- Rar.exe (PID: 5072)
- Rar.exe (PID: 2896)
- Rar.exe (PID: 4068)
- Rar.exe (PID: 7516)
- Rar.exe (PID: 7576)
- Rar.exe (PID: 5056)
- Rar.exe (PID: 6980)
- Rar.exe (PID: 6476)
- Rar.exe (PID: 6372)
- Rar.exe (PID: 6344)
- Rar.exe (PID: 8080)
- Rar.exe (PID: 7372)
- Rar.exe (PID: 5680)
- Rar.exe (PID: 2192)
- Rar.exe (PID: 896)
- Rar.exe (PID: 4728)
- Rar.exe (PID: 1136)
- Rar.exe (PID: 5304)
- Rar.exe (PID: 8000)
- Rar.exe (PID: 6800)
- Rar.exe (PID: 7364)
- Rar.exe (PID: 8056)
- Rar.exe (PID: 7672)
- Rar.exe (PID: 1004)
- Rar.exe (PID: 3016)
- Rar.exe (PID: 5176)
- Rar.exe (PID: 2796)
- Rar.exe (PID: 6244)
- Rar.exe (PID: 5132)
- Rar.exe (PID: 8040)
- Rar.exe (PID: 7836)
- Rar.exe (PID: 3132)
- Rar.exe (PID: 7820)
- Rar.exe (PID: 6872)
- Rar.exe (PID: 7548)
- Rar.exe (PID: 4920)
- Rar.exe (PID: 6436)
- Rar.exe (PID: 8144)
- Rar.exe (PID: 968)
- Rar.exe (PID: 4528)
- Rar.exe (PID: 7840)
- Rar.exe (PID: 7752)
- Rar.exe (PID: 3100)
- Rar.exe (PID: 8064)
- Rar.exe (PID: 7816)
- Rar.exe (PID: 6384)
- Rar.exe (PID: 4756)
- Rar.exe (PID: 4120)
- Rar.exe (PID: 6656)
- Rar.exe (PID: 7824)
- Rar.exe (PID: 5384)
- Rar.exe (PID: 2288)
- Rar.exe (PID: 7880)
- Rar.exe (PID: 7176)
- Rar.exe (PID: 5256)
- Rar.exe (PID: 6392)
- Rar.exe (PID: 1452)
- Rar.exe (PID: 5796)
- Rar.exe (PID: 8036)
- Rar.exe (PID: 5952)
- Rar.exe (PID: 7980)
- Rar.exe (PID: 1852)
- Rar.exe (PID: 7144)
- Rar.exe (PID: 5084)
- Rar.exe (PID: 7000)
- Rar.exe (PID: 2692)
- Rar.exe (PID: 1184)
- Rar.exe (PID: 3124)
- Rar.exe (PID: 2568)
- Rar.exe (PID: 5188)
- Rar.exe (PID: 8140)
- Rar.exe (PID: 7860)
- Rar.exe (PID: 2064)
- Rar.exe (PID: 5232)
- Rar.exe (PID: 3012)
- Rar.exe (PID: 6712)
- Rar.exe (PID: 300)
- Rar.exe (PID: 7328)
- Rar.exe (PID: 6324)
- Rar.exe (PID: 660)
- Rar.exe (PID: 4620)
- Rar.exe (PID: 6192)
- Rar.exe (PID: 1672)
- Rar.exe (PID: 5812)
- Rar.exe (PID: 8032)
- Rar.exe (PID: 3796)
- Rar.exe (PID: 2960)
- Rar.exe (PID: 872)
- Rar.exe (PID: 5064)
- Rar.exe (PID: 7316)
- Rar.exe (PID: 6652)
- Rar.exe (PID: 6036)
- Rar.exe (PID: 6964)
- Rar.exe (PID: 4172)
- Rar.exe (PID: 2600)
- Rar.exe (PID: 4724)
- Rar.exe (PID: 6032)
- Rar.exe (PID: 7324)
- Rar.exe (PID: 6184)
- Rar.exe (PID: 536)
- Rar.exe (PID: 7540)
- Rar.exe (PID: 7636)
- Rar.exe (PID: 5960)
- Rar.exe (PID: 664)
- Rar.exe (PID: 7952)
- Rar.exe (PID: 6252)
- Rar.exe (PID: 6760)
- Rar.exe (PID: 540)
- Rar.exe (PID: 4268)
- Rar.exe (PID: 208)
- Rar.exe (PID: 7300)
- Rar.exe (PID: 8048)
- Rar.exe (PID: 672)
- Rar.exe (PID: 1272)
- Rar.exe (PID: 4228)
- Rar.exe (PID: 4336)
- Rar.exe (PID: 6960)
- Rar.exe (PID: 132)
- Rar.exe (PID: 7292)
- Rar.exe (PID: 7828)
- Rar.exe (PID: 7272)
- Rar.exe (PID: 8188)
- Rar.exe (PID: 1532)
- Rar.exe (PID: 7484)
- Rar.exe (PID: 7352)
- Rar.exe (PID: 2416)
- Rar.exe (PID: 7304)
- Rar.exe (PID: 8124)
- Rar.exe (PID: 5044)
- Rar.exe (PID: 5512)
- Rar.exe (PID: 8208)
- Rar.exe (PID: 4428)
- Rar.exe (PID: 8288)
- Rar.exe (PID: 8368)
- Rar.exe (PID: 8448)
- Rar.exe (PID: 8528)
- Rar.exe (PID: 8608)
- Rar.exe (PID: 8692)
- Rar.exe (PID: 7784)
- Rar.exe (PID: 236)
- Rar.exe (PID: 8924)
- Rar.exe (PID: 9084)
- Rar.exe (PID: 9164)
- Rar.exe (PID: 8244)
- Rar.exe (PID: 8292)
- Rar.exe (PID: 8768)
- Rar.exe (PID: 8848)
- Rar.exe (PID: 7444)
- Rar.exe (PID: 8616)
- Rar.exe (PID: 8480)
- Rar.exe (PID: 8700)
- Rar.exe (PID: 9024)
- Rar.exe (PID: 8940)
- Rar.exe (PID: 9096)
- Rar.exe (PID: 2840)
- Rar.exe (PID: 8264)
- Rar.exe (PID: 8436)
- Rar.exe (PID: 8596)
- Rar.exe (PID: 8844)
- Rar.exe (PID: 8424)
- Rar.exe (PID: 8504)
- Rar.exe (PID: 8520)
- Rar.exe (PID: 8672)
- Rar.exe (PID: 8724)
- Rar.exe (PID: 8764)
- Rar.exe (PID: 8892)
- Rar.exe (PID: 8936)
- Rar.exe (PID: 9104)
- Rar.exe (PID: 8344)
- Rar.exe (PID: 8220)
- Rar.exe (PID: 8312)
- Rar.exe (PID: 8564)
- Rar.exe (PID: 8720)
- Rar.exe (PID: 8652)
- Rar.exe (PID: 8836)
- Rar.exe (PID: 8880)
- Rar.exe (PID: 8992)
- Rar.exe (PID: 9192)
- Rar.exe (PID: 9204)
- Rar.exe (PID: 8252)
- Rar.exe (PID: 8512)
- Rar.exe (PID: 8300)
- Rar.exe (PID: 8440)
- Rar.exe (PID: 8780)
- Rar.exe (PID: 8628)
- Rar.exe (PID: 2244)
- Rar.exe (PID: 9100)
- Rar.exe (PID: 9152)
- Rar.exe (PID: 8968)
- Rar.exe (PID: 9016)
- Rar.exe (PID: 8584)
- Rar.exe (PID: 1056)
- Rar.exe (PID: 8296)
- Rar.exe (PID: 8408)
- Rar.exe (PID: 8732)
- Rar.exe (PID: 9000)
- Rar.exe (PID: 9148)
- Rar.exe (PID: 4348)
- Rar.exe (PID: 9188)
- Rar.exe (PID: 9128)
- Rar.exe (PID: 9196)
- Rar.exe (PID: 8460)
- Rar.exe (PID: 8224)
- Rar.exe (PID: 8576)
- Rar.exe (PID: 8680)
- Rar.exe (PID: 8640)
- Rar.exe (PID: 8784)
- Rar.exe (PID: 8872)
- Rar.exe (PID: 8888)
- Rar.exe (PID: 8868)
- Rar.exe (PID: 9076)
- Rar.exe (PID: 812)
- Rar.exe (PID: 8360)
- Rar.exe (PID: 5964)
- Rar.exe (PID: 8232)
- Rar.exe (PID: 8632)
- Rar.exe (PID: 8736)
- Rar.exe (PID: 8668)
- Rar.exe (PID: 8740)
- Rar.exe (PID: 8976)
- Rar.exe (PID: 9140)
- Rar.exe (PID: 8276)
- Rar.exe (PID: 8272)
- Rar.exe (PID: 8568)
- Rar.exe (PID: 9052)
- Rar.exe (PID: 8644)
- Rar.exe (PID: 8984)
- Rar.exe (PID: 7268)
- Rar.exe (PID: 8372)
- Rar.exe (PID: 9176)
- Rar.exe (PID: 7296)
- Rar.exe (PID: 8404)
- Rar.exe (PID: 8636)
- Rar.exe (PID: 8912)
- Rar.exe (PID: 8592)
- Rar.exe (PID: 8816)
- Rar.exe (PID: 8796)
- Rar.exe (PID: 8932)
- Rar.exe (PID: 8956)
- Rar.exe (PID: 9184)
- Rar.exe (PID: 8260)
- Rar.exe (PID: 8364)
- Rar.exe (PID: 8604)
- Rar.exe (PID: 8696)
- Rar.exe (PID: 8896)
- Rar.exe (PID: 9108)
- Rar.exe (PID: 8444)
- Rar.exe (PID: 8392)
- Rar.exe (PID: 8600)
- Rar.exe (PID: 8852)
- Rar.exe (PID: 7136)
- Rar.exe (PID: 8356)
- Rar.exe (PID: 8804)
- Rar.exe (PID: 8952)
- Rar.exe (PID: 9040)
- Rar.exe (PID: 8352)
- Rar.exe (PID: 3976)
- Rar.exe (PID: 9212)
- Rar.exe (PID: 8752)
- Rar.exe (PID: 8548)
- Rar.exe (PID: 8988)
- Rar.exe (PID: 8916)
- Rar.exe (PID: 7504)
- Rar.exe (PID: 9072)
- Rar.exe (PID: 6564)
- Rar.exe (PID: 8708)
- Rar.exe (PID: 8756)
- Rar.exe (PID: 8388)
- Rar.exe (PID: 8376)
- Rar.exe (PID: 8748)
- Rar.exe (PID: 8336)
- Rar.exe (PID: 7152)
- Rar.exe (PID: 8996)
- Rar.exe (PID: 6908)
- Rar.exe (PID: 8828)
- Rar.exe (PID: 8928)
- Rar.exe (PID: 8500)
- Rar.exe (PID: 8556)
- Rar.exe (PID: 8384)
- Rar.exe (PID: 8484)
- Rar.exe (PID: 8516)
- Rar.exe (PID: 8728)
- Rar.exe (PID: 7244)
- Rar.exe (PID: 9168)
- Rar.exe (PID: 5864)
- Rar.exe (PID: 8612)
- Rar.exe (PID: 9036)
- Rar.exe (PID: 8316)
- Rar.exe (PID: 6904)
- Rar.exe (PID: 5404)
- Rar.exe (PID: 8524)
- Rar.exe (PID: 8864)
- Rar.exe (PID: 8660)
- Rar.exe (PID: 9080)
- Rar.exe (PID: 9208)
- Rar.exe (PID: 8428)
- Rar.exe (PID: 6240)
- Rar.exe (PID: 9116)
- Rar.exe (PID: 8560)
- Rar.exe (PID: 9200)
- Rar.exe (PID: 8824)
- Rar.exe (PID: 8328)
- Rar.exe (PID: 8964)
- Rar.exe (PID: 8304)
- Rar.exe (PID: 8236)
- Rar.exe (PID: 8820)
- Rar.exe (PID: 6820)
- Rar.exe (PID: 8348)
- Rar.exe (PID: 4244)
- Rar.exe (PID: 8256)
- Rar.exe (PID: 8716)
- Rar.exe (PID: 7100)
- Rar.exe (PID: 9020)
- Rar.exe (PID: 7260)
- Rar.exe (PID: 8200)
- Rar.exe (PID: 8772)
- Rar.exe (PID: 8788)
- Rar.exe (PID: 1300)
- Rar.exe (PID: 9092)
- Rar.exe (PID: 4024)
- Rar.exe (PID: 8656)
- Rar.exe (PID: 8464)
- Rar.exe (PID: 7264)
- Rar.exe (PID: 4944)
- Rar.exe (PID: 8456)
- Rar.exe (PID: 8400)
- Rar.exe (PID: 9032)
- Rar.exe (PID: 8468)
- Rar.exe (PID: 8684)
- Rar.exe (PID: 4208)
- Rar.exe (PID: 6612)
- Rar.exe (PID: 8488)
- Rar.exe (PID: 4276)
- Rar.exe (PID: 8624)
- Rar.exe (PID: 9060)
- Rar.exe (PID: 8972)
- Rar.exe (PID: 8396)
- Rar.exe (PID: 9056)
- Rar.exe (PID: 8884)
- Rar.exe (PID: 8320)
- Rar.exe (PID: 8840)
- Rar.exe (PID: 9132)
- Rar.exe (PID: 8544)
- Rar.exe (PID: 8248)
- Rar.exe (PID: 8204)
- Rar.exe (PID: 9068)
- Rar.exe (PID: 8808)
- Rar.exe (PID: 9144)
- Rar.exe (PID: 5308)
- Rar.exe (PID: 8744)
- Rar.exe (PID: 8268)
- Rar.exe (PID: 2408)
- Rar.exe (PID: 8324)
- Rar.exe (PID: 9156)
- Rar.exe (PID: 8332)
- Rar.exe (PID: 8676)
- Rar.exe (PID: 8800)
- Rar.exe (PID: 6620)
- Rar.exe (PID: 8492)
- Rar.exe (PID: 8980)
- Rar.exe (PID: 5608)
- Rar.exe (PID: 9160)
- Rar.exe (PID: 8960)
- Rar.exe (PID: 8832)
- Rar.exe (PID: 8196)
- Rar.exe (PID: 8028)
- Rar.exe (PID: 8432)
- Rar.exe (PID: 8240)
- Rar.exe (PID: 444)
- Rar.exe (PID: 8472)
- Rar.exe (PID: 9008)
- Rar.exe (PID: 6472)
- Rar.exe (PID: 8908)
- Rar.exe (PID: 4200)
- Rar.exe (PID: 9180)
- Rar.exe (PID: 8704)
- Rar.exe (PID: 8944)
- Rar.exe (PID: 8476)
- Rar.exe (PID: 4308)
- Rar.exe (PID: 8508)
- Rar.exe (PID: 3760)
- Rar.exe (PID: 9064)
- Rar.exe (PID: 8712)
- Rar.exe (PID: 8340)
- Rar.exe (PID: 8648)
- Rar.exe (PID: 8792)
- Rar.exe (PID: 8228)
- Rar.exe (PID: 8580)
- Rar.exe (PID: 8536)
- Rar.exe (PID: 8380)
- Rar.exe (PID: 8496)
- Rar.exe (PID: 9172)
- Rar.exe (PID: 7276)
- Rar.exe (PID: 8688)
- Rar.exe (PID: 8308)
- Rar.exe (PID: 8904)
- Rar.exe (PID: 5048)
- Rar.exe (PID: 6228)
- Rar.exe (PID: 4932)
- Rar.exe (PID: 8812)
- Rar.exe (PID: 8920)
- Rar.exe (PID: 9048)
- Rar.exe (PID: 9124)
- Rar.exe (PID: 9088)
- Rar.exe (PID: 8856)
- Rar.exe (PID: 8532)
- Rar.exe (PID: 9232)
- Rar.exe (PID: 7368)
- Rar.exe (PID: 9472)
- Rar.exe (PID: 9392)
- Rar.exe (PID: 9552)
- Rar.exe (PID: 8216)
- Rar.exe (PID: 8412)
- Rar.exe (PID: 9312)
- Rar.exe (PID: 9712)
- Rar.exe (PID: 9800)
- Rar.exe (PID: 9884)
- Rar.exe (PID: 9964)
- Rar.exe (PID: 10044)
- Rar.exe (PID: 4108)
- Rar.exe (PID: 10124)
- Rar.exe (PID: 10204)
- Rar.exe (PID: 9632)
- Rar.exe (PID: 9304)
- Rar.exe (PID: 9468)
- Rar.exe (PID: 10104)
- Rar.exe (PID: 9548)
- Rar.exe (PID: 9656)
- Rar.exe (PID: 9896)
- Rar.exe (PID: 9728)
- Rar.exe (PID: 9812)
- Rar.exe (PID: 10028)
- Rar.exe (PID: 10180)
- Rar.exe (PID: 6900)
- Rar.exe (PID: 9284)
- Rar.exe (PID: 9372)
- Rar.exe (PID: 9500)
- Rar.exe (PID: 9636)
- Rar.exe (PID: 9756)
- Rar.exe (PID: 10020)
- Rar.exe (PID: 9980)
- Rar.exe (PID: 10184)
- Rar.exe (PID: 10208)
- Rar.exe (PID: 9280)
- Rar.exe (PID: 9012)
- Rar.exe (PID: 9900)
- Rar.exe (PID: 9876)
- Rar.exe (PID: 9508)
- Rar.exe (PID: 9672)
- Rar.exe (PID: 9792)
- Rar.exe (PID: 9940)
- Rar.exe (PID: 10060)
- Rar.exe (PID: 10080)
- Rar.exe (PID: 8664)
- Rar.exe (PID: 9356)
- Rar.exe (PID: 9620)
- Rar.exe (PID: 9568)
- Rar.exe (PID: 9644)
- Rar.exe (PID: 8876)
- Rar.exe (PID: 9996)
- Rar.exe (PID: 10172)
- Rar.exe (PID: 9112)
- Rar.exe (PID: 9324)
- Rar.exe (PID: 9440)
- Rar.exe (PID: 9720)
- Rar.exe (PID: 9520)
- Rar.exe (PID: 9768)
- Rar.exe (PID: 9832)
- Rar.exe (PID: 9348)
- Rar.exe (PID: 9516)
- Rar.exe (PID: 9920)
- Rar.exe (PID: 10156)
- Rar.exe (PID: 9276)
- Rar.exe (PID: 2084)
- Rar.exe (PID: 9504)
- Rar.exe (PID: 9588)
- Rar.exe (PID: 9944)
- Rar.exe (PID: 9936)
- Rar.exe (PID: 10008)
- Rar.exe (PID: 10032)
- Rar.exe (PID: 9364)
- Rar.exe (PID: 10228)
- Rar.exe (PID: 9664)
- Rar.exe (PID: 9376)
- Rar.exe (PID: 9764)
- Rar.exe (PID: 9748)
- Rar.exe (PID: 10052)
- Rar.exe (PID: 9968)
- Rar.exe (PID: 10148)
- Rar.exe (PID: 9976)
- Rar.exe (PID: 10160)
- Rar.exe (PID: 9336)
- Rar.exe (PID: 9484)
- Rar.exe (PID: 9476)
- Rar.exe (PID: 9480)
- Rar.exe (PID: 9852)
- Rar.exe (PID: 9992)
- Rar.exe (PID: 9716)
- Rar.exe (PID: 9872)
- Rar.exe (PID: 9432)
- Rar.exe (PID: 9492)
- Rar.exe (PID: 9772)
- Rar.exe (PID: 9924)
- Rar.exe (PID: 10136)
- Rar.exe (PID: 10088)
- Rar.exe (PID: 10168)
- Rar.exe (PID: 9272)
- Rar.exe (PID: 9340)
- Rar.exe (PID: 10116)
- Rar.exe (PID: 9684)
- Rar.exe (PID: 9624)
- Rar.exe (PID: 9828)
- Rar.exe (PID: 10140)
- Rar.exe (PID: 9264)
- Rar.exe (PID: 5156)
- Rar.exe (PID: 8776)
- Rar.exe (PID: 9292)
- Rar.exe (PID: 9732)
- Rar.exe (PID: 9880)
- Rar.exe (PID: 10132)
- Rar.exe (PID: 9256)
- Rar.exe (PID: 9228)
- Rar.exe (PID: 9420)
- Rar.exe (PID: 9652)
- Rar.exe (PID: 2392)
- Rar.exe (PID: 9804)
- Rar.exe (PID: 9268)
- Rar.exe (PID: 9496)
- Rar.exe (PID: 9260)
- Rar.exe (PID: 9616)
- Rar.exe (PID: 9776)
- Rar.exe (PID: 9988)
- Rar.exe (PID: 10120)
- Rar.exe (PID: 9328)
- Rar.exe (PID: 9612)
- Rar.exe (PID: 9608)
- Rar.exe (PID: 9960)
- Rar.exe (PID: 9840)
- Rar.exe (PID: 10036)
- Rar.exe (PID: 10144)
- Rar.exe (PID: 8540)
- Rar.exe (PID: 9352)
- Rar.exe (PID: 9972)
- Rar.exe (PID: 9824)
- Rar.exe (PID: 9740)
- Rar.exe (PID: 10188)
- Rar.exe (PID: 9460)
- Rar.exe (PID: 10176)
- Rar.exe (PID: 9700)
- Rar.exe (PID: 9240)
- Rar.exe (PID: 9600)
- Rar.exe (PID: 9628)
- Rar.exe (PID: 9752)
- Rar.exe (PID: 9888)
- Rar.exe (PID: 10200)
- Rar.exe (PID: 9224)
Creates files or folders in the user directory
- Rar.exe (PID: 8104)
- Rar.exe (PID: 8184)
- Rar.exe (PID: 5164)
- Rar.exe (PID: 5640)
- Rar.exe (PID: 2564)
- Rar.exe (PID: 7428)
- HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe (PID: 7808)
- Rar.exe (PID: 1196)
- Rar.exe (PID: 7204)
- Rar.exe (PID: 7928)
- Rar.exe (PID: 8128)
- Rar.exe (PID: 5280)
- Rar.exe (PID: 1188)
- Rar.exe (PID: 3304)
- Rar.exe (PID: 7340)
- Rar.exe (PID: 6068)
- Rar.exe (PID: 5984)
- Rar.exe (PID: 3020)
- Rar.exe (PID: 7552)
- Rar.exe (PID: 5024)
- Rar.exe (PID: 7792)
- Rar.exe (PID: 780)
- Rar.exe (PID: 7596)
- Rar.exe (PID: 7948)
- Rar.exe (PID: 7912)
- Rar.exe (PID: 5380)
- Rar.exe (PID: 8176)
- Rar.exe (PID: 1228)
- Rar.exe (PID: 5772)
- Rar.exe (PID: 7416)
- Rar.exe (PID: 7356)
- Rar.exe (PID: 6148)
- Rar.exe (PID: 6480)
- Rar.exe (PID: 7216)
- Rar.exe (PID: 5260)
- Rar.exe (PID: 472)
- Rar.exe (PID: 7988)
- Rar.exe (PID: 1348)
- Rar.exe (PID: 6300)
- Rar.exe (PID: 2908)
- Rar.exe (PID: 8108)
- Rar.exe (PID: 6808)
- Rar.exe (PID: 6132)
- Rar.exe (PID: 2148)
- Rar.exe (PID: 7476)
- Rar.exe (PID: 1764)
- Rar.exe (PID: 6828)
- Rar.exe (PID: 2040)
- Rar.exe (PID: 4692)
- Rar.exe (PID: 7692)
- Rar.exe (PID: 7740)
- Rar.exe (PID: 8016)
- Rar.exe (PID: 7212)
- Rar.exe (PID: 3240)
- Rar.exe (PID: 7400)
- Rar.exe (PID: 5756)
- Rar.exe (PID: 7532)
- Rar.exe (PID: 7656)
- Rar.exe (PID: 7940)
- Rar.exe (PID: 5728)
- Rar.exe (PID: 5668)
- Rar.exe (PID: 7460)
- Rar.exe (PID: 1096)
- Rar.exe (PID: 6028)
- Rar.exe (PID: 2240)
- Rar.exe (PID: 4152)
- Rar.exe (PID: 744)
- Rar.exe (PID: 7624)
- Rar.exe (PID: 5868)
- Rar.exe (PID: 7020)
- Rar.exe (PID: 4112)
- Rar.exe (PID: 7648)
- Rar.exe (PID: 8004)
- Rar.exe (PID: 7012)
- Rar.exe (PID: 8052)
- Rar.exe (PID: 1660)
- Rar.exe (PID: 4000)
- Rar.exe (PID: 3884)
- Rar.exe (PID: 6816)
- Rar.exe (PID: 5360)
- Rar.exe (PID: 6940)
- Rar.exe (PID: 7520)
- Rar.exe (PID: 7924)
- Rar.exe (PID: 7196)
- Rar.exe (PID: 6560)
- Rar.exe (PID: 8100)
- Rar.exe (PID: 8136)
- Rar.exe (PID: 3396)
- Rar.exe (PID: 7592)
- Rar.exe (PID: 5936)
- Rar.exe (PID: 6272)
- Rar.exe (PID: 3268)
- Rar.exe (PID: 4408)
- Rar.exe (PID: 2236)
- Rar.exe (PID: 3896)
- Rar.exe (PID: 7172)
- Rar.exe (PID: 4212)
- Rar.exe (PID: 6136)
- Rar.exe (PID: 7696)
- Rar.exe (PID: 7788)
- Rar.exe (PID: 1676)
- Rar.exe (PID: 3024)
- Rar.exe (PID: 2800)
- Rar.exe (PID: 5800)
- Rar.exe (PID: 7728)
- Rar.exe (PID: 644)
- Rar.exe (PID: 7944)
- Rar.exe (PID: 2504)
- Rar.exe (PID: 8152)
- Rar.exe (PID: 5720)
- Rar.exe (PID: 7440)
- Rar.exe (PID: 6264)
- Rar.exe (PID: 1020)
- Rar.exe (PID: 7732)
- Rar.exe (PID: 7616)
- Rar.exe (PID: 7960)
- Rar.exe (PID: 8180)
- Rar.exe (PID: 924)
- Rar.exe (PID: 7224)
- Rar.exe (PID: 5204)
- Rar.exe (PID: 456)
- Rar.exe (PID: 7456)
- Rar.exe (PID: 1164)
- Rar.exe (PID: 7700)
- Rar.exe (PID: 7148)
- Rar.exe (PID: 5136)
- Rar.exe (PID: 7976)
- Rar.exe (PID: 6156)
- Rar.exe (PID: 6824)
- Rar.exe (PID: 6416)
- Rar.exe (PID: 960)
- Rar.exe (PID: 8024)
- Rar.exe (PID: 5892)
- Rar.exe (PID: 7412)
- Rar.exe (PID: 7180)
- Rar.exe (PID: 4188)
- Rar.exe (PID: 2332)
- Rar.exe (PID: 8060)
- Rar.exe (PID: 1240)
- Rar.exe (PID: 8168)
- Rar.exe (PID: 7688)
- Rar.exe (PID: 7544)
- Rar.exe (PID: 7184)
- Rar.exe (PID: 6584)
- Rar.exe (PID: 8148)
- Rar.exe (PID: 680)
- Rar.exe (PID: 7420)
- Rar.exe (PID: 4892)
- Rar.exe (PID: 4284)
- Rar.exe (PID: 5200)
- Rar.exe (PID: 7608)
- Rar.exe (PID: 7376)
- Rar.exe (PID: 2420)
- Rar.exe (PID: 8116)
- Rar.exe (PID: 7604)
- Rar.exe (PID: 2552)
- Rar.exe (PID: 6700)
- Rar.exe (PID: 7932)
- Rar.exe (PID: 7488)
- Rar.exe (PID: 7436)
- Rar.exe (PID: 7424)
- Rar.exe (PID: 7736)
- Rar.exe (PID: 6724)
- Rar.exe (PID: 5116)
- Rar.exe (PID: 6248)
- Rar.exe (PID: 8164)
- Rar.exe (PID: 6740)
- Rar.exe (PID: 4452)
- Rar.exe (PID: 3828)
- Rar.exe (PID: 7984)
- Rar.exe (PID: 5408)
- Rar.exe (PID: 5352)
- Rar.exe (PID: 7104)
- Rar.exe (PID: 3800)
- Rar.exe (PID: 1812)
- Rar.exe (PID: 7556)
- Rar.exe (PID: 1388)
- Rar.exe (PID: 1040)
- Rar.exe (PID: 900)
- Rar.exe (PID: 5172)
- Rar.exe (PID: 6512)
- Rar.exe (PID: 4988)
- Rar.exe (PID: 3956)
- Rar.exe (PID: 5364)
- Rar.exe (PID: 7500)
- Rar.exe (PID: 7764)
- Rar.exe (PID: 7844)
- Rar.exe (PID: 7320)
- Rar.exe (PID: 7452)
- Rar.exe (PID: 7192)
- Rar.exe (PID: 4180)
- Rar.exe (PID: 7396)
- Rar.exe (PID: 7632)
- Rar.exe (PID: 7388)
- Rar.exe (PID: 2896)
- Rar.exe (PID: 4068)
- Rar.exe (PID: 3016)
- Rar.exe (PID: 7364)
- Rar.exe (PID: 5132)
- Rar.exe (PID: 7836)
- Rar.exe (PID: 4920)
- Rar.exe (PID: 7548)
- Rar.exe (PID: 968)
- Rar.exe (PID: 7824)
- Rar.exe (PID: 7816)
- Rar.exe (PID: 6656)
- Rar.exe (PID: 6384)
- Rar.exe (PID: 1452)
- Rar.exe (PID: 1184)
- Rar.exe (PID: 1852)
- Rar.exe (PID: 7980)
- Rar.exe (PID: 5796)
- Rar.exe (PID: 3012)
- Rar.exe (PID: 300)
- Rar.exe (PID: 5812)
- Rar.exe (PID: 4724)
- Rar.exe (PID: 872)
- Rar.exe (PID: 7540)
- Rar.exe (PID: 5960)
- Rar.exe (PID: 7324)
- Rar.exe (PID: 664)
- Rar.exe (PID: 4268)
- Rar.exe (PID: 540)
- Rar.exe (PID: 7828)
- Rar.exe (PID: 4336)
- Rar.exe (PID: 5512)
- Rar.exe (PID: 8124)
- Rar.exe (PID: 7304)
- Rar.exe (PID: 8768)
- Rar.exe (PID: 8924)
- Rar.exe (PID: 9004)
- Rar.exe (PID: 7444)
- Rar.exe (PID: 8244)
- Rar.exe (PID: 8892)
- Rar.exe (PID: 8520)
- Rar.exe (PID: 8992)
- Rar.exe (PID: 9192)
- Rar.exe (PID: 9000)
- Rar.exe (PID: 9148)
- Rar.exe (PID: 8584)
- Rar.exe (PID: 8968)
- Rar.exe (PID: 9128)
- Rar.exe (PID: 8640)
- Rar.exe (PID: 8740)
- Rar.exe (PID: 8636)
- Rar.exe (PID: 8592)
- Rar.exe (PID: 8372)
- Rar.exe (PID: 9184)
- Rar.exe (PID: 8952)
- Rar.exe (PID: 9108)
- Rar.exe (PID: 3976)
- Rar.exe (PID: 6564)
- Rar.exe (PID: 8756)
- Rar.exe (PID: 8484)
- Rar.exe (PID: 5864)
- Rar.exe (PID: 8316)
- Rar.exe (PID: 8864)
- Rar.exe (PID: 9208)
- Rar.exe (PID: 6240)
- Rar.exe (PID: 8304)
- Rar.exe (PID: 4244)
- Rar.exe (PID: 9020)
- Rar.exe (PID: 9092)
- Rar.exe (PID: 4024)
- Rar.exe (PID: 8684)
- Rar.exe (PID: 4208)
- Rar.exe (PID: 8248)
- Rar.exe (PID: 8808)
- Rar.exe (PID: 8332)
- Rar.exe (PID: 8492)
- Rar.exe (PID: 9180)
- Rar.exe (PID: 8228)
- Rar.exe (PID: 8688)
- Rar.exe (PID: 8856)
- Rar.exe (PID: 8532)
- Rar.exe (PID: 9884)
- Rar.exe (PID: 10124)
- Rar.exe (PID: 9632)
- Rar.exe (PID: 9728)
- Rar.exe (PID: 10184)
- Rar.exe (PID: 9592)
- Rar.exe (PID: 9876)
- Rar.exe (PID: 10072)
- Rar.exe (PID: 9768)
- Rar.exe (PID: 9516)
- Rar.exe (PID: 9832)
- Rar.exe (PID: 9920)
- Rar.exe (PID: 9320)
- Rar.exe (PID: 9664)
- Rar.exe (PID: 9936)
- Rar.exe (PID: 10228)
- Rar.exe (PID: 9476)
- Rar.exe (PID: 9492)
- Rar.exe (PID: 9924)
- Rar.exe (PID: 10076)
- Rar.exe (PID: 9624)
- Rar.exe (PID: 5156)
- Rar.exe (PID: 10132)
- Rar.exe (PID: 9256)
Reads the software policy settings
- slui.exe (PID: 7272)
- slui.exe (PID: 7352)
Checks proxy server information
- HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe (PID: 7808)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2020:02:04 14:55:14+00:00 |
| ArchivedFileName: | HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe |
Total processes
2 154
Monitored processes
2 020
Malicious processes
111
Suspicious processes
11
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Rar.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Rar.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Rar.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 132 | "C:\Users\admin\AppData\Local\Temp\Rar.exe" a -y -ep -inul -k -m0 -hp"j65>8Y{9mmipX>MsOJ>O0gc#h.%P:BxW" "C:\Users\admin\AppData\Local\Microsoft\OneDrive\LogoImages\532 Файл зашифрован. Пиши noallpossible@cock.li .happy new year" "C:\Users\admin\AppData\Local\Microsoft\OneDrive\LogoImages\OneDriveMedTile.contrast-black_scale-150.png" | C:\Users\admin\AppData\Local\Temp\Rar.exe | — | HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: Command line RAR Exit code: 0 Version: 5.80.0 Modules
| |||||||||||||||
| 208 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Rar.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Rar.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Rar.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | "C:\Users\admin\AppData\Local\Temp\Rar.exe" a -y -ep -inul -k -m0 -hp"l%wS$iB#lU("2uX8:IED:Q?Bh#RASx}Z" "C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\523 Файл зашифрован. Пиши noallpossible@cock.li .happy new year" "C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\QuotaCritical.png" | C:\Users\admin\AppData\Local\Temp\Rar.exe | — | HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: Command line RAR Exit code: 10 Version: 5.80.0 Modules
| |||||||||||||||
| 232 | "C:\Users\admin\AppData\Local\Temp\Rar.exe" a -y -ep -inul -k -m0 -hp"cQ>*0lfKy<>}wem@}4$@Z^)z>w3V")8O" "C:\Users\admin\AppData\Local\Microsoft\Office\SolutionPackages\4cbd178c1d90aa388a105a9925ef93e\PackageResources\OfflineFiles\374 Файл зашифрован. Пиши noallpossible@cock.li .happy new year" "C:\Users\admin\AppData\Local\Microsoft\Office\SolutionPackages\4cbd178c1d90aa388a105a9925ef93e\PackageResources\OfflineFiles\microsoft.office.smartlookup.client.pt-pt_32c9222a50a8ae17ec972499312fecb7.js" | C:\Users\admin\AppData\Local\Temp\Rar.exe | — | HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: Command line RAR Exit code: 10 Version: 5.80.0 Modules
| |||||||||||||||
| 236 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Rar.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
224 757
Read events
224 734
Write events
23
Delete events
0
Modification events
| (PID) Process: | (3156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.7z | |||
| (PID) Process: | (3156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
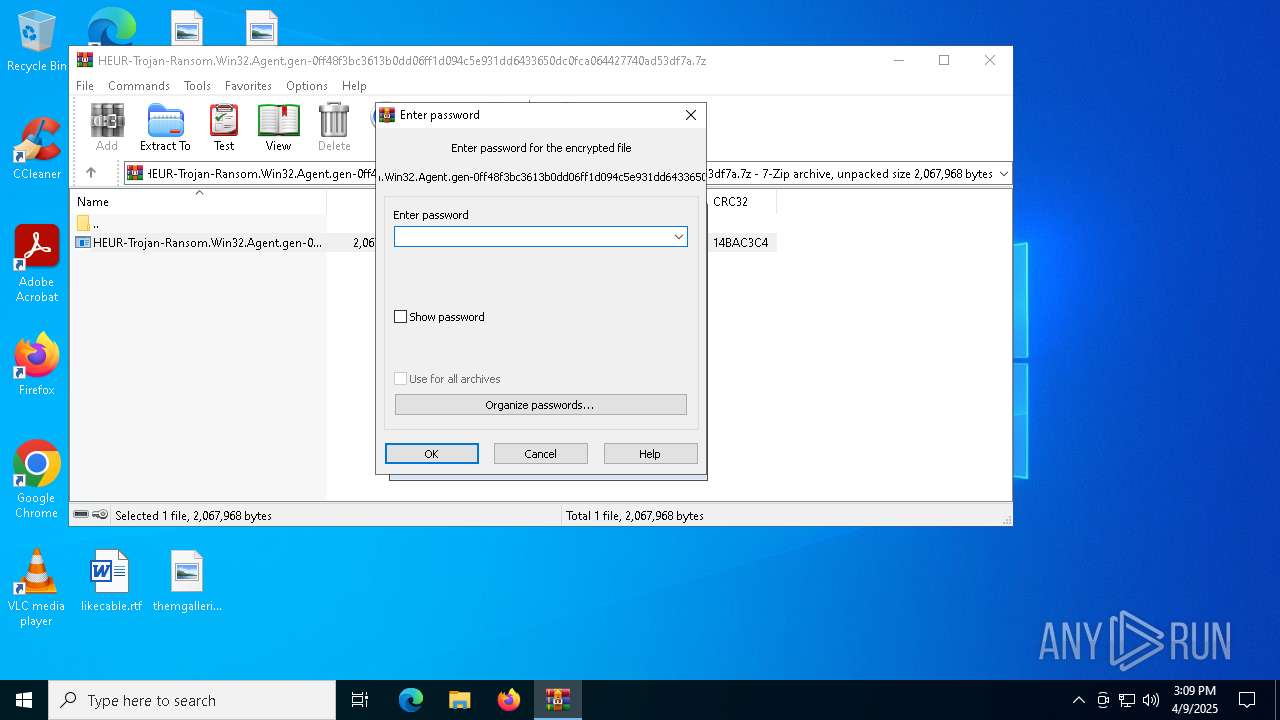
| (PID) Process: | (3156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (7808) HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion |
| Operation: | write | Name: | getsbi |
Value: matka | |||
Executable files
2
Suspicious files
742
Text files
277
Unknown types
0
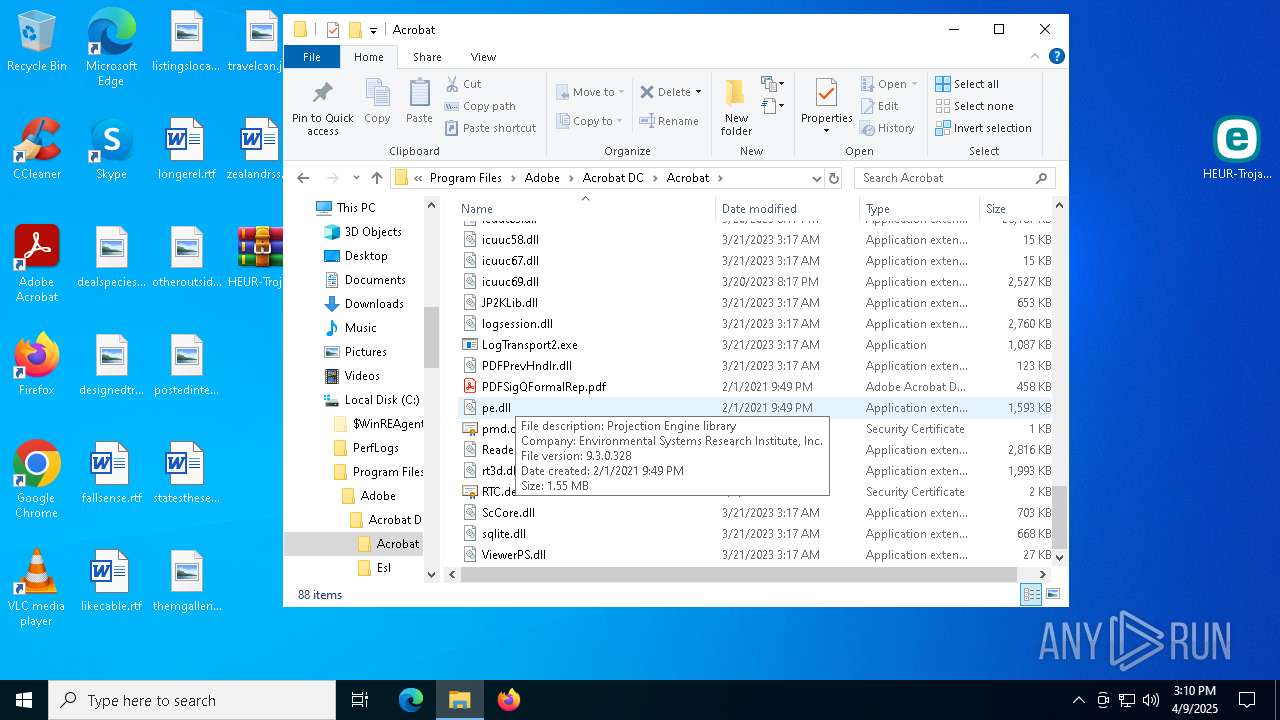
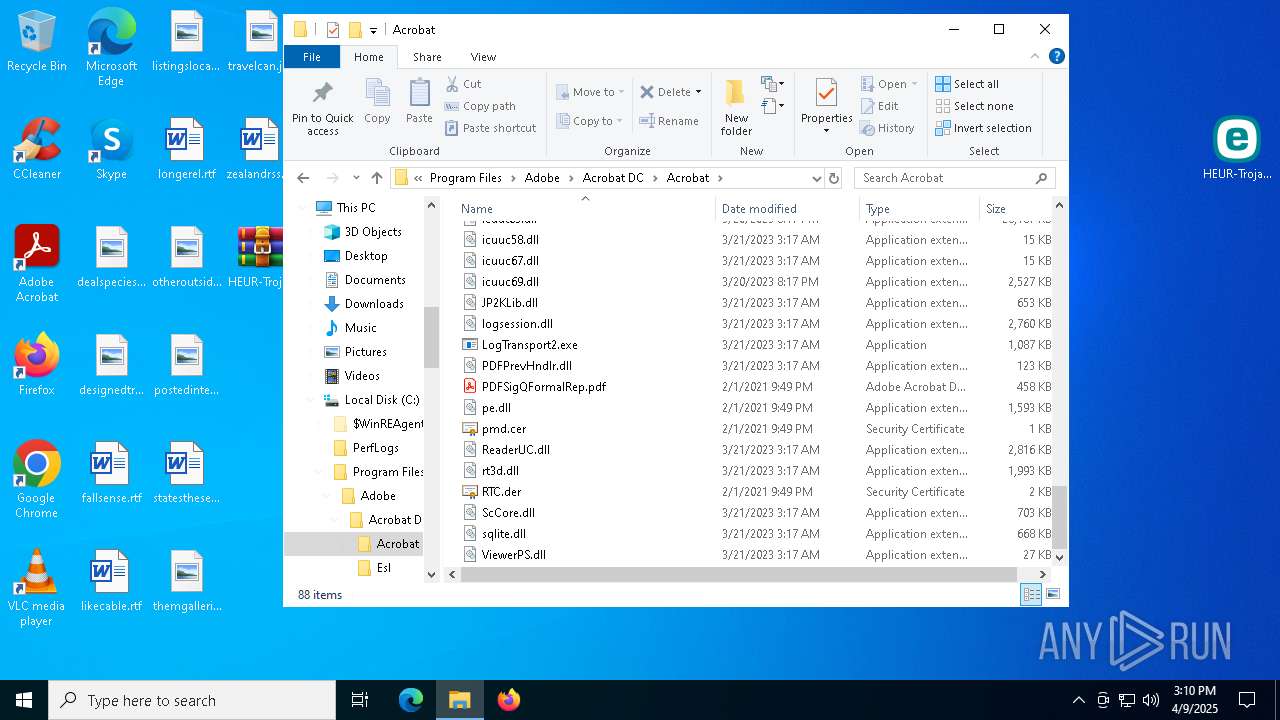
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7808 | HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe | C:\Users\admin\AppData\Local\Temp\Public.key | binary | |
MD5:35BF9F0042A7AF1613494090BF0B53B4 | SHA256:6DB94D5AD9E472B29DD35FAF5CB62AE2298D014058439AC969C8CB8D2CED18EF | |||
| 8020 | Rar.exe | C:\Users\admin\Desktop\Файл.rar | compressed | |
MD5:E63C56C7D7D4EE7D2AE75E09E2CAF787 | SHA256:BD5D5B04ED3BC7EC6BC66DF1AC79642F110358B099BC5361BAA33E569FC8E9EF | |||
| 6576 | Rar.exe | C:\Users\admin\Desktop\Файл.rar | compressed | |
MD5:03498836DB004F022F9094B9875B7C40 | SHA256:B7C6058FFA473F2644010FFE6B95E88D0D4A73A75F9F2DF26C789B4162283A8D | |||
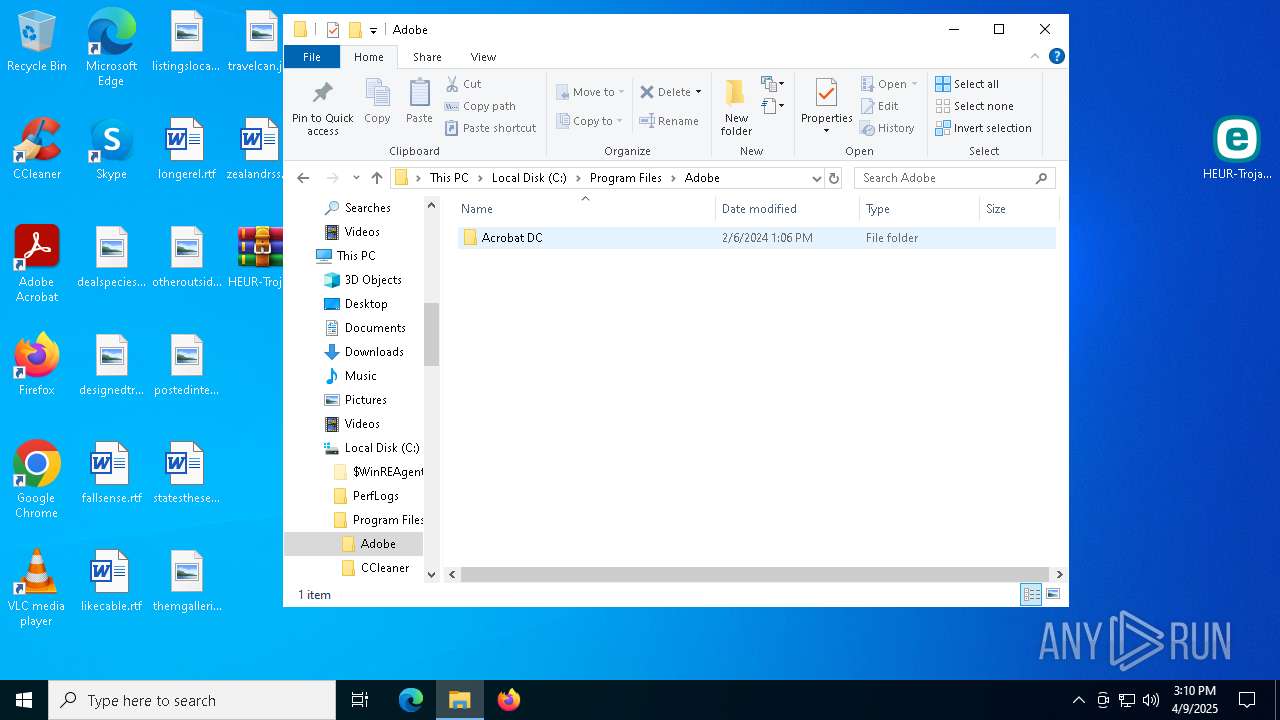
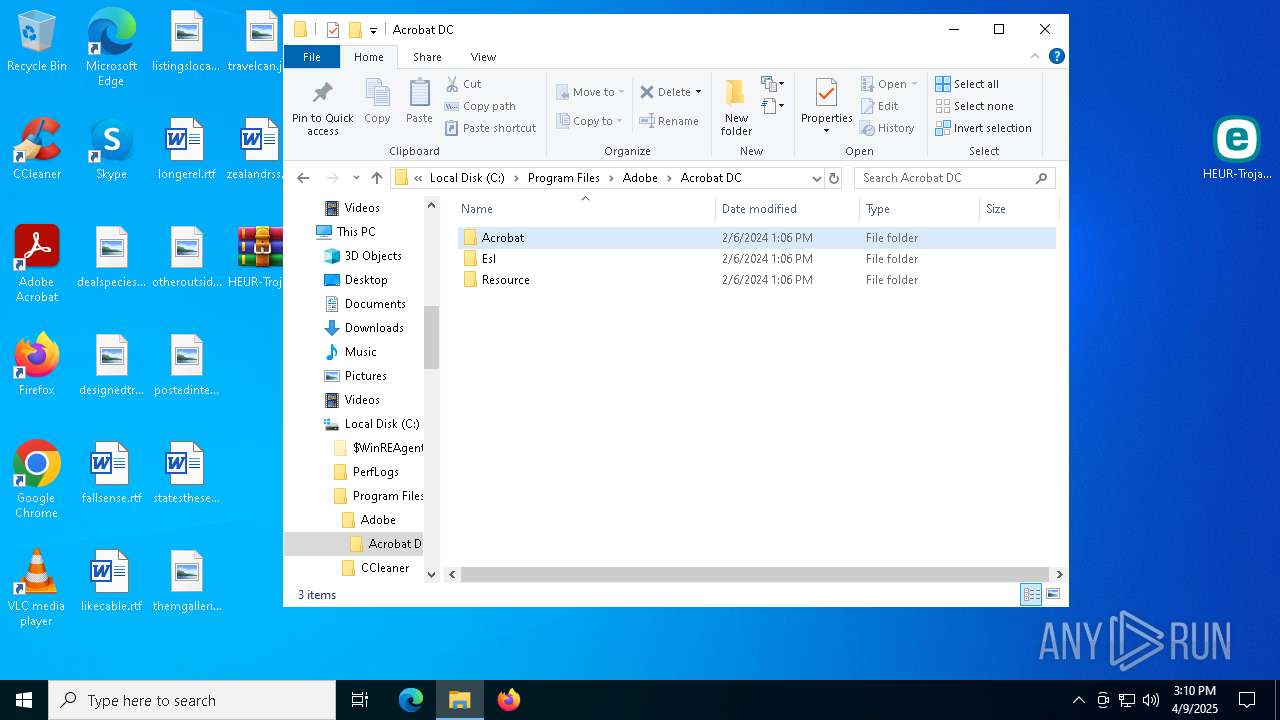
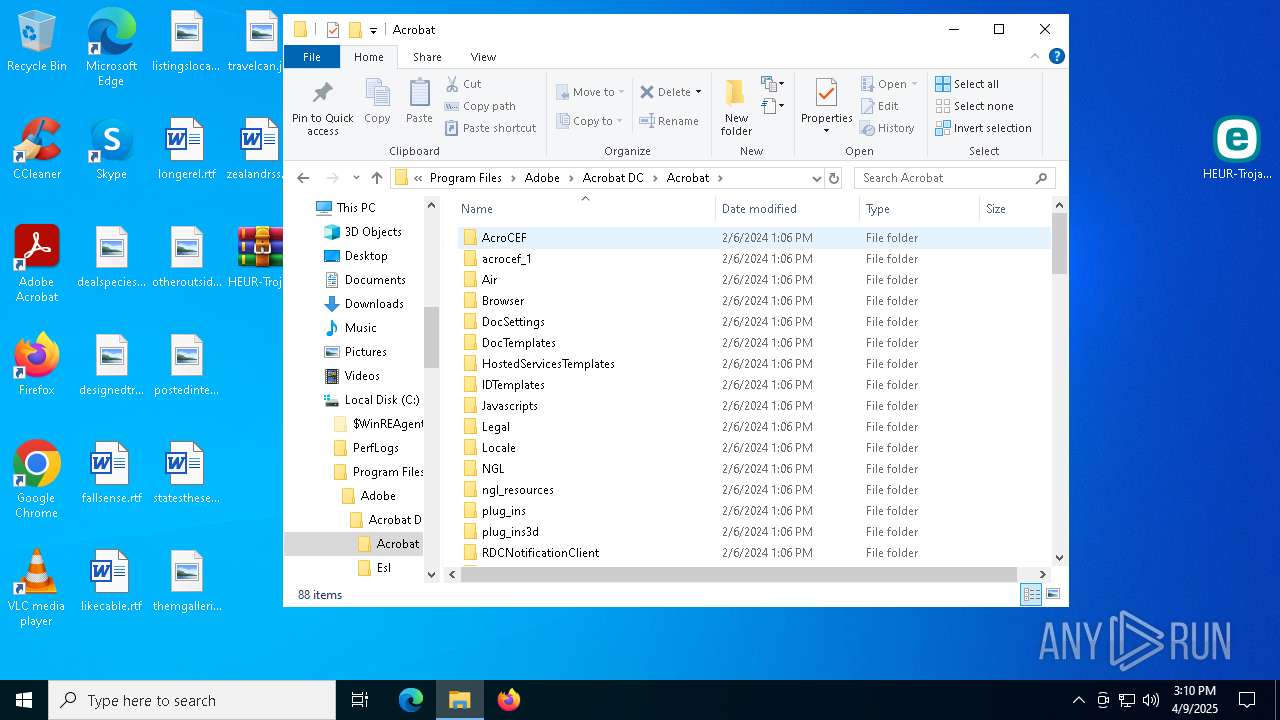
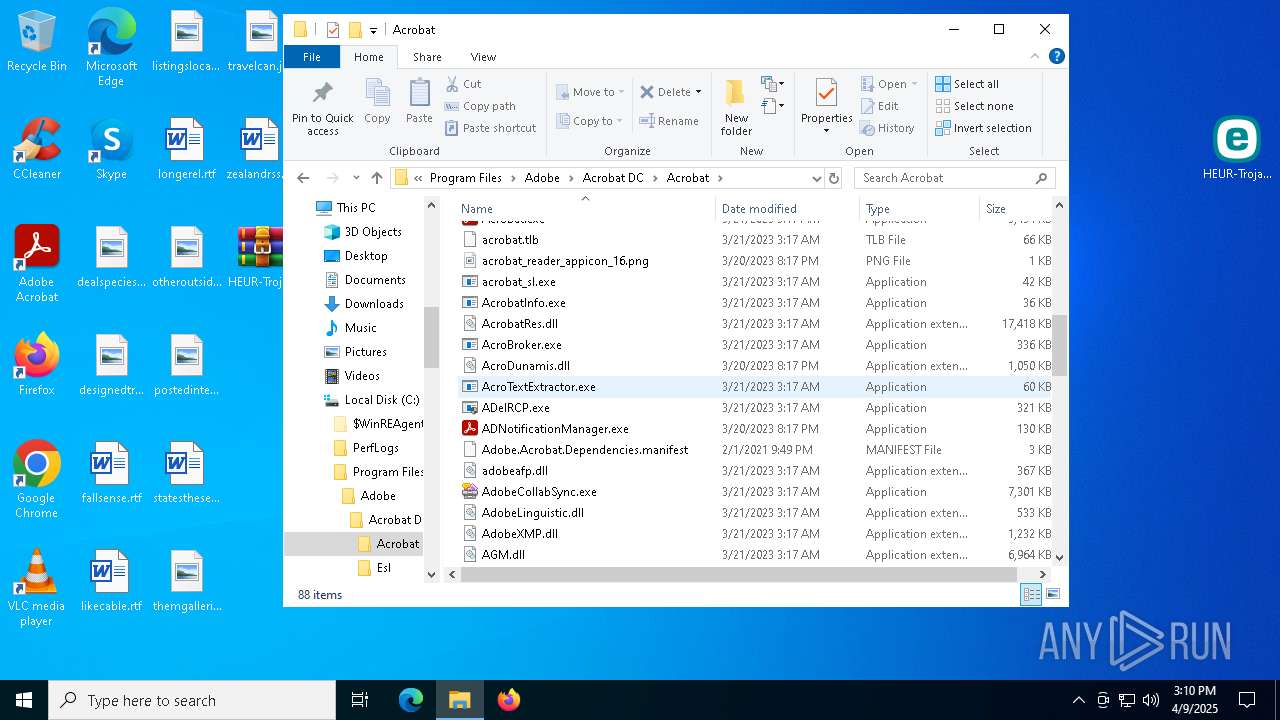
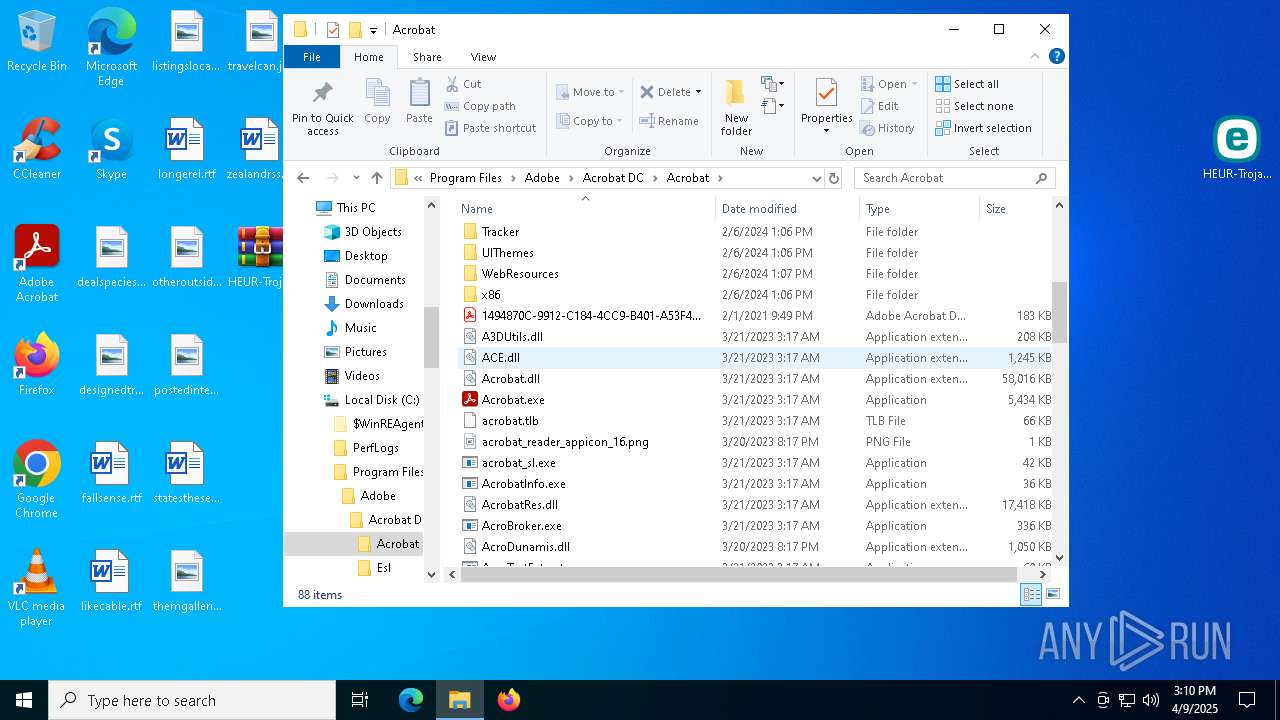
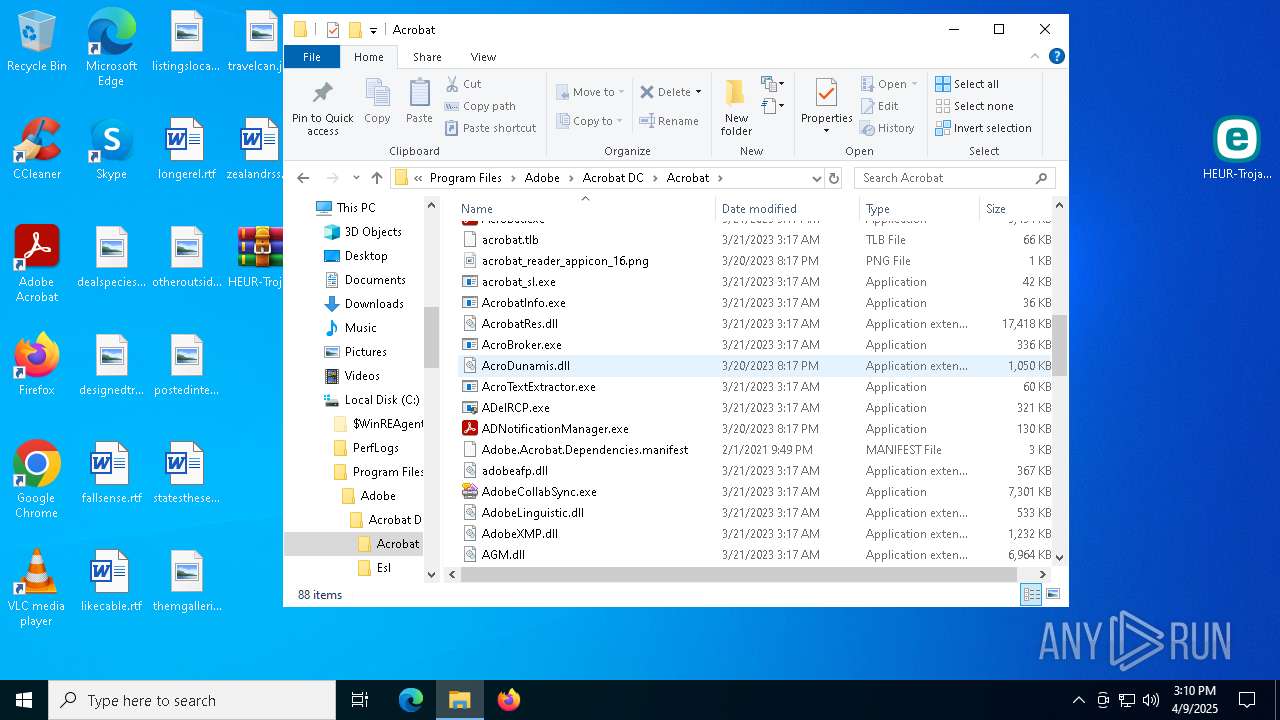
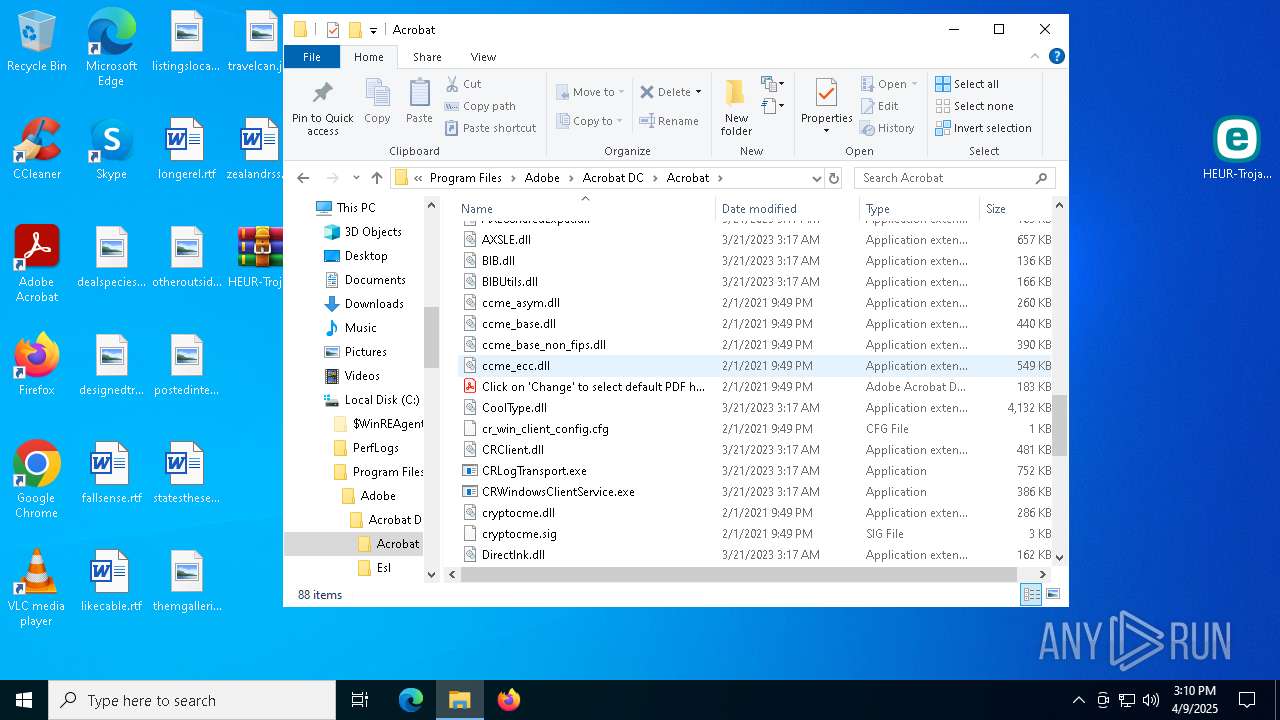
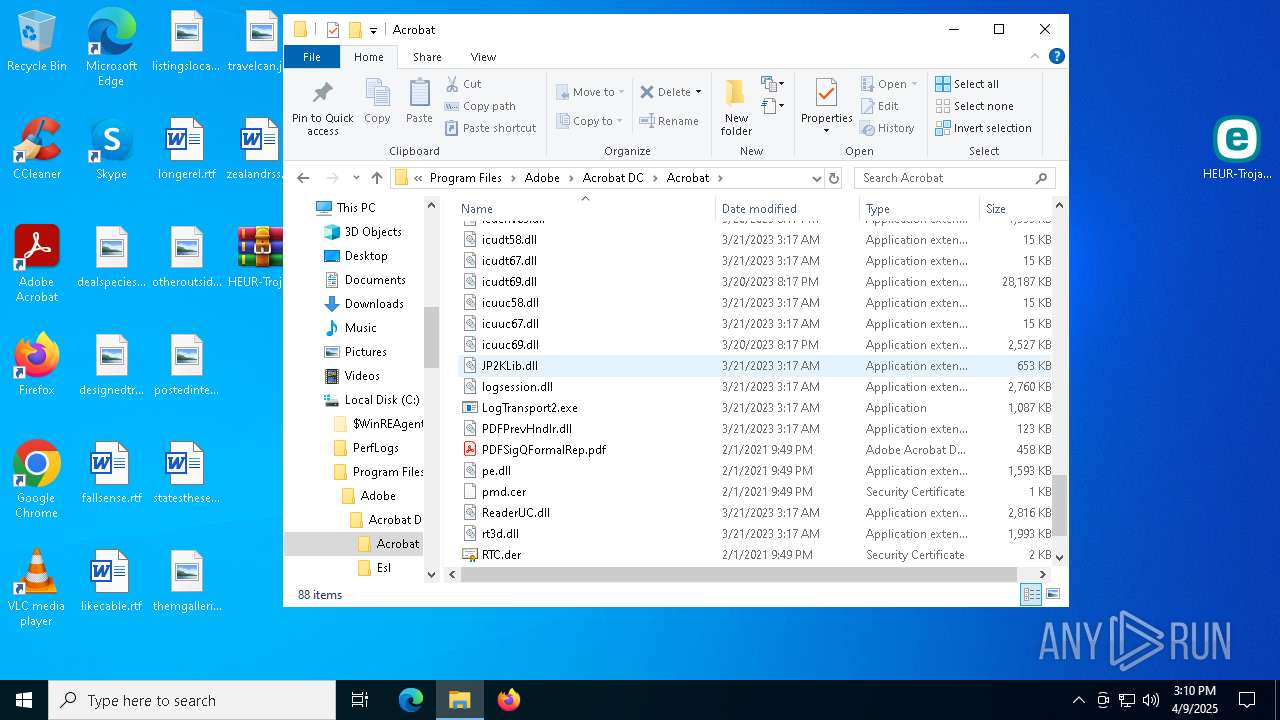
| 7808 | HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\1 Файл зашифрован. Пиши noallpossible@cock.li .happy new year | text | |
MD5:CB0536A6CACA35D740C9DC73C65DAEA0 | SHA256:59BC93EEDB9ACA7CB62A66C725CF36077D5152503A20090195A82194268F9751 | |||
| 8184 | Rar.exe | C:\Users\admin\AppData\Local\dummy\4 Файл зашифрован. Пиши noallpossible@cock.li .happy new year | compressed | |
MD5:73C4C291BB762394131D0B71E28BC0D9 | SHA256:3AEC7CC8C0B3865ACC288EE5E76F34E46D5E369CA628161F6890FDC4AC252635 | |||
| 7808 | HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe | C:\Users\admin\AppData\Local\ConnectedDevicesPlatform\2 Файл зашифрован. Пиши noallpossible@cock.li .happy new year | text | |
MD5:C727E5E1185902DE95311275A44CE6F7 | SHA256:8EEC34CAA127F7F55E3080EEA351598A07CD861DB02CADED089B147ACB993388 | |||
| 2088 | Rar.exe | C:\Users\admin\AppData\Local\dummy\6 Файл зашифрован. Пиши noallpossible@cock.li .happy new year | compressed | |
MD5:96F7ED3371D3BFB3353CCC2280AC1487 | SHA256:8CBF90A71747ECF6258C9FADAD6946D9B923F4EA40B2DB71A6CFC7FD3943A5AD | |||
| 5164 | Rar.exe | C:\Users\admin\AppData\Local\dummy\5 Файл зашифрован. Пиши noallpossible@cock.li .happy new year | compressed | |
MD5:88FB7BC3A993E94B6785D7E3C3985A8B | SHA256:939412990D5322B7EE2B94829D91DDB2245979D1A5B75D7367EDB12B10DBDA32 | |||
| 5640 | Rar.exe | C:\Users\admin\AppData\Local\ElevatedDiagnostics\3243677927\2021090614.000\7 Файл зашифрован. Пиши noallpossible@cock.li .happy new year | compressed | |
MD5:0E6D439CB731DF332CCFF9409378F60E | SHA256:2141CBC9B14FA4A9B5E50CFFED5CB76DC094B7EAA49DA624DA5EA6EFC25AA857 | |||
| 7536 | Rar.exe | C:\Users\admin\Desktop\Файл.rar | compressed | |
MD5:0206ED43C2AD34F43DD9A2E86F70434C | SHA256:B0C53FE5F743D22FDEAE840590A6B17F5C2C33EA54F92D6F7F1EC1EE7259D16A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
26
DNS requests
19
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7968 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7968 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7808 | HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe | GET | 200 | 142.250.185.195:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
7808 | HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe | GET | 200 | 142.250.185.195:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1196 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.76:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potential Corporate Privacy Violation | ET INFO IP Check Domain (iplogger .org in DNS Lookup) |
7808 | HEUR-Trojan-Ransom.Win32.Agent.gen-0ff48f3bc3613b0dd06ff1d094c5e931dd6433650dc0fca064427740ad53df7a.exe | Potential Corporate Privacy Violation | ET INFO IP Check Domain (iplogger .org in TLS SNI) |