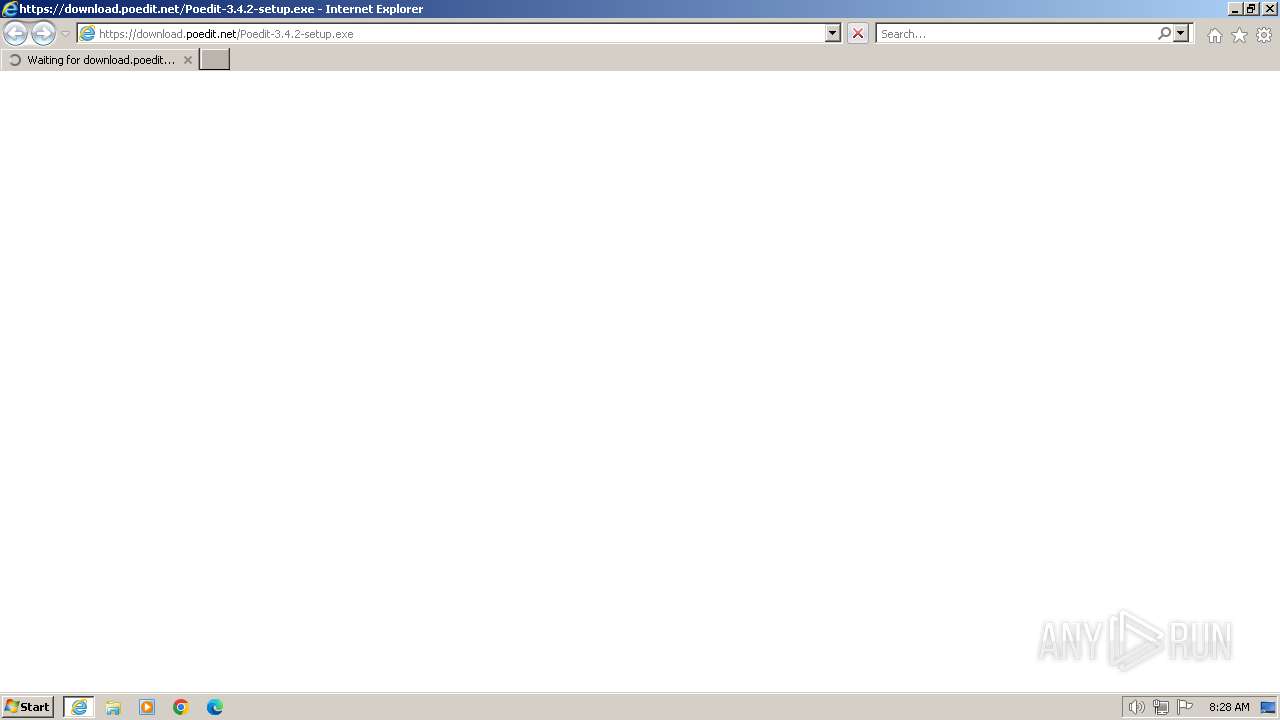
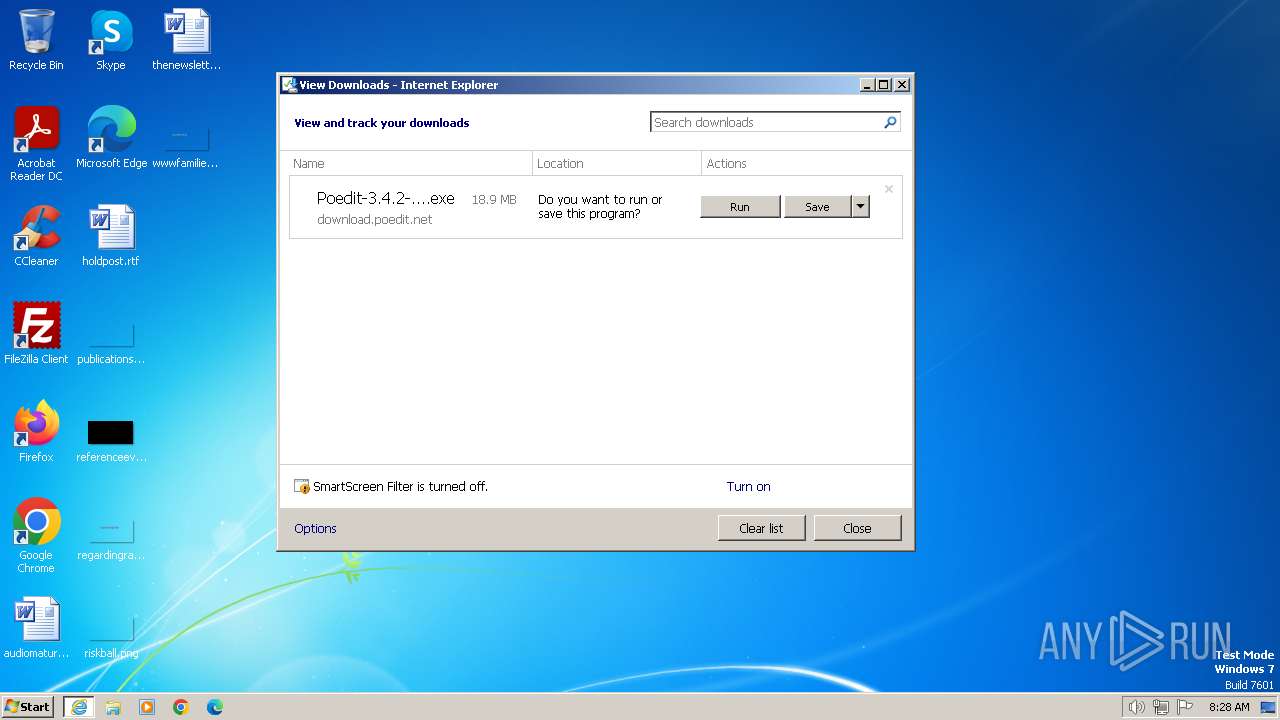
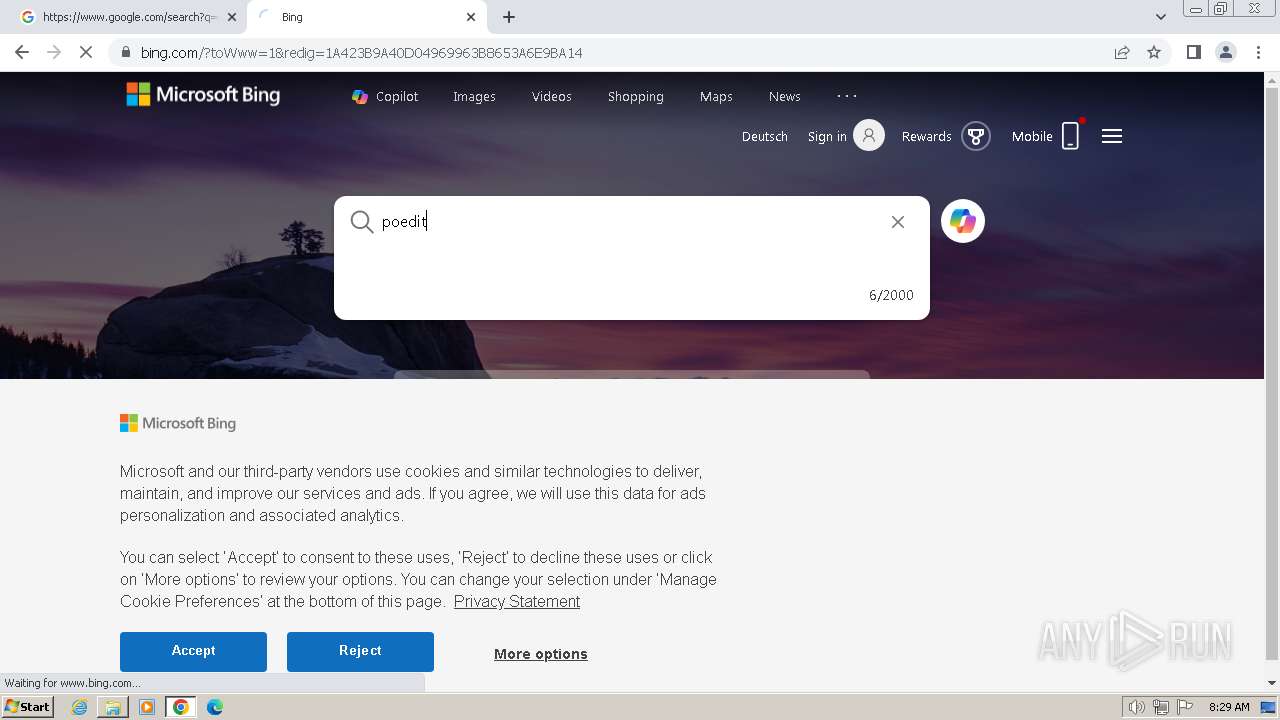
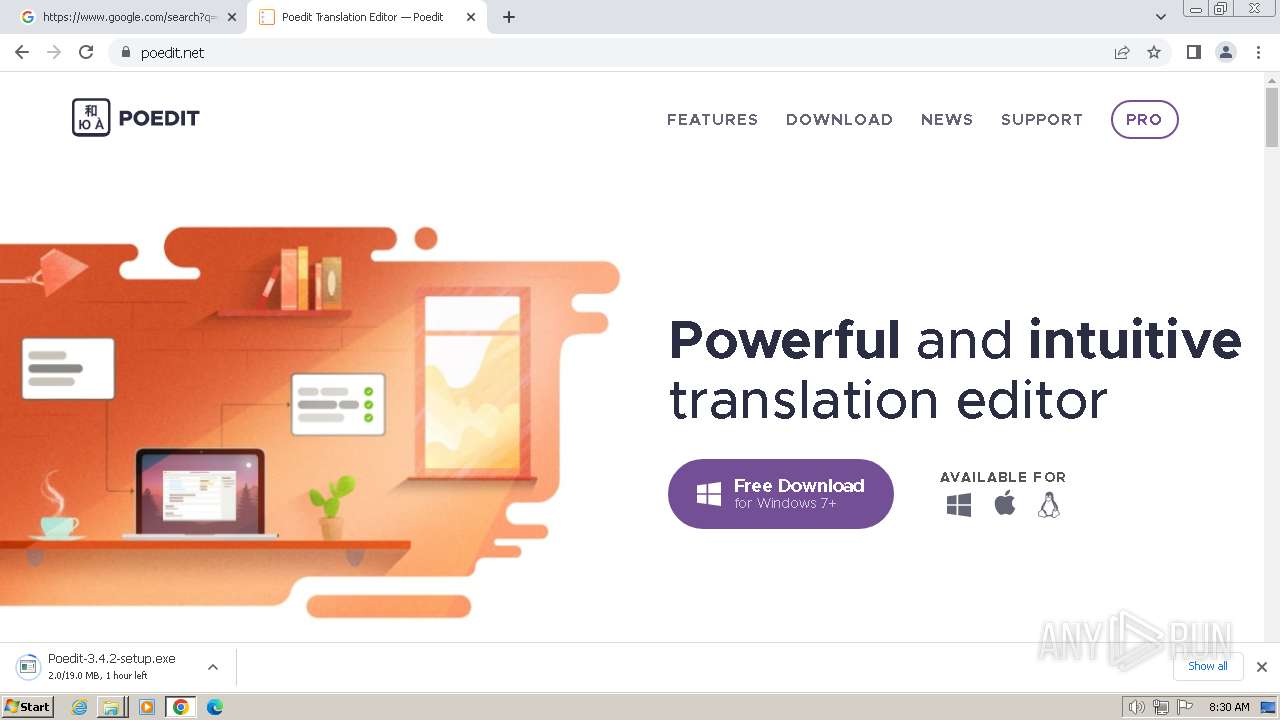
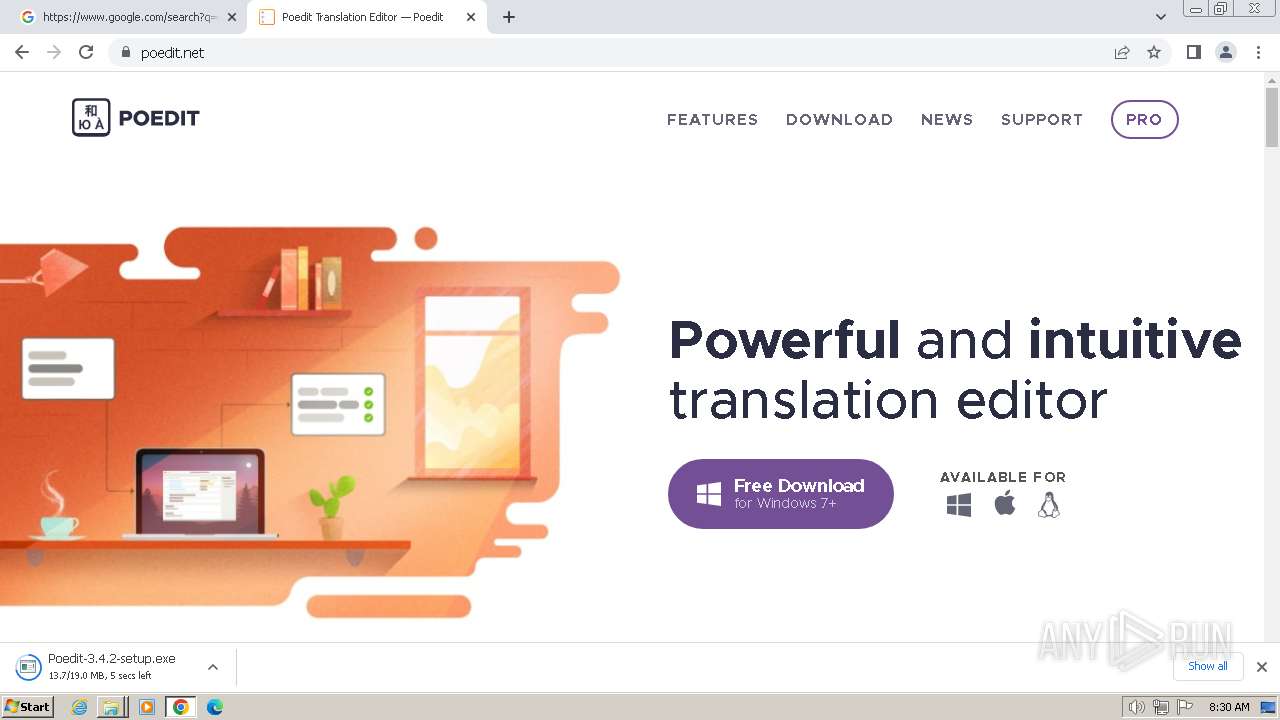
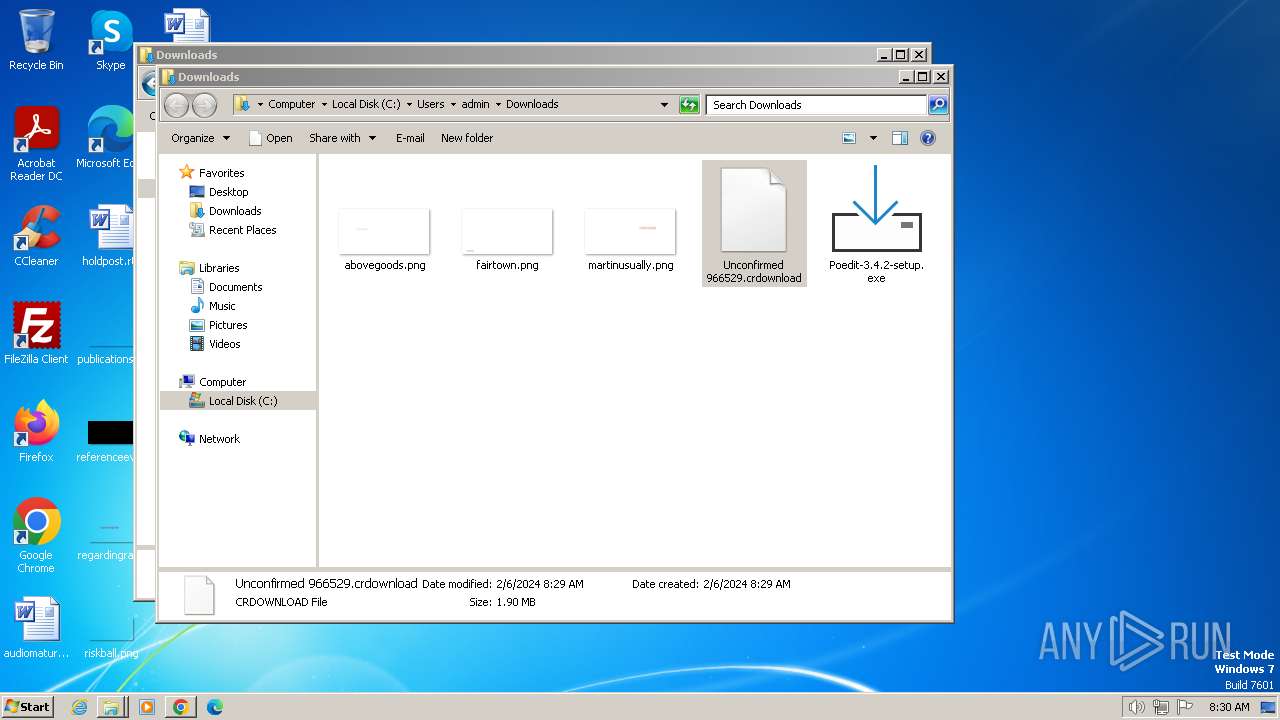
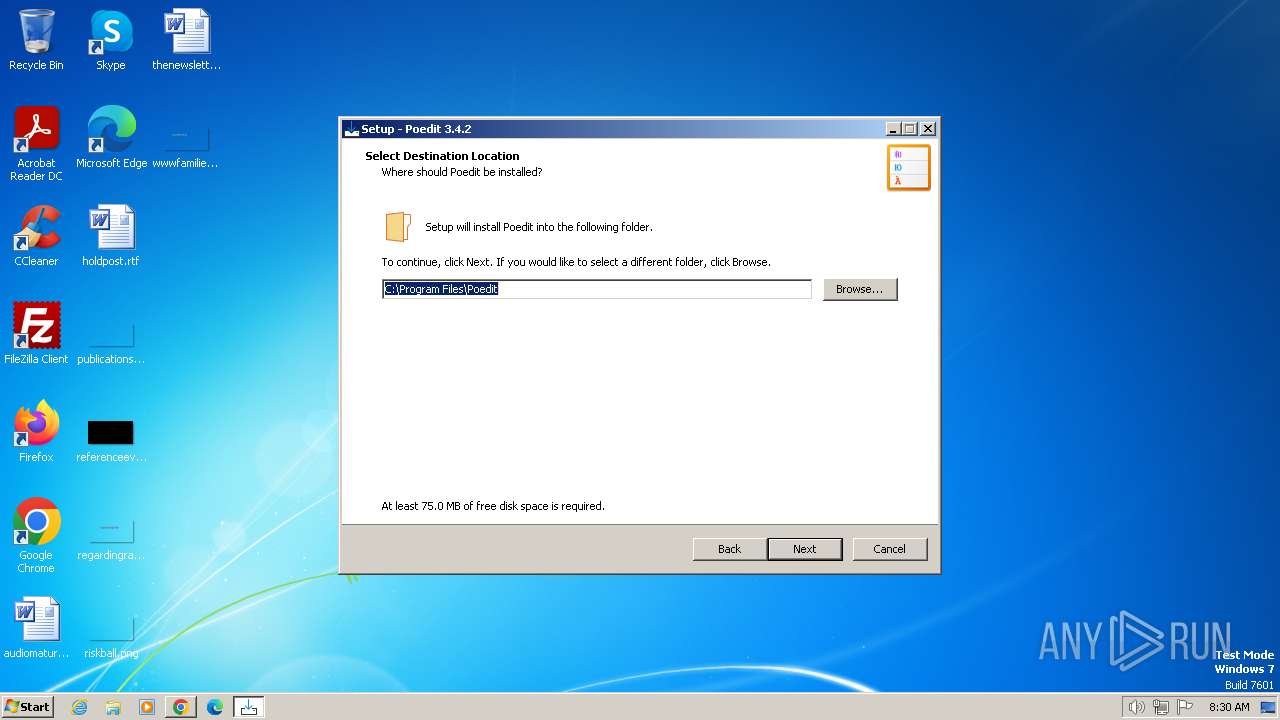
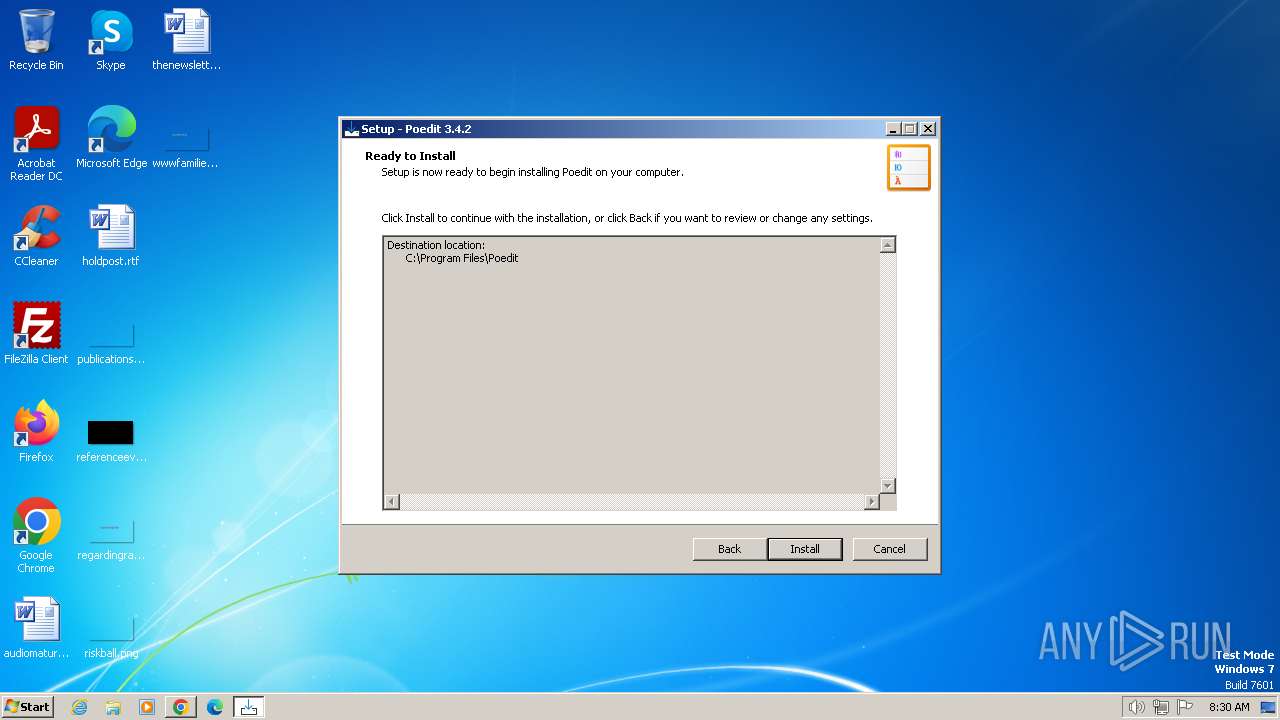
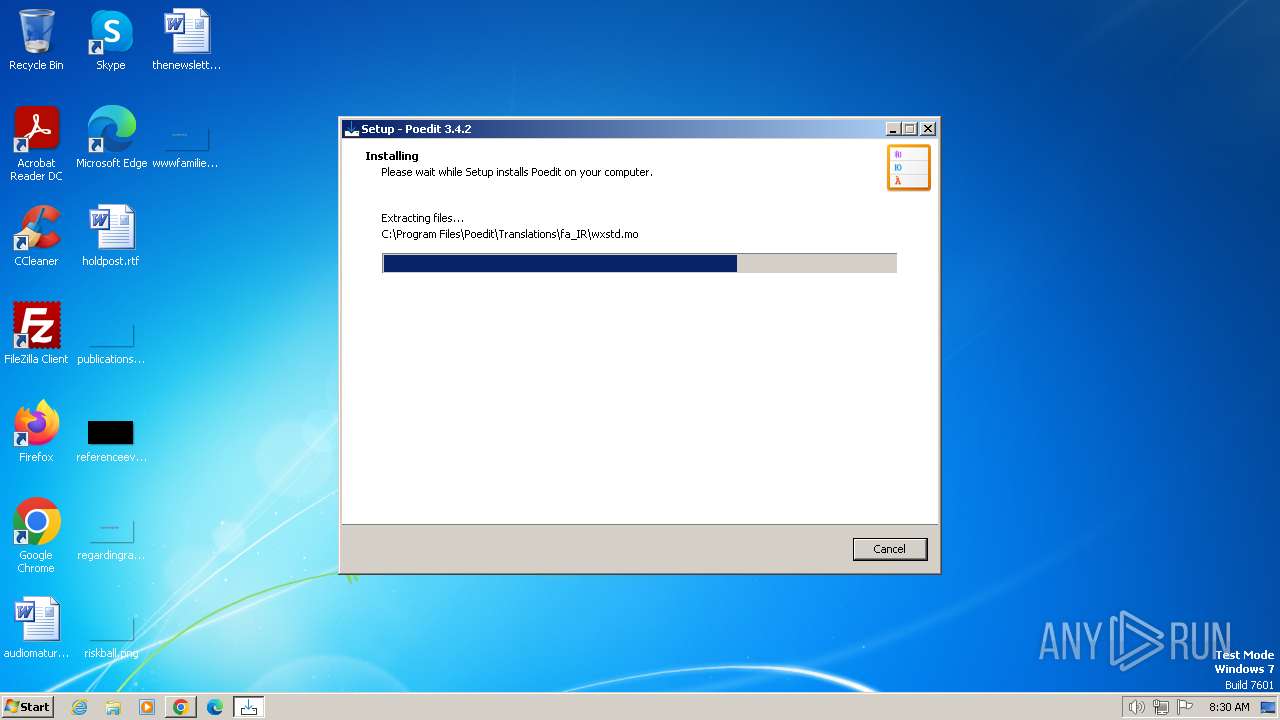
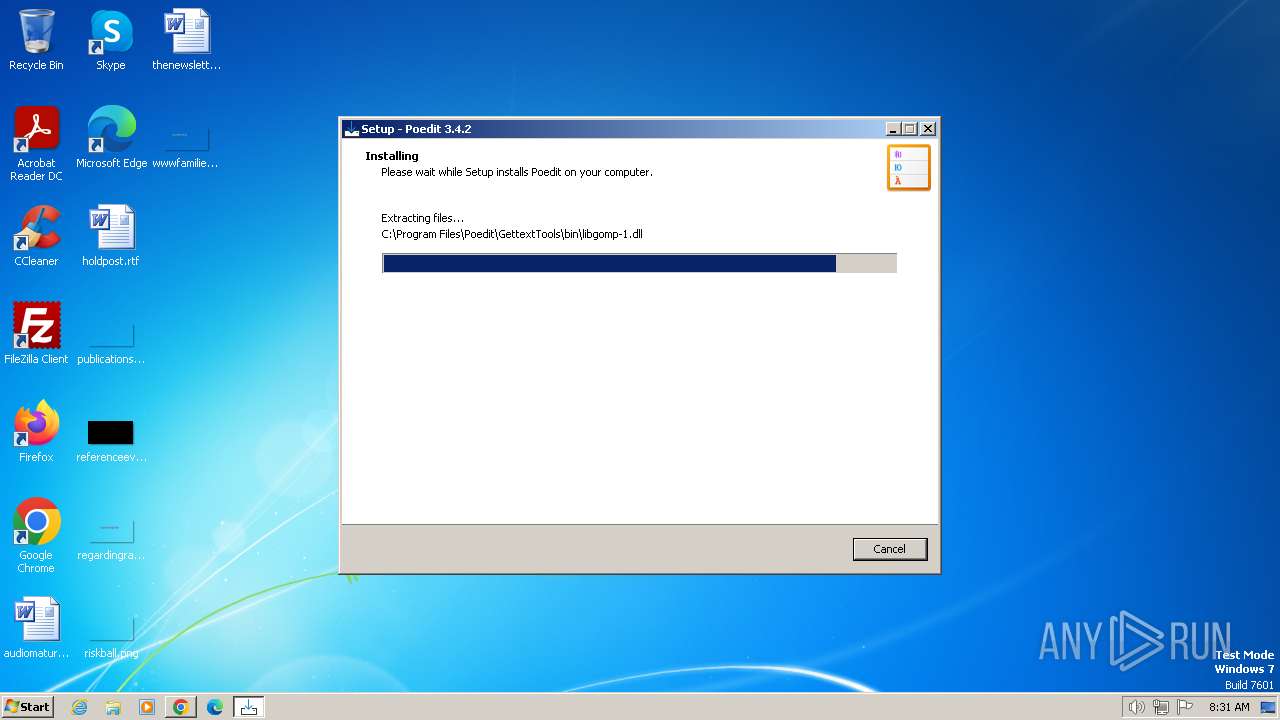
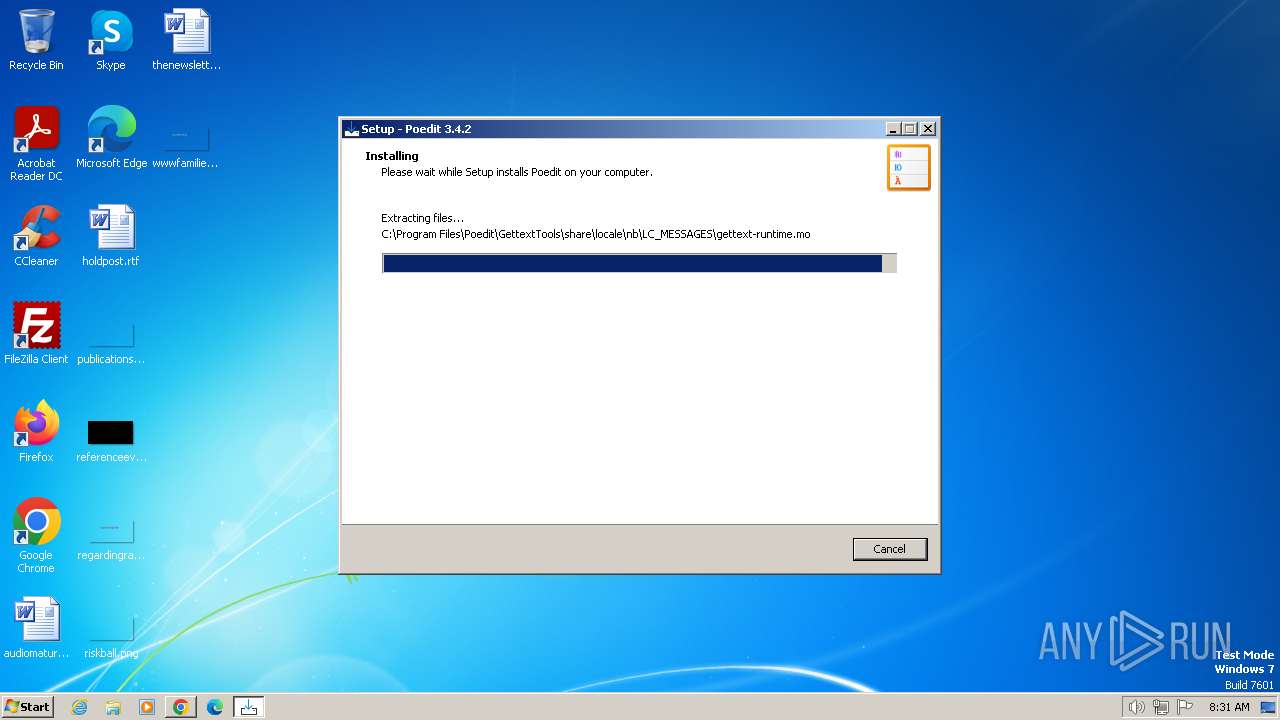
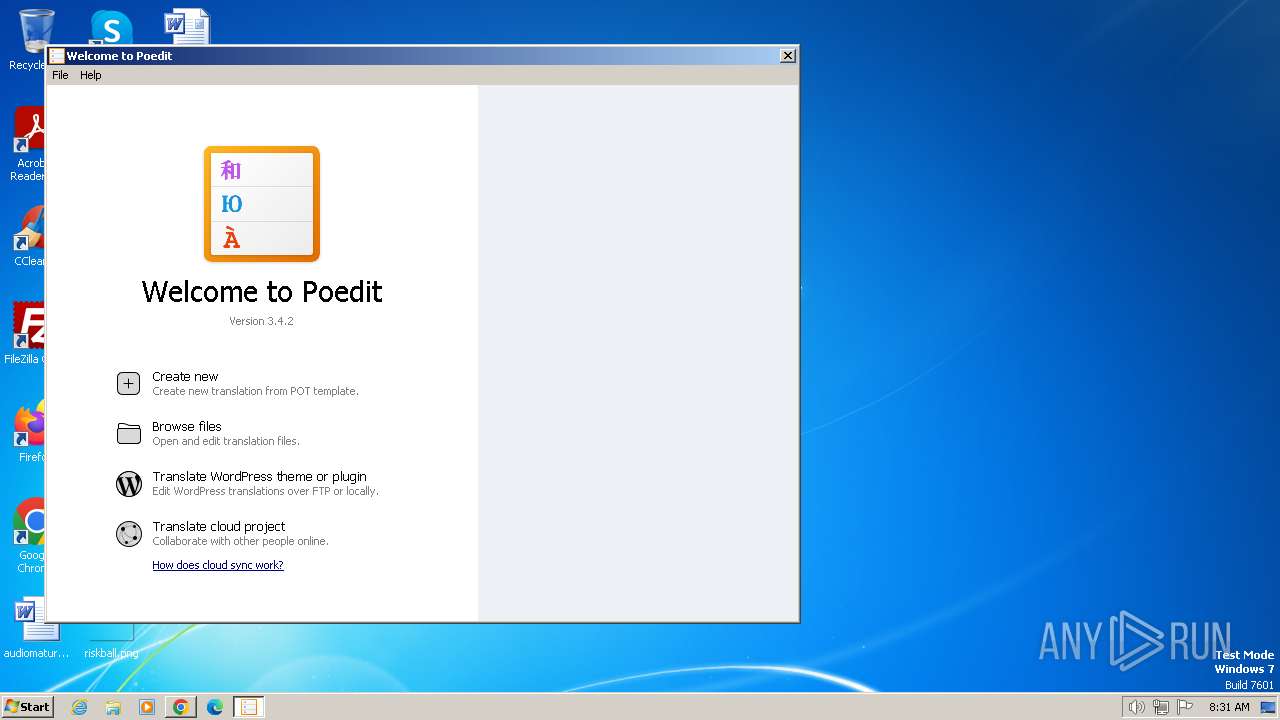
| URL: | https://download.poedit.net/Poedit-3.4.2-setup.exe |
| Full analysis: | https://app.any.run/tasks/a2c733e2-dbfe-4667-8bed-8e0fe2f5b30f |
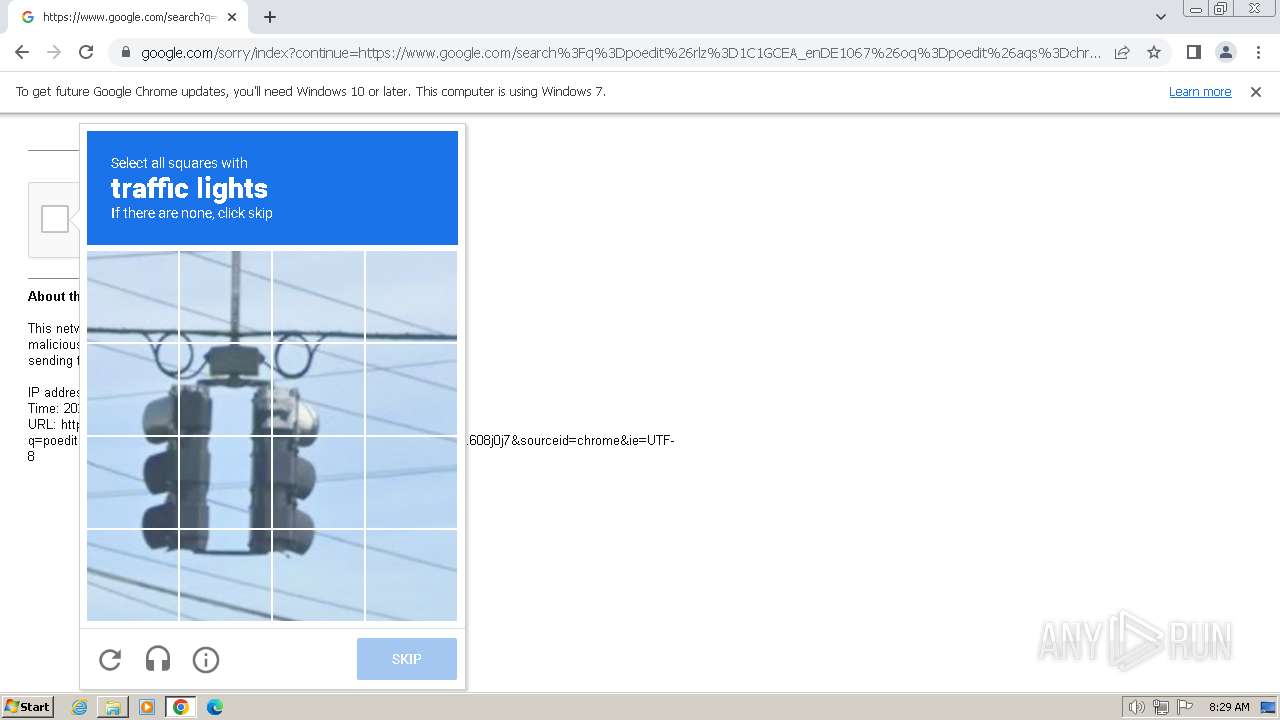
| Verdict: | Malicious activity |
| Analysis date: | February 06, 2024, 08:27:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CFE4435B7AD8C1BE00ACF1F63AC5ADAB |
| SHA1: | 1CF55C70CAB1242A60276435383B092E892E26C6 |
| SHA256: | 4A6EA460769DF3459D2E076FB5A9B4F2D407DEF9F8575964AC6725FDBBC948D0 |
| SSDEEP: | 3:N8SEl6bBQIWLR0HvA:2SKGSuA |
MALICIOUS
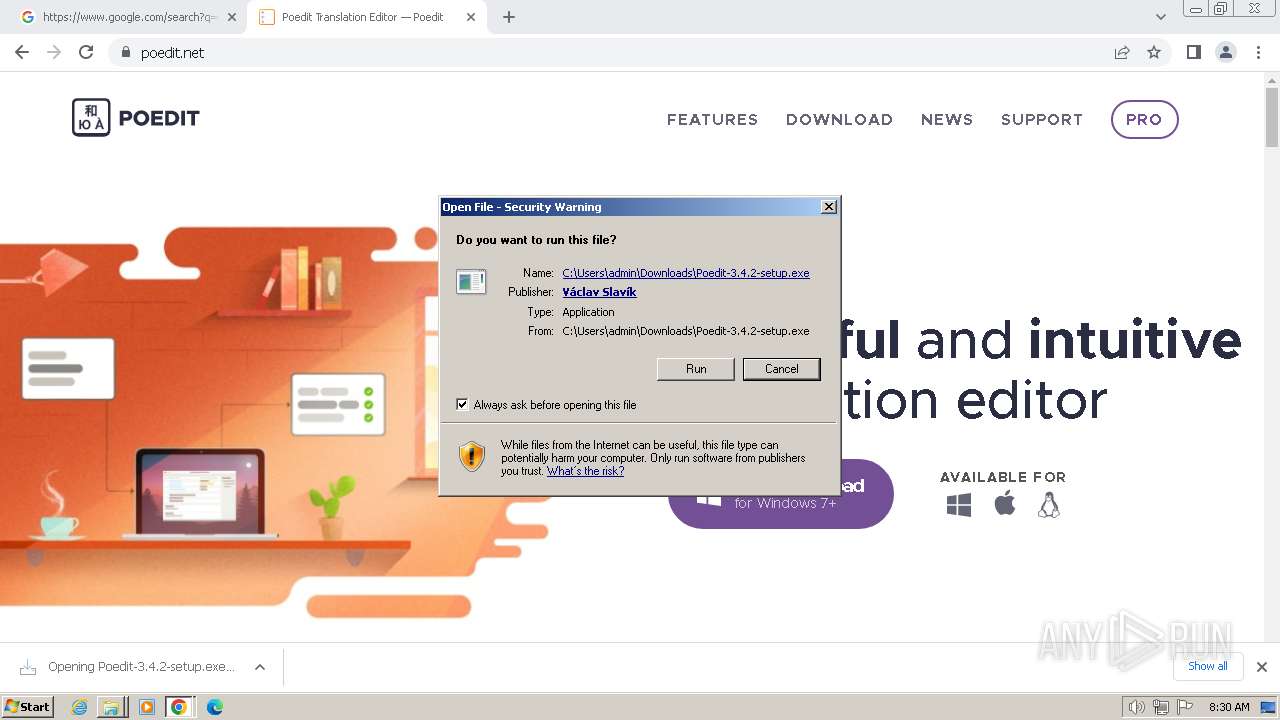
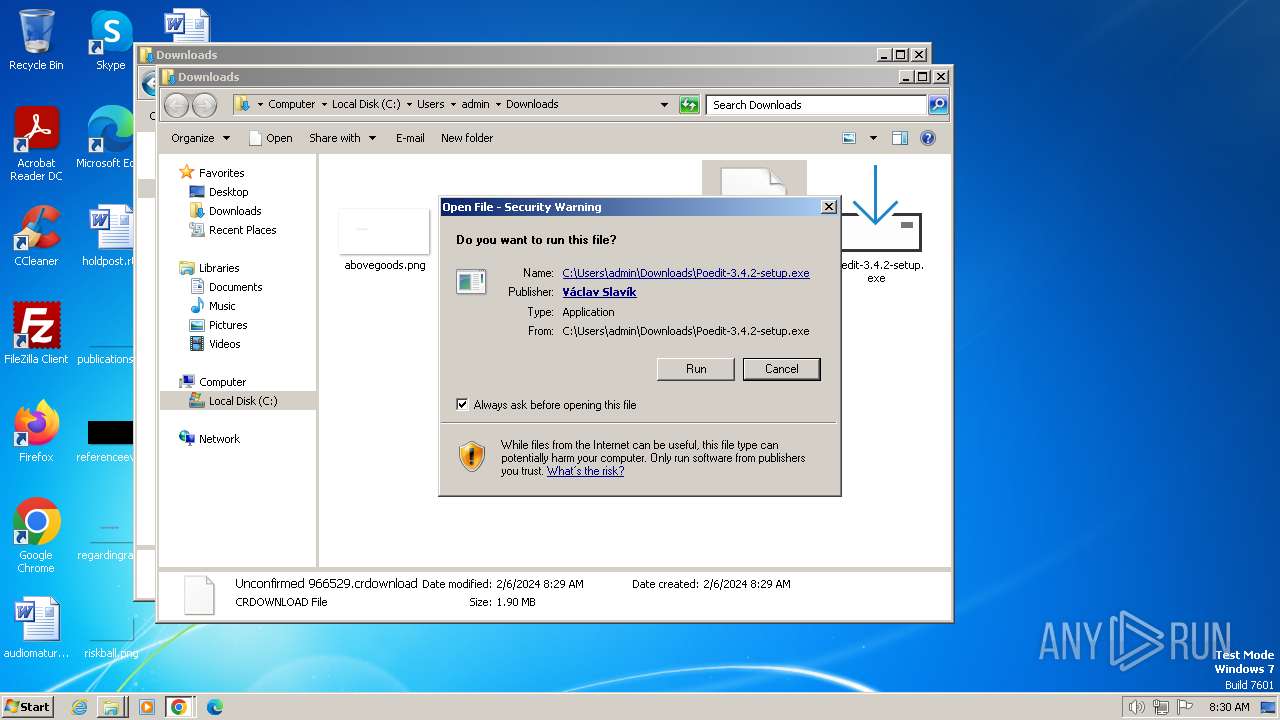
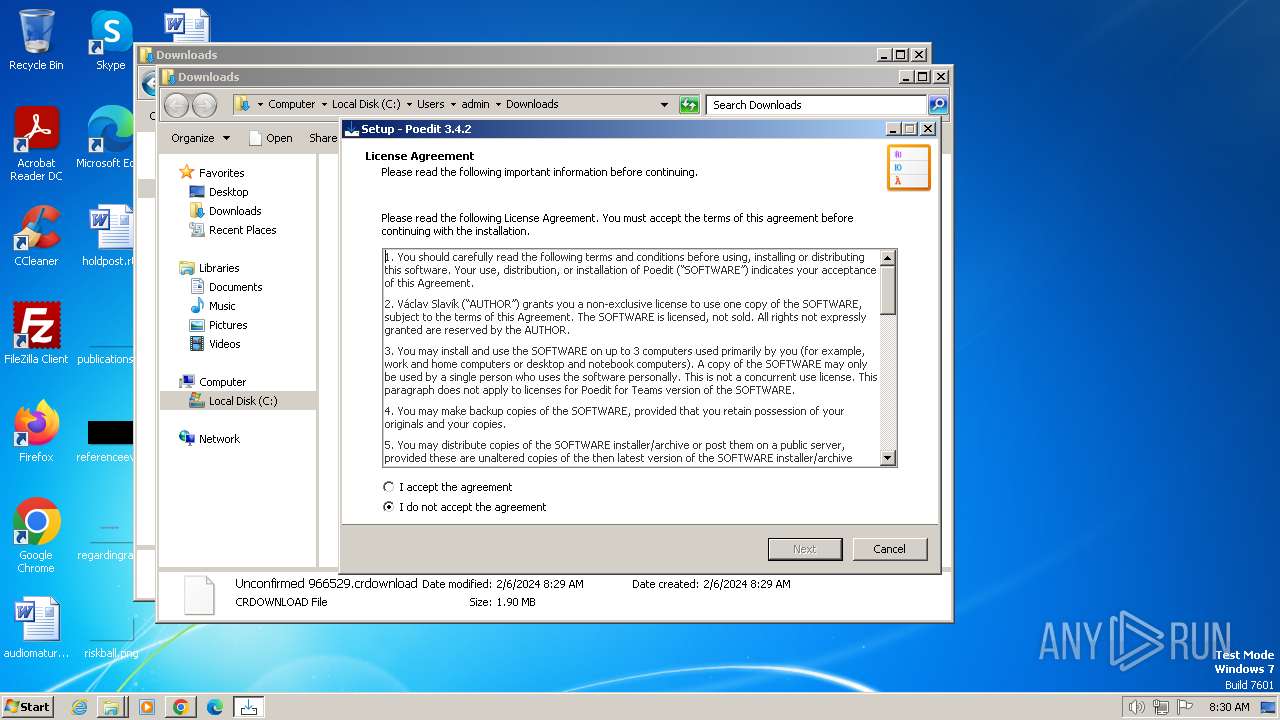
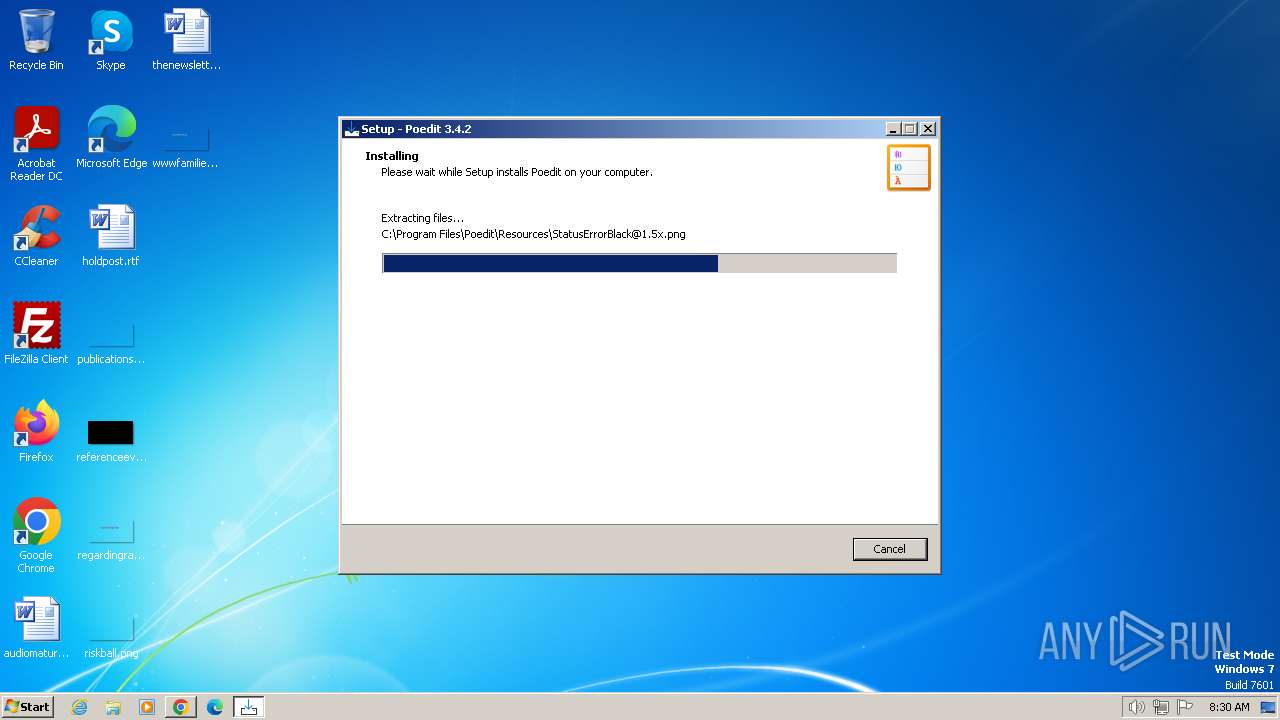
Drops the executable file immediately after the start
- Poedit-3.4.2-setup.exe (PID: 1376)
- Poedit-3.4.2-setup.exe (PID: 2168)
- Poedit-3.4.2-setup.tmp (PID: 1808)
SUSPICIOUS
Executable content was dropped or overwritten
- Poedit-3.4.2-setup.tmp (PID: 1808)
- Poedit-3.4.2-setup.exe (PID: 2168)
- Poedit-3.4.2-setup.exe (PID: 1376)
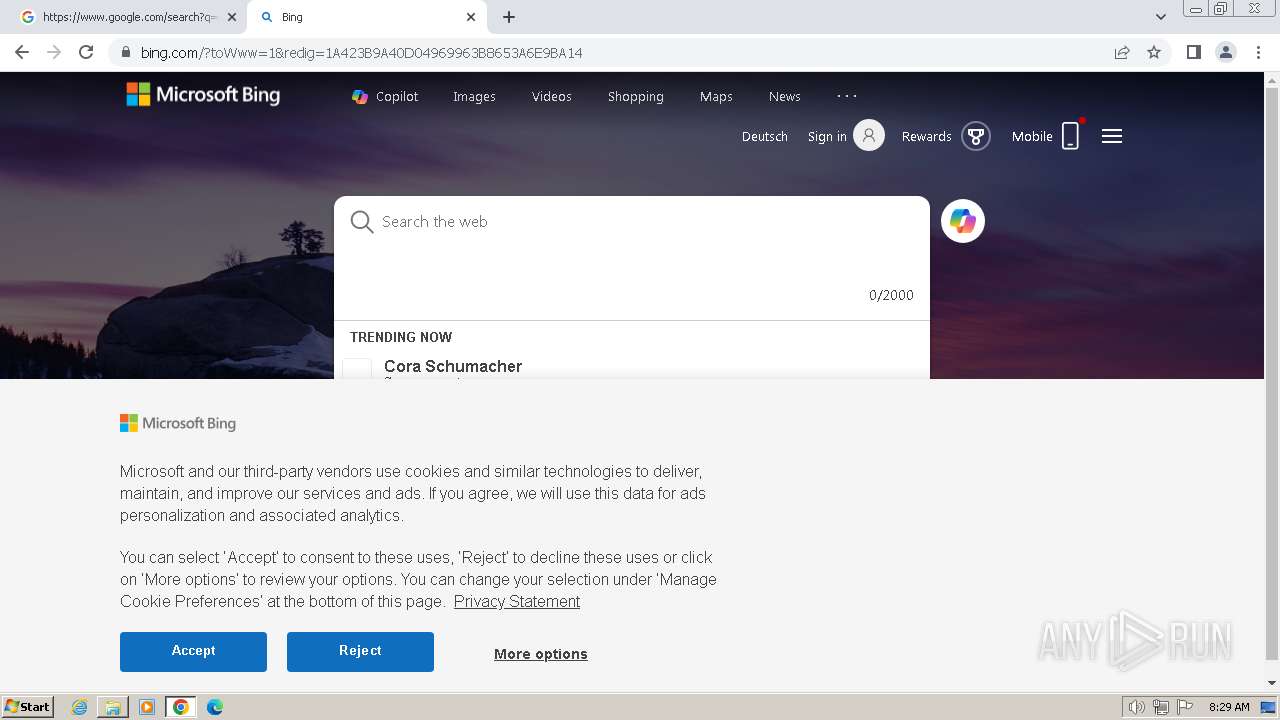
Reads the Internet Settings
- Poedit.exe (PID: 784)
Reads the Windows owner or organization settings
- Poedit-3.4.2-setup.tmp (PID: 1808)
Reads settings of System Certificates
- Poedit.exe (PID: 784)
Checks Windows Trust Settings
- Poedit.exe (PID: 784)
Reads security settings of Internet Explorer
- Poedit.exe (PID: 784)
Process drops legitimate windows executable
- Poedit-3.4.2-setup.tmp (PID: 1808)
The process drops C-runtime libraries
- Poedit-3.4.2-setup.tmp (PID: 1808)
INFO
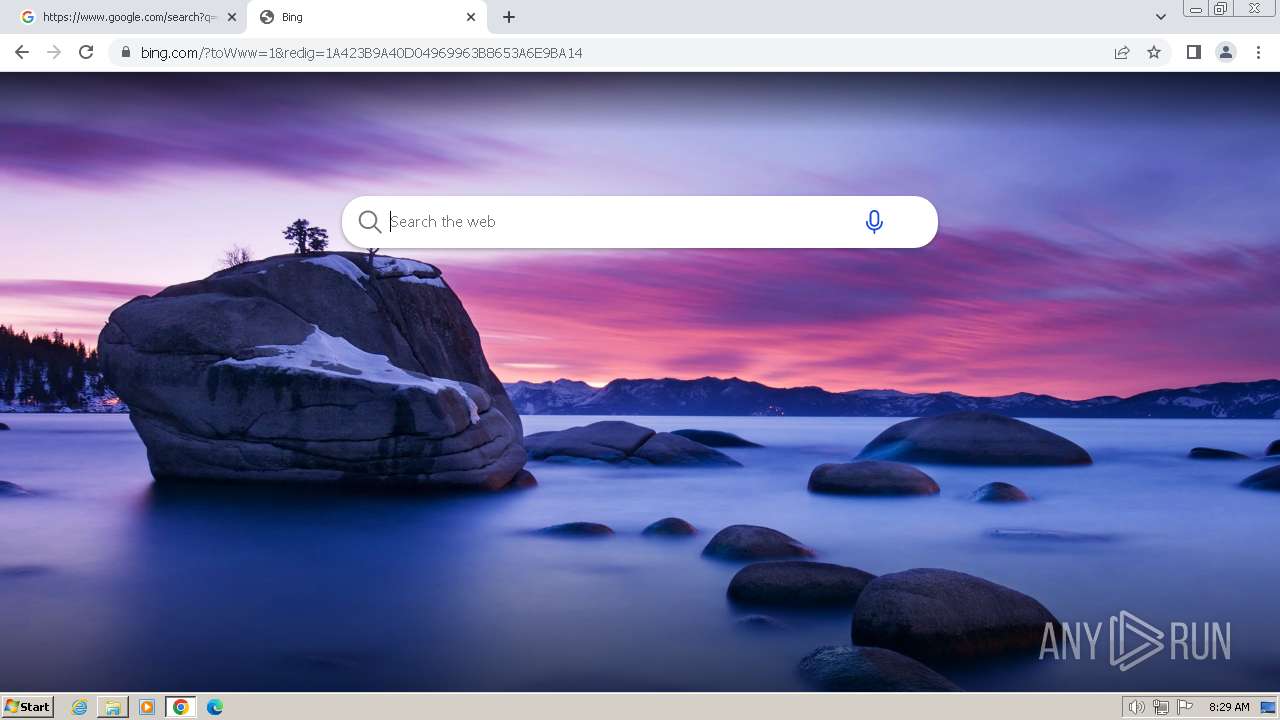
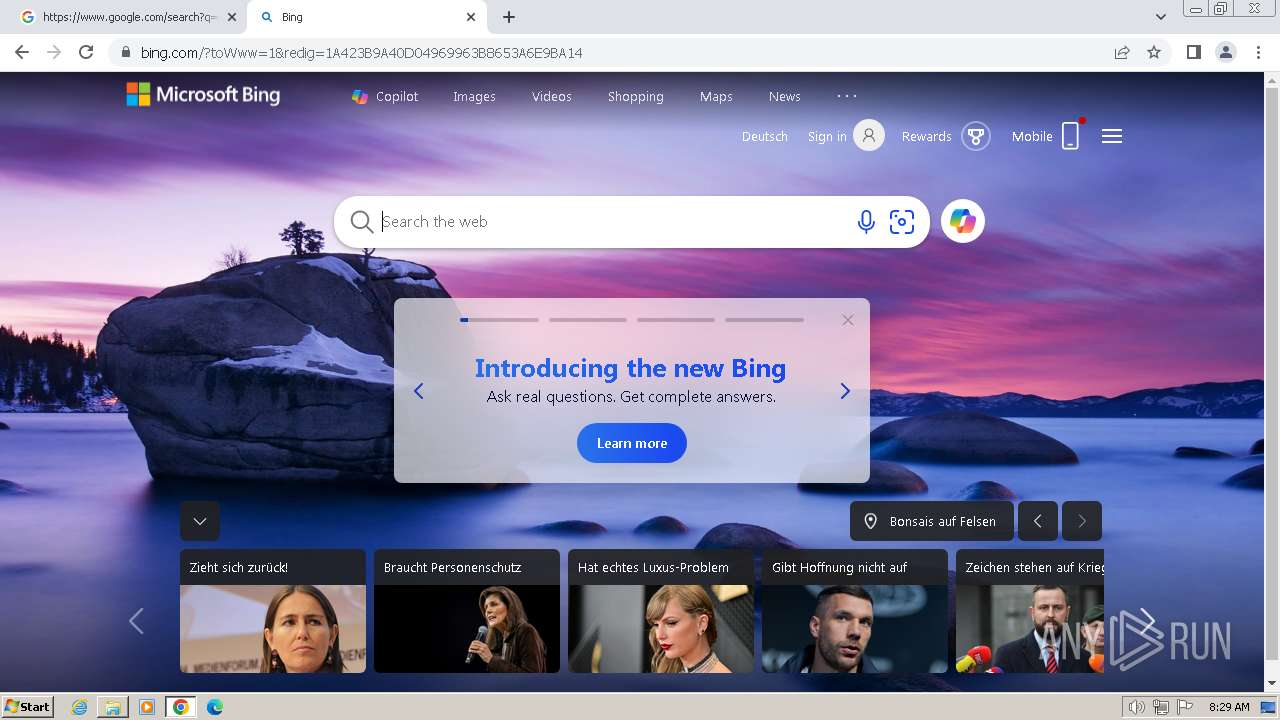
Application launched itself
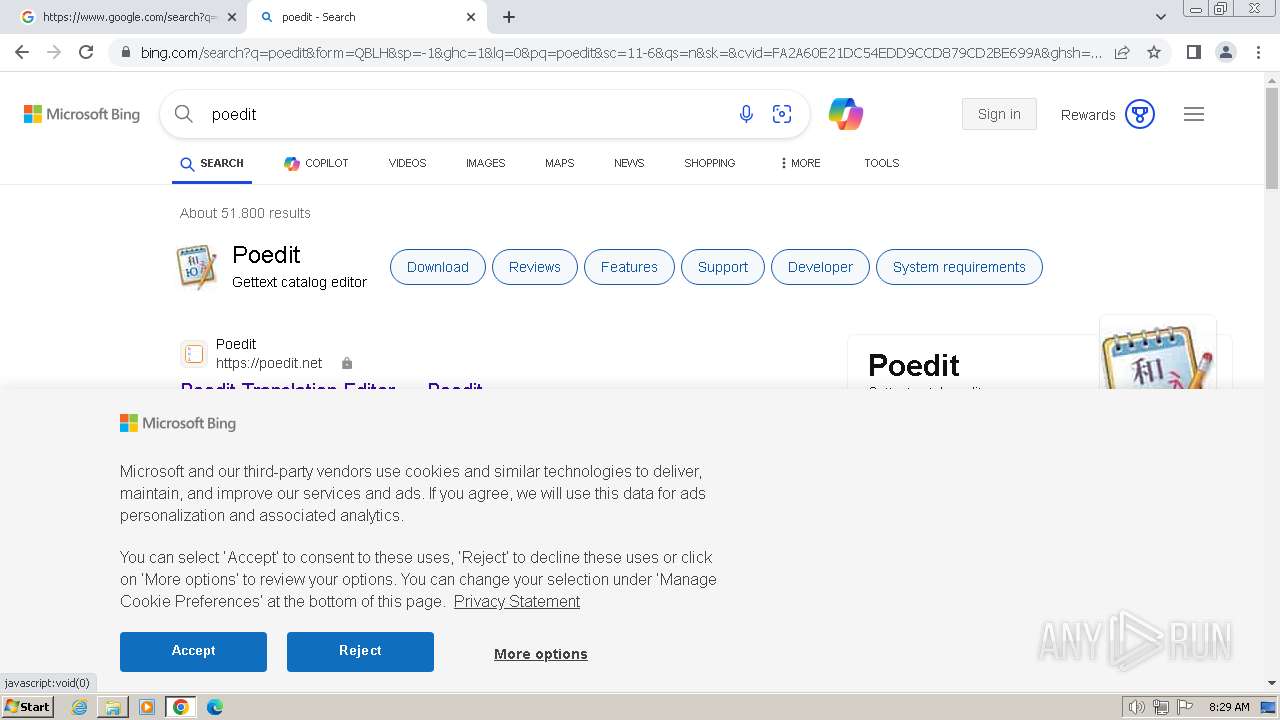
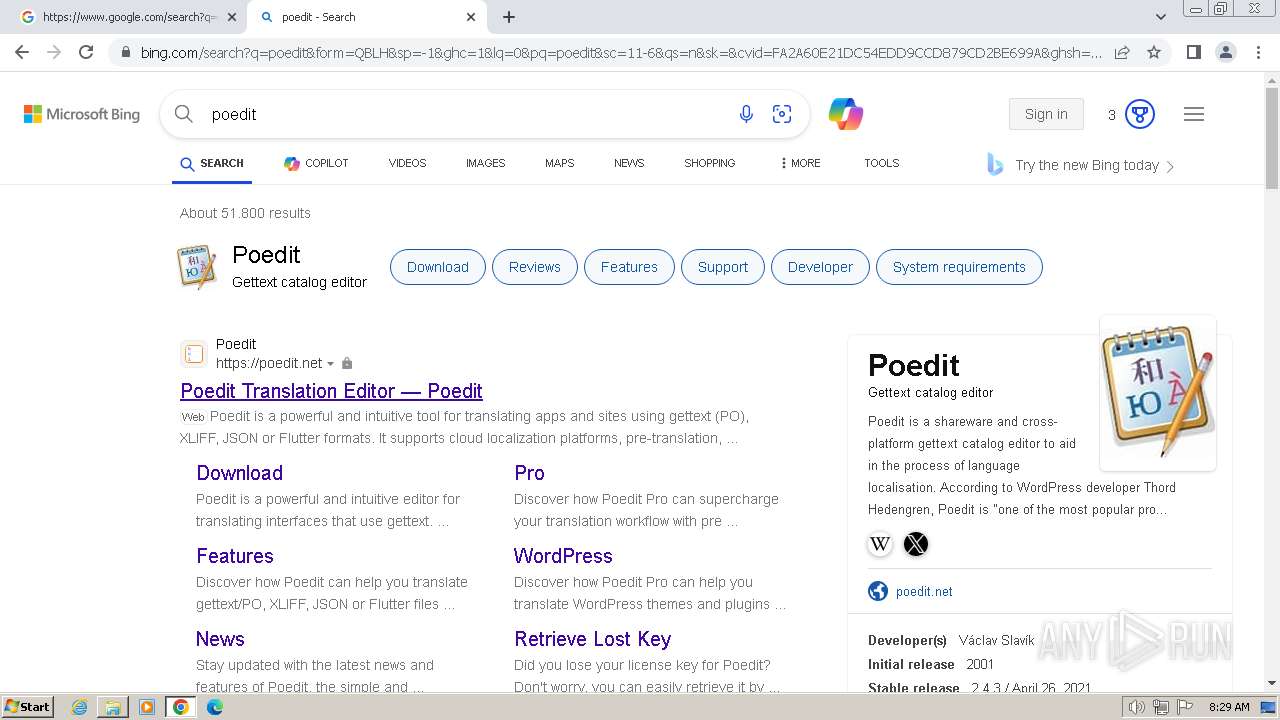
- iexplore.exe (PID: 752)
- chrome.exe (PID: 3728)
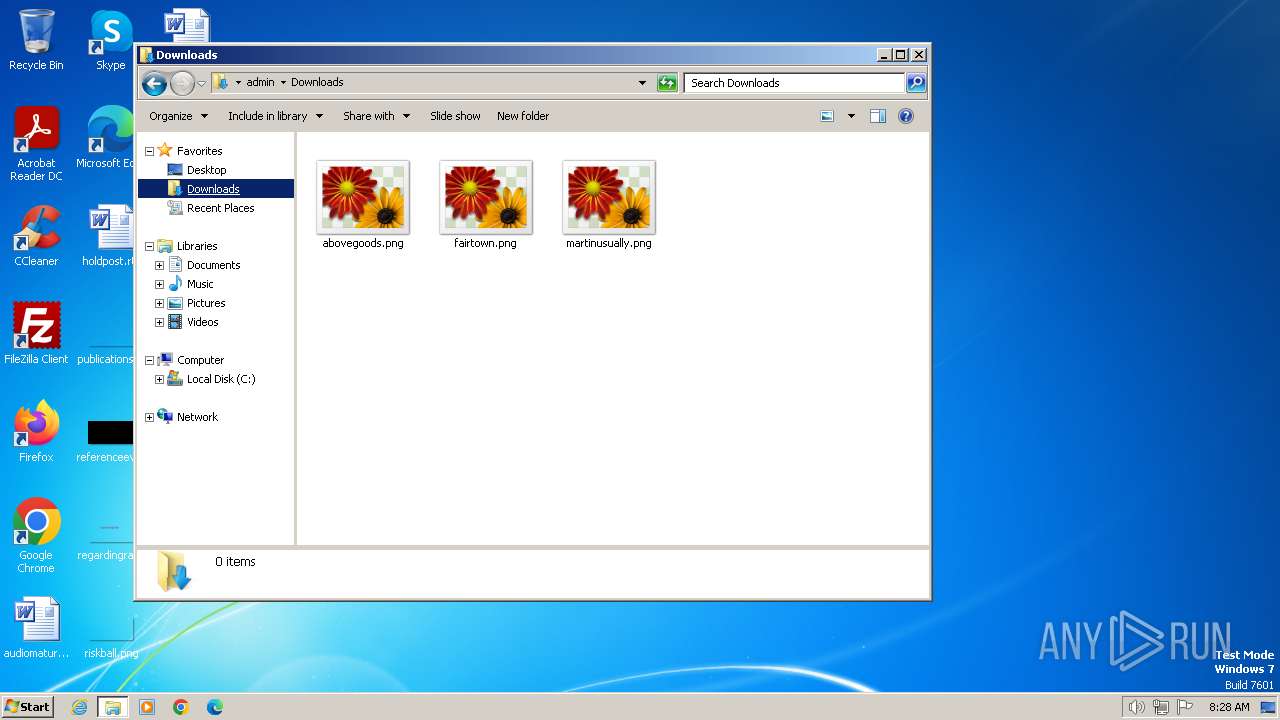
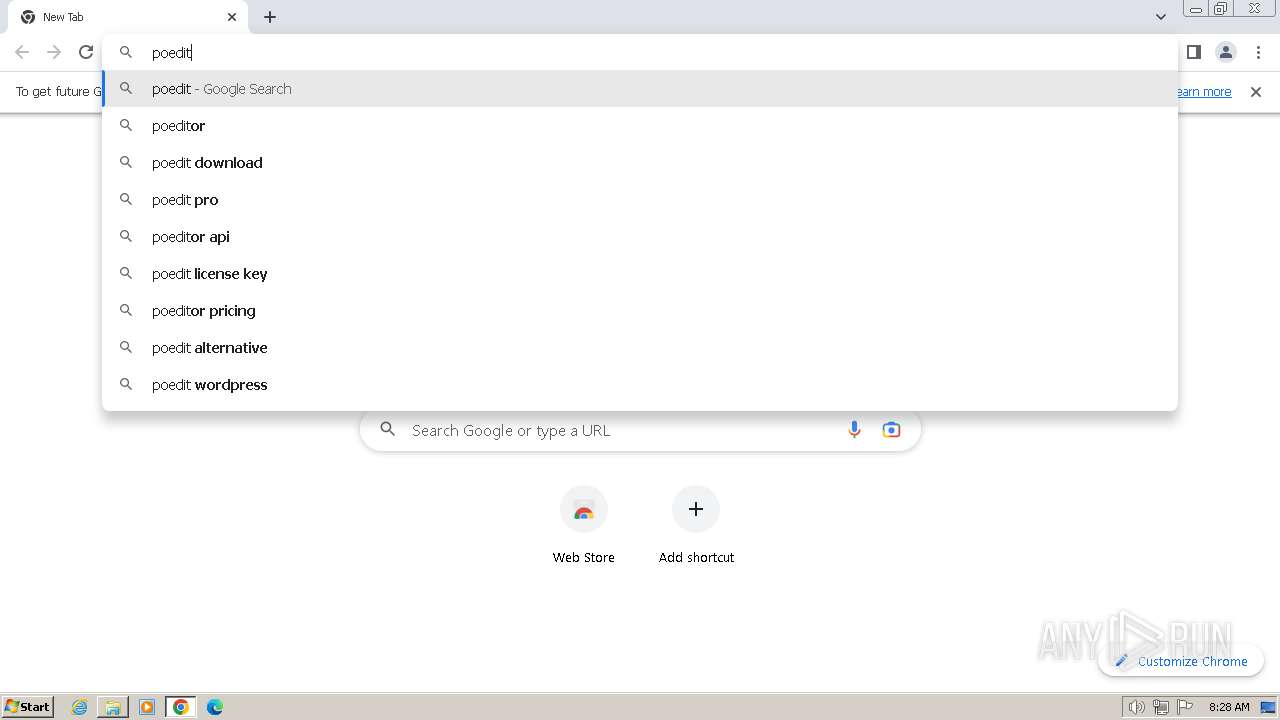
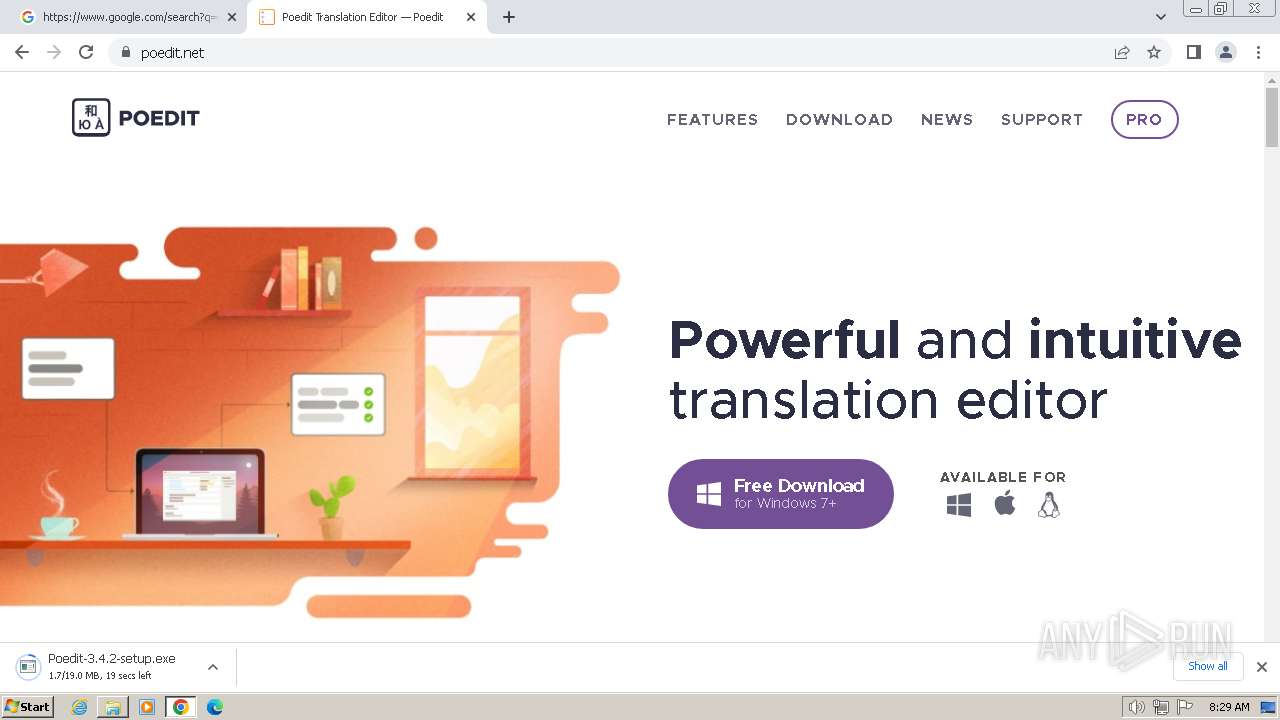
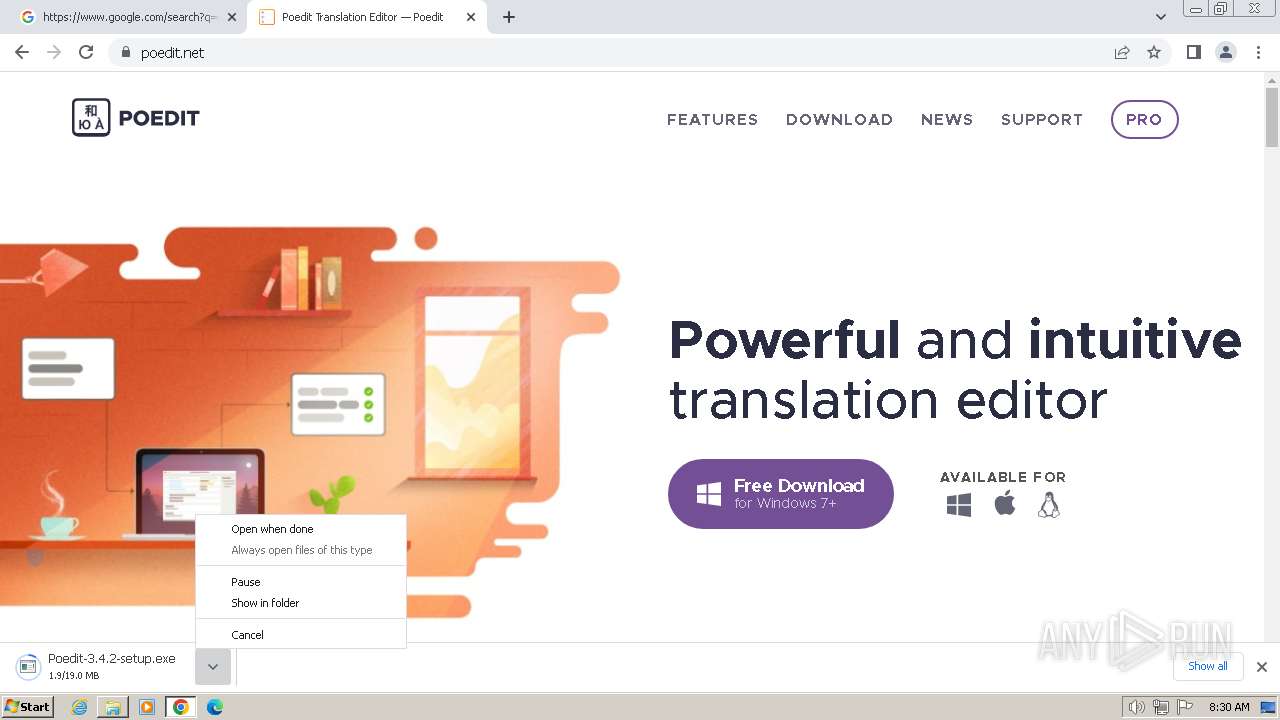
Manual execution by a user
- chrome.exe (PID: 3728)
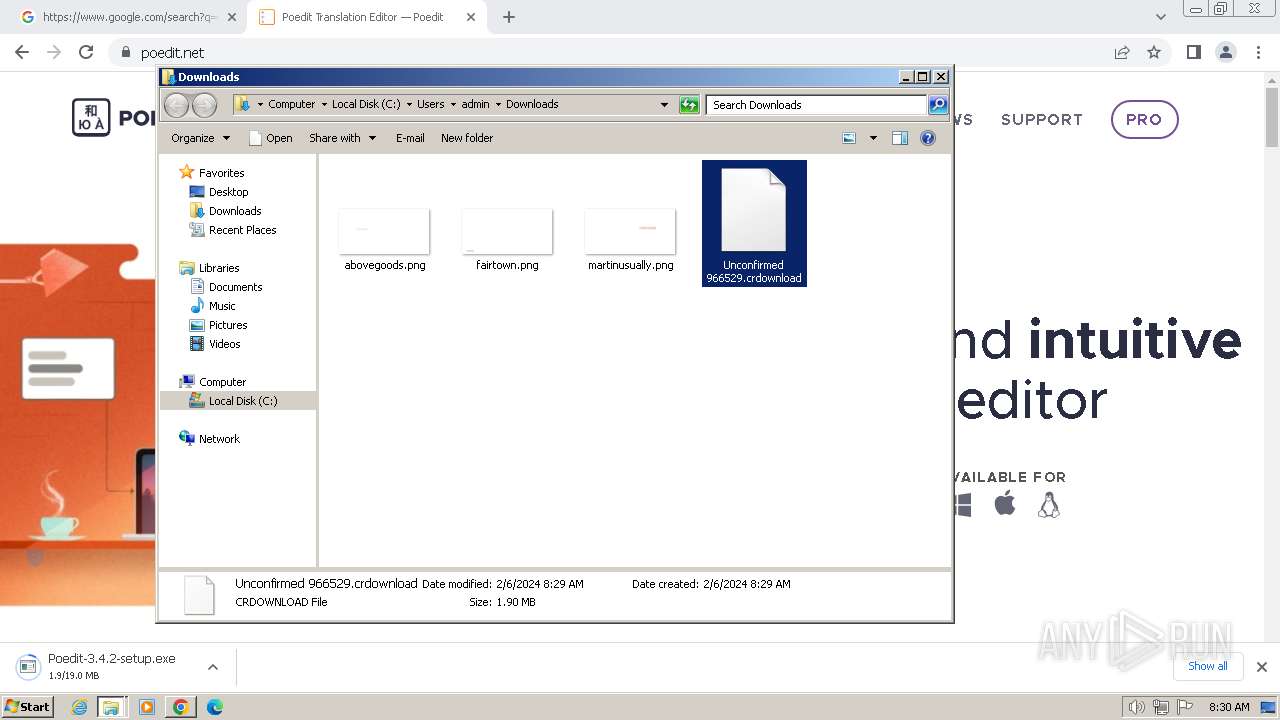
- explorer.exe (PID: 3380)
Drops the executable file immediately after the start
- iexplore.exe (PID: 2736)
- chrome.exe (PID: 2916)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 2292)
Executable content was dropped or overwritten
- iexplore.exe (PID: 2736)
- chrome.exe (PID: 2292)
- chrome.exe (PID: 2916)
- chrome.exe (PID: 3728)
The process uses the downloaded file
- chrome.exe (PID: 3728)
- chrome.exe (PID: 4052)
Create files in a temporary directory
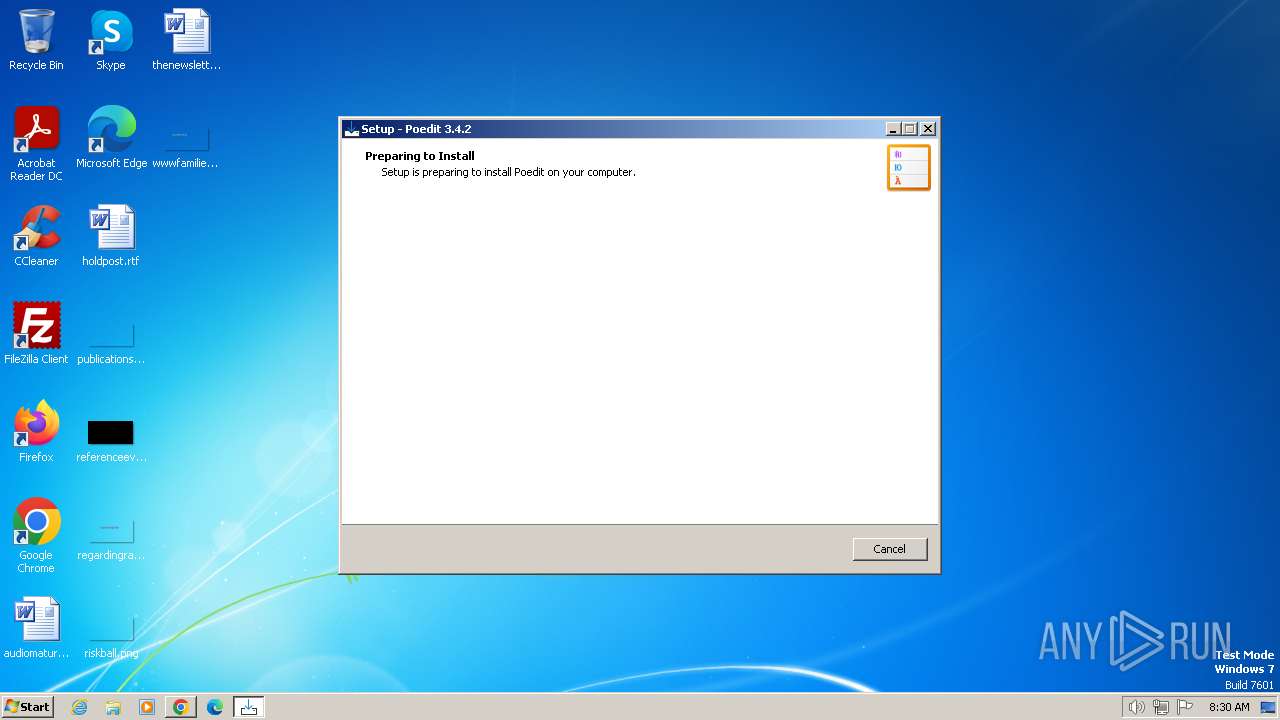
- Poedit-3.4.2-setup.exe (PID: 1376)
- Poedit-3.4.2-setup.exe (PID: 2168)
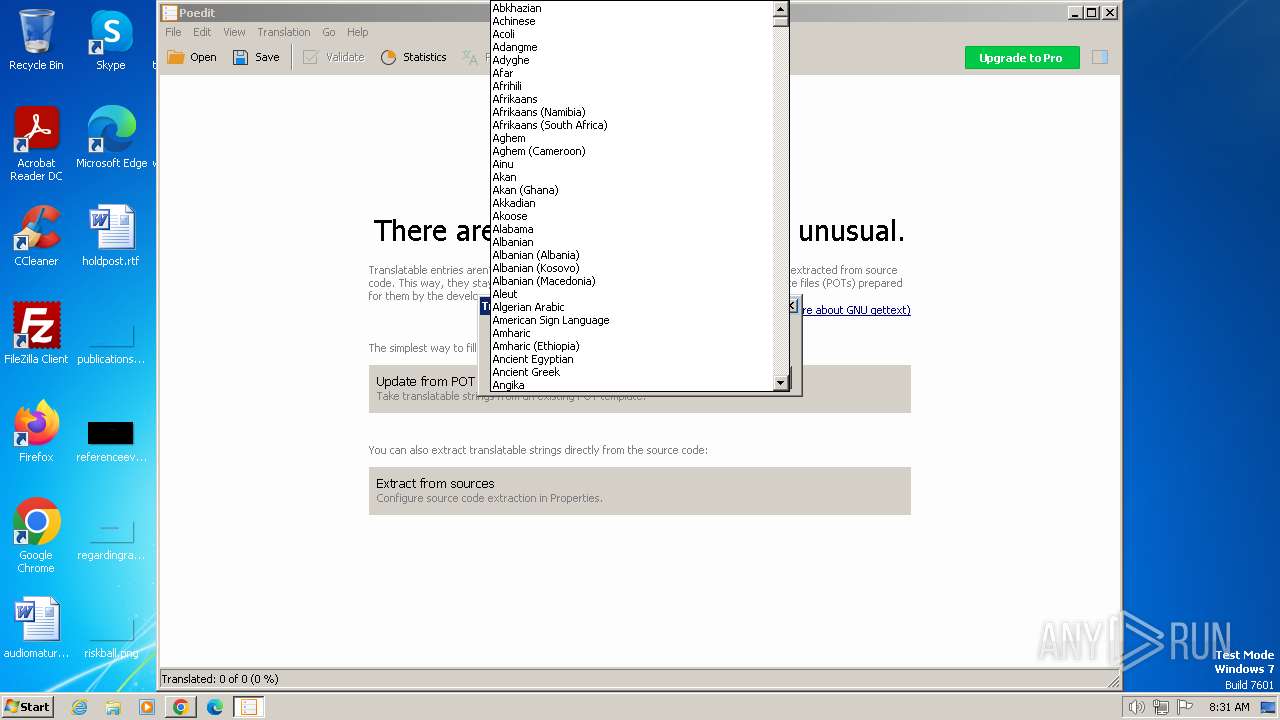
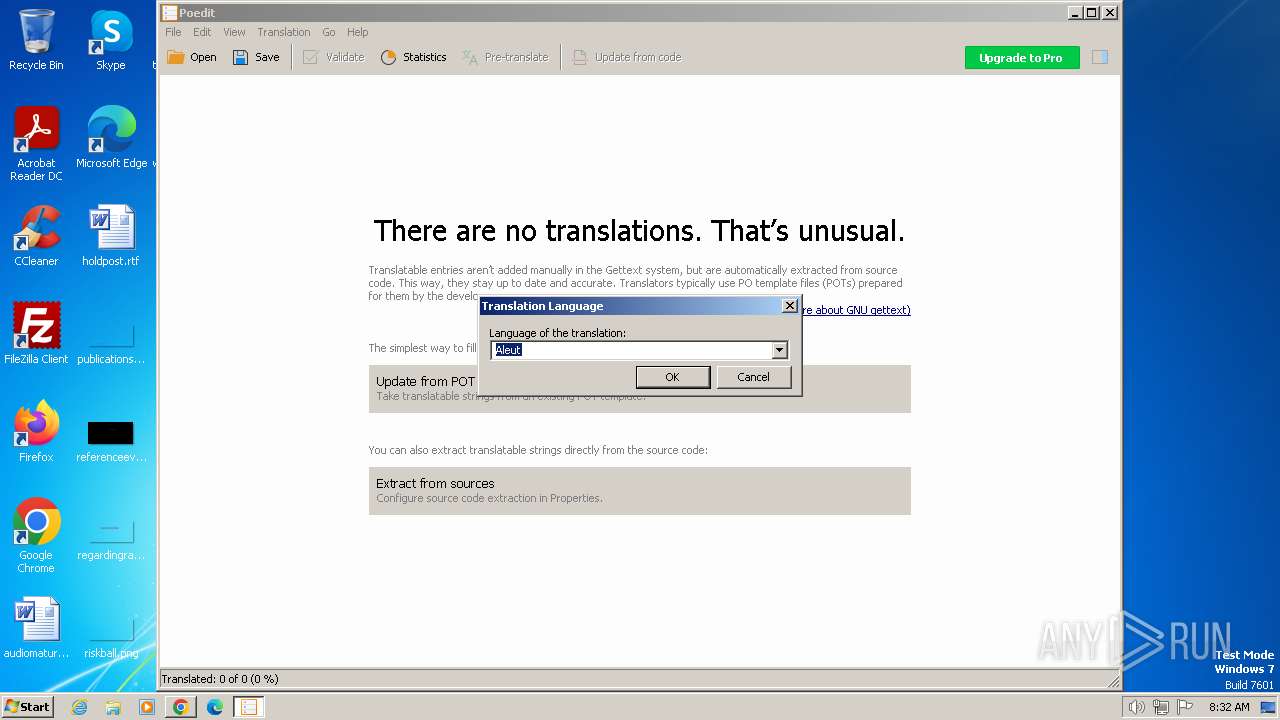
Checks supported languages
- Poedit-3.4.2-setup.tmp (PID: 1196)
- Poedit-3.4.2-setup.exe (PID: 2168)
- Poedit-3.4.2-setup.tmp (PID: 1808)
- Poedit.exe (PID: 784)
- msgfmt.exe (PID: 2936)
- msgfmt.exe (PID: 3980)
- msgcat.exe (PID: 3964)
- Poedit-3.4.2-setup.exe (PID: 1376)
Reads the computer name
- Poedit-3.4.2-setup.tmp (PID: 1808)
- Poedit.exe (PID: 784)
- Poedit-3.4.2-setup.tmp (PID: 1196)
Checks proxy server information
- Poedit.exe (PID: 784)
Creates files in the program directory
- Poedit-3.4.2-setup.tmp (PID: 1808)
Reads the machine GUID from the registry
- Poedit.exe (PID: 784)
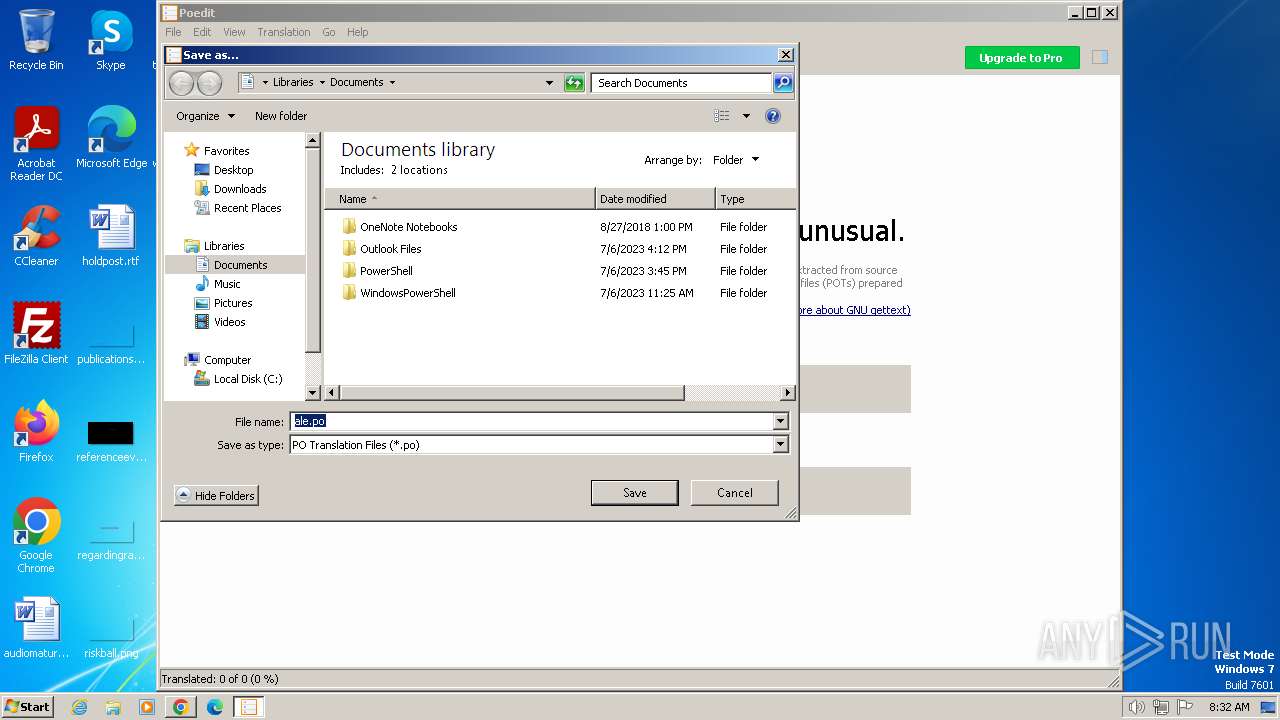
Creates files or folders in the user directory
- Poedit.exe (PID: 784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
94
Monitored processes
41
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=4536 --field-trial-handle=1128,i,1794141905279178769,8964855523407109174,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 752 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://download.poedit.net/Poedit-3.4.2-setup.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
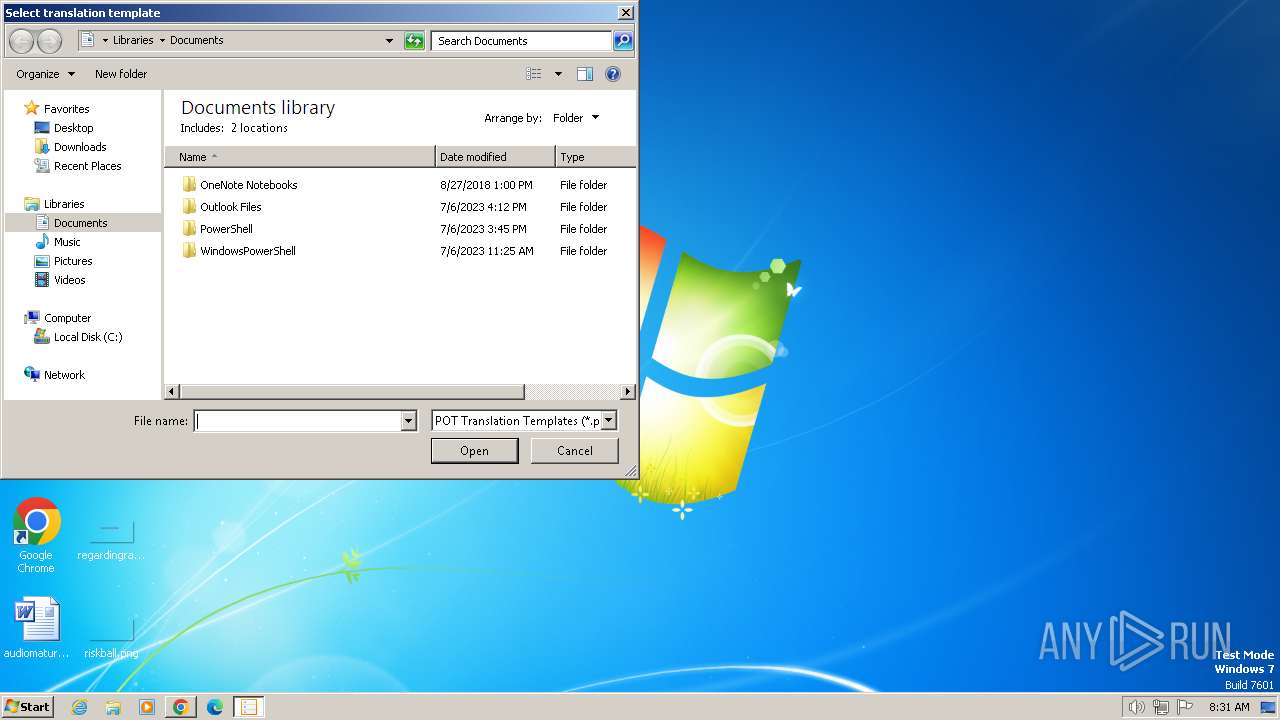
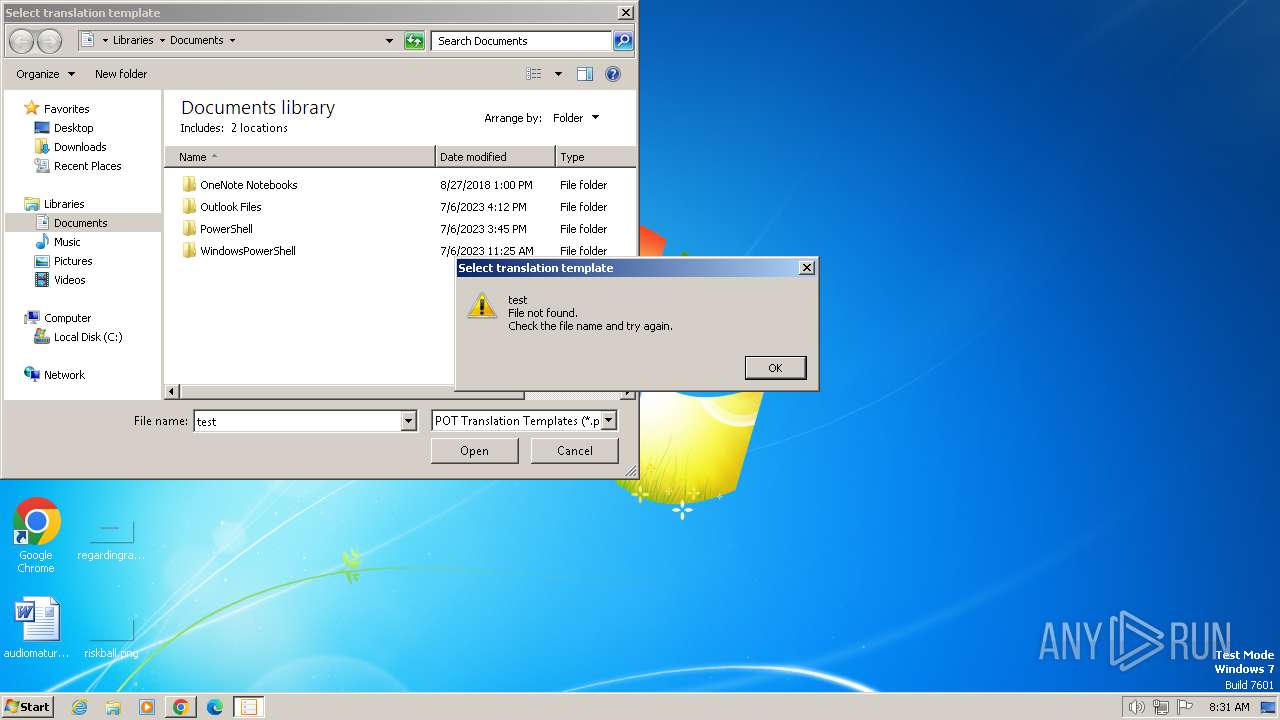
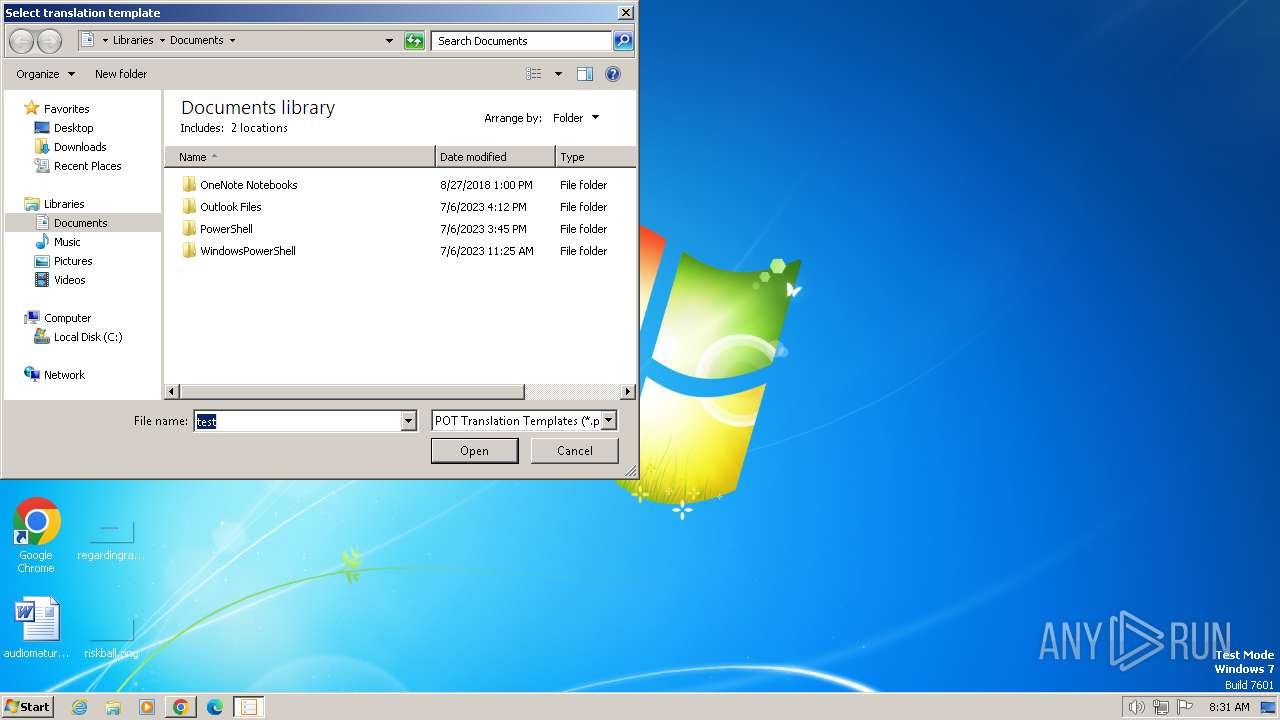
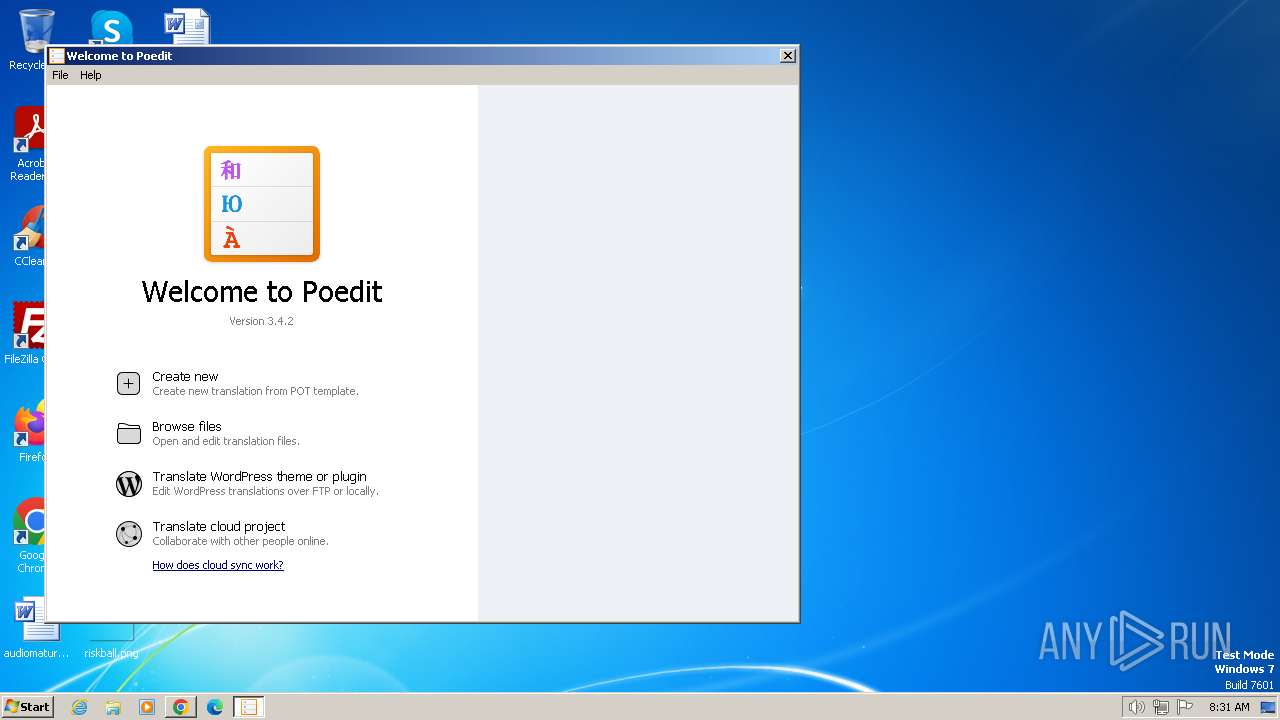
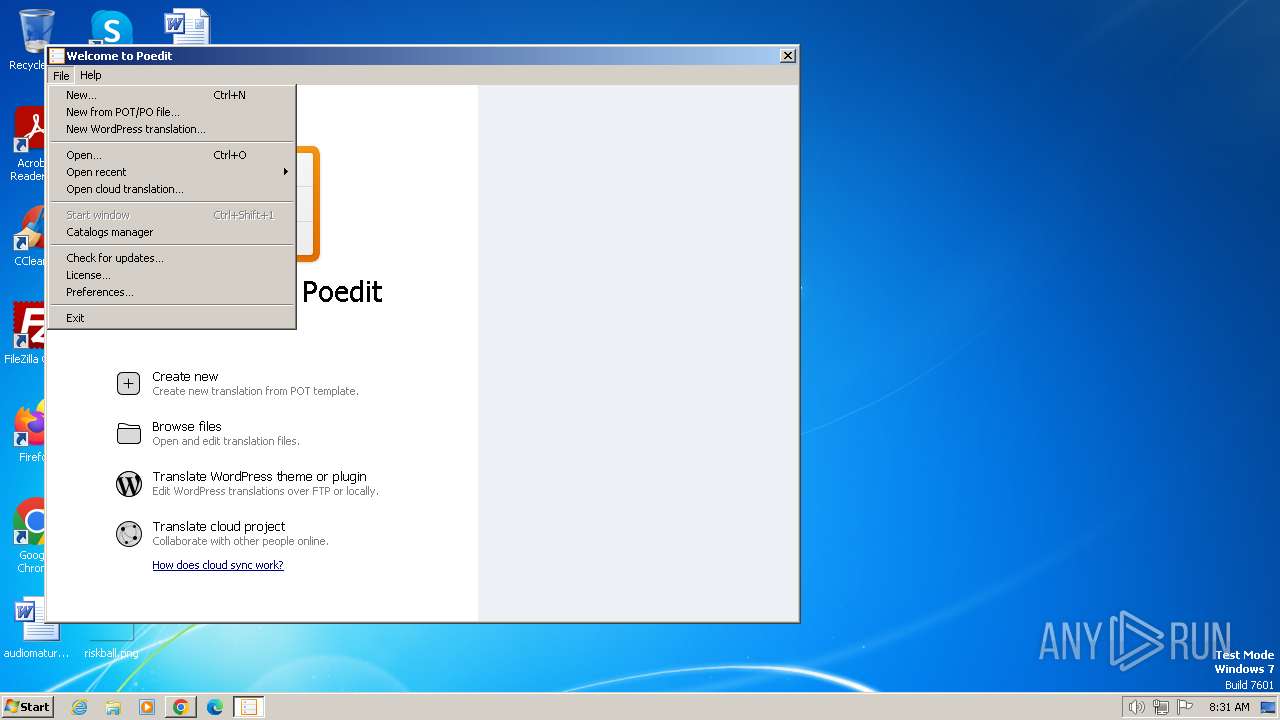
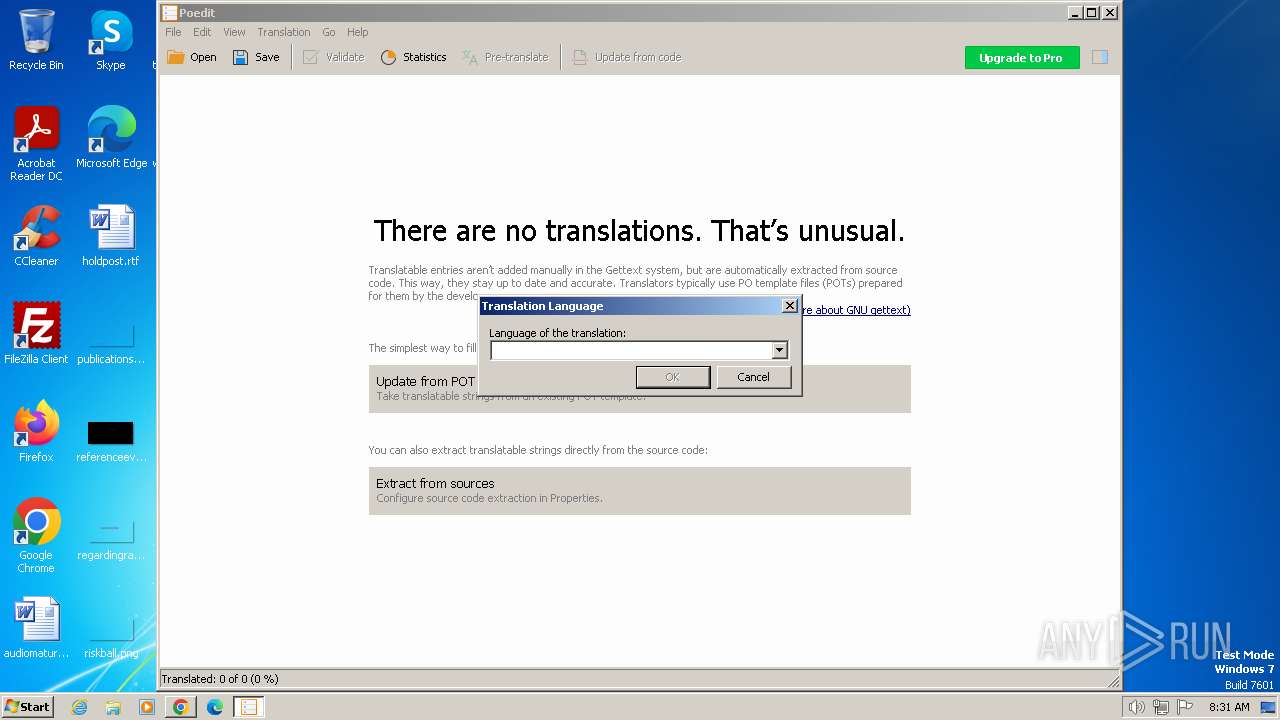
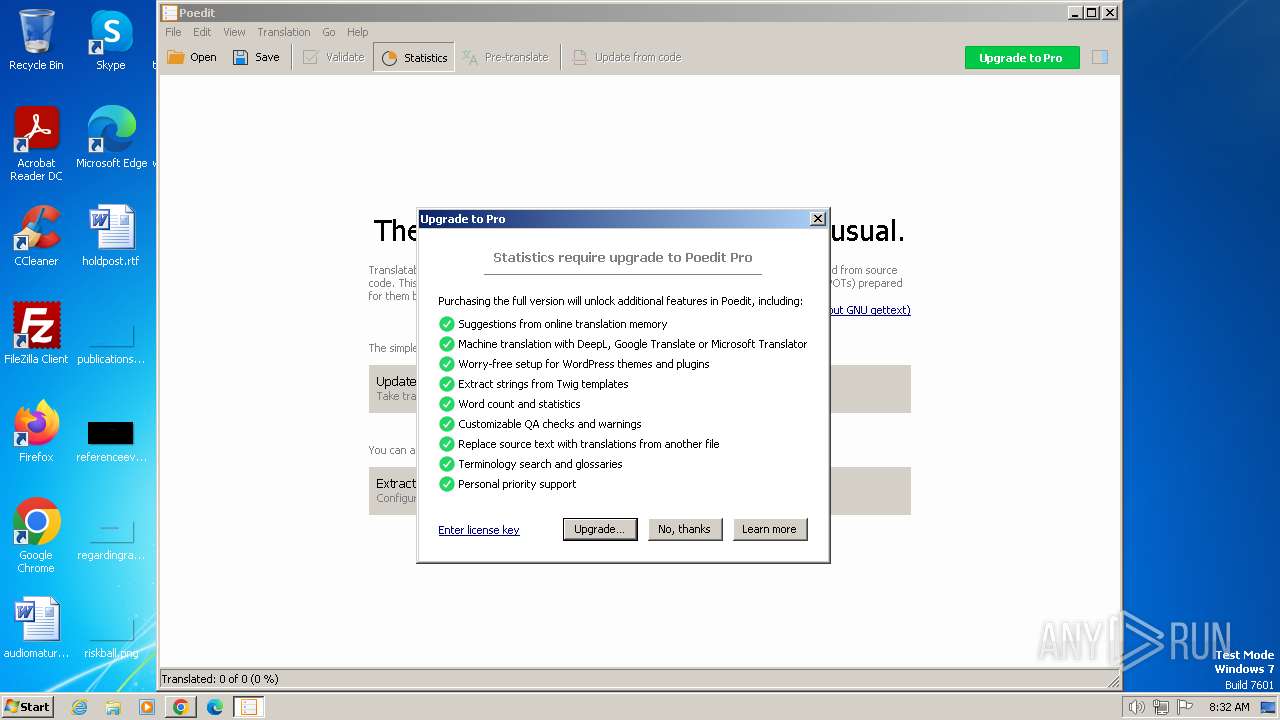
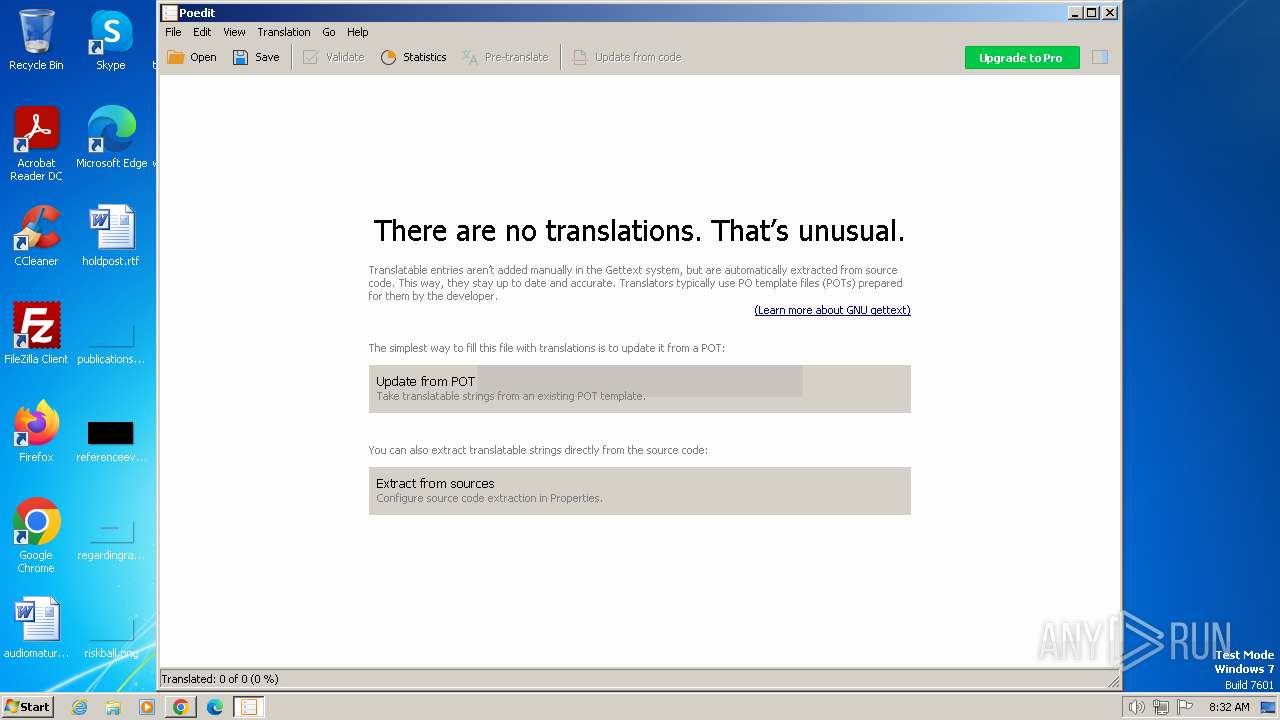
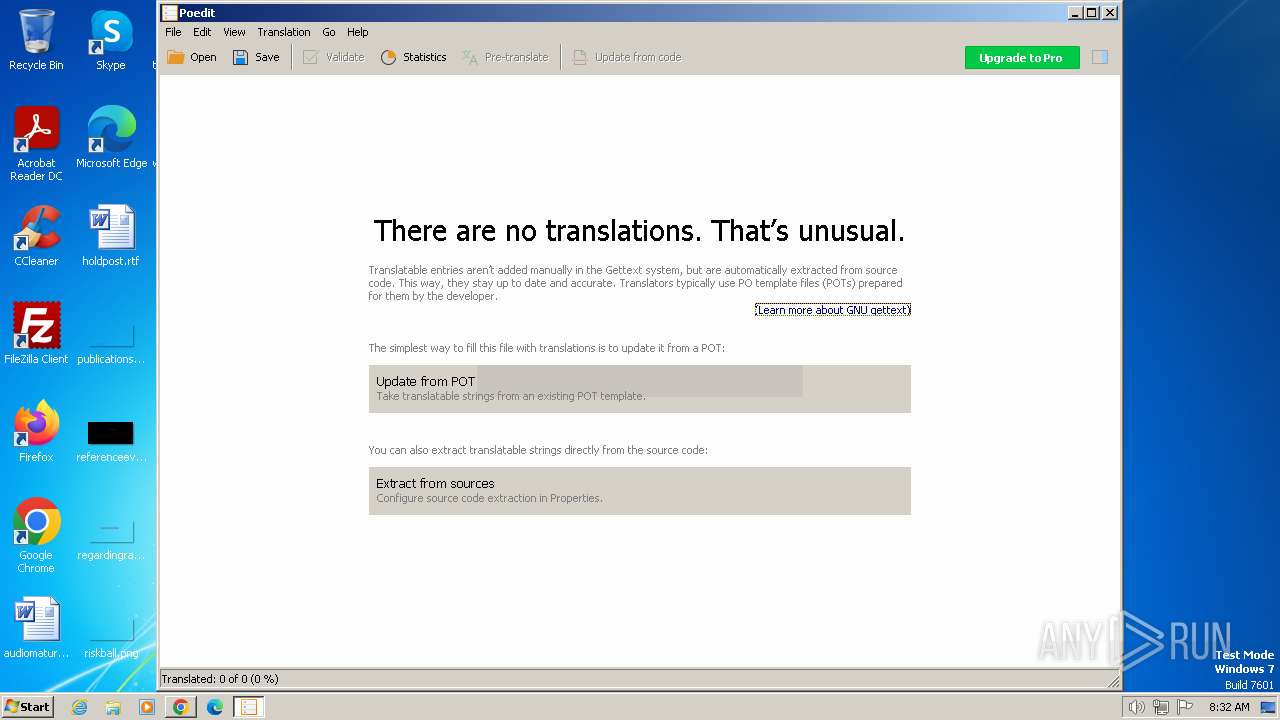
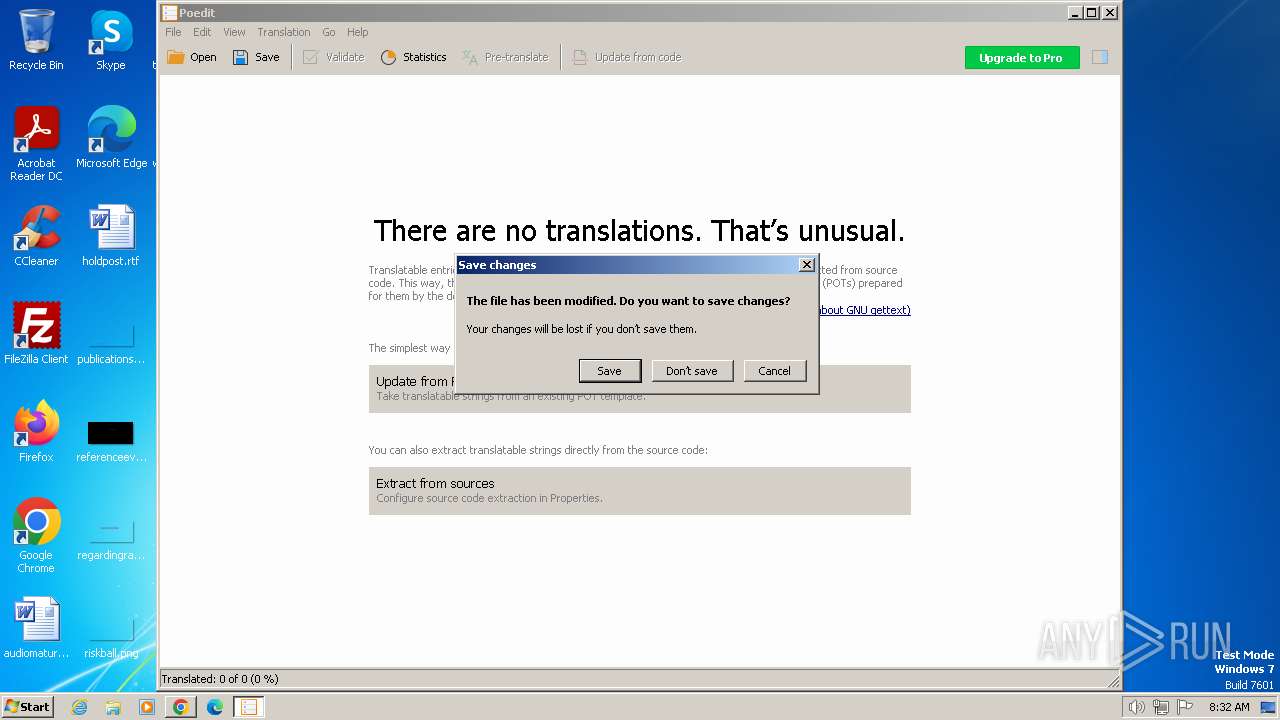
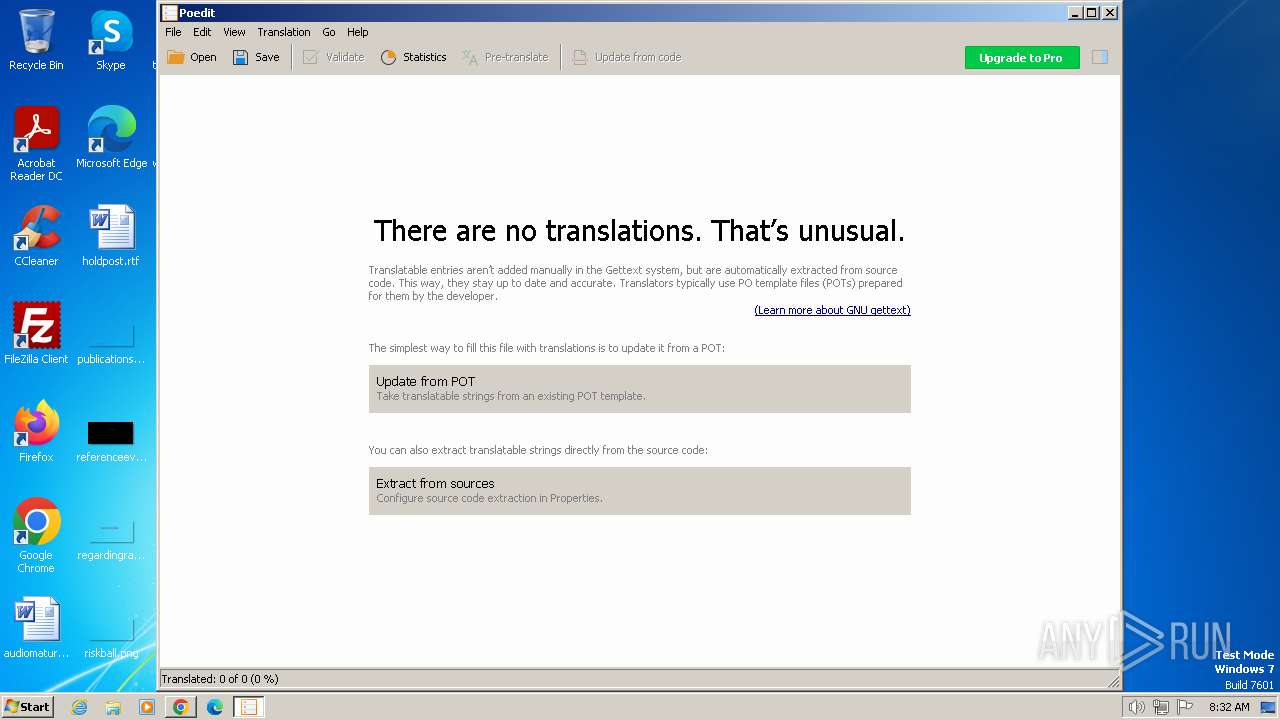
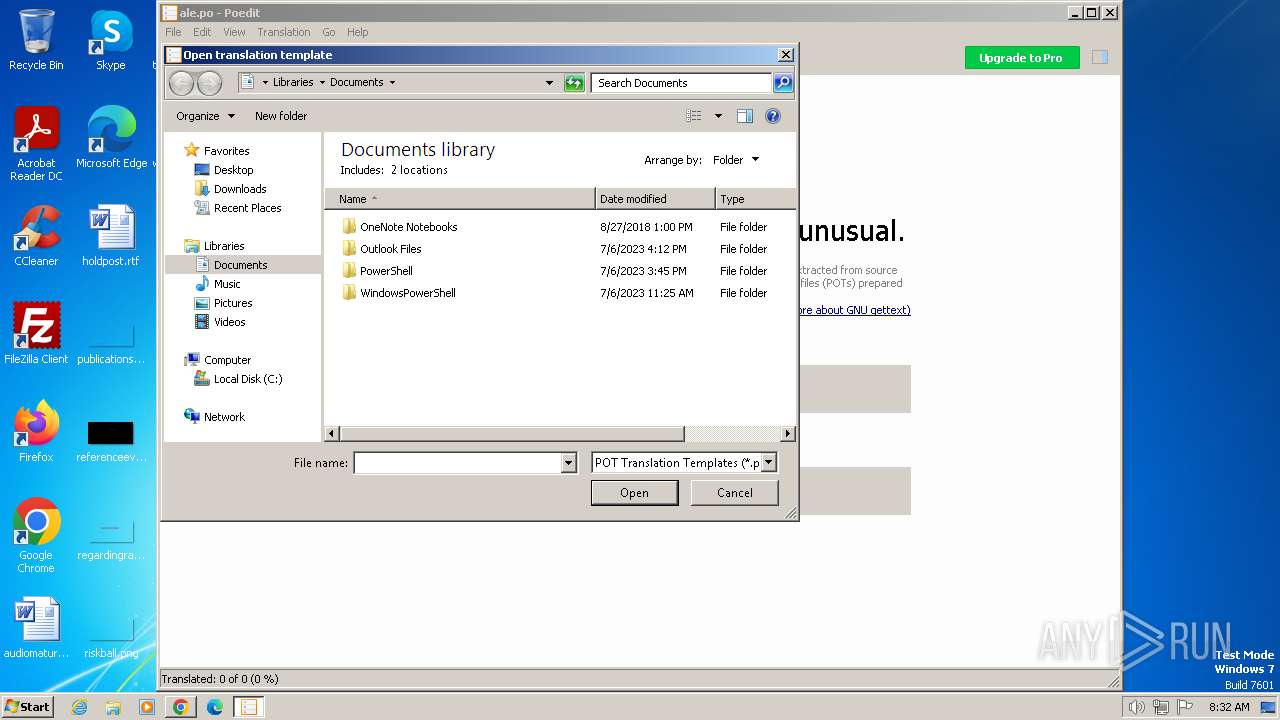
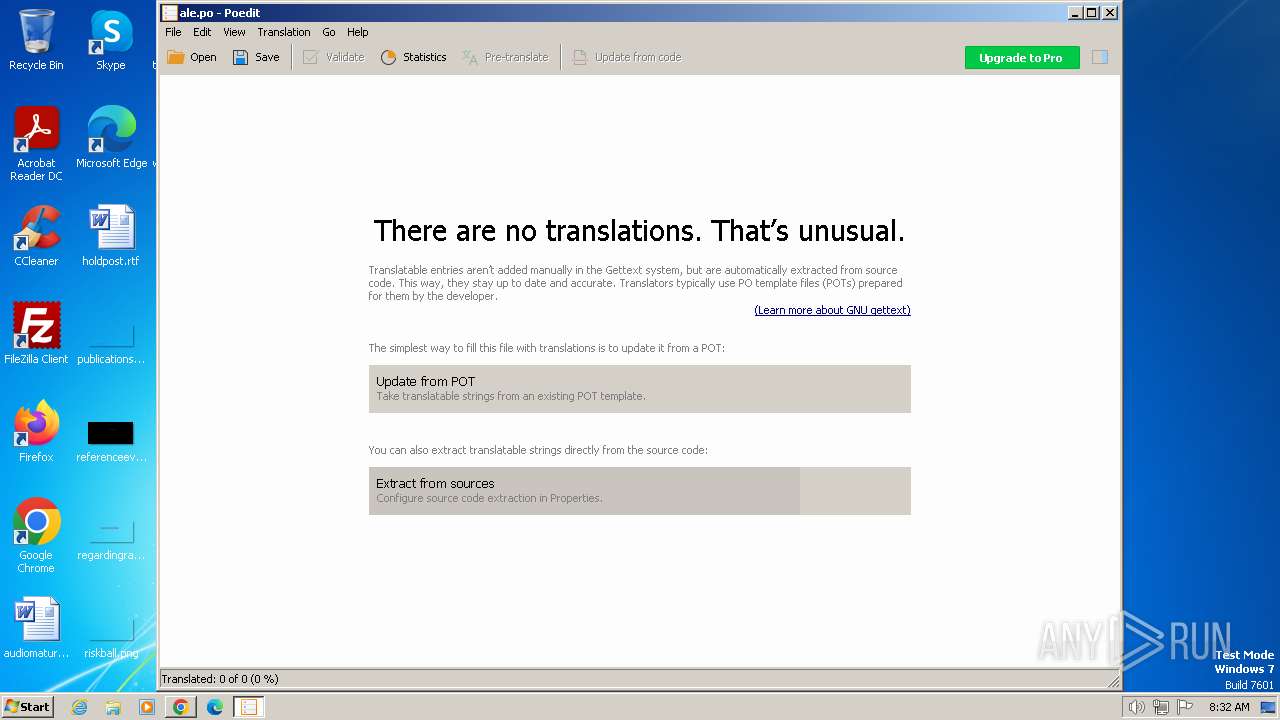
| 784 | "C:\Program Files\Poedit\Poedit.exe" | C:\Program Files\Poedit\Poedit.exe | Poedit-3.4.2-setup.tmp | ||||||||||||
User: admin Company: Vaclav Slavik Integrity Level: MEDIUM Description: Poedit Exit code: 0 Version: 3.4.2 Modules
| |||||||||||||||
| 840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --mojo-platform-channel-handle=2284 --field-trial-handle=1128,i,1794141905279178769,8964855523407109174,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --mojo-platform-channel-handle=3936 --field-trial-handle=1128,i,1794141905279178769,8964855523407109174,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1196 | "C:\Users\admin\AppData\Local\Temp\is-R2R06.tmp\Poedit-3.4.2-setup.tmp" /SL5="$60232,18952845,832512,C:\Users\admin\Downloads\Poedit-3.4.2-setup.exe" | C:\Users\admin\AppData\Local\Temp\is-R2R06.tmp\Poedit-3.4.2-setup.tmp | — | Poedit-3.4.2-setup.exe | |||||||||||
User: admin Company: Vaclav Slavik Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --disable-quic --mojo-platform-channel-handle=2116 --field-trial-handle=1128,i,1794141905279178769,8964855523407109174,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1376 | "C:\Users\admin\Downloads\Poedit-3.4.2-setup.exe" | C:\Users\admin\Downloads\Poedit-3.4.2-setup.exe | chrome.exe | ||||||||||||
User: admin Company: Vaclav Slavik Integrity Level: MEDIUM Description: Poedit Installer Exit code: 0 Version: 3.4.2 Modules
| |||||||||||||||
| 1624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=16 --mojo-platform-channel-handle=3864 --field-trial-handle=1128,i,1794141905279178769,8964855523407109174,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --mojo-platform-channel-handle=3668 --field-trial-handle=1128,i,1794141905279178769,8964855523407109174,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
30 138
Read events
29 805
Write events
313
Delete events
20
Modification events
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
202
Suspicious files
631
Text files
589
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 752 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:C274F203E827BA1F2283ED1D3A105806 | SHA256:3804158167E49780115547BB153E41E5D402AFCC9404731BF38ABFBBE65E00E9 | |||
| 2736 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:98D1FE2814944644C9A1714FCAF89748 | SHA256:6F5E08A0551280CEAC43EA2760F57BB34E941380DAC86B38B5AC04570FA98042 | |||
| 752 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2736 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 752 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[2].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF16bb46.TMP | — | |
MD5:— | SHA256:— | |||
| 3728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2736 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\666ADFE761C62A9599CF2B191CC8A40A | binary | |
MD5:172DA2D5B40EBFDF95CBC0A64E1C9283 | SHA256:86D64E6E1D6D4E147D5464D4FBD8F4FD35D2F0CCB25AECAD5310CA6403A5154D | |||
| 752 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{A464D52D-C4C9-11EE-AE0A-12A9866C77DE}.dat | binary | |
MD5:0686D51A4CE73853A83E77628C2C17D2 | SHA256:93D1FF6219F9630EE54963395C27B27F3F55357D6002B4398C347195380ADF50 | |||
| 2736 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab5589.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
64
DNS requests
81
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
752 | iexplore.exe | GET | 304 | 23.32.238.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?36150233369f924a | unknown | — | — | unknown |
752 | iexplore.exe | GET | 304 | 23.32.238.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?95d95b669c097e41 | unknown | — | — | unknown |
2736 | iexplore.exe | GET | 304 | 23.32.238.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f324de6a56943962 | unknown | — | — | unknown |
2736 | iexplore.exe | GET | 304 | 23.32.238.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?26bc83074cde97bc | unknown | — | — | unknown |
752 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 313 b | unknown |
2736 | iexplore.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
2736 | iexplore.exe | GET | 200 | 23.32.238.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?d7a4c83e7f191cf0 | unknown | compressed | 65.2 Kb | unknown |
2736 | iexplore.exe | GET | 200 | 23.32.238.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?5da2680ebcdcdef2 | unknown | compressed | 65.2 Kb | unknown |
2736 | iexplore.exe | GET | 200 | 184.24.77.54:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgOu4NHhAPyFsQP4WqRO7qesrg%3D%3D | unknown | binary | 503 b | unknown |
1080 | svchost.exe | GET | 304 | 41.63.96.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?624d1ab720bef5f8 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2736 | iexplore.exe | 169.150.247.38:443 | download.poedit.net | — | GB | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2736 | iexplore.exe | 23.32.238.178:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
752 | iexplore.exe | 92.123.104.20:443 | www.bing.com | Akamai International B.V. | DE | unknown |
752 | iexplore.exe | 23.32.238.178:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
752 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2736 | iexplore.exe | 69.192.161.44:80 | x1.c.lencr.org | AKAMAI-AS | DE | unknown |
2736 | iexplore.exe | 184.24.77.54:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.poedit.net |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
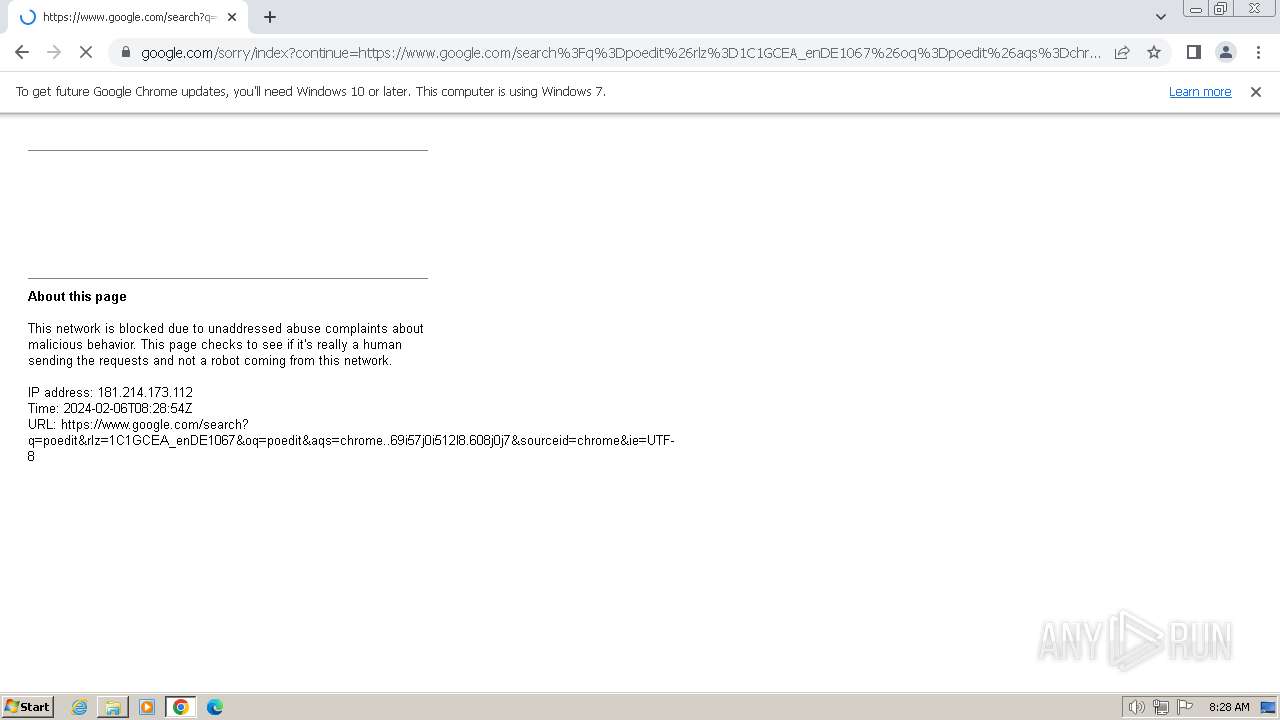
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2916 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] A free CDN for open source projects (jsdelivr .net) |