| File name: | fvfd.exe |
| Full analysis: | https://app.any.run/tasks/80408adc-69ab-4f79-b75c-91e5aea8df64 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | August 12, 2022, 16:08:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | 83418A9AF56DB91FF2C78C4B2B9D62F8 |
| SHA1: | 0EA68AAB3721E509CE0B1BFF7E574EDA037798BE |
| SHA256: | 4A688F571024B08F9793559427D8692471F5AA715882899C631C3052EAC7C6A1 |
| SSDEEP: | 6144:/6ZMFXzqfoSHr/mvcQYbi2HN8C8BgifO7y7TcuVqrWLWN7Ypsi6Ih9vH0/oUHahE:/8MFX47ivcQMNsrD4KJjO69cI |
MALICIOUS
EMOTET detected by memory dumps
- regsvr32.exe (PID: 3244)
Connects to CnC server
- regsvr32.exe (PID: 3244)
Drops executable file immediately after starts
- rundll32.exe (PID: 3160)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 3244)
SUSPICIOUS
Executable content was dropped or overwritten
- rundll32.exe (PID: 3160)
Drops a file with a compile date too recent
- rundll32.exe (PID: 3160)
INFO
Checks supported languages
- rundll32.exe (PID: 3160)
- taskmgr.exe (PID: 924)
- explorer.exe (PID: 2708)
- regsvr32.exe (PID: 3244)
Loads main object executable
- rundll32.exe (PID: 3160)
Reads the computer name
- regsvr32.exe (PID: 3244)
- taskmgr.exe (PID: 924)
- explorer.exe (PID: 2708)
- rundll32.exe (PID: 3160)
Reads settings of System Certificates
- regsvr32.exe (PID: 3244)
Manual execution by user
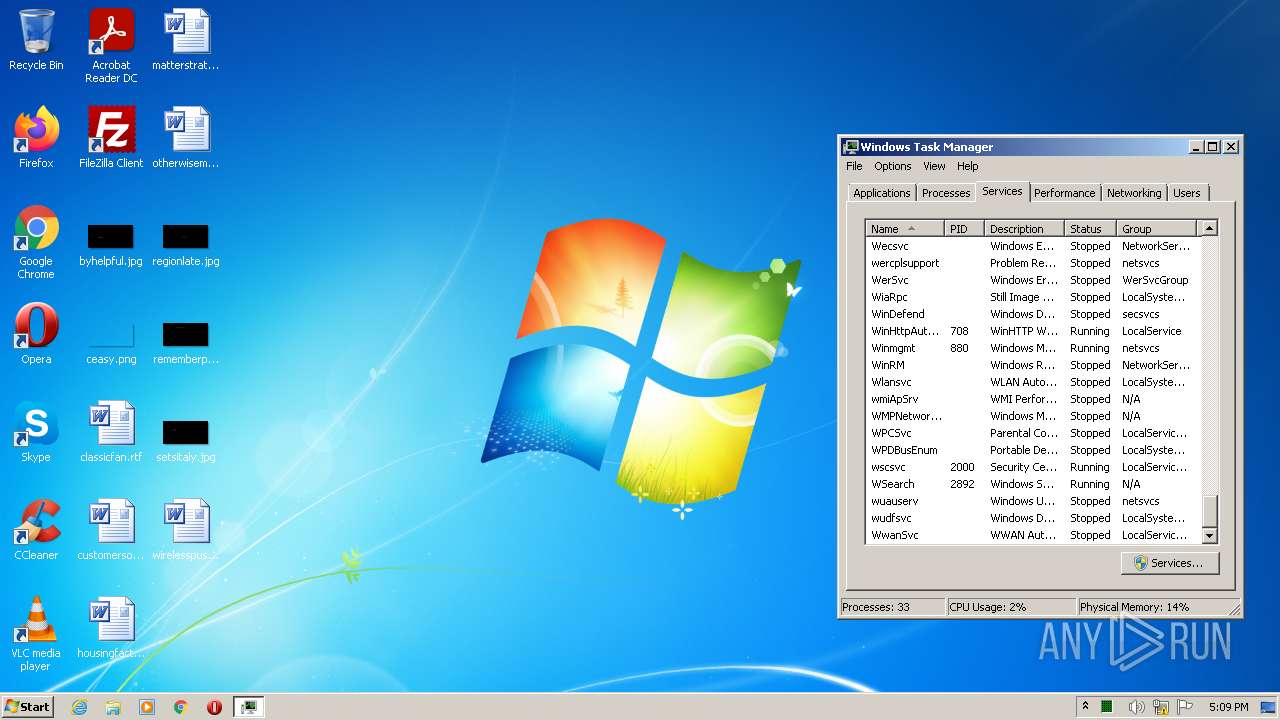
- taskmgr.exe (PID: 924)
- explorer.exe (PID: 2708)
Checks Windows Trust Settings
- regsvr32.exe (PID: 3244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Emotet
(PID) Process(3244) regsvr32.exe
C2 (58)70.36.102.35:443
92.240.254.110:8080
51.91.76.89:8080
217.182.25.250:8080
119.193.124.41:7080
45.142.114.231:8080
176.56.128.118:443
51.254.140.238:7080
173.212.193.249:8080
131.100.24.231:80
188.44.20.25:443
1.234.2.232:8080
153.126.146.25:7080
51.91.7.5:8080
151.106.112.196:8080
46.55.222.11:443
107.182.225.142:8080
82.165.152.127:8080
212.237.17.99:8080
195.201.151.129:8080
197.242.150.244:8080
103.43.46.182:443
206.188.212.92:8080
196.218.30.83:443
5.9.116.246:8080
185.157.82.211:8080
176.104.106.96:8080
159.65.88.10:8080
212.24.98.99:8080
209.250.246.206:443
45.118.135.203:7080
50.116.54.215:443
178.79.147.66:8080
72.15.201.15:8080
101.50.0.91:8080
103.75.201.2:443
31.24.158.56:8080
146.59.226.45:443
110.232.117.186:8080
138.185.72.26:8080
45.176.232.124:443
189.126.111.200:7080
129.232.188.93:443
158.69.222.101:443
164.68.99.3:8080
209.126.98.206:8080
58.227.42.236:80
203.114.109.124:443
195.154.133.20:443
192.99.251.50:443
1.234.21.73:7080
50.30.40.196:8080
216.158.226.206:443
185.8.212.130:7080
159.8.59.82:8080
45.118.115.99:8080
167.99.115.35:8080
79.172.212.216:8080
Keys
ECS1-----BEGIN PUBLIC KEY-----
MFkwEwYHKoZIzj0CAQYIKoZIzj0DAQcDQgAEQF90tsTY3Aw9HwZ6N9y5+be9Xoov
pqHyD6F5DRTl9THosAoePIs/e5AdJiYxhmV8Gq3Zw1ysSPBghxjZdDxY+Q==
-----END PUBLIC KEY-----
ECK1-----BEGIN PUBLIC KEY-----
MFkwEwYHKoZIzj0CAQYIKoZIzj0DAQcDQgAE86M1tQ4uK/Q1Vs0KTCk+fPEQ3cuw
TyCz+gIgzky2DB5Elr60DubJW5q9Tr2dj8/gEFs0TIIEJgLTuqzx+58sdg==
-----END PUBLIC KEY-----
Strings (44)--%S--
%u.%u.%u.%u
Cookie: %s=%s
Content-Type: multipart/form-data; boundary=%s
--%S
Content-Disposition: form-data; name="%S"; filename="%S"
Content-Type: application/octet-stream
%s\%s
%s\*
%s:Zone.Identifier
%s\%s.exe
crypt32.dll
bcrypt.dll
urlmon.dll
shell32.dll
wtsapi32.dll
userenv.dll
shlwapi.dll
wininet.dll
advapi32.dll
POST
WinSta0\Default
%s\%s
%s\regsvr32.exe /s "%s\%s"
%s\%s%x
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
%s\regsvr32.exe /s "%s\%s" %s
RNG
%s_%08X
nltest /dclist:
ipconfig /all
systeminfo
Microsoft Primitive Provider
ECCPUBLICBLOB
ObjectLength
SHA256
ECDSA_P256
AES
HASH
ECDH_P256
KeyDataBlob
%s%s.dll
%s%s.exe
%s\regsvr32.exe /s "%s"
%s\regsvr32.exe /s "%s" %s
DllRegisterServer
C2 (58)70.36.102.35:443
92.240.254.110:8080
51.91.76.89:8080
217.182.25.250:8080
119.193.124.41:7080
45.142.114.231:8080
176.56.128.118:443
51.254.140.238:7080
173.212.193.249:8080
131.100.24.231:80
188.44.20.25:443
1.234.2.232:8080
153.126.146.25:7080
51.91.7.5:8080
151.106.112.196:8080
46.55.222.11:443
107.182.225.142:8080
82.165.152.127:8080
212.237.17.99:8080
195.201.151.129:8080
197.242.150.244:8080
103.43.46.182:443
206.188.212.92:8080
196.218.30.83:443
5.9.116.246:8080
185.157.82.211:8080
176.104.106.96:8080
159.65.88.10:8080
212.24.98.99:8080
209.250.246.206:443
45.118.135.203:7080
50.116.54.215:443
178.79.147.66:8080
72.15.201.15:8080
101.50.0.91:8080
103.75.201.2:443
31.24.158.56:8080
146.59.226.45:443
110.232.117.186:8080
138.185.72.26:8080
45.176.232.124:443
189.126.111.200:7080
129.232.188.93:443
158.69.222.101:443
164.68.99.3:8080
209.126.98.206:8080
58.227.42.236:80
203.114.109.124:443
195.154.133.20:443
192.99.251.50:443
1.234.21.73:7080
50.30.40.196:8080
216.158.226.206:443
185.8.212.130:7080
159.8.59.82:8080
45.118.115.99:8080
167.99.115.35:8080
79.172.212.216:8080
Keys
ECS1-----BEGIN PUBLIC KEY-----
MFkwEwYHKoZIzj0CAQYIKoZIzj0DAQcDQgAEQF90tsTY3Aw9HwZ6N9y5+be9Xoov
pqHyD6F5DRTl9THosAoePIs/e5AdJiYxhmV8Gq3Zw1ysSPBghxjZdDxY+Q==
-----END PUBLIC KEY-----
ECK1-----BEGIN PUBLIC KEY-----
MFkwEwYHKoZIzj0CAQYIKoZIzj0DAQcDQgAE86M1tQ4uK/Q1Vs0KTCk+fPEQ3cuw
TyCz+gIgzky2DB5Elr60DubJW5q9Tr2dj8/gEFs0TIIEJgLTuqzx+58sdg==
-----END PUBLIC KEY-----
Strings (44)--%S--
%u.%u.%u.%u
Cookie: %s=%s
Content-Type: multipart/form-data; boundary=%s
--%S
Content-Disposition: form-data; name="%S"; filename="%S"
Content-Type: application/octet-stream
%s\%s
%s\*
%s:Zone.Identifier
%s\%s.exe
crypt32.dll
bcrypt.dll
urlmon.dll
shell32.dll
wtsapi32.dll
userenv.dll
shlwapi.dll
wininet.dll
advapi32.dll
POST
WinSta0\Default
%s\%s
%s\regsvr32.exe /s "%s\%s"
%s\%s%x
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
%s\regsvr32.exe /s "%s\%s" %s
RNG
%s_%08X
nltest /dclist:
ipconfig /all
systeminfo
Microsoft Primitive Provider
ECCPUBLICBLOB
ObjectLength
SHA256
ECDSA_P256
AES
HASH
ECDH_P256
KeyDataBlob
%s%s.dll
%s%s.exe
%s\regsvr32.exe /s "%s"
%s\regsvr32.exe /s "%s" %s
DllRegisterServer
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (38.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (34.3) |
| .scr | | | Windows screen saver (16.2) |
| .exe | | | Win32 Executable (generic) (5.6) |
| .exe | | | Generic Win/DOS Executable (2.4) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1131c |
| UninitializedDataSize: | - |
| InitializedDataSize: | 421888 |
| CodeSize: | 241664 |
| LinkerVersion: | 7.1 |
| PEType: | PE32 |
| TimeStamp: | 2022:03:25 00:15:10+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Mar-2022 23:15:10 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 24-Mar-2022 23:15:10 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0003A49E | 0x0003B000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.61164 |
.rdata | 0x0003C000 | 0x0000EAAE | 0x0000F000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04653 |
.data | 0x0004B000 | 0x00005CB8 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.83461 |
.rsrc | 0x00051000 | 0x000480A0 | 0x00049000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.07779 |
.reloc | 0x0009A000 | 0x00008810 | 0x00009000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.48952 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.42708 | 67624 | UNKNOWN | Spanish - Spain (International sort) | RT_ICON |
2 | 3.42708 | 67624 | UNKNOWN | Spanish - Spain (International sort) | RT_ICON |
3 | 2.4028 | 744 | UNKNOWN | Spanish - Spain (International sort) | RT_ICON |
4 | 2.68898 | 296 | UNKNOWN | Spanish - Spain (International sort) | RT_ICON |
5 | 2.4028 | 744 | UNKNOWN | Spanish - Spain (International sort) | RT_ICON |
6 | 2.68898 | 296 | UNKNOWN | Spanish - Spain (International sort) | RT_ICON |
7 | 2.4028 | 744 | UNKNOWN | Spanish - Spain (International sort) | RT_ICON |
8 | 2.68898 | 296 | UNKNOWN | Spanish - Spain (International sort) | RT_ICON |
9 | 2.57534 | 146 | UNKNOWN | Spanish - Spain (International sort) | RT_STRING |
10 | 2.74274 | 180 | UNKNOWN | Spanish - Spain (International sort) | RT_CURSOR |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEACC.dll (delay-loaded) |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WINSPOOL.DRV |
Exports
Title | Ordinal | Address |
|---|---|---|
DllRegisterServer | 1 | 0x00005090 |
DllUnregisterServerr | 2 | 0x000050C0 |
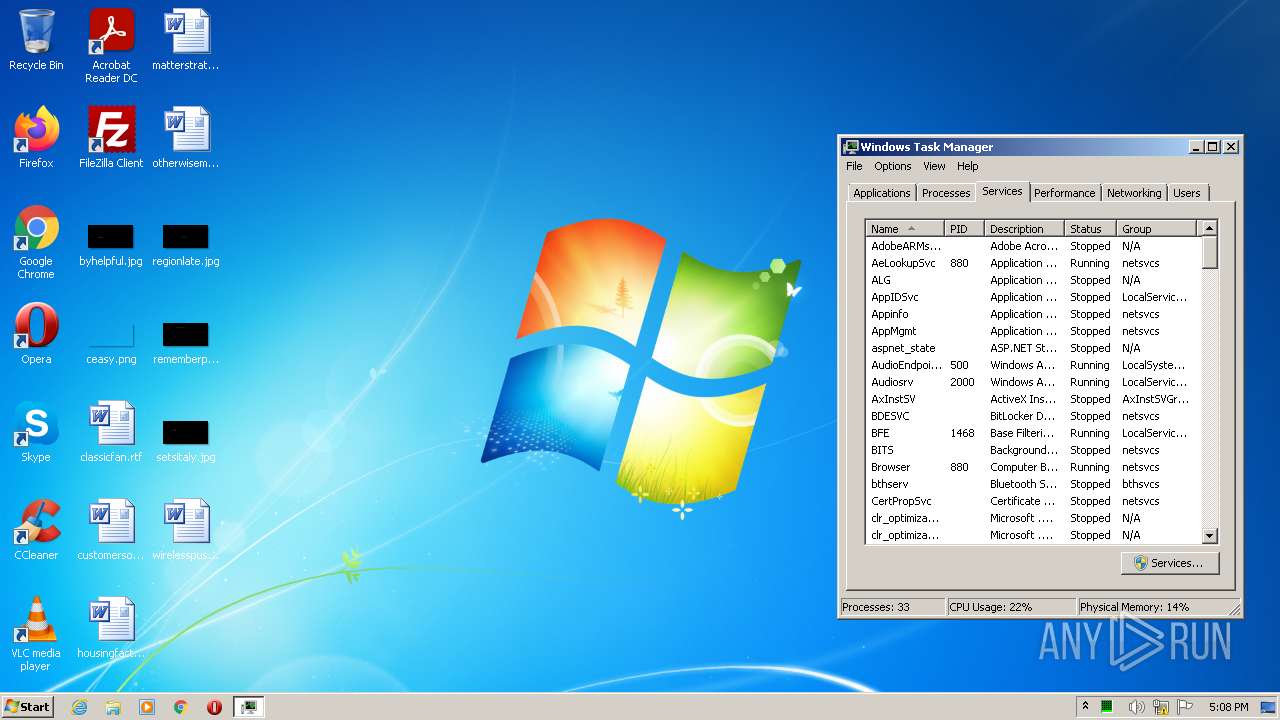
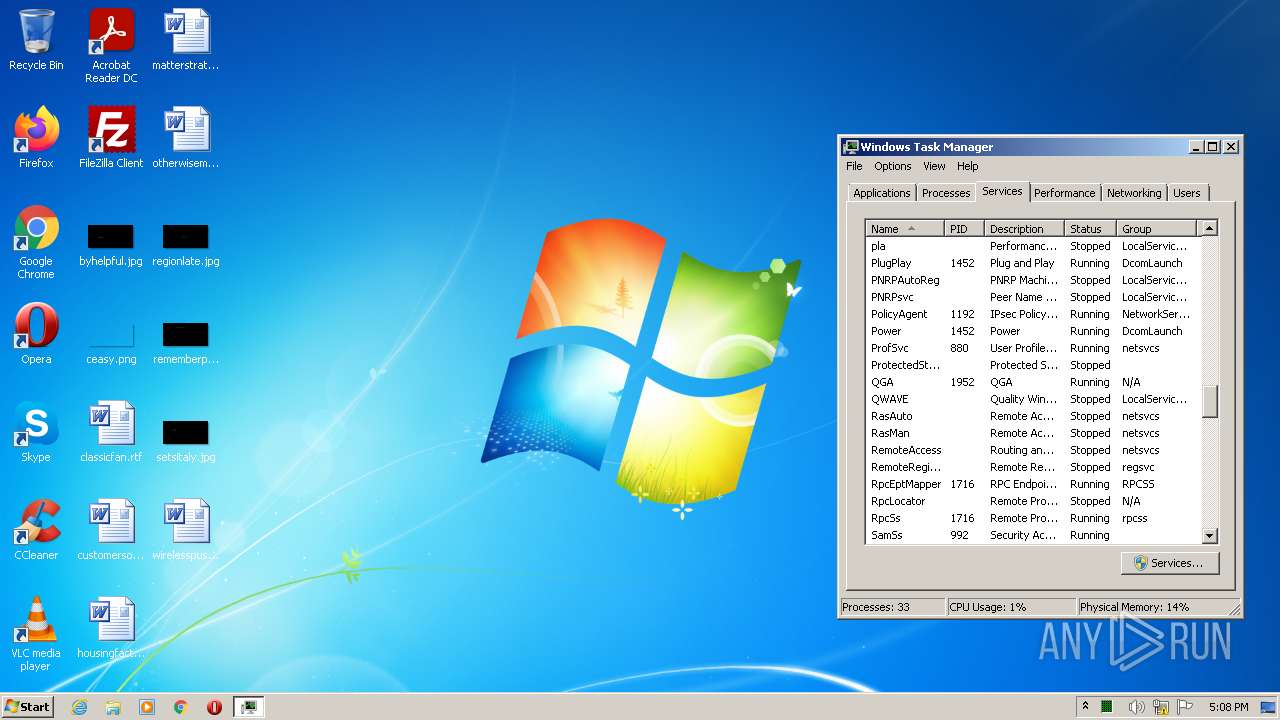
Total processes
41
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 924 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2708 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3160 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\fvfd.exe", DllRegisterServer | C:\Windows\System32\rundll32.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3244 | C:\Windows\system32\regsvr32.exe /s "C:\Users\admin\AppData\Local\Kmabujgvflhj\jons.wnd" | C:\Windows\system32\regsvr32.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
Emotet(PID) Process(3244) regsvr32.exe C2 (58)70.36.102.35:443 92.240.254.110:8080 51.91.76.89:8080 217.182.25.250:8080 119.193.124.41:7080 45.142.114.231:8080 176.56.128.118:443 51.254.140.238:7080 173.212.193.249:8080 131.100.24.231:80 188.44.20.25:443 1.234.2.232:8080 153.126.146.25:7080 51.91.7.5:8080 151.106.112.196:8080 46.55.222.11:443 107.182.225.142:8080 82.165.152.127:8080 212.237.17.99:8080 195.201.151.129:8080 197.242.150.244:8080 103.43.46.182:443 206.188.212.92:8080 196.218.30.83:443 5.9.116.246:8080 185.157.82.211:8080 176.104.106.96:8080 159.65.88.10:8080 212.24.98.99:8080 209.250.246.206:443 45.118.135.203:7080 50.116.54.215:443 178.79.147.66:8080 72.15.201.15:8080 101.50.0.91:8080 103.75.201.2:443 31.24.158.56:8080 146.59.226.45:443 110.232.117.186:8080 138.185.72.26:8080 45.176.232.124:443 189.126.111.200:7080 129.232.188.93:443 158.69.222.101:443 164.68.99.3:8080 209.126.98.206:8080 58.227.42.236:80 203.114.109.124:443 195.154.133.20:443 192.99.251.50:443 1.234.21.73:7080 50.30.40.196:8080 216.158.226.206:443 185.8.212.130:7080 159.8.59.82:8080 45.118.115.99:8080 167.99.115.35:8080 79.172.212.216:8080 Keys ECS1-----BEGIN PUBLIC KEY-----
MFkwEwYHKoZIzj0CAQYIKoZIzj0DAQcDQgAEQF90tsTY3Aw9HwZ6N9y5+be9Xoov
pqHyD6F5DRTl9THosAoePIs/e5AdJiYxhmV8Gq3Zw1ysSPBghxjZdDxY+Q==
-----END PUBLIC KEY----- ECK1-----BEGIN PUBLIC KEY-----
MFkwEwYHKoZIzj0CAQYIKoZIzj0DAQcDQgAE86M1tQ4uK/Q1Vs0KTCk+fPEQ3cuw
TyCz+gIgzky2DB5Elr60DubJW5q9Tr2dj8/gEFs0TIIEJgLTuqzx+58sdg==
-----END PUBLIC KEY----- Strings (44)--%S-- %u.%u.%u.%u Cookie: %s=%s Content-Type: multipart/form-data; boundary=%s --%S
Content-Disposition: form-data; name="%S"; filename="%S"
Content-Type: application/octet-stream %s\%s %s\* %s:Zone.Identifier %s\%s.exe crypt32.dll bcrypt.dll urlmon.dll shell32.dll wtsapi32.dll userenv.dll shlwapi.dll wininet.dll advapi32.dll POST WinSta0\Default %s\%s %s\regsvr32.exe /s "%s\%s" %s\%s%x SOFTWARE\Microsoft\Windows\CurrentVersion\Run %s\regsvr32.exe /s "%s\%s" %s RNG %s_%08X nltest /dclist: ipconfig /all systeminfo Microsoft Primitive Provider ECCPUBLICBLOB ObjectLength SHA256 ECDSA_P256 AES HASH ECDH_P256 KeyDataBlob %s%s.dll %s%s.exe %s\regsvr32.exe /s "%s" %s\regsvr32.exe /s "%s" %s DllRegisterServer (PID) Process(3244) regsvr32.exe C2 (58)70.36.102.35:443 92.240.254.110:8080 51.91.76.89:8080 217.182.25.250:8080 119.193.124.41:7080 45.142.114.231:8080 176.56.128.118:443 51.254.140.238:7080 173.212.193.249:8080 131.100.24.231:80 188.44.20.25:443 1.234.2.232:8080 153.126.146.25:7080 51.91.7.5:8080 151.106.112.196:8080 46.55.222.11:443 107.182.225.142:8080 82.165.152.127:8080 212.237.17.99:8080 195.201.151.129:8080 197.242.150.244:8080 103.43.46.182:443 206.188.212.92:8080 196.218.30.83:443 5.9.116.246:8080 185.157.82.211:8080 176.104.106.96:8080 159.65.88.10:8080 212.24.98.99:8080 209.250.246.206:443 45.118.135.203:7080 50.116.54.215:443 178.79.147.66:8080 72.15.201.15:8080 101.50.0.91:8080 103.75.201.2:443 31.24.158.56:8080 146.59.226.45:443 110.232.117.186:8080 138.185.72.26:8080 45.176.232.124:443 189.126.111.200:7080 129.232.188.93:443 158.69.222.101:443 164.68.99.3:8080 209.126.98.206:8080 58.227.42.236:80 203.114.109.124:443 195.154.133.20:443 192.99.251.50:443 1.234.21.73:7080 50.30.40.196:8080 216.158.226.206:443 185.8.212.130:7080 159.8.59.82:8080 45.118.115.99:8080 167.99.115.35:8080 79.172.212.216:8080 Keys ECS1-----BEGIN PUBLIC KEY-----
MFkwEwYHKoZIzj0CAQYIKoZIzj0DAQcDQgAEQF90tsTY3Aw9HwZ6N9y5+be9Xoov
pqHyD6F5DRTl9THosAoePIs/e5AdJiYxhmV8Gq3Zw1ysSPBghxjZdDxY+Q==
-----END PUBLIC KEY----- ECK1-----BEGIN PUBLIC KEY-----
MFkwEwYHKoZIzj0CAQYIKoZIzj0DAQcDQgAE86M1tQ4uK/Q1Vs0KTCk+fPEQ3cuw
TyCz+gIgzky2DB5Elr60DubJW5q9Tr2dj8/gEFs0TIIEJgLTuqzx+58sdg==
-----END PUBLIC KEY----- Strings (44)--%S-- %u.%u.%u.%u Cookie: %s=%s Content-Type: multipart/form-data; boundary=%s --%S
Content-Disposition: form-data; name="%S"; filename="%S"
Content-Type: application/octet-stream %s\%s %s\* %s:Zone.Identifier %s\%s.exe crypt32.dll bcrypt.dll urlmon.dll shell32.dll wtsapi32.dll userenv.dll shlwapi.dll wininet.dll advapi32.dll POST WinSta0\Default %s\%s %s\regsvr32.exe /s "%s\%s" %s\%s%x SOFTWARE\Microsoft\Windows\CurrentVersion\Run %s\regsvr32.exe /s "%s\%s" %s RNG %s_%08X nltest /dclist: ipconfig /all systeminfo Microsoft Primitive Provider ECCPUBLICBLOB ObjectLength SHA256 ECDSA_P256 AES HASH ECDH_P256 KeyDataBlob %s%s.dll %s%s.exe %s\regsvr32.exe /s "%s" %s\regsvr32.exe /s "%s" %s DllRegisterServer | |||||||||||||||
Total events
3 605
Read events
3 539
Write events
64
Delete events
2
Modification events
| (PID) Process: | (3244) regsvr32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3244) regsvr32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3244) regsvr32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3244) regsvr32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3244) regsvr32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3244) regsvr32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3244) regsvr32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{362E934C-743B-4588-8259-D2482DB771A8} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
| (PID) Process: | (3244) regsvr32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{362E934C-743B-4588-8259-D2482DB771A8} |
| Operation: | write | Name: | WpadDecisionTime |
Value: D04307C465AED801 | |||
| (PID) Process: | (3244) regsvr32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{362E934C-743B-4588-8259-D2482DB771A8} |
| Operation: | write | Name: | WpadDecision |
Value: 0 | |||
| (PID) Process: | (3244) regsvr32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{362E934C-743B-4588-8259-D2482DB771A8} |
| Operation: | write | Name: | WpadNetworkName |
Value: Network 4 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3160 | rundll32.exe | C:\Users\admin\AppData\Local\Kmabujgvflhj\jons.wnd | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
14
DNS requests
3
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
444 | svchost.exe | GET | 404 | 23.216.77.69:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c9b97448db899c45 | US | xml | 341 b | whitelisted |
444 | svchost.exe | GET | 404 | 67.27.235.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6222b3da51bb1163 | US | xml | 341 b | whitelisted |
3244 | regsvr32.exe | GET | 404 | 8.249.61.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8419297a08e74ad2 | US | xml | 341 b | whitelisted |
3244 | regsvr32.exe | GET | 404 | 67.27.235.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3564613867e1a183 | US | xml | 341 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3244 | regsvr32.exe | 70.36.102.35:443 | — | Perfect International, Inc | US | malicious |
3244 | regsvr32.exe | 92.240.254.110:8080 | — | LightStorm Communications s.r.o. | SK | malicious |
3244 | regsvr32.exe | 51.91.76.89:8080 | — | — | GB | malicious |
444 | svchost.exe | 67.27.235.126:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3244 | regsvr32.exe | 217.182.25.250:8080 | — | OVH SAS | FR | malicious |
3244 | regsvr32.exe | 119.193.124.41:7080 | — | Korea Telecom | KR | malicious |
444 | svchost.exe | 23.216.77.69:80 | ctldl.windowsupdate.com | NTT DOCOMO, INC. | US | suspicious |
3244 | regsvr32.exe | 45.142.114.231:8080 | — | — | — | malicious |
3244 | regsvr32.exe | 176.56.128.118:443 | — | SEEWEB s.r.l. | CH | malicious |
3244 | regsvr32.exe | 51.254.140.238:7080 | — | OVH SAS | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3244 | regsvr32.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 20 |
3244 | regsvr32.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 3 |
3244 | regsvr32.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 18 |
3244 | regsvr32.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 4 |
2 ETPRO signatures available at the full report