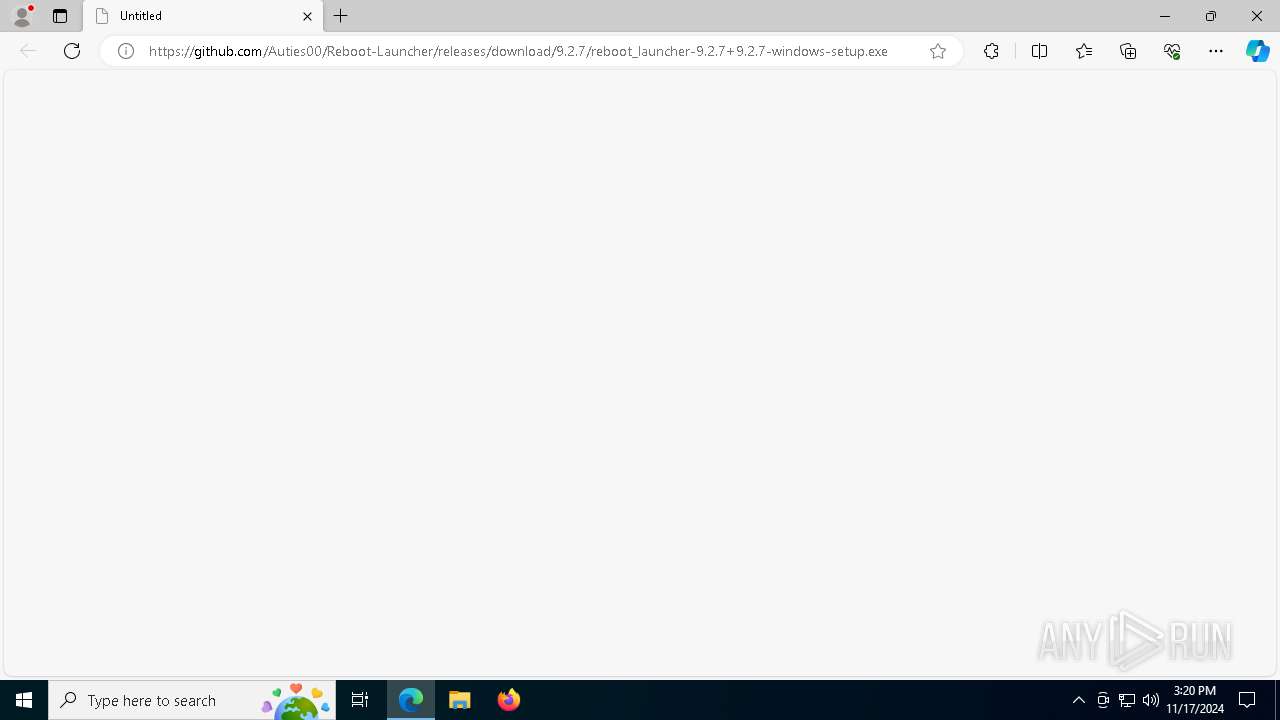
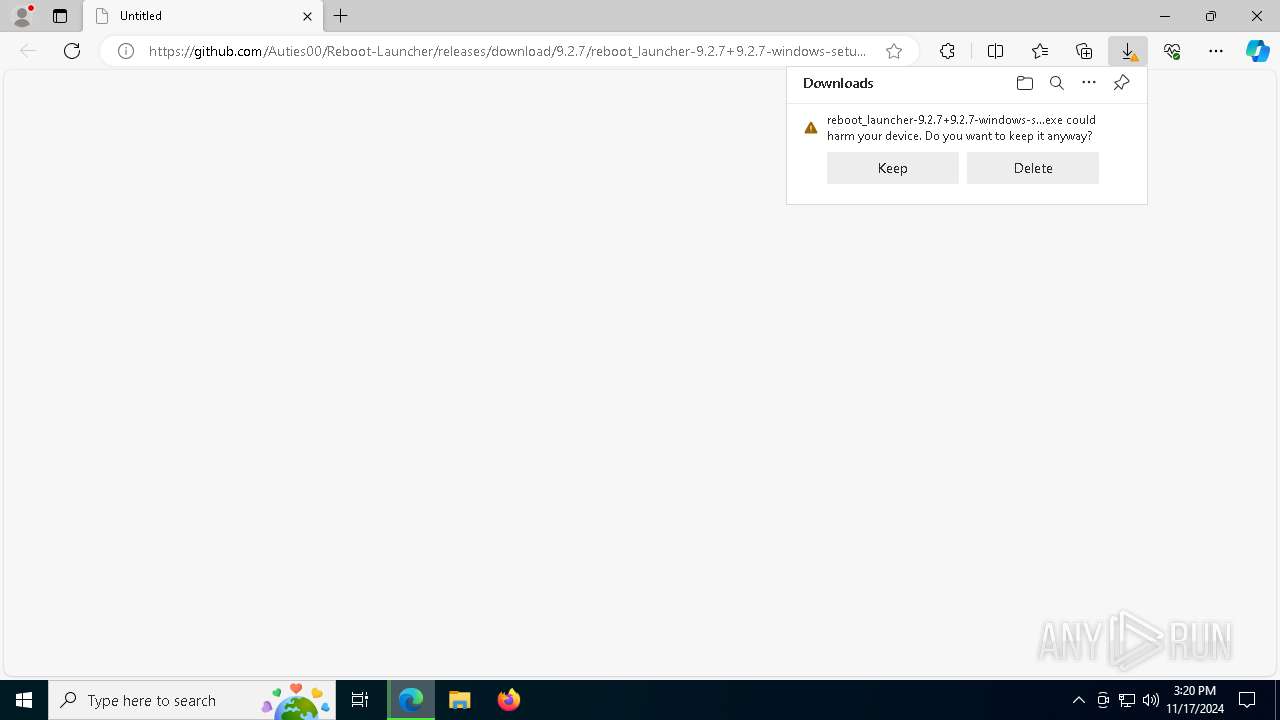
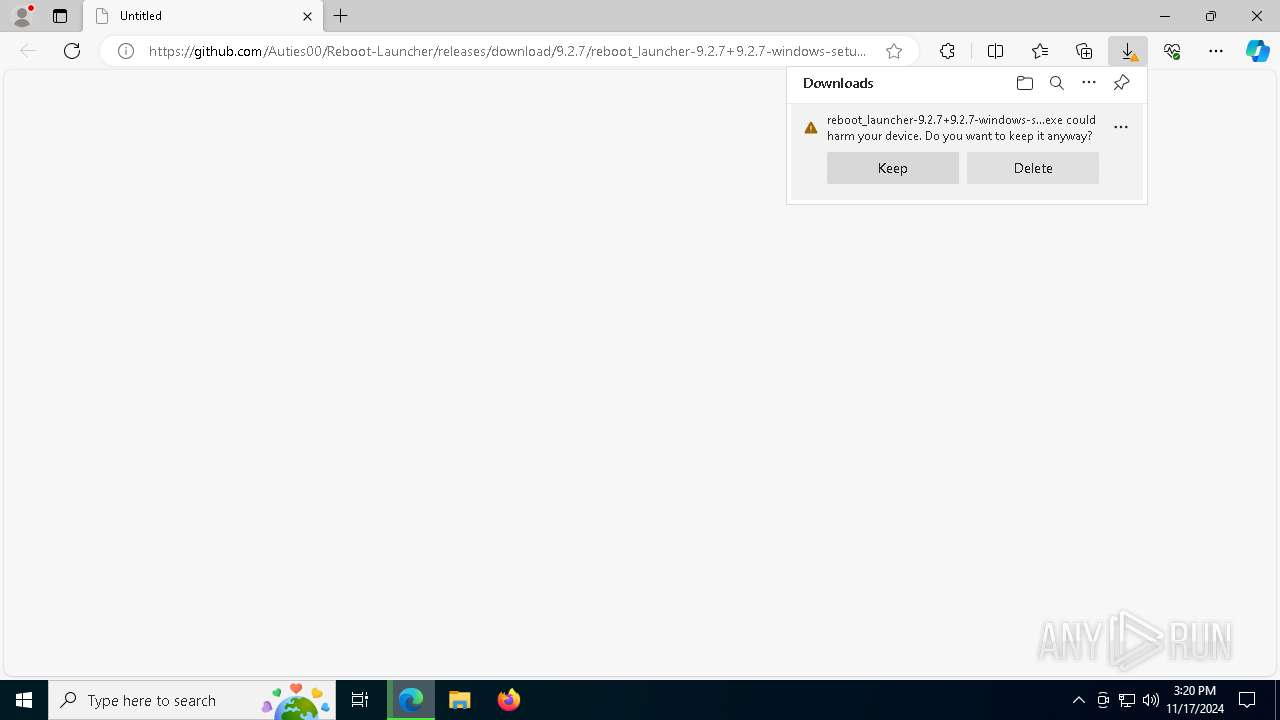
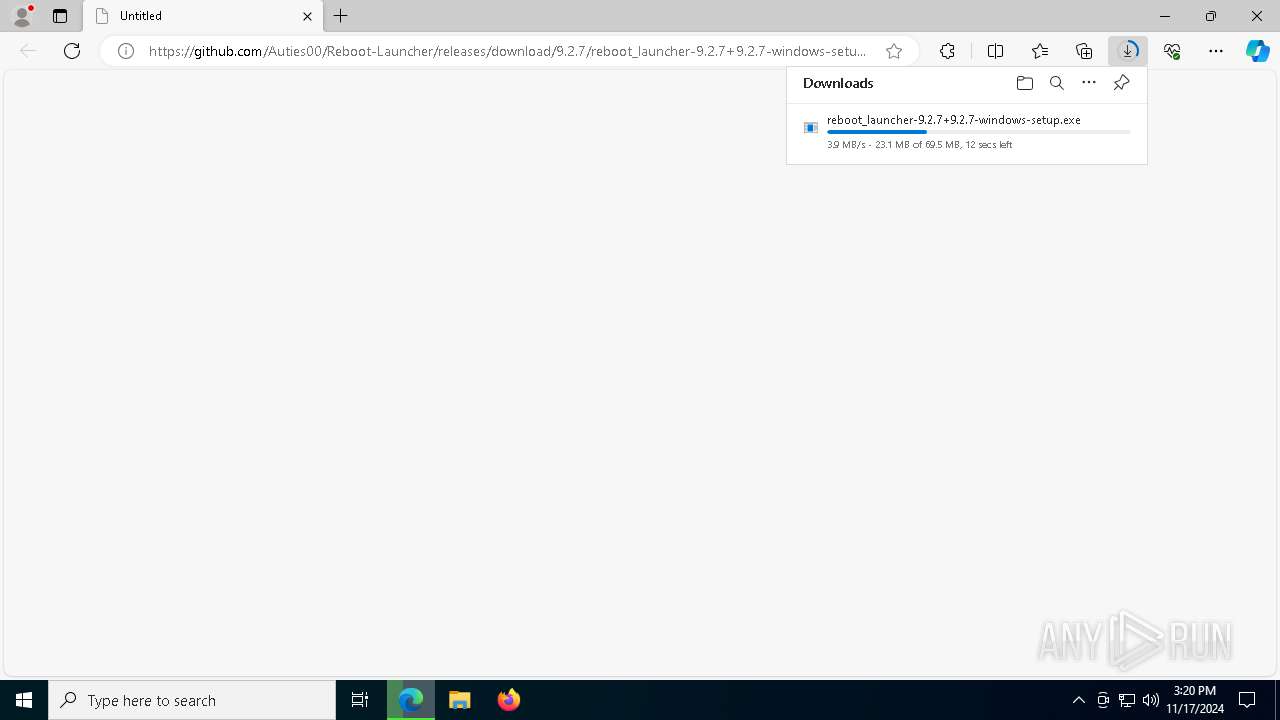
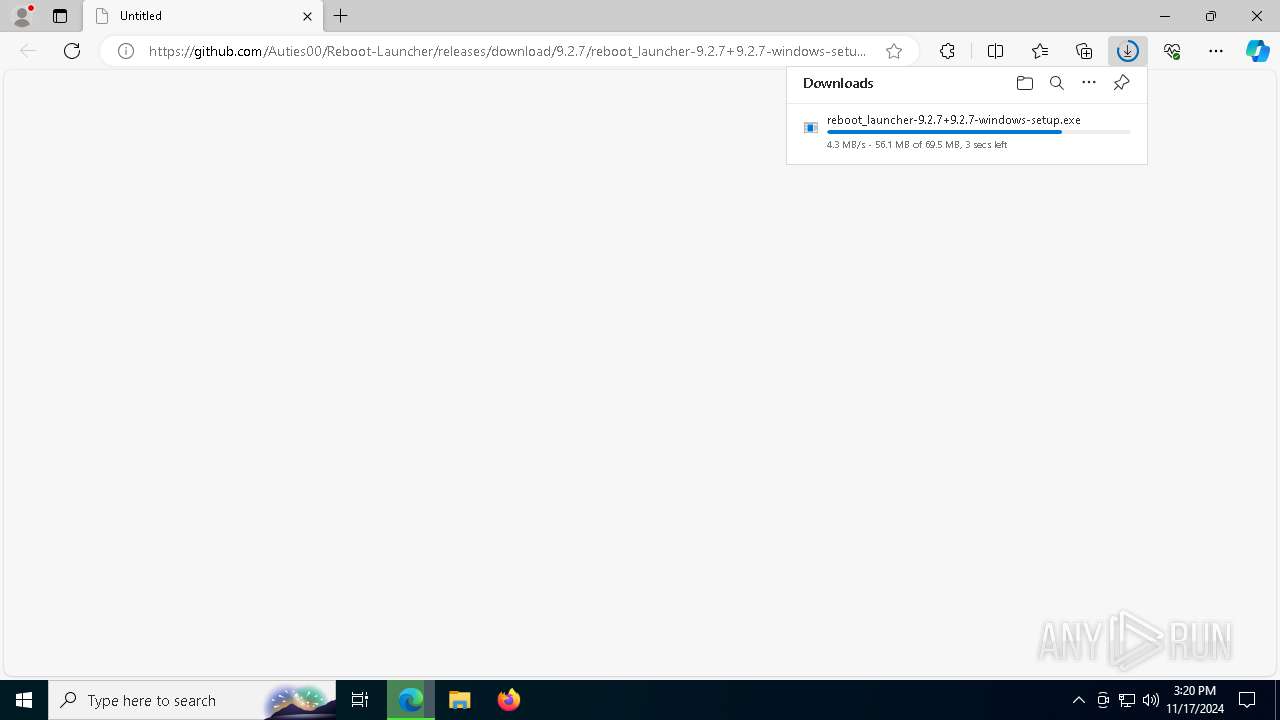
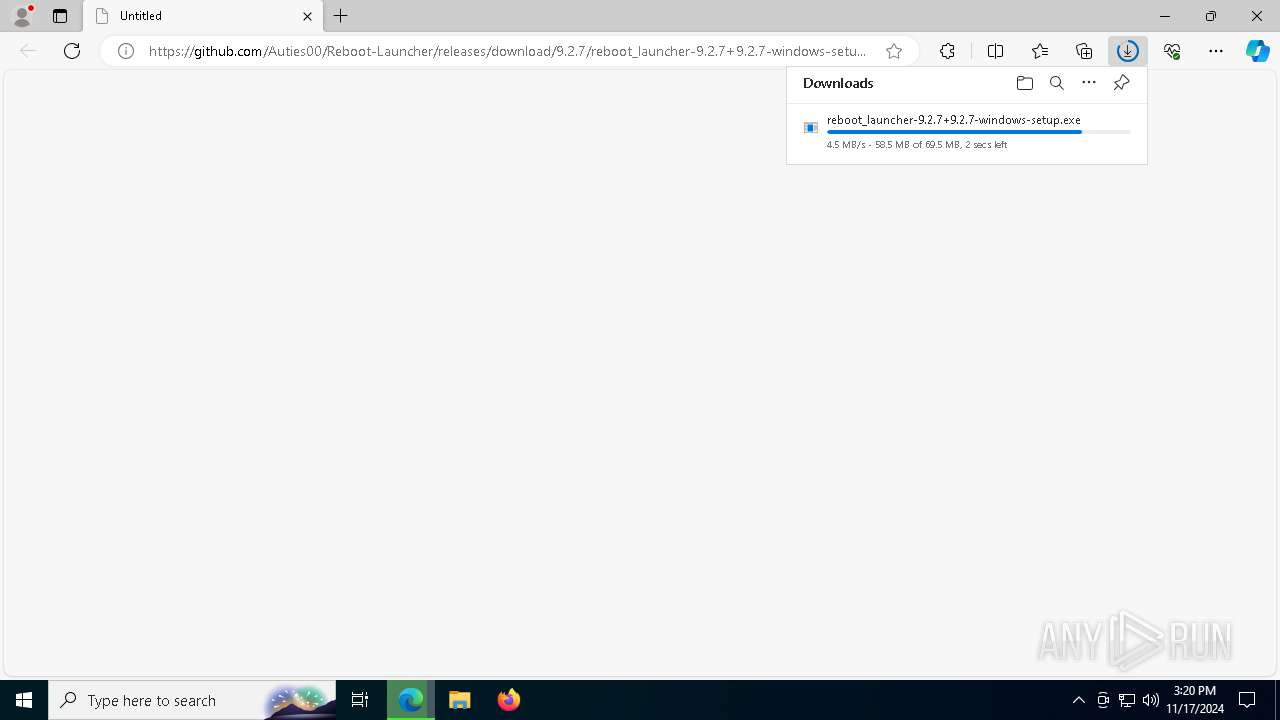
| URL: | https://github.com/Auties00/Reboot-Launcher/releases/download/9.2.7/reboot_launcher-9.2.7+9.2.7-windows-setup.exe |
| Full analysis: | https://app.any.run/tasks/7ddb4db5-d80d-4b02-bc99-d27a4934b0a2 |
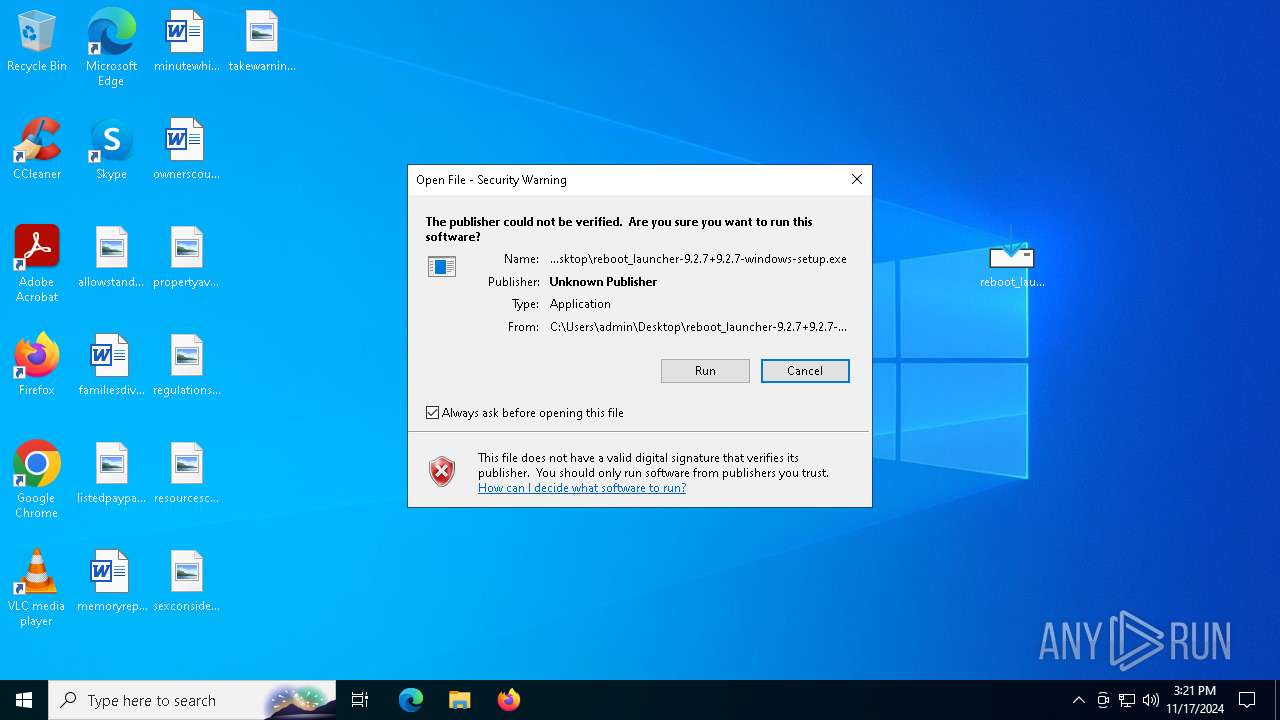
| Verdict: | Malicious activity |
| Analysis date: | November 17, 2024, 15:20:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D1E62D240764D0AFE2448DB835A3C7F2 |
| SHA1: | 2C9AF532FA61B370398EA7142A059910F5C09072 |
| SHA256: | 4A66AFF489CC465DC96CB5411F7142A832642BB663D30B0831B75C146EFD6F60 |
| SSDEEP: | 3:N8tEdfB9yRRL1E2kCcjL5XiKKefUO6bSULDXA:2udvoL1ry35XDG3XA |
MALICIOUS
Adds path to the Windows Defender exclusion list
- reboot_launcher-9.2.7+9.2.7-windows-setup.tmp (PID: 7280)
Changes powershell execution policy (Bypass)
- reboot_launcher-9.2.7+9.2.7-windows-setup.tmp (PID: 7280)
Bypass execution policy to execute commands
- powershell.exe (PID: 6044)
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2172)
SUSPICIOUS
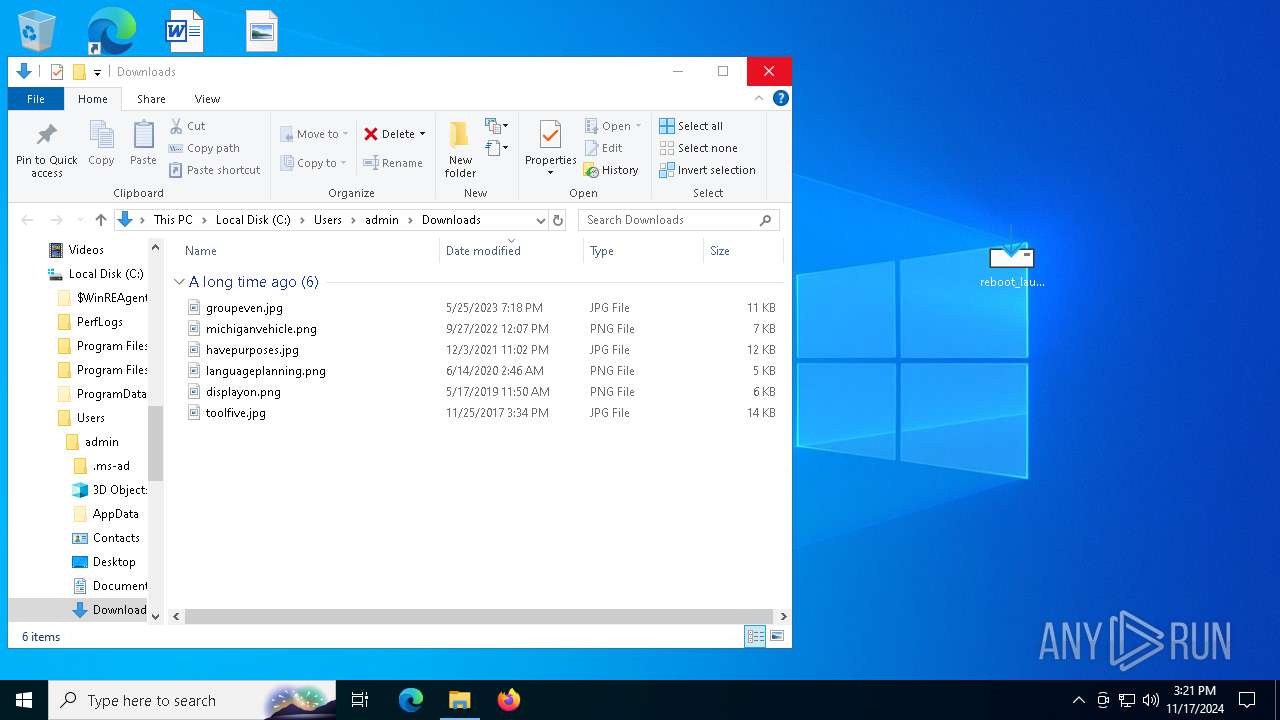
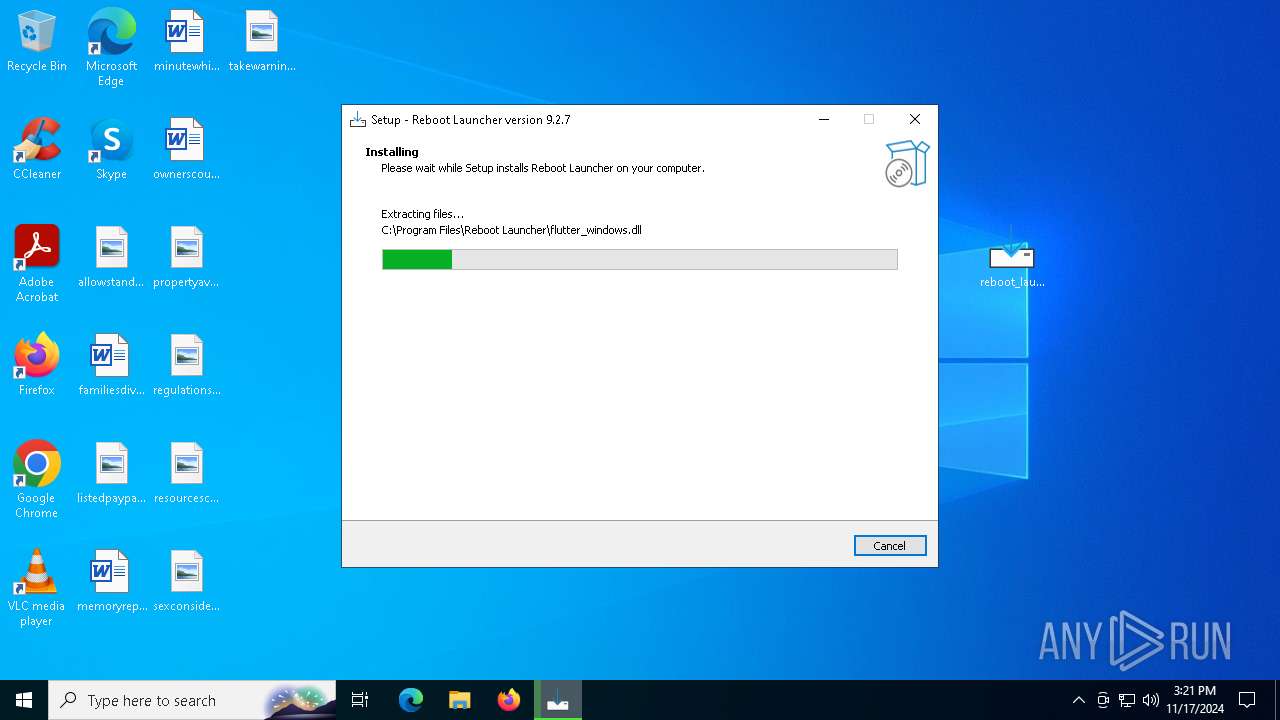
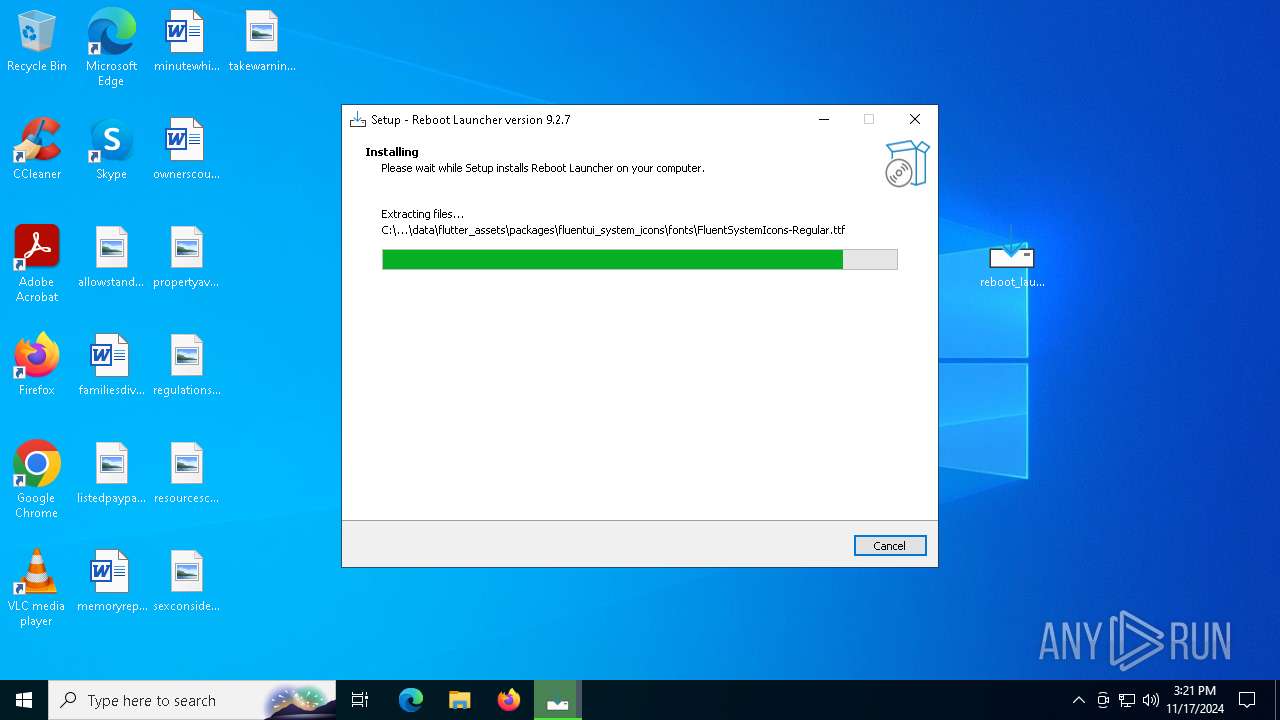
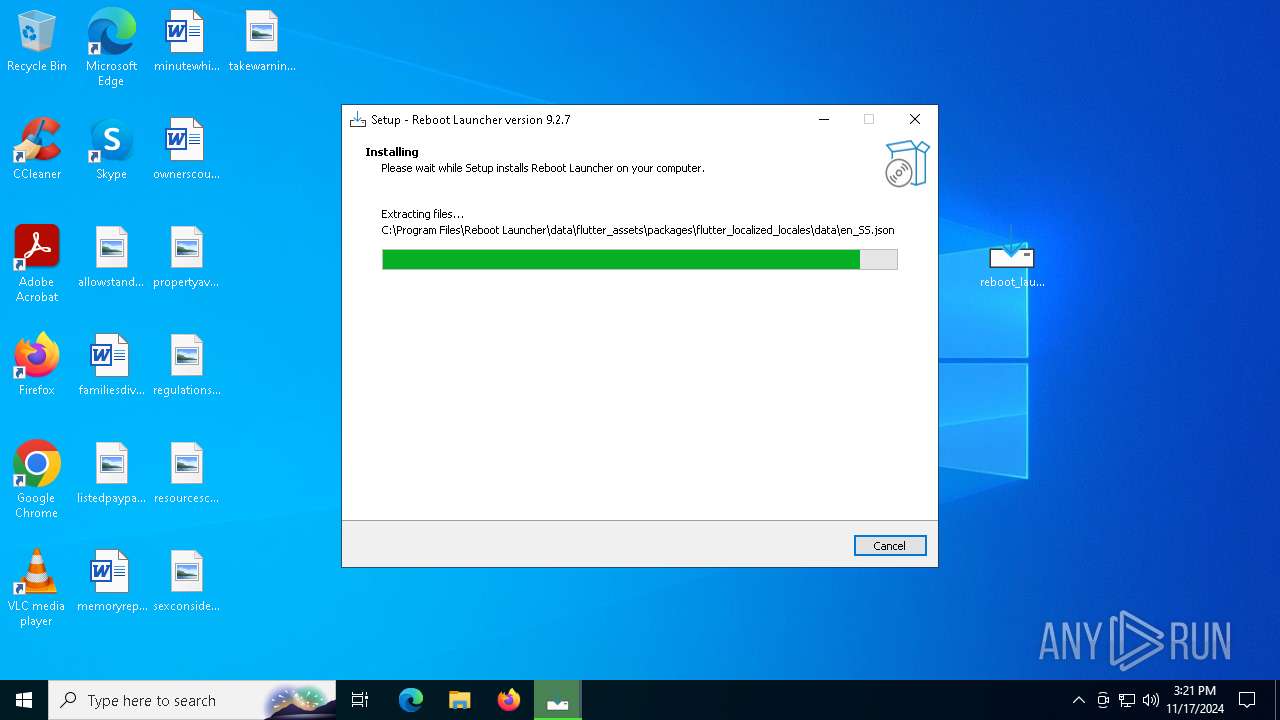
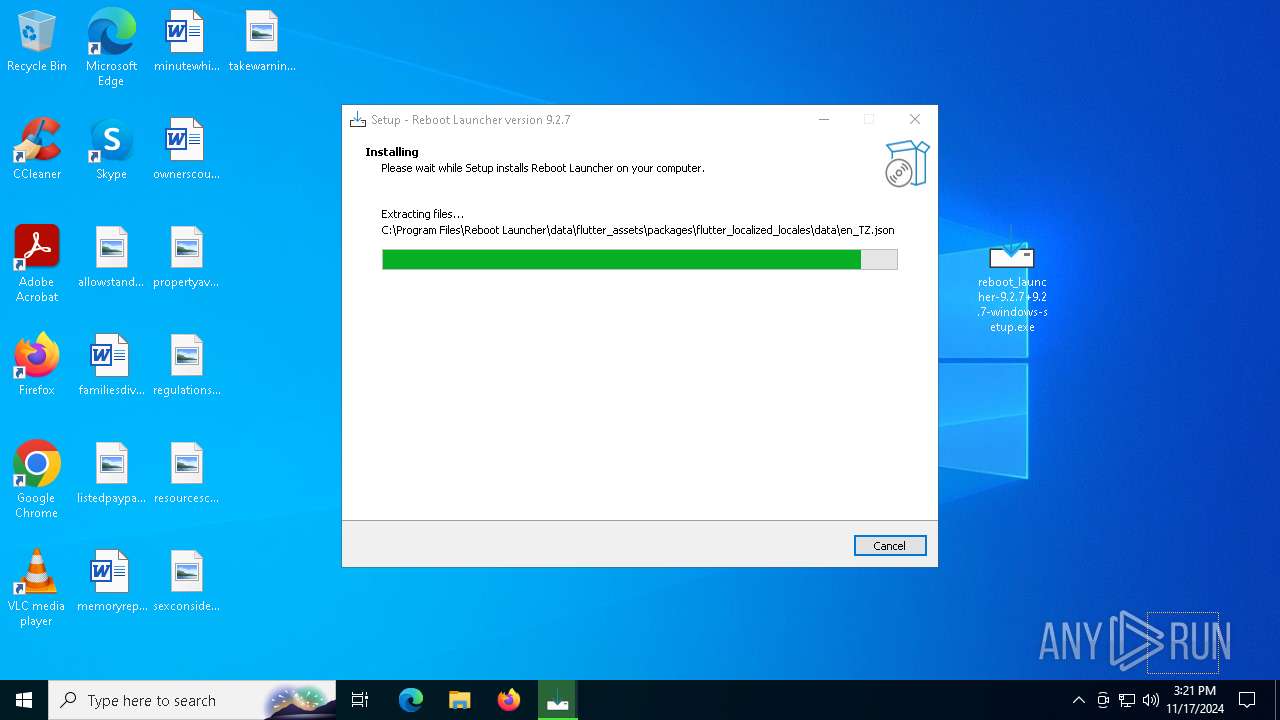
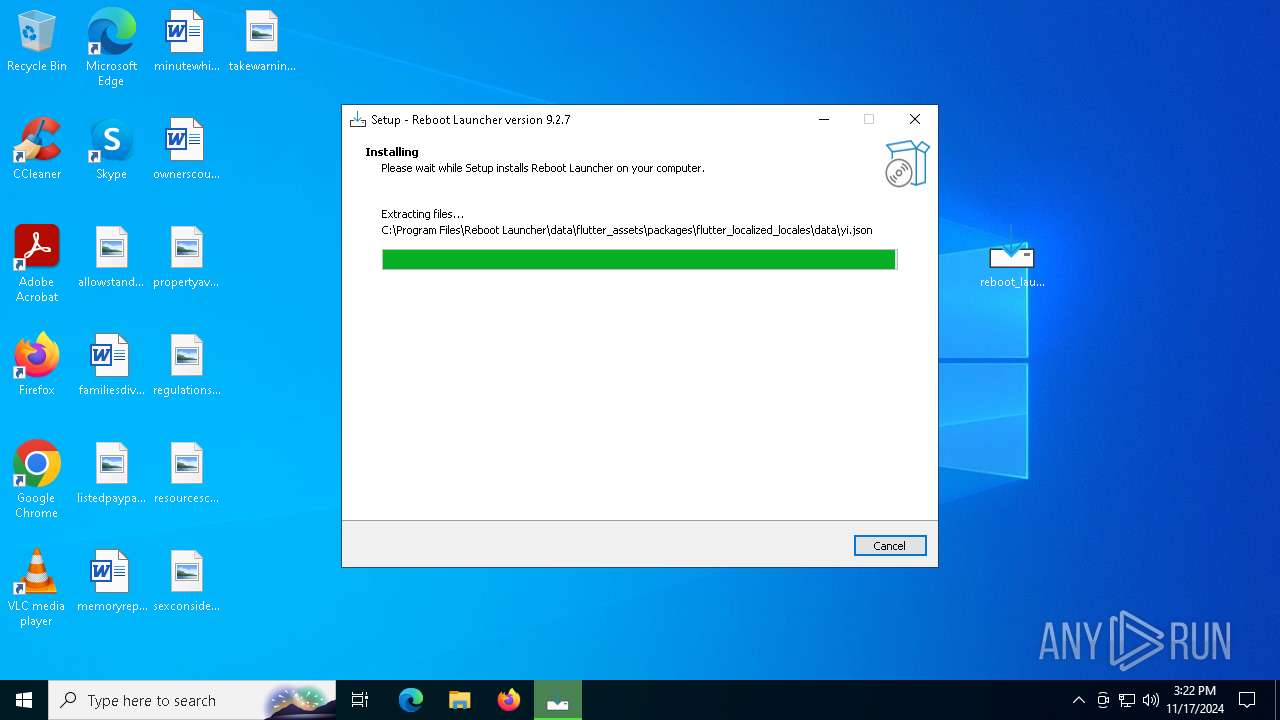
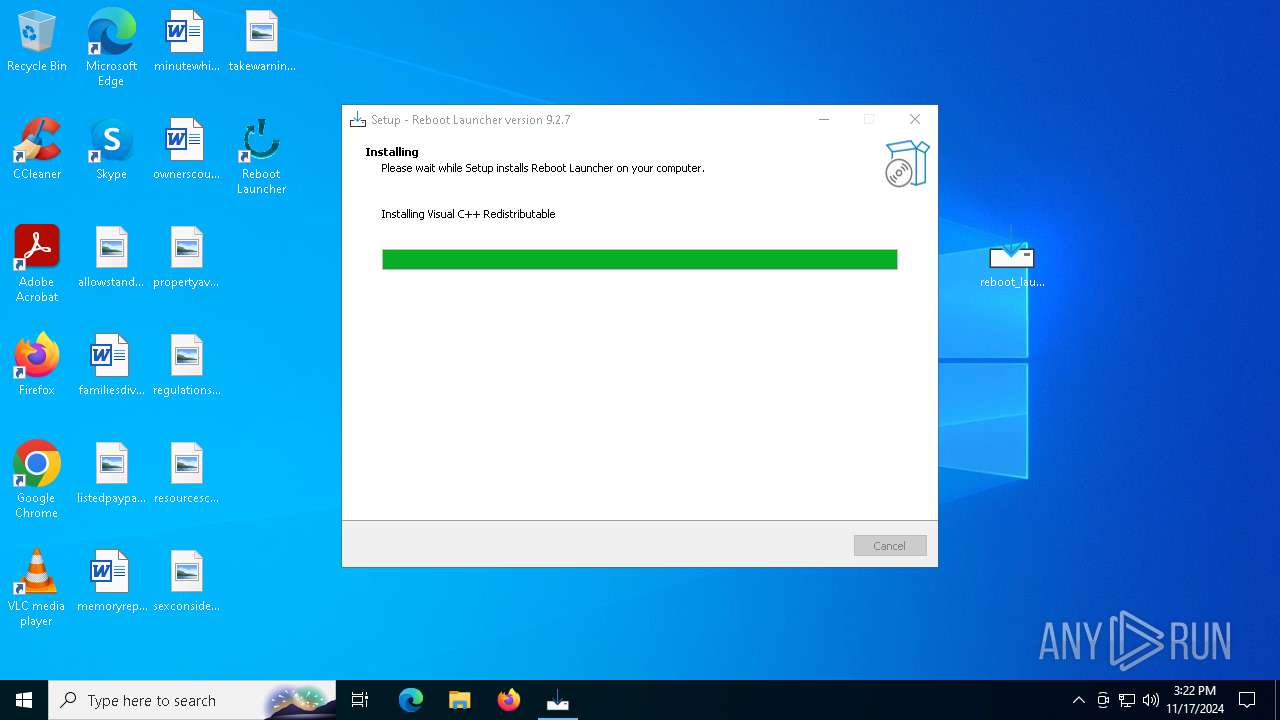
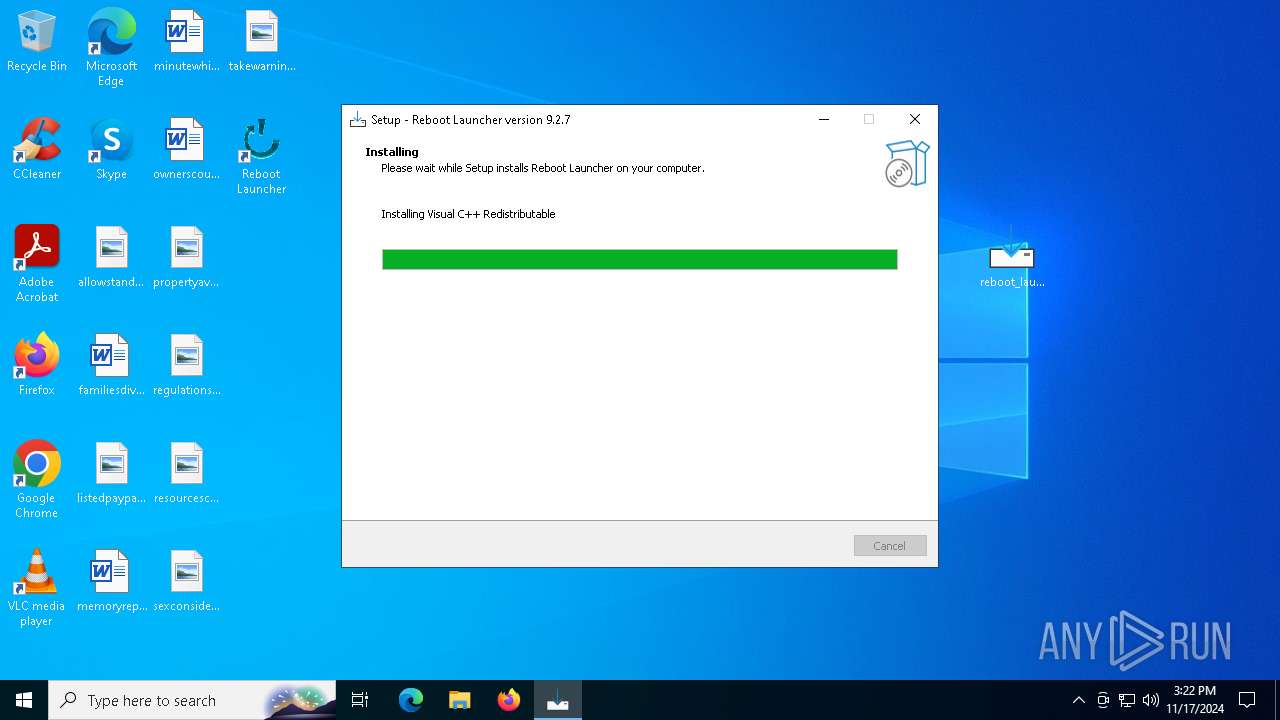
Executable content was dropped or overwritten
- reboot_launcher-9.2.7+9.2.7-windows-setup.exe (PID: 528)
- reboot_launcher-9.2.7+9.2.7-windows-setup.tmp (PID: 7280)
- reboot_launcher-9.2.7+9.2.7-windows-setup.exe (PID: 7932)
- VC_redist.x64.exe (PID: 1332)
- VC_redist.x64.exe (PID: 6768)
- VC_redist.x64.exe (PID: 692)
- VC_redist.x64.exe (PID: 6728)
- reboot_launcher.exe (PID: 6484)
- VC_redist.x64.exe (PID: 7104)
Reads security settings of Internet Explorer
- reboot_launcher-9.2.7+9.2.7-windows-setup.tmp (PID: 7592)
Reads the Windows owner or organization settings
- reboot_launcher-9.2.7+9.2.7-windows-setup.tmp (PID: 7280)
Drops 7-zip archiver for unpacking
- reboot_launcher-9.2.7+9.2.7-windows-setup.tmp (PID: 7280)
Script adds exclusion path to Windows Defender
- reboot_launcher-9.2.7+9.2.7-windows-setup.tmp (PID: 7280)
Starts POWERSHELL.EXE for commands execution
- reboot_launcher-9.2.7+9.2.7-windows-setup.tmp (PID: 7280)
Starts a Microsoft application from unusual location
- VC_redist.x64.exe (PID: 692)
- VC_redist.x64.exe (PID: 1332)
- VC_redist.x64.exe (PID: 6768)
Process drops legitimate windows executable
- VC_redist.x64.exe (PID: 692)
- msiexec.exe (PID: 4568)
- reboot_launcher-9.2.7+9.2.7-windows-setup.tmp (PID: 7280)
- VC_redist.x64.exe (PID: 1332)
- VC_redist.x64.exe (PID: 6768)
- VC_redist.x64.exe (PID: 6728)
Starts itself from another location
- VC_redist.x64.exe (PID: 1332)
Executes as Windows Service
- VSSVC.exe (PID: 7756)
The process drops C-runtime libraries
- msiexec.exe (PID: 4568)
Application launched itself
- VC_redist.x64.exe (PID: 7104)
- VC_redist.x64.exe (PID: 2776)
Executing commands from a ".bat" file
- reboot_launcher.exe (PID: 6484)
Starts CMD.EXE for commands execution
- reboot_launcher.exe (PID: 6484)
INFO
Checks supported languages
- identity_helper.exe (PID: 8028)
- identity_helper.exe (PID: 7332)
- reboot_launcher-9.2.7+9.2.7-windows-setup.exe (PID: 528)
- reboot_launcher-9.2.7+9.2.7-windows-setup.tmp (PID: 7592)
- reboot_launcher-9.2.7+9.2.7-windows-setup.exe (PID: 7932)
- reboot_launcher-9.2.7+9.2.7-windows-setup.tmp (PID: 7280)
- _setup64.tmp (PID: 7788)
Executable content was dropped or overwritten
- msedge.exe (PID: 6568)
- msiexec.exe (PID: 4568)
Reads Environment values
- identity_helper.exe (PID: 8028)
- identity_helper.exe (PID: 7332)
Application launched itself
- msedge.exe (PID: 6568)
- msedge.exe (PID: 6336)
Reads the computer name
- identity_helper.exe (PID: 8028)
- identity_helper.exe (PID: 7332)
- reboot_launcher-9.2.7+9.2.7-windows-setup.tmp (PID: 7592)
- reboot_launcher-9.2.7+9.2.7-windows-setup.tmp (PID: 7280)
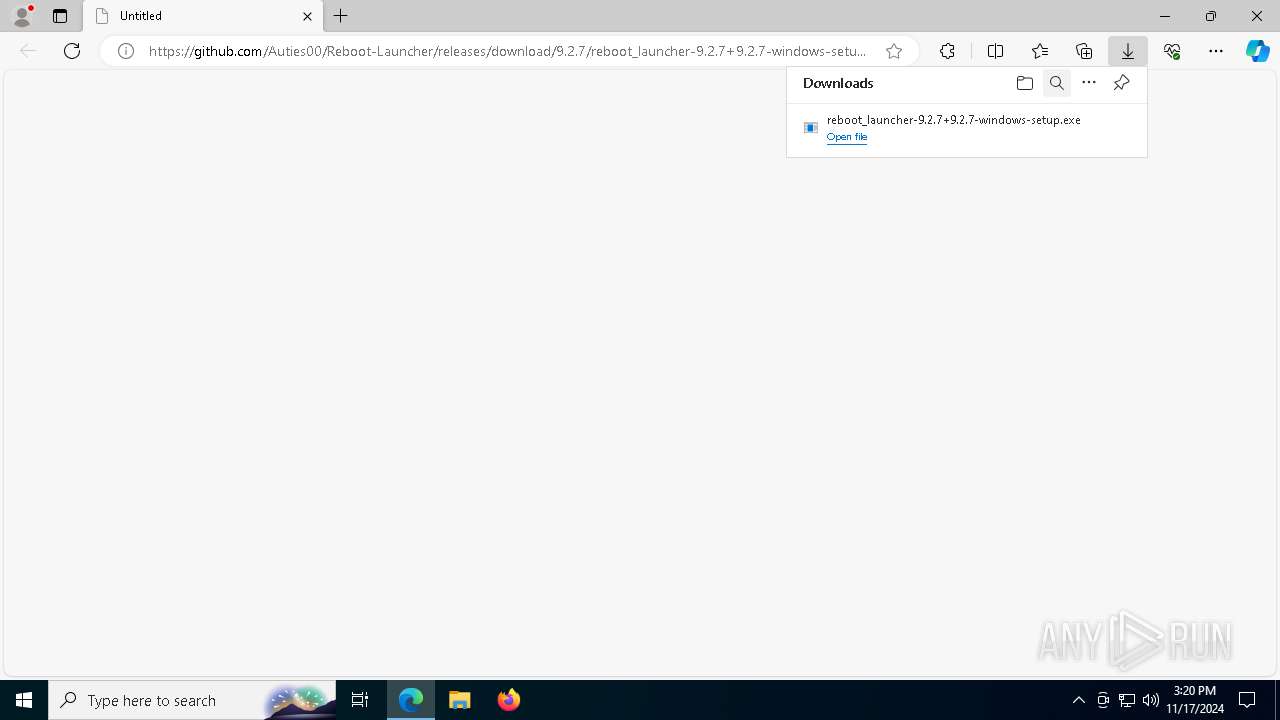
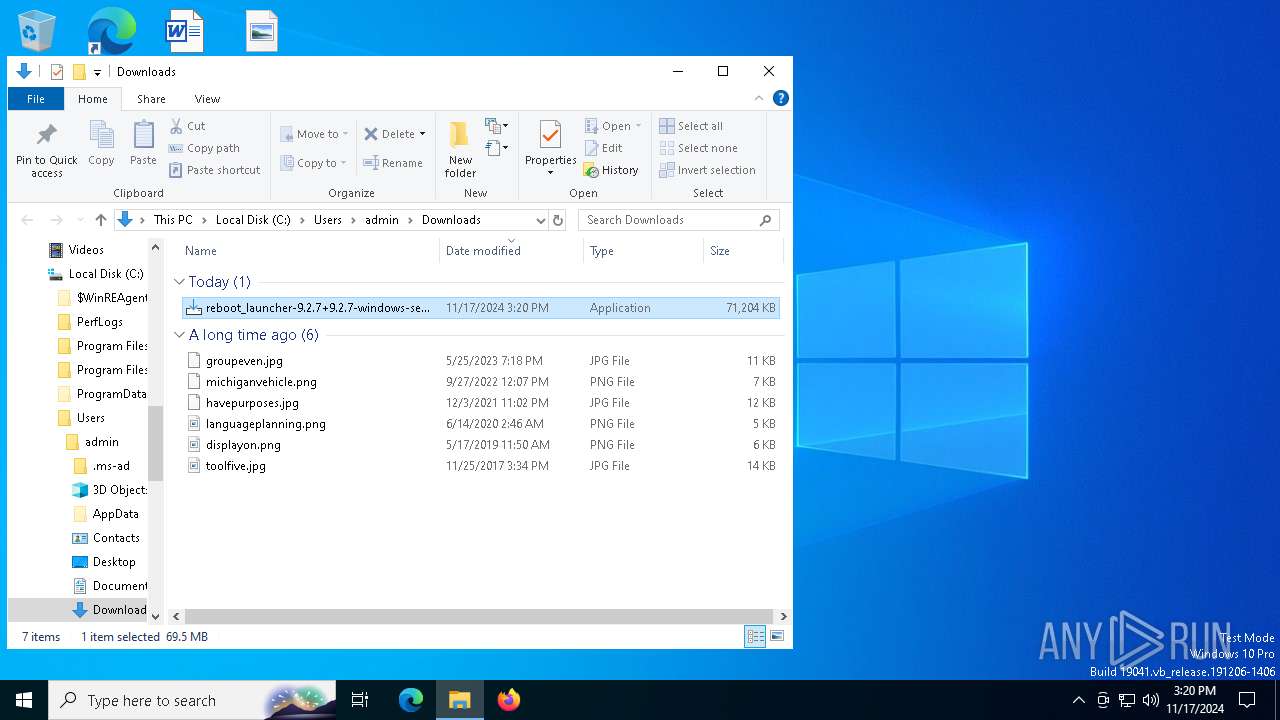
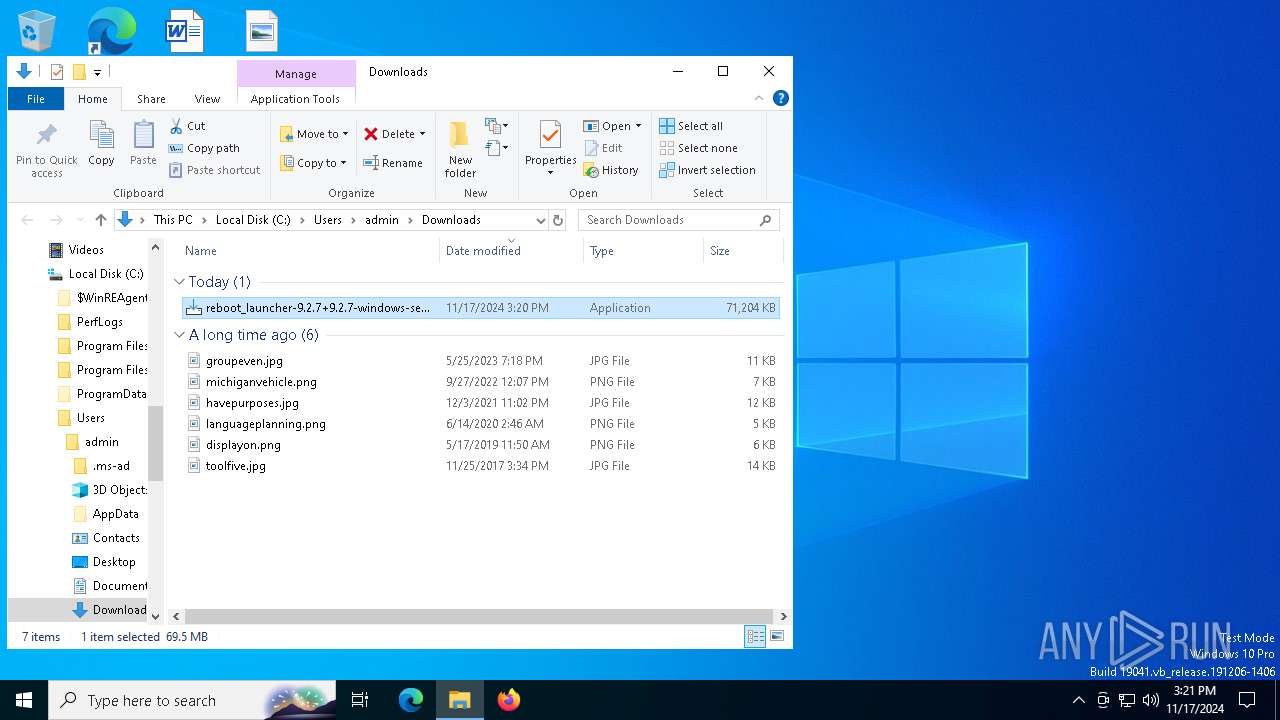
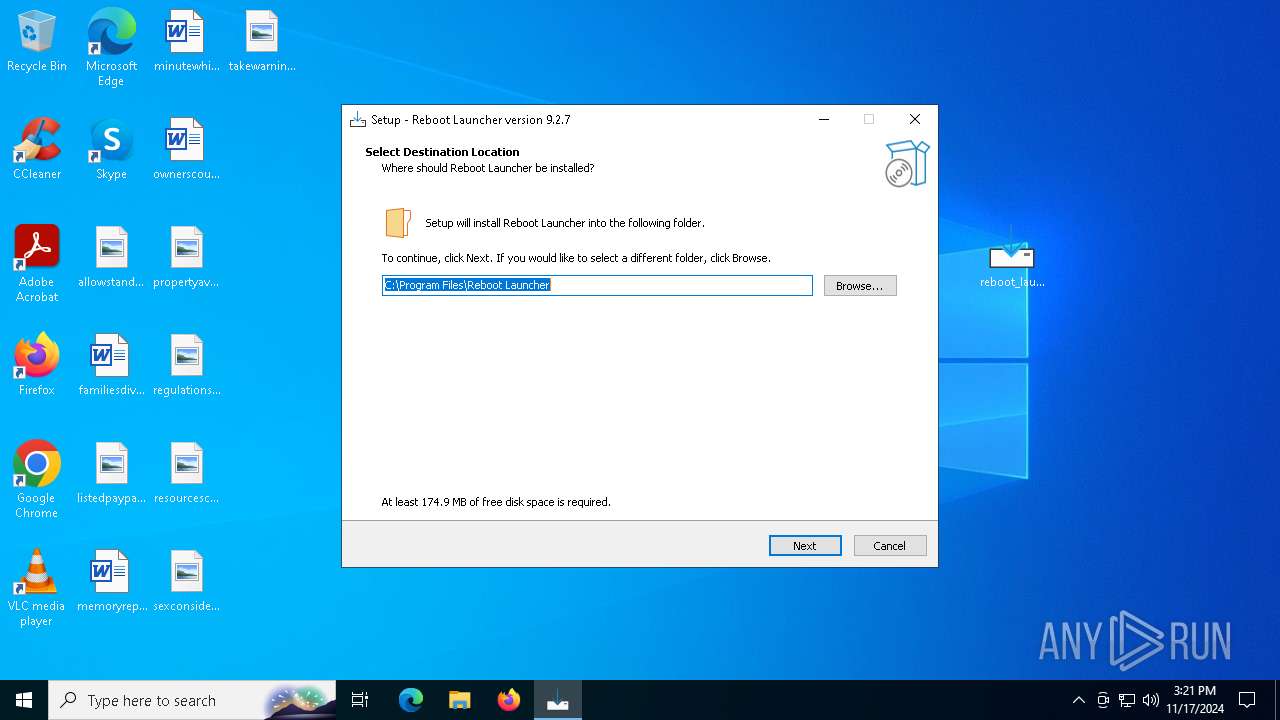
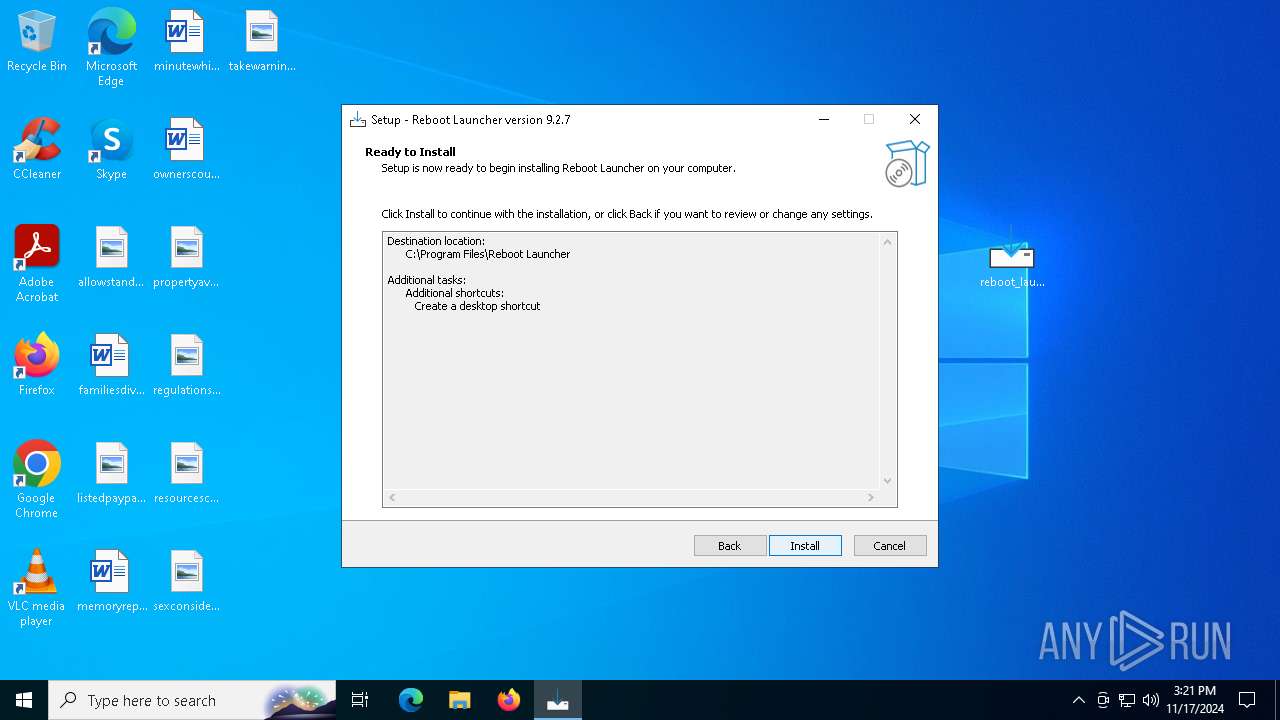
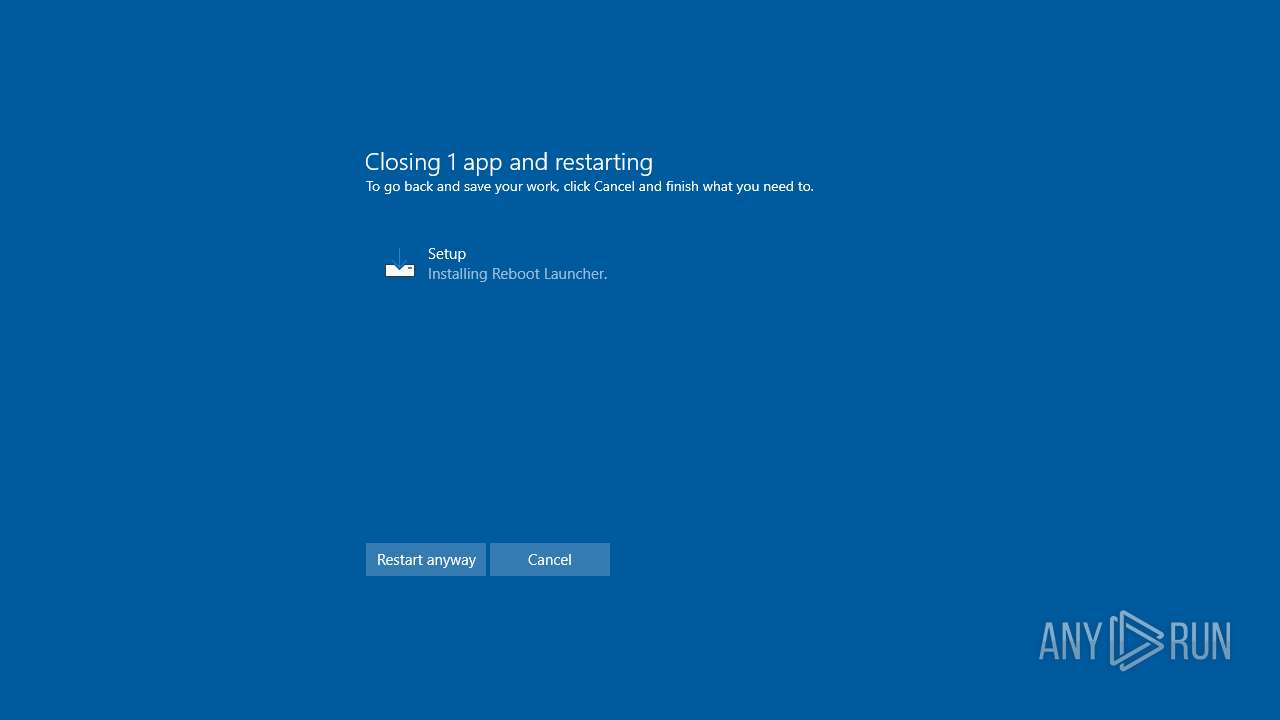
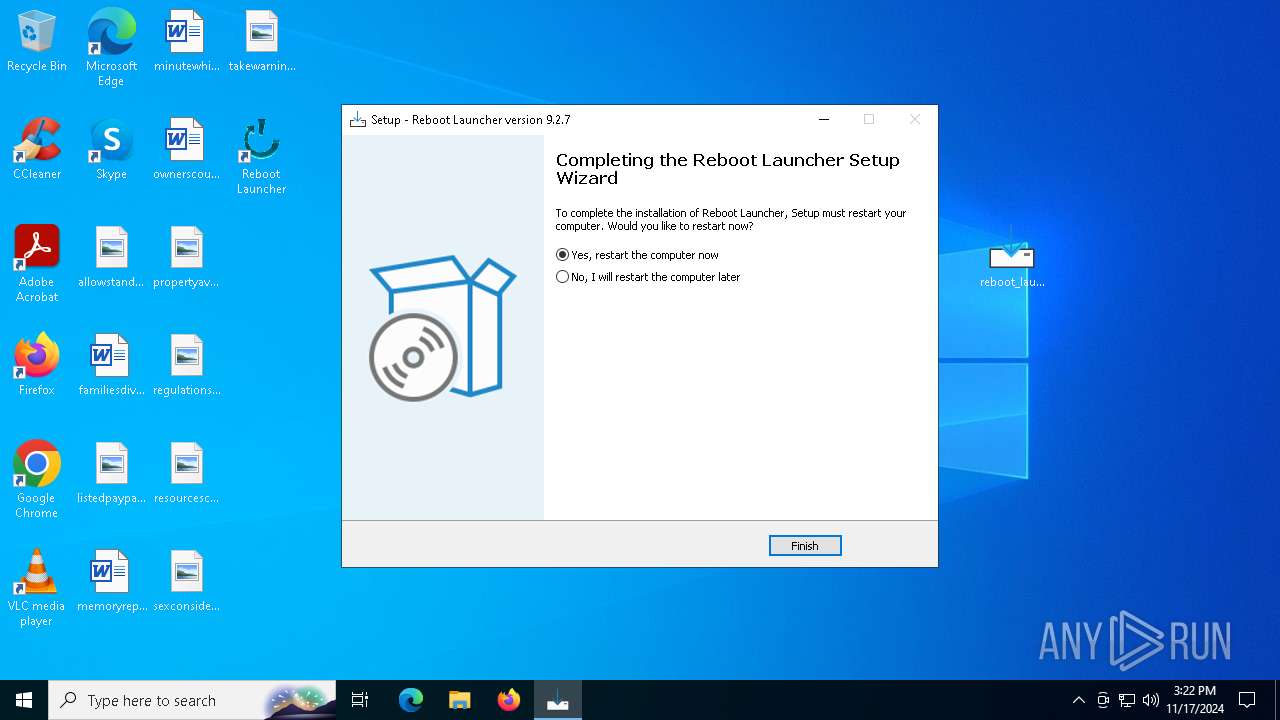
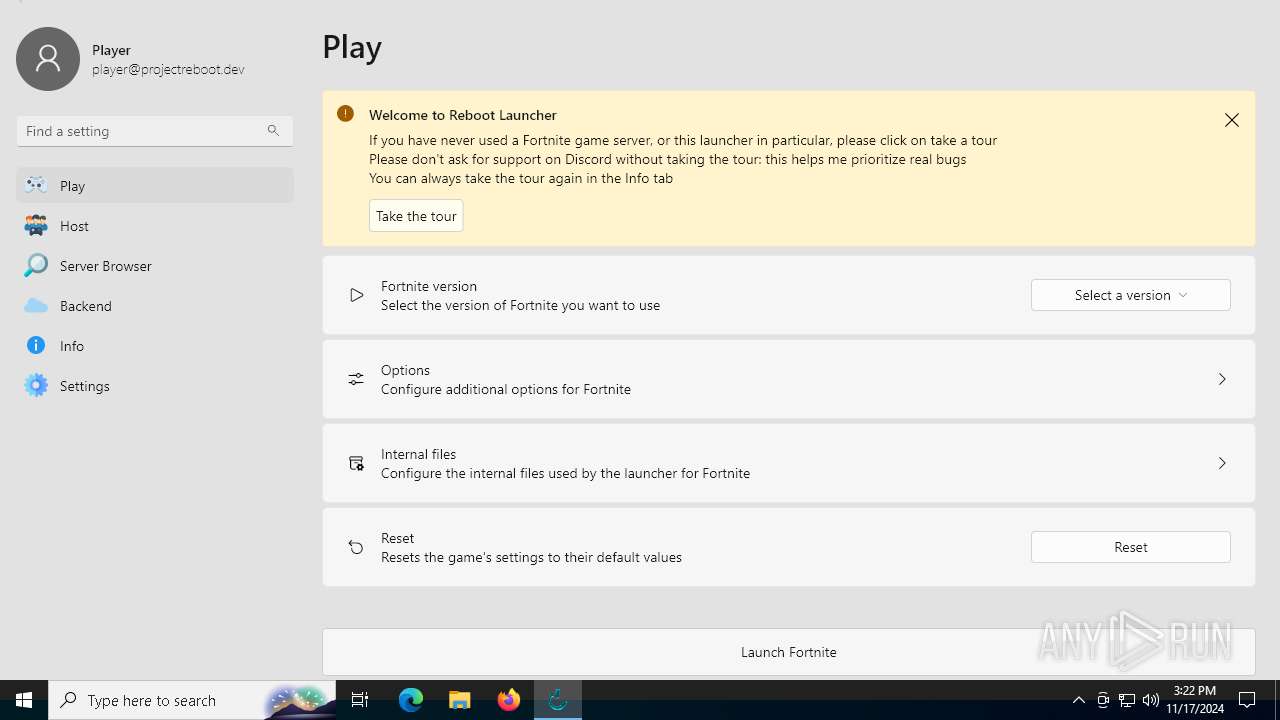
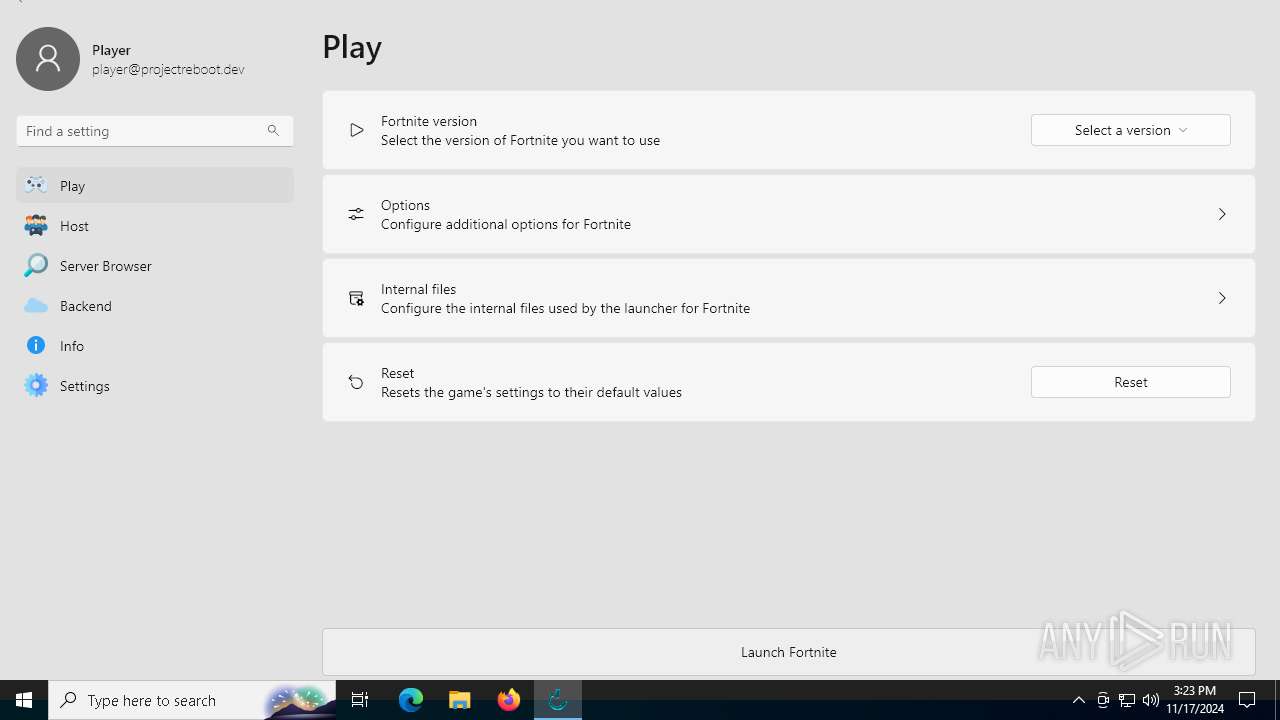
Manual execution by a user
- reboot_launcher-9.2.7+9.2.7-windows-setup.exe (PID: 528)
- reboot_launcher.exe (PID: 6484)
Reads the software policy settings
- slui.exe (PID: 7212)
Creates a software uninstall entry
- reboot_launcher-9.2.7+9.2.7-windows-setup.tmp (PID: 7280)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6044)
Process checks computer location settings
- reboot_launcher-9.2.7+9.2.7-windows-setup.tmp (PID: 7592)
Manages system restore points
- SrTasks.exe (PID: 4012)
Sends debugging messages
- msiexec.exe (PID: 4568)
- reboot_launcher.exe (PID: 6484)
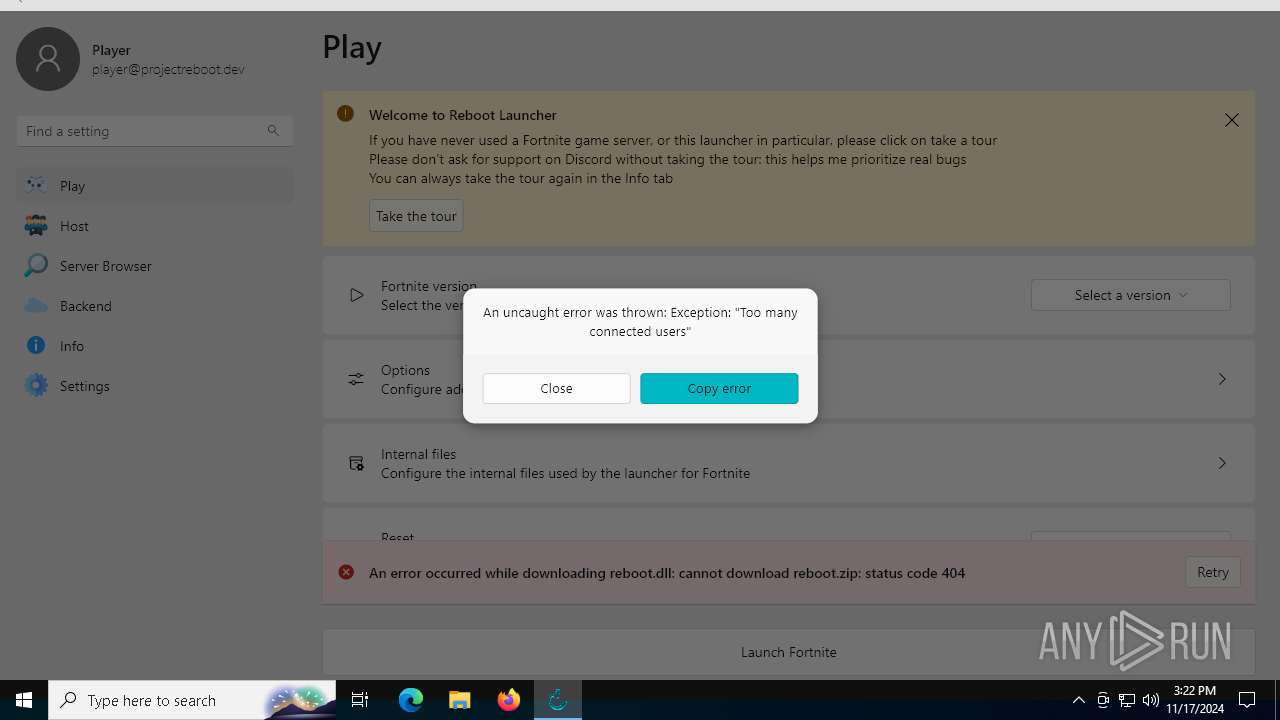
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
219
Monitored processes
76
Malicious processes
4
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 528 | "C:\Users\admin\Desktop\reboot_launcher-9.2.7+9.2.7-windows-setup.exe" | C:\Users\admin\Desktop\reboot_launcher-9.2.7+9.2.7-windows-setup.exe | explorer.exe | ||||||||||||
User: admin Company: Auties00 Integrity Level: MEDIUM Description: Reboot Launcher Setup Exit code: 1073807364 Version: Modules
| |||||||||||||||
| 540 | C:\WINDOWS\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 692 | "C:\Users\admin\AppData\Local\Temp\is-6C7A2.tmp\VC_redist.x64.exe" /quiet | C:\Users\admin\AppData\Local\Temp\is-6C7A2.tmp\VC_redist.x64.exe | reboot_launcher-9.2.7+9.2.7-windows-setup.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.40.33810 Exit code: 3010 Version: 14.40.33810.0 Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4076 --field-trial-handle=2448,i,12884543212545580752,7027905319399961686,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1008 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x290,0x294,0x298,0x288,0x2a0,0x7ffbc2115fd8,0x7ffbc2115fe4,0x7ffbc2115ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1332 | "C:\WINDOWS\Temp\{EC1FE154-8FAD-4A85-AC0F-239B926CE787}\.cr\VC_redist.x64.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\is-6C7A2.tmp\VC_redist.x64.exe" -burn.filehandle.attached=668 -burn.filehandle.self=776 /quiet | C:\Windows\Temp\{EC1FE154-8FAD-4A85-AC0F-239B926CE787}\.cr\VC_redist.x64.exe | VC_redist.x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.40.33810 Exit code: 3010 Version: 14.40.33810.0 Modules
| |||||||||||||||
| 1804 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2464 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4040 --field-trial-handle=2448,i,12884543212545580752,7027905319399961686,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2776 | "C:\ProgramData\Package Cache\{8bdfe669-9705-4184-9368-db9ce581e0e7}\VC_redist.x64.exe" -uninstall -quiet -burn.related.upgrade -burn.ancestors={5af95fd8-a22e-458f-acee-c61bd787178e} -burn.filehandle.self=1336 -burn.embedded BurnPipe.{AD9C2A25-3FD5-4E31-A84B-D5F38061D638} {3DB68E81-0B7E-4BA5-B340-BB893C88A3E0} 6768 | C:\ProgramData\Package Cache\{8bdfe669-9705-4184-9368-db9ce581e0e7}\VC_redist.x64.exe | — | VC_redist.x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.36.32532 Exit code: 0 Version: 14.36.32532.0 Modules
| |||||||||||||||
Total events
30 258
Read events
29 242
Write events
648
Delete events
368
Modification events
| (PID) Process: | (6568) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6568) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6568) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6568) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6568) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 1A9AE49FB3852F00 | |||
| (PID) Process: | (6568) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B9FCEB9FB3852F00 | |||
| (PID) Process: | (6568) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262880 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {746CEB73-97FD-4A52-A1D8-1E321714BC69} | |||
| (PID) Process: | (6568) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262880 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E5227A39-1BD4-45AC-9F8A-A98CC35F75BD} | |||
| (PID) Process: | (6568) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 13BB0DA0B3852F00 | |||
| (PID) Process: | (6568) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
109
Suspicious files
1 588
Text files
213
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF8b8e9.TMP | — | |
MD5:— | SHA256:— | |||
| 6568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF8b8e9.TMP | — | |
MD5:— | SHA256:— | |||
| 6568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF8b8e9.TMP | — | |
MD5:— | SHA256:— | |||
| 6568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF8b8e9.TMP | — | |
MD5:— | SHA256:— | |||
| 6568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF8b8e9.TMP | — | |
MD5:— | SHA256:— | |||
| 6568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
98
DNS requests
74
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7028 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7524 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7524 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1712 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2272 | svchost.exe | HEAD | 200 | 2.16.10.182:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/771cebfe-873c-42bc-8377-b54128b62b41?P1=1732436472&P2=404&P3=2&P4=bdVrsvo1iVXs%2bOKO3OHmwRxxIpJIzbpn9SpjewCfvklyzUfx4keOZu5wZ3%2blI1DOnHWfnUeaeb1HugP%2bo1JK2w%3d%3d | unknown | — | — | whitelisted |
2272 | svchost.exe | GET | 206 | 2.16.10.182:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/771cebfe-873c-42bc-8377-b54128b62b41?P1=1732436472&P2=404&P3=2&P4=bdVrsvo1iVXs%2bOKO3OHmwRxxIpJIzbpn9SpjewCfvklyzUfx4keOZu5wZ3%2blI1DOnHWfnUeaeb1HugP%2bo1JK2w%3d%3d | unknown | — | — | whitelisted |
2272 | svchost.exe | GET | 206 | 2.16.10.182:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/771cebfe-873c-42bc-8377-b54128b62b41?P1=1732436472&P2=404&P3=2&P4=bdVrsvo1iVXs%2bOKO3OHmwRxxIpJIzbpn9SpjewCfvklyzUfx4keOZu5wZ3%2blI1DOnHWfnUeaeb1HugP%2bo1JK2w%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2464 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4360 | SearchApp.exe | 104.126.37.186:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5592 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6568 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5592 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
github.com |
| shared |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Misc activity | ET INFO Supabase Development Platform Related Domain in DNS Lookup |
2172 | svchost.exe | Misc activity | ET INFO Supabase Development Platform Related Domain in DNS Lookup |
2172 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain was identified as Phishing (.supabase.co) |
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2172 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain was identified as Phishing (.supabase.co) |
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6484 | reboot_launcher.exe | Misc activity | ET INFO Observed Online Application Hosting Domain (supabase .co in TLS SNI) |
6484 | reboot_launcher.exe | Misc activity | ET INFO Observed Online Application Hosting Domain (supabase .co in TLS SNI) |
6484 | reboot_launcher.exe | Misc activity | ET INFO Observed Online Application Hosting Domain (supabase .co in TLS SNI) |
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
msiexec.exe | Failed to release Service
|
reboot_launcher.exe | ****** SYSTEM_THEME_PLUGIN ******: Message Handle Registered |