| File name: | 4a6340c389dfee905c542ef4c8db27329b1de9f88240a67da68dac3faa1869fa.exe |
| Full analysis: | https://app.any.run/tasks/dad39952-6857-4e37-af1f-8d5c6d40bd24 |
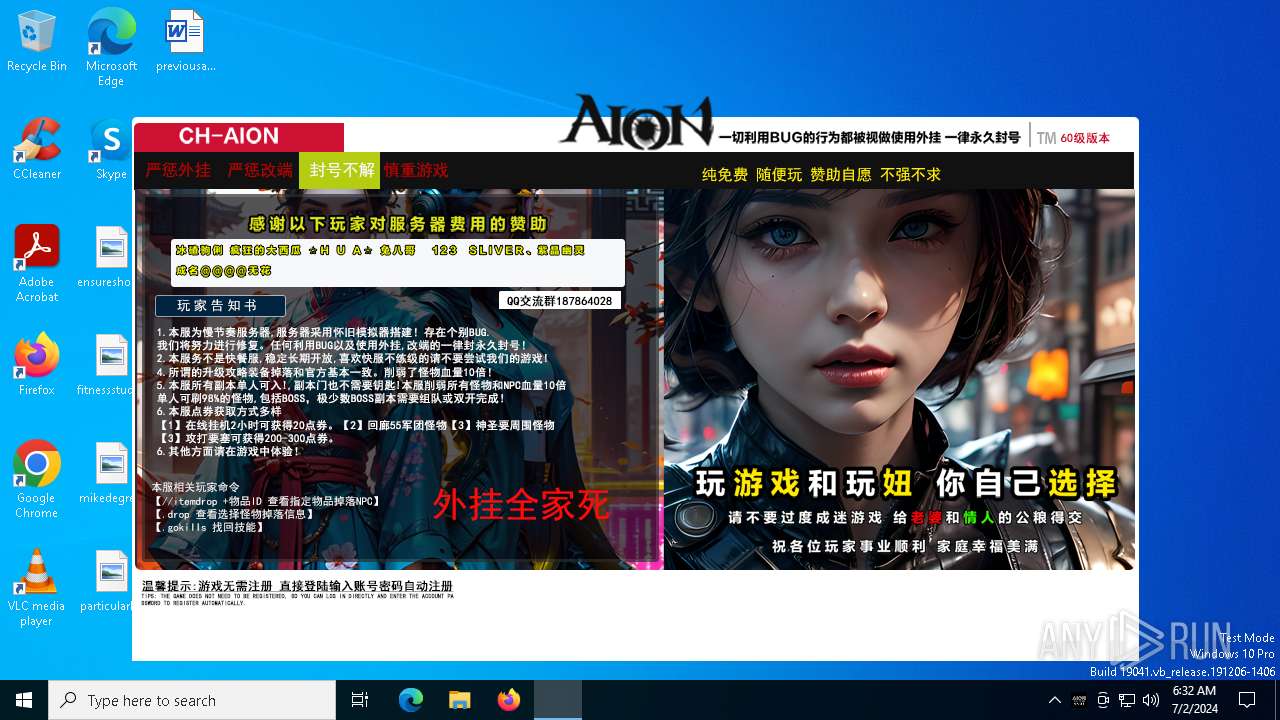
| Verdict: | Malicious activity |
| Analysis date: | July 02, 2024, 06:32:21 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 44162D693B68EFCAF2BDD46FB0AECF62 |
| SHA1: | 5BADAFF403E776DBBFF088B69B22647A5DA8A09D |
| SHA256: | 4A6340C389DFEE905C542EF4C8DB27329B1DE9F88240A67DA68DAC3FAA1869FA |
| SSDEEP: | 98304:jqh0HMNxrwGfntPm/ErSalXugs9tu4qw/tR/GD8gpOhtzcM5pOWreTO11rmQ7Bvp:BsPm/n8IX |
MALICIOUS
Drops the executable file immediately after the start
- 4a6340c389dfee905c542ef4c8db27329b1de9f88240a67da68dac3faa1869fa.exe (PID: 2176)
SUSPICIOUS
Reads the BIOS version
- 4a6340c389dfee905c542ef4c8db27329b1de9f88240a67da68dac3faa1869fa.exe (PID: 2176)
Reads security settings of Internet Explorer
- 4a6340c389dfee905c542ef4c8db27329b1de9f88240a67da68dac3faa1869fa.exe (PID: 2176)
Write to the desktop.ini file (may be used to cloak folders)
- 4a6340c389dfee905c542ef4c8db27329b1de9f88240a67da68dac3faa1869fa.exe (PID: 2176)
Executable content was dropped or overwritten
- 4a6340c389dfee905c542ef4c8db27329b1de9f88240a67da68dac3faa1869fa.exe (PID: 2176)
Connects to unusual port
- 4a6340c389dfee905c542ef4c8db27329b1de9f88240a67da68dac3faa1869fa.exe (PID: 2176)
INFO
Reads the machine GUID from the registry
- 4a6340c389dfee905c542ef4c8db27329b1de9f88240a67da68dac3faa1869fa.exe (PID: 2176)
Checks supported languages
- 4a6340c389dfee905c542ef4c8db27329b1de9f88240a67da68dac3faa1869fa.exe (PID: 2176)
Reads the computer name
- 4a6340c389dfee905c542ef4c8db27329b1de9f88240a67da68dac3faa1869fa.exe (PID: 2176)
Create files in a temporary directory
- 4a6340c389dfee905c542ef4c8db27329b1de9f88240a67da68dac3faa1869fa.exe (PID: 2176)
Reads Environment values
- 4a6340c389dfee905c542ef4c8db27329b1de9f88240a67da68dac3faa1869fa.exe (PID: 2176)
Reads CPU info
- 4a6340c389dfee905c542ef4c8db27329b1de9f88240a67da68dac3faa1869fa.exe (PID: 2176)
.NET Reactor protector has been detected
- 4a6340c389dfee905c542ef4c8db27329b1de9f88240a67da68dac3faa1869fa.exe (PID: 2176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:06:28 10:23:54+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 104448 |
| InitializedDataSize: | 1304064 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x302000 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.0.0.4 |
| ProductVersionNumber: | 3.0.0.4 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | 支持外挂查杀,文件校检,以及账号注册,密码修改和密码找回等众多功能与一体 |
| CompanyName: | 灰色枫叶 QQ93900604 |
| FileDescription: | 登录器 |
| FileVersion: | 3.0.0.4 |
| InternalName: | tmp8C9.tmp |
| LegalCopyright: | Copyright © 灰色枫叶 2015 |
| OriginalFileName: | tmp8C9.tmp |
| ProductName: | AionLanucher |
| ProductVersion: | 3.0.0.4 |
| AssemblyVersion: | 3.0.0.4 |
Total processes
134
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | "C:\Users\admin\AppData\Local\Temp\4a6340c389dfee905c542ef4c8db27329b1de9f88240a67da68dac3faa1869fa.exe" | C:\Users\admin\AppData\Local\Temp\4a6340c389dfee905c542ef4c8db27329b1de9f88240a67da68dac3faa1869fa.exe | — | explorer.exe | |||||||||||
User: admin Company: 灰色枫叶 QQ93900604 Integrity Level: MEDIUM Description: 登录器 Exit code: 3221226540 Version: 3.0.0.4 Modules
| |||||||||||||||
| 2176 | "C:\Users\admin\AppData\Local\Temp\4a6340c389dfee905c542ef4c8db27329b1de9f88240a67da68dac3faa1869fa.exe" | C:\Users\admin\AppData\Local\Temp\4a6340c389dfee905c542ef4c8db27329b1de9f88240a67da68dac3faa1869fa.exe | explorer.exe | ||||||||||||
User: admin Company: 灰色枫叶 QQ93900604 Integrity Level: HIGH Description: 登录器 Version: 3.0.0.4 Modules
| |||||||||||||||
Total events
911
Read events
911
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2176 | 4a6340c389dfee905c542ef4c8db27329b1de9f88240a67da68dac3faa1869fa.exe | C:\WINDOWS\assembly\Desktop.ini | binary | |
MD5:F7F759A5CD40BC52172E83486B6DE404 | SHA256:A709C2551B8818D7849D31A65446DC2F8C4CCA2DCBBC5385604286F49CFDAF1C | |||
| 2176 | 4a6340c389dfee905c542ef4c8db27329b1de9f88240a67da68dac3faa1869fa.exe | C:\Users\admin\AppData\Local\Temp\TEMP102.tmp | executable | |
MD5:44162D693B68EFCAF2BDD46FB0AECF62 | SHA256:4A6340C389DFEE905C542EF4C8DB27329B1DE9F88240A67DA68DAC3FAA1869FA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
89
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1544 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
6068 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
3040 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | unknown |
6584 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
6584 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
1888 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2504 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3540 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6004 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1544 | svchost.exe | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1544 | svchost.exe | 192.229.221.95:80 | — | EDGECAST | US | whitelisted |
4656 | SearchApp.exe | 104.126.37.146:443 | — | Akamai International B.V. | DE | unknown |
2176 | 4a6340c389dfee905c542ef4c8db27329b1de9f88240a67da68dac3faa1869fa.exe | 103.91.208.68:8000 | — | CHINA UNICOM China169 Backbone | CN | unknown |
2176 | 4a6340c389dfee905c542ef4c8db27329b1de9f88240a67da68dac3faa1869fa.exe | 101.43.96.192:443 | keerroy.gicp.net | Shenzhen Tencent Computer Systems Company Limited | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
keerroy.gicp.net |
| unknown |
go.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
4a6340c389dfee905c542ef4c8db27329b1de9f88240a67da68dac3faa1869fa.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2010 Oreans Technologies ---
------------------------------------------------
|