| File name: | ActualizaPolicy_v2Junio.msi |
| Full analysis: | https://app.any.run/tasks/752b88a7-e98e-440b-8334-3cf83b8dce66 |
| Verdict: | Malicious activity |
| Analysis date: | June 13, 2022, 19:34:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Last Printed: Fri Dec 11 11:47:44 2009, Create Time/Date: Fri Dec 11 11:47:44 2009, Last Saved Time/Date: Fri Sep 18 15:06:51 2020, Security: 0, Code page: 1252, Revision Number: {6F89D77B-BB04-46BE-B73E-6D1888389F85}, Number of Words: 2, Subject: IDSE, Author: IMSS, Name of Creating Application: Advanced Installer 18.3 build e2a0201b, Template: ;1033, Title: Installation Database, Keywords: Installer, MSI, Database, Number of Pages: 200 |
| MD5: | 0C15A122A7E0E052E867A85C403773EC |
| SHA1: | F8F7BA836CCFACC7066A0D8197CB2C398CE0B1C8 |
| SHA256: | 4A5B20F2745139193F1A88975CCB386CF7AFED2B5665DFC1A179E7E94C9D1341 |
| SSDEEP: | 393216:VlEky3InEroX/lh2p814S2gn0NmkSY6aMqUH2N2Yn4:MkyYErUNQp7g1PYu |
MALICIOUS
Drops executable file immediately after starts
- msiexec.exe (PID: 3416)
- MsiExec.exe (PID: 2196)
Loads the Task Scheduler COM API
- aipackagechainer.exe (PID: 3440)
Changes the autorun value in the registry
- aipackagechainer.exe (PID: 3440)
Changes settings of System certificates
- powershell.exe (PID: 564)
Application was dropped or rewritten from another process
- aipackagechainer.exe (PID: 3440)
SUSPICIOUS
Checks supported languages
- msiexec.exe (PID: 3416)
- MSIAA43.tmp (PID: 2460)
- MsiExec.exe (PID: 2196)
- aipackagechainer.exe (PID: 3440)
- powershell.exe (PID: 564)
Reads the computer name
- msiexec.exe (PID: 3416)
- MSIAA43.tmp (PID: 2460)
- MsiExec.exe (PID: 2196)
- aipackagechainer.exe (PID: 3440)
- powershell.exe (PID: 564)
Drops a file with a compile date too recent
- msiexec.exe (PID: 3416)
- MsiExec.exe (PID: 2196)
Reads Windows owner or organization settings
- msiexec.exe (PID: 3416)
- msiexec.exe (PID: 3132)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3416)
- MsiExec.exe (PID: 2196)
Executed via COM
- iexplore.exe (PID: 2656)
Reads the Windows organization settings
- msiexec.exe (PID: 3132)
- msiexec.exe (PID: 3416)
Creates files in the user directory
- MsiExec.exe (PID: 2196)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3068)
Creates a directory in Program Files
- msiexec.exe (PID: 3416)
Changes the autorun value in the registry
- msiexec.exe (PID: 3416)
Reads Environment values
- aipackagechainer.exe (PID: 3440)
Executes PowerShell scripts
- aipackagechainer.exe (PID: 3440)
Creates files in the Windows directory
- powershell.exe (PID: 564)
Adds / modifies Windows certificates
- powershell.exe (PID: 564)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2688)
INFO
Reads the computer name
- msiexec.exe (PID: 3132)
- iexplore.exe (PID: 2656)
- iexplore.exe (PID: 3068)
- chrome.exe (PID: 2688)
- chrome.exe (PID: 2148)
- chrome.exe (PID: 2212)
- chrome.exe (PID: 3732)
- chrome.exe (PID: 3476)
Checks supported languages
- msiexec.exe (PID: 3132)
- iexplore.exe (PID: 2656)
- iexplore.exe (PID: 3068)
- chrome.exe (PID: 2688)
- chrome.exe (PID: 888)
- chrome.exe (PID: 2148)
- chrome.exe (PID: 2604)
- chrome.exe (PID: 2288)
- chrome.exe (PID: 3448)
- chrome.exe (PID: 2212)
- chrome.exe (PID: 2412)
- chrome.exe (PID: 2756)
- chrome.exe (PID: 3128)
- chrome.exe (PID: 2060)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 3732)
Starts application with an unusual extension
- msiexec.exe (PID: 3416)
Application launched itself
- msiexec.exe (PID: 3416)
- iexplore.exe (PID: 2656)
- chrome.exe (PID: 2688)
Checks Windows Trust Settings
- iexplore.exe (PID: 3068)
- iexplore.exe (PID: 2656)
- powershell.exe (PID: 564)
Changes internet zones settings
- iexplore.exe (PID: 2656)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2196)
Application was dropped or rewritten from another process
- MSIAA43.tmp (PID: 2460)
Reads settings of System Certificates
- iexplore.exe (PID: 3068)
- powershell.exe (PID: 564)
- iexplore.exe (PID: 2656)
- chrome.exe (PID: 3476)
Creates a software uninstall entry
- msiexec.exe (PID: 3416)
Reads internet explorer settings
- iexplore.exe (PID: 3068)
Manual execution by user
- chrome.exe (PID: 2688)
Creates files in the user directory
- iexplore.exe (PID: 3068)
Reads the hosts file
- chrome.exe (PID: 2688)
- chrome.exe (PID: 3476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (88.6) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (10) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Pages: | 200 |
|---|---|
| Keywords: | Installer, MSI, Database |
| Title: | Installation Database |
| Comments: | - |
| Template: | ;1033 |
| Software: | Advanced Installer 18.3 build e2a0201b |
| LastModifiedBy: | - |
| Author: | IMSS |
| Subject: | IDSE |
| Words: | 2 |
| RevisionNumber: | {6F89D77B-BB04-46BE-B73E-6D1888389F85} |
| CodePage: | Windows Latin 1 (Western European) |
| Security: | None |
| ModifyDate: | 2020:09:18 14:06:51 |
| CreateDate: | 2009:12:11 11:47:44 |
| LastPrinted: | 2009:12:11 11:47:44 |
Total processes
57
Monitored processes
21
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 564 | "C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe" -NonInteractive -NoLogo -ExecutionPolicy AllSigned -Command "C:\Users\admin\AppData\Local\Temp\AI_B0C8.ps1 -paths 'C:\Users\admin\AppData\Roaming\IMSS\IDSE\prerequisites\file_deleter.ps1','C:\Users\admin\AppData\Roaming\IMSS\IDSE\prerequisites\aipackagechainer.exe','C:\Users\admin\AppData\Roaming\IMSS\IDSE','C:\Users\admin\AppData\Roaming\IMSS','C:\Users\admin\AppData\Roaming\IMSS' -retry_count 10" | C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe | aipackagechainer.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6ea3d988,0x6ea3d998,0x6ea3d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,15542712207785472476,5362592490089323433,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3356 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,15542712207785472476,5362592490089323433,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1068 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2196 | C:\Windows\system32\MsiExec.exe -Embedding C96E20C1438E24747659ADF115C105CF | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,15542712207785472476,5362592490089323433,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1036 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,15542712207785472476,5362592490089323433,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1040,15542712207785472476,5362592490089323433,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3616 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
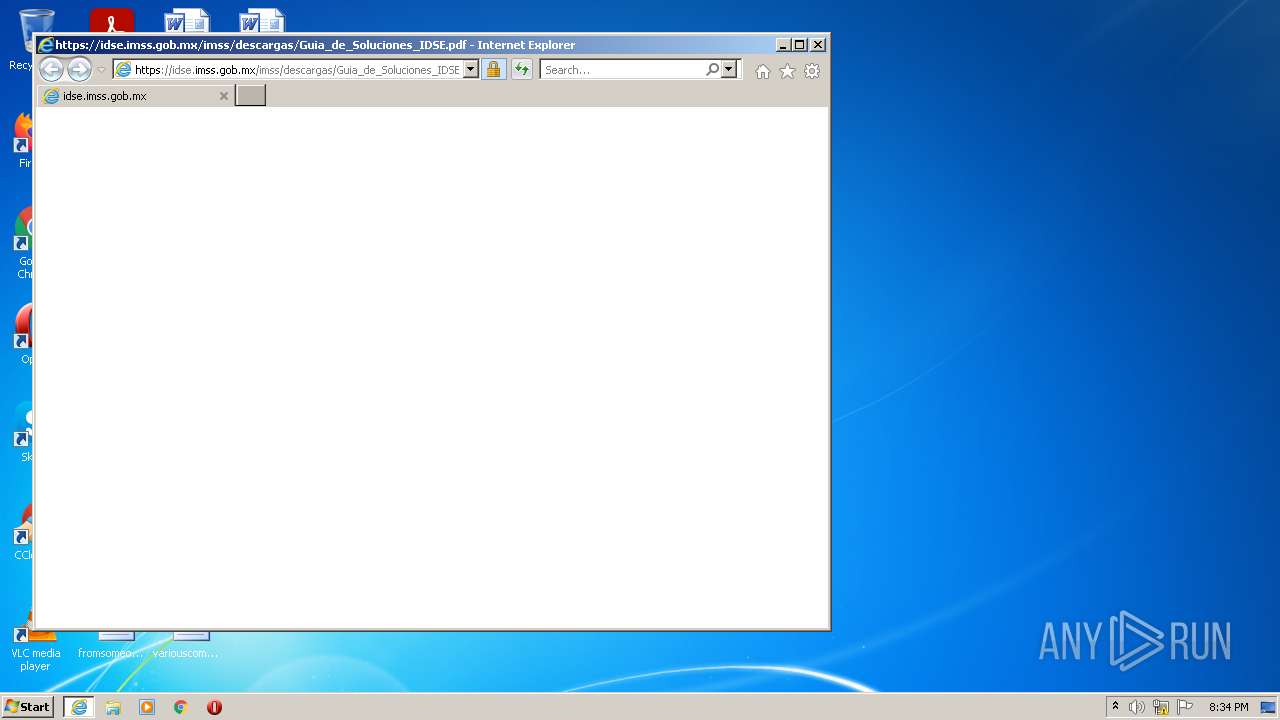
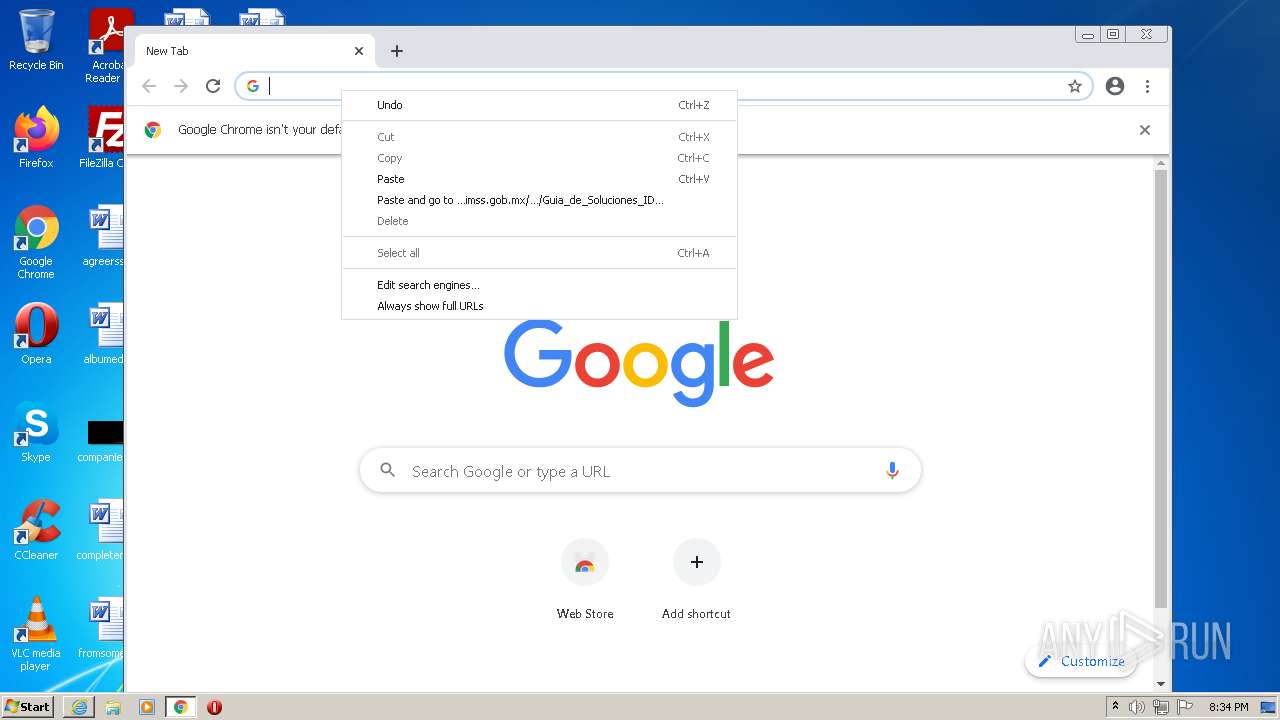
| 2460 | "C:\Windows\Installer\MSIAA43.tmp" https://idse.imss.gob.mx/imss/descargas/Guia_de_Soluciones_IDSE.pdf | C:\Windows\Installer\MSIAA43.tmp | — | msiexec.exe | |||||||||||
User: admin Company: Caphyon LTD Integrity Level: MEDIUM Description: File that launches another file Exit code: 0 Version: 18.3.0.0 Modules
| |||||||||||||||
| 2604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,15542712207785472476,5362592490089323433,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2292 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
34 761
Read events
34 429
Write events
312
Delete events
20
Modification events
| (PID) Process: | (3416) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 580D000036CC52905C7FD801 | |||
| (PID) Process: | (3416) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: C4C541ED2D65CD22C18881D7EFF89B0212E6389CB6DDDC791501953219379354 | |||
| (PID) Process: | (3416) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2460) MSIAA43.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {FBF23B40-E3F0-101B-8488-00AA003E56F8} {000214E4-0000-0000-C000-000000000046} 0xFFFF |
Value: 010000000000000064AF18915C7FD801 | |||
| (PID) Process: | (2656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30965596 | |||
| (PID) Process: | (2656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30965596 | |||
| (PID) Process: | (2656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
9
Suspicious files
132
Text files
97
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3416 | msiexec.exe | C:\Windows\Installer\fa6c6.msi | — | |
MD5:— | SHA256:— | |||
| 2460 | MSIAA43.tmp | C:\Users\admin\AppData\Local\Temp\URLAA60.url | — | |
MD5:— | SHA256:— | |||
| 3416 | msiexec.exe | C:\Windows\Installer\fa6ca.msi | — | |
MD5:— | SHA256:— | |||
| 3416 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF65597FD92A25EFD0.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3416 | msiexec.exe | C:\Windows\Installer\fa6c8.ipi | binary | |
MD5:— | SHA256:— | |||
| 3416 | msiexec.exe | C:\Config.Msi\fa6c9.rbs | binary | |
MD5:— | SHA256:— | |||
| 2196 | MsiExec.exe | C:\Users\admin\AppData\Roaming\IMSS\IDSE\prerequisites\versionIDSE\actualizacionIDSE.exe | executable | |
MD5:— | SHA256:— | |||
| 3416 | msiexec.exe | C:\Windows\Installer\MSIA9F2.tmp | executable | |
MD5:20C782EB64C81AC14C83A853546A8924 | SHA256:0ED6836D55180AF20F71F7852E3D728F2DEFE22AA6D2526C54CFBBB4B48CC6A1 | |||
| 2196 | MsiExec.exe | C:\Users\admin\AppData\Roaming\IMSS\IDSE\prerequisites\aipackagechainer.ini | text | |
MD5:— | SHA256:— | |||
| 3416 | msiexec.exe | C:\Windows\Installer\MSIAEFA.tmp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
46
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
564 | powershell.exe | GET | 200 | 23.37.43.27:80 | http://t2.symcb.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQwF4prw9S7mCbCEHD%2Fyl6nWPkczAQUe1tFz6%2FOy3r9MZIaarbzRutXSFACEHGgtzaV3bGvwjsrmhjuVMs%3D | NL | der | 1.49 Kb | whitelisted |
3068 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2656 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3068 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEHxMIovC4uGoEl9OwTOkmXY%3D | US | der | 471 b | whitelisted |
3068 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDHX3iCvc0o2BIcmpte%2Byj7 | US | der | 472 b | whitelisted |
3068 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
564 | powershell.exe | GET | 200 | 23.37.43.27:80 | http://tl.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSFBjxN%2BWY73bfUnSOp7HDKJ%2Fbx0wQUV4abVLi%2BpimK5PbC4hMYiYXN3LcCEHl9WWYEkVW%2Bvzg%2F%2BwvjKRA%3D | NL | der | 1.41 Kb | whitelisted |
2656 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3068 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3068 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://crl.pki.goog/gsr1/gsr1.crl | US | der | 1.61 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
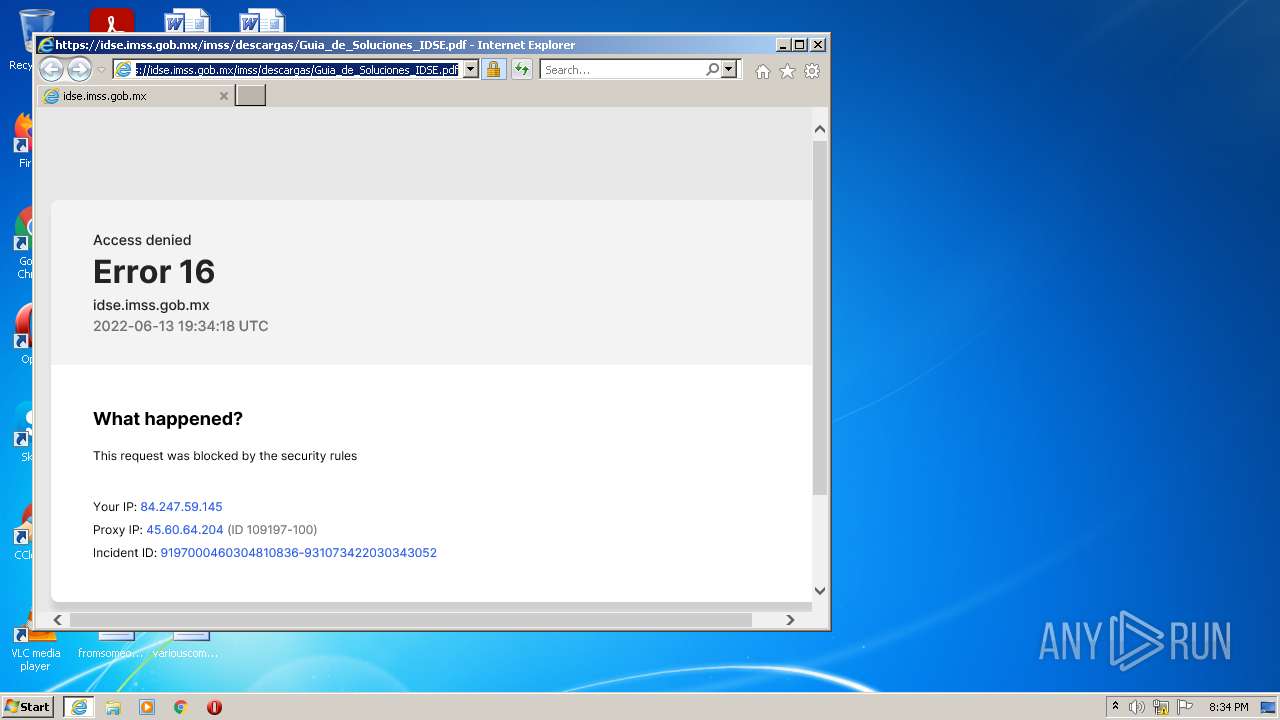
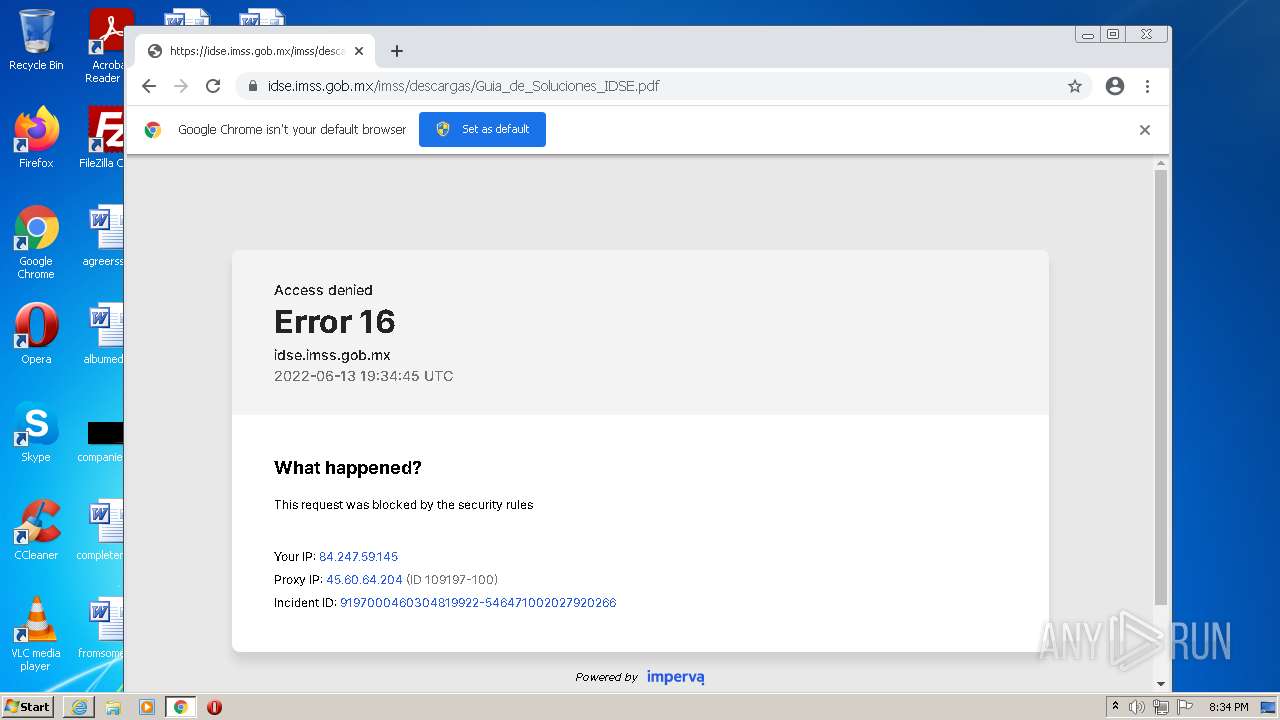
3068 | iexplore.exe | 45.60.64.204:443 | idse.imss.gob.mx | Incapsula Inc | US | suspicious |
3068 | iexplore.exe | 142.250.185.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
564 | powershell.exe | 23.37.43.27:80 | t2.symcb.com | Akamai Technologies, Inc. | NL | whitelisted |
3068 | iexplore.exe | 172.217.23.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2656 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2656 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3068 | iexplore.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3476 | chrome.exe | 142.250.181.227:443 | crl.pki.goog | Google Inc. | US | whitelisted |
3476 | chrome.exe | 142.250.184.228:443 | www.google.com | Google Inc. | US | whitelisted |
3476 | chrome.exe | 142.250.185.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
idse.imss.gob.mx |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
t2.symcb.com |
| whitelisted |
tl.symcd.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.pki.goog |
| whitelisted |