| File name: | AgentSetup.exe |
| Full analysis: | https://app.any.run/tasks/168764bb-e0e2-4421-8fee-b557833b5d3a |
| Verdict: | Malicious activity |
| Analysis date: | February 07, 2020, 03:35:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | AD146AAE3A2683DAAEF16249741E2237 |
| SHA1: | C87355A1AB62B3D9AC6CF9BA8F778748CD72F18D |
| SHA256: | 4A5911B927168C4E719BB0852DDC893AEEED356E1EA3C558128EAE06F4730730 |
| SSDEEP: | 196608:+Iy5enGuZ/D4kg5Gf/gt9FxHCiL48HTNzZW+8mC71COPnfWOXnljVDf:+Iy5q4GXgbFx/L48ZZW+8mC71CIf5Xh9 |
MALICIOUS
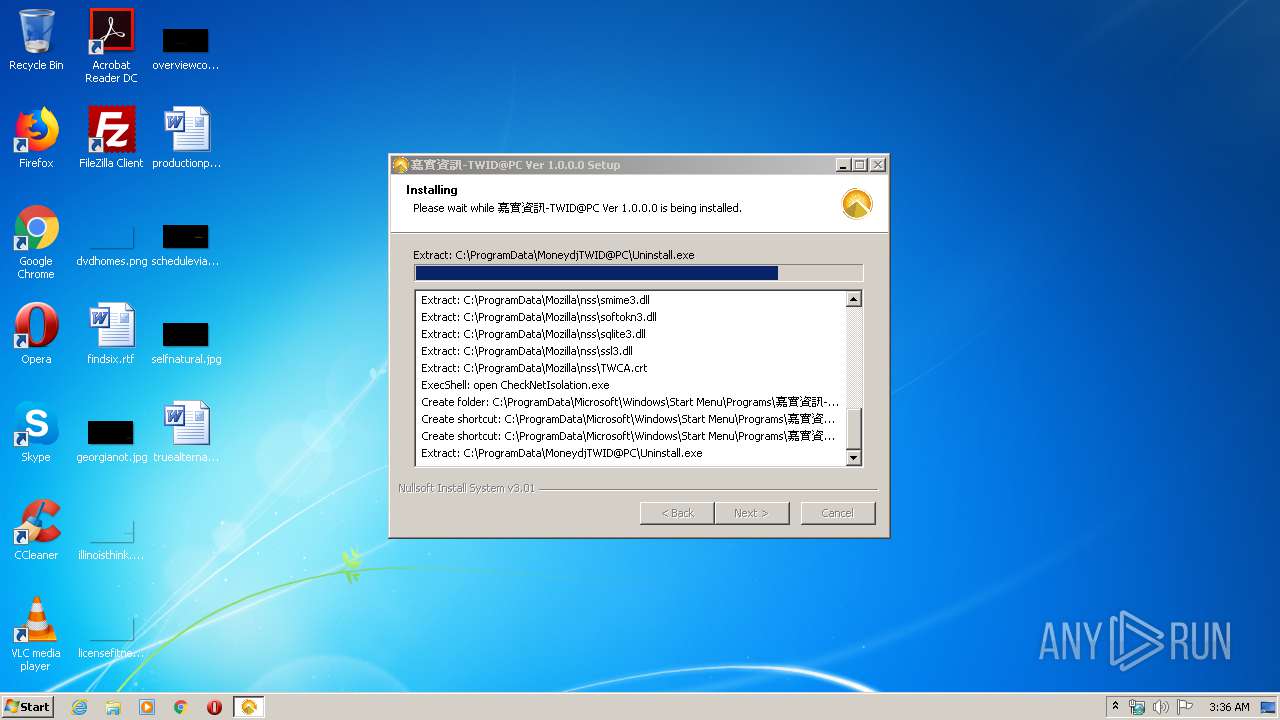
Changes settings of System certificates
- AgentSetup.exe (PID: 2412)
Application was dropped or rewritten from another process
- MoneydjTWID.exe (PID: 604)
- certutil.exe (PID: 2888)
Changes internet zones settings
- MoneydjTWID.exe (PID: 604)
Loads dropped or rewritten executable
- AgentSetup.exe (PID: 2412)
- certutil.exe (PID: 2888)
Changes the autorun value in the registry
- MoneydjTWID.exe (PID: 604)
SUSPICIOUS
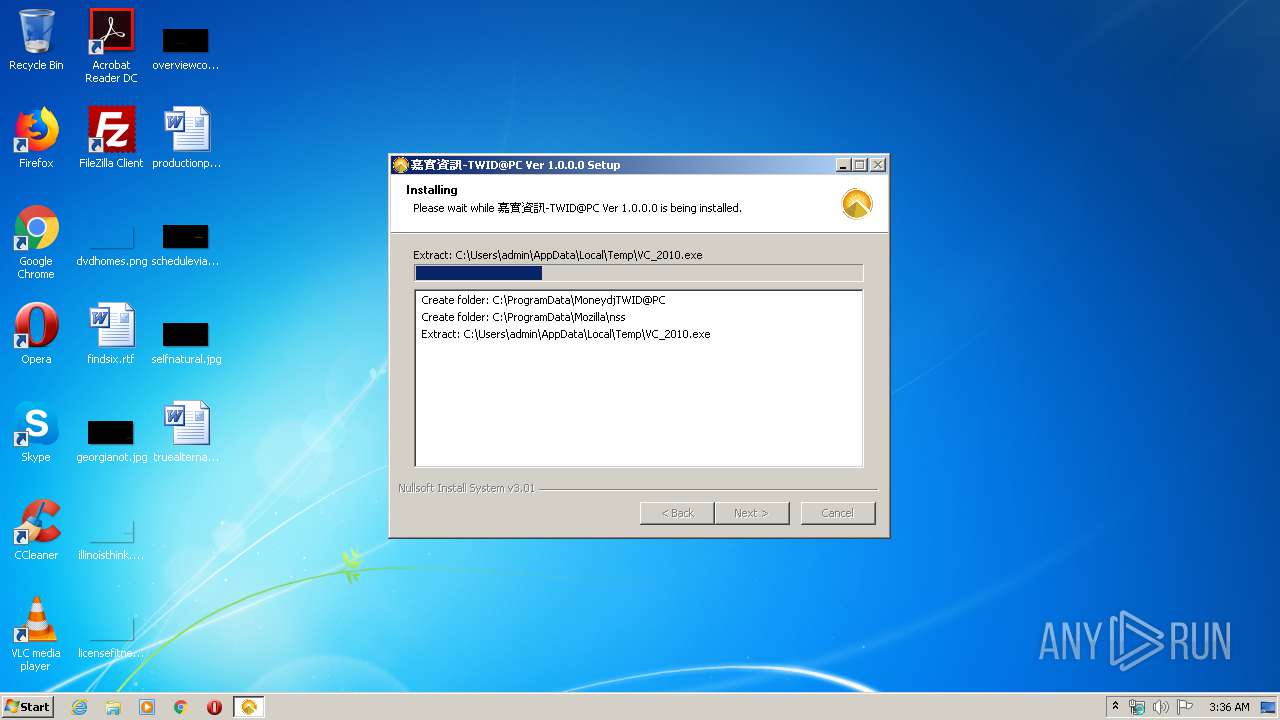
Creates files in the program directory
- AgentSetup.exe (PID: 2412)
Executable content was dropped or overwritten
- AgentSetup.exe (PID: 2412)
Creates files in the user directory
- MoneydjTWID.exe (PID: 604)
- certutil.exe (PID: 2888)
Creates a software uninstall entry
- AgentSetup.exe (PID: 2412)
INFO
Manual execution by user
- MoneydjTWID.exe (PID: 604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:12:11 22:50:48+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x344a |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Windows, Chinese (Simplified) |
| CompanyName: | 臺灣網路認證股份有限公司 |
| FileDescription: | 臺灣網路認證股份有限公司元件安裝程式 |
| FileVersion: | 1.0.0.0 |
| LegalCopyright: | 2019 臺灣網路認證股份有限公司版權所有 c |
| LegalTrademarks: | - |
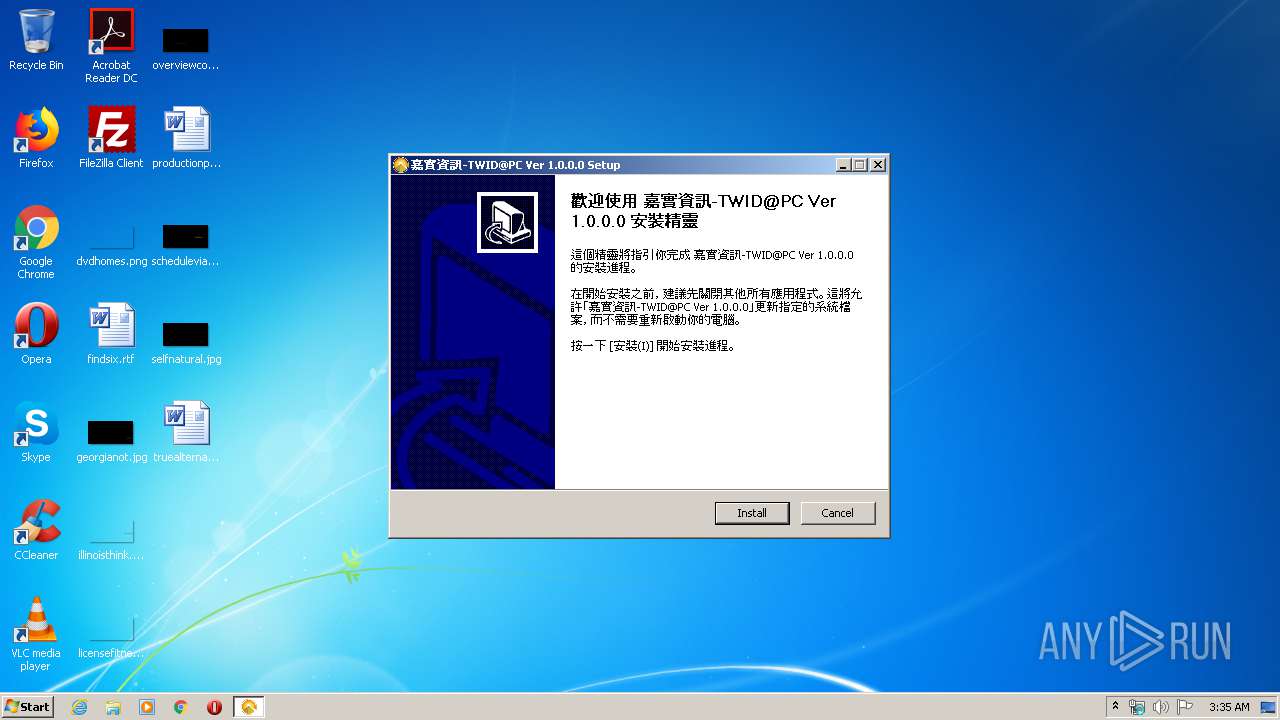
| ProductName: | 嘉實資訊-TWID@PC |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Dec-2016 21:50:48 |
| Detected languages: |
|
| CompanyName: | 臺灣網路認證股份有限公司 |
| FileDescription: | 臺灣網路認證股份有限公司元件安裝程式 |
| FileVersion: | 1.0.0.0 |
| LegalCopyright: | 2019 臺灣網路認證股份有限公司版權所有 c |
| LegalTrademarks: | - |
| ProductName: | 嘉實資訊-TWID@PC |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Dec-2016 21:50:48 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000061F1 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47707 |
.rdata | 0x00008000 | 0x000013A4 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.163 |
.data | 0x0000A000 | 0x00020338 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.97456 |
.ndata | 0x0002B000 | 0x00017000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00042000 | 0x0001DDF8 | 0x0001DE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.50411 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28813 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 7.9681 | 43224 | UNKNOWN | English - United States | RT_ICON |
3 | 0 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 0 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 3.11012 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
41
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 604 | "C:\ProgramData\MoneydjTWID@PC\MoneydjTWID.exe" | C:\ProgramData\MoneydjTWID@PC\MoneydjTWID.exe | explorer.exe | ||||||||||||
User: admin Company: 臺灣網路認證股份有限公司 Integrity Level: MEDIUM Description: TSTARTWID Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2412 | "C:\Users\admin\AppData\Local\Temp\AgentSetup.exe" | C:\Users\admin\AppData\Local\Temp\AgentSetup.exe | explorer.exe | ||||||||||||
User: admin Company: 臺灣網路認證股份有限公司 Integrity Level: HIGH Description: 臺灣網路認證股份有限公司元件安裝程式 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2500 | "C:\Users\admin\AppData\Local\Temp\AgentSetup.exe" | C:\Users\admin\AppData\Local\Temp\AgentSetup.exe | — | explorer.exe | |||||||||||
User: admin Company: 臺灣網路認證股份有限公司 Integrity Level: MEDIUM Description: 臺灣網路認證股份有限公司元件安裝程式 Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2888 | "C:\ProgramData\Mozilla\nss\certutil.exe" -A -n "TWCA_SSLCA" -i "C:\ProgramData\Mozilla\nss\TWCA.crt" -t "CT,c,c" -d "C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default" | C:\ProgramData\Mozilla\nss\certutil.exe | — | MoneydjTWID.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
413
Read events
400
Write events
13
Delete events
0
Modification events
| (PID) Process: | (2412) AgentSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\415D5BF4EEAEB7075C2AFBC16896B23923ECA026 |
| Operation: | write | Name: | Blob |
Value: 0400000001000000100000004208B4B301331AB9AC92EBC283CF1C880F00000001000000200000009AABF2FA47DC8C09B6631573744073527BFA12C439EA1192332A13CDF59371771400000001000000140000009835F31DB59D86CF612297BFB427BF35345723BA190000000100000010000000AC473495A236CFB9315E466C442EA970030000000100000014000000415D5BF4EEAEB7075C2AFBC16896B23923ECA0265C00000001000000040000000010000020000000010000008B050000308205873082036FA003020102020701020304050001300D06092A864886F70D01010B05003059310B3009060355040613025457310D300B060355040A13045457434131163014060355040B130D5457434120446576656C6F7065312330210603550403131A5457434120436572746966696361746520417574686F72697479301E170D3139303332383036303930305A170D3239303332383036303930305A3059310B3009060355040613025457310D300B060355040A13045457434131163014060355040B130D5457434120446576656C6F7065312330210603550403131A5457434120436572746966696361746520417574686F7269747930820222300D06092A864886F70D01010105000382020F003082020A0282020100B2CF12398E6546C04AEEFE33FFF607AF91F463B1B13C1F1CCAE16479562F7467CD02063359EE57DEDF90F08E023DDC14A7ADB0DE9948CA2EDC1E2BD6BDFE9A3ED6DD0E00235F3589E87BF0D23F1E1AC68826B69BF6E7243DAC42A0467182CCD8613568F5421C99FF900981B8DC5CFE229D6D886D0D10A6C31B963BC99888286CC96AD81D2AA94E8F2925CFC09AB17E2A5CD188F8869C826B54235B74C9355638EFEC482637CD104030D63EC50EA3CD2D29528DC967790B23E2671A3231539BAD5ACC57635E1619DE4262222392163BBEC8057B5523265294AD35FE5E25D4AA8A949E39DA90CDCF49C59862135C5CA73BA2061113D5029DB7E4EBCD92B9EC5E2994729B17AE6A0B063BBB69AC9BEA827017DFA448D09A1D5DE6534C73EA646E6E94EC1EC1FDF70A52214F0D759010596A5F8F65E43B1863AF3A186EBA8FCC65E53A340D65932463891F95A1035A3B5F25F7345932EE17A16E7EE8DC299C90D2E95D55AB472440332D01DA953430F26AC0365E2170522D90A2CECC14A6124DDE803758DCEC4262604A8787EB6A4FA77E9B187D11347DD900492FAB08B3AB430236F2717BA87A199F5F7516993F9F3830F07D4104487A810C3FD7BD5DB43298DACB46E26230EA522920238574B656F92FA132A37AE03D6196CAFC97D1901CD3269C2152D23C79CD26C3E669D36BBC6096A1BE1F75C6FB6AC9D870DC6E16115C01F90203010001A3543052300F0603551D130101FF040530030101FF301D0603551D0E041604149835F31DB59D86CF612297BFB427BF35345723BA300B0603551D0F0404030202FC30130603551D25040C300A06082B06010505070301300D06092A864886F70D01010B0500038202010059896C4C2DED1222C3E43EB6C881C27601B59C2E3192AD32223BC6D91A0750AB08F9A9F0D6B2B51971949C3DD1CDE958F20B4B0B4ACD107705708AF8B7B0EBB677FD2C990713B99E7D4A645E9C5E34111AAC531439EE84835FC15455B724BA74806E84BA750ABF8664112536EA70D053A66BCEE06D100730190070618C123823BDEC08ACF935DCBED5EADA3928782F8BE2834450B0FCE8493854357B40018529F3569D7609F137979130FC975D022E0B30AB2B9ADC35B5C6F13BF06A0BD86573E51E6065AACFB9F95AB8B53DA44E7919B8A10C9F7DA64D7CC5E81DB65C53FFCCDB60092956C150A2FDBF4639C032D49BB68D7CFB610644D85933CAE2BBF594A5DA68CD865C20ACD5DE5423AE14778BF979317E19BD611CA369D0A1FFB7B7DB7E091BEF04B17F8FAFBAEEB5A66BF0109409F5E3947C1D3AE58D94BC6912EFD39C897A491D83966C4FC8733E959BAD73A54B52FDD3E5F3F8FC9E74D820FF6F79101528FD5F6AAD495C179D5F01B75980EC7B3FD8054A0765786617EAE237675E42913211A76D58EA31362D7BC64412B6F6537F788C9D79D08FBC01C4B369DA70E164C08FA57DE8D265B7AE218D2FC89B31F352242F5A660B8E8233301DC22C54E27869F4EB12B17725F15D735BEF4940413B52370CD7CECA8C8B8E3D4BE56BA1BF6E119E339826B1FBD60F36B47FB07DFA190039226643EE457518A03353151B5F | |||
| (PID) Process: | (604) MoneydjTWID.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (604) MoneydjTWID.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (604) MoneydjTWID.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | TWID-Moneydj |
Value: "C:\ProgramData\MoneydjTWID@PC\MoneydjTWID.exe" | |||
| (PID) Process: | (604) MoneydjTWID.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\1 |
| Operation: | write | Name: | 1406 |
Value: 0 | |||
| (PID) Process: | (604) MoneydjTWID.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2 |
| Operation: | write | Name: | 1406 |
Value: 0 | |||
| (PID) Process: | (604) MoneydjTWID.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\3 |
| Operation: | write | Name: | 1406 |
Value: 0 | |||
| (PID) Process: | (2412) AgentSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MoneydjTWID@PC |
| Operation: | write | Name: | DisplayName |
Value: 嘉實資訊-TWID@PC (remove only) | |||
| (PID) Process: | (2412) AgentSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MoneydjTWID@PC |
| Operation: | write | Name: | DisplayIcon |
Value: C:\ProgramData\MoneydjTWID@PC\tcwIcon.ico | |||
| (PID) Process: | (2412) AgentSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MoneydjTWID@PC |
| Operation: | write | Name: | UninstallString |
Value: C:\ProgramData\MoneydjTWID@PC\Uninstall.exe | |||
Executable files
31
Suspicious files
0
Text files
28
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2412 | AgentSetup.exe | C:\Users\admin\AppData\Local\Temp\nsd821B.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 2412 | AgentSetup.exe | C:\Users\admin\AppData\Local\Temp\nsd821B.tmp\FindProcDLL.dll | executable | |
MD5:6F73B00AEF6C49EAC62128EF3ECA677E | SHA256:6EB09CE25C7FC62E44DC2F71761C6D60DD4B2D0C7D15E9651980525103AAC0A9 | |||
| 2412 | AgentSetup.exe | C:\ProgramData\MoneydjTWID@PC\tcwIcon.ico | image | |
MD5:F4D0C41E0C0F4A2D61A8BE872A8E05F7 | SHA256:AC8CE323E0E127A4054804B0D11B9C51DDFB941DF5AE7A2A78F0F3BAC956C1DA | |||
| 2412 | AgentSetup.exe | C:\ProgramData\MoneydjTWID@PC\TWCAHiCOSPKCS11V6.dll | executable | |
MD5:4915AA611E9FCF93762150F6E0CBECAE | SHA256:52022D04B9473C0D1A868E9518FBA7906AABDE8747297A572F20C0F1C0AE1571 | |||
| 2412 | AgentSetup.exe | C:\ProgramData\MoneydjTWID@PC\TWCAATM.dll | executable | |
MD5:0C12CABAD7E90C498E108606EFBBD017 | SHA256:8F6AD38F406A06898963B334DB62C5B3615AB7B676FF218175E7D1C647993449 | |||
| 2412 | AgentSetup.exe | C:\ProgramData\MoneydjTWID@PC\SecuComp.dll | executable | |
MD5:6BB67C4C78CB37352FA63D4CDEBC7C66 | SHA256:B7D43BC5B15C199F13917C1BF3CB766E9FB55E8F22CA5912DA080071D8D02222 | |||
| 2412 | AgentSetup.exe | C:\ProgramData\MoneydjTWID@PC\TWCACapiATL.dll | executable | |
MD5:C70B8533AA7F9C303CC759D4D5A01754 | SHA256:33645C15FA93715028A8FD41E6D239DFB6EEA6E54D798354BA545BDD24E9075B | |||
| 2412 | AgentSetup.exe | C:\ProgramData\MoneydjTWID@PC\ICCDFCDLL.dll | executable | |
MD5:B250791F99A3C28C9169A6AE81A75939 | SHA256:CD7486312F073013417BB45B6C91D5170A0AFA1B8FF5677BC234C64EA24D7FD6 | |||
| 2412 | AgentSetup.exe | C:\Users\admin\AppData\Local\Temp\VC_2010.exe | executable | |
MD5:B88228D5FEF4B6DC019D69D4471F23EC | SHA256:8162B2D665CA52884507EDE19549E99939CE4EA4A638C537FA653539819138C8 | |||
| 2412 | AgentSetup.exe | C:\ProgramData\MoneydjTWID@PC\TWCAPKCS11V3.dll | executable | |
MD5:3E0E128A7165E53D7E4A5503BD22283A | SHA256:95A0CBDF36A4959E8509A9C29C165130411830364C2A12AFA0A089530A45D900 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report