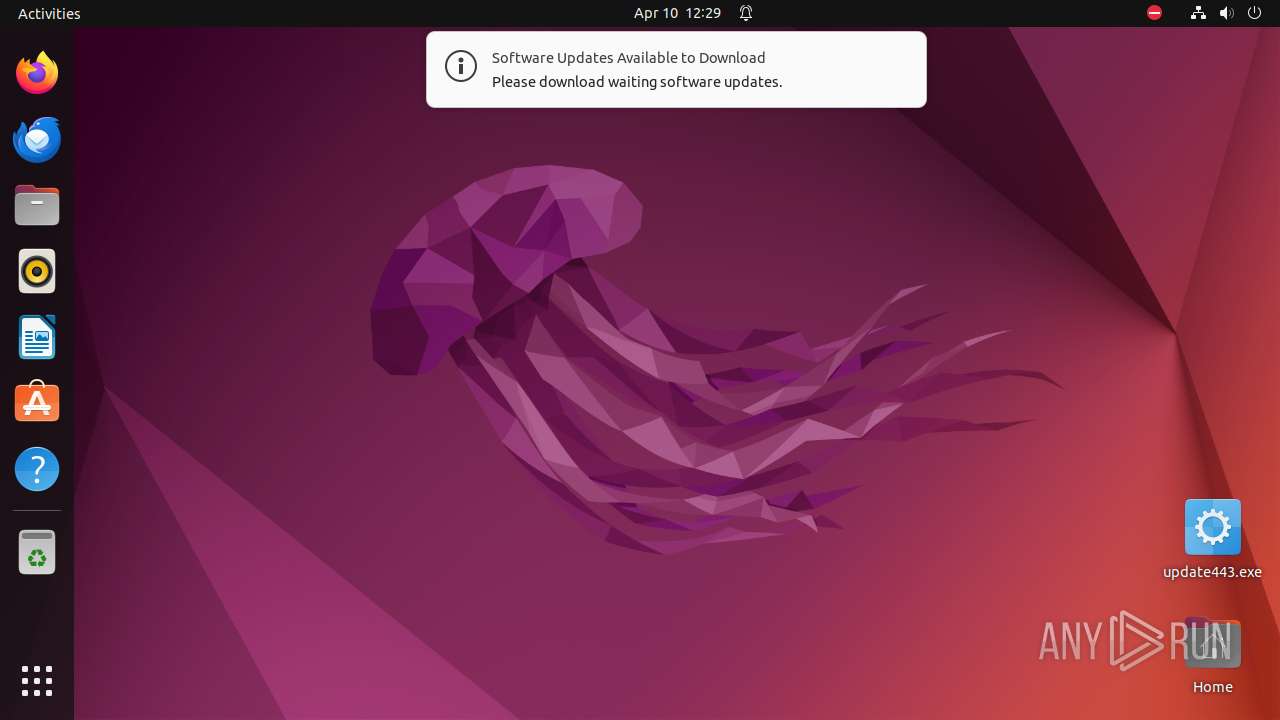
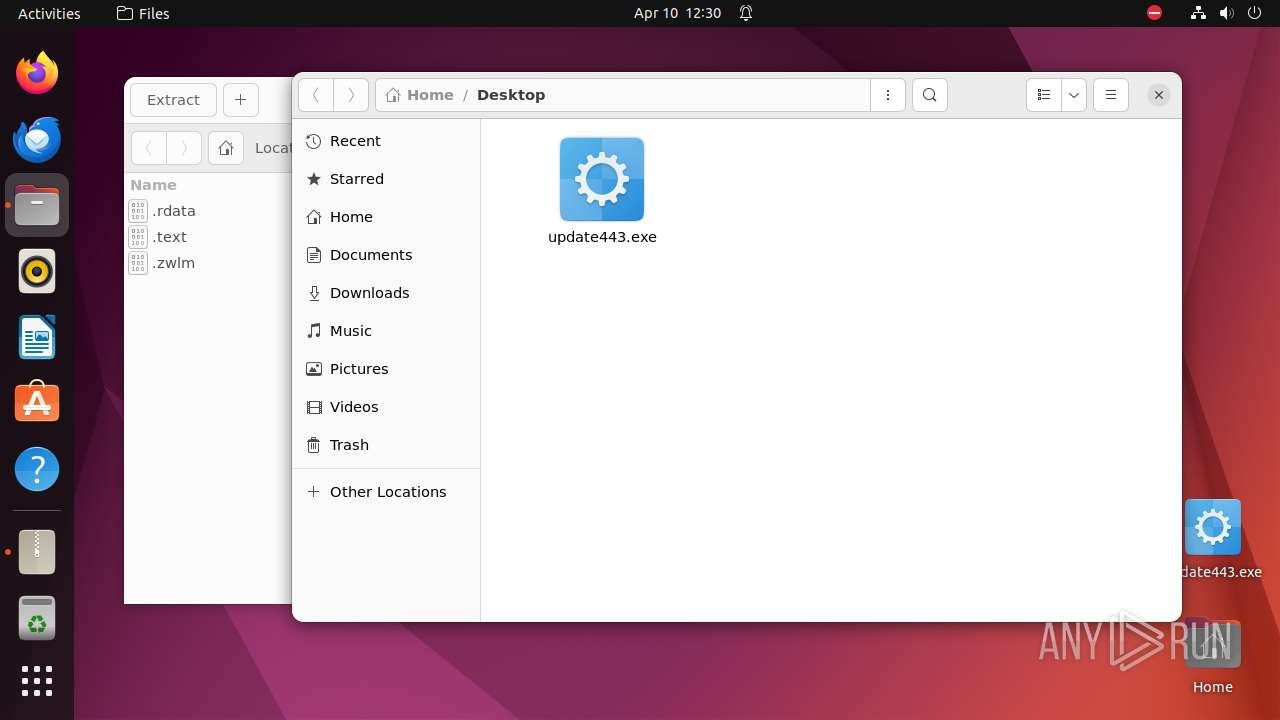
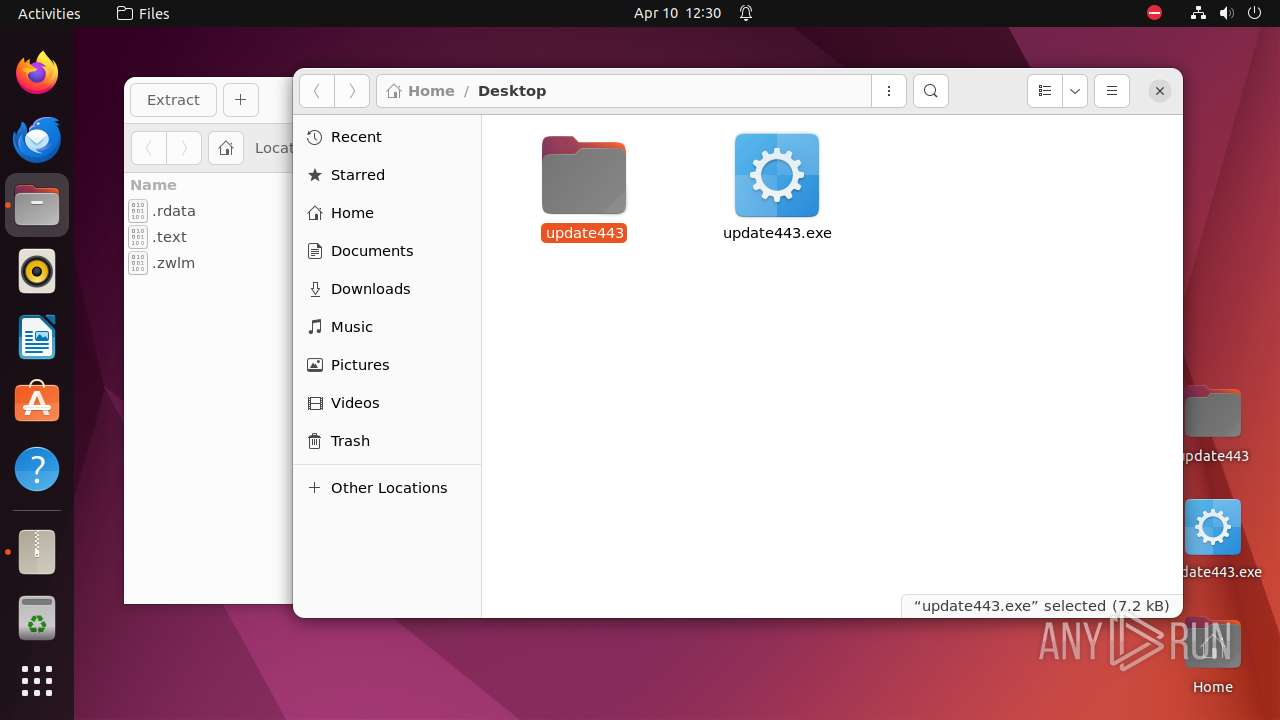
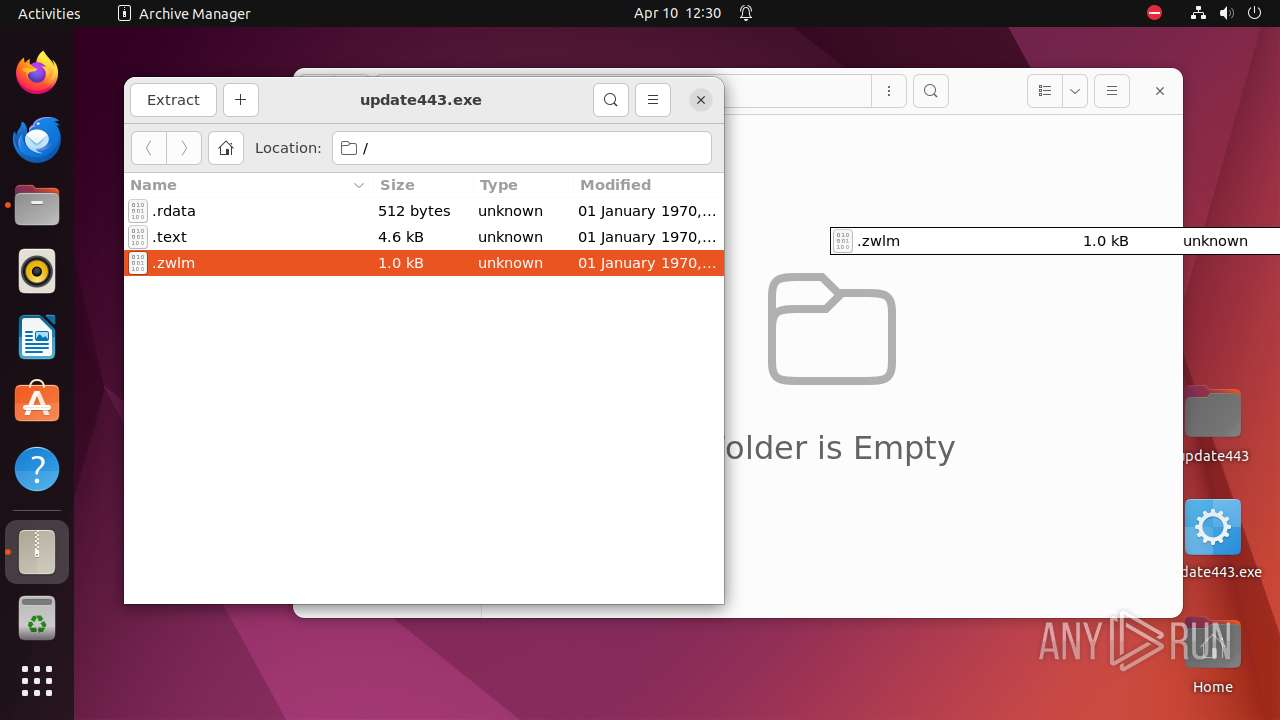
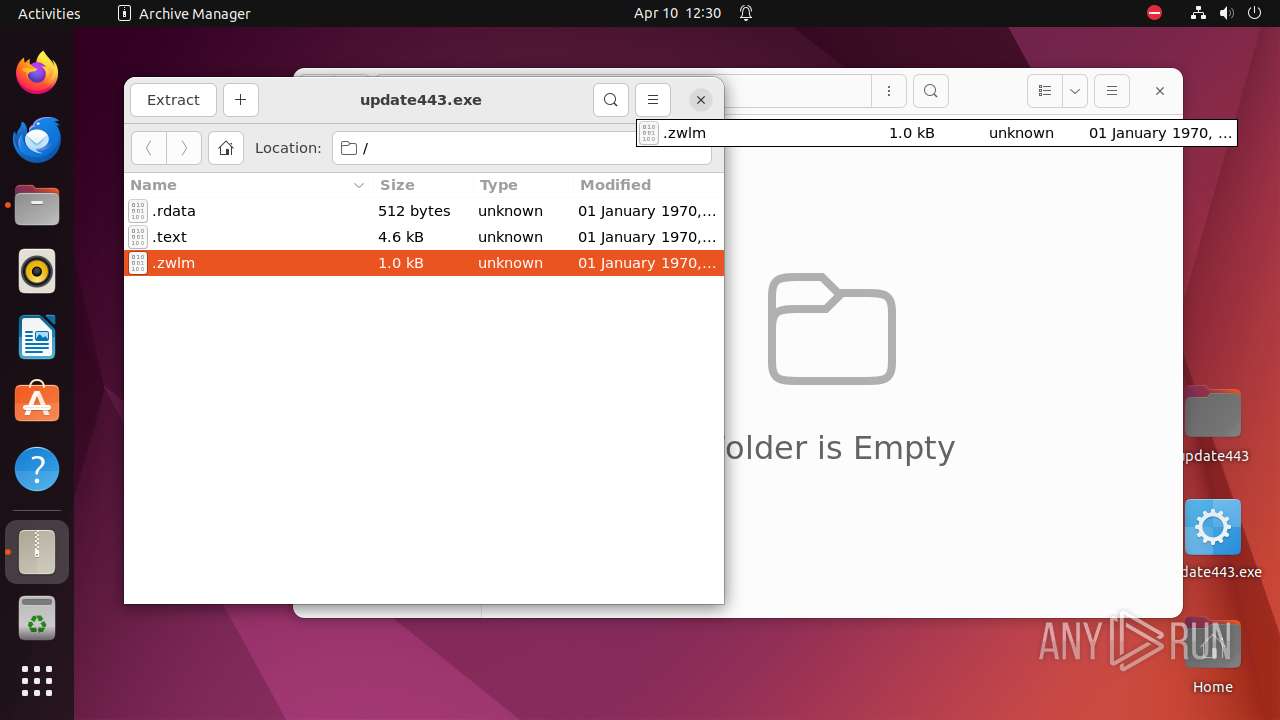
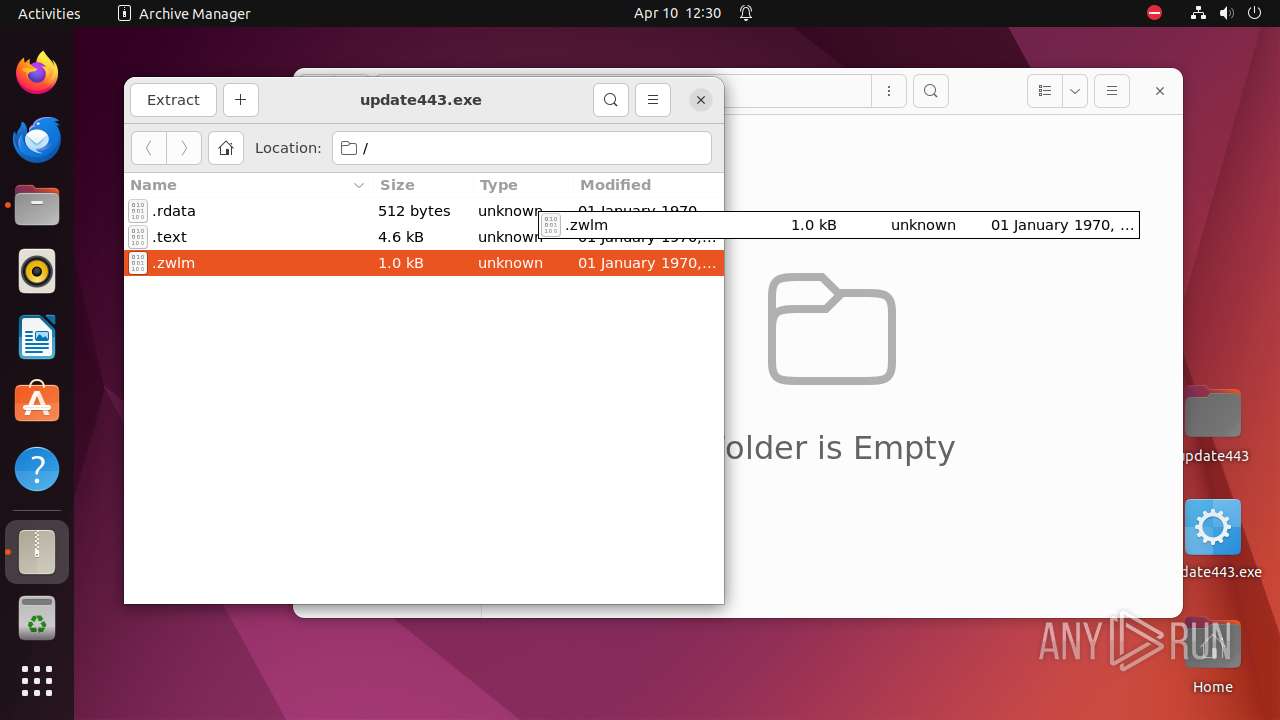
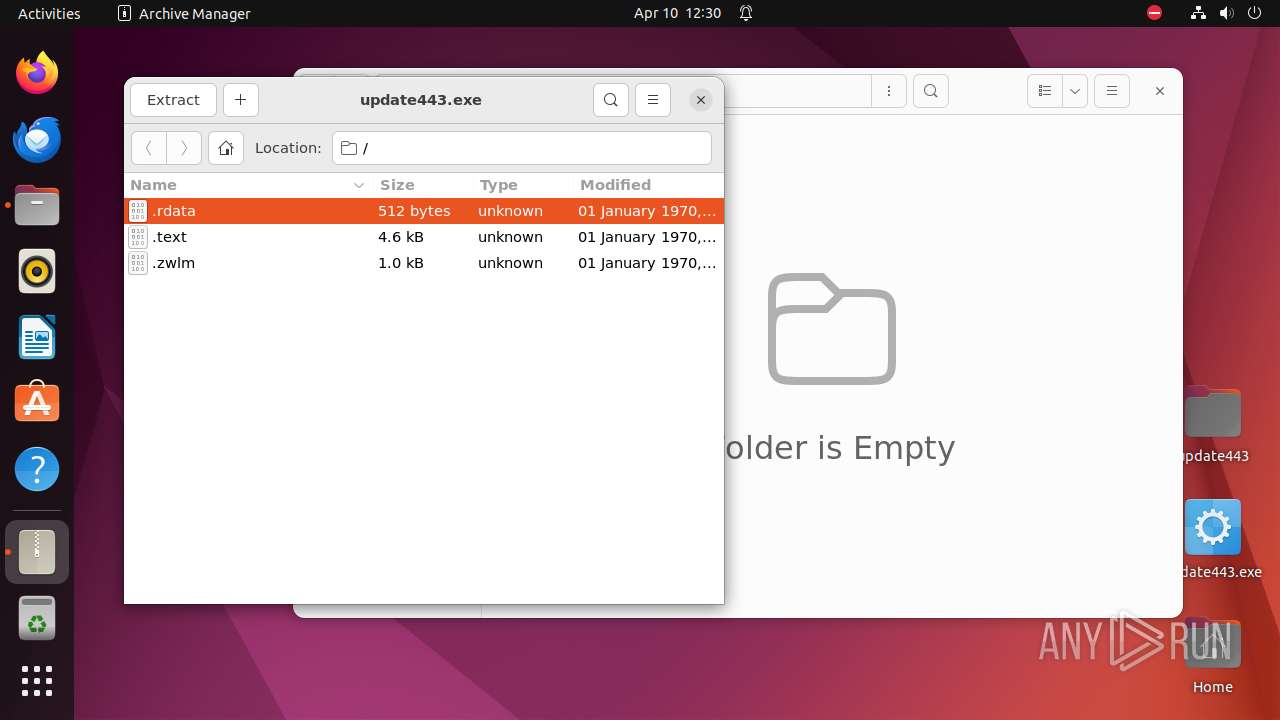
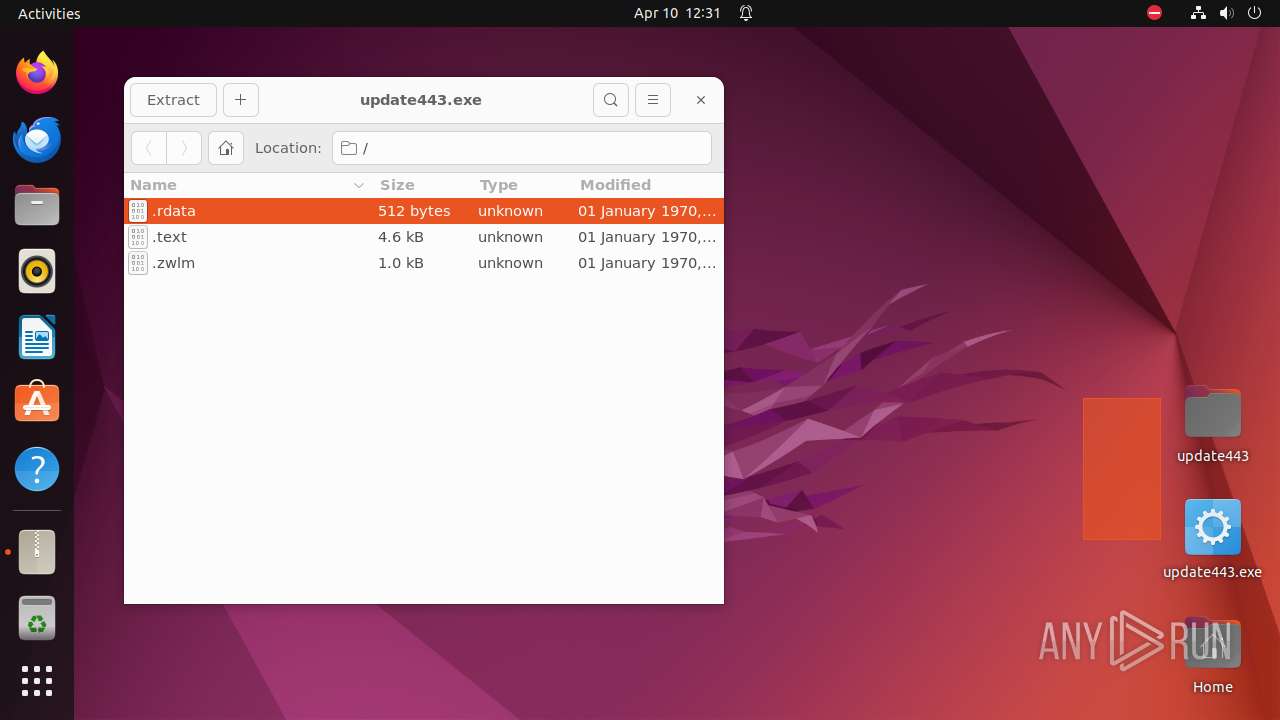
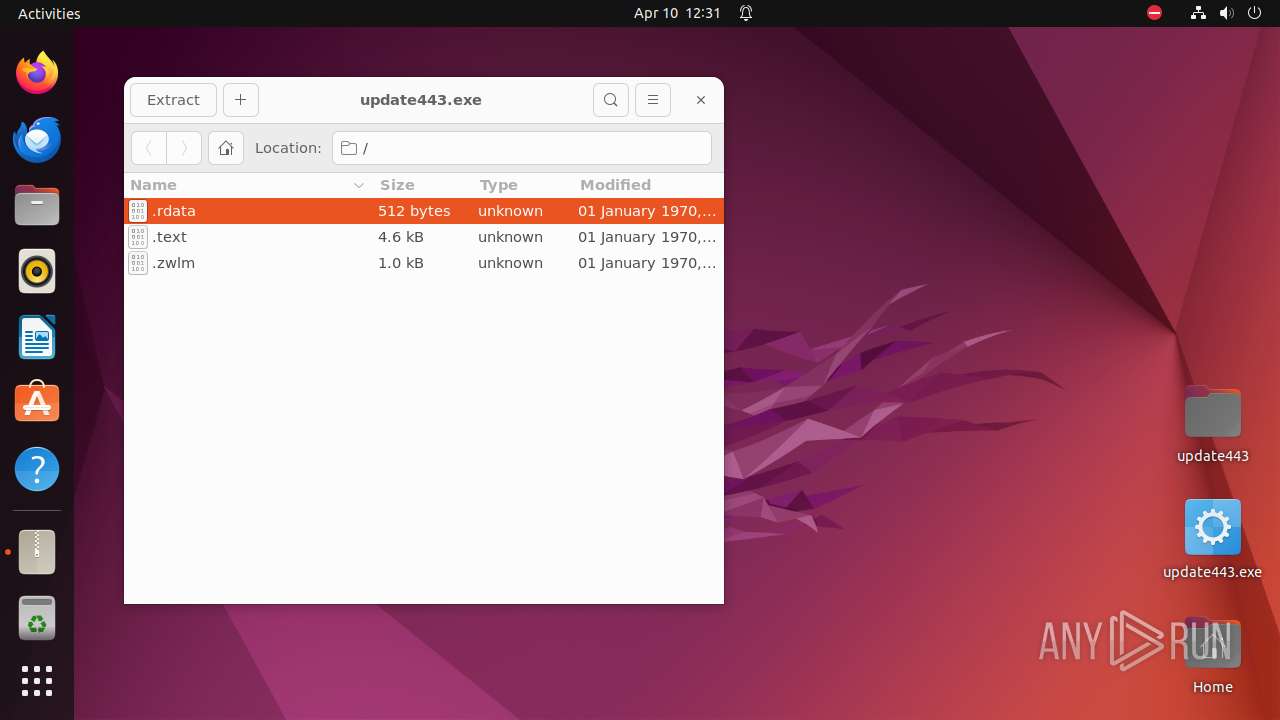
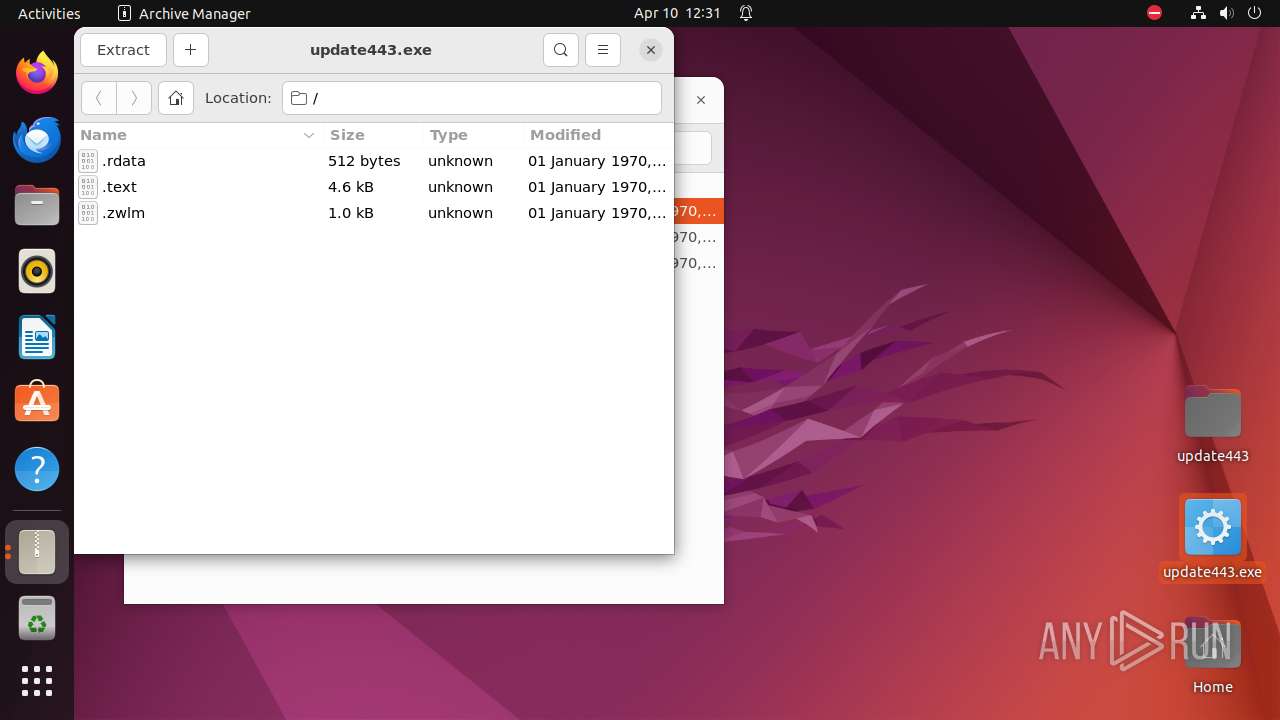
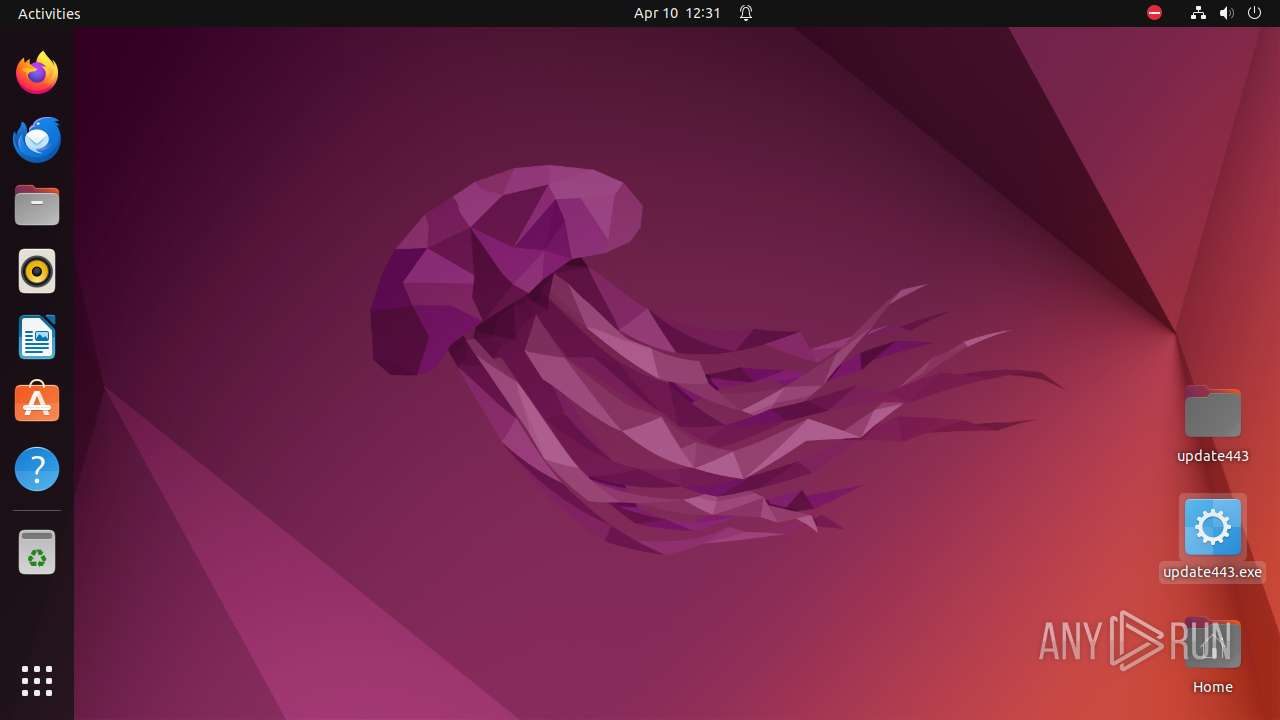
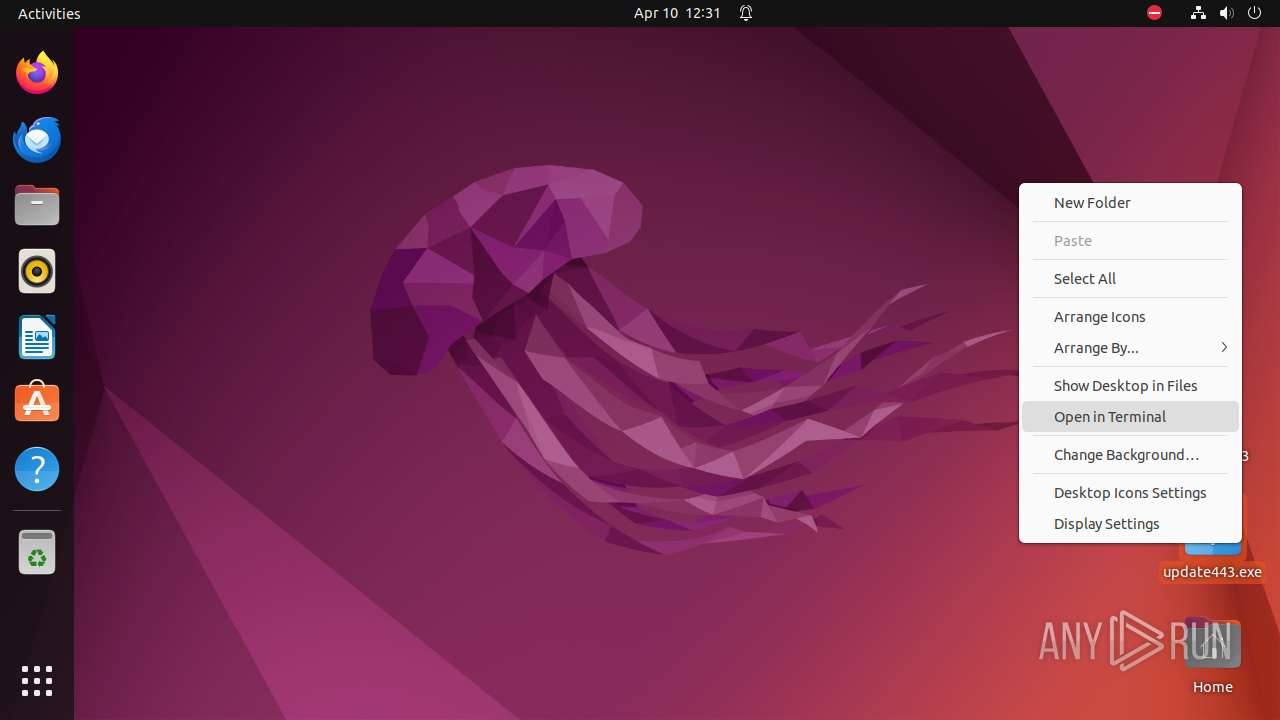
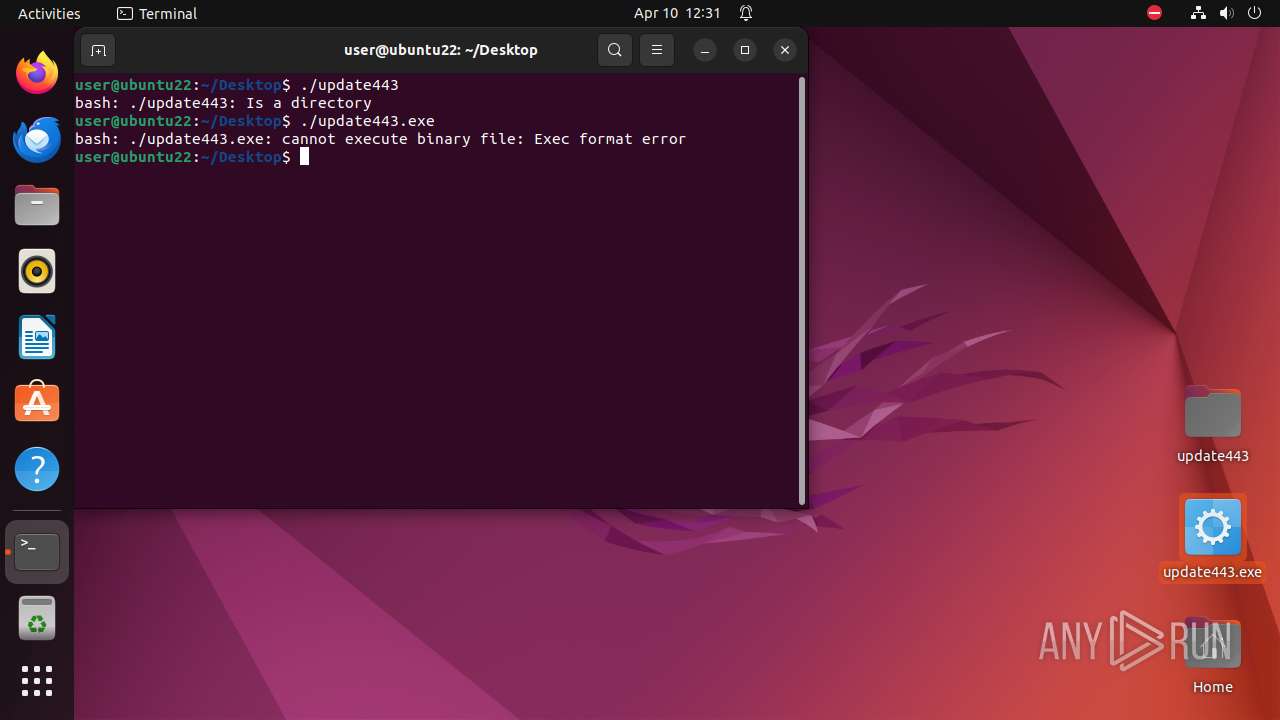
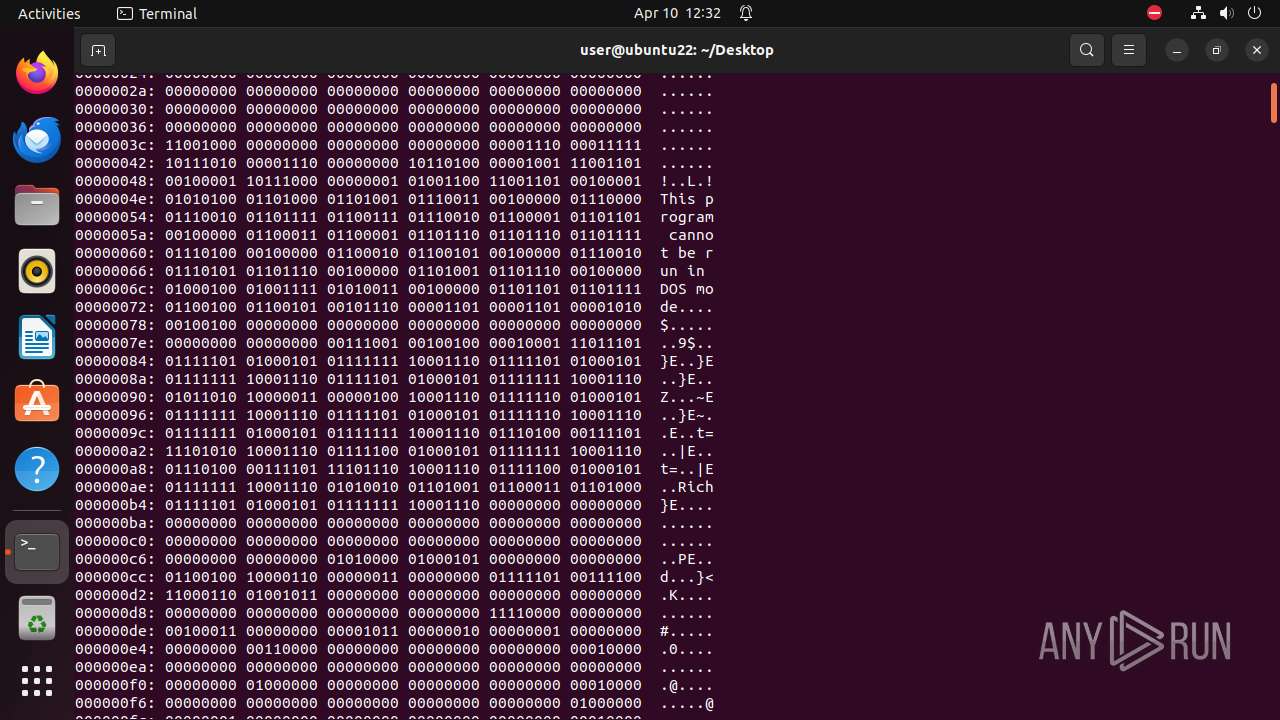
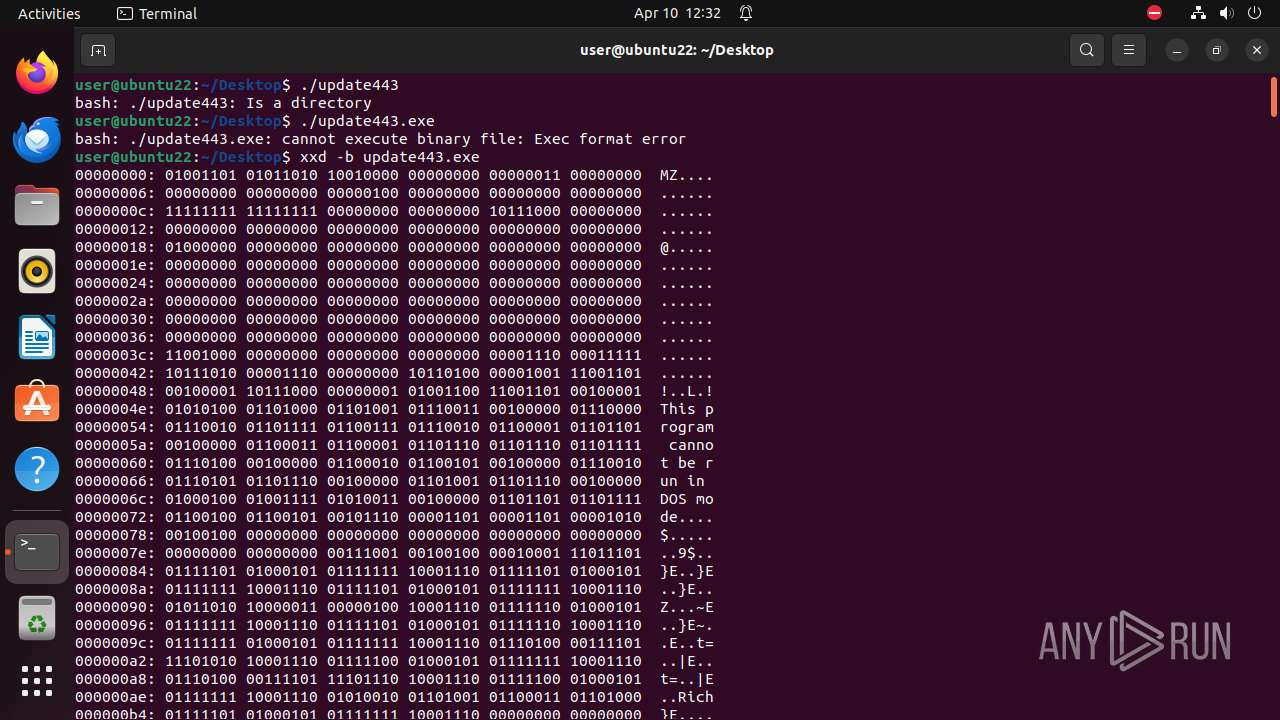
| File name: | update443.exe |
| Full analysis: | https://app.any.run/tasks/1ffe6652-2b7e-4d1b-ac29-b41c01cb2867 |
| Verdict: | Malicious activity |
| Analysis date: | April 10, 2024, 11:29:46 |
| OS: | Ubuntu 22.04.2 |
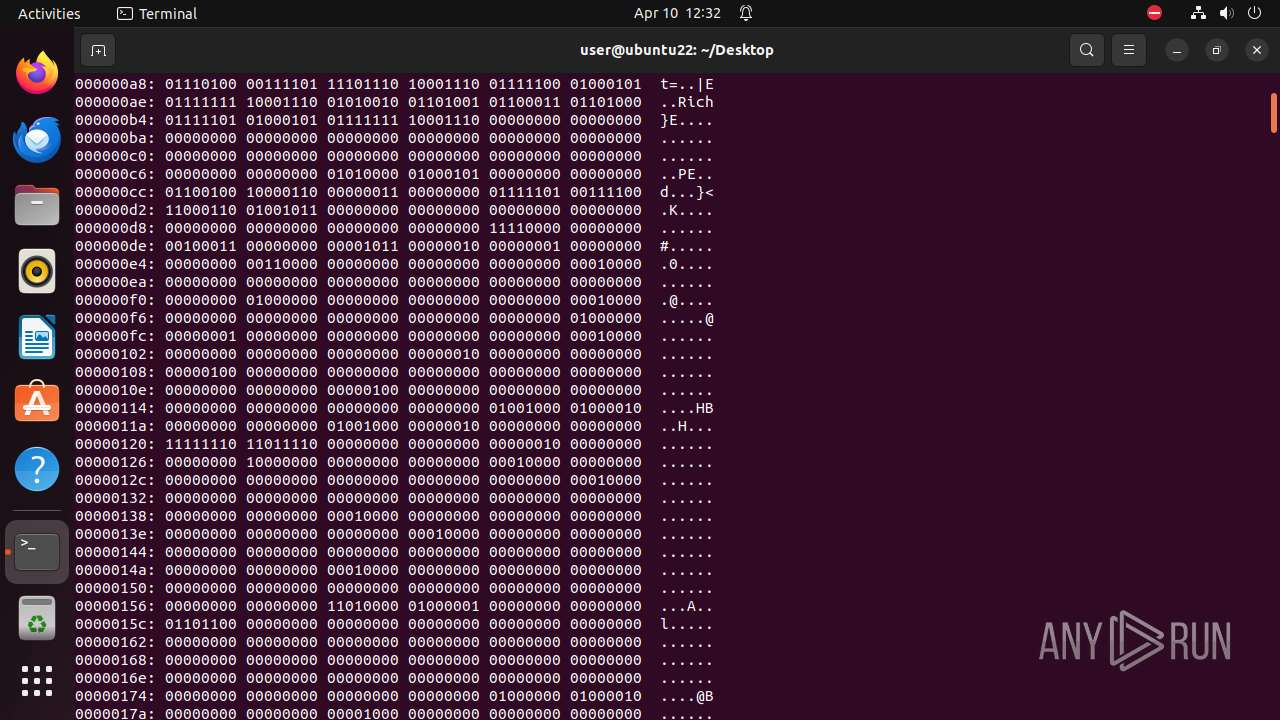
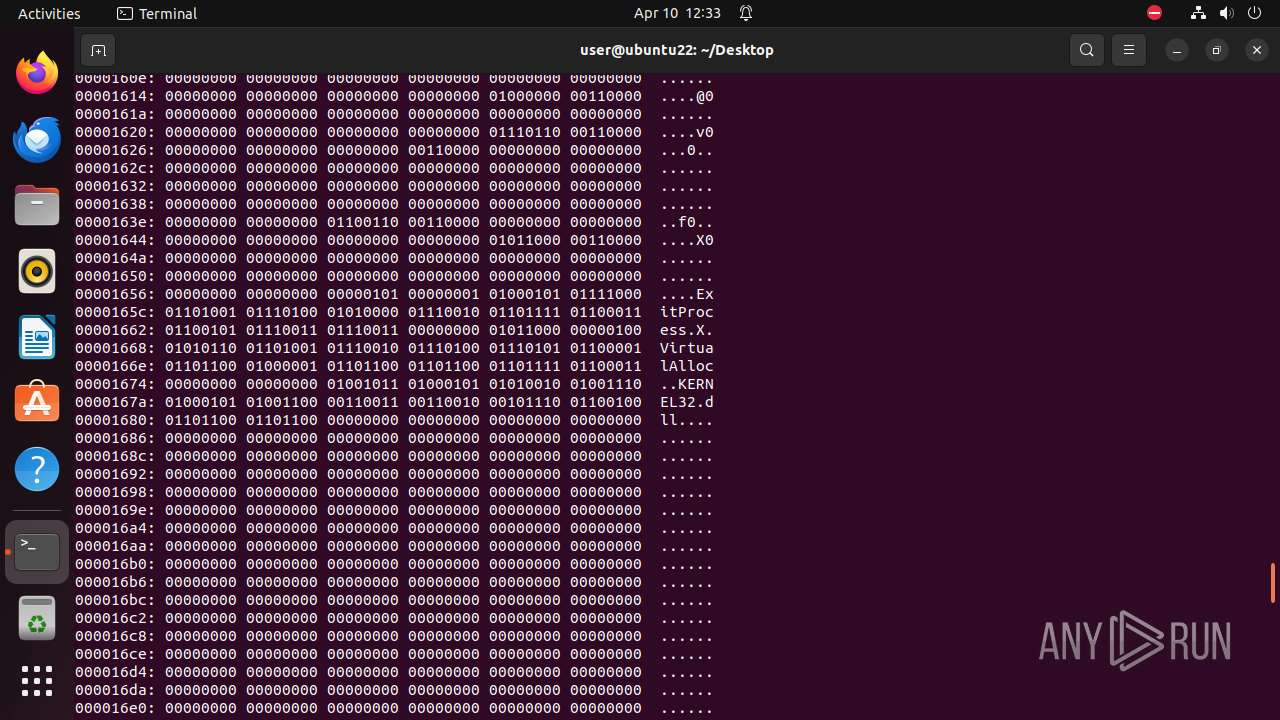
| MIME: | application/x-dosexec |
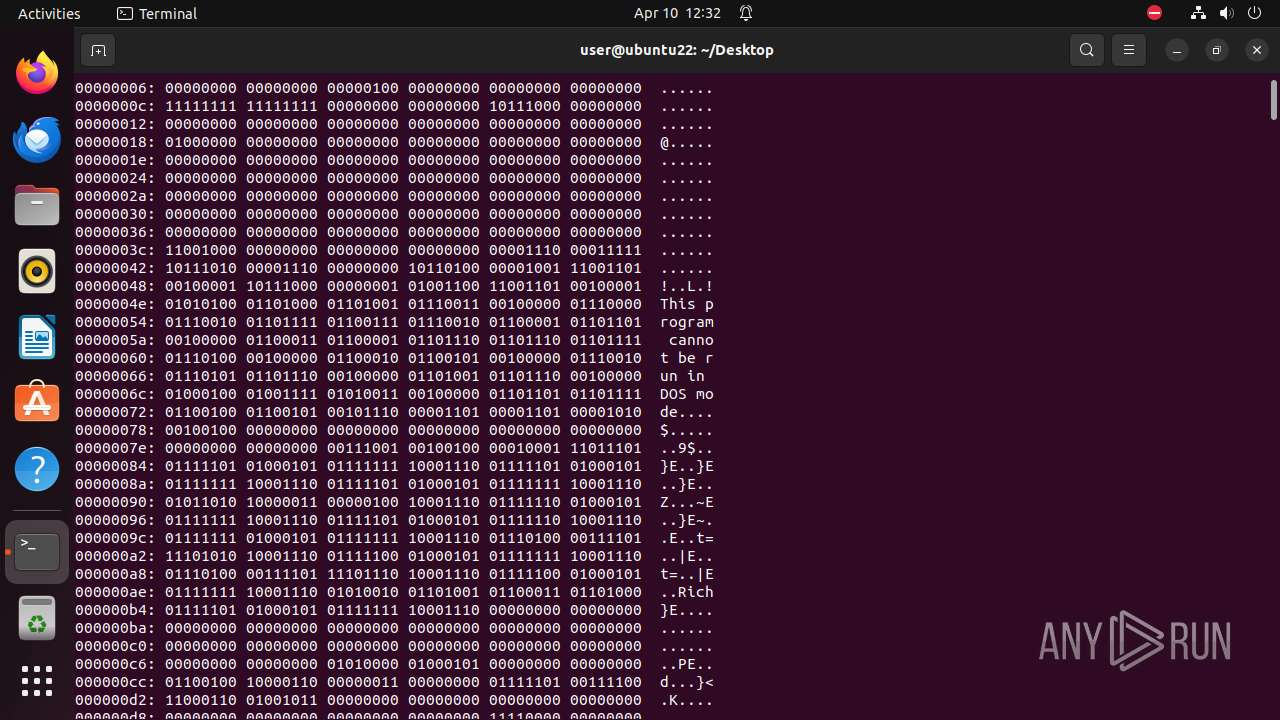
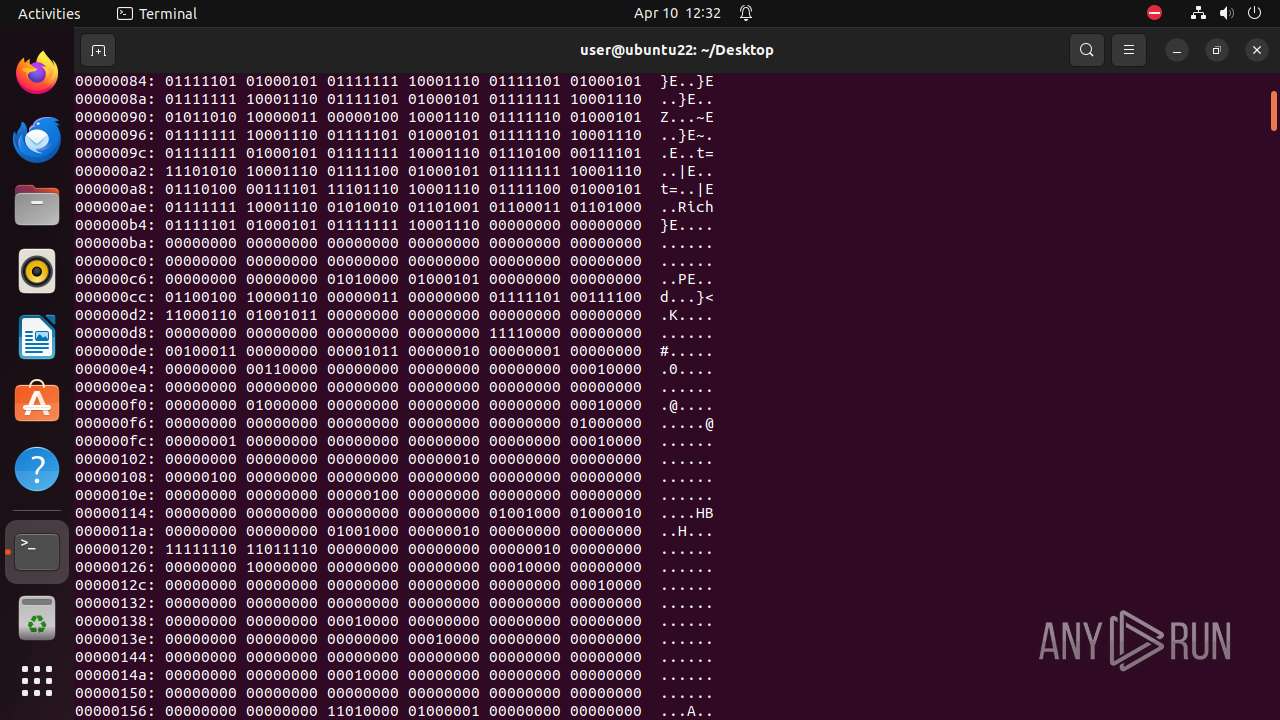
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | 93078118C1BB96FCD5B371829F010206 |
| SHA1: | B09BA498FB9EE129BD57764B871D625062C74A4E |
| SHA256: | 4A542218618B368FC5C1DEB414C514D2029FEF38813AAA9350721247839C83B2 |
| SSDEEP: | 48:YH+vj1BQ6qlrAAj2fja4hhhbcooMcL5zNwB:iQSrlrAMWjgP1Nw |
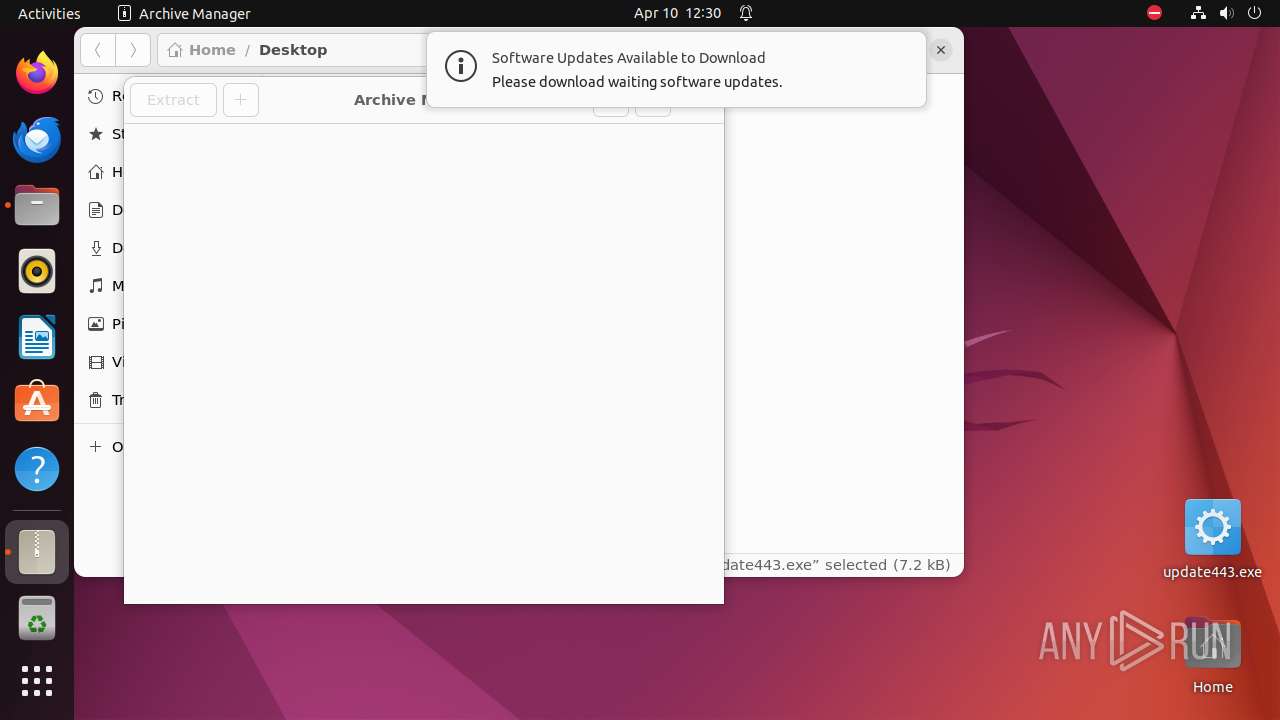
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks DMI information (probably VM detection)
- systemd-hostnamed (PID: 9305)
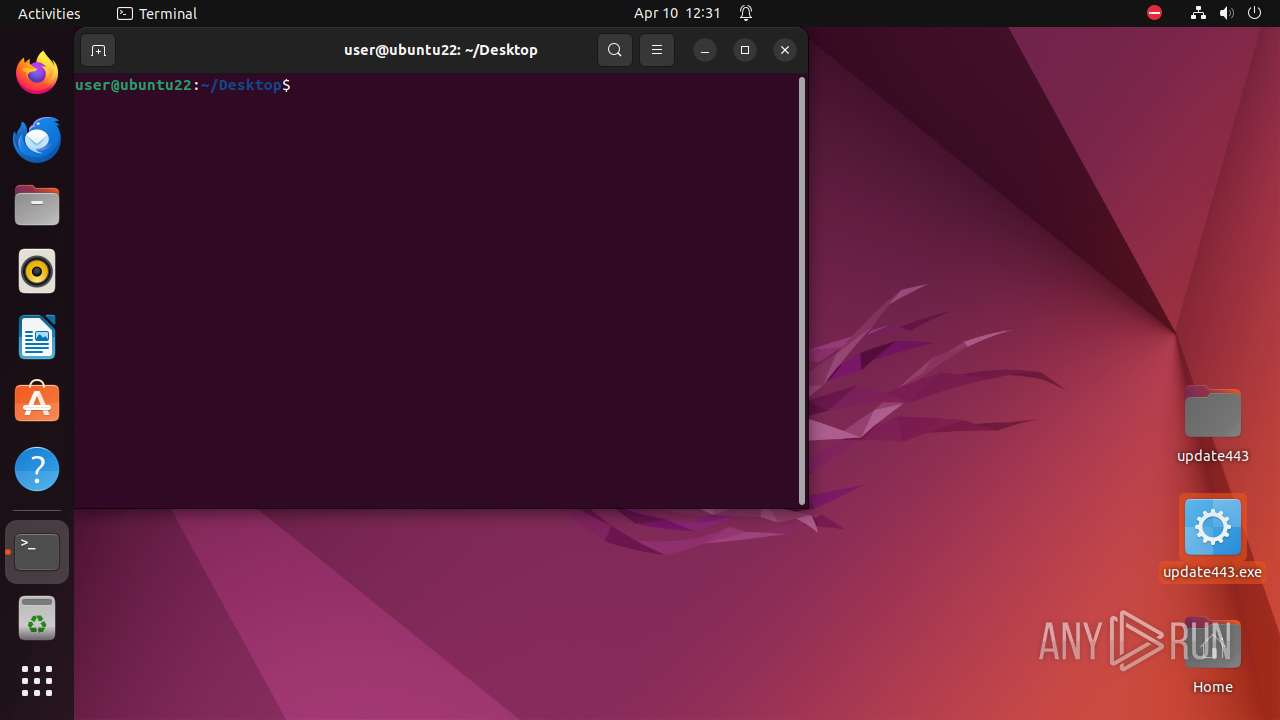
Executes commands using command-line interpreter
- cron (PID: 9374)
- gnome-terminal-server (PID: 9423)
Checks the user who created the process
- cron (PID: 9374)
Manipulating modules (likely to execute programs on system boot)
- modprobe (PID: 9450)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2010:04:14 22:06:53+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 1 |
| CodeSize: | 12288 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | - |
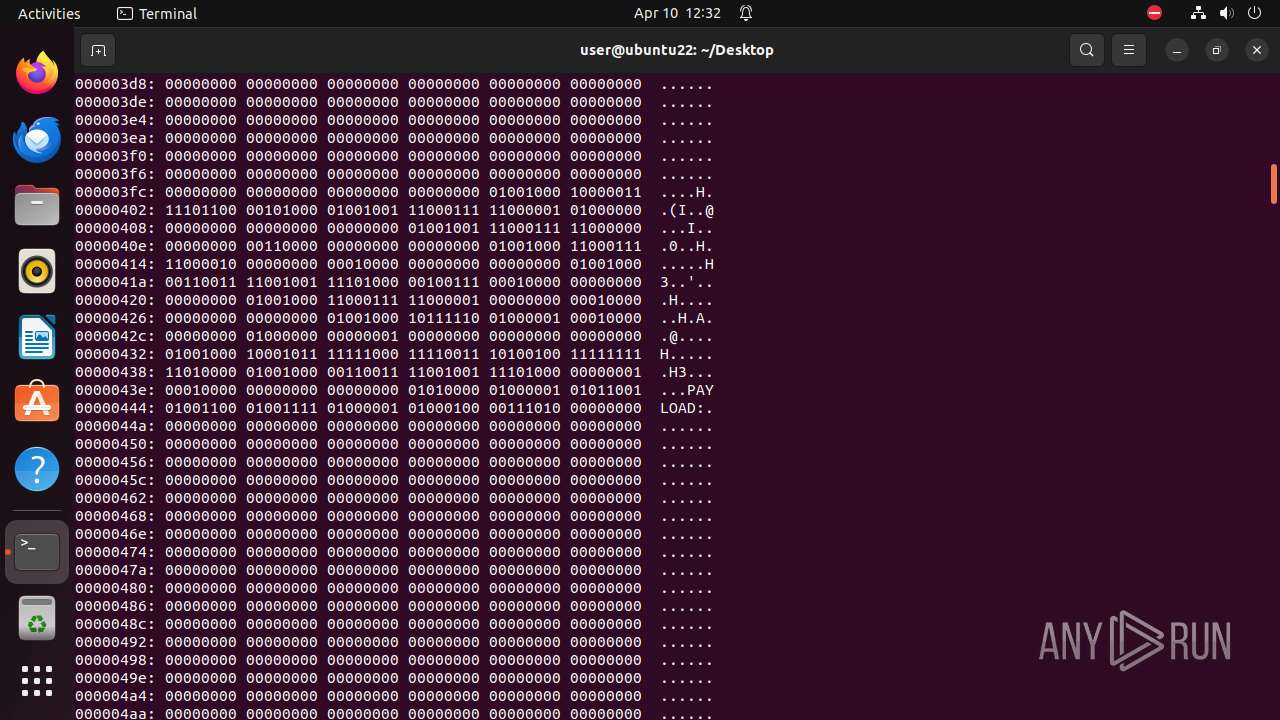
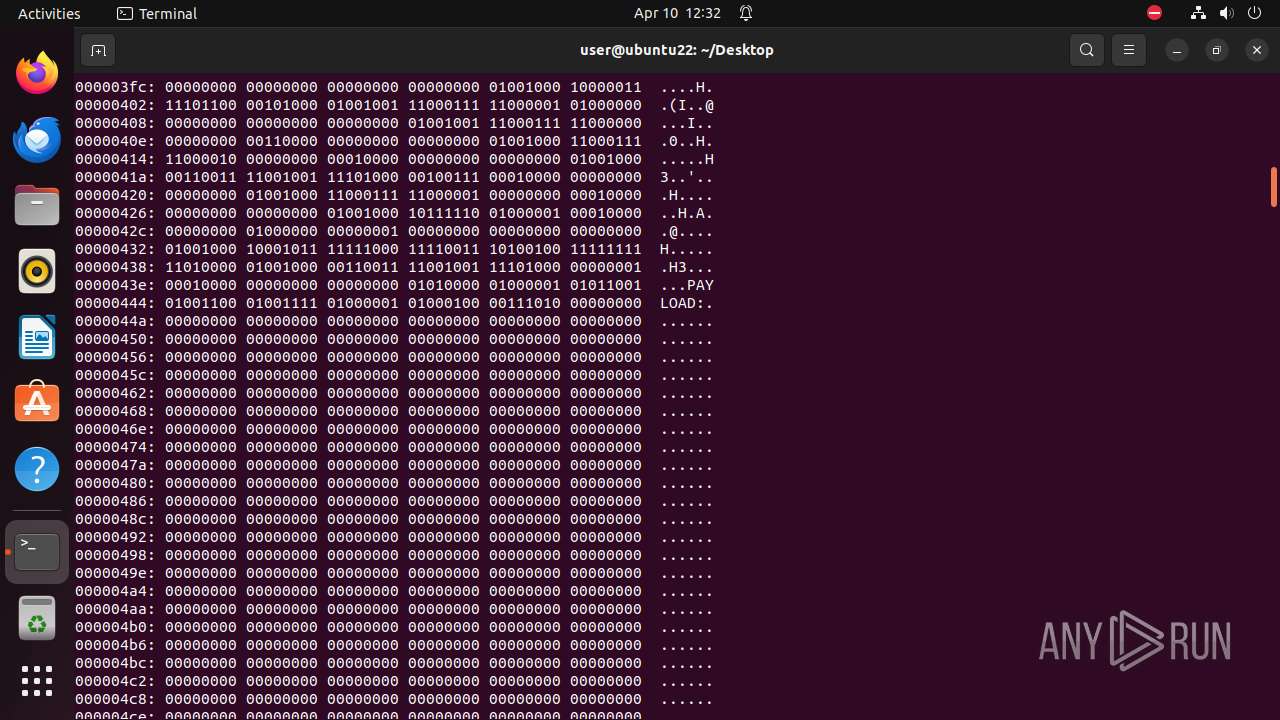
| EntryPoint: | 0x4000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
265
Monitored processes
42
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
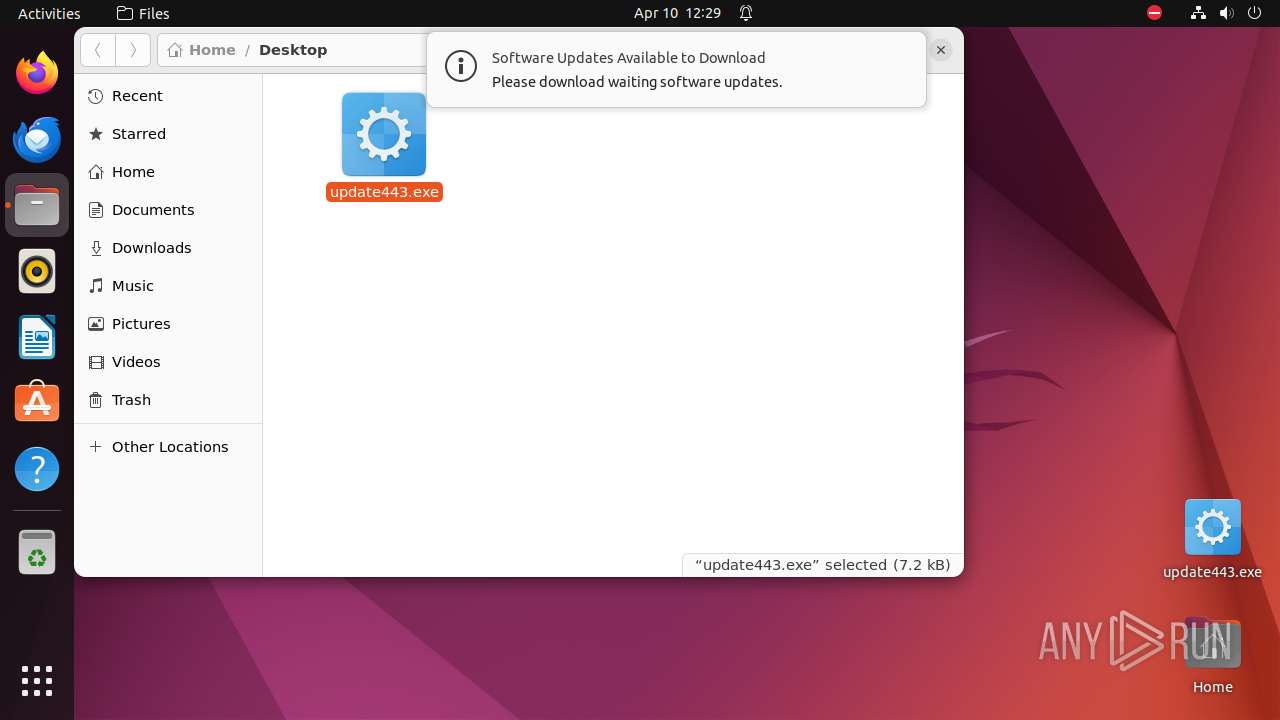
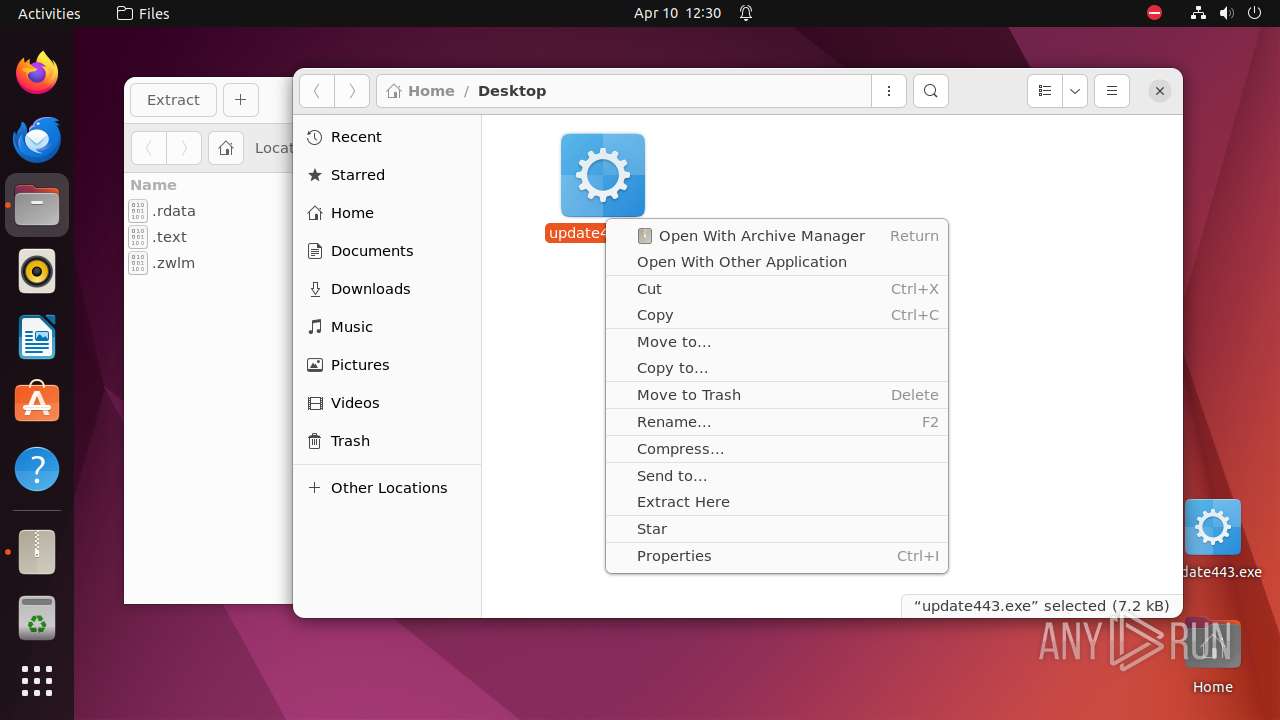
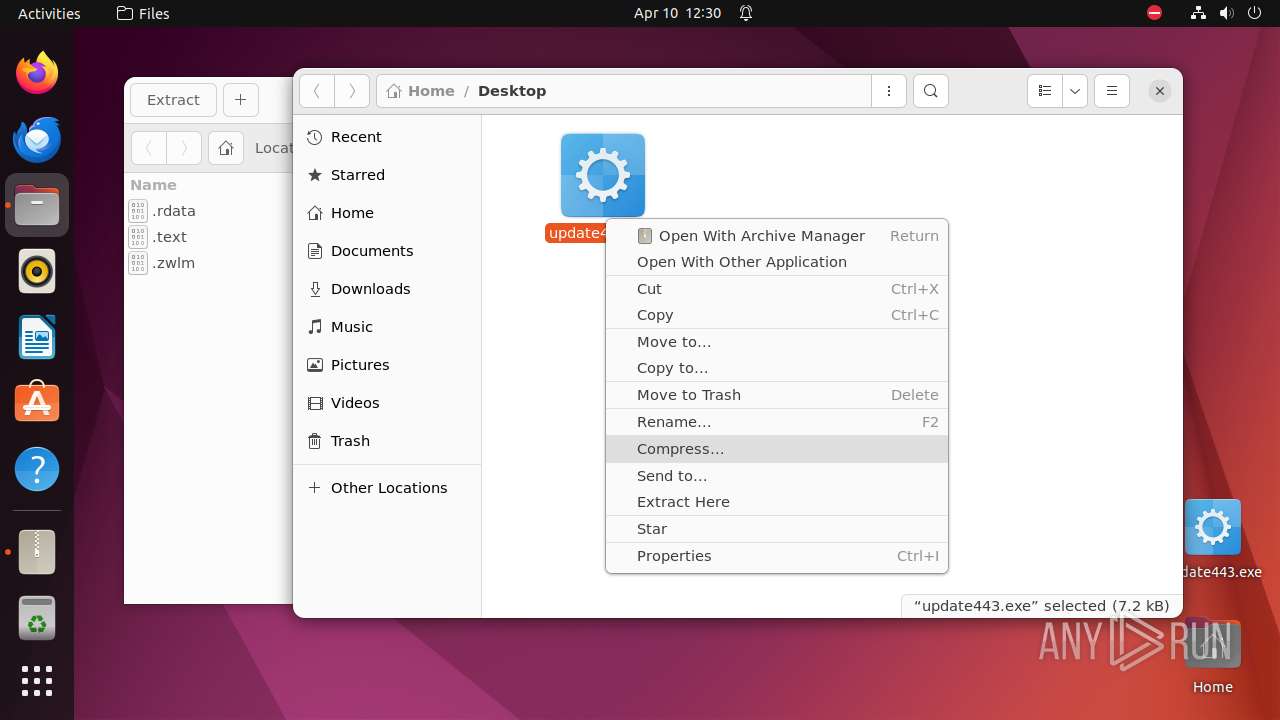
| 9284 | /bin/sh -c "DISPLAY=:0 sudo -iu user nautilus \"/home/user/Desktop/update443\.exe\" " | /bin/sh | — | any-guest-agent |
User: user Integrity Level: UNKNOWN Exit code: 9312 | ||||
| 9285 | sudo -iu user nautilus /home/user/Desktop/update443.exe | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN Exit code: 209 | ||||
| 9286 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
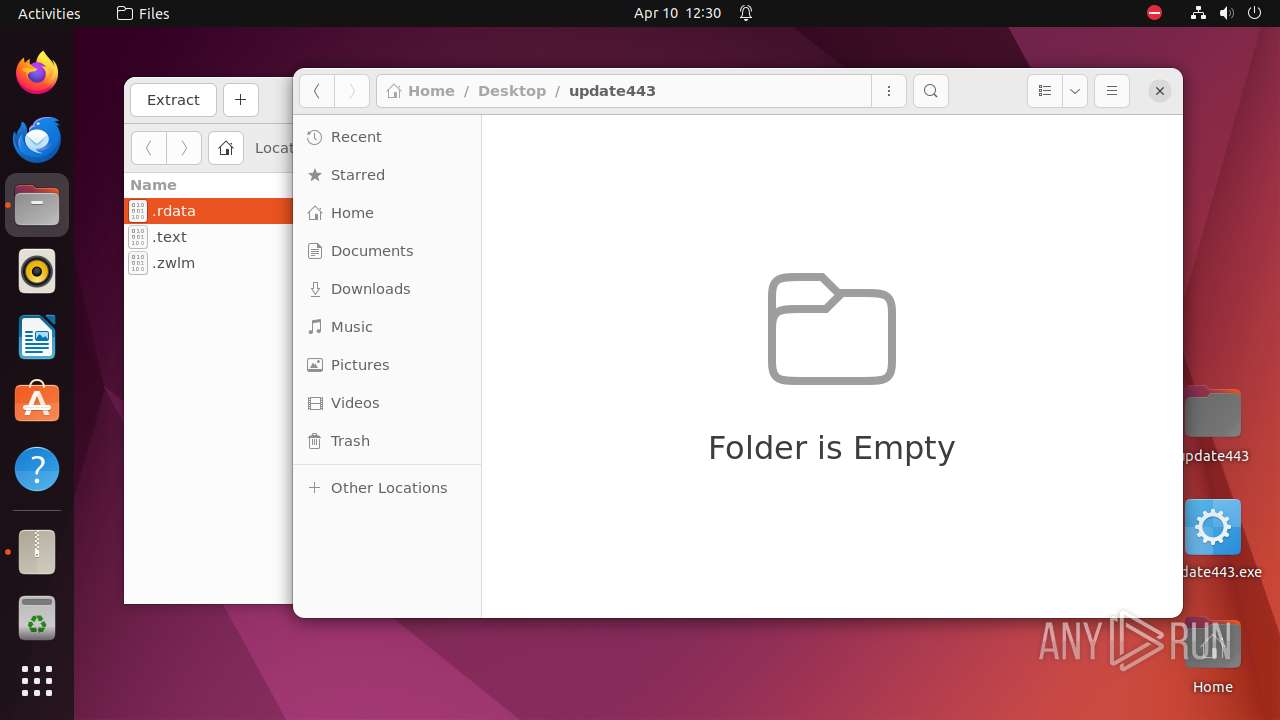
| 9287 | nautilus /home/user/Desktop/update443.exe | /usr/bin/nautilus | — | sudo |
User: user Integrity Level: UNKNOWN Exit code: 416 | ||||
| 9288 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | nautilus |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9305 | /lib/systemd/systemd-hostnamed | /lib/systemd/systemd-hostnamed | — | systemd |
User: root Integrity Level: UNKNOWN Exit code: 416 | ||||
| 9311 | nautilus /home/user/Desktop/update443.exe | /usr/bin/nautilus | — | nautilus |
User: user Integrity Level: UNKNOWN Exit code: 496 | ||||
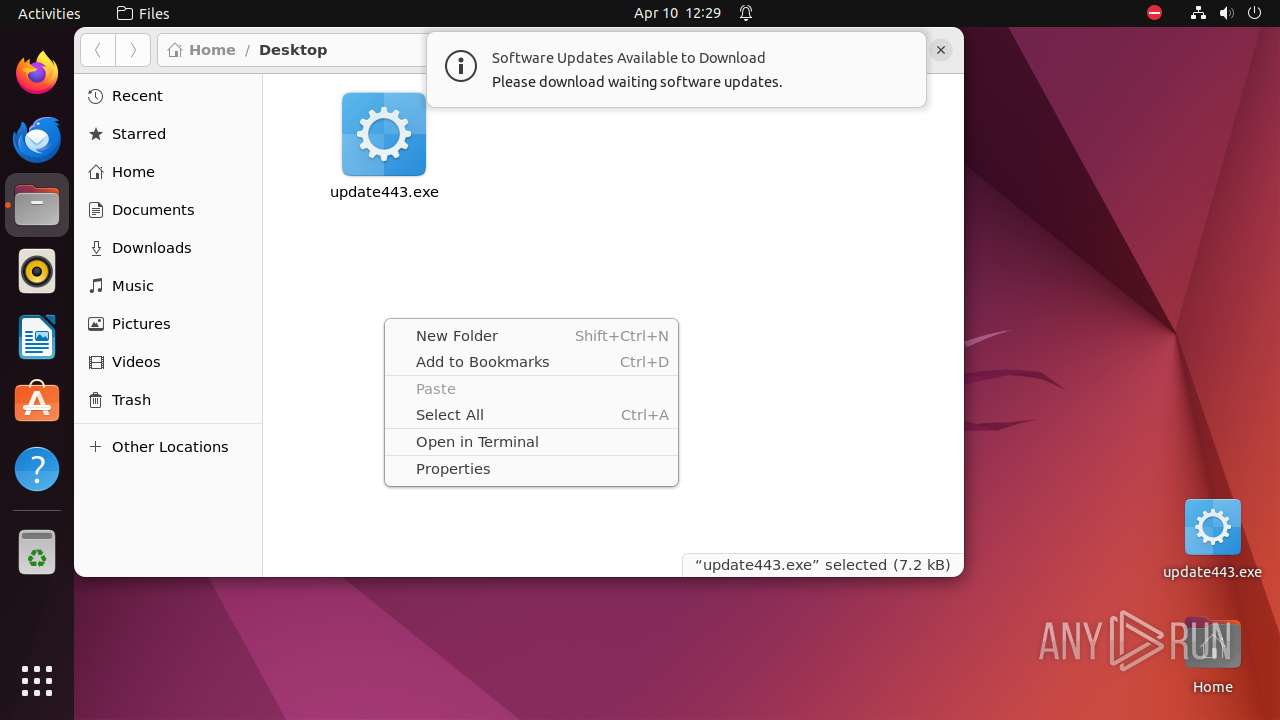
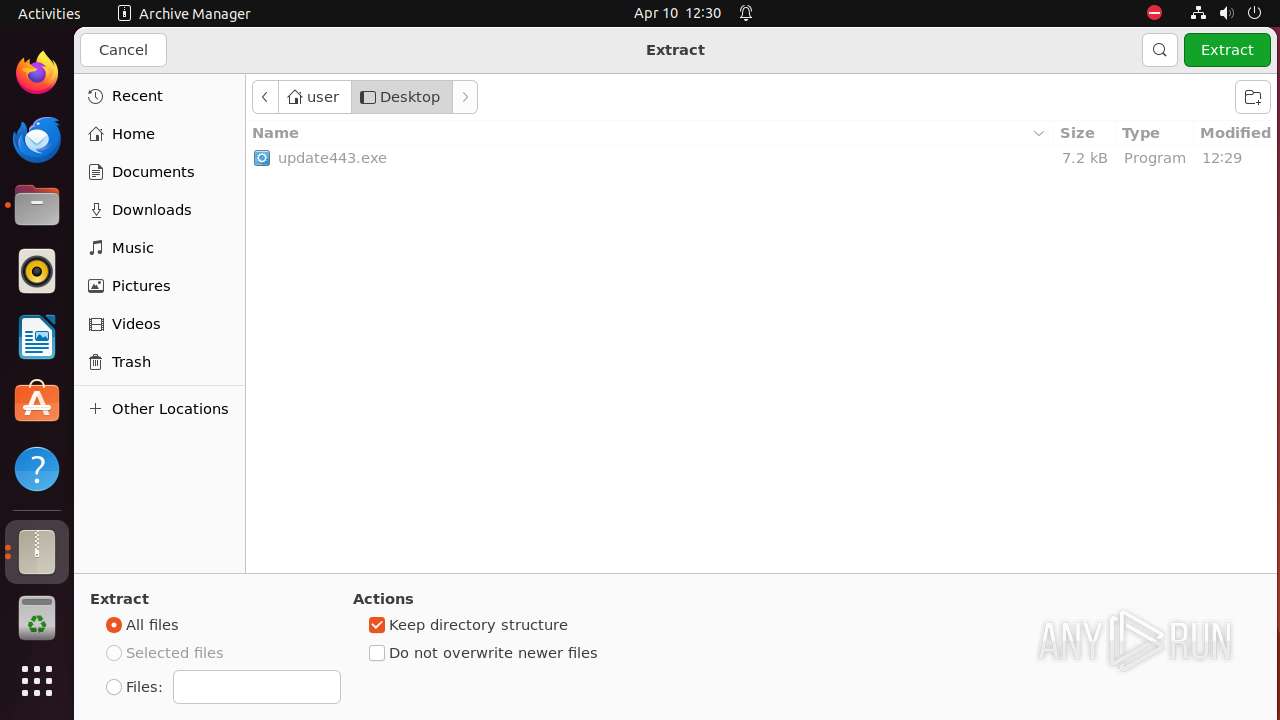
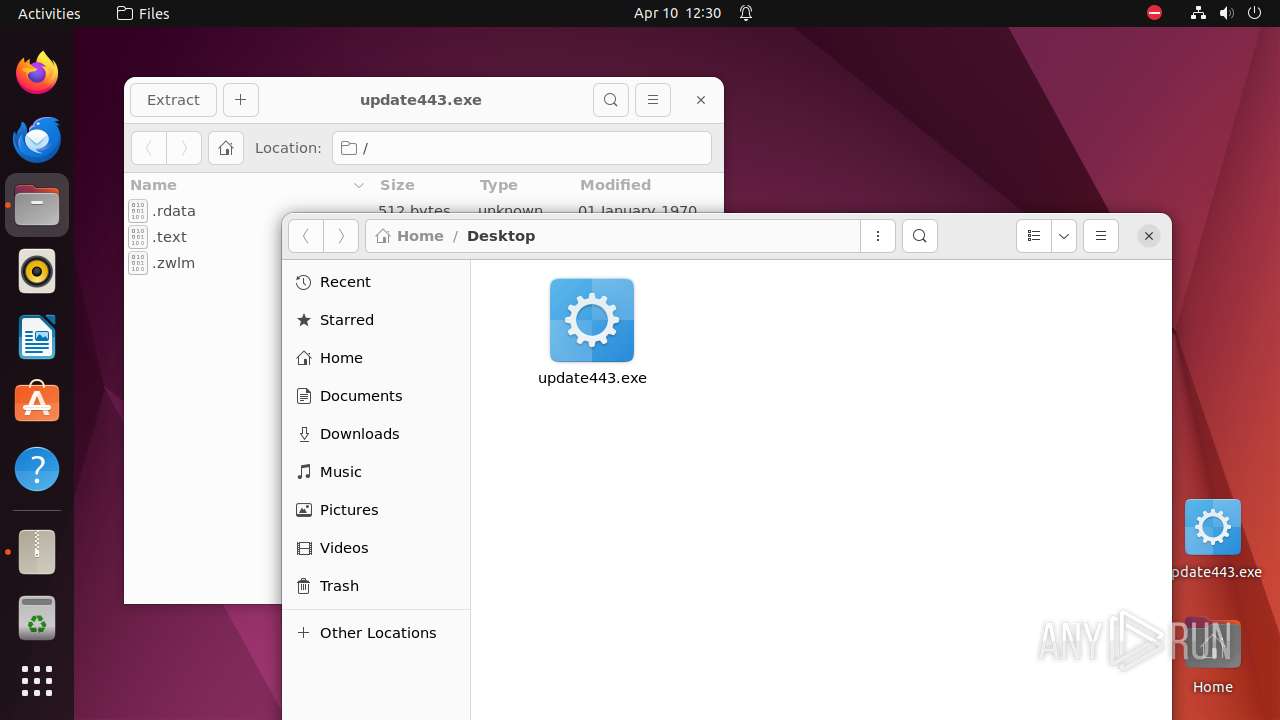
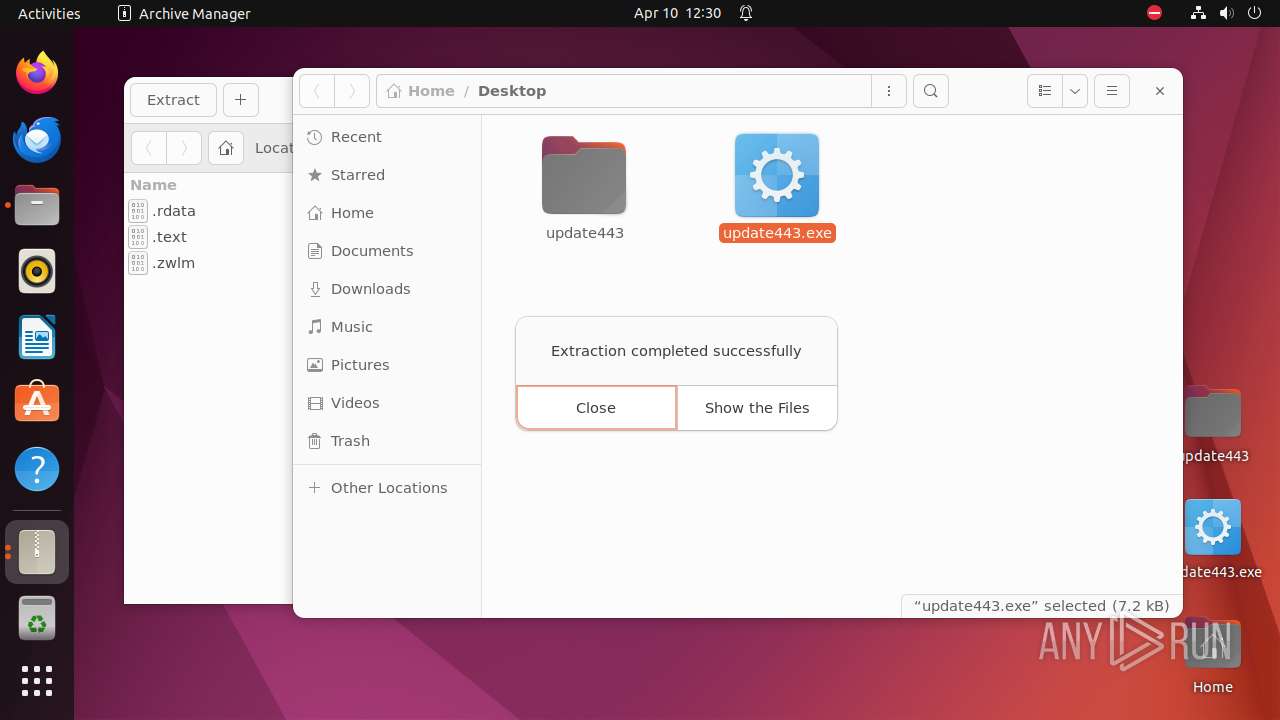
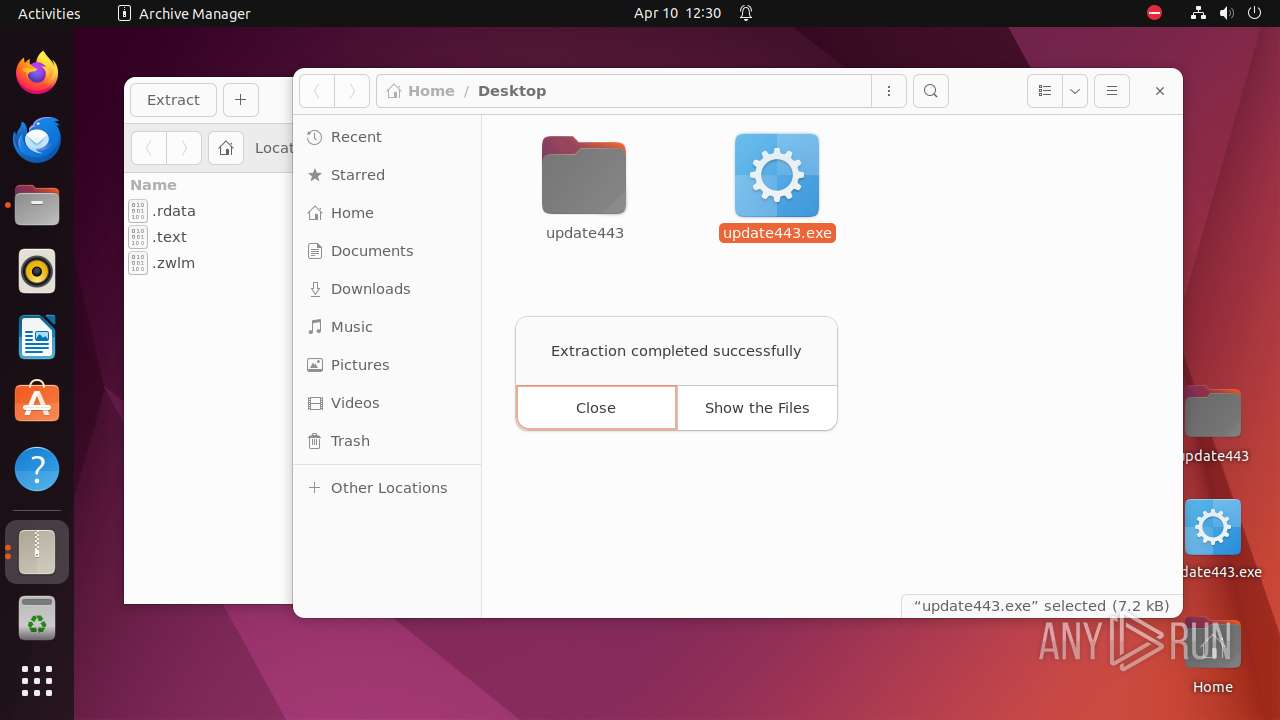
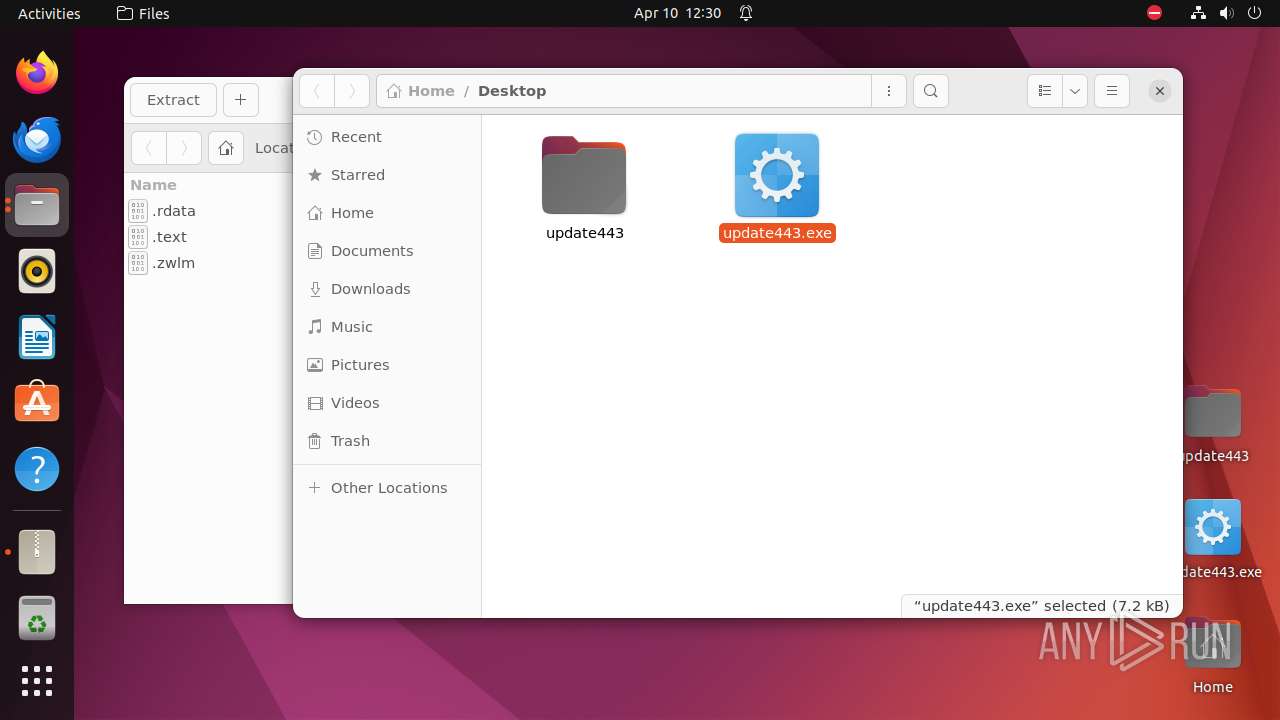
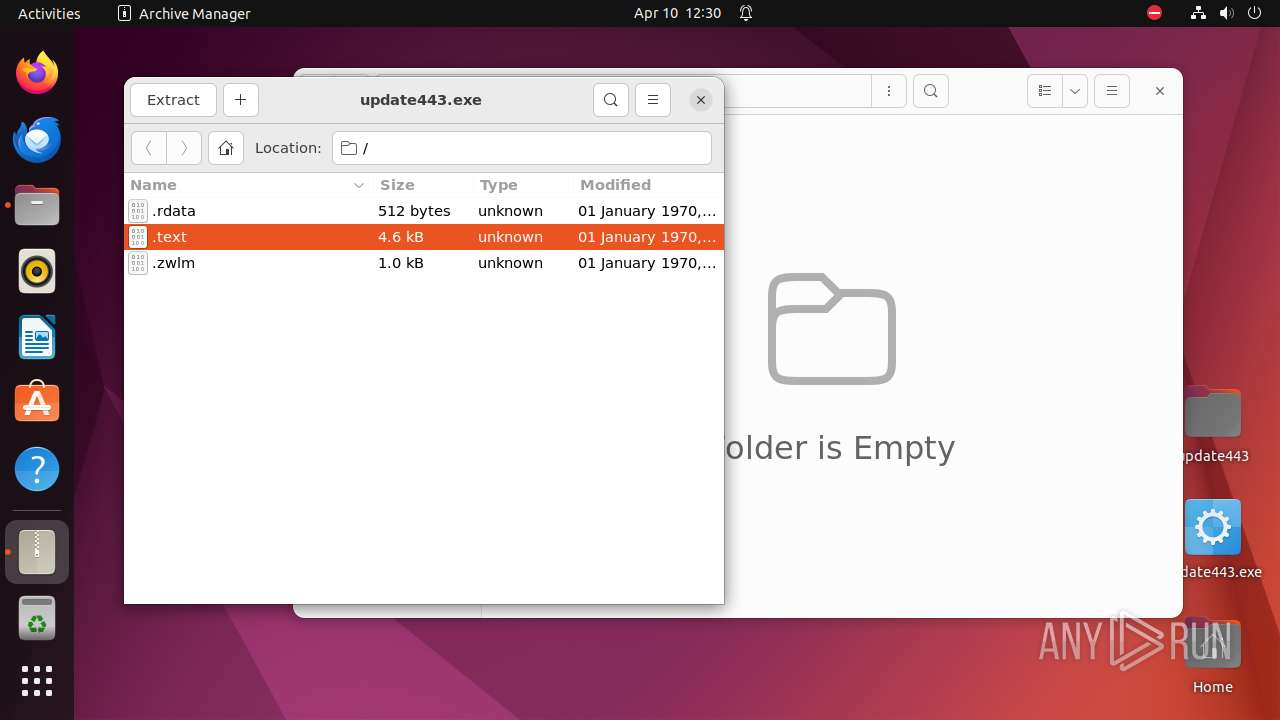
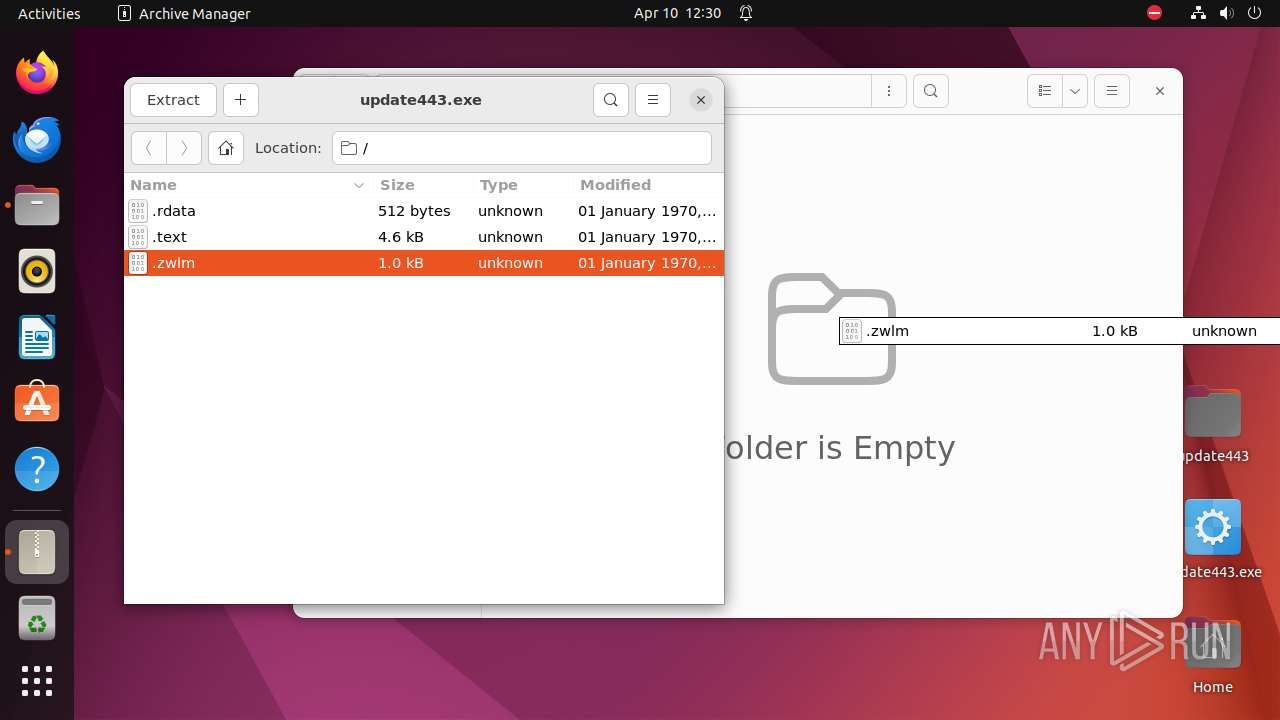
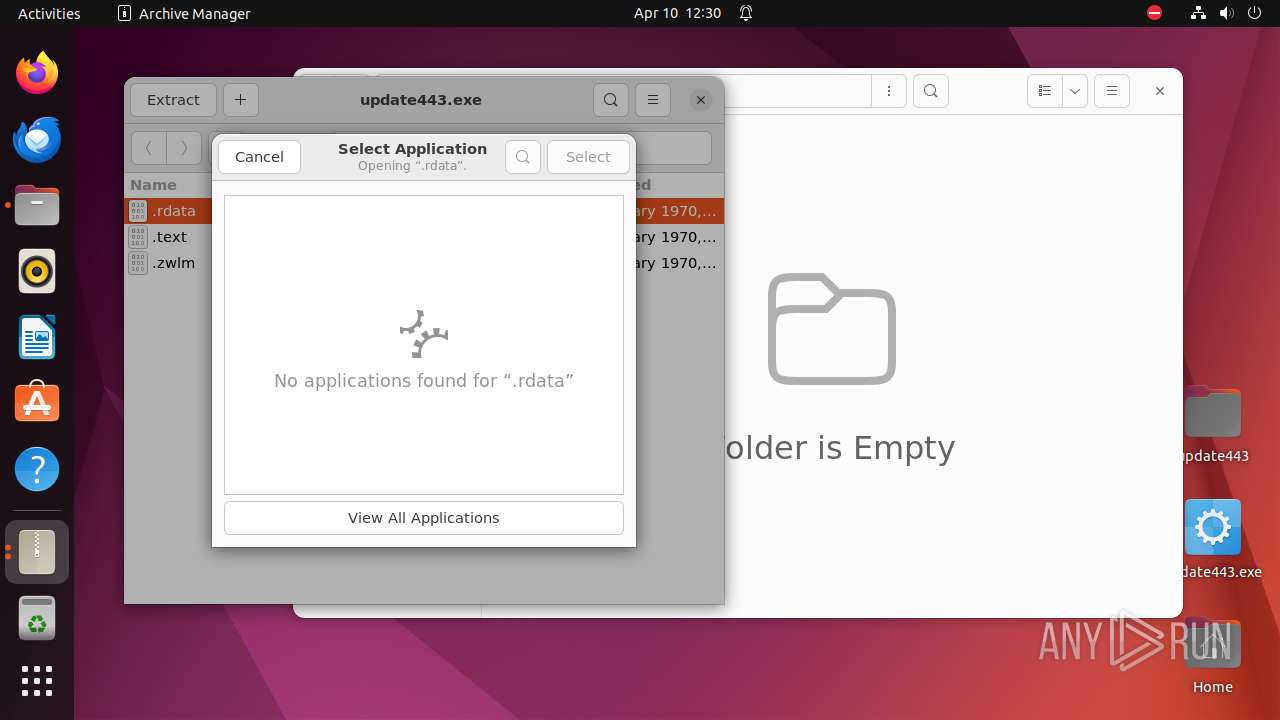
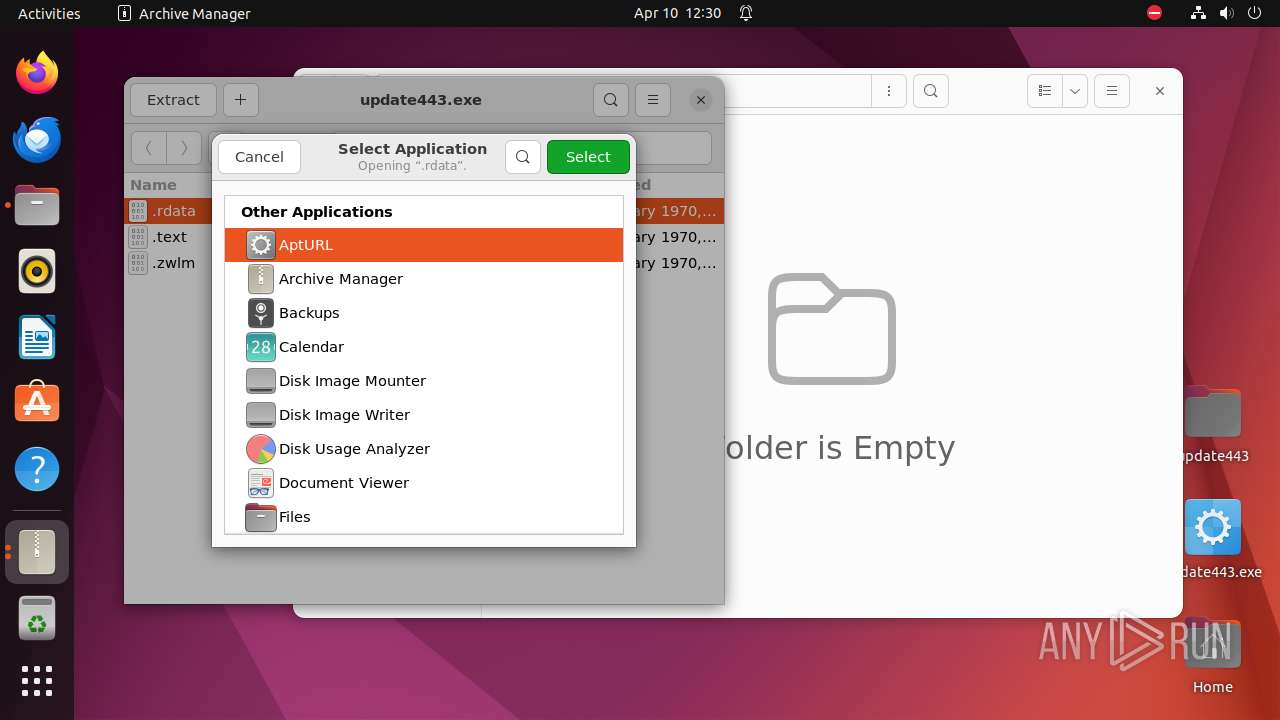
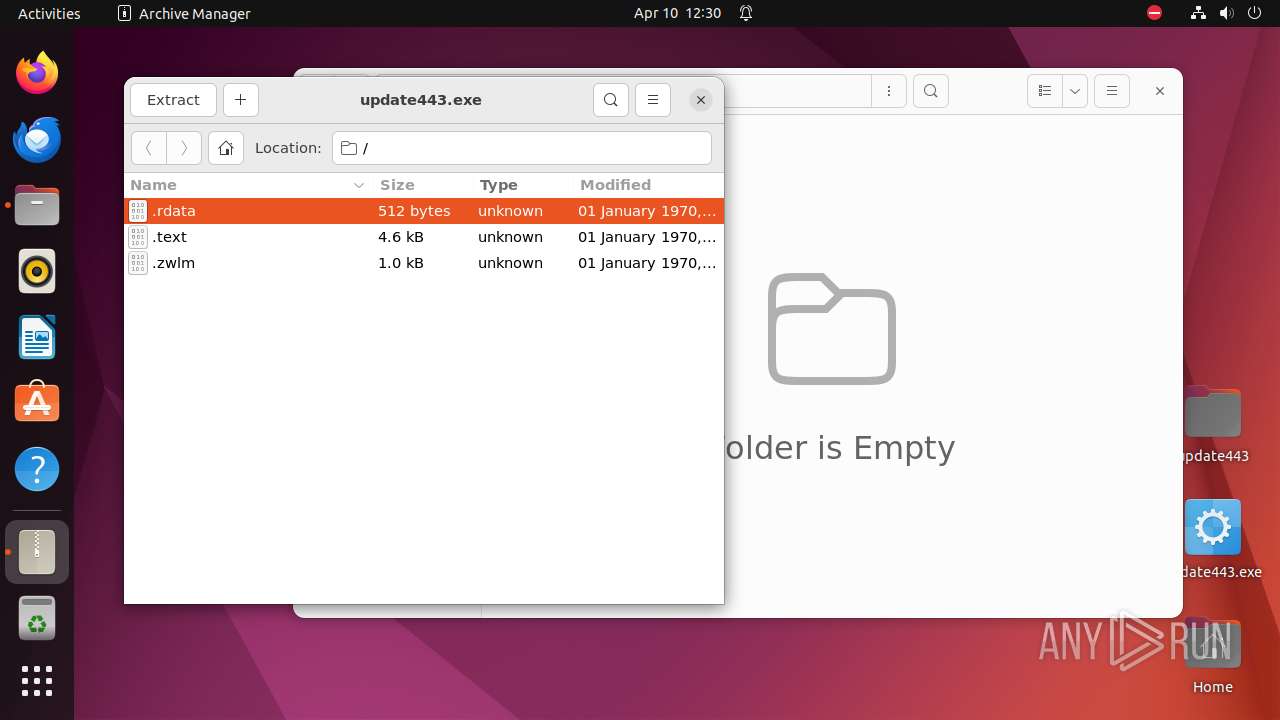
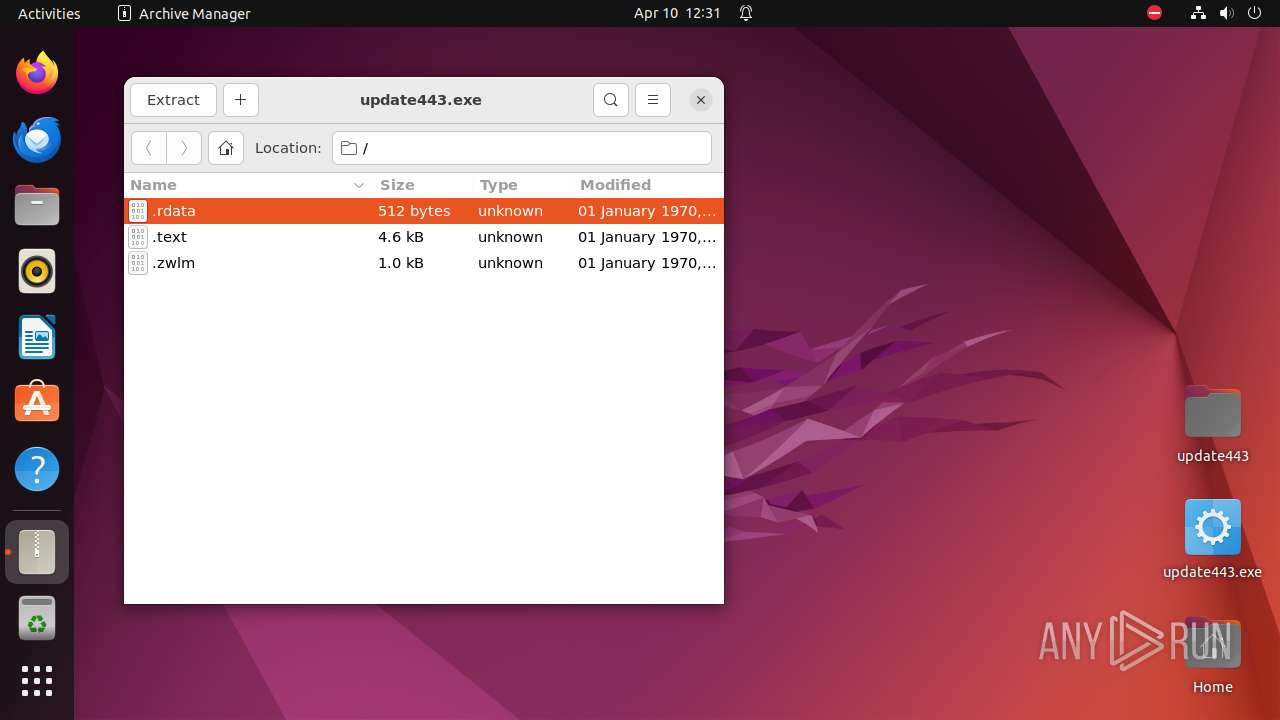
| 9312 | file-roller /home/user/Desktop/update443.exe | /usr/bin/file-roller | — | nautilus |
User: user Integrity Level: UNKNOWN Exit code: 9287 | ||||
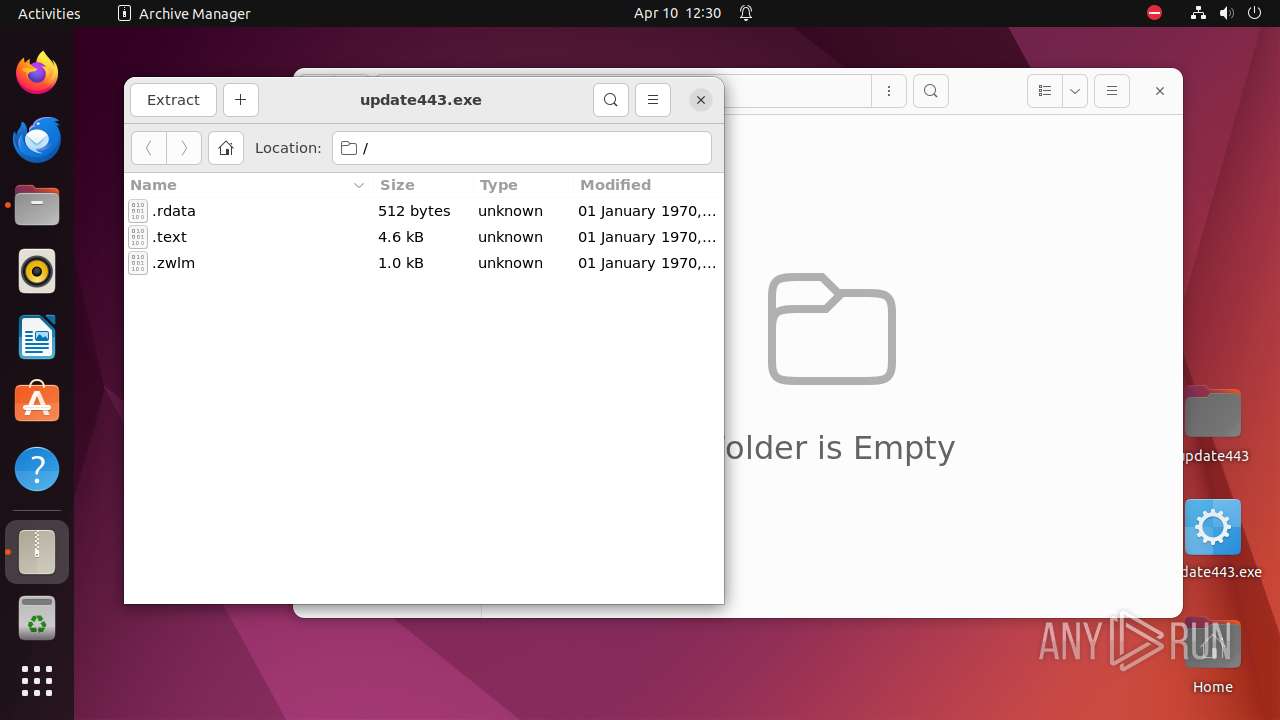
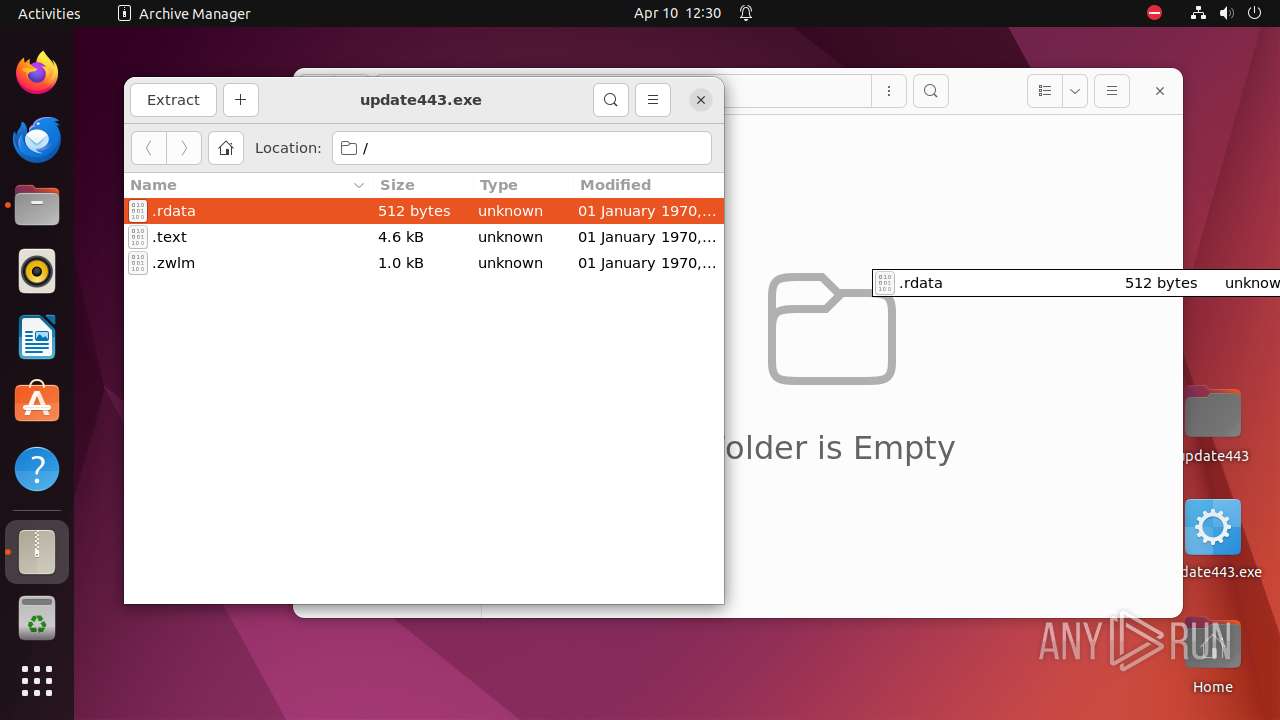
| 9327 | /usr/lib/p7zip/7z l -slt -bd -y -- /home/user/Desktop/update443.exe | /usr/lib/p7zip/7z | — | file-roller |
User: user Integrity Level: UNKNOWN Exit code: 496 | ||||
| 9338 | /usr/lib/p7zip/7z x -bd -bb1 -y -o/home/user/Desktop -- /home/user/Desktop/update443.exe | /usr/lib/p7zip/7z | — | file-roller |
User: user Integrity Level: UNKNOWN Exit code: 9287 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 9287 | nautilus | /home/user/.local/share/nautilus/tags/meta.db-wal | — | |
MD5:— | SHA256:— | |||
| 9287 | nautilus | /home/user/.local/share/nautilus/tags/meta.db-shm | — | |
MD5:— | SHA256:— | |||
| 9287 | nautilus | /home/user/.local/share/nautilus/tags/.meta.isrunning | — | |
MD5:— | SHA256:— | |||
| 9287 | nautilus | /home/user/.local/share/recently-used.xbel.JD6ZL2 | — | |
MD5:— | SHA256:— | |||
| 9312 | file-roller | /dconf/user | — | |
MD5:— | SHA256:— | |||
| 9312 | file-roller | /home/user/.local/share/recently-used.xbel.XBTVL2 | — | |
MD5:— | SHA256:— | |||
| 9287 | nautilus | /dconf/user | — | |
MD5:— | SHA256:— | |||
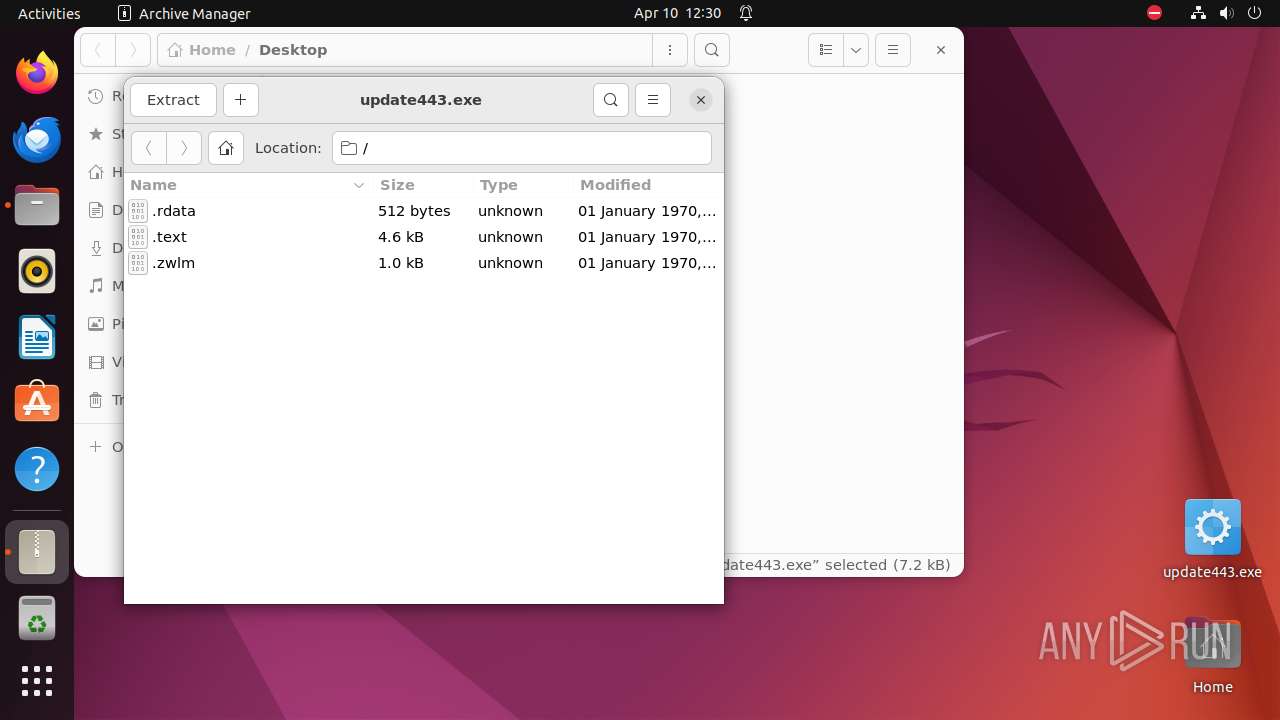
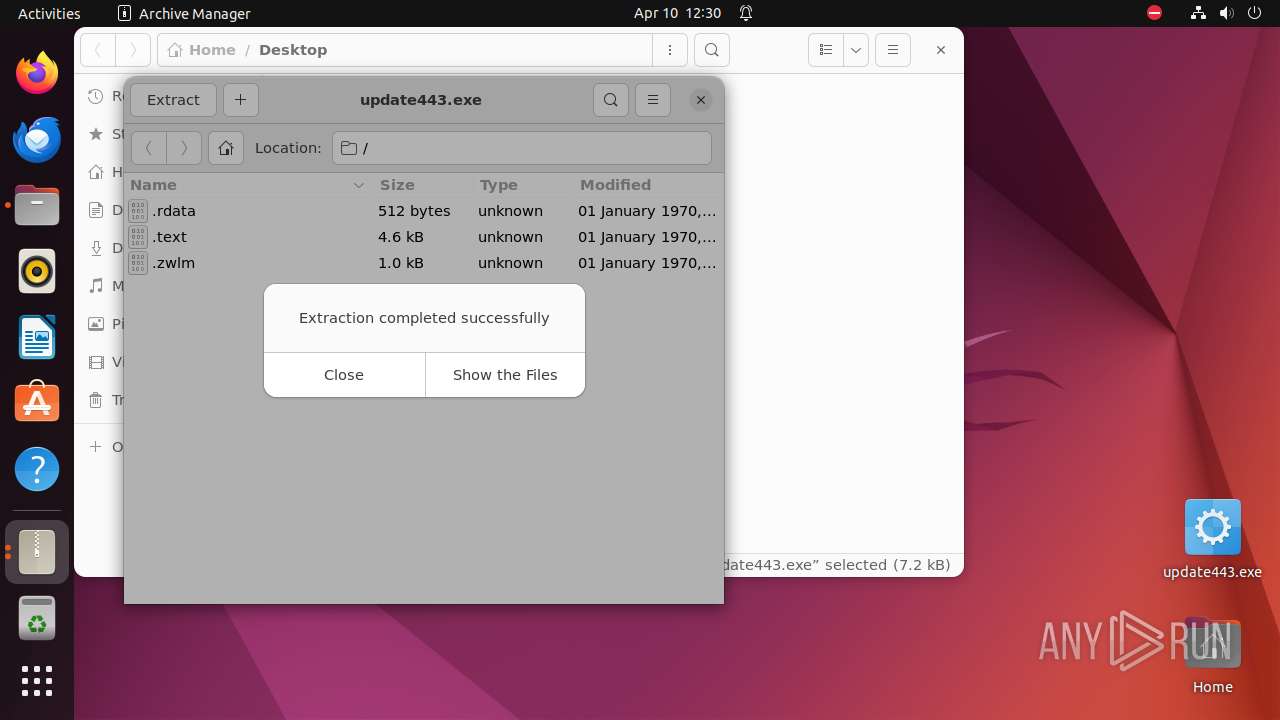
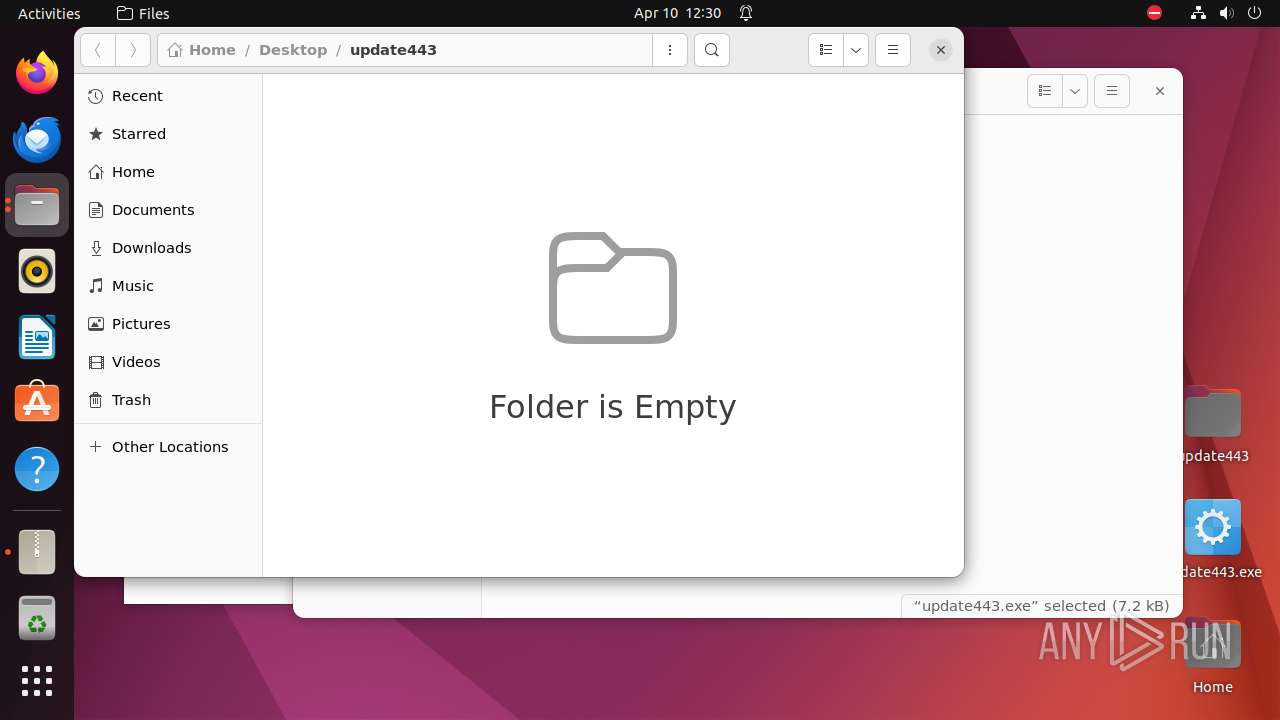
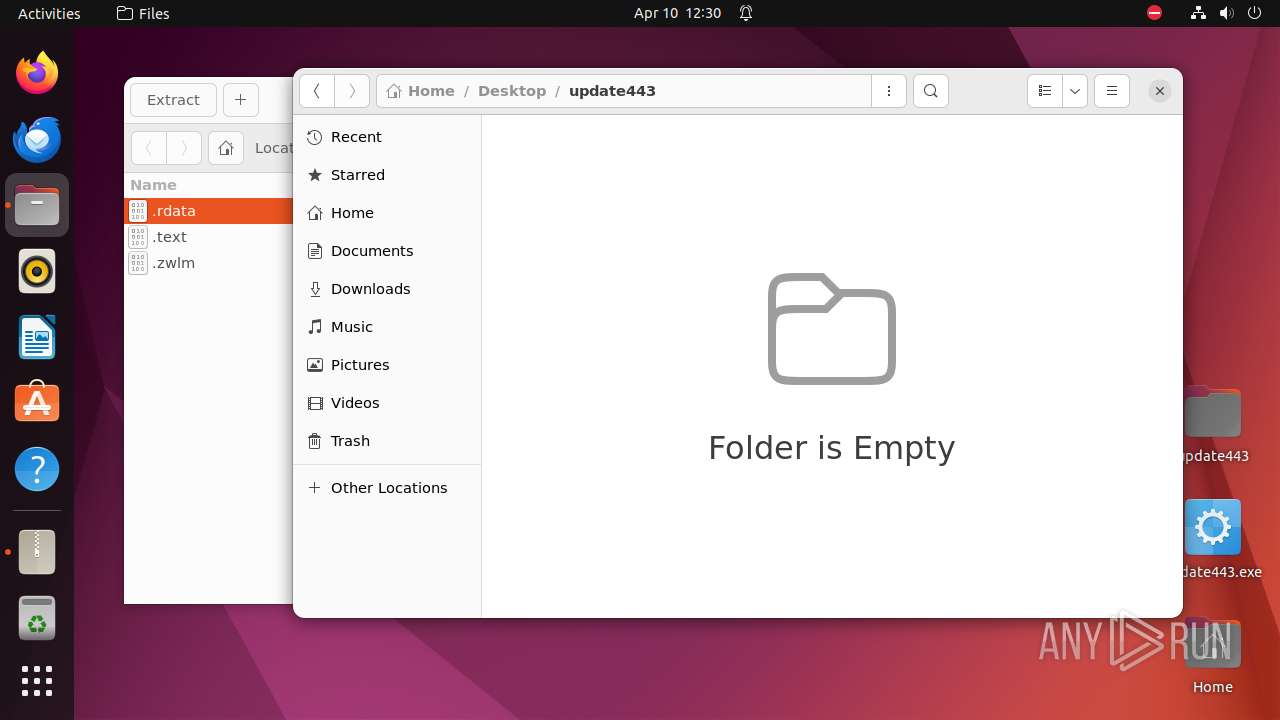
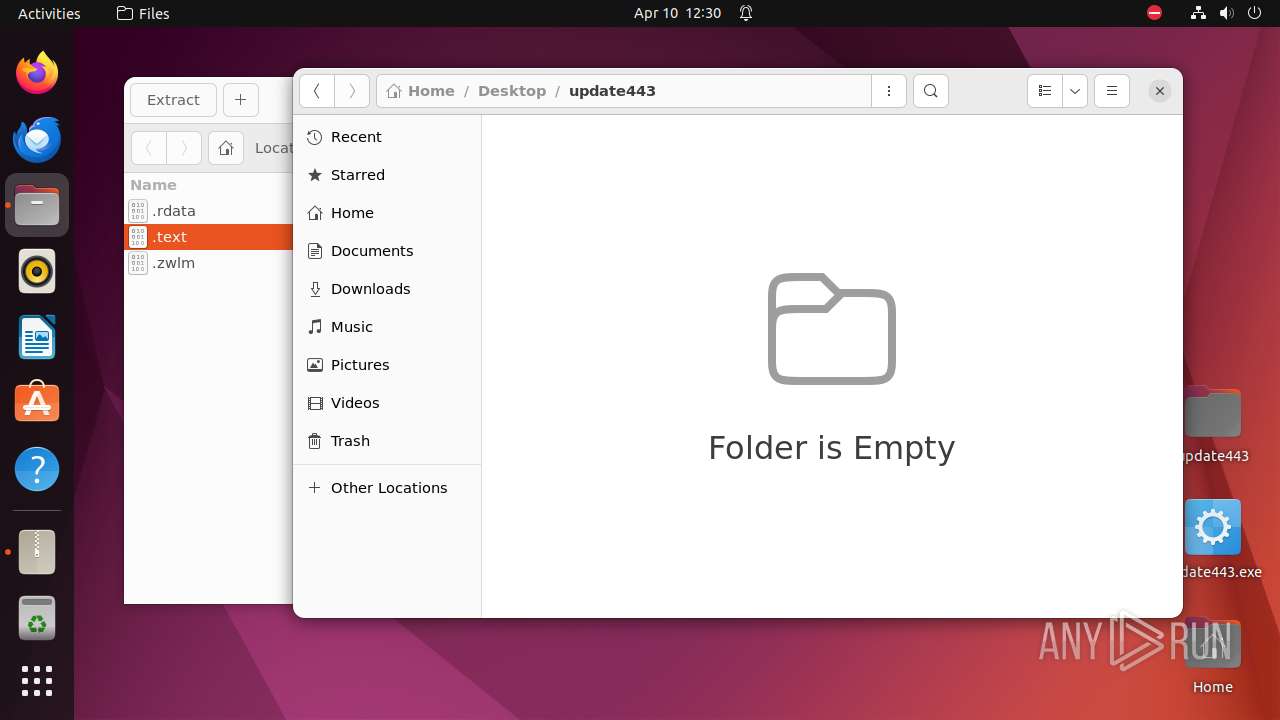
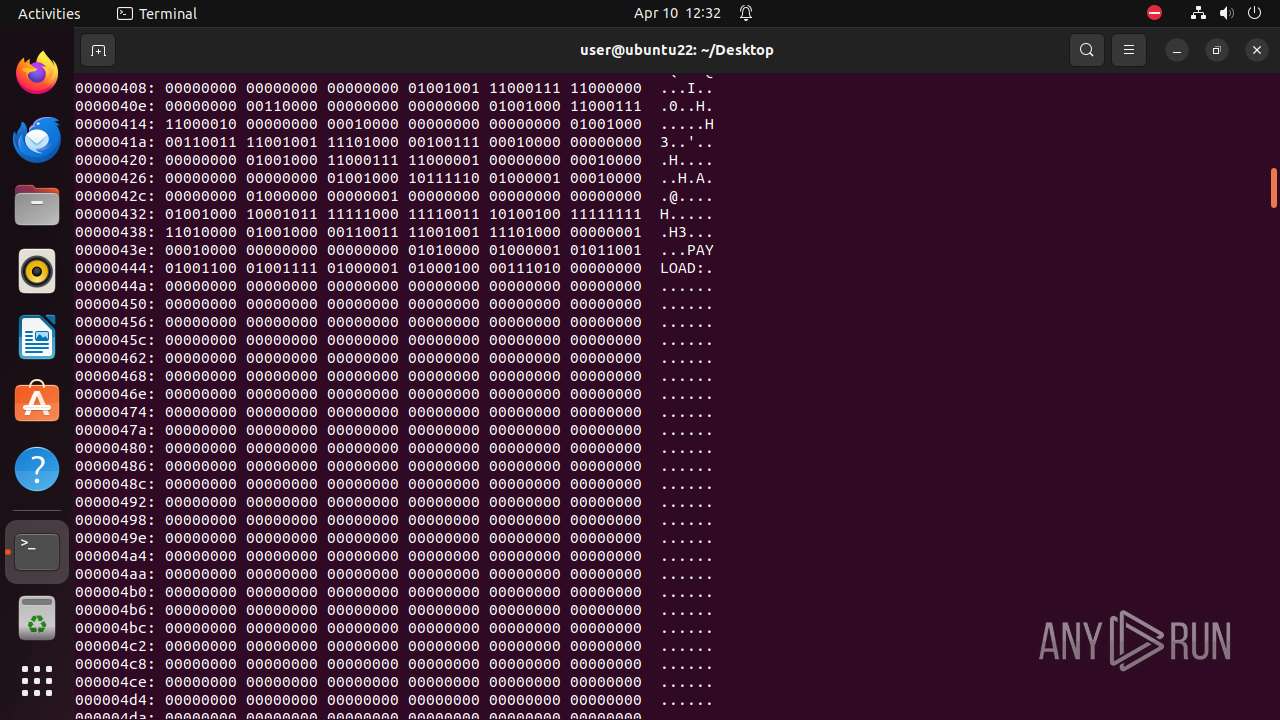
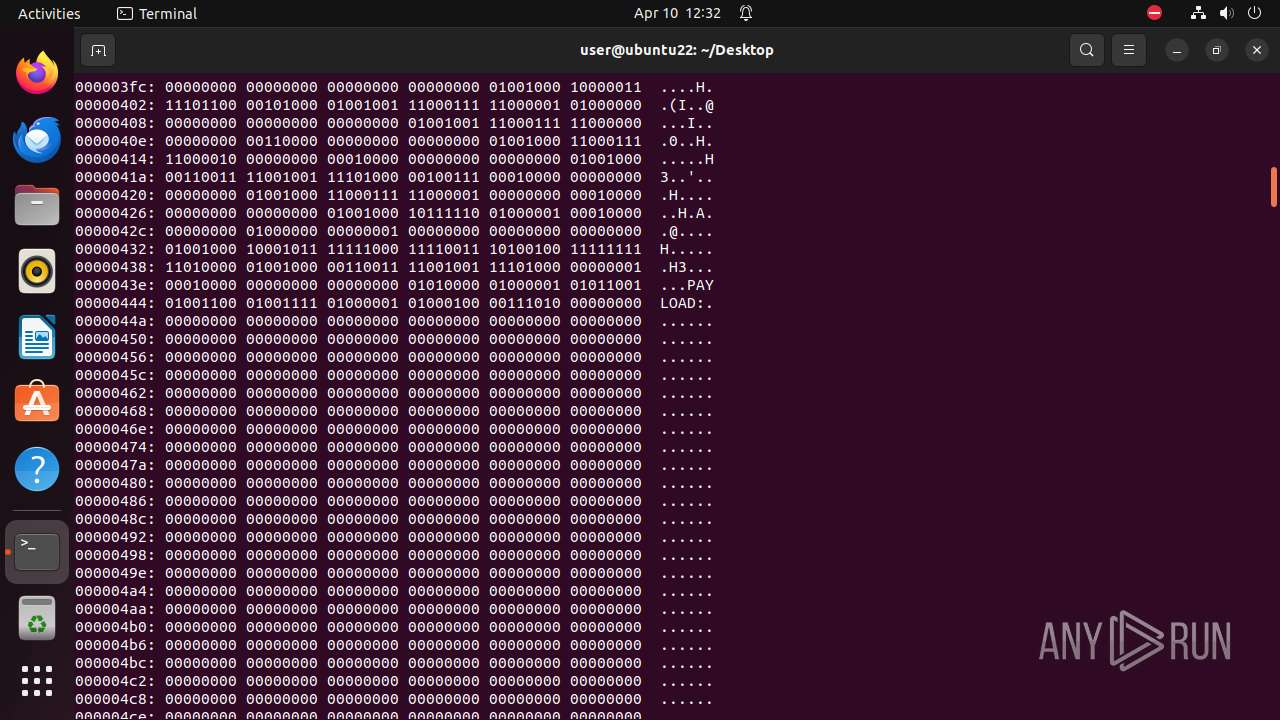
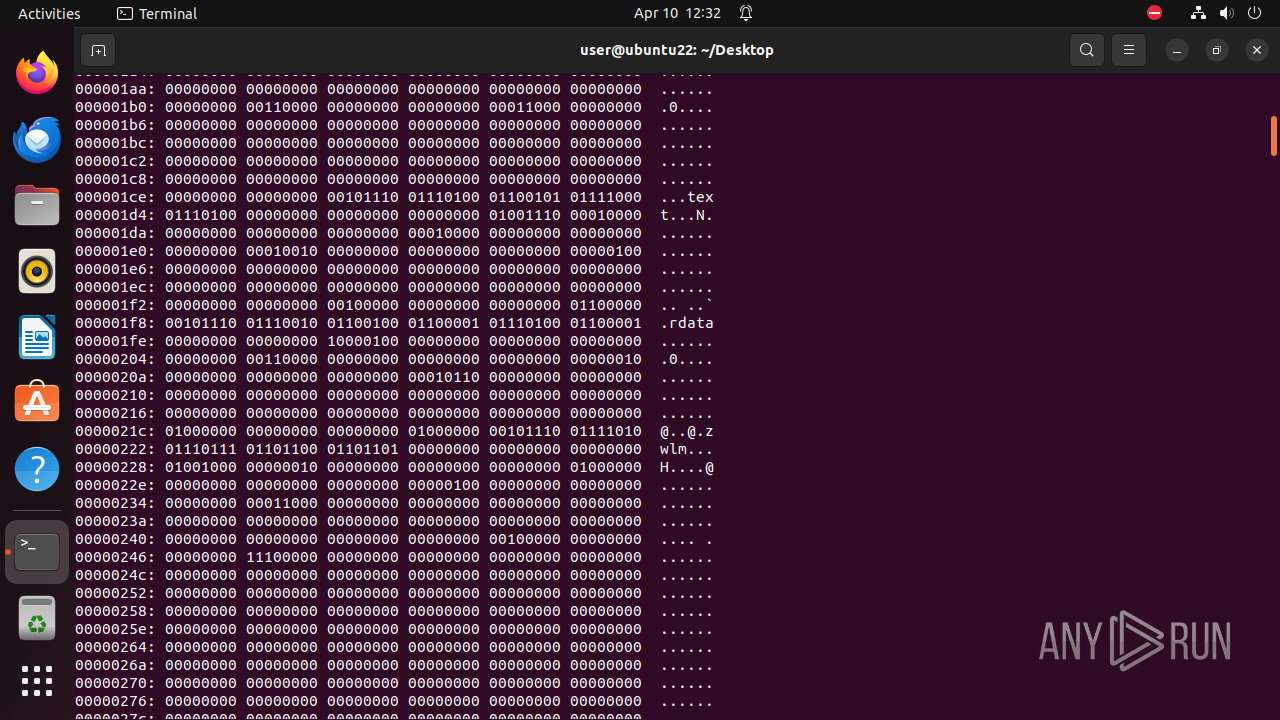
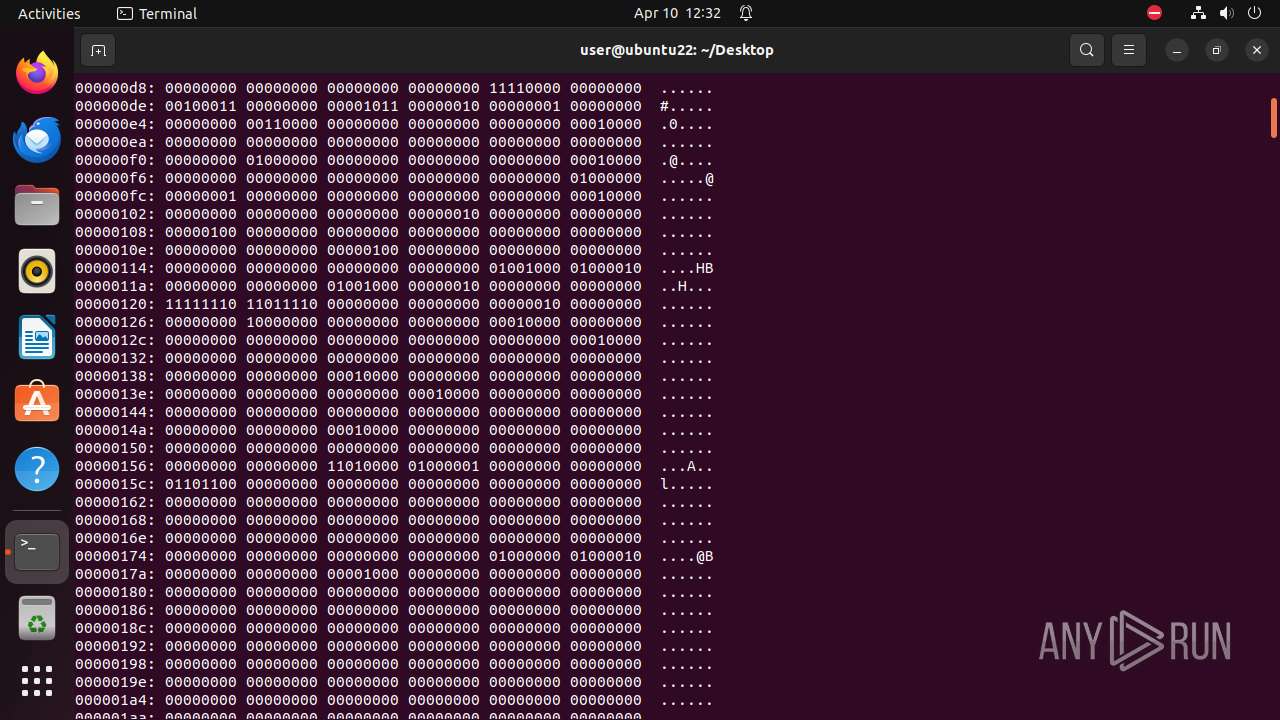
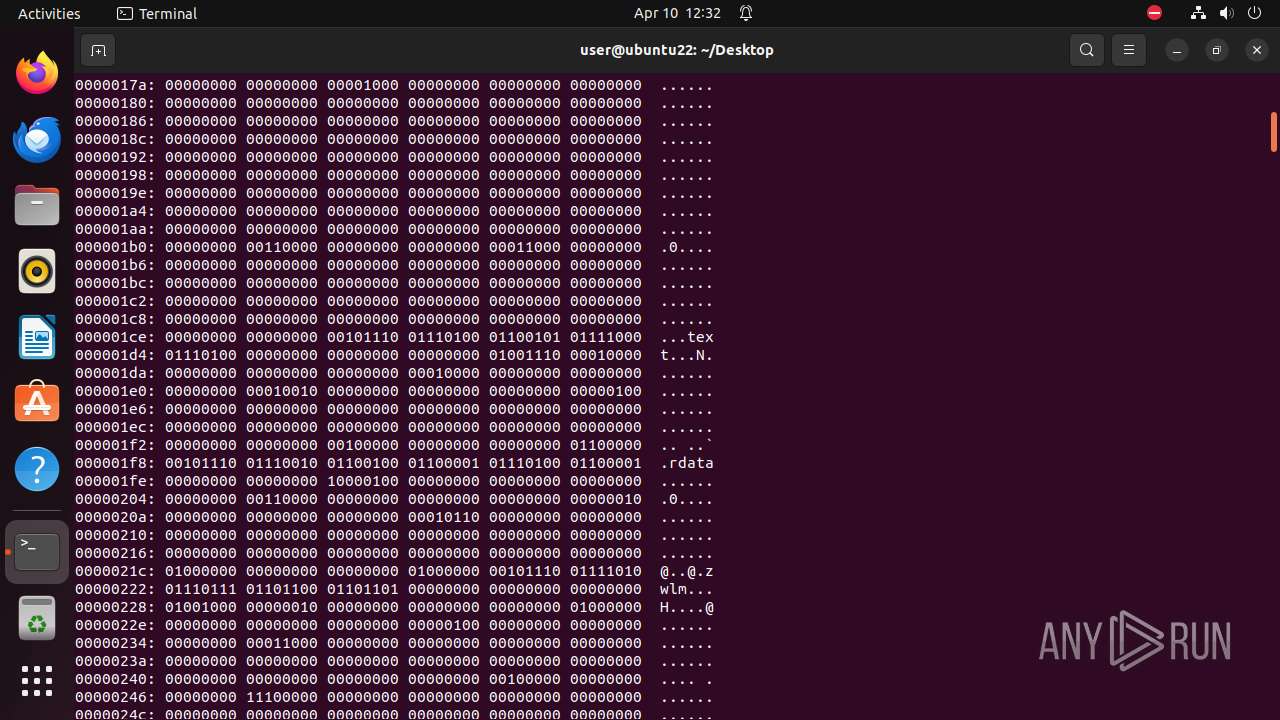
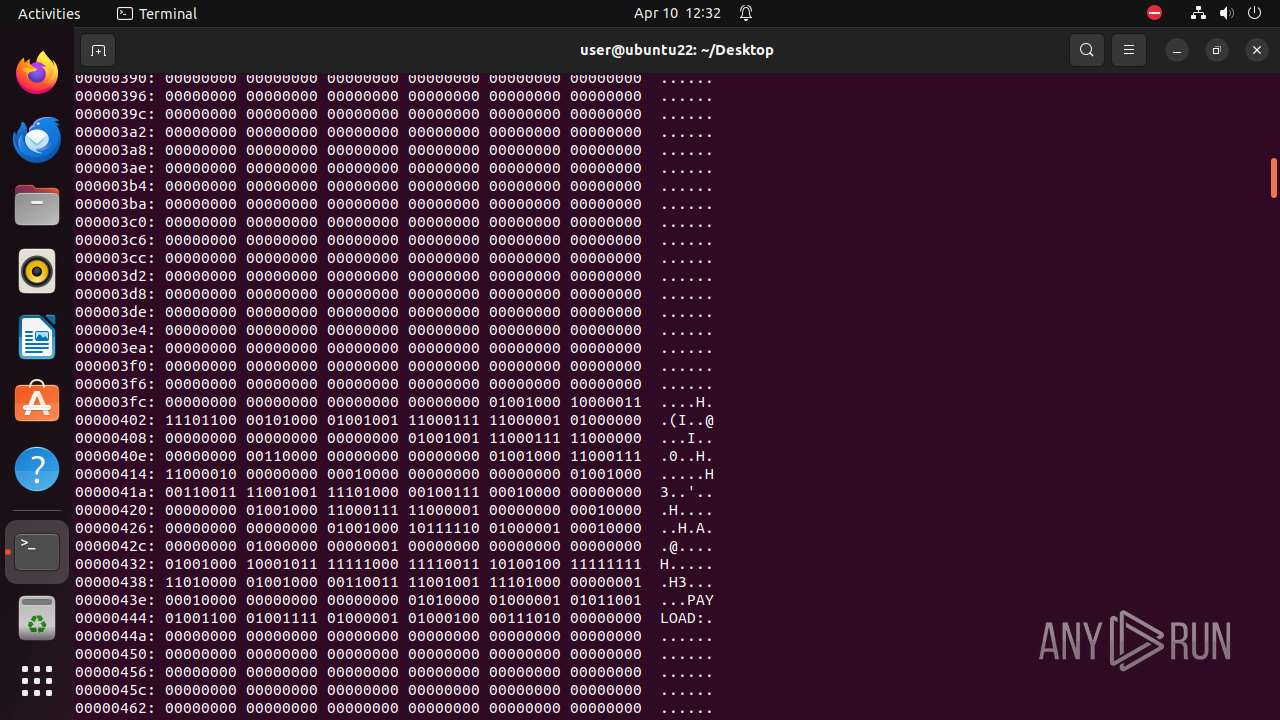
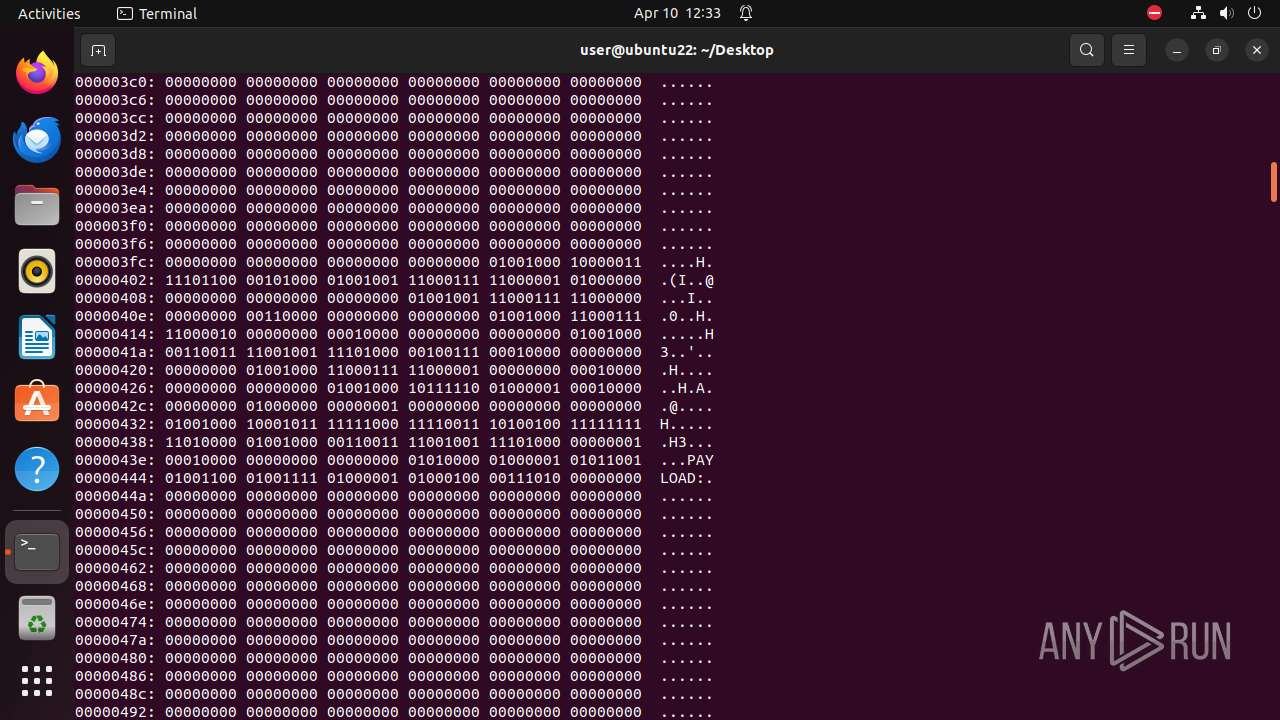
| 9338 | 7z | /home/user/Desktop/.text | — | |
MD5:— | SHA256:— | |||
| 9338 | 7z | /home/user/Desktop/.rdata | — | |
MD5:— | SHA256:— | |||
| 9338 | 7z | /home/user/Desktop/.zwlm | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
5
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.98:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
— | — | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
— | — | 224.0.0.251:5353 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.snapcraft.io |
| unknown |
163.100.168.192.in-addr.arpa |
| unknown |
connectivity-check.ubuntu.com |
| unknown |