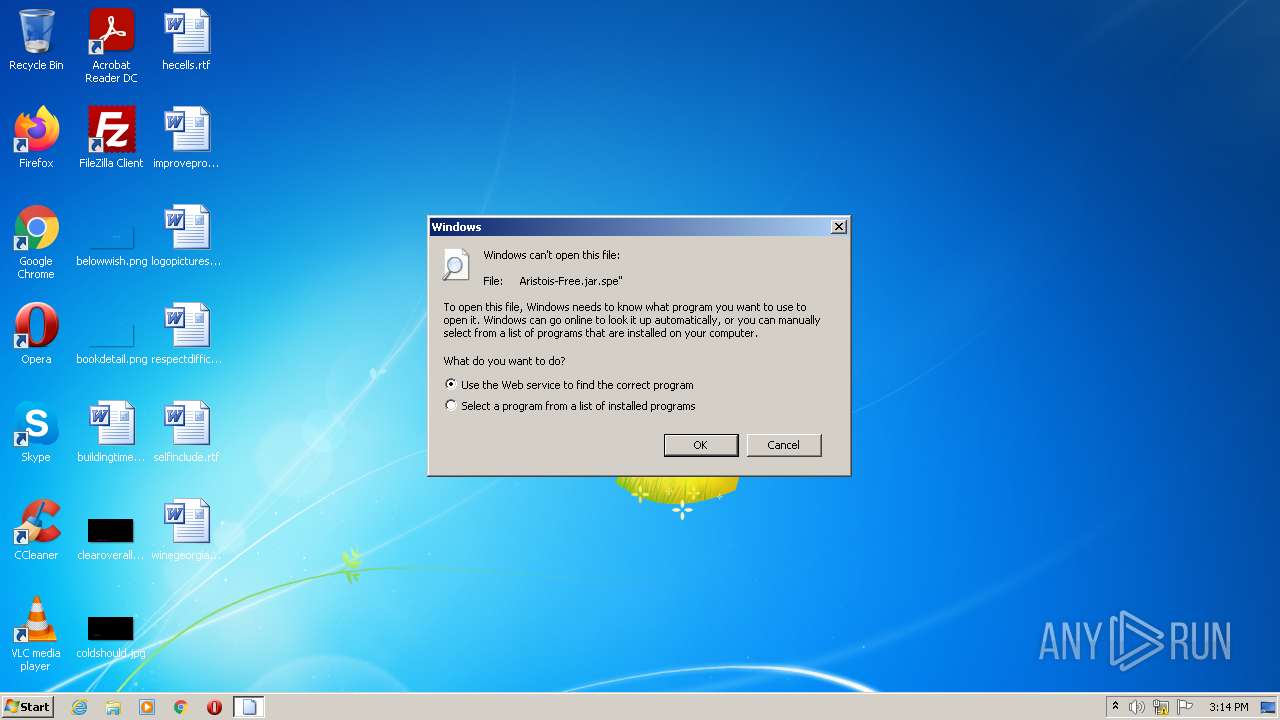
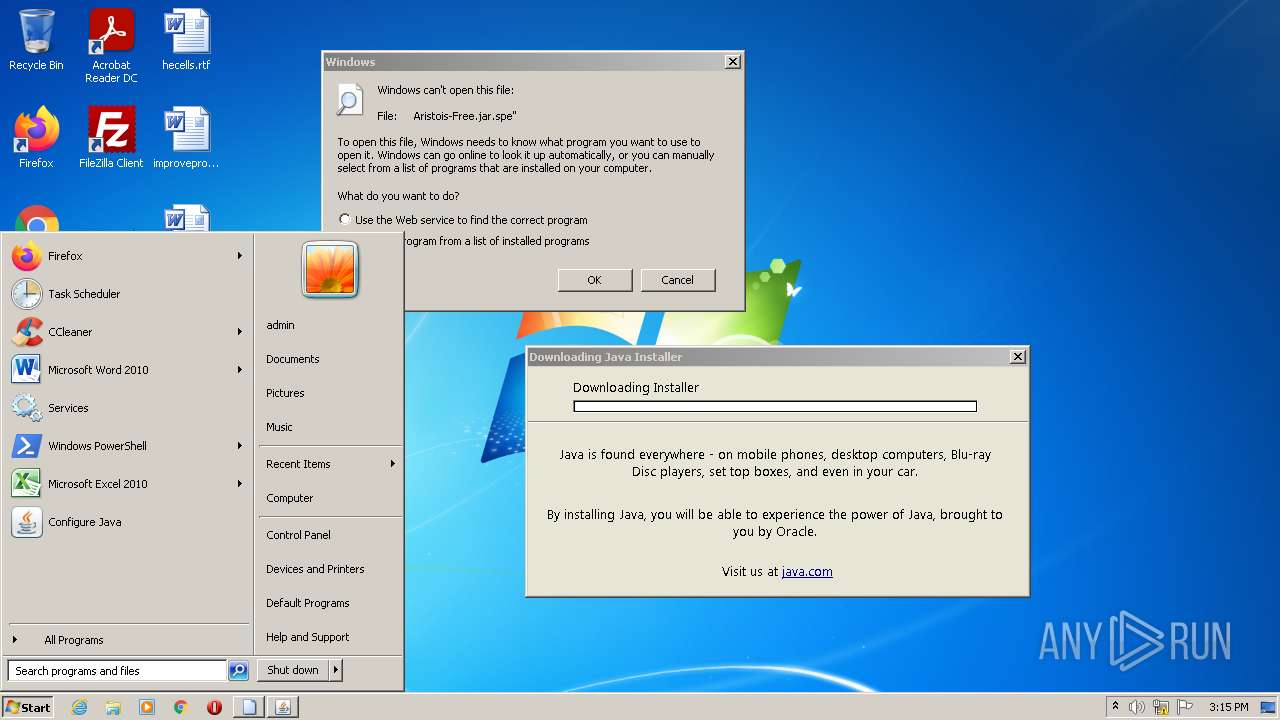
| File name: | Aristois-Free.jar |
| Full analysis: | https://app.any.run/tasks/aaf2998e-eadb-43cb-9be2-9dfc87fd859b |
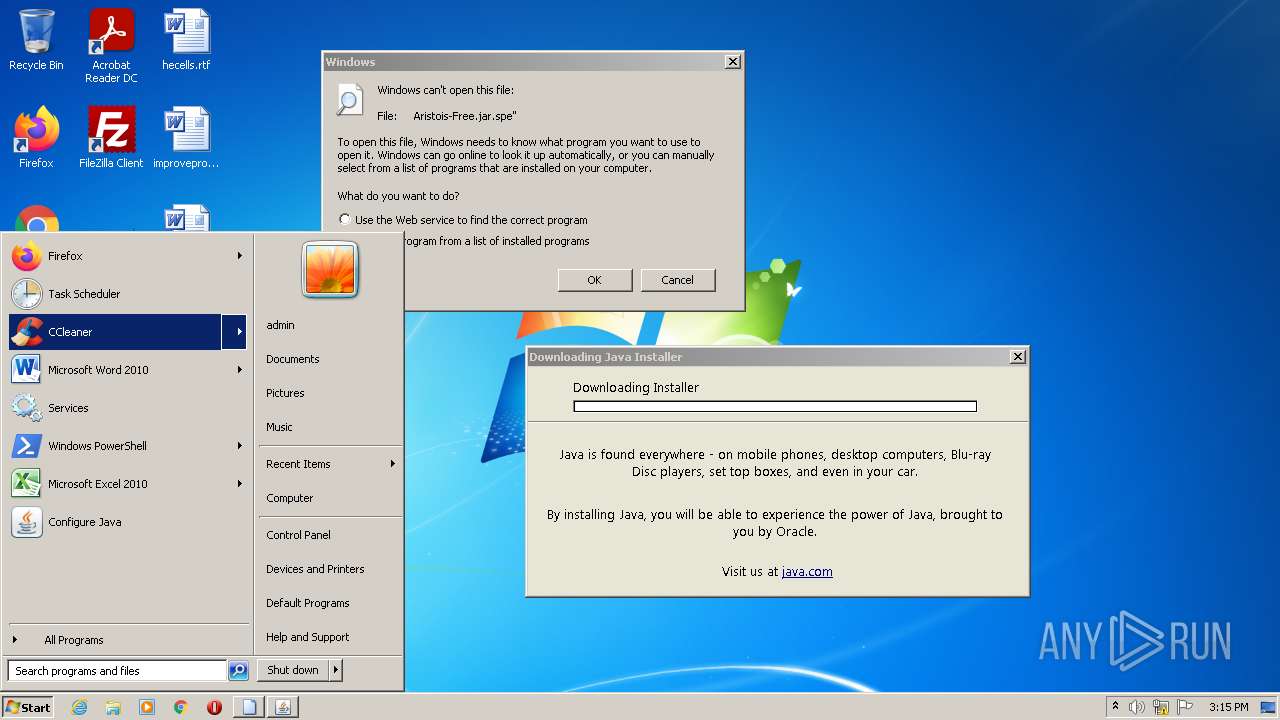
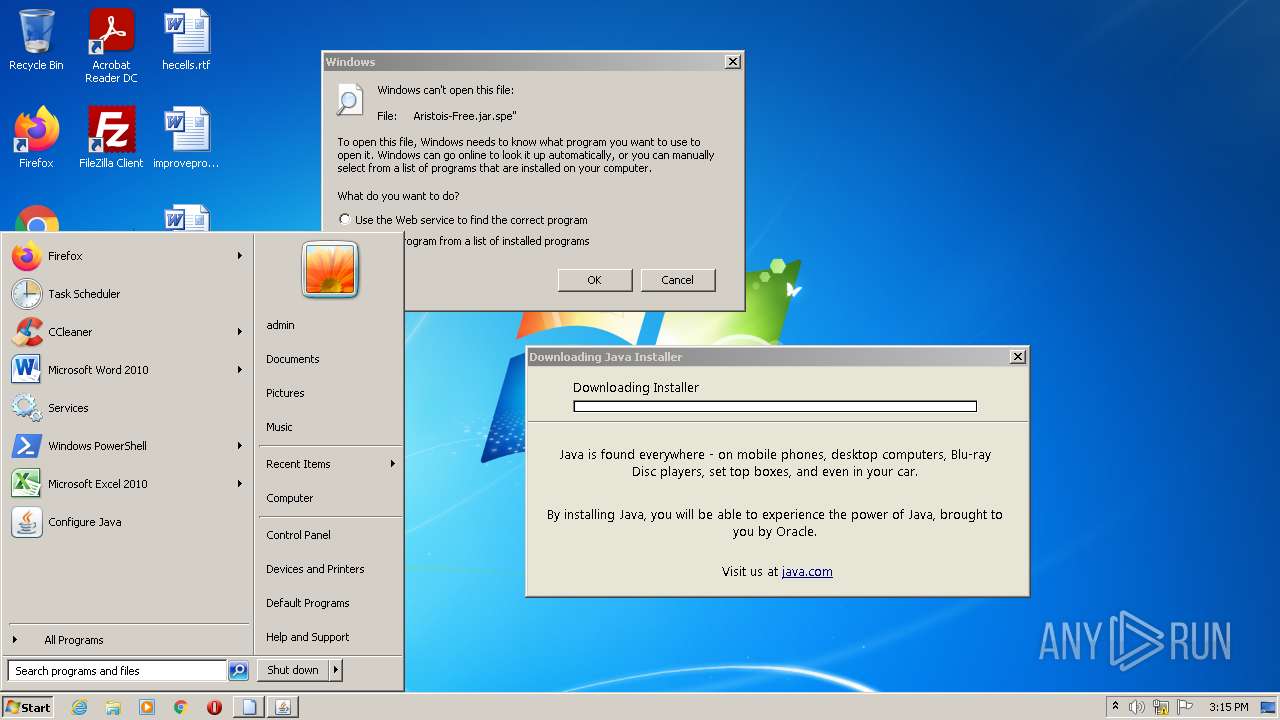
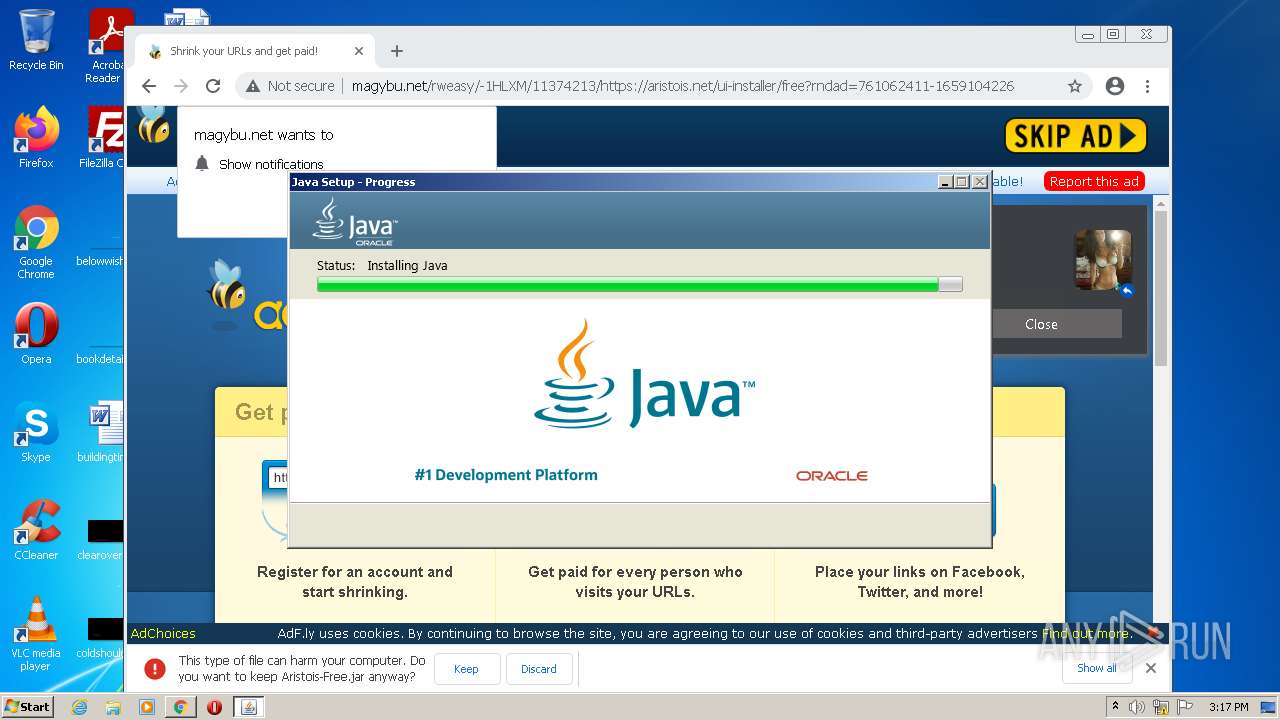
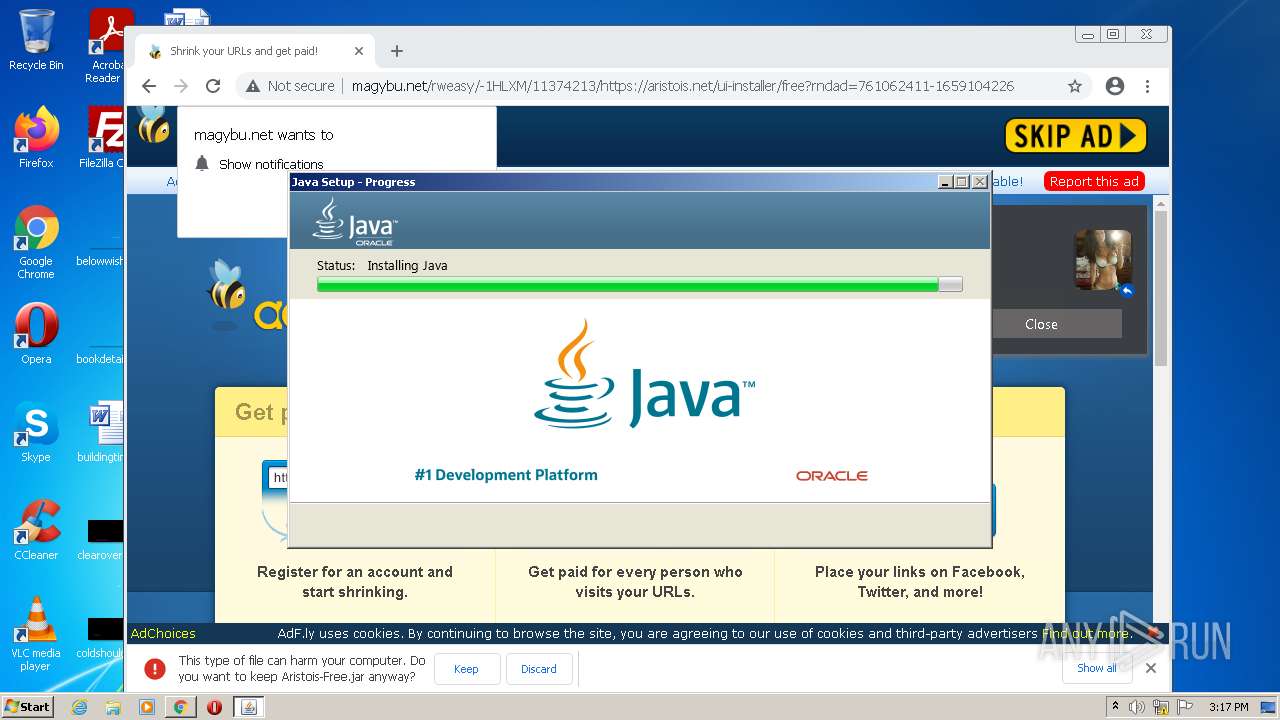
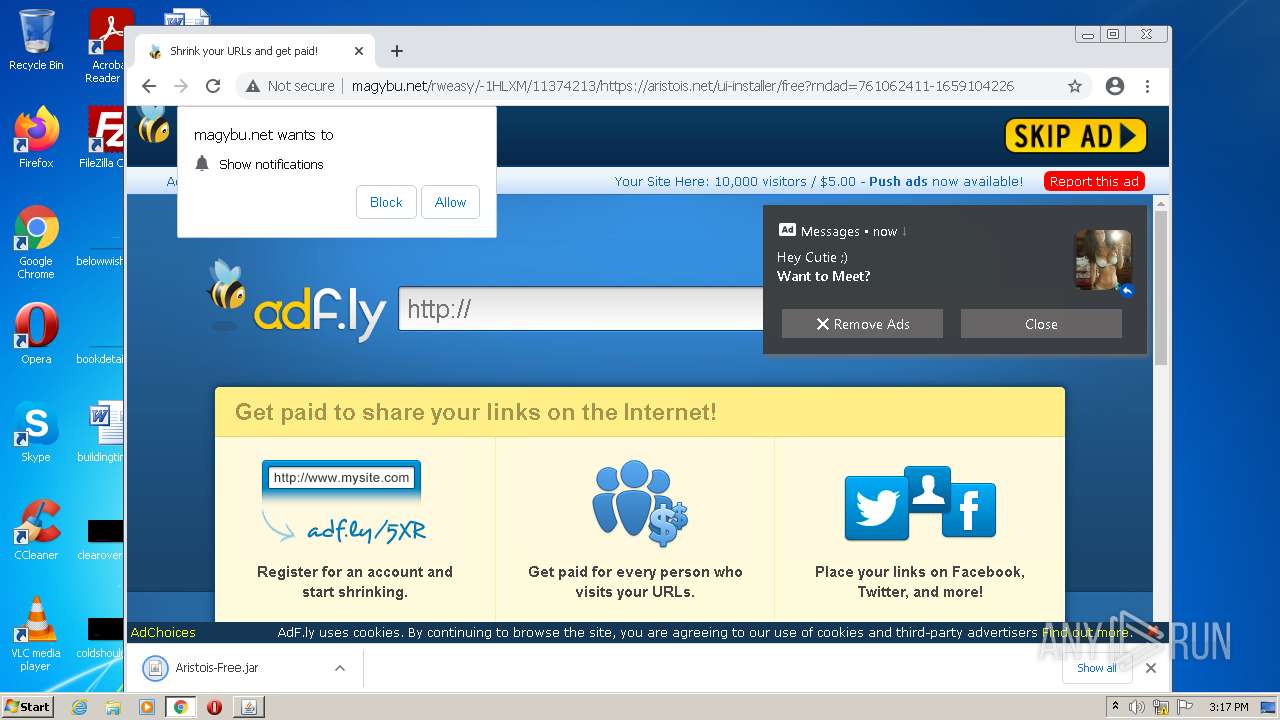
| Verdict: | Malicious activity |
| Analysis date: | July 29, 2022, 14:13:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 3C7956C53ECE5D641B9E145FDCABFB0A |
| SHA1: | 3FBB8E7B6A3F6CB01E881181E7B28EE0420A816C |
| SHA256: | 4A4E9F8D9EAE98098D438BEEB81FF0714FC9A94506DCBDA12DE242460B7236C9 |
| SSDEEP: | 98304:wrhNHr4fQuzae+8O8jeIzlKB63IwRB9JjxUoa3X1PdXFpw3ApcUtZFN35q:ONHUhzd+8O8jTF3XHxUoUPrCQphtZs |
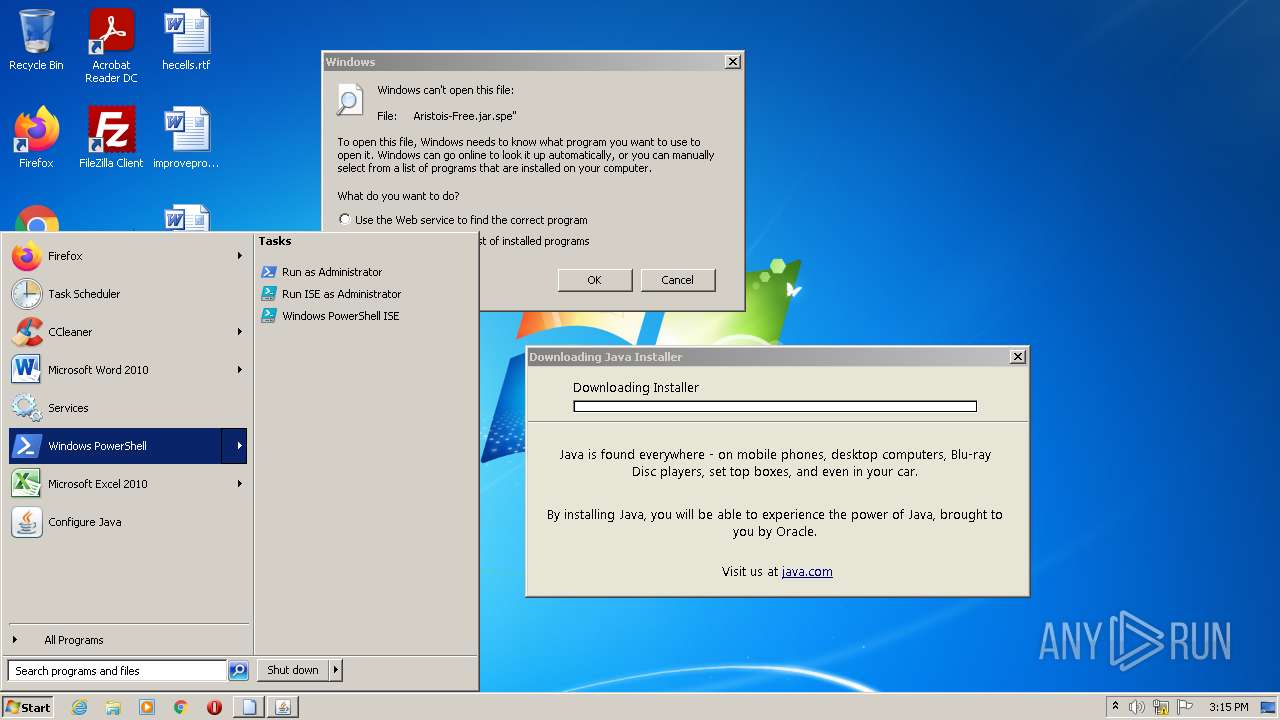
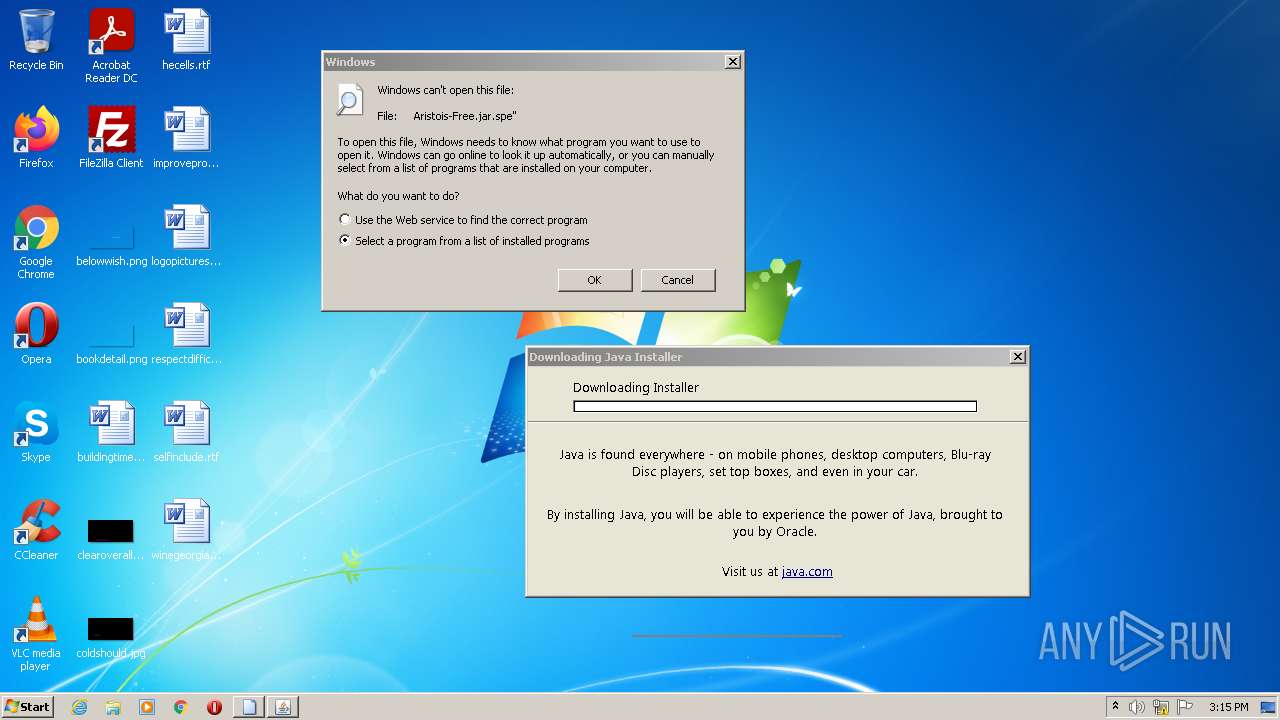
MALICIOUS
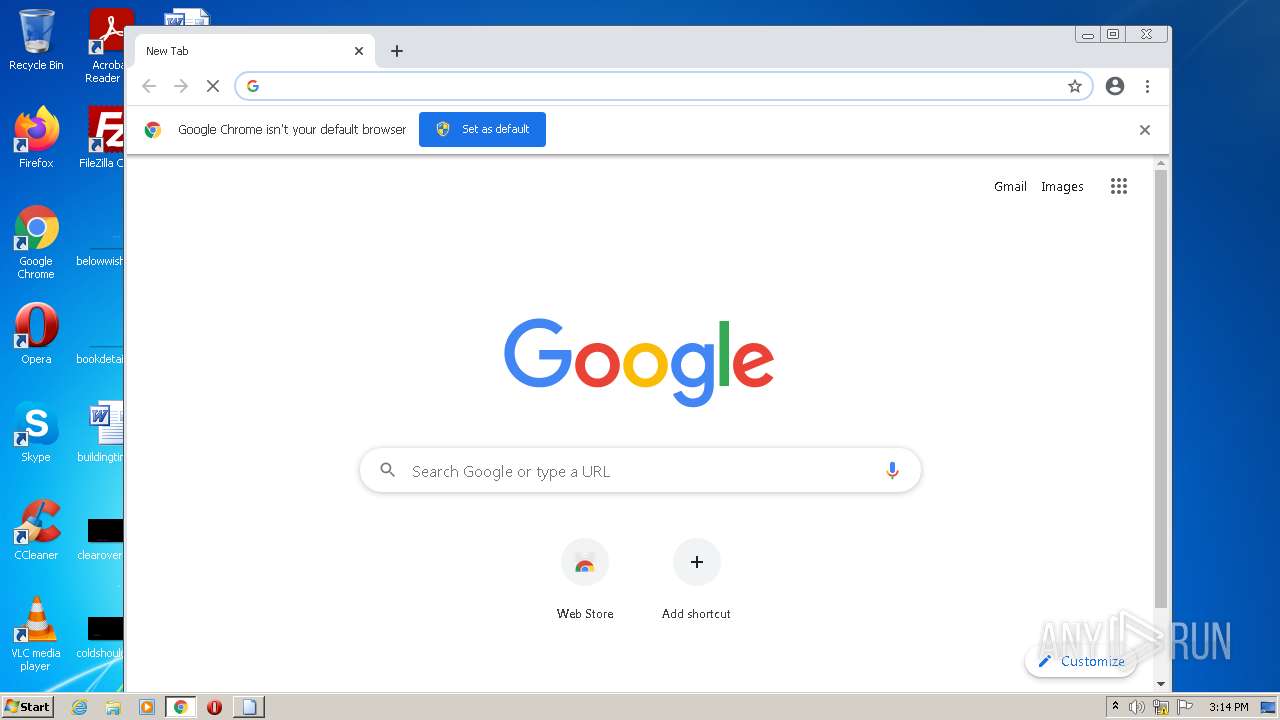
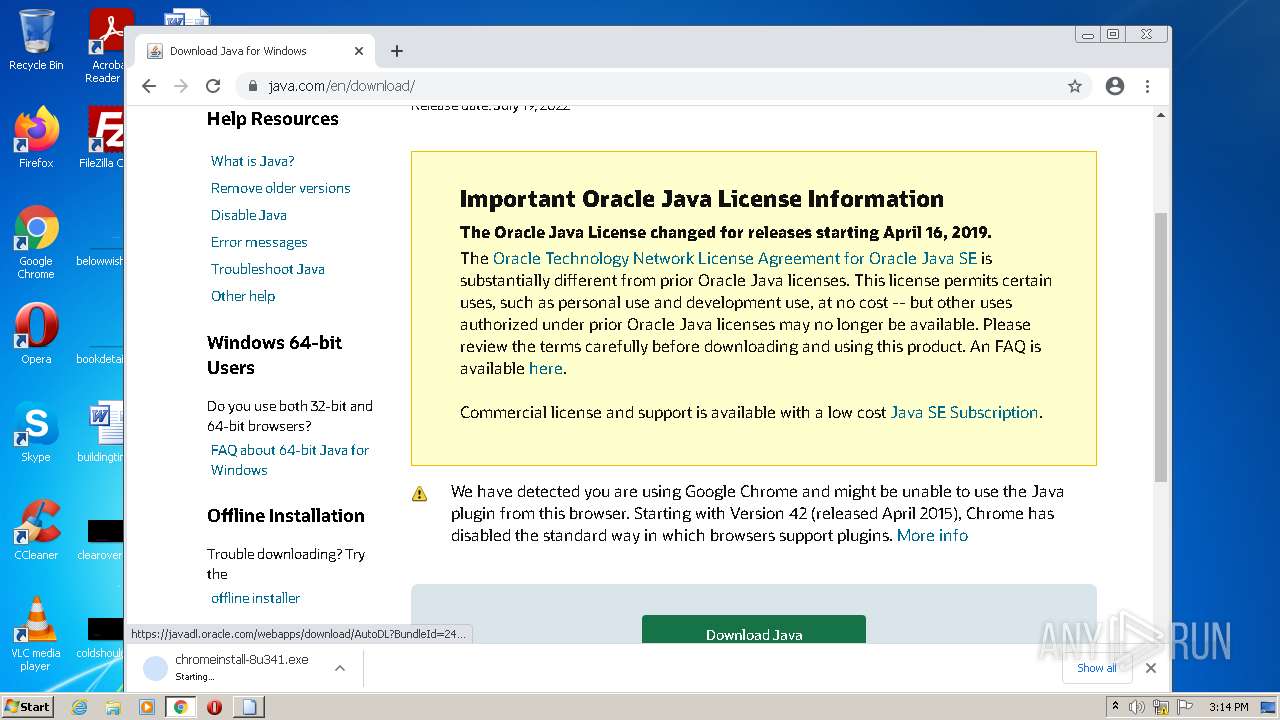
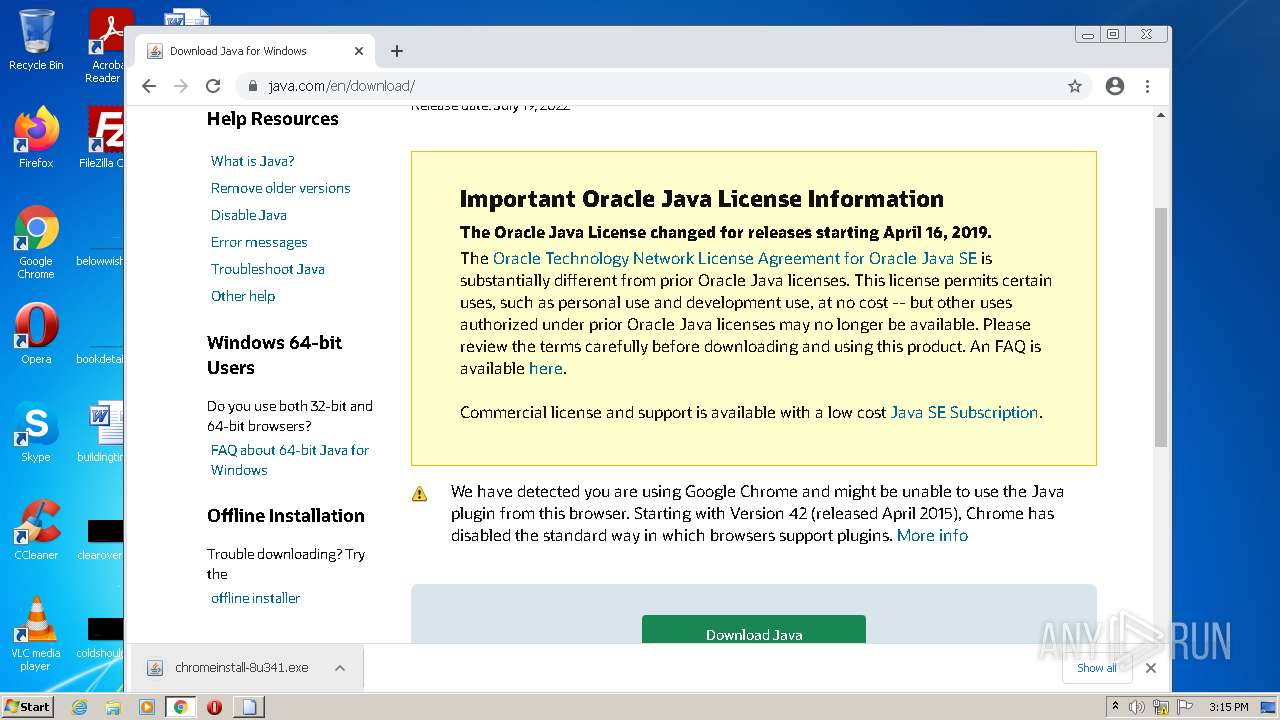
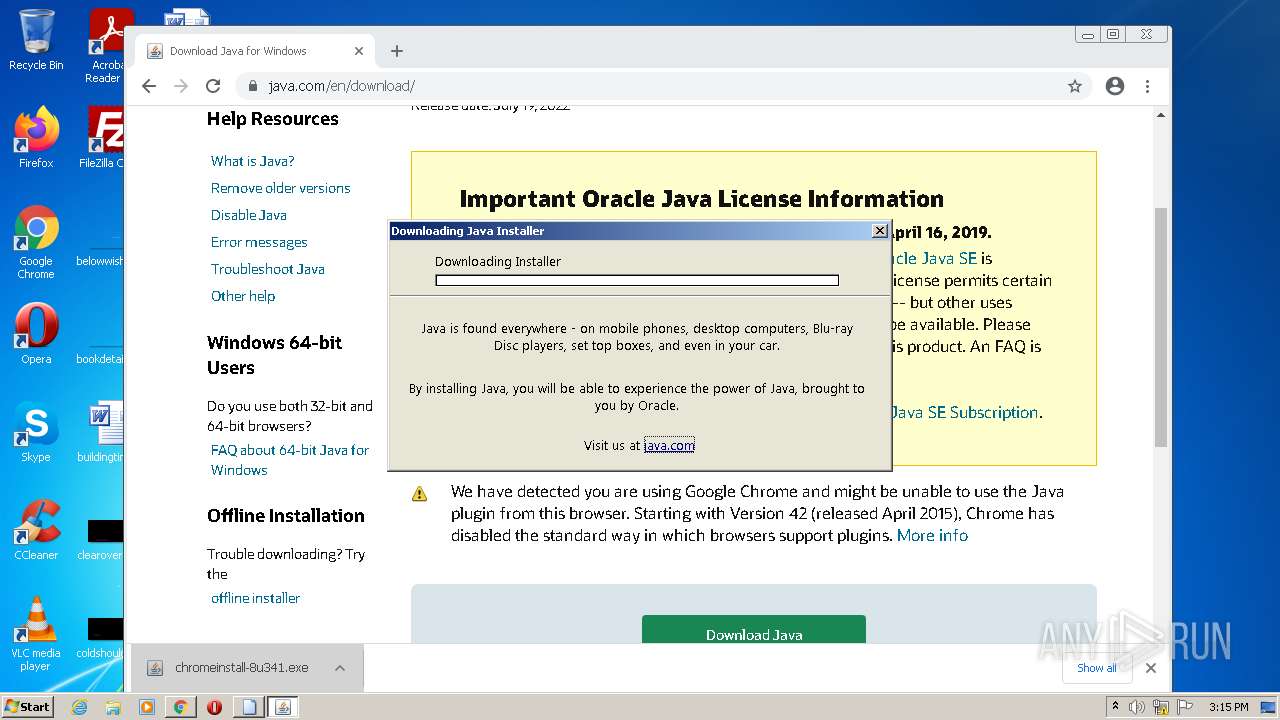
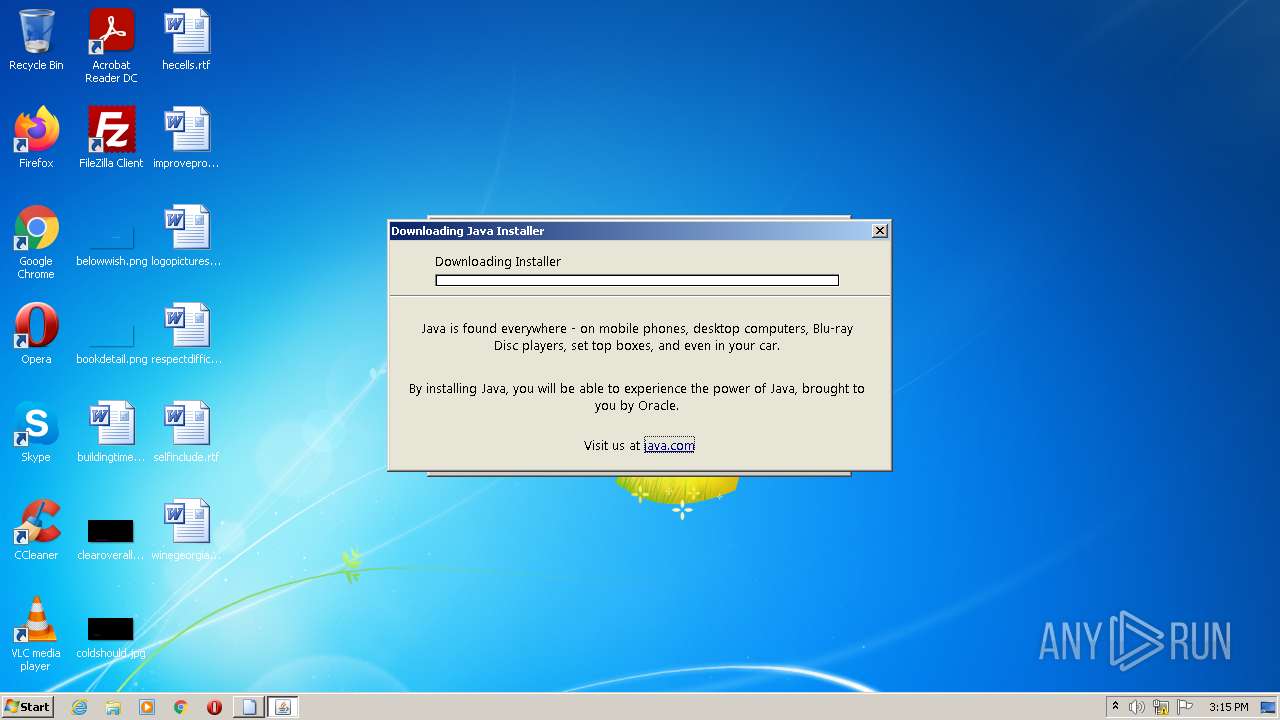
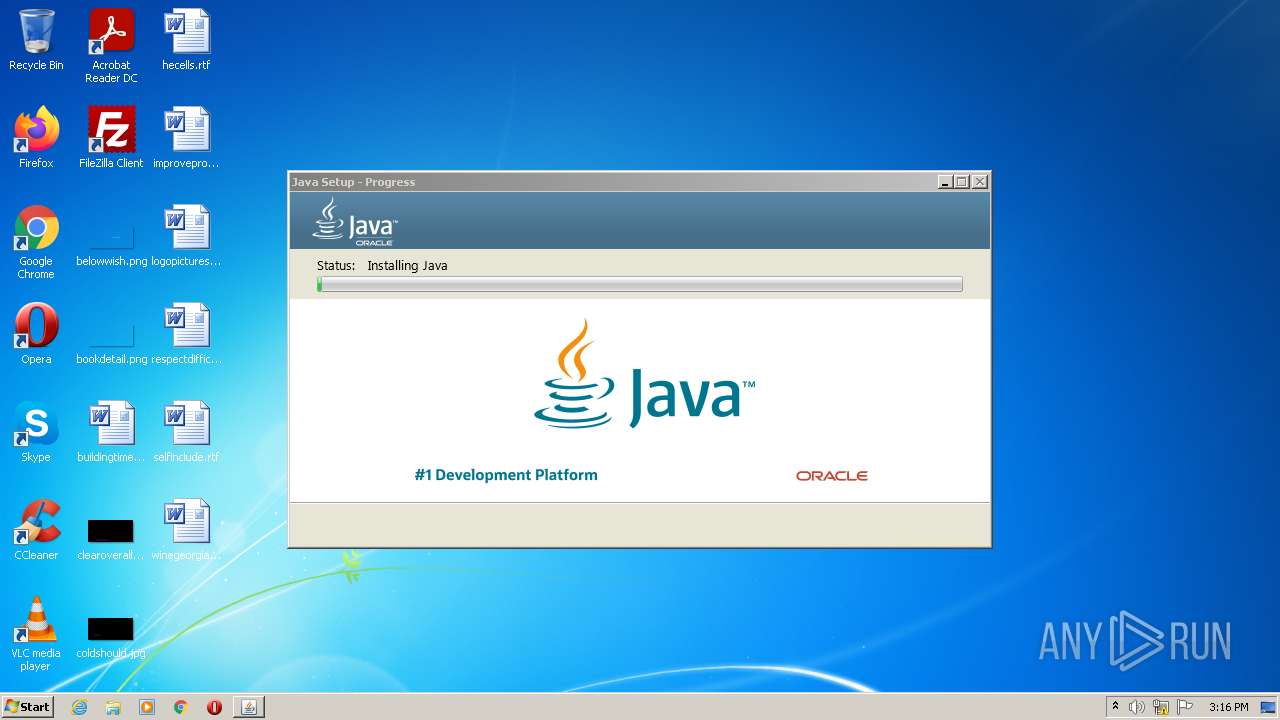
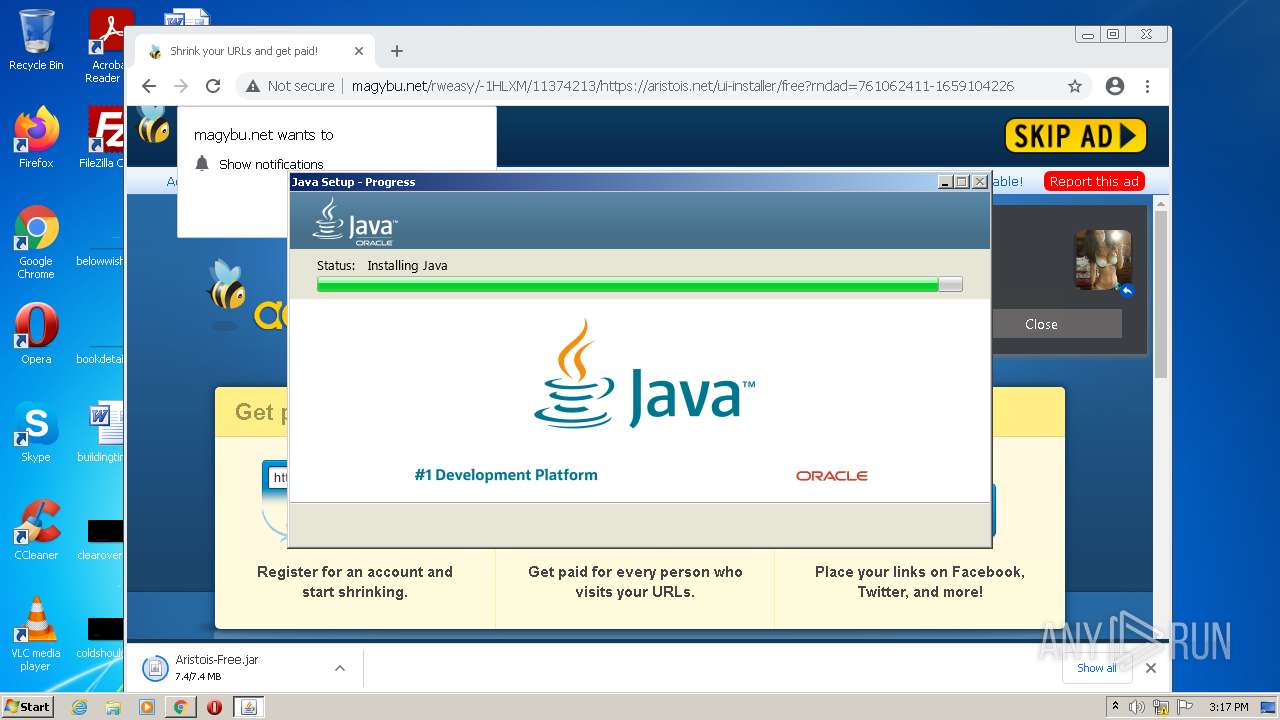
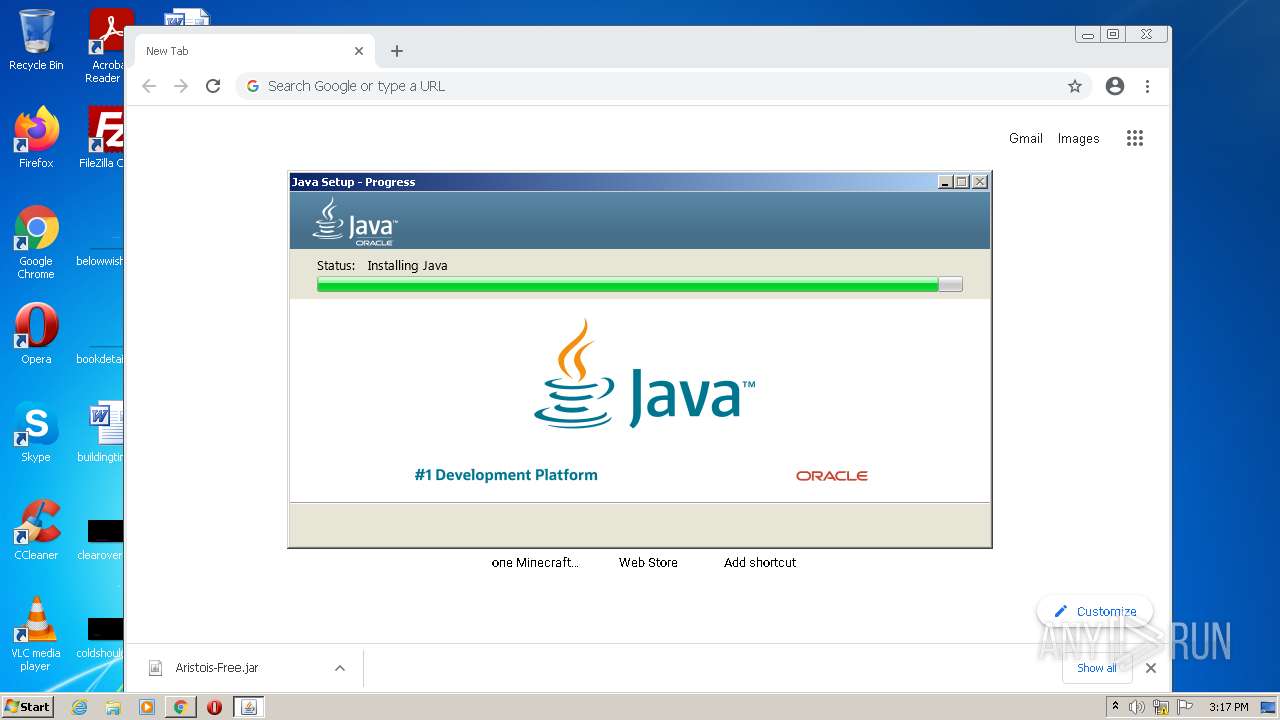
Drops executable file immediately after starts
- chrome.exe (PID: 3476)
- chrome.exe (PID: 960)
- chromeinstall-8u341.exe (PID: 2740)
- chromeinstall-8u341.exe (PID: 3752)
- msiexec.exe (PID: 4080)
- installer.exe (PID: 3088)
- javaw.exe (PID: 4076)
Application was dropped or rewritten from another process
- chromeinstall-8u341.exe (PID: 2740)
- chromeinstall-8u341.exe (PID: 2928)
- chromeinstall-8u341.exe (PID: 3752)
- LZMA_EXE (PID: 4004)
- LZMA_EXE (PID: 1856)
- bspatch.exe (PID: 1120)
- unpack200.exe (PID: 2956)
- ssvagent.exe (PID: 4060)
- javaw.exe (PID: 2024)
- unpack200.exe (PID: 3140)
- unpack200.exe (PID: 2268)
- unpack200.exe (PID: 3208)
- unpack200.exe (PID: 2996)
- javaws.exe (PID: 3208)
- jp2launcher.exe (PID: 3168)
- javaws.exe (PID: 1644)
- jp2launcher.exe (PID: 3820)
- unpack200.exe (PID: 1048)
- unpack200.exe (PID: 968)
- javaw.exe (PID: 4076)
- javaw.exe (PID: 2748)
- javaw.exe (PID: 1964)
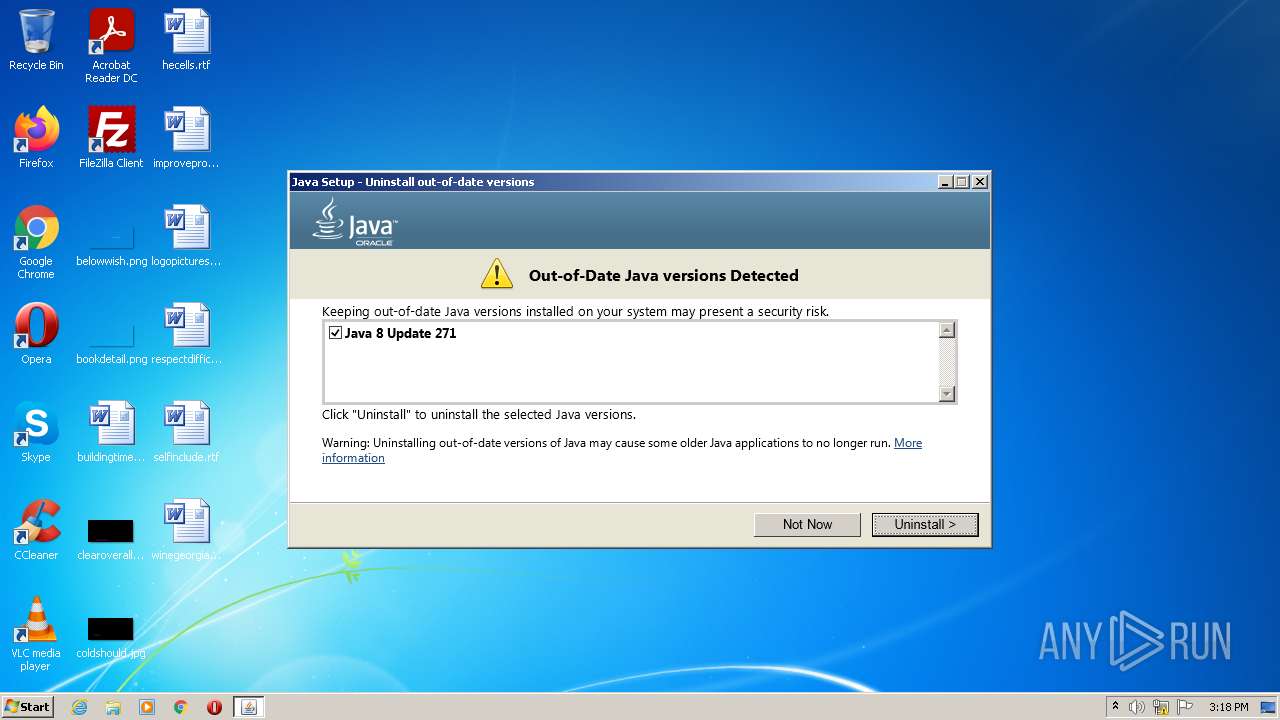
Changes settings of System certificates
- chromeinstall-8u341.exe (PID: 3752)
Loads dropped or rewritten executable
- unpack200.exe (PID: 2956)
- unpack200.exe (PID: 2268)
- unpack200.exe (PID: 3140)
- unpack200.exe (PID: 2996)
- unpack200.exe (PID: 3208)
- unpack200.exe (PID: 968)
- unpack200.exe (PID: 1048)
- javaw.exe (PID: 2024)
- installer.exe (PID: 3088)
- ssvagent.exe (PID: 4060)
- Explorer.EXE (PID: 1080)
- svchost.exe (PID: 872)
- jp2launcher.exe (PID: 3168)
- jp2launcher.exe (PID: 3820)
- svchost.exe (PID: 804)
- chrome.exe (PID: 2540)
- javaw.exe (PID: 4076)
- chromeinstall-8u341.exe (PID: 3752)
- javaw.exe (PID: 1964)
- javaw.exe (PID: 2748)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3476)
Reads default file associations for system extensions
- Explorer.EXE (PID: 1080)
Executable content was dropped or overwritten
- chrome.exe (PID: 3476)
- chrome.exe (PID: 960)
- chromeinstall-8u341.exe (PID: 2740)
- chromeinstall-8u341.exe (PID: 3752)
- LZMA_EXE (PID: 4004)
- msiexec.exe (PID: 4080)
- installer.exe (PID: 3088)
- javaw.exe (PID: 4076)
Drops a file with a compile date too recent
- chrome.exe (PID: 3476)
- chrome.exe (PID: 960)
- chromeinstall-8u341.exe (PID: 2740)
- chromeinstall-8u341.exe (PID: 3752)
- msiexec.exe (PID: 4080)
- installer.exe (PID: 3088)
- javaw.exe (PID: 4076)
Checks supported languages
- chromeinstall-8u341.exe (PID: 2740)
- chromeinstall-8u341.exe (PID: 3752)
- msiexec.exe (PID: 4080)
- LZMA_EXE (PID: 4004)
- LZMA_EXE (PID: 1856)
- MsiExec.exe (PID: 3332)
- bspatch.exe (PID: 1120)
- installer.exe (PID: 3088)
- unpack200.exe (PID: 2956)
- unpack200.exe (PID: 2268)
- unpack200.exe (PID: 3140)
- unpack200.exe (PID: 2996)
- unpack200.exe (PID: 3208)
- unpack200.exe (PID: 968)
- unpack200.exe (PID: 1048)
- javaw.exe (PID: 2024)
- ssvagent.exe (PID: 4060)
- jp2launcher.exe (PID: 3168)
- javaws.exe (PID: 1644)
- jp2launcher.exe (PID: 3820)
- javaws.exe (PID: 3208)
- MsiExec.exe (PID: 2344)
- MsiExec.exe (PID: 3620)
- MsiExec.exe (PID: 3124)
- MsiExec.exe (PID: 1968)
- MsiExec.exe (PID: 752)
- javaw.exe (PID: 4076)
- javaw.exe (PID: 2748)
- javaw.exe (PID: 1964)
Reads the computer name
- chromeinstall-8u341.exe (PID: 2740)
- chromeinstall-8u341.exe (PID: 3752)
- msiexec.exe (PID: 4080)
- MsiExec.exe (PID: 3332)
- installer.exe (PID: 3088)
- javaws.exe (PID: 3208)
- javaws.exe (PID: 1644)
- jp2launcher.exe (PID: 3168)
- MsiExec.exe (PID: 752)
- MsiExec.exe (PID: 2344)
- MsiExec.exe (PID: 3620)
- MsiExec.exe (PID: 3124)
- MsiExec.exe (PID: 1968)
- jp2launcher.exe (PID: 3820)
- javaw.exe (PID: 4076)
- javaw.exe (PID: 2748)
- javaw.exe (PID: 1964)
Reads internet explorer settings
- chromeinstall-8u341.exe (PID: 3752)
Reads Microsoft Outlook installation path
- chromeinstall-8u341.exe (PID: 3752)
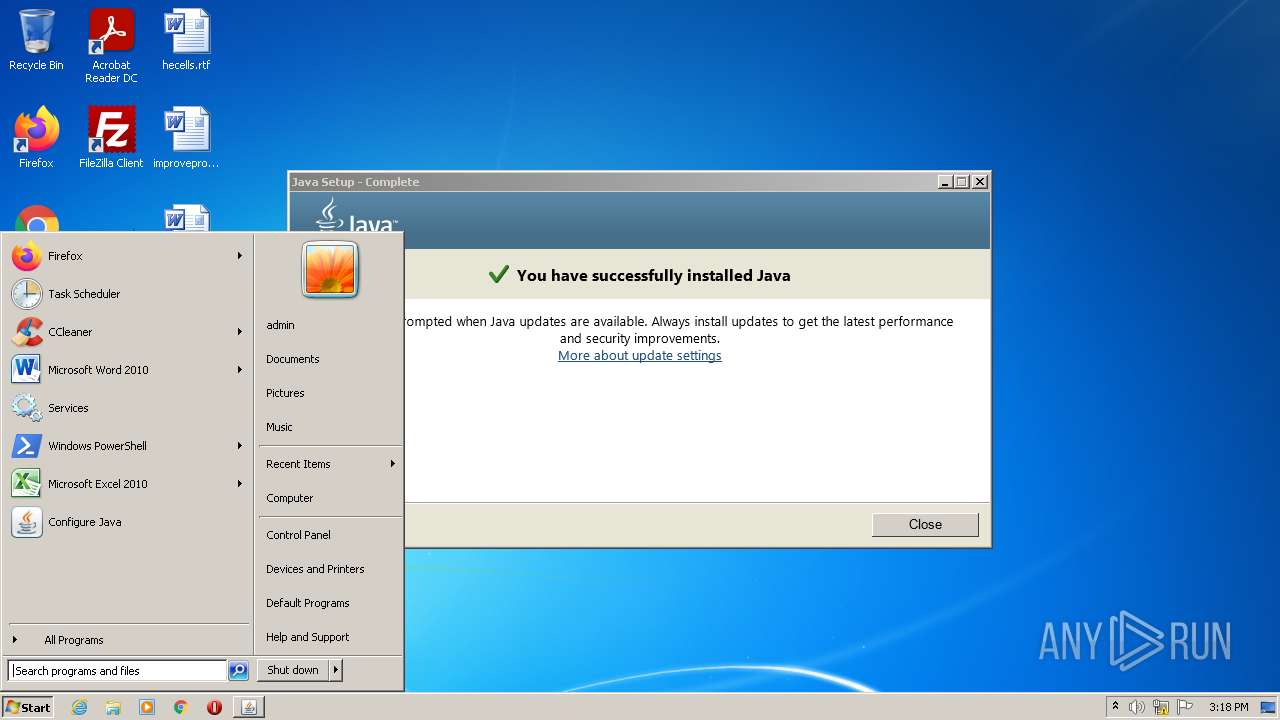
Searches for installed software
- svchost.exe (PID: 804)
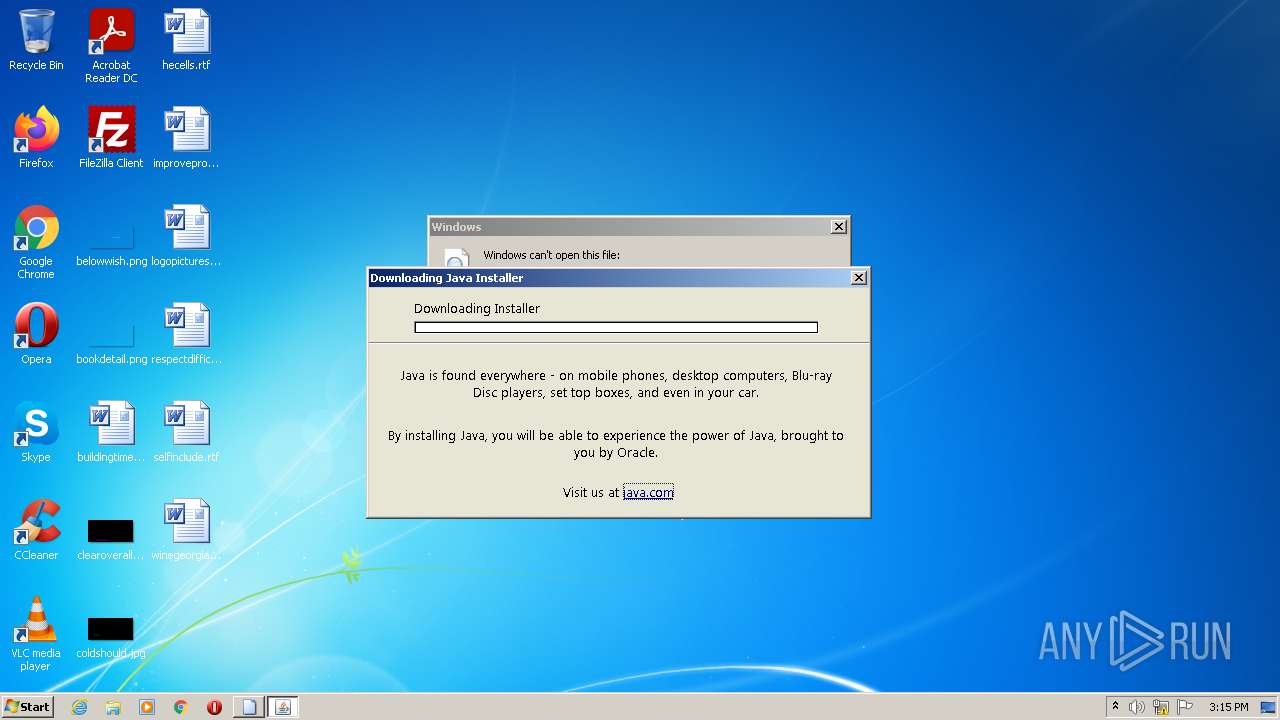
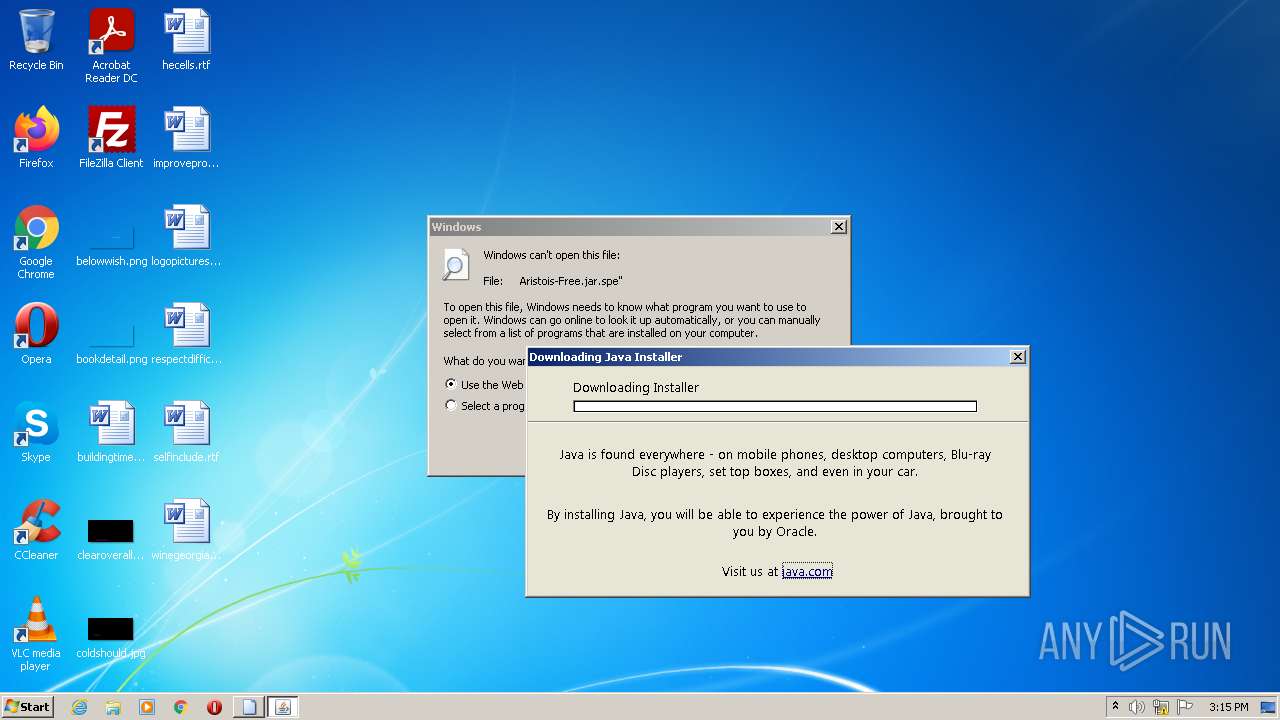
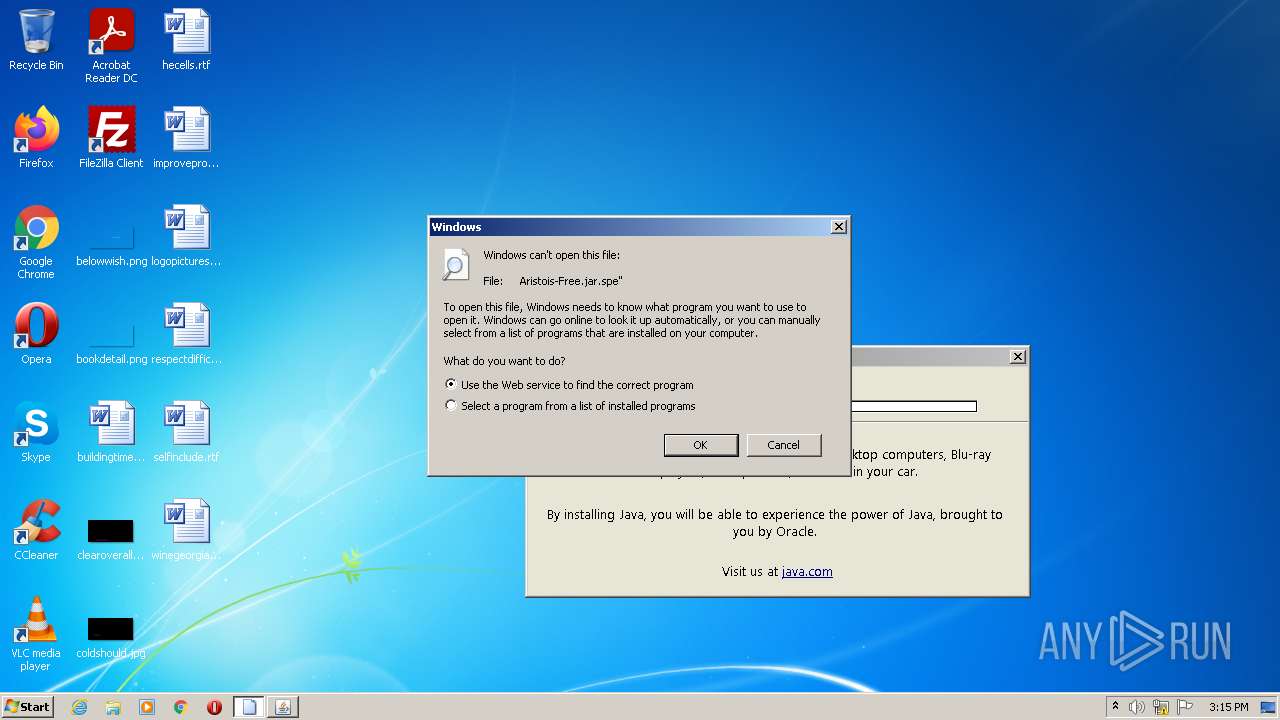
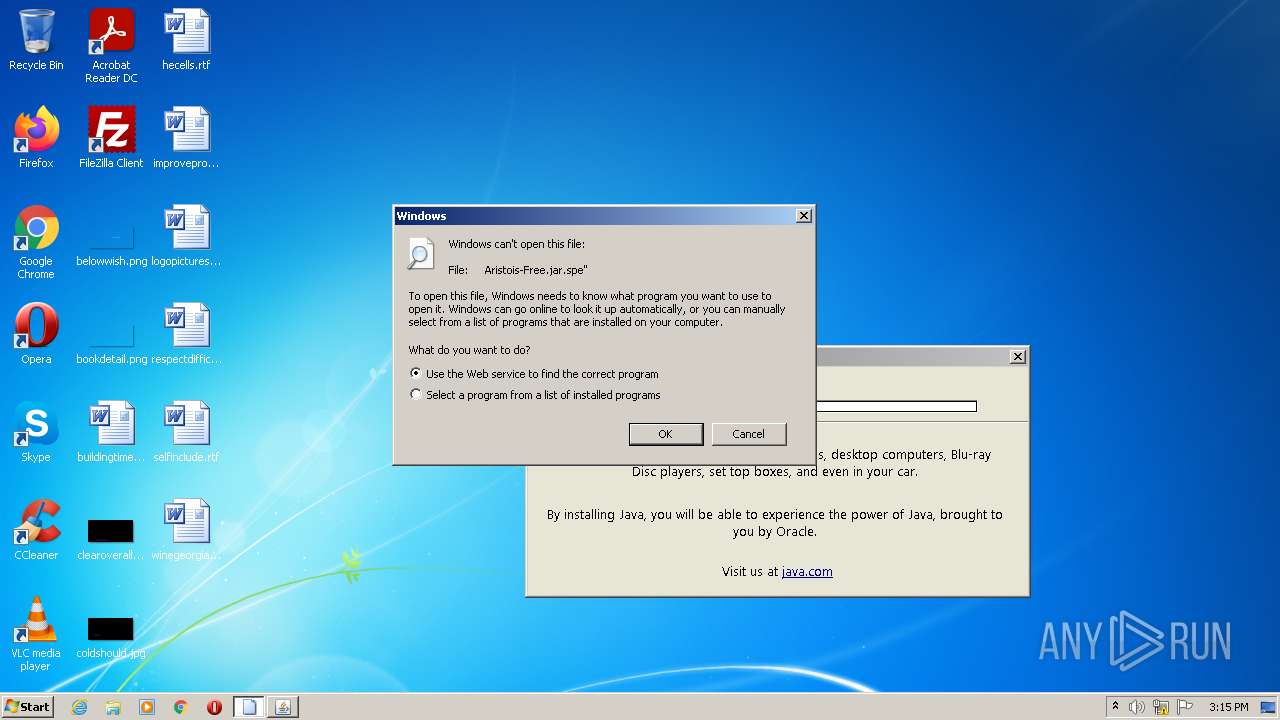
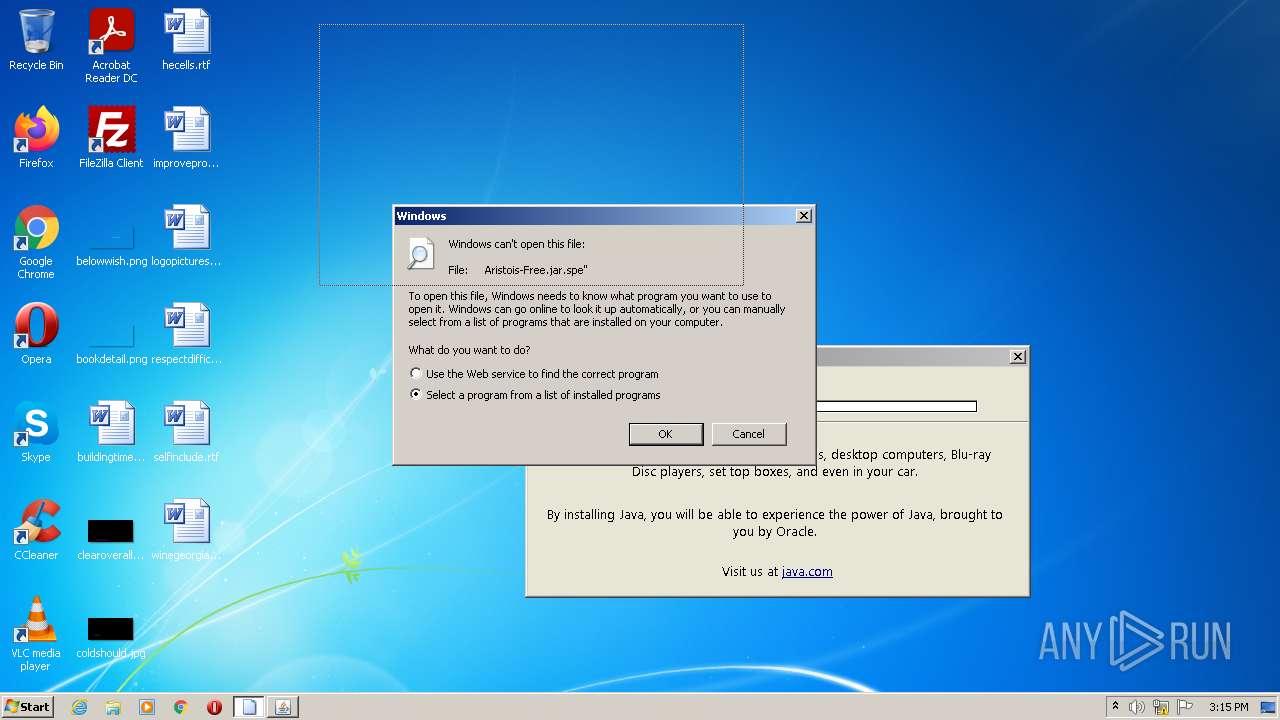
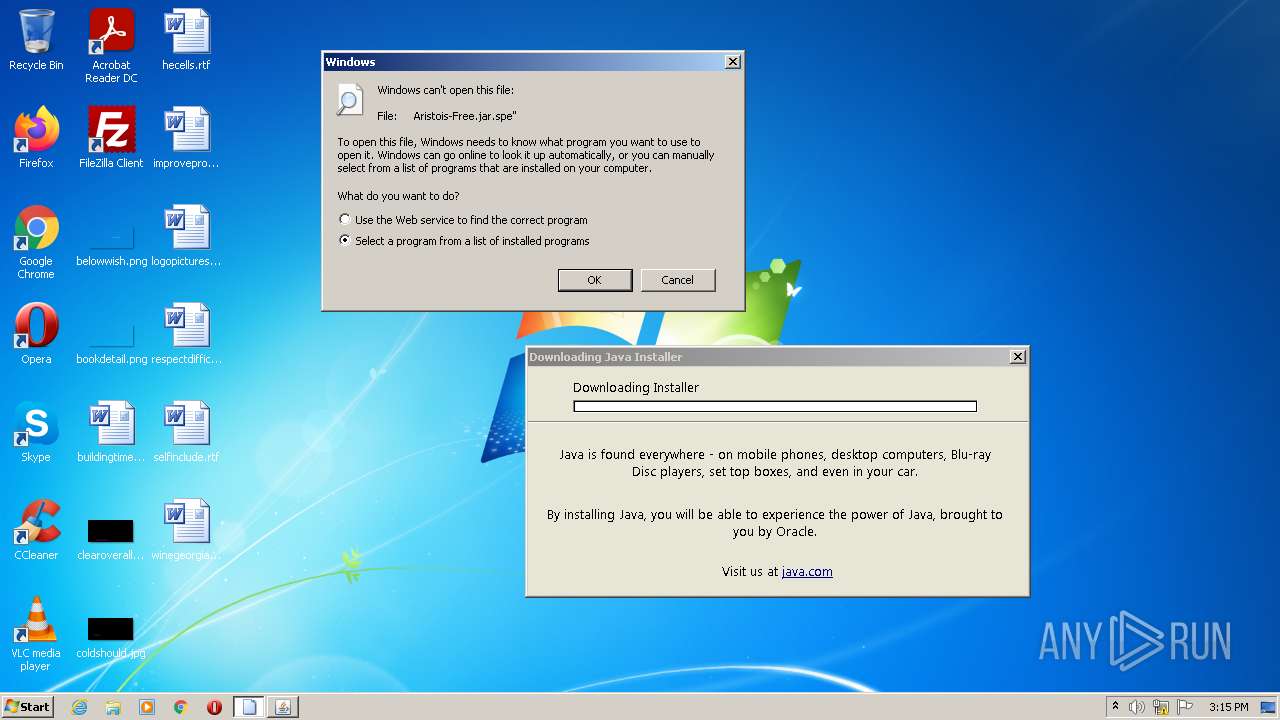
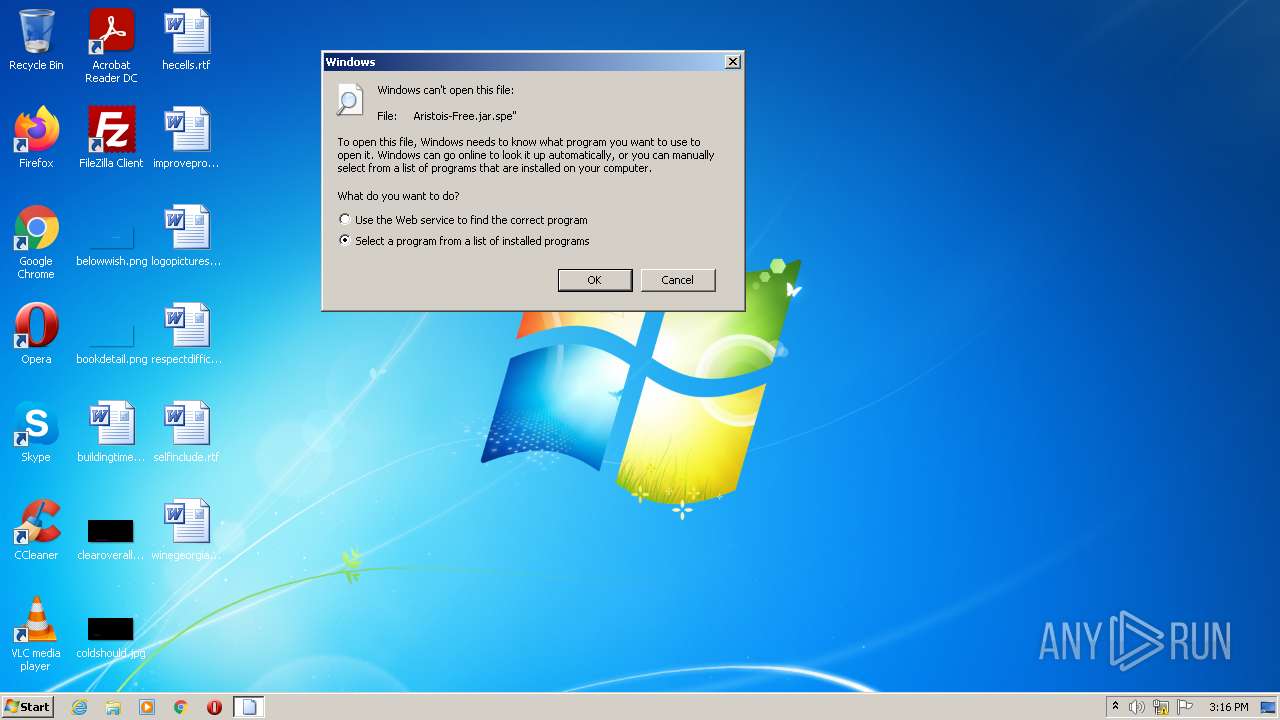
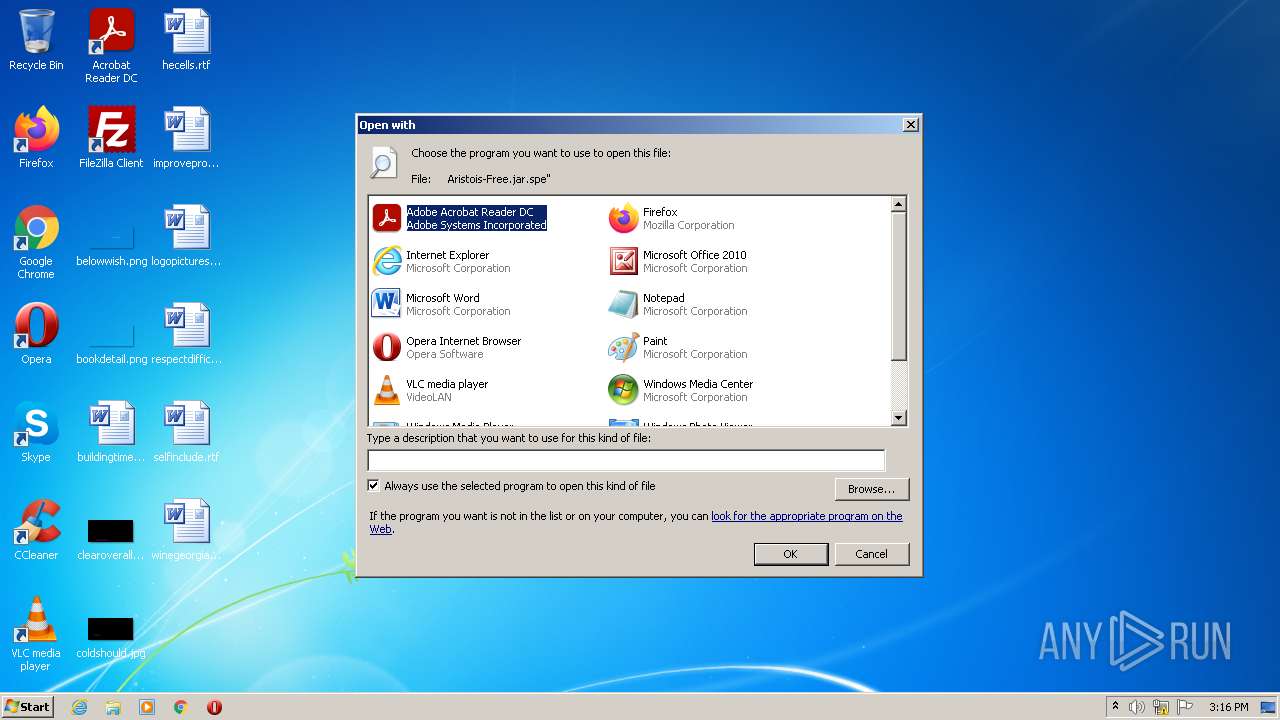
Starts application with an unusual extension
- chromeinstall-8u341.exe (PID: 3752)
Reads Windows owner or organization settings
- msiexec.exe (PID: 4080)
Adds / modifies Windows certificates
- chromeinstall-8u341.exe (PID: 3752)
Reads the Windows organization settings
- msiexec.exe (PID: 4080)
Creates a directory in Program Files
- msiexec.exe (PID: 4080)
- installer.exe (PID: 3088)
Reads CPU info
- msiexec.exe (PID: 4080)
Creates files in the program directory
- installer.exe (PID: 3088)
- bspatch.exe (PID: 1120)
- unpack200.exe (PID: 3140)
- unpack200.exe (PID: 2956)
- unpack200.exe (PID: 2268)
- unpack200.exe (PID: 3208)
- unpack200.exe (PID: 2996)
- unpack200.exe (PID: 1048)
- javaw.exe (PID: 2024)
- unpack200.exe (PID: 968)
- javaw.exe (PID: 4076)
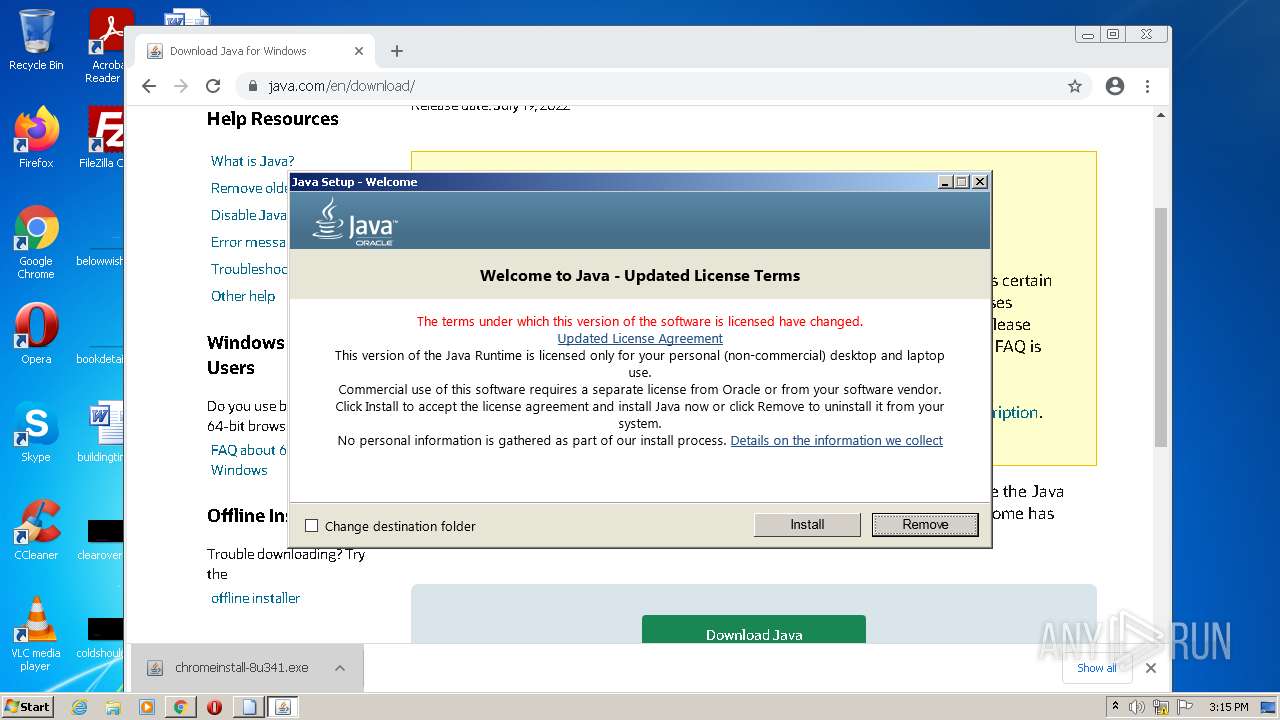
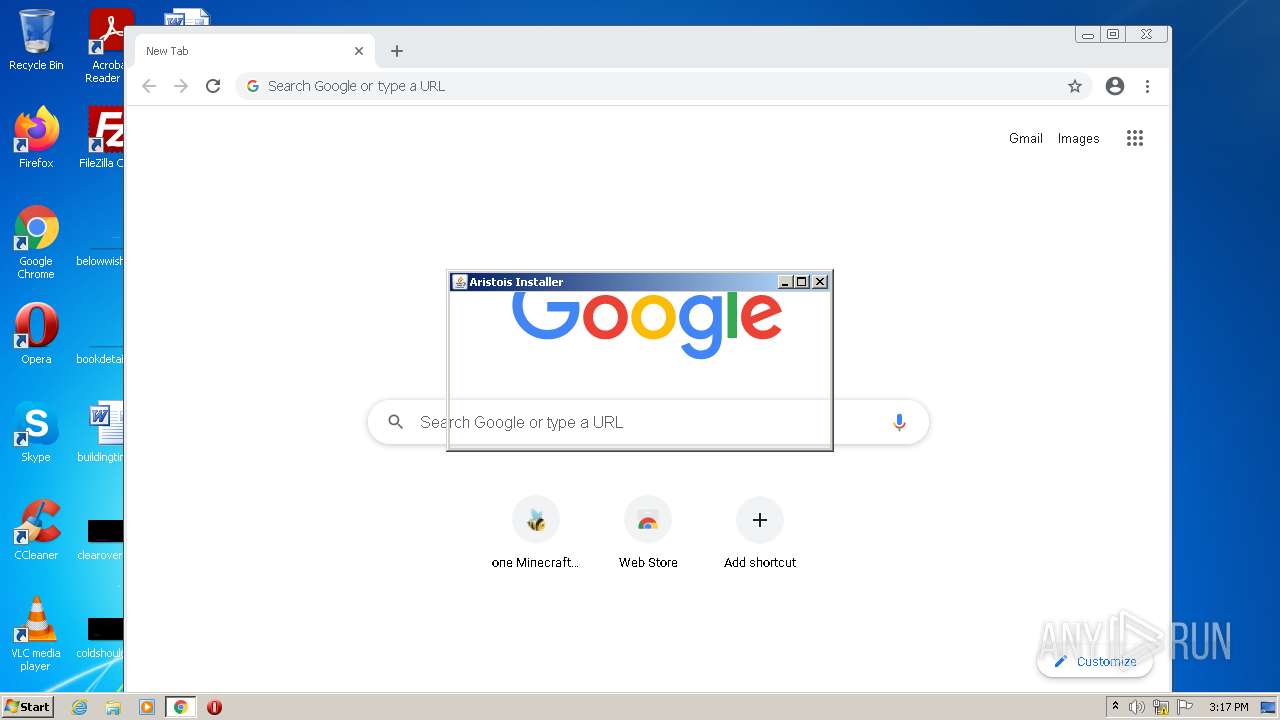
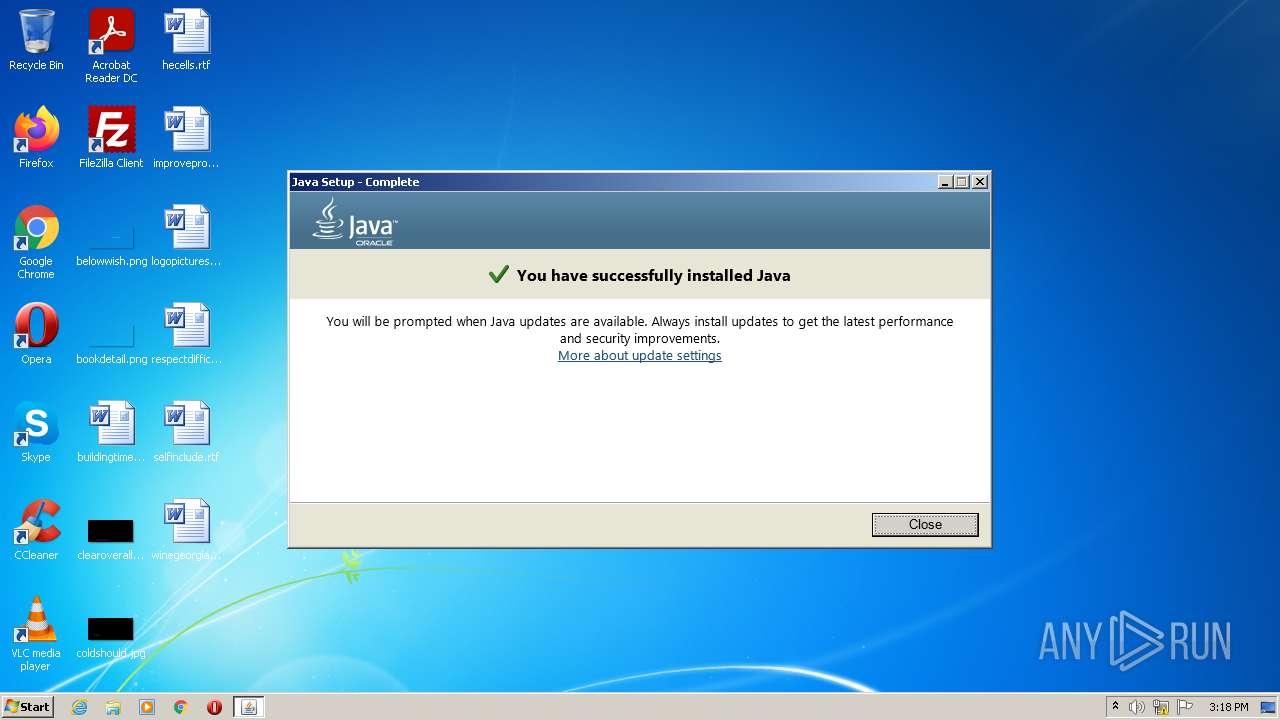
Check for Java to be installed
- installer.exe (PID: 3088)
- ssvagent.exe (PID: 4060)
- jp2launcher.exe (PID: 3168)
- jp2launcher.exe (PID: 3820)
- chromeinstall-8u341.exe (PID: 3752)
- msiexec.exe (PID: 4080)
- javaw.exe (PID: 2748)
Changes default file association
- installer.exe (PID: 3088)
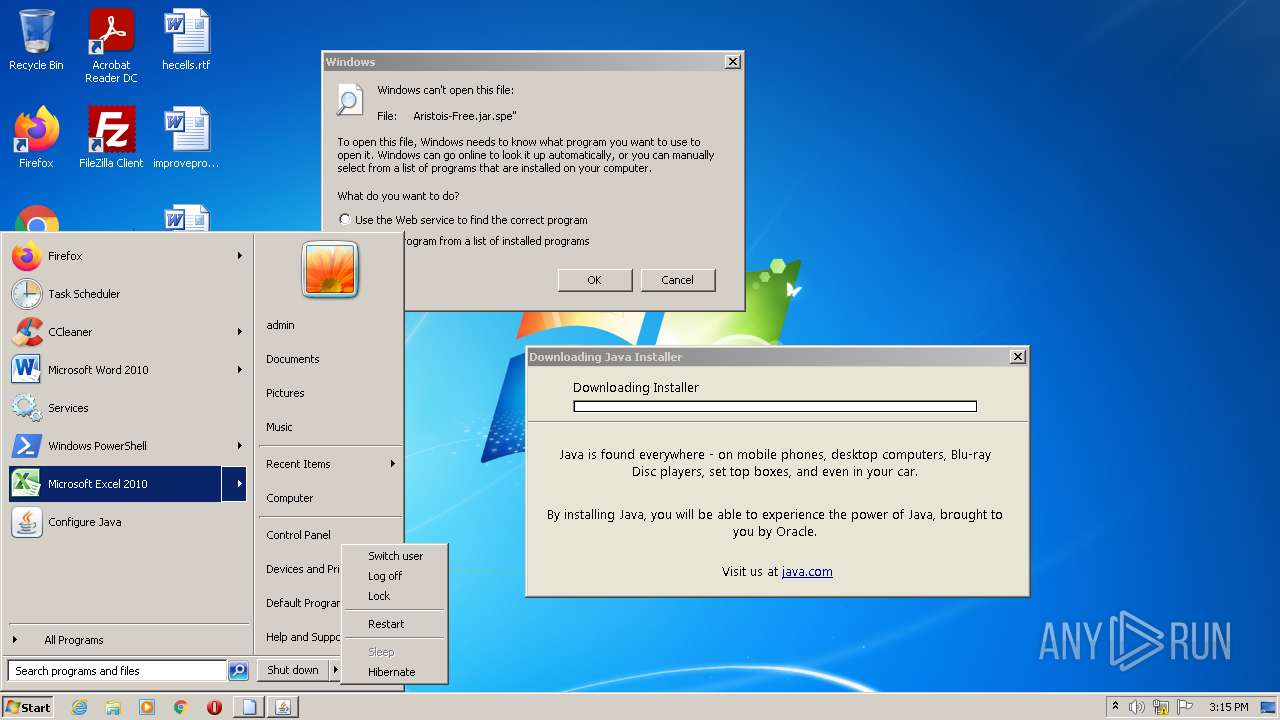
Changes the autorun value in the registry
- msiexec.exe (PID: 4080)
Creates/Modifies COM task schedule object
- ssvagent.exe (PID: 4060)
- installer.exe (PID: 3088)
INFO
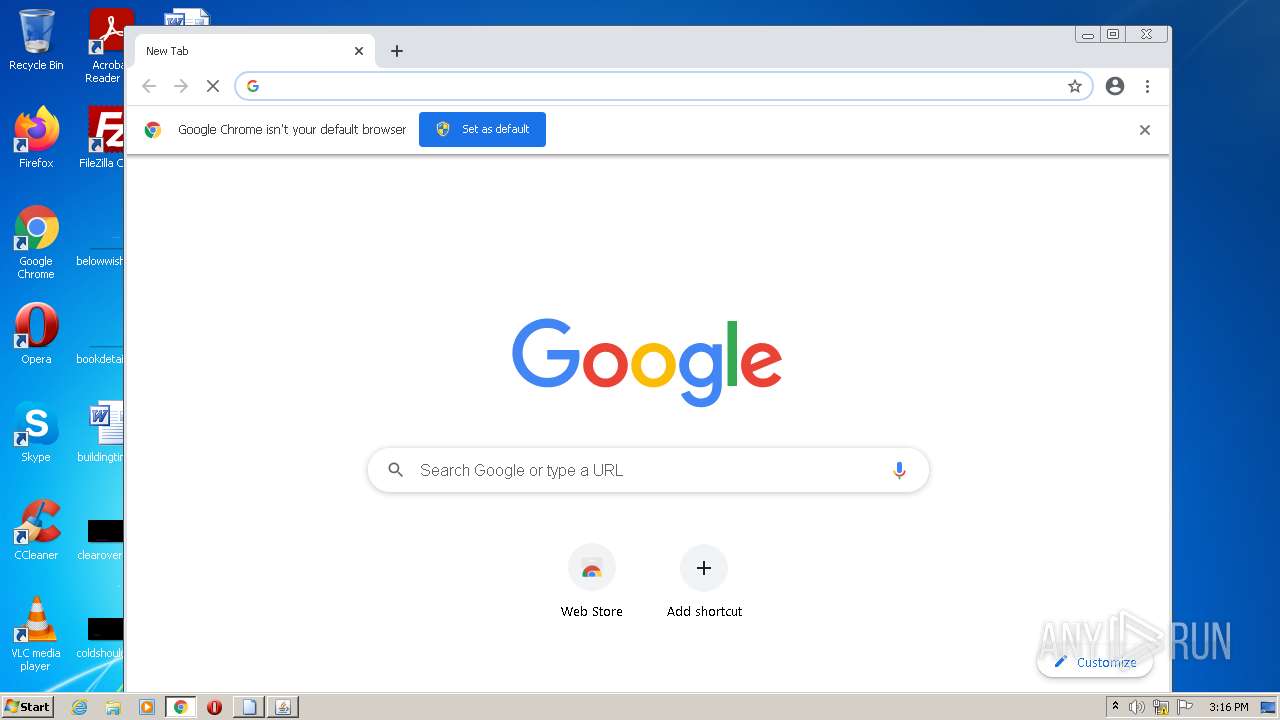
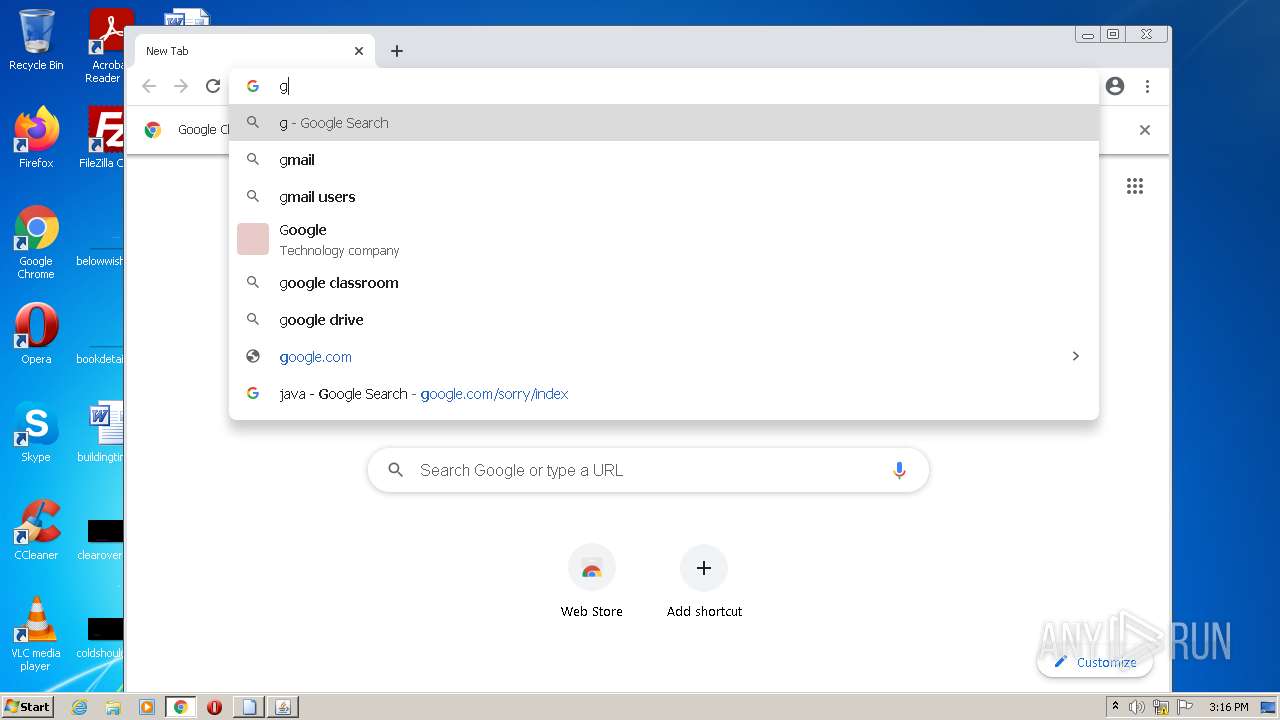
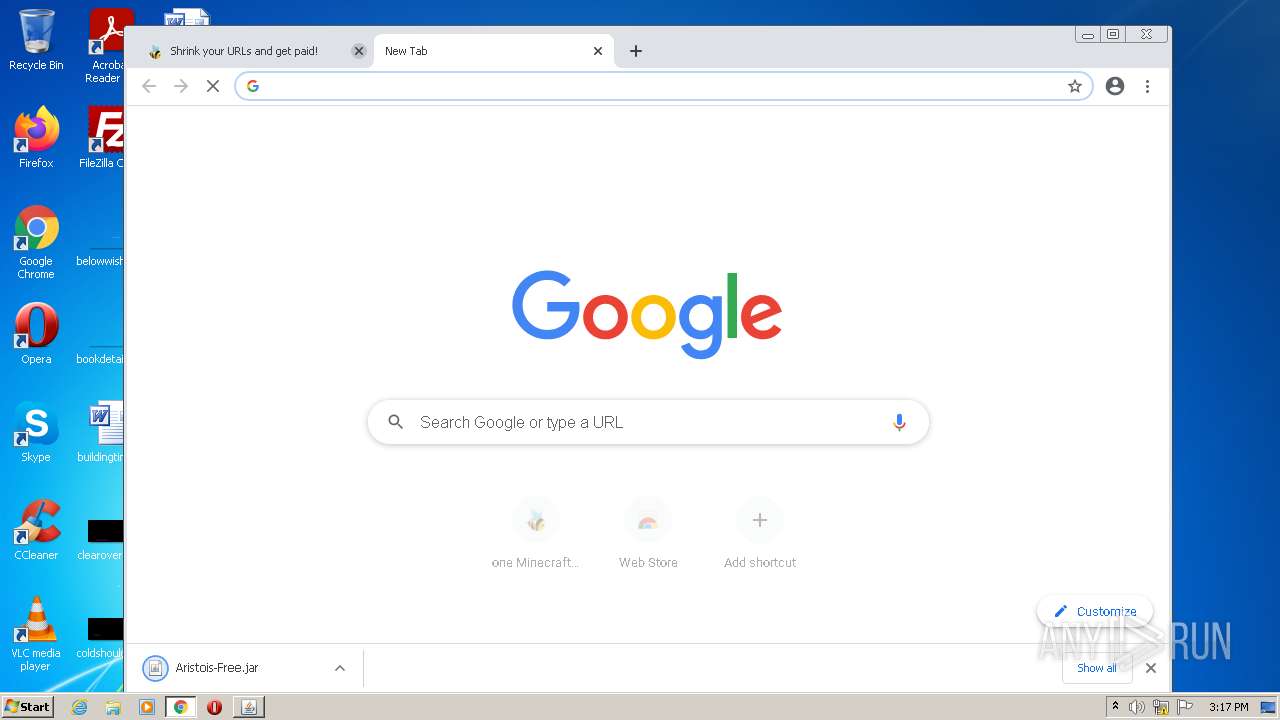
Application launched itself
- chrome.exe (PID: 3476)
- chrome.exe (PID: 3184)
- msiexec.exe (PID: 4080)
- chrome.exe (PID: 2540)
Checks supported languages
- chrome.exe (PID: 1576)
- rundll32.exe (PID: 2864)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 2796)
- chrome.exe (PID: 960)
- chrome.exe (PID: 4040)
- chrome.exe (PID: 2752)
- chrome.exe (PID: 2044)
- chrome.exe (PID: 2884)
- chrome.exe (PID: 3648)
- chrome.exe (PID: 1980)
- chrome.exe (PID: 3164)
- chrome.exe (PID: 3524)
- chrome.exe (PID: 3232)
- chrome.exe (PID: 3188)
- chrome.exe (PID: 2564)
- chrome.exe (PID: 4020)
- chrome.exe (PID: 4008)
- chrome.exe (PID: 1820)
- chrome.exe (PID: 2904)
- chrome.exe (PID: 2860)
- chrome.exe (PID: 1340)
- chrome.exe (PID: 3564)
- chrome.exe (PID: 3272)
- chrome.exe (PID: 2104)
- chrome.exe (PID: 2988)
- chrome.exe (PID: 1572)
- chrome.exe (PID: 2436)
- chrome.exe (PID: 3088)
- chrome.exe (PID: 3080)
- chrome.exe (PID: 3084)
- chrome.exe (PID: 2204)
- chrome.exe (PID: 3876)
- chrome.exe (PID: 2668)
- chrome.exe (PID: 3620)
- chrome.exe (PID: 3856)
- chrome.exe (PID: 2964)
- chrome.exe (PID: 3184)
- chrome.exe (PID: 584)
- chrome.exe (PID: 1544)
- chrome.exe (PID: 3848)
- chrome.exe (PID: 852)
- chrome.exe (PID: 3784)
- chrome.exe (PID: 3968)
- chrome.exe (PID: 2472)
- chrome.exe (PID: 4024)
- chrome.exe (PID: 3828)
- chrome.exe (PID: 3084)
- chrome.exe (PID: 2988)
- chrome.exe (PID: 752)
- chrome.exe (PID: 2236)
- chrome.exe (PID: 1988)
- chrome.exe (PID: 3280)
- chrome.exe (PID: 2540)
- chrome.exe (PID: 2800)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 3668)
- chrome.exe (PID: 3156)
- chrome.exe (PID: 3064)
- chrome.exe (PID: 3036)
- chrome.exe (PID: 2536)
- chrome.exe (PID: 1416)
- chrome.exe (PID: 3396)
- chrome.exe (PID: 1540)
- chrome.exe (PID: 3916)
- chrome.exe (PID: 3256)
- chrome.exe (PID: 1564)
- chrome.exe (PID: 2964)
- chrome.exe (PID: 584)
- chrome.exe (PID: 3236)
- chrome.exe (PID: 2136)
- chrome.exe (PID: 672)
- chrome.exe (PID: 1312)
- chrome.exe (PID: 3960)
- chrome.exe (PID: 3384)
- chrome.exe (PID: 892)
- chrome.exe (PID: 2788)
- chrome.exe (PID: 3444)
- chrome.exe (PID: 3592)
- chrome.exe (PID: 3288)
- chrome.exe (PID: 2892)
- chrome.exe (PID: 3952)
- chrome.exe (PID: 3920)
- chrome.exe (PID: 2908)
- chrome.exe (PID: 4016)
- chrome.exe (PID: 3972)
- chrome.exe (PID: 2208)
- chrome.exe (PID: 3928)
- chrome.exe (PID: 2320)
- chrome.exe (PID: 2516)
- chrome.exe (PID: 940)
- chrome.exe (PID: 2608)
- chrome.exe (PID: 584)
- chrome.exe (PID: 2420)
- chrome.exe (PID: 3236)
- icacls.exe (PID: 1208)
- chrome.exe (PID: 1148)
- chrome.exe (PID: 3064)
- chrome.exe (PID: 672)
- chrome.exe (PID: 4032)
- chrome.exe (PID: 3720)
- chrome.exe (PID: 2312)
- chrome.exe (PID: 1228)
- chrome.exe (PID: 1828)
- chrome.exe (PID: 3284)
- chrome.exe (PID: 2180)
- chrome.exe (PID: 2888)
- chrome.exe (PID: 3804)
- chrome.exe (PID: 3388)
- svchost.exe (PID: 872)
- chrome.exe (PID: 936)
Reads the computer name
- chrome.exe (PID: 960)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 4040)
- chrome.exe (PID: 2796)
- chrome.exe (PID: 3188)
- chrome.exe (PID: 1340)
- chrome.exe (PID: 1572)
- chrome.exe (PID: 3084)
- chrome.exe (PID: 2668)
- chrome.exe (PID: 3184)
- chrome.exe (PID: 2964)
- chrome.exe (PID: 3620)
- chrome.exe (PID: 4024)
- chrome.exe (PID: 3280)
- rundll32.exe (PID: 2864)
- chrome.exe (PID: 2540)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 2800)
- chrome.exe (PID: 1540)
- chrome.exe (PID: 892)
- chrome.exe (PID: 2788)
- chrome.exe (PID: 4016)
- chrome.exe (PID: 3928)
- chrome.exe (PID: 584)
- chrome.exe (PID: 2420)
- chrome.exe (PID: 3236)
- icacls.exe (PID: 1208)
- chrome.exe (PID: 3064)
Manual execution by user
- chrome.exe (PID: 3476)
- chrome.exe (PID: 3184)
- chrome.exe (PID: 2540)
Reads settings of System Certificates
- chrome.exe (PID: 960)
- chromeinstall-8u341.exe (PID: 3752)
- chrome.exe (PID: 3184)
- msiexec.exe (PID: 4080)
- chrome.exe (PID: 2540)
Reads the date of Windows installation
- chrome.exe (PID: 1572)
- chrome.exe (PID: 2420)
Checks Windows Trust Settings
- chromeinstall-8u341.exe (PID: 3752)
- msiexec.exe (PID: 4080)
- chrome.exe (PID: 2540)
Creates files in the program directory
- msiexec.exe (PID: 4080)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3332)
- MsiExec.exe (PID: 3620)
- MsiExec.exe (PID: 2344)
- MsiExec.exe (PID: 3124)
Creates a software uninstall entry
- msiexec.exe (PID: 4080)
Searches for installed software
- msiexec.exe (PID: 4080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .spe | | | SPSS Extension (47.2) |
|---|---|---|
| .jar | | | Java Archive (22.8) |
| .zip | | | ZIP compressed archive (6.2) |
EXIF
ZIP
| ZipFileName: | META-INF/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | 2 |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2022:05:25 14:33:26 |
| ZipCompression: | Deflated |
| ZipBitFlag: | 0x0800 |
| ZipRequiredVersion: | 10 |
Total processes
197
Monitored processes
144
Malicious processes
27
Suspicious processes
2
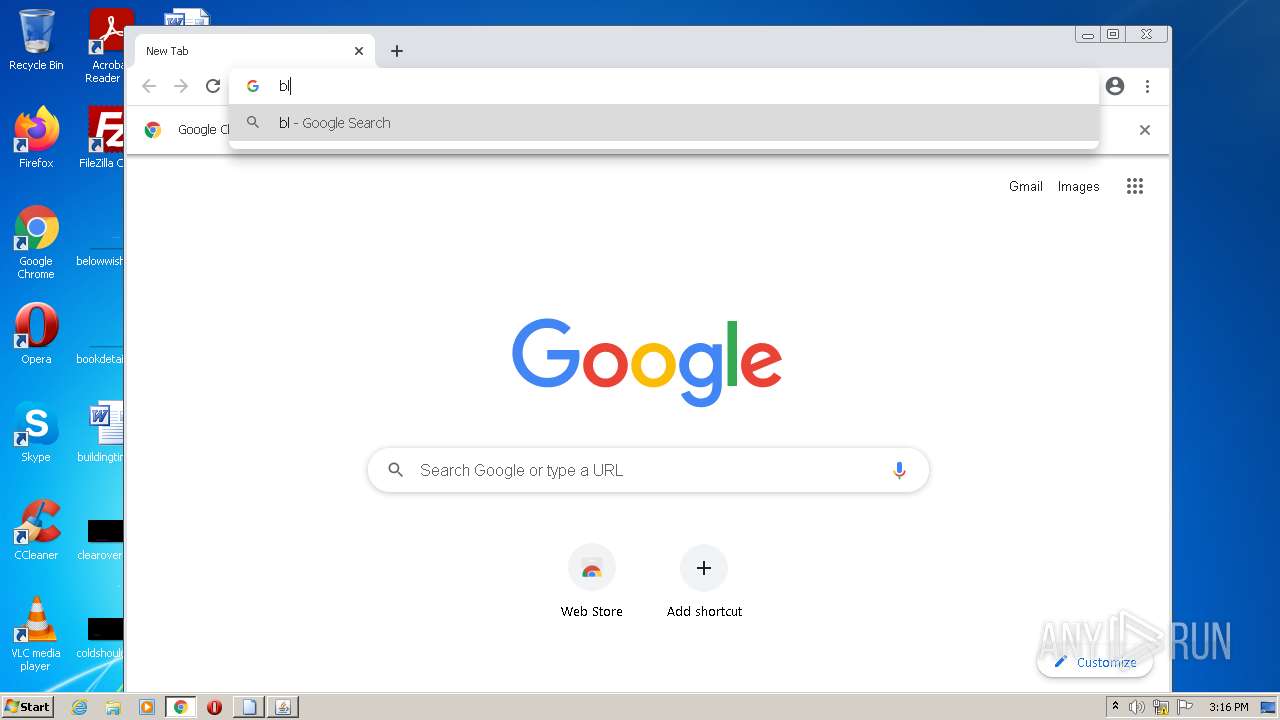
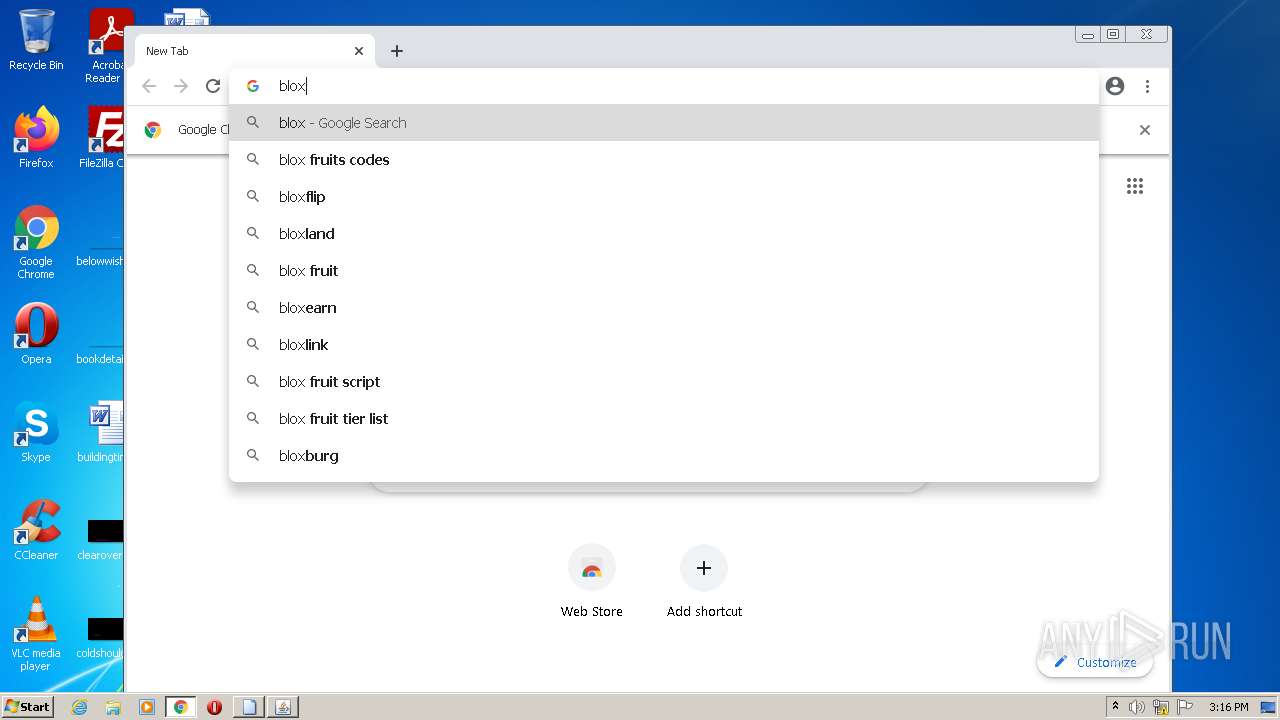
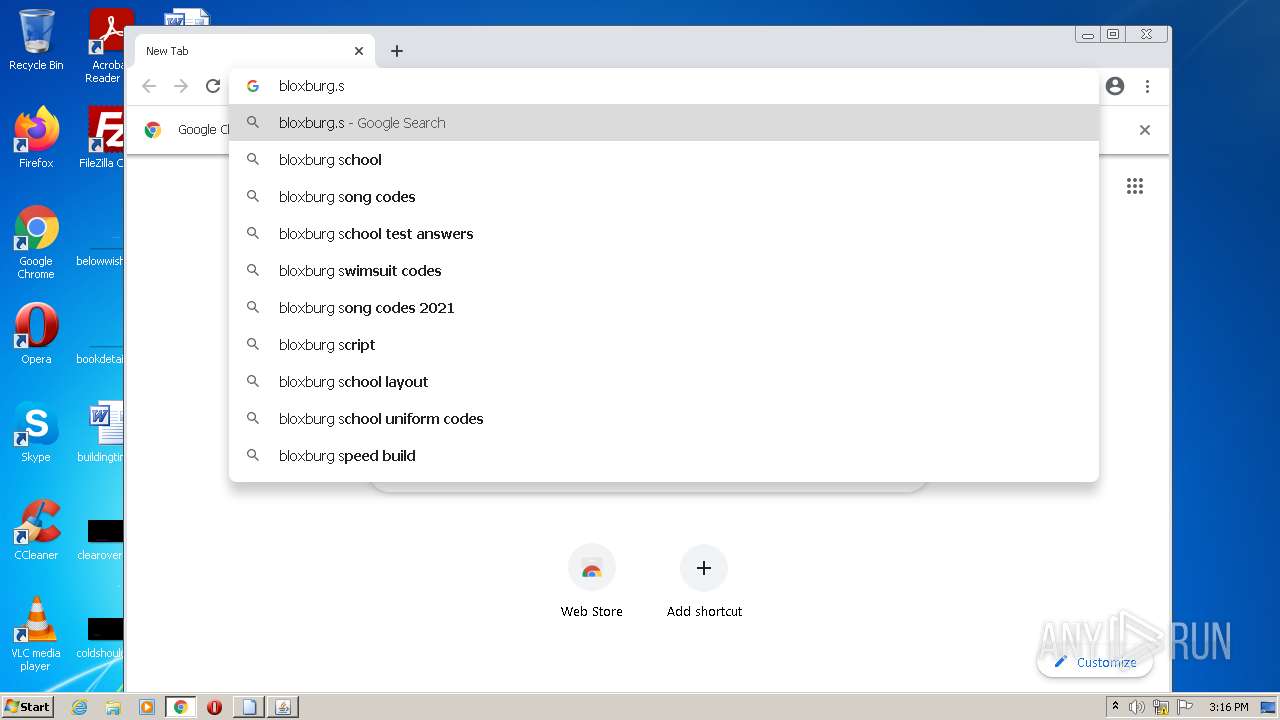
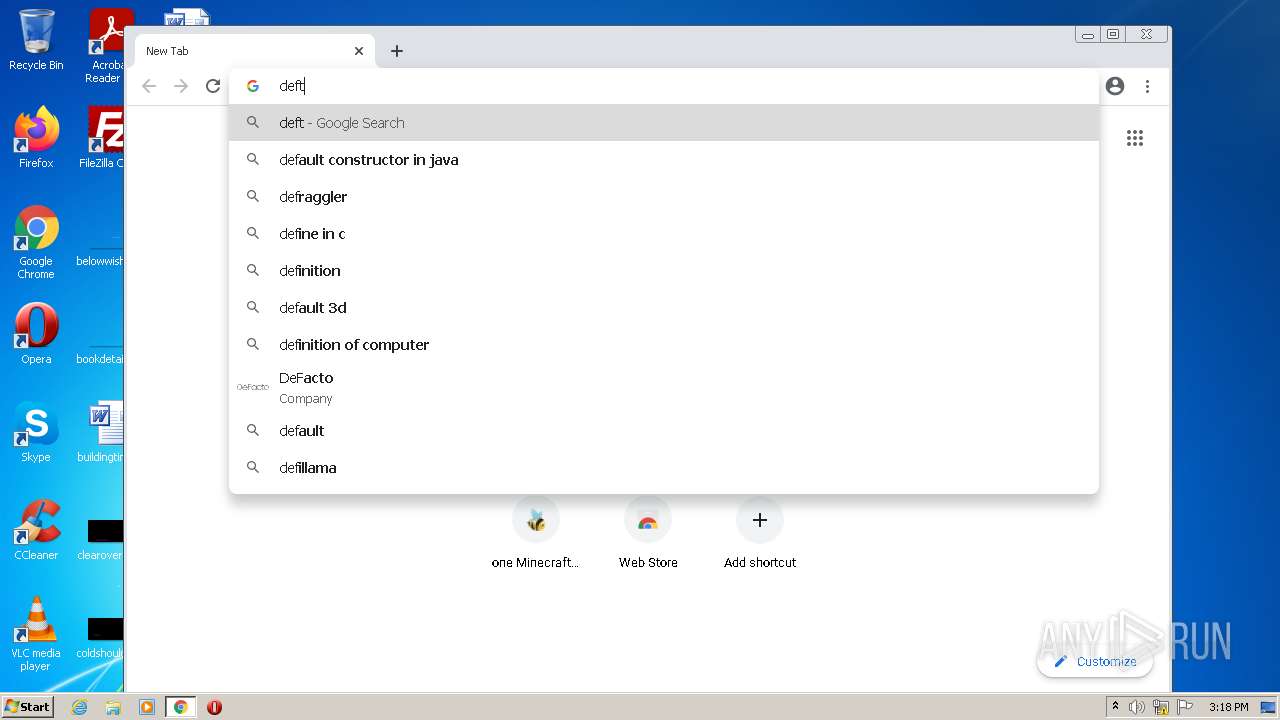
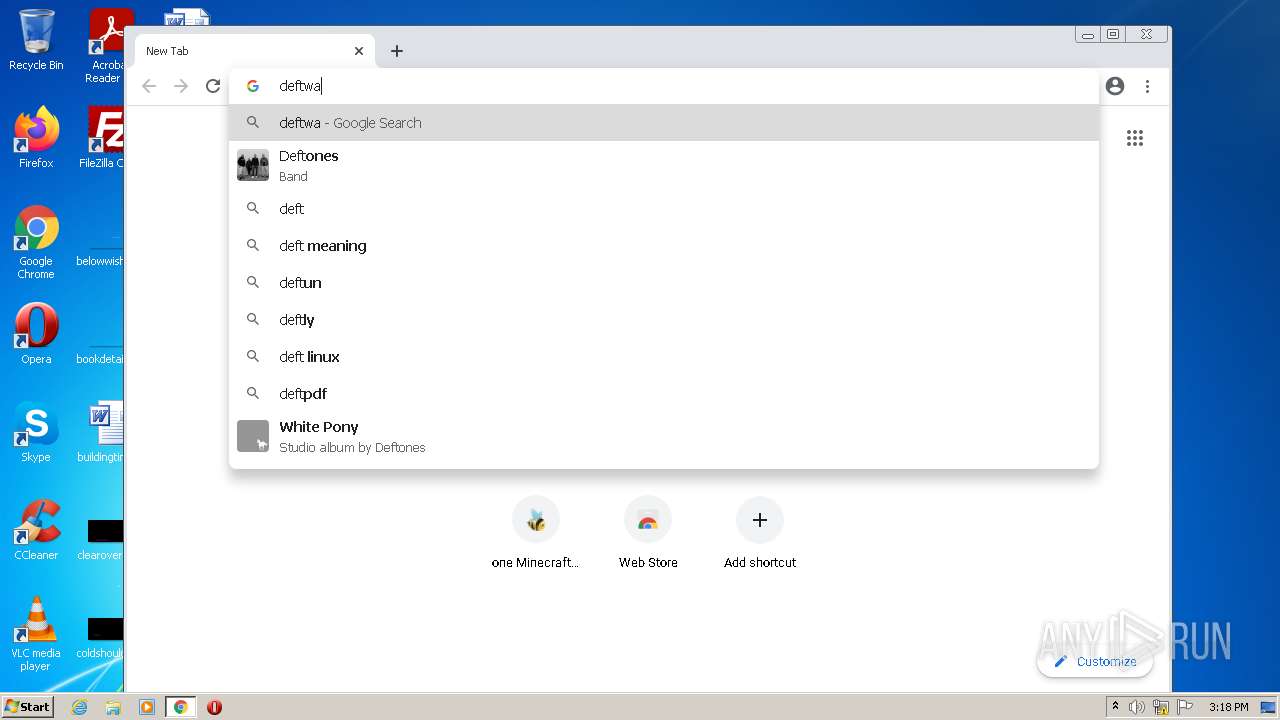
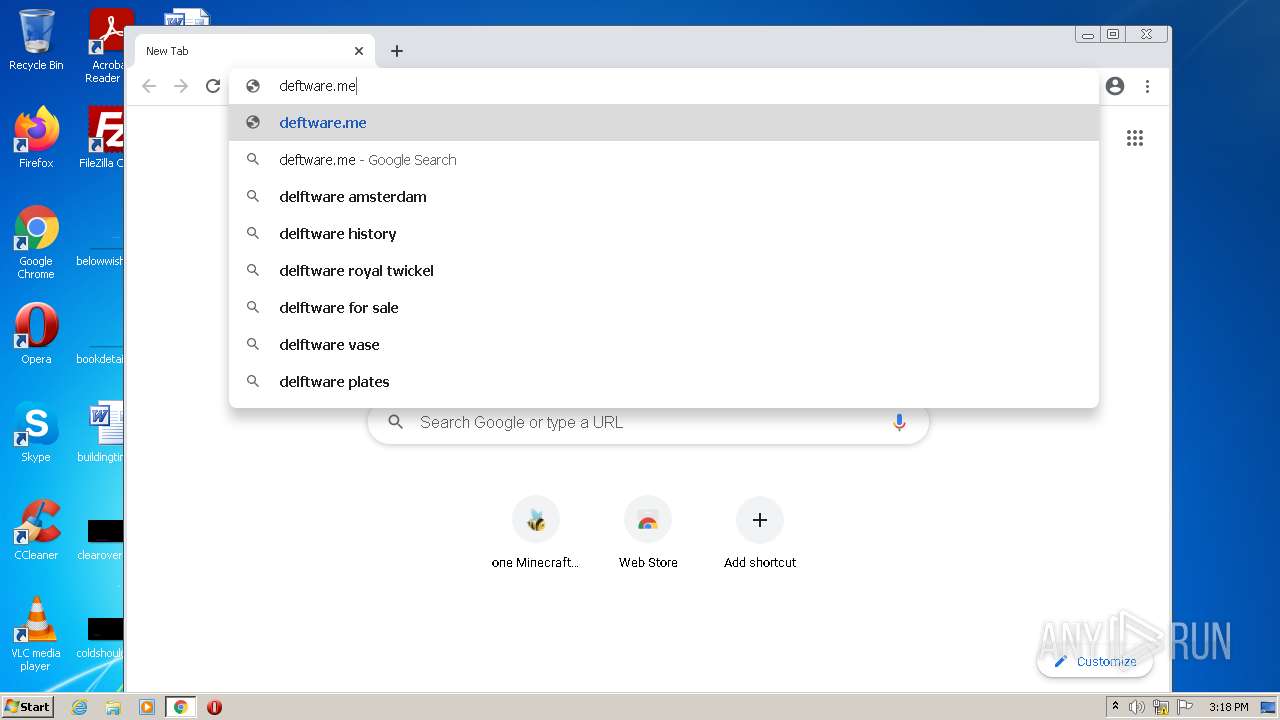
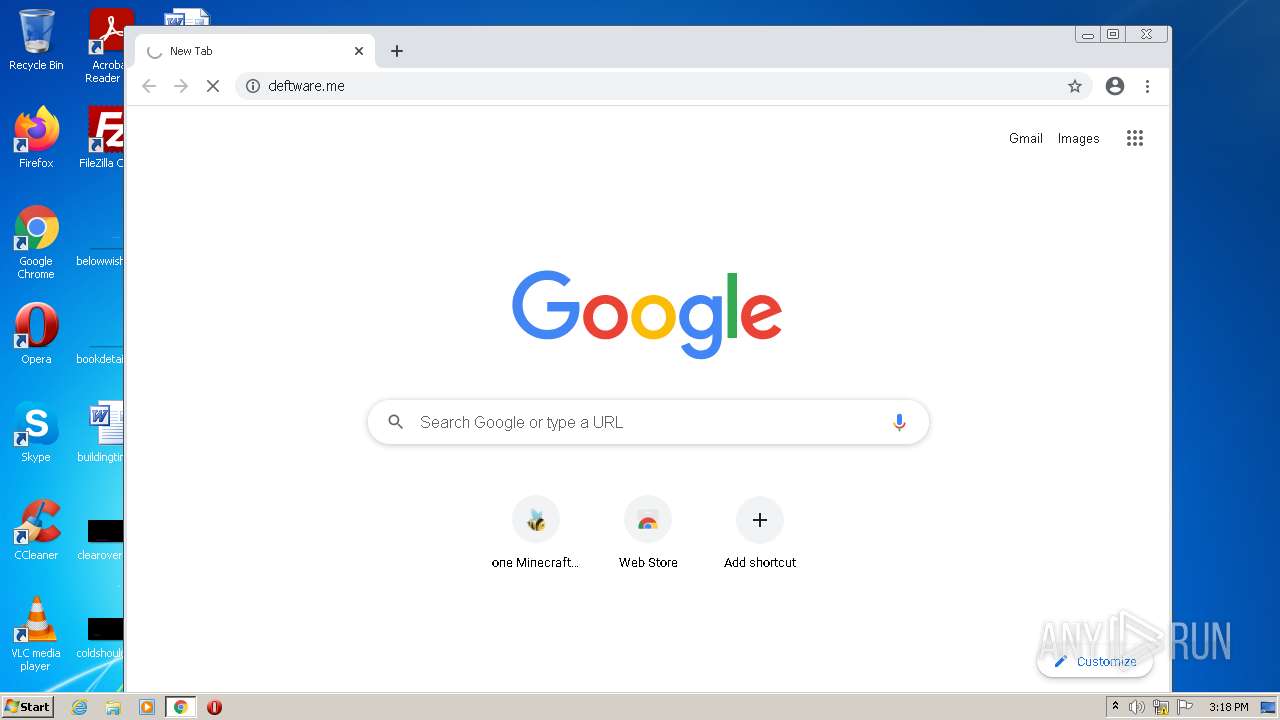
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --field-trial-handle=1032,5333350479319346494,8510092043079161866,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1780 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1076,13855209234112350979,16113751657401082108,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3696 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1076,13855209234112350979,16113751657401082108,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4284 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1076,13855209234112350979,16113751657401082108,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4228 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1076,13855209234112350979,16113751657401082108,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1016 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1032,5333350479319346494,8510092043079161866,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3984 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 752 | C:\Windows\system32\MsiExec.exe -Embedding 38B20076DE224EDB7C63FCBD54032745 E Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 804 | C:\Windows\System32\svchost.exe -k LocalSystemNetworkRestricted | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,5333350479319346494,8510092043079161866,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2376 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 872 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\system32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
112 067
Read events
60 174
Write events
32 380
Delete events
19 513
Modification events
| (PID) Process: | (1080) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | Puebzr |
Value: 00000000160000002F000000116B1600000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF602E757955A3D80100000000 | |||
| (PID) Process: | (1080) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000490100007B0200004B6B17013F0000004A0000008E0F0D004D006900630072006F0073006F00660074002E0049006E007400650072006E00650074004500780070006C006F007200650072002E00440065006600610075006C007400000028003E004000A4E75102B8E651020000000000000000000000000000080274E45102000008026CE25102000000000000D26CFFFFFFFF705911750000000000000000A4E251027C900D75000400000000000008E35102FFFFFFFF38EA7000FFFFFFFF080A7400D80E740030EA7000D4E25102F7AF3D7680D0707614F05102081D3E76E4613E766820700008E351020000000071000000BBF2CB00E8E25102A1693E766820700008E351020000000014E551023F613E766820700008E3510200000400000000800400000026E4510298E351025DA5147726E45102D26E147779A51477D6794D7526E4510210E65102000100006400610072E3510226E451026F0061006D0069006E0067005C006D006900630072006F0073006F0066007400CCE351023400000080E35102DE70310033003300350033003800310030003000F8E551025A000000A0E351021DA71477D6610E02D4E351025A00000010E651025C00000011000000104F7000084F7000F8E55102C4E3510220E40000D7F3CB00D0E351025E903E7620E45102D4E3510203943E760000000064561802FCE35102A9933E7664561802A8E45102D8511802BD933E7600000000D8511802A8E4510204E45102000000007200000032AC5D004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E0043006F006E00740072006F006C00500061006E0065006C00000045003700430036004500410037004400320037007D005C0063006D0064002E0065007800650000000000D45D38760000000005000000D80B3902000000000000000000000000000000000000000000000000CB0501AD000000000000000000000000000000000000000000000000000000000000000030E69D01A8323876B8E59D01C0E59D0154E59D0100000000000000000000000000000000480B39020000000005000000D80B390200000000340C390268E59D01B0E59D010000000000000000E8B93902050000002000000000000000000000000400400000001A0098E59D0100000000000000000000000000000000040000009EE69D0110E69D015DA5B3779EE69D01D26EB37779A5B377114526769EE69D0188E89D0104000000C6E69D0138E69D015DA5B377C6E69D01D26EB37779A5B37739452676C6E69D01B0E89D0100010000E8FE1C0012E69D01C6E69D0168E69D015DA5310033003300350033003800310011000000104F1D00084F1D001AE79D018CE69D015DA5B37774E60000B777588D24E69D015E90D47674E69D0128E69D010394D47600000000D422E60250E69D01A993D476D422E602FCE69D01481EE602BD93D47600000000481EE602FCE69D0158E69D01000000007200000032AC5D004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E0043006F006E00740072006F006C00500061006E0065006C00000045003700430036004500410037004400320037007D005C0063006D0064002E0065007800650000000000D45D38760000000005000000D80B3902000000000000000000000000000000000000000000000000CB0501AD000000000000000000000000000000000000000000000000000000000000000030E69D01A8323876B8E59D01C0E59D0154E59D0100000000000000000000000000000000480B39020000000005000000D80B390200000000340C390268E59D01B0E59D010000000000000000E8B93902050000002000000000000000000000000400400000001A0098E59D0100000000000000000000000000000000040000009EE69D0110E69D015DA5B3779EE69D01D26EB37779A5B377114526769EE69D0188E89D0104000000C6E69D0138E69D015DA5B377C6E69D01D26EB37779A5B37739452676C6E69D01B0E89D0100010000E8FE1C0012E69D01C6E69D0168E69D015DA5310033003300350033003800310011000000104F1D00084F1D001AE79D018CE69D015DA5B37774E60000B777588D24E69D015E90D47674E69D0128E69D010394D47600000000D422E60250E69D01A993D476D422E602FCE69D01481EE602BD93D47600000000481EE602FCE69D0158E69D01 | |||
| (PID) Process: | (1080) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Tbbtyr Puebzr.yax |
Value: 000000000E000000000000000D000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF602E757955A3D80100000000 | |||
| (PID) Process: | (1080) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000B500000000000000B40000003E000000000000003E0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C0049006E007400650072006E006500740020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000987880574F8C6244BB6371042380B109000000000000000000006D000000000078AB287598117500084B7600981175000000000000000000DE1C0000E0791401C8D4D60313A91477E01D32BD0C0C00001027000002000000FF560200FCD4D603D8A81477FF560200E07914011CD5D603C05C18029CD5D60300000000A40100005CD500009BC44C010CD5D6035E903E765CD5D60310D5D60303943E76000000004C61180238D5D603A9933E764C611802E4D5D603C05C1802BD933E7600000000C05C1802E4D5D60340D5D6033E000000000000003E0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C0049006E007400650072006E006500740020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000987880574F8C6244BB6371042380B109000000000000000000006D000000000078AB287598117500084B7600981175000000000000000000DE1C0000E0791401C8D4D60313A91477E01D32BD0C0C00001027000002000000FF560200FCD4D603D8A81477FF560200E07914011CD5D603C05C18029CD5D60300000000A40100005CD500009BC44C010CD5D6035E903E765CD5D60310D5D60303943E76000000004C61180238D5D603A9933E764C611802E4D5D603C05C1802BD933E7600000000C05C1802E4D5D60340D5D6033E000000000000003E0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C0049006E007400650072006E006500740020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000987880574F8C6244BB6371042380B109000000000000000000006D000000000078AB287598117500084B7600981175000000000000000000DE1C0000E0791401C8D4D60313A91477E01D32BD0C0C00001027000002000000FF560200FCD4D603D8A81477FF560200E07914011CD5D603C05C18029CD5D60300000000A40100005CD500009BC44C010CD5D6035E903E765CD5D60310D5D60303943E76000000004C61180238D5D603A9933E764C611802E4D5D603C05C1802BD933E7600000000C05C1802E4D5D60340D5D603 | |||
| (PID) Process: | (1080) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Tbbtyr Puebzr.yax |
Value: 000000000E000000000000000E000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF602E757955A3D80100000000 | |||
| (PID) Process: | (1080) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000B500000000000000B50000003E000000000000003E0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C0049006E007400650072006E006500740020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000987880574F8C6244BB6371042380B109000000000000000000006D000000000078AB287598117500084B7600981175000000000000000000DE1C0000E0791401C8D4D60313A91477E01D32BD0C0C00001027000002000000FF560200FCD4D603D8A81477FF560200E07914011CD5D603C05C18029CD5D60300000000A40100005CD500009BC44C010CD5D6035E903E765CD5D60310D5D60303943E76000000004C61180238D5D603A9933E764C611802E4D5D603C05C1802BD933E7600000000C05C1802E4D5D60340D5D6033E000000000000003E0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C0049006E007400650072006E006500740020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000987880574F8C6244BB6371042380B109000000000000000000006D000000000078AB287598117500084B7600981175000000000000000000DE1C0000E0791401C8D4D60313A91477E01D32BD0C0C00001027000002000000FF560200FCD4D603D8A81477FF560200E07914011CD5D603C05C18029CD5D60300000000A40100005CD500009BC44C010CD5D6035E903E765CD5D60310D5D60303943E76000000004C61180238D5D603A9933E764C611802E4D5D603C05C1802BD933E7600000000C05C1802E4D5D60340D5D6033E000000000000003E0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C0049006E007400650072006E006500740020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000987880574F8C6244BB6371042380B109000000000000000000006D000000000078AB287598117500084B7600981175000000000000000000DE1C0000E0791401C8D4D60313A91477E01D32BD0C0C00001027000002000000FF560200FCD4D603D8A81477FF560200E07914011CD5D603C05C18029CD5D60300000000A40100005CD500009BC44C010CD5D6035E903E765CD5D60310D5D60303943E76000000004C61180238D5D603A9933E764C611802E4D5D603C05C1802BD933E7600000000C05C1802E4D5D60340D5D603 | |||
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
Executable files
181
Suspicious files
330
Text files
425
Unknown types
60
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62E3EB33-D94.pma | — | |
MD5:— | SHA256:— | |||
| 960 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9f648edc-afea-4f9d-a362-8f7d493b7eff.tmp | text | |
MD5:— | SHA256:— | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1576 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF107ddc.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF107dcd.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
163
DNS requests
94
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
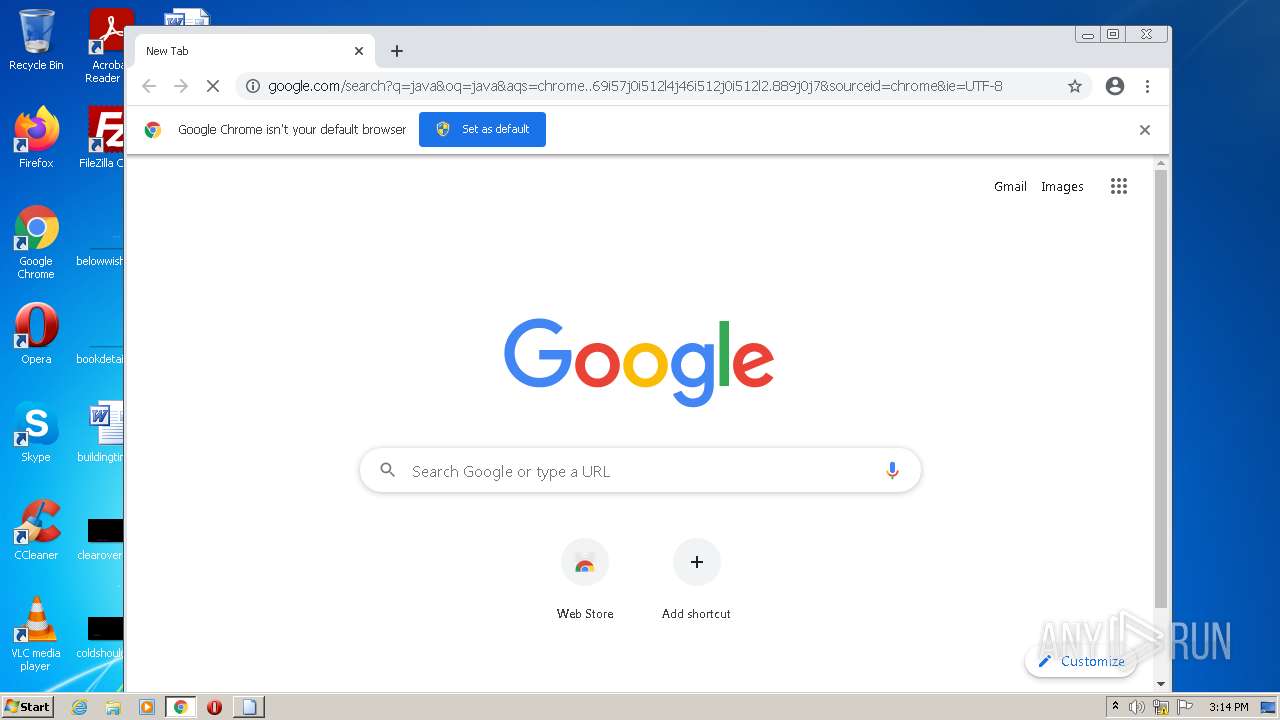
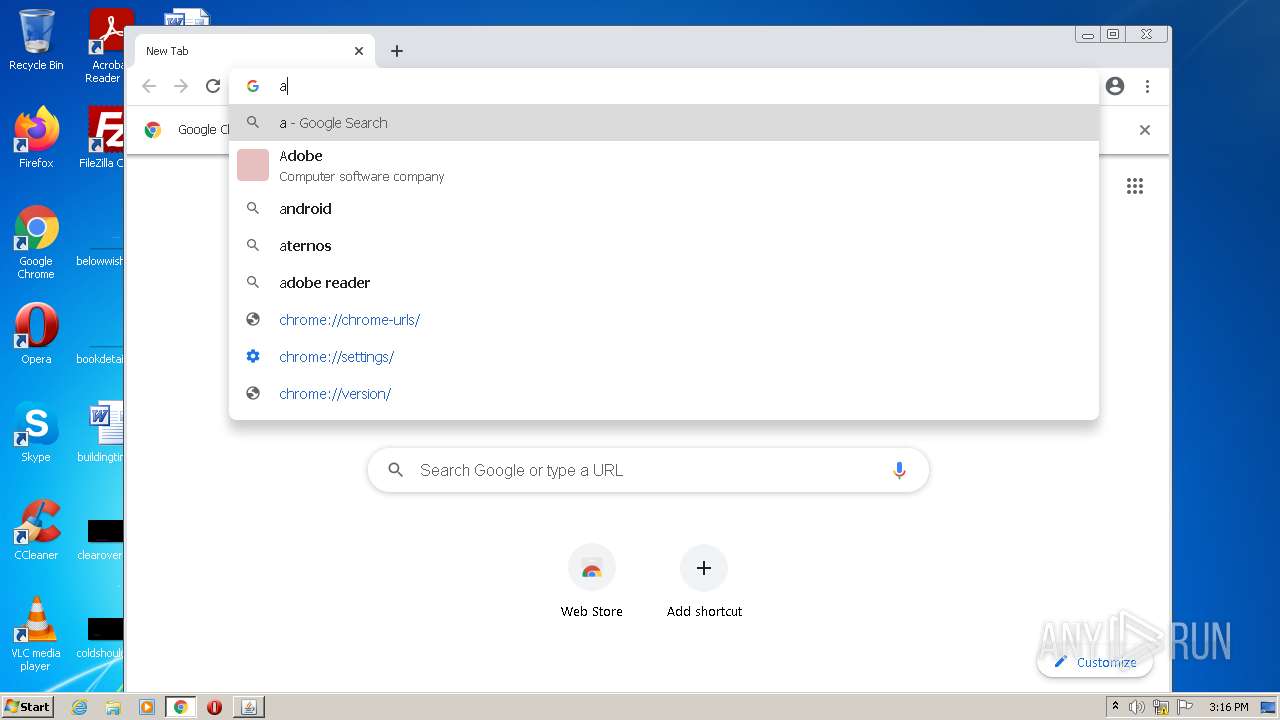
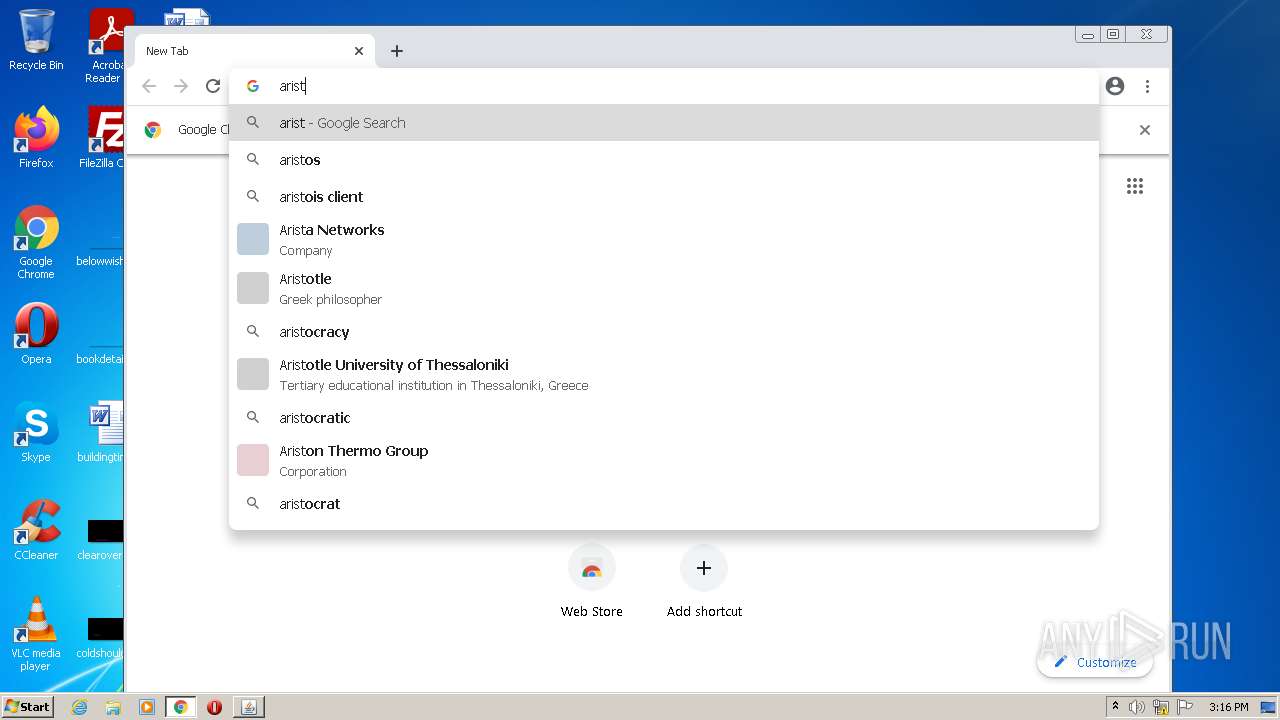
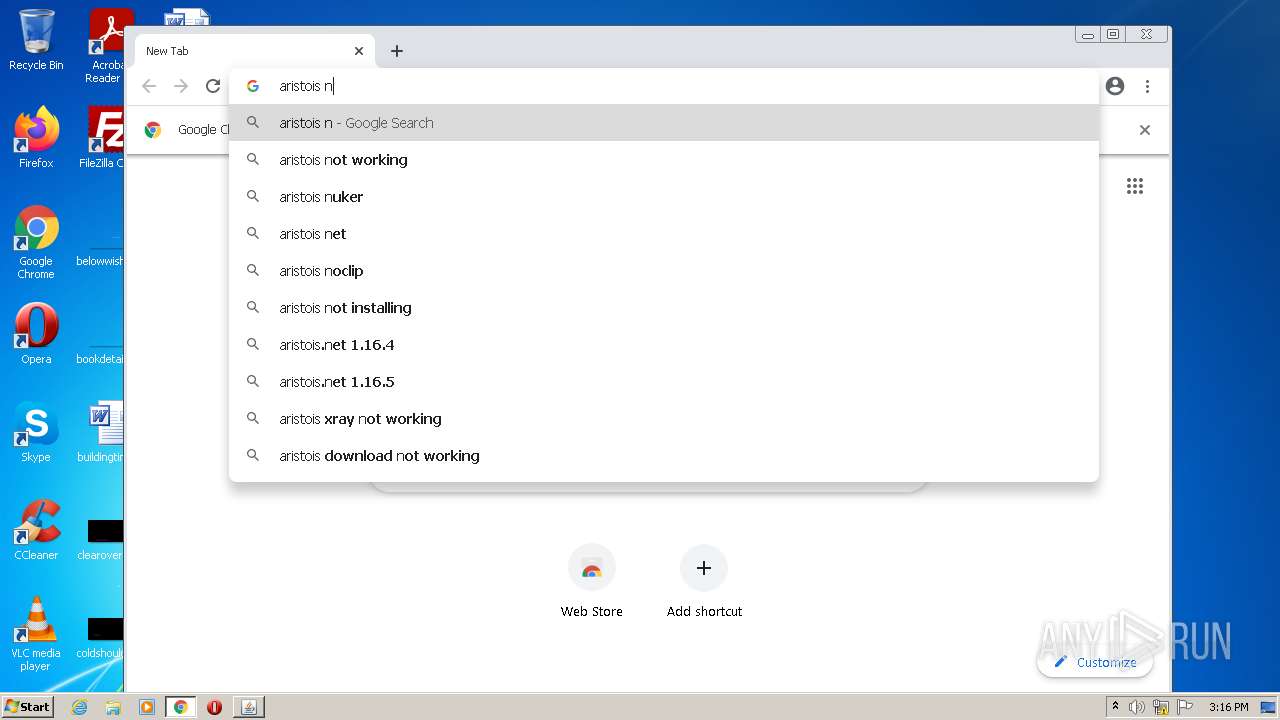
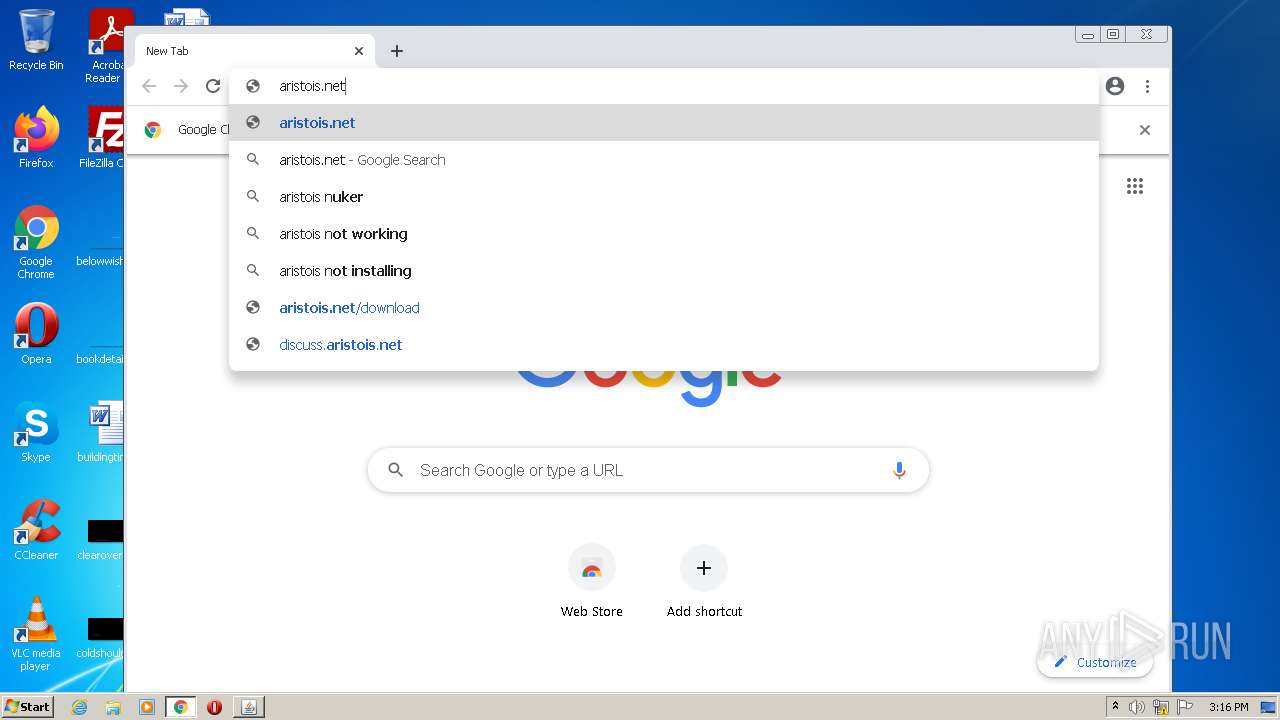
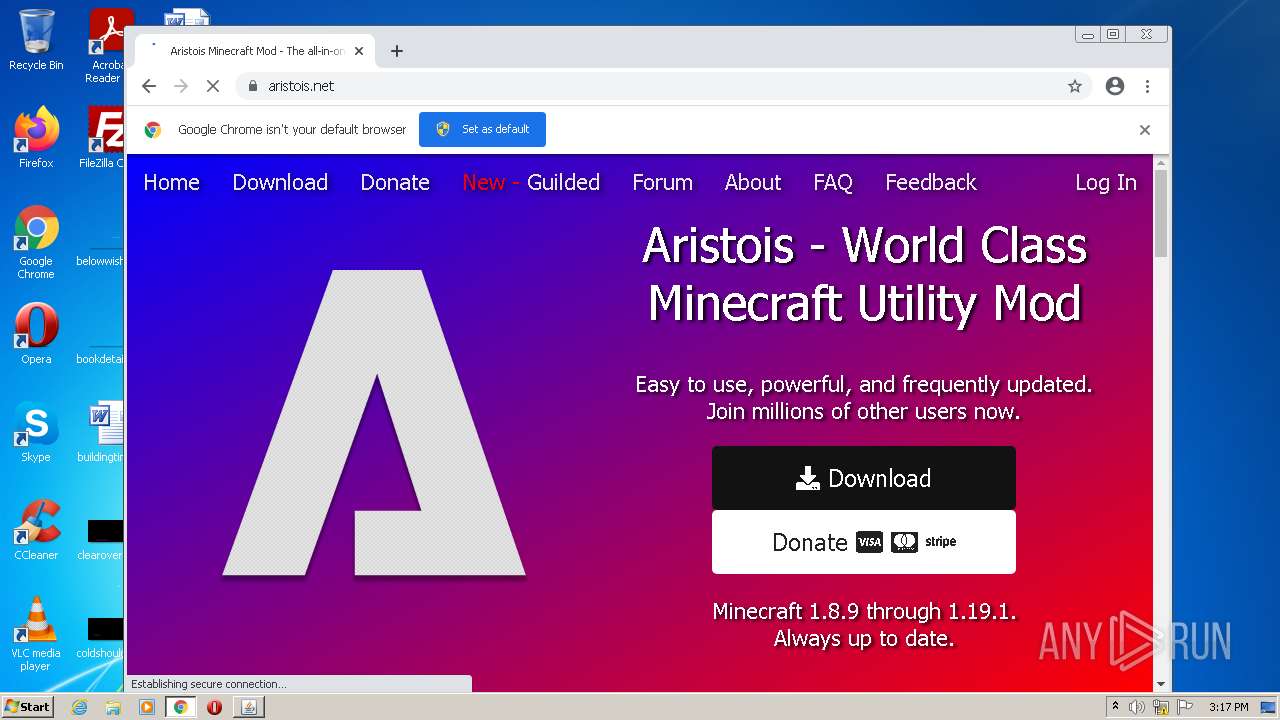
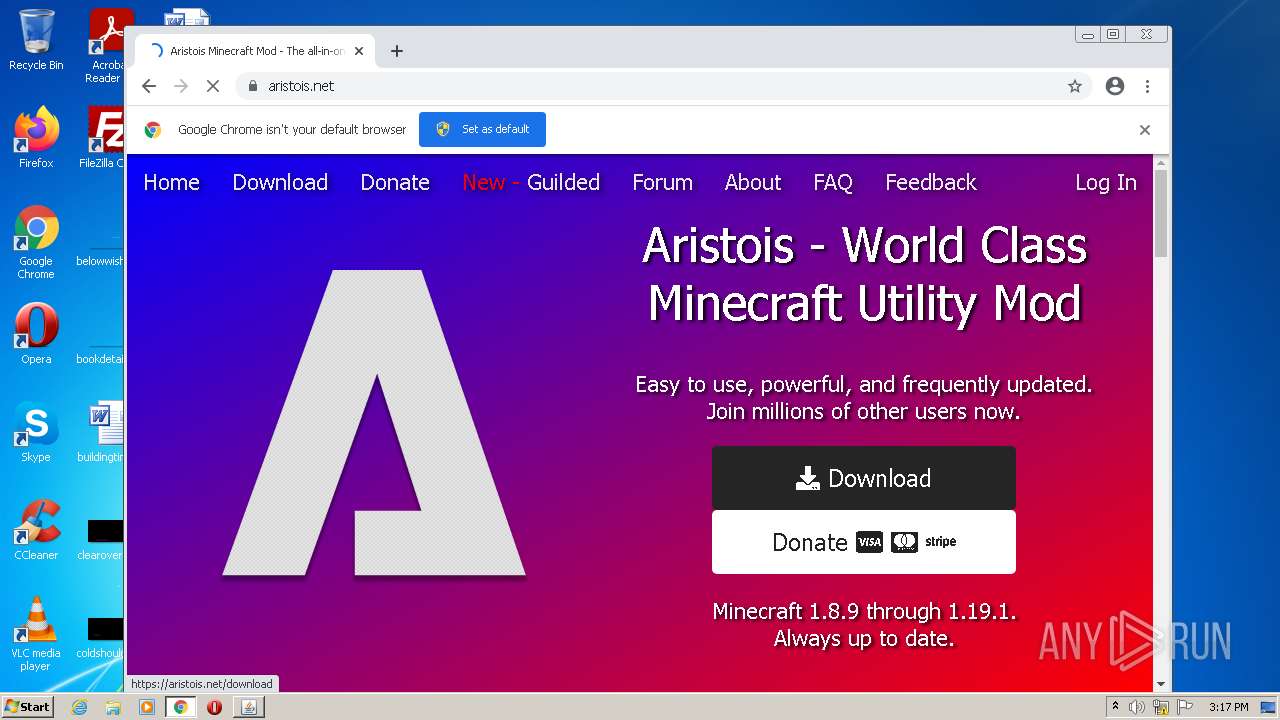
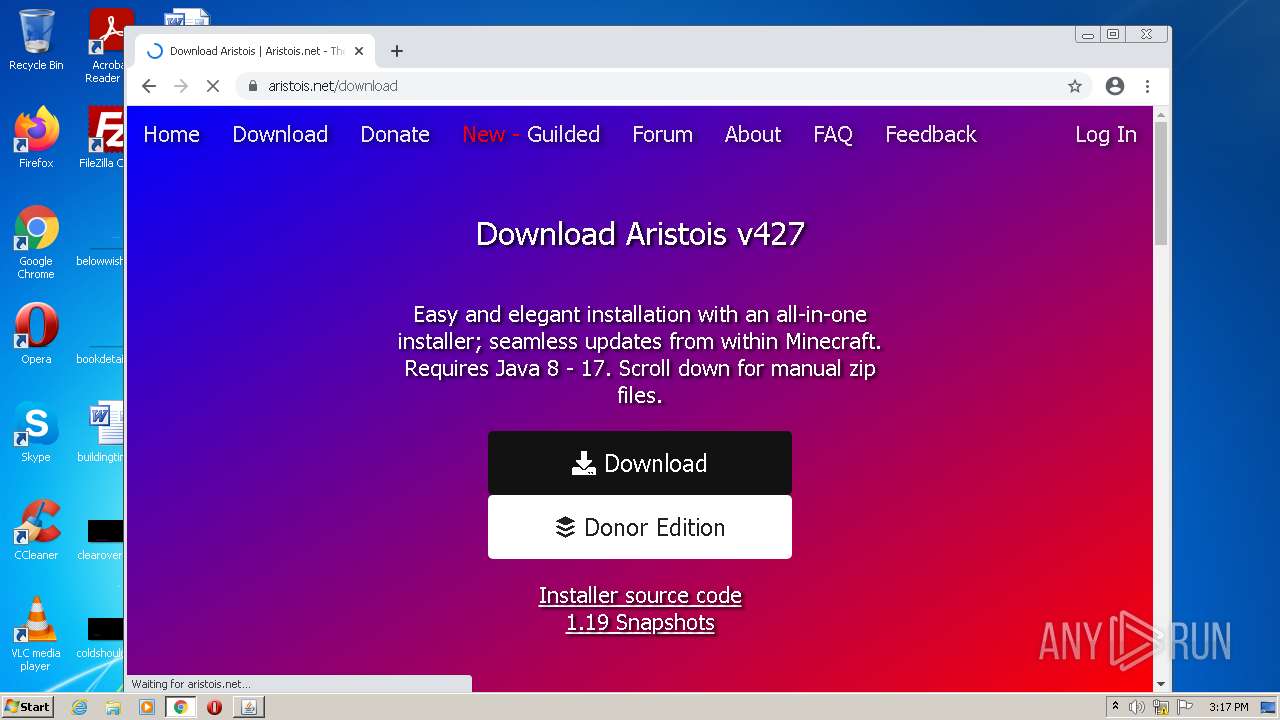
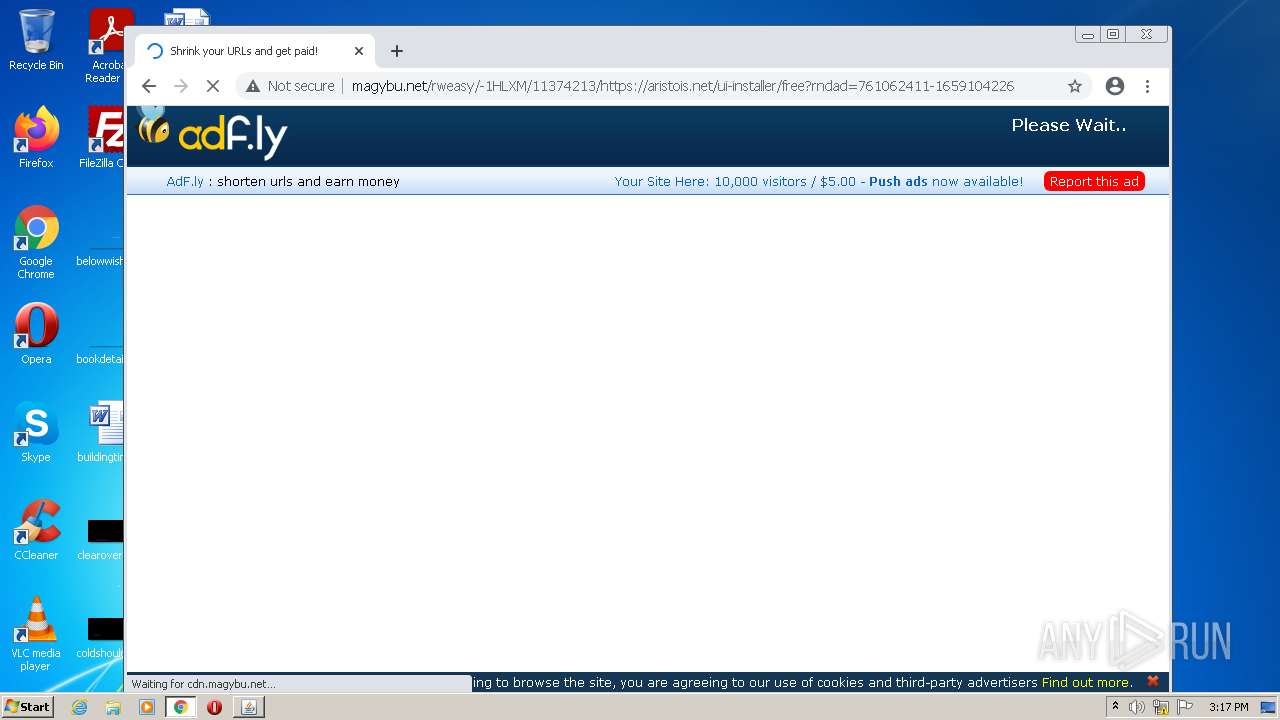
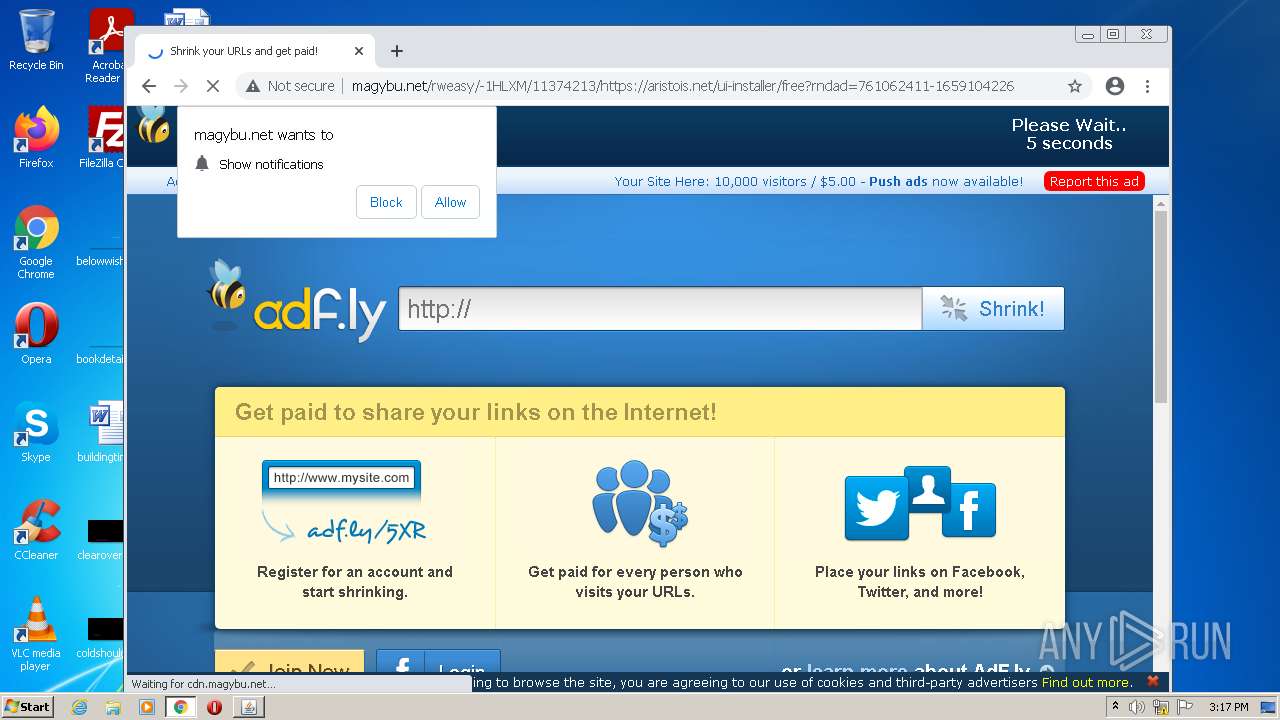
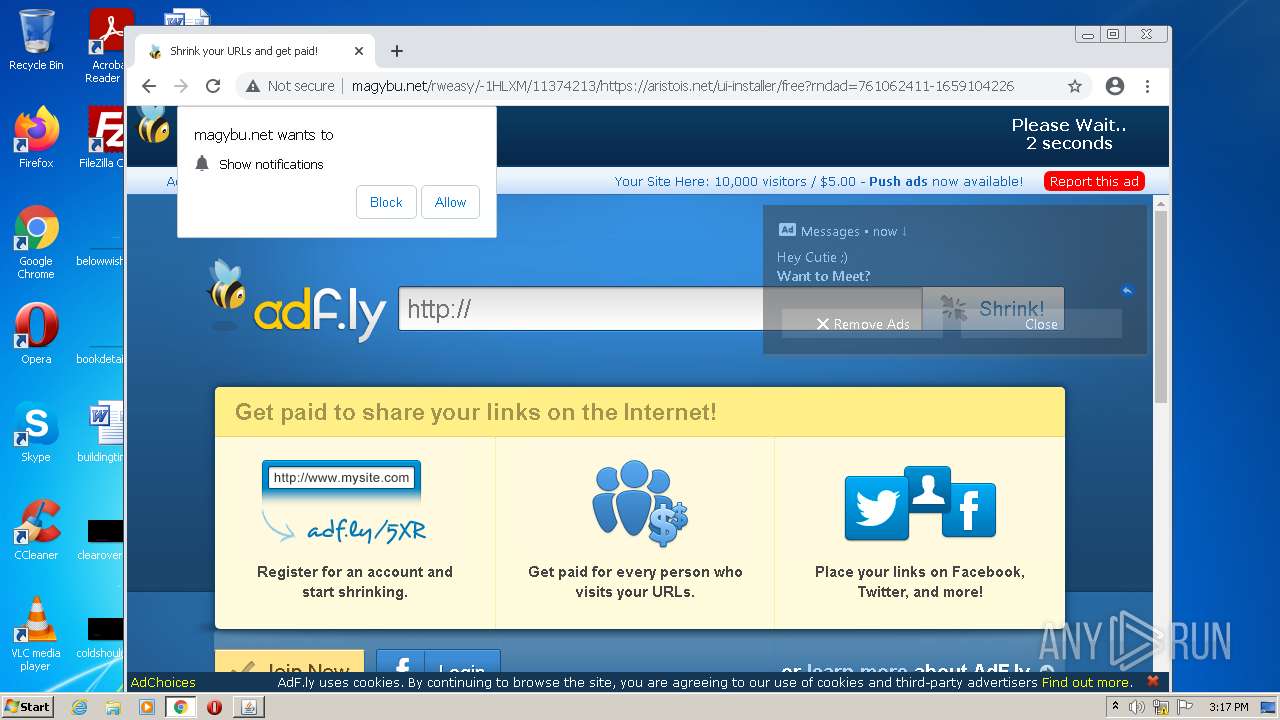
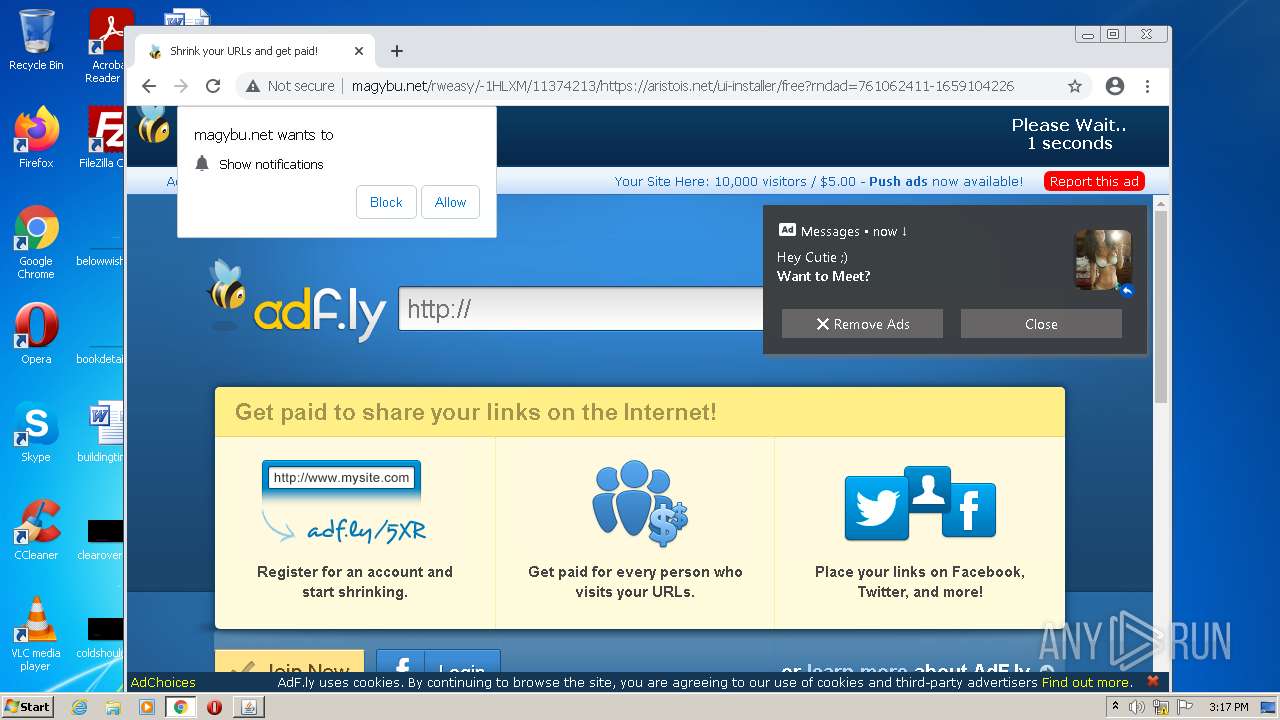
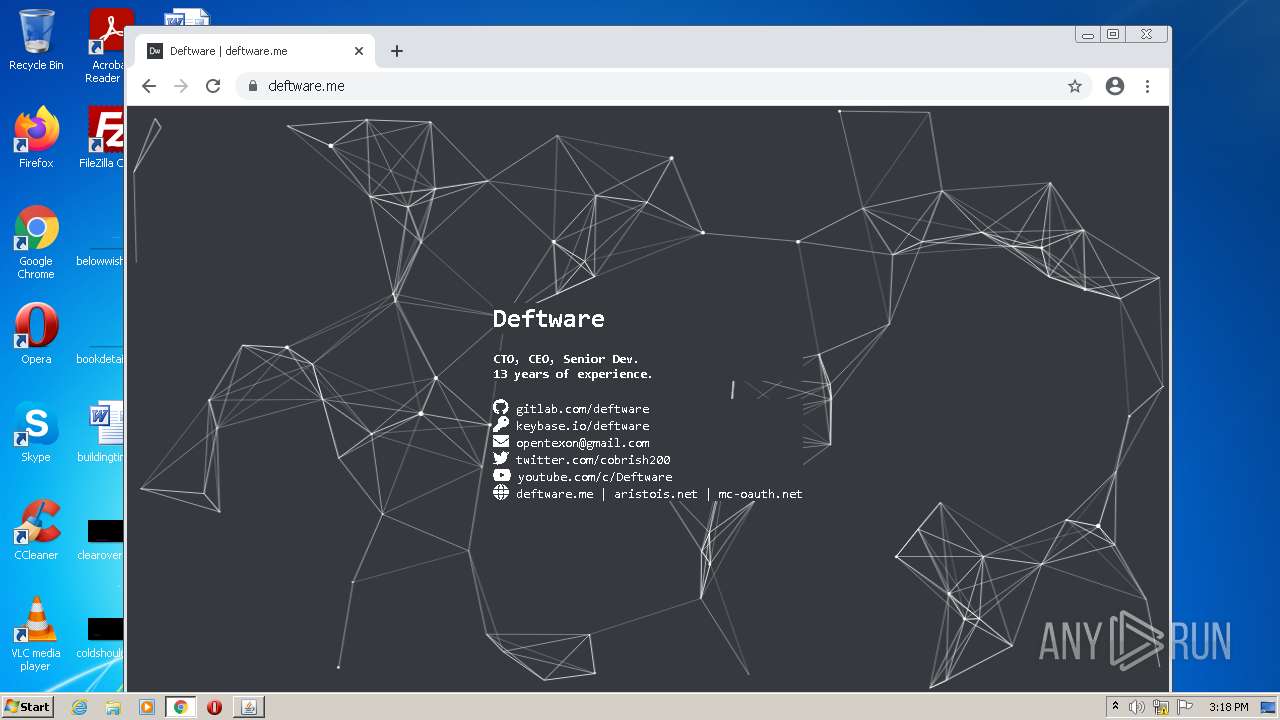
2800 | chrome.exe | GET | 301 | 104.21.43.36:80 | http://aristois.net/ | US | — | — | suspicious |
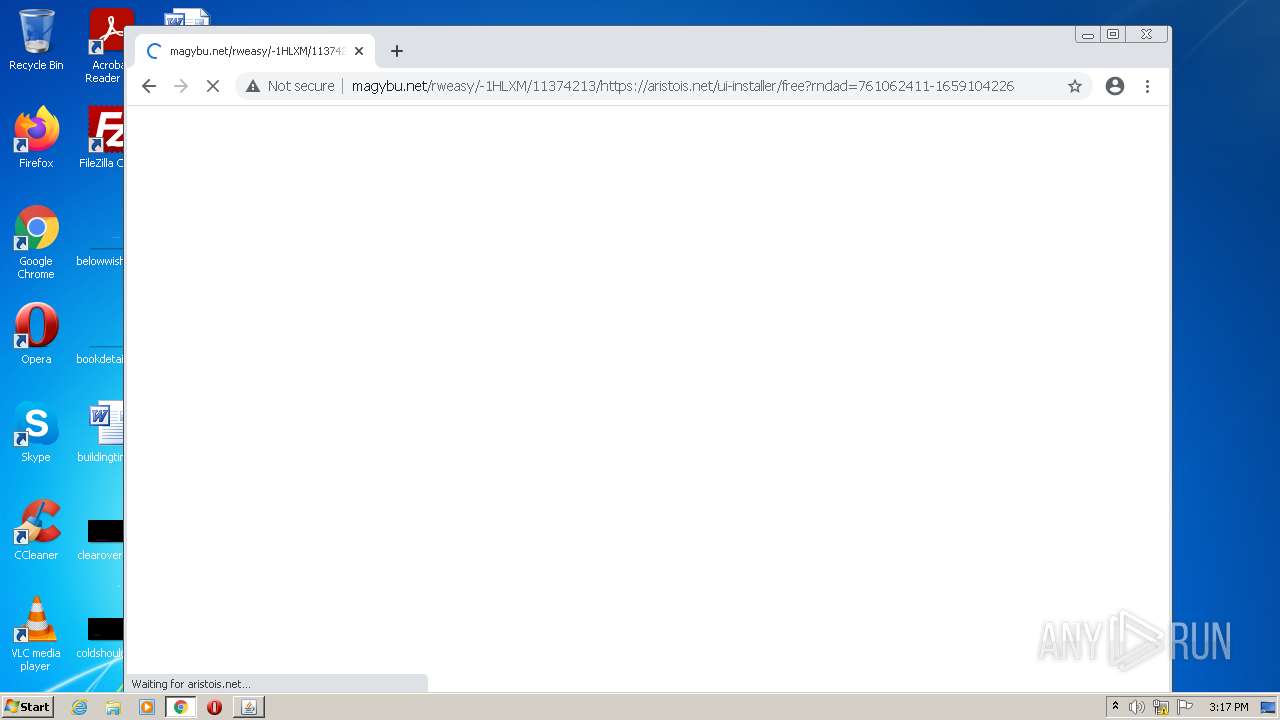
2800 | chrome.exe | GET | 200 | 172.67.203.187:80 | http://cdn.magybu.net/static/js/amvn.js | US | compressed | 82.1 Kb | suspicious |
2800 | chrome.exe | GET | 200 | 18.66.17.5:80 | http://d1a3jb5hjny5s4.cloudfront.net/?hbjad=709056 | US | text | 35.2 Kb | whitelisted |
960 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
3752 | chromeinstall-8u341.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
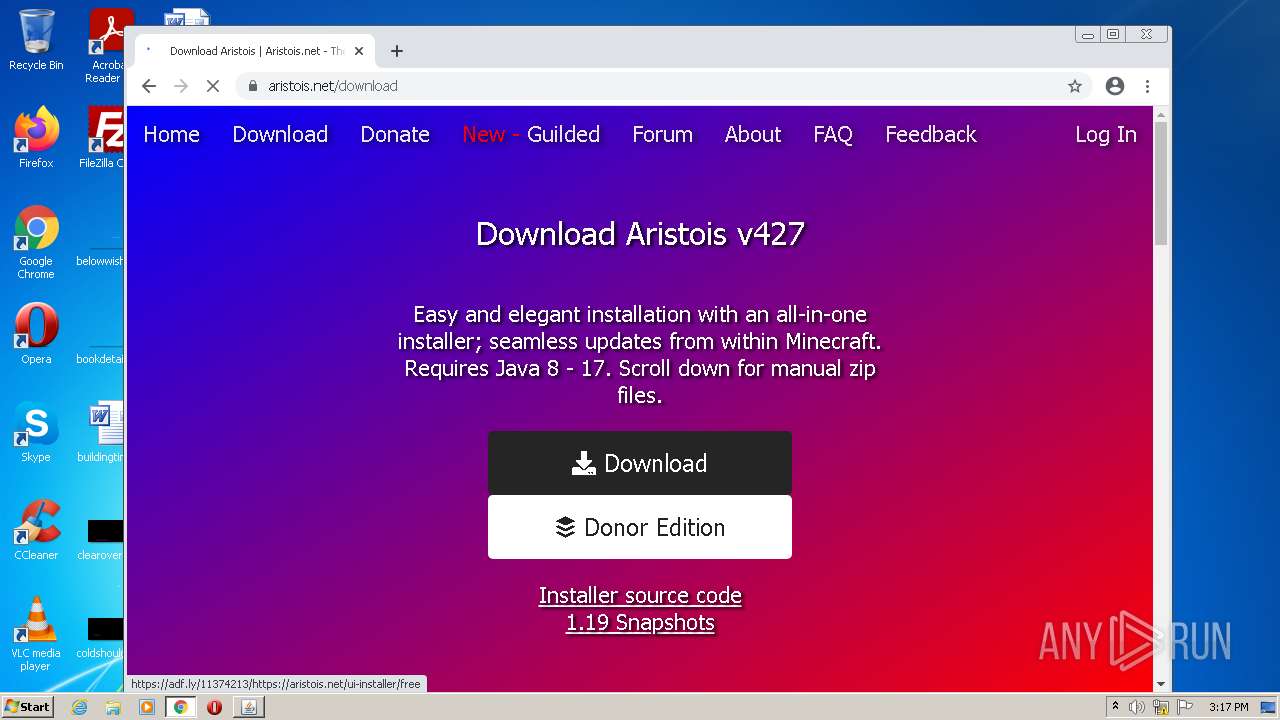
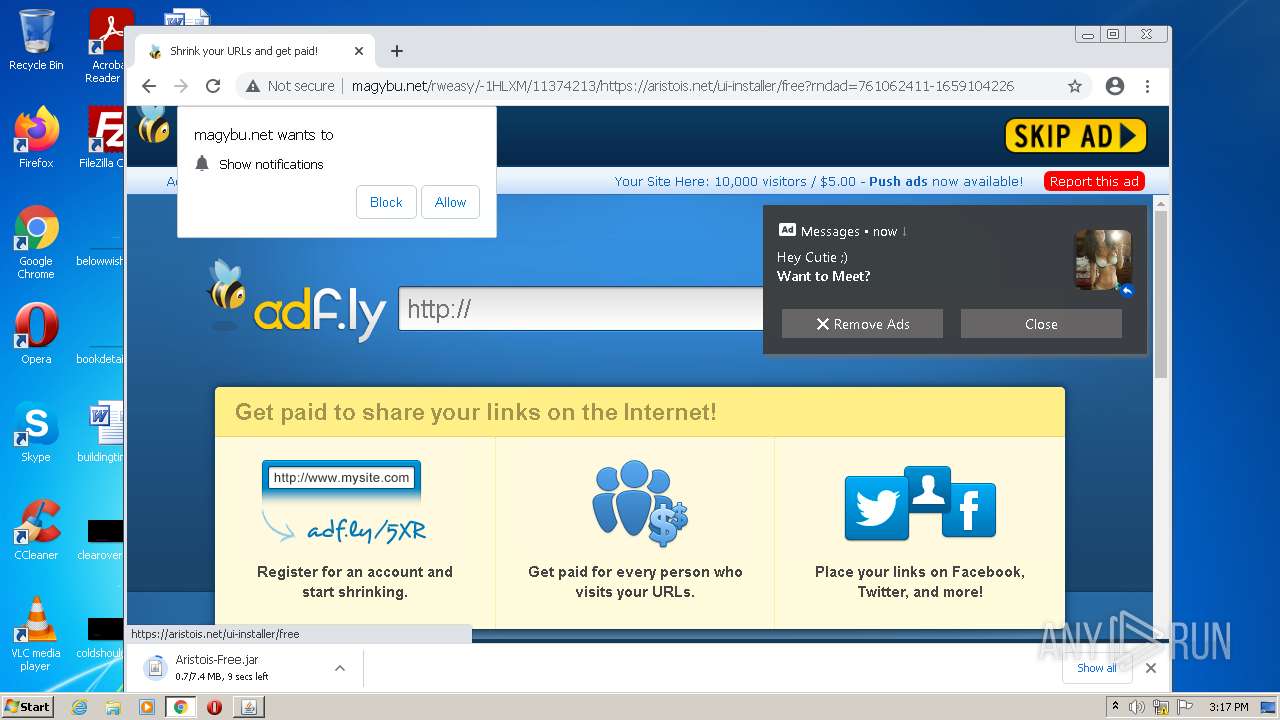
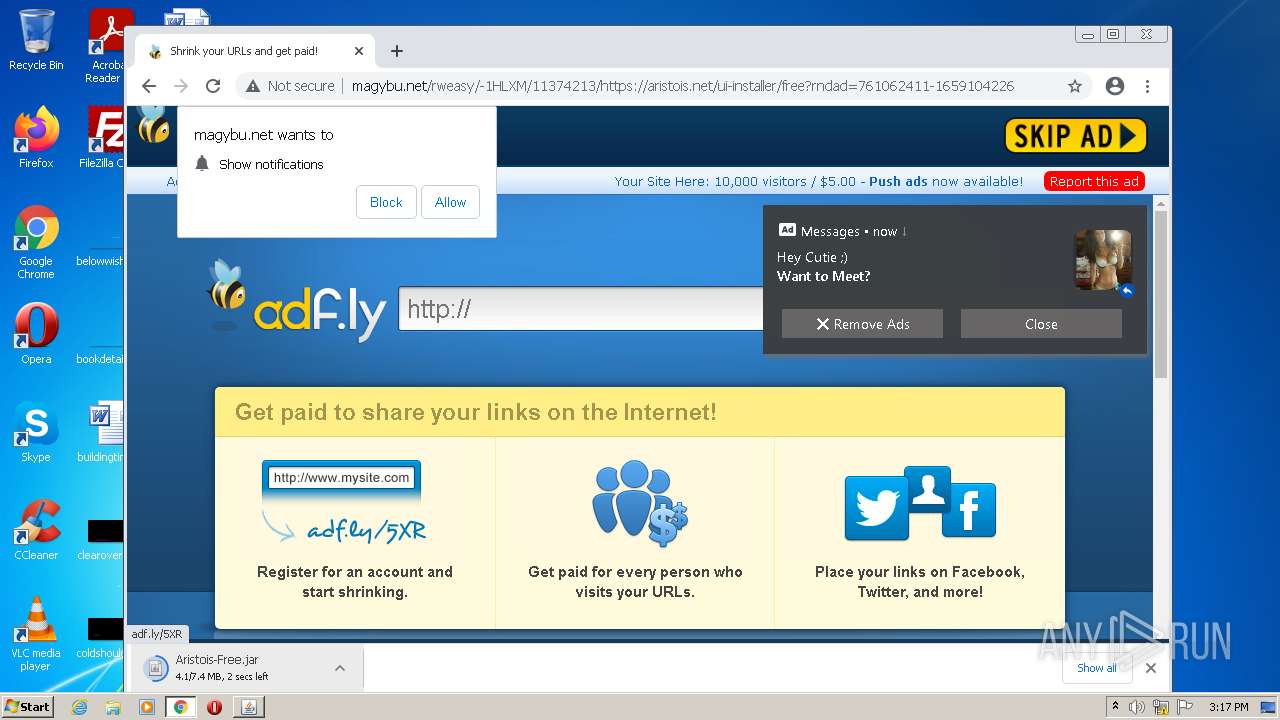
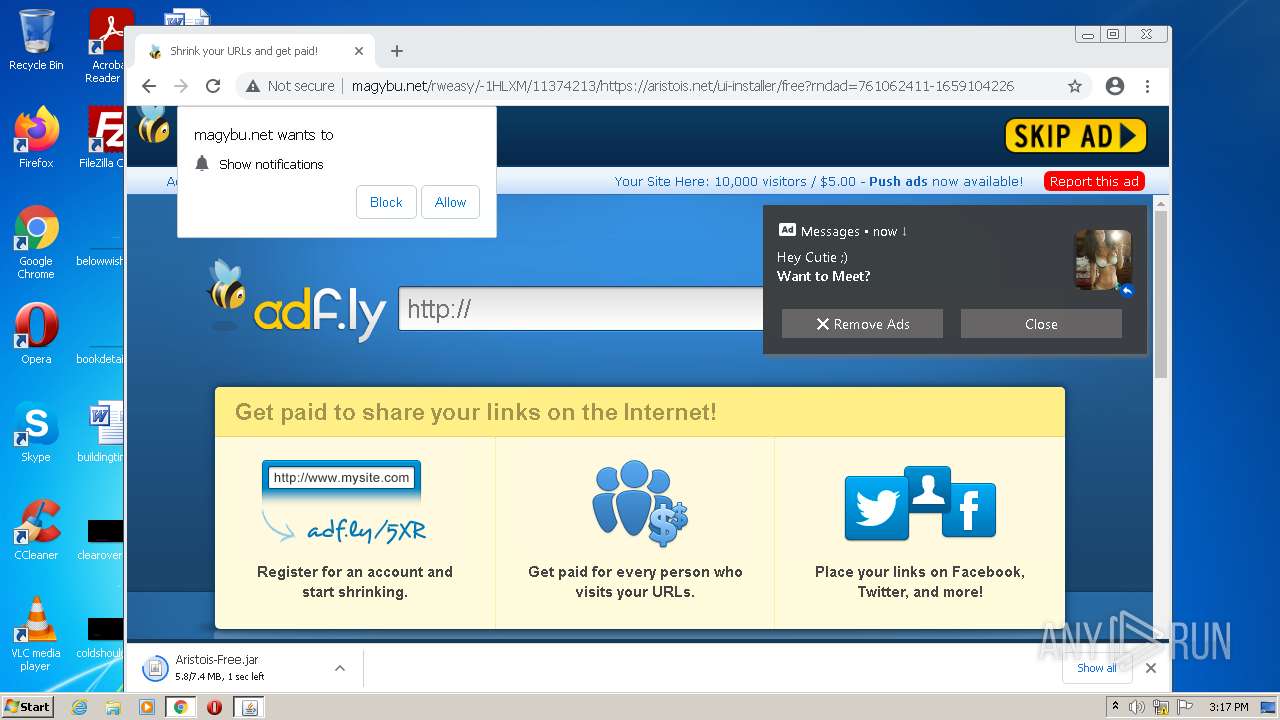
2800 | chrome.exe | GET | 200 | 104.21.37.41:80 | http://magybu.net/rweasy/-1HLXM/11374213/https://aristois.net/ui-installer/free?rndad=761062411-1659104226 | US | html | 4.86 Kb | suspicious |
960 | chrome.exe | GET | 200 | 74.125.110.136:80 | http://r3---sn-5goeen7y.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=e_&mip=45.92.228.11&mm=28&mn=sn-5goeen7y&ms=nvh&mt=1659103703&mv=m&mvi=3&pl=24&rmhost=r5---sn-5goeen7y.gvt1.com&shardbypass=sd&smhost=r1---sn-5goeen76.gvt1.com | US | crx | 242 Kb | whitelisted |
960 | chrome.exe | GET | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | text | 37 b | whitelisted |
2800 | chrome.exe | GET | 200 | 172.67.203.187:80 | http://cdn.magybu.net/static/image/logo_fb2.png | US | image | 6.14 Kb | suspicious |
2800 | chrome.exe | GET | 200 | 172.67.203.187:80 | http://cdn.magybu.net/static/css/adfly_7.css | US | text | 875 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
960 | chrome.exe | 142.250.186.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
960 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
960 | chrome.exe | 142.250.186.164:443 | www.google.com | Google Inc. | US | whitelisted |
960 | chrome.exe | 142.250.186.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
960 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
960 | chrome.exe | 142.250.186.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
960 | chrome.exe | 142.250.185.174:443 | apis.google.com | Google Inc. | US | whitelisted |
960 | chrome.exe | 142.250.186.110:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
960 | chrome.exe | 142.250.185.202:443 | content-autofill.googleapis.com | Google Inc. | US | whitelisted |
960 | chrome.exe | 142.250.186.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
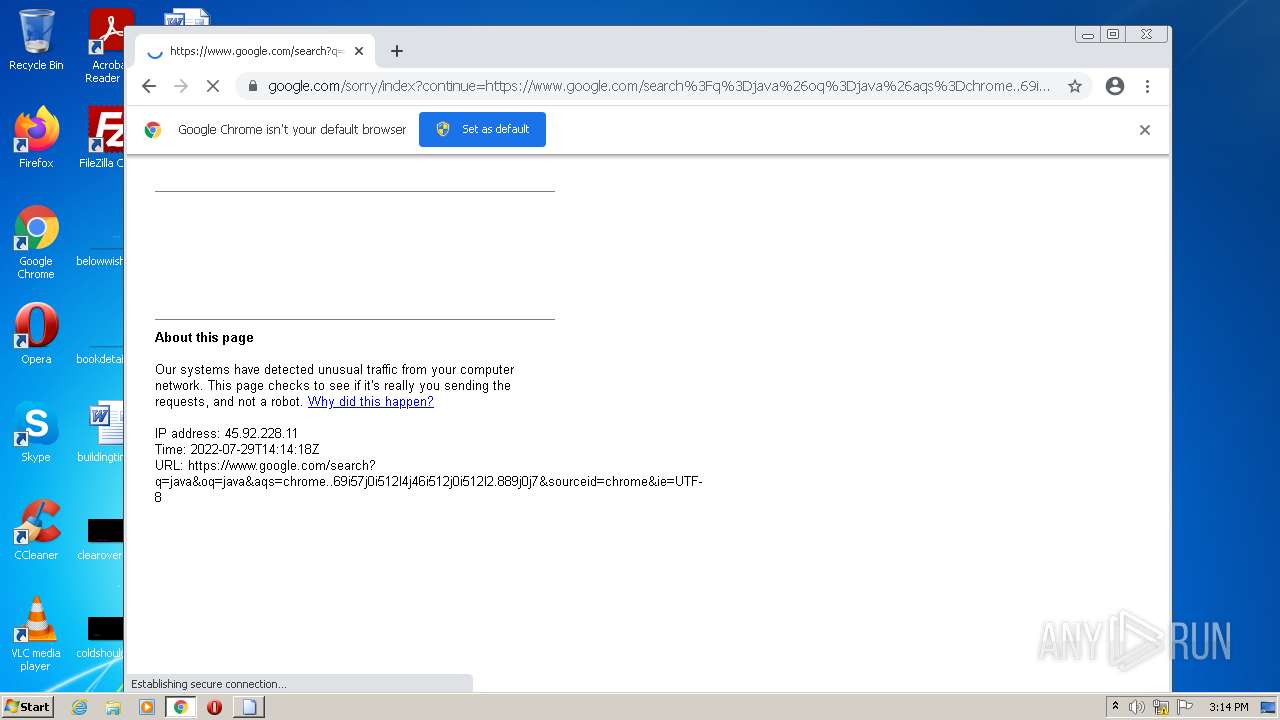
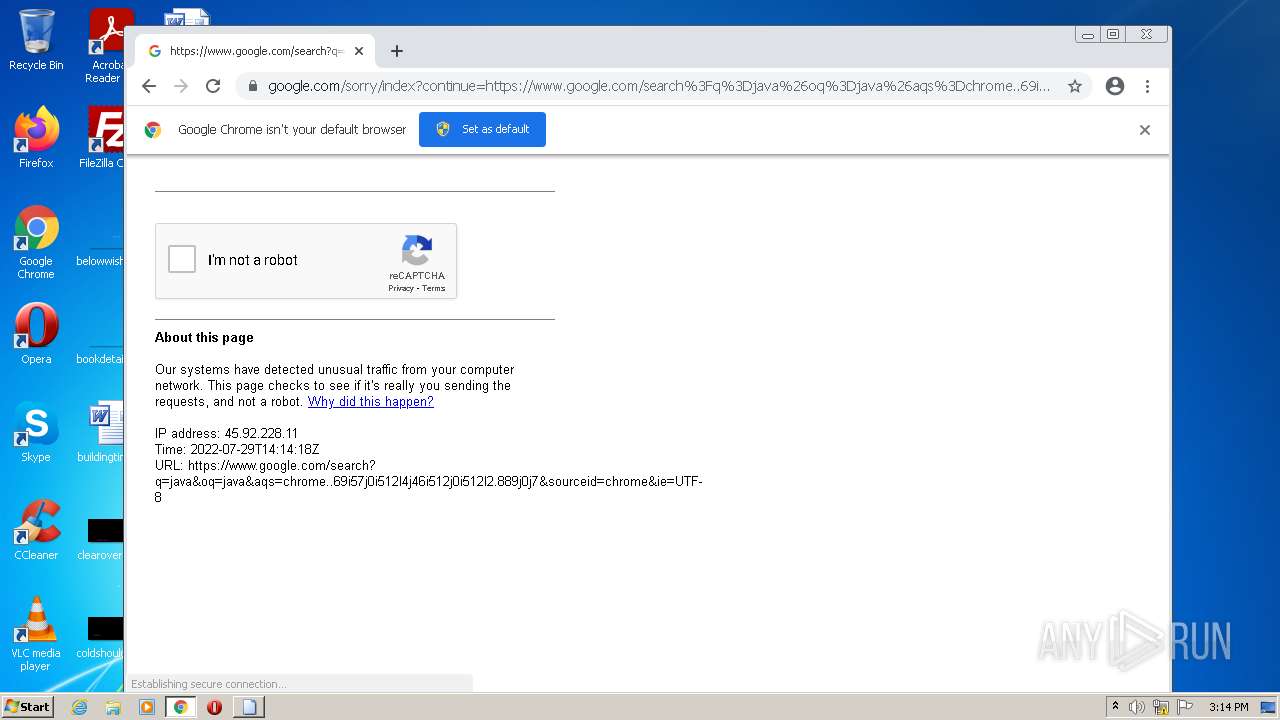
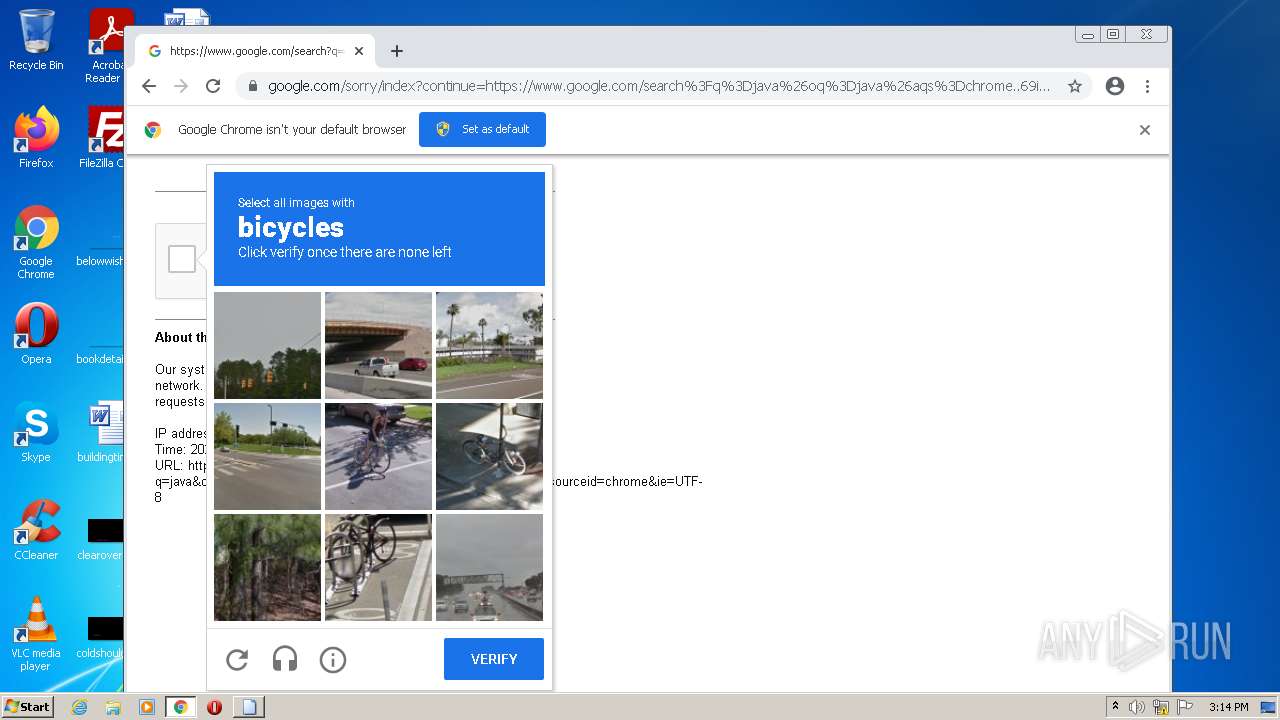
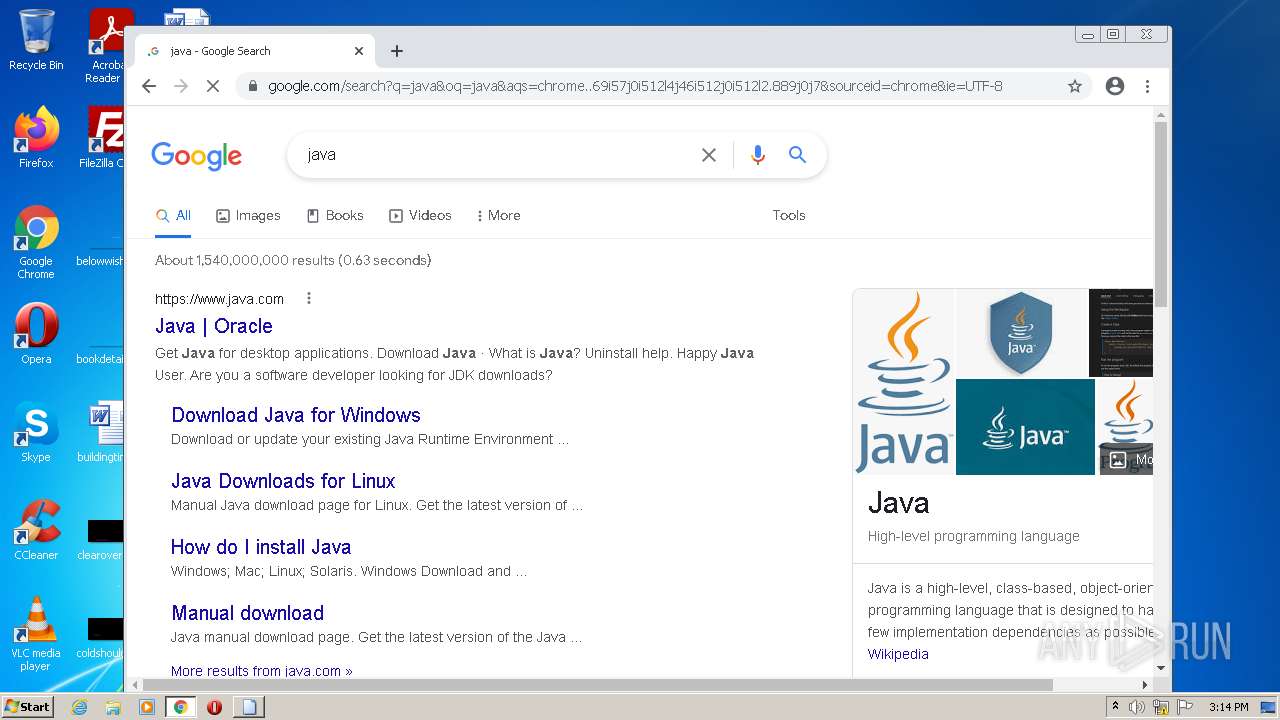
www.google.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2800 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.asia domain |
2800 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.asia domain |
2800 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.asia domain |