| URL: | http://syndication.exdynsrv.com/splash.php?cat=&idzone=769989&type=8&p=http%3A%2F%2Fwww.drsnysvet.cz%2Fjeji-pritel-prisel-o-nohu%2F&sub=&tags=&el=&cookieconsent=true&scr_info=cmVtb3RlfHBvcHVuZGVyanN8MjUxNzcwOTA%3D |
| Full analysis: | https://app.any.run/tasks/94bd868e-eb4e-4657-b033-949d762a5d9e |
| Verdict: | Malicious activity |
| Analysis date: | February 03, 2022, 10:56:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B33F8A624D075EF081B22F1704EC88B0 |
| SHA1: | 43567F4B3257D8E80F3AF3F928D406C7C2B8BC51 |
| SHA256: | 4A4E0AD409242F9EFB63C75A6125DB00F7D7F487A7BB08C19F565E28683DB831 |
| SSDEEP: | 6:COii63jjnO6OV9jiszDM0DvDHh3zgY4Wh:xj63HnVOVcsE6dzfh |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2100)
Checks supported languages
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3448)
Reads the computer name
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3448)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3448)
Creates files in the user directory
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3448)
INFO
Checks supported languages
- iexplore.exe (PID: 3428)
- iexplore.exe (PID: 2100)
Reads the computer name
- iexplore.exe (PID: 3428)
- iexplore.exe (PID: 2100)
Changes internet zones settings
- iexplore.exe (PID: 3428)
Creates files in the user directory
- iexplore.exe (PID: 2100)
Checks Windows Trust Settings
- iexplore.exe (PID: 3428)
- iexplore.exe (PID: 2100)
Application launched itself
- iexplore.exe (PID: 3428)
Reads internet explorer settings
- iexplore.exe (PID: 2100)
Reads settings of System Certificates
- iexplore.exe (PID: 2100)
- iexplore.exe (PID: 3428)
Reads CPU info
- iexplore.exe (PID: 2100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2100 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3428 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3428 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://syndication.exdynsrv.com/splash.php?cat=&idzone=769989&type=8&p=http%3A%2F%2Fwww.drsnysvet.cz%2Fjeji-pritel-prisel-o-nohu%2F&sub=&tags=&el=&cookieconsent=true&scr_info=cmVtb3RlfHBvcHVuZGVyanN8MjUxNzcwOTA%3D" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3448 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe� Flash� Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
Total events
15 149
Read events
14 966
Write events
183
Delete events
0
Modification events
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30939372 | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30939372 | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
19
Text files
165
Unknown types
73
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2100 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\N321I2XM.txt | text | |
MD5:— | SHA256:— | |||
| 2100 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\RIQREU1B.txt | text | |
MD5:— | SHA256:— | |||
| 2100 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\splash[1].htm | html | |
MD5:— | SHA256:— | |||
| 3428 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 3428 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 2100 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3F26ED5DE6B4E859CCCA6035ECB8D9CB | der | |
MD5:— | SHA256:— | |||
| 2100 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2100 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 2100 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3F26ED5DE6B4E859CCCA6035ECB8D9CB | binary | |
MD5:— | SHA256:— | |||
| 2100 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
71
DNS requests
29
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2100 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEQCTi7COYph7T3X5jLalBFyW | US | der | 728 b | whitelisted |
2100 | iexplore.exe | GET | 200 | 95.211.229.246:80 | http://syndication.exdynsrv.com/splash.php?cat=&idzone=769989&type=8&p=http%3A%2F%2Fwww.drsnysvet.cz%2Fjeji-pritel-prisel-o-nohu%2F&sub=&tags=&el=&cookieconsent=true&scr_info=cmVtb3RlfHBvcHVuZGVyanN8MjUxNzcwOTA%3D | NL | html | 574 b | suspicious |
2100 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRyyuDOSqb8BtprWZSAvBT9kFoYdwQU%2BftQxItnu2dk%2FoMhpqnOP1WEk5kCEAUJ2mRQFrOMLy2XSuH%2FsGw%3D | US | der | 471 b | whitelisted |
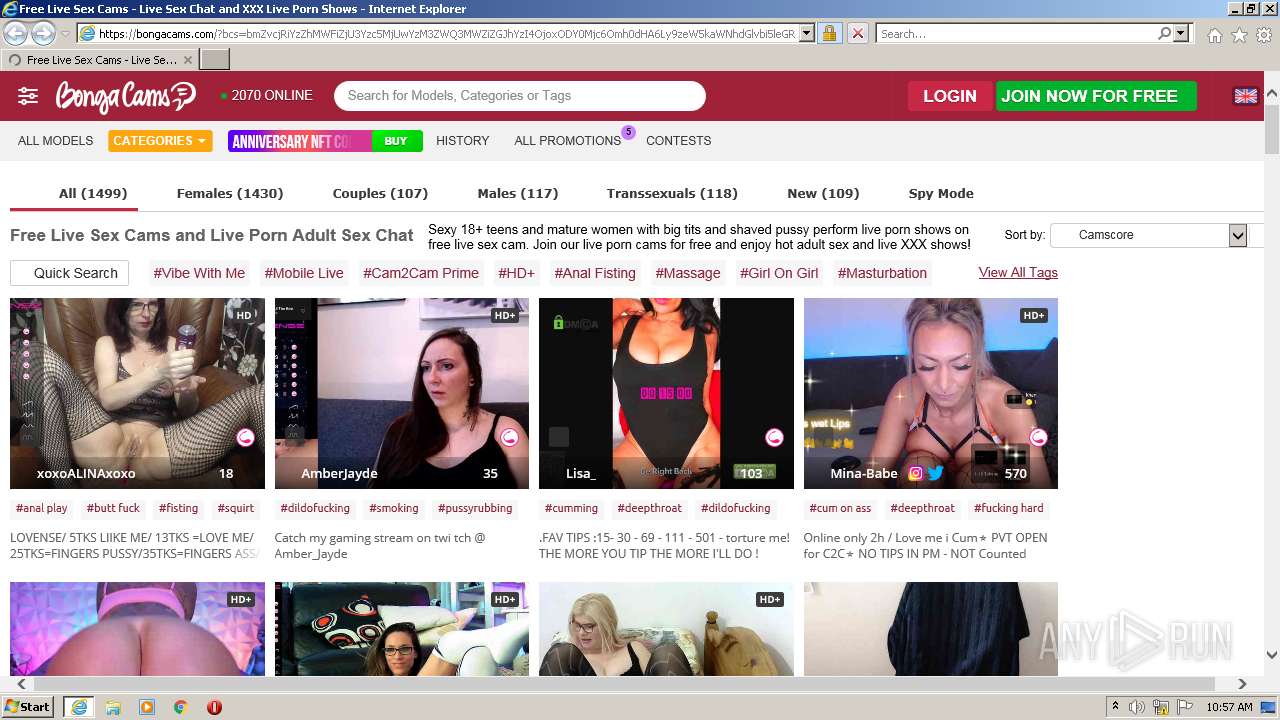
2100 | iexplore.exe | GET | 302 | 95.211.229.246:80 | http://syndication.exdynsrv.com/splash.php?cat=&idzone=769989&type=8&p=http%3A%2F%2Fwww.drsnysvet.cz%2Fjeji-pritel-prisel-o-nohu%2F&sub=&tags=&el=&cookieconsent=true&scr_info=cmVtb3RlfHBvcHVuZGVyanN8MjUxNzcwOTA%3D&tested=1&check=690bb46f3c907462c25877c9ed457b58&screen_resolution=1280x720&container_resolution=1280x621&iframe=0 | NL | compressed | 574 b | suspicious |
2100 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCLHtDCfO2bBwoAAAABLgJa | US | der | 472 b | whitelisted |
2100 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2100 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2100 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEEFKxQHtEPcBCgAAAAErfHU%3D | US | der | 471 b | whitelisted |
2100 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCv%2F46iPAj3HwoAAAABLgd6 | US | der | 472 b | whitelisted |
2100 | iexplore.exe | GET | 200 | 143.204.101.74:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2100 | iexplore.exe | 95.211.229.246:80 | syndication.exdynsrv.com | LeaseWeb Netherlands B.V. | NL | suspicious |
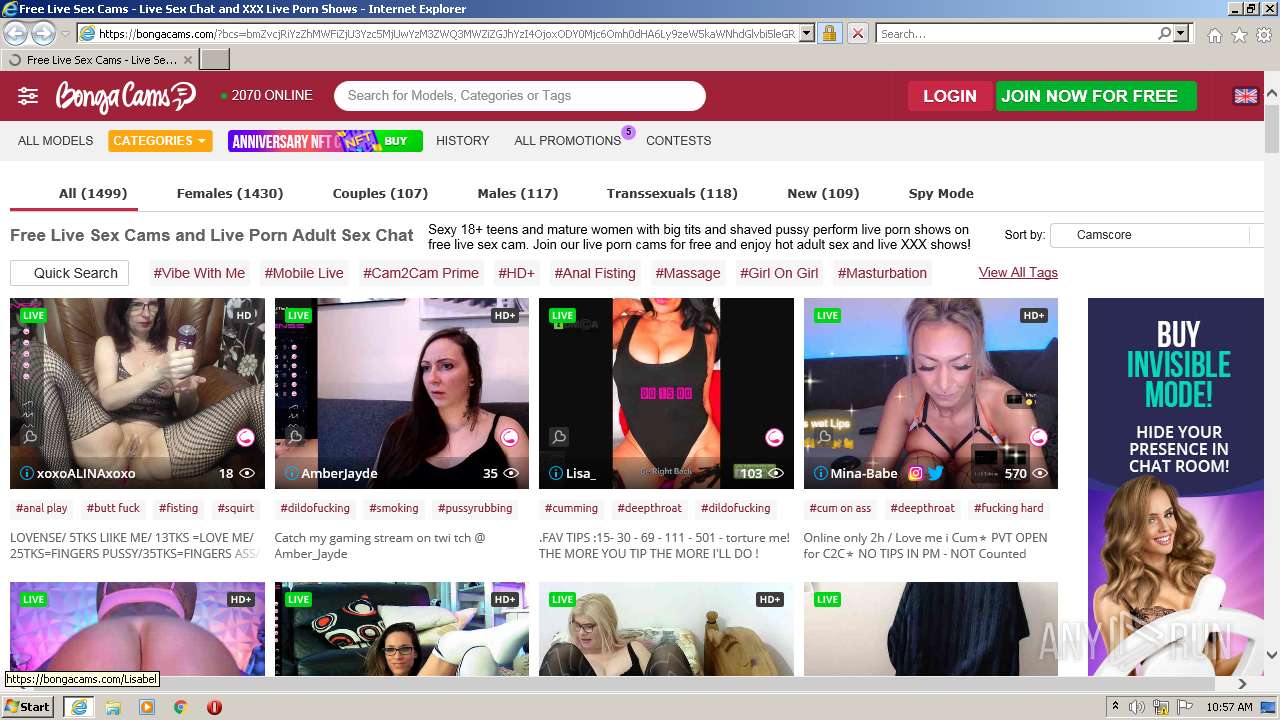
2100 | iexplore.exe | 195.85.23.222:443 | bongacams10.com | DUPONT NUTRITION BIOSCIENCES ApS | DK | unknown |
2100 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3428 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2100 | iexplore.exe | 8.248.113.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3428 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2100 | iexplore.exe | 95.211.229.245:80 | syndication.exdynsrv.com | LeaseWeb Netherlands B.V. | NL | suspicious |
2100 | iexplore.exe | 31.192.112.221:443 | trkbc.com | Viking Host B.V. | NL | suspicious |
2100 | iexplore.exe | 142.250.184.200:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
— | — | 143.204.98.84:443 | d31qbv1cthcecs.cloudfront.net | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
syndication.exdynsrv.com |
| suspicious |
bongacams10.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
trkbc.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |