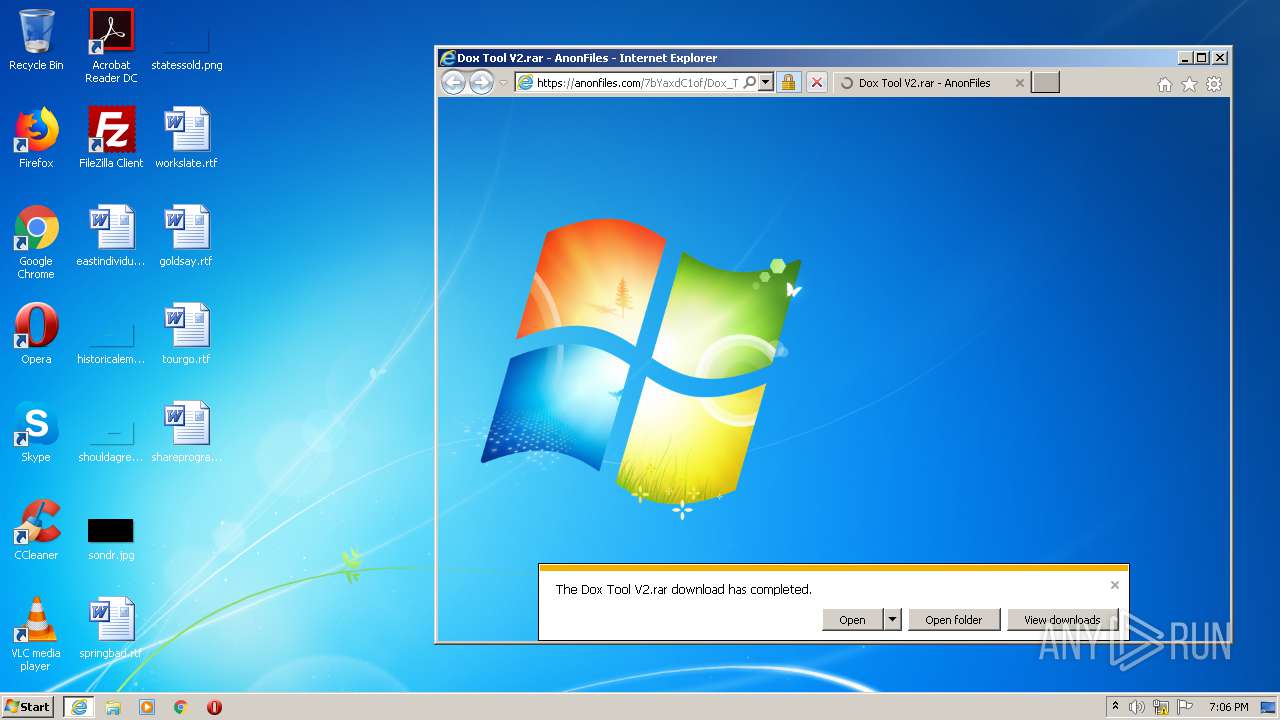
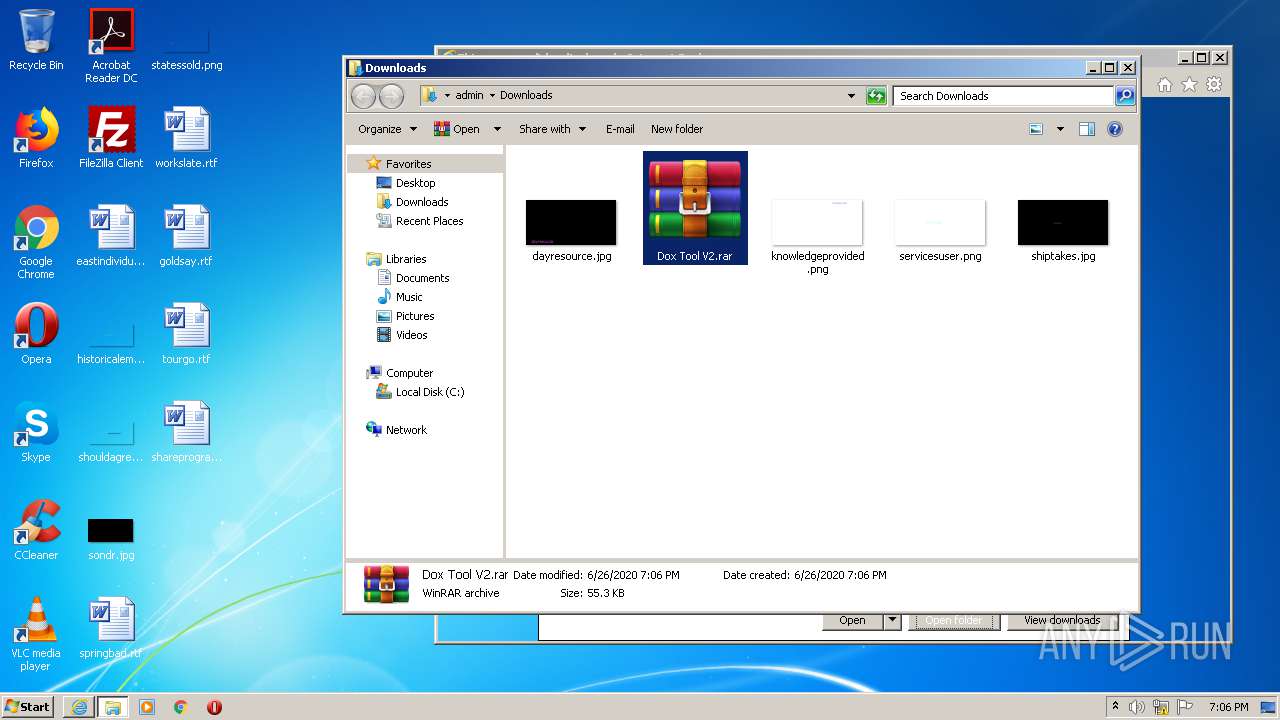
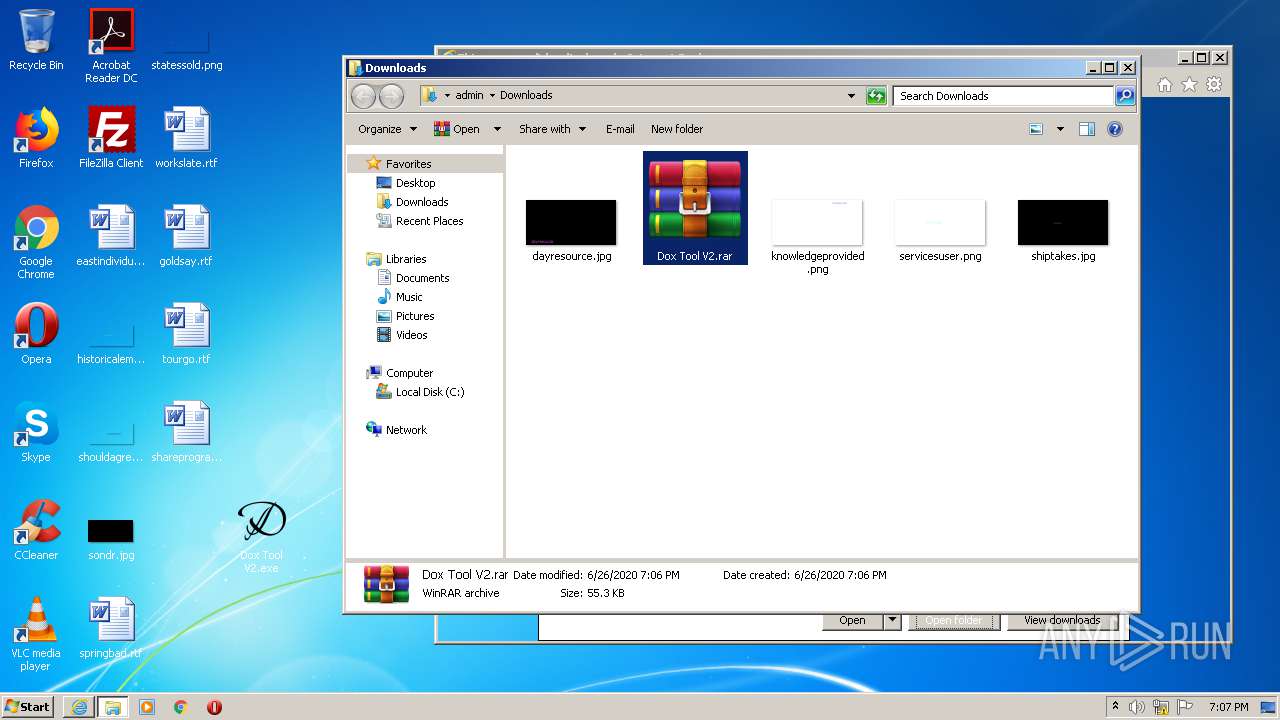
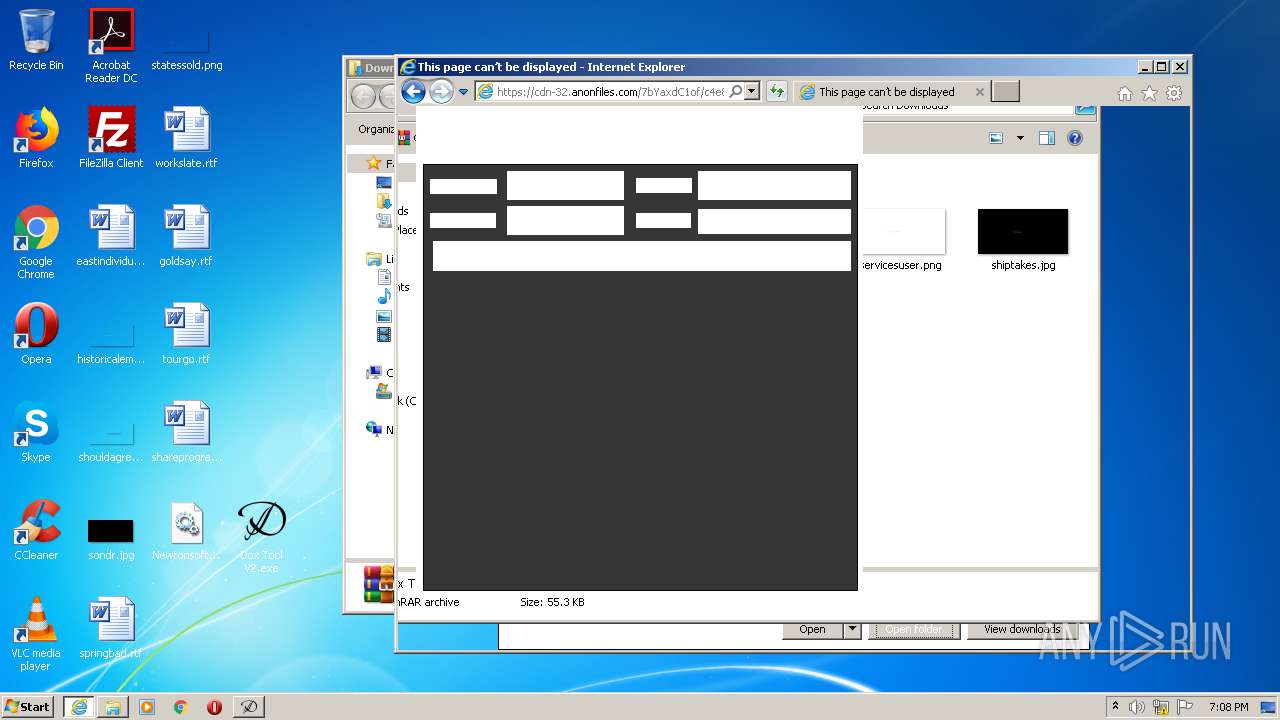
| URL: | https://anonfiles.com/7bYaxdC1of/Dox_Tool_V2_rar |
| Full analysis: | https://app.any.run/tasks/5d623480-46cb-4a70-b798-10eb349ec6b5 |
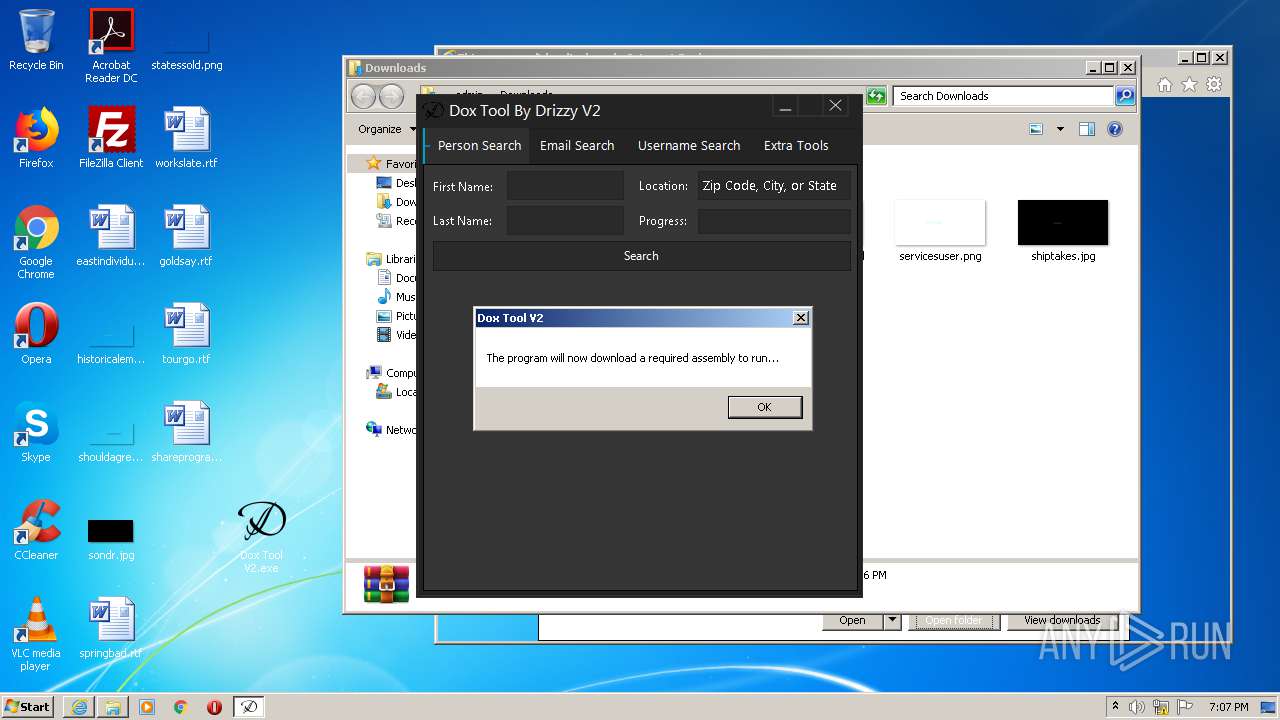
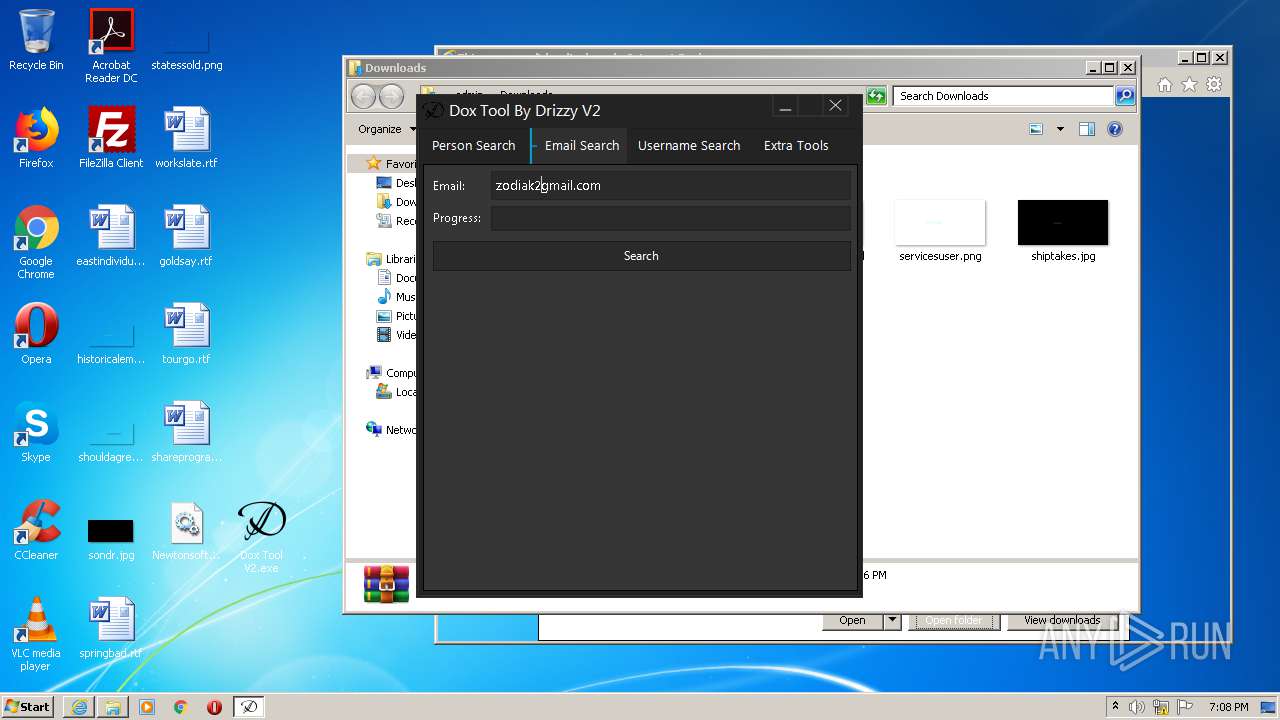
| Verdict: | Malicious activity |
| Analysis date: | June 26, 2020, 18:05:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5D05C2999B327F2B729070905E546DA4 |
| SHA1: | 3CC6B60B02C97CF5152960800DD4F1D59AF74E59 |
| SHA256: | 4A4CE9CFD200CFD6BD7DE7AE4FF5CAD41CC87BD43525513D3172F64B2934E83B |
| SSDEEP: | 3:N8M2NBYKc4MJp:2M2vbMJp |
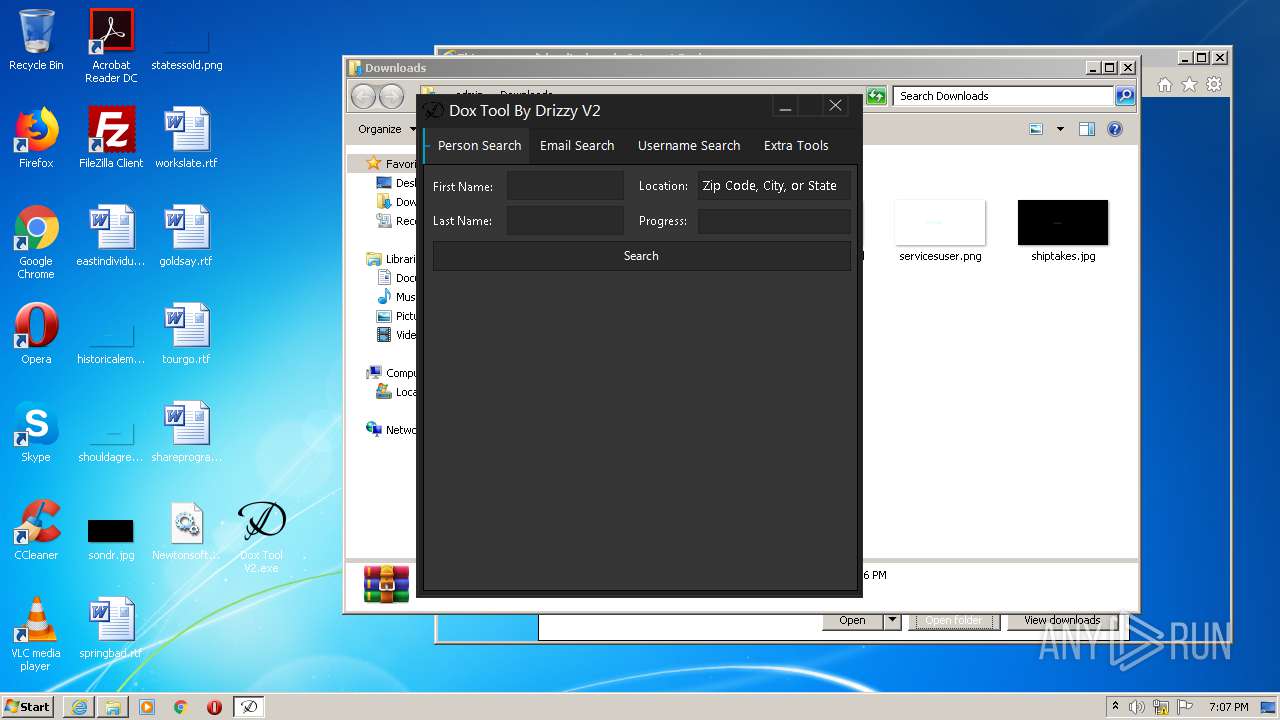
MALICIOUS
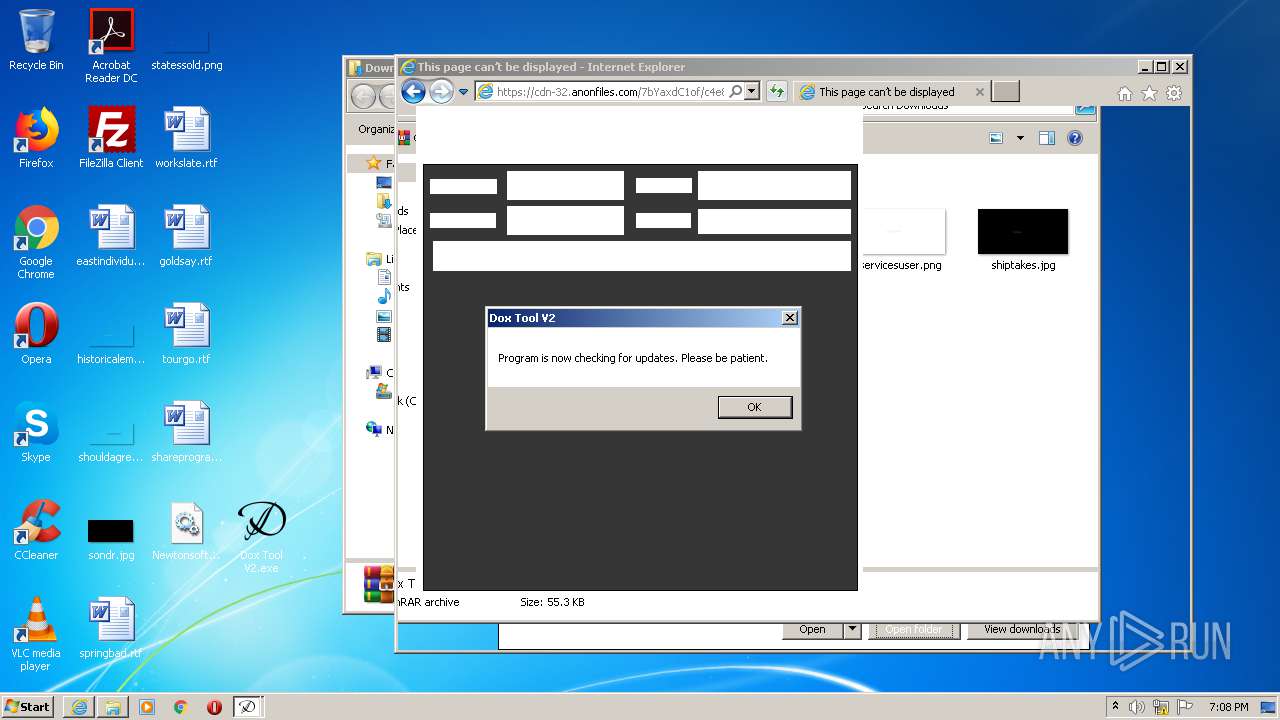
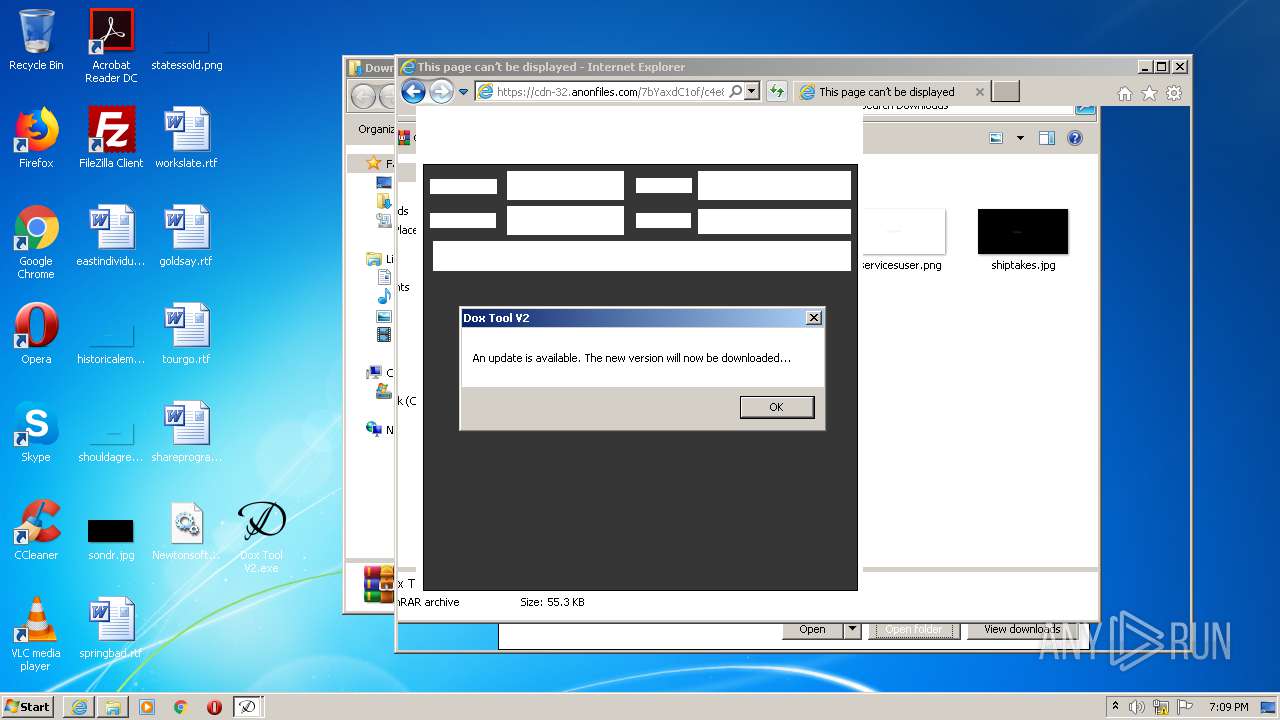
Application was dropped or rewritten from another process
- Dox Tool V2.exe (PID: 3648)
- Dox Tool V2.exe (PID: 2312)
Changes settings of System certificates
- Dox Tool V2.exe (PID: 2312)
- Dox Tool V2.exe (PID: 3648)
SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3372)
Adds / modifies Windows certificates
- Dox Tool V2.exe (PID: 2312)
- Dox Tool V2.exe (PID: 3648)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2408)
- iexplore.exe (PID: 2788)
- iexplore.exe (PID: 3864)
Creates files in the user directory
- iexplore.exe (PID: 2408)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3372)
- iexplore.exe (PID: 2788)
Changes internet zones settings
- iexplore.exe (PID: 2788)
Application launched itself
- iexplore.exe (PID: 2788)
Reads internet explorer settings
- iexplore.exe (PID: 2408)
- iexplore.exe (PID: 3864)
Reads settings of System Certificates
- iexplore.exe (PID: 3864)
- iexplore.exe (PID: 2788)
- Dox Tool V2.exe (PID: 2312)
- Dox Tool V2.exe (PID: 3648)
- iexplore.exe (PID: 2408)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2788)
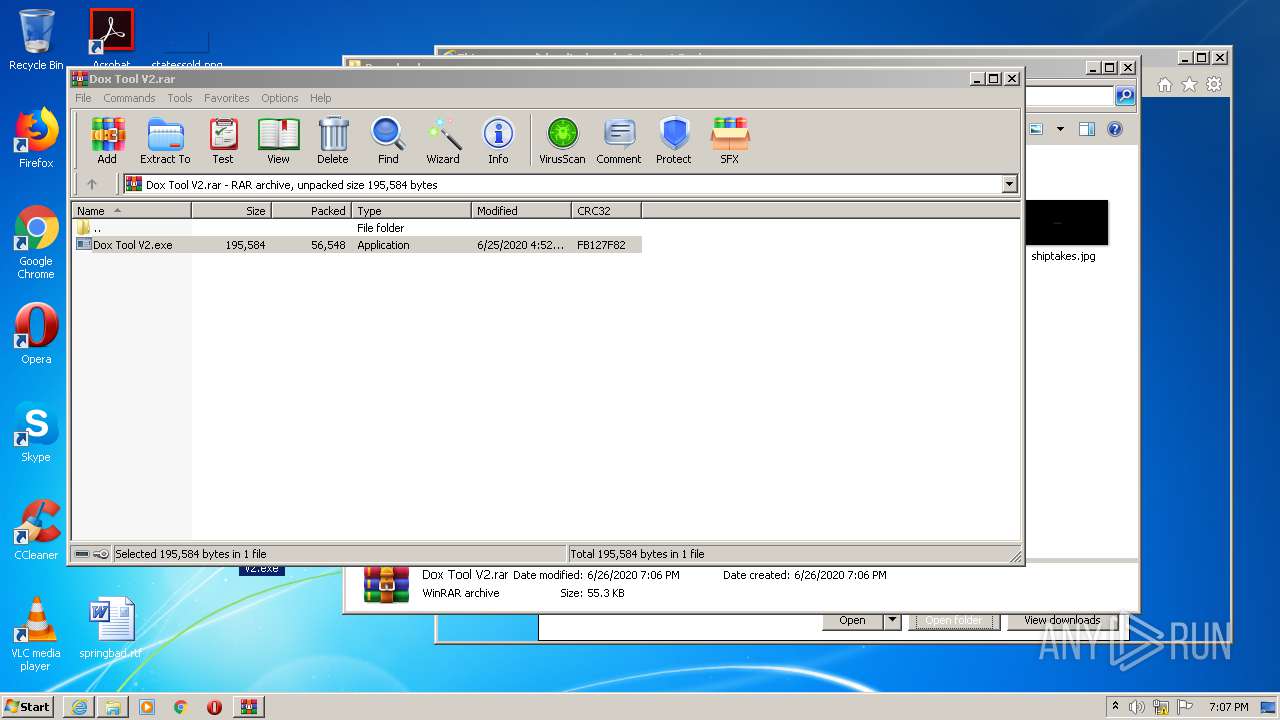
Manual execution by user
- Dox Tool V2.exe (PID: 3648)
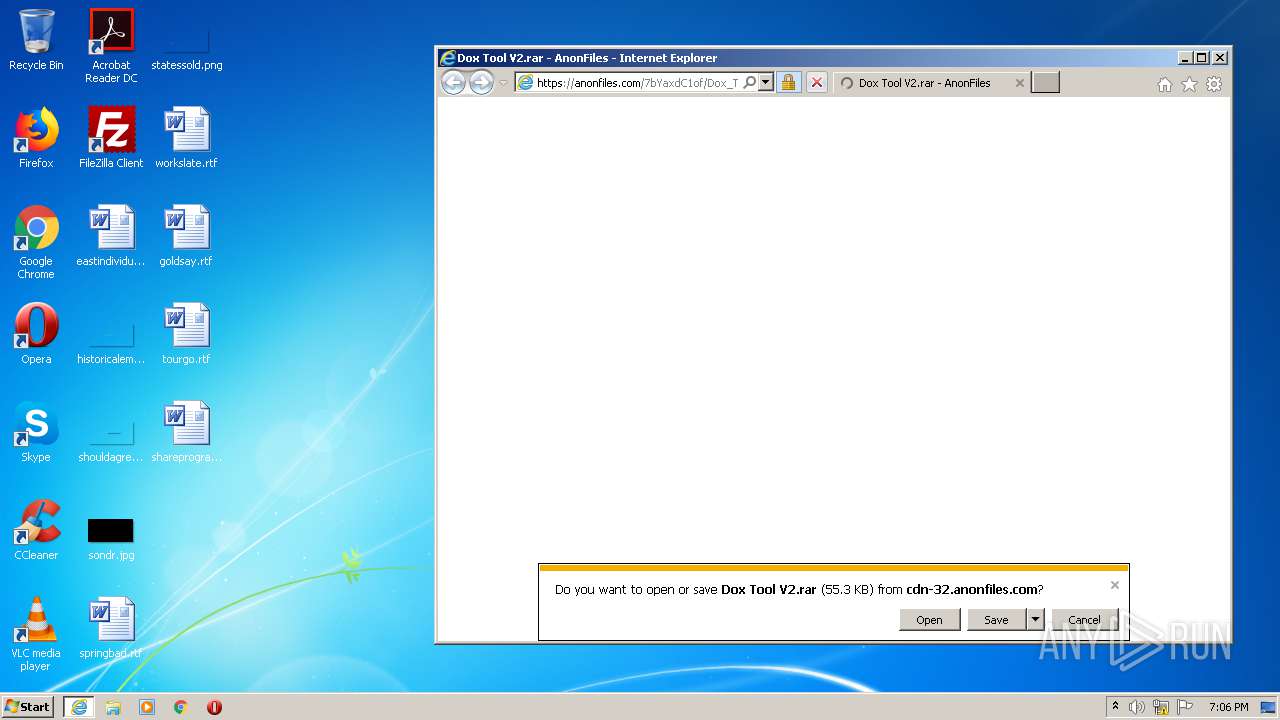
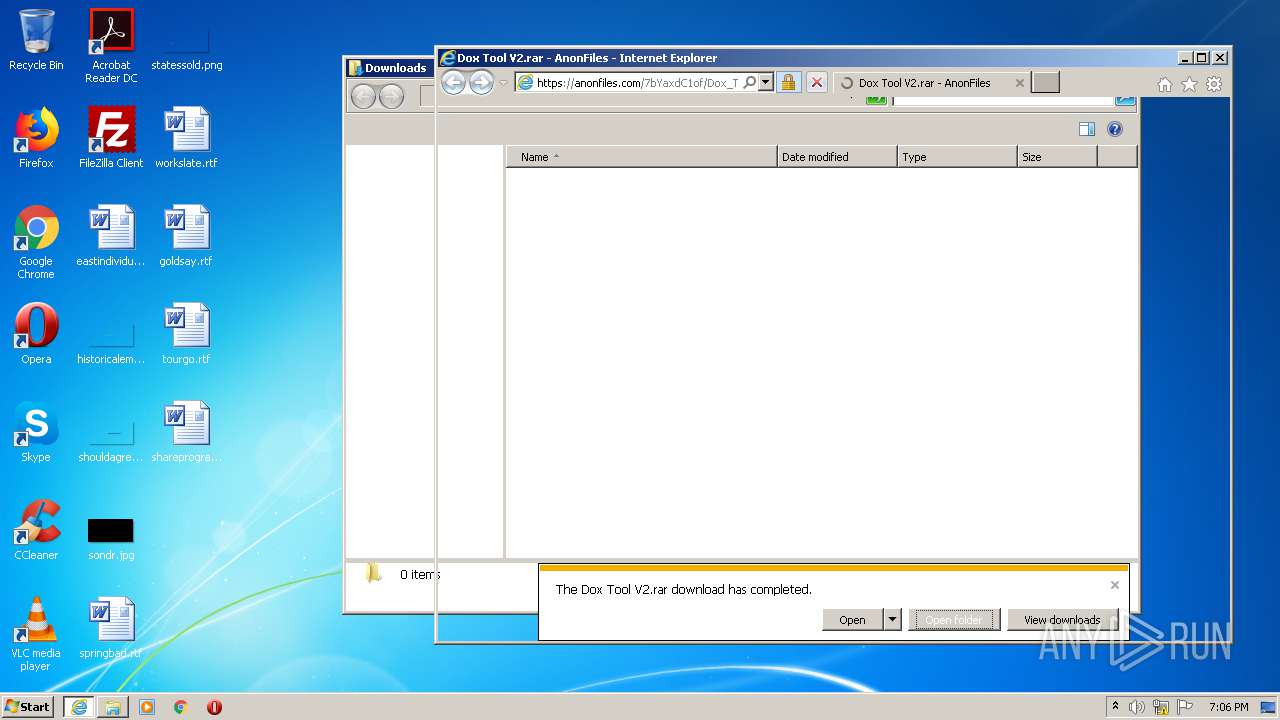
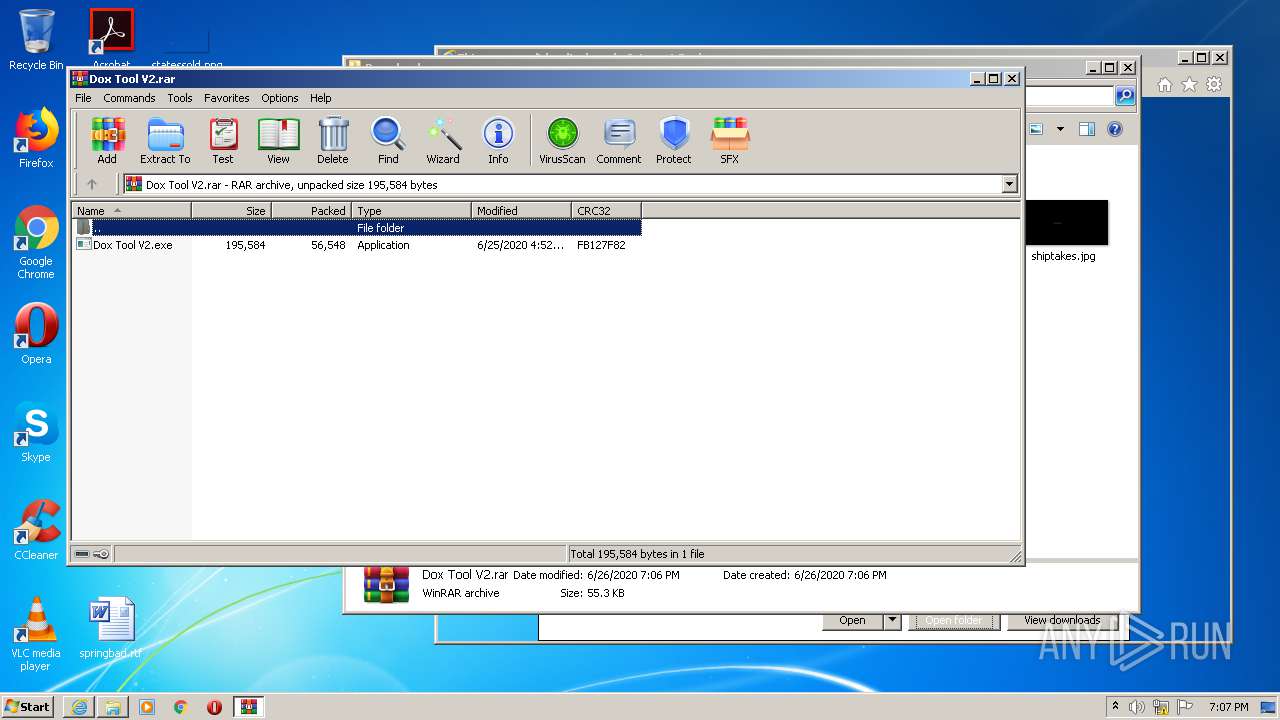
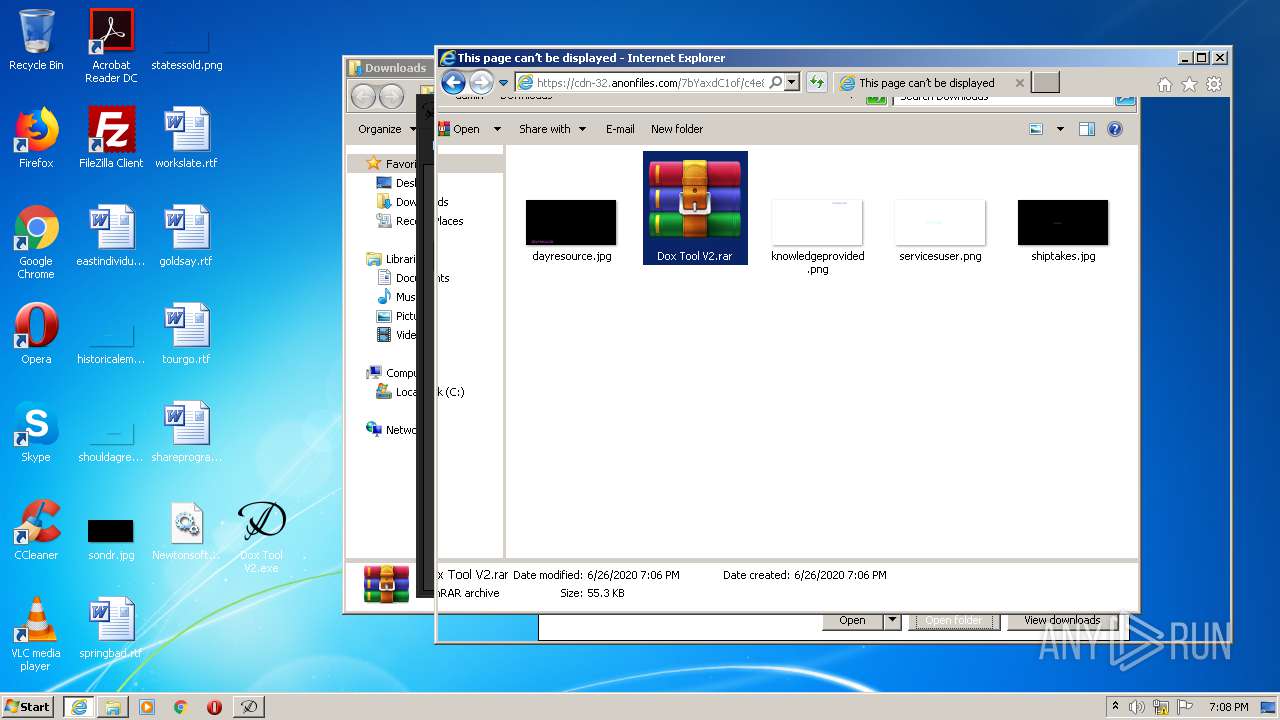
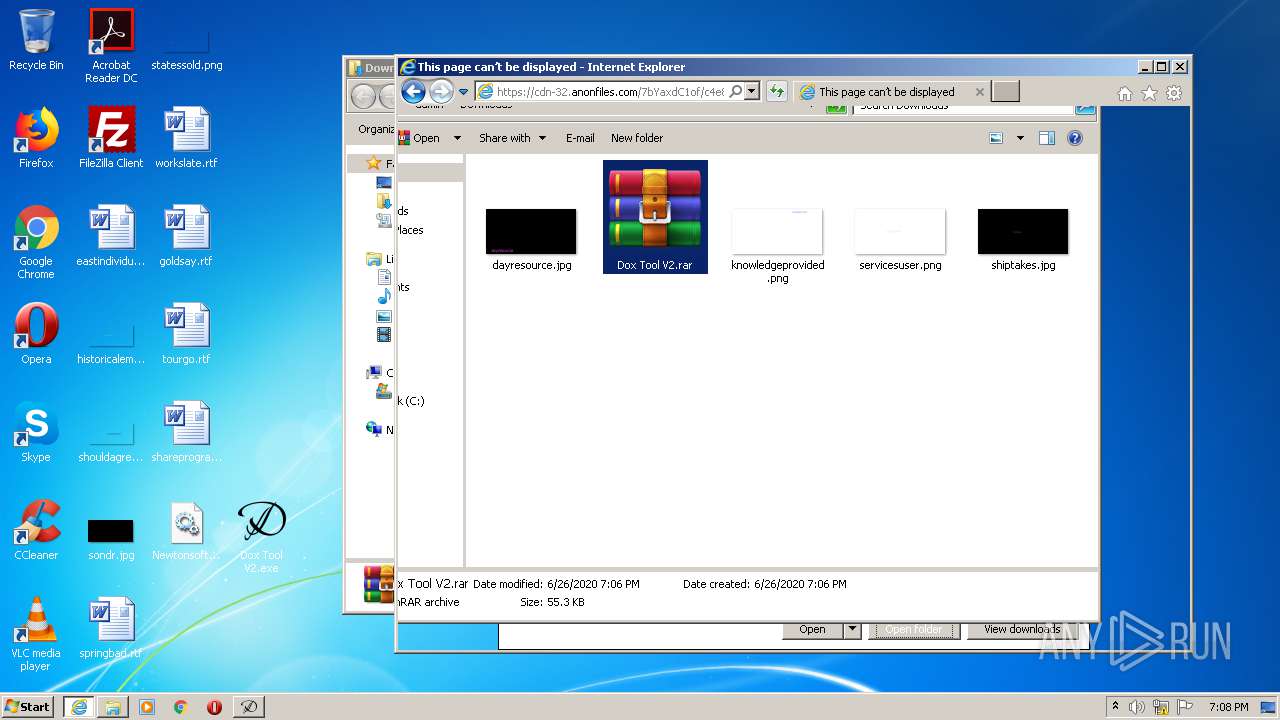
- WinRAR.exe (PID: 3248)
- Dox Tool V2.exe (PID: 2312)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2788)
Changes settings of System certificates
- iexplore.exe (PID: 2788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2312 | "C:\Users\admin\Desktop\Dox Tool V2.exe" | C:\Users\admin\Desktop\Dox Tool V2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Dox Tool V2 Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2788 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2788 | "C:\Program Files\Internet Explorer\iexplore.exe" https://anonfiles.com/7bYaxdC1of/Dox_Tool_V2_rar | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3248 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Dox Tool V2.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3372 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 3648 | "C:\Users\admin\Desktop\Dox Tool V2.exe" | C:\Users\admin\Desktop\Dox Tool V2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Dox Tool V2 Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 3864 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2788 CREDAT:4134175 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
13 932
Read events
1 801
Write events
8 126
Delete events
4 005
Modification events
| (PID) Process: | (2788) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1802382492 | |||
| (PID) Process: | (2788) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30821348 | |||
| (PID) Process: | (2788) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2788) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2788) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2788) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2788) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2788) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2788) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2788) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
36
Text files
36
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2408 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarEF27.tmp | — | |
MD5:— | SHA256:— | |||
| 2408 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 2408 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 2408 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\anonfiles[1].css | text | |
MD5:— | SHA256:— | |||
| 2408 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\LIL96OVD.txt | text | |
MD5:— | SHA256:— | |||
| 2408 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\app[1].js | text | |
MD5:— | SHA256:— | |||
| 2408 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\Dox_Tool_V2_rar[1].htm | html | |
MD5:— | SHA256:— | |||
| 2408 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabEF26.tmp | compressed | |
MD5:767760B1B3B838B2DE0599D0E76D1C76 | SHA256:C0F37380971FB93ECB0CFA3C2BD6D91CC77F254F0A6CA41EDEFF47FDA0E409CC | |||
| 2408 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\de[1].png | image | |
MD5:9F8CC07C258BCD2DE0C7900861E20FFC | SHA256:07CD5A4CAD20604F77DCED9C7D8A92CA9AE3321718E5A1935296E4D75F921A19 | |||
| 2408 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\rar[1].png | image | |
MD5:D33954367BC5D15C7F0E01857E7AE8EA | SHA256:A6F8963DD8D602E135E8B860B7E48BADFD78C2B1BEF9EC362A39CE2FC484606F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
51
DNS requests
22
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
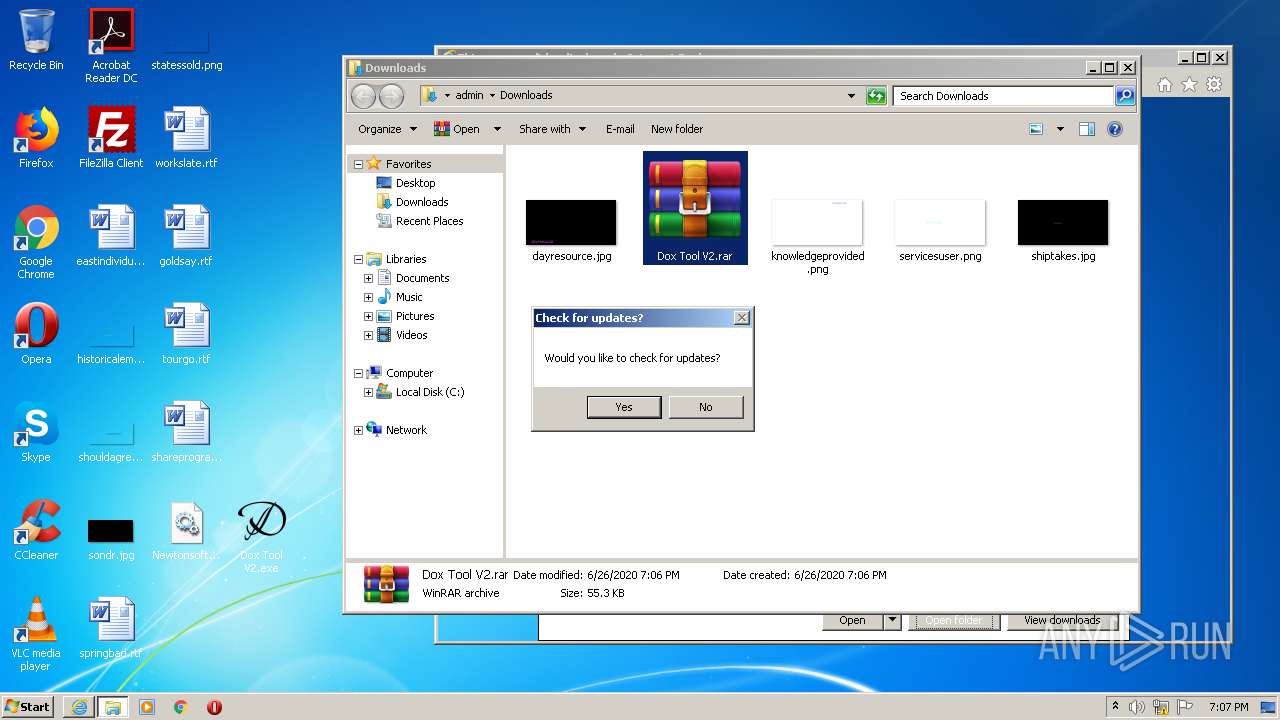
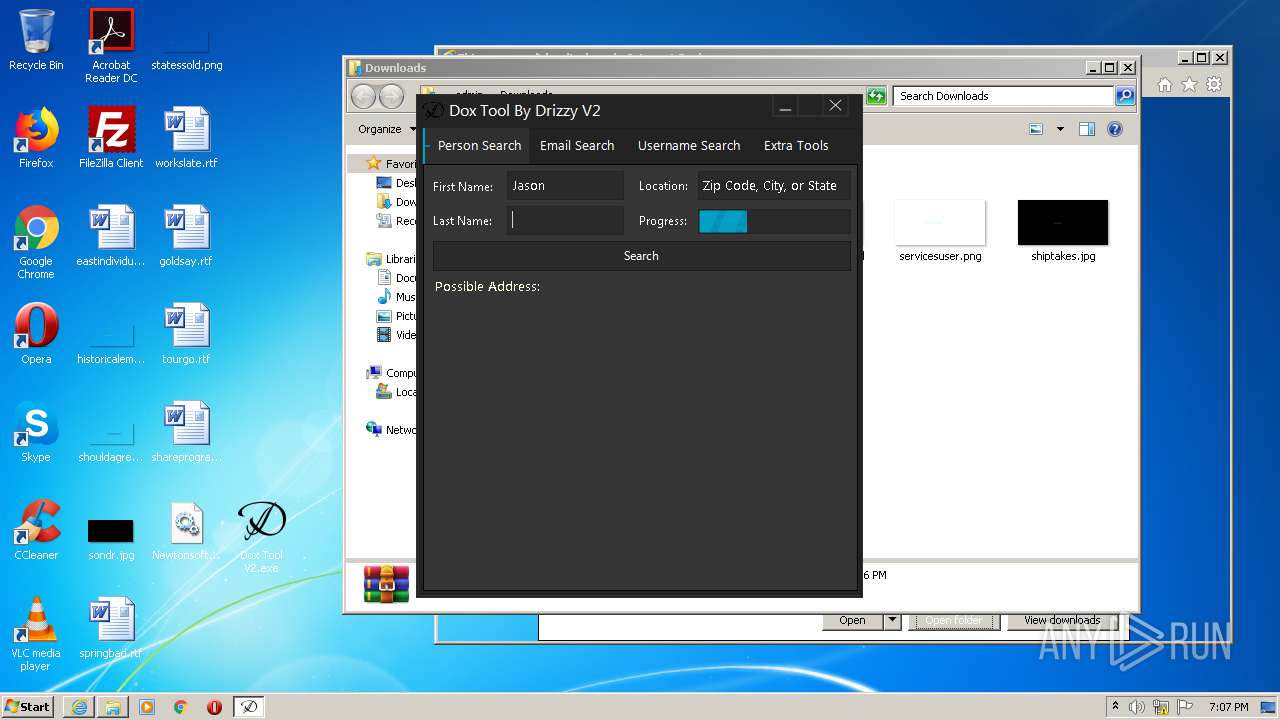
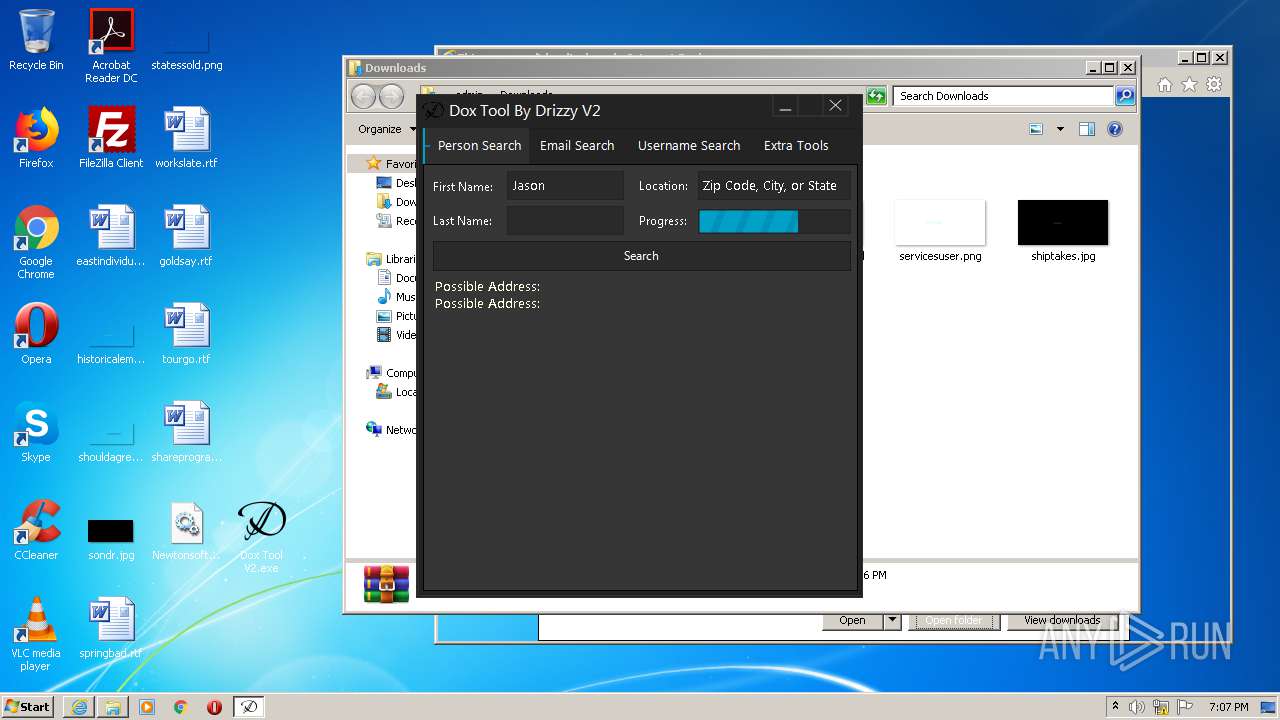
3648 | Dox Tool V2.exe | GET | — | 169.45.189.53:80 | http://10digits.us/n/Jason_/location/Zip%20Code,%20City,%20or%20State | NL | — | — | unknown |
3648 | Dox Tool V2.exe | GET | — | 169.45.189.53:80 | http://10digits.us/n/Jason_/location/Zip%20Code,%20City,%20or%20State | NL | — | — | unknown |
3648 | Dox Tool V2.exe | GET | 301 | 172.67.161.150:80 | http://www.zabasearch.com/people/Jason+/Zip%20Code,%20City,%20or%20State | US | — | — | malicious |
2408 | iexplore.exe | GET | 200 | 23.51.123.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.71 Kb | shared |
2408 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 471 b | whitelisted |
2408 | iexplore.exe | GET | 200 | 23.51.123.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.71 Kb | shared |
2408 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://crl.globalsign.com/root.crl | US | der | 914 b | whitelisted |
2788 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2408 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAyO4MkNaokViAQGHuJB%2Ba8%3D | US | der | 471 b | whitelisted |
3864 | iexplore.exe | GET | 200 | 192.35.177.64:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | US | der | 994 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2408 | iexplore.exe | 151.101.66.217:443 | vjs.zencdn.net | Fastly | US | suspicious |
2408 | iexplore.exe | 45.148.16.53:443 | cdn-32.anonfiles.com | — | — | unknown |
2408 | iexplore.exe | 104.18.21.226:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
2788 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2408 | iexplore.exe | 104.24.116.23:443 | anonfiles.com | Cloudflare Inc | US | unknown |
2408 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2408 | iexplore.exe | 151.101.2.217:443 | vjs.zencdn.net | Fastly | US | suspicious |
2408 | iexplore.exe | 13.35.253.58:443 | djv99sxoqpv11.cloudfront.net | — | US | malicious |
2788 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2788 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anonfiles.com |
| shared |
ocsp.digicert.com |
| whitelisted |
vjs.zencdn.net |
| whitelisted |
djv99sxoqpv11.cloudfront.net |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
s.symcd.com |
| shared |
crl.globalsign.com |
| whitelisted |
cdn-32.anonfiles.com |
| suspicious |
Threats
1 ETPRO signatures available at the full report