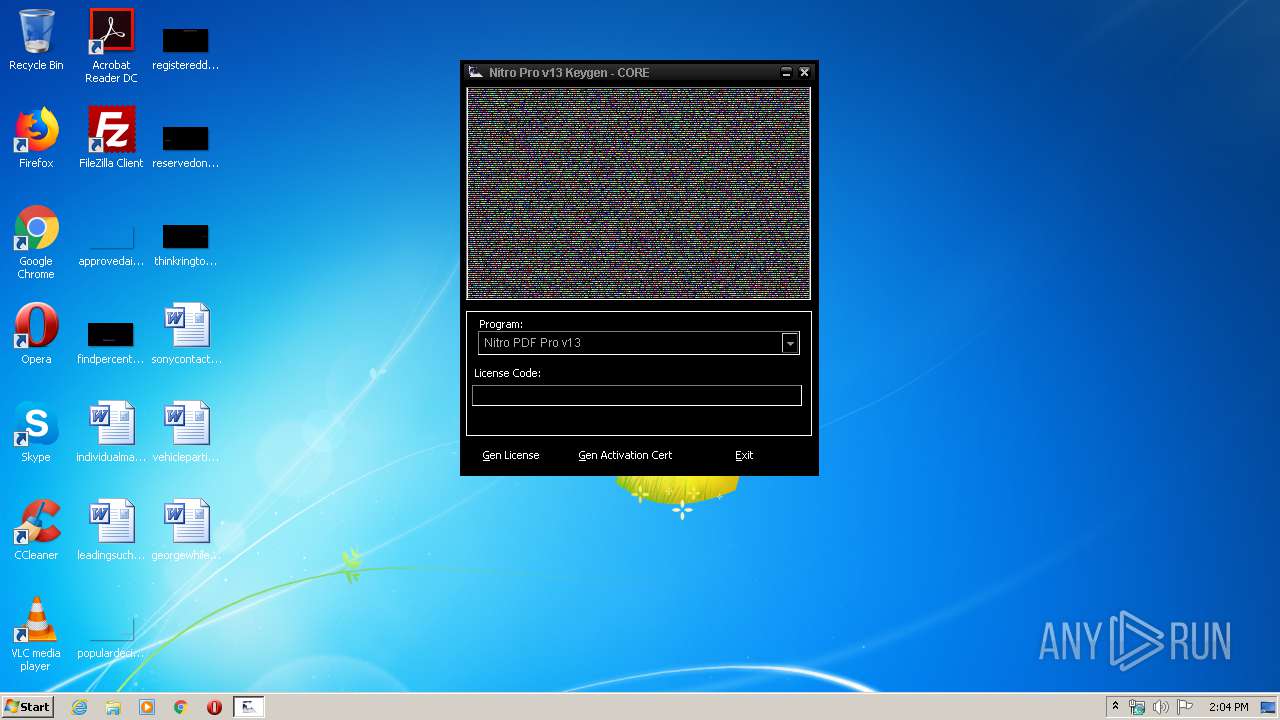
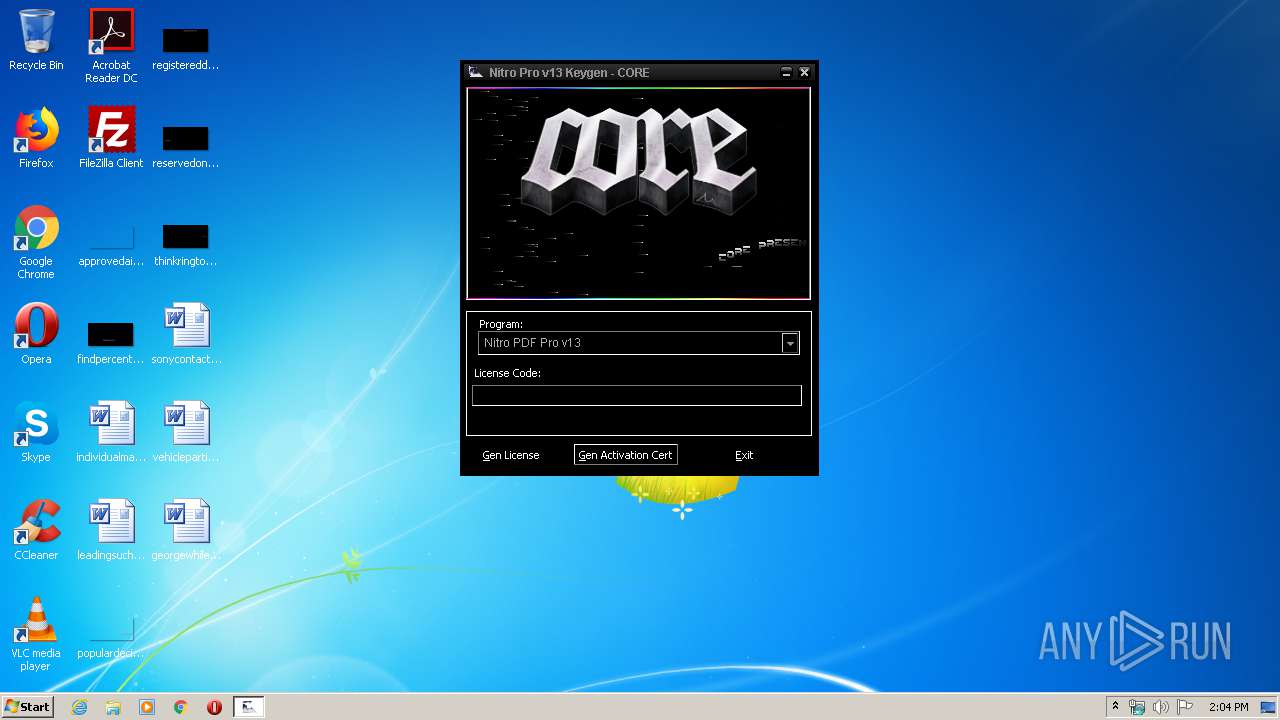
| File name: | keygen.exe |
| Full analysis: | https://app.any.run/tasks/b0e78f58-cbb9-48d8-bac5-0f6c18f0b65b |
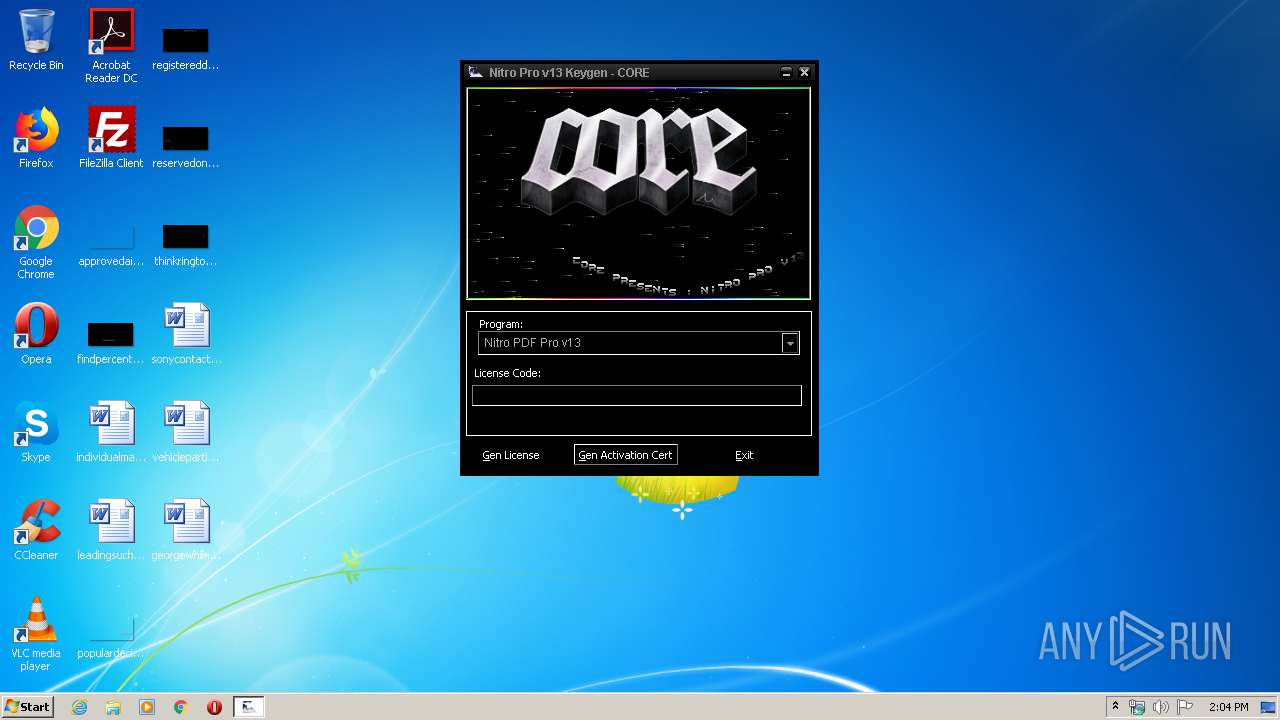
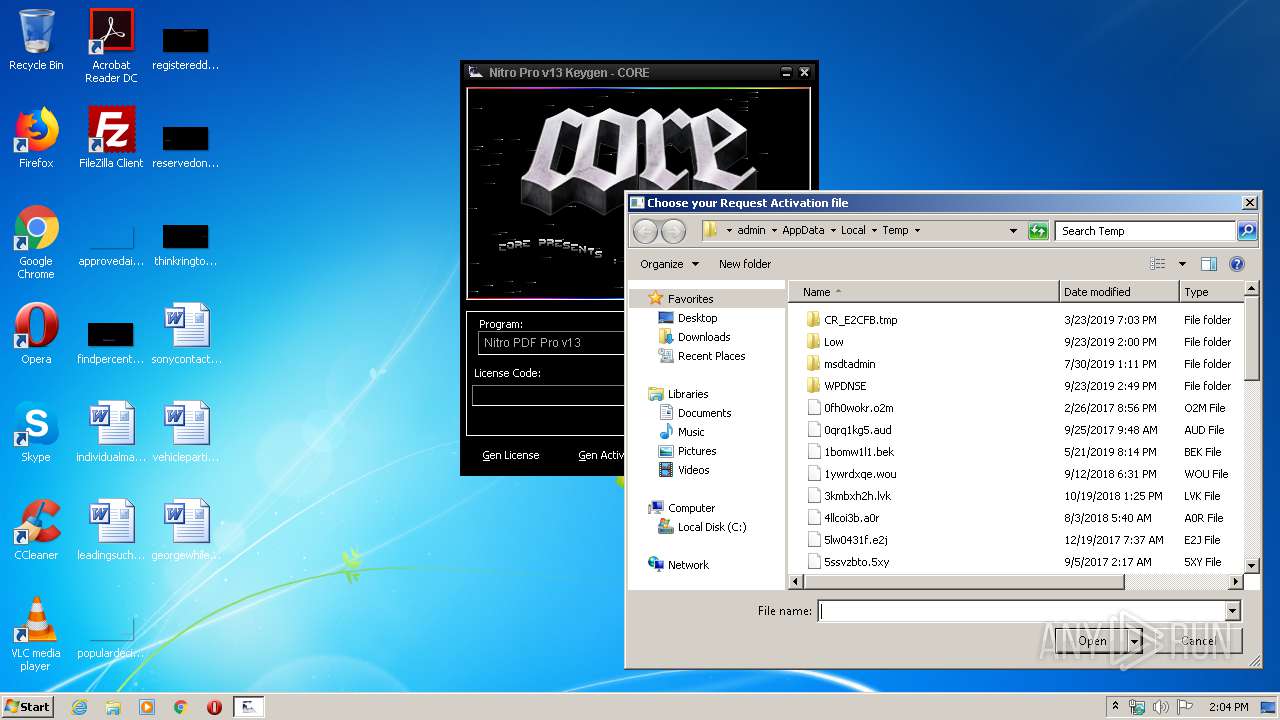
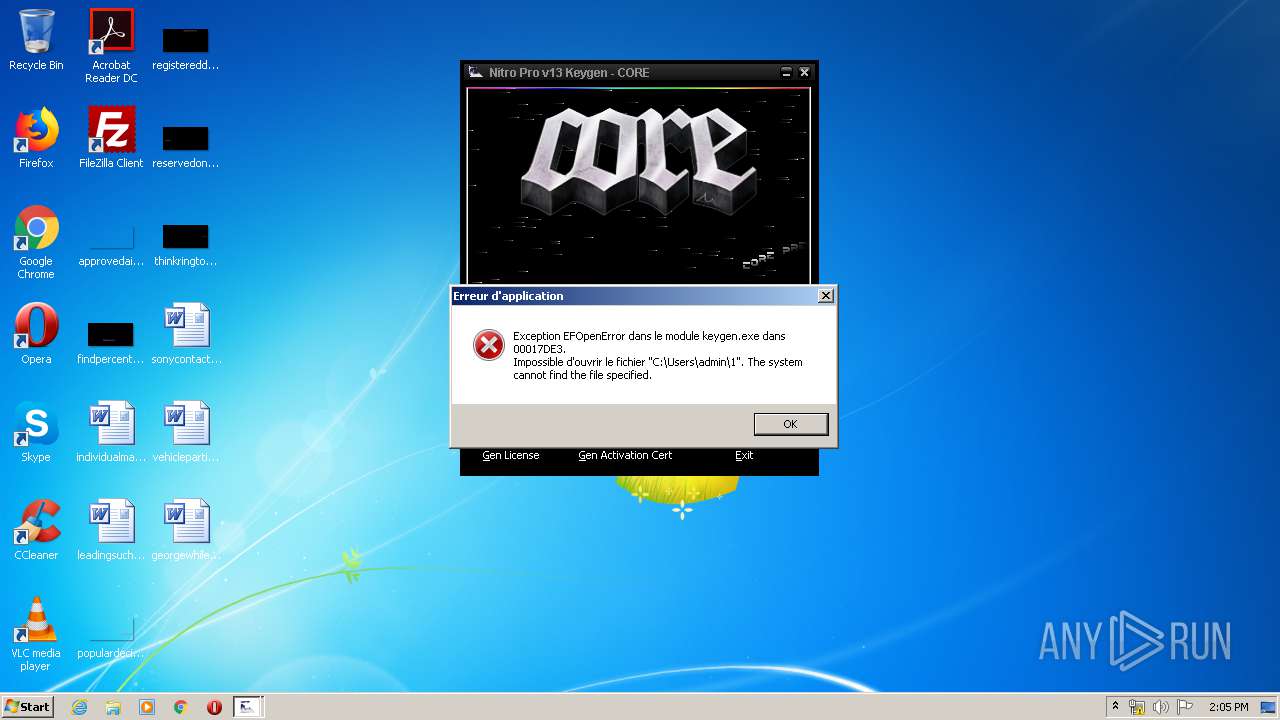
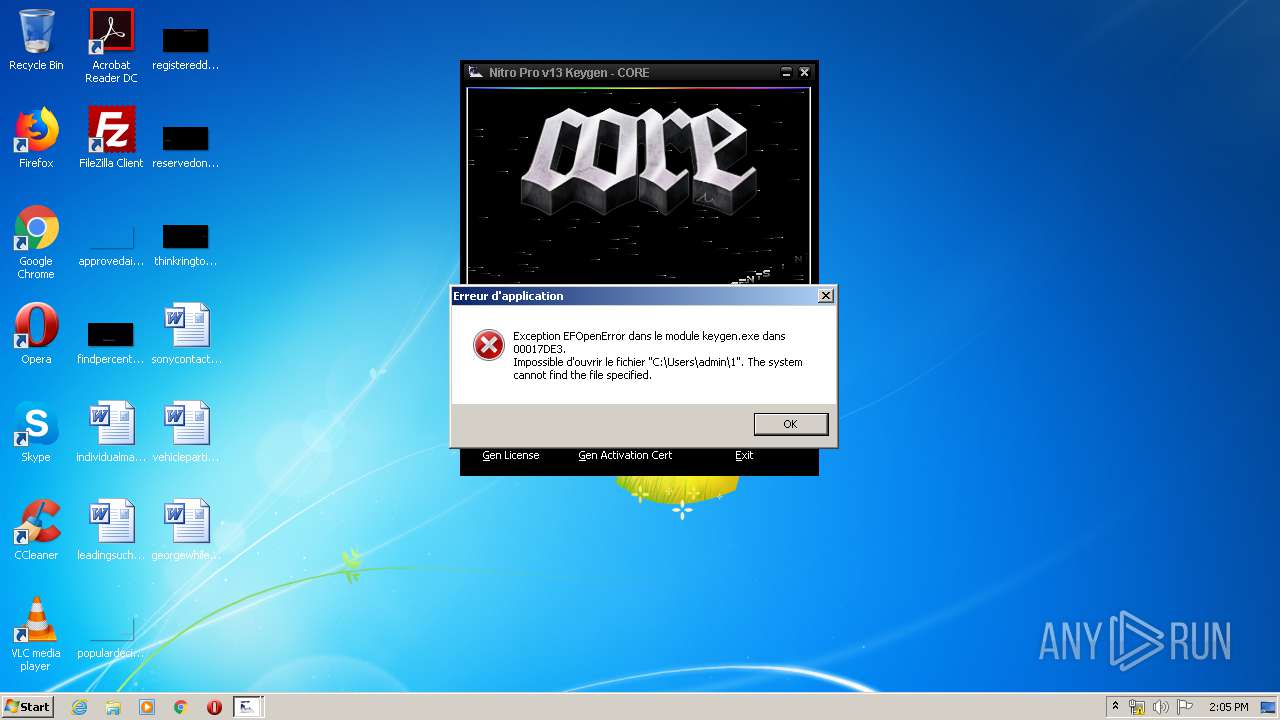
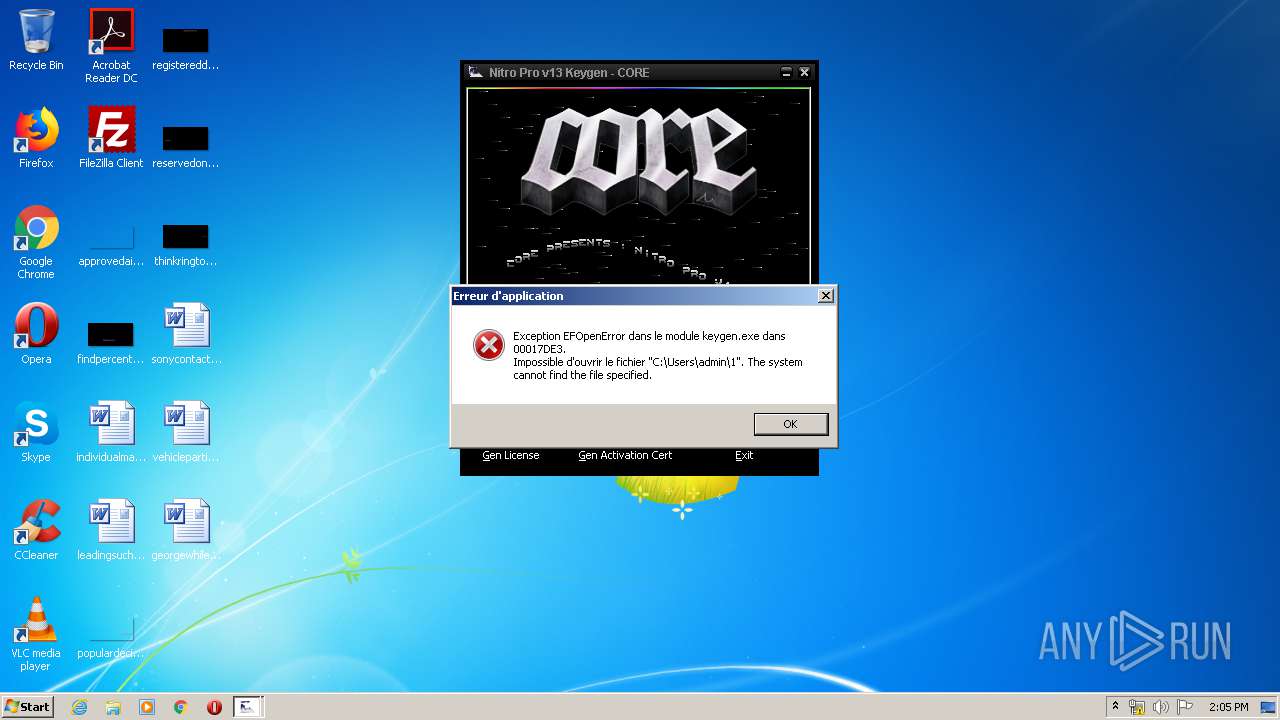
| Verdict: | Suspicious activity |
| Analysis date: | March 08, 2020, 14:03:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, PECompact2 compressed |
| MD5: | 1537DFB19E396EE3687019D65B59DB97 |
| SHA1: | D0C35E7C5B3A6D0C9195408E21D28FD33020A0DA |
| SHA256: | 4A435E0B87E8BD6F3E9F9B306F661FF5428017F33F742FA0788107212757F64C |
| SSDEEP: | 6144:nCWyPqAbxbDv6qjWYN0JdGn/oq/PO3sPQ/aH8ooxZPfv8I8:CQ2DvjjLNkdGn/oWPa1/aHCfb8 |
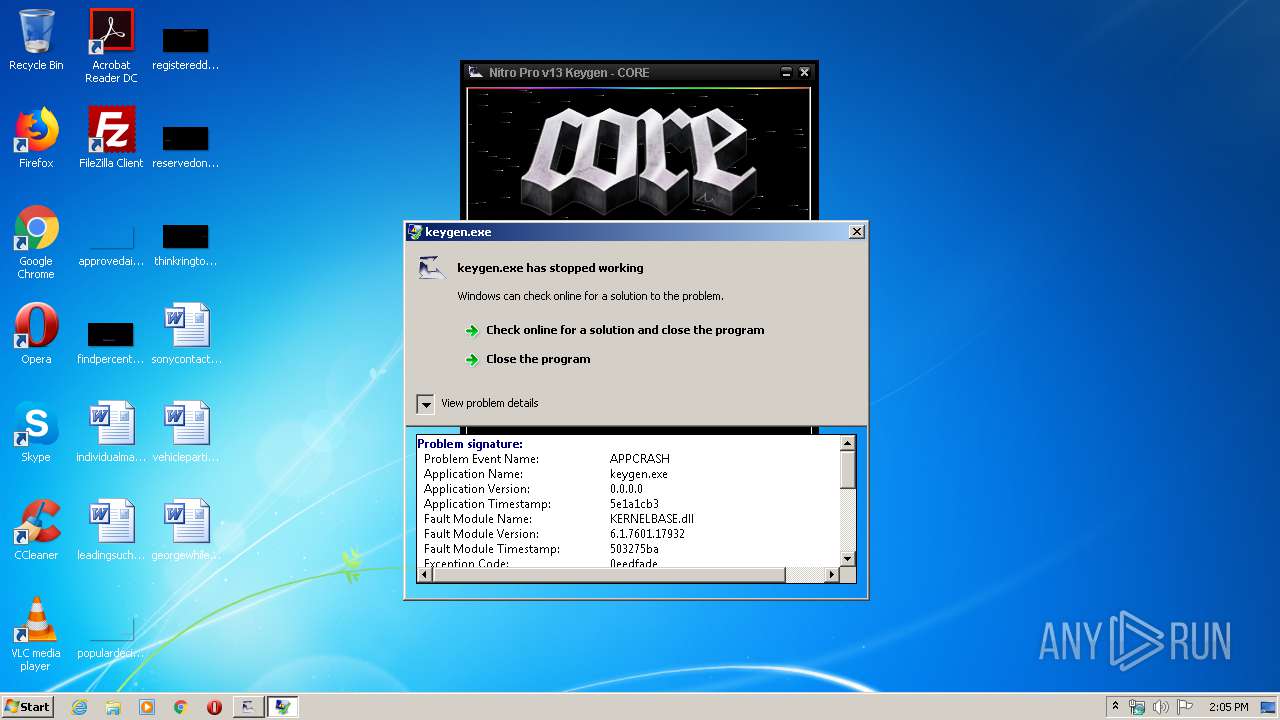
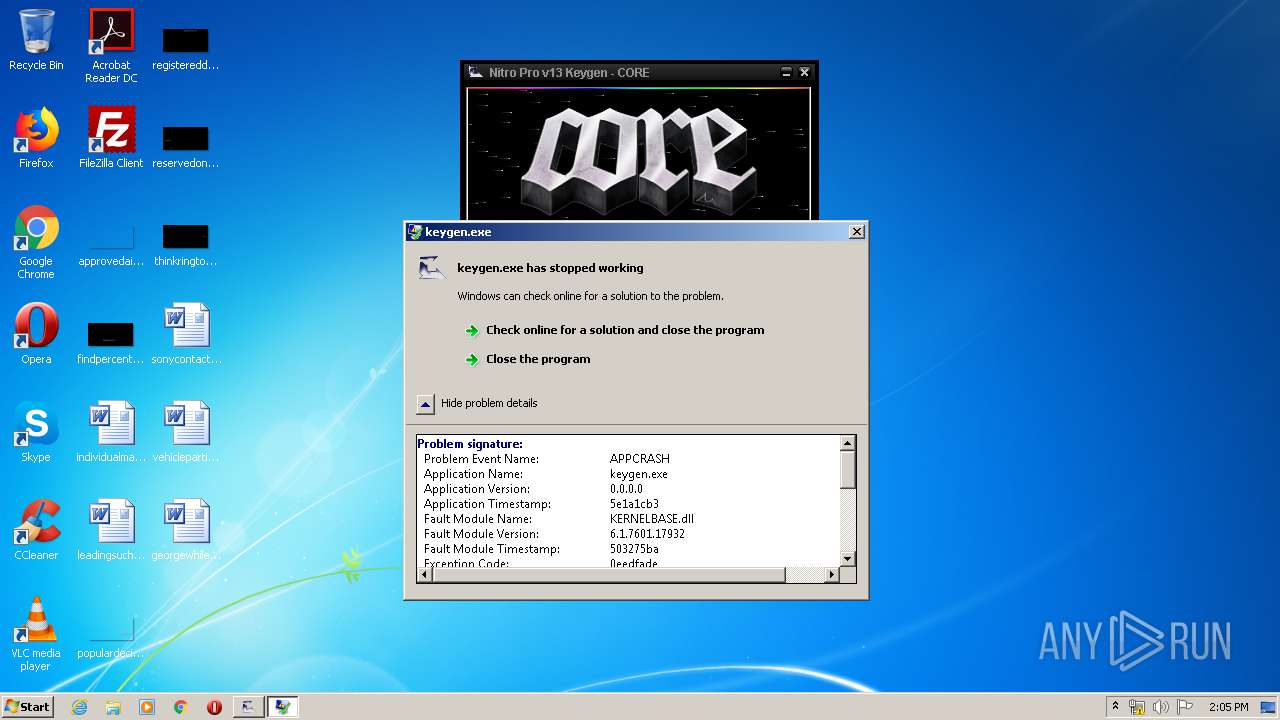
MALICIOUS
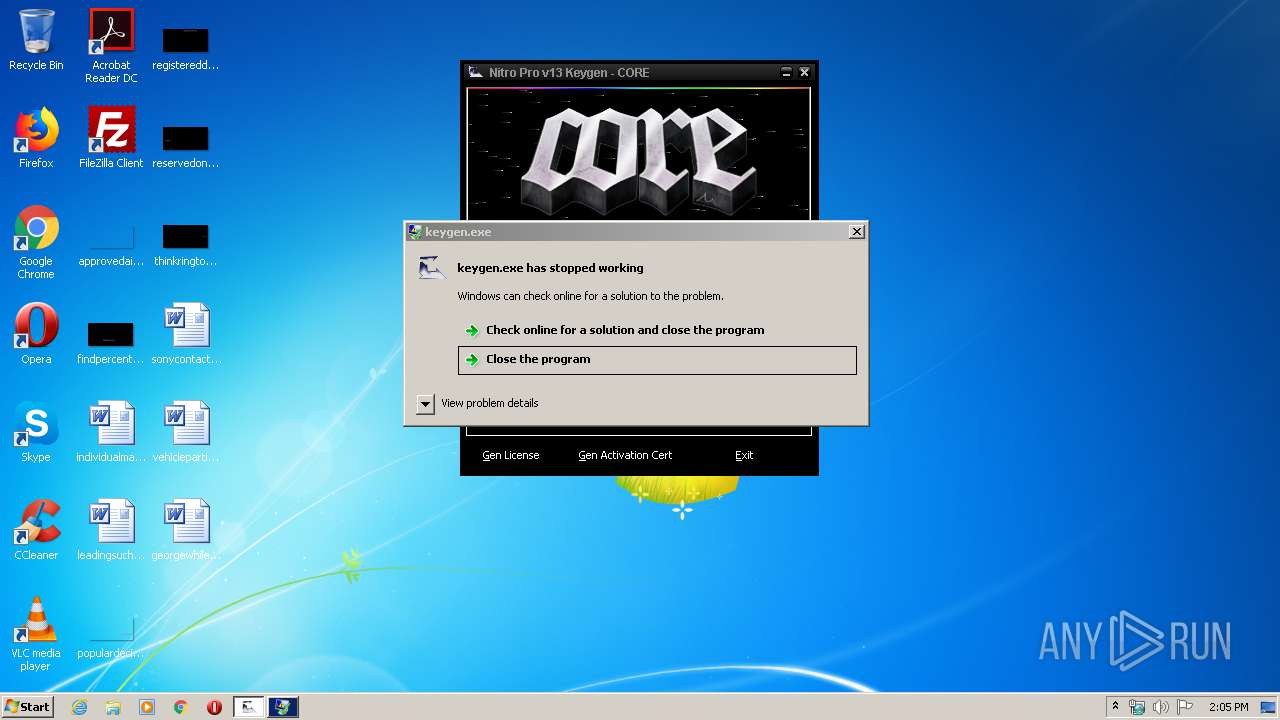
Loads dropped or rewritten executable
- WerFault.exe (PID: 1516)
- keygen.exe (PID: 3040)
SUSPICIOUS
Executable content was dropped or overwritten
- keygen.exe (PID: 3040)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (v2.x) (50.1) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (35.2) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.5) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Win16/32 Executable Delphi generic (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:01:11 20:06:27+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 459776 |
| InitializedDataSize: | 345600 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Jan-2020 19:06:27 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 2 |
| Time date stamp: | 11-Jan-2020 19:06:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000CE000 | 0x0004D200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99938 |
.rsrc | 0x000CF000 | 0x00004000 | 0x00003C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.13465 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 0 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 0 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 2.07909 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 0 | 308 | UNKNOWN | English - United States | RT_CURSOR |
5 | 0 | 308 | UNKNOWN | English - United States | RT_CURSOR |
6 | 0 | 308 | UNKNOWN | English - United States | RT_CURSOR |
7 | 0 | 308 | UNKNOWN | English - United States | RT_CURSOR |
101 | 0 | 444 | UNKNOWN | English - United States | RT_DIALOG |
130 | 0 | 227 | UNKNOWN | UNKNOWN | RT_RCDATA |
131 | 0 | 222 | UNKNOWN | UNKNOWN | RT_RCDATA |
Imports
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
kernel32.dll |
msimg32.dll |
ole32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Total processes
39
Monitored processes
2
Malicious processes
0
Suspicious processes
1
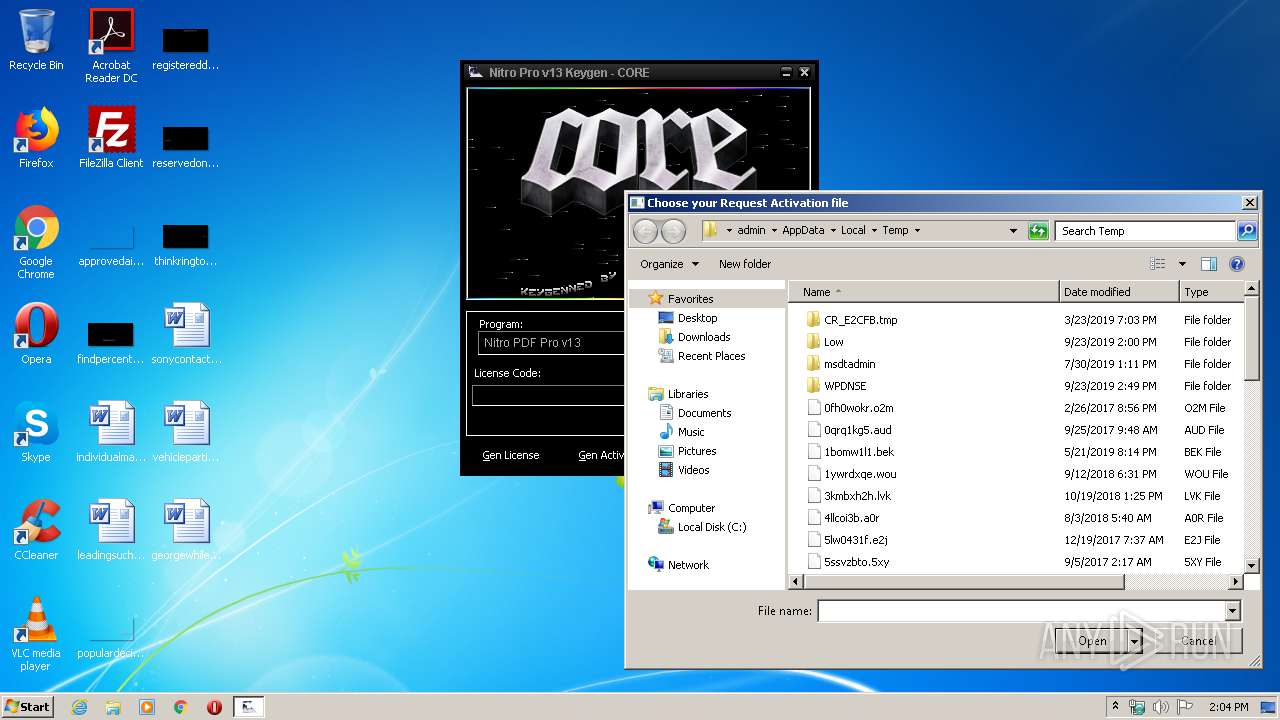
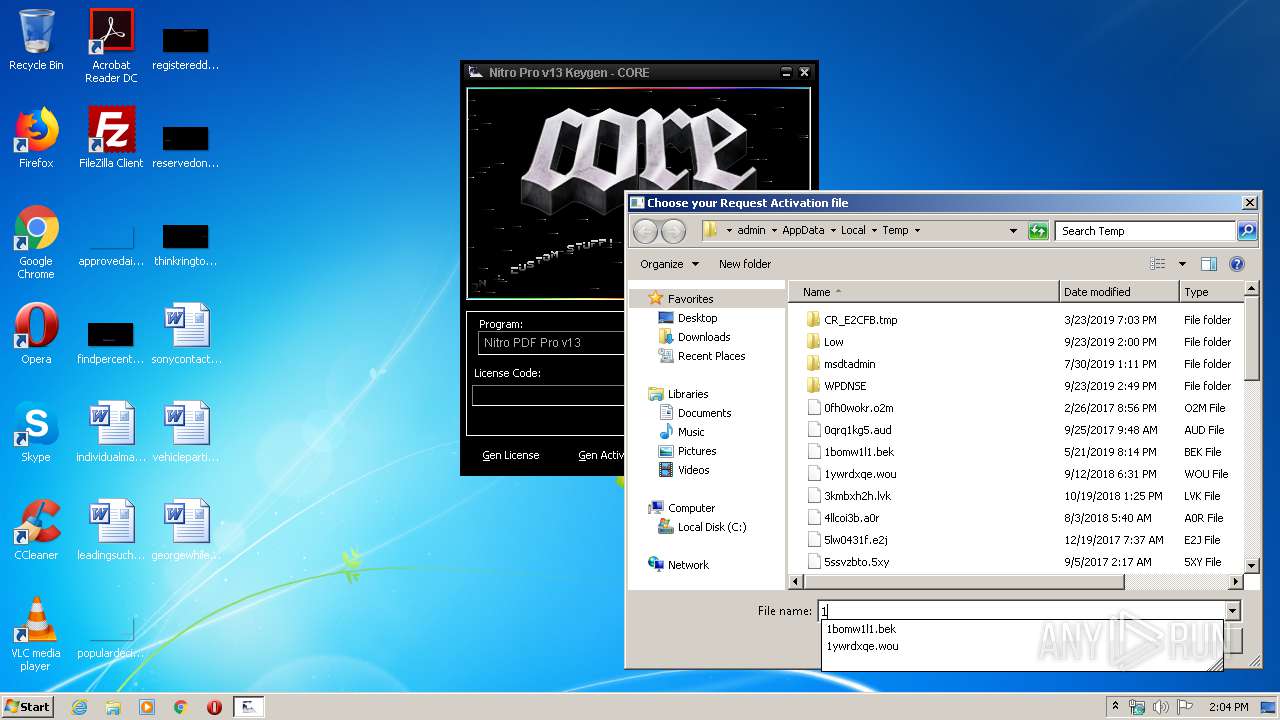
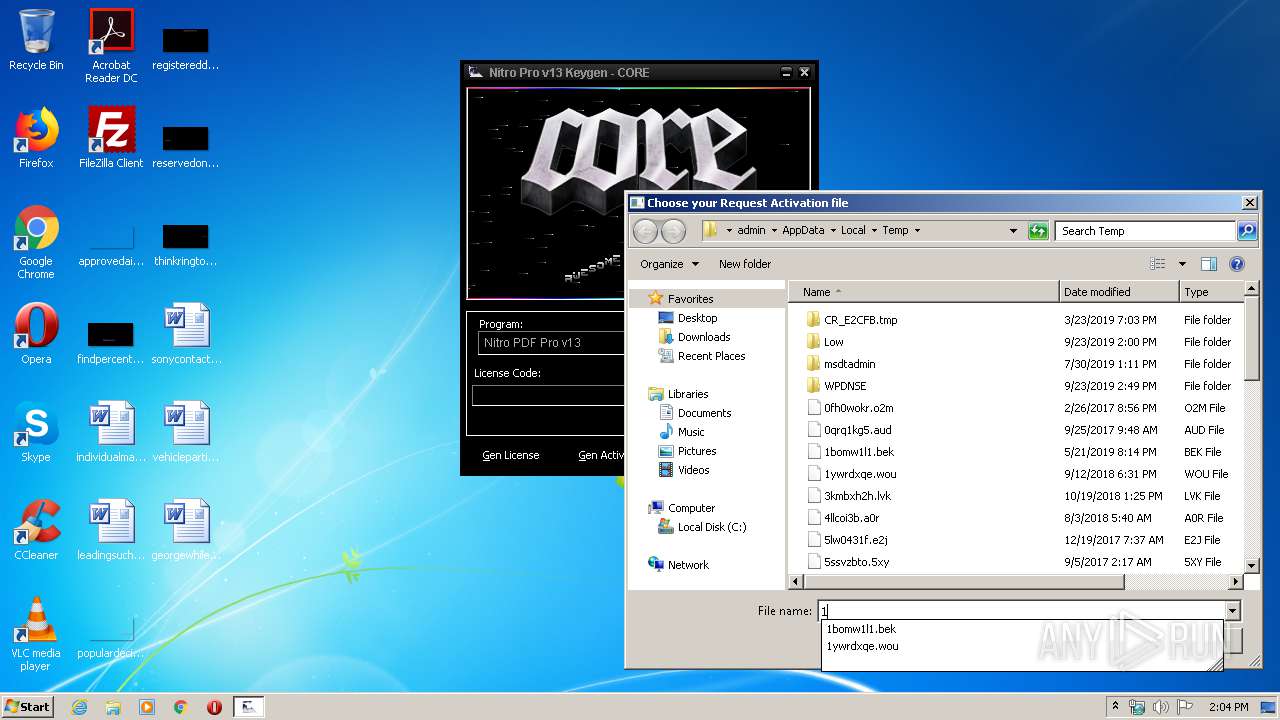
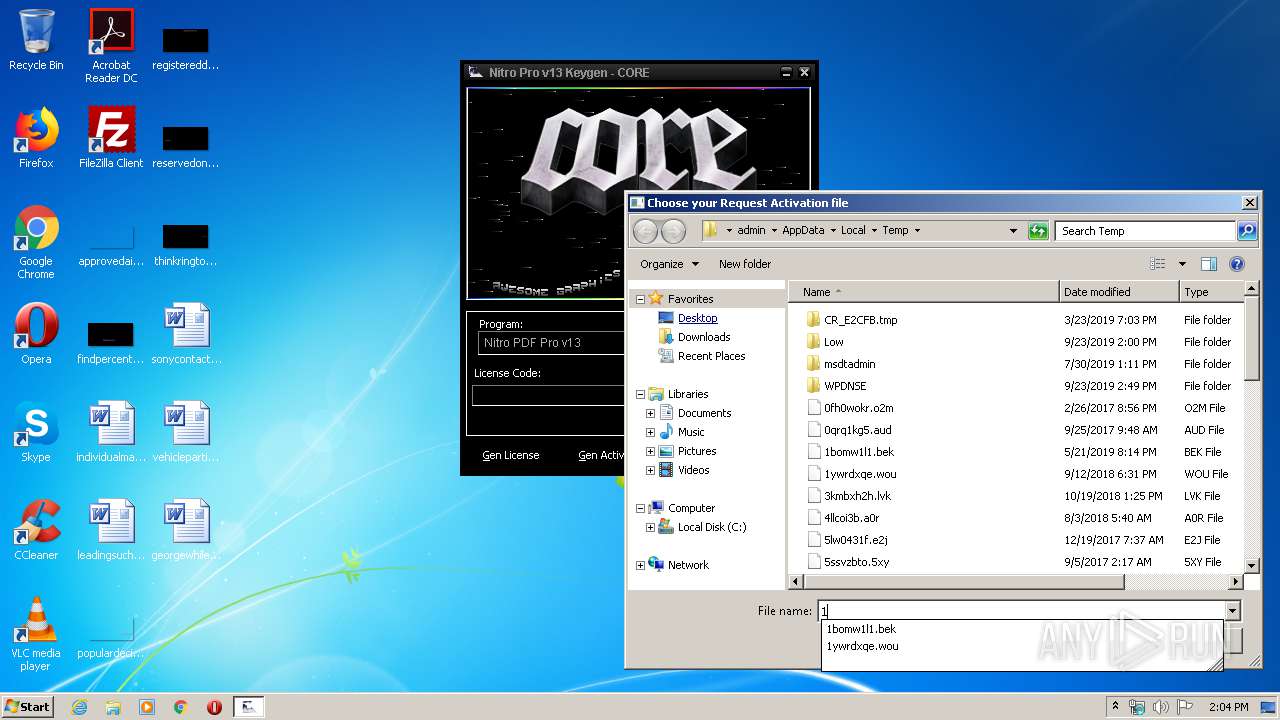
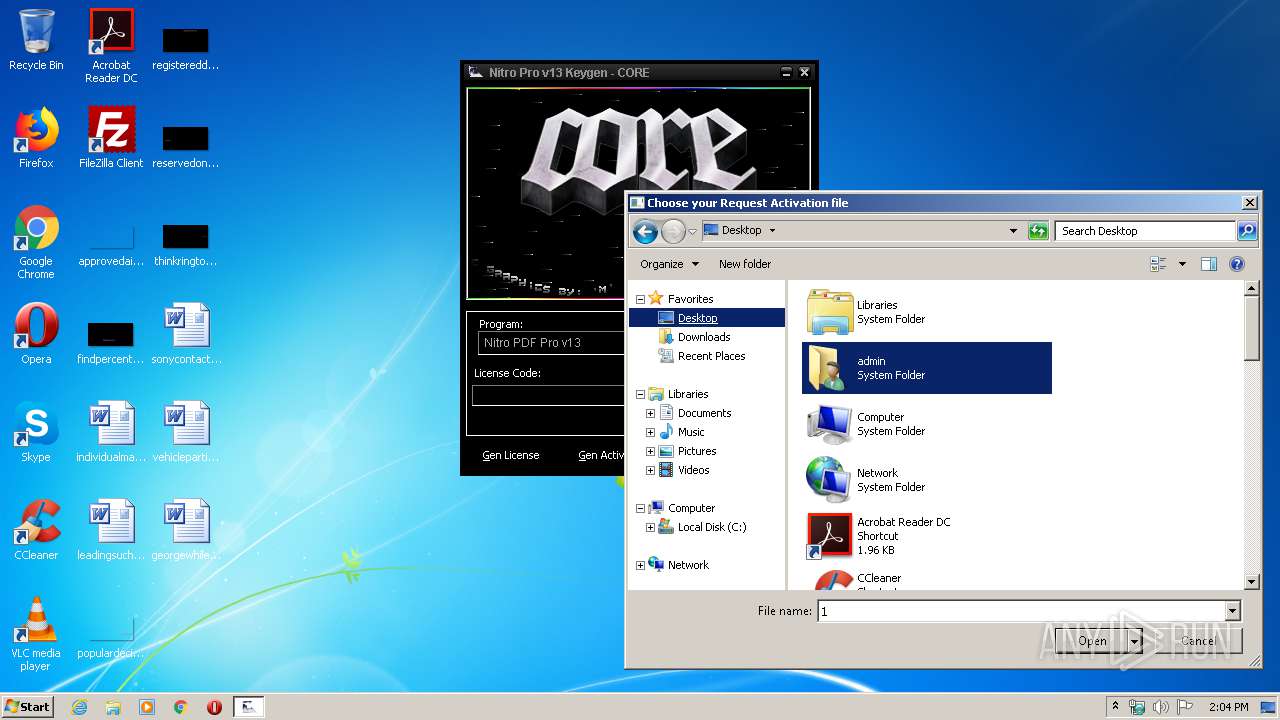
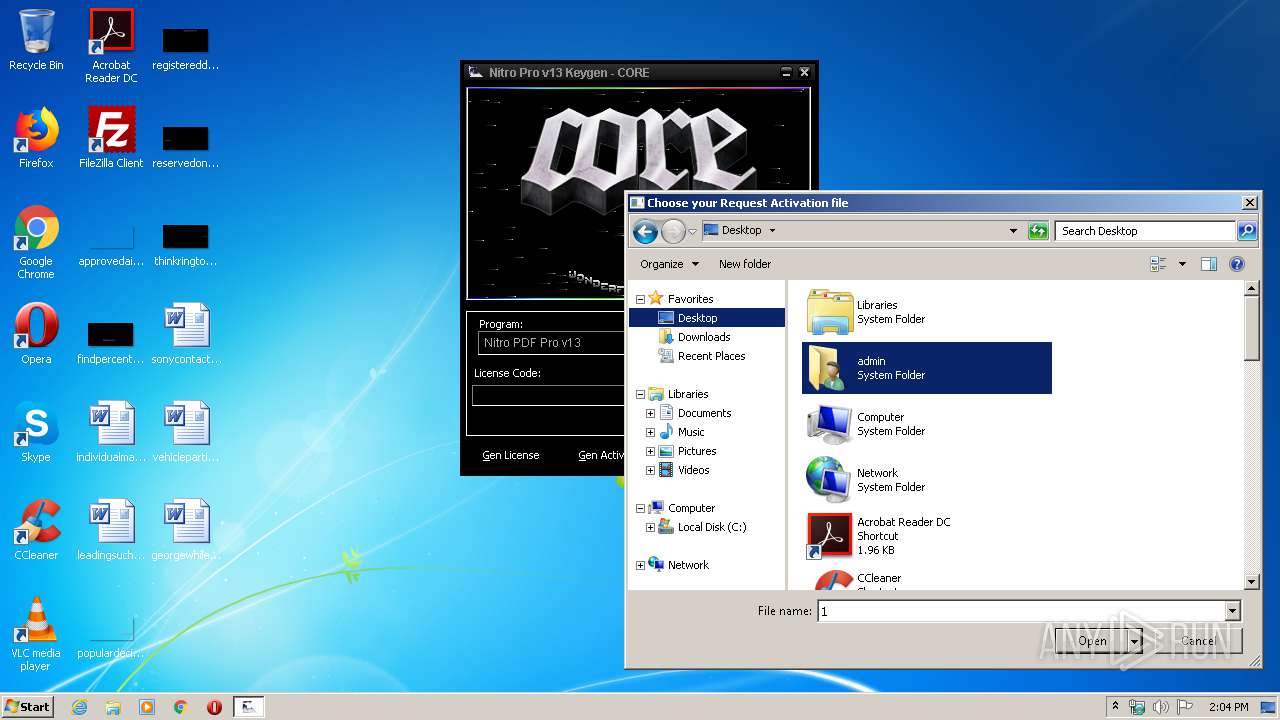
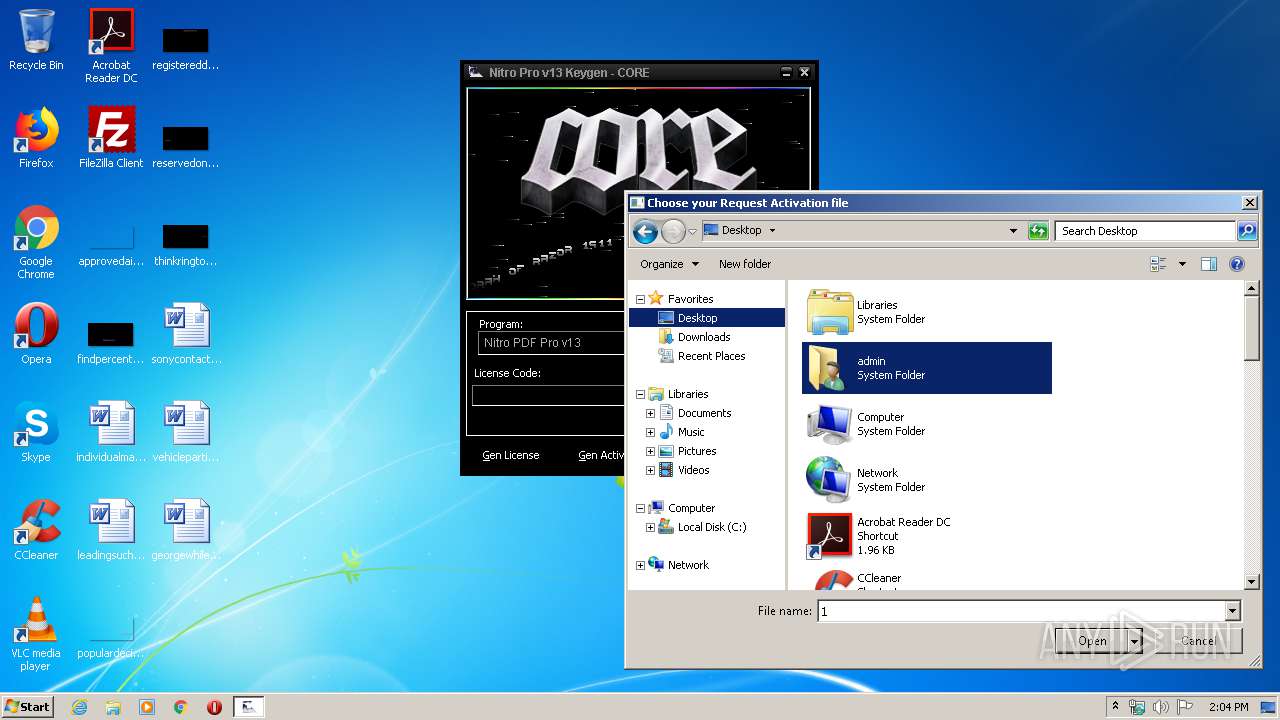
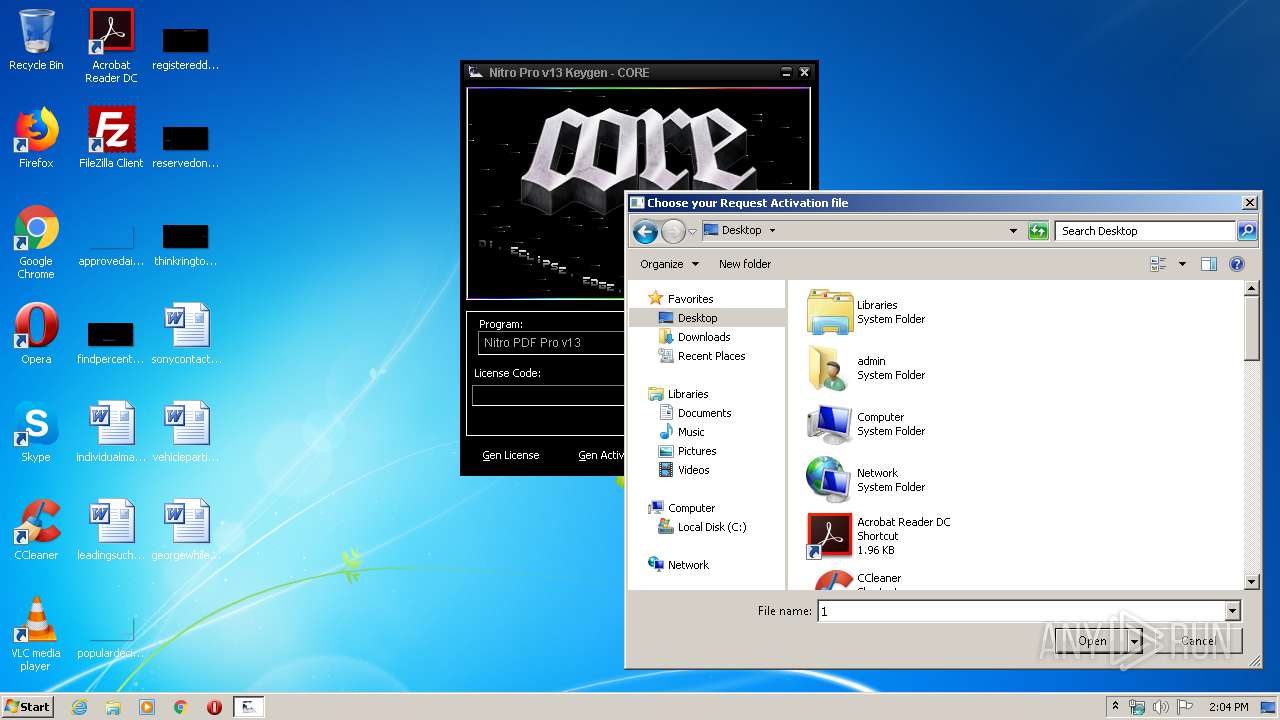
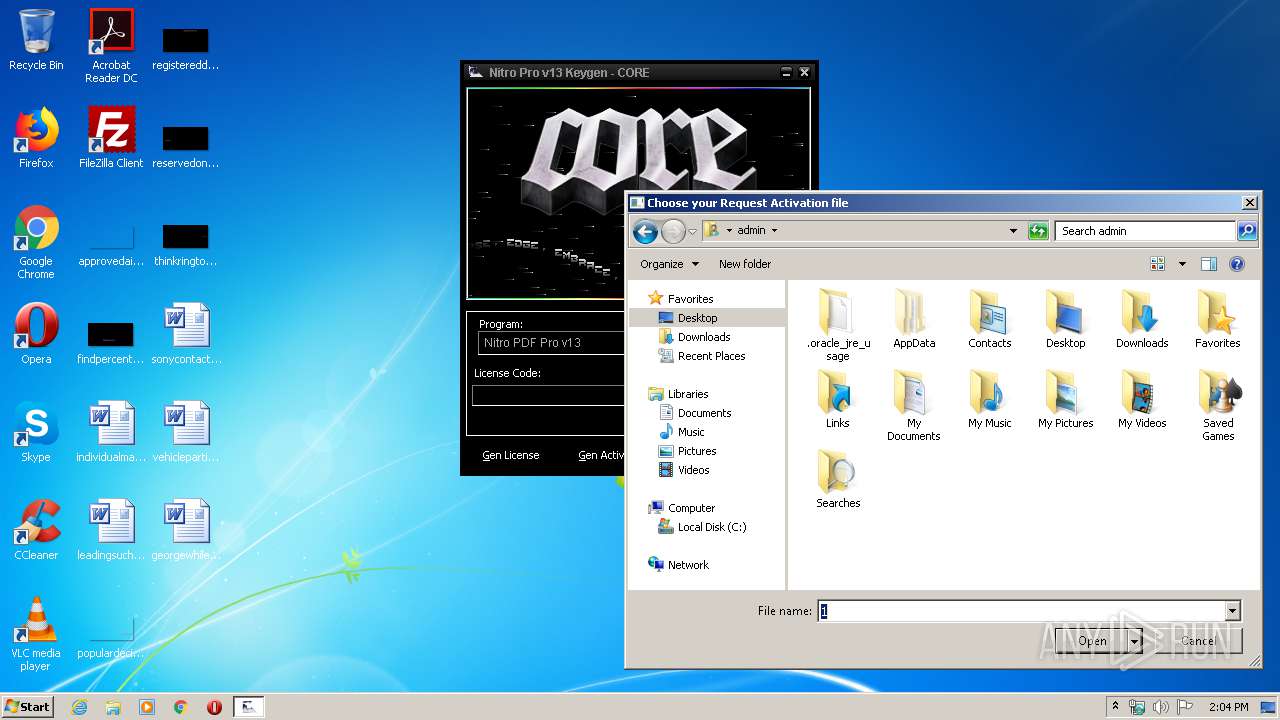
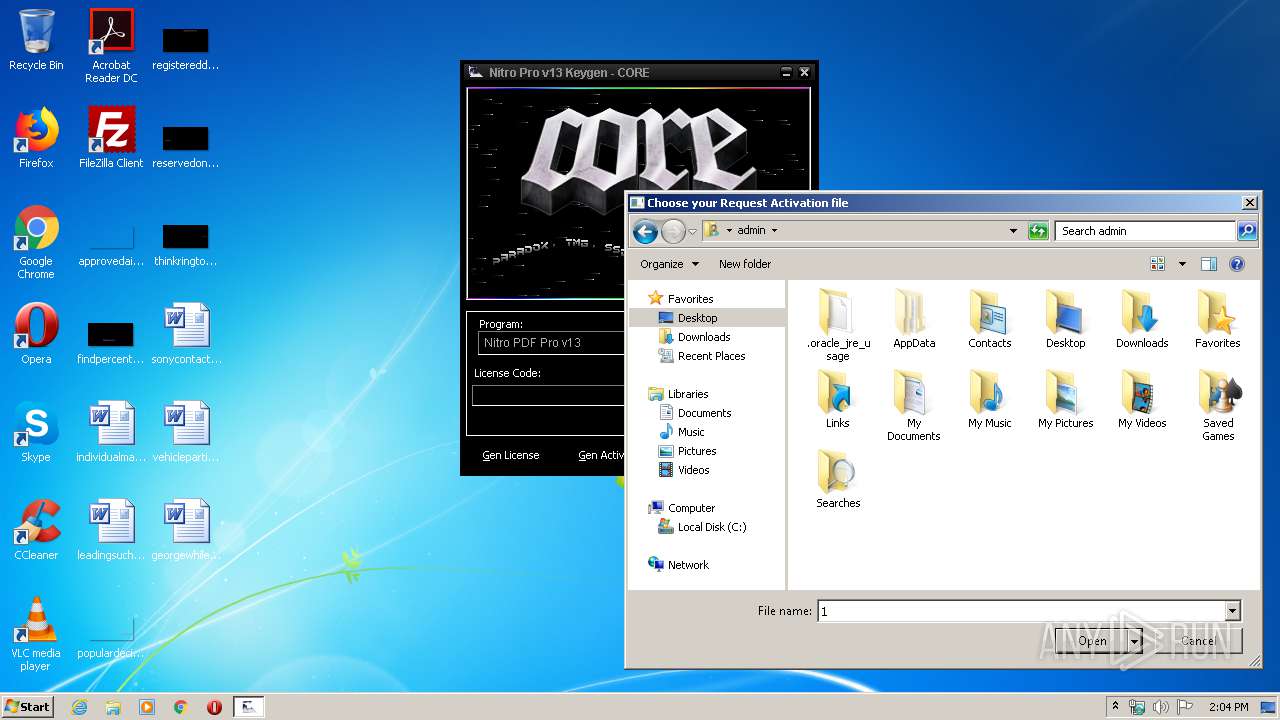
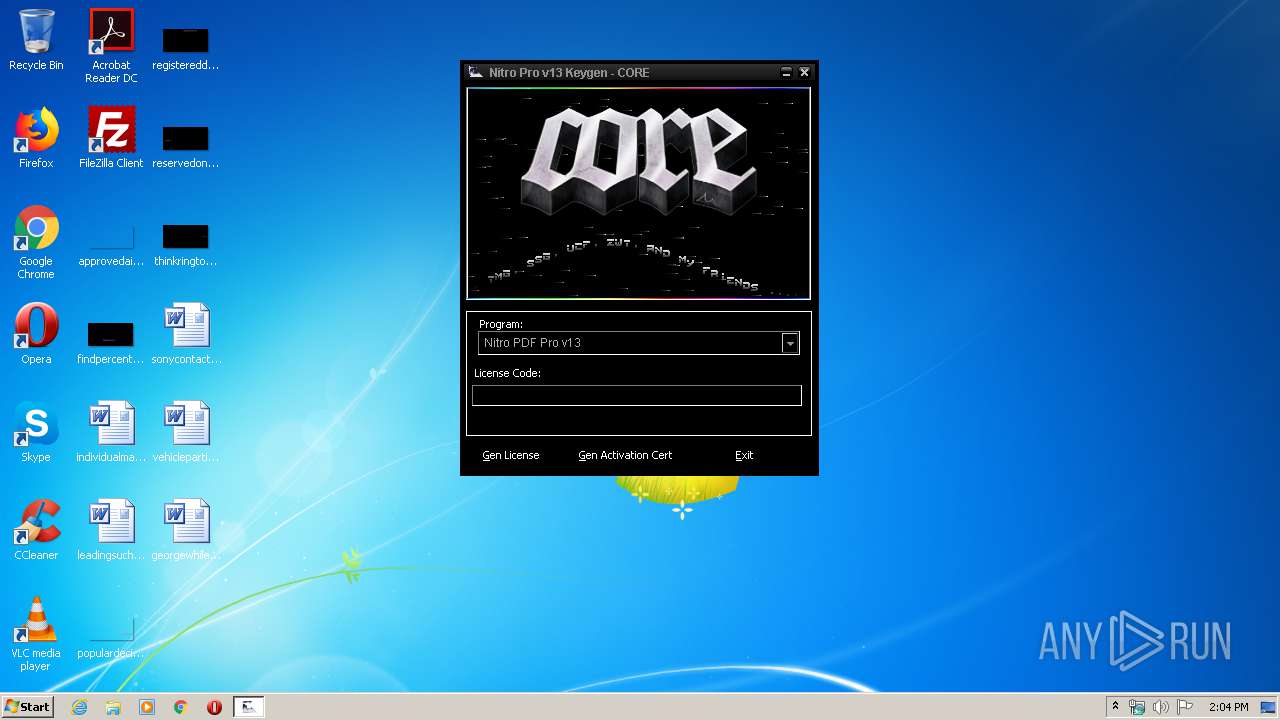
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1516 | C:\Windows\system32\WerFault.exe -u -p 3040 -s 1528 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
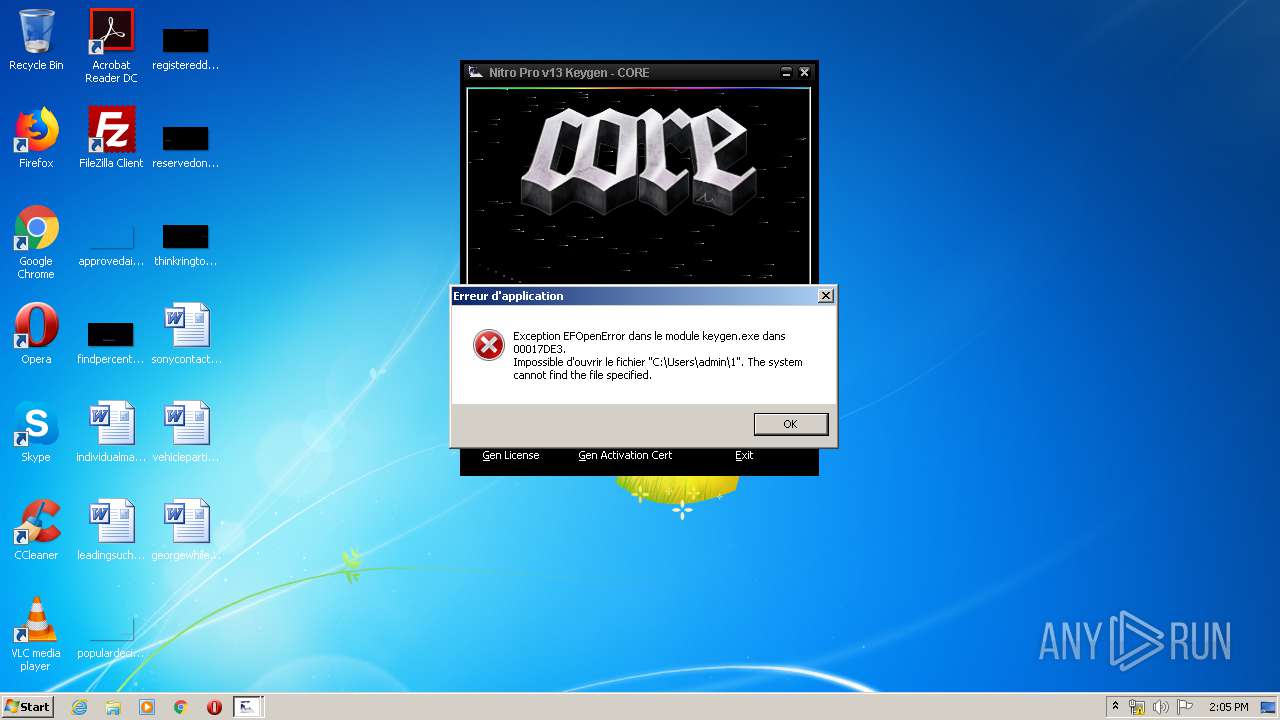
| 3040 | "C:\Users\admin\AppData\Local\Temp\keygen.exe" | C:\Users\admin\AppData\Local\Temp\keygen.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
Total events
893
Read events
742
Write events
150
Delete events
1
Modification events
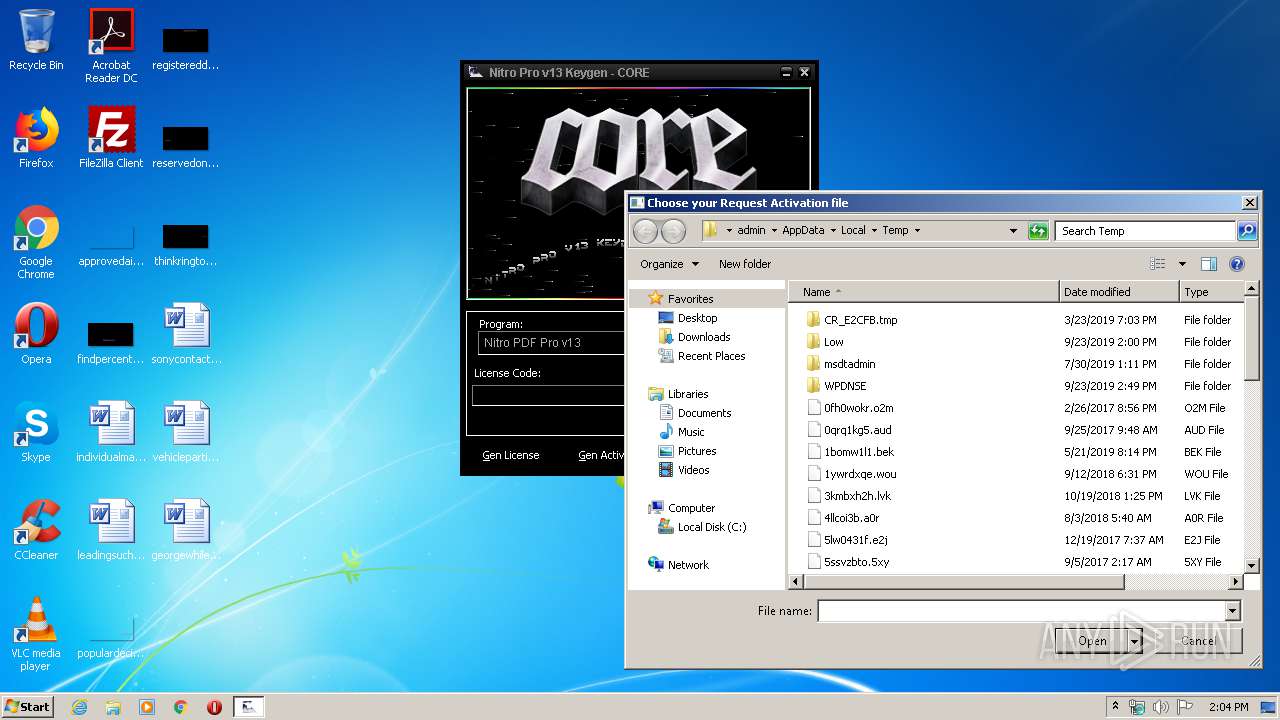
| (PID) Process: | (3040) keygen.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3040) keygen.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0700000001000000020000000A00000009000000080000000000000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3040) keygen.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\103\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
| (PID) Process: | (3040) keygen.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3040) keygen.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\103\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (3040) keygen.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\103\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
| (PID) Process: | (3040) keygen.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\103\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | FFlags |
Value: 1092616257 | |||
| (PID) Process: | (3040) keygen.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\103\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | IconSize |
Value: 16 | |||
| (PID) Process: | (3040) keygen.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\103\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | ColInfo |
Value: 00000000000000000000000000000000FDDFDFFD100000000000000000000000040000001800000030F125B7EF471A10A5F102608C9EEBAC0A0000001001000030F125B7EF471A10A5F102608C9EEBAC0E0000007800000030F125B7EF471A10A5F102608C9EEBAC040000007800000030F125B7EF471A10A5F102608C9EEBAC0C00000050000000 | |||
| (PID) Process: | (3040) keygen.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\103\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | Sort |
Value: 000000000000000000000000000000000100000030F125B7EF471A10A5F102608C9EEBAC0A00000001000000 | |||
Executable files
3
Suspicious files
1
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3040 | keygen.exe | C:\Users\admin\AppData\Local\Temp\Test.dat | — | |
MD5:— | SHA256:— | |||
| 1516 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportArchive\AppCrash_keygen.exe_7c5ca718f9246b90aa56f593e6c1af83feb7f9_054b50f2\Report.wer | binary | |
MD5:— | SHA256:— | |||
| 1516 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\keygen.exe.3040.dmp | dmp | |
MD5:— | SHA256:— | |||
| 3040 | keygen.exe | C:\Users\admin\AppData\Local\Temp\edODcYZHiiYKOeNubhWK.DLL | executable | |
MD5:E6144FB36C1FDC6BA1D1AFA9632588F8 | SHA256:B141412D0611571DF381C26186B3FC438C725D6E45AD66FD76413322C17A9AC6 | |||
| 3040 | keygen.exe | C:\Users\admin\AppData\Local\Temp\GgNEvFnHOQ.DLL | executable | |
MD5:E4EC57E8508C5C4040383EBE6D367928 | SHA256:8AD9E47693E292F381DA42DDC13724A3063040E51C26F4CA8E1F8E2F1DDD547F | |||
| 3040 | keygen.exe | C:\Users\admin\AppData\Local\Temp\oHqQctQvFpiuTqkLOyTD.DLL | executable | |
MD5:76A9565C5F51775719EEBDA1F25530A5 | SHA256:A1A7C4F74D4FE7784ED03709E5F946B94CC10A64E3AE0AD5A9A3BECE9A8A2C0A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
keygen.exe | %s%c%s%c%s |