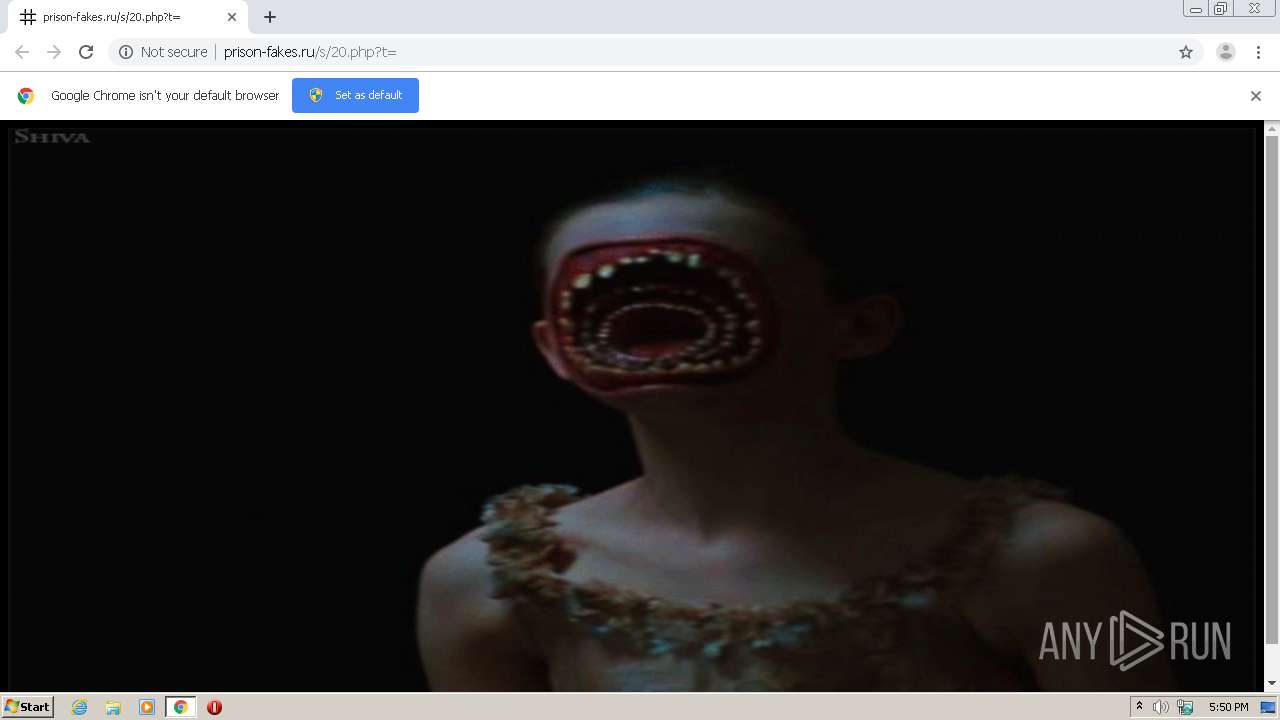
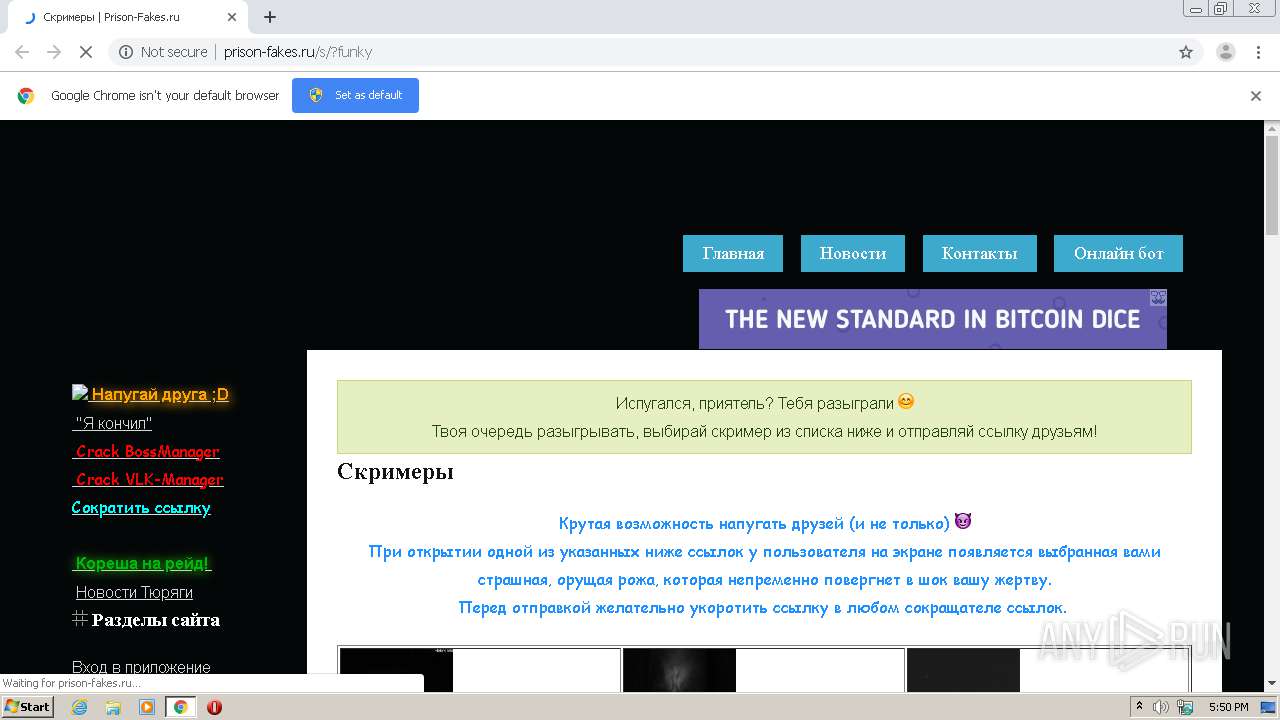
| URL: | http://prison-fakes.ru/s/20.php?t= |
| Full analysis: | https://app.any.run/tasks/6f2b9ce6-78c0-4e16-9c9f-7dec60684831 |
| Verdict: | Malicious activity |
| Analysis date: | November 26, 2020, 17:50:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BADF55B268B18E465A591D5DDEAC381E |
| SHA1: | 247D26D34CF7140E263515132160305410E91D19 |
| SHA256: | 4A302262D2AEA9D3F366F0F96A7AD4916B96DAA0B2D0404CF44DDA1BF89D304C |
| SSDEEP: | 3:N1KOXAIYvWsYX2Y:COXWYmY |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the computer name
- chrome.exe (PID: 3628)
- chrome.exe (PID: 2400)
- chrome.exe (PID: 2504)
Reads the hosts file
- chrome.exe (PID: 3628)
- chrome.exe (PID: 2504)
Checks supported languages
- chrome.exe (PID: 2400)
- chrome.exe (PID: 3628)
- chrome.exe (PID: 3280)
- chrome.exe (PID: 3528)
- chrome.exe (PID: 2820)
- chrome.exe (PID: 2560)
- chrome.exe (PID: 3932)
- chrome.exe (PID: 3892)
Application launched itself
- chrome.exe (PID: 3628)
Reads settings of System Certificates
- chrome.exe (PID: 2504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
12
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1080,8833393850117723751,7397097107622584508,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3911894509049792393 --mojo-platform-channel-handle=1044 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1080,8833393850117723751,7397097107622584508,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=13209402471417054944 --mojo-platform-channel-handle=1484 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1080,8833393850117723751,7397097107622584508,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13917094909387416524 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3324 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1080,8833393850117723751,7397097107622584508,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4174673357572613987 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2128 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1080,8833393850117723751,7397097107622584508,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10894902598603925862 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2136 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6de7a9d0,0x6de7a9e0,0x6de7a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1080,8833393850117723751,7397097107622584508,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1609590029645137541 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2472 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://prison-fakes.ru/s/20.php?t=" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1080,8833393850117723751,7397097107622584508,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10381160587721661837 --mojo-platform-channel-handle=4208 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1080,8833393850117723751,7397097107622584508,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2411343221210410027 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3828 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
5 136
Read events
5 091
Write events
42
Delete events
3
Modification events
| (PID) Process: | (3628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (4032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3628-13250886646533890 |
Value: 259 | |||
| (PID) Process: | (3628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
| (PID) Process: | (3628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (3628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
20
Text files
37
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG | text | |
MD5:7C660E4E4F3FD1572A688D89FA10F083 | SHA256:B53806CBAB21C324A1269CD4DA2260DC16433F3F4135784A72AE479F476C2087 | |||
| 3628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:002E7D1B1D33254423BA7F3730E3762E | SHA256:499183581E58D05A82903D68A16E5A19FCE2CB1AC431F6E5FF3C4C7BB30FB3AE | |||
| 3628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8D59E1D6856DFD5251CA22F88C53C8FD | SHA256:AA4D23B4F75FE030E529B8CEB04B9F542182120AF1F82D50577461DC2E3FB8A6 | |||
| 3628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG | text | |
MD5:B43EF6D9C98C9342927925DED0C556AC | SHA256:97B8FBB050D4B11A5CB3510312C40798F40992B508F2DBED94296C37950BE0F8 | |||
| 3628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG | text | |
MD5:DD7C0BFDD74CC3B3FEC0F1F823420FE8 | SHA256:36897356FFEAB172368D87980014D0B62AA5AF8FF2CDD5FB8D999B6CF2D95C13 | |||
| 3628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:184DBE339392AC7F1D5C45EDE6496561 | SHA256:DB35161FDB22F465DAA22B38DAEE789CB14946E95B09D7E911FC545C1849D164 | |||
| 3628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG | — | |
MD5:— | SHA256:— | |||
| 3628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:D40150F7161EA16CBE92CDA68420FD63 | SHA256:E1D75CF4B9C6915BF6718F015419BC67DAC1C3F566999EEFCF2D8A6BCB894B1A | |||
| 3628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG | text | |
MD5:D3D94119FADA33B877BAB87C1E343E8E | SHA256:5DD57145249CCE1F40FF94C9F41A4CE89B9BB63DF00E865D863BD10D70D354D4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
82
TCP/UDP connections
48
DNS requests
35
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2504 | chrome.exe | GET | 200 | 87.236.16.203:80 | http://prison-fakes.ru/s/20.php?t= | RU | html | 947 b | malicious |
2504 | chrome.exe | GET | 200 | 87.236.16.203:80 | http://prison-fakes.ru/s/js/block_copy.js | RU | text | 180 b | malicious |
2504 | chrome.exe | GET | 200 | 87.236.16.203:80 | http://prison-fakes.ru/favicon.ico | RU | image | 1.12 Kb | malicious |
2504 | chrome.exe | GET | 206 | 87.236.16.203:80 | http://prison-fakes.ru/s/mp3/2.mp3 | RU | mp3 | 117 Kb | malicious |
2504 | chrome.exe | GET | 200 | 87.236.16.203:80 | http://prison-fakes.ru/site_style.css?2 | RU | text | 1.17 Kb | malicious |
2504 | chrome.exe | GET | 200 | 87.236.16.203:80 | http://prison-fakes.ru/s/gif/20.gif | RU | image | 880 Kb | malicious |
2504 | chrome.exe | GET | 302 | 87.236.16.203:80 | http://prison-fakes.ru/images/new_year_logo.png | RU | html | 288 b | malicious |
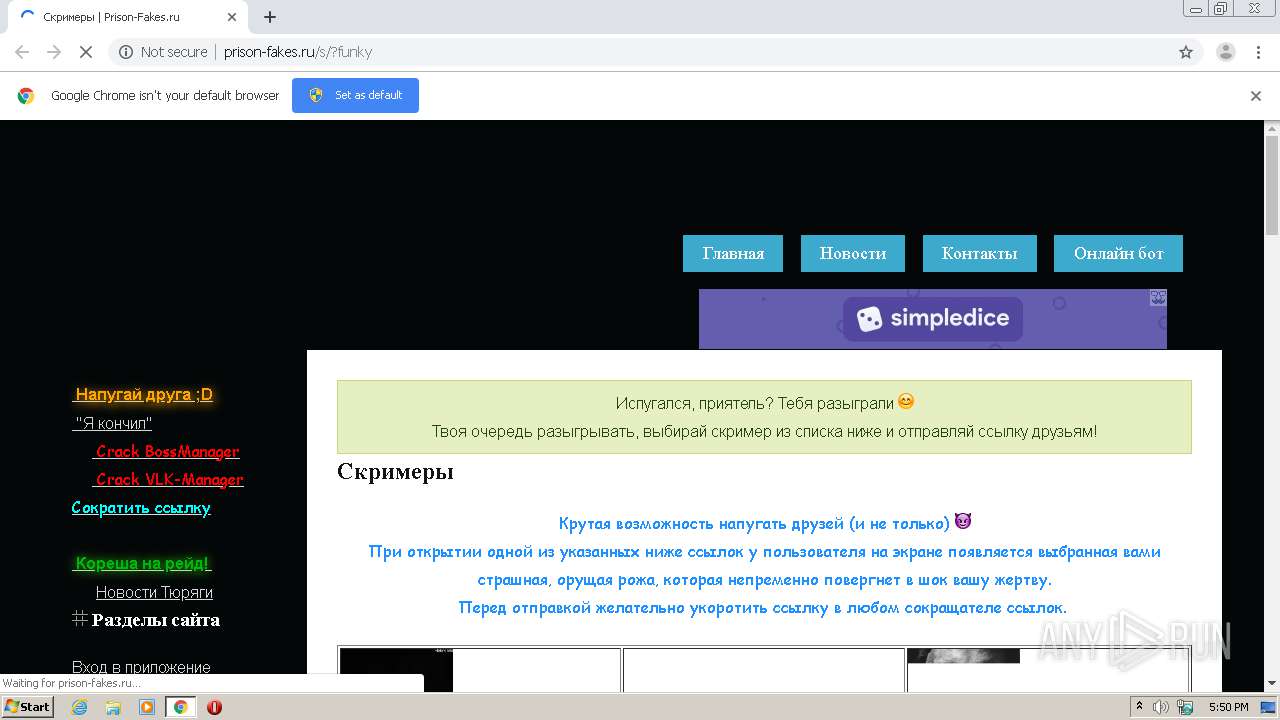
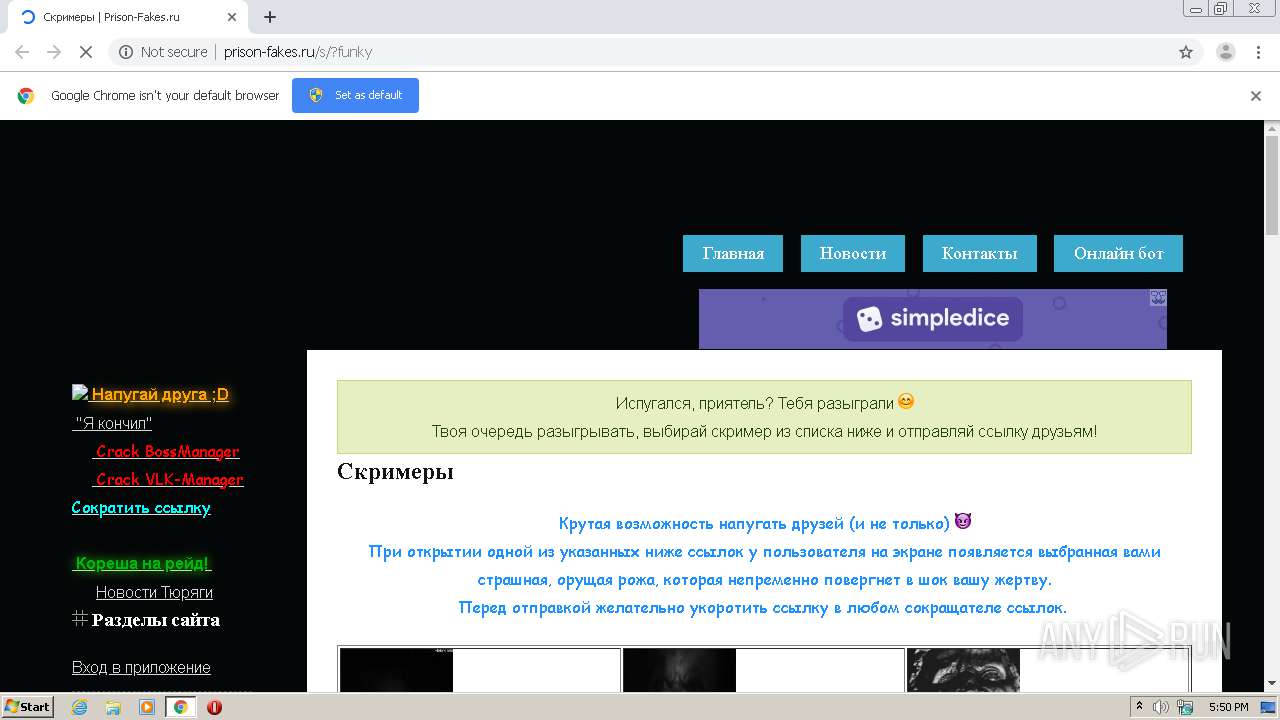
2504 | chrome.exe | GET | 200 | 87.236.16.203:80 | http://prison-fakes.ru/s/?funky | RU | html | 4.82 Kb | malicious |
2504 | chrome.exe | GET | 200 | 87.236.16.203:80 | http://prison-fakes.ru/pc.php?sid=265935 | RU | — | — | malicious |
2504 | chrome.exe | GET | 200 | 87.236.16.203:80 | http://prison-fakes.ru/php_code.php?sid=265935 | RU | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2504 | chrome.exe | 206.54.181.244:80 | rydresa.info | Webzilla B.V. | NL | unknown |
2504 | chrome.exe | 172.217.23.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
2504 | chrome.exe | 85.10.201.130:443 | static.a-ads.com | Hetzner Online GmbH | DE | suspicious |
2504 | chrome.exe | 88.85.75.116:80 | rydresa.info | Webzilla B.V. | NL | unknown |
2504 | chrome.exe | 88.212.201.198:443 | counter.yadro.ru | United Network LLC | RU | suspicious |
2504 | chrome.exe | 88.85.75.98:80 | rydresa.info | Webzilla B.V. | NL | suspicious |
2504 | chrome.exe | 185.94.237.101:443 | poweredby.jads.co | Mojohost B.v. | NL | suspicious |
2504 | chrome.exe | 88.85.84.106:443 | doptik.ru | Webzilla B.V. | NL | unknown |
2504 | chrome.exe | 185.94.237.101:80 | poweredby.jads.co | Mojohost B.v. | NL | suspicious |
2504 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
prison-fakes.ru |
| malicious |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
vk.com |
| whitelisted |
rydresa.info |
| suspicious |
shonadoer.vk-admin.ru |
| malicious |
ad.a-ads.com |
| whitelisted |
telonko.com |
| unknown |
fonts.gstatic.com |
| whitelisted |
counter.yadro.ru |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |