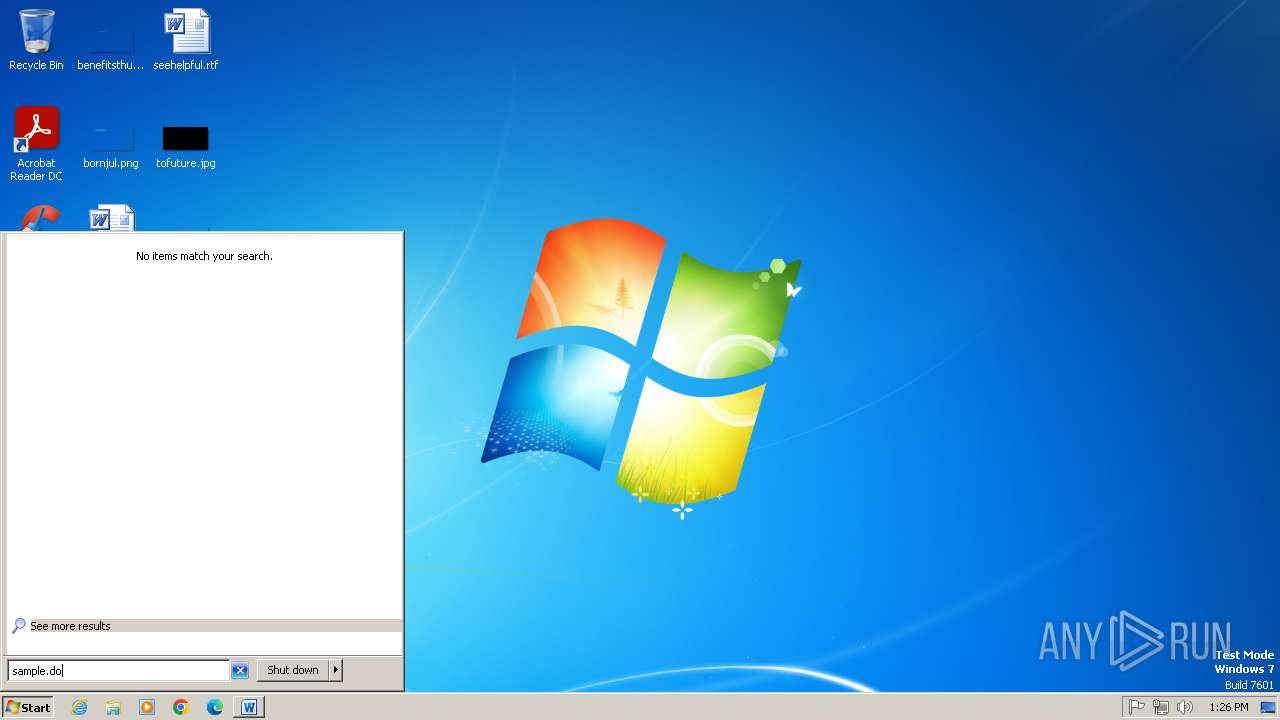
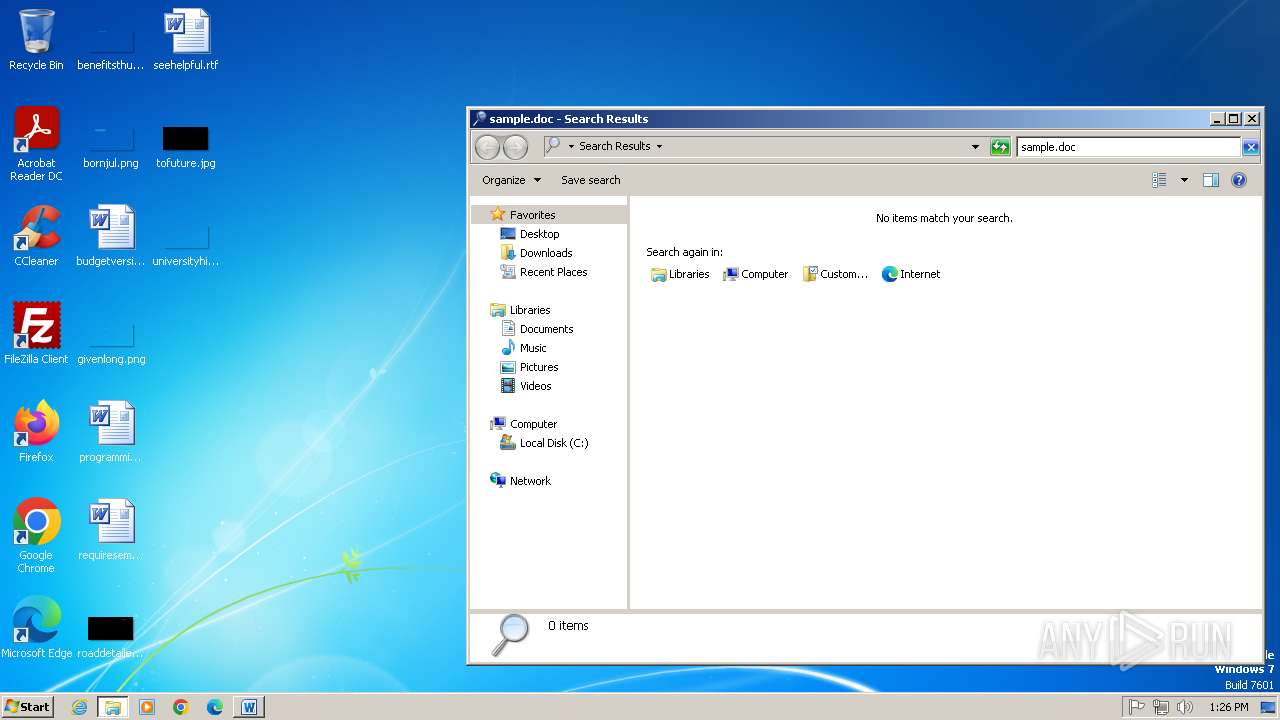
| File name: | sample.doc |
| Full analysis: | https://app.any.run/tasks/ec3cce94-1e6f-4046-8207-75e63c56c4e4 |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 12:25:16 |
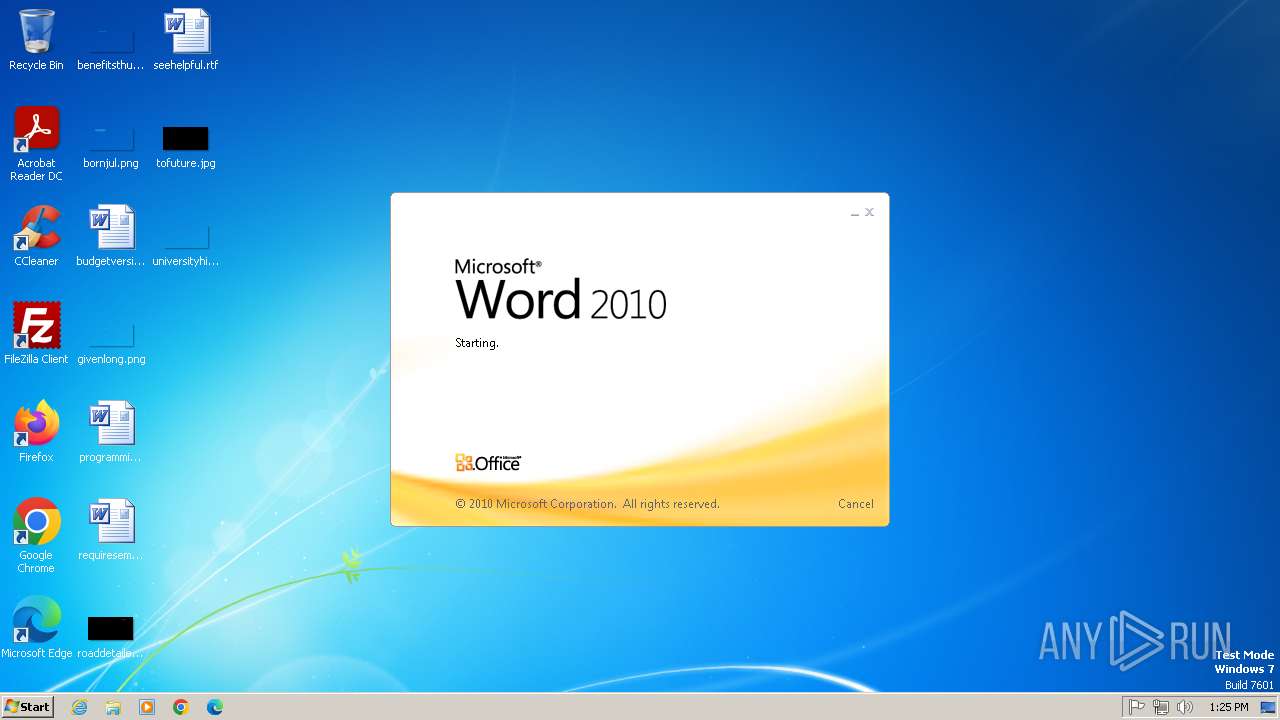
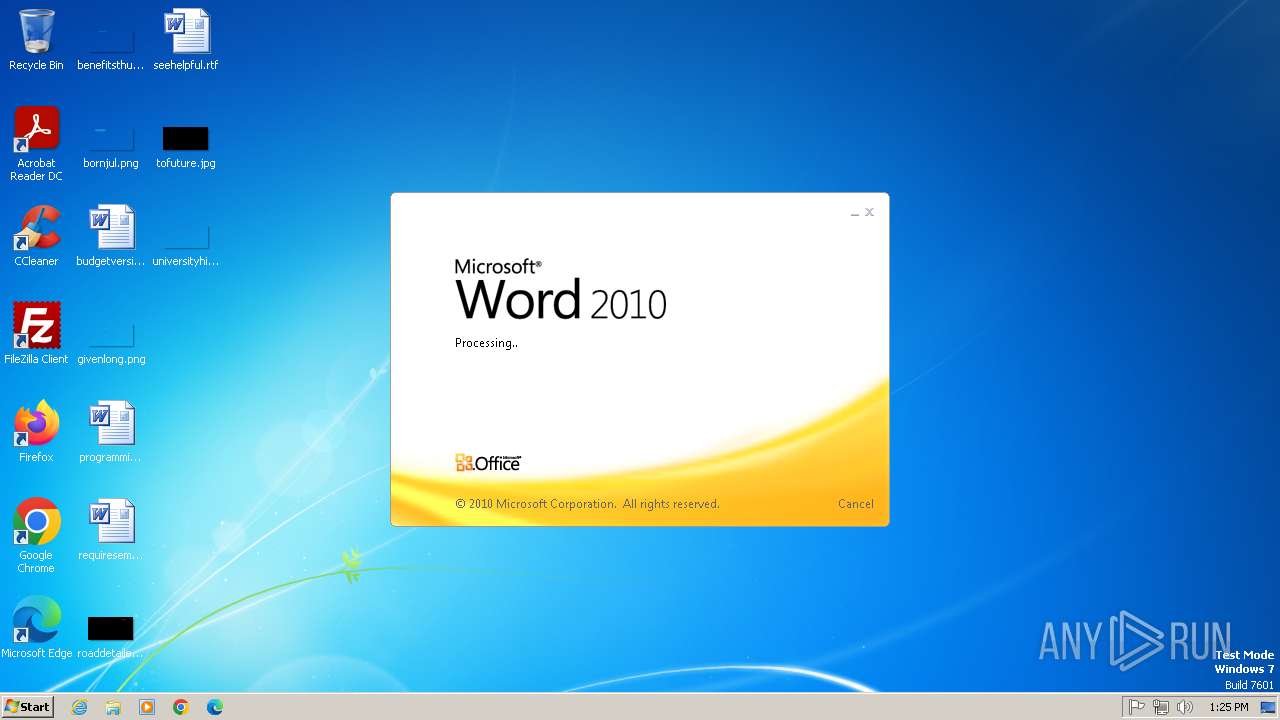
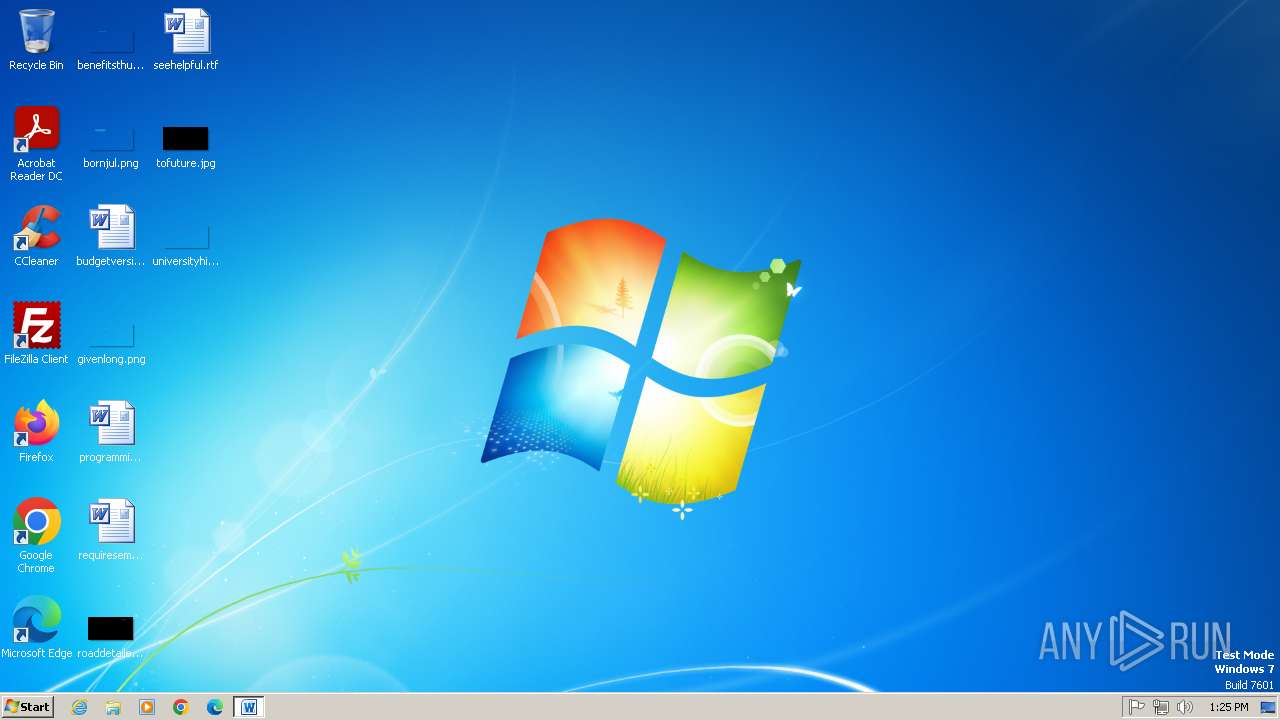
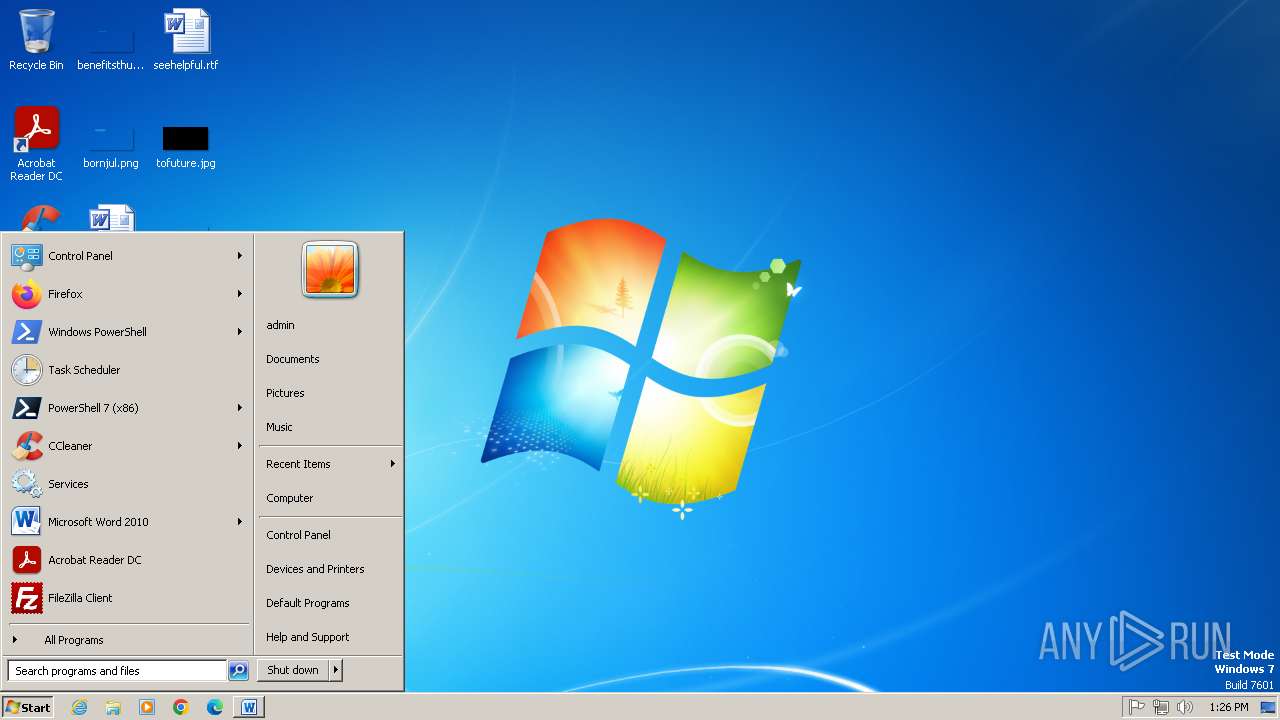
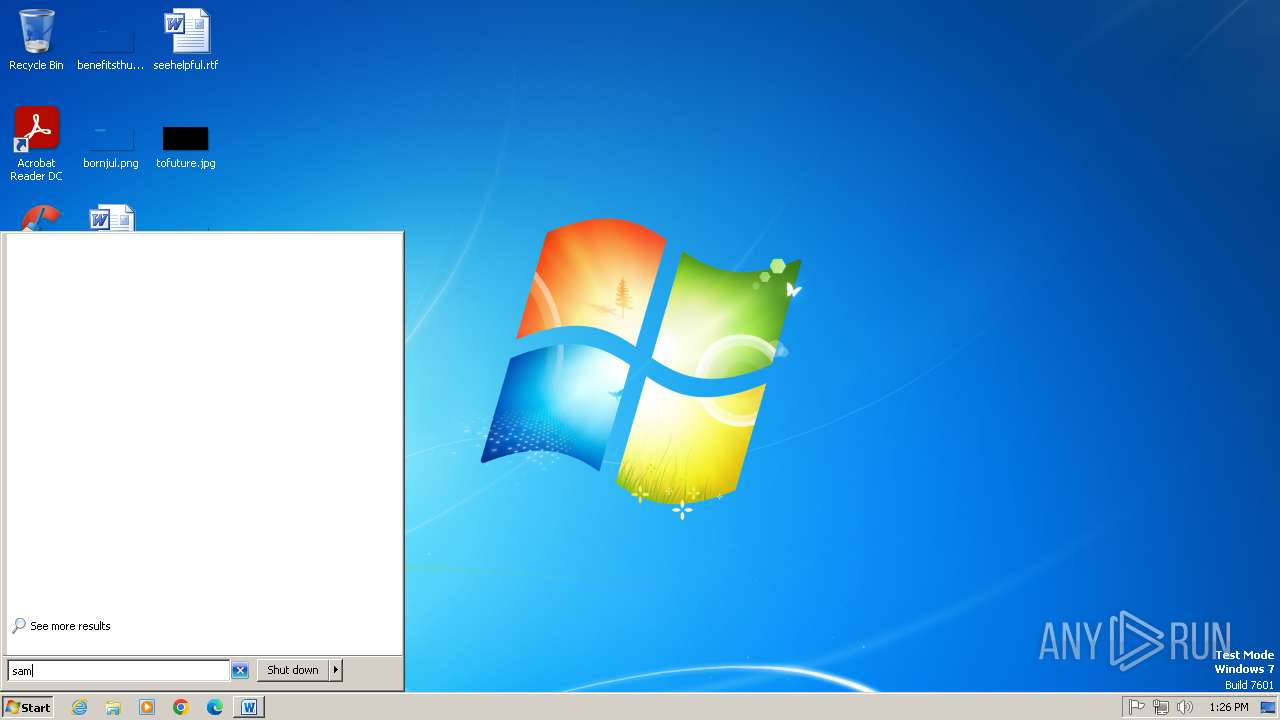
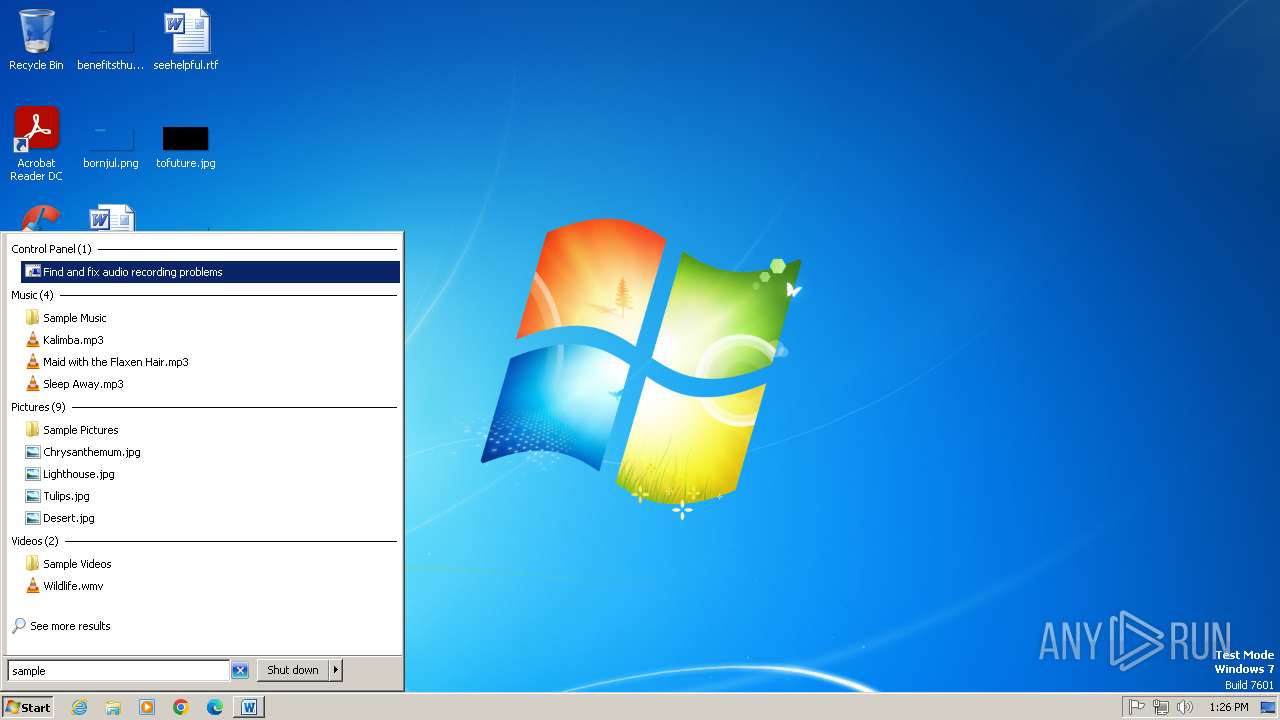
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 52945AF1DEF85B171870B31FA4782E52 |
| SHA1: | 06727FFDA60359236A8029E0B3E8A0FD11C23313 |
| SHA256: | 4A24048F81AFBE9FB62E7A6A49ADBD1FAF41F266B5F9FEECDCEB567AEC096784 |
| SSDEEP: | 192:AEhM7fIUU09264wptGheab8h7Z/c+8poF1d3jvvtl59rGxjPQDasYBcG7h+:AqWfIz092hwLGAabkcfa7pr1lzyxjPQ9 |
MALICIOUS
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 1080)
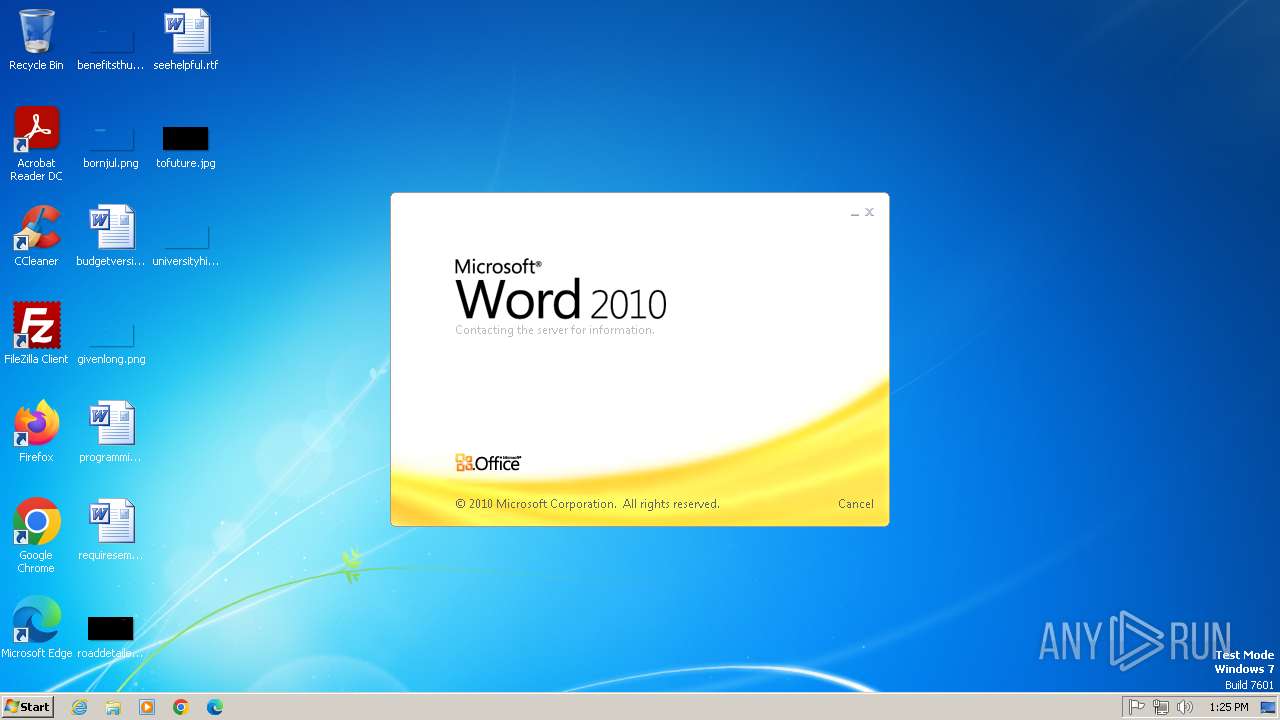
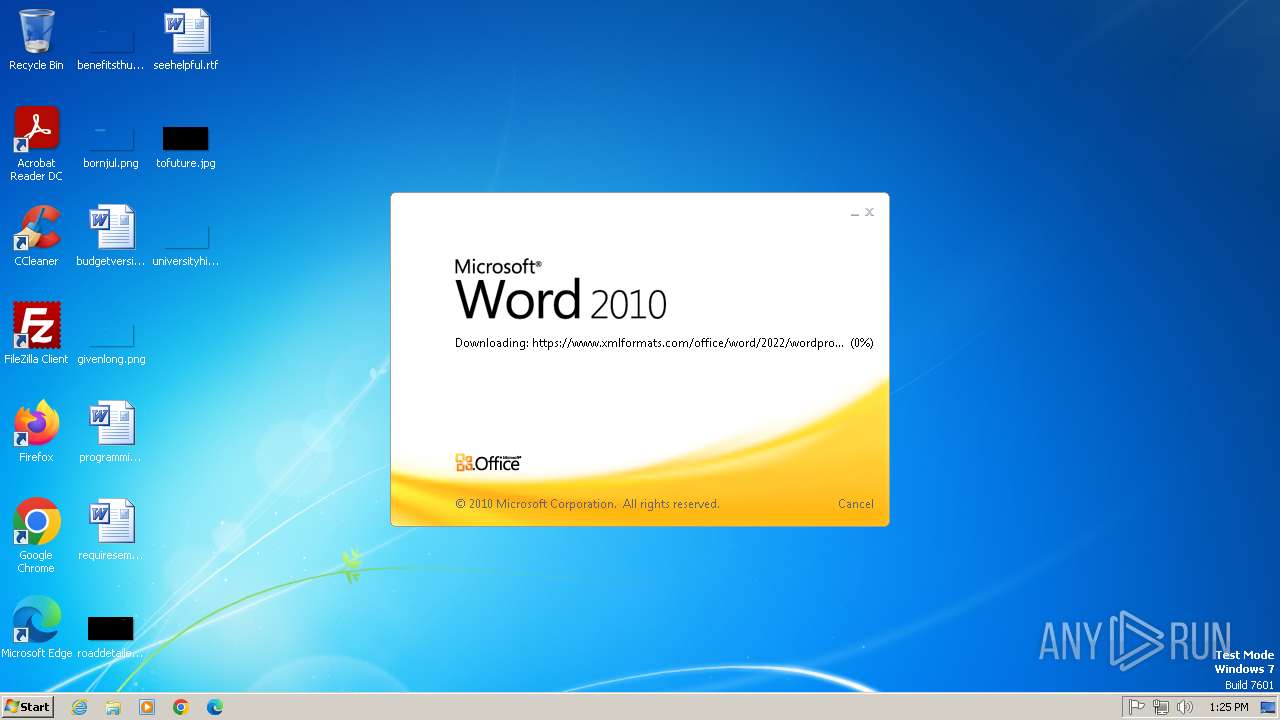
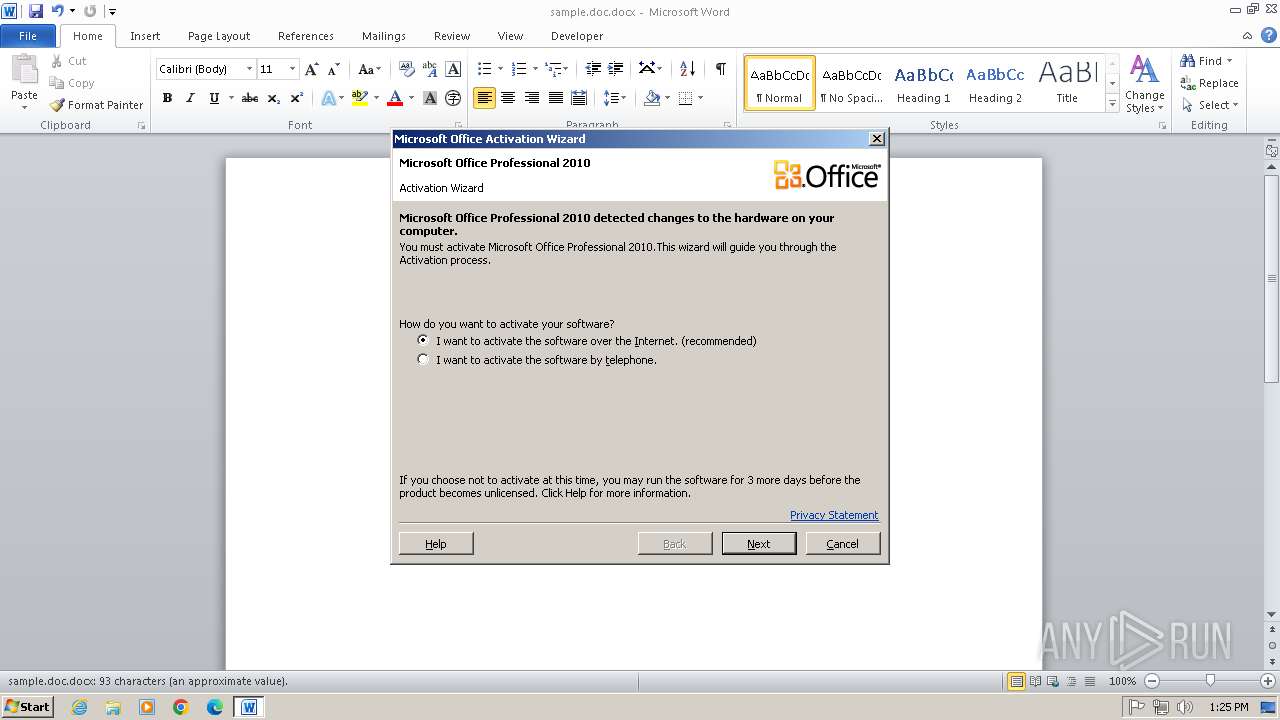
CVE-2022-30190 detected
- WINWORD.EXE (PID: 1396)
SUSPICIOUS
Abuses WebDav for code execution
- svchost.exe (PID: 832)
Uses RUNDLL32.EXE to load library
- svchost.exe (PID: 832)
INFO
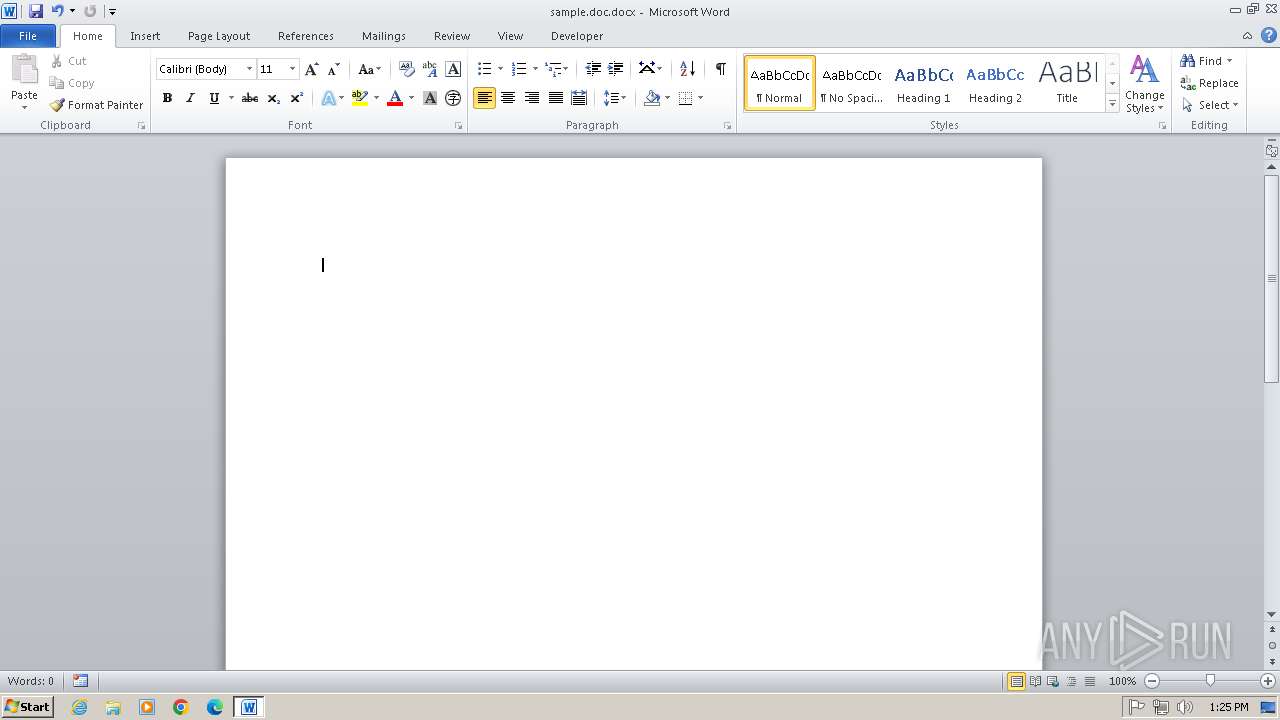
An automatically generated document
- WINWORD.EXE (PID: 1396)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2022:05:26 23:08:14 |
| ZipCRC: | 0x6cd2a4df |
| ZipCompressedSize: | 340 |
| ZipUncompressedSize: | 1312 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal |
|---|---|
| TotalEditTime: | - |
| Pages: | 1 |
| Words: | - |
| Characters: | - |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | - |
| Paragraphs: | - |
| ScaleCrop: | No |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | - |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
| Keywords: | - |
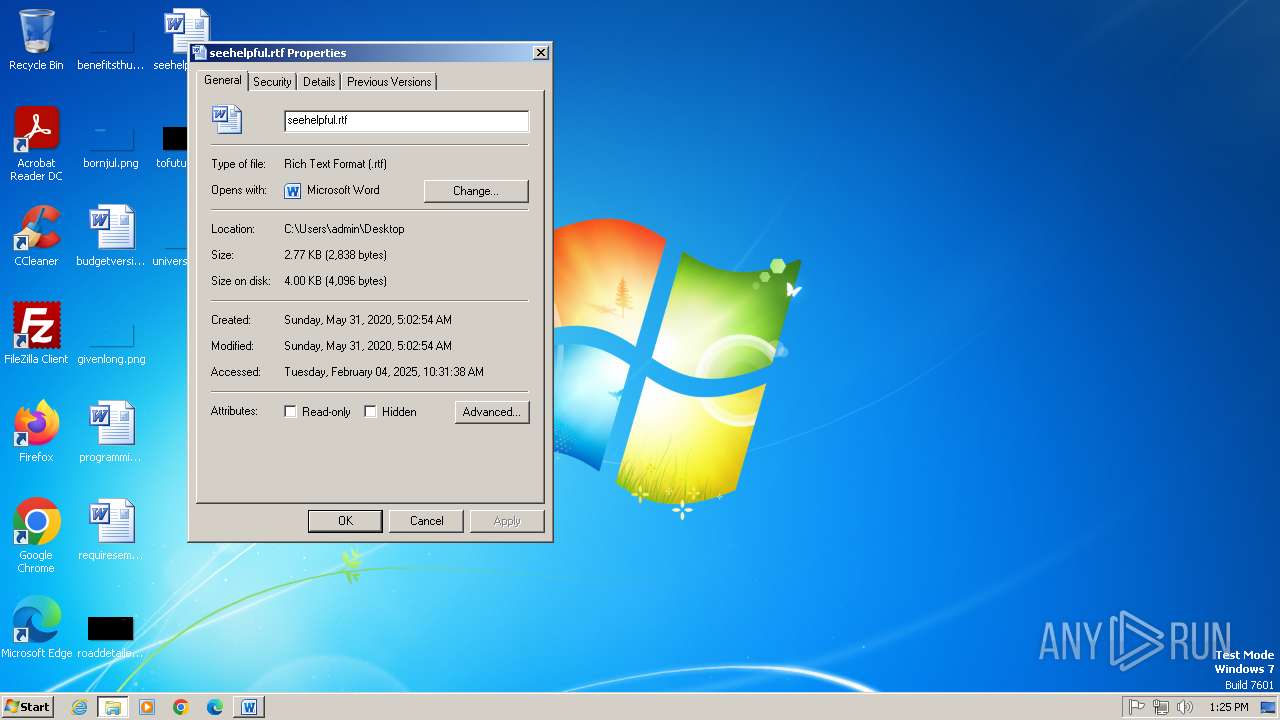
| LastModifiedBy: | KIS2 |
| RevisionNumber: | 3 |
| CreateDate: | 2022:05:25 13:14:00Z |
| ModifyDate: | 2022:05:25 13:14:00Z |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | KIS2 |
| Description: | - |
Total processes
38
Monitored processes
3
Malicious processes
2
Suspicious processes
1
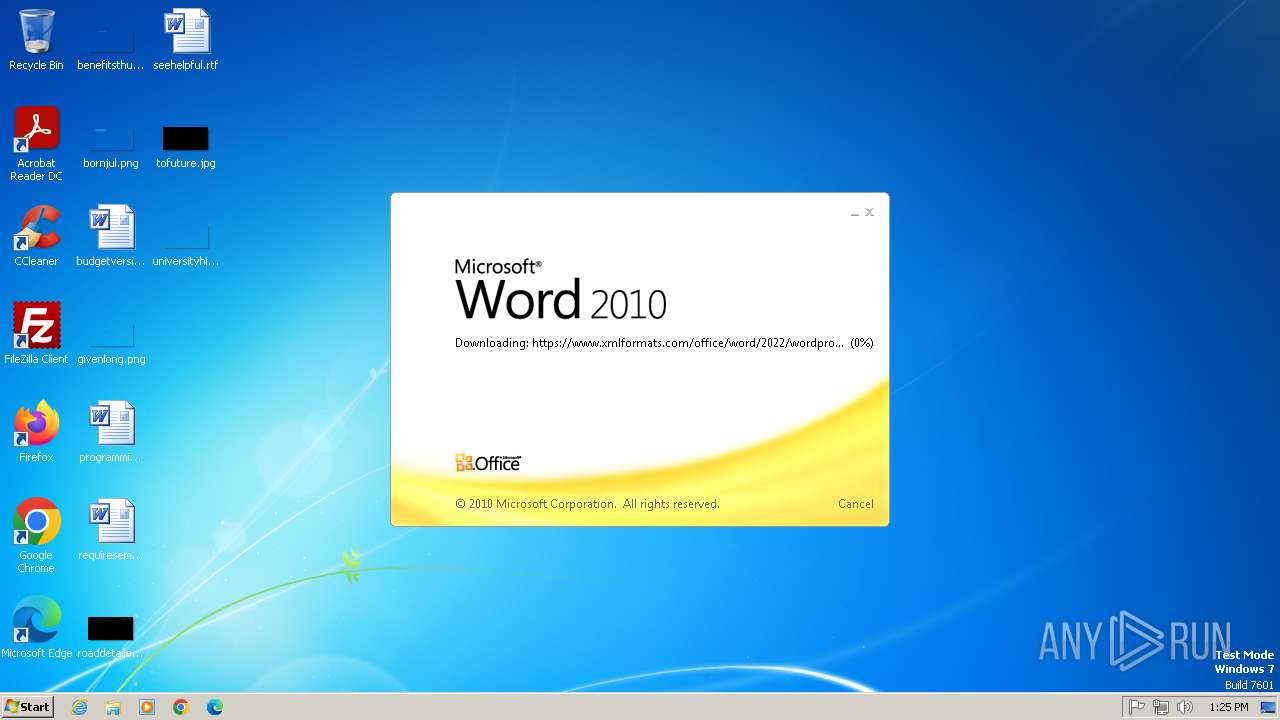
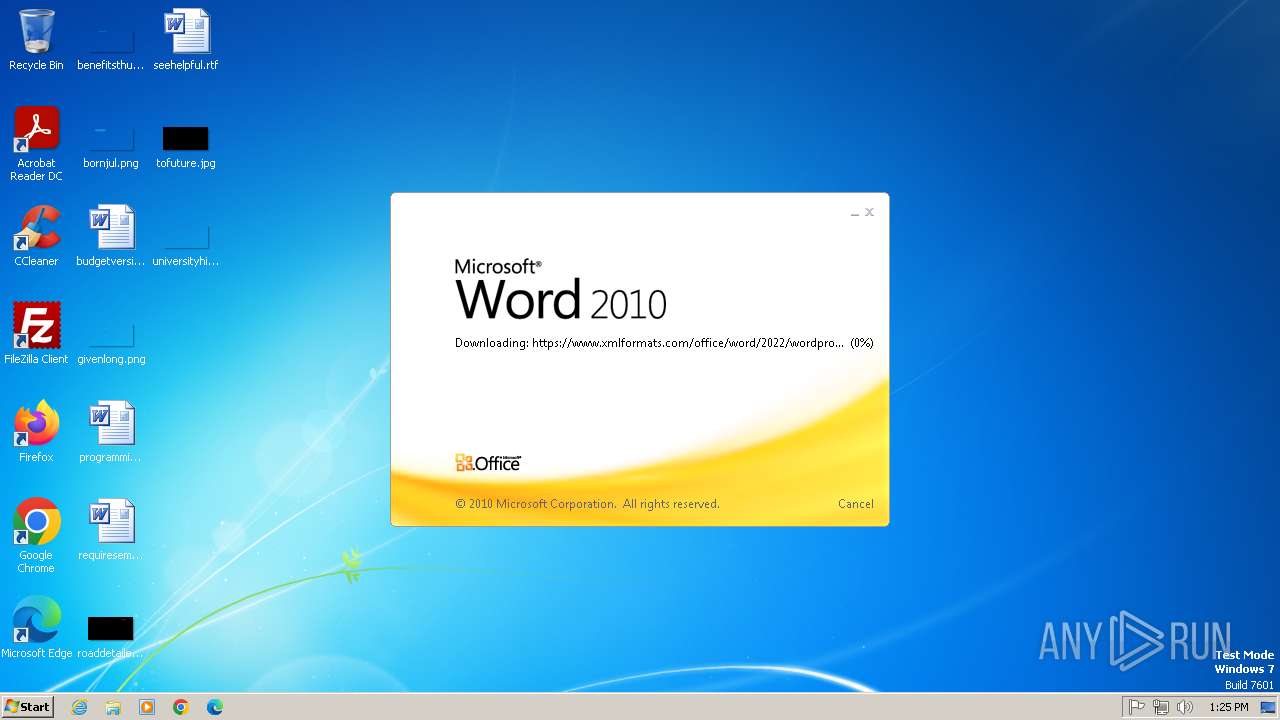
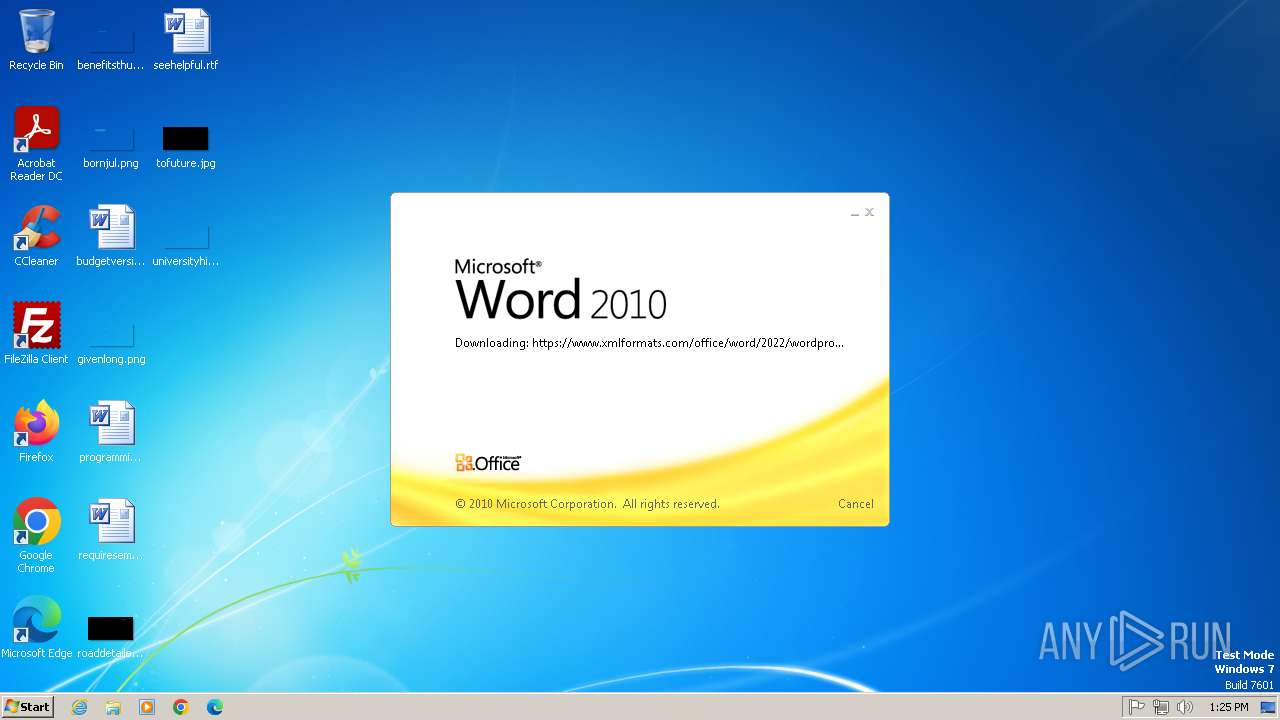
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 832 | C:\Windows\system32\svchost.exe -k LocalService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1080 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
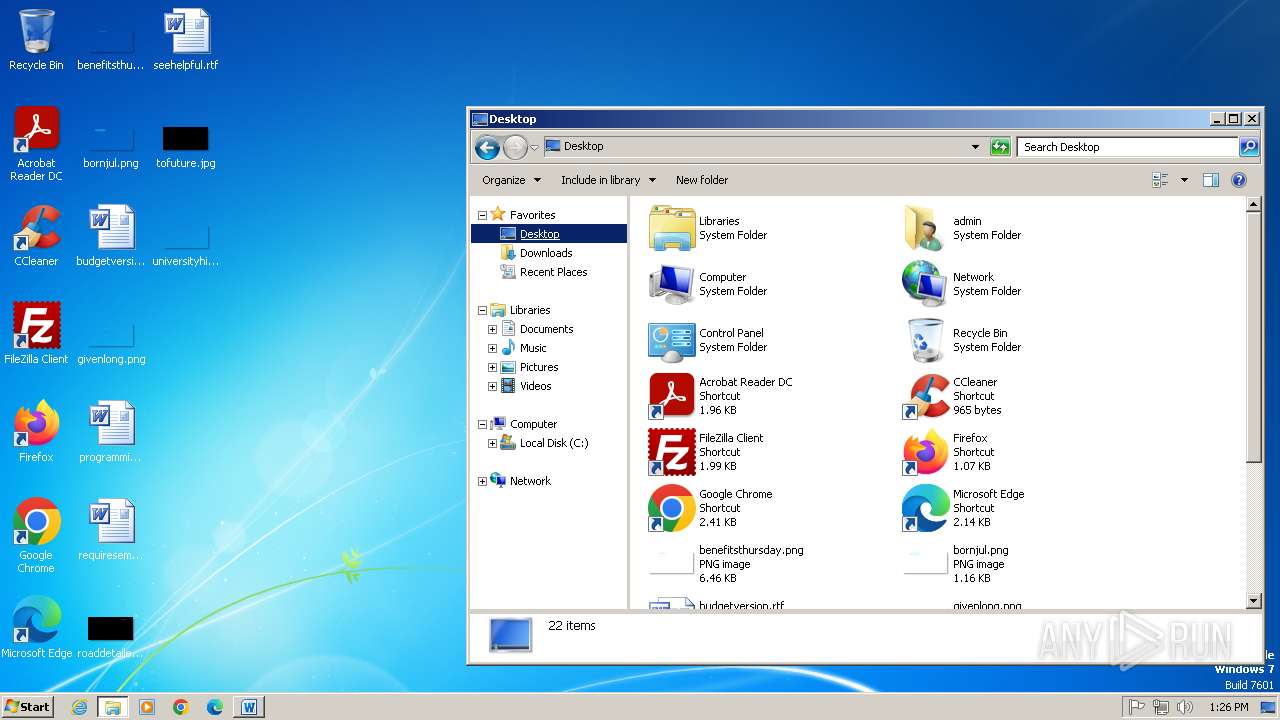
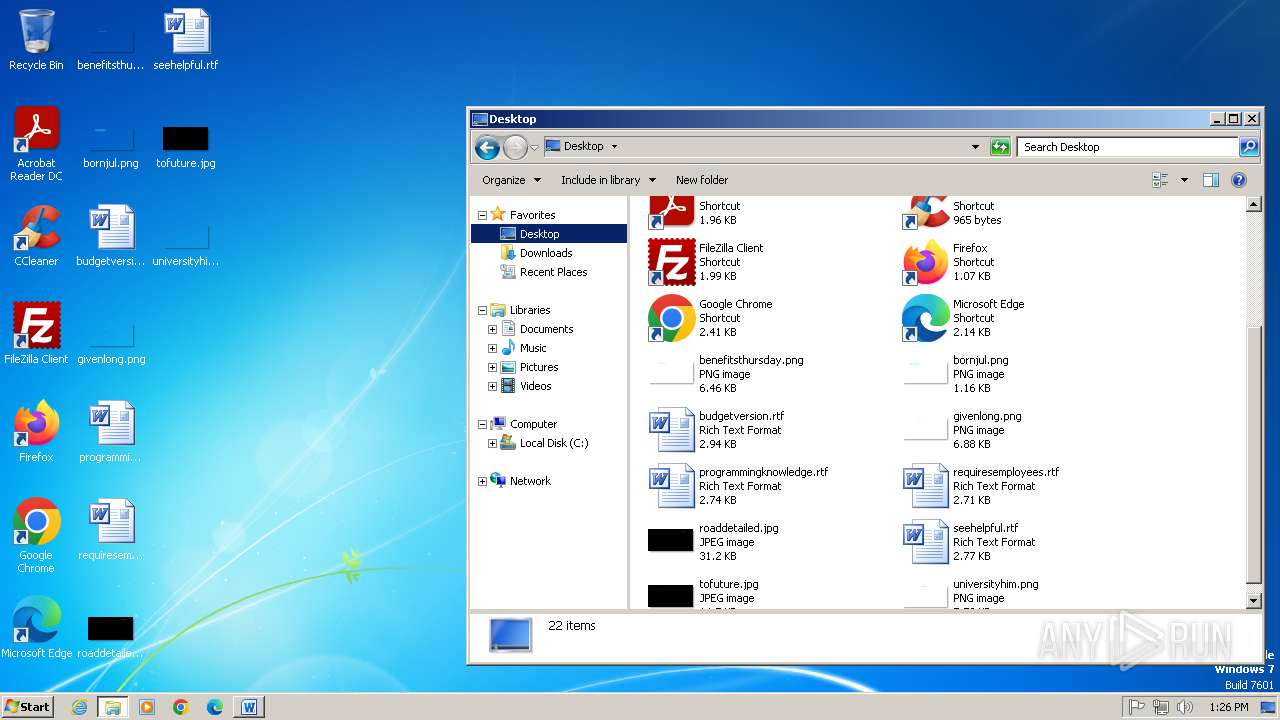
| 1396 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n C:\Users\admin\AppData\Local\Temp\sample.doc.docx | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
15 986
Read events
15 154
Write events
587
Delete events
245
Modification events
| (PID) Process: | (1396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | #<" |
Value: 233C220074050000010000000000000000000000 | |||
| (PID) Process: | (1396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
20
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1396 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR1894.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1396 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{959C6B68-3198-4BDD-B467-F0C1419A4188} | binary | |
MD5:B3823B1EAEB9FE155E57638513B34A25 | SHA256:6DA3FAC4EDBA11A4E97542122EDF417C39CF76696337B6FCD49FB991AE8F2CF4 | |||
| 1080 | svchost.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Local\Temp\Cab1D66.tmp | compressed | |
MD5:77B20B5CD41BC6BB475CCA3F91AE6E3C | SHA256:5511A9B9F9144ED7BDE4CCB074733B7C564D918D2A8B10D391AFC6BE5B3B1509 | |||
| 1396 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:D0C2C25A73CC9FCB80897D73BD5EA8ED | SHA256:D7135F580E7E71382F24543200A8349B22985F097DE80E42B884D58AF5FDFEE9 | |||
| 1396 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:77B20B5CD41BC6BB475CCA3F91AE6E3C | SHA256:5511A9B9F9144ED7BDE4CCB074733B7C564D918D2A8B10D391AFC6BE5B3B1509 | |||
| 1396 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:E192462F281446B5D1500D474FBACC4B | SHA256:F1BA9F1B63C447682EBF9DE956D0DA2A027B1B779ABEF9522D347D3479139A60 | |||
| 1080 | svchost.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Local\Temp\Tar1D67.tmp | binary | |
MD5:91A1B89AA7A488DBB204DBB4767F1F21 | SHA256:F6BE95C88C20EF82EE8A6878E16F9ECD77300BC1905EB826592A0DD41AD1C0F8 | |||
| 1396 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:A115549B1DAF0838F1CA178B09E85971 | SHA256:D6C87986CB8F7EB1BBE672698DBF1BCECD27BB600D069E7BCB21600396FCECC1 | |||
| 1396 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSD-CNRY.FSD | binary | |
MD5:B3823B1EAEB9FE155E57638513B34A25 | SHA256:6DA3FAC4EDBA11A4E97542122EDF417C39CF76696337B6FCD49FB991AE8F2CF4 | |||
| 1396 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\96027925CAA49D567EF24E394DA96DDC_E3A1357637564DB9BE9C638629EAA28C | binary | |
MD5:49EC1E263A7FC5A4AF4EEF0819933CBA | SHA256:1B13195022F3DD626EF5E3D4E721D153BB41AD6119331D02DBD2CB90279B51CC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
20
DNS requests
7
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1396 | WINWORD.EXE | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fc246f5336ead010 | unknown | — | — | whitelisted |
1396 | WINWORD.EXE | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
1396 | WINWORD.EXE | GET | 200 | 184.24.77.62:80 | http://r10.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRpD%2BQVZ%2B1vf7U0RGQGBm8JZwdxcgQUdKR2KRcYVIUxN75n5gZYwLzFBXICEgbDfqxCJlObkwJ9KGuu2JC5Yg%3D%3D | unknown | — | — | whitelisted |
1396 | WINWORD.EXE | HEAD | 200 | 199.59.243.228:80 | http://survey-smiles.com/ | unknown | — | — | whitelisted |
1396 | WINWORD.EXE | HEAD | 200 | 199.59.243.228:80 | http://survey-smiles.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
1396 | WINWORD.EXE | 185.107.56.60:443 | www.xmlformats.com | NForce Entertainment B.V. | NL | malicious |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1396 | WINWORD.EXE | 199.232.210.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
1396 | WINWORD.EXE | 69.192.161.44:80 | x1.c.lencr.org | AKAMAI-AS | DE | whitelisted |
1396 | WINWORD.EXE | 184.24.77.62:80 | r10.o.lencr.org | Akamai International B.V. | DE | whitelisted |
832 | svchost.exe | 185.107.56.60:443 | www.xmlformats.com | NForce Entertainment B.V. | NL | malicious |
1396 | WINWORD.EXE | 199.59.243.228:80 | survey-smiles.com | AMAZON-02 | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.xmlformats.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r10.o.lencr.org |
| whitelisted |
survey-smiles.com |
| whitelisted |
dns.msftncsi.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1396 | WINWORD.EXE | Misc activity | ET USER_AGENTS Microsoft Office Existence Discovery User-Agent |
1 ETPRO signatures available at the full report